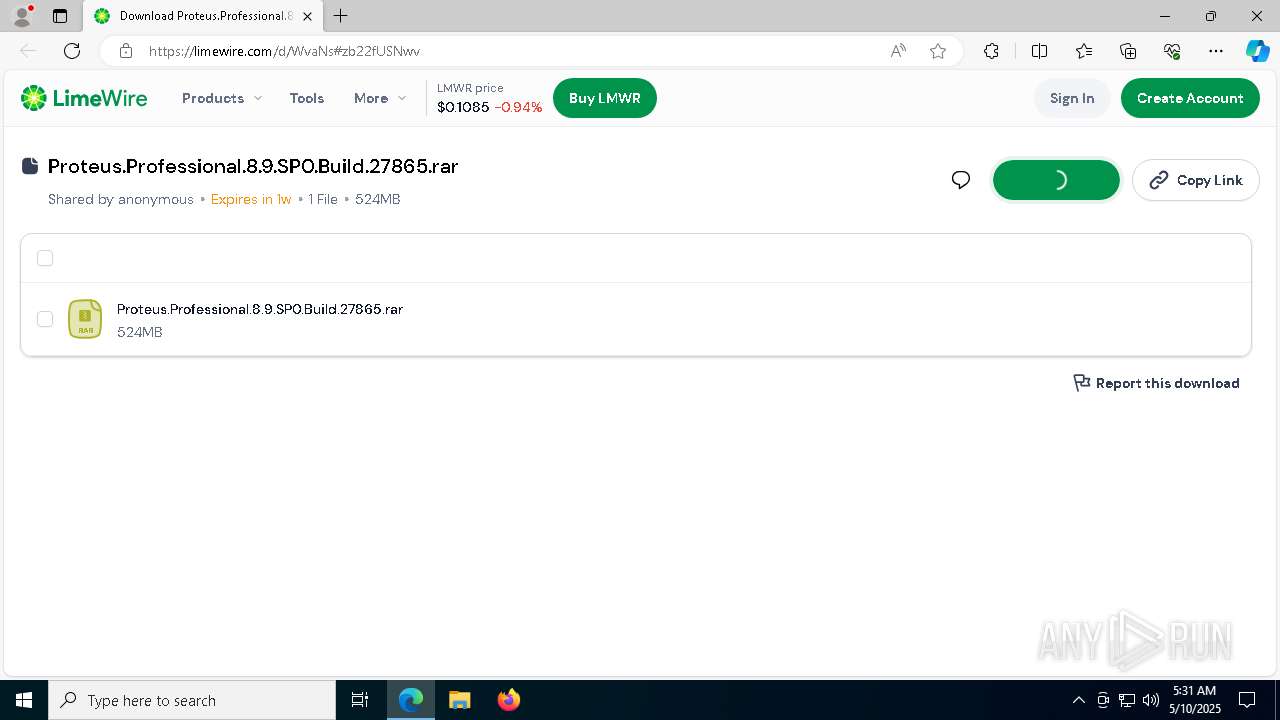
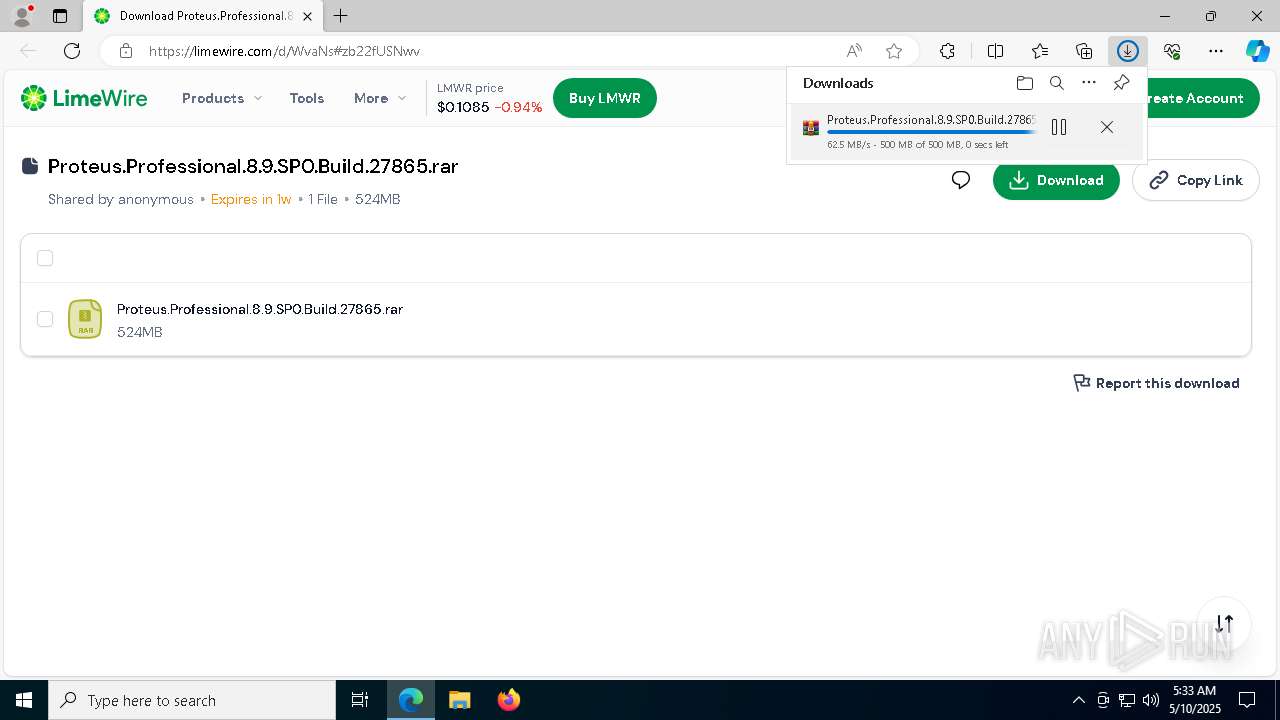
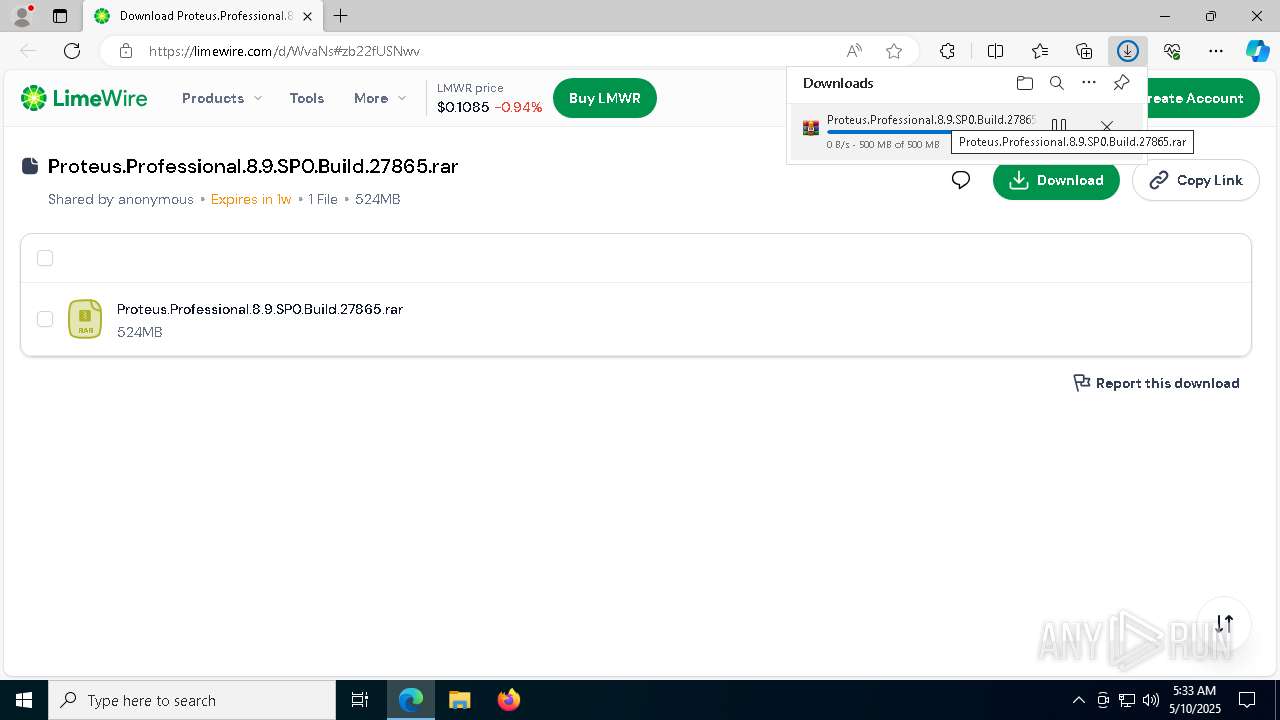
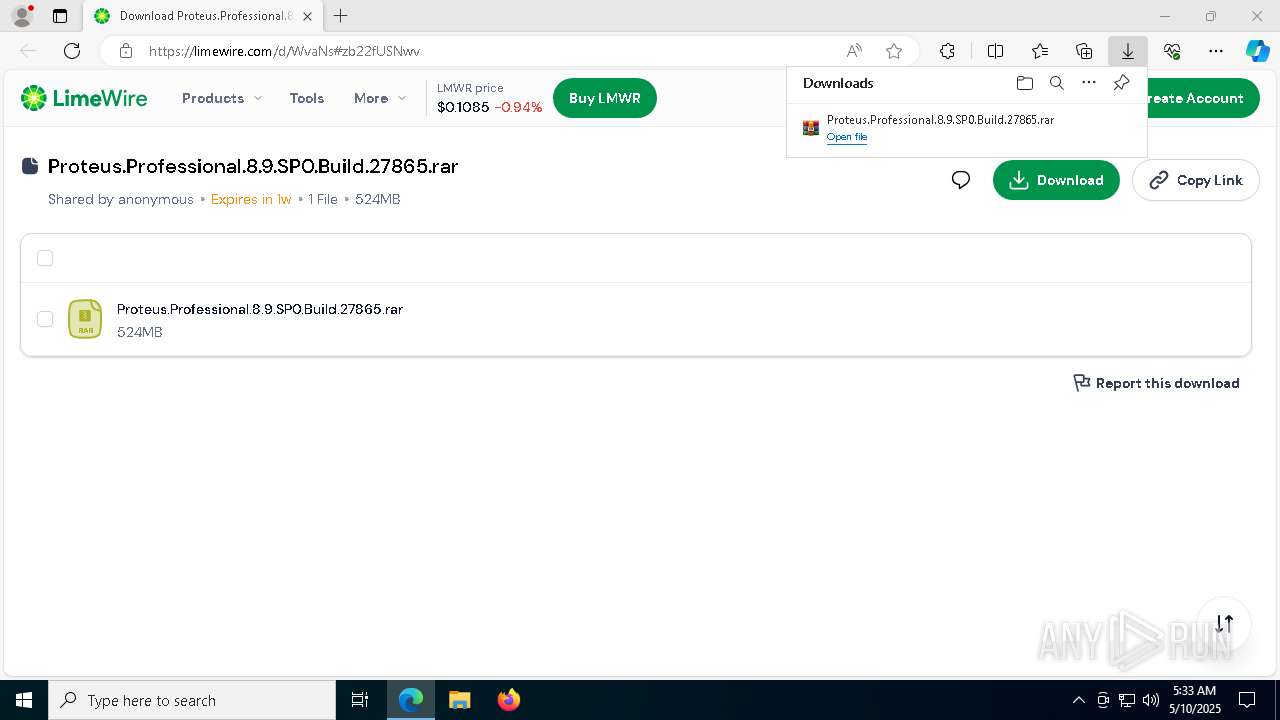
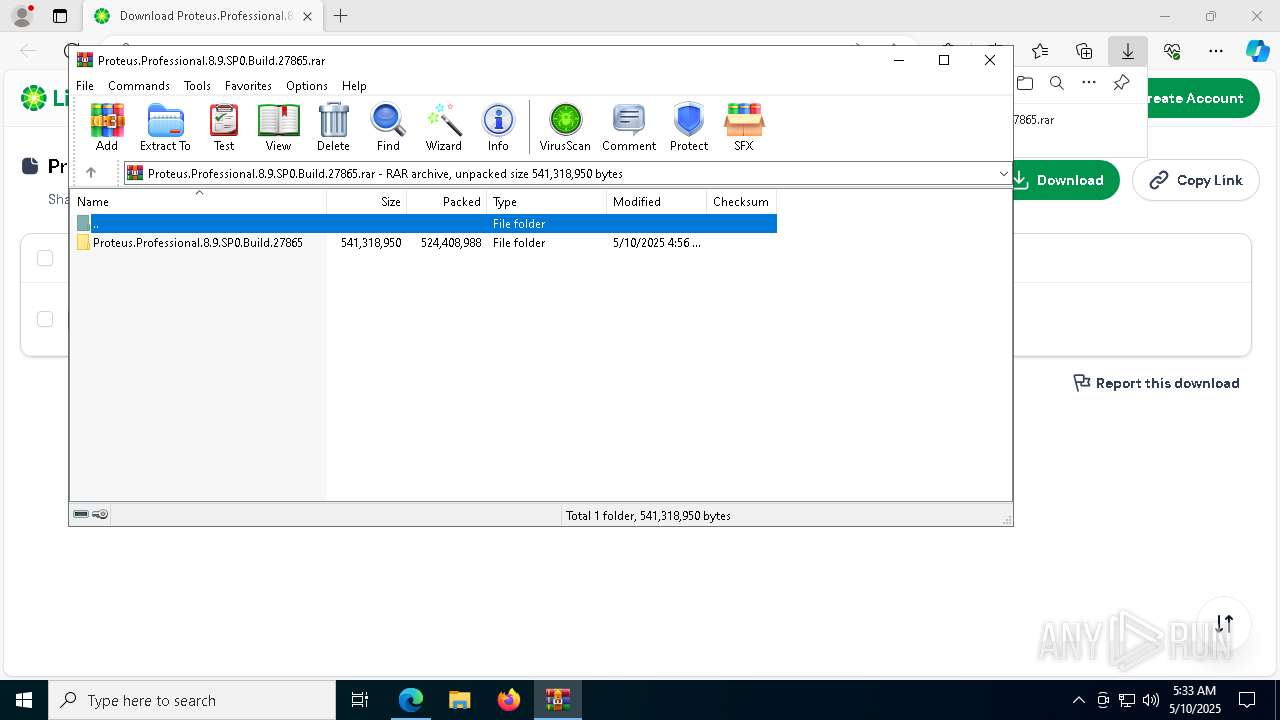
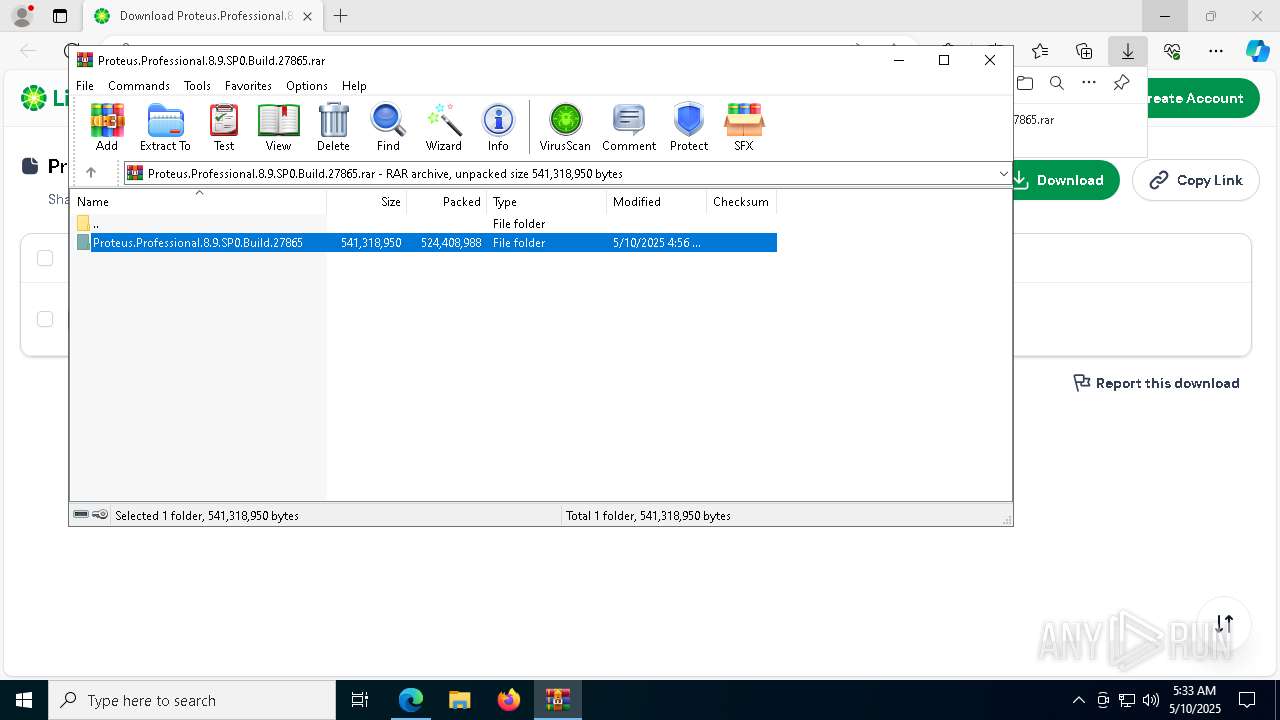
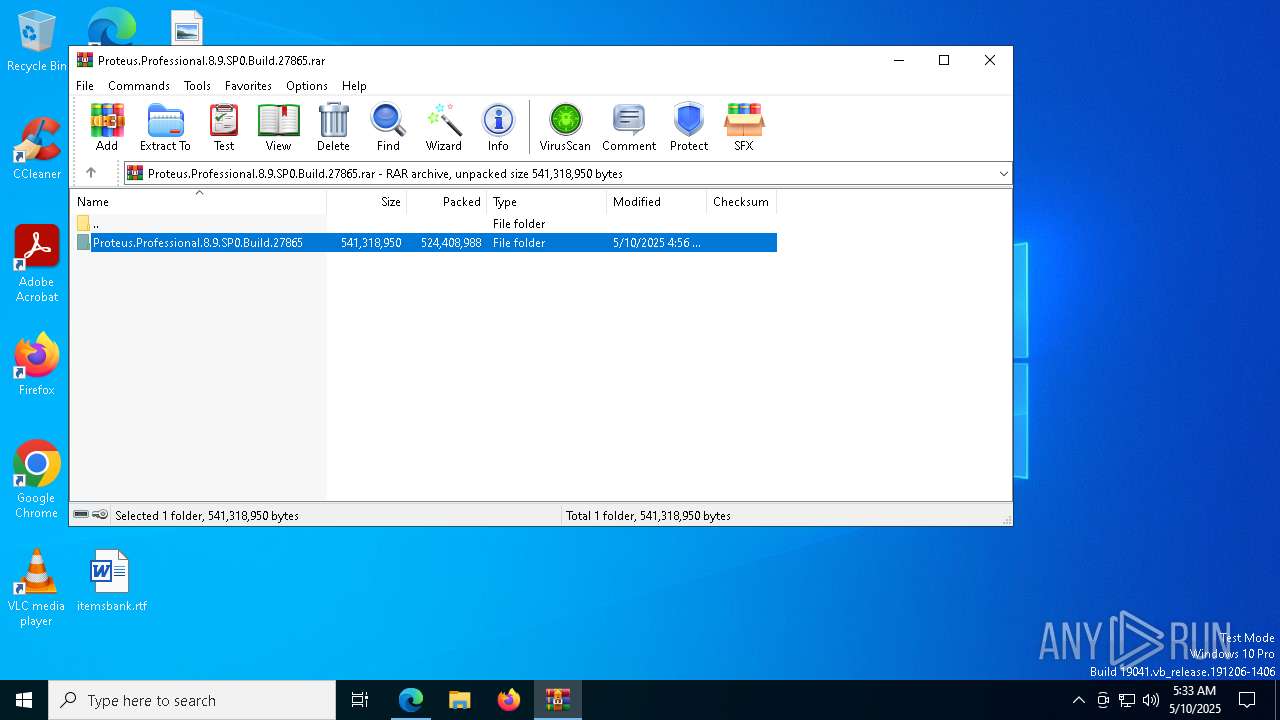
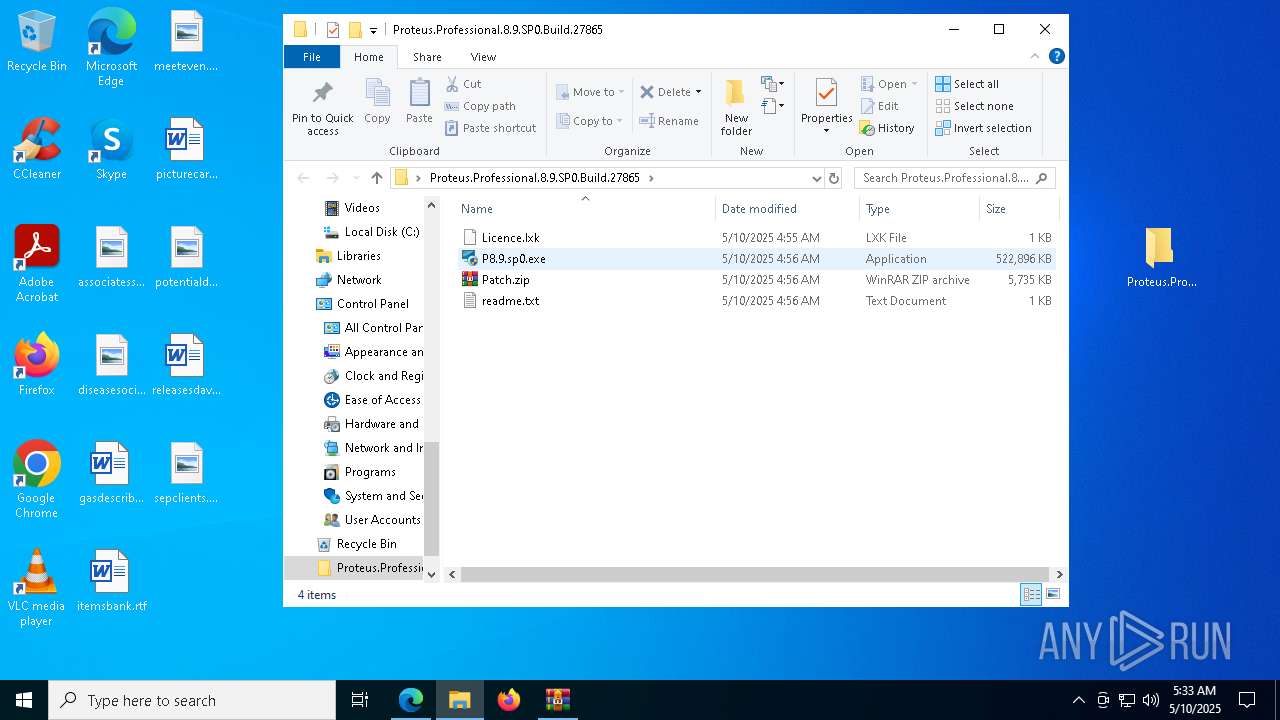
| URL: | https://limewire.com/d/WvaNs#zb22fUSNwv |
| Full analysis: | https://app.any.run/tasks/83583c7b-4ed2-48f8-b2d9-d8002d4d551c |
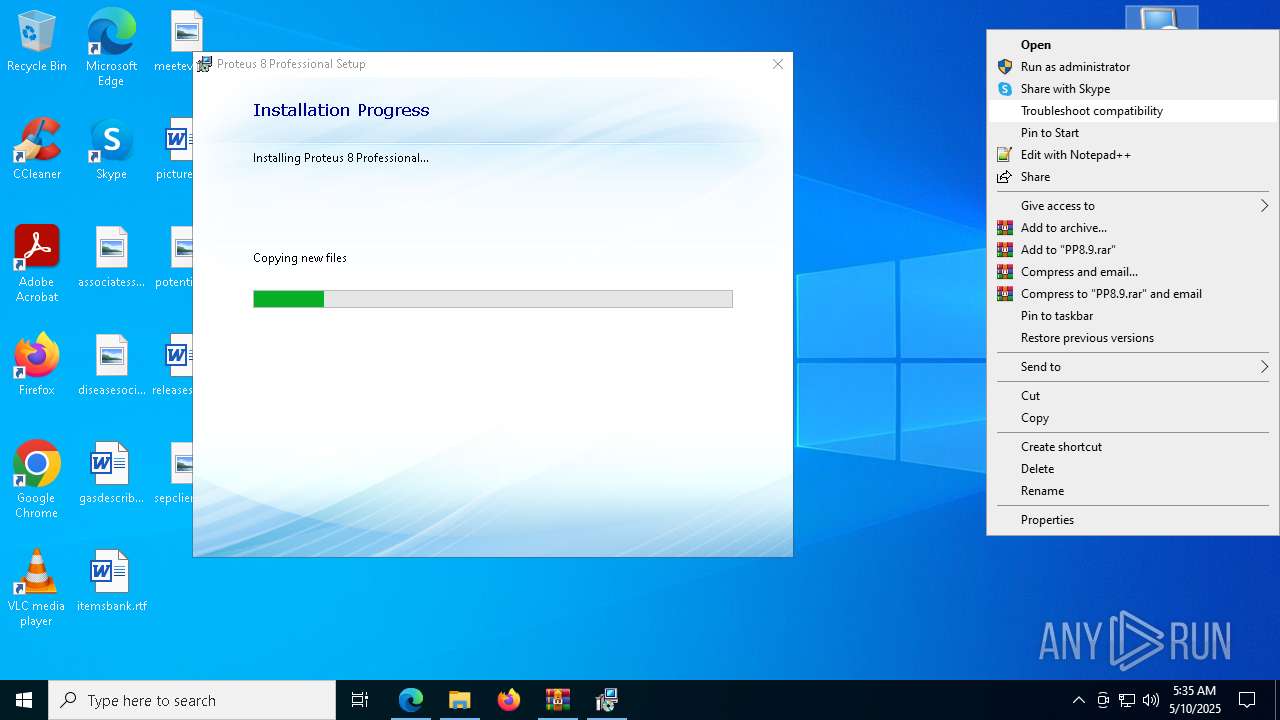
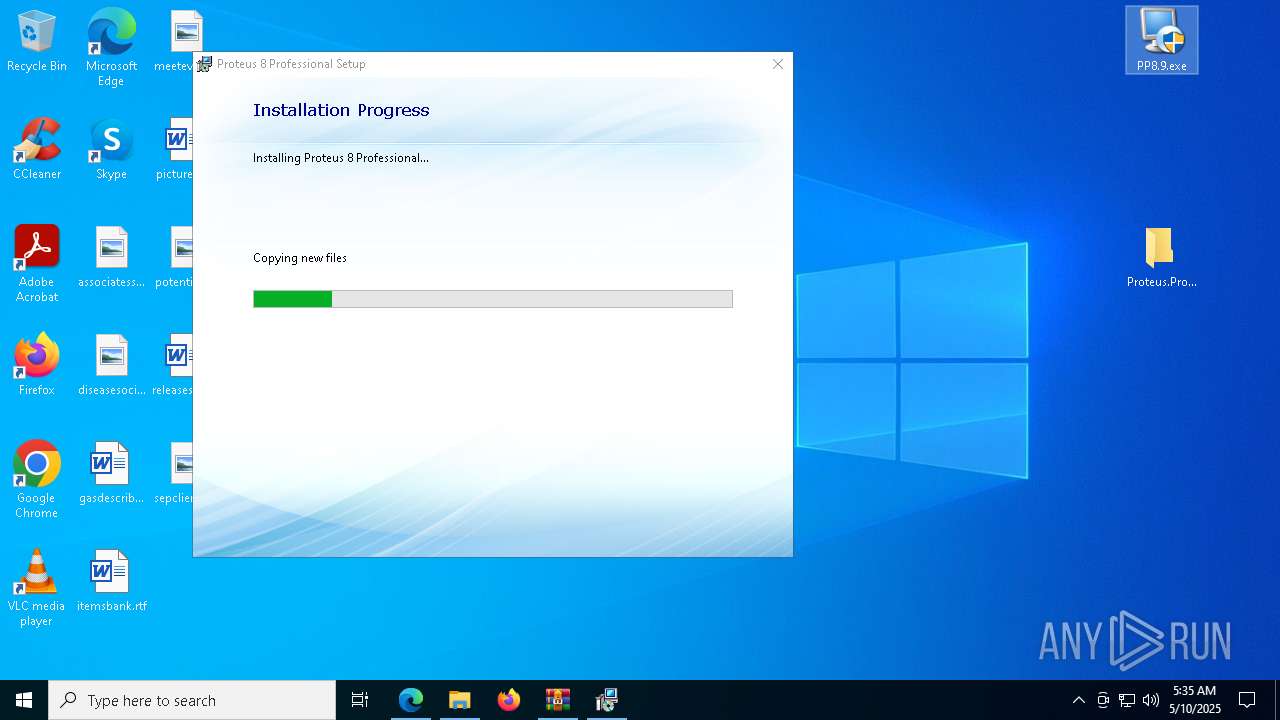
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 05:30:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B39F4CE6F1C63A49BF7A3F053CF5CAE8 |
| SHA1: | C5BEEC4C895000E1EB279ACA5C96650BCEE91095 |
| SHA256: | B17D21B989F49ED9A1C9CBD810FF7C52CCBC9546133CDFDADB79E08AF262C830 |
| SSDEEP: | 3:N8MIA/enKhCInsf:2MIA/eKhlnsf |
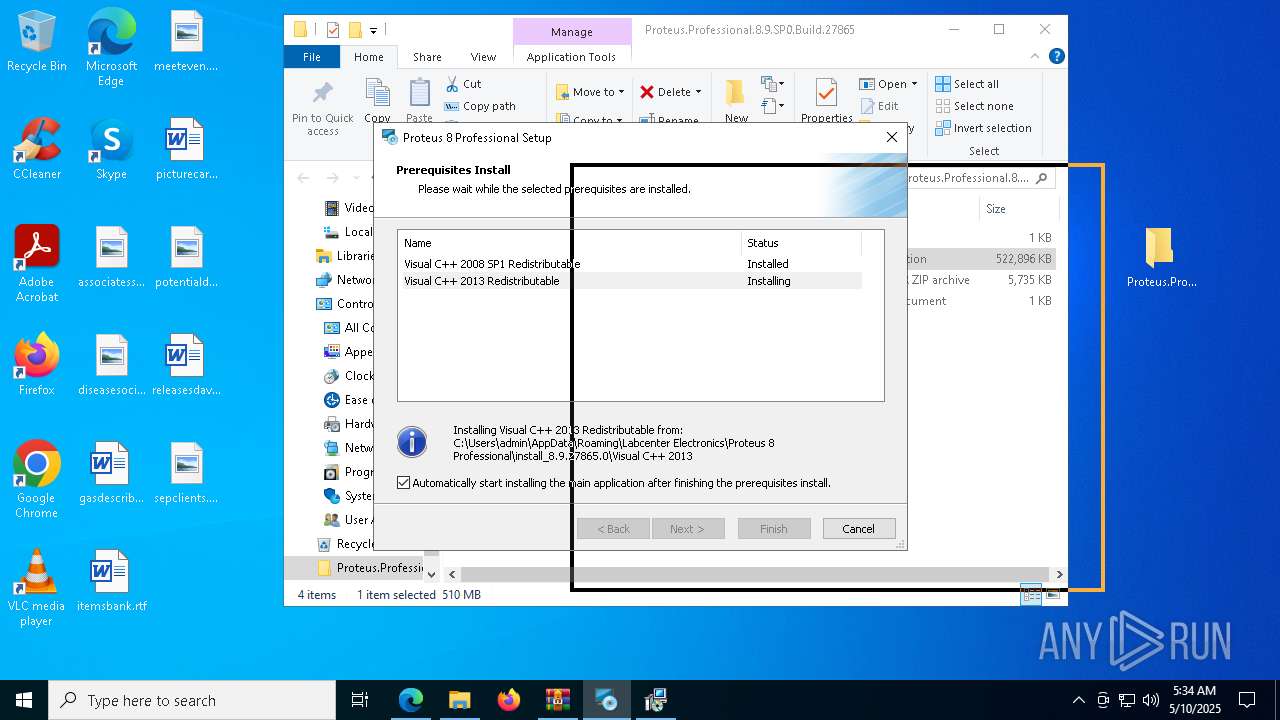
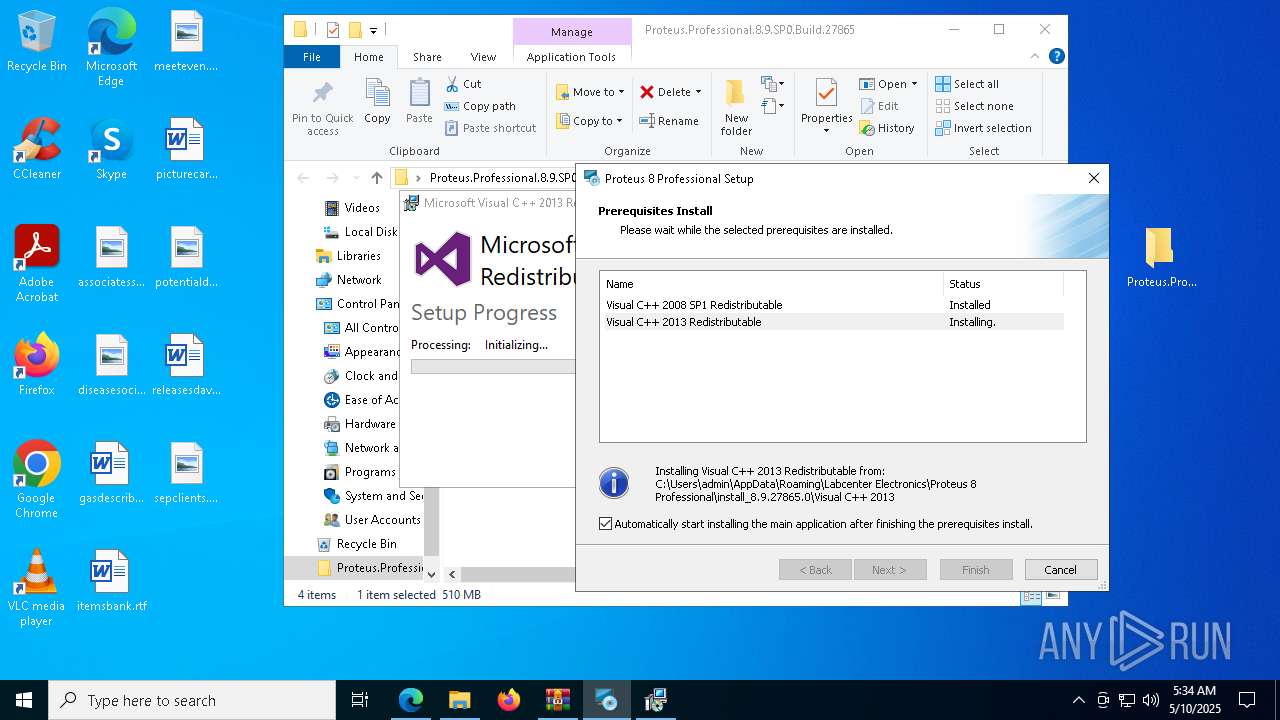
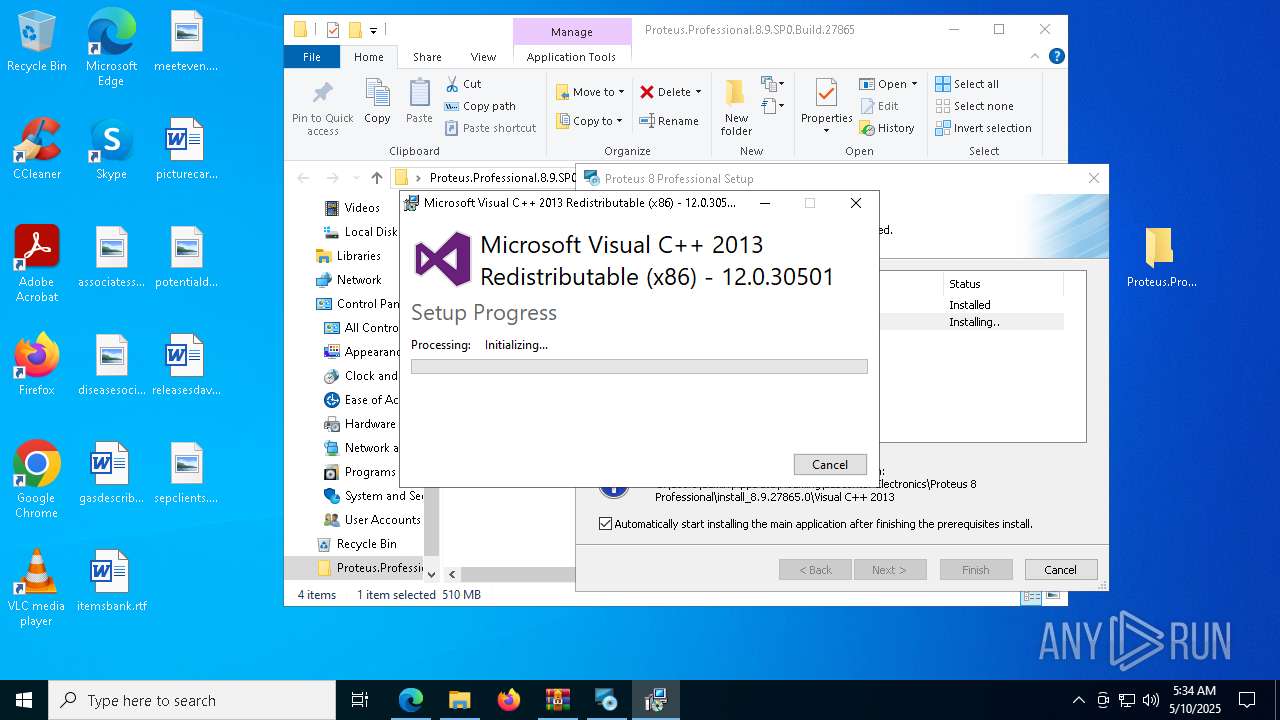
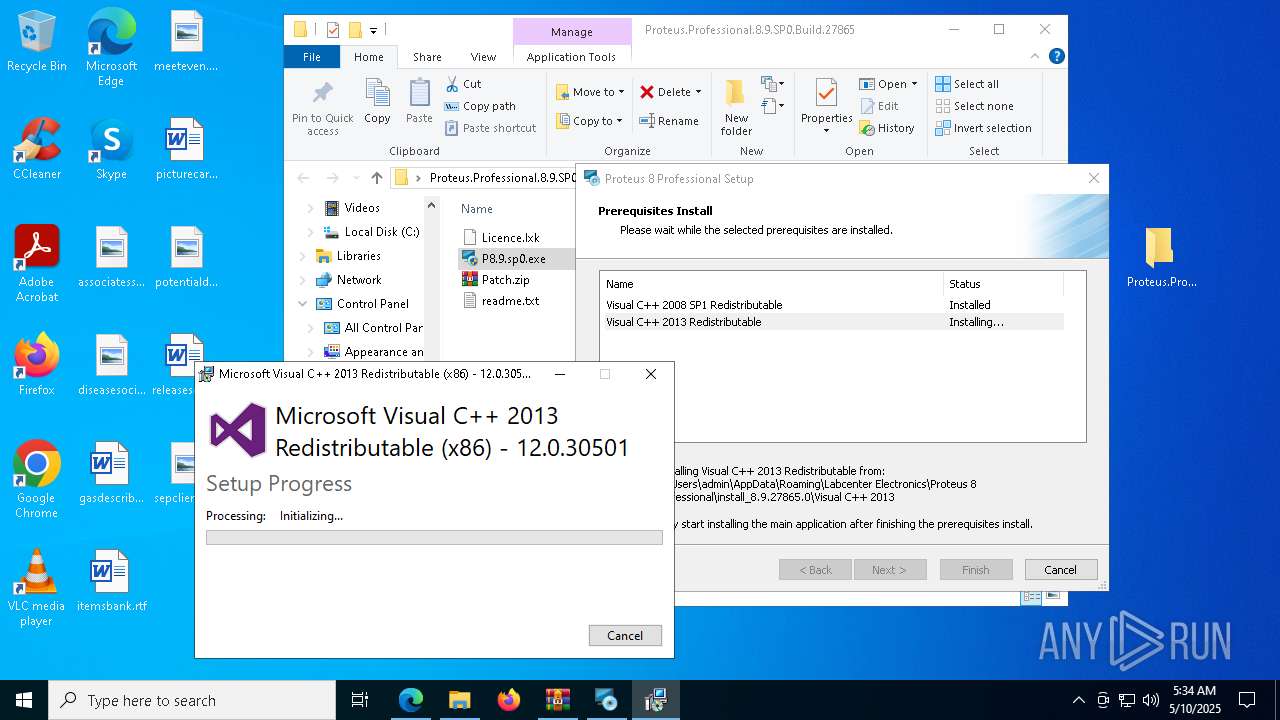
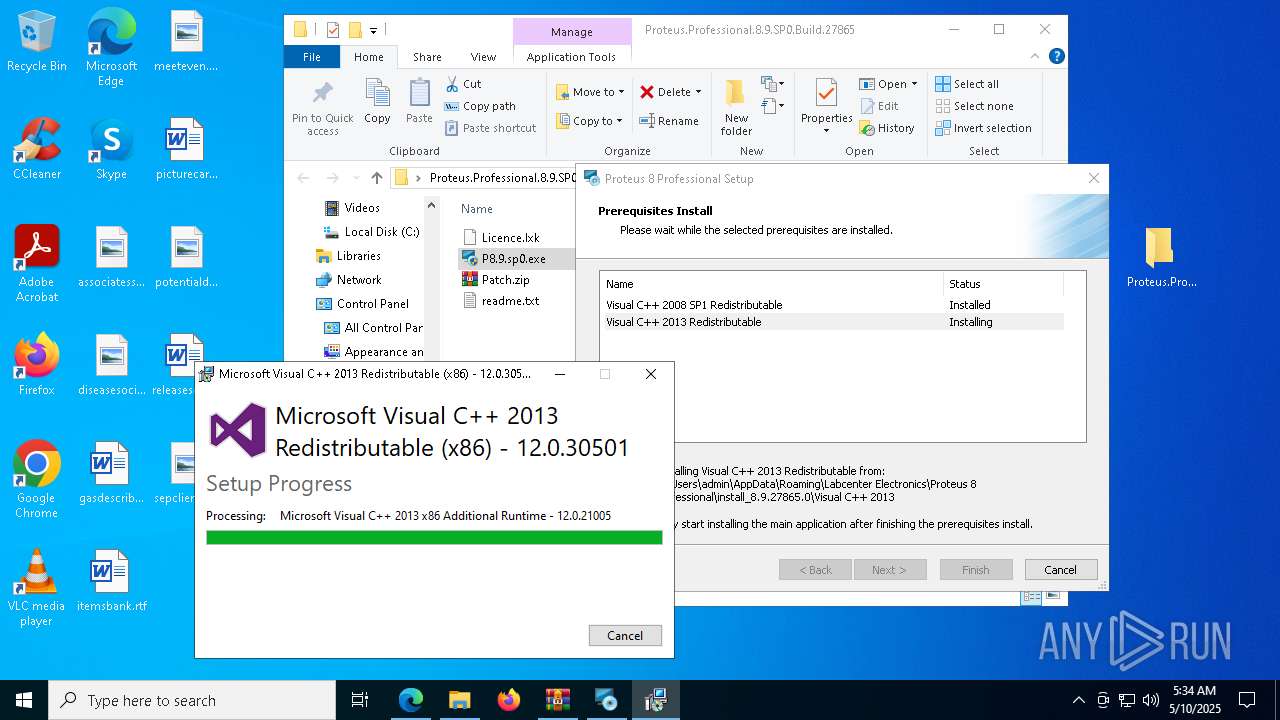
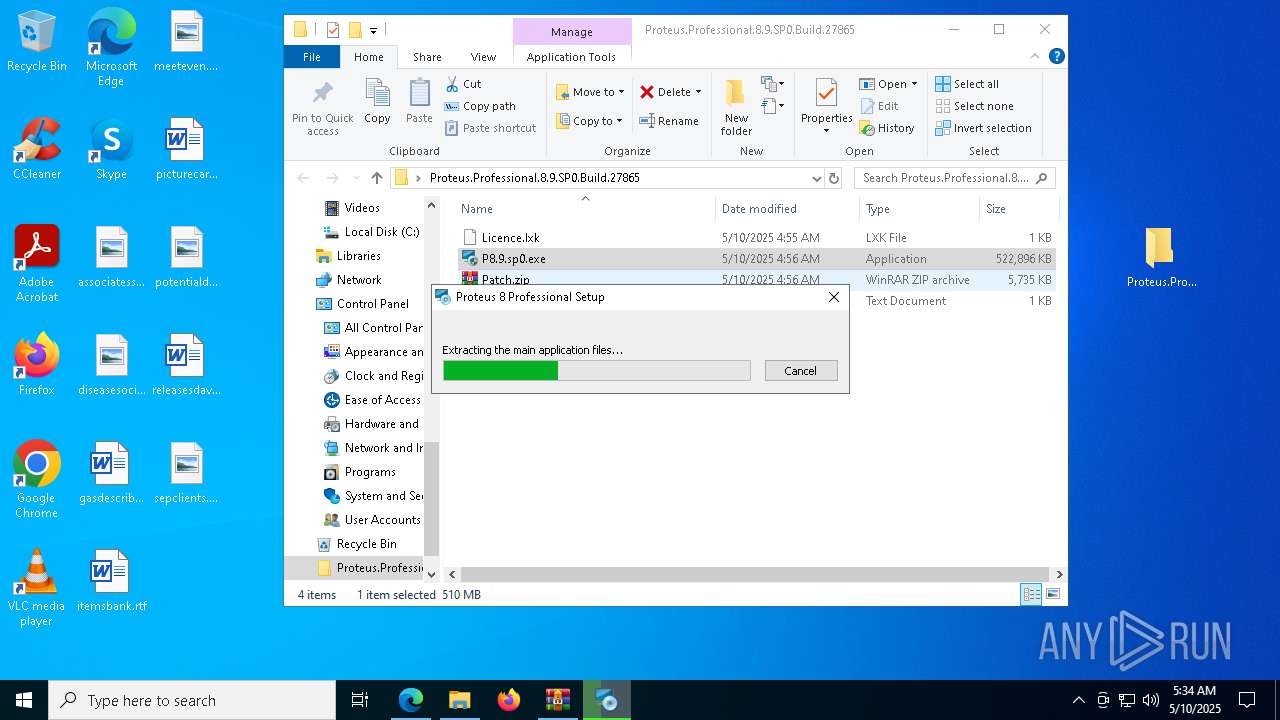
MALICIOUS
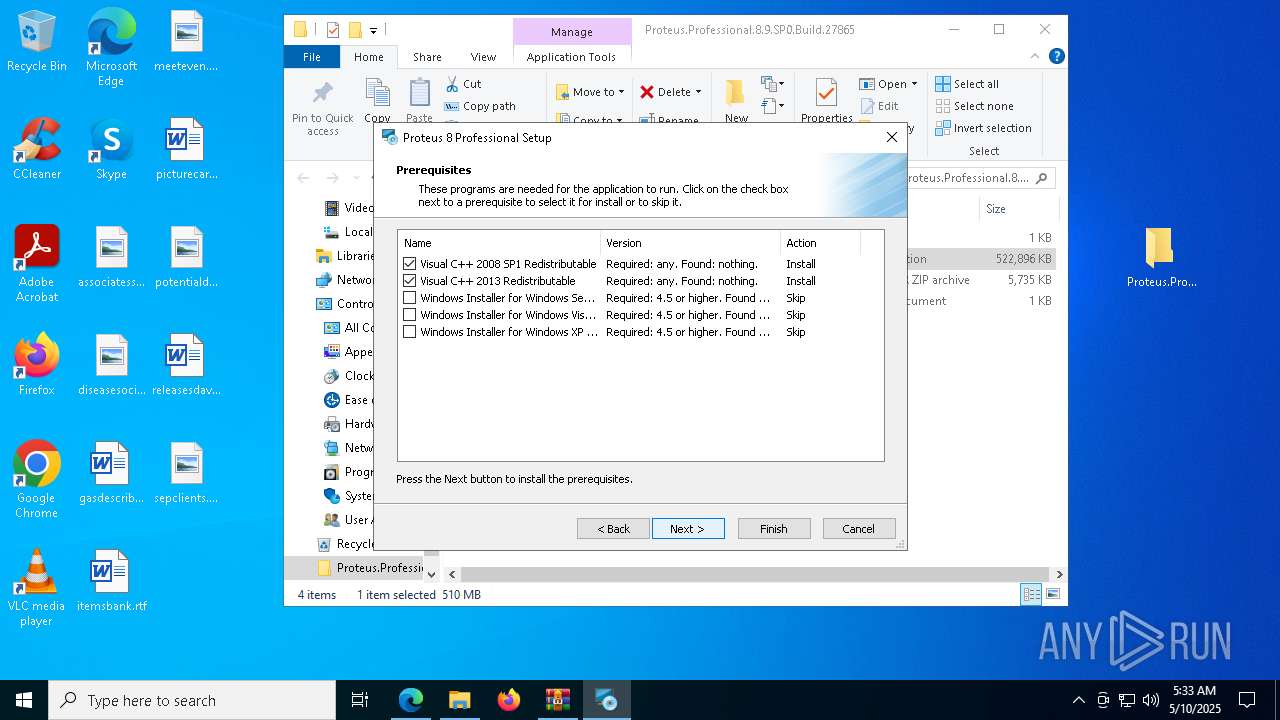
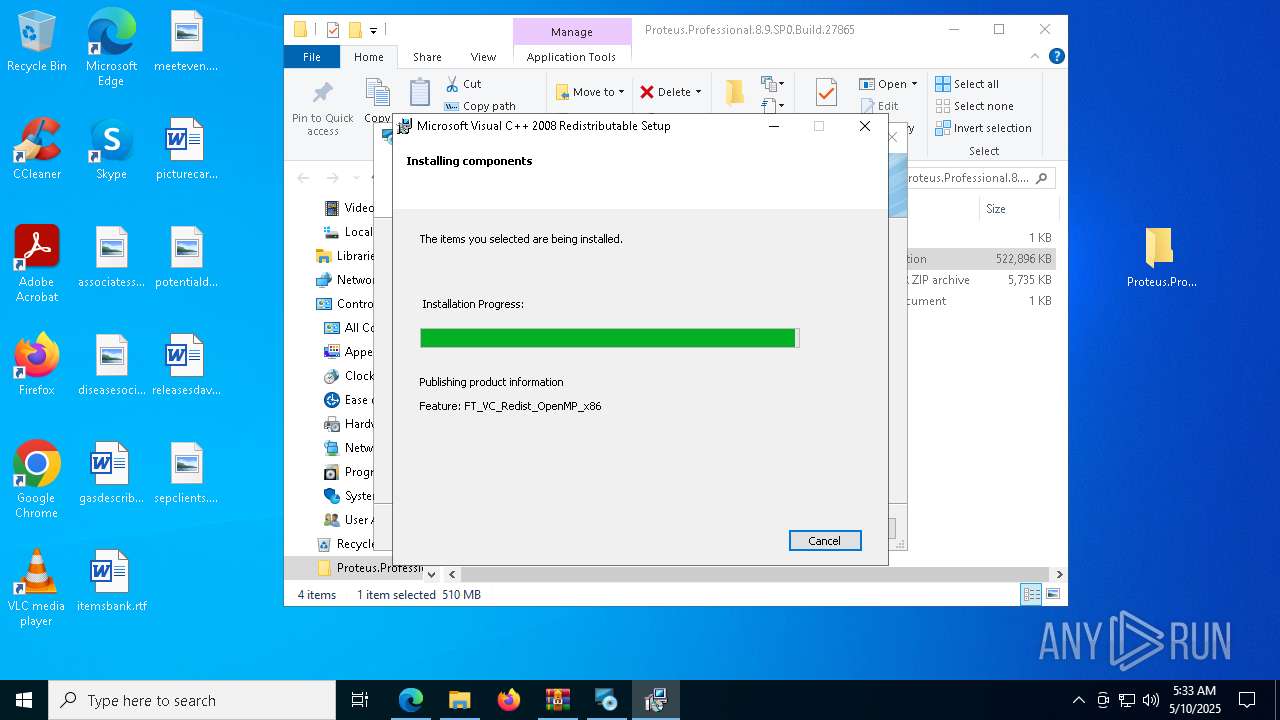
Executing a file with an untrusted certificate
- vcredist_x86.exe (PID: 6980)
- install.exe (PID: 540)
- vcredist_x86_2013.exe (PID: 4868)
- vcredist_x86_2013.exe (PID: 896)
SUSPICIOUS
ADVANCEDINSTALLER mutex has been found
- P8.9.sp0.exe (PID: 4920)
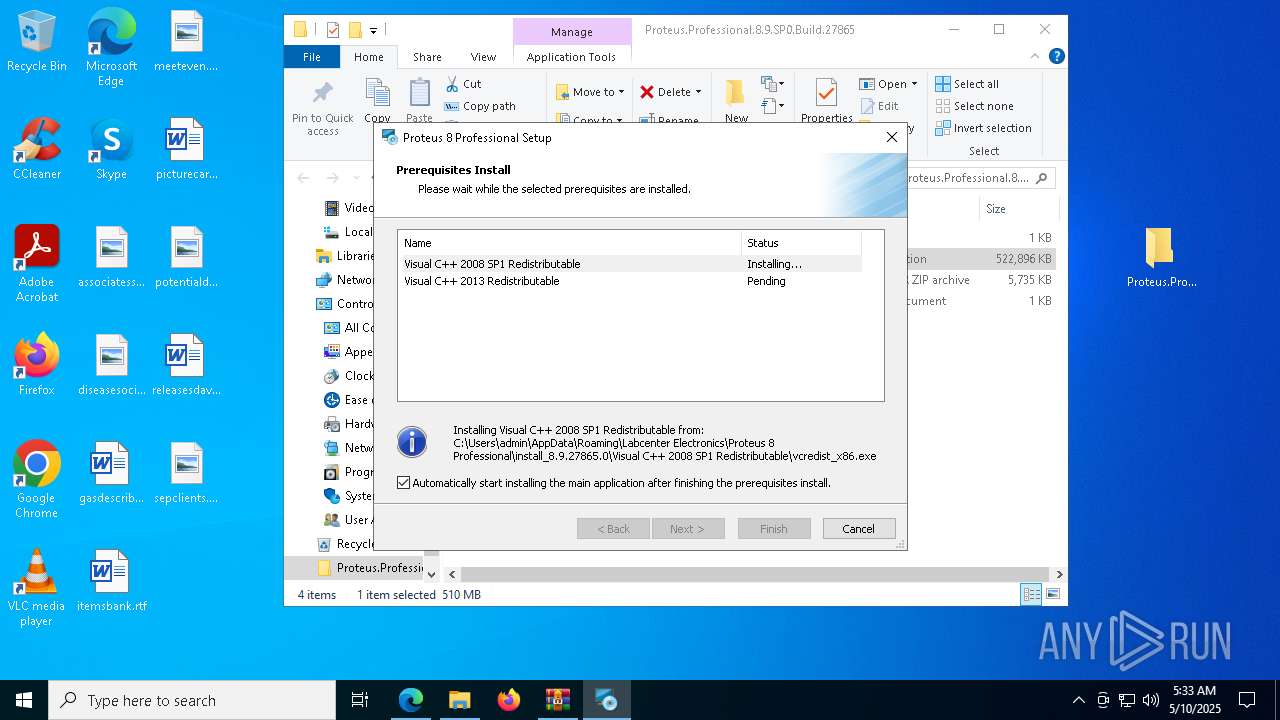
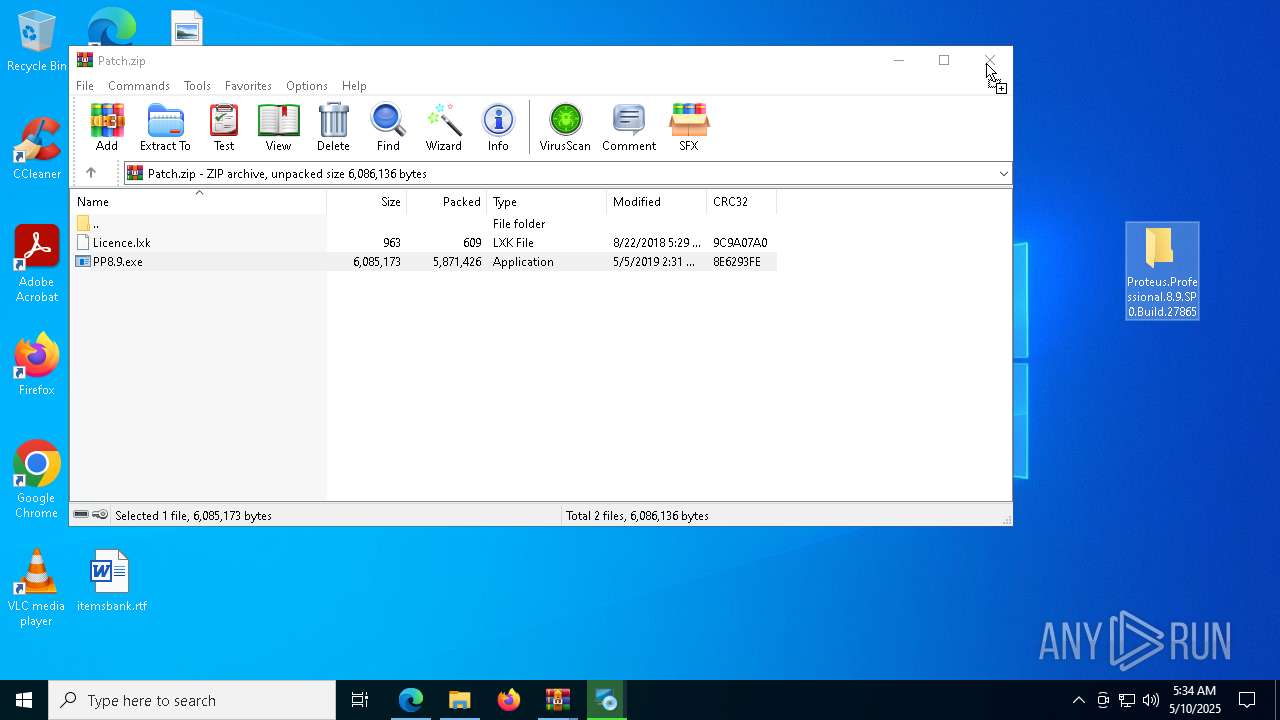
Executable content was dropped or overwritten
- vcredist_x86.exe (PID: 6980)
- P8.9.sp0.exe (PID: 4920)
- TiWorker.exe (PID: 7624)
- vcredist_x86_2013.exe (PID: 4868)
- vcredist_x86_2013.exe (PID: 896)
- irsetup.exe (PID: 5504)
- PP8.9.exe (PID: 7440)
- PP8.9.exe (PID: 5480)
- irsetup.exe (PID: 5944)
- PP8.9.exe (PID: 2148)
- irsetup.exe (PID: 5624)
- PP8.9.exe (PID: 7020)
- irsetup.exe (PID: 7440)
- PP8.9.exe (PID: 8152)
- irsetup.exe (PID: 7996)
- irsetup.exe (PID: 7872)
- PP8.9.exe (PID: 5944)
- PP8.9.exe (PID: 6048)
- irsetup.exe (PID: 3888)
- irsetup.exe (PID: 5936)
- PP8.9.exe (PID: 8144)
Process drops legitimate windows executable
- vcredist_x86.exe (PID: 6980)
- P8.9.sp0.exe (PID: 4920)
- msiexec.exe (PID: 6584)
- TiWorker.exe (PID: 7624)
- vcredist_x86_2013.exe (PID: 4868)
- vcredist_x86_2013.exe (PID: 896)
Reads security settings of Internet Explorer
- P8.9.sp0.exe (PID: 4920)
- install.exe (PID: 540)
Creates file in the systems drive root
- vcredist_x86.exe (PID: 6980)
Detects AdvancedInstaller (YARA)
- P8.9.sp0.exe (PID: 4920)
There is functionality for taking screenshot (YARA)
- P8.9.sp0.exe (PID: 4920)
Reads the Windows owner or organization settings
- install.exe (PID: 540)
The process drops C-runtime libraries
- msiexec.exe (PID: 6584)
- TiWorker.exe (PID: 7624)
Application launched itself
- vcredist_x86_2013.exe (PID: 896)
Executes as Windows Service
- VSSVC.exe (PID: 7980)
INFO
Application launched itself
- msedge.exe (PID: 5776)
Checks supported languages
- identity_helper.exe (PID: 1228)
- P8.9.sp0.exe (PID: 4920)
- vcredist_x86.exe (PID: 6980)
- install.exe (PID: 540)
- msiexec.exe (PID: 6584)
Reads Environment values
- identity_helper.exe (PID: 1228)
Reads the computer name
- identity_helper.exe (PID: 1228)
- P8.9.sp0.exe (PID: 4920)
- vcredist_x86.exe (PID: 6980)
- install.exe (PID: 540)
- msiexec.exe (PID: 6584)
Reads the software policy settings
- slui.exe (PID: 720)
- slui.exe (PID: 6752)
- install.exe (PID: 540)
- msiexec.exe (PID: 6584)
Checks proxy server information
- slui.exe (PID: 6752)
- install.exe (PID: 540)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5776)
The sample compiled with english language support
- WinRAR.exe (PID: 4284)
- vcredist_x86.exe (PID: 6980)
- P8.9.sp0.exe (PID: 4920)
- msiexec.exe (PID: 6584)
- TiWorker.exe (PID: 7624)
- vcredist_x86_2013.exe (PID: 4868)
- vcredist_x86_2013.exe (PID: 896)
- msedge.exe (PID: 2084)
- msiexec.exe (PID: 1004)
- PP8.9.exe (PID: 7440)
- WinRAR.exe (PID: 5164)
- irsetup.exe (PID: 5504)
- PP8.9.exe (PID: 5480)
- irsetup.exe (PID: 5944)
- PP8.9.exe (PID: 2148)
- irsetup.exe (PID: 5624)
- irsetup.exe (PID: 7440)
- PP8.9.exe (PID: 7020)
- PP8.9.exe (PID: 8152)
- irsetup.exe (PID: 7872)
- PP8.9.exe (PID: 5944)
- irsetup.exe (PID: 7996)
- PP8.9.exe (PID: 6048)
- irsetup.exe (PID: 3888)
- irsetup.exe (PID: 5936)
- PP8.9.exe (PID: 8144)
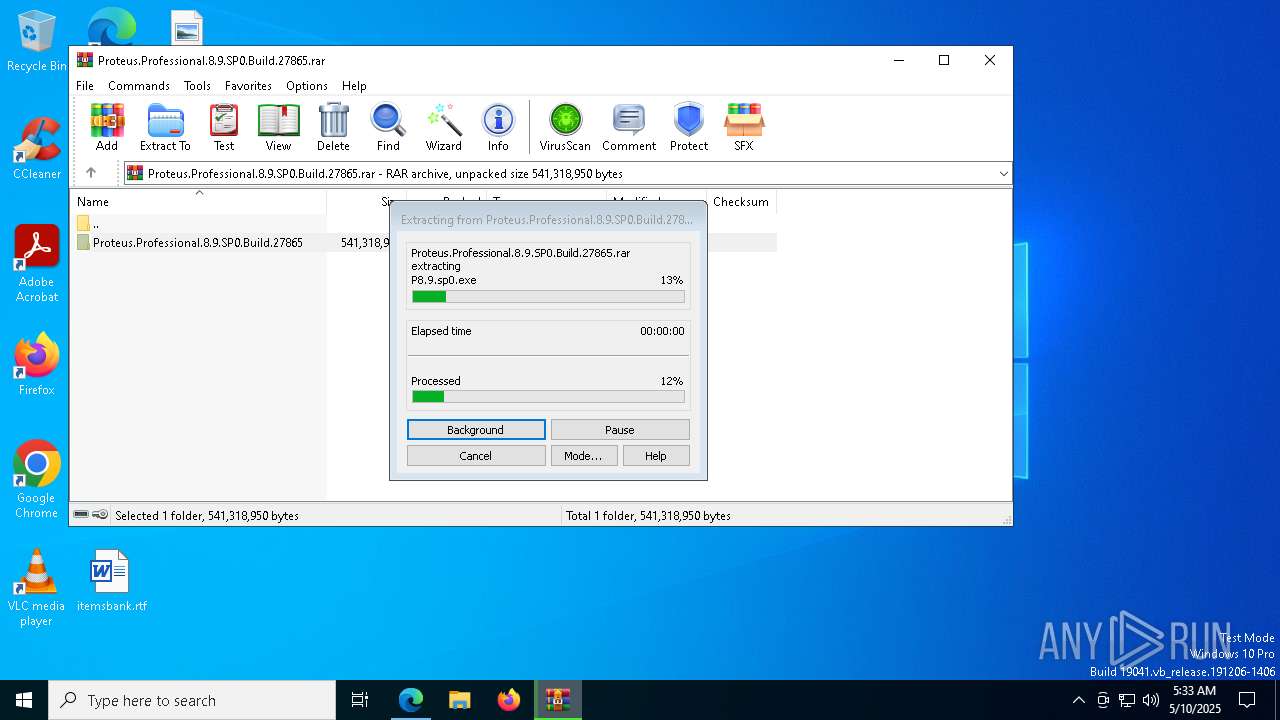
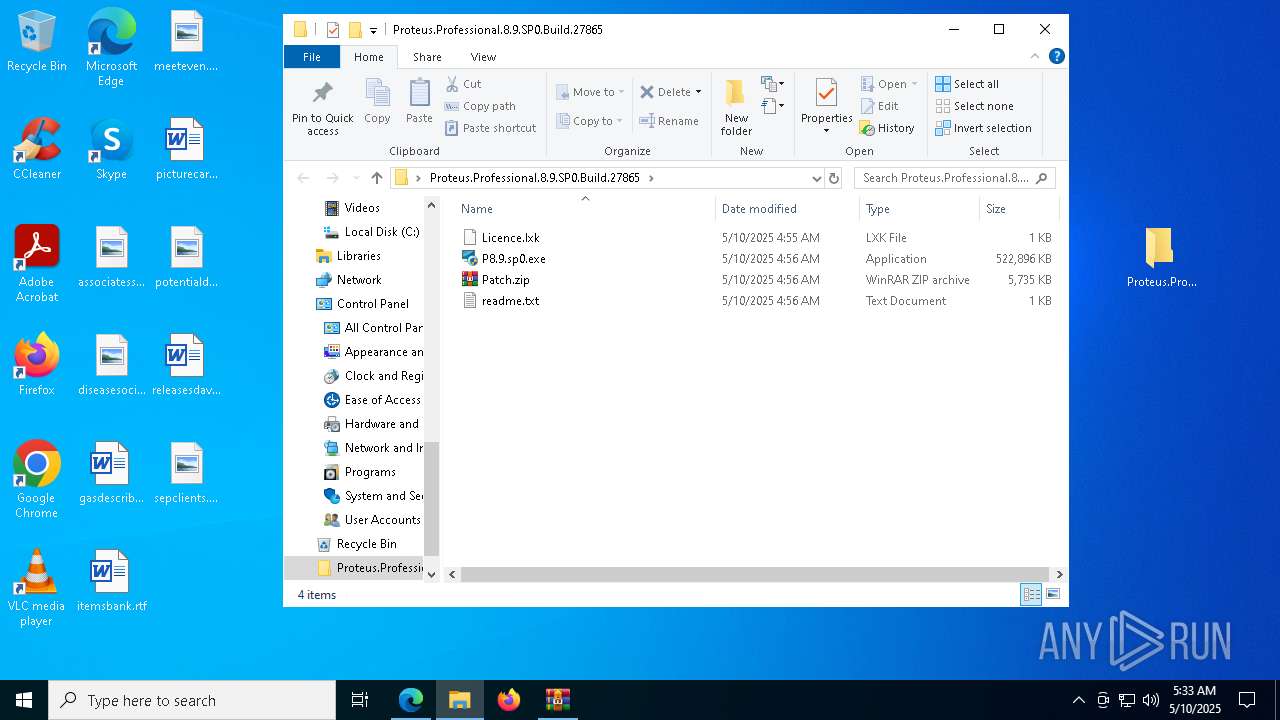
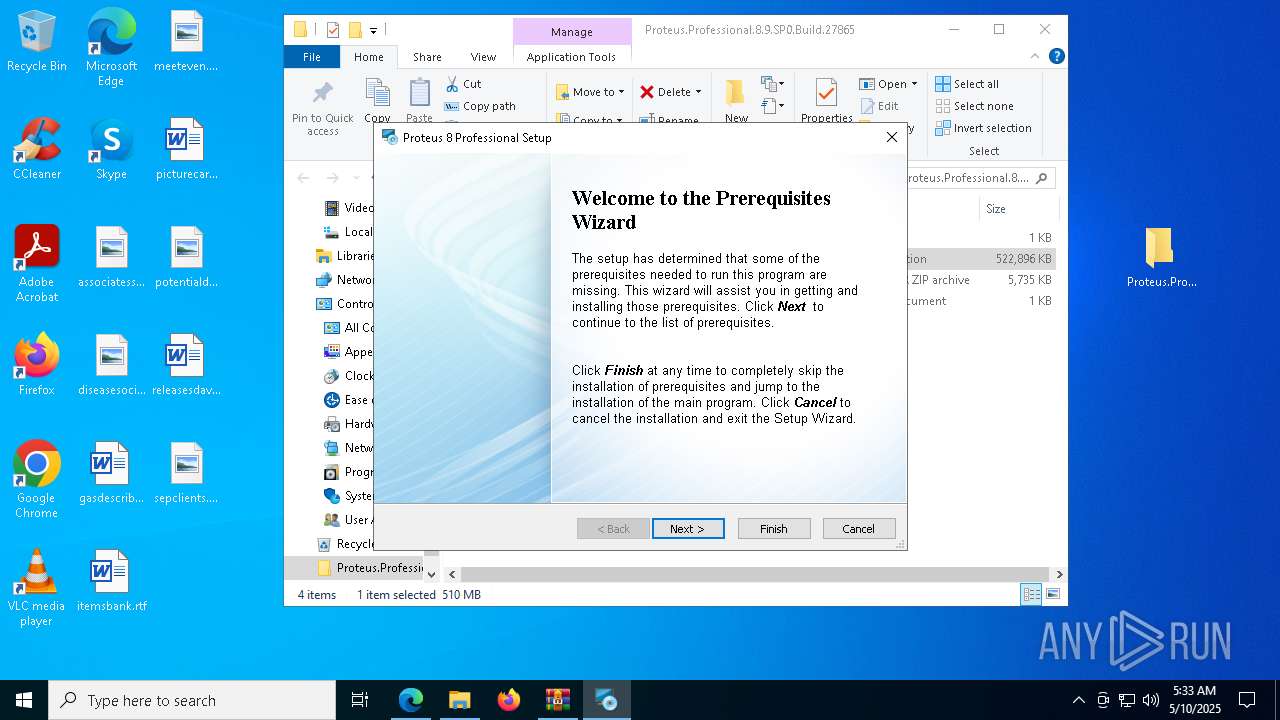
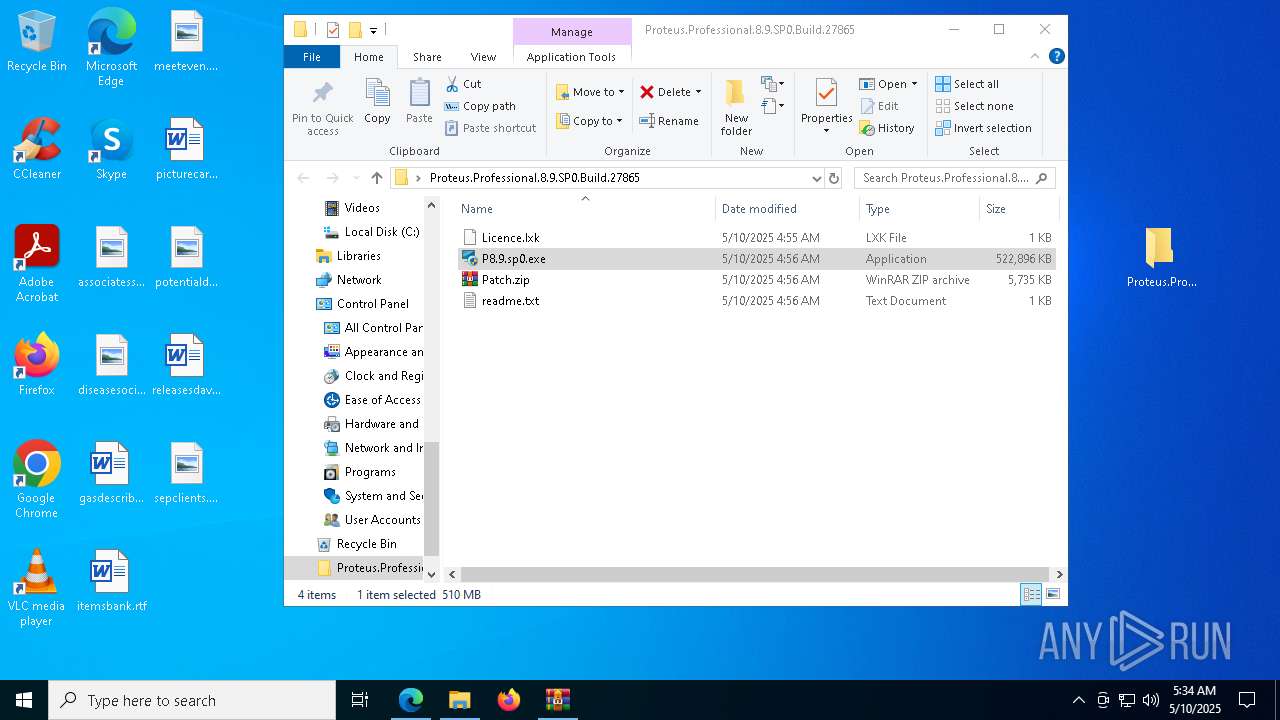
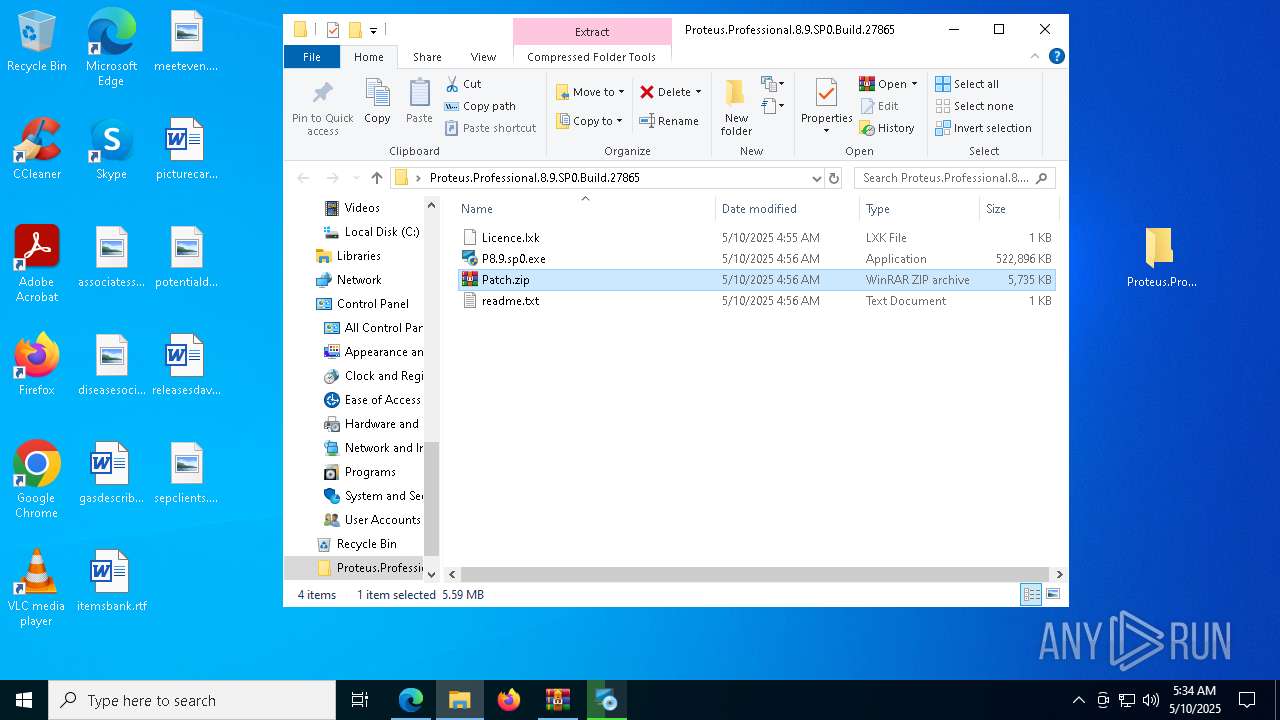
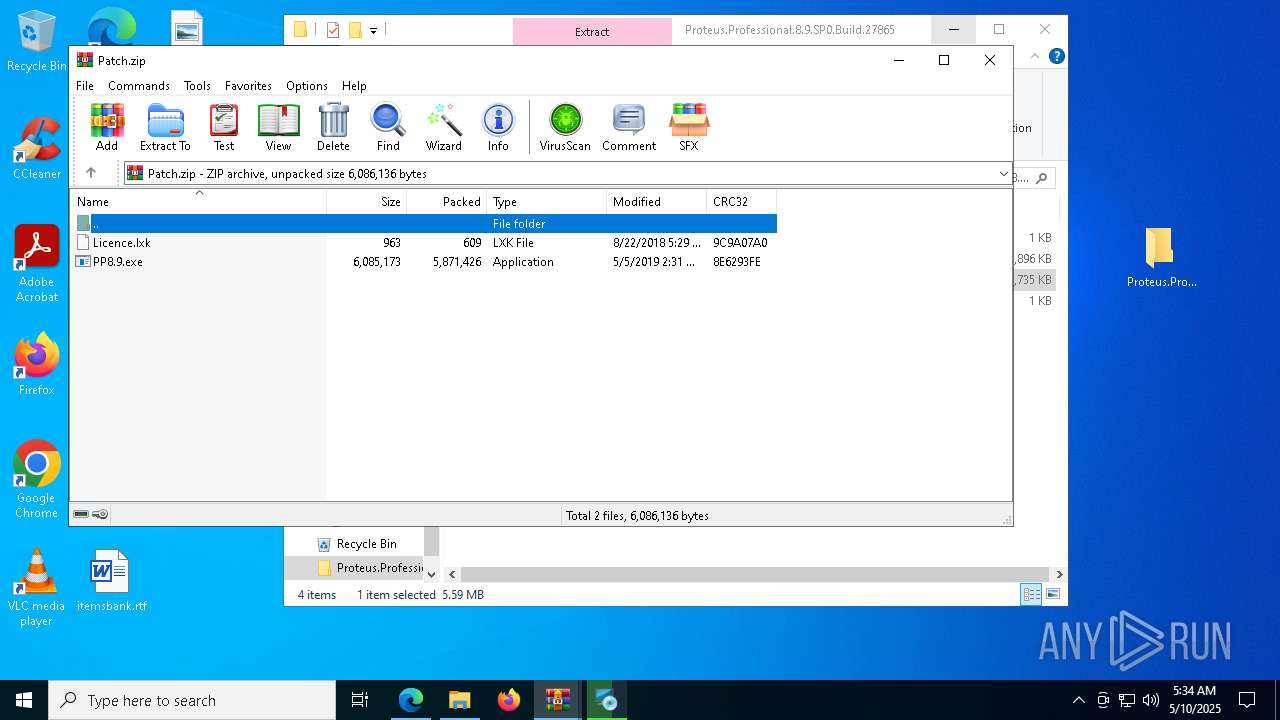
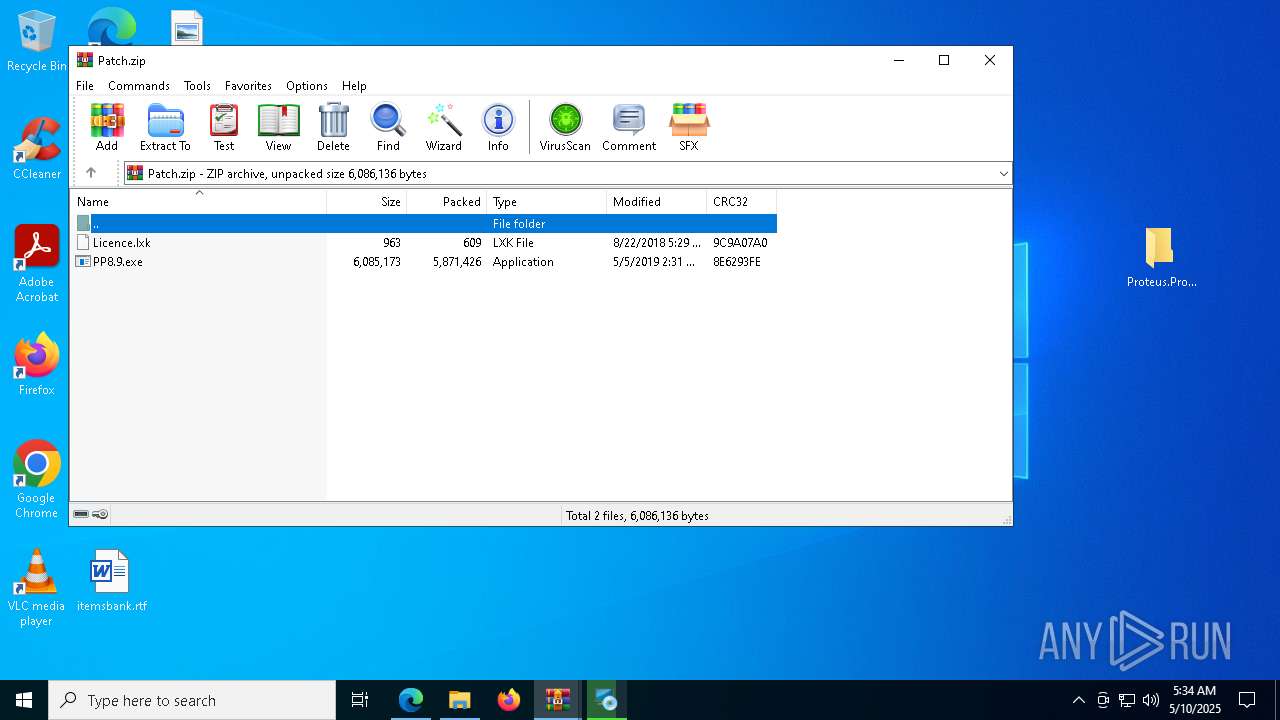
Manual execution by a user
- P8.9.sp0.exe (PID: 7100)
- P8.9.sp0.exe (PID: 4920)
- WinRAR.exe (PID: 5164)
- PP8.9.exe (PID: 776)
- PP8.9.exe (PID: 7440)
- PP8.9.exe (PID: 5480)
- PP8.9.exe (PID: 456)
- PP8.9.exe (PID: 2524)
- PP8.9.exe (PID: 2148)
- PP8.9.exe (PID: 7920)
- PP8.9.exe (PID: 7020)
- PP8.9.exe (PID: 8164)
- PP8.9.exe (PID: 8152)
- PP8.9.exe (PID: 3276)
- PP8.9.exe (PID: 5944)
- PP8.9.exe (PID: 3396)
- PP8.9.exe (PID: 6048)
- PP8.9.exe (PID: 8144)
Process checks computer location settings
- P8.9.sp0.exe (PID: 4920)
The sample compiled with russian language support
- vcredist_x86.exe (PID: 6980)
- msiexec.exe (PID: 6584)
- TiWorker.exe (PID: 7624)
Reads the machine GUID from the registry
- vcredist_x86.exe (PID: 6980)
- install.exe (PID: 540)
- msiexec.exe (PID: 6584)
The sample compiled with japanese language support
- vcredist_x86.exe (PID: 6980)
- msiexec.exe (PID: 6584)
- TiWorker.exe (PID: 7624)
The sample compiled with Italian language support
- vcredist_x86.exe (PID: 6980)
- msiexec.exe (PID: 6584)
- TiWorker.exe (PID: 7624)
Create files in a temporary directory
- P8.9.sp0.exe (PID: 4920)
- install.exe (PID: 540)
Creates files or folders in the user directory
- P8.9.sp0.exe (PID: 4920)
- install.exe (PID: 540)
The sample compiled with chinese language support
- vcredist_x86.exe (PID: 6980)
- msiexec.exe (PID: 6584)
- TiWorker.exe (PID: 7624)
The sample compiled with french language support
- vcredist_x86.exe (PID: 6980)
- msiexec.exe (PID: 6584)
- TiWorker.exe (PID: 7624)
The sample compiled with german language support
- vcredist_x86.exe (PID: 6980)
- msiexec.exe (PID: 6584)
- TiWorker.exe (PID: 7624)
The sample compiled with spanish language support
- vcredist_x86.exe (PID: 6980)
- msiexec.exe (PID: 6584)
- TiWorker.exe (PID: 7624)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6584)
- msedge.exe (PID: 2084)
- WinRAR.exe (PID: 5164)
- msiexec.exe (PID: 2392)
- msiexec.exe (PID: 1004)
The sample compiled with korean language support
- msiexec.exe (PID: 6584)
- TiWorker.exe (PID: 7624)
Manages system restore points
- SrTasks.exe (PID: 4688)
- SrTasks.exe (PID: 7792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
261
Monitored processes
110
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Users\admin\Desktop\PP8.9.exe" | C:\Users\admin\Desktop\PP8.9.exe | — | explorer.exe | |||||||||||
User: admin Company: packing case Integrity Level: MEDIUM Description: PATCH Application Exit code: 3221226540 Version: 3.0.0.0 Modules
| |||||||||||||||
| 540 | c:\5d6ed9218e20c690af17467d6ea5\.\install.exe | C:\5d6ed9218e20c690af17467d6ea5\install.exe | vcredist_x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: External Installer Exit code: 0 Version: 9.0.30729.1 built by: SP Modules
| |||||||||||||||
| 720 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=6752 --field-trial-handle=2308,i,7069788906576544140,10601954393101679973,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 776 | "C:\Users\admin\Desktop\PP8.9.exe" | C:\Users\admin\Desktop\PP8.9.exe | — | explorer.exe | |||||||||||
User: admin Company: packing case Integrity Level: MEDIUM Description: PATCH Application Exit code: 3221226540 Version: 3.0.0.0 Modules
| |||||||||||||||
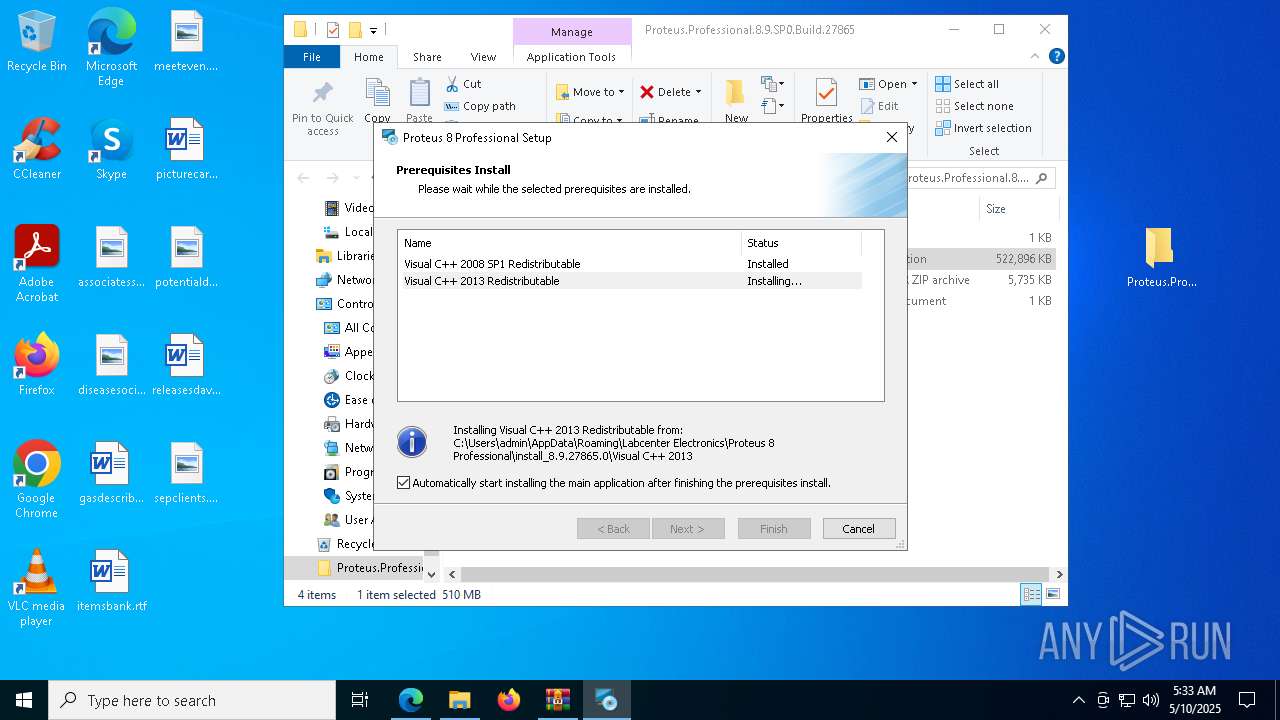
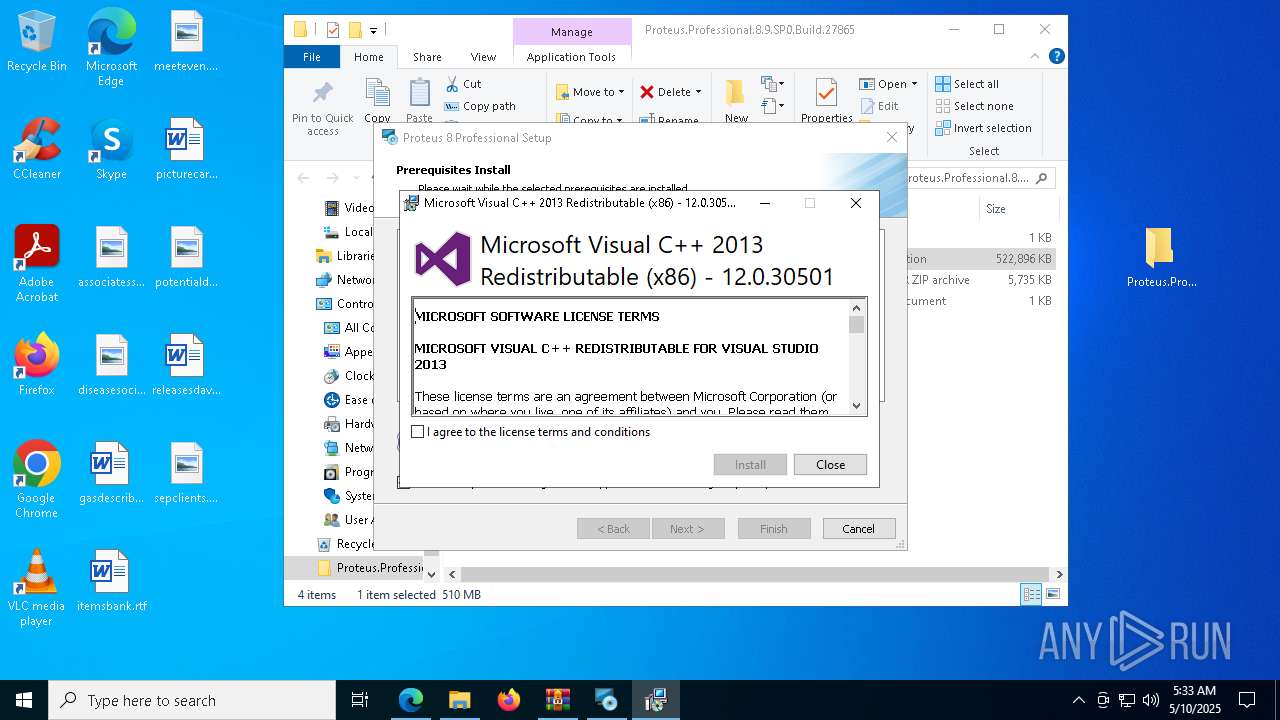
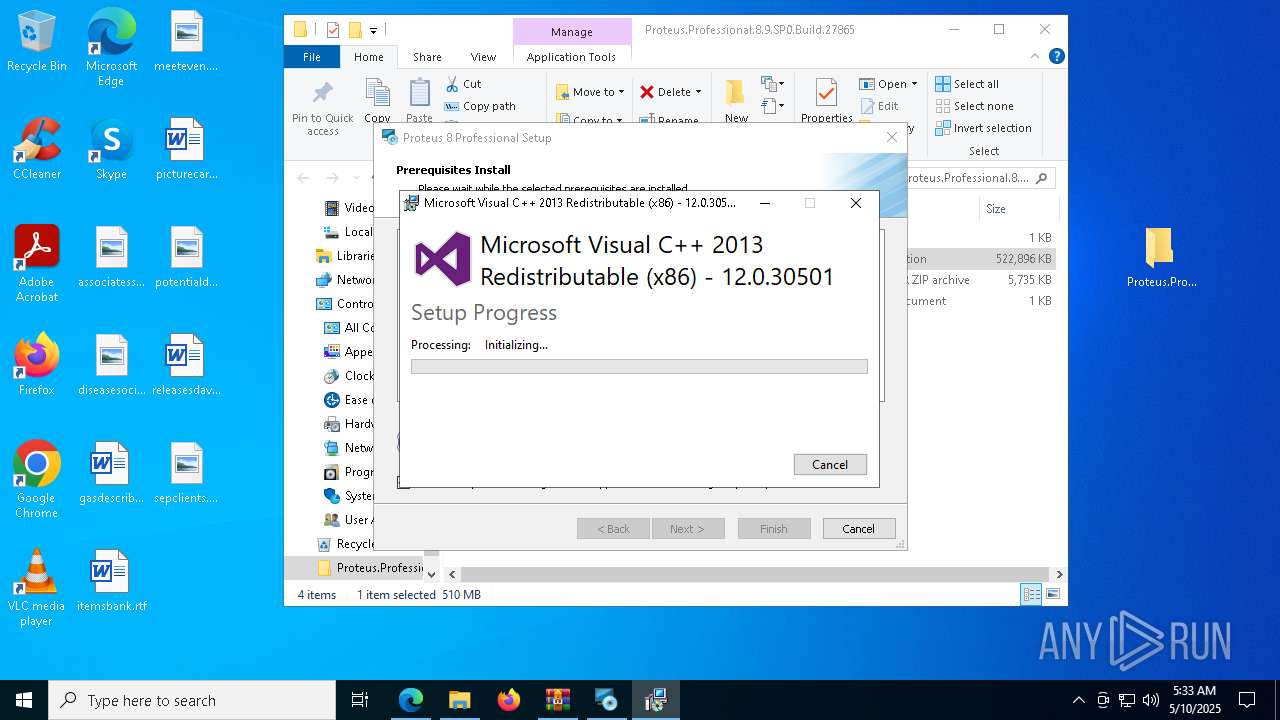
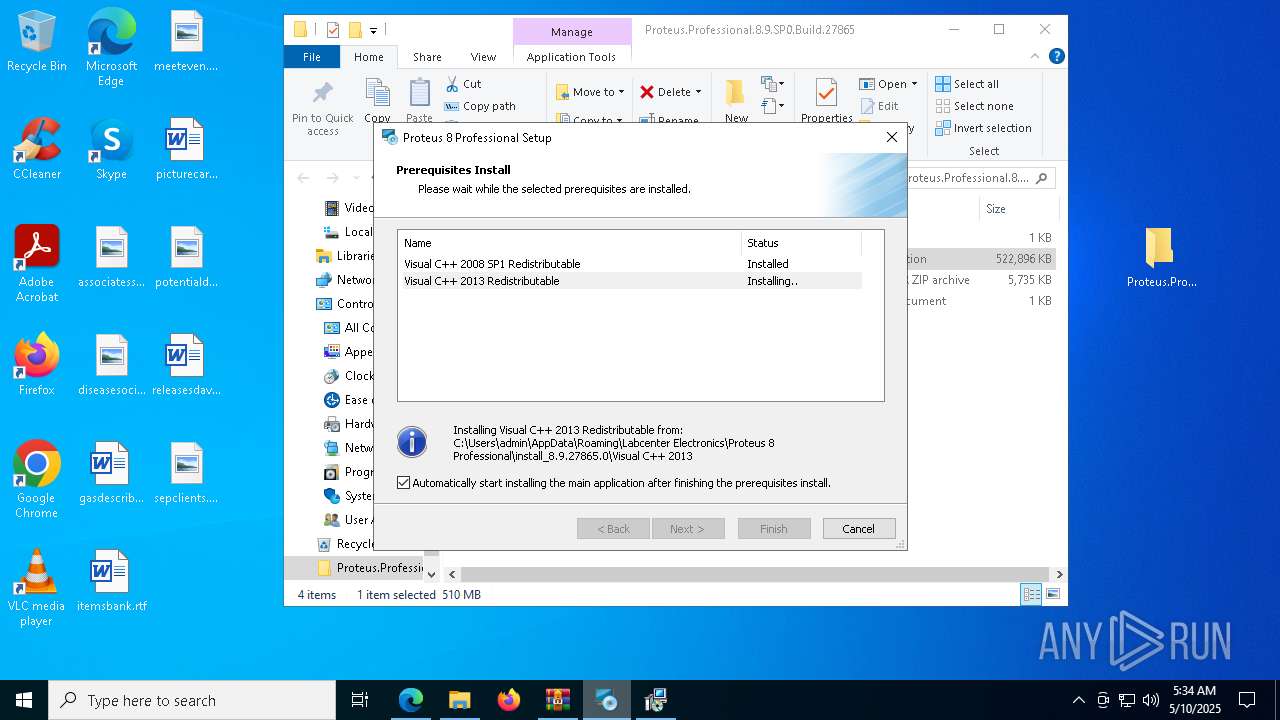
| 896 | "C:\Users\admin\AppData\Roaming\Labcenter Electronics\Proteus 8 Professional\install_8.9.27865.0\Visual C++ 2013 Redistributable\vcredist_x86_2013.exe" | C:\Users\admin\AppData\Roaming\Labcenter Electronics\Proteus 8 Professional\install_8.9.27865.0\Visual C++ 2013 Redistributable\vcredist_x86_2013.exe | P8.9.sp0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.30501 Exit code: 0 Version: 12.0.30501.0 Modules
| |||||||||||||||
| 1004 | C:\Windows\syswow64\MsiExec.exe -Embedding 78AD071DCDA0B03991F50E454CD4060F C | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5696 --field-trial-handle=2308,i,7069788906576544140,10601954393101679973,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6928 --field-trial-handle=2308,i,7069788906576544140,10601954393101679973,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6476 --field-trial-handle=2308,i,7069788906576544140,10601954393101679973,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
52 029
Read events
47 826
Write events
4 071
Delete events
132
Modification events
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 086F8CAB57932F00 | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 97BD95AB57932F00 | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {499C2DD5-2C40-4A9B-8C42-F18BF4B99A05} | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {692FC748-B708-4314-9222-67518D8690BC} | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DA86D4C5-71B6-411D-A3EA-A3BB433F38B1} | |||
| (PID) Process: | (5776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CE751027-9695-4C32-A99D-2B6157EA56CF} | |||
Executable files
382
Suspicious files
1 068
Text files
281
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10af1e.TMP | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10af1e.TMP | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10af1e.TMP | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10af2d.TMP | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10af2d.TMP | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
95
DNS requests
105
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 868 b | whitelisted |
6268 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5964 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747237928&P2=404&P3=2&P4=Yh%2bGc0LHy0qGFRKT9kXXmvO13zw49yqRKQBfGfFR2cDcISkXJ1zIT%2fOxNyysChz%2bczntntbbx3Z1aEOY0N5V%2bw%3d%3d | US | — | — | whitelisted |
6268 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
5964 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747237928&P2=404&P3=2&P4=Yh%2bGc0LHy0qGFRKT9kXXmvO13zw49yqRKQBfGfFR2cDcISkXJ1zIT%2fOxNyysChz%2bczntntbbx3Z1aEOY0N5V%2bw%3d%3d | US | binary | 1.09 Kb | whitelisted |
5964 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747237928&P2=404&P3=2&P4=Yh%2bGc0LHy0qGFRKT9kXXmvO13zw49yqRKQBfGfFR2cDcISkXJ1zIT%2fOxNyysChz%2bczntntbbx3Z1aEOY0N5V%2bw%3d%3d | US | binary | 16 b | whitelisted |
5964 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747237928&P2=404&P3=2&P4=Yh%2bGc0LHy0qGFRKT9kXXmvO13zw49yqRKQBfGfFR2cDcISkXJ1zIT%2fOxNyysChz%2bczntntbbx3Z1aEOY0N5V%2bw%3d%3d | US | compressed | 748 b | whitelisted |
5964 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747237928&P2=404&P3=2&P4=Zk1uLOvm%2fll%2beFDR7w09q0768kvtGSZFpBaySwjkFjFGm64mNACVit5lKaqVOfLY2yqGGT3GlqQuxhEy8RPC0w%3d%3d | US | compressed | 748 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5776 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7336 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7336 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7336 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
limewire.com |
| unknown |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
7336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |