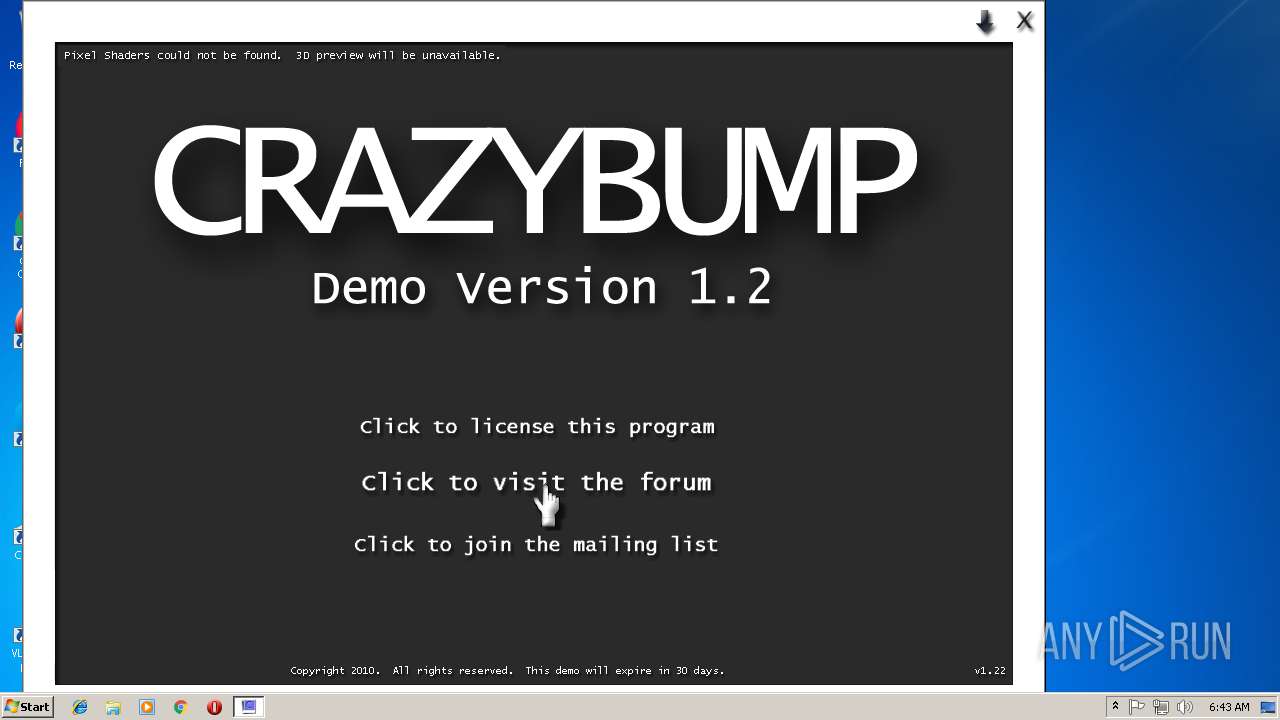
| File name: | CrazyBumpSetup122.exe |
| Full analysis: | https://app.any.run/tasks/27025a24-7961-4f15-94d0-4a60c4868f82 |
| Verdict: | Malicious activity |
| Analysis date: | November 05, 2018, 06:41:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | ED057BFBBE3E6537AFF4D9EE97CF3ED3 |
| SHA1: | F8403491A4CFB1350790D92AF56C73E318598A61 |
| SHA256: | B178F2A6A1C8A3110818D7EB79561AF87168448C3A339C51FFE9BF6746E0B5D8 |
| SSDEEP: | 98304:FvWZQgdWvWEs9sXygmx76gDUimkG0GUKbd8W8FHtBi/hs4qURDN4Yb5RD:FvqhWWEs9CygmxVDekMFl8F3GsM6Ytl |
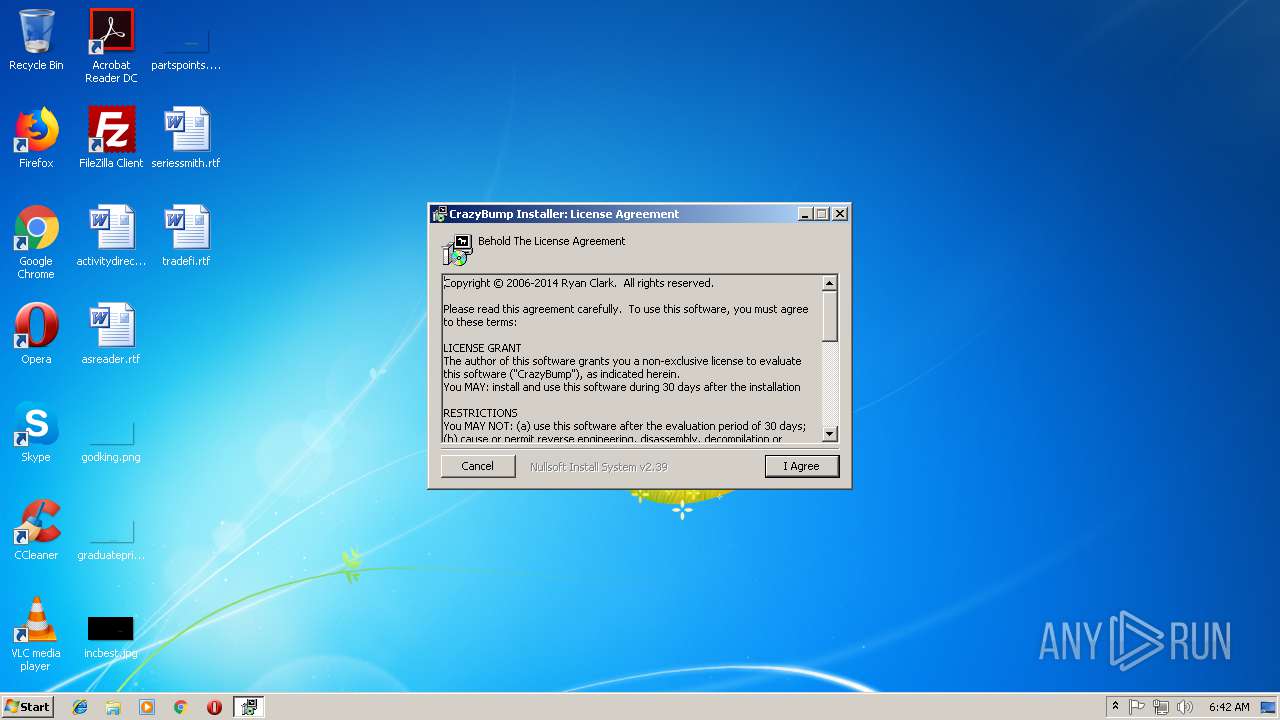
MALICIOUS
Loads dropped or rewritten executable
- CrazyBumpSetup122.exe (PID: 2896)
- CrazyBump.exe (PID: 2024)
Application was dropped or rewritten from another process
- CrazyBump.exe (PID: 2024)
SUSPICIOUS
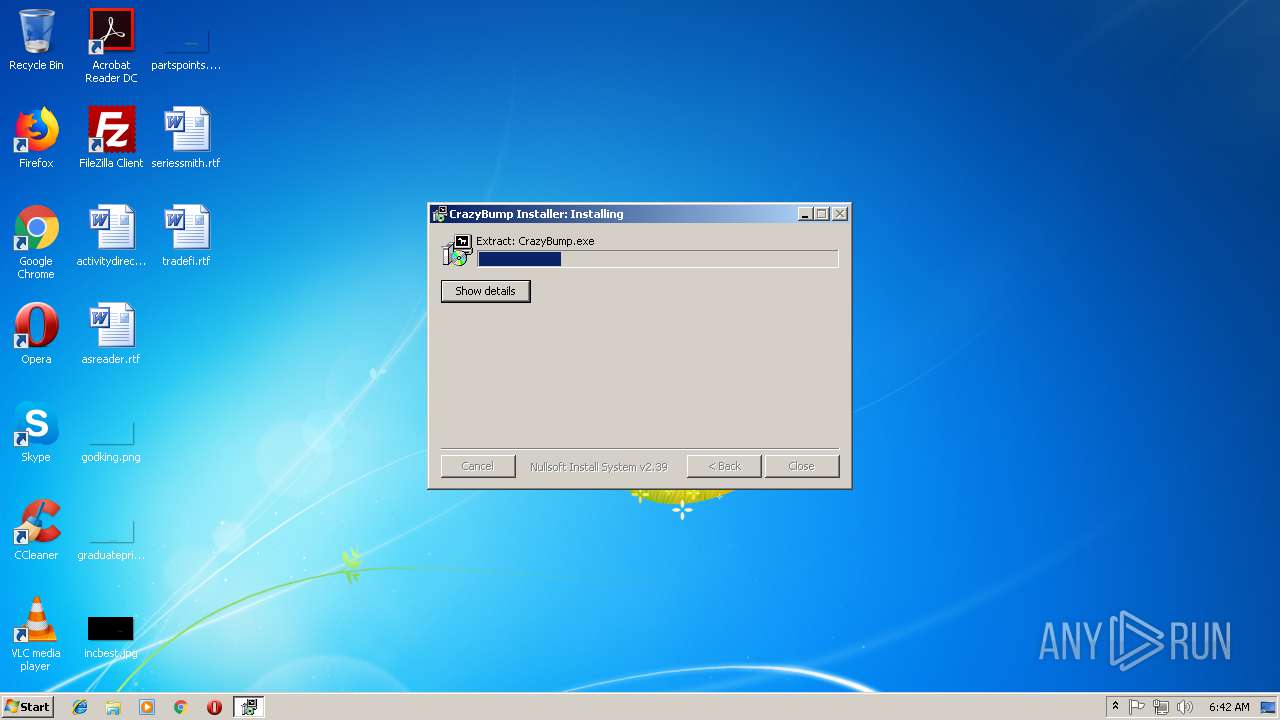
Executable content was dropped or overwritten
- CrazyBumpSetup122.exe (PID: 2896)
Creates files in the program directory
- CrazyBumpSetup122.exe (PID: 2896)
- CrazyBump.exe (PID: 2024)
Creates files in the user directory
- CrazyBumpSetup122.exe (PID: 2896)
Creates a software uninstall entry
- CrazyBumpSetup122.exe (PID: 2896)
Low-level read access rights to disk partition
- CrazyBump.exe (PID: 2024)
INFO
Dropped object may contain Bitcoin addresses
- CrazyBumpSetup122.exe (PID: 2896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:08:16 22:26:10+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 22528 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30b4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Aug-2008 20:26:10 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Aug-2008 20:26:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000057EC | 0x00005800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47541 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17644 |
.data | 0x00009000 | 0x0001AF58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59051 |
.ndata | 0x00024000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002C000 | 0x00000C50 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.91755 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08664 | 733 | UNKNOWN | English - United States | RT_MANIFEST |
102 | 2.74309 | 184 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2024 | "C:\Program Files\Crazybump\CrazyBump.exe" | C:\Program Files\Crazybump\CrazyBump.exe | CrazyBumpSetup122.exe | ||||||||||||
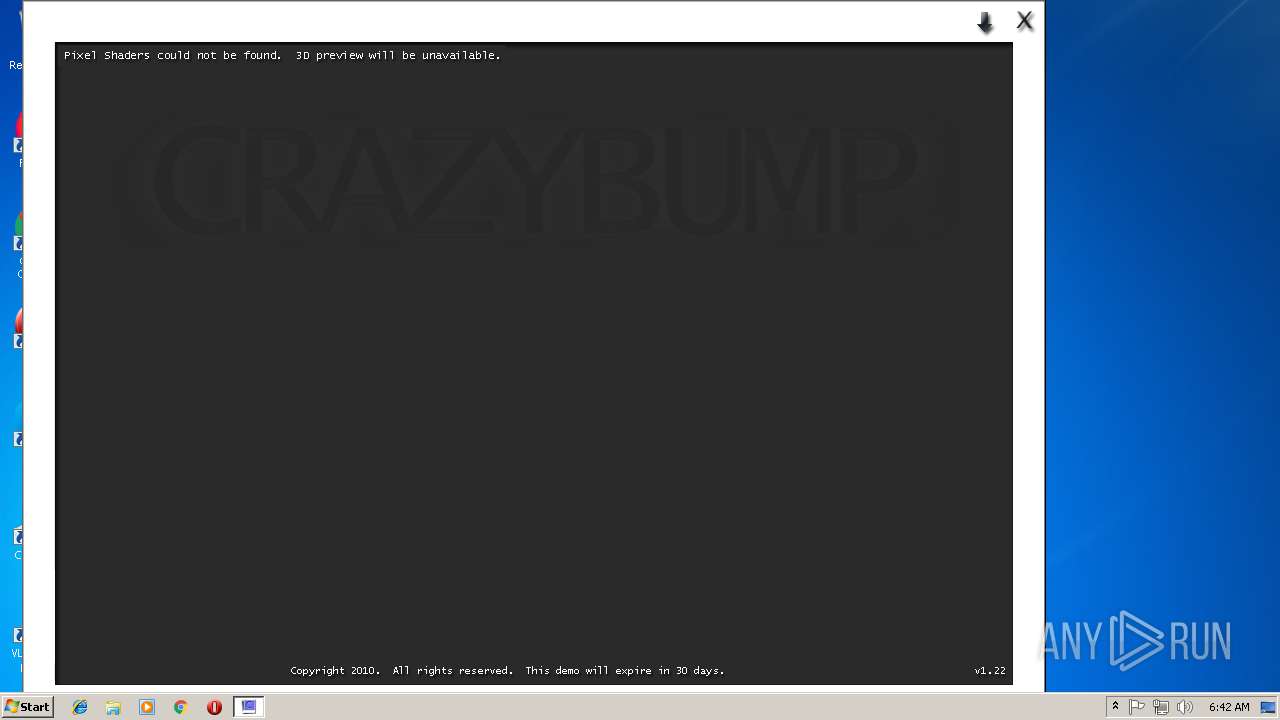
User: admin Company: CrazyBump Software Integrity Level: HIGH Description: CrazyBump 3D Material Editor Exit code: 0 Version: 1, 2, 0, 1 Modules
| |||||||||||||||
| 2896 | "C:\Users\admin\AppData\Local\Temp\CrazyBumpSetup122.exe" | C:\Users\admin\AppData\Local\Temp\CrazyBumpSetup122.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4092 | "C:\Users\admin\AppData\Local\Temp\CrazyBumpSetup122.exe" | C:\Users\admin\AppData\Local\Temp\CrazyBumpSetup122.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
423
Read events
376
Write events
47
Delete events
0
Modification events
| (PID) Process: | (2896) CrazyBumpSetup122.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Crazybump |
| Operation: | write | Name: | DisplayName |
Value: Crazybump (remove only) | |||
| (PID) Process: | (2896) CrazyBumpSetup122.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Crazybump |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Crazybump\uninst.exe" | |||
| (PID) Process: | (2024) CrazyBump.exe | Key: | HKEY_CLASSES_ROOT\.slk57o |
| Operation: | write | Name: | Extension (sq211) |
Value: D8CE3540D8CE3540 | |||
| (PID) Process: | (2024) CrazyBump.exe | Key: | HKEY_CLASSES_ROOT\.sfs83k |
| Operation: | write | Name: | Extension (sd284) |
Value: 2911551095CC2AEE | |||
| (PID) Process: | (2024) CrazyBump.exe | Key: | HKEY_CLASSES_ROOT\.rae23m |
| Operation: | write | Name: | Extension (di856) |
Value: D84EC128D84EC128 | |||
| (PID) Process: | (2024) CrazyBump.exe | Key: | HKEY_CLASSES_ROOT\.hlv71x |
| Operation: | write | Name: | Extension (bn780) |
Value: AAC52A112A852AEE | |||
| (PID) Process: | (2024) CrazyBump.exe | Key: | HKEY_CURRENT_USER\Software\CrazyBump |
| Operation: | write | Name: | 122 |
Value: 1 | |||
| (PID) Process: | (2024) CrazyBump.exe | Key: | HKEY_CURRENT_USER\Software\licensecb |
| Operation: | write | Name: | 111r |
Value: 923454 | |||
| (PID) Process: | (2024) CrazyBump.exe | Key: | HKEY_CURRENT_USER\Software\CrazyBump |
| Operation: | write | Name: | AutomateSaveNormals |
Value: 1 | |||
| (PID) Process: | (2024) CrazyBump.exe | Key: | HKEY_CURRENT_USER\Software\CrazyBump |
| Operation: | write | Name: | AutomateSaveDisplacement |
Value: 0 | |||
Executable files
22
Suspicious files
0
Text files
15
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | CrazyBumpSetup122.exe | C:\Users\admin\AppData\Local\CrazyBump\box.3ds | 3ds | |
MD5:B562089B1FB8014A57D699647CBA6267 | SHA256:5FB151DDAE3097A405C0CC637A1B52F821393BF719E08B37E19342B1DC7D1173 | |||
| 2896 | CrazyBumpSetup122.exe | C:\Program Files\Crazybump\CrazyInputBox.dll | executable | |
MD5:CC13695F5A204490EA9016C472B6ED09 | SHA256:464983C4E6D59BD2A71E1F398992D1EAEF5E901F561E1E1D2AC8F665BBFF1F91 | |||
| 2896 | CrazyBumpSetup122.exe | C:\Program Files\Crazybump\CrazyTrackbar.dll | executable | |
MD5:C2EF4F360C28A5C568F47F9FC9A1E279 | SHA256:4CD0FCD7412C4EE753BD90788F76D852ACABEC228182DD47D18A8F597DEE62B5 | |||
| 2896 | CrazyBumpSetup122.exe | C:\Program Files\Crazybump\CrazyBump.exe | executable | |
MD5:5EC5B98F4C7BB4143844336FA6CFD079 | SHA256:C14E7BE00B58A2BB3F5C2244BC4578D4A580759180EF5C09A2AE0FE4A851A4DD | |||
| 2896 | CrazyBumpSetup122.exe | C:\Program Files\Crazybump\DevIL.NET.dll | executable | |
MD5:2C642572957CB4F7D57E23817E969598 | SHA256:710F2631CD560E626BF3757C43F1ED04019B812F0B11DBF644052A003FE77503 | |||
| 2896 | CrazyBumpSetup122.exe | C:\Users\admin\AppData\Local\CrazyBump\ball.x | text | |
MD5:F7FDC129C949BB37E01A31121C429A9A | SHA256:64FAE2F03529E8F2D14E2FB8C96ACA1EF29832079BB7881B6968BDF06CE731E6 | |||
| 2896 | CrazyBumpSetup122.exe | C:\Users\admin\AppData\Local\CrazyBump\cyl.x | text | |
MD5:FA7DC2D78F8B8B7248E3D176253C2B43 | SHA256:735B5046C8FC5A407C085530090FFB8FE0285AA98559CBAC75D7F479BC6EA788 | |||
| 2896 | CrazyBumpSetup122.exe | C:\Program Files\Crazybump\CrazyLib.dll | executable | |
MD5:8CEC6677B534F6B80BDCC401E6257784 | SHA256:8B019DB4B88D9C9524B41047A96071617F9B89334BF0F3A4A70EDDB9B8354E96 | |||
| 2896 | CrazyBumpSetup122.exe | C:\Users\admin\AppData\Local\Temp\nsiB4E5.tmp\splash.bmp | image | |
MD5:F1DA441BB3B2D922F5DFD17536BD66D7 | SHA256:EC0E4F62A050C9588E1E7F31D9FD59B04B312B2DF9F3419548182BC11C1D3BFC | |||
| 2896 | CrazyBumpSetup122.exe | C:\Program Files\Crazybump\PictureViewer.exe | executable | |
MD5:D129481CC46E22A251FB458649BF2CCE | SHA256:E586CD461A478D8DFE10BD43FDA72429957AB4FB12516798D64B95D4DE334D88 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2024 | CrazyBump.exe | GET | 404 | 64.90.42.96:80 | http://crazybump.com/beta/controlPage2 | US | html | 334 b | suspicious |
2024 | CrazyBump.exe | GET | 404 | 64.90.42.96:80 | http://crazybump.com/beta/upgrade/122.html | US | html | 338 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2024 | CrazyBump.exe | 64.90.42.96:80 | crazybump.com | New Dream Network, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crazybump.com |
| suspicious |
formmail.dreamhost.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2024 | CrazyBump.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent (MyAgent) |
2024 | CrazyBump.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent (MyAgent) |
Process | Message |
|---|---|
CrazyBump.exe |
%s------------------------------------------------
--- WinLicense Professional ---
--- (c)2010 Oreans Technologies ---
------------------------------------------------
|