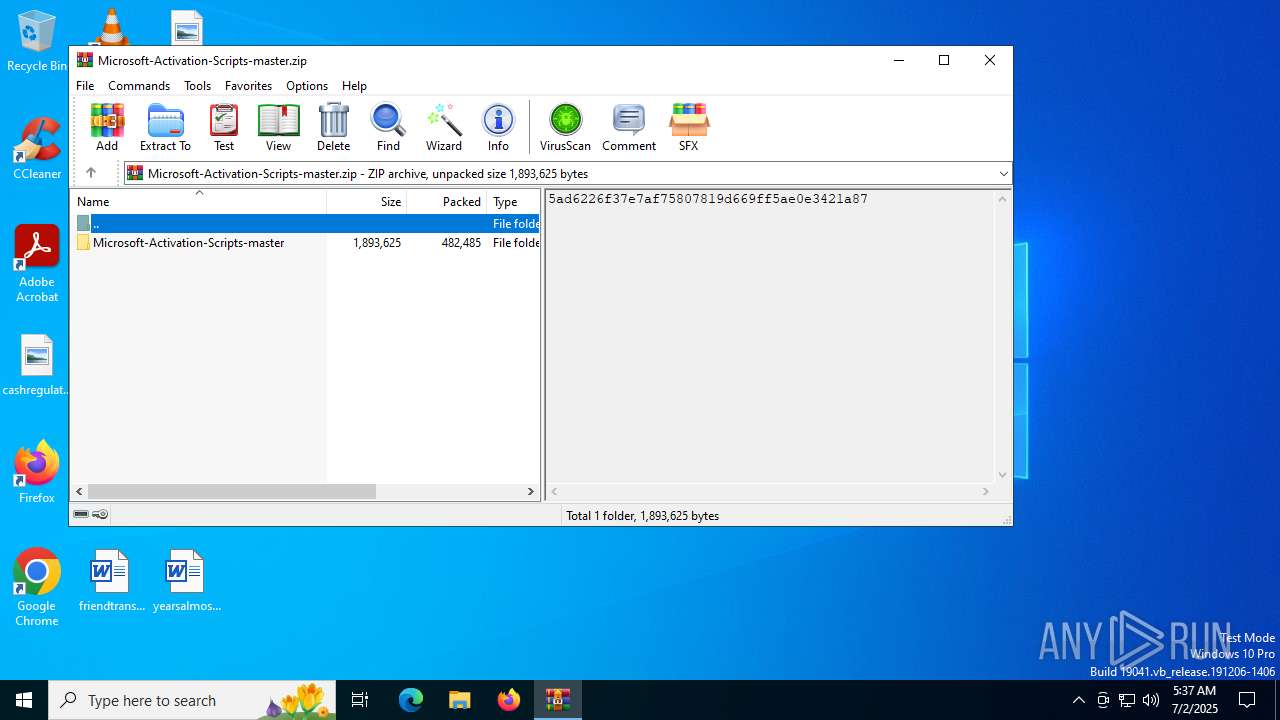
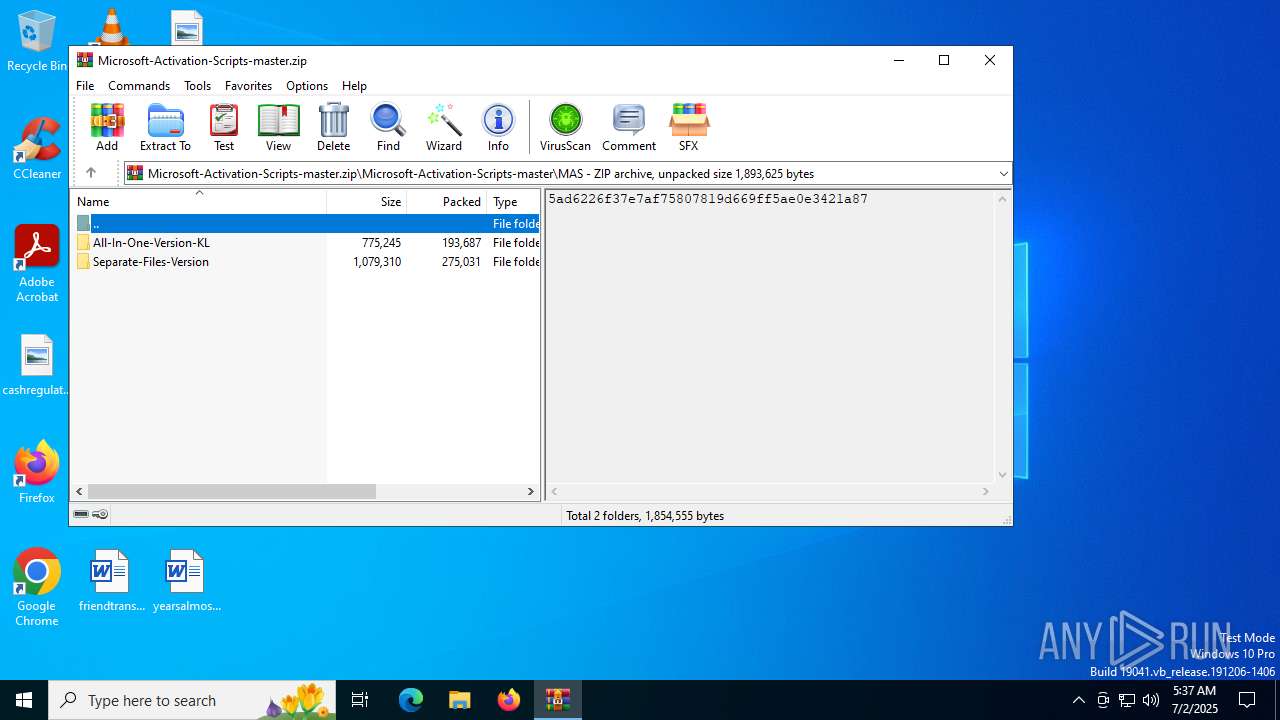
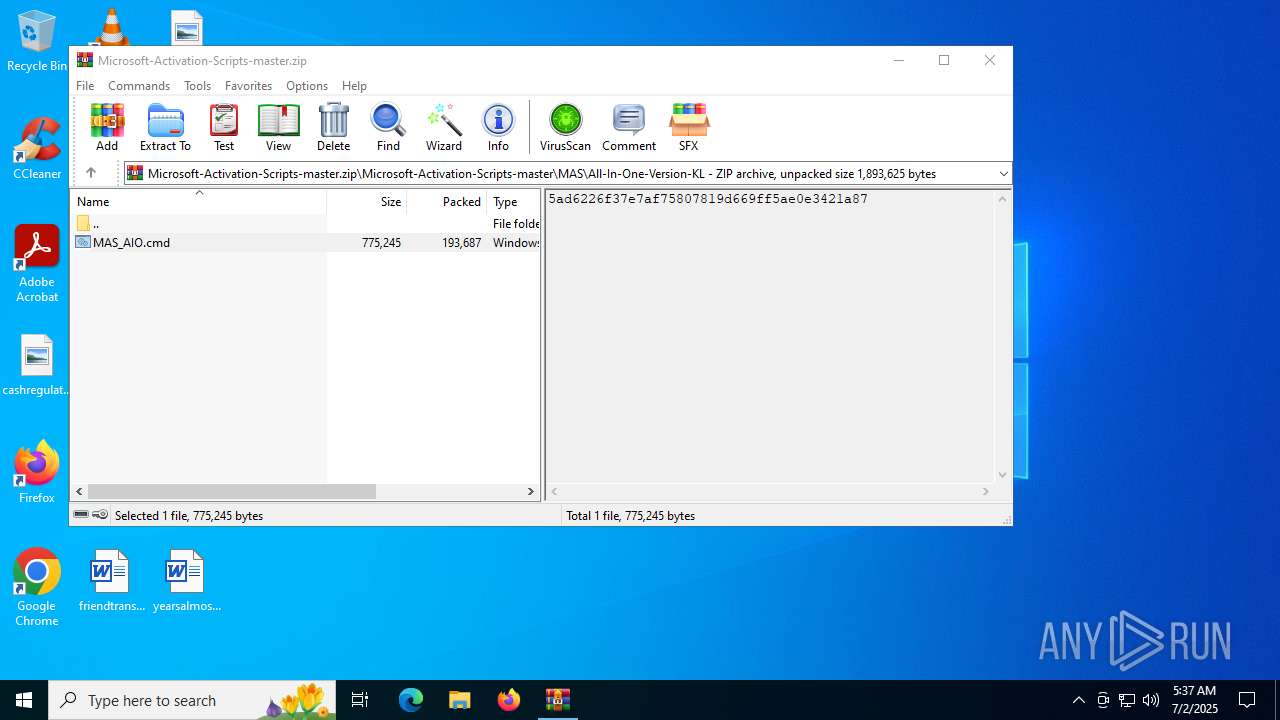
| File name: | Microsoft-Activation-Scripts-master.zip |
| Full analysis: | https://app.any.run/tasks/30c735f3-8fa3-48df-a5dc-64d747989e0a |
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2025, 05:37:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 4B1E6AB264CCA09E85C89E1F484761F2 |
| SHA1: | 1438077440F89DEE6EA9E9913351AB62231C1673 |
| SHA256: | B14DB0C28487D8F3EF043AF25489233C7719C1E6EA950B09AE38C34C1569B069 |
| SSDEEP: | 24576:pD5nJqS522wbbO/rvUezlyH61fqD8p8YCgDLBwkP5d:pVnJqS522wbbO/rvUeZ0AfqD8p8YC6LL |
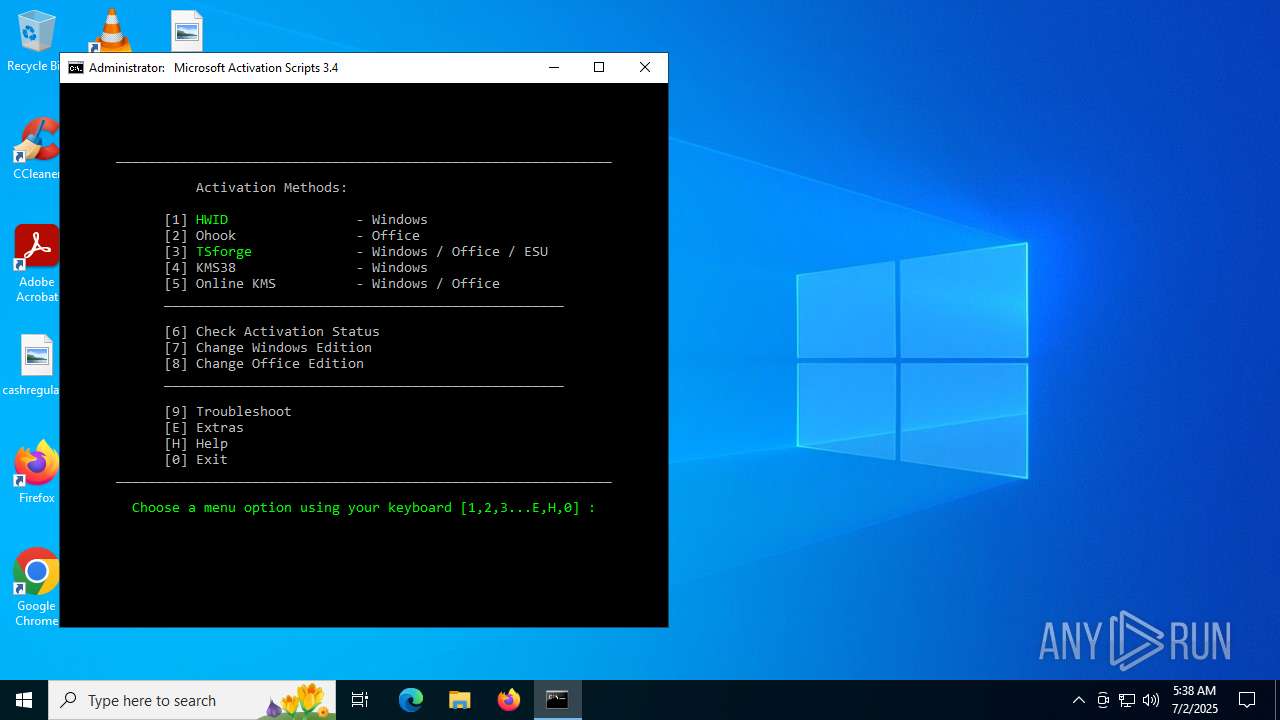
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7100)
SUSPICIOUS
Windows service management via SC.EXE
- sc.exe (PID: 3028)
- sc.exe (PID: 4920)
- sc.exe (PID: 5528)
- sc.exe (PID: 4932)
- sc.exe (PID: 6520)
- sc.exe (PID: 6264)
- sc.exe (PID: 4788)
- sc.exe (PID: 5564)
- sc.exe (PID: 4764)
- sc.exe (PID: 6228)
- sc.exe (PID: 1976)
- sc.exe (PID: 6684)
- sc.exe (PID: 3948)
- sc.exe (PID: 6772)
- sc.exe (PID: 728)
- sc.exe (PID: 6348)
- sc.exe (PID: 2612)
- sc.exe (PID: 2272)
- sc.exe (PID: 2132)
- sc.exe (PID: 1216)
- sc.exe (PID: 6956)
- sc.exe (PID: 5900)
- sc.exe (PID: 724)
- sc.exe (PID: 6536)
- sc.exe (PID: 7164)
- sc.exe (PID: 1508)
- sc.exe (PID: 5548)
- sc.exe (PID: 4868)
- sc.exe (PID: 2040)
- sc.exe (PID: 5952)
- sc.exe (PID: 3028)
- sc.exe (PID: 4644)
- sc.exe (PID: 3704)
- sc.exe (PID: 3656)
- sc.exe (PID: 6516)
- sc.exe (PID: 7080)
- sc.exe (PID: 4160)
Starts SC.EXE for service management
- cmd.exe (PID: 888)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 5744)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 888)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 5744)
Application launched itself
- cmd.exe (PID: 888)
- cmd.exe (PID: 4552)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 436)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 3820)
- powershell.exe (PID: 3400)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4552)
- cmd.exe (PID: 888)
- powershell.exe (PID: 6224)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 436)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 3820)
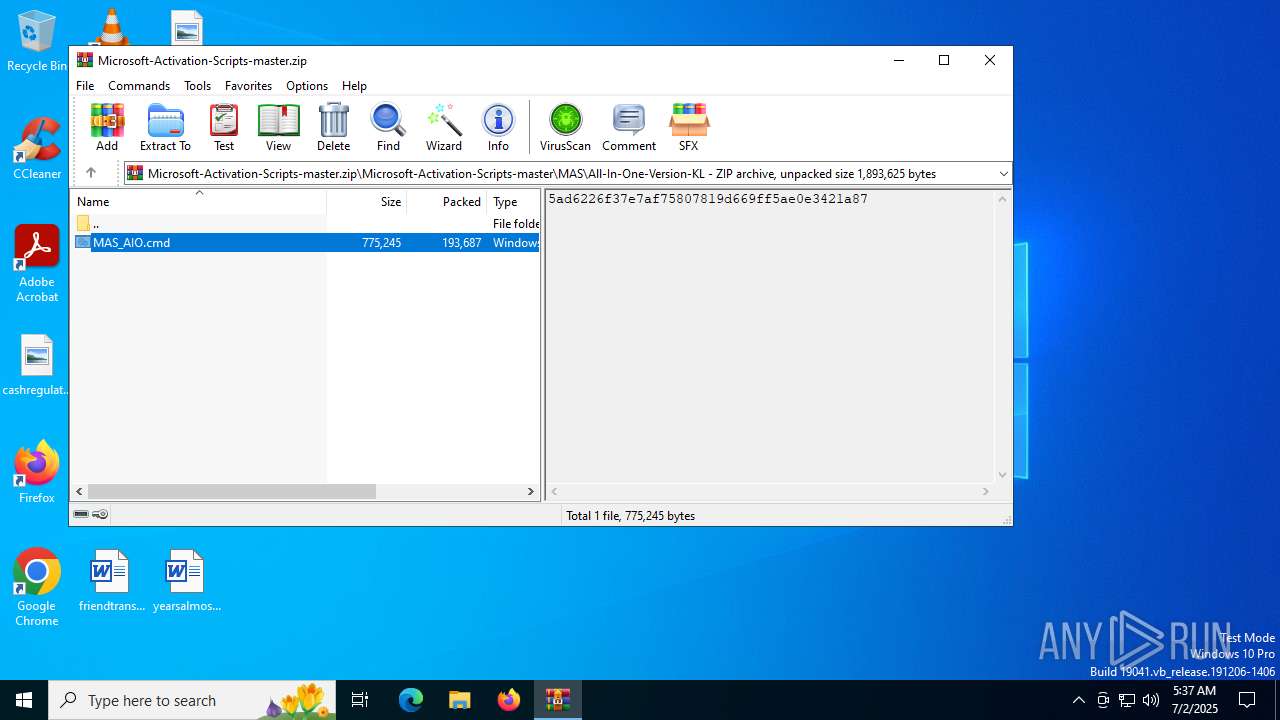
Executing commands from ".cmd" file
- cmd.exe (PID: 888)
- powershell.exe (PID: 6224)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 5744)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 888)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 1356)
- cmd.exe (PID: 436)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 4820)
- powershell.exe (PID: 3400)
- cmd.exe (PID: 6748)
- cmd.exe (PID: 5432)
Executes script without checking the security policy
- powershell.exe (PID: 6224)
- powershell.exe (PID: 6492)
- powershell.exe (PID: 188)
- powershell.exe (PID: 3924)
- powershell.exe (PID: 5620)
- powershell.exe (PID: 6344)
- powershell.exe (PID: 3400)
- powershell.exe (PID: 4112)
- powershell.exe (PID: 6400)
- powershell.exe (PID: 1052)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 2276)
- powershell.exe (PID: 2212)
- powershell.exe (PID: 5020)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 888)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 1356)
- cmd.exe (PID: 436)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 4820)
- powershell.exe (PID: 3400)
- cmd.exe (PID: 6748)
- cmd.exe (PID: 5432)
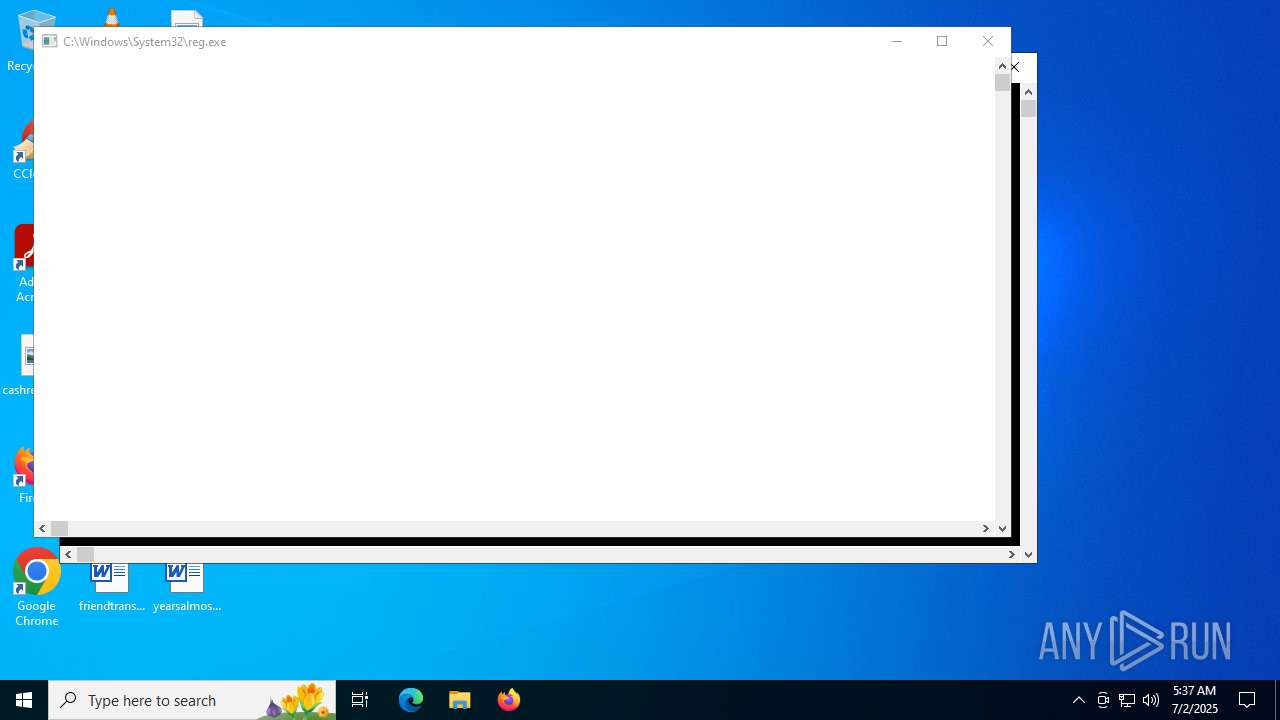
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7060)
- cmd.exe (PID: 5744)
Hides command output
- cmd.exe (PID: 6344)
- cmd.exe (PID: 1356)
- cmd.exe (PID: 4312)
- cmd.exe (PID: 3756)
- cmd.exe (PID: 6748)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 2128)
- cmd.exe (PID: 4100)
- cmd.exe (PID: 4748)
- cmd.exe (PID: 5432)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 6344)
- cmd.exe (PID: 1356)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 4820)
- cmd.exe (PID: 6748)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 6344)
- cmd.exe (PID: 1356)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 6748)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 6492)
- powershell.exe (PID: 188)
- powershell.exe (PID: 5620)
- powershell.exe (PID: 4112)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6492)
- powershell.exe (PID: 188)
- powershell.exe (PID: 5620)
- powershell.exe (PID: 4112)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 6492)
- powershell.exe (PID: 188)
- powershell.exe (PID: 5620)
- powershell.exe (PID: 4112)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 5444)
- cmd.exe (PID: 5744)
Probably file/command deobfuscation
- cmd.exe (PID: 4820)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 3756)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 3400)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5744)
- cmd.exe (PID: 2128)
- cmd.exe (PID: 4100)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 5744)
INFO
Manual execution by a user
- cmd.exe (PID: 888)
Checks operating system version
- cmd.exe (PID: 888)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 5744)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 6492)
- powershell.exe (PID: 188)
- powershell.exe (PID: 5620)
- powershell.exe (PID: 4112)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6492)
- powershell.exe (PID: 188)
- powershell.exe (PID: 5620)
- powershell.exe (PID: 4112)
Starts MODE.COM to configure console settings
- mode.com (PID: 1300)
- mode.com (PID: 6472)
- mode.com (PID: 2664)
- mode.com (PID: 6388)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6492)
- powershell.exe (PID: 188)
- powershell.exe (PID: 5620)
- powershell.exe (PID: 4112)
Checks supported languages
- mode.com (PID: 1300)
- mode.com (PID: 6388)
- mode.com (PID: 6472)
- mode.com (PID: 2664)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5924)
- WMIC.exe (PID: 4948)
- WMIC.exe (PID: 2664)
- WMIC.exe (PID: 4700)
- WMIC.exe (PID: 6492)
- WMIC.exe (PID: 2612)
- WMIC.exe (PID: 4400)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:06:03 06:07:58 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Microsoft-Activation-Scripts-master/ |
Total processes
387
Monitored processes
251
Malicious processes
12
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "C:\Users\admin\Desktop\MAS_AIO.cmd" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c "if ($PSVersionTable.PSEdition -ne 'Core') {$f=[io.file]::ReadAllText('C:\Users\admin\Desktop\MAS_AIO.cmd') -split ':pstst';iex ($f[1])}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sppsvc.exe" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | C:\WINDOWS\System32\cmd.exe /c echo prompt $E | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | C:\WINDOWS\System32\cmd.exe /c "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c $AssemblyBuilder = [AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1); $ModuleBuilder = $AssemblyBuilder.DefineDynamicModule(2, $False); $TypeBuilder = $ModuleBuilder.DefineType(0); [void]$TypeBuilder.DefinePInvokeMethod('SLGetWindowsInformationDWORD', 'slc.dll', 'Public, Static', 1, [int], @([String], [int].MakeByRefType()), 1, 3); $Sku = 0; [void]$TypeBuilder.CreateType()::SLGetWindowsInformationDWORD('Kernel-BrandingInfo', [ref]$Sku); $Sku" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | reg query "HKU\S-1-5-20\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\PersistedTSReArmed" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 592 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\taskcache\tasks" /f Path /s | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 592 | reg query HKLM\SYSTEM\CurrentControlSet\Services\LicenseManager /v Description | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo prompt $E " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
84 183
Read events
84 162
Write events
21
Delete events
0
Modification events
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Microsoft-Activation-Scripts-master.zip | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
1
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6224 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rolh5nff.24a.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3924 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ufek1kul.ewt.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6492 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ms11dtb1.vay.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3924 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mq0fmts0.0nr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 188 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_53ha0mht.oyz.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bvaiel1e.t2m.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6128 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yb5op4fu.jxb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5620 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kgs2z3bg.xv5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6128 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ahrillt5.fkv.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4112 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uo0s5hl0.zo2.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6700 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
640 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
640 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2192 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6700 | svchost.exe | 40.126.31.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6700 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
activated.win |
| unknown |
updatecheck34.activated.win |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |