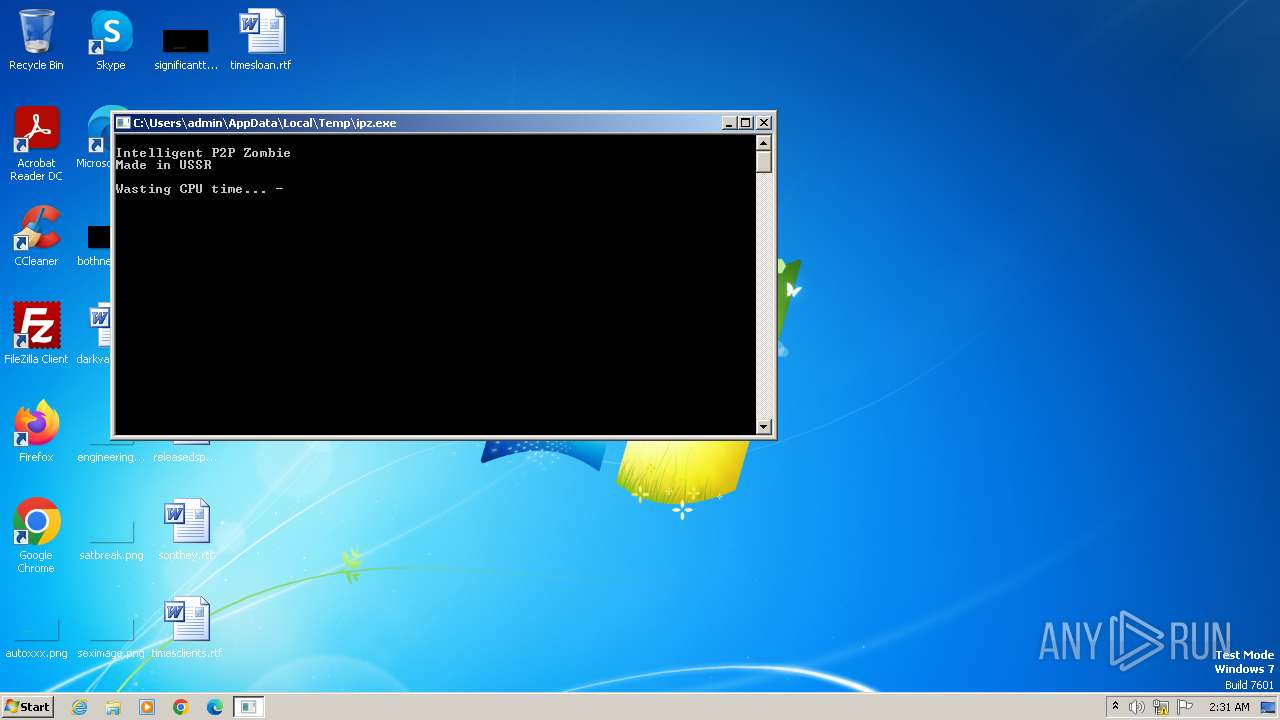
| File name: | ipz.exe |
| Full analysis: | https://app.any.run/tasks/f01f14fa-d69a-4e8d-a858-cc882f6f6919 |
| Verdict: | Malicious activity |
| Analysis date: | November 03, 2023, 02:31:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 4CABBDEC75761FB44B1AD7DE00CDD64E |
| SHA1: | 90464E7EC6B224FD67DCF8FB37EC753CDC73265B |
| SHA256: | B17A54F5218927664F4FD4861F761C6965A4F11353DAC9CA290227C70A73F0C0 |
| SSDEEP: | 12288:CUB9t73KRbidcQJWlvVcuRNim9isH9bqdz3q4txYR/w:CUB9J3OidcQJWl5RNB9isH9baa4txYRY |
MALICIOUS
No malicious indicators.SUSPICIOUS
Connects to unusual port
- ipz.exe (PID: 3416)
INFO
Reads the computer name
- ipz.exe (PID: 3416)
- wmpnscfg.exe (PID: 3764)
Checks supported languages
- ipz.exe (PID: 3416)
- wmpnscfg.exe (PID: 3764)
Create files in a temporary directory
- ipz.exe (PID: 3416)
Manual execution by a user
- wmpnscfg.exe (PID: 3764)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3764)
- ipz.exe (PID: 3416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:09:25 01:07:13+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 319488 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 376832 |
| EntryPoint: | 0xaa290 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3416 | "C:\Users\admin\AppData\Local\Temp\ipz.exe" | C:\Users\admin\AppData\Local\Temp\ipz.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3764 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
174
Read events
171
Write events
0
Delete events
3
Modification events
| (PID) Process: | (3764) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{AAC37AC4-9953-4780-BC8D-23897F0ACAC9}\{A14FA5A2-006D-4BF5-A90E-1EFEFAC68723} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3764) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{AAC37AC4-9953-4780-BC8D-23897F0ACAC9} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3764) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{531F5BF2-C7AB-4BA3-8F69-E85FB837A9DC} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
308
DNS requests
0
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3416 | ipz.exe | 73.150.24.105:4899 | — | COMCAST-7922 | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3416 | ipz.exe | 24.127.104.223:4899 | — | COMCAST-7922 | US | unknown |
3416 | ipz.exe | 66.69.130.61:4899 | — | TWC-11427-TEXAS | US | unknown |
3416 | ipz.exe | 27.15.0.192:4899 | — | CHINA UNICOM China169 Backbone | CN | unknown |
3416 | ipz.exe | 172.117.114.107:4899 | — | TWC-20001-PACWEST | US | unknown |
3416 | ipz.exe | 49.255.173.189:4899 | — | Vocus Connect International Backbone | AU | unknown |
3416 | ipz.exe | 89.12.11.22:4899 | — | Telefonica Germany | DE | unknown |
3416 | ipz.exe | 178.116.189.248:4899 | — | Telenet BVBA | BE | unknown |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3416 | ipz.exe | Potential Corporate Privacy Violation | ET POLICY Radmin Remote Control Session Setup Initiate OUTBOUND |
Process | Message |
|---|---|
ipz.exe | Peer started
|
ipz.exe | Thread 3656 - trying to connect to 83.79.104.114:4899
|
ipz.exe | Thread 3944 - trying to connect to 73.150.24.105:4899
|
ipz.exe | Thread 3844 - trying to connect to 24.127.104.223:4899
|
ipz.exe | Thread 3444 - trying to connect to 66.69.130.61:4899
|
ipz.exe | Thread 3424 - trying to connect to 27.15.0.192:4899
|
ipz.exe | Thread 3124 - trying to connect to 172.117.114.107:4899
|
ipz.exe | Thread 2424 - trying to connect to 49.255.173.189:4899
|
ipz.exe | Thread 3464 - trying to connect to 89.12.11.22:4899
|
ipz.exe | Thread 3680 - trying to connect to 178.116.189.248:4899
|