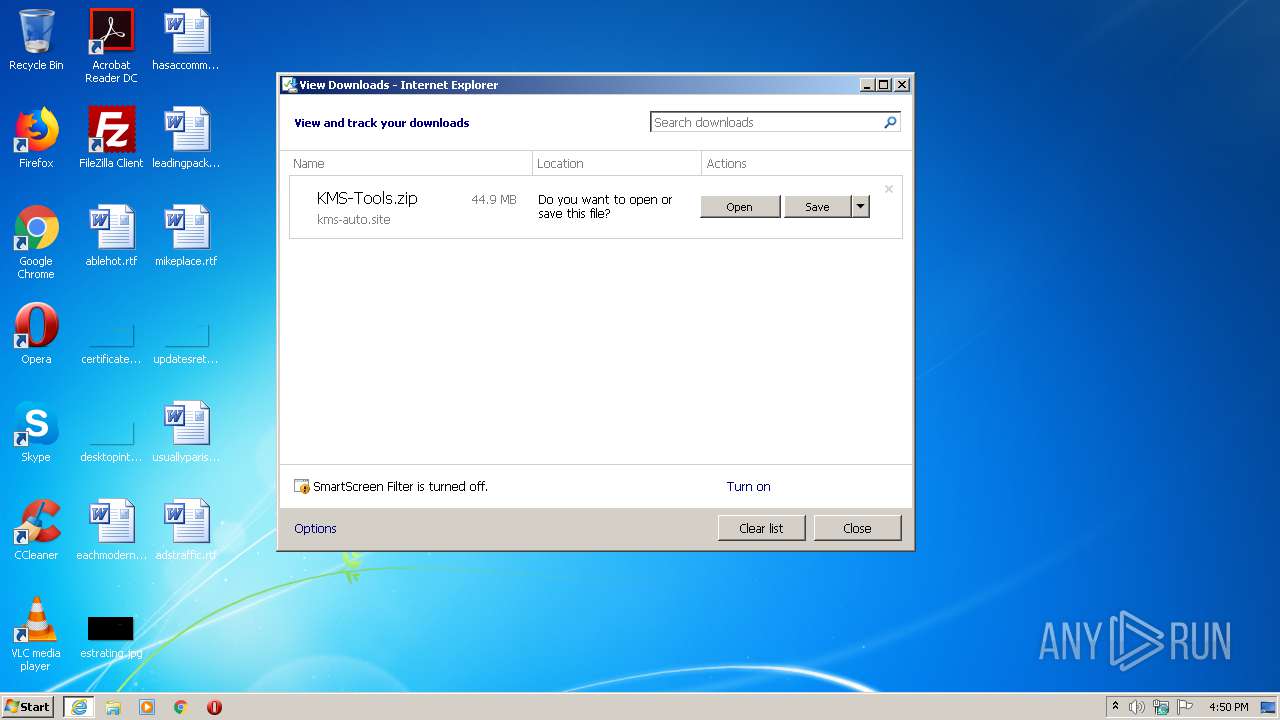
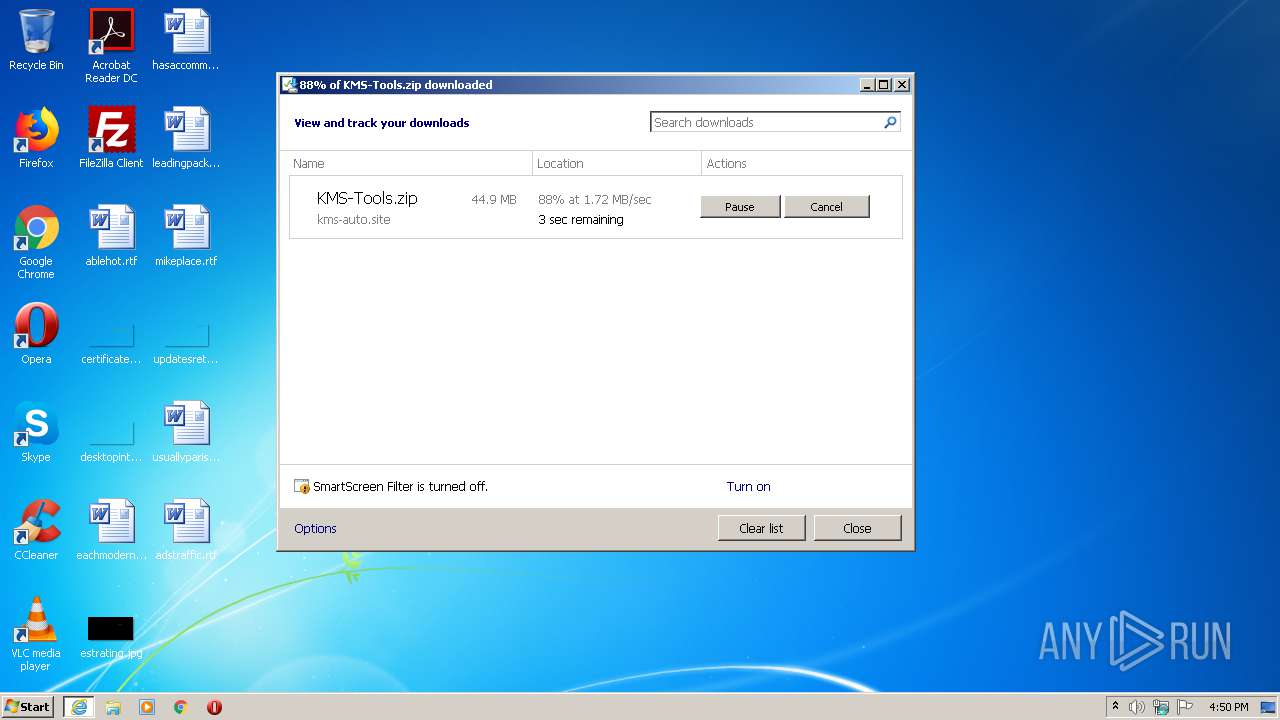
| URL: | https://kms-auto.site/wp-content/uploads/2018/12/KMS-Tools.zip |
| Full analysis: | https://app.any.run/tasks/f8d05f8b-f954-48bc-be58-9b1c195d0052 |
| Verdict: | Suspicious activity |
| Analysis date: | June 19, 2020, 15:49:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4979D274DE8EE89797387545AD842577 |
| SHA1: | 1177AF892B60FFDDE9DD5B1427B0522134EA3FB2 |
| SHA256: | B0FD60624E5443CF9E35714C70403897AB09D13830E297E6D612C76E144CDA9F |
| SSDEEP: | 3:N8NPEQRQWXVYAQyXbnDJW4n:2tQkVYAZLn84n |
MALICIOUS
Application was dropped or rewritten from another process
- 7zaxxx.exe (PID: 3804)
- KMSAuto.exe (PID: 3980)
SUSPICIOUS
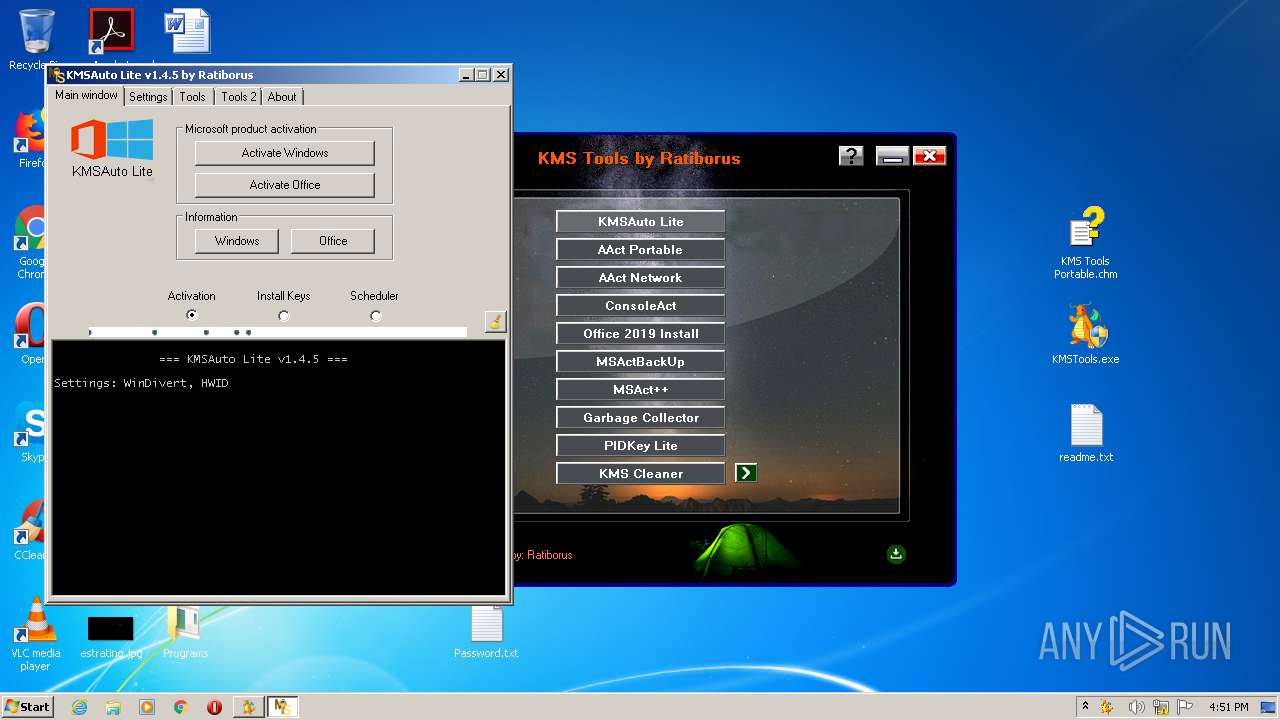
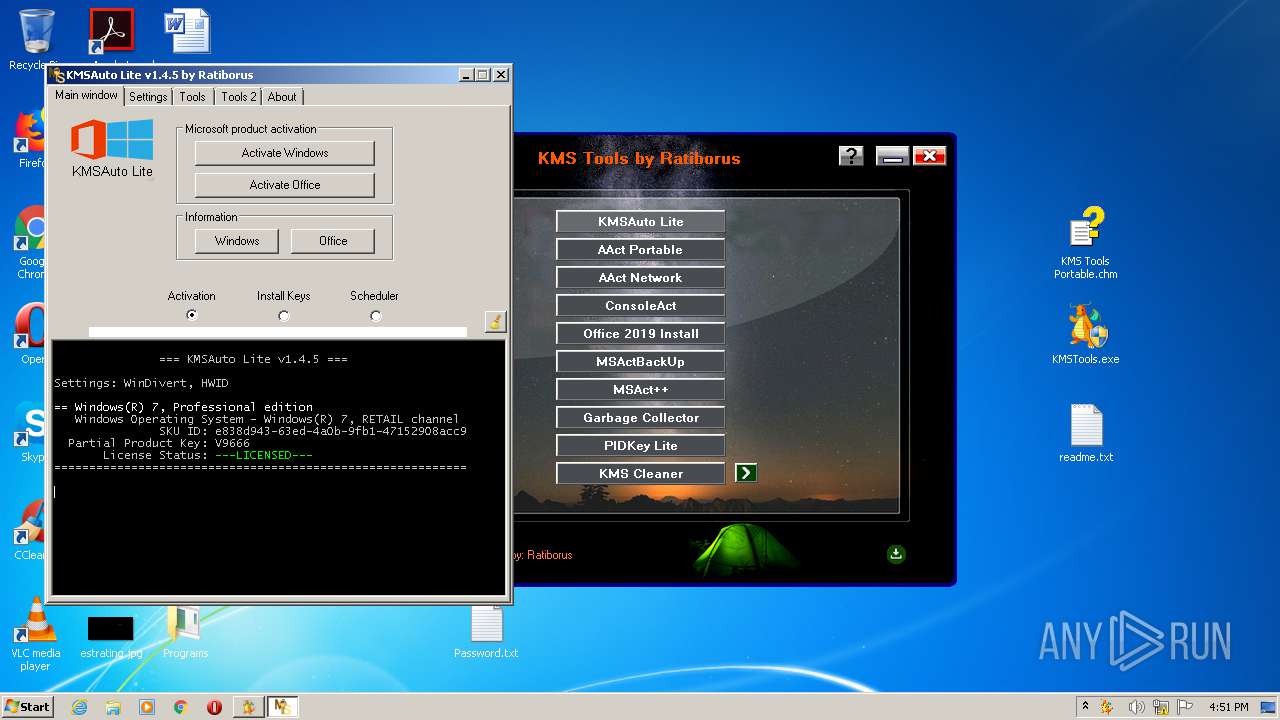
Starts CMD.EXE for commands execution
- KMSTools.exe (PID: 2876)
- KMSAuto.exe (PID: 3980)
Executable content was dropped or overwritten
- KMSTools.exe (PID: 2876)
- 7zaxxx.exe (PID: 3804)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 1604)
- cmd.exe (PID: 3948)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2416)
Reads Internet Cache Settings
- iexplore.exe (PID: 2416)
- iexplore.exe (PID: 1640)
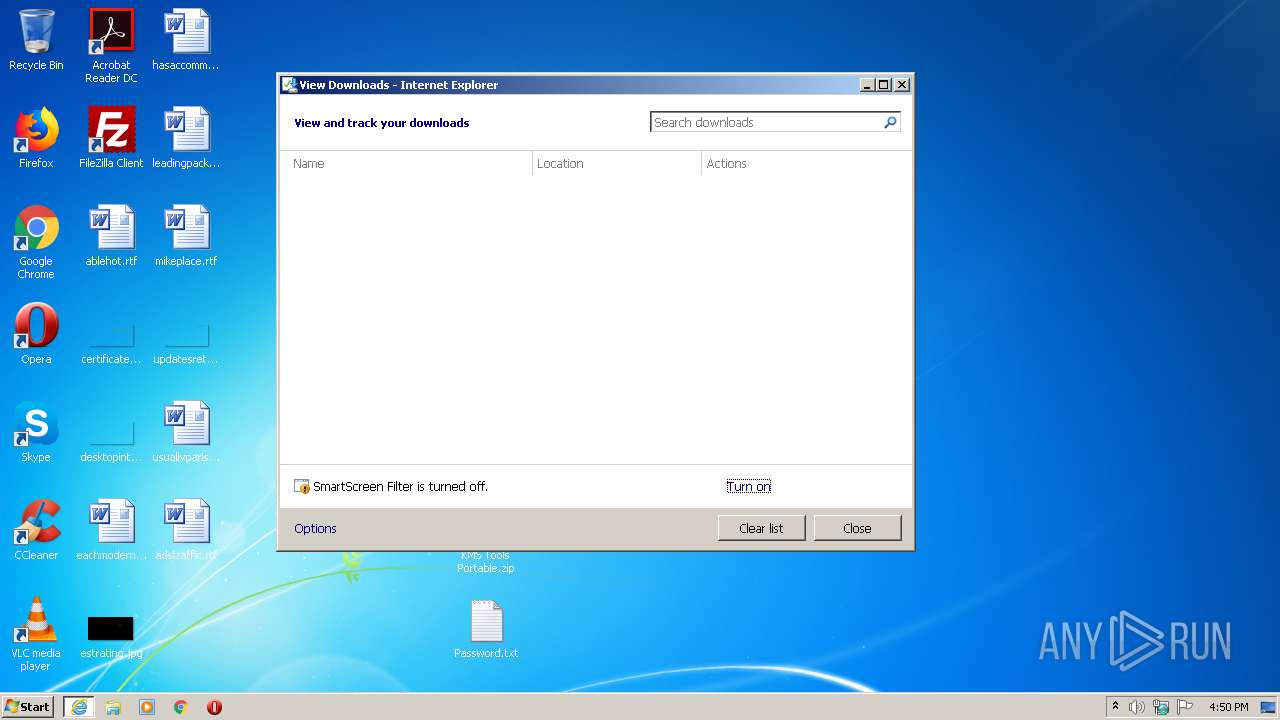
Application launched itself
- iexplore.exe (PID: 2416)
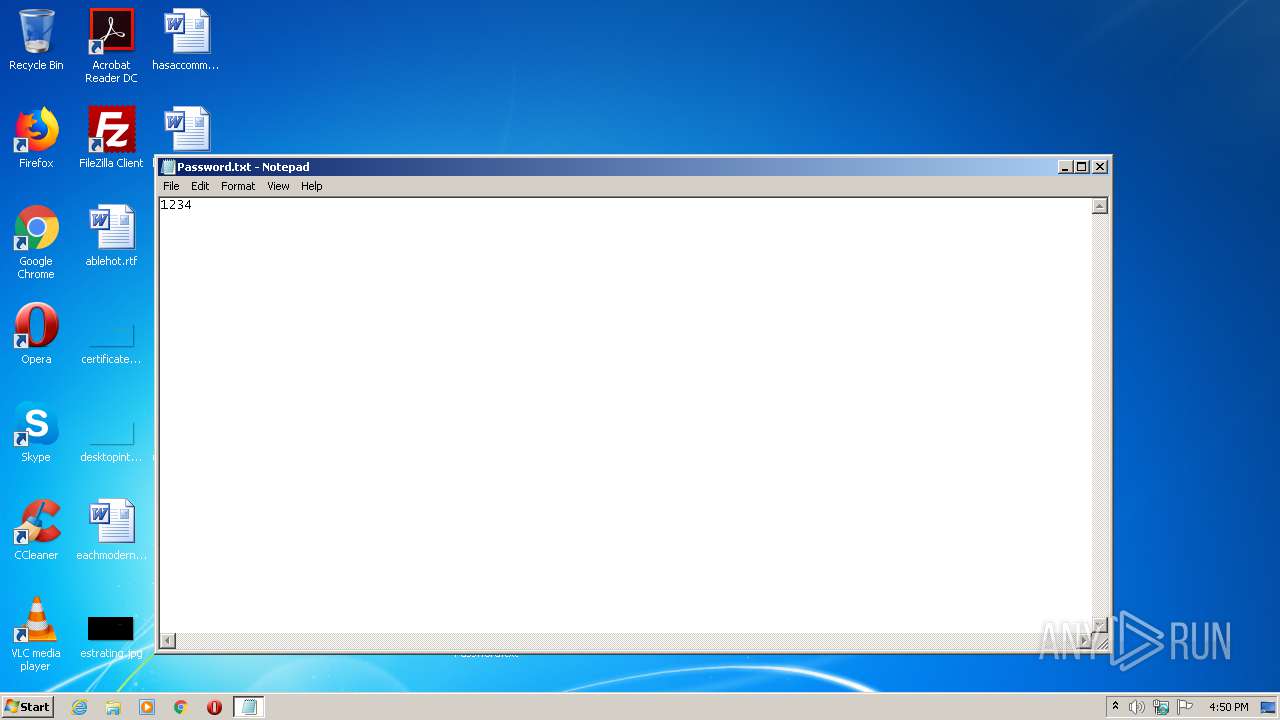
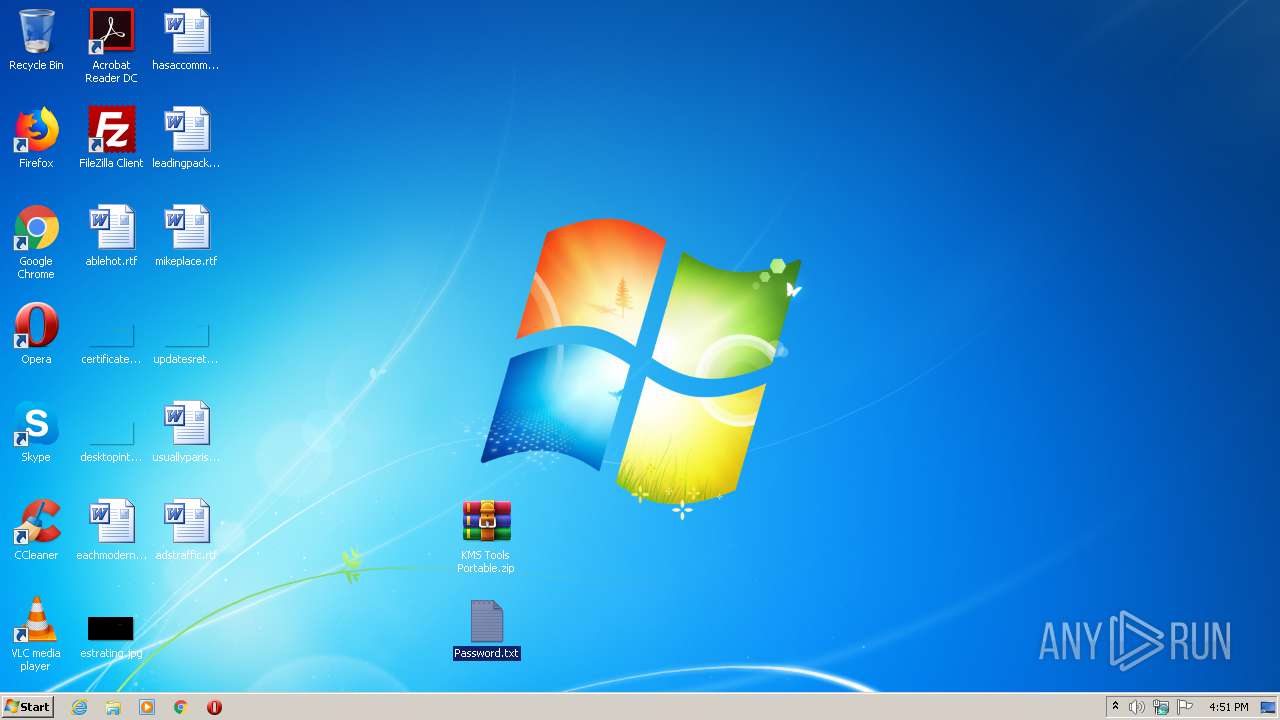
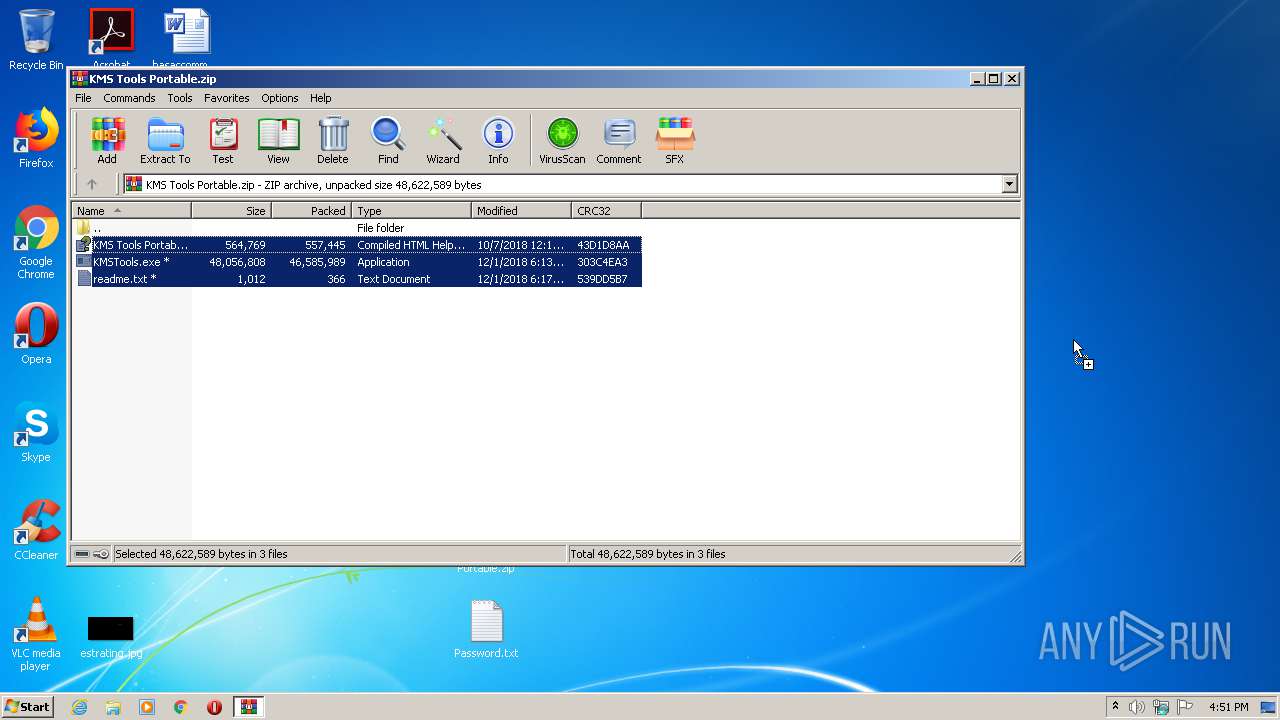
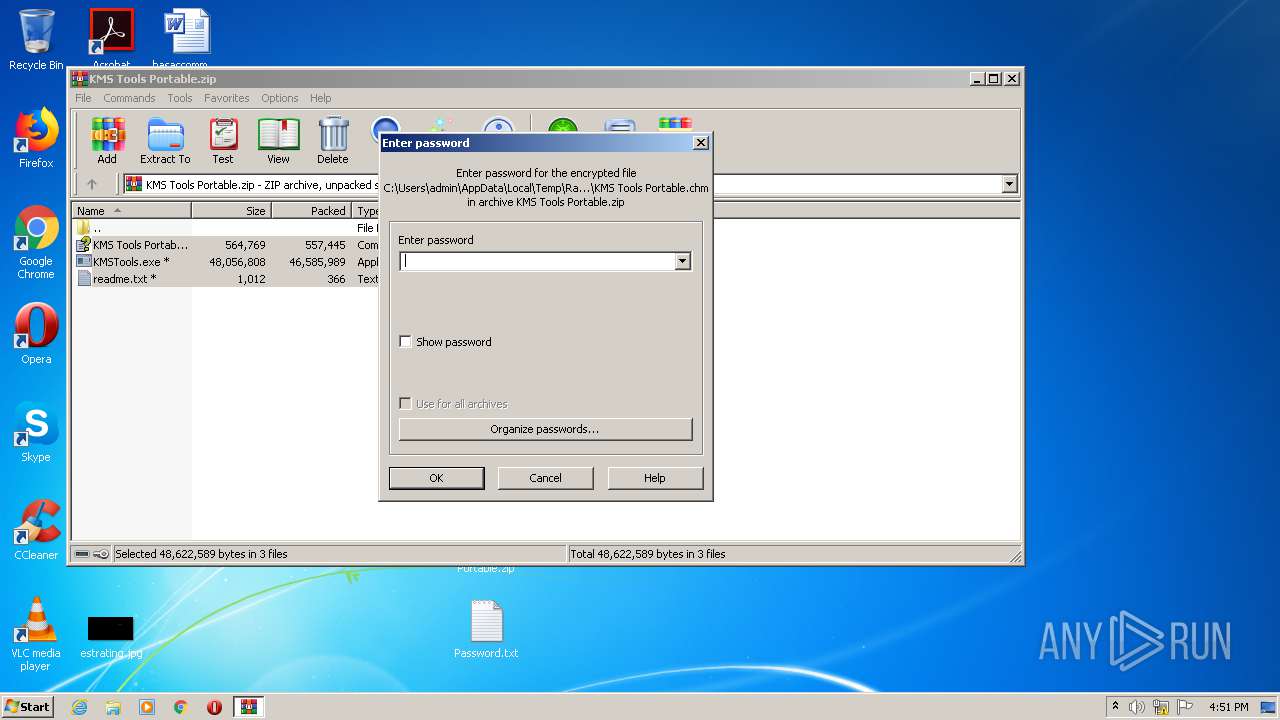
Manual execution by user
- NOTEPAD.EXE (PID: 2484)
- KMSTools.exe (PID: 2180)
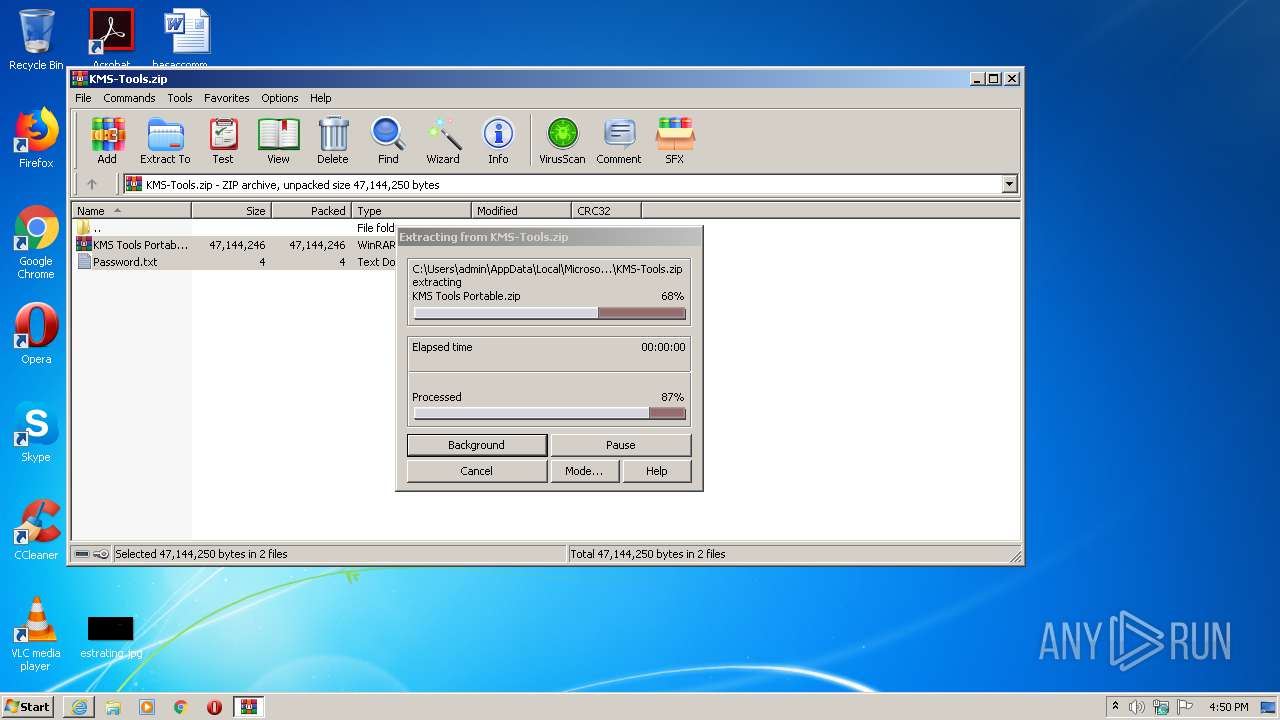
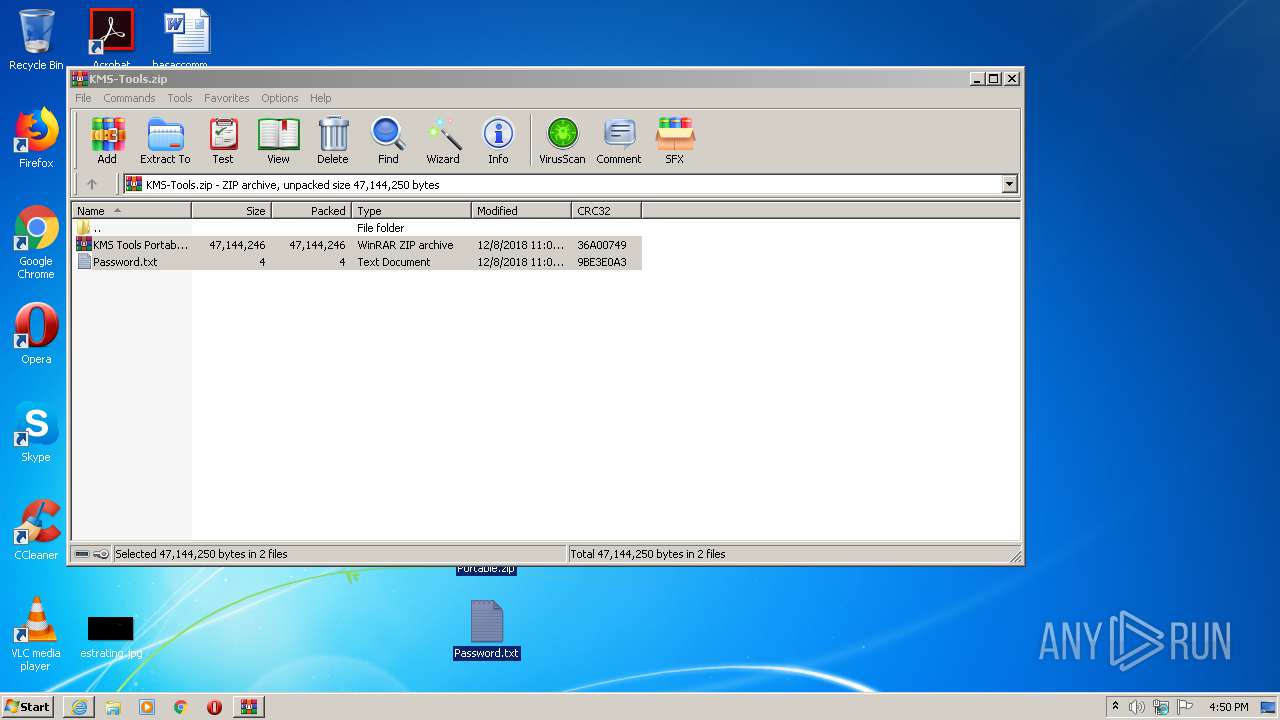
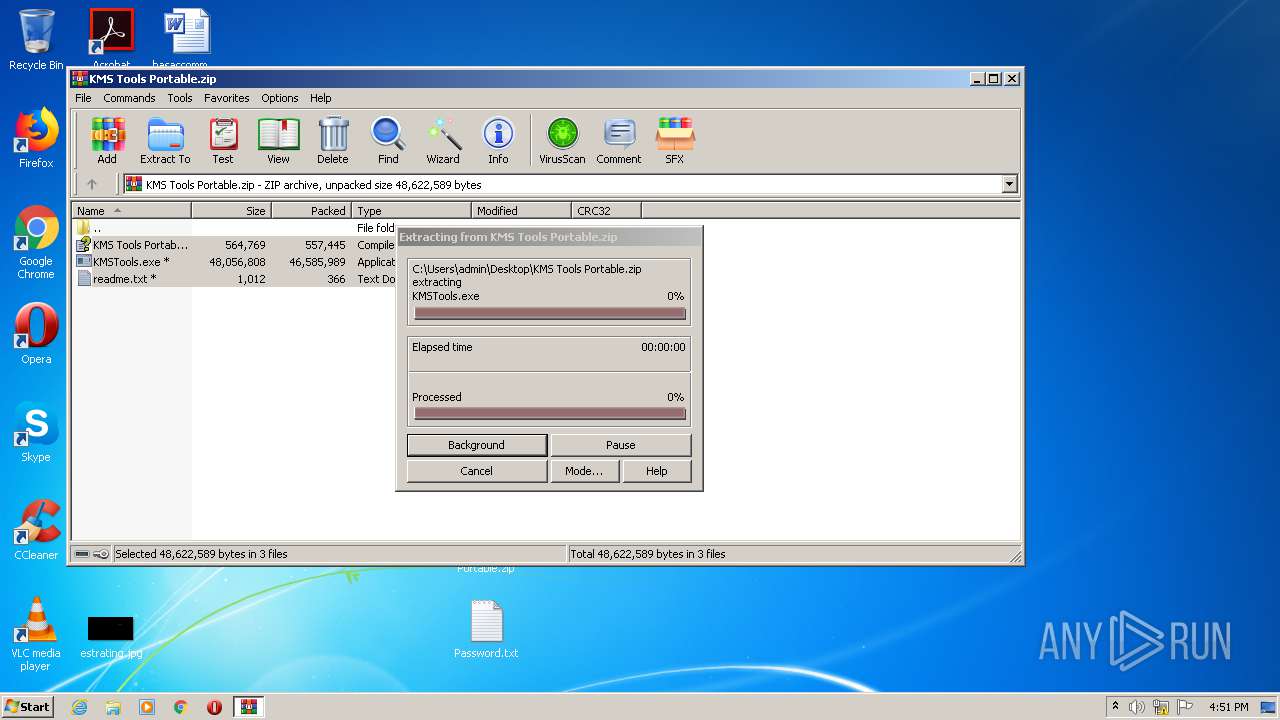
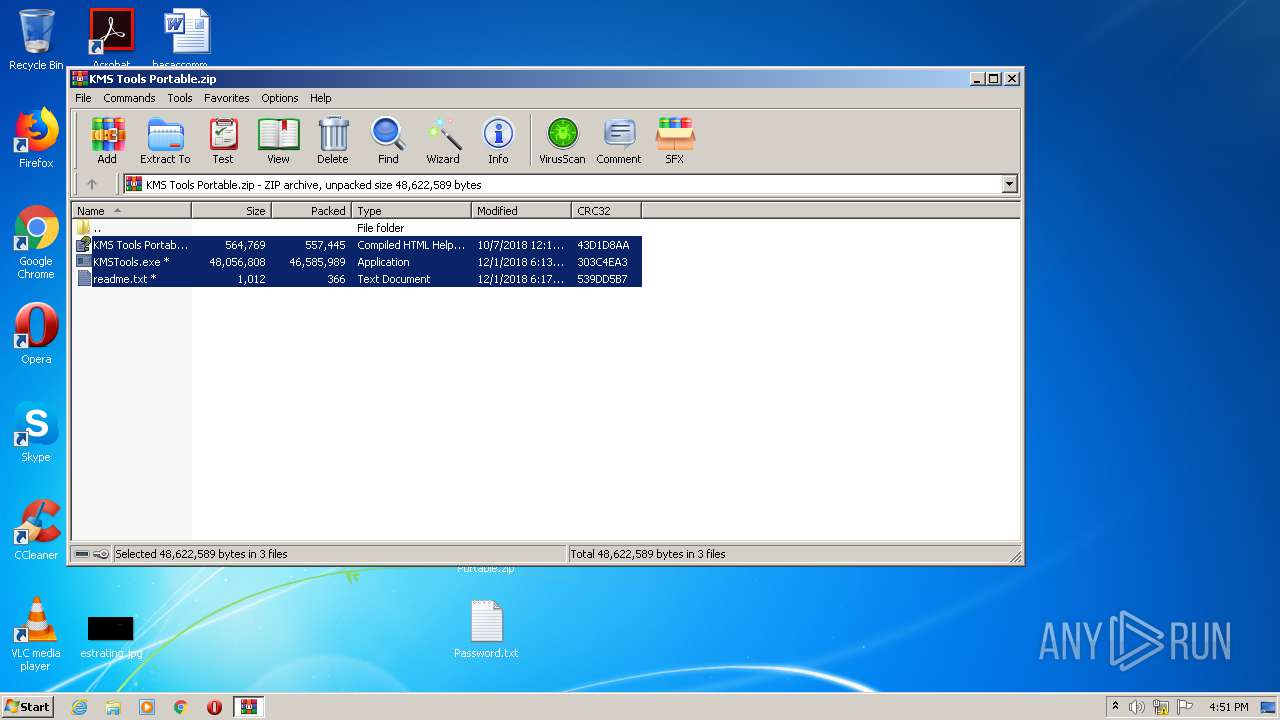
- WinRAR.exe (PID: 2252)
- KMSTools.exe (PID: 2876)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
15
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1604 | "C:\Windows\System32\cmd.exe" /c wmic path SoftwareLicensingProduct where (Name LIKE 'Windows%%' And PartialProductKey is Not NULL) get Name, Description, ID, PartialProductKey, LicenseStatus, KeyManagementServiceMachine, KeyManagementServicePort, VLRenewalInterval, GracePeriodRemaining, KeyManagementServicePort, KeyManagementServiceProductKeyID /FORMAT:List | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2416 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2180 | "C:\Users\admin\Desktop\KMSTools.exe" | C:\Users\admin\Desktop\KMSTools.exe | — | explorer.exe | |||||||||||
User: admin Company: Ratiborus Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\KMS Tools Portable.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\KMS-Tools.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Internet Explorer\iexplore.exe" https://kms-auto.site/wp-content/uploads/2018/12/KMS-Tools.zip | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2484 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Password.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2812 | "C:\Windows\System32\cmd.exe" /c copy C:\Windows\system32\Tasks\KMSAuto "C:\Users\admin\AppData\Local\Temp\KMSAuto.tmp" /Y | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2860 | wmic path SoftwareLicensingProduct where (Name LIKE 'Windows%%' And PartialProductKey is Not NULL) get Name, Description, ID, PartialProductKey, LicenseStatus, KeyManagementServiceMachine, KeyManagementServicePort, VLRenewalInterval, GracePeriodRemaining, KeyManagementServicePort, KeyManagementServiceProductKeyID /FORMAT:List | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2876 | "C:\Users\admin\Desktop\KMSTools.exe" | C:\Users\admin\Desktop\KMSTools.exe | explorer.exe | ||||||||||||
User: admin Company: Ratiborus Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 573
Read events
1 469
Write events
100
Delete events
4
Modification events
| (PID) Process: | (1640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1681128884 | |||
| (PID) Process: | (2416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30819921 | |||
| (PID) Process: | (2416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
4
Suspicious files
5
Text files
7
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1640 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9F4F.tmp | — | |
MD5:— | SHA256:— | |||
| 1640 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9F50.tmp | — | |
MD5:— | SHA256:— | |||
| 1640 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\KMS-Tools[1].zip | — | |
MD5:— | SHA256:— | |||
| 1640 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\KMS-Tools.zip.tlm27m0.partial | — | |
MD5:— | SHA256:— | |||
| 2416 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF69AD9F68C48DE5EE.TMP | — | |
MD5:— | SHA256:— | |||
| 2416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\KMS-Tools.zip.tlm27m0.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\KMS-Tools.zip | — | |
MD5:— | SHA256:— | |||
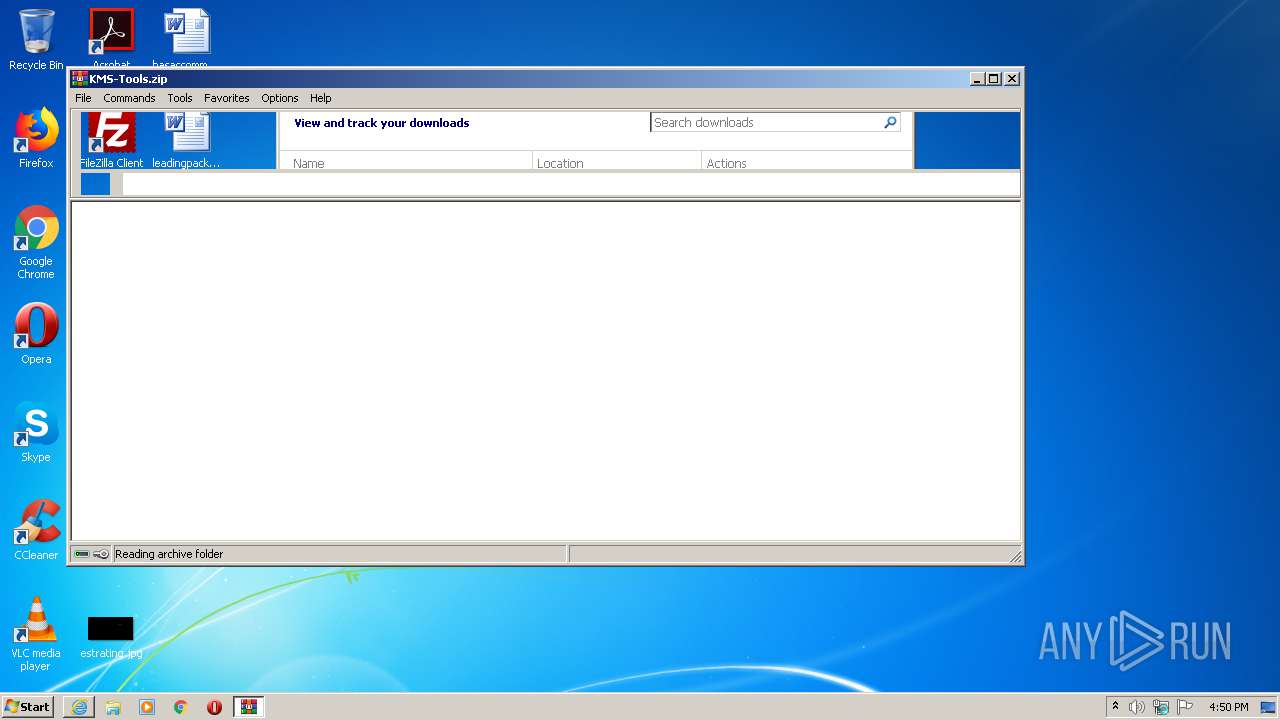
| 2372 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2372.18188\KMS Tools Portable.zip | — | |
MD5:— | SHA256:— | |||
| 2416 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFEE697E047F1BAF10.TMP | — | |
MD5:— | SHA256:— | |||
| 2416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{8FF09873-B244-11EA-82DB-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1640 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgNxS51%2BYyiWnS1yg6lytke4Qw%3D%3D | unknown | der | 527 b | whitelisted |
1640 | iexplore.exe | GET | 200 | 2.16.186.35:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1640 | iexplore.exe | 2.16.186.35:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
1640 | iexplore.exe | 87.236.16.130:443 | kms-auto.site | Beget Ltd | RU | suspicious |
1640 | iexplore.exe | 2.16.186.27:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kms-auto.site |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |