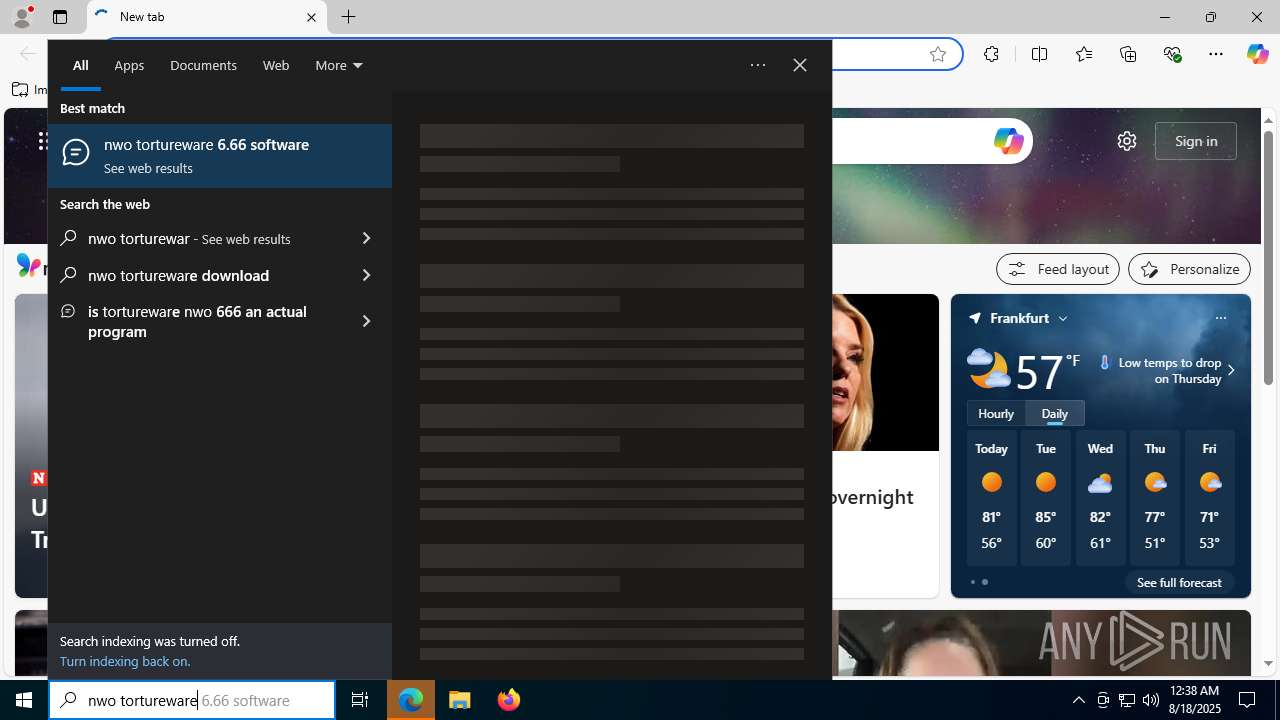
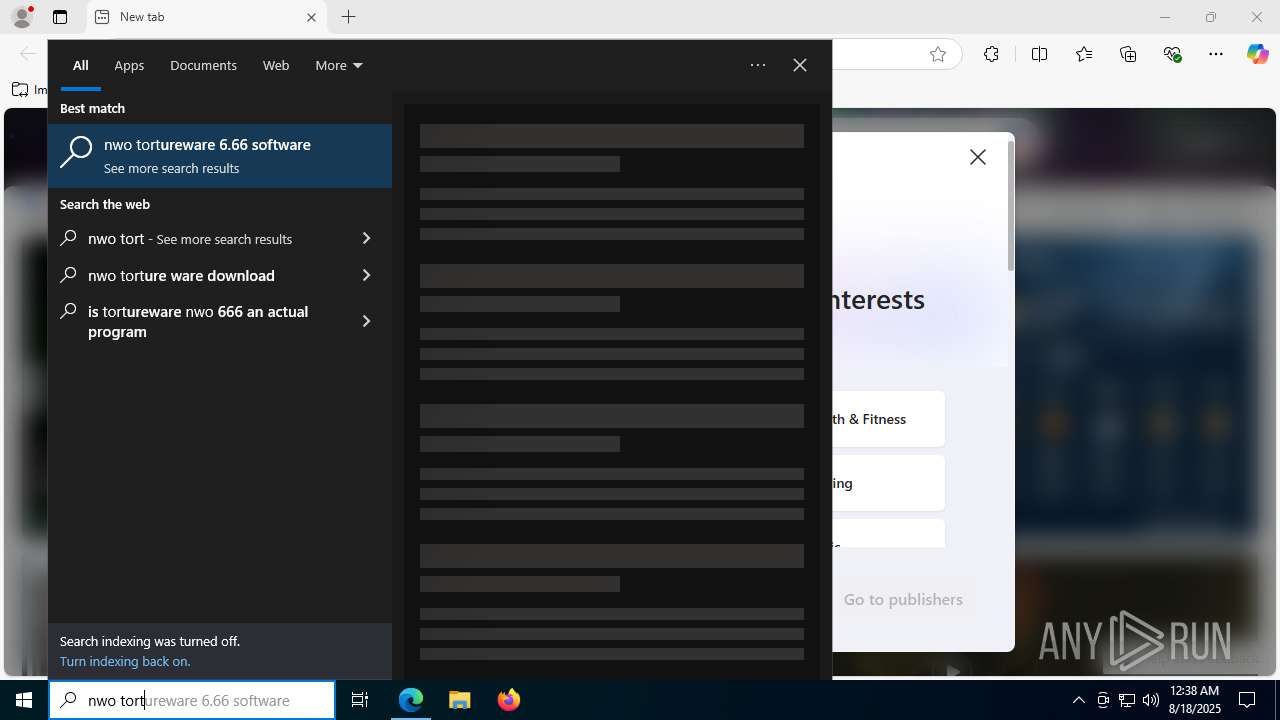
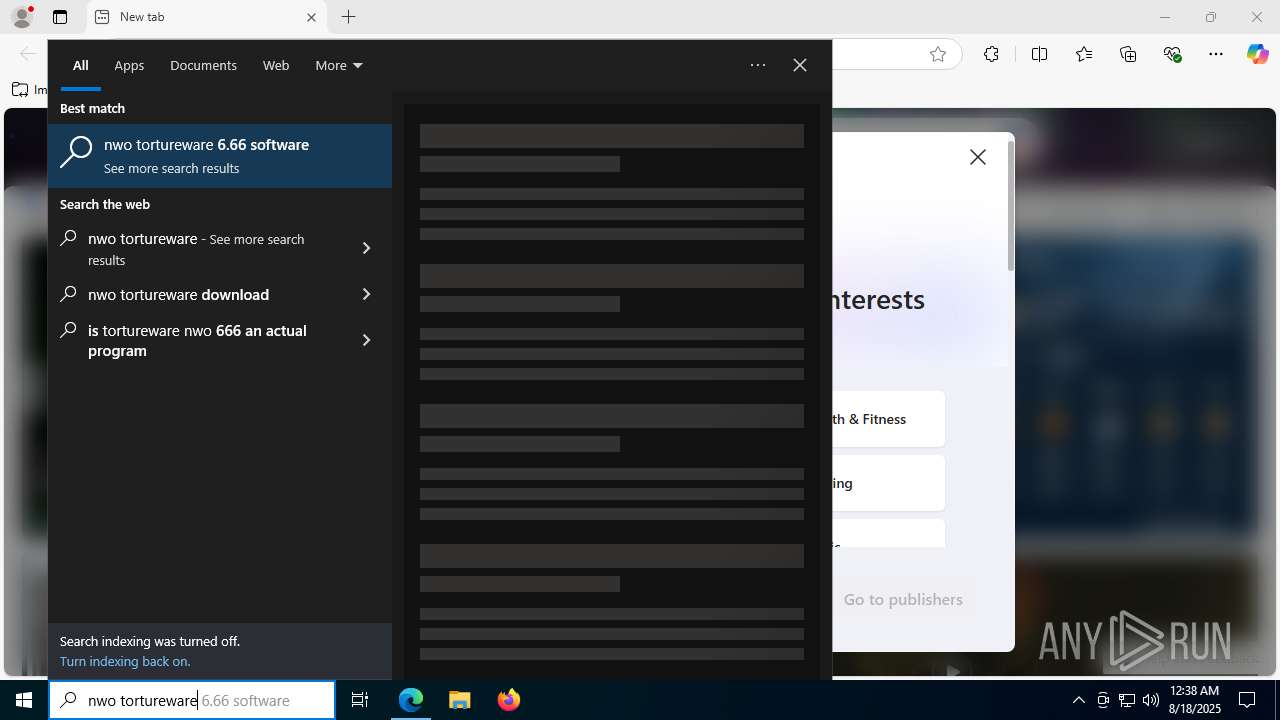
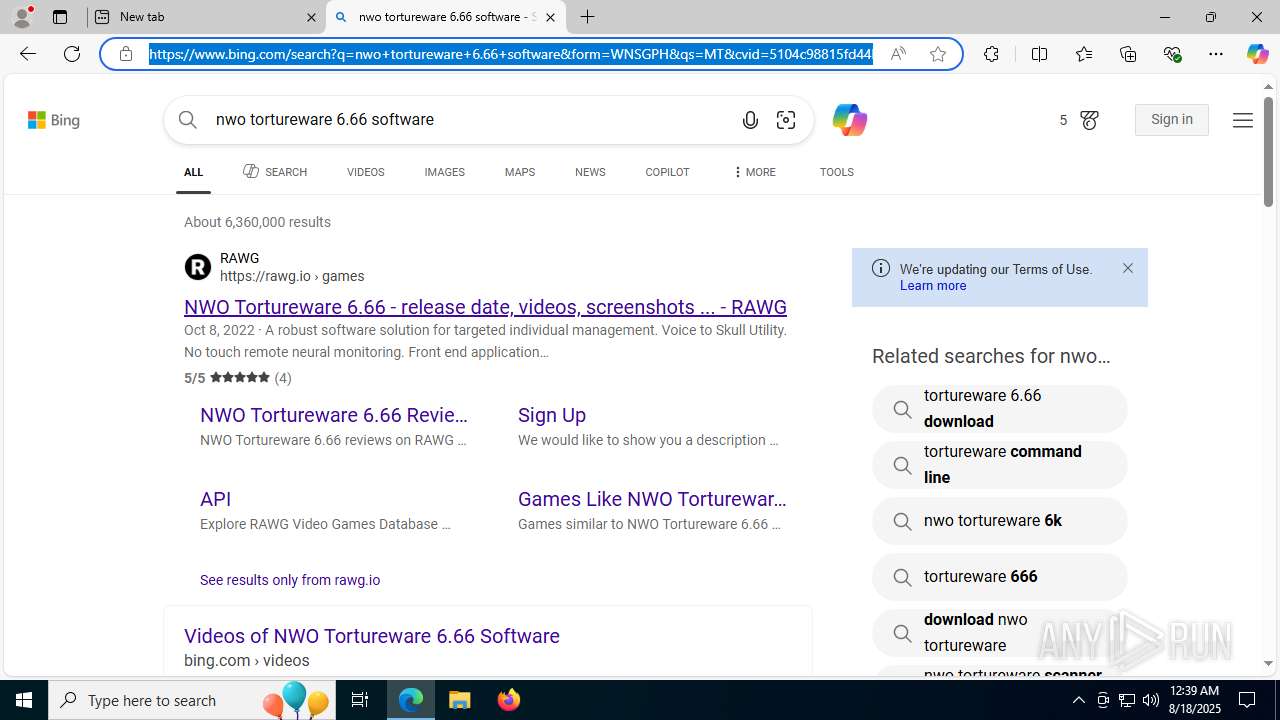
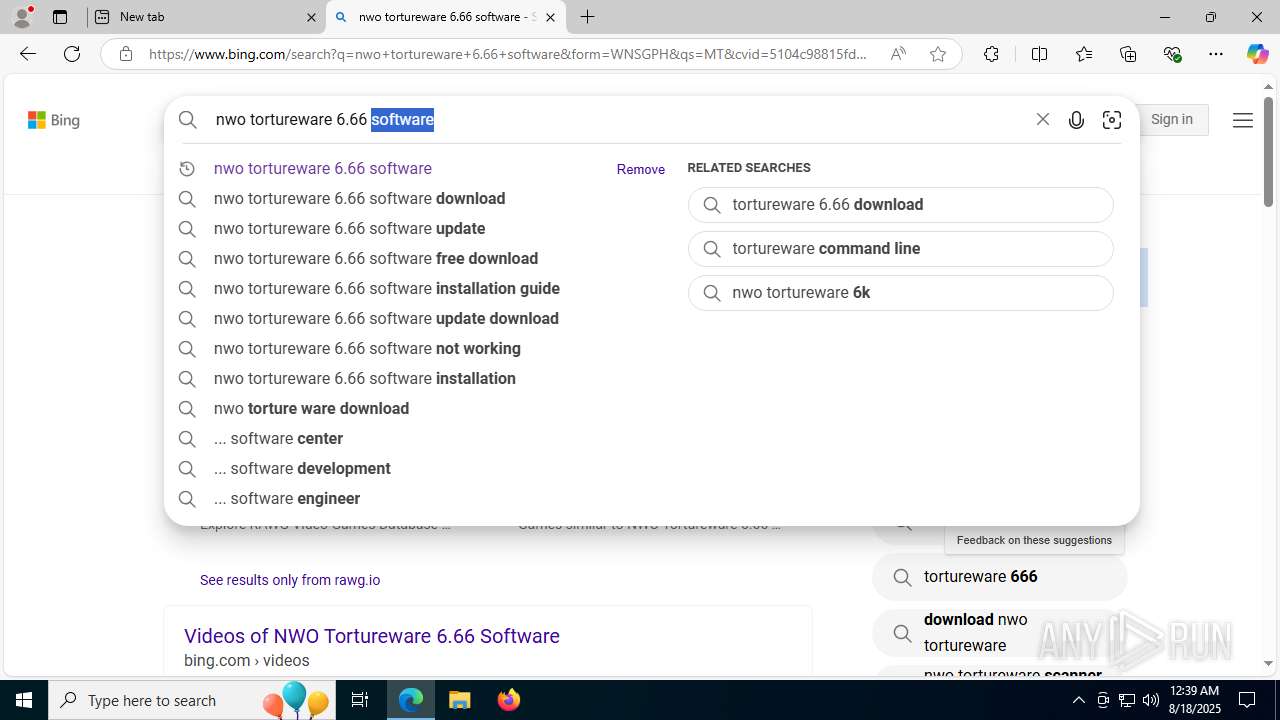
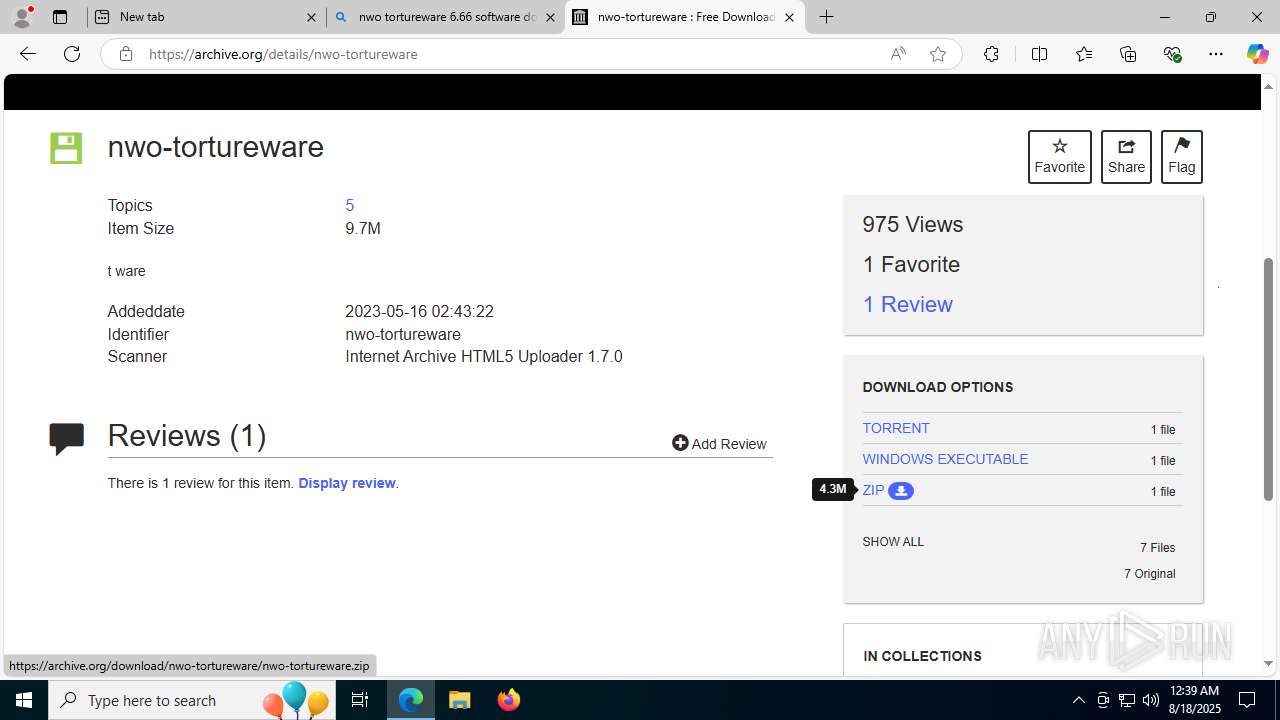
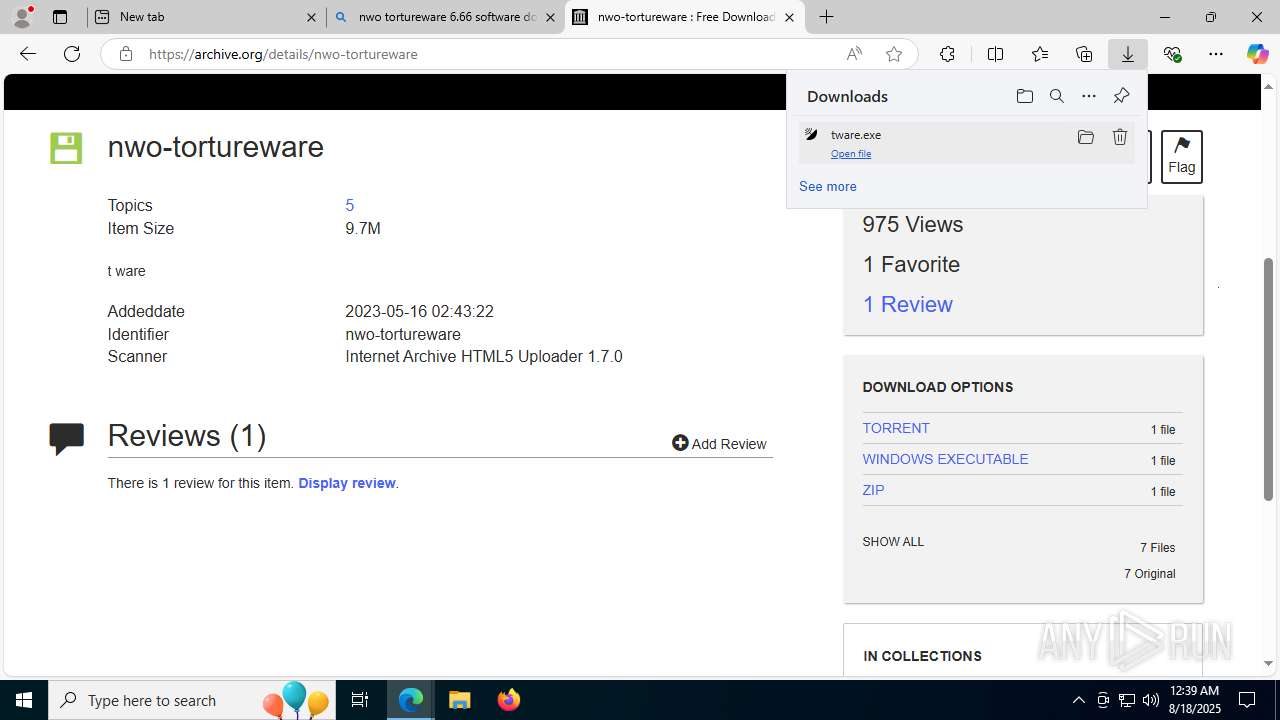
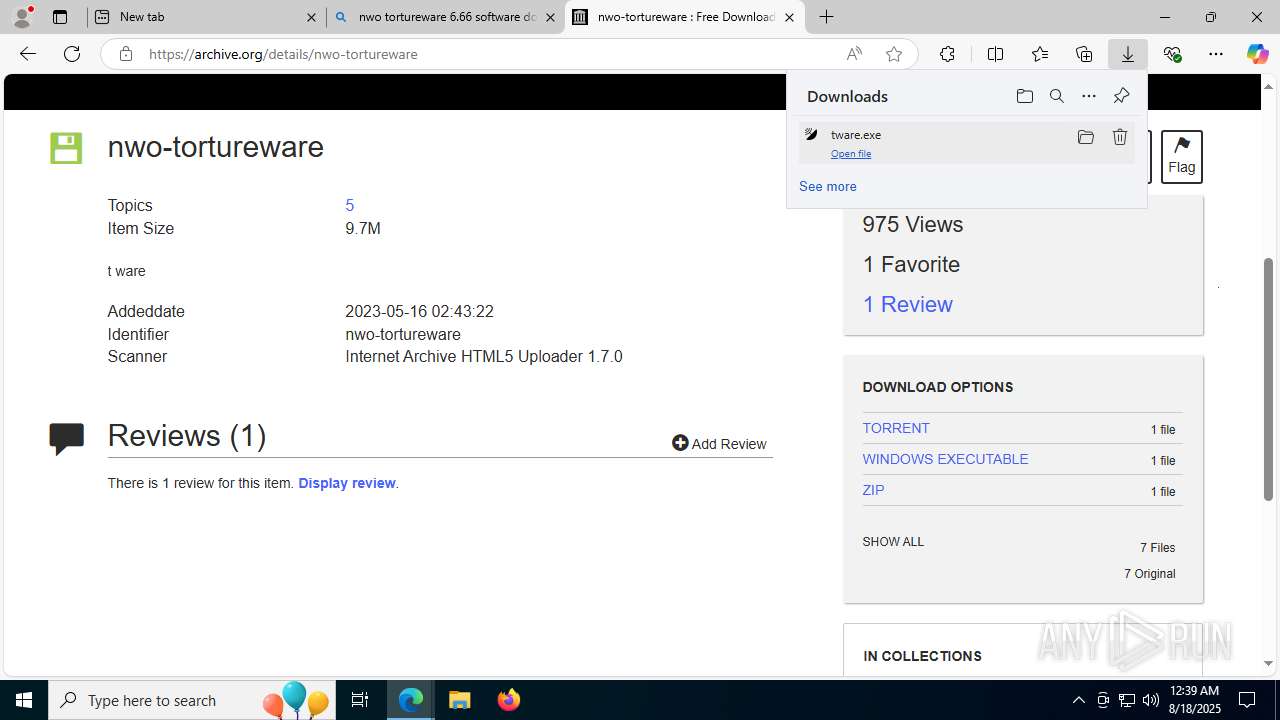
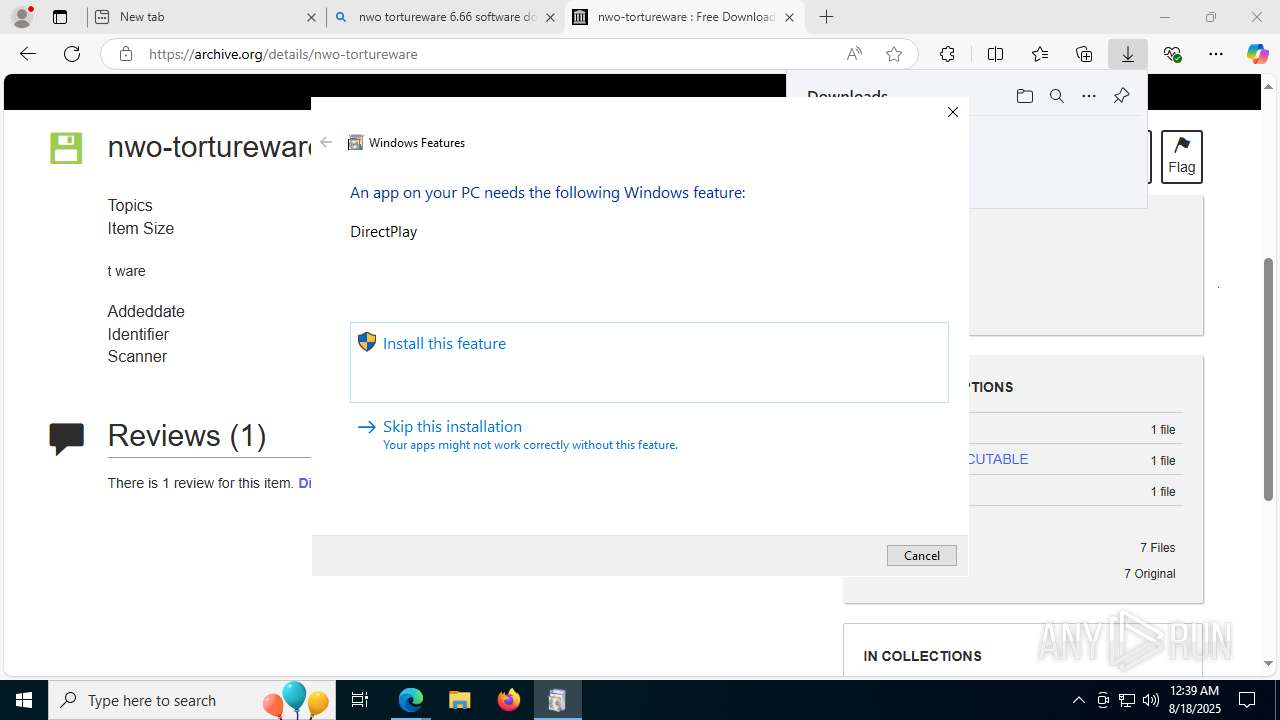
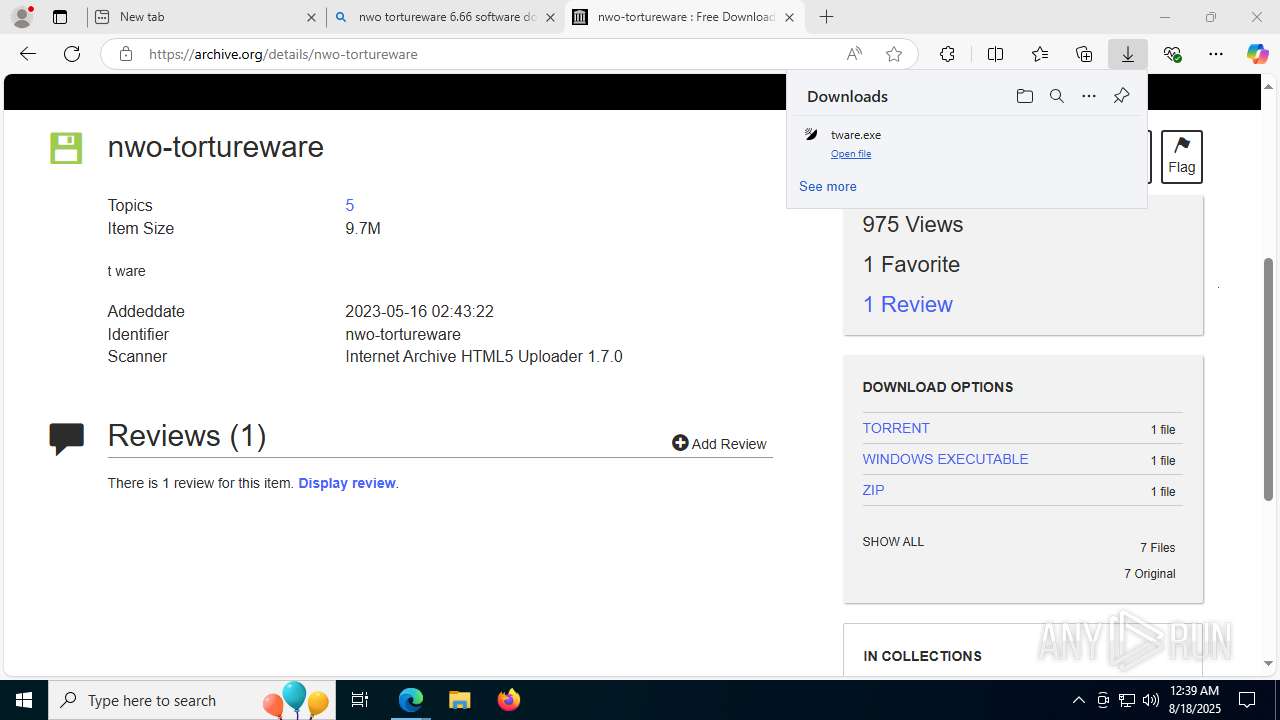
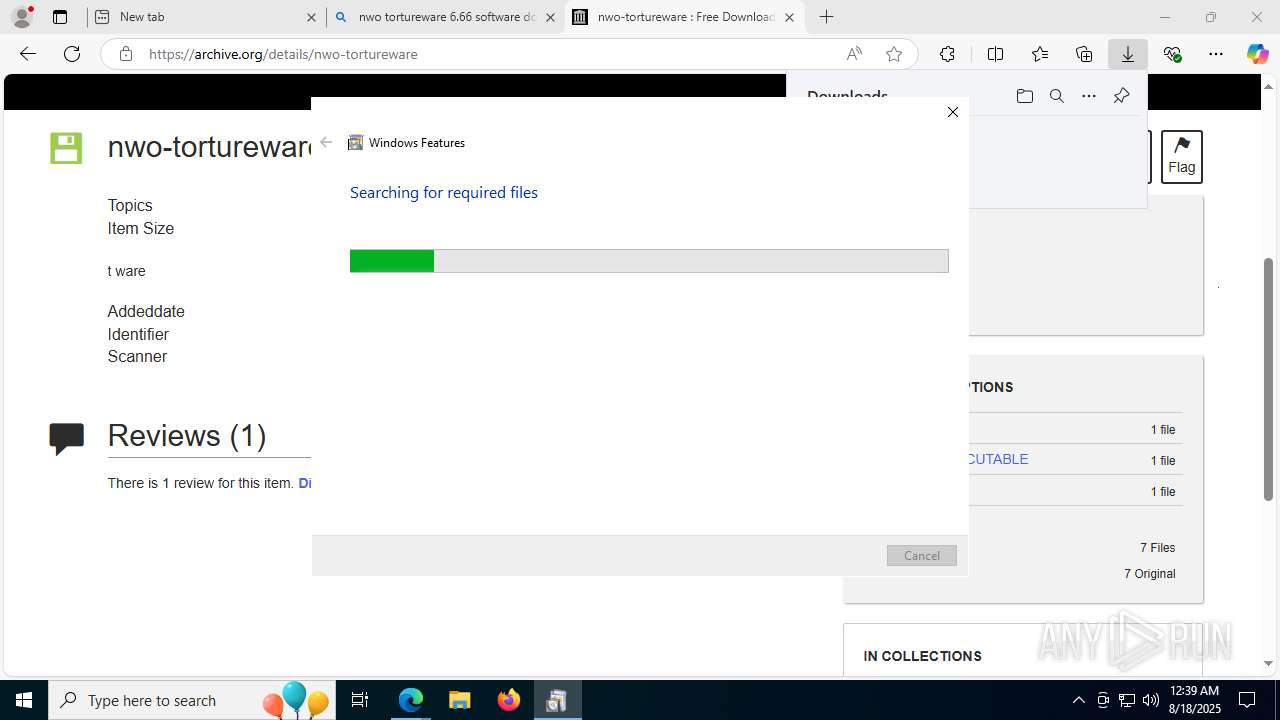
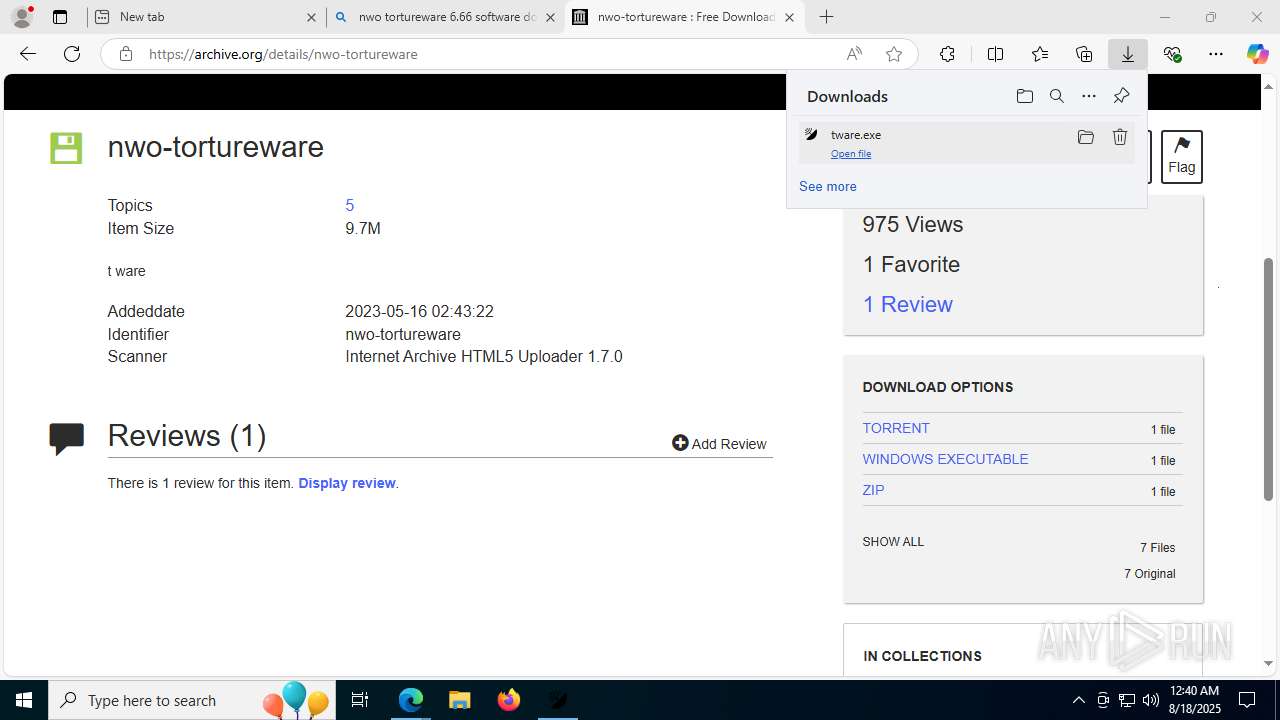
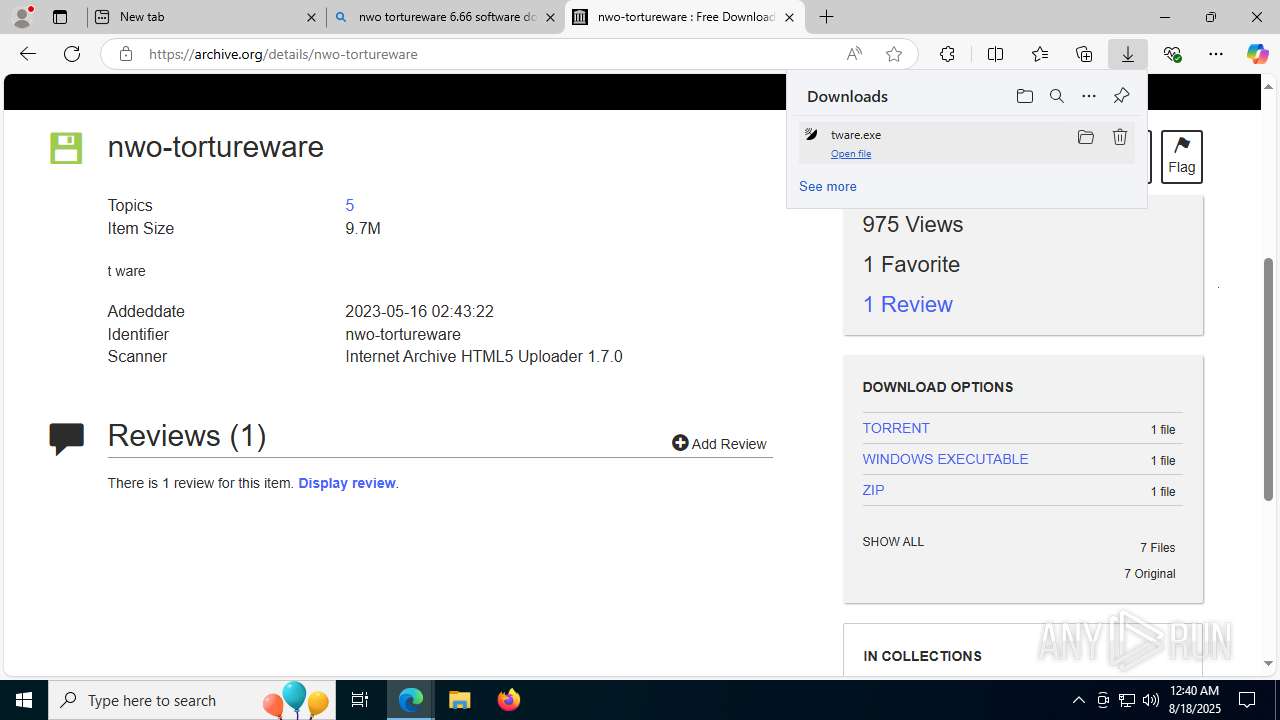
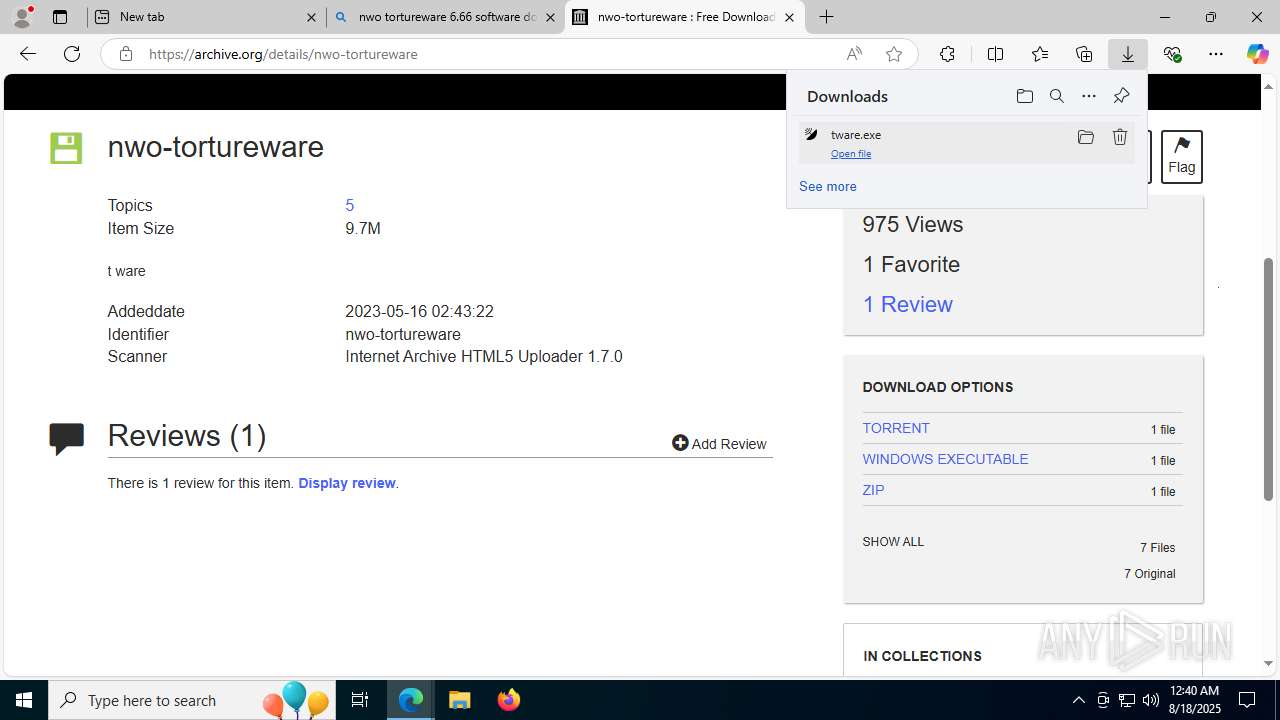
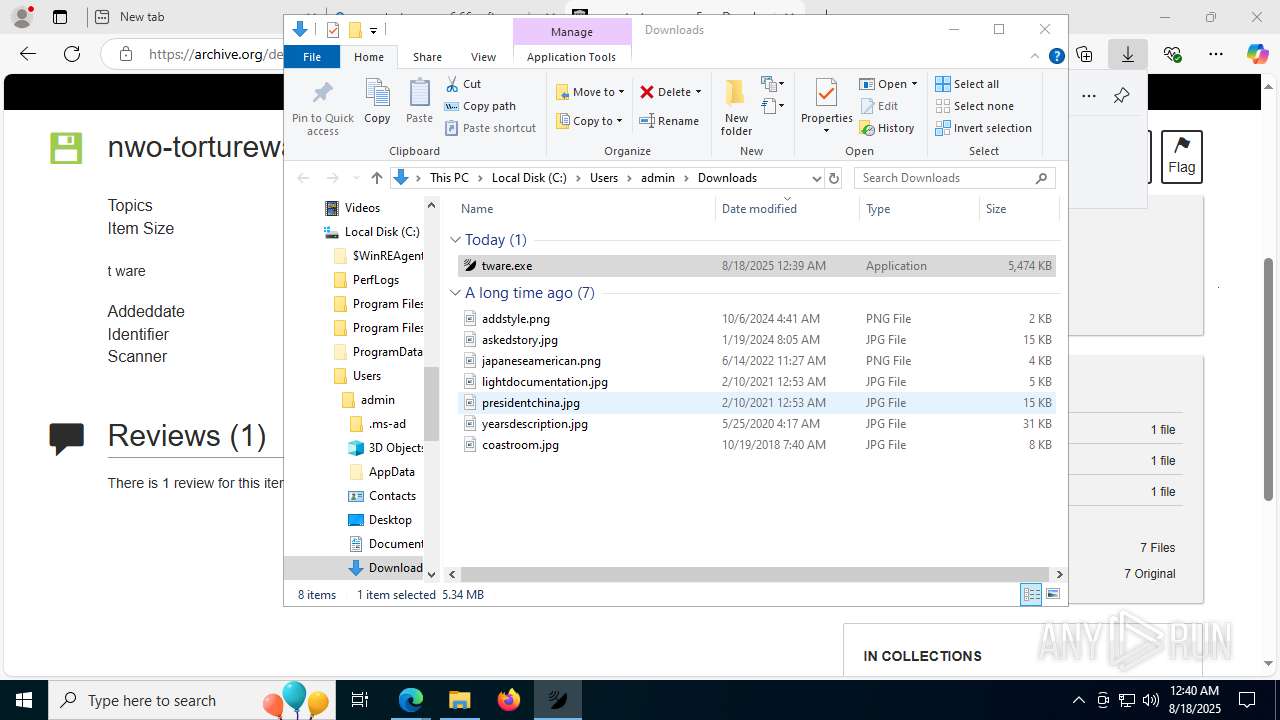
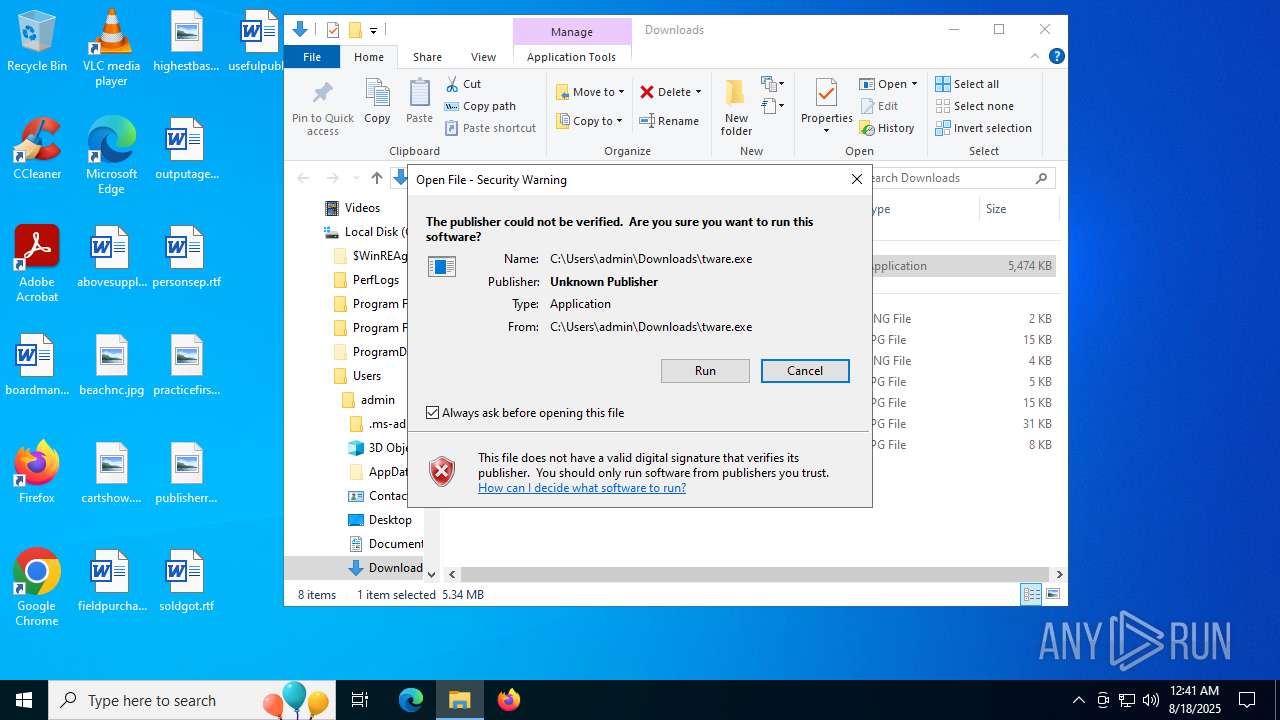
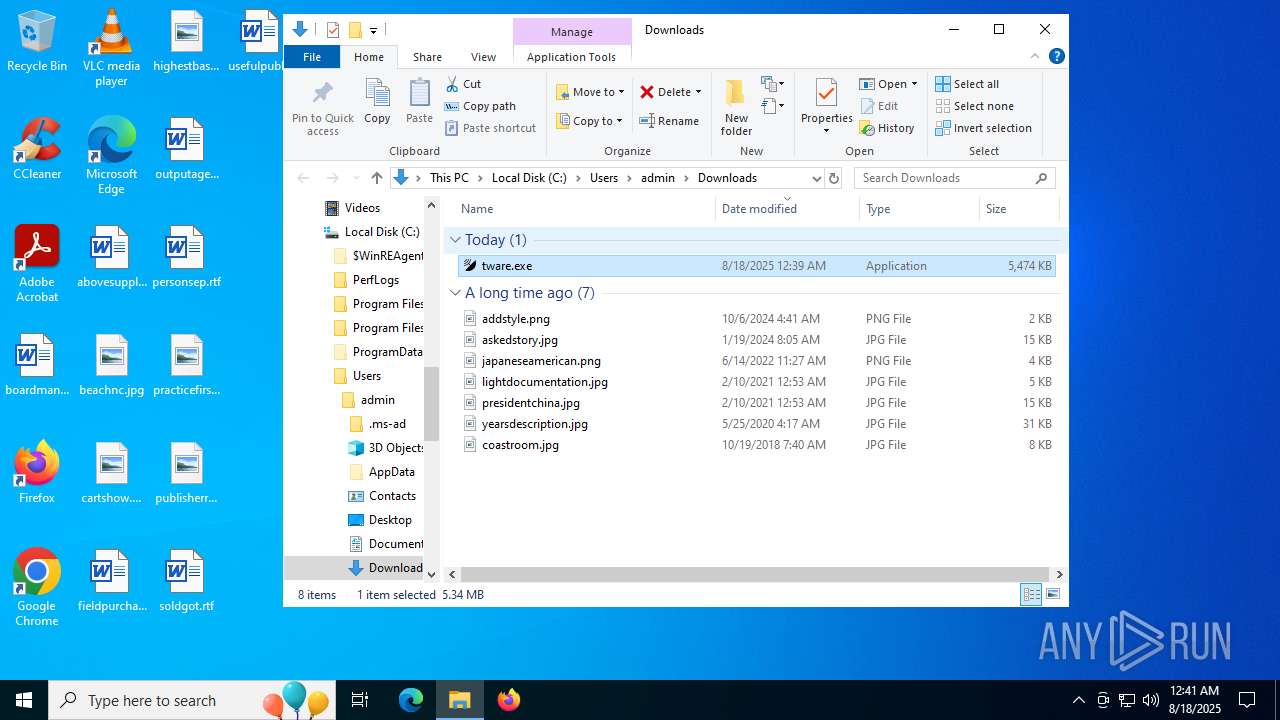
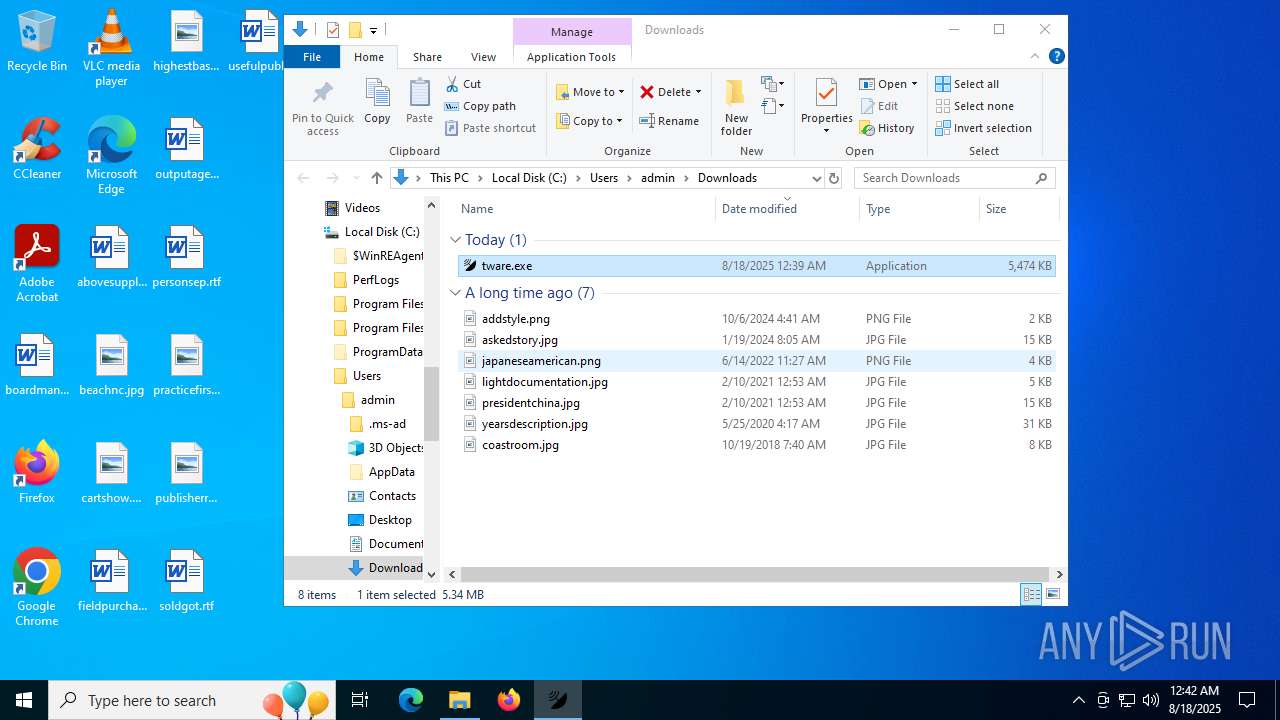
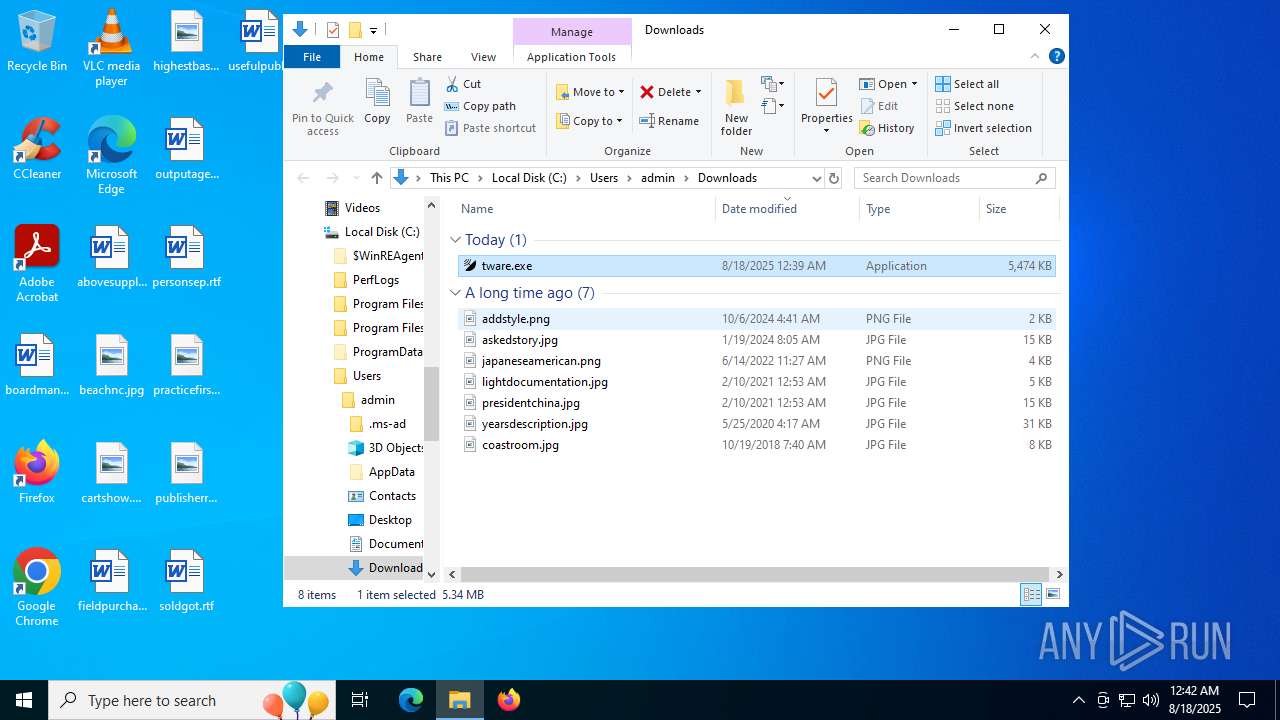
| File name: | tware.exe |
| Full analysis: | https://app.any.run/tasks/97127f53-dff2-419a-8cf4-12c07b228459 |
| Verdict: | Malicious activity |
| Analysis date: | August 18, 2025, 00:37:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 9 sections |
| MD5: | B0089F097200D11828A29C8FDF61F77C |
| SHA1: | 1E6BC9A1D1FB74CA2B2017507F75271C0078F00E |
| SHA256: | B0E5B9EADB3ACA16ED87FF68AF40BEA54AAC276B911C23B3387D71DA45CBFBA3 |
| SSDEEP: | 98304:rC36cpEw+geGzRJi8Bt3OVLQ9c2gEOYnW80bZ0/WSvyHm7qRWgkabDojOuWjWkRd:eSkmqky+ |
MALICIOUS
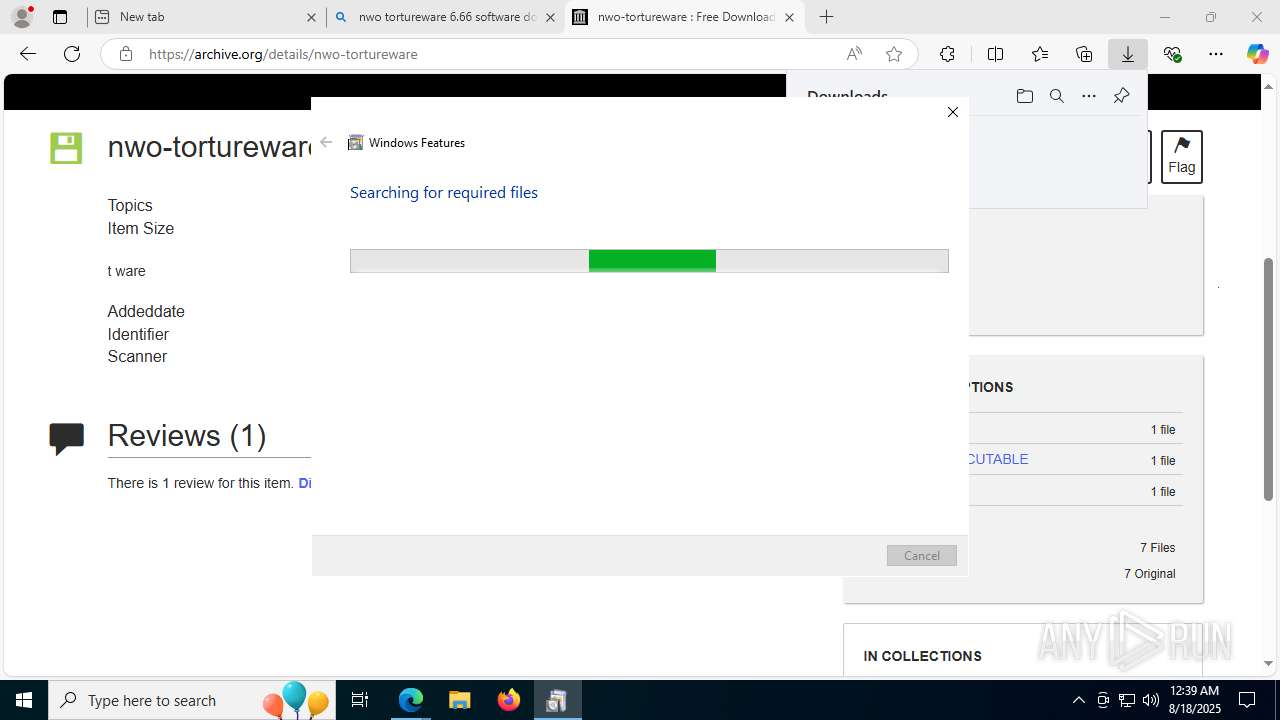
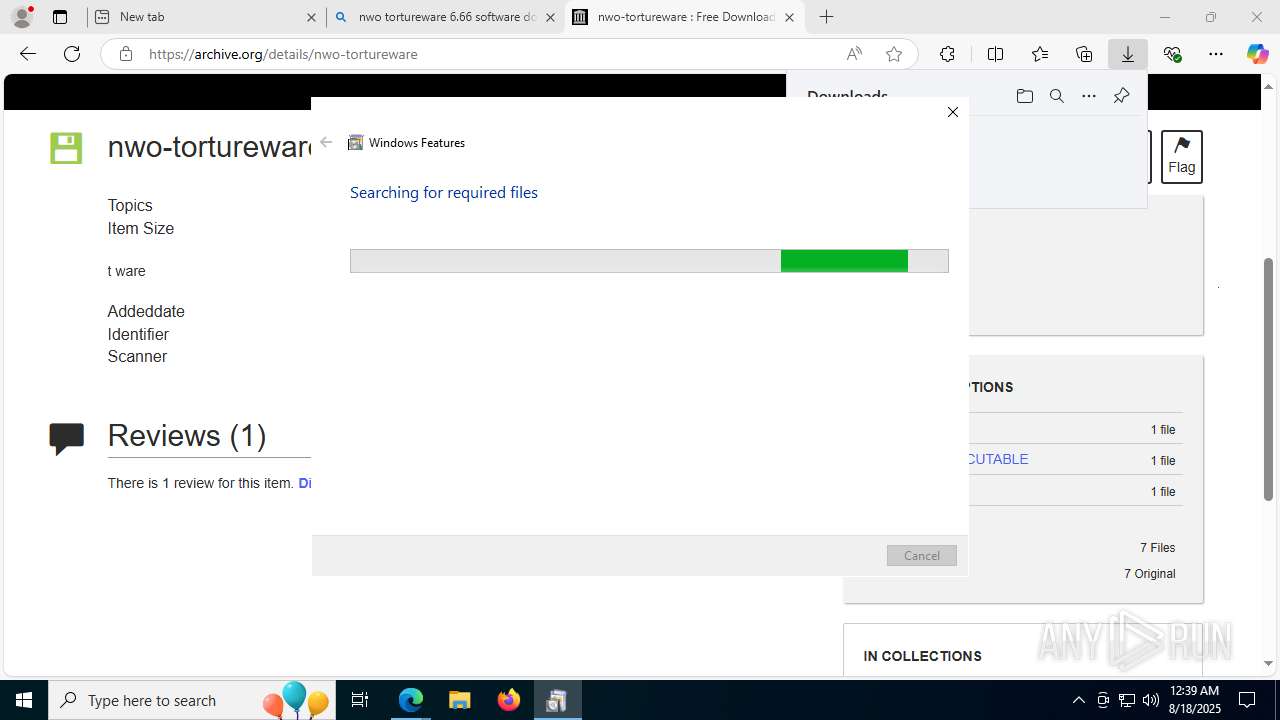
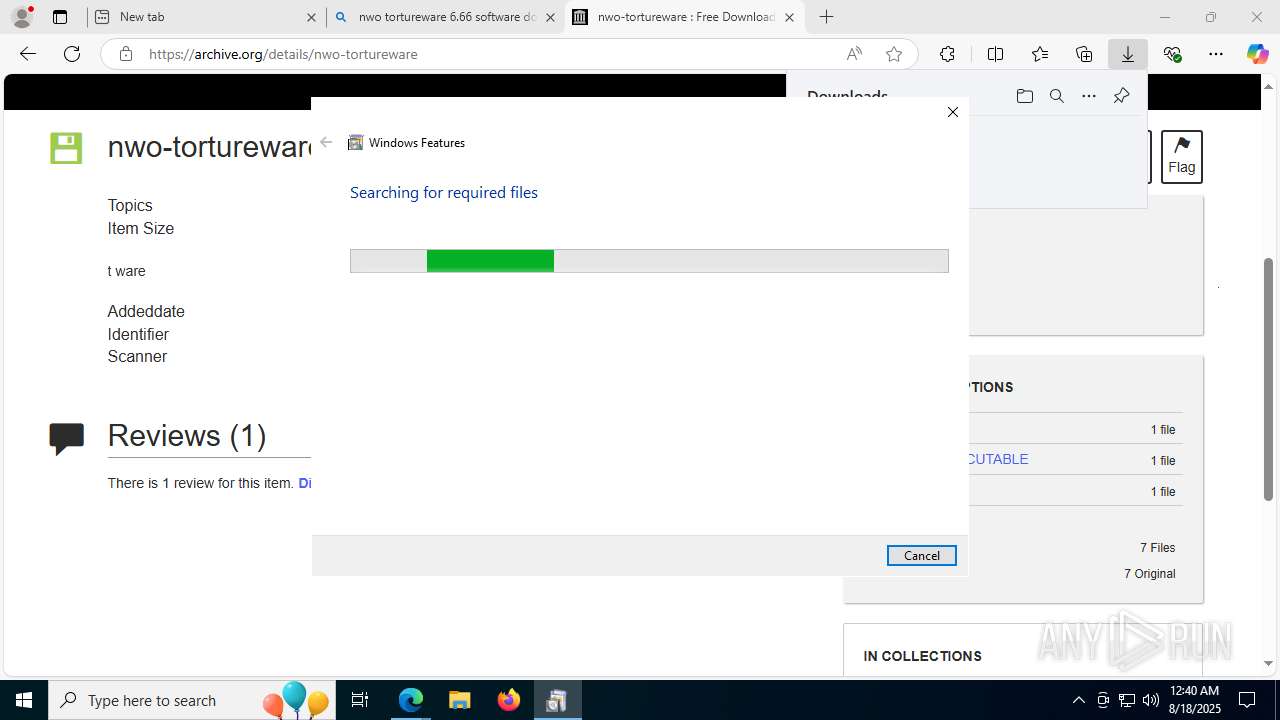
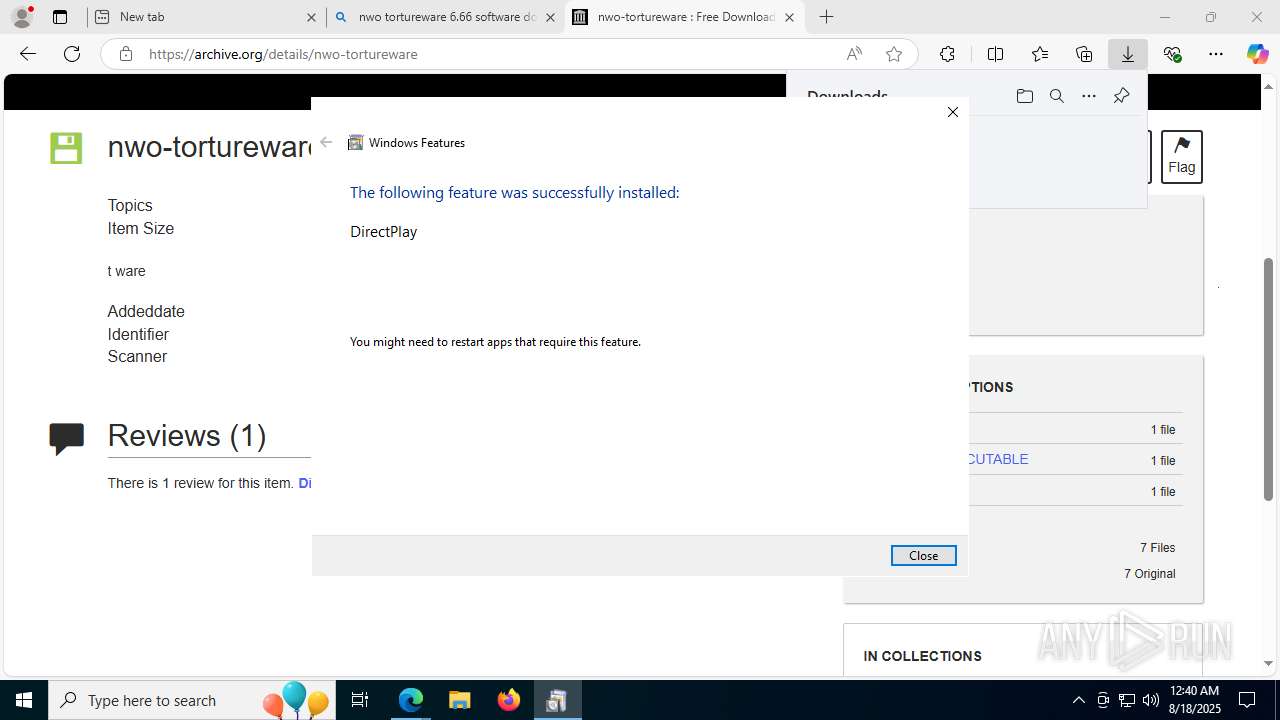
Application was injected by another process
- csrss.exe (PID: 608)
Runs injected code in another process
- tware.exe (PID: 1592)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- tware.exe (PID: 1592)
- tware.exe (PID: 5548)
Executes as Windows Service
- VSSVC.exe (PID: 2696)
Reads security settings of Internet Explorer
- tware.exe (PID: 1592)
- tware.exe (PID: 5548)
- tware.exe (PID: 7984)
- tware.exe (PID: 8032)
- tware.exe (PID: 8148)
- tware.exe (PID: 1660)
- tware.exe (PID: 8168)
- tware.exe (PID: 3740)
- tware.exe (PID: 72)
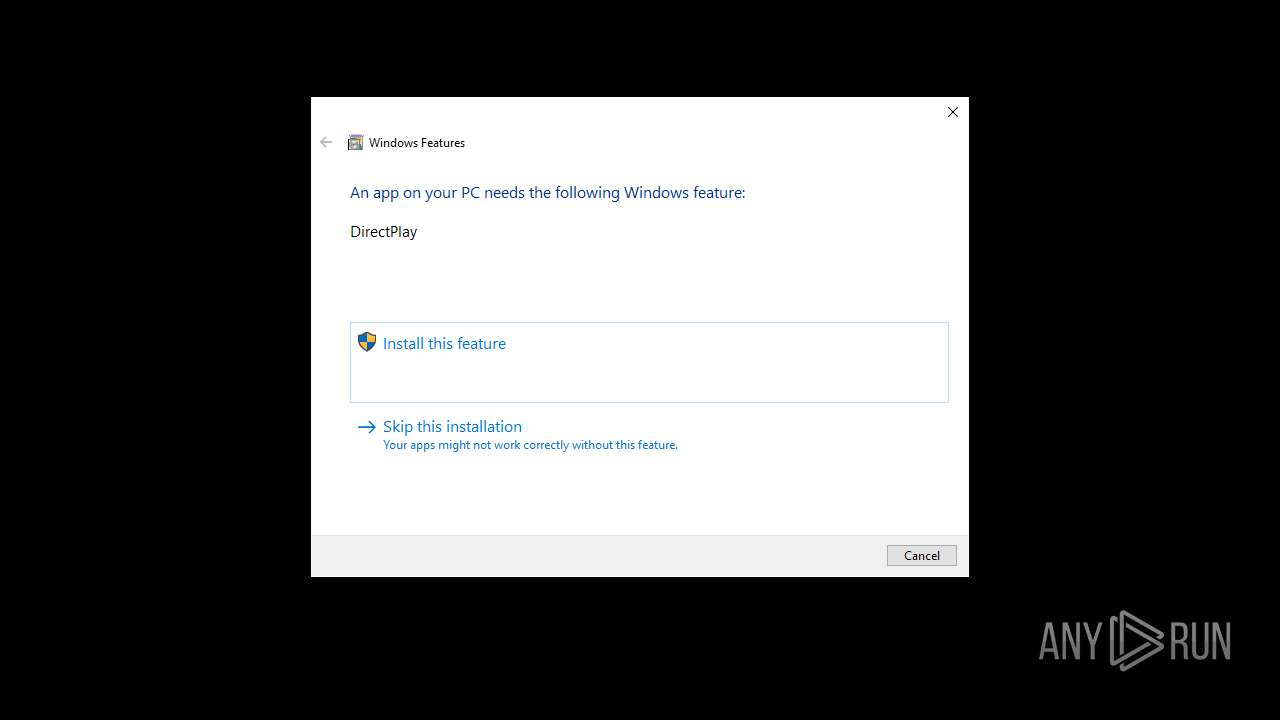
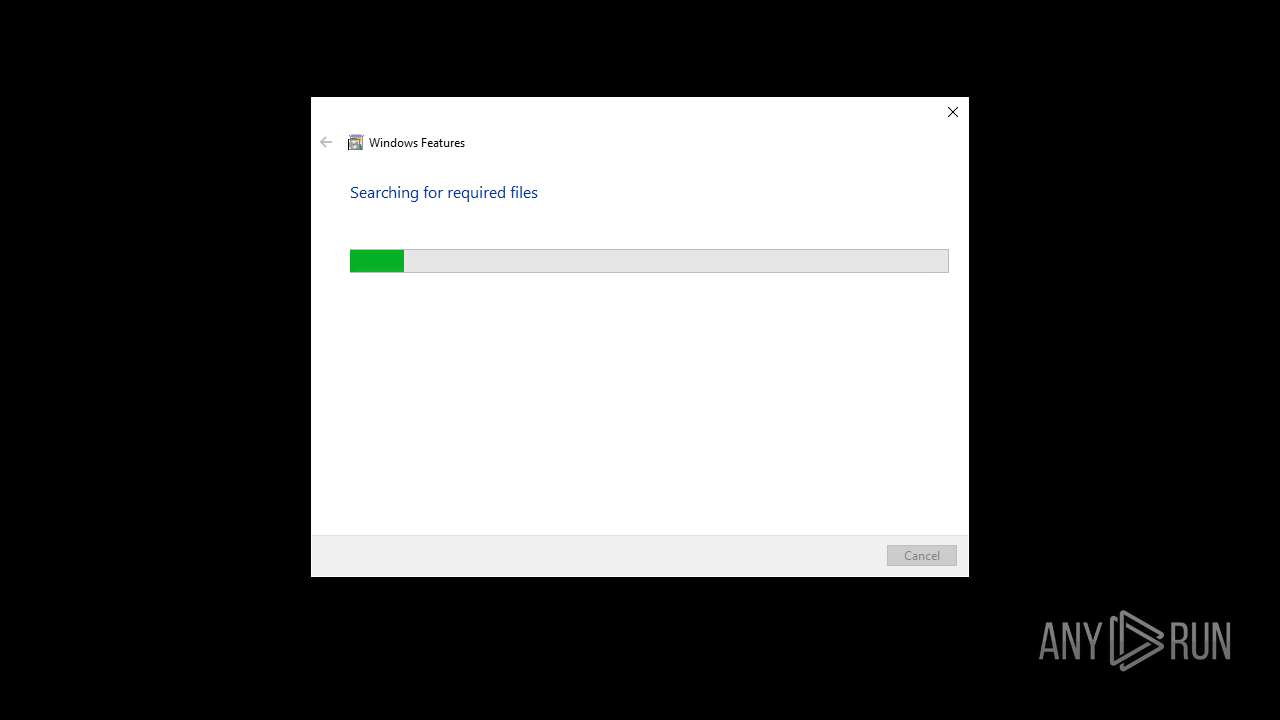
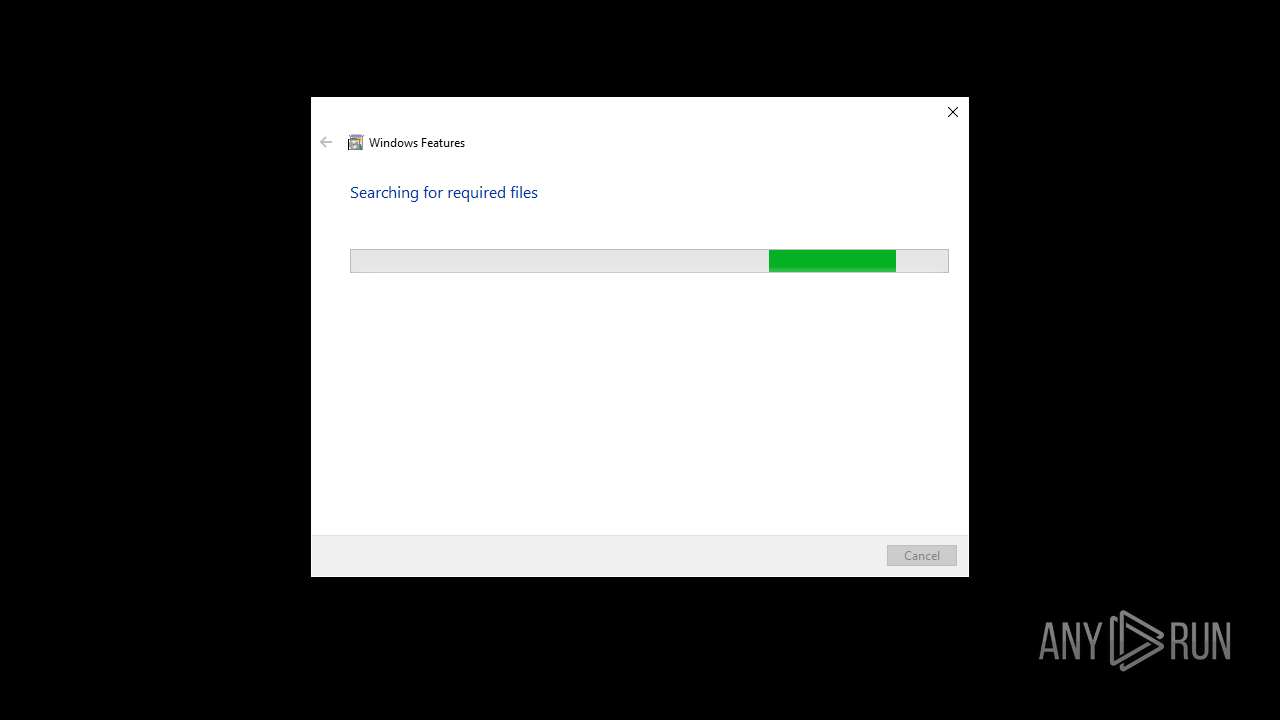
Searches for installed software
- TiWorker.exe (PID: 2508)
Process drops legitimate windows executable
- TiWorker.exe (PID: 2508)
INFO
Checks proxy server information
- tware.exe (PID: 1592)
- slui.exe (PID: 4084)
- tware.exe (PID: 5548)
- tware.exe (PID: 7984)
- tware.exe (PID: 8032)
- tware.exe (PID: 8148)
- tware.exe (PID: 1660)
- tware.exe (PID: 72)
- tware.exe (PID: 8168)
- tware.exe (PID: 3740)
Compiled with Borland Delphi (YARA)
- tware.exe (PID: 1592)
- tware.exe (PID: 5548)
Create files in a temporary directory
- tware.exe (PID: 1592)
- tware.exe (PID: 7984)
- tware.exe (PID: 5548)
- tware.exe (PID: 8032)
- tware.exe (PID: 1660)
- tware.exe (PID: 8148)
- tware.exe (PID: 72)
- tware.exe (PID: 8168)
- tware.exe (PID: 3740)
The sample compiled with english language support
- tware.exe (PID: 1592)
- TiWorker.exe (PID: 2508)
- msedge.exe (PID: 5616)
- msedge.exe (PID: 1028)
Manages system restore points
- SrTasks.exe (PID: 5184)
- SrTasks.exe (PID: 7448)
Reads the computer name
- tware.exe (PID: 1592)
- identity_helper.exe (PID: 7336)
- tware.exe (PID: 7984)
- tware.exe (PID: 5548)
- tware.exe (PID: 8032)
- tware.exe (PID: 8148)
- tware.exe (PID: 1660)
- identity_helper.exe (PID: 4456)
- tware.exe (PID: 72)
- tware.exe (PID: 8168)
- tware.exe (PID: 3740)
Checks supported languages
- tware.exe (PID: 1592)
- identity_helper.exe (PID: 7336)
- tware.exe (PID: 5548)
- tware.exe (PID: 8032)
- tware.exe (PID: 7984)
- tware.exe (PID: 8148)
- tware.exe (PID: 1660)
- identity_helper.exe (PID: 4456)
- tware.exe (PID: 8168)
- tware.exe (PID: 3740)
- tware.exe (PID: 72)
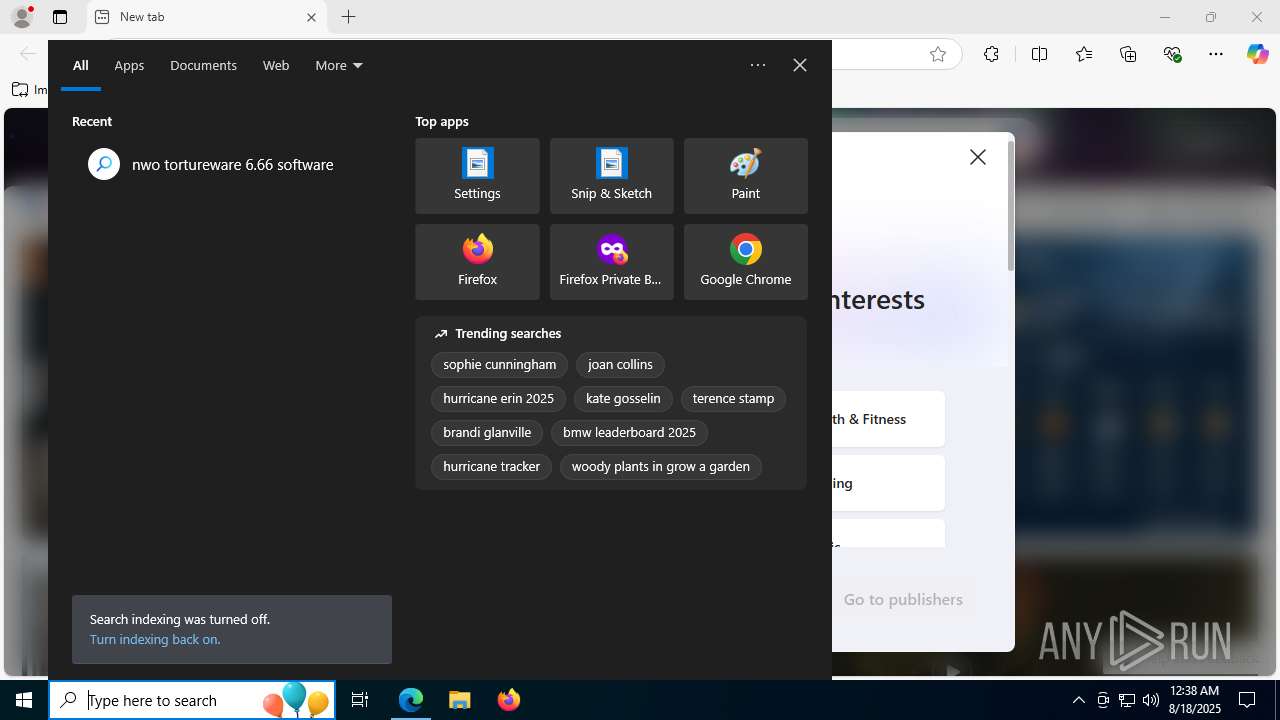
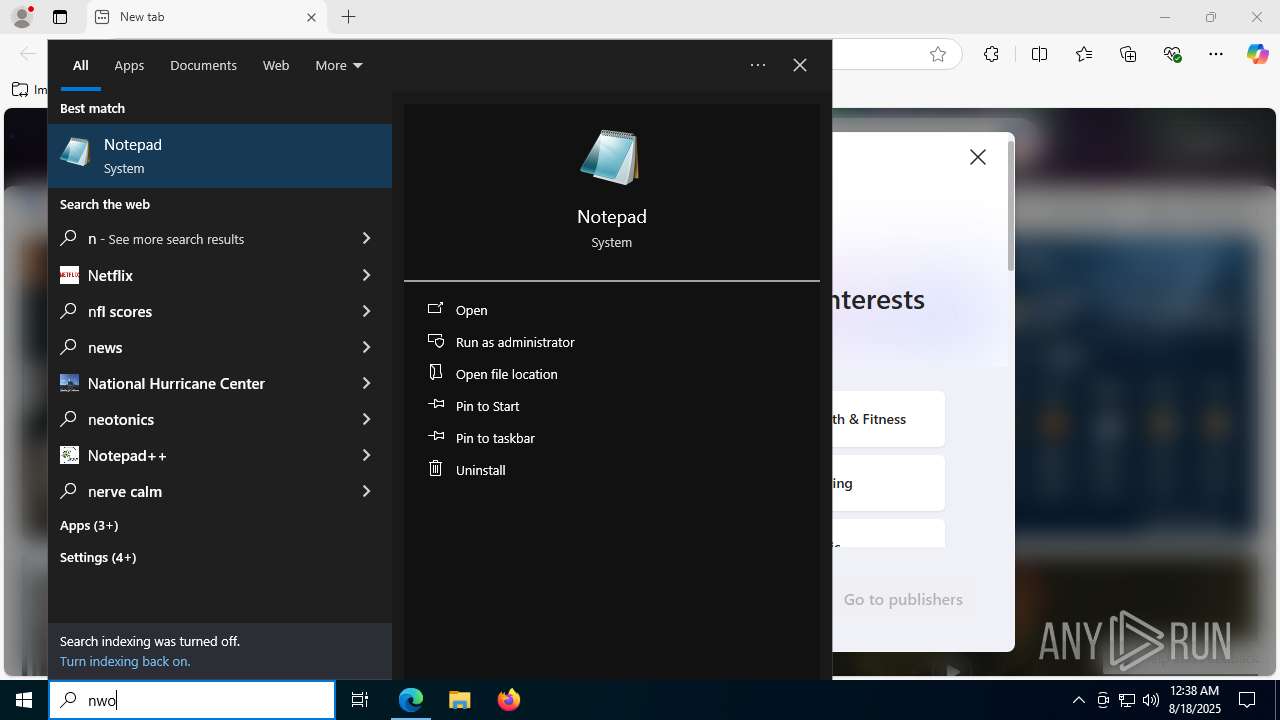
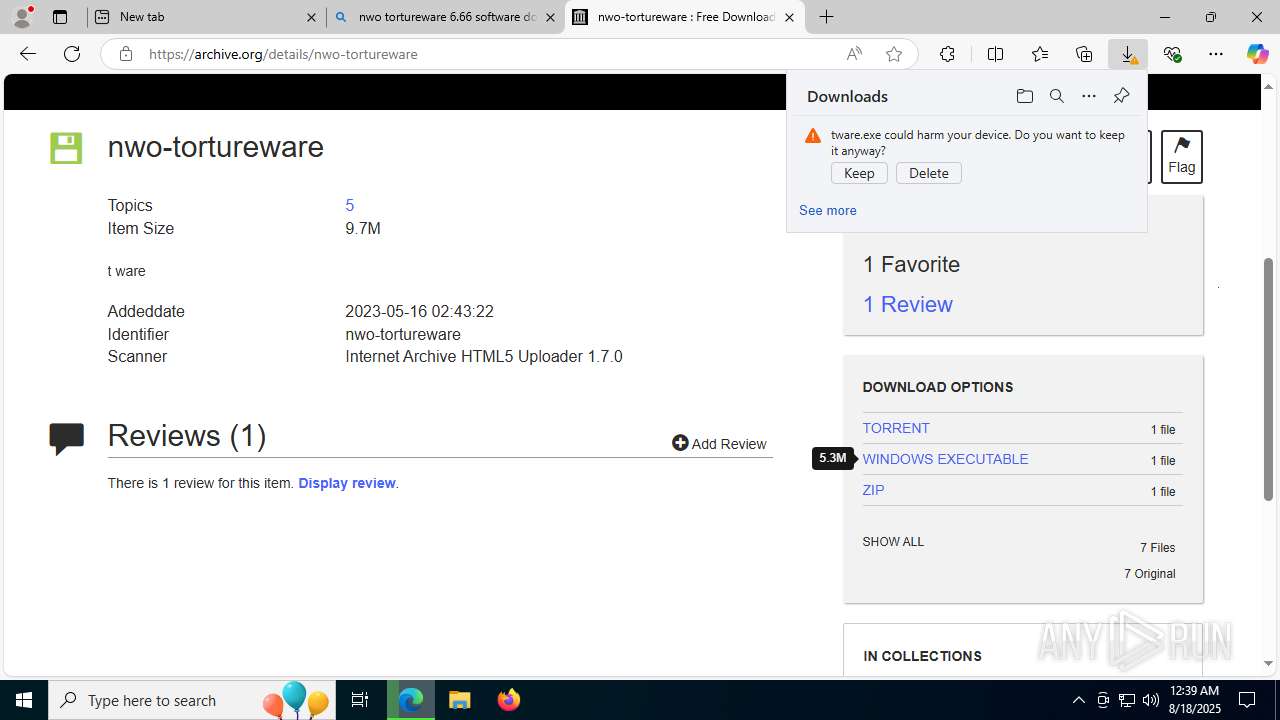
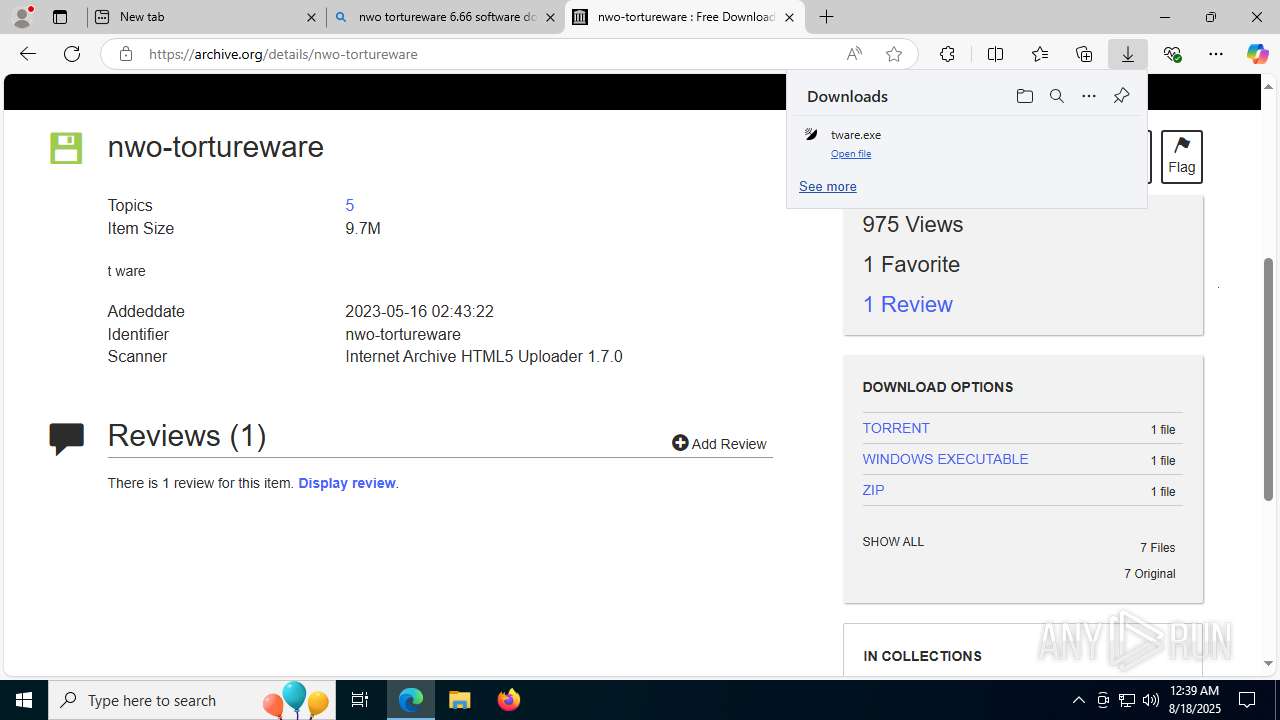
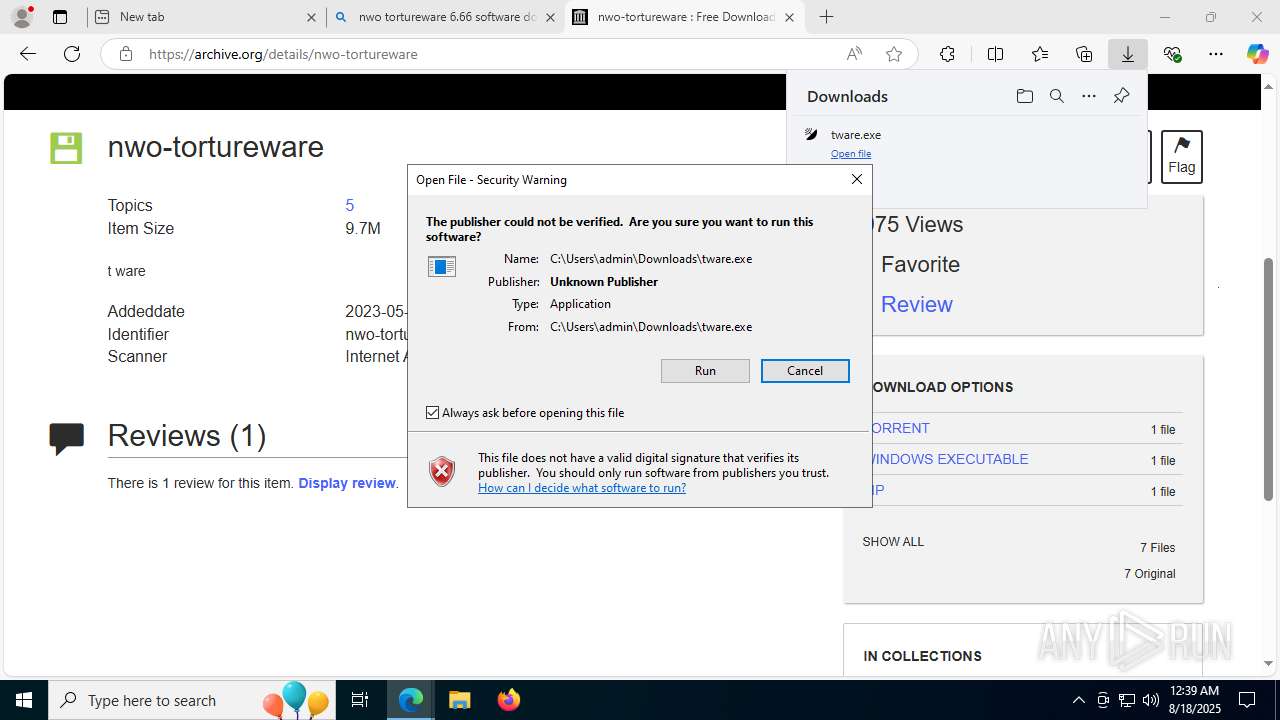
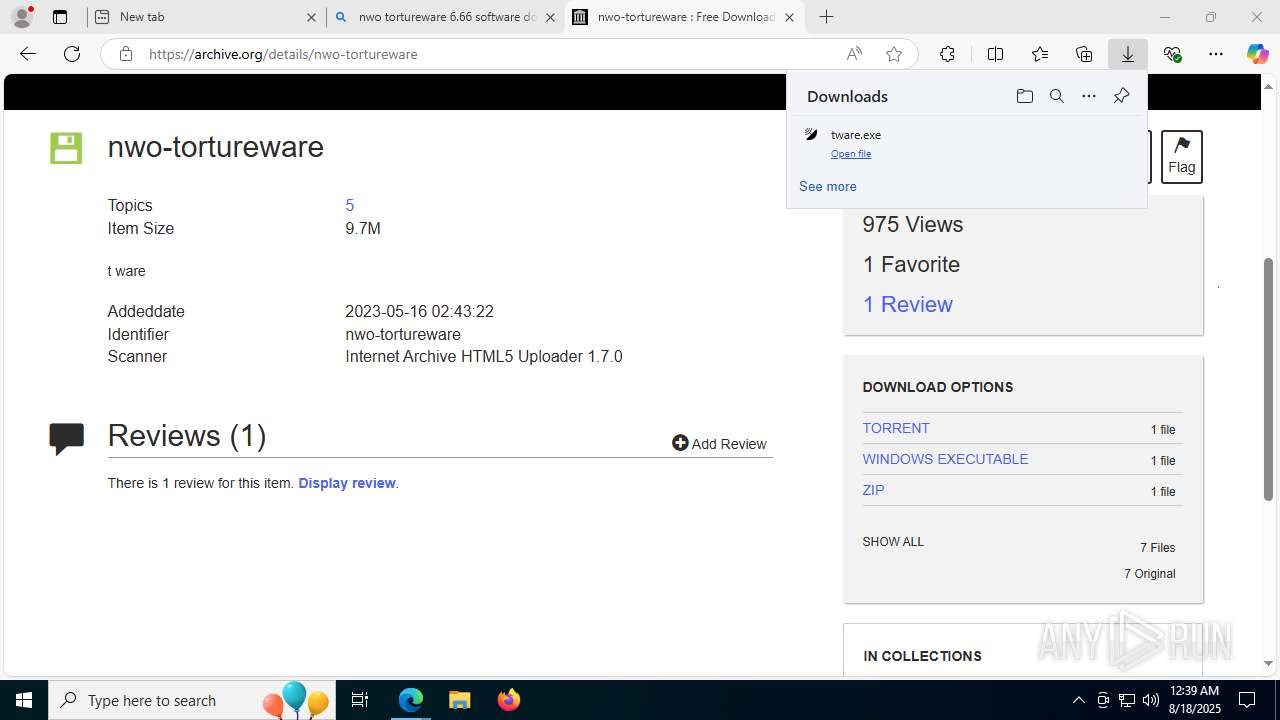
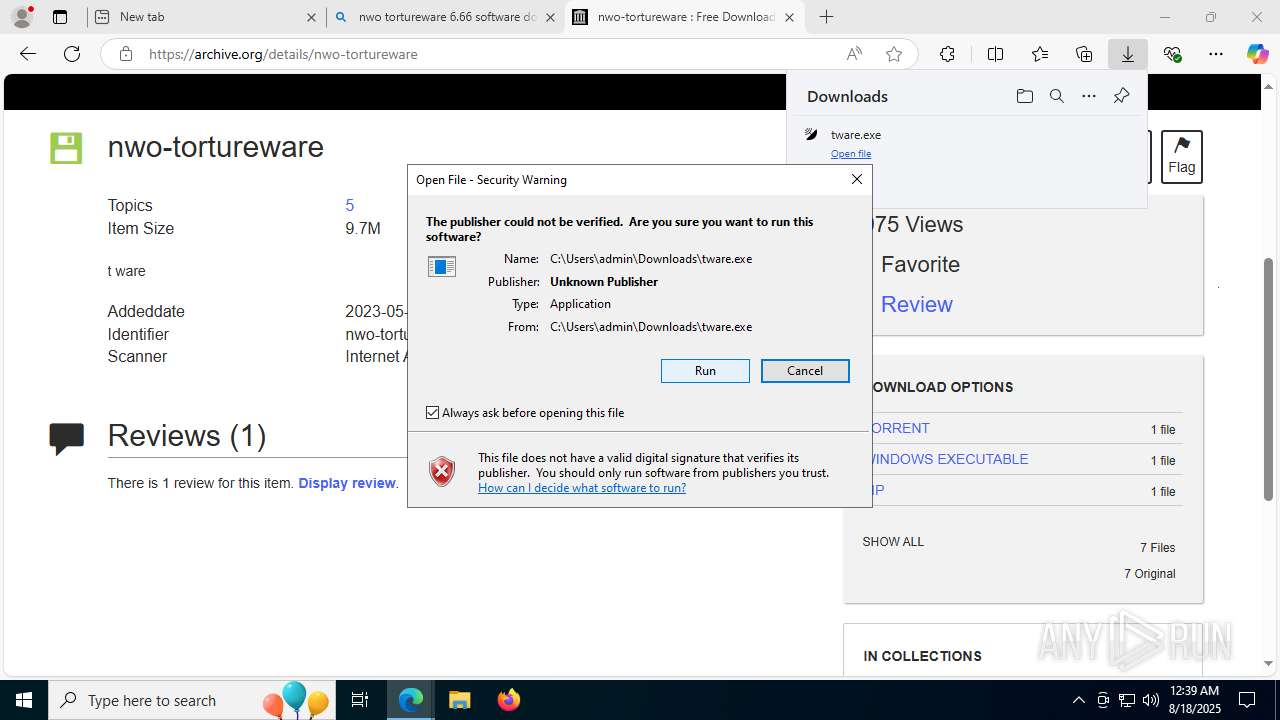
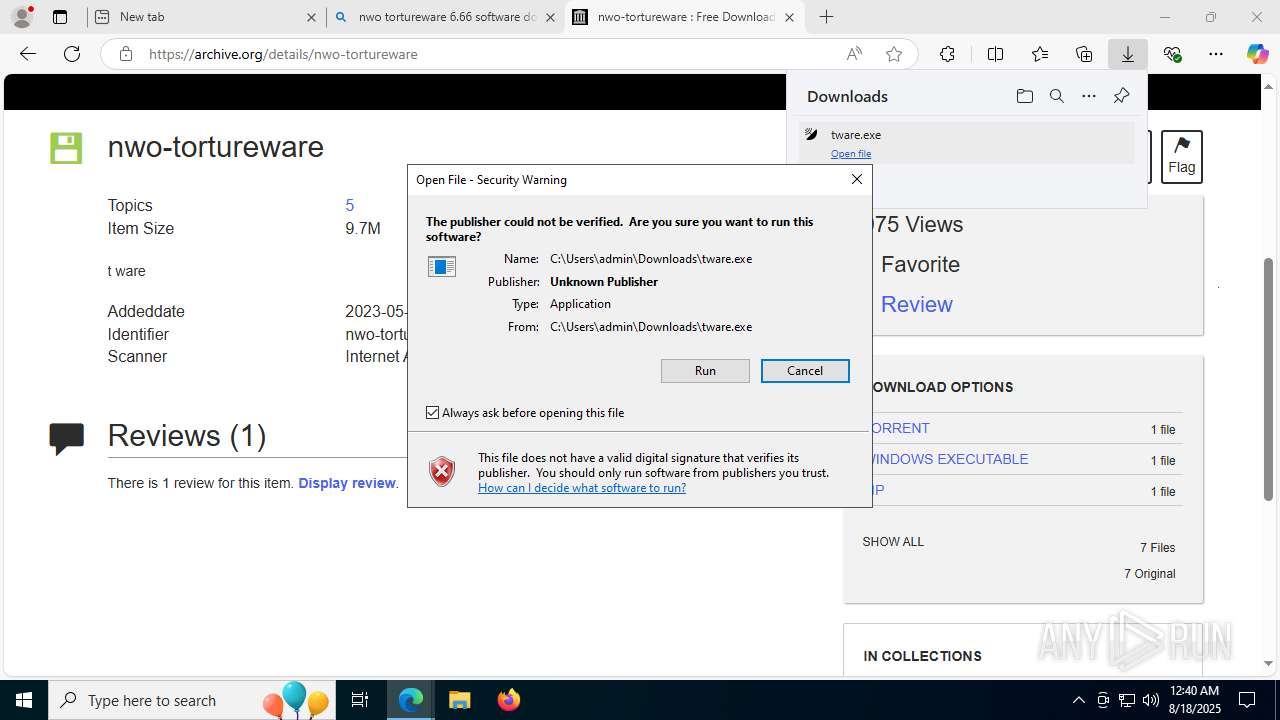
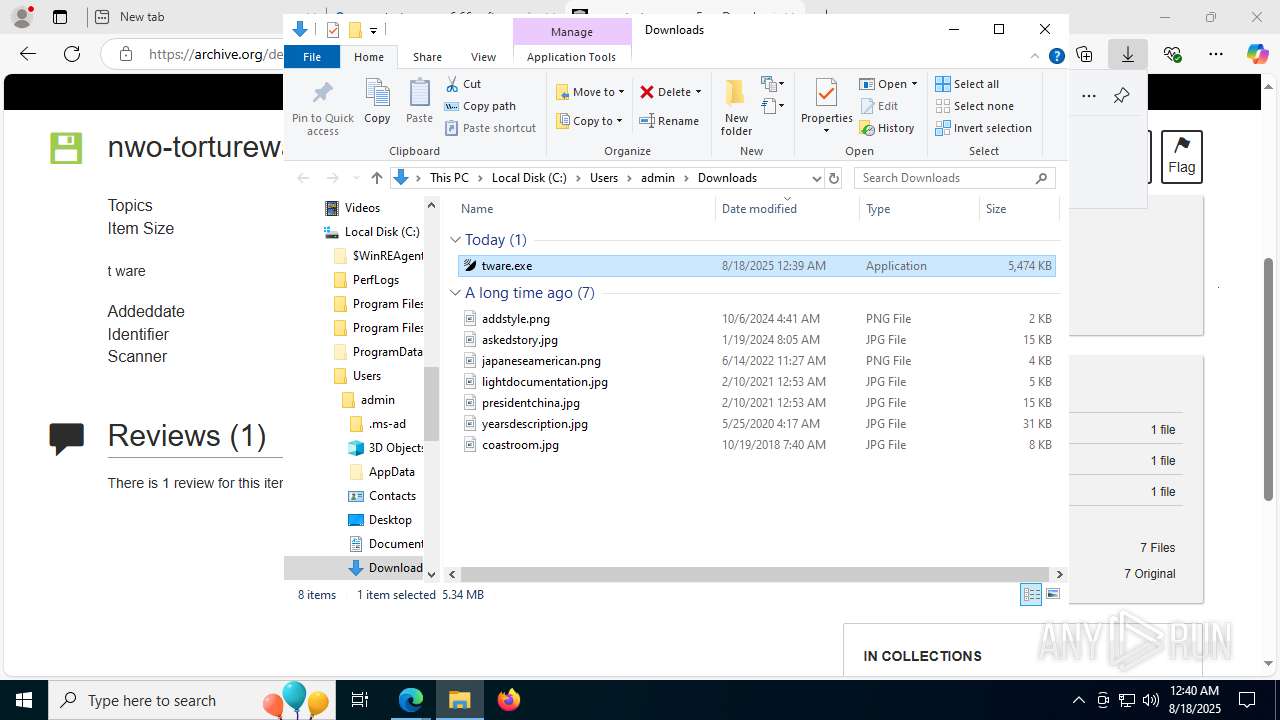
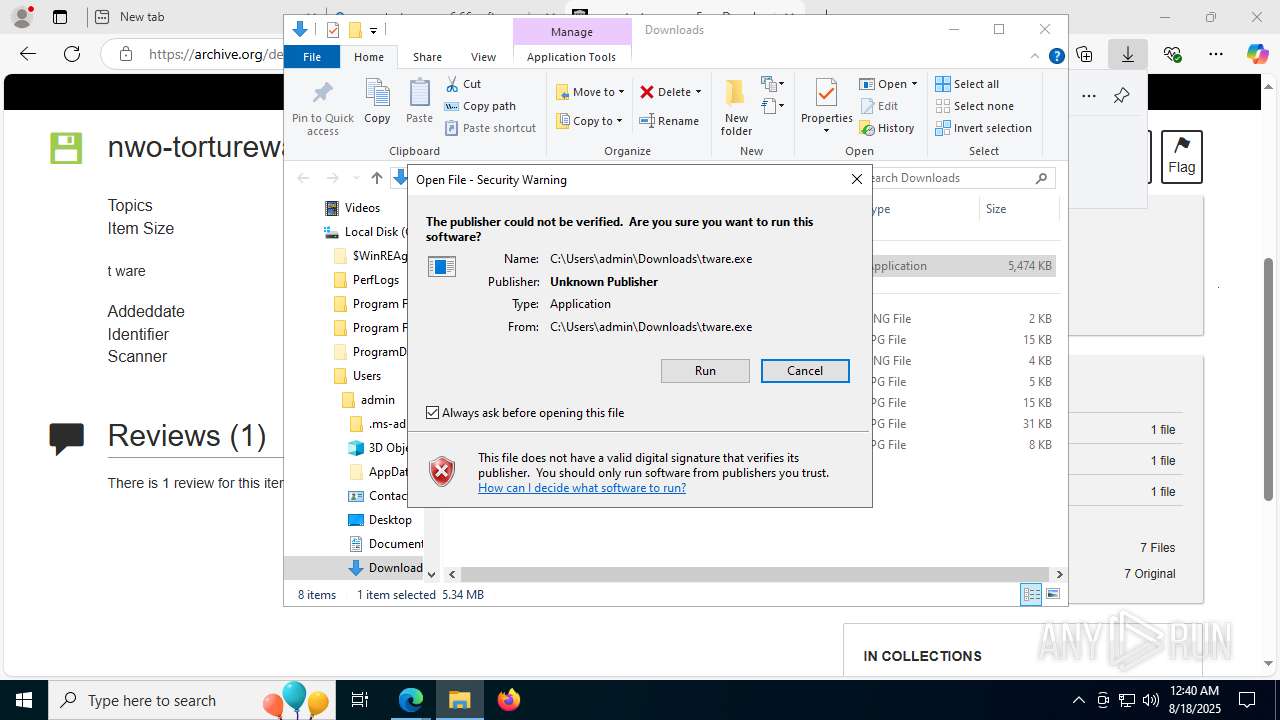
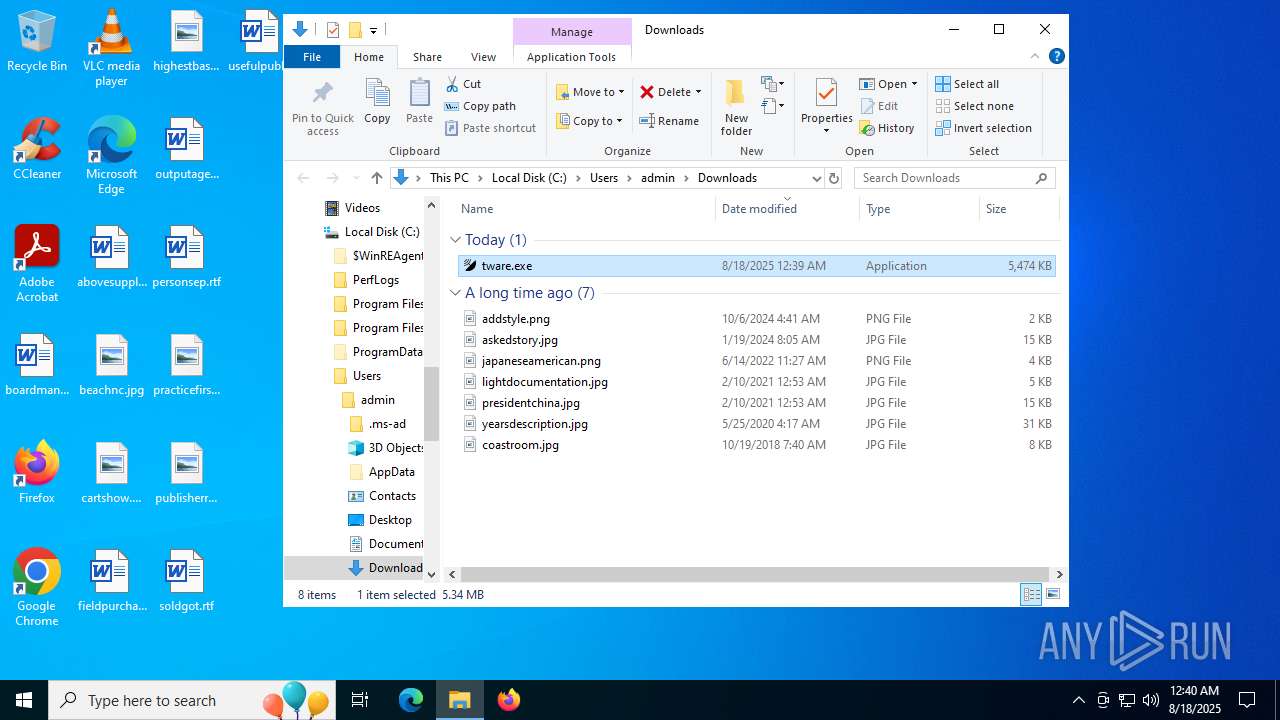
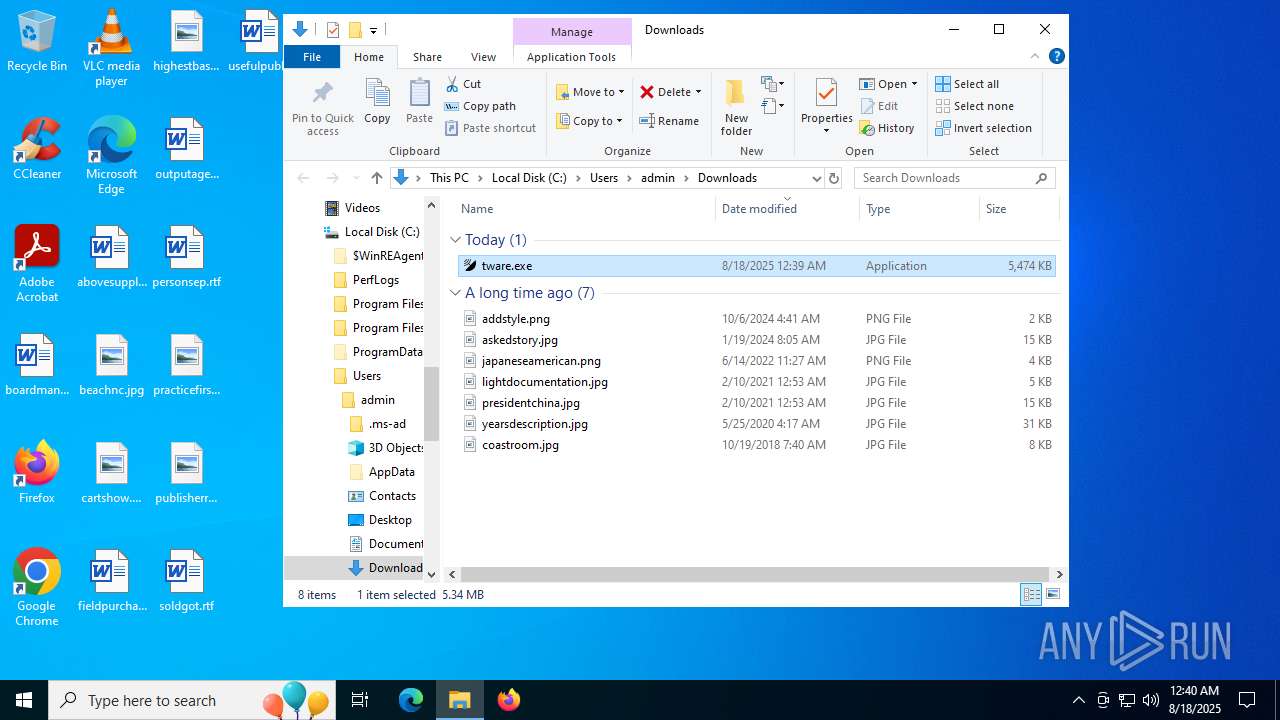
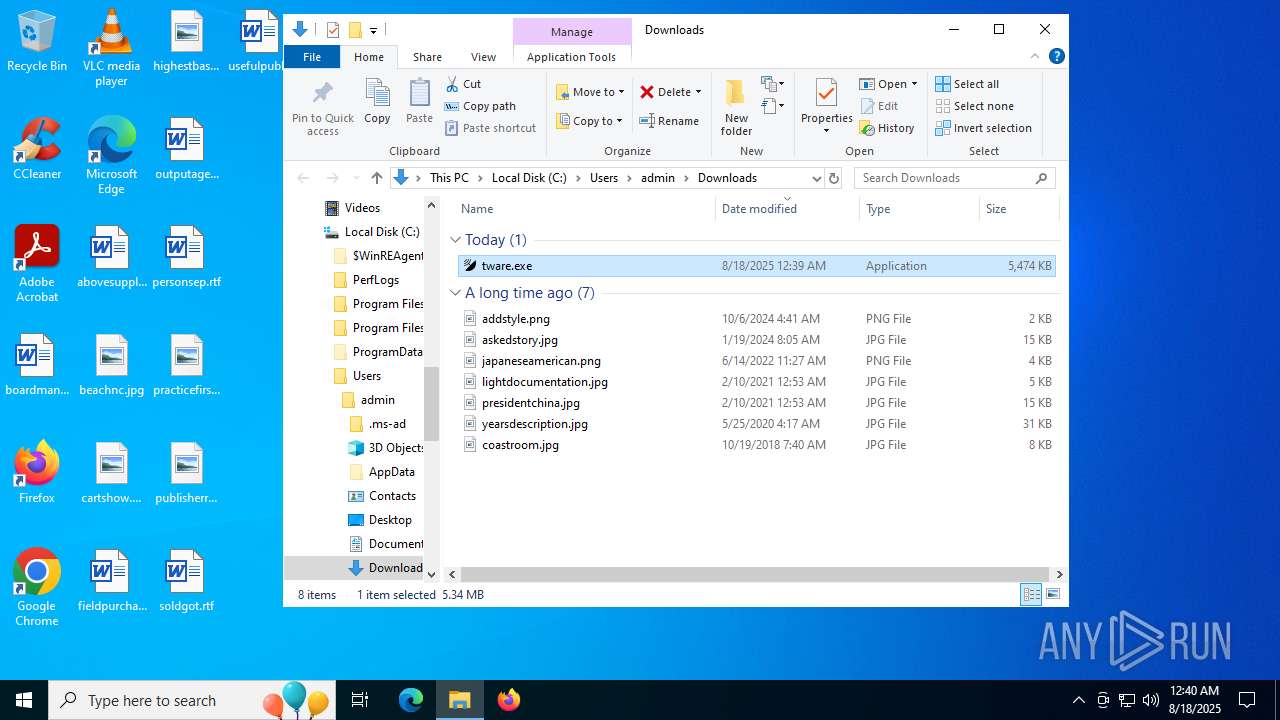
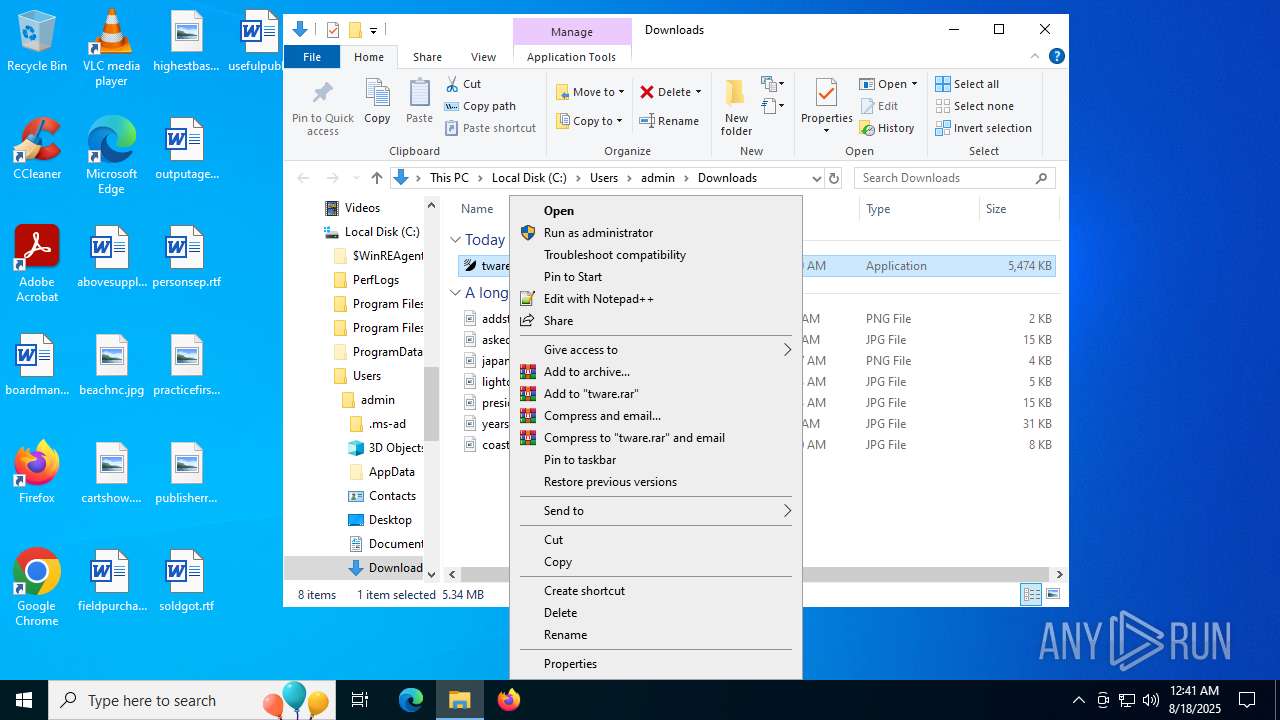
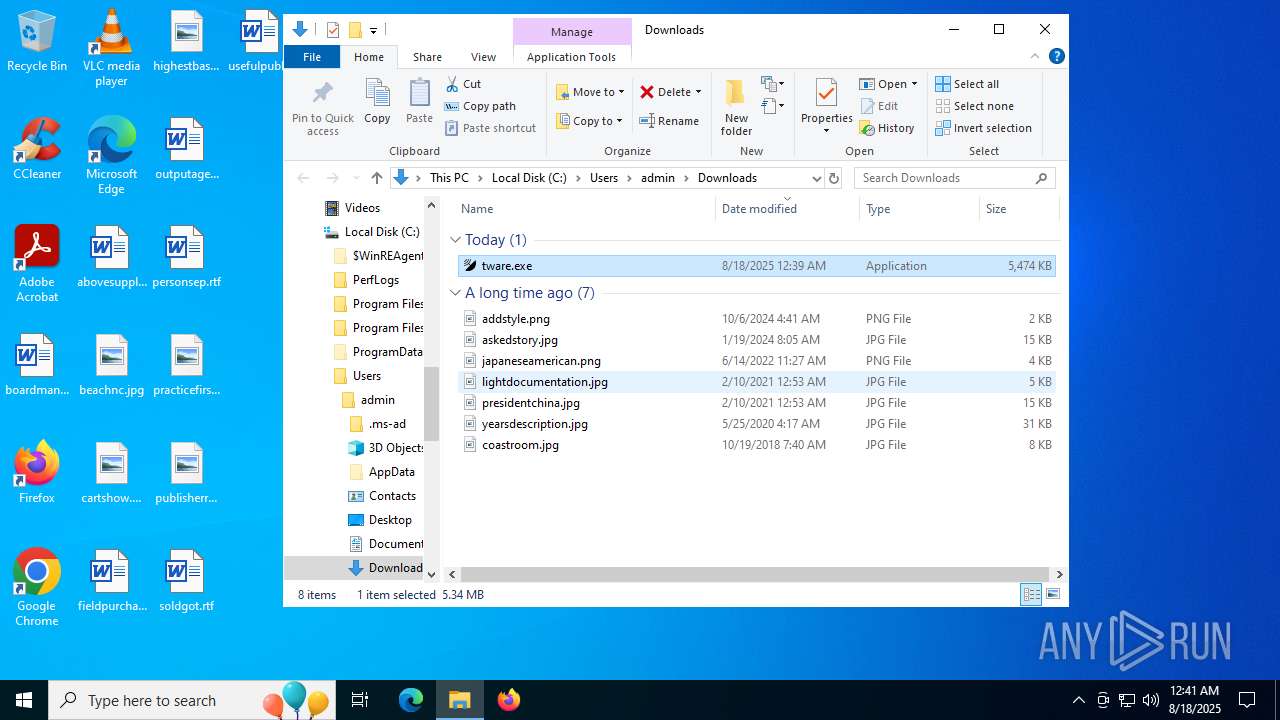
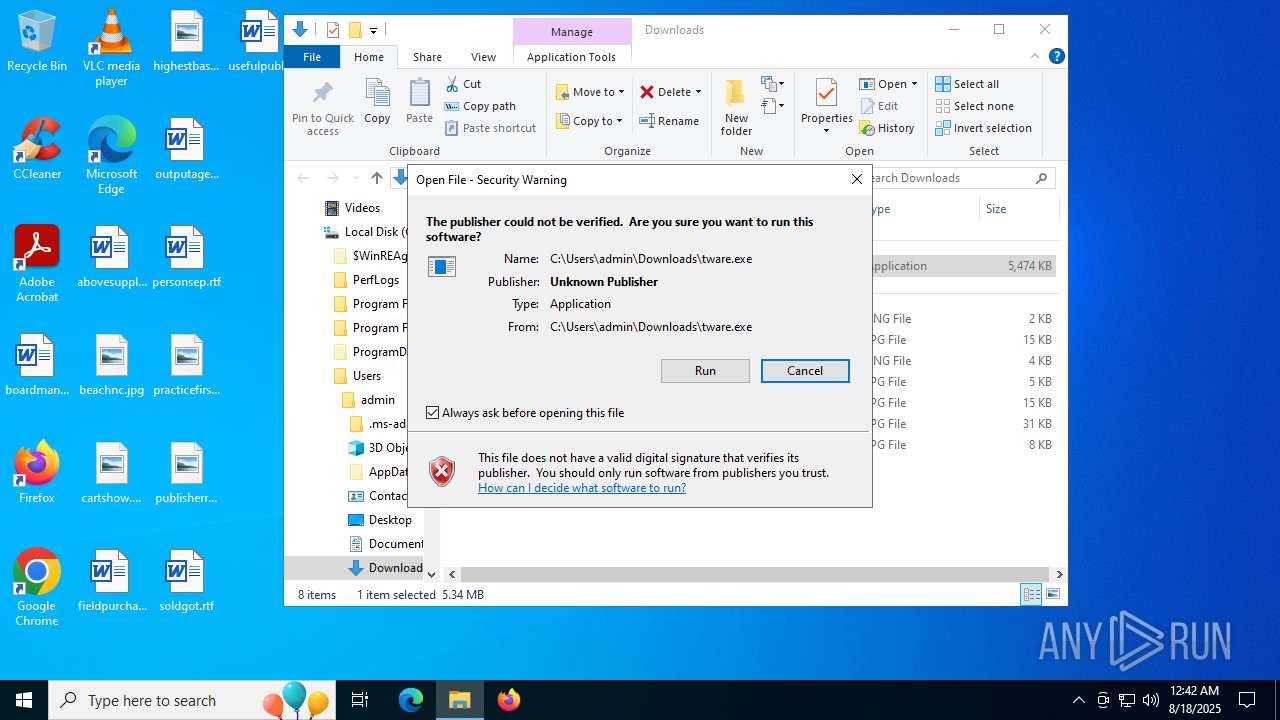
Manual execution by a user
- msedge.exe (PID: 1028)
- tware.exe (PID: 1660)
- tware.exe (PID: 72)
- tware.exe (PID: 8168)
- tware.exe (PID: 3740)
Reads Environment values
- identity_helper.exe (PID: 7336)
- identity_helper.exe (PID: 4456)
Application launched itself
- msedge.exe (PID: 1028)
- msedge.exe (PID: 7236)
Reads the software policy settings
- slui.exe (PID: 4084)
- TiWorker.exe (PID: 2508)
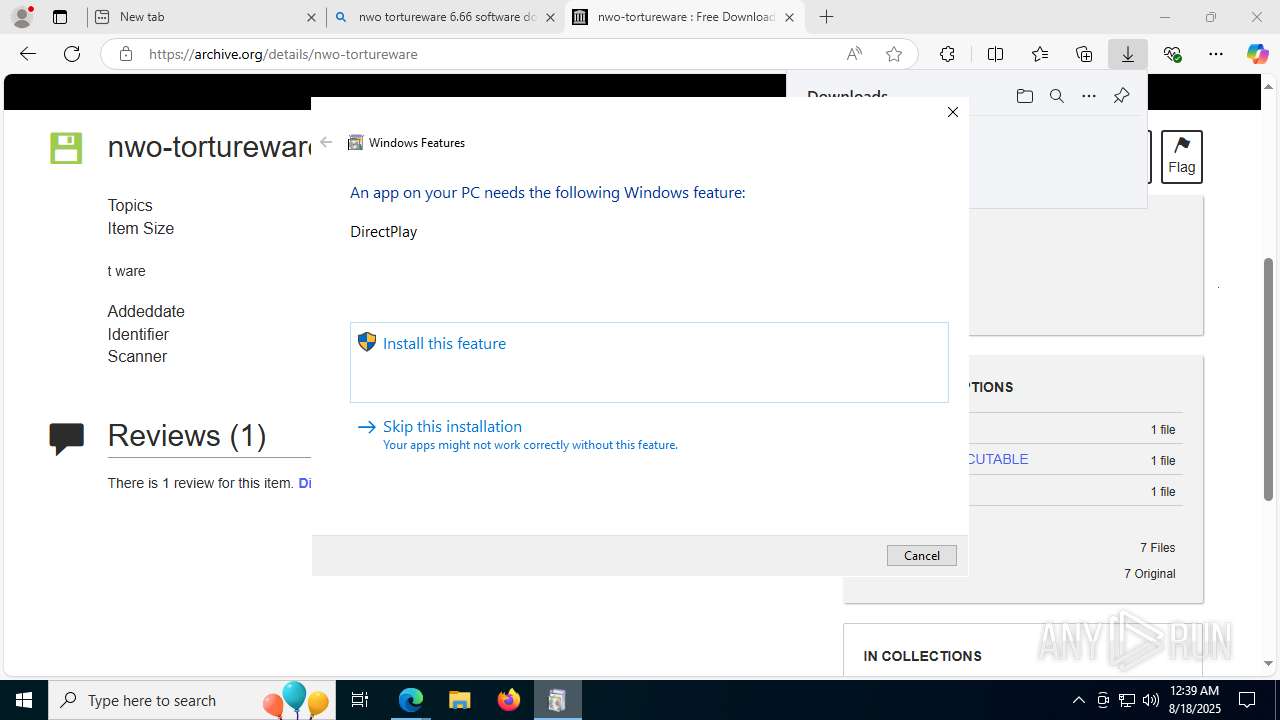
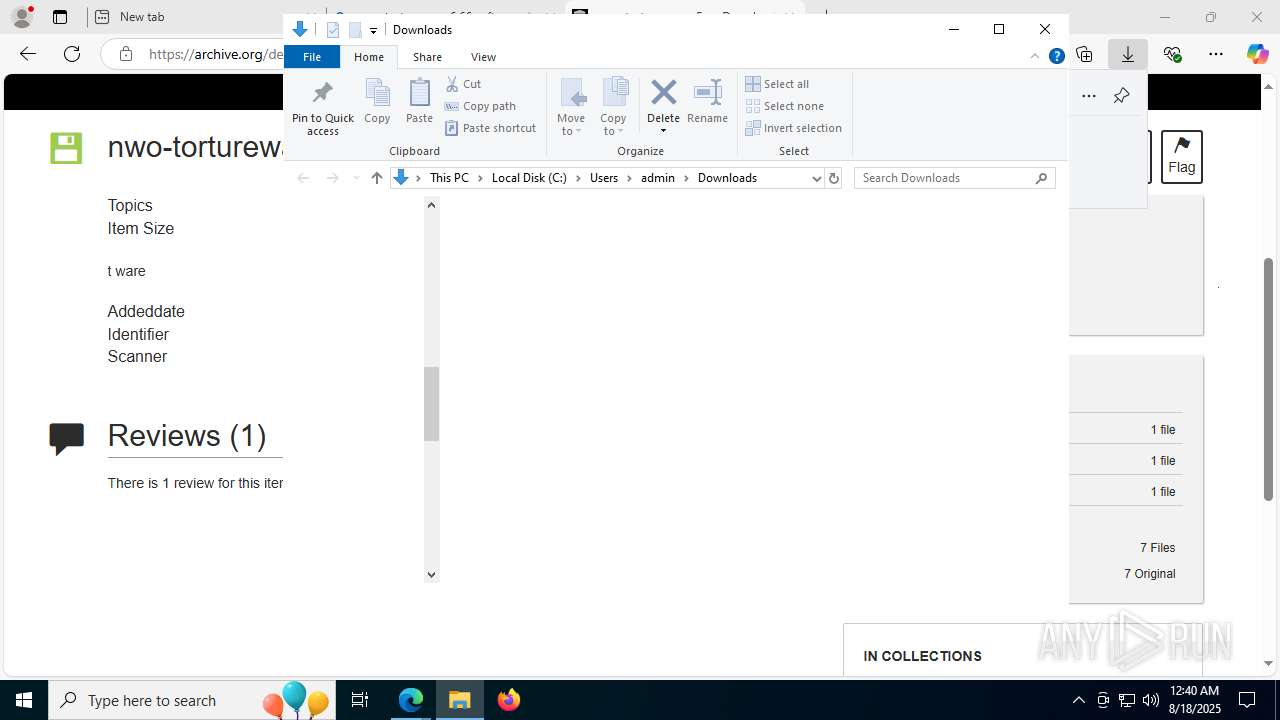
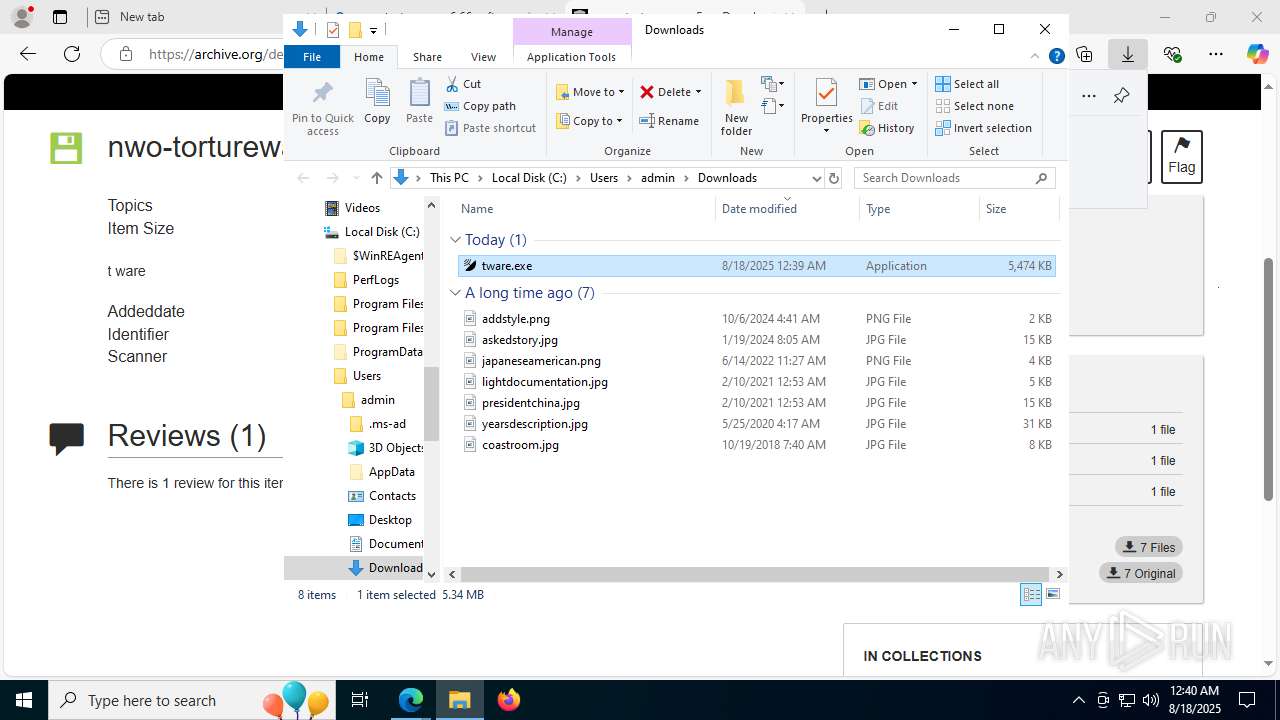
Launching a file from the Downloads directory
- msedge.exe (PID: 1028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
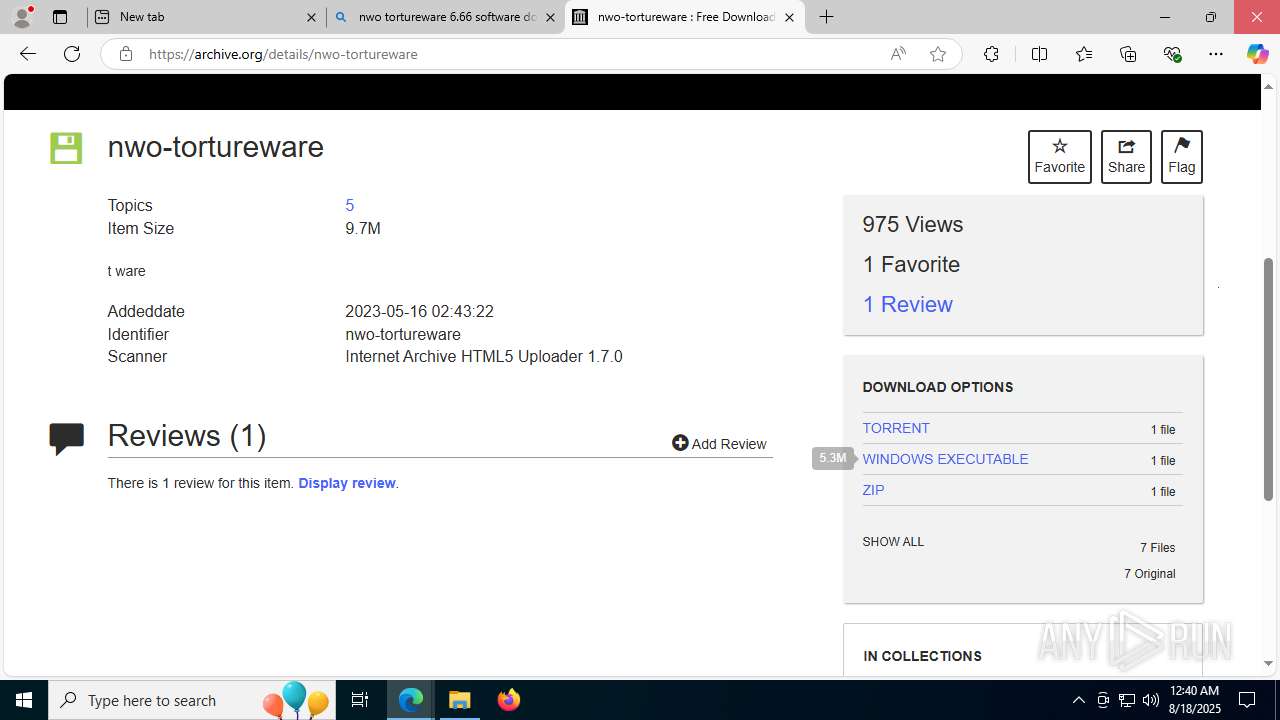
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (85.8) |
|---|---|---|
| .exe | | | InstallShield setup (5.5) |
| .exe | | | Win32 EXE PECompact compressed (generic) (5.3) |
| .exe | | | Win32 Executable Delphi generic (1.8) |
| .exe | | | Win32 Executable (generic) (0.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 1602560 |
| InitializedDataSize: | 370688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x188750 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.6.6.0 |
| ProductVersionNumber: | 6.6.6.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
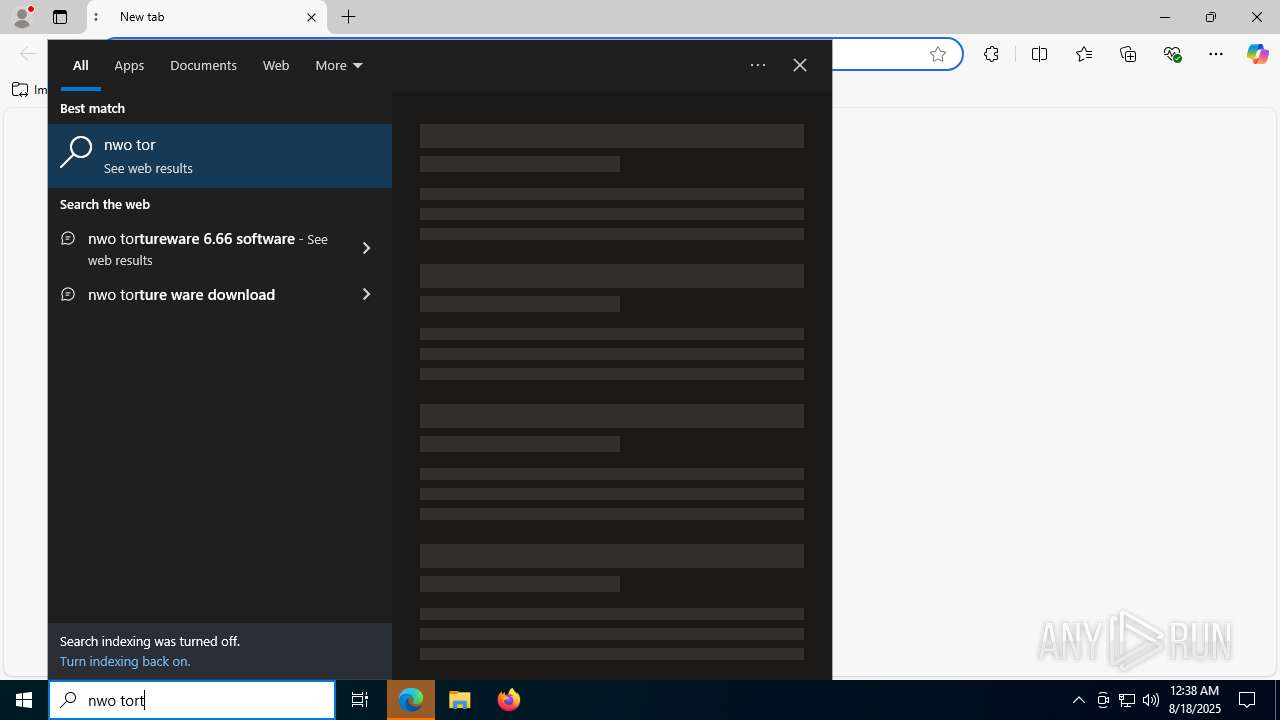
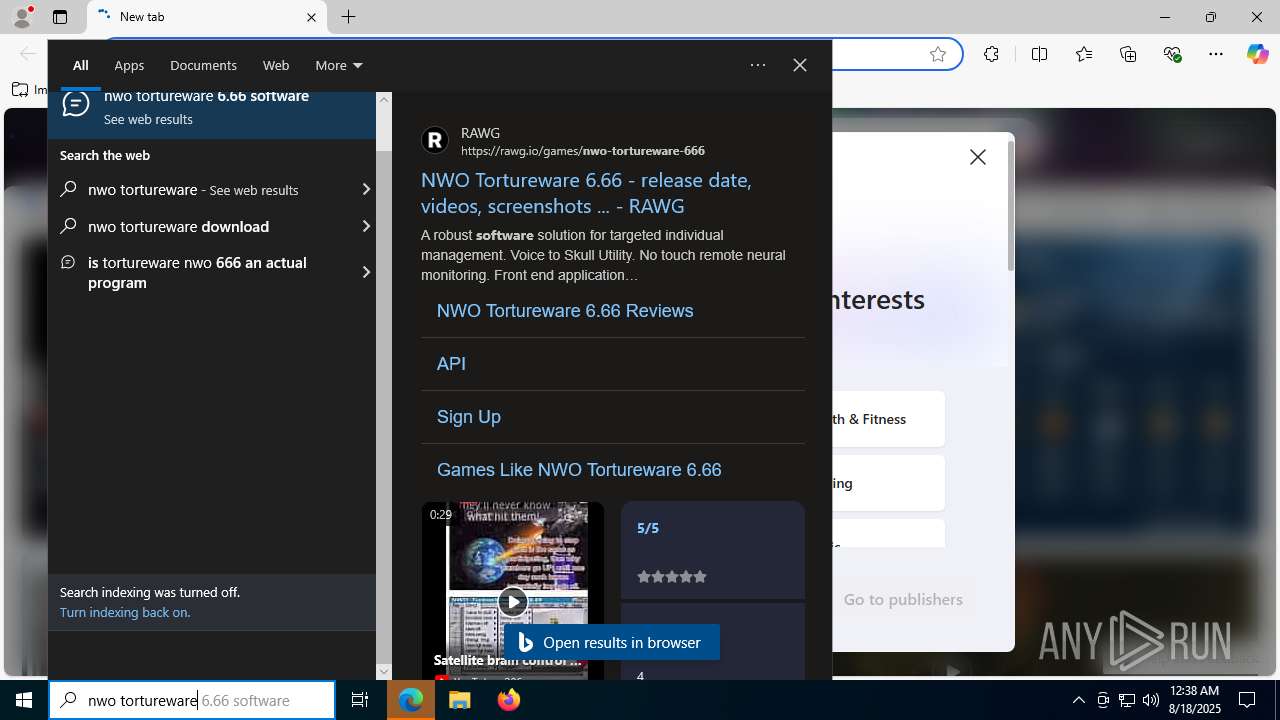
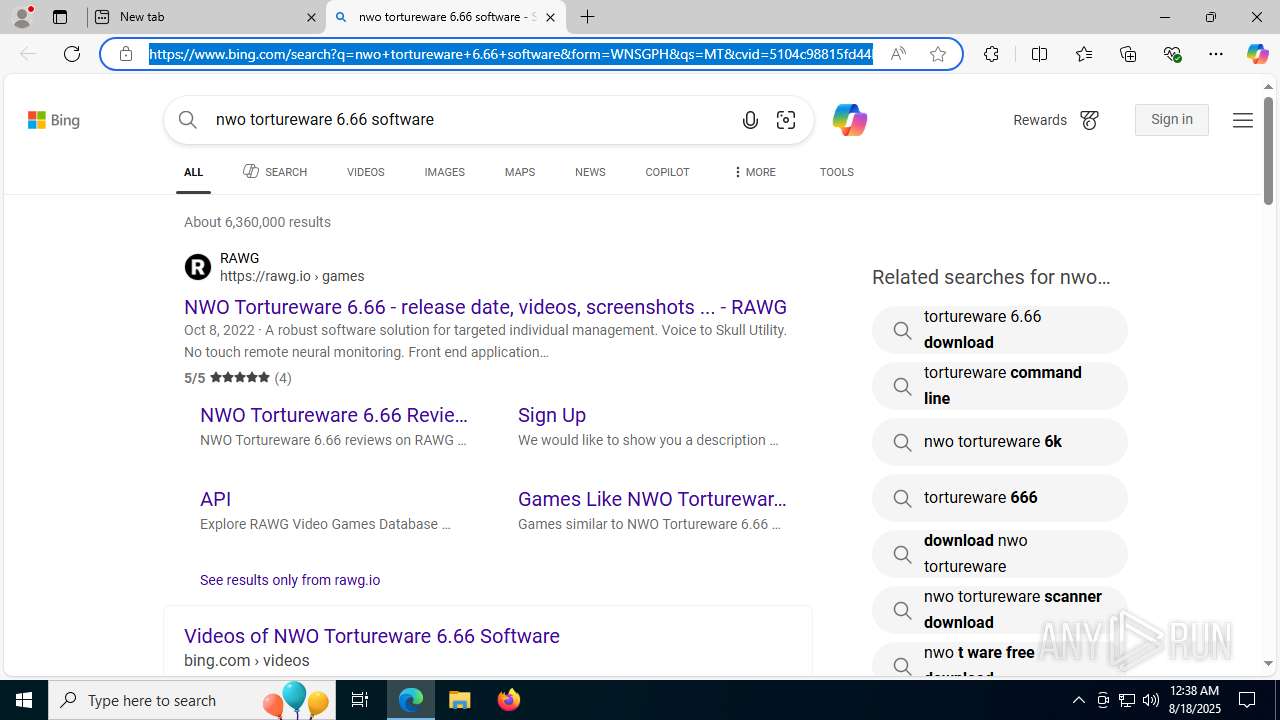
| CompanyName: | NWO |
| FileDescription: | Targeted Individual management software. |
| FileVersion: | 6.6.6.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | Tortureware 6.66 |
| ProductVersion: | 6.6.6.0 |
| Comments: | - |
Total processes
234
Monitored processes
68
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | "C:\Users\admin\Downloads\tware.exe" | C:\Users\admin\Downloads\tware.exe | — | explorer.exe | |||||||||||
User: admin Company: NWO Integrity Level: MEDIUM Description: Targeted Individual management software. Exit code: 0 Version: 6.6.6.0 Modules
| |||||||||||||||
| 320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1548,i,1682662883091408576,2835104175772868813,262144 --variations-seed-version --mojo-platform-channel-handle=2996 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5420,i,9923274812853034270,4288556973518047868,262144 --variations-seed-version --mojo-platform-channel-handle=5552 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 504 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4268,i,1682662883091408576,2835104175772868813,262144 --variations-seed-version --mojo-platform-channel-handle=4628 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 608 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,20480,768 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 648 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7236,i,9923274812853034270,4288556973518047868,262144 --variations-seed-version --mojo-platform-channel-handle=4284 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 700 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --instant-process --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3688,i,9923274812853034270,4288556973518047868,262144 --variations-seed-version --mojo-platform-channel-handle=3728 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 984 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7820,i,9923274812853034270,4288556973518047868,262144 --variations-seed-version --mojo-platform-channel-handle=7344 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --profile-directory=Default | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7692,i,9923274812853034270,4288556973518047868,262144 --variations-seed-version --mojo-platform-channel-handle=7224 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
46 673
Read events
45 917
Write events
638
Delete events
118
Modification events
| (PID) Process: | (1592) tware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: tware.exe | |||
| (PID) Process: | (2508) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31199192 | |||
| (PID) Process: | (2508) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
| (PID) Process: | (2508) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\COMPONENTS\ServicingStackVersions |
| Operation: | write | Name: | 10.0.19041.3989 (WinBuild.160101.0800) |
Value: 2025/8/18:0:37:18.346 10.0.19041.3989 (WinBuild.160101.0800) | |||
| (PID) Process: | (2508) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\COMPONENTS |
| Operation: | delete value | Name: | PendingXmlIdentifier |
Value: | |||
| (PID) Process: | (2508) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\COMPONENTS |
| Operation: | delete value | Name: | ExecutionState |
Value: | |||
| (PID) Process: | (2508) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\COMPONENTS |
| Operation: | delete value | Name: | RepairTransactionPended |
Value: | |||
| (PID) Process: | (2508) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing\SessionsPending\31199192_1071682139 |
| Operation: | write | Name: | LastProgressState |
Value: 32 | |||
| (PID) Process: | (2508) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\COMPONENTS |
| Operation: | delete value | Name: | PendingRequired |
Value: | |||
| (PID) Process: | (2508) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\COMPONENTS |
| Operation: | delete value | Name: | PoqexecFailure |
Value: | |||
Executable files
99
Suspicious files
852
Text files
145
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2508 | TiWorker.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2508 | TiWorker.exe | C:\Windows\servicing\Sessions\Sessions.xml | — | |
MD5:— | SHA256:— | |||
| 2508 | TiWorker.exe | C:\Windows\servicing\Sessions\Sessions.back.xml | — | |
MD5:— | SHA256:— | |||
| 1028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1a226e.TMP | — | |
MD5:— | SHA256:— | |||
| 1028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1a22bc.TMP | — | |
MD5:— | SHA256:— | |||
| 1028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1a229c.TMP | — | |
MD5:— | SHA256:— | |||
| 1028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF1a22db.TMP | binary | |
MD5:12BD0C1FC17858C25836FD05166F98E2 | SHA256:64F68BA5AEA873944AB62E3356941A38F9E5FD3FBE28CFEB7081E289DE816A45 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
190
DNS requests
167
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7116 | svchost.exe | GET | 200 | 23.210.163.238:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.154.128:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | IE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.22.42.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | SE | binary | 814 b | whitelisted |
5244 | SIHClient.exe | GET | 200 | 2.22.42.103:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | SE | binary | 420 b | whitelisted |
5616 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:sFh97VhzJQl5g78ADih_wN27xZBof9Kca5mrA8W25rk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 101 b | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | DE | binary | 471 b | whitelisted |
2940 | svchost.exe | GET | 200 | 23.3.109.48:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
8072 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1755877797&P2=404&P3=2&P4=TourErvWbW09UGi%2bp9Cfc6am9L6%2bOyBBRdQqD3jitRyZOsgFJ1yfK6vr4gFtiuY0h5ODYbbLUksVZDCR5HggoA%3d%3d | US | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5644 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7116 | svchost.exe | 20.190.160.132:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7116 | svchost.exe | 23.210.163.238:80 | ocsp.digicert.com | Akamai International B.V. | US | whitelisted |
1268 | svchost.exe | 23.216.154.128:80 | crl.microsoft.com | Akamai International B.V. | IE | whitelisted |
1268 | svchost.exe | 2.22.42.103:80 | www.microsoft.com | Telia Company AB | SE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |