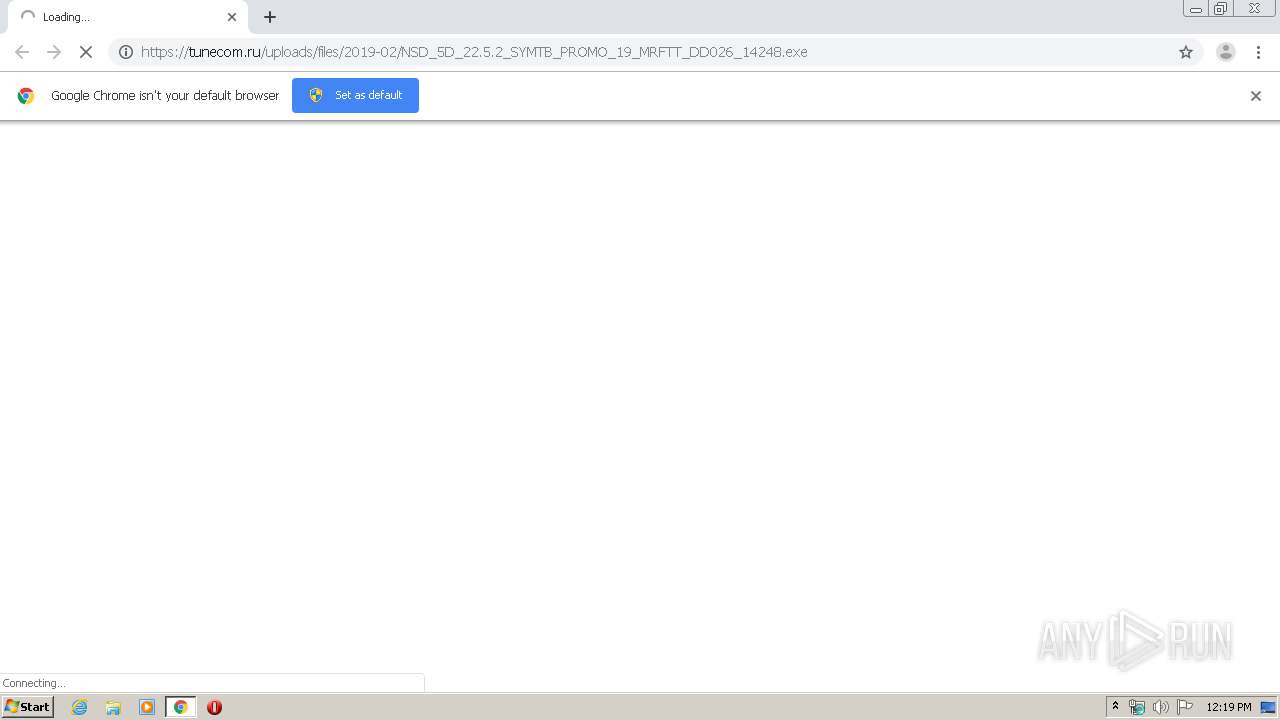
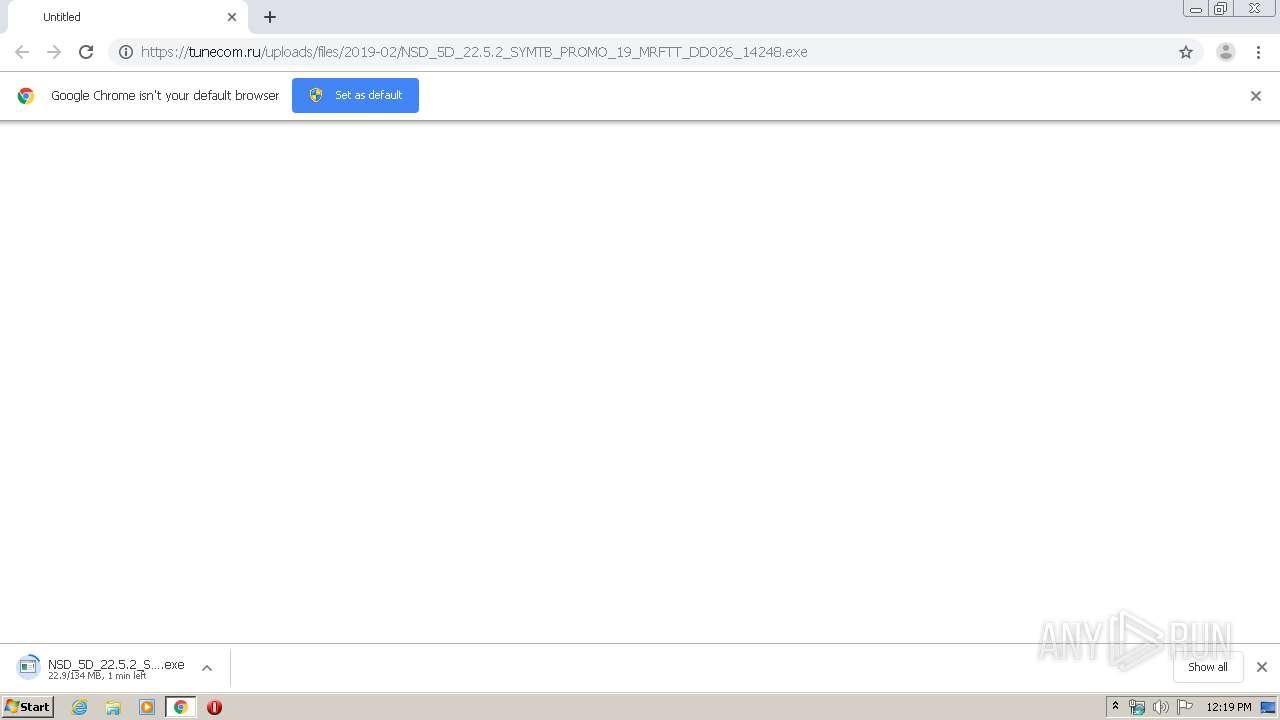
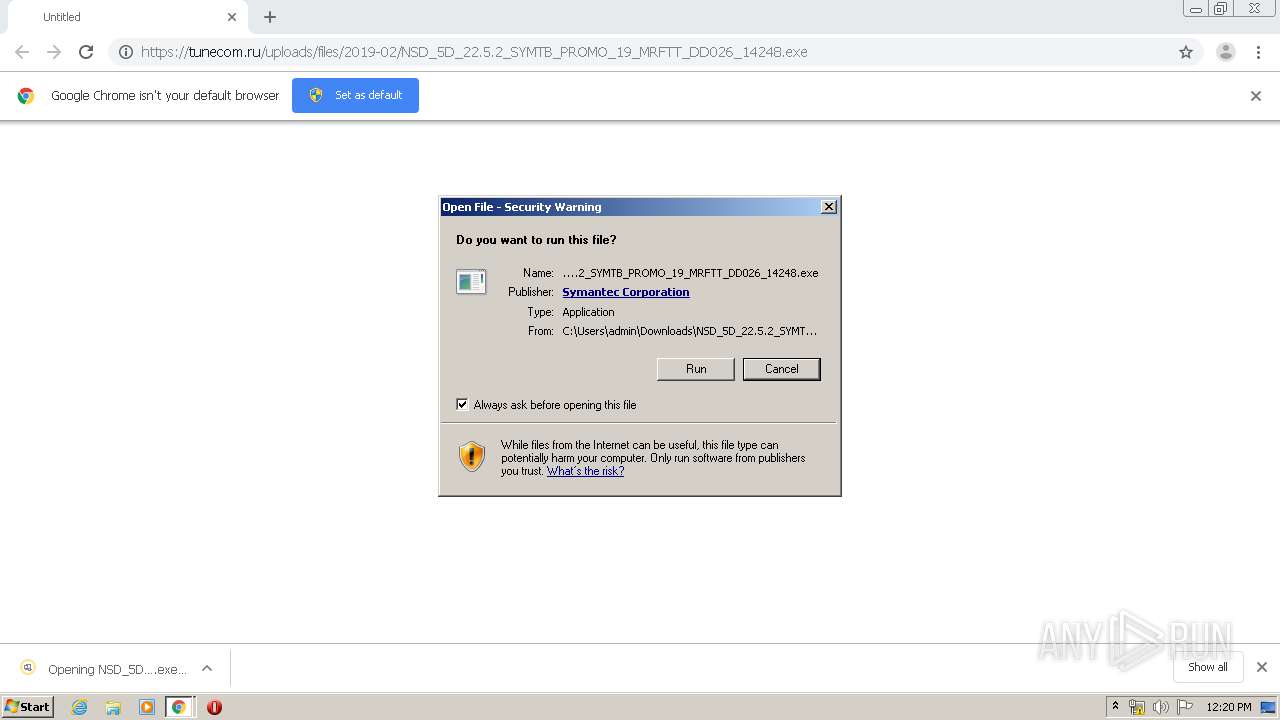
| URL: | https://tunecom.ru/uploads/files/2019-02/NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe |
| Full analysis: | https://app.any.run/tasks/3493971e-c1d2-497f-b65c-f2cd79a81630 |
| Verdict: | Malicious activity |
| Analysis date: | February 04, 2020, 12:18:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 777048EFDC9FA27F15A32C877C1D7FE8 |
| SHA1: | FFF8B3EB2A08B5D9E69954E60BB3442FB3825253 |
| SHA256: | B1664274888DE9CE3A251DF20698875F381C02BE09747ABFD6DACEACBDD35CE0 |
| SSDEEP: | 3:N8Y/XkfPfX0Rxb+sne3LD3CD6URfACn:2YMfP/0uXXCD6IfACn |
MALICIOUS
Changes the autorun value in the registry
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
Application was dropped or rewritten from another process
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3512)
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
- buIH.exe (PID: 3080)
- BHCA.exe (PID: 2356)
- Sevinst.exe (PID: 3928)
- coInst.exe (PID: 2580)
- coInst.exe (PID: 2944)
- cltLMH.exe (PID: 3608)
- InstCA.exe (PID: 3796)
- EFAInst.exe (PID: 2644)
- NS.exe (PID: 3720)
- NS.exe (PID: 3516)
- NSc.exe (PID: 2924)
- NSc.exe (PID: 3692)
- tuIH.exe (PID: 3880)
- RuleUp.exe (PID: 3048)
- SymIMIns.exe (PID: 2392)
- WSCStub.exe (PID: 3284)
- WSCStub.exe (PID: 3216)
- cltLMH.exe (PID: 2776)
- WSCStub.exe (PID: 3604)
- WSCStub.exe (PID: 3504)
- WSCStub.exe (PID: 2420)
- WSCStub.exe (PID: 2932)
- WSCStub.exe (PID: 2428)
Loads dropped or rewritten executable
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
- explorer.exe (PID: 372)
- SearchProtocolHost.exe (PID: 3548)
- buIH.exe (PID: 3080)
- coInst.exe (PID: 2580)
- coInst.exe (PID: 2944)
- EFAInst.exe (PID: 2644)
- RuleUp.exe (PID: 3048)
- SymIMIns.exe (PID: 2392)
- tuIH.exe (PID: 3880)
- InstCA.exe (PID: 3796)
- NS.exe (PID: 3720)
- NS.exe (PID: 3516)
- cltLMH.exe (PID: 3608)
- NSc.exe (PID: 2924)
- NSc.exe (PID: 3692)
- WSCStub.exe (PID: 3604)
- WSCStub.exe (PID: 3216)
- WSCStub.exe (PID: 3504)
- WSCStub.exe (PID: 3284)
- cltLMH.exe (PID: 2776)
- WSCStub.exe (PID: 2932)
- WSCStub.exe (PID: 2420)
- WSCStub.exe (PID: 2428)
- svchost.exe (PID: 860)
Changes settings of System certificates
- EFAInst.exe (PID: 2644)
- NS.exe (PID: 3720)
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
Loads the Task Scheduler COM API
- tuIH.exe (PID: 3880)
- NS.exe (PID: 3720)
- InstCA.exe (PID: 3796)
Loads the Task Scheduler DLL interface
- NS.exe (PID: 3516)
SUSPICIOUS
Application launched itself
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3512)
- NSc.exe (PID: 2924)
- NS.exe (PID: 3720)
Executable content was dropped or overwritten
- chrome.exe (PID: 3152)
- Sevinst.exe (PID: 3928)
- NS.exe (PID: 3720)
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
Creates a software uninstall entry
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
- Sevinst.exe (PID: 3928)
Creates files in the driver directory
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
- Sevinst.exe (PID: 3928)
Creates files in the Windows directory
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
- Sevinst.exe (PID: 3928)
- NS.exe (PID: 3720)
- svchost.exe (PID: 860)
Creates or modifies windows services
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
- NS.exe (PID: 3720)
Writes to a desktop.ini file (may be used to cloak folders)
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
Creates COM task schedule object
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
- NS.exe (PID: 3720)
Creates files in the program directory
- BHCA.exe (PID: 2356)
- buIH.exe (PID: 3080)
- EFAInst.exe (PID: 2644)
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
- Sevinst.exe (PID: 3928)
- SymIMIns.exe (PID: 2392)
- tuIH.exe (PID: 3880)
- RuleUp.exe (PID: 3048)
- InstCA.exe (PID: 3796)
- NS.exe (PID: 3516)
- NSc.exe (PID: 2924)
- cltLMH.exe (PID: 2776)
- NS.exe (PID: 3720)
Adds / modifies Windows certificates
- EFAInst.exe (PID: 2644)
- NS.exe (PID: 3720)
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
Executed as Windows Service
- NS.exe (PID: 3720)
Creates files in the user directory
- NS.exe (PID: 3516)
Low-level read access rights to disk partition
- cltLMH.exe (PID: 3608)
- NS.exe (PID: 3720)
Removes files from Windows directory
- NS.exe (PID: 3720)
INFO
Application launched itself
- chrome.exe (PID: 3152)
Reads the hosts file
- chrome.exe (PID: 3152)
- chrome.exe (PID: 1392)
- NS.exe (PID: 3720)
- NSc.exe (PID: 2924)
Reads Internet Cache Settings
- chrome.exe (PID: 3152)
Reads settings of System Certificates
- chrome.exe (PID: 1392)
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
- EFAInst.exe (PID: 2644)
- NS.exe (PID: 3720)
- explorer.exe (PID: 372)
Dropped object may contain Bitcoin addresses
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 2692)
Reads Microsoft Office registry keys
- NS.exe (PID: 3516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
39
Malicious processes
26
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3076 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16896908327748358704 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1746392300276854664 --mojo-platform-channel-handle=1540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Norton Security\Engine\22.5.4.24\BHCA.exe" /d /logdir "C:\ProgramData\NortonInstaller\Logs\2020-02-04-12h20m55s" | C:\Program Files\Norton Security\Engine\22.5.4.24\BHCA.exe | NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe | ||||||||||||
User: admin Company: Symantec Corporation Integrity Level: HIGH Description: BASH Custom Action Exit code: 0 Version: 5.0.0.24 Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Norton Security\Engine\22.5.4.24\SymIMIns.exe" /install | C:\Program Files\Norton Security\Engine\22.5.4.24\SymIMIns.exe | NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe | ||||||||||||
User: admin Company: Symantec Corporation Integrity Level: HIGH Description: SymIM Install Custom Action Executable Exit code: 0 Version: 15.1.0.70 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Norton Security\Engine\22.5.4.24\WSCStub.exe" | C:\Program Files\Norton Security\Engine\22.5.4.24\WSCStub.exe | — | NS.exe | |||||||||||
User: SYSTEM Company: Symantec Corporation Integrity Level: SYSTEM Description: WSCStub Exit code: 0 Version: 22.5.4.24 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14106872544350466770 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Norton Security\Engine\22.5.4.24\WSCStub.exe" | C:\Program Files\Norton Security\Engine\22.5.4.24\WSCStub.exe | — | NS.exe | |||||||||||
User: SYSTEM Company: Symantec Corporation Integrity Level: SYSTEM Description: WSCStub Exit code: 0 Version: 22.5.4.24 Modules
| |||||||||||||||
Total events
9 015
Read events
5 530
Write events
3 390
Delete events
95
Modification events
| (PID) Process: | (3152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3152-13225292348305750 |
Value: 259 | |||
| (PID) Process: | (3152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3152) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1 589
Suspicious files
446
Text files
312
Unknown types
98
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E39613C-C50.pma | — | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b839542e-b924-4eaa-9822-23ffe37fd39b.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa66c8d.TMP | text | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66c4f.TMP | text | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFa66ccc.TMP | text | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
37
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2776 | cltLMH.exe | GET | 200 | 40.112.194.94:80 | http://csasmain.symantec.com/228228131/0MYBX82AMJMd2/OGRVDYX9/iMBmvQEA/v/7j0cEKMU/CY9C8lBjh3bYDkIMTNCrJaPVHWSUXZO/323011679066709249984822051768396996202002&7E3DA3A8ECBE1F0E?NAM=VVNFUi1QQw==&MFN=REVMTA==&MFM=REVMTA==&OLA=ENG&OLO=USA | US | text | 1.90 Kb | unknown |
2692 | NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe | POST | 200 | 52.234.215.129:80 | http://stats.norton.com/n/p?module=9000&error=100&MID=E5A26C37-6D71-4D48-A546-8341350BC293&build=0E0E934A62F340CEA14110580997AC17&d=0&f=6.1.7601.1.0.0&g=E5A26C37-6D71-4D48-A546-8341350BC293&i=0&l=0&language=09.01&product=Norton%20Security&q=21362284&s=7B9C0F2D-7D2F-4FA4-BDA3-3282C4FE2AB6&t=0&u=00000003&upgrade=0&v=11.2.0.25&version=22.5.4.24&w=2&x=0&z=0&zzz=0e9d5e33296c61b61 | US | text | 13 b | whitelisted |
2924 | NSc.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2924 | NSc.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAm3ppIN5HLIYi%2ByfP1KmX4%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1392 | chrome.exe | 172.217.16.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1392 | chrome.exe | 172.217.19.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
1392 | chrome.exe | 172.217.16.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2692 | NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe | 52.234.215.129:80 | stats.norton.com | Microsoft Corporation | US | whitelisted |
3720 | NS.exe | 168.62.24.23:443 | shasta-rrs.symantec.com | Microsoft Corporation | US | unknown |
2924 | NSc.exe | 52.179.171.71:443 | cloudconnect2.norton.com | Microsoft Corporation | US | unknown |
2924 | NSc.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2924 | NSc.exe | 95.101.197.22:443 | static.nortoncdn.com | Akamai Technologies, Inc. | — | unknown |
2924 | NSc.exe | 172.217.19.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
2776 | cltLMH.exe | 40.112.194.94:80 | csasmain.symantec.com | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tunecom.ru |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
stats.qalabs.symantec.com |
| unknown |
stats.norton.com |
| unknown |
Threats
Process | Message |
|---|---|
BHCA.exe | 2020-02-04-12-21-45-383 : BHCA : 0x0934 : 0x0D48 : Information : wWinMain(98) : BHCA Version 5.0.0.24
|
BHCA.exe | 2020-02-04-12-21-45-383 : BHCA : 0x0934 : 0x0D48 : Information : ccVerifyTrust::CVerifyTrustImpl::Create(75) : bLoadTrustPolicy = 0
|
BHCA.exe | 2020-02-04-12-21-45-383 : BHCA : 0x0934 : 0x0D48 : Information : wWinMain(93) : BHCA starting...
|
BHCA.exe | 2020-02-04-12-21-45-399 : BHCA : 0x0934 : 0x0D48 : Information : ccVerifyTrust::CVerifyFile::Create(132) : WTPF_TESTCANBEVALID flag is not set.
|
BHCA.exe | 2020-02-04-12-21-45-399 : BHCA : 0x0934 : 0x0D48 : Warning : CPrivilege::GrantThread() : GetLastError() == ERROR_NO_TOKEN
|
BHCA.exe | 2020-02-04-12-21-45-399 : BHCA : 0x0934 : 0x0D48 : Information : ccVerifyTrust::CVerifyFile::Create(136) : WTPF_OFFLINEOKNBU_IND flag is set.
|
BHCA.exe | 2020-02-04-12-21-45-399 : BHCA : 0x0934 : 0x0D48 : Information : ccVerifyTrust::CVerifyFile::Create(131) : WTPF_TRUSTTEST flag is not set.
|
BHCA.exe | 2020-02-04-12-21-45-399 : BHCA : 0x0934 : 0x0D48 : Information : ccVerifyTrust::CVerifyFile::Create(134) : WTPF_IGNOREREVOKATION flag is set.
|
BHCA.exe | 2020-02-04-12-21-45-399 : BHCA : 0x0934 : 0x0D48 : Information : ccVerifyTrust::CVerifyFile::Create(137) : WTPF_OFFLINEOKNBU_COM flag is set.
|
BHCA.exe | 2020-02-04-12-21-45-399 : BHCA : 0x0934 : 0x0D48 : Information : ccVerifyTrust::CVerifyFile::Create(136) : WTPF_OFFLINEOKNBU_IND flag is set.
|