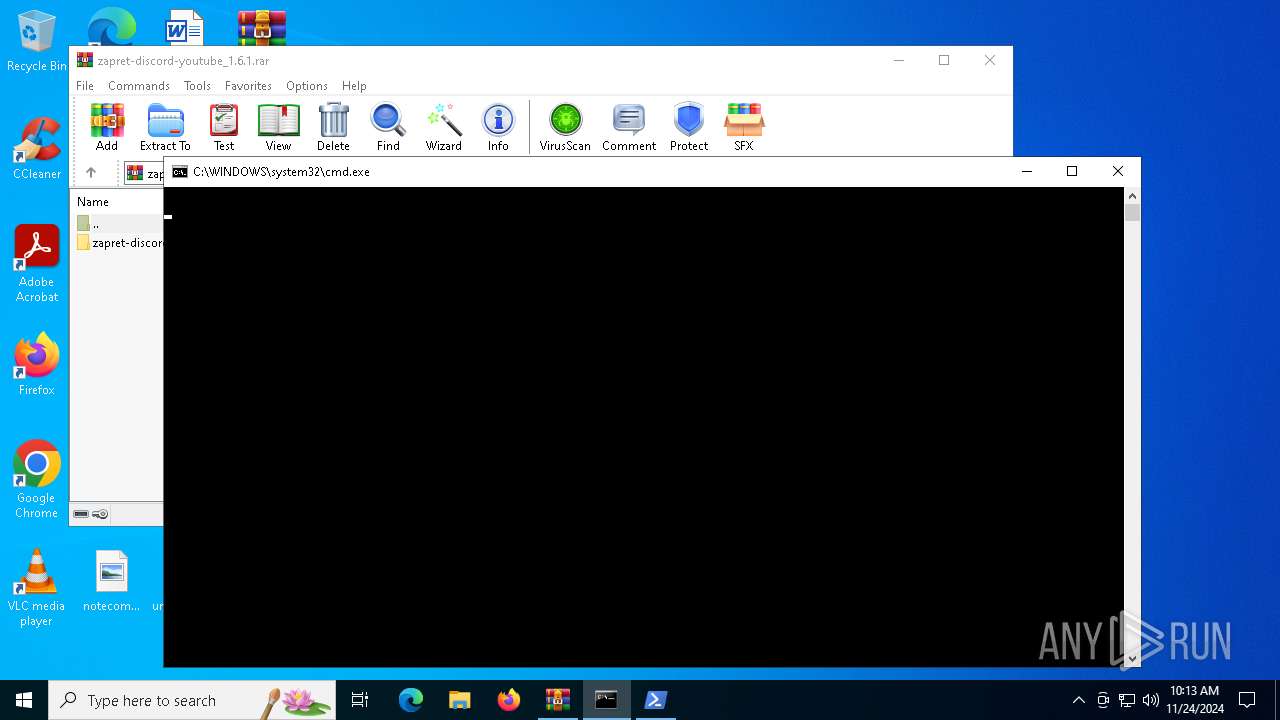
| File name: | zapret-discord-youtube_1.6.1.rar |
| Full analysis: | https://app.any.run/tasks/b634f036-e788-4b27-a854-8d0f71f8479b |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2024, 10:13:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | CC512374A9C3A2B3F4DD18A5BB9BB37D |
| SHA1: | 83F3C97F9AFC66ED1A2D27D04A6356FB448CDCA5 |
| SHA256: | B16350F65628FE98BE286F6CC2D0F1C94686DD9FB84A099F6B2348F1A28127DB |
| SSDEEP: | 393216:eiSK0YZzcgtmO9xVrZEDy0YZzcgtmO9xVrZEDa:5J0YGgtdP6Dy0YGgtdP6Da |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5096)
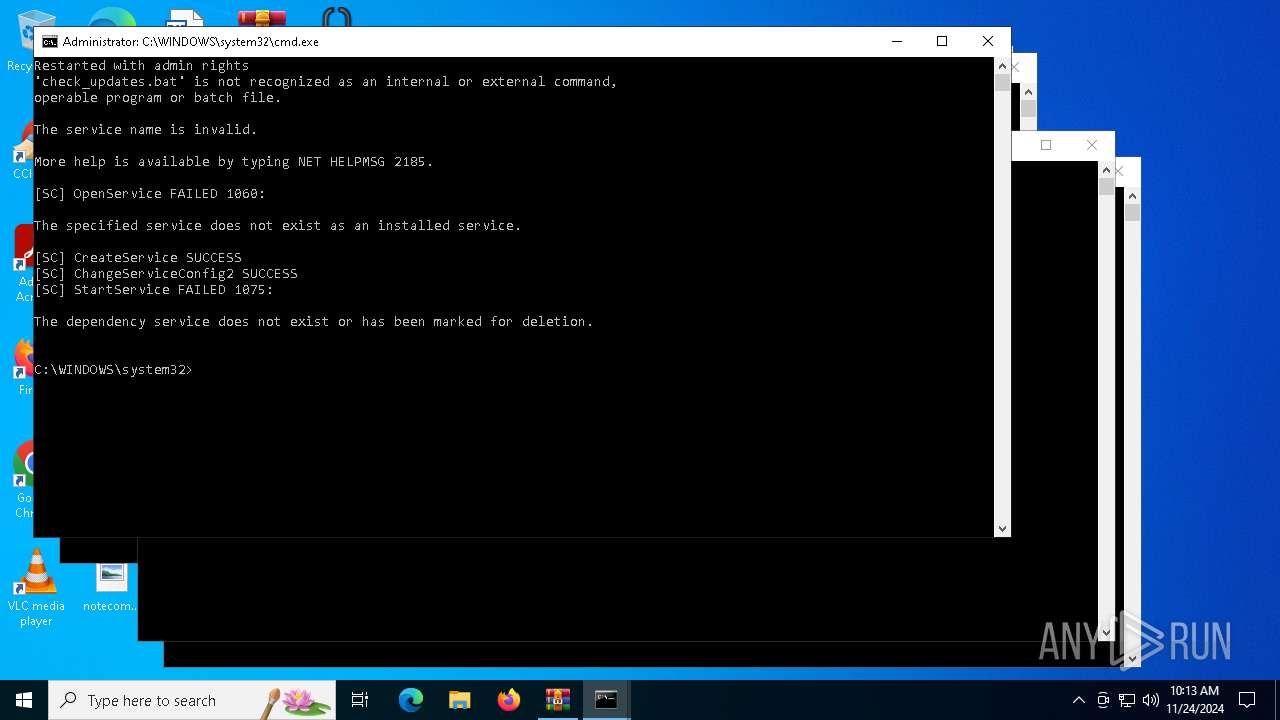
Starts NET.EXE for service management
- net.exe (PID: 6936)
- net.exe (PID: 7084)
- net.exe (PID: 3260)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 6208)
- net.exe (PID: 6432)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5532)
- cmd.exe (PID: 5788)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 6320)
- cmd.exe (PID: 3188)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 6168)
Starts process via Powershell
- powershell.exe (PID: 5964)
- powershell.exe (PID: 1704)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 6412)
- powershell.exe (PID: 6884)
- powershell.exe (PID: 6684)
- powershell.exe (PID: 6852)
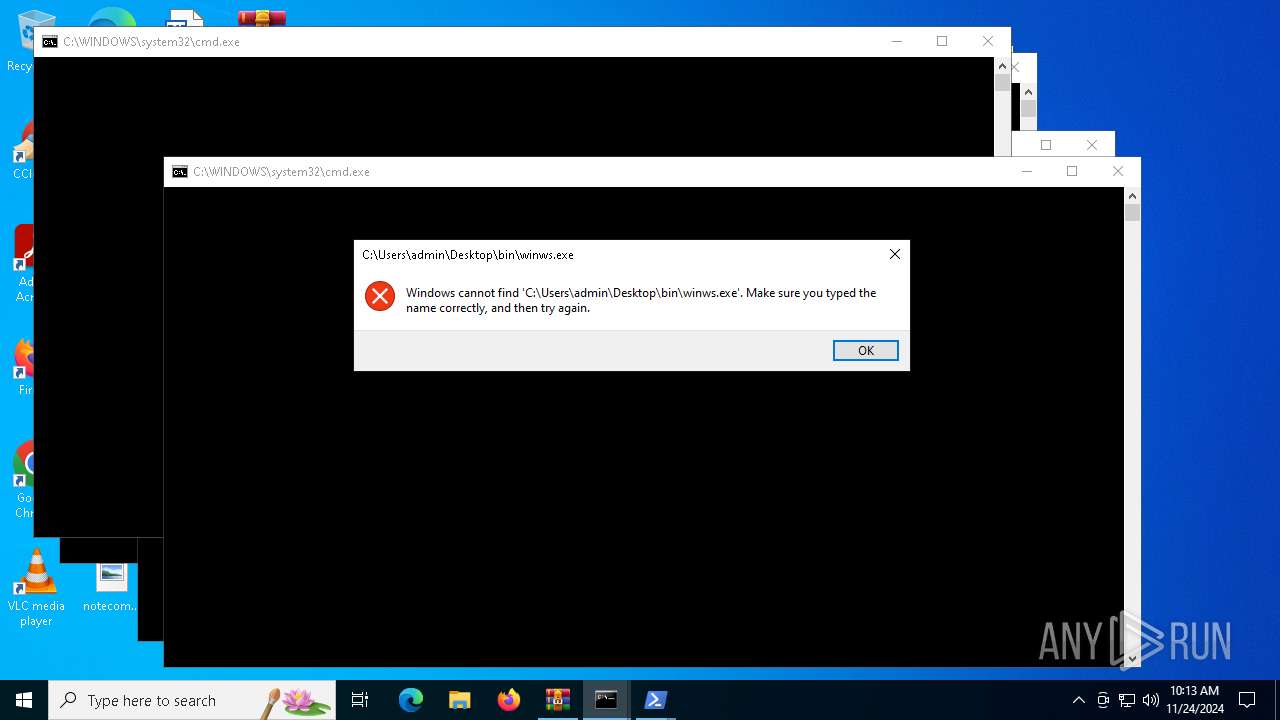
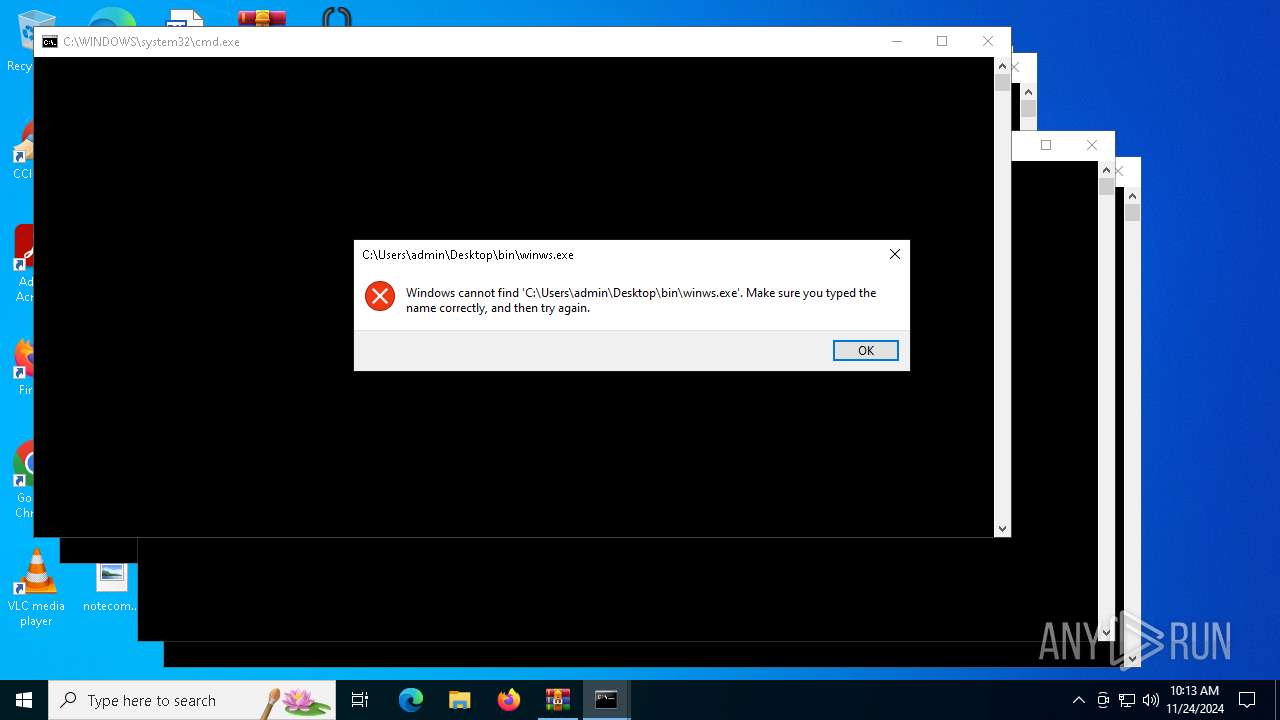
Starts application with an unusual extension
- cmd.exe (PID: 5532)
- cmd.exe (PID: 5788)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 6320)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 3188)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 6208)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5788)
- cmd.exe (PID: 5532)
- cmd.exe (PID: 6320)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 6168)
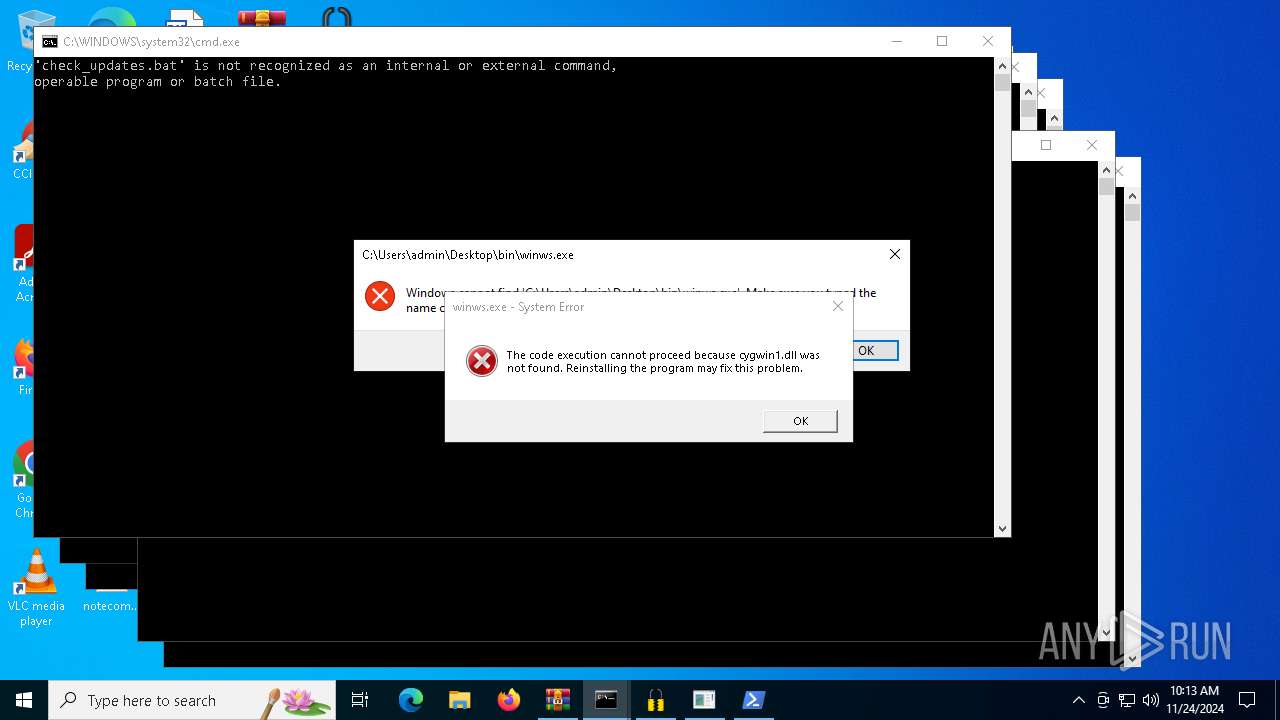
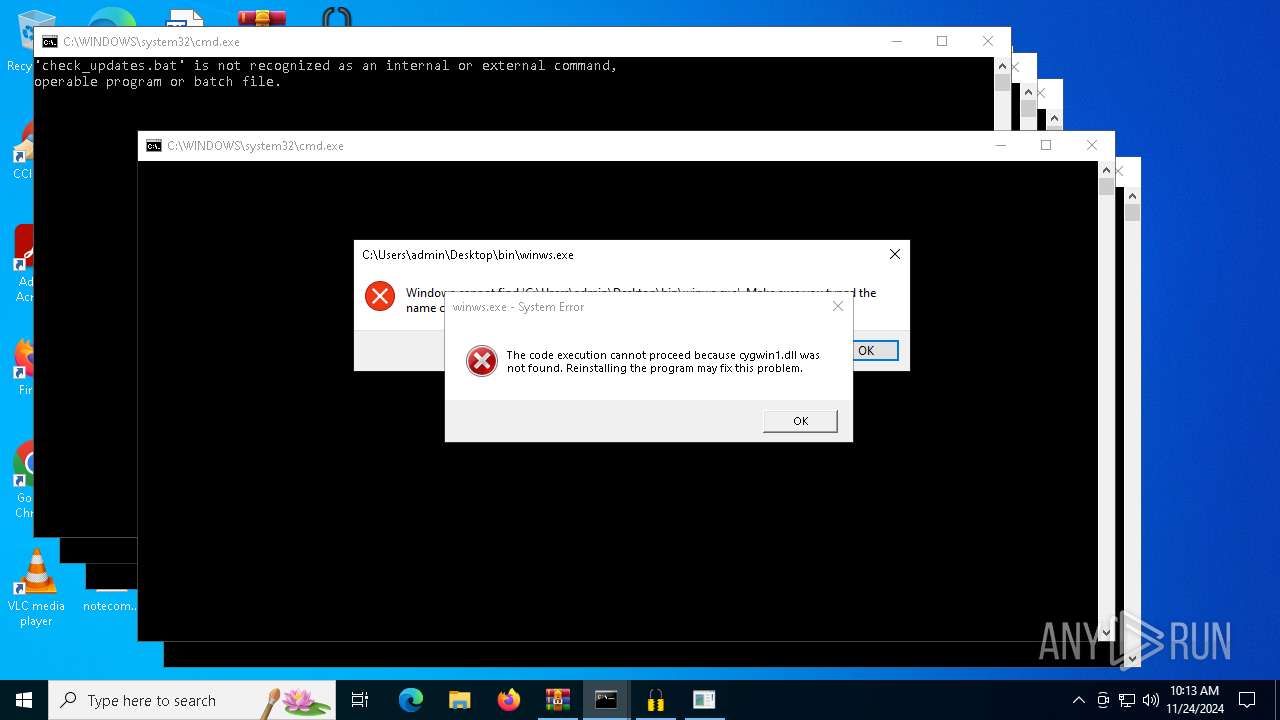
Executing commands from a ".bat" file
- powershell.exe (PID: 6212)
- powershell.exe (PID: 6684)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6212)
- powershell.exe (PID: 6684)
Starts SC.EXE for service management
- cmd.exe (PID: 6712)
- cmd.exe (PID: 6208)
INFO
Checks supported languages
- chcp.com (PID: 5092)
- chcp.com (PID: 2736)
- chcp.com (PID: 6196)
- chcp.com (PID: 6396)
- chcp.com (PID: 6832)
- chcp.com (PID: 6864)
- chcp.com (PID: 848)
- chcp.com (PID: 6772)
- chcp.com (PID: 2728)
- chcp.com (PID: 6404)
Manual execution by a user
- cmd.exe (PID: 5532)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 5788)
- cmd.exe (PID: 6320)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 3188)
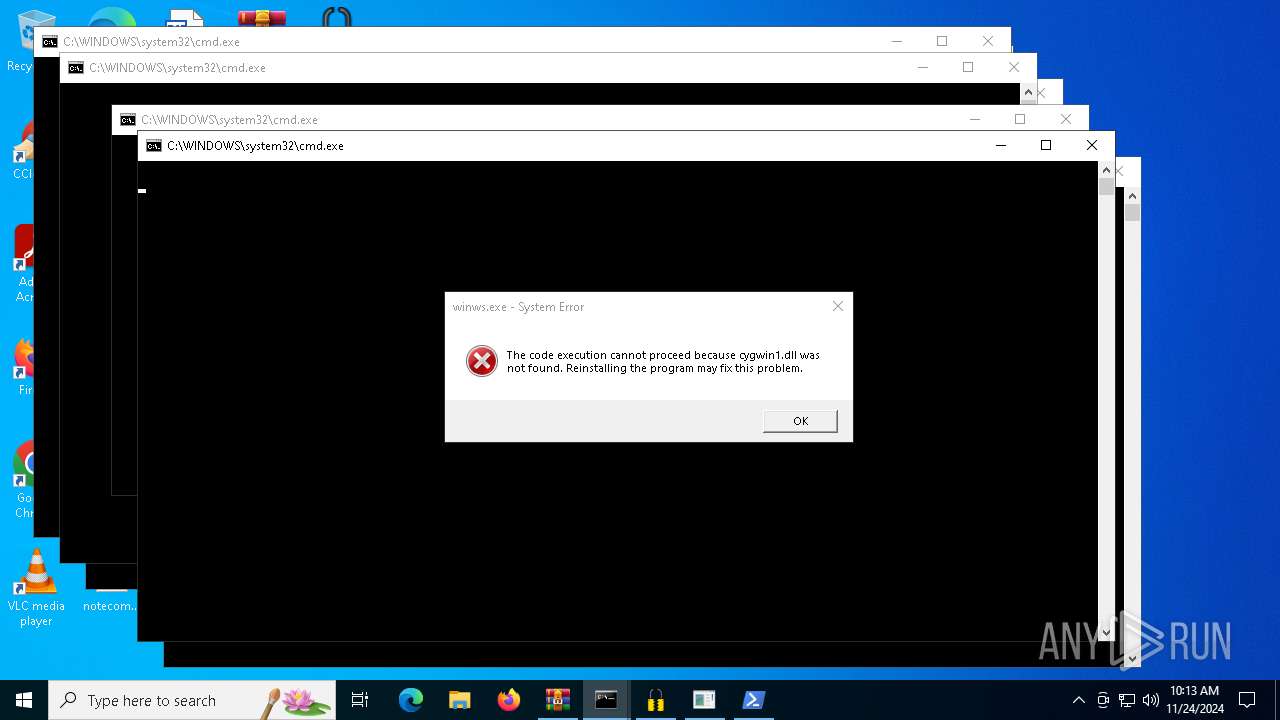
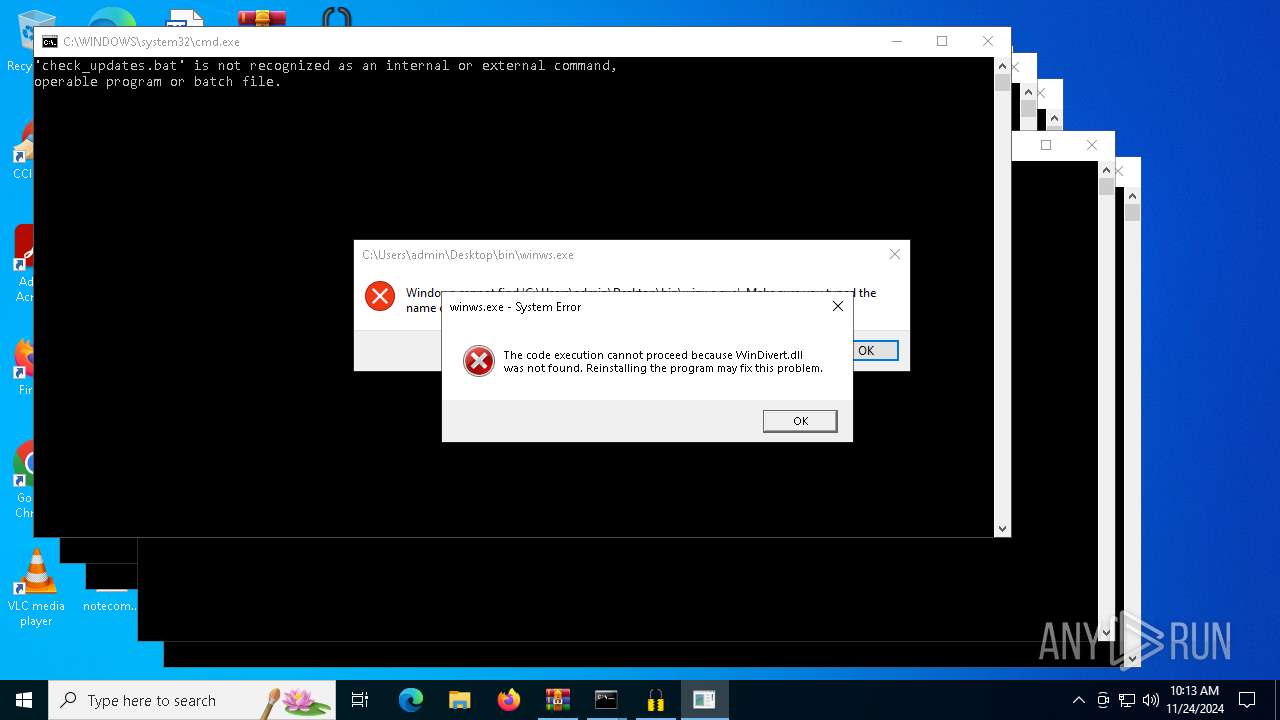
- winws.exe (PID: 4708)
- winws.exe (PID: 2076)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 6464)
Changes the display of characters in the console
- cmd.exe (PID: 5788)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 5532)
- cmd.exe (PID: 6320)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 3188)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 6208)
- cmd.exe (PID: 6464)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5964)
- powershell.exe (PID: 1704)
- powershell.exe (PID: 6412)
- powershell.exe (PID: 6884)
- powershell.exe (PID: 6852)
The process uses the downloaded file
- powershell.exe (PID: 6212)
- powershell.exe (PID: 6684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 981657 |
| UncompressedSize: | 1022005 |
| OperatingSystem: | Win32 |
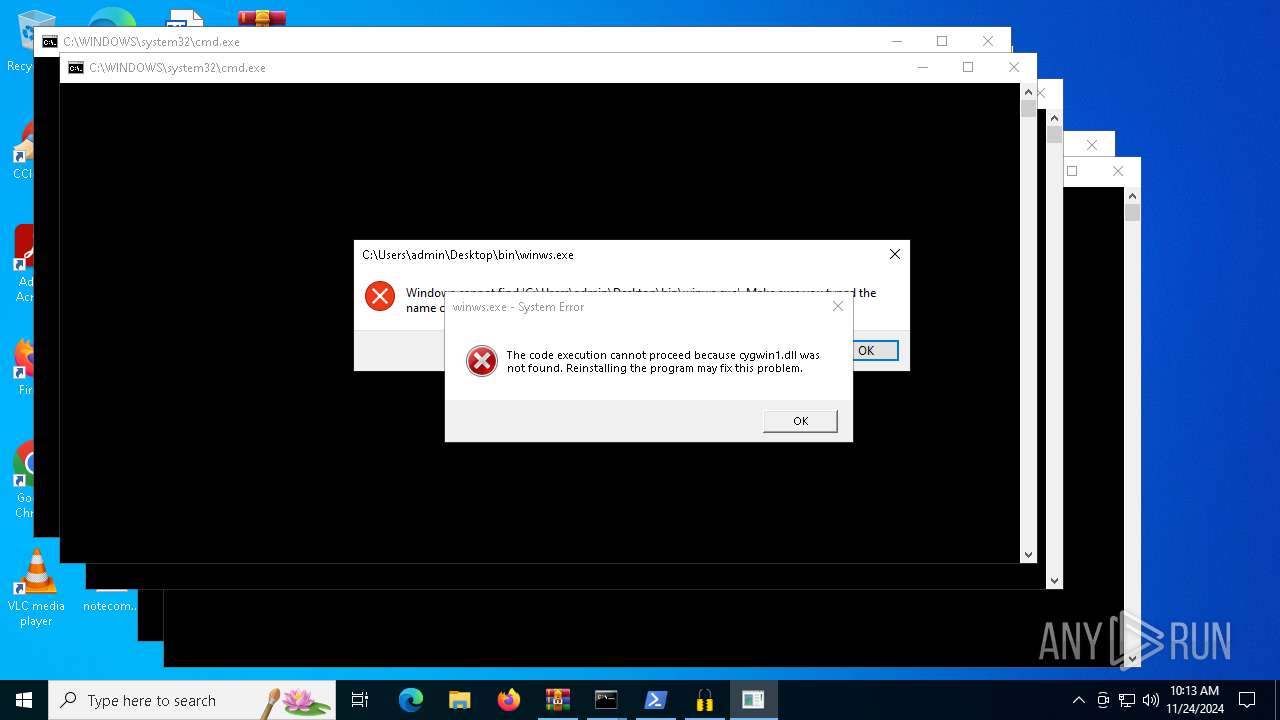
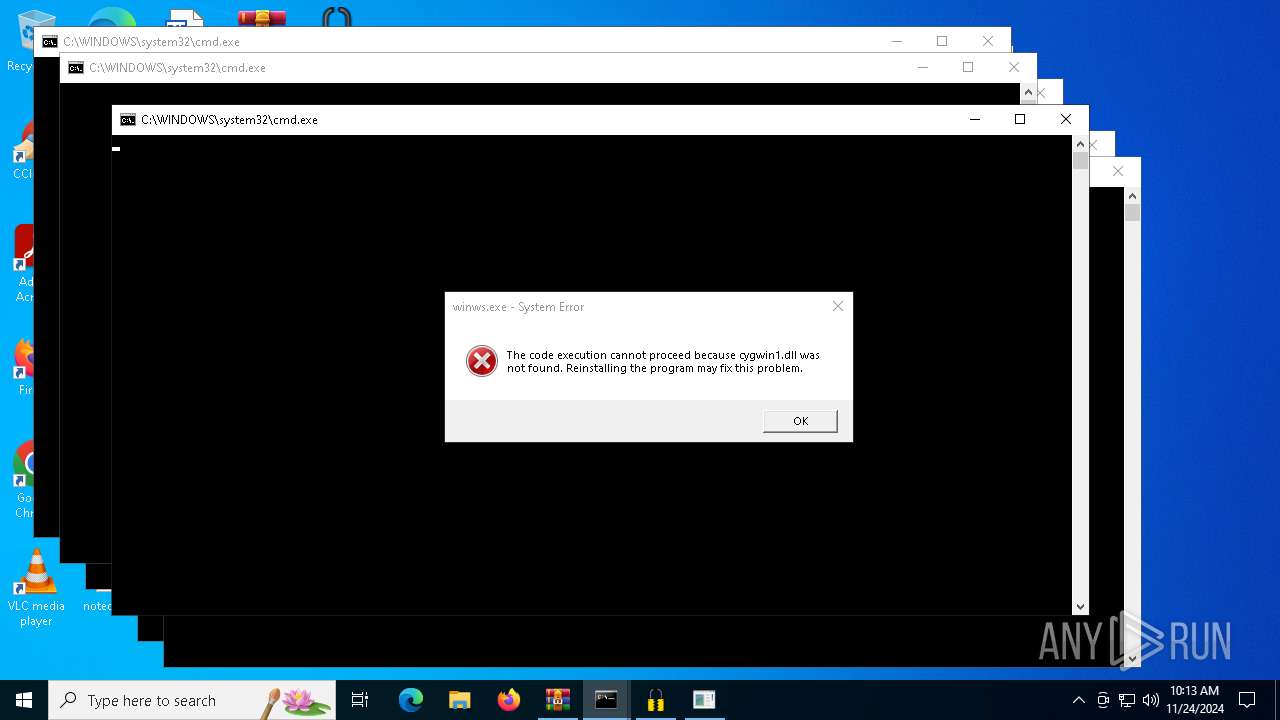
| ArchivedFileName: | zapret-discord-youtube_1.6.1/bin/cygwin1.dll |
Total processes
188
Monitored processes
66
Malicious processes
6
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1704 | powershell -Command "Start-Process 'C:\Users\admin\Desktop\bin\' -Verb RunAs" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\Desktop\winws.exe" | C:\Users\admin\Desktop\winws.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225781 Modules
| |||||||||||||||
| 2380 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2728 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2736 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2744 | sc delete zapret | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2996 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | winws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
32 218
Read events
32 210
Write events
8
Delete events
0
Modification events
| (PID) Process: | (5096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\zapret-discord-youtube_1.6.1.rar | |||
| (PID) Process: | (5096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
16
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1704 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1374b6.TMP | binary | |
MD5:016BF5CAD7C4125EFDD48626AFEBB580 | SHA256:7B5BC41794491CA4852204DDC3DC27214C7D1EB98996E553544EF96F51142CE9 | |||
| 5964 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:016BF5CAD7C4125EFDD48626AFEBB580 | SHA256:7B5BC41794491CA4852204DDC3DC27214C7D1EB98996E553544EF96F51142CE9 | |||
| 6412 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:ABC51238A994CFD0CA1484DA33725430 | SHA256:A5B995985D79961453713650E2C8AE70721F7615873682271B21DDEE783A78AB | |||
| 5964 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1370ce.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6884 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZLM2Z8BFPUOAYSTD343N.temp | binary | |
MD5:6C3A14FD4CEDEC09AEEBA301985F7316 | SHA256:A022ECEC9B3AD09B67EC5C30985A85358D9ABD92DF81289C3B5482C407F7692D | |||
| 1704 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:05350E79CF9E3DE51BB7ADBE3BCA5251 | SHA256:722215264636CC0F844E7E48F877806A2B761A31E1F279E286B48B3180716B48 | |||
| 6412 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_izjydwfs.4pw.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5964 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\54XLTJBJGSWCBCF074S9.temp | binary | |
MD5:016BF5CAD7C4125EFDD48626AFEBB580 | SHA256:7B5BC41794491CA4852204DDC3DC27214C7D1EB98996E553544EF96F51142CE9 | |||
| 6884 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF13835c.TMP | binary | |
MD5:ABC51238A994CFD0CA1484DA33725430 | SHA256:A5B995985D79961453713650E2C8AE70721F7615873682271B21DDEE783A78AB | |||
| 6212 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4qvsgyrc.kdb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
21
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5988 | RUXIMICS.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5892 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5892 | svchost.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5988 | RUXIMICS.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5892 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.106.196:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5988 | RUXIMICS.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5892 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5988 | RUXIMICS.exe | 23.200.189.225:80 | www.microsoft.com | Moratelindo Internet Exchange Point | ID | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |