| File name: | ViraLock.zip |
| Full analysis: | https://app.any.run/tasks/88c2c725-dc57-49e8-9886-0047092d40ce |
| Verdict: | Malicious activity |
| Analysis date: | March 11, 2021, 11:04:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 6A47990541C573D44444F9AD5AA61774 |
| SHA1: | F230FFF199A57A07A972E2EE7169BC074D9E0CD5 |
| SHA256: | B161C762C5894D820CC10D9027F2404A6FEC3BC9F8FD84D23FF1DAEF98493115 |
| SSDEEP: | 3072:EVGcVUZ2RO+vvmYYN4ul1c0wTLcc0JuEzXiXoNn59cz+P+gJmq:EFVOYM4IwUc0JpzXYorWyL |
MALICIOUS
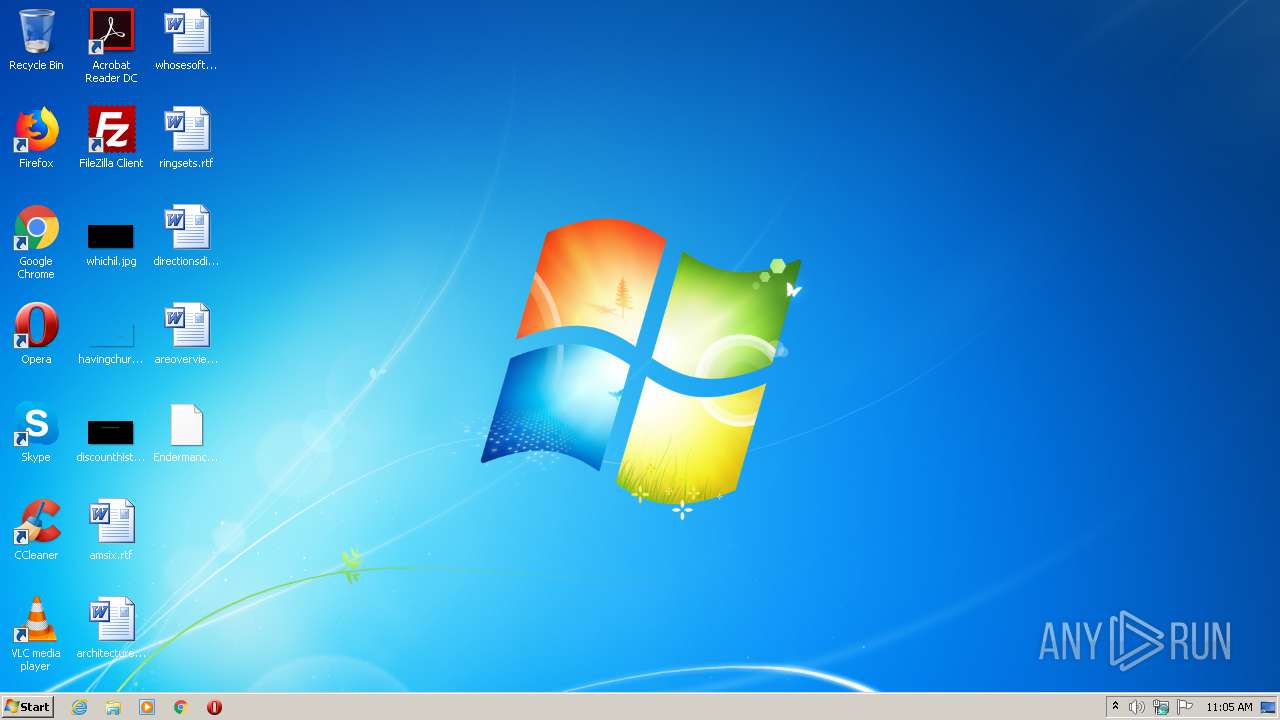
Application was dropped or rewritten from another process
- Endermanch@ViraLock.exe (PID: 556)
- nSoAoQMI.exe (PID: 3728)
- Endermanch@ViraLock.exe (PID: 1512)
- Endermanch@ViraLock.exe (PID: 3752)
- QyswEEgY.exe (PID: 4020)
- Endermanch@ViraLock.exe (PID: 2148)
- Endermanch@ViraLock.exe (PID: 2068)
- QyswEEgY.exe (PID: 1592)
Drops executable file immediately after starts
- Endermanch@ViraLock.exe (PID: 556)
Changes the autorun value in the registry
- Endermanch@ViraLock.exe (PID: 556)
- nSoAoQMI.exe (PID: 3728)
- QyswEEgY.exe (PID: 4020)
- QyswEEgY.exe (PID: 1592)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2920)
- Endermanch@ViraLock.exe (PID: 556)
- nSoAoQMI.exe (PID: 3728)
Drops a file with too old compile date
- WinRAR.exe (PID: 2920)
- Endermanch@ViraLock.exe (PID: 556)
- nSoAoQMI.exe (PID: 3728)
Creates files in the program directory
- Endermanch@ViraLock.exe (PID: 556)
- QyswEEgY.exe (PID: 4020)
Starts CMD.EXE for commands execution
- Endermanch@ViraLock.exe (PID: 556)
- Endermanch@ViraLock.exe (PID: 1512)
- Endermanch@ViraLock.exe (PID: 3752)
- Endermanch@ViraLock.exe (PID: 2148)
- Endermanch@ViraLock.exe (PID: 2068)
Uses REG.EXE to modify Windows registry
- Endermanch@ViraLock.exe (PID: 556)
- Endermanch@ViraLock.exe (PID: 1512)
- Endermanch@ViraLock.exe (PID: 3752)
- Endermanch@ViraLock.exe (PID: 2148)
- Endermanch@ViraLock.exe (PID: 2068)
Executes scripts
- cmd.exe (PID: 3352)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 3920)
- cmd.exe (PID: 3916)
- cmd.exe (PID: 4092)
Uses TASKKILL.EXE to kill process
- nSoAoQMI.exe (PID: 3728)
INFO
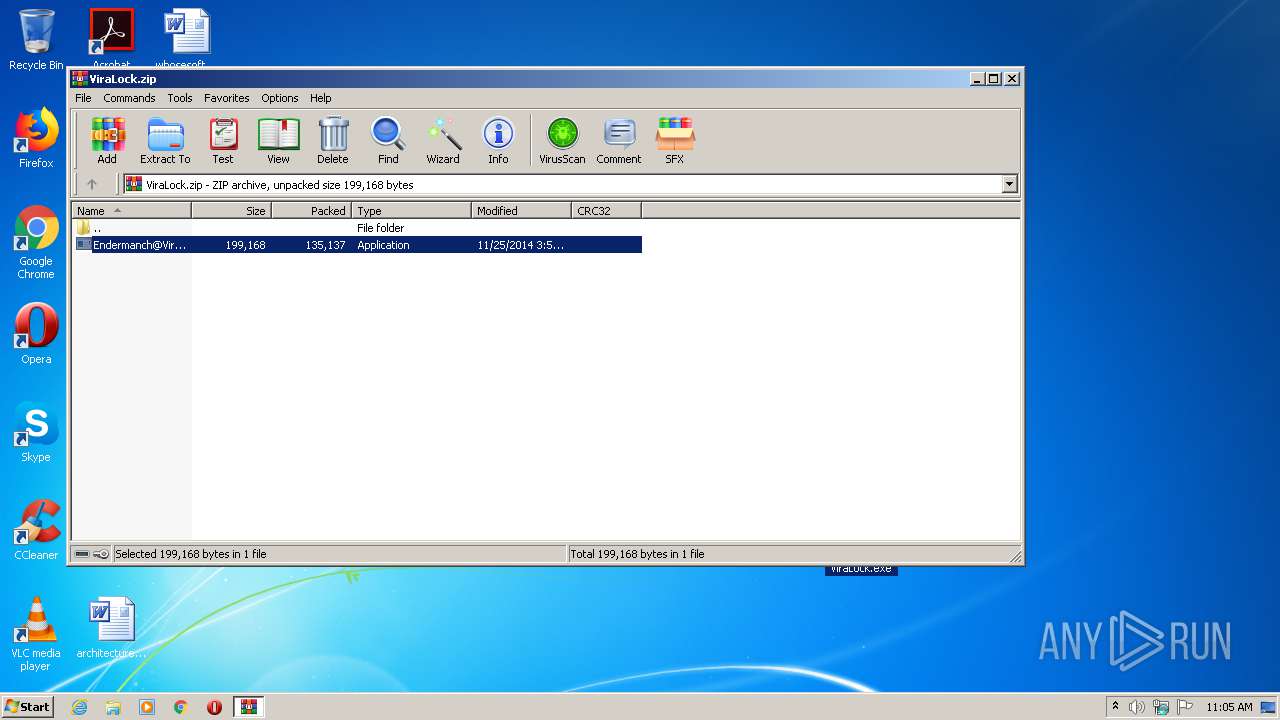
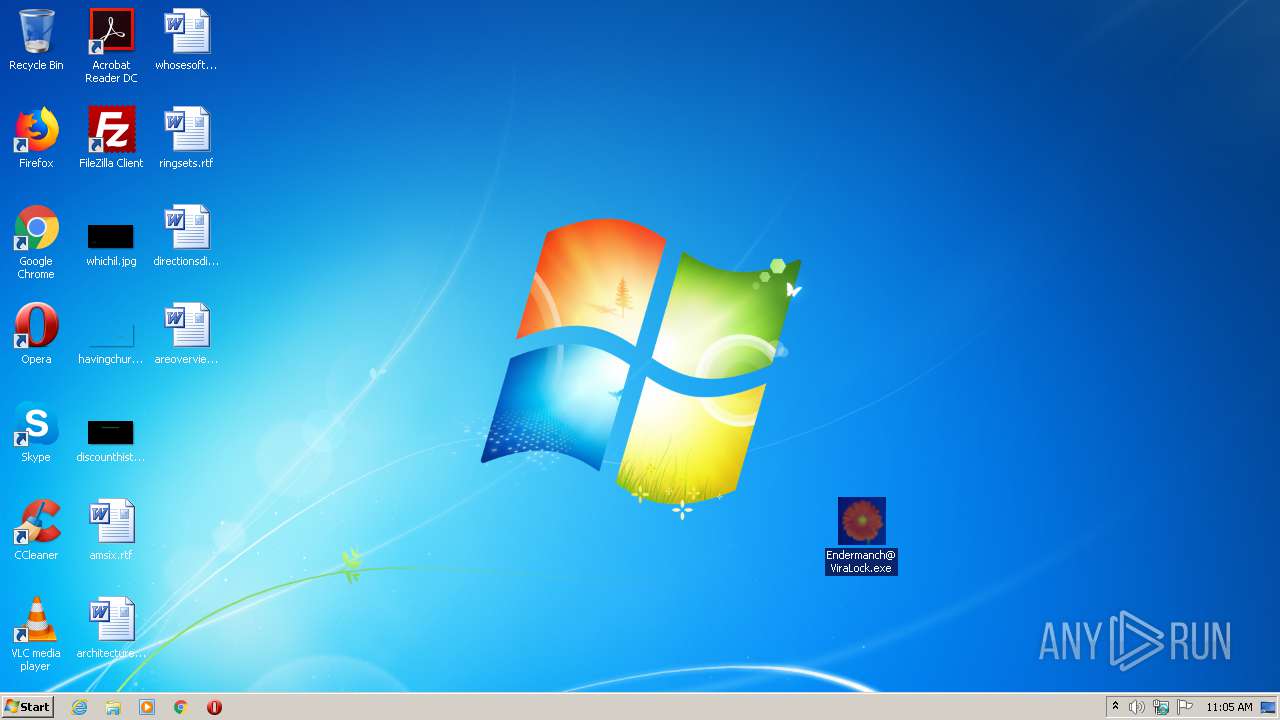
Manual execution by user
- Endermanch@ViraLock.exe (PID: 556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
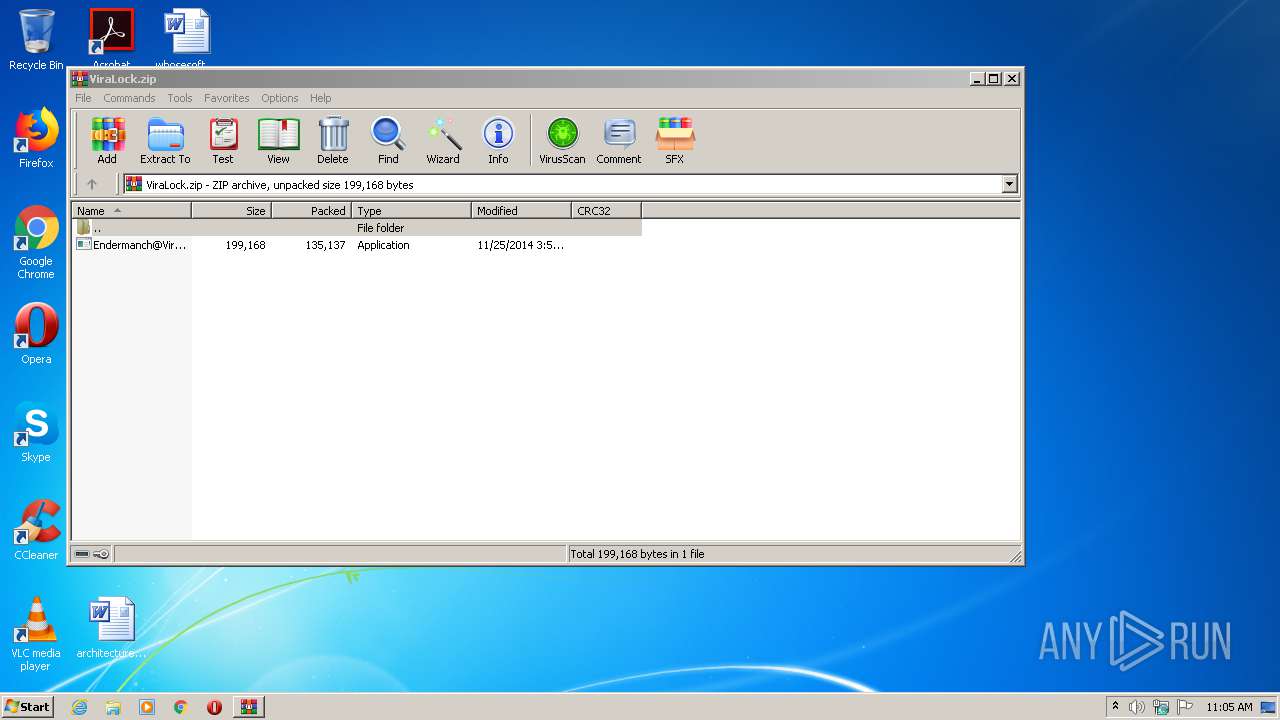
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2014:11:25 06:56:15 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 135137 |
| ZipUncompressedSize: | 199168 |
| ZipFileName: | Endermanch@ViraLock.exe |
Total processes
106
Monitored processes
40
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | taskkill /FI "USERNAME eq admin" /F /IM QyswEEgY.exe | C:\Windows\system32\taskkill.exe | — | nSoAoQMI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 556 | "C:\Users\admin\Desktop\Endermanch@ViraLock.exe" | C:\Users\admin\Desktop\Endermanch@ViraLock.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1108 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced /f /v Hidden /t REG_DWORD /d 2 | C:\Windows\system32\reg.exe | — | Endermanch@ViraLock.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1512 | C:\Users\admin\Desktop\Endermanch@ViraLock | C:\Users\admin\Desktop\Endermanch@ViraLock.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1552 | cmd /c "C:\Users\admin\Desktop\Endermanch@ViraLock" | C:\Windows\system32\cmd.exe | — | Endermanch@ViraLock.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1592 | "C:\ProgramData\QYEcYIMU\QyswEEgY.exe" | C:\ProgramData\QYEcYIMU\QyswEEgY.exe | nSoAoQMI.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1644 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced /f /v Hidden /t REG_DWORD /d 2 | C:\Windows\system32\reg.exe | — | Endermanch@ViraLock.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1652 | cscript C:\Users\admin\AppData\Local\Temp/file.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1716 | cscript C:\Users\admin\AppData\Local\Temp/file.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1924 | reg add HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /d 0 /t REG_DWORD /f | C:\Windows\system32\reg.exe | — | Endermanch@ViraLock.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
600
Read events
565
Write events
35
Delete events
0
Modification events
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ViraLock.zip | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
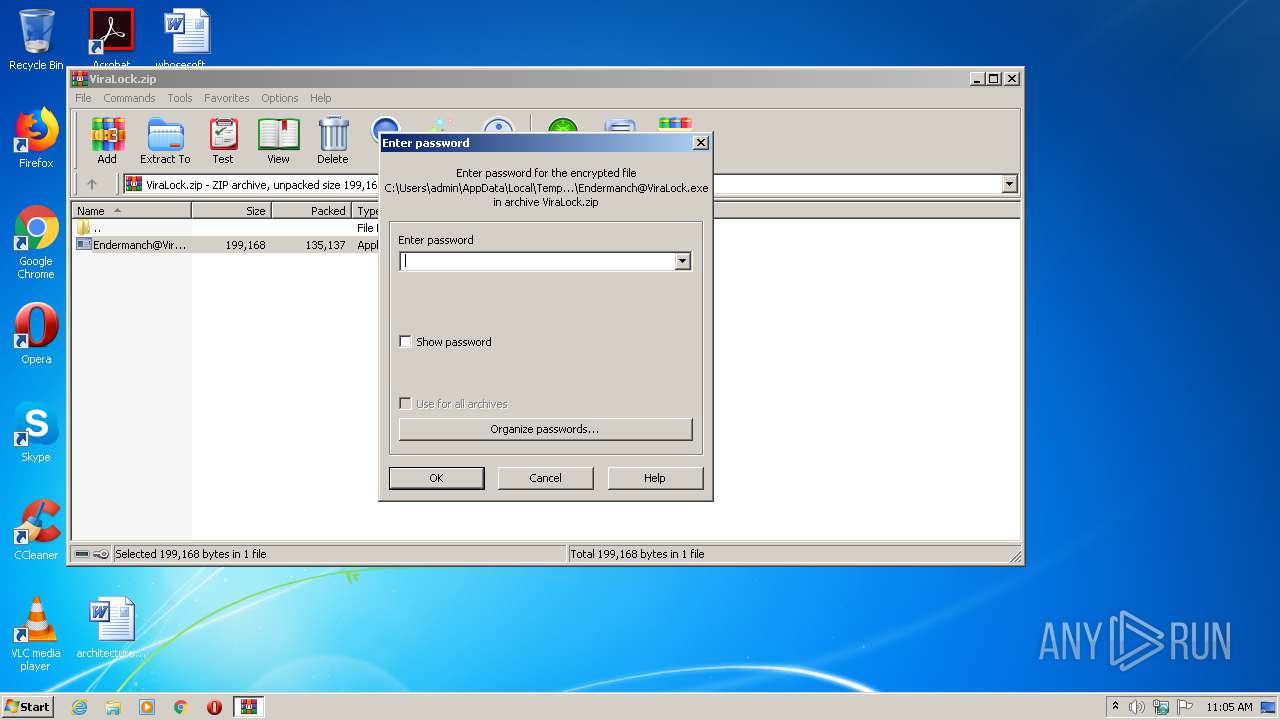
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
7
Suspicious files
0
Text files
70
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 556 | Endermanch@ViraLock.exe | C:\Users\admin\AppData\Local\Temp\JkkYsIcg.bat | — | |
MD5:— | SHA256:— | |||
| 1512 | Endermanch@ViraLock.exe | C:\Users\admin\AppData\Local\Temp\hkYgsIcg.bat | — | |
MD5:— | SHA256:— | |||
| 2148 | Endermanch@ViraLock.exe | C:\Users\admin\AppData\Local\Temp\qyIosIcg.bat | — | |
MD5:— | SHA256:— | |||
| 2068 | Endermanch@ViraLock.exe | C:\Users\admin\AppData\Local\Temp\XkwosIcg.bat | — | |
MD5:— | SHA256:— | |||
| 556 | Endermanch@ViraLock.exe | C:\Users\admin\qKQocMko\nSoAoQMI.exe | executable | |
MD5:— | SHA256:— | |||
| 3728 | nSoAoQMI.exe | C:\Users\admin\Desktop\mcAu.ico | — | |
MD5:— | SHA256:— | |||
| 3728 | nSoAoQMI.exe | C:\Users\admin\Desktop\dcAw.exe | — | |
MD5:— | SHA256:— | |||
| 3728 | nSoAoQMI.exe | C:\Users\admin\AppData\Local\VirtualStore\RCXAC28.tmp | — | |
MD5:— | SHA256:— | |||
| 3728 | nSoAoQMI.exe | C:\Users\admin\Desktop\XQEc.ico | — | |
MD5:— | SHA256:— | |||
| 3728 | nSoAoQMI.exe | C:\Users\admin\Desktop\GQEe.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
0
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4020 | QyswEEgY.exe | GET | 301 | 142.250.186.46:80 | http://google.com/ | US | html | 219 b | whitelisted |
3728 | nSoAoQMI.exe | GET | 301 | 142.250.186.46:80 | http://google.com/ | US | html | 219 b | whitelisted |
1592 | QyswEEgY.exe | GET | 301 | 142.250.186.46:80 | http://google.com/ | US | html | 219 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3728 | nSoAoQMI.exe | 200.119.204.12:9999 | — | COTAS LTDA. | BO | malicious |
3728 | nSoAoQMI.exe | 200.87.164.69:9999 | — | Entel S.A. - EntelNet | BO | malicious |
1592 | QyswEEgY.exe | 200.87.164.69:9999 | — | Entel S.A. - EntelNet | BO | malicious |
4020 | QyswEEgY.exe | 200.119.204.12:9999 | — | COTAS LTDA. | BO | malicious |
1592 | QyswEEgY.exe | 142.250.186.46:80 | — | Google Inc. | US | whitelisted |
3728 | nSoAoQMI.exe | 142.250.186.46:80 | — | Google Inc. | US | whitelisted |
4020 | QyswEEgY.exe | 142.250.186.46:80 | — | Google Inc. | US | whitelisted |
4020 | QyswEEgY.exe | 200.87.164.69:9999 | — | Entel S.A. - EntelNet | BO | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
4020 | QyswEEgY.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible automated connectivity check (www.google.com) |