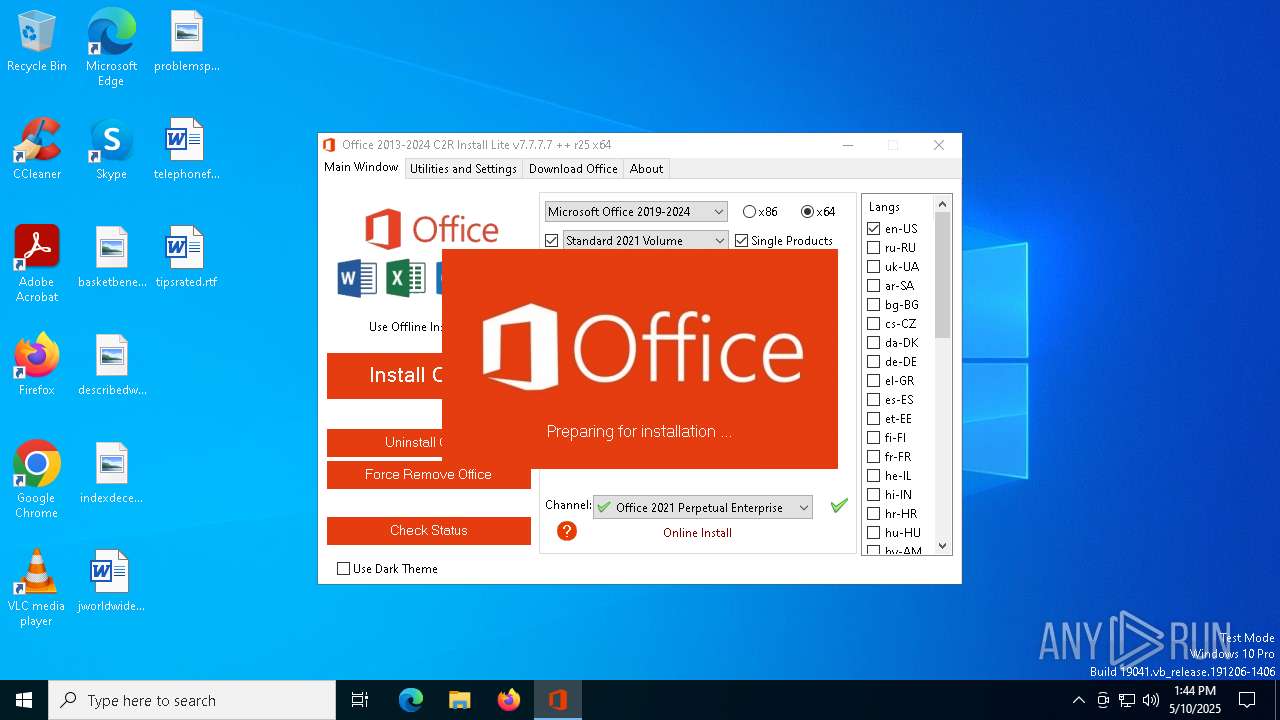
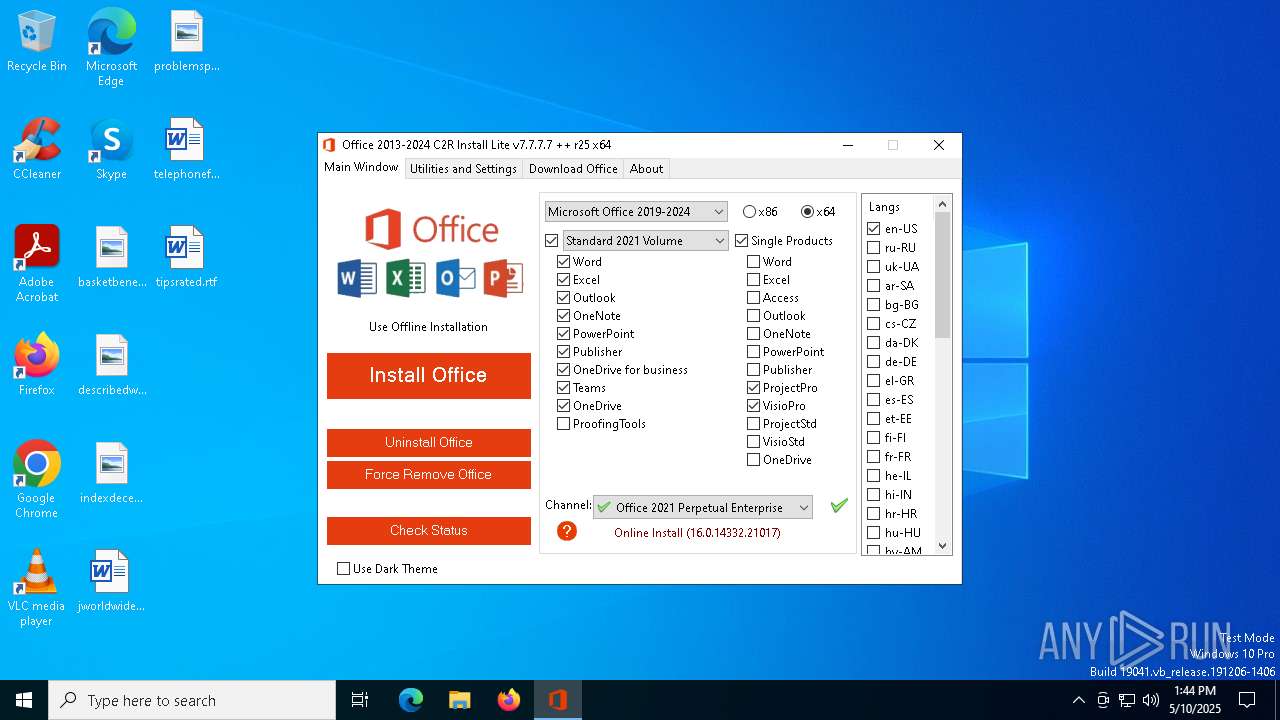
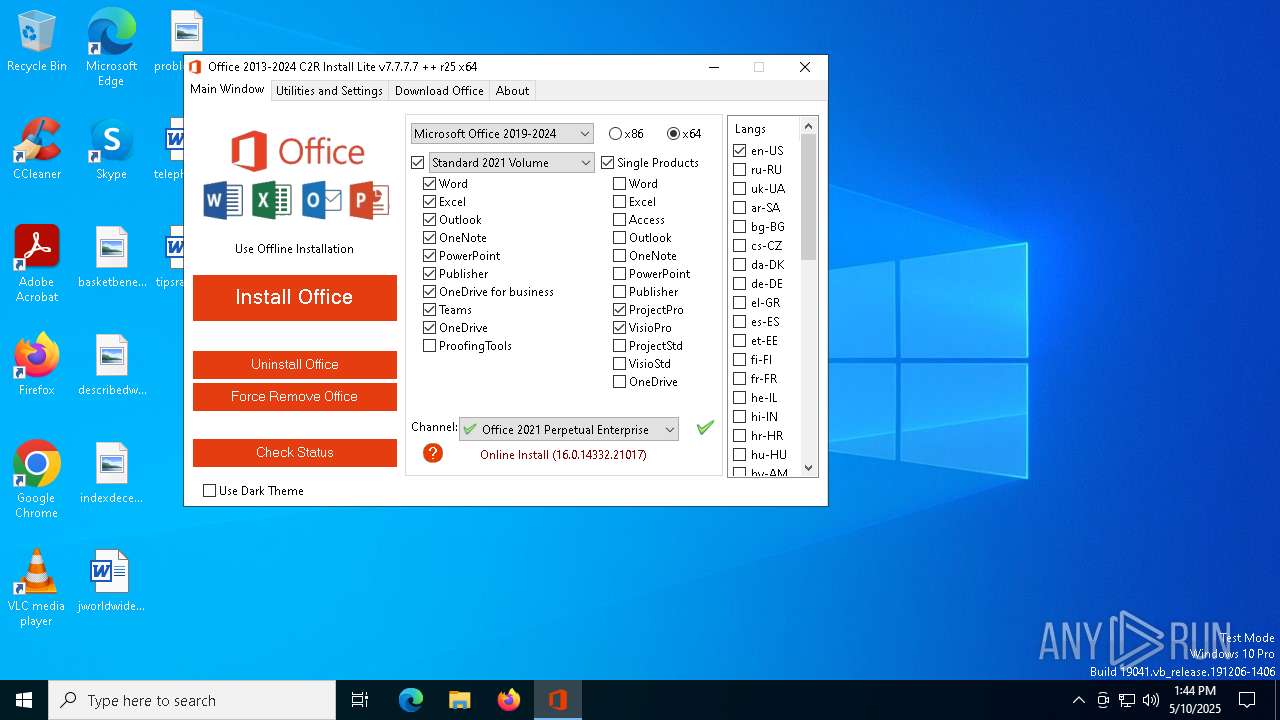
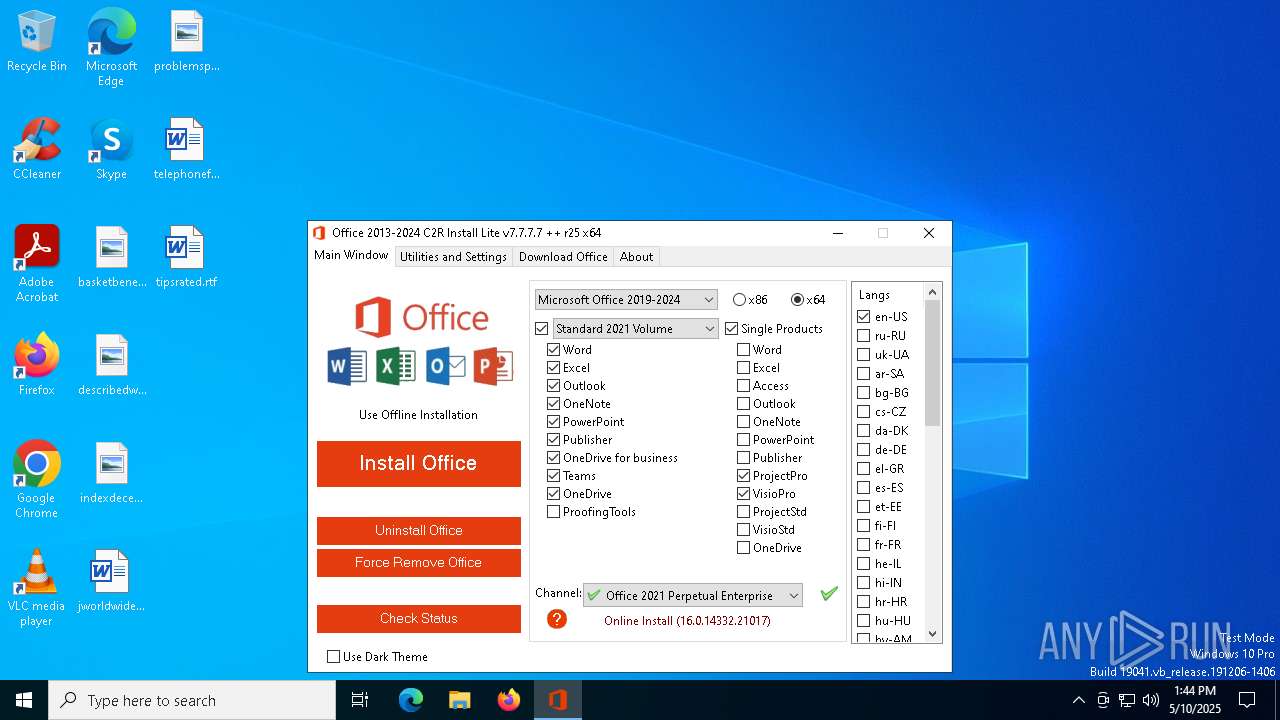
| File name: | OInstallLite_x64.exe |
| Full analysis: | https://app.any.run/tasks/dfb221a8-617f-46f2-86a9-a431116a22e1 |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 13:44:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 8F5FA1CE3B25FD25B94399A31D3D098D |
| SHA1: | 04E8101D2512F3ECA75F335972ABFBC8B42C7C44 |
| SHA256: | B150BF1945D43CCC57EEA85C23B980020C37C0F583EF89D996D3E6384053A973 |
| SSDEEP: | 98304:wDui2UfmFAyXzKtHucp+r4laH0hWD9yfsIB+O7xEjeA6aKJqMBOA0Euj6pEZ9d+S:Kuju7 |
MALICIOUS
Uses WMIC.EXE to add exclusions to the Windows Defender
- cmd.exe (PID: 6724)
- cmd.exe (PID: 6028)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 1052)
SUSPICIOUS
Found strings related to reading or modifying Windows Defender settings
- OInstallLite_x64.exe (PID: 6032)
Uses REG/REGEDIT.EXE to modify registry
- OInstallLite_x64.exe (PID: 6032)
Executable content was dropped or overwritten
- OInstallLite_x64.exe (PID: 6032)
- files.dat (PID: 5800)
Starts CMD.EXE for commands execution
- OInstallLite_x64.exe (PID: 6032)
Drops 7-zip archiver for unpacking
- OInstallLite_x64.exe (PID: 6032)
The executable file from the user directory is run by the CMD process
- files.dat (PID: 5800)
Starts application with an unusual extension
- cmd.exe (PID: 4724)
Process drops legitimate windows executable
- files.dat (PID: 5800)
The process drops C-runtime libraries
- files.dat (PID: 5800)
Starts POWERSHELL.EXE for commands execution
- OInstallLite_x64.exe (PID: 6032)
The process bypasses the loading of PowerShell profile settings
- OInstallLite_x64.exe (PID: 6032)
Probably download files using WebClient
- OInstallLite_x64.exe (PID: 6032)
Executes script without checking the security policy
- powershell.exe (PID: 1052)
INFO
Checks supported languages
- OInstallLite_x64.exe (PID: 6032)
- files.dat (PID: 5800)
Reads Microsoft Office registry keys
- OInstallLite_x64.exe (PID: 6032)
Reads Environment values
- OInstallLite_x64.exe (PID: 6032)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2236)
- WMIC.exe (PID: 1628)
Create files in a temporary directory
- files.dat (PID: 5800)
- OInstallLite_x64.exe (PID: 6032)
The sample compiled with english language support
- files.dat (PID: 5800)
- OInstallLite_x64.exe (PID: 6032)
Reads the computer name
- OInstallLite_x64.exe (PID: 6032)
Checks proxy server information
- powershell.exe (PID: 1052)
Disables trace logs
- powershell.exe (PID: 1052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:23 07:48:19+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.5 |
| CodeSize: | 1415168 |
| InitializedDataSize: | 10930176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.7.7.7 |
| ProductVersionNumber: | 7.7.7.7 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
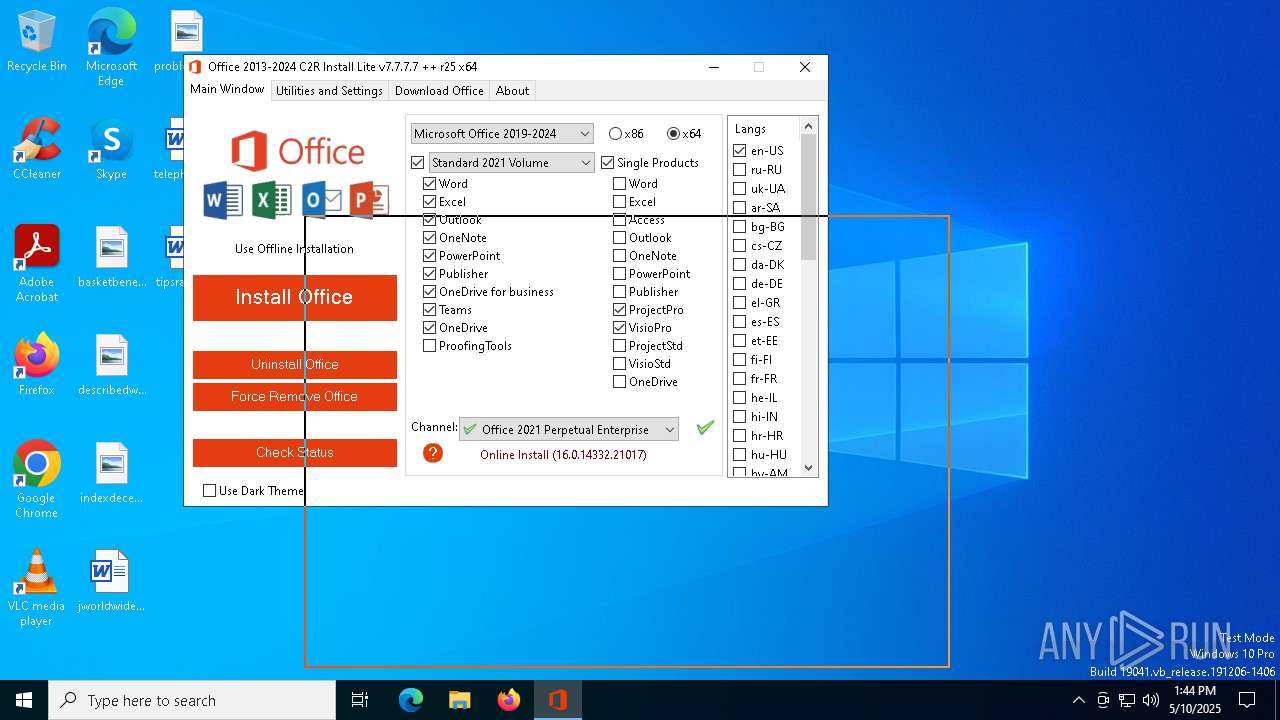
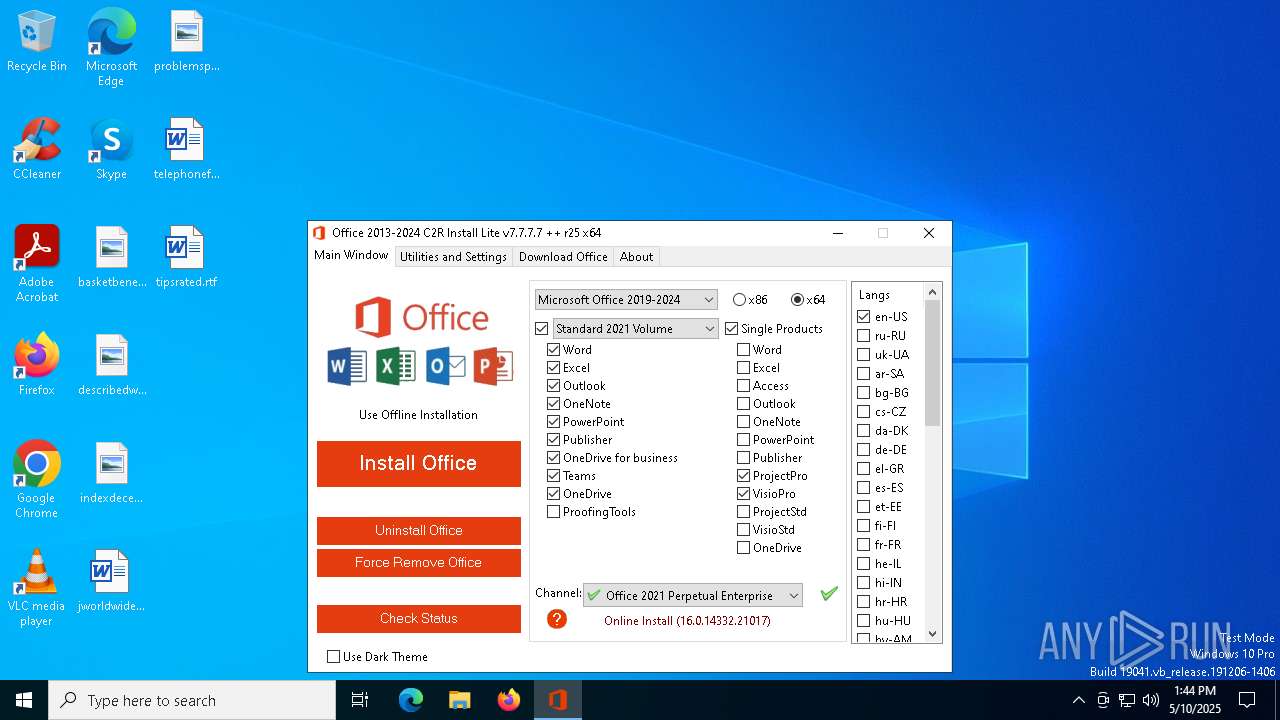
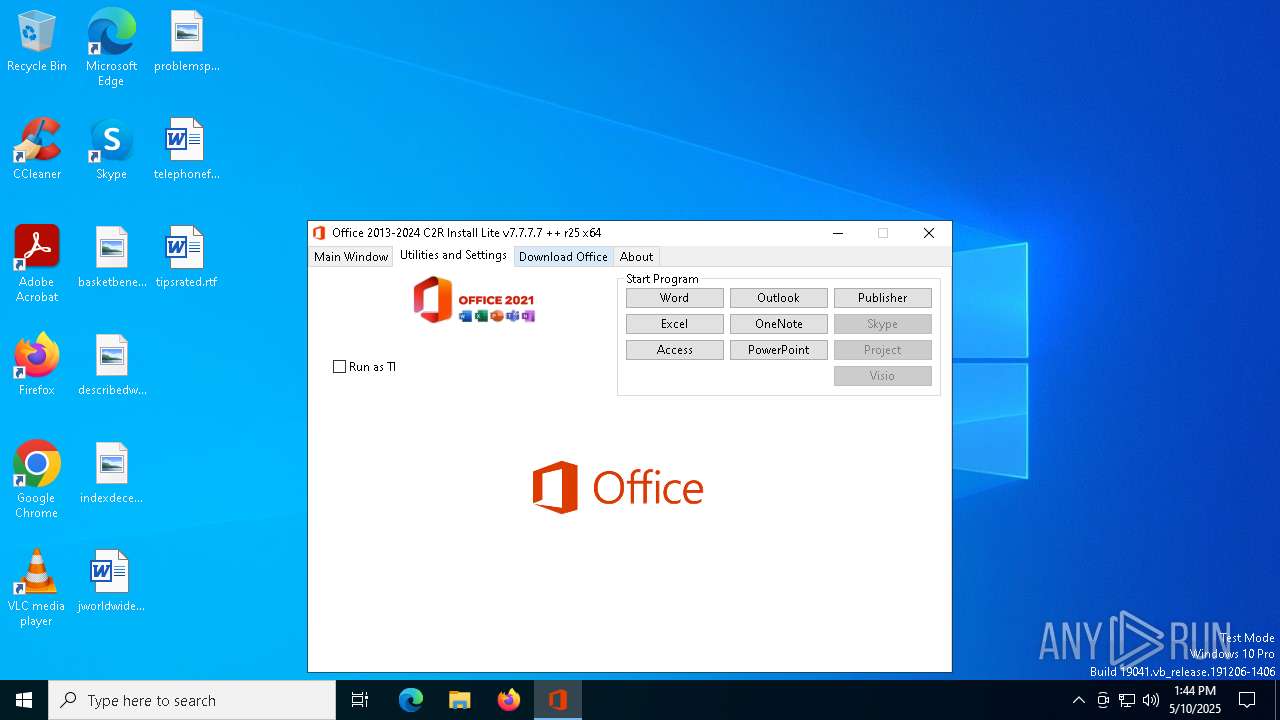
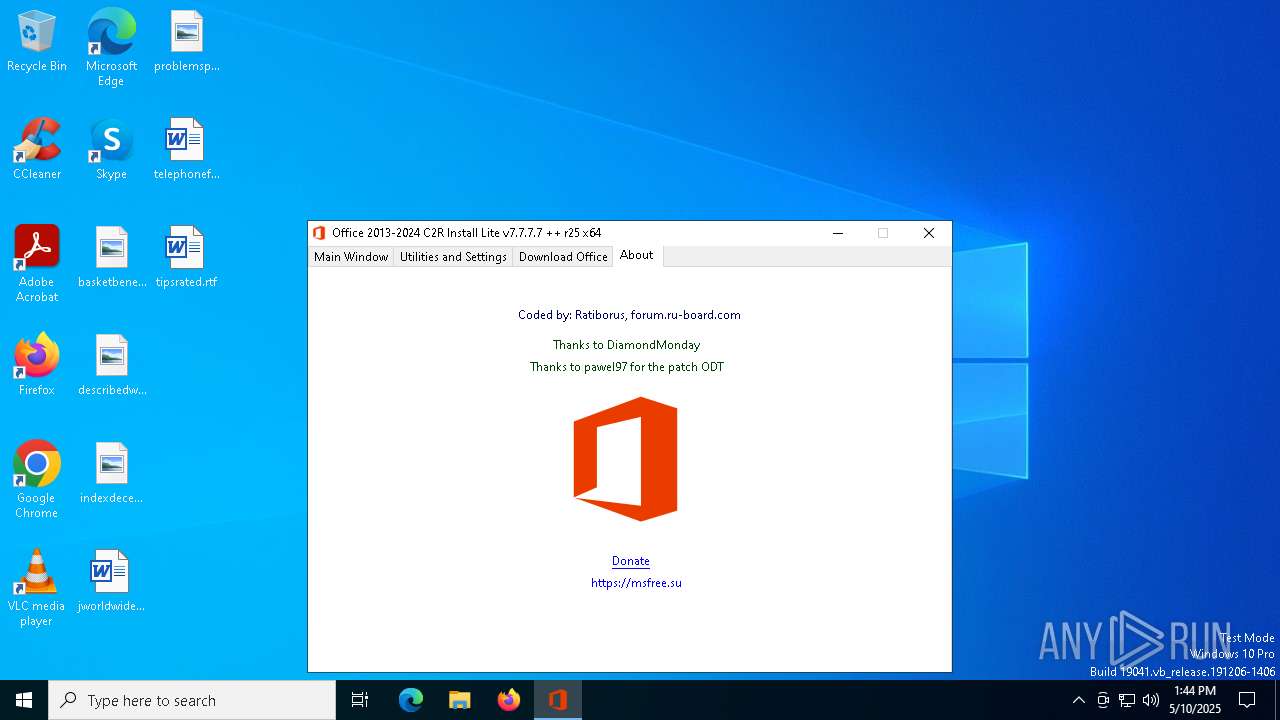
| ProductName: | Office 2013-2024 C2R Install Lite |
| FileDescription: | Office 2013-2024 C2R Install Lite |
Total processes
142
Monitored processes
15
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1052 | "powershell" -nop -command "& { (New-Object Net.WebClient).DownloadFile('https://mrodevicemgr.officeapps.live.com/mrodevicemgrsvc/api/v2/C2RReleaseData', 'C:\Users\admin\AppData\Local\Temp\ver.txt') }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | OInstallLite_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | WMIC /NAMESPACE:\\root\Microsoft\Windows\Defender PATH MSFT_MpPreference call Add ExclusionPath="C:\Users\admin\AppData\Local\Temp\files" | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\WINDOWS\System32\reg.exe" add "HKLM\SOFTWARE\Microsoft\Windows Script Host\Settings" /v Enabled /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | OInstallLite_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | WMIC /NAMESPACE:\\root\Microsoft\Windows\Defender PATH MSFT_MpPreference call Add ExclusionPath="C:\Users\admin\AppData\Local\Temp\OInstallLite_x64.exe" | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 2147749889 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4724 | "C:\WINDOWS\System32\cmd.exe" /D /c files.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | OInstallLite_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5072 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5256 | "C:\Users\admin\AppData\Local\Temp\OInstallLite_x64.exe" | C:\Users\admin\AppData\Local\Temp\OInstallLite_x64.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Office 2013-2024 C2R Install Lite Exit code: 3221226540 Modules
| |||||||||||||||
| 5512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 5800 | files.dat -y -pkmsauto | C:\Users\admin\AppData\Local\Temp\files\files.dat | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 870
Read events
1 869
Write events
1
Delete events
0
Modification events
| (PID) Process: | (1660) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
Executable files
6
Suspicious files
1
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5800 | files.dat | C:\Users\admin\AppData\Local\Temp\files\Uninstall.xml | text | |
MD5:364F86F97324EA82FE0D142CD01CF6DD | SHA256:09D5B42140BAB13165BA97FBD0E77792304C3C93555BE02C3DCE21A7A69C66DD | |||
| 1052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_i04b1lhi.v34.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5800 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x86\cleanospp.exe | executable | |
MD5:98821A7A5737D656633D10A3AFB724BD | SHA256:04BA4487F95290E0B0557B44300C18F637FBAF0872EE96E3111013B8A1539F25 | |||
| 5800 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x64\msvcr100.dll | executable | |
MD5:DF3CA8D16BDED6A54977B30E66864D33 | SHA256:1D1A1AE540BA132F998D60D3622F0297B6E86AE399332C3B47462D7C0F560A36 | |||
| 5800 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x86\msvcr100.dll | executable | |
MD5:BF38660A9125935658CFA3E53FDC7D65 | SHA256:60C06E0FA4449314DA3A0A87C1A9D9577DF99226F943637E06F61188E5862EFA | |||
| 5800 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x64\cleanospp.exe | executable | |
MD5:D3467CB7B83B654C2D05407DC7BA2360 | SHA256:EDF85F4E2EF1A427B34265A22F261D664EC78DE90C3B5DA4174EF28558C8522A | |||
| 6032 | OInstallLite_x64.exe | C:\Users\admin\AppData\Local\Temp\files\Configure.xml | text | |
MD5:46C7CEAD7726B1530BB4C096A648137E | SHA256:BF9CA6C946B42346C8E4B5B1EDCEAA9385069F680F53BEA30C9B16529C39EA8B | |||
| 6032 | OInstallLite_x64.exe | C:\Users\admin\AppData\Local\Temp\files\files.dat | executable | |
MD5:BB5569B15D68C10B7FF2D96B45825120 | SHA256:4E3B13B56BEC0E41778E6506430282BBBD75CCAA600FD4B645CE37DD95B44C8E | |||
| 1052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ver.txt | text | |
MD5:C82DD15FFAF8C5F4B9E9362002B1A03F | SHA256:5BA7032CCC52FA6EA0938D83612CB7DC15B732B6E4BEFDE67CB5C58BC216AFE8 | |||
| 1052 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:5C5BD151E74334D38A1F159EB0E9AE5E | SHA256:AEE43A3134C15FB56D15B489A13260941192F832D79A52362BEC8E1CFD936386 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
16
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1052 | powershell.exe | 52.110.17.38:443 | mrodevicemgr.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
mrodevicemgr.officeapps.live.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |