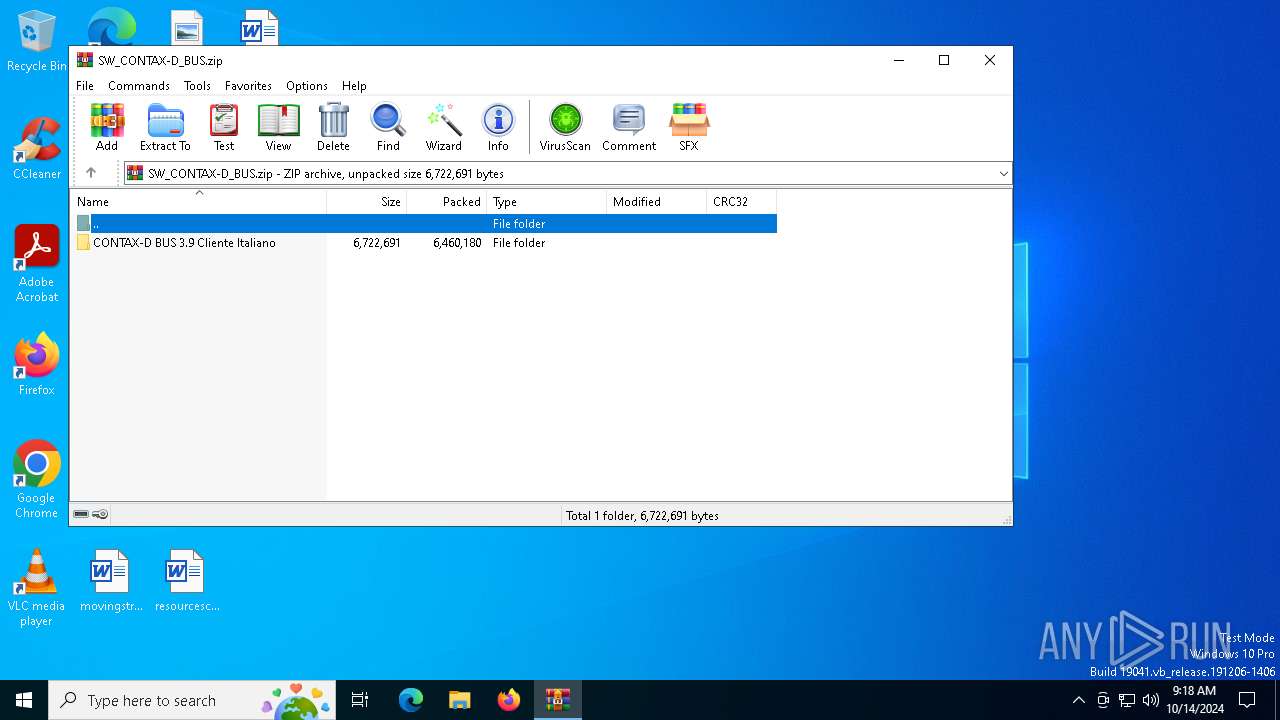
| File name: | SW_CONTAX-D_BUS.zip |
| Full analysis: | https://app.any.run/tasks/24a602b2-9d4e-43ac-8049-6f5f13a9e289 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2024, 09:18:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | C3394A17097FFD38EFD376D963A4AC78 |
| SHA1: | EB3E69E5AC77E134C2431CC0B67084E0CC921175 |
| SHA256: | B1779E466C157BB86B2FCA4A8F510889D12D6439146BBB3638D2A5AAA0297D4B |
| SSDEEP: | 98304:MSYA49dQp4V49sMyFIRU8wy5QRFYe1+zeYotaHLtWesisPZn8yJoZAxkQ9bvuy9H:FKkdYSwvBvd |
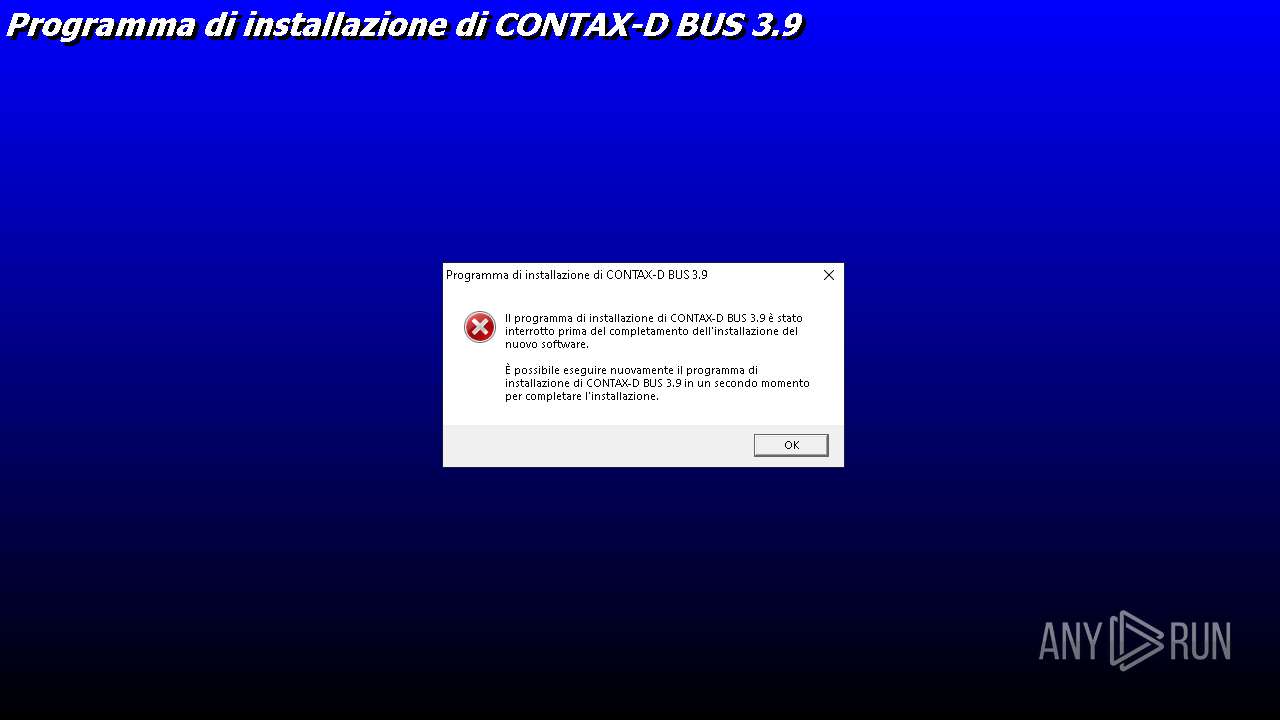
MALICIOUS
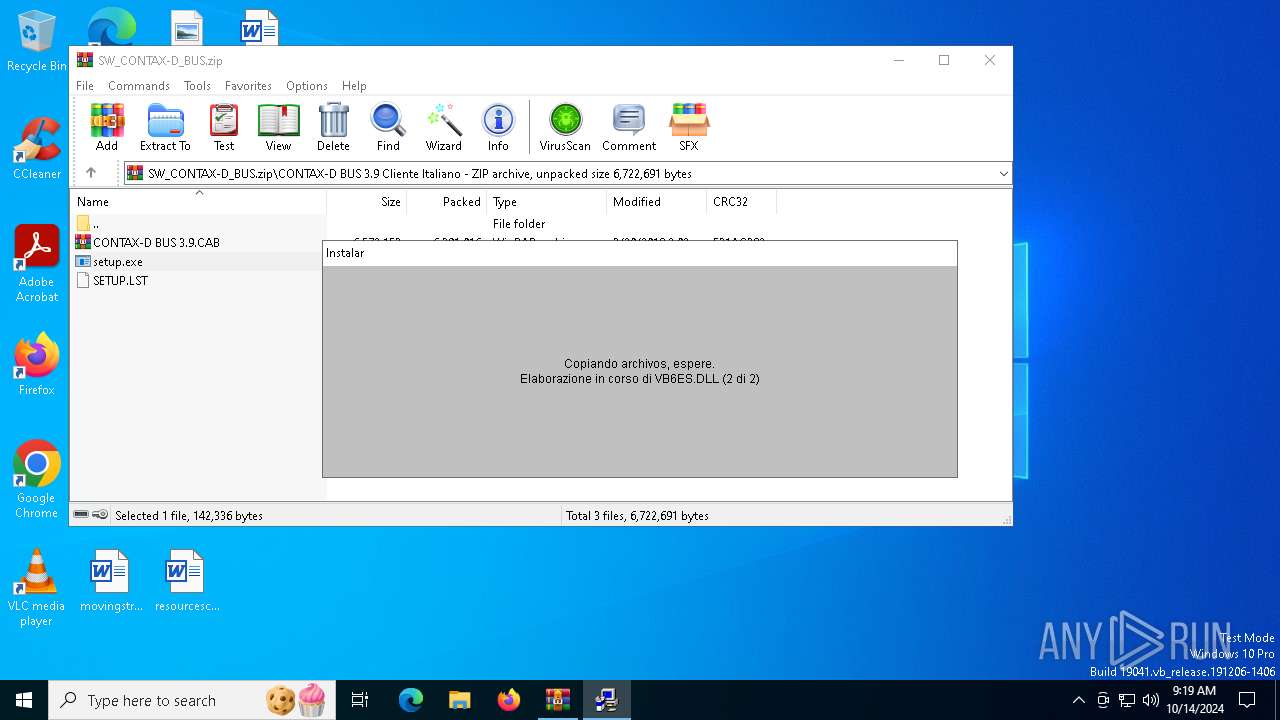
Generic archive extractor
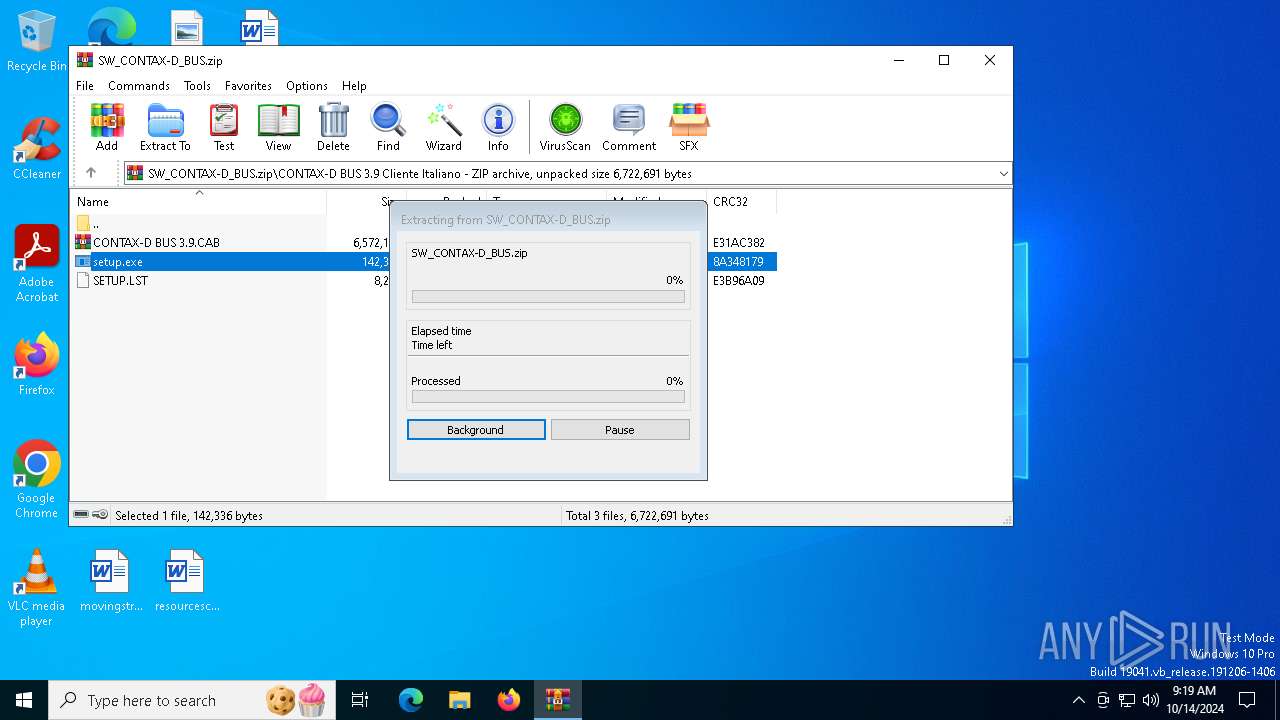
- WinRAR.exe (PID: 6696)
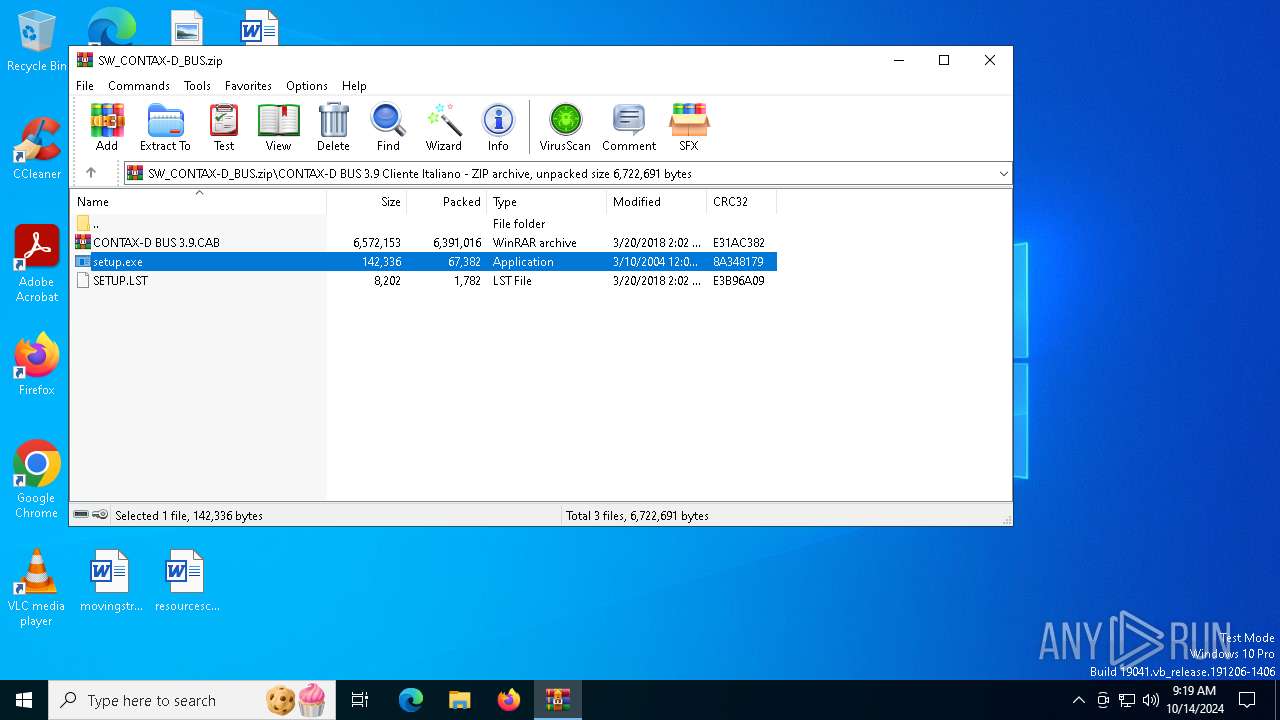
SUSPICIOUS
Starts a Microsoft application from unusual location
- setup.exe (PID: 3156)
- setup.exe (PID: 5356)
Process drops legitimate windows executable
- WinRAR.exe (PID: 6696)
- setup.exe (PID: 5356)
Executable content was dropped or overwritten
- setup.exe (PID: 5356)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:03:20 14:02:40 |
| ZipCRC: | 0xe31ac382 |
| ZipCompressedSize: | 6391016 |
| ZipUncompressedSize: | 6572153 |
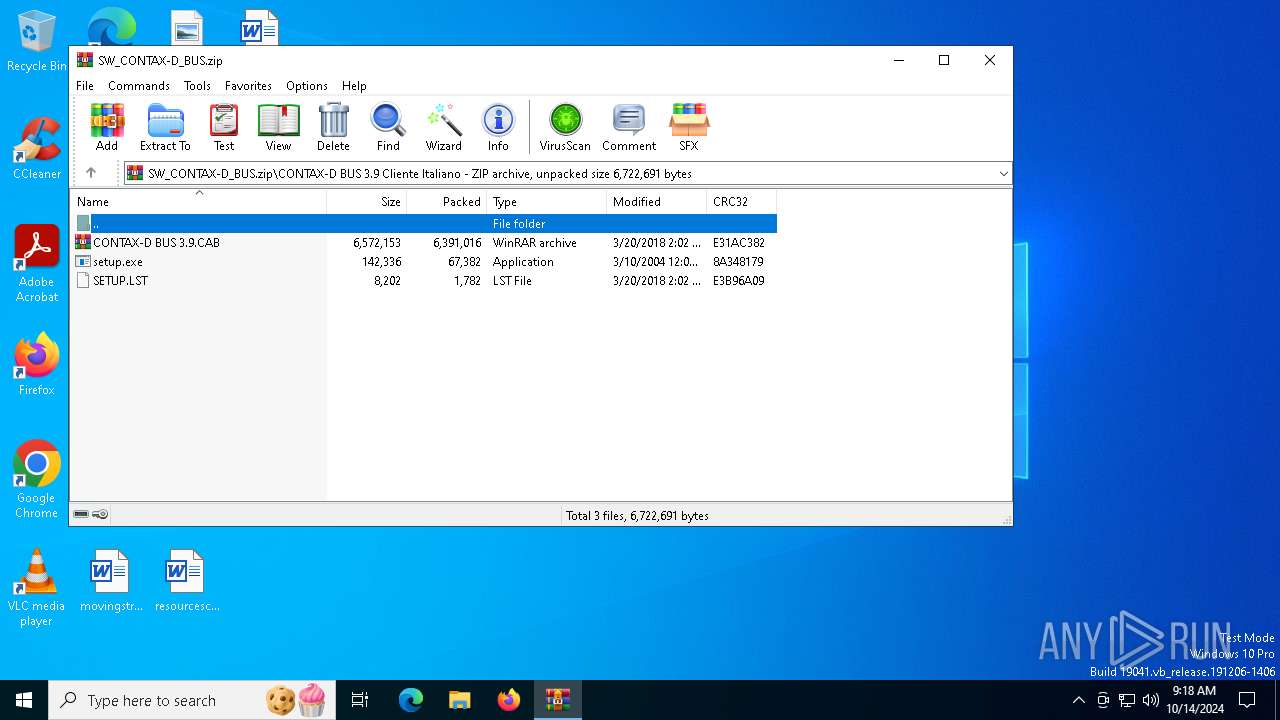
| ZipFileName: | CONTAX-D BUS 3.9 Cliente Italiano/CONTAX-D BUS 3.9.CAB |
Total processes
136
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2620 | C:\WINDOWS\Setup1.exe "C:\Users\admin\AppData\Local\Temp\Rar$EXa6696.35102\CONTAX-D BUS 3.9 Cliente Italiano\" "C:\WINDOWS\ST6UNST.000" "C:\WINDOWS\st6unst.exe" | C:\Windows\Setup1.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Kit di installazione Visual Basic 6.0 Exit code: 1 Version: 6.00.9782 Modules
| |||||||||||||||
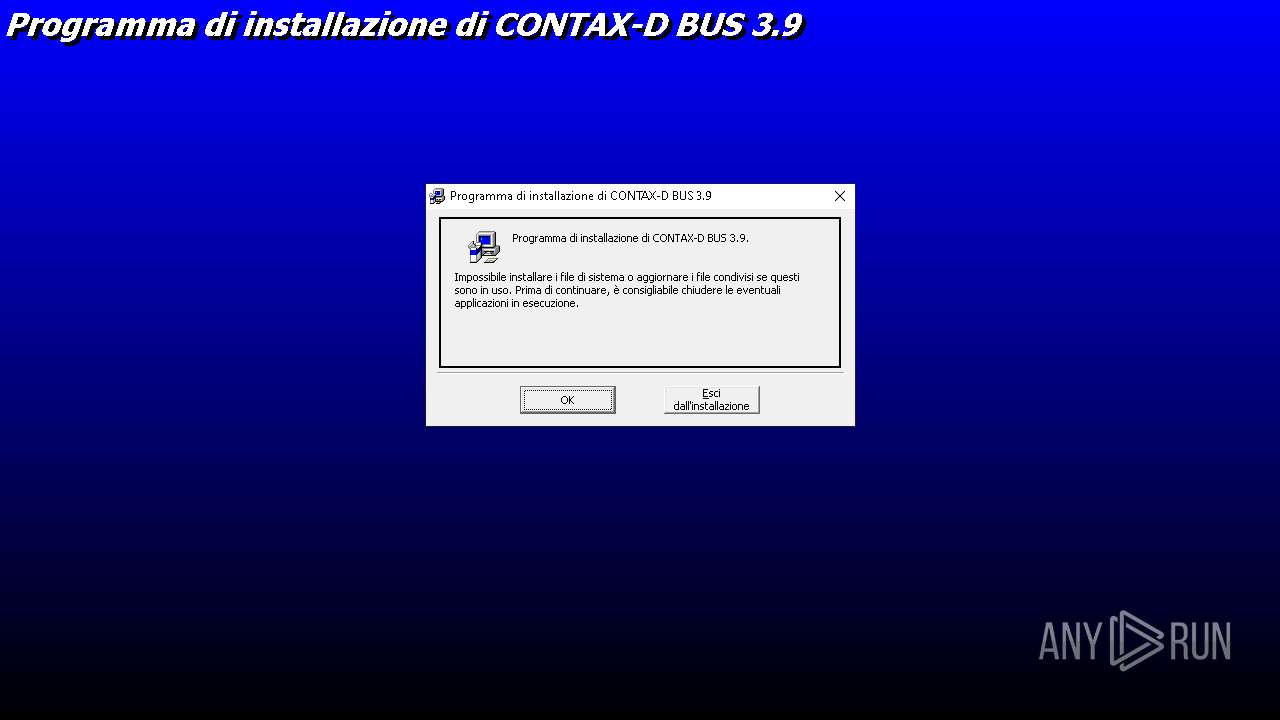
| 3156 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6696.35102\CONTAX-D BUS 3.9 Cliente Italiano\setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6696.35102\CONTAX-D BUS 3.9 Cliente Italiano\setup.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Bootstrap dell'installazione per il Kit di installazione di Visual Basic Exit code: 3221226540 Version: 6.00.9782 Modules
| |||||||||||||||
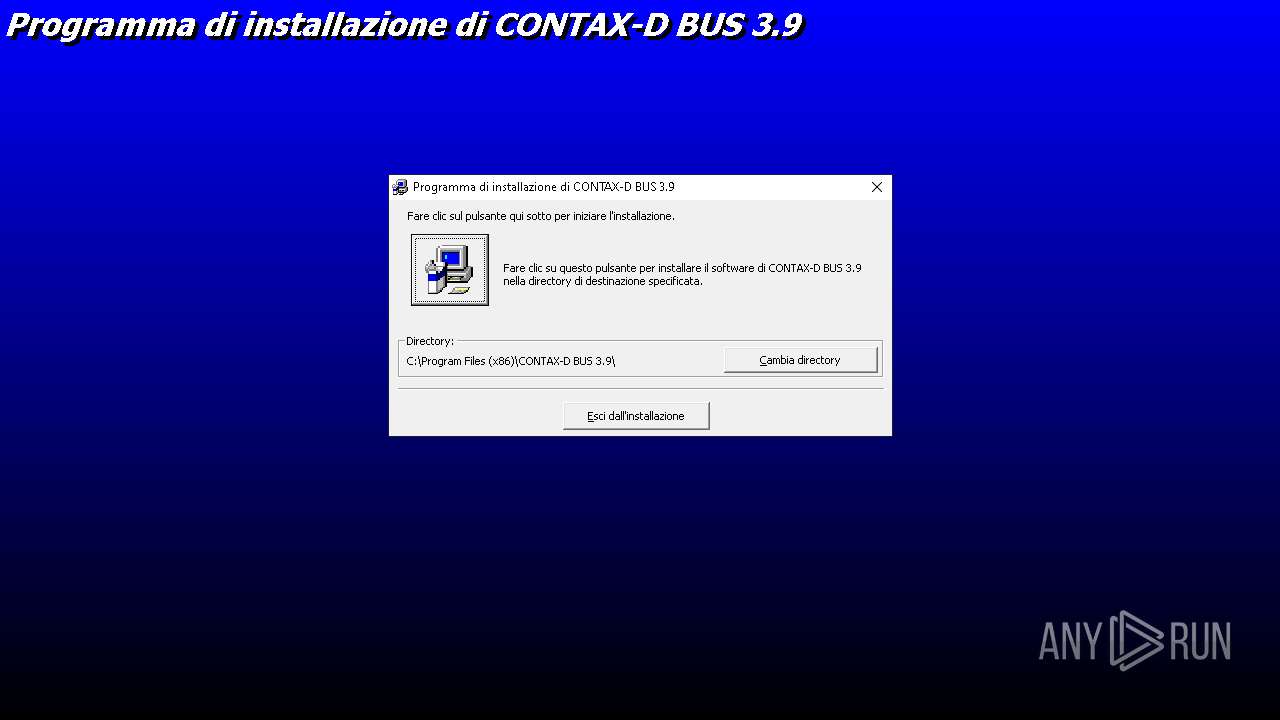
| 5356 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6696.35102\CONTAX-D BUS 3.9 Cliente Italiano\setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6696.35102\CONTAX-D BUS 3.9 Cliente Italiano\setup.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Bootstrap dell'installazione per il Kit di installazione di Visual Basic Exit code: 1 Version: 6.00.9782 Modules
| |||||||||||||||
| 6696 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\SW_CONTAX-D_BUS.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
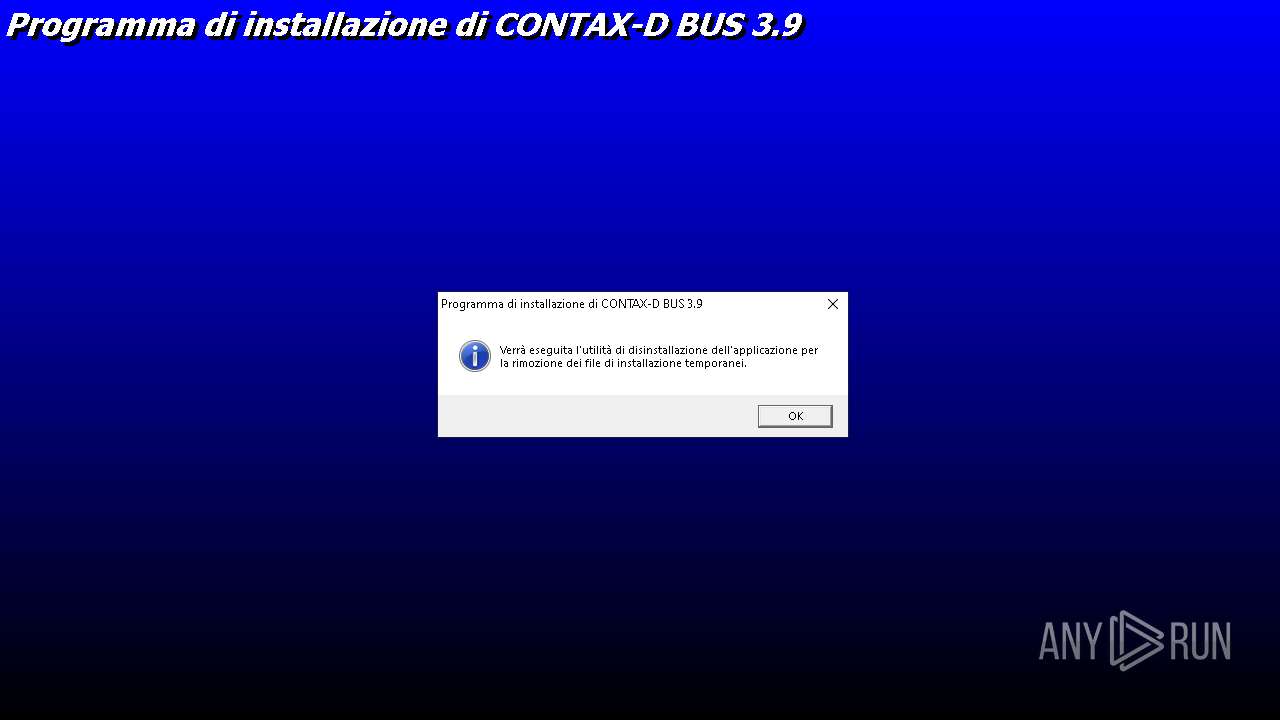
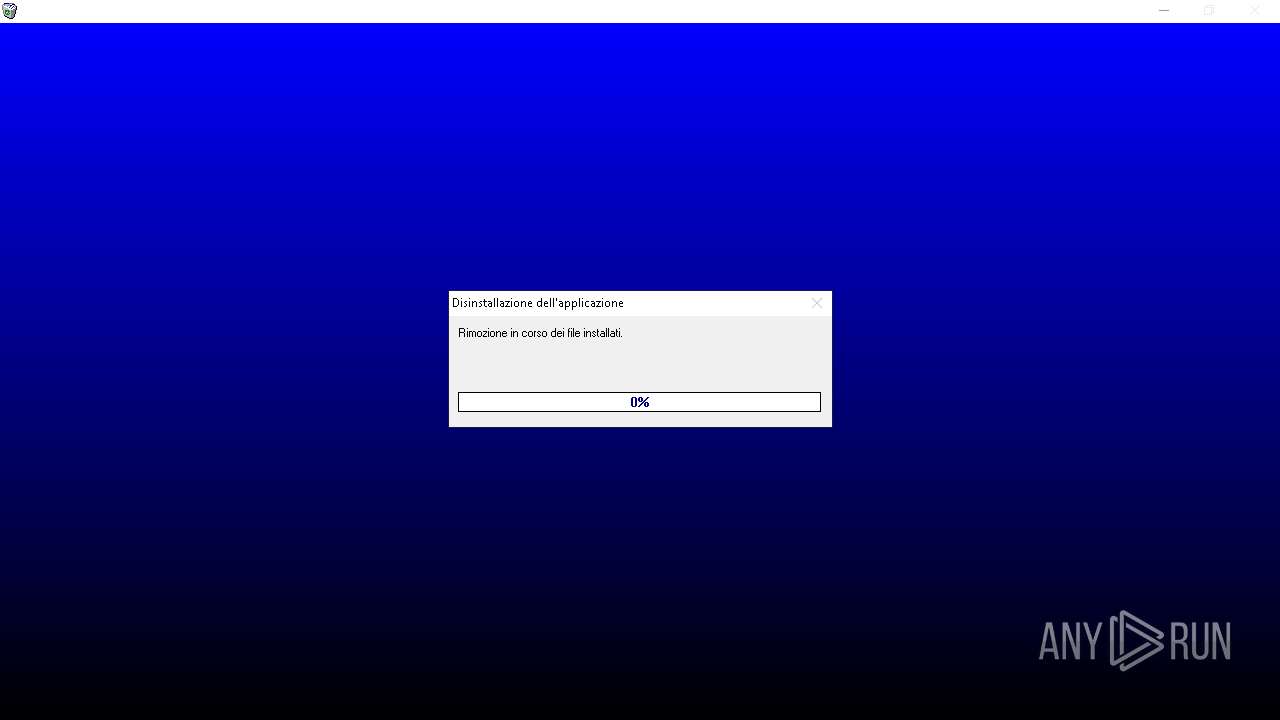
| 7084 | C:\WINDOWS\st6unst.exe -n "C:\Windows\ST6UNST.000" -e 3 -f -w 2620 | C:\Windows\ST6UNST.EXE | — | Setup1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Programma di disinstallazione del Kit di installazione di Visual Basic Version: 6.00.9782 Modules
| |||||||||||||||
Total events
2 502
Read events
2 457
Write events
45
Delete events
0
Modification events
| (PID) Process: | (6696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SW_CONTAX-D_BUS.zip | |||
| (PID) Process: | (6696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5356) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Windows\System32\VB6STKIT.DLL |
Value: 1 | |||
| (PID) Process: | (5356) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\WINDOWS\SYSTEM32\COMCAT.DLL |
Value: 2 | |||
| (PID) Process: | (5356) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Windows\System32\VB6ES.DLL |
Value: 1 | |||
| (PID) Process: | (5356) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\WINDOWS\SYSTEM32\STDOLE2.TLB |
Value: 2 | |||
Executable files
11
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6696.35102\CONTAX-D BUS 3.9 Cliente Italiano\CONTAX-D BUS 3.9.CAB | — | |
MD5:— | SHA256:— | |||
| 5356 | setup.exe | C:\Windows\CONTAX-D BUS 3.9.CAB | — | |
MD5:— | SHA256:— | |||
| 5356 | setup.exe | C:\Windows\ST6UNST.EXE | executable | |
MD5:4F0F514EC34D5090F1BC67E545B78DD2 | SHA256:455AF45C954A60F22A6D9D171981597A7D504E16F2D3864EDDE176C5D9FA0613 | |||
| 5356 | setup.exe | C:\Windows\SETUP.LST | ini | |
MD5:EC7CD5034EA40BABD67926EAF78BA058 | SHA256:A0F3BBE13A98CF736CD487DDD4984F49067A090F4D4284BCCADF61176A4B5271 | |||
| 5356 | setup.exe | C:\Windows\ST6UNST.000 | text | |
MD5:DD53897AEFB74ED121A0195C79C45A4C | SHA256:355DAF71577B9E3595CCF683DFE6A6C9020996C4D4860B693BEF756D7412479E | |||
| 5356 | setup.exe | C:\Users\admin\AppData\Local\Temp\msftqws.pdw\st6unst.exe | executable | |
MD5:4F0F514EC34D5090F1BC67E545B78DD2 | SHA256:455AF45C954A60F22A6D9D171981597A7D504E16F2D3864EDDE176C5D9FA0613 | |||
| 5356 | setup.exe | C:\Windows\temp.000 | executable | |
MD5:4F0F514EC34D5090F1BC67E545B78DD2 | SHA256:455AF45C954A60F22A6D9D171981597A7D504E16F2D3864EDDE176C5D9FA0613 | |||
| 6696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6696.35102\CONTAX-D BUS 3.9 Cliente Italiano\setup.exe | executable | |
MD5:073A1E6B956CE804A586F302CB1D1605 | SHA256:B3C2FE04ACB899B1A8CECDE3D5FF64BDB5AC94135A694D2E83FA75328AB6664D | |||
| 5356 | setup.exe | C:\Windows\SysWOW64\temp.000 | executable | |
MD5:87AA9155ACC202711F5720718E1DFFCB | SHA256:564747CFF8ABB9367F4D435BFADDB578AAB7E4CB4BF174F361D33846207540FE | |||
| 5356 | setup.exe | C:\Windows\SysWOW64\VB6STKIT.DLL | executable | |
MD5:87AA9155ACC202711F5720718E1DFFCB | SHA256:564747CFF8ABB9367F4D435BFADDB578AAB7E4CB4BF174F361D33846207540FE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
55
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3948 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5084 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4080 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4080 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7044 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4360 | SearchApp.exe | 184.86.251.18:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.32.238.112:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 104.79.89.142:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
816 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |