| File name: | KitchenCanvas_430195.exe |
| Full analysis: | https://app.any.run/tasks/c9b9feca-af25-4a68-b816-aef8003bdb24 |
| Verdict: | Malicious activity |
| Analysis date: | March 28, 2026, 04:04:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
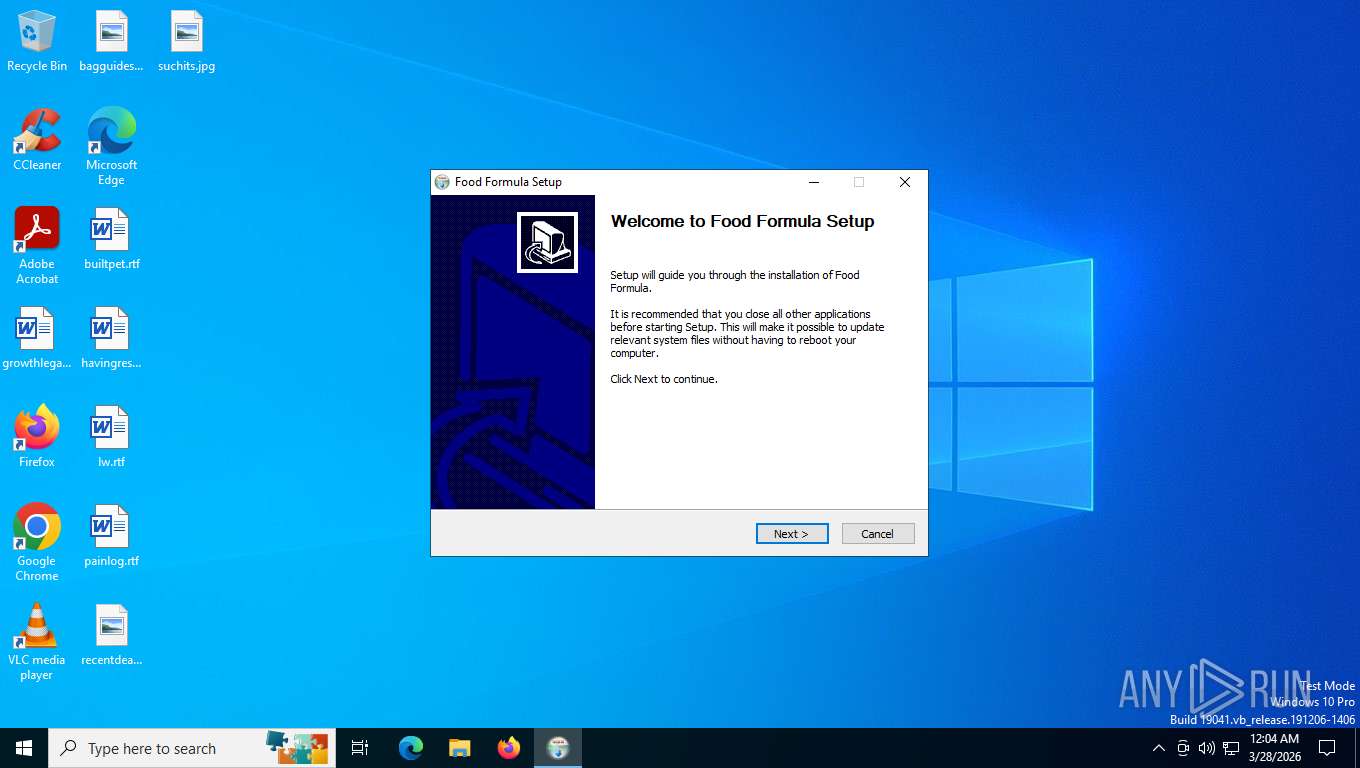
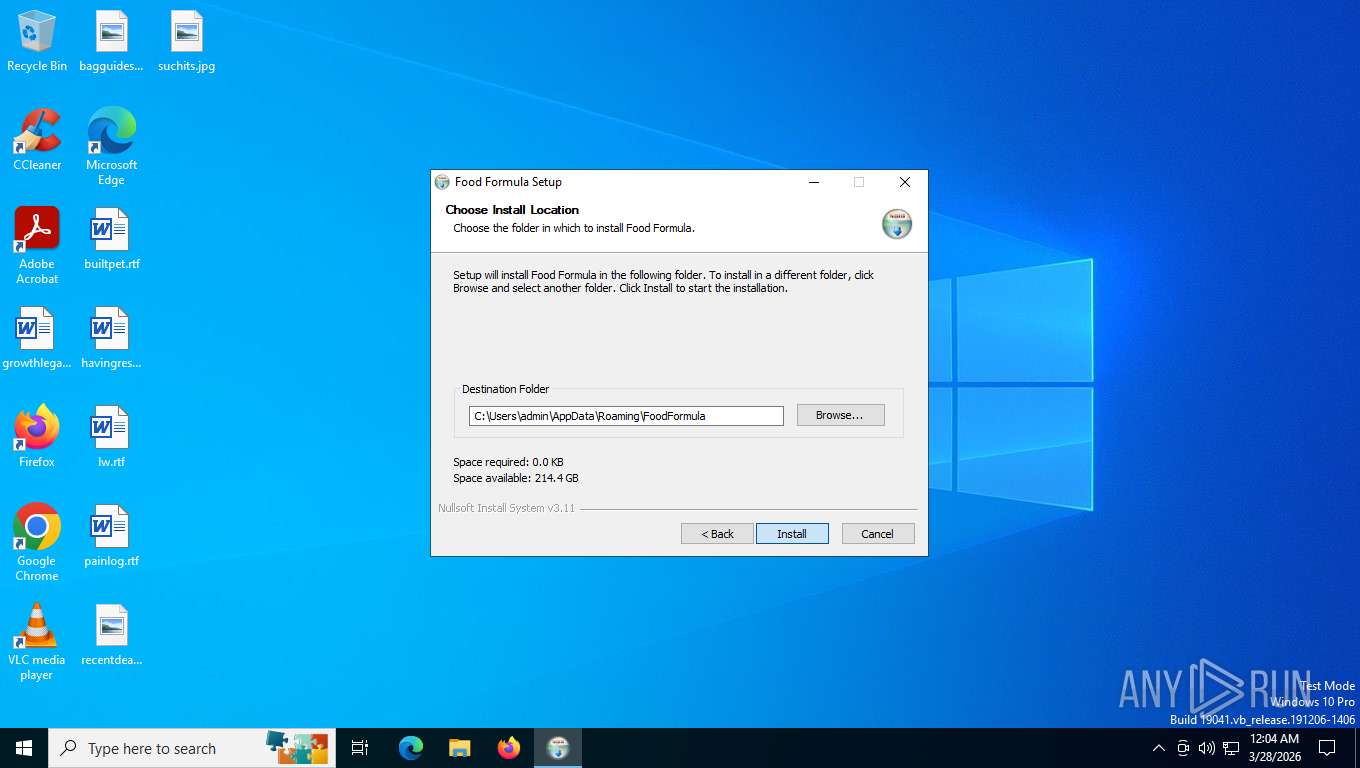
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | E0817B5012726EFCC854BB396259823C |
| SHA1: | 7B290C26CAAA28A9D08D55A9D2B8E80AEA003355 |
| SHA256: | B179BEC73EFE194BFFB69EEEDC8C136B5E7506A10B3589D223B1E6F8A8FBFB53 |
| SSDEEP: | 98304:7J8cPg35gkd9iB4QvZHlmXBUgXZDvm+PepXq1UhA8XYeBXtULw8PhERYPLujTLpE:7AScvKsl3NOhvU |
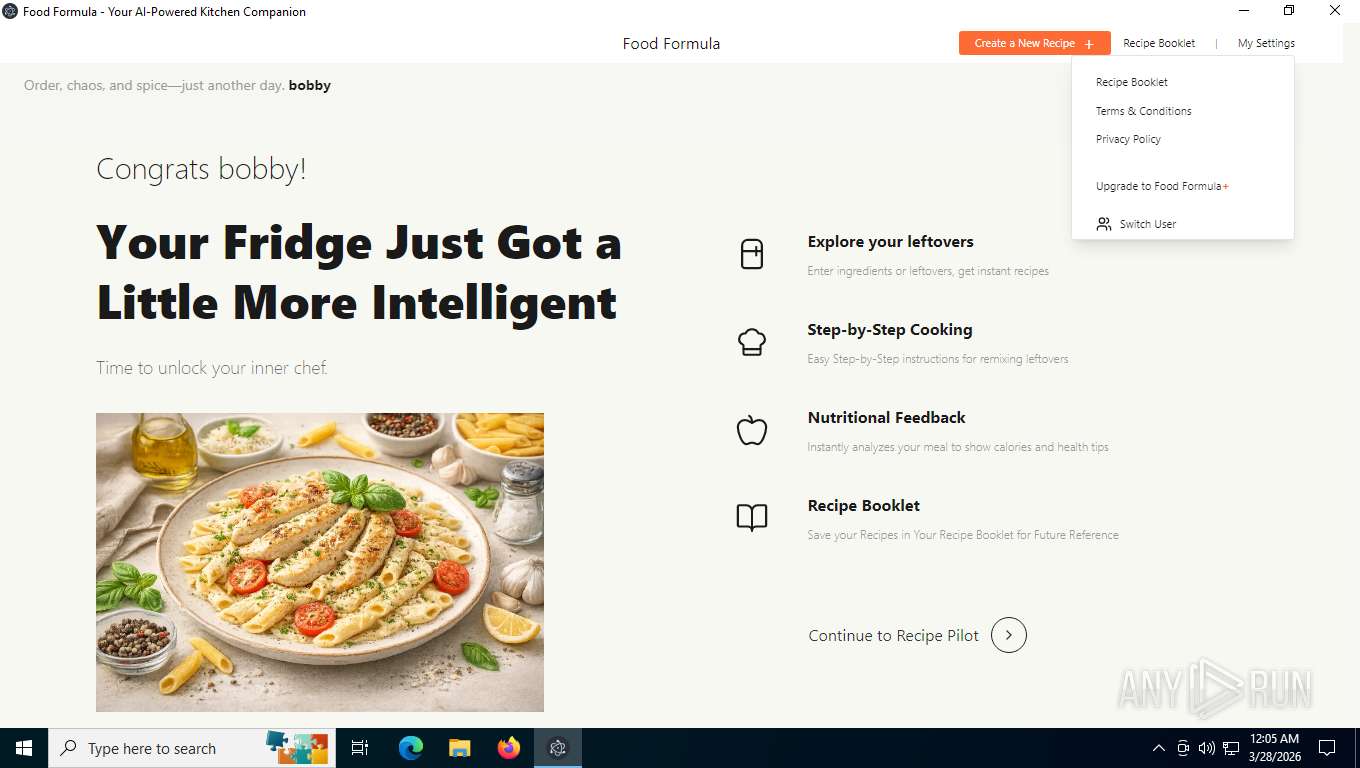
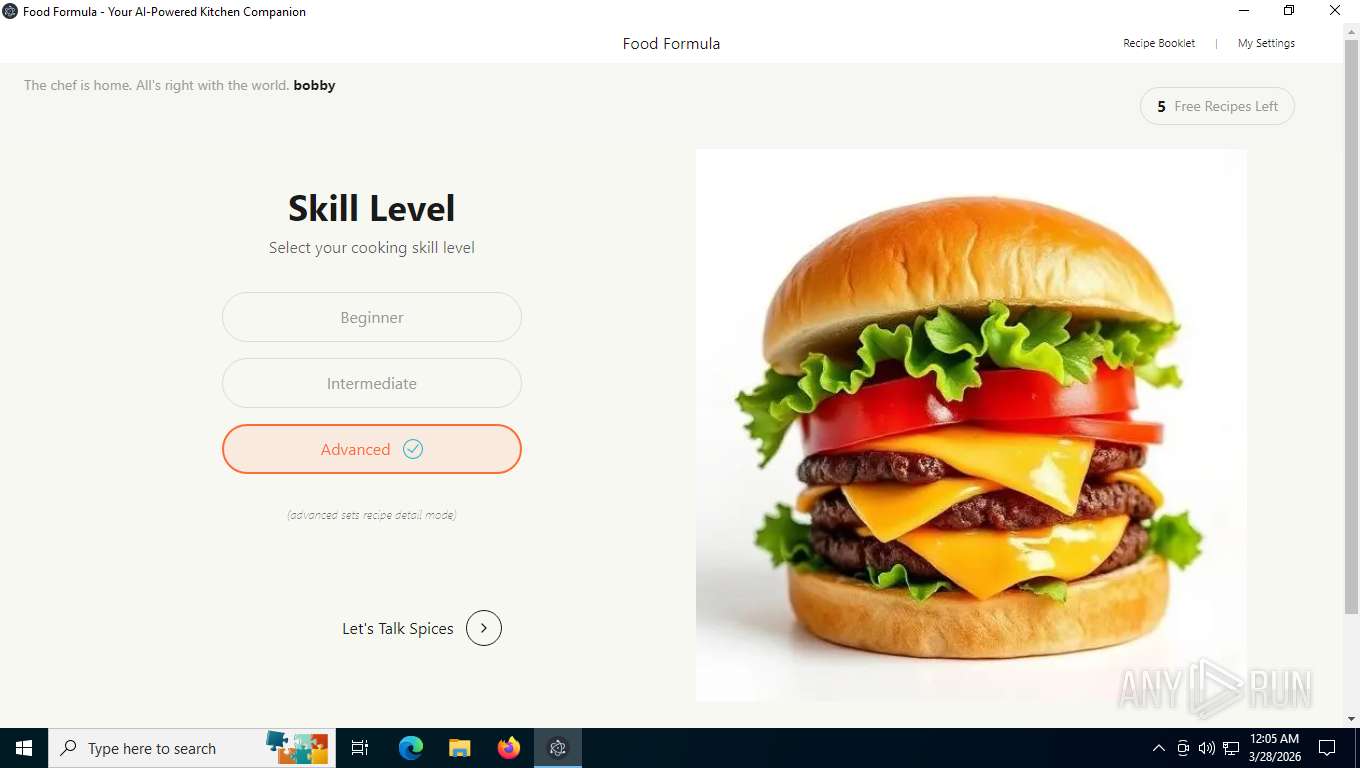
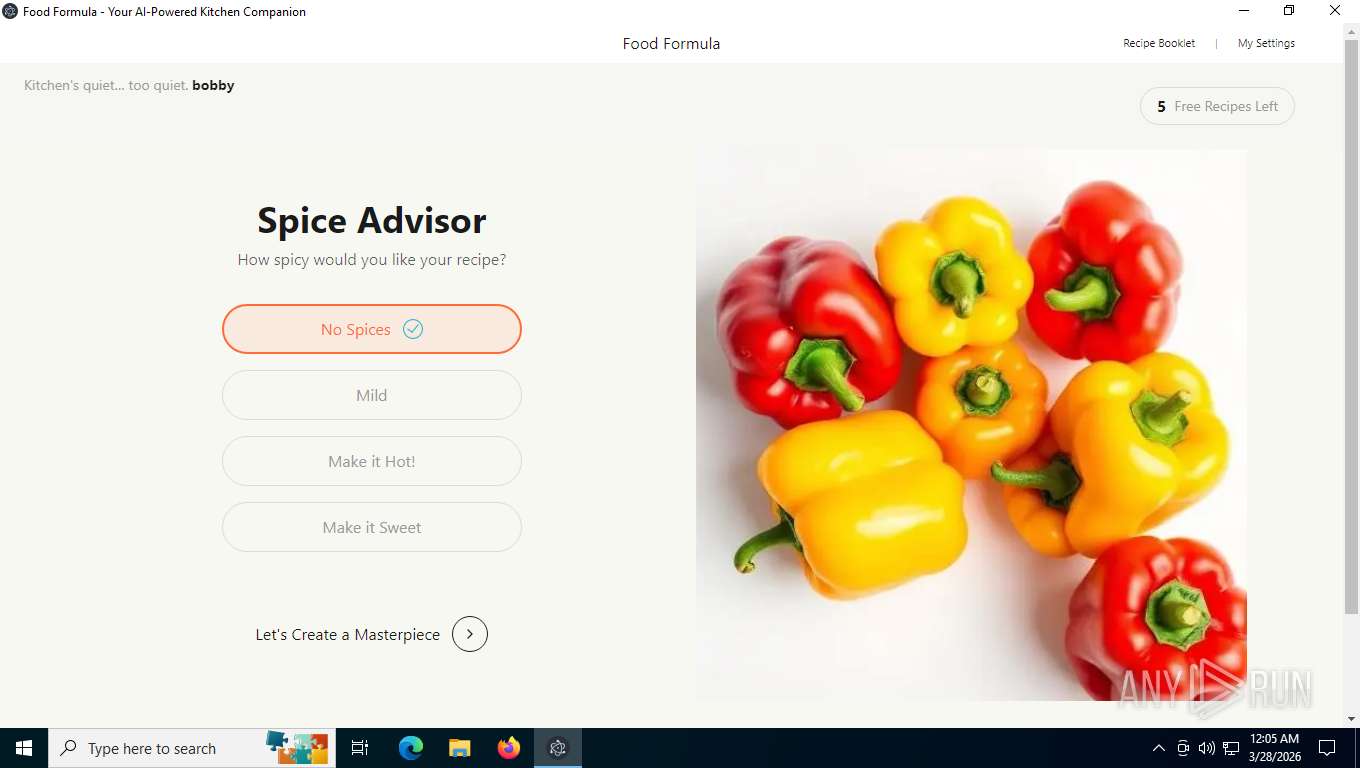
MALICIOUS
No malicious indicators.SUSPICIOUS
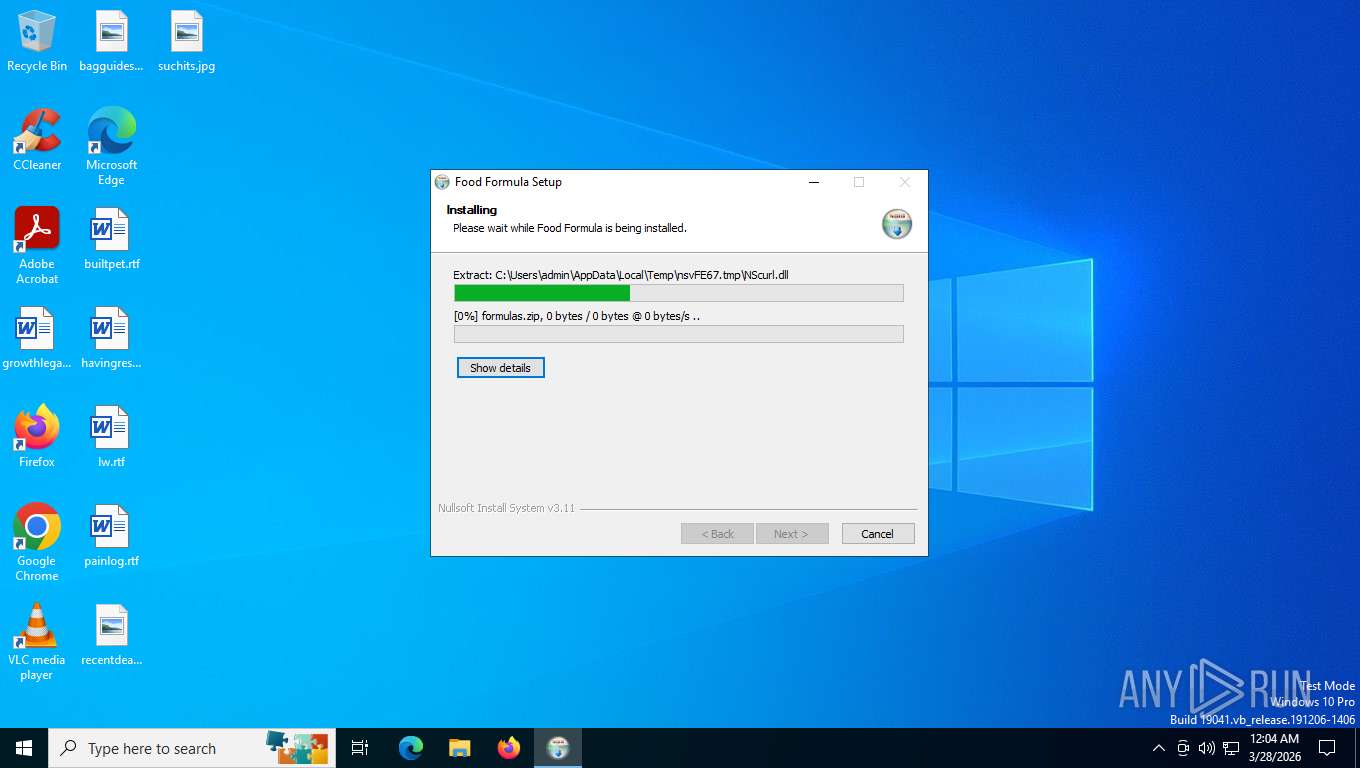
The process creates files with name similar to system file names
- KitchenCanvas_430195.exe (PID: 2576)
Malware-specific behavior (creating "System.dll" in Temp)
- KitchenCanvas_430195.exe (PID: 2576)
Application launched itself
- Food Formula.exe (PID: 5876)
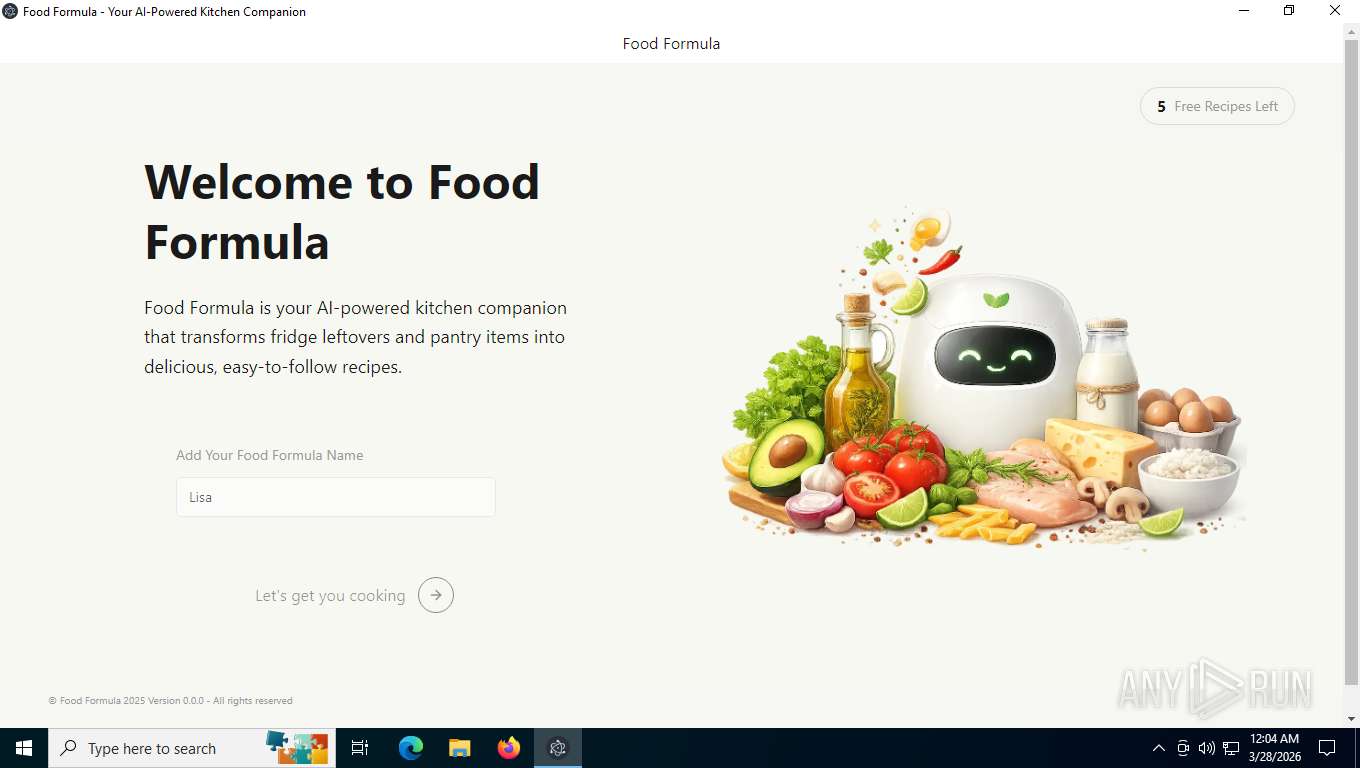
Found regular expressions for crypto-addresses (YARA)
- Food Formula.exe (PID: 8172)
INFO
Checks supported languages
- KitchenCanvas_430195.exe (PID: 2576)
- Food Formula.exe (PID: 5876)
- Food Formula.exe (PID: 5716)
- Food Formula.exe (PID: 7856)
- Food Formula.exe (PID: 7972)
- Food Formula.exe (PID: 8172)
Create files in a temporary directory
- KitchenCanvas_430195.exe (PID: 2576)
- Food Formula.exe (PID: 5876)
Creates files or folders in the user directory
- KitchenCanvas_430195.exe (PID: 2576)
- Food Formula.exe (PID: 5876)
- Food Formula.exe (PID: 7856)
- Food Formula.exe (PID: 7972)
Reads the machine GUID from the registry
- KitchenCanvas_430195.exe (PID: 2576)
- Food Formula.exe (PID: 5876)
- Food Formula.exe (PID: 7972)
The sample compiled with english language support
- KitchenCanvas_430195.exe (PID: 2576)
Reads the computer name
- KitchenCanvas_430195.exe (PID: 2576)
- Food Formula.exe (PID: 5876)
- Food Formula.exe (PID: 5716)
- Food Formula.exe (PID: 7856)
- Food Formula.exe (PID: 7972)
There is functionality for taking screenshot (YARA)
- KitchenCanvas_430195.exe (PID: 2576)
- Food Formula.exe (PID: 5716)
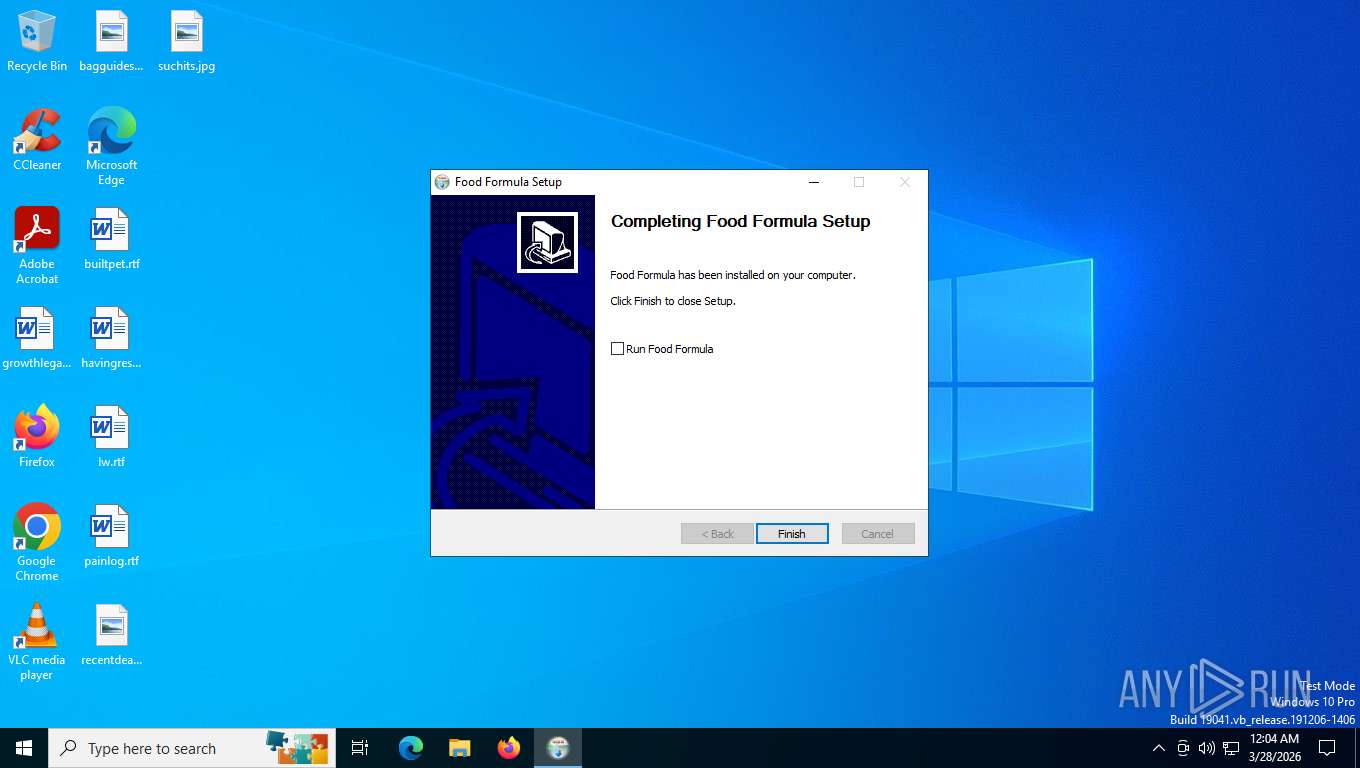
Creates a software uninstall entry
- KitchenCanvas_430195.exe (PID: 2576)
Reads product name
- Food Formula.exe (PID: 5876)
- Food Formula.exe (PID: 8172)
Reads Environment values
- Food Formula.exe (PID: 5876)
- Food Formula.exe (PID: 8172)
Node.js compiler has been detected
- Food Formula.exe (PID: 5876)
- Food Formula.exe (PID: 5716)
- Food Formula.exe (PID: 7856)
- Food Formula.exe (PID: 8172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:56:47+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3640 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.6.8.3 |
| ProductVersionNumber: | 2.6.8.3 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | FormulaSetup |
| FileVersion: | 2.6.8.3 |
| ProductName: | FormulaSetup |
| ProductVersion: | 2.6.8.3 |
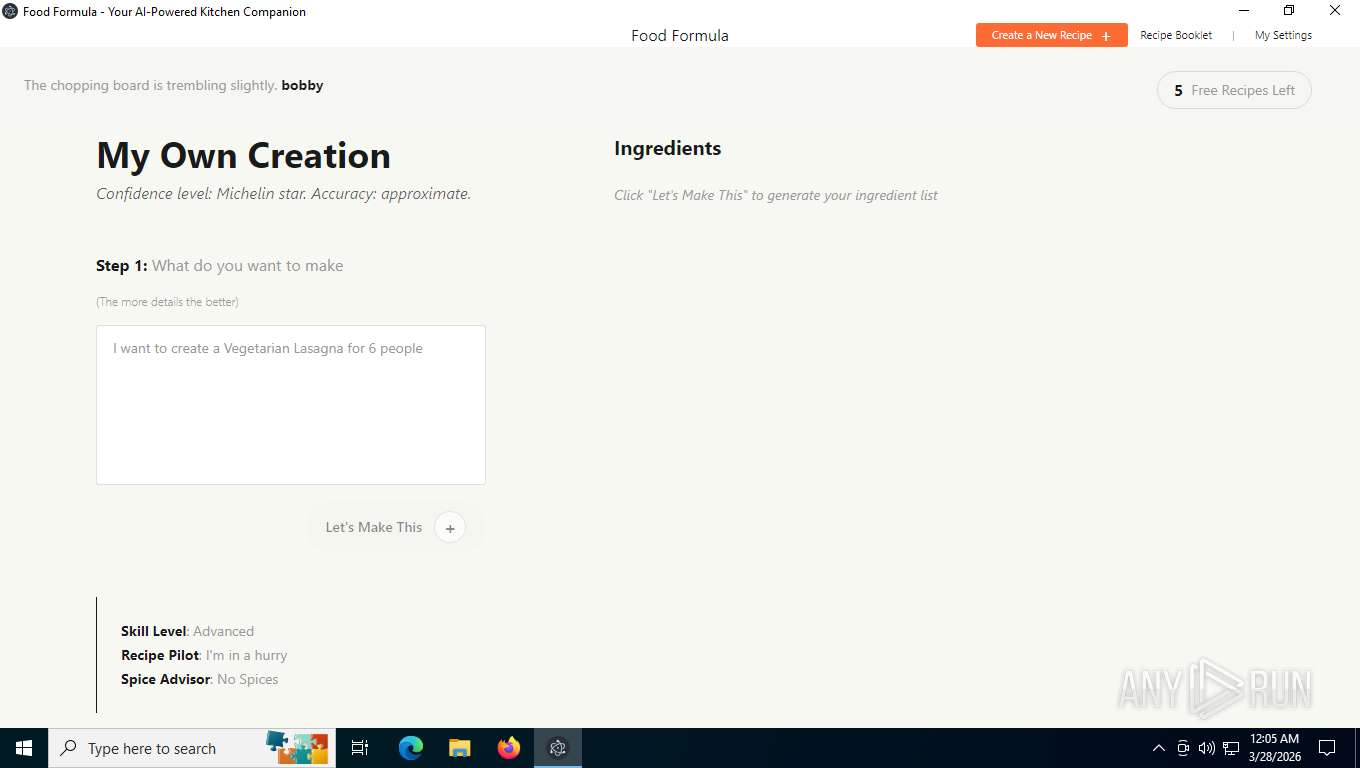
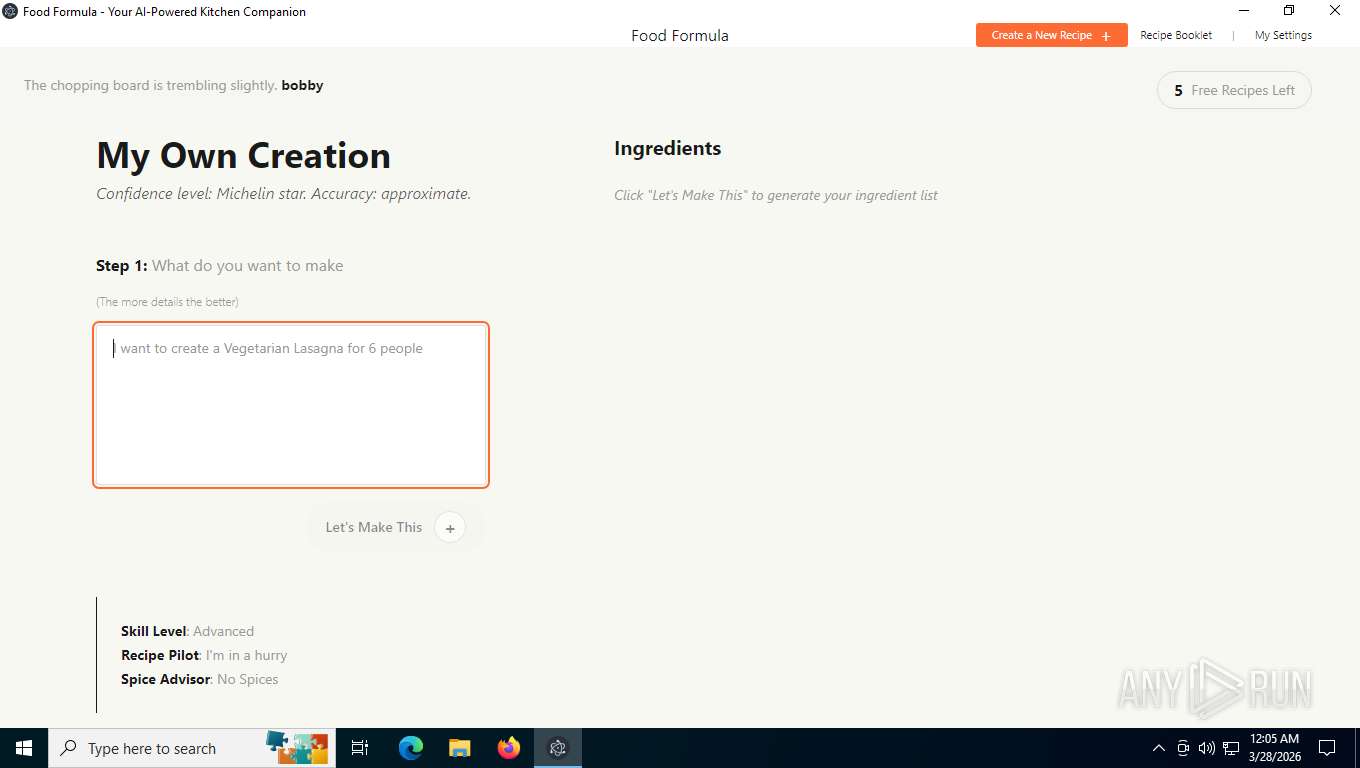
Total processes
145
Monitored processes
6
Malicious processes
3
Suspicious processes
0
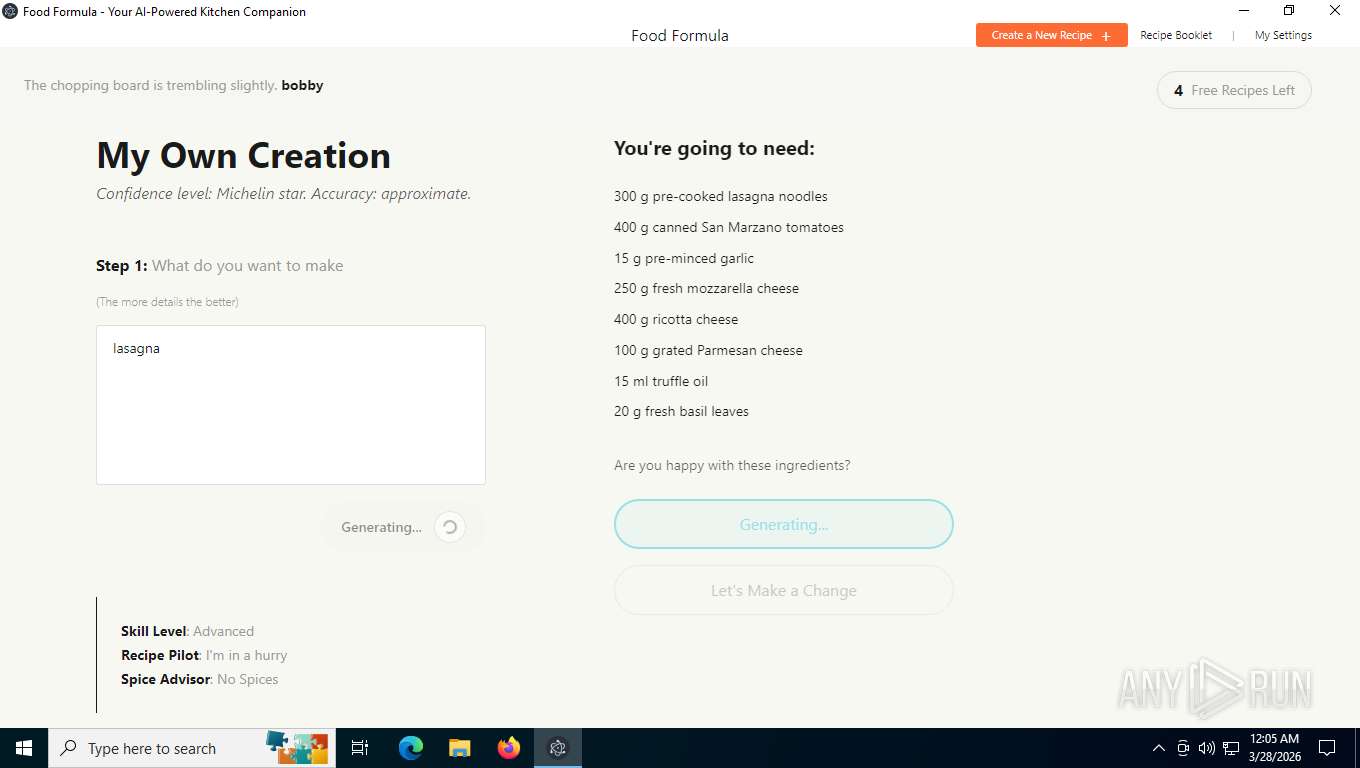
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2576 | "C:\Users\admin\AppData\Local\Temp\KitchenCanvas_430195.exe" | C:\Users\admin\AppData\Local\Temp\KitchenCanvas_430195.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: FormulaSetup Exit code: 0 Version: 2.6.8.3 Modules
| |||||||||||||||
| 5716 | "C:\Users\admin\AppData\Roaming\FoodFormula\Food Formula.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\food-formula-nativefier-cc6e45" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1616 --field-trial-handle=1696,i,3260034670217952264,6593247457260441118,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Roaming\FoodFormula\Food Formula.exe | — | Food Formula.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: LOW Description: Food Formula Version: 2.6.8.3 Modules
| |||||||||||||||
| 5876 | "C:\Users\admin\AppData\Roaming\FoodFormula\Food Formula.exe" | C:\Users\admin\AppData\Roaming\FoodFormula\Food Formula.exe | — | KitchenCanvas_430195.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: Food Formula Version: 2.6.8.3 Modules
| |||||||||||||||
| 7856 | "C:\Users\admin\AppData\Roaming\FoodFormula\Food Formula.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\food-formula-nativefier-cc6e45" --mojo-platform-channel-handle=2036 --field-trial-handle=1696,i,3260034670217952264,6593247457260441118,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Roaming\FoodFormula\Food Formula.exe | Food Formula.exe | ||||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: Food Formula Version: 2.6.8.3 Modules
| |||||||||||||||
| 7972 | "C:\Users\admin\AppData\Roaming\FoodFormula\Food Formula.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --user-data-dir="C:\Users\admin\AppData\Roaming\food-formula-nativefier-cc6e45" --gpu-preferences=UAAAAAAAAADoAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=3324 --field-trial-handle=1696,i,3260034670217952264,6593247457260441118,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Roaming\FoodFormula\Food Formula.exe | — | Food Formula.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: Food Formula Exit code: 0 Version: 2.6.8.3 Modules
| |||||||||||||||
| 8172 | "C:\Users\admin\AppData\Roaming\FoodFormula\Food Formula.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\food-formula-nativefier-cc6e45" --app-user-model-id=food-formula-nativefier-cc6e45 --app-path="C:\Users\admin\AppData\Roaming\FoodFormula\resources\app" --no-sandbox --no-zygote --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2408 --field-trial-handle=1696,i,3260034670217952264,6593247457260441118,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Roaming\FoodFormula\Food Formula.exe | — | Food Formula.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: Food Formula Version: 2.6.8.3 Modules
| |||||||||||||||
Total events
8 176
Read events
8 154
Write events
4
Delete events
18
Modification events
| (PID) Process: | (2576) KitchenCanvas_430195.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FoodFormula |
| Operation: | write | Name: | DisplayName |
Value: Food Formula | |||
| (PID) Process: | (2576) KitchenCanvas_430195.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FoodFormula |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Roaming\FoodFormula\uninstall.exe" | |||
| (PID) Process: | (2576) KitchenCanvas_430195.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FoodFormula |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Users\admin\AppData\Roaming\FoodFormula\Food Formula.exe" | |||
| (PID) Process: | (2576) KitchenCanvas_430195.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FoodFormula |
| Operation: | write | Name: | DisplayVersion |
Value: 2.6.8.3 | |||
| (PID) Process: | (5876) Food Formula.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (5876) Food Formula.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (5876) Food Formula.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
Executable files
0
Suspicious files
2
Text files
4
Unknown types
133
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2576 | KitchenCanvas_430195.exe | C:\Users\admin\AppData\Roaming\FoodFormula\formulas.zip | — | |
MD5:— | SHA256:— | |||
| 2576 | KitchenCanvas_430195.exe | C:\Users\admin\AppData\Roaming\FoodFormula\Food Formula.exe | — | |
MD5:— | SHA256:— | |||
| 2576 | KitchenCanvas_430195.exe | C:\Users\admin\AppData\Roaming\FoodFormula\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 2576 | KitchenCanvas_430195.exe | C:\Users\admin\AppData\Roaming\FoodFormula\LICENSES.chromium.html | — | |
MD5:— | SHA256:— | |||
| 2576 | KitchenCanvas_430195.exe | C:\Users\admin\AppData\Local\Temp\nsvFE67.tmp\modern-wizard.bmp | binary | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2576 | KitchenCanvas_430195.exe | C:\Users\admin\AppData\Local\Temp\nsvFE67.tmp\nsDialogs.dll | binary | |
MD5:6C3F8C94D0727894D706940A8A980543 | SHA256:56B96ADD1978B1ABBA286F7F8982B0EFBE007D4A48B3DED6A4D408E01D753FE2 | |||
| 2576 | KitchenCanvas_430195.exe | C:\Users\admin\AppData\Local\Temp\nsvFE67.tmp\System.dll | binary | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 2576 | KitchenCanvas_430195.exe | C:\Users\admin\AppData\Local\Temp\nsvFE67.tmp\math.dll | binary | |
MD5:180E3D5A7BBA737C402C9A1B86BFCE2A | SHA256:DFD1251DA5DA673223FC362F9EA82F9F536EF04C95C70435B7D5A1B7B9106396 | |||
| 2576 | KitchenCanvas_430195.exe | C:\Users\admin\AppData\Local\Temp\nsvFE67.tmp\NScurl.dll | binary | |
MD5:22A84B82B3CC522E426A12B1F47FFEB8 | SHA256:618BFD44228132C037D5F607D16AD2BE0CBA238824AC3A366DD602BF93BD464E | |||
| 2576 | KitchenCanvas_430195.exe | C:\Users\admin\AppData\Roaming\FoodFormula\libEGL.dll | binary | |
MD5:961C060F241A7AE22E962C82D7803EF1 | SHA256:C8E8007D746DF73EDBF73CDFF18C09BB756F43814978C84A28A72F95D0AC5DC9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
33
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2576 | KitchenCanvas_430195.exe | GET | 200 | 172.67.73.218:443 | https://foodformulasetup.com/?s=d9c2a37cd6c586250adaa11f77794916253d8010587f5cbf28cf9a7453d3af7a&d=917375 | US | binary | 64 b | unknown |
5276 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
5316 | svchost.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | NL | binary | 471 b | whitelisted |
5316 | svchost.exe | POST | 400 | 40.126.31.67:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | binary | 203 b | whitelisted |
4708 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
4708 | SIHClient.exe | GET | 200 | 135.232.92.97:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
4708 | SIHClient.exe | GET | 200 | 74.178.240.61:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
4708 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
5316 | svchost.exe | POST | 400 | 40.126.31.67:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | binary | 203 b | whitelisted |
5316 | svchost.exe | POST | 400 | 40.126.31.67:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | binary | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8044 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
2576 | KitchenCanvas_430195.exe | 172.67.73.218:443 | foodformulasetup.com | CLOUDFLARENET | US | whitelisted |
5316 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3428 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5316 | svchost.exe | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
8044 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
foodformulasetup.com |
| unknown |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
formulas.foodformulasetup.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8044 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |