| download: | lj1488en.exe |
| Full analysis: | https://app.any.run/tasks/98528711-b656-4689-95e5-b0ffee80bdb8 |
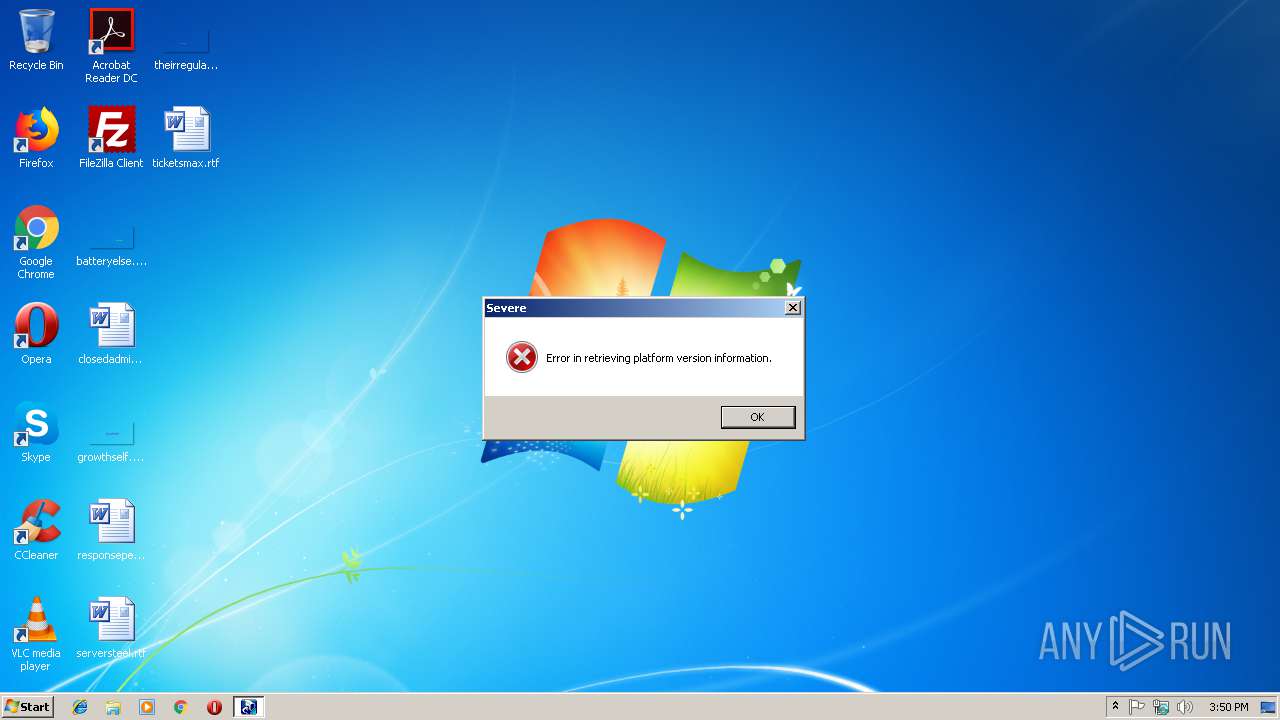
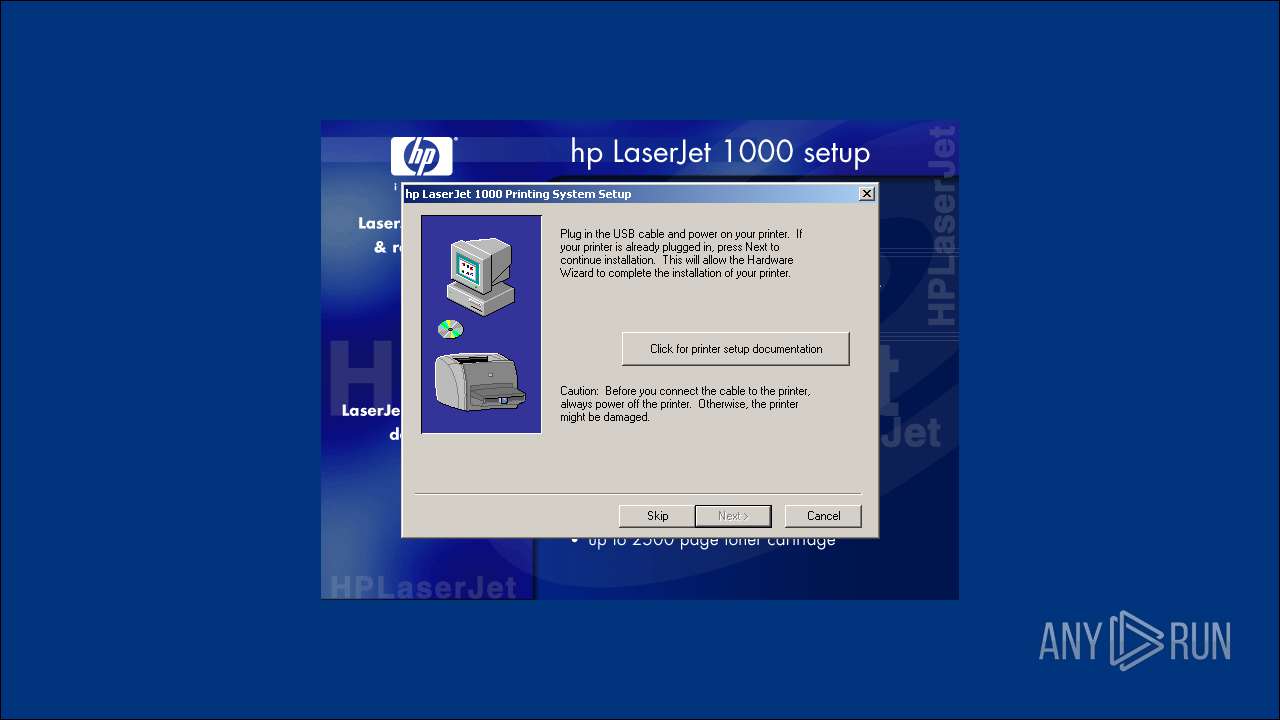
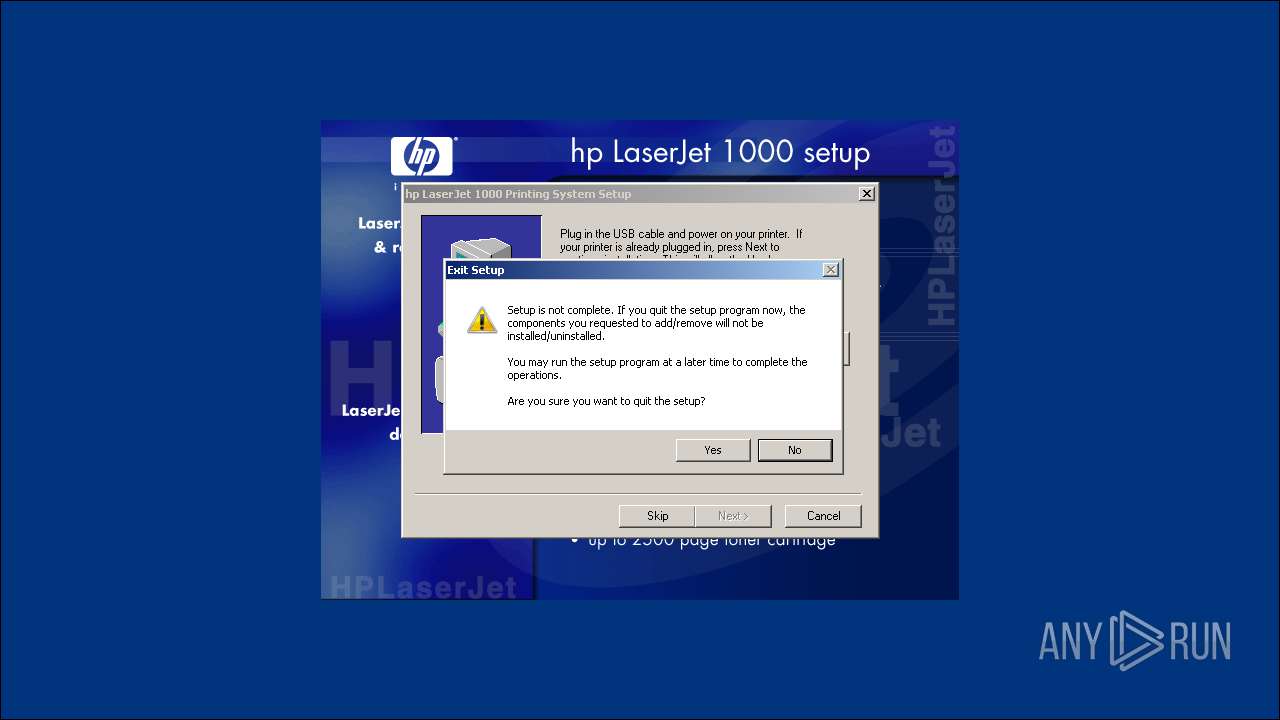
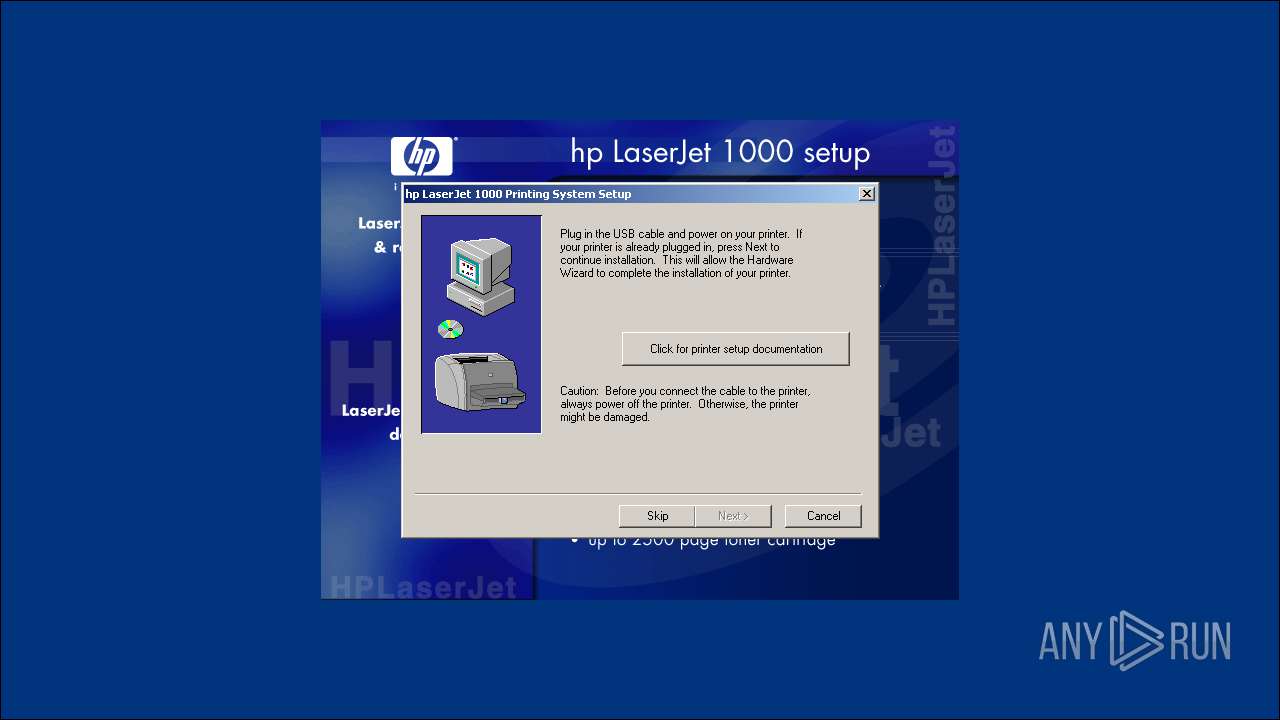
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2019, 15:50:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | 412643BEE7EECFAF5E1A303E26DDF3F9 |
| SHA1: | 94A3315BD1BCB4888B39286258C636CEE92E32DA |
| SHA256: | B162C2D70BB49D52F47437A4DC8BFBCB89EF33284503E997323114F712584A9E |
| SSDEEP: | 393216:tX6OIZbbdo2aKMVzVgeiLnDKZ3aatj//mx:tX8Vp965gFGph//e |
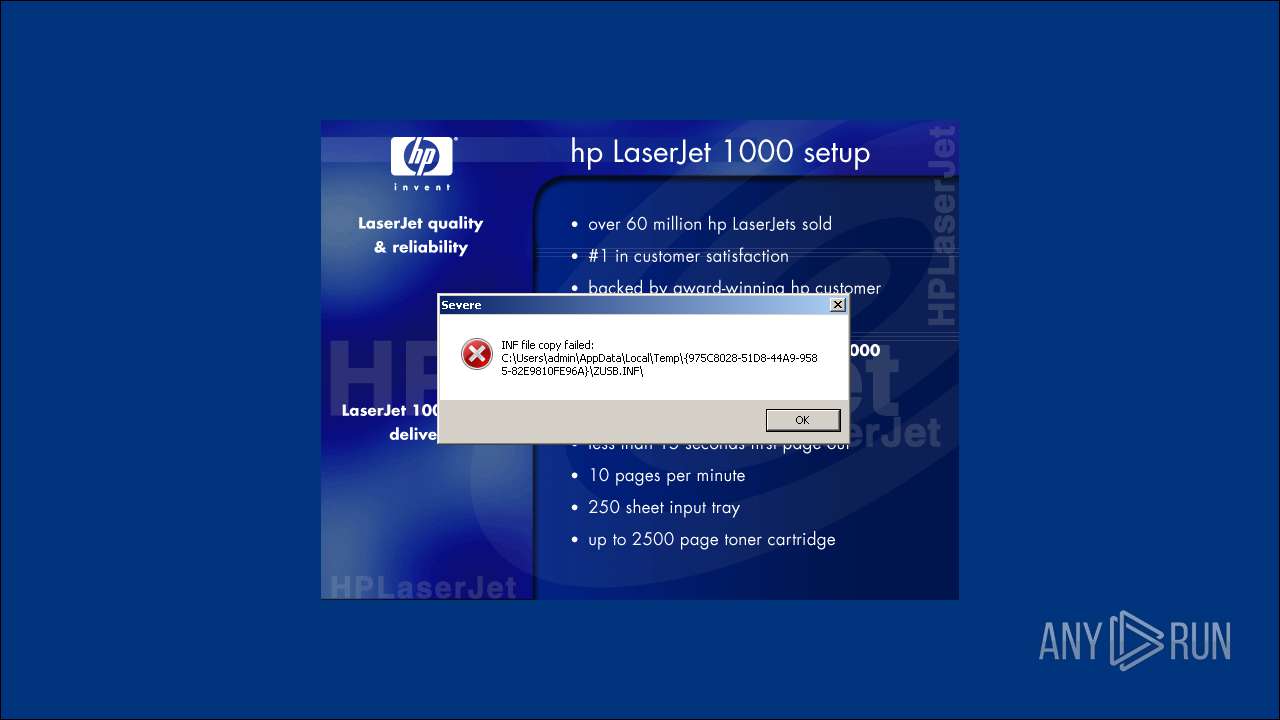
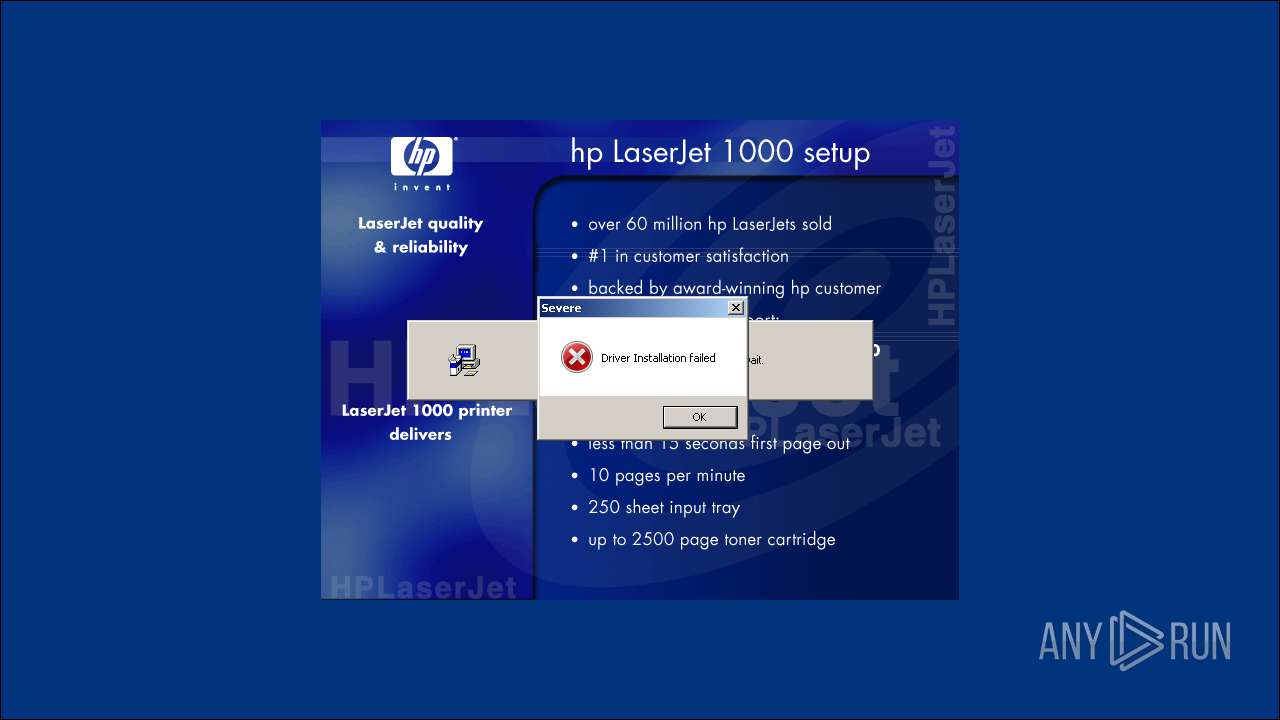
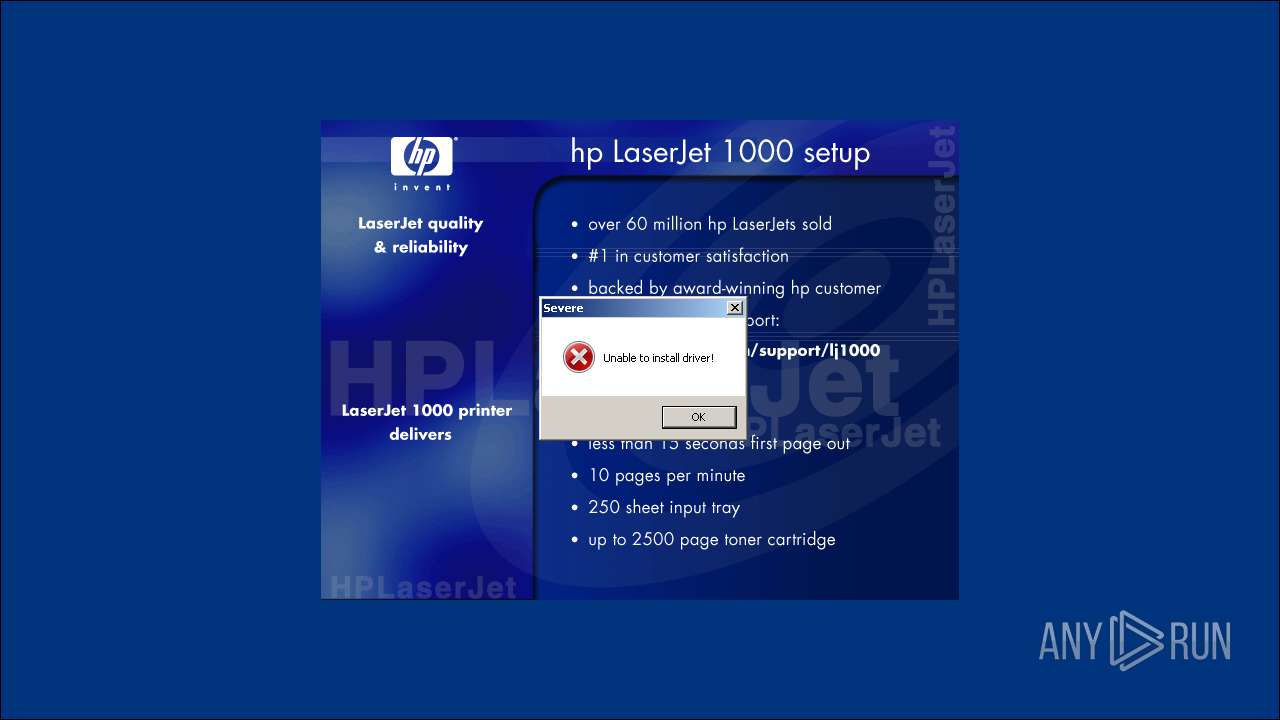
MALICIOUS
Loads dropped or rewritten executable
- IKernel.exe (PID: 3260)
- Setup.exe (PID: 3180)
- spoolsv.exe (PID: 1196)
Application was dropped or rewritten from another process
- Setup.exe (PID: 3180)
- IKernel.exe (PID: 3868)
- IKernel.exe (PID: 3260)
- iKernel.exe (PID: 3700)
- iKernel.exe (PID: 3500)
SUSPICIOUS
Creates files in the program directory
- Setup.exe (PID: 3180)
- IKernel.exe (PID: 3260)
Executable content was dropped or overwritten
- lj1488en.exe (PID: 3908)
- Setup.exe (PID: 3180)
- IKernel.exe (PID: 3260)
Creates files in the Windows directory
- IKernel.exe (PID: 3260)
Creates a software uninstall entry
- IKernel.exe (PID: 3260)
Searches for installed software
- IKernel.exe (PID: 3260)
- DllHost.exe (PID: 2460)
Starts itself from another location
- IKernel.exe (PID: 3260)
Creates COM task schedule object
- IKernel.exe (PID: 3260)
Removes files from Windows directory
- IKernel.exe (PID: 3260)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 3600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:08:02 09:01:18+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 77824 |
| InitializedDataSize: | 221184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8af7 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.100.1332 |
| ProductVersionNumber: | 4.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | |
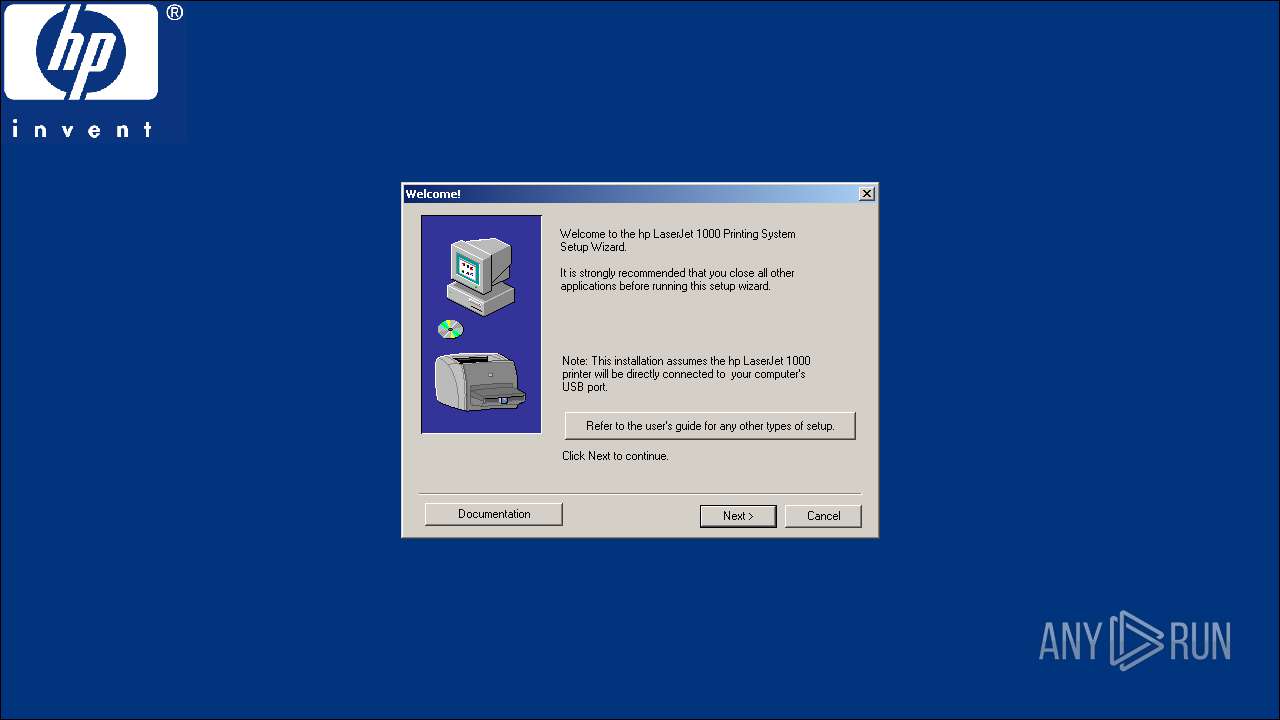
| CompanyName: | Hewlett Packard |
| FileDescription: | |
| InternalName: | stub32 |
| OriginalFileName: | stub32i.exe |
| FileVersion: | |
| LegalCopyright: | |
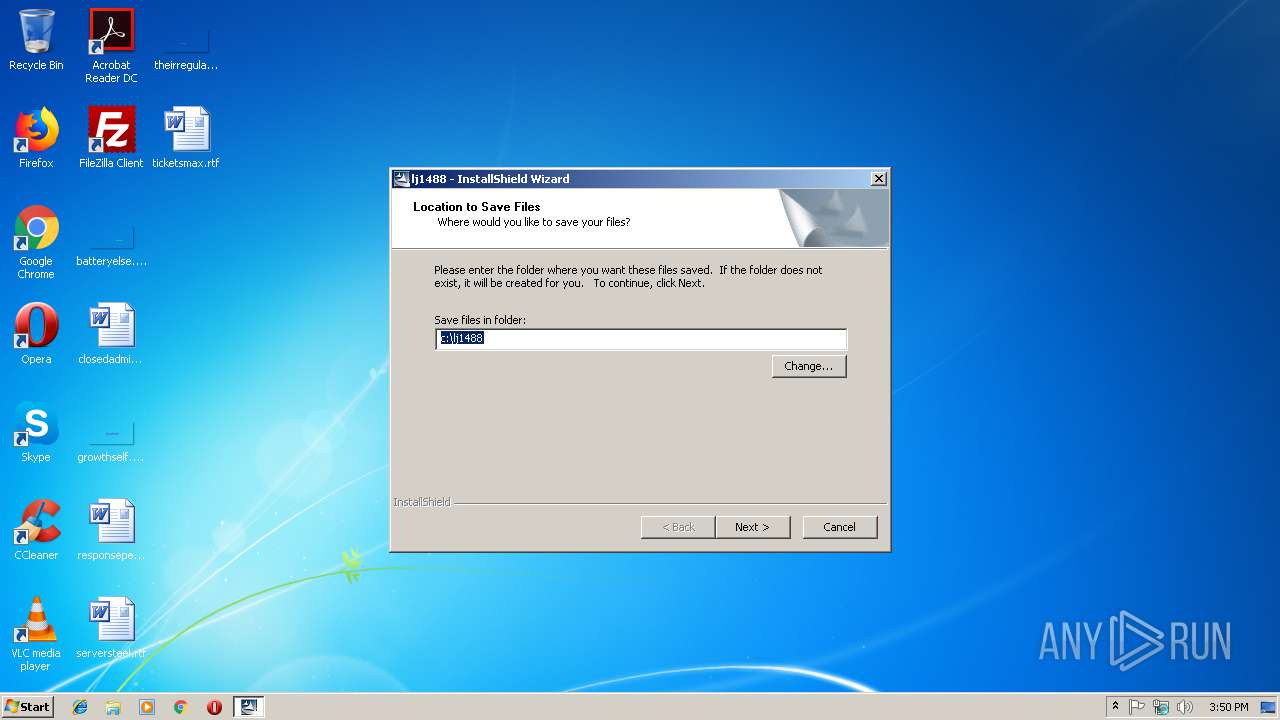
| ProductName: | lj1488 |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Aug-2002 07:01:18 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Hewlett Packard |
| FileDescription: | - |
| InternalName: | stub32 |
| OriginalFilename: | stub32i.exe |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | lj1488 |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Aug-2002 07:01:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00012436 | 0x00013000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53609 |
.rdata | 0x00014000 | 0x000019B2 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.8719 |
.data | 0x00016000 | 0x00006E64 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.35003 |
.rsrc | 0x0001D000 | 0x0002CAA8 | 0x0002D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.02308 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.31177 | 1640 | UNKNOWN | English - United States | RT_VERSION |
2 | 6.39652 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 3.18406 | 424 | UNKNOWN | English - United States | RT_STRING |
4 | 3.07096 | 282 | UNKNOWN | English - United States | RT_STRING |
19 | 2.86832 | 186 | UNKNOWN | English - United States | RT_STRING |
20 | 3.28952 | 870 | UNKNOWN | English - United States | RT_STRING |
21 | 2.89596 | 152 | UNKNOWN | English - United States | RT_STRING |
103 | 2.64576 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
118 | 7.04133 | 154530 | UNKNOWN | English - United States | RT_BITMAP |
132 | 4.04914 | 14564 | UNKNOWN | English - United States | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
LZ32.dll |
SHELL32.dll |
USER32.dll |
Total processes
43
Monitored processes
11
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1196 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2460 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2800 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "00000550" "00000330" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3180 | "c:\lj1488\Setup.exe" | c:\lj1488\Setup.exe | lj1488en.exe | ||||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Launcher Exit code: 0 Version: 6, 30, 100, 1255 Modules
| |||||||||||||||
| 3260 | C:\PROGRA~1\COMMON~1\INSTAL~1\Engine\6\INTEL3~1\IKernel.exe -Embedding | C:\PROGRA~1\COMMON~1\INSTAL~1\Engine\6\INTEL3~1\IKernel.exe | svchost.exe | ||||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Engine Exit code: 0 Version: 6, 30, 100, 1255 Modules
| |||||||||||||||
| 3388 | "C:\Users\admin\AppData\Local\Temp\lj1488en.exe" | C:\Users\admin\AppData\Local\Temp\lj1488en.exe | — | explorer.exe | |||||||||||
User: admin Company: Hewlett Packard Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 3500 | "C:\Program Files\Common Files\InstallShield\engine\6\Intel 32\iKernel.exe" /UNREGSERVER | C:\Program Files\Common Files\InstallShield\engine\6\Intel 32\iKernel.exe | — | IKernel.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Engine Exit code: 0 Version: 6, 30, 100, 1255 Modules
| |||||||||||||||
| 3600 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3700 | "C:\Program Files\Common Files\InstallShield\engine\6\Intel 32\iKernel.exe" /REGSERVER | C:\Program Files\Common Files\InstallShield\engine\6\Intel 32\iKernel.exe | — | IKernel.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Engine Exit code: 0 Version: 6, 30, 100, 1255 Modules
| |||||||||||||||
| 3868 | "C:\Program Files\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe" -RegServer | C:\Program Files\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe | — | Setup.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Engine Exit code: 0 Version: 6, 30, 100, 1255 Modules
| |||||||||||||||
Total events
1 948
Read events
545
Write events
1 023
Delete events
380
Modification events
| (PID) Process: | (3868) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Setup.Kernel.1 |
| Operation: | write | Name: | |
Value: InstallShield setup kernel | |||
| (PID) Process: | (3868) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Setup.Kernel.1\CLSID |
| Operation: | write | Name: | |
Value: {91814EC0-B5F0-11D2-80B9-00104B1F6CEA} | |||
| (PID) Process: | (3868) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Setup.Kernel |
| Operation: | write | Name: | |
Value: InstallShield setup kernel | |||
| (PID) Process: | (3868) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Setup.Kernel\CLSID |
| Operation: | write | Name: | |
Value: {91814EC0-B5F0-11D2-80B9-00104B1F6CEA} | |||
| (PID) Process: | (3868) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{91814EC0-B5F0-11D2-80B9-00104B1F6CEA} |
| Operation: | write | Name: | |
Value: InstallShield setup kernel | |||
| (PID) Process: | (3868) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{91814EC0-B5F0-11D2-80B9-00104B1F6CEA}\ProgID |
| Operation: | write | Name: | |
Value: Setup.Kernel.1 | |||
| (PID) Process: | (3868) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{91814EC0-B5F0-11D2-80B9-00104B1F6CEA}\VersionIndependentProgID |
| Operation: | write | Name: | |
Value: Setup.Kernel | |||
| (PID) Process: | (3868) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{91814EC0-B5F0-11D2-80B9-00104B1F6CEA}\LocalServer32 |
| Operation: | write | Name: | |
Value: C:\PROGRA~1\COMMON~1\INSTAL~1\Engine\6\INTEL3~1\IKernel.exe | |||
| (PID) Process: | (3868) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Setup.LogServices.1 |
| Operation: | write | Name: | |
Value: SetupLogServices Class | |||
| (PID) Process: | (3868) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Setup.LogServices.1\CLSID |
| Operation: | write | Name: | |
Value: {22D84EC7-E201-4432-B3ED-A9DCA3604594} | |||
Executable files
121
Suspicious files
25
Text files
198
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3908 | lj1488en.exe | C:\Users\admin\AppData\Local\Temp\ext6B1F.tmp | — | |
MD5:— | SHA256:— | |||
| 3908 | lj1488en.exe | C:\Users\admin\AppData\Local\Temp\pft81E4.tmp\pftw1.pkg | — | |
MD5:— | SHA256:— | |||
| 3908 | lj1488en.exe | C:\lj1488\apptune.ini | text | |
MD5:— | SHA256:— | |||
| 3908 | lj1488en.exe | C:\lj1488\autorun.inf | inf | |
MD5:— | SHA256:— | |||
| 3908 | lj1488en.exe | C:\lj1488\autorun.exe | executable | |
MD5:— | SHA256:— | |||
| 3908 | lj1488en.exe | C:\lj1488\data1.cab | compressed | |
MD5:— | SHA256:— | |||
| 3908 | lj1488en.exe | C:\lj1488\data1.hdr | hdr | |
MD5:— | SHA256:— | |||
| 3908 | lj1488en.exe | C:\lj1488\dour65w.ttf | ttf | |
MD5:— | SHA256:— | |||
| 3908 | lj1488en.exe | C:\lj1488\apptune.exe | executable | |
MD5:— | SHA256:— | |||
| 3908 | lj1488en.exe | C:\lj1488\data2.cab | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report