| URL: | http://reply.repairshopr.com/ls/click?upn=u001.0LdkpZLuMcTayV74o1xH-2FMaWFcrIfj3KGVaE1TFDaQuCVoSCz45MSSM9b3pFauXRCbh9XtvZcHL-2FWoJDPfx2HA-3D-3DVRSl_E3jX7UdwUvWW16GmiaKN7CfJ5EKnp32UjaokugJC9ydcXRGxhbjJ10ma-2FfXXiGie3j2LPIoypHM349kLqPzNv7Zf0yY7z7IXqMSb9zYbeCZTF1j-2B5YqyaekdfJNNX1u7cnOF-2FbBBP2KyANkmlEs0U04Zdg1wwgLJOJzERfQ6BWRLid5FUiLU0PVZ3WQ9tZxmhd1-2FcPUlPTrrAhtVs9pE3uv1sNOfarCcCIHdtewx9ythCegDiPJrwgGV4X06aD28 |
| Full analysis: | https://app.any.run/tasks/a562a3e1-b164-4cc0-879b-5488b3754b7e |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2025, 08:28:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 63F24535B242092D70026D94C9C54835 |
| SHA1: | E9E501A4231D7F11759AAB41A93E7E870EC31519 |
| SHA256: | B19B6471456D3CF00116D463E3551DC07262134F04BCE31A1EF9E48F7A0F37A2 |
| SSDEEP: | 12:ZZjJSxBOKiBRIHMhpvmzIiEqbHbpowxTHr:TQO7wMhQzTJRL |
MALICIOUS
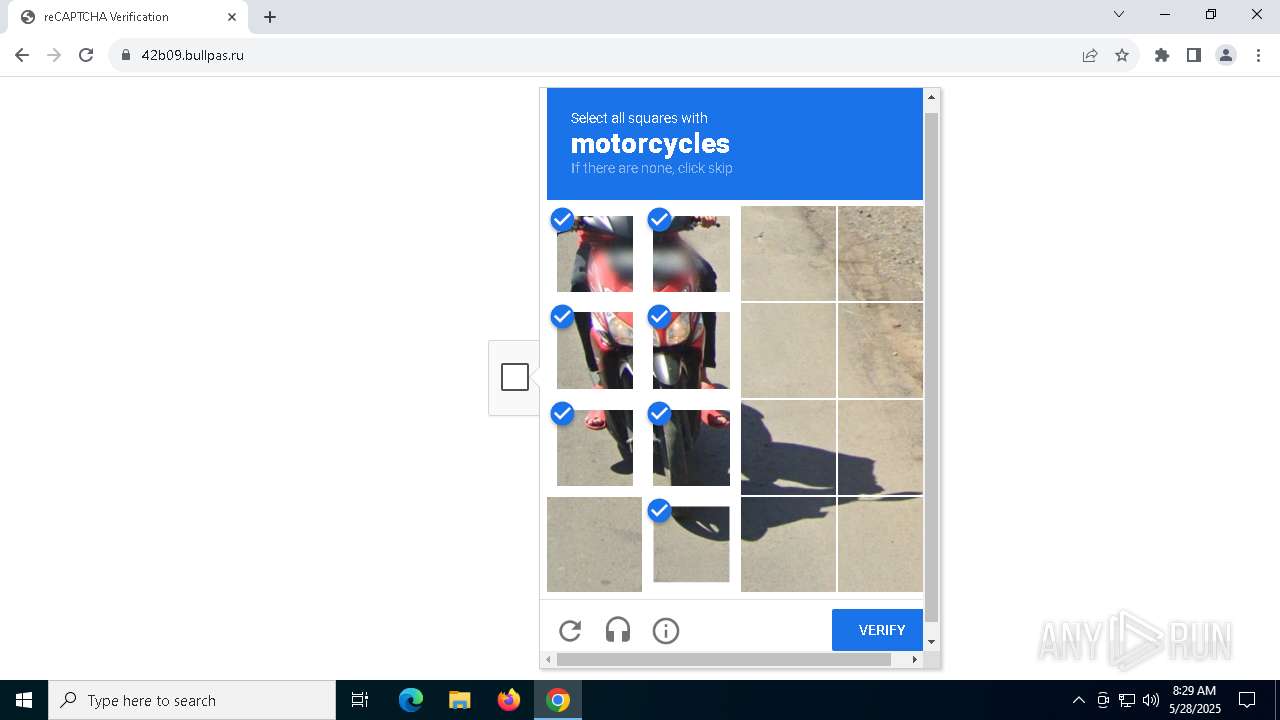
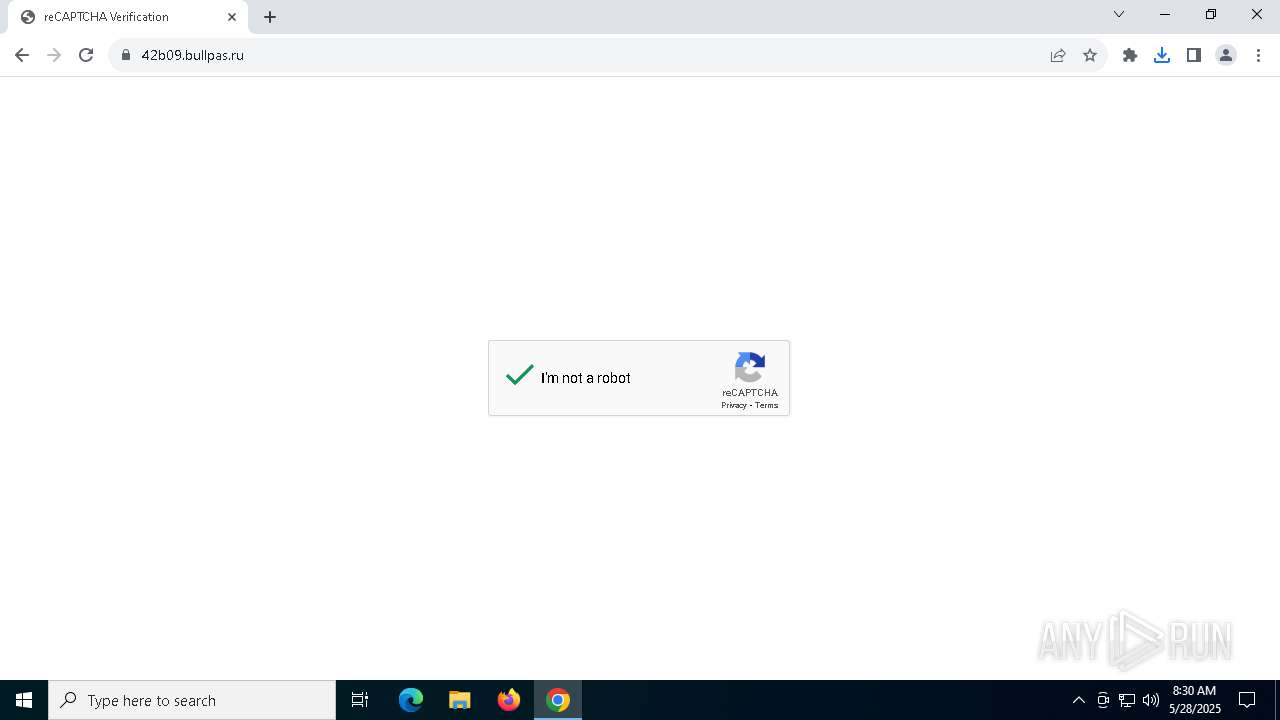
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 7528)
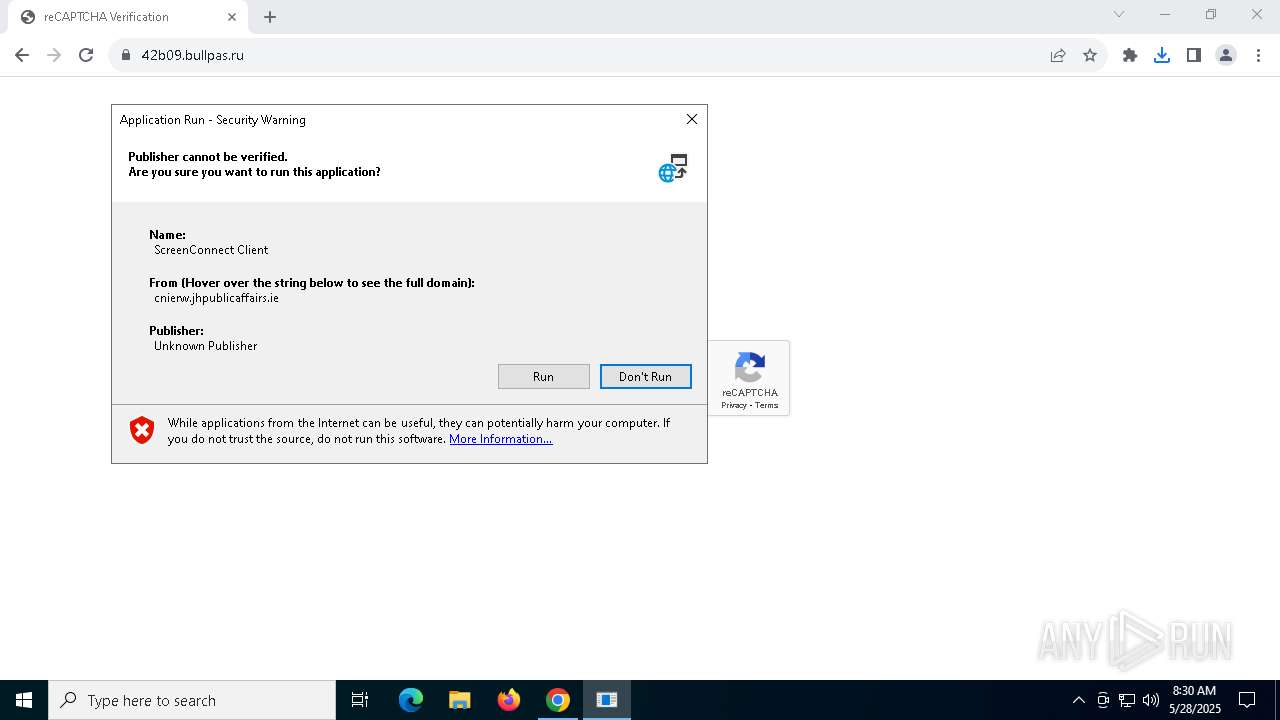
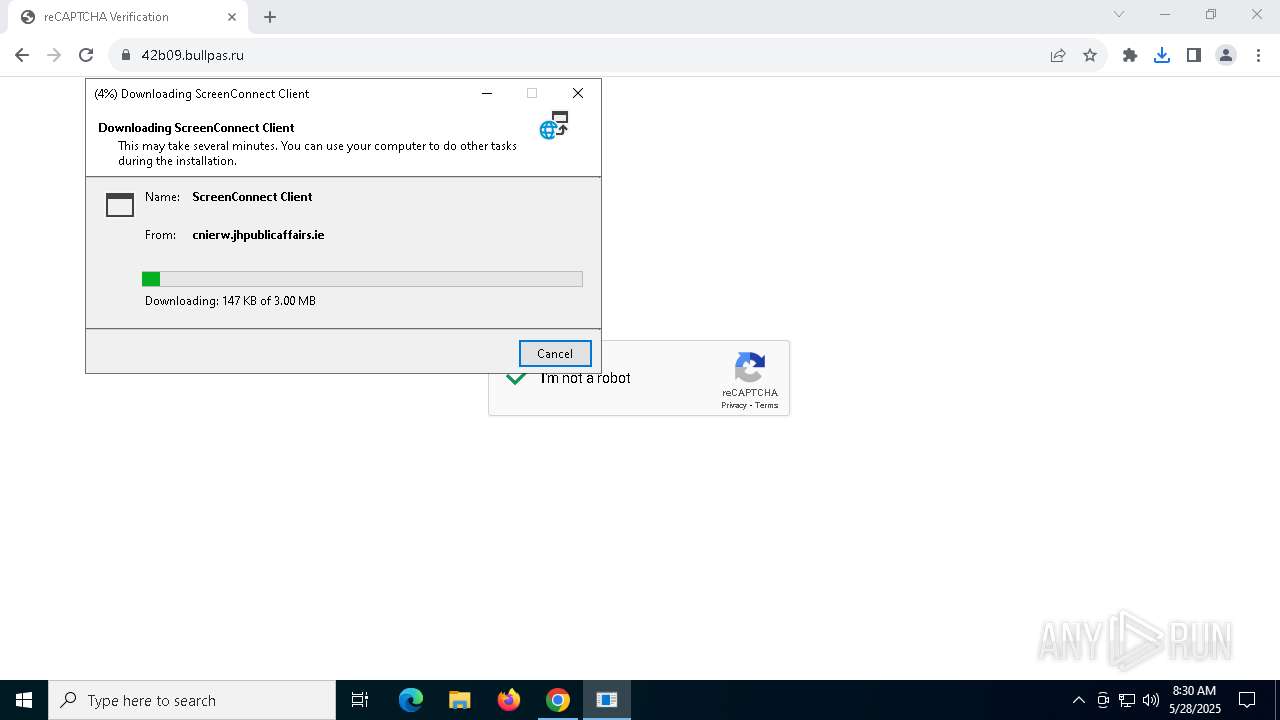
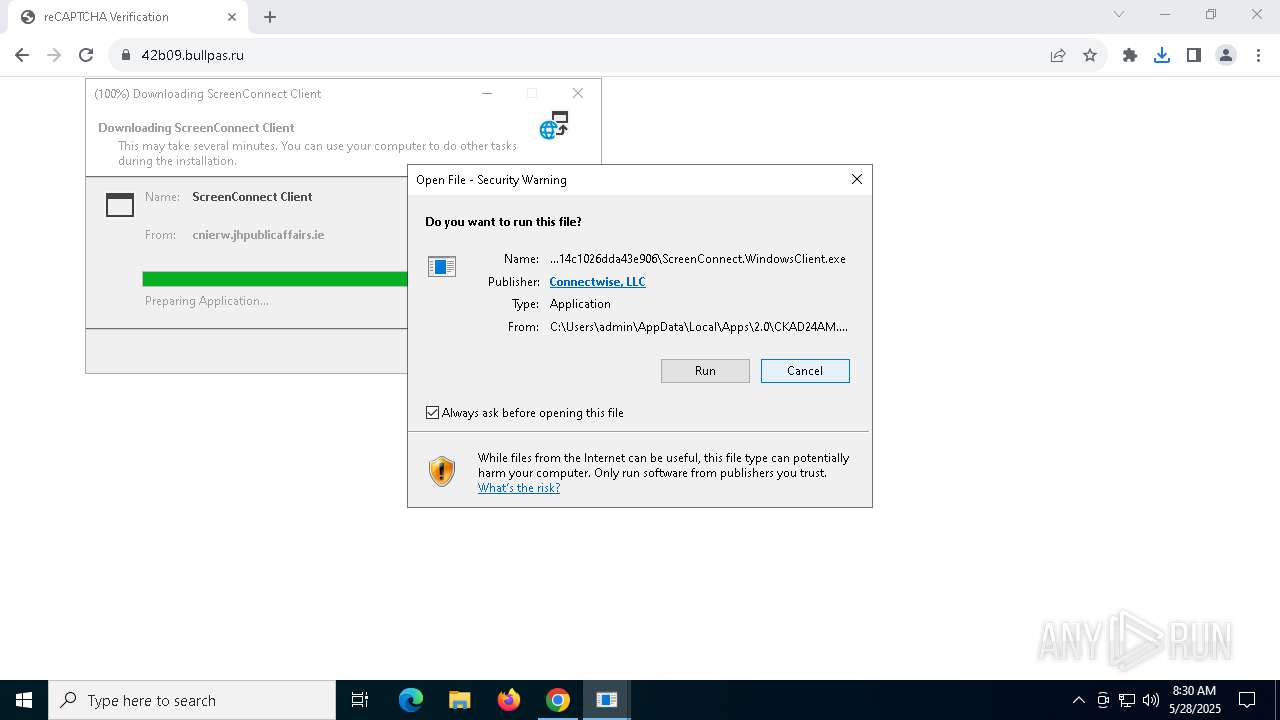
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 6148)
SUSPICIOUS
Adds/modifies Windows certificates
- Document_6836c981b19b7.exe (PID: 8144)
- dfsvc.exe (PID: 5404)
Connects to unusual port
- dfsvc.exe (PID: 5404)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 5404)
Reads the date of Windows installation
- dfsvc.exe (PID: 5404)
- ScreenConnect.WindowsClient.exe (PID: 7208)
Reads security settings of Internet Explorer
- dfsvc.exe (PID: 5404)
- ScreenConnect.WindowsClient.exe (PID: 7208)
- ScreenConnect.ClientService.exe (PID: 2552)
- ScreenConnect.ClientService.exe (PID: 6148)
- ScreenConnect.WindowsClient.exe (PID: 2908)
- ScreenConnect.WindowsClient.exe (PID: 7176)
Reads Internet Explorer settings
- dfsvc.exe (PID: 5404)
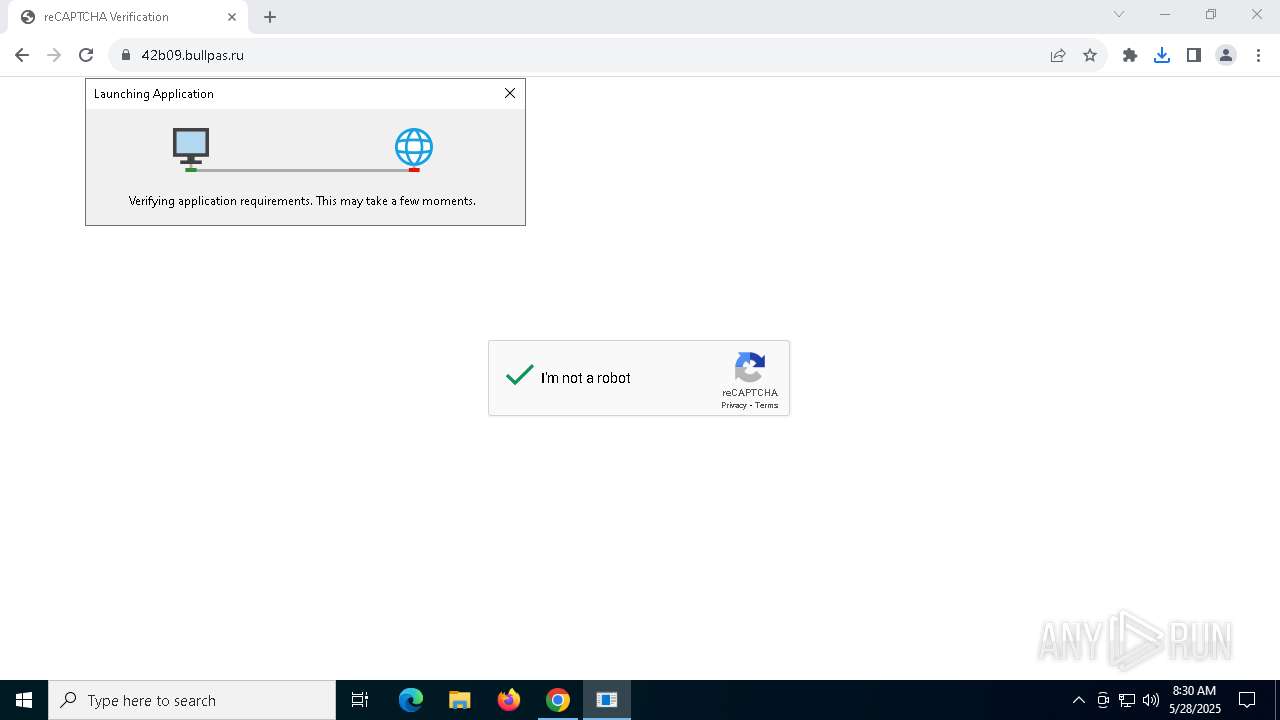
Executable content was dropped or overwritten
- dfsvc.exe (PID: 5404)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 6148)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 6148)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 6148)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 6148)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 6148)
INFO
Application launched itself
- chrome.exe (PID: 7268)
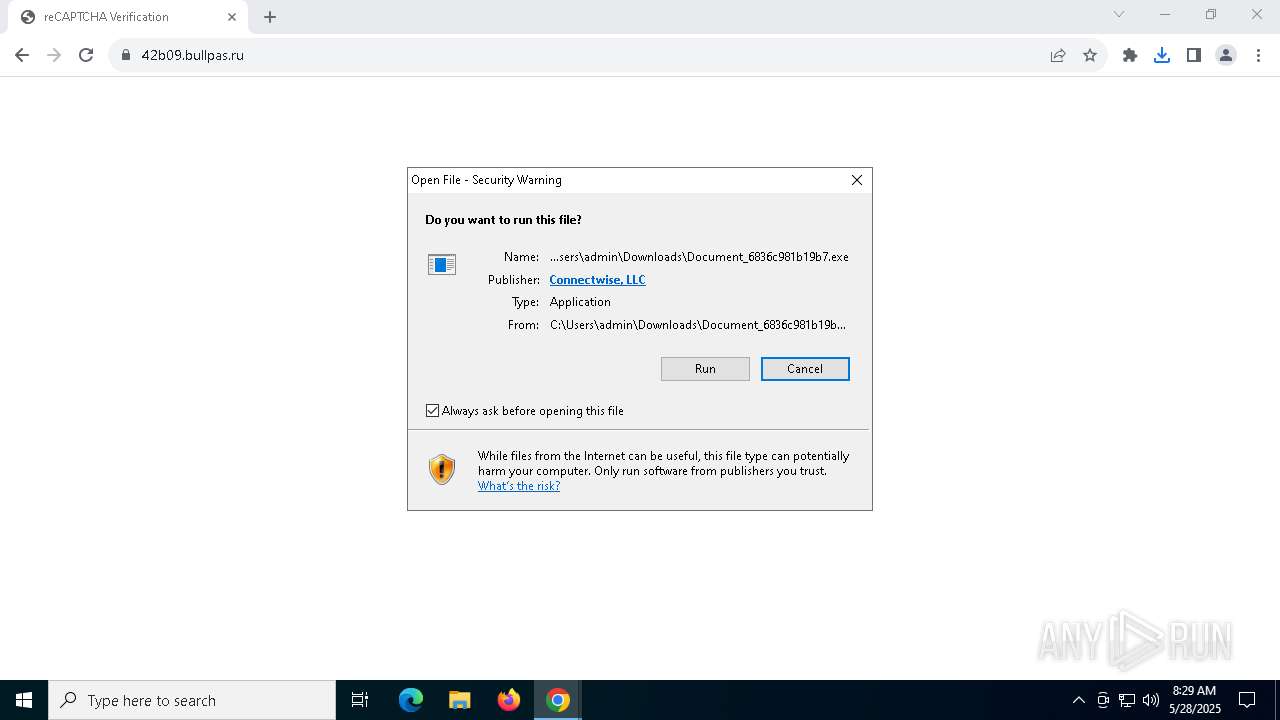
Launch of the file from Downloads directory
- chrome.exe (PID: 4284)
- chrome.exe (PID: 7268)
Executable content was dropped or overwritten
- chrome.exe (PID: 7268)
Reads the machine GUID from the registry
- Document_6836c981b19b7.exe (PID: 8144)
- dfsvc.exe (PID: 5404)
- ScreenConnect.ClientService.exe (PID: 2552)
- ScreenConnect.ClientService.exe (PID: 6148)
- ScreenConnect.WindowsClient.exe (PID: 7208)
- ScreenConnect.WindowsClient.exe (PID: 2908)
- ScreenConnect.WindowsClient.exe (PID: 7176)
Checks supported languages
- Document_6836c981b19b7.exe (PID: 8144)
- dfsvc.exe (PID: 5404)
- ScreenConnect.ClientService.exe (PID: 2552)
- ScreenConnect.ClientService.exe (PID: 6148)
- ScreenConnect.WindowsClient.exe (PID: 7208)
- ScreenConnect.WindowsClient.exe (PID: 7176)
- ScreenConnect.WindowsClient.exe (PID: 2908)
Reads the computer name
- dfsvc.exe (PID: 5404)
- Document_6836c981b19b7.exe (PID: 8144)
- ScreenConnect.ClientService.exe (PID: 2552)
- ScreenConnect.ClientService.exe (PID: 6148)
- ScreenConnect.WindowsClient.exe (PID: 7208)
- ScreenConnect.WindowsClient.exe (PID: 7176)
- ScreenConnect.WindowsClient.exe (PID: 2908)
Reads the software policy settings
- slui.exe (PID: 8052)
- dfsvc.exe (PID: 5404)
Creates files or folders in the user directory
- dfsvc.exe (PID: 5404)
- ScreenConnect.WindowsClient.exe (PID: 7208)
- ScreenConnect.ClientService.exe (PID: 6148)
Disables trace logs
- dfsvc.exe (PID: 5404)
Reads Environment values
- dfsvc.exe (PID: 5404)
Checks proxy server information
- dfsvc.exe (PID: 5404)
Create files in a temporary directory
- dfsvc.exe (PID: 5404)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 5404)
Process checks computer location settings
- ScreenConnect.WindowsClient.exe (PID: 7208)
- dfsvc.exe (PID: 5404)
SCREENCONNECT has been detected
- ScreenConnect.ClientService.exe (PID: 6148)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 2908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
163
Monitored processes
28
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2552 | "C:\Users\admin\AppData\Local\Apps\2.0\CKAD24AM.2AX\9448W384.5GZ\scre..tion_25b0fbb6ef7eb094_0017.0002_14c1026dda43e906\ScreenConnect.ClientService.exe" "?y=Guest&h=843m.securenethub.ru&p=443&s=d4d8ceab-1814-438c-9f9d-63645815a589&k=BgIAAACkAABSU0ExAAgAAAEAAQBVXsSEc%2bx9uXD3C%2f7hA6k%2bCkYq8qNt9ddXTDuk6xtcDXcigKgagdDrv%2fcdVObs%2b5PsIEqa3J7G2KVNlw%2fruJmp5gWKLUA7CGK0M2xYP%2fnHrh8PGKb6APgX8%2bMmK%2fRI%2fuG1ObyHzrZSA2zDxqMWtbhBTbrYOR9GzyZRtT2sHBbUlx41DAcKHlRcqgqrm7UWwNY1mXMg1RfS2uCkTVjdU3GL7AKxo9LZAF%2bNZ31xMPej0IfTdjxJIuBFFPQhiLUl3MrrnM%2bcDzOJ4R5qzkEDJux1InHPO4447uQgY2C%2fpH9XXbyUJCVvgFFCPS5LSQJiQ7CvgPW3fKiAsEahrr56vu2y&r=&i=Untitled%20Session" "5" | C:\Users\admin\AppData\Local\Apps\2.0\CKAD24AM.2AX\9448W384.5GZ\scre..tion_25b0fbb6ef7eb094_0017.0002_14c1026dda43e906\ScreenConnect.ClientService.exe | ScreenConnect.WindowsClient.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 23.2.9.8466 Modules
| |||||||||||||||
| 2908 | "C:\Users\admin\AppData\Local\Apps\2.0\CKAD24AM.2AX\9448W384.5GZ\scre..tion_25b0fbb6ef7eb094_0017.0002_14c1026dda43e906\ScreenConnect.WindowsClient.exe" "RunRole" "67f0fbcf-58d8-4fe8-8ad4-34455c80eb09" "System" | C:\Users\admin\AppData\Local\Apps\2.0\CKAD24AM.2AX\9448W384.5GZ\scre..tion_25b0fbb6ef7eb094_0017.0002_14c1026dda43e906\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: SYSTEM Company: ScreenConnect Software Integrity Level: SYSTEM Description: Exit code: 0 Version: 23.2.9.8466 Modules
| |||||||||||||||
| 3784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=5372 --field-trial-handle=1848,i,18441352507465304619,8878038631329269286,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=3024 --field-trial-handle=1848,i,18441352507465304619,8878038631329269286,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5464 --field-trial-handle=1848,i,18441352507465304619,8878038631329269286,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5404 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe | Document_6836c981b19b7.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 6148 | "C:\Users\admin\AppData\Local\Apps\2.0\CKAD24AM.2AX\9448W384.5GZ\scre..tion_25b0fbb6ef7eb094_0017.0002_14c1026dda43e906\ScreenConnect.ClientService.exe" "?y=Guest&h=843m.securenethub.ru&p=443&s=d4d8ceab-1814-438c-9f9d-63645815a589&k=BgIAAACkAABSU0ExAAgAAAEAAQBVXsSEc%2bx9uXD3C%2f7hA6k%2bCkYq8qNt9ddXTDuk6xtcDXcigKgagdDrv%2fcdVObs%2b5PsIEqa3J7G2KVNlw%2fruJmp5gWKLUA7CGK0M2xYP%2fnHrh8PGKb6APgX8%2bMmK%2fRI%2fuG1ObyHzrZSA2zDxqMWtbhBTbrYOR9GzyZRtT2sHBbUlx41DAcKHlRcqgqrm7UWwNY1mXMg1RfS2uCkTVjdU3GL7AKxo9LZAF%2bNZ31xMPej0IfTdjxJIuBFFPQhiLUl3MrrnM%2bcDzOJ4R5qzkEDJux1InHPO4447uQgY2C%2fpH9XXbyUJCVvgFFCPS5LSQJiQ7CvgPW3fKiAsEahrr56vu2y&r=&i=Untitled%20Session" "5" | C:\Users\admin\AppData\Local\Apps\2.0\CKAD24AM.2AX\9448W384.5GZ\scre..tion_25b0fbb6ef7eb094_0017.0002_14c1026dda43e906\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 23.2.9.8466 Modules
| |||||||||||||||
| 6404 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7176 | "C:\Users\admin\AppData\Local\Apps\2.0\CKAD24AM.2AX\9448W384.5GZ\scre..tion_25b0fbb6ef7eb094_0017.0002_14c1026dda43e906\ScreenConnect.WindowsClient.exe" "RunRole" "cd68cea7-d7fa-4dec-a740-3248f53e071c" "User" | C:\Users\admin\AppData\Local\Apps\2.0\CKAD24AM.2AX\9448W384.5GZ\scre..tion_25b0fbb6ef7eb094_0017.0002_14c1026dda43e906\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: Version: 23.2.9.8466 Modules
| |||||||||||||||
| 7208 | "C:\Users\admin\AppData\Local\Apps\2.0\CKAD24AM.2AX\9448W384.5GZ\scre..tion_25b0fbb6ef7eb094_0017.0002_14c1026dda43e906\ScreenConnect.WindowsClient.exe" | C:\Users\admin\AppData\Local\Apps\2.0\CKAD24AM.2AX\9448W384.5GZ\scre..tion_25b0fbb6ef7eb094_0017.0002_14c1026dda43e906\ScreenConnect.WindowsClient.exe | — | dfsvc.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: Exit code: 0 Version: 23.2.9.8466 Modules
| |||||||||||||||
Total events
16 704
Read events
16 508
Write events
166
Delete events
30
Modification events
| (PID) Process: | (7268) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7268) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7268) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7268) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7268) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4284) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000009D093BB0AACFDB01 | |||
| (PID) Process: | (5404) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: 8VW787ATNNNQ8MVPC6X91W1T | |||
| (PID) Process: | (5404) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete value | Name: | ComponentStore_RandomString |
Value: 8VW787ATNNNQ8MVPC6X91W1T | |||
| (PID) Process: | (5404) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5404) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: CKAD24AM2AX9448W3845GZ2K | |||
Executable files
18
Suspicious files
61
Text files
46
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10a990.TMP | — | |
MD5:— | SHA256:— | |||
| 7268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10a9a0.TMP | — | |
MD5:— | SHA256:— | |||
| 7268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10a9a0.TMP | — | |
MD5:— | SHA256:— | |||
| 7268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10a9af.TMP | — | |
MD5:— | SHA256:— | |||
| 7268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10a961.TMP | — | |
MD5:— | SHA256:— | |||
| 7268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
48
DNS requests
58
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5796 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4724 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4724 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7268 | chrome.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7268 | chrome.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAuTYAUbzPZmQpmJmNW6l84%3D | unknown | — | — | whitelisted |
7268 | chrome.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
1568 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
1568 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1472 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5796 | svchost.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7268 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7528 | chrome.exe | 108.177.119.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7528 | chrome.exe | 104.18.5.17:443 | reply.repairshopr.com | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
reply.repairshopr.com |
| whitelisted |
accounts.google.com |
| whitelisted |
newsde836249.multiscreensite.com |
| whitelisted |
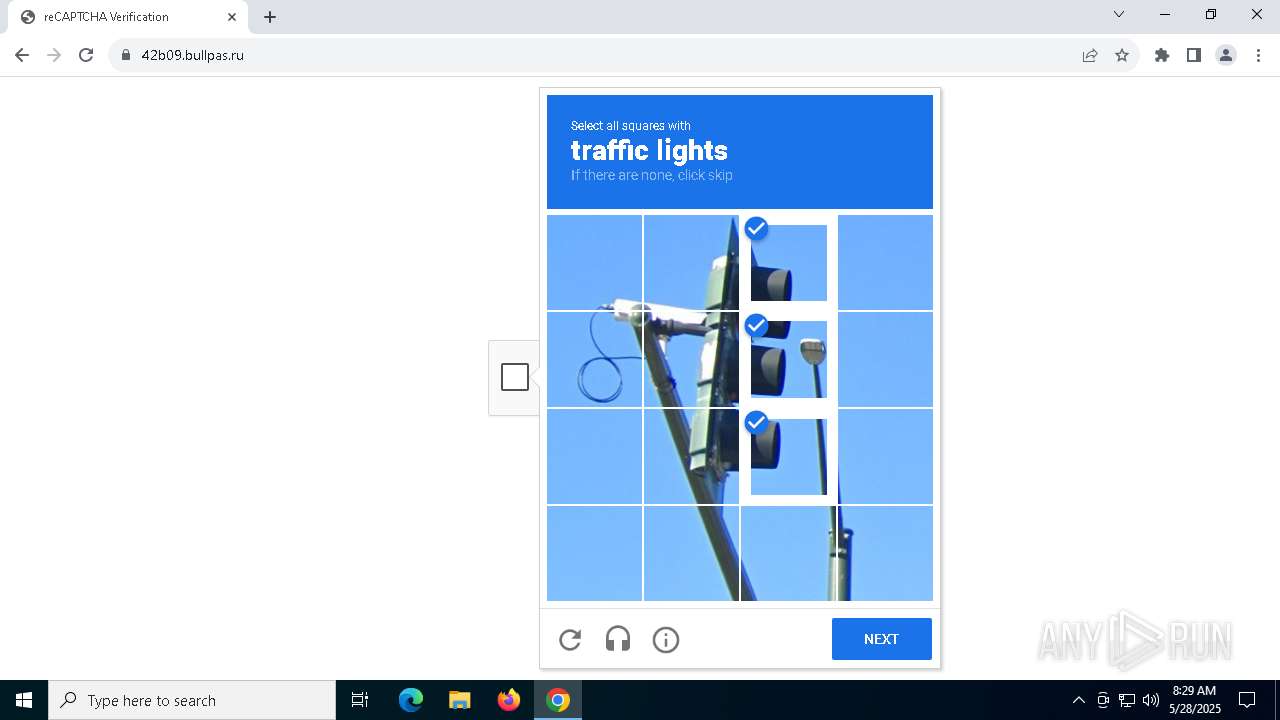
42b09.bullpas.ru |
| unknown |
a.nel.cloudflare.com |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7528 | chrome.exe | Potentially Bad Traffic | ET REMOTE_ACCESS Observed SyncroMSP Remote Management Software Domain (repairshopr .com in TLS SNI) |
7528 | chrome.exe | Potentially Bad Traffic | ET REMOTE_ACCESS Observed SyncroMSP Remote Management Software Domain in DNS Lookup (repairshopr .com) |
7528 | chrome.exe | Potentially Bad Traffic | ET REMOTE_ACCESS Observed SyncroMSP Remote Management Software Domain in DNS Lookup (repairshopr .com) |
7528 | chrome.exe | Potentially Bad Traffic | ET REMOTE_ACCESS Observed SyncroMSP Remote Management Software Domain in DNS Lookup (repairshopr .com) |
7528 | chrome.exe | Potentially Bad Traffic | ET REMOTE_ACCESS Observed SyncroMSP Remote Management Software Domain in DNS Lookup (repairshopr .com) |
7528 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7528 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
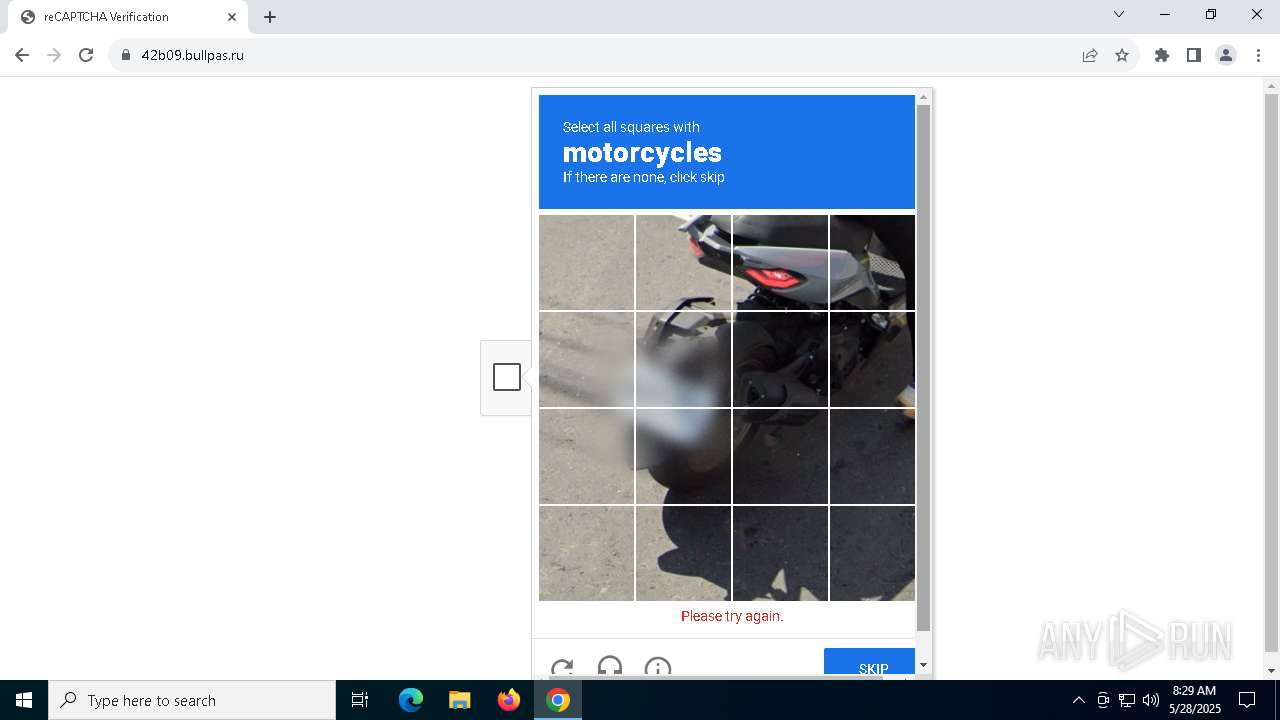
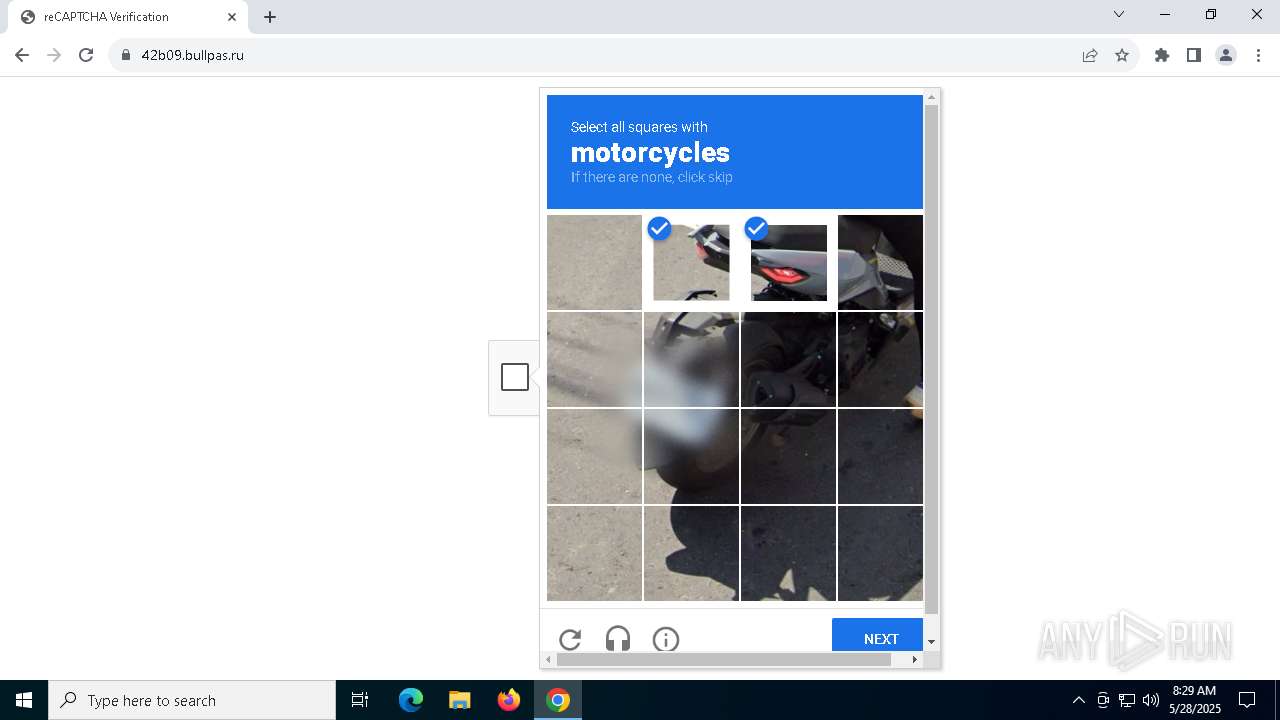
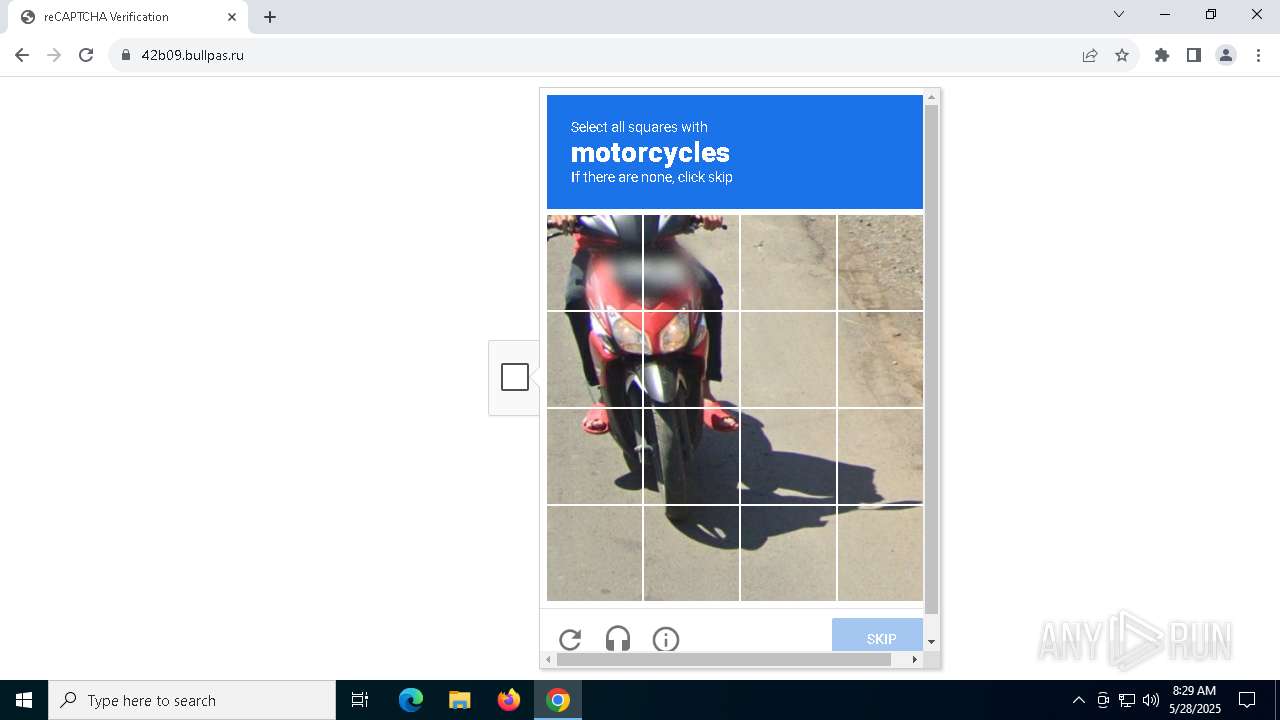
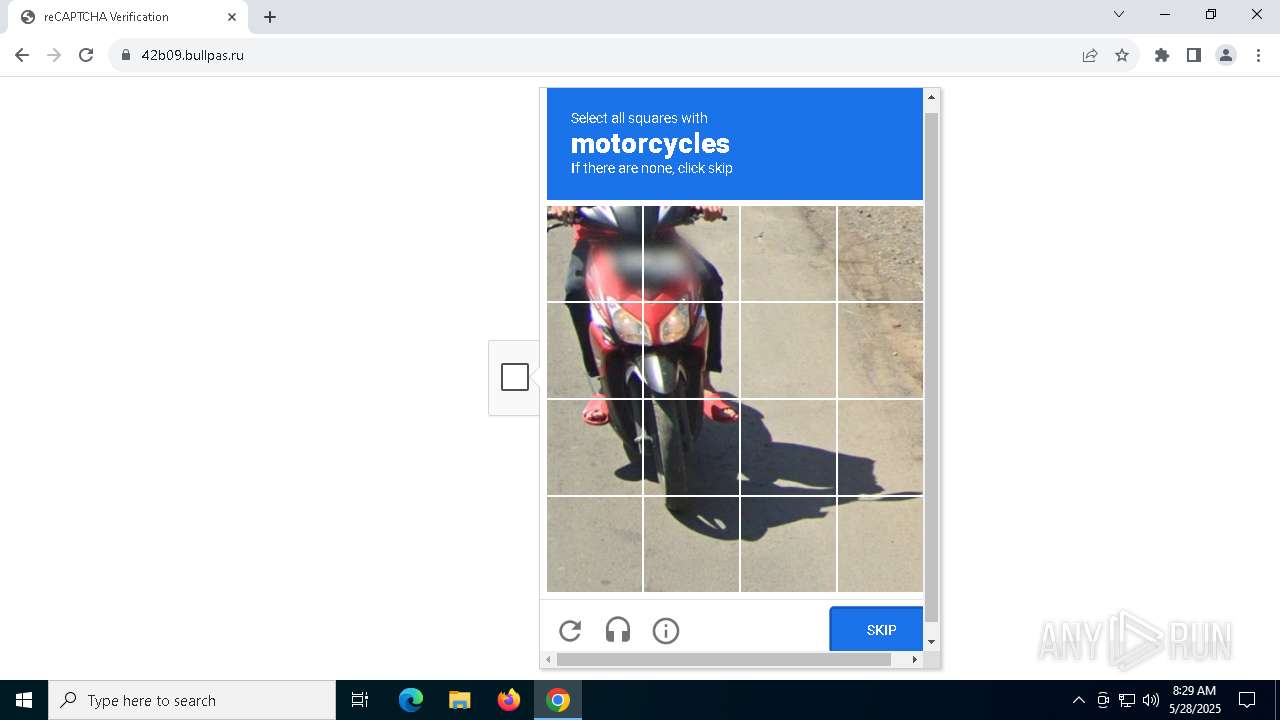
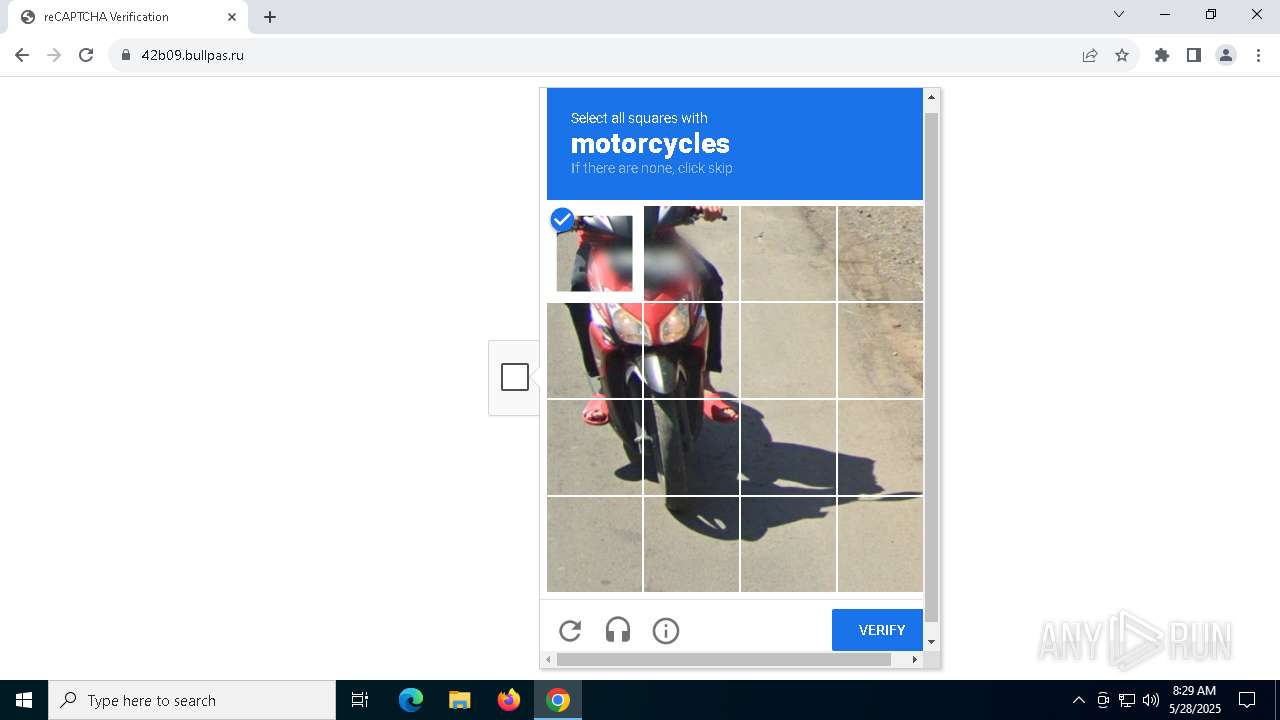
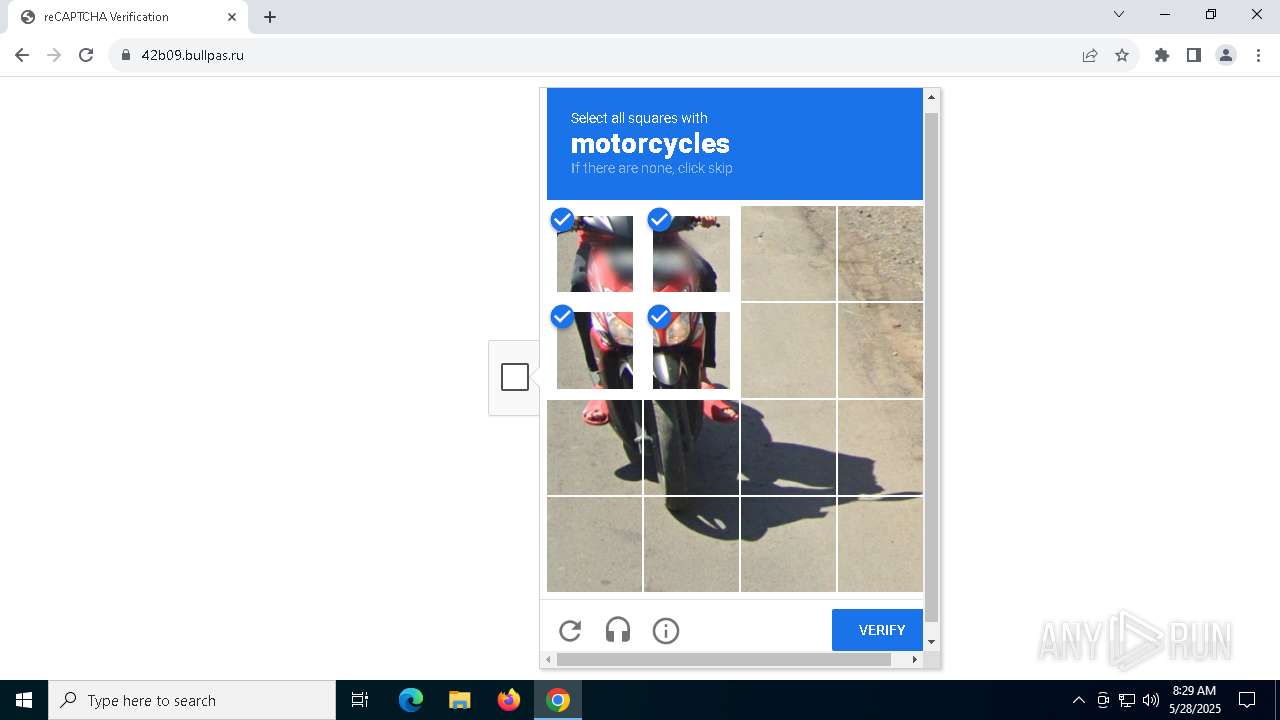
7528 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing |
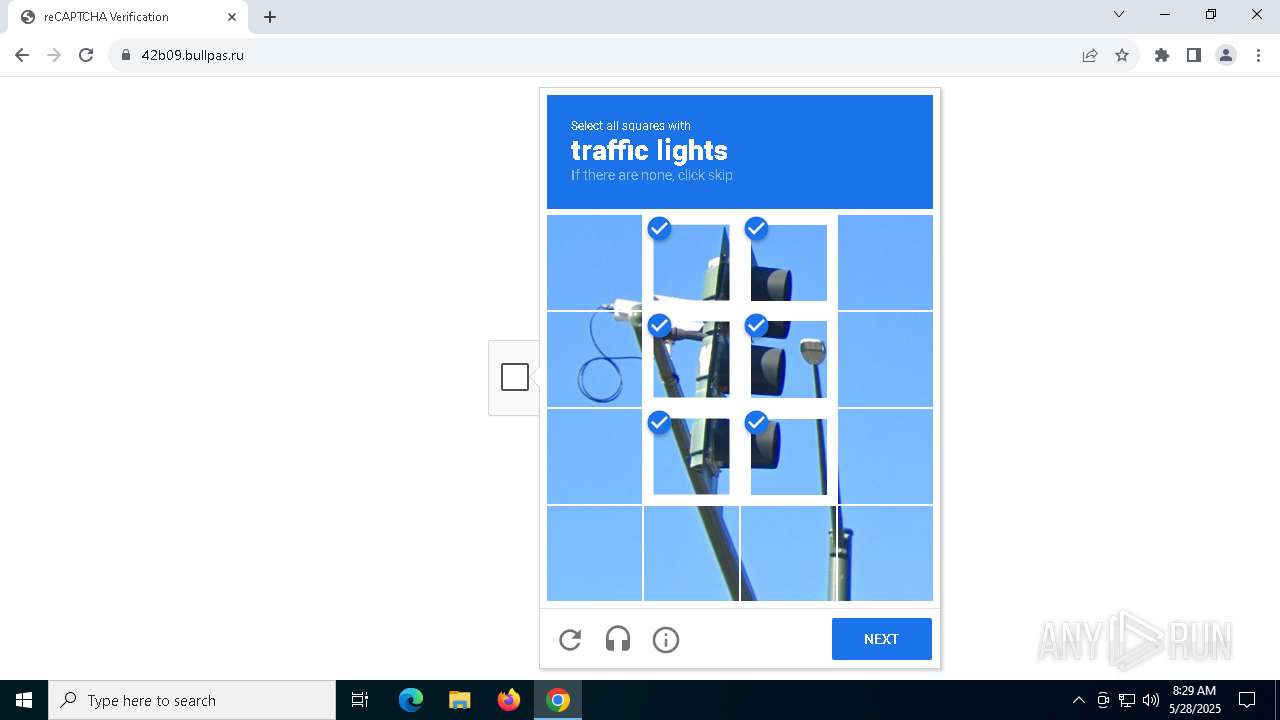
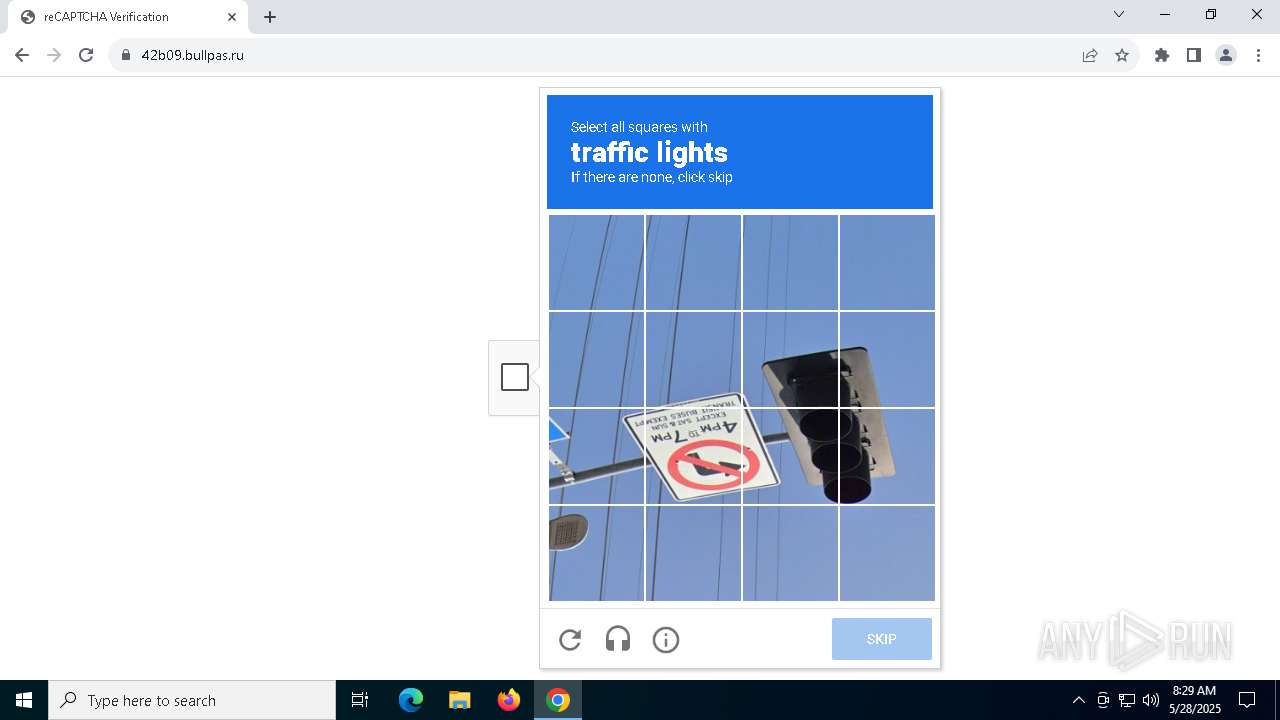
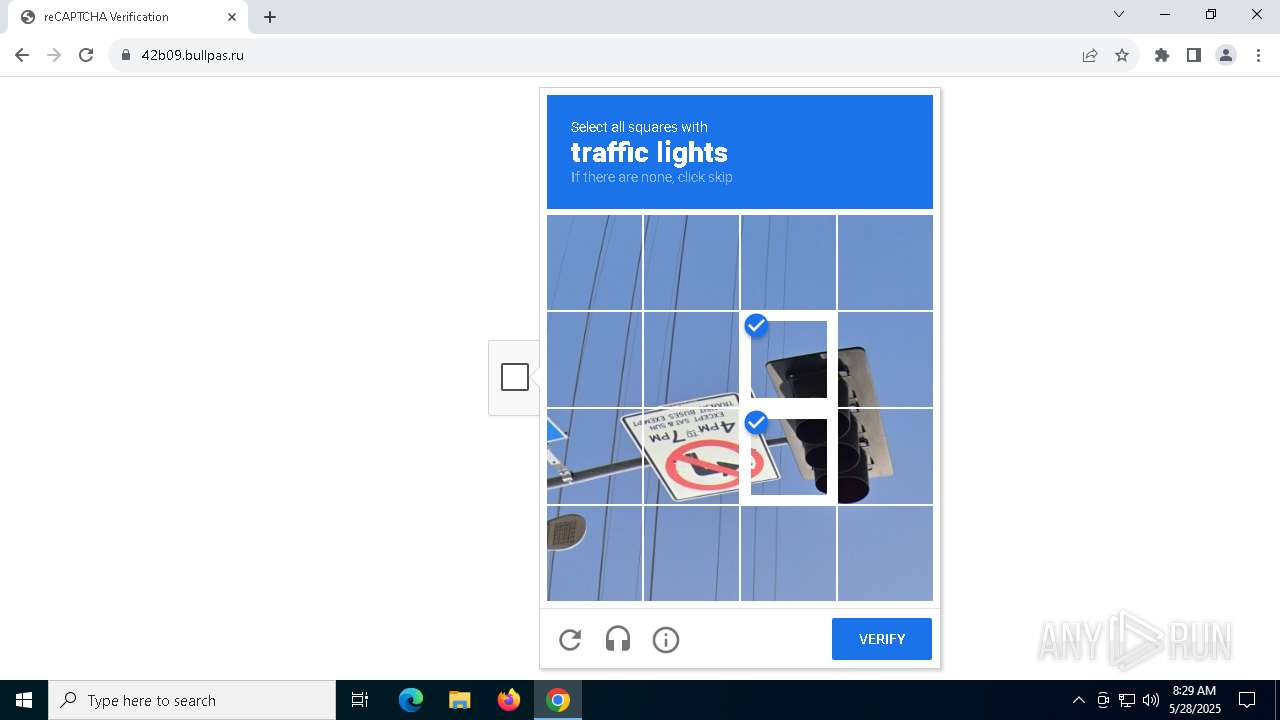
7528 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7528 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |