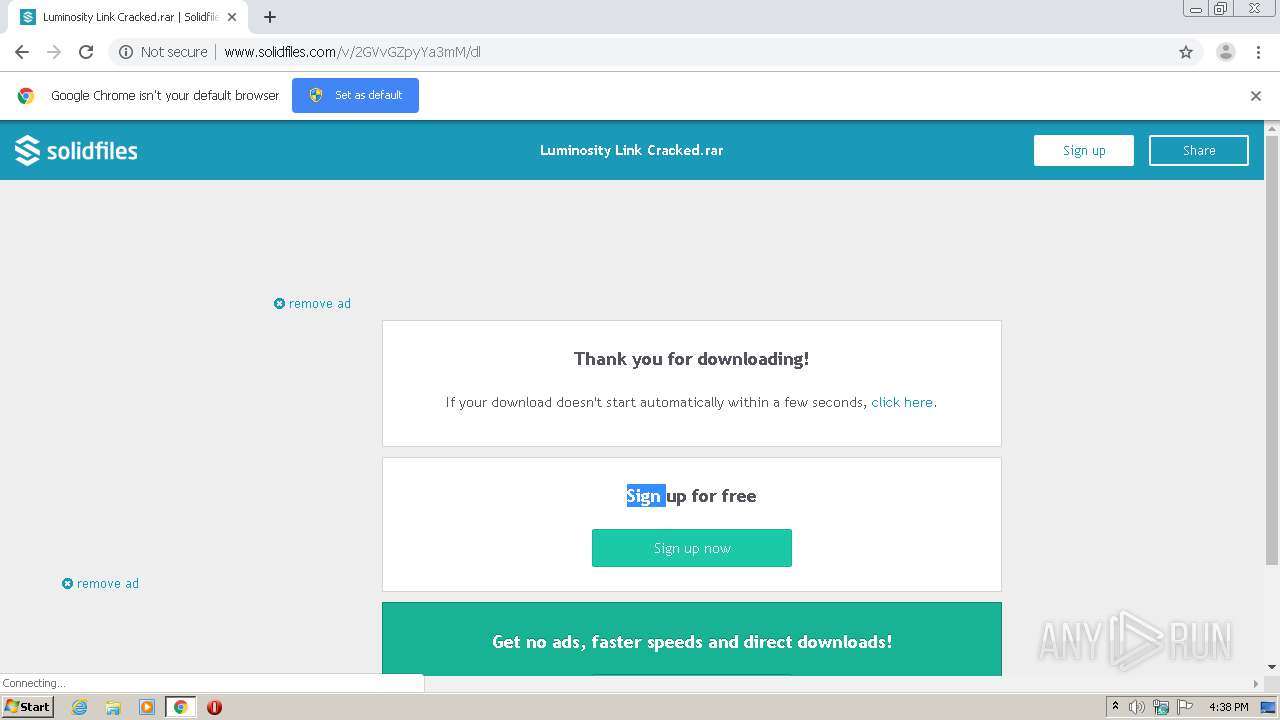
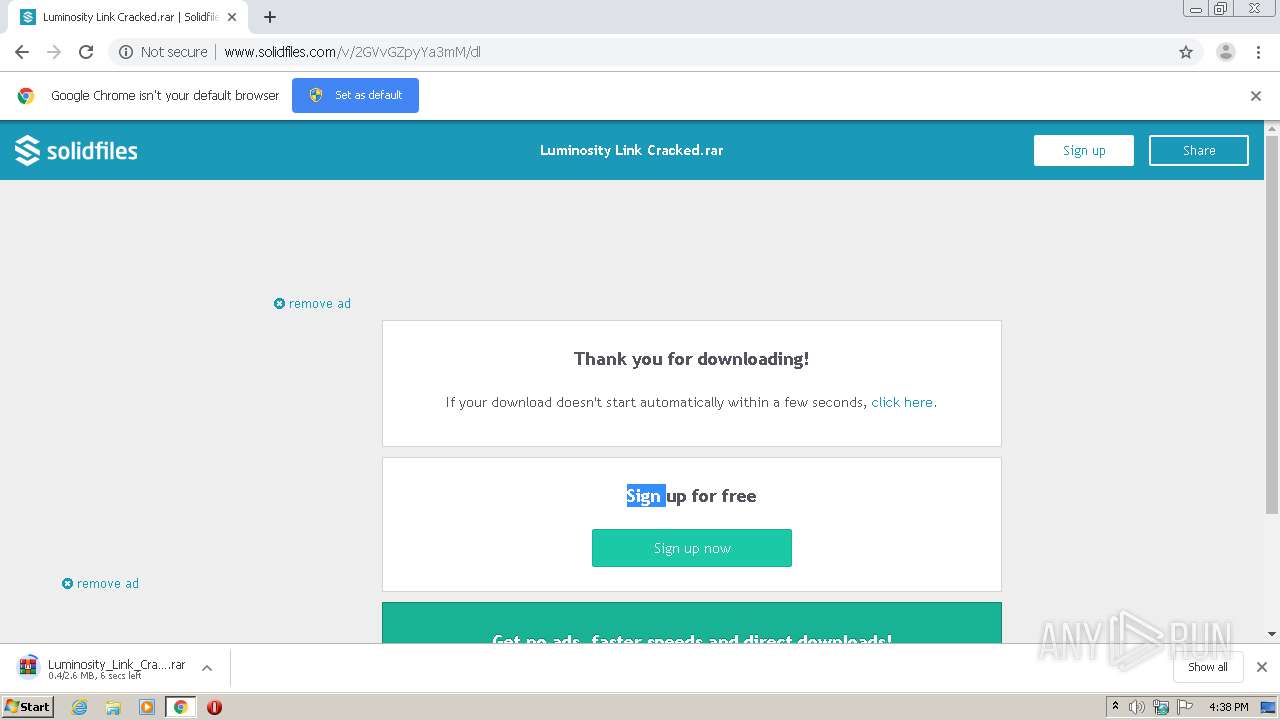
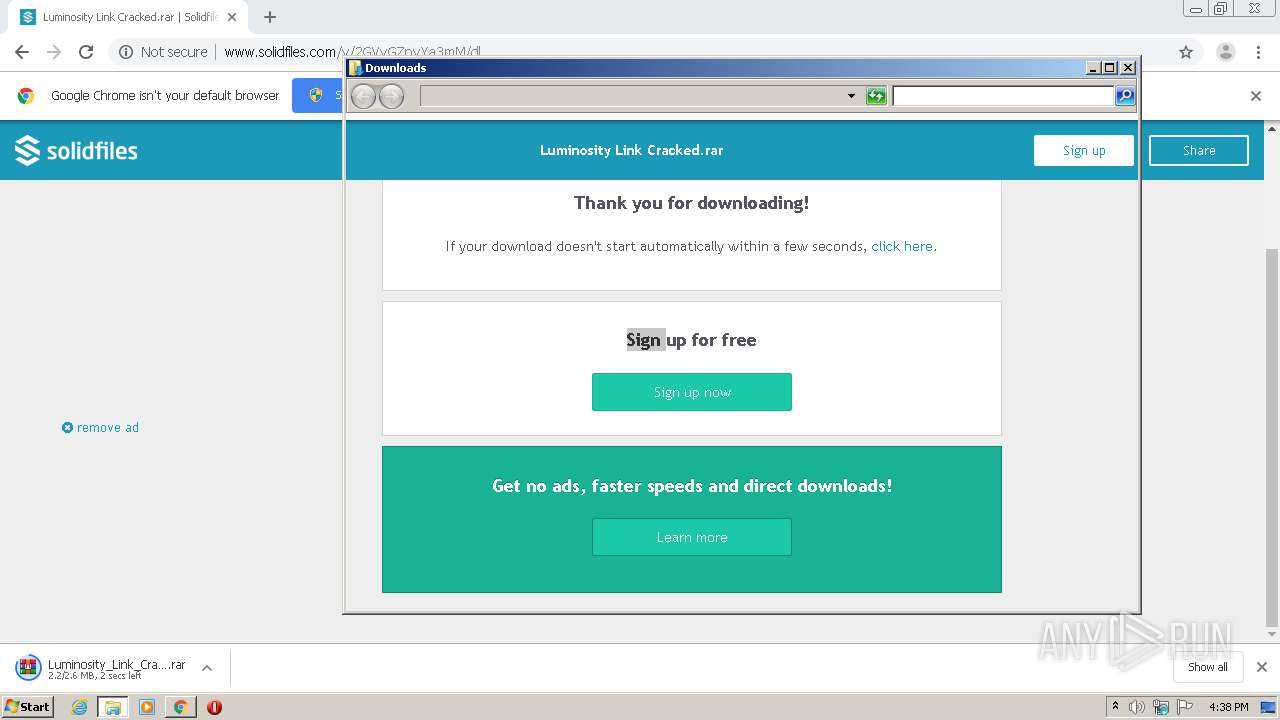
| URL: | http://www.solidfiles.com/v/2GVvGZpyYa3mM |
| Full analysis: | https://app.any.run/tasks/bf886bb8-7eda-4ade-8928-3f45ec3ad352 |
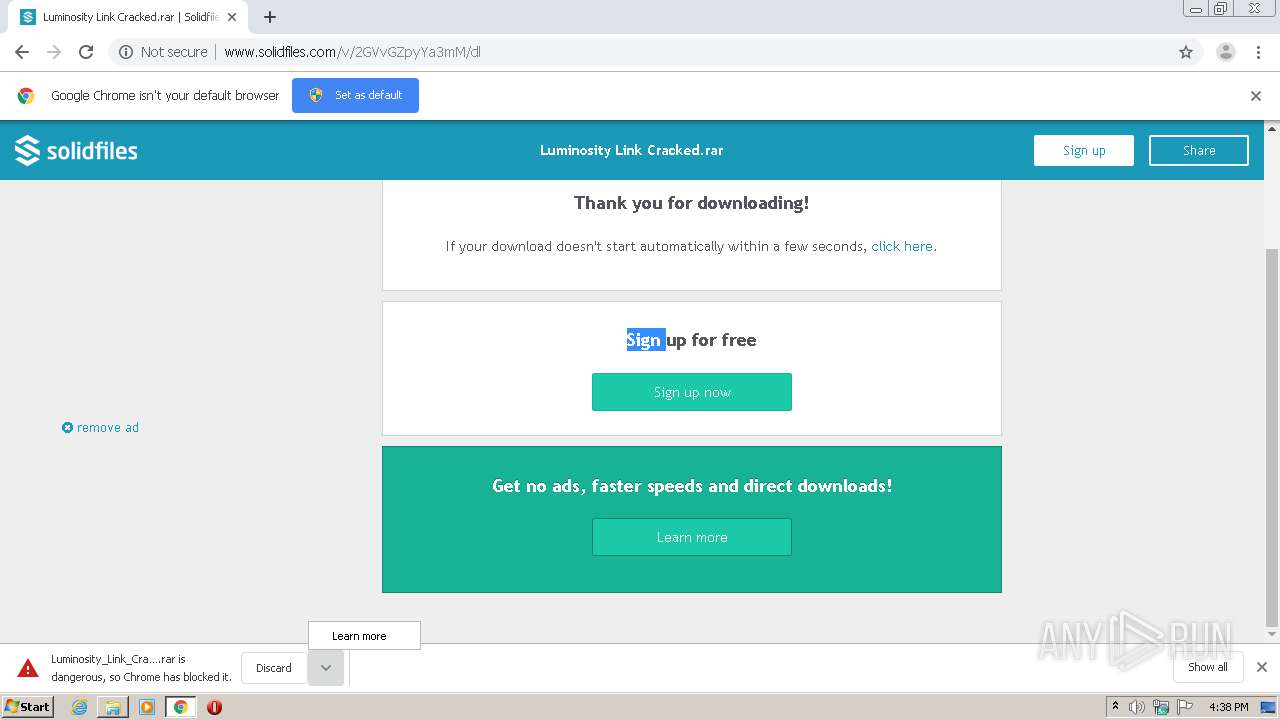
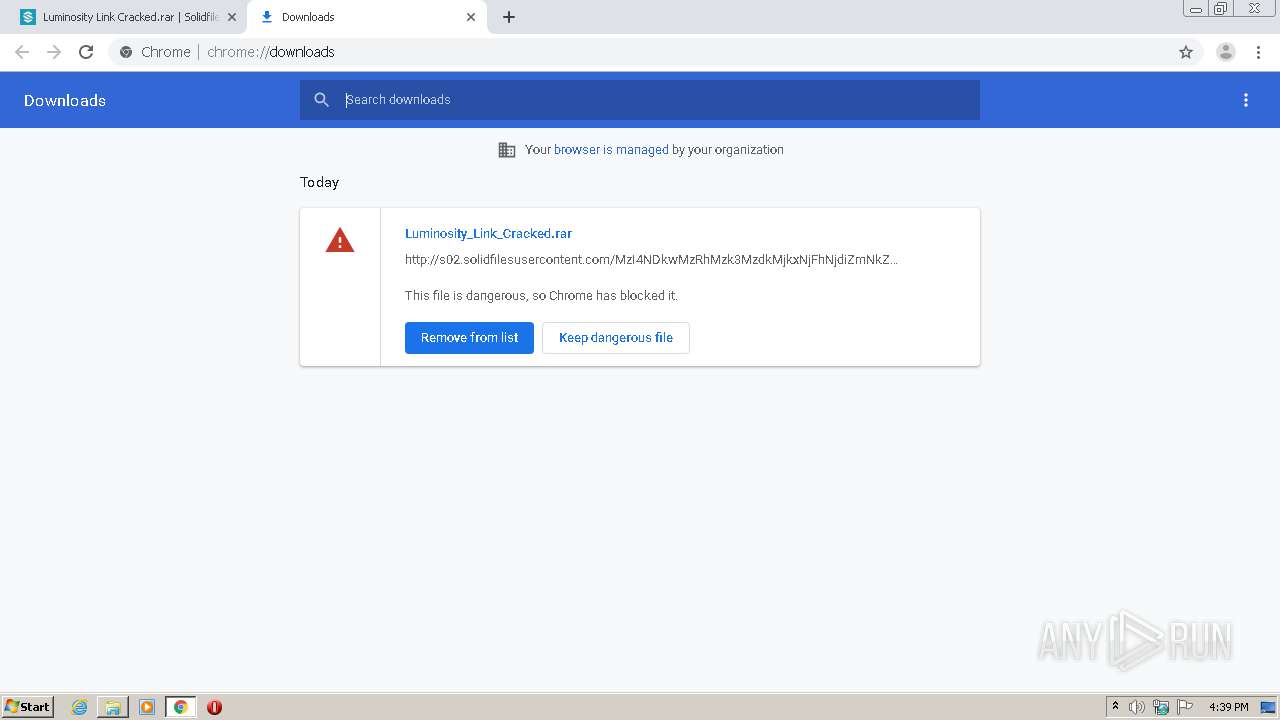
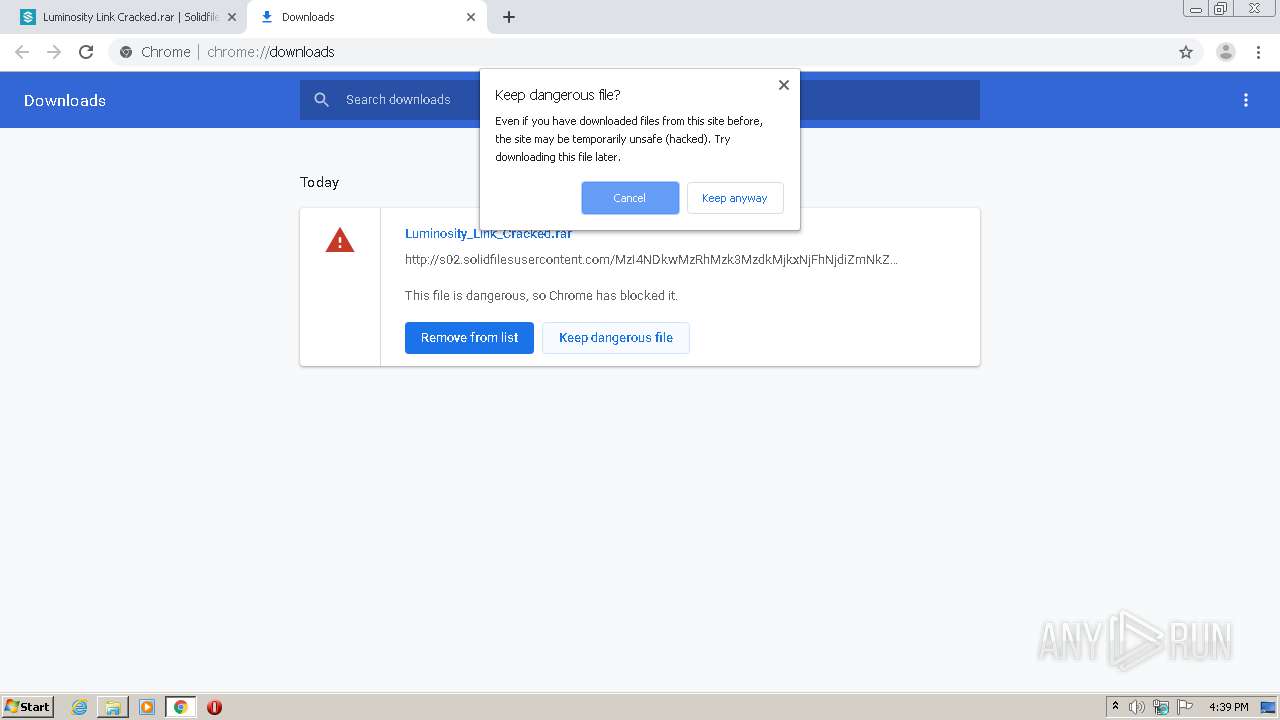
| Verdict: | Malicious activity |
| Analysis date: | April 13, 2021, 15:38:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5081360622F621DB4235F10B4D86FC11 |
| SHA1: | A764300F6BADD5BDD361DAAA160316C7EF2486A1 |
| SHA256: | B0E1CE88CF54CEEB35AC0A5167B9FE27267783220AFBEA27EE9FAF30F1A9571D |
| SSDEEP: | 3:N1KJS4kIKX1VcVPo:Cc4k3X1VWPo |
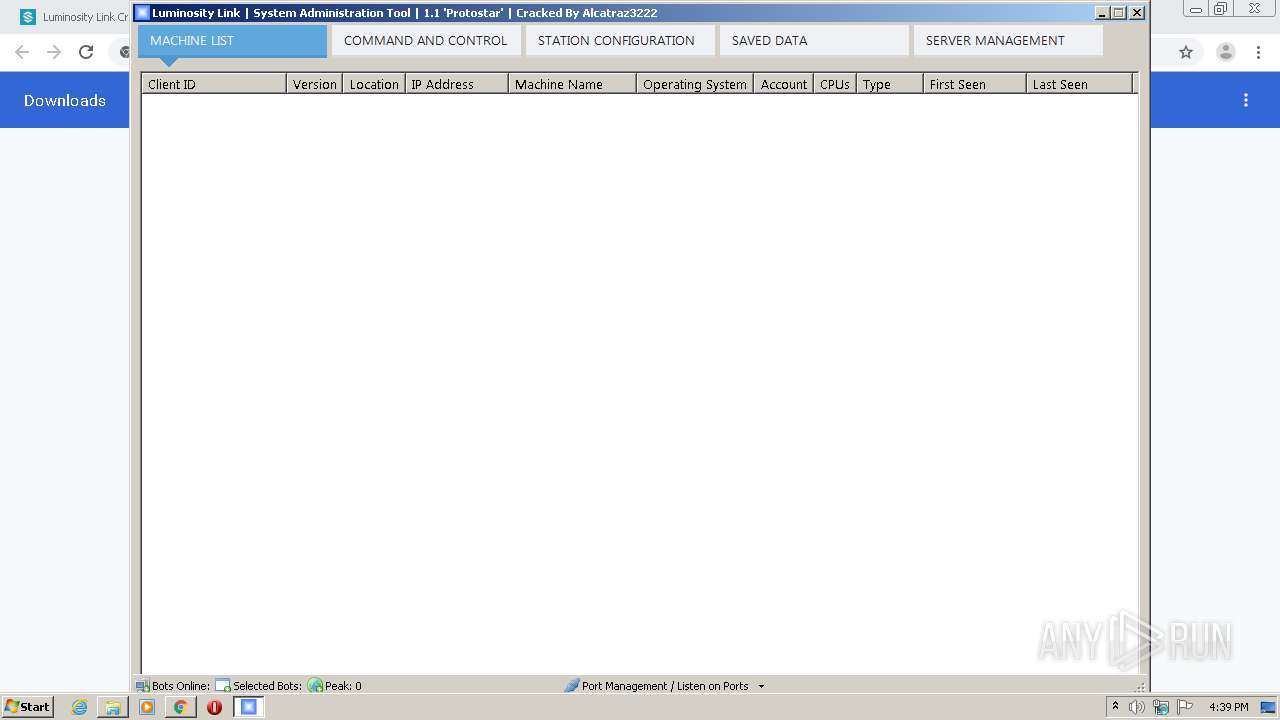
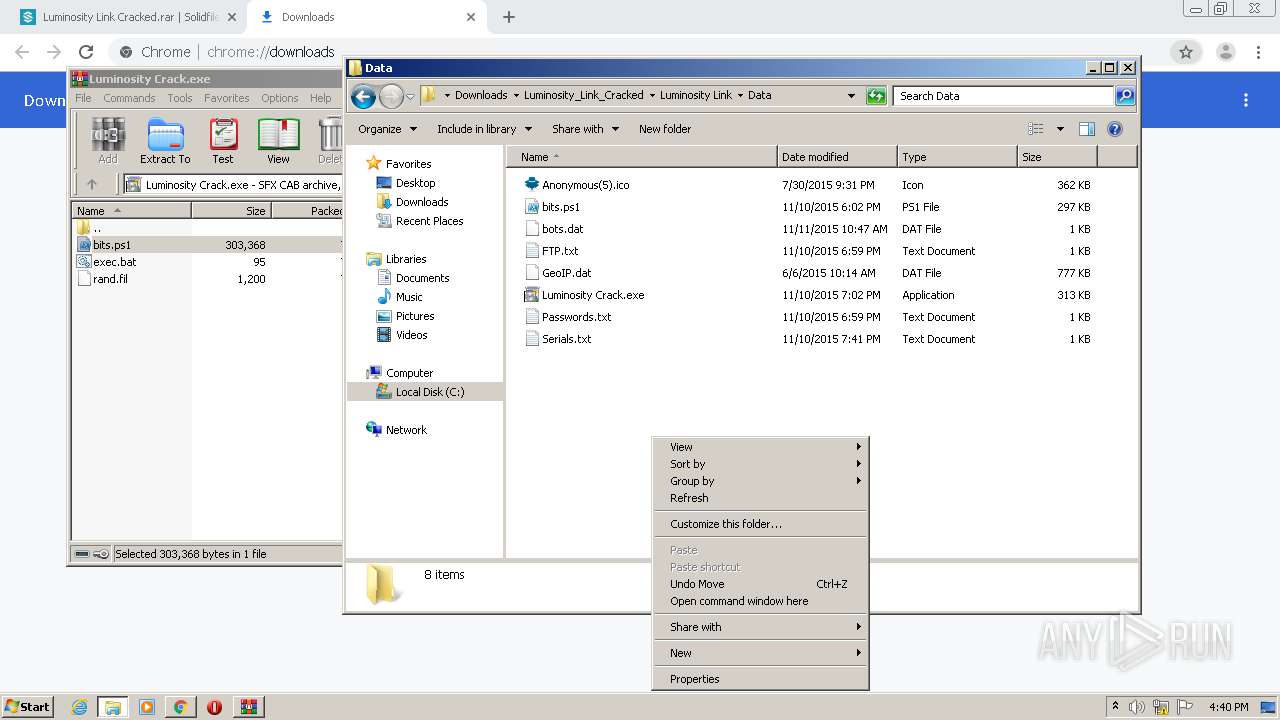
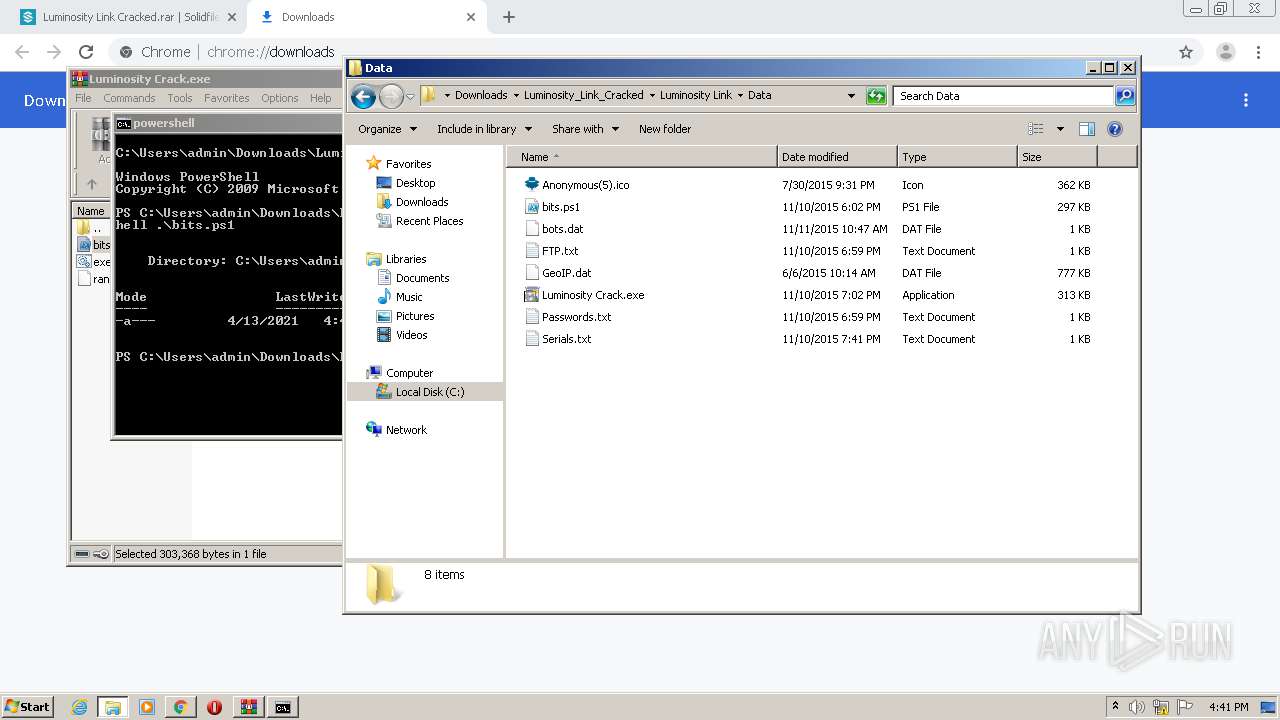
MALICIOUS
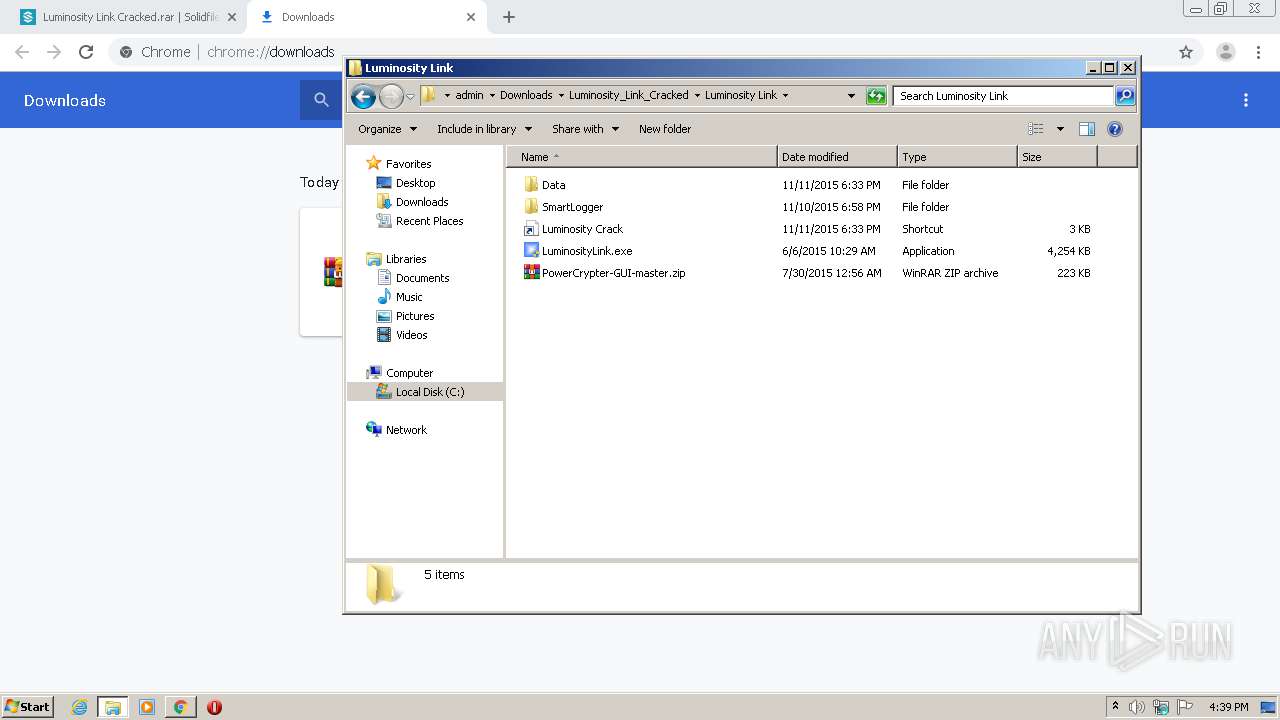
Application was dropped or rewritten from another process
- LuminosityLink.exe (PID: 480)
- LuminosityLink.exe (PID: 1060)
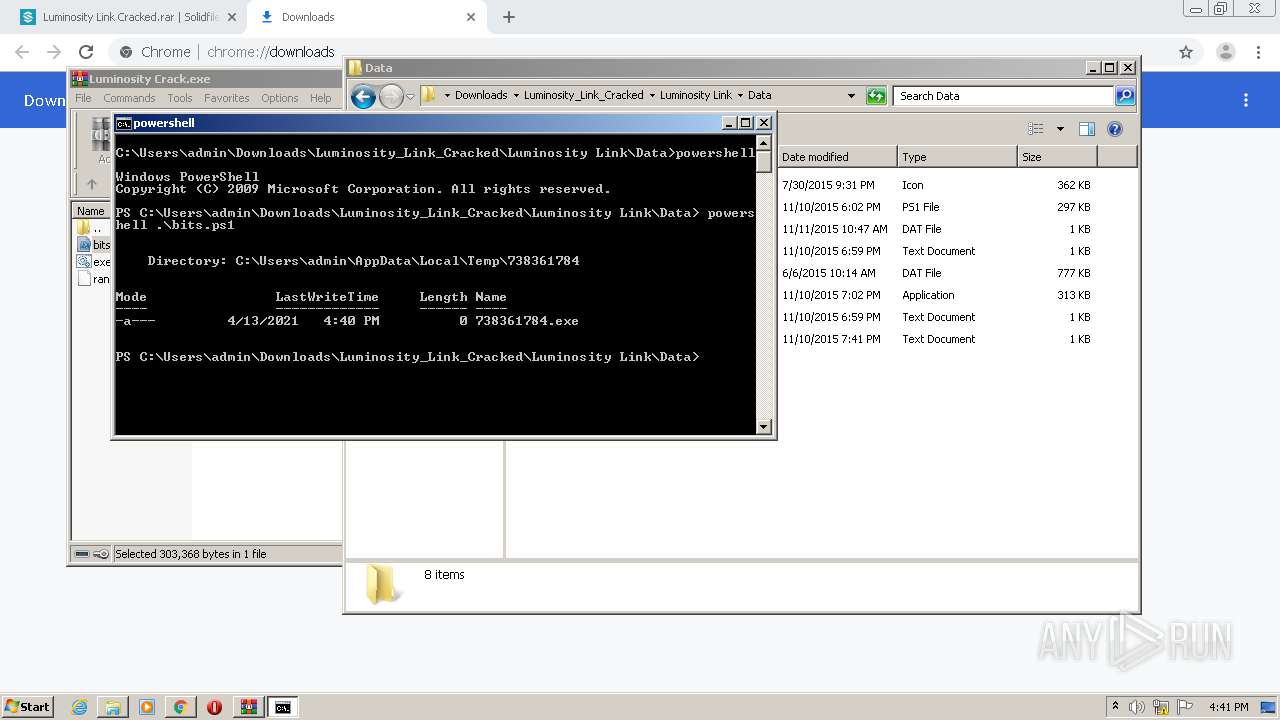
- 738361784.exe (PID: 2364)
- sysmon.exe (PID: 2980)
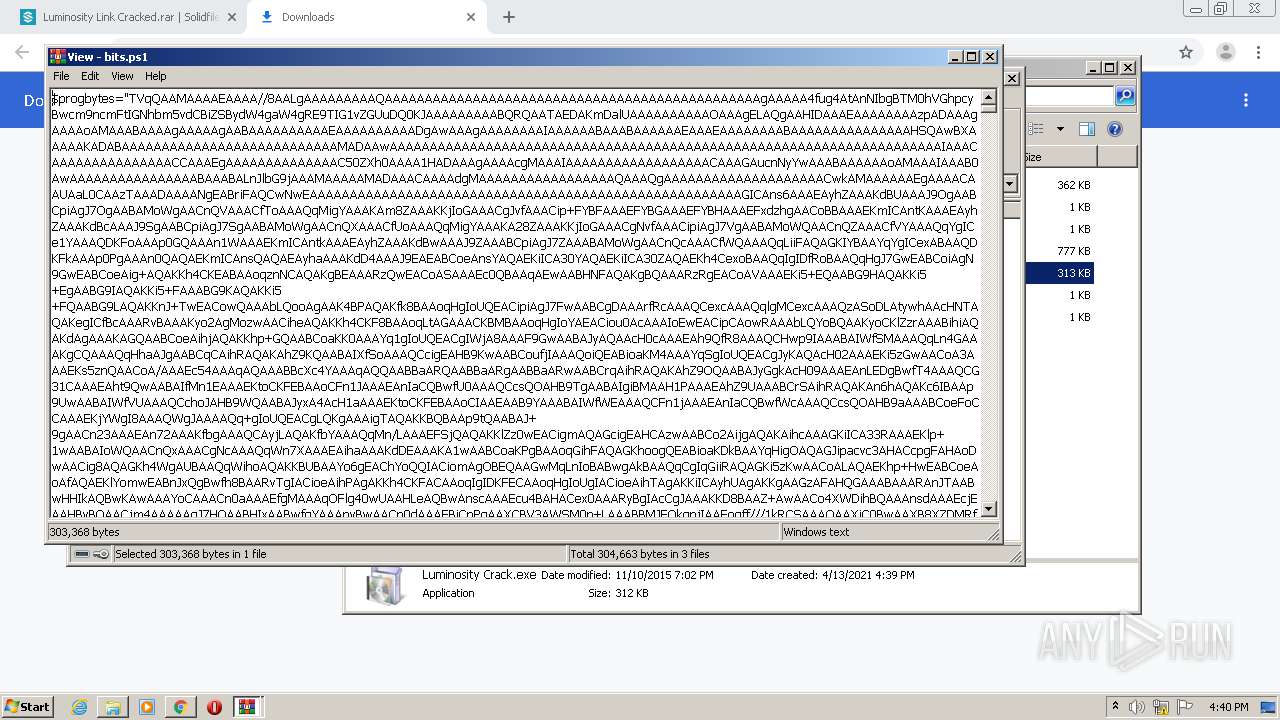
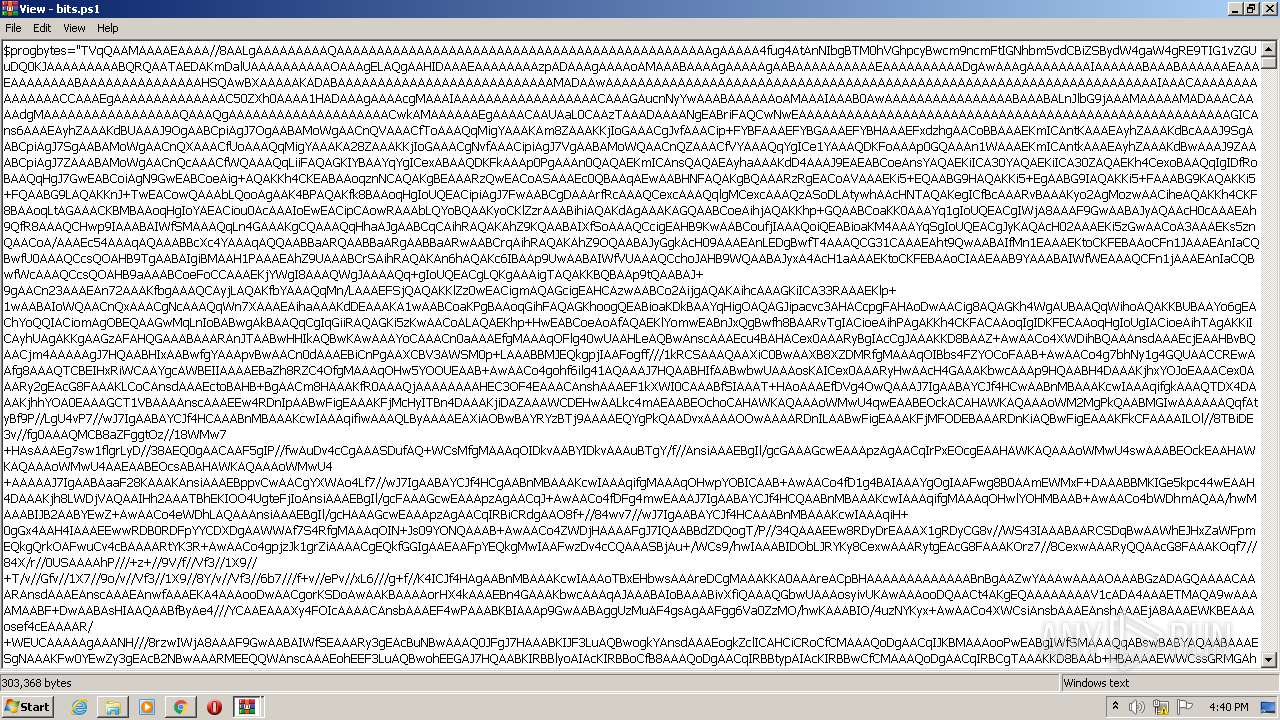
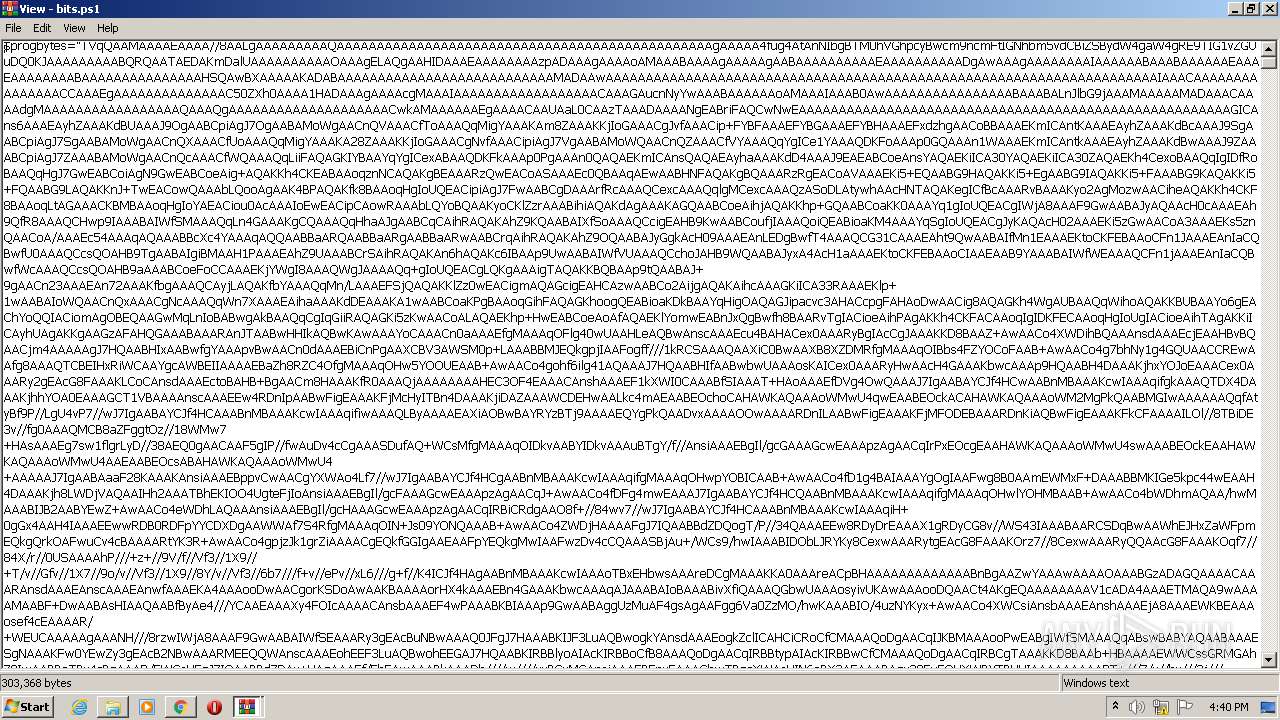
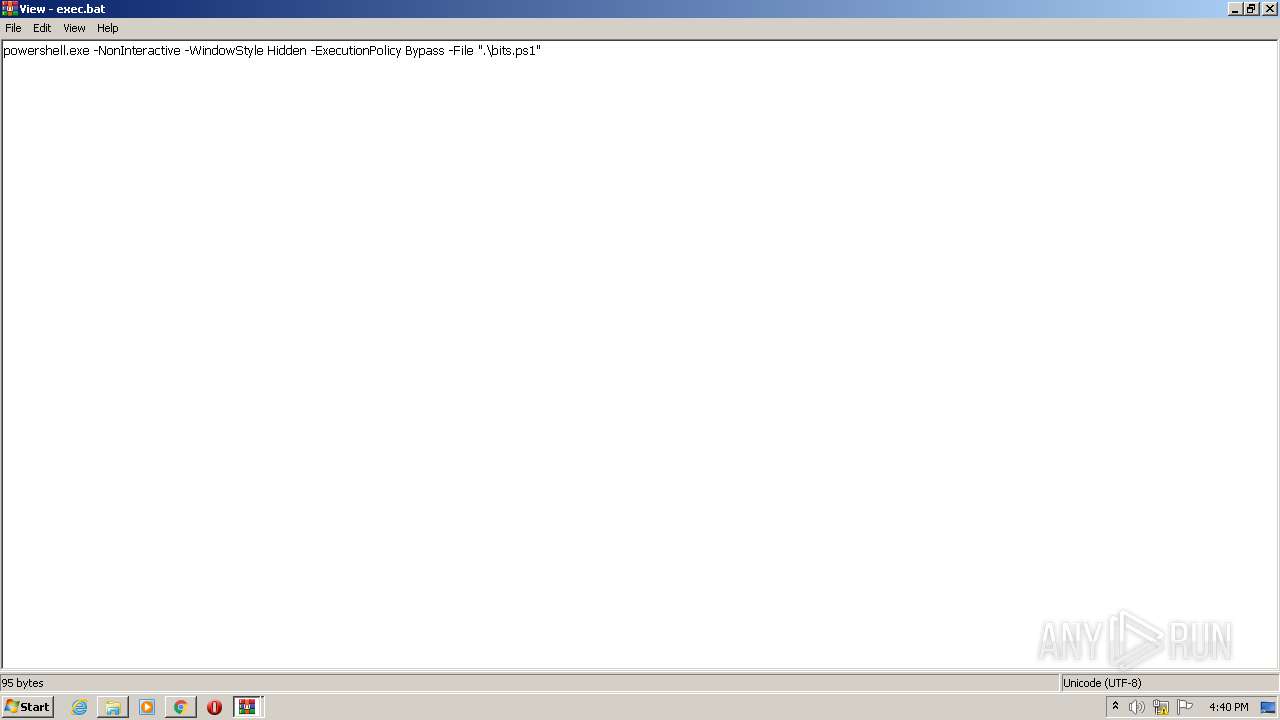
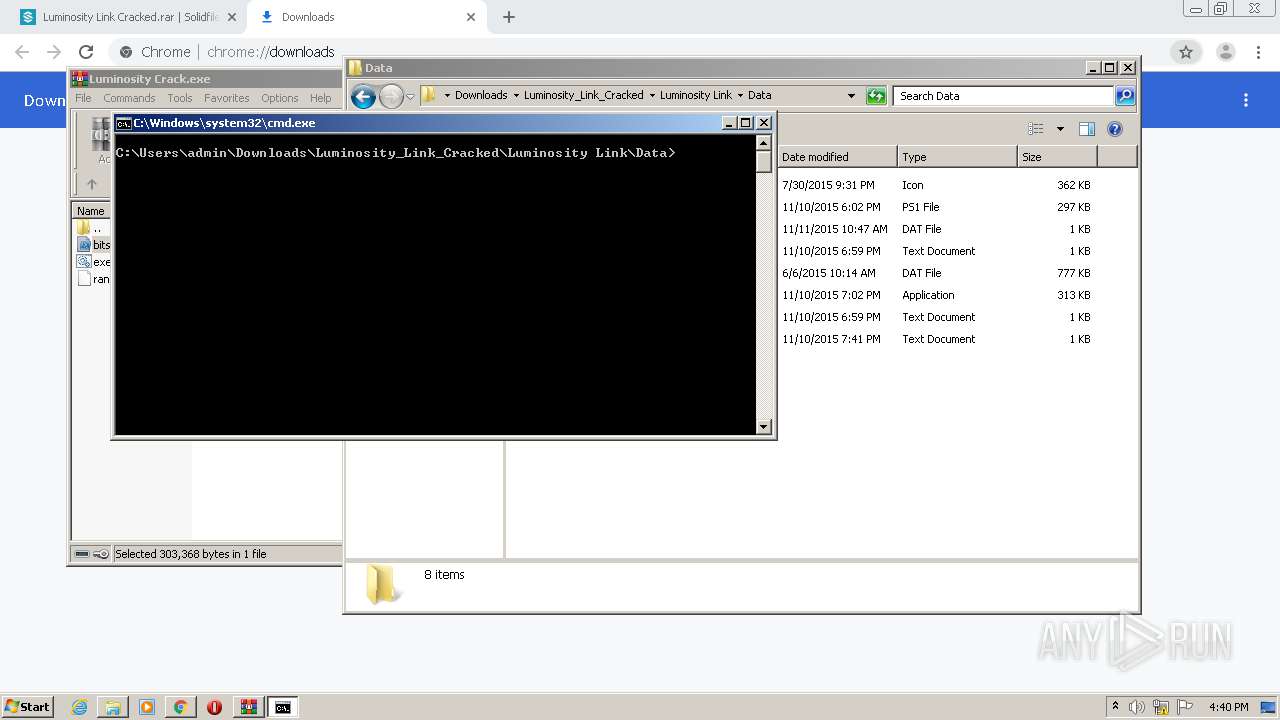
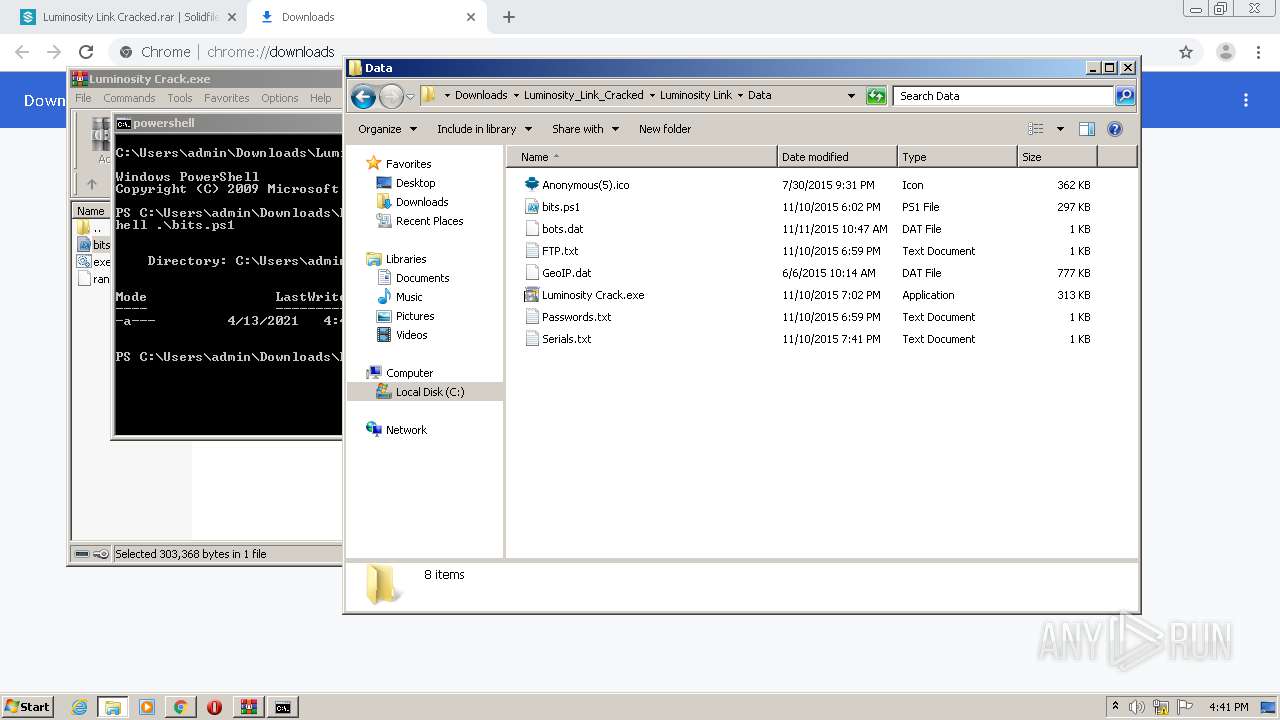
Executes PowerShell scripts
- cmd.exe (PID: 2952)
Application was injected by another process
- taskeng.exe (PID: 1548)
- conhost.exe (PID: 1520)
- dwm.exe (PID: 1676)
- host.exe (PID: 4048)
- explorer.exe (PID: 1784)
- ctfmon.exe (PID: 1852)
Changes the login/logoff helper path in the registry
- sysmon.exe (PID: 2980)
Runs injected code in another process
- sysmon.exe (PID: 2980)
Changes the autorun value in the registry
- sysmon.exe (PID: 2980)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1804)
Creates files in the user directory
- explorer.exe (PID: 1784)
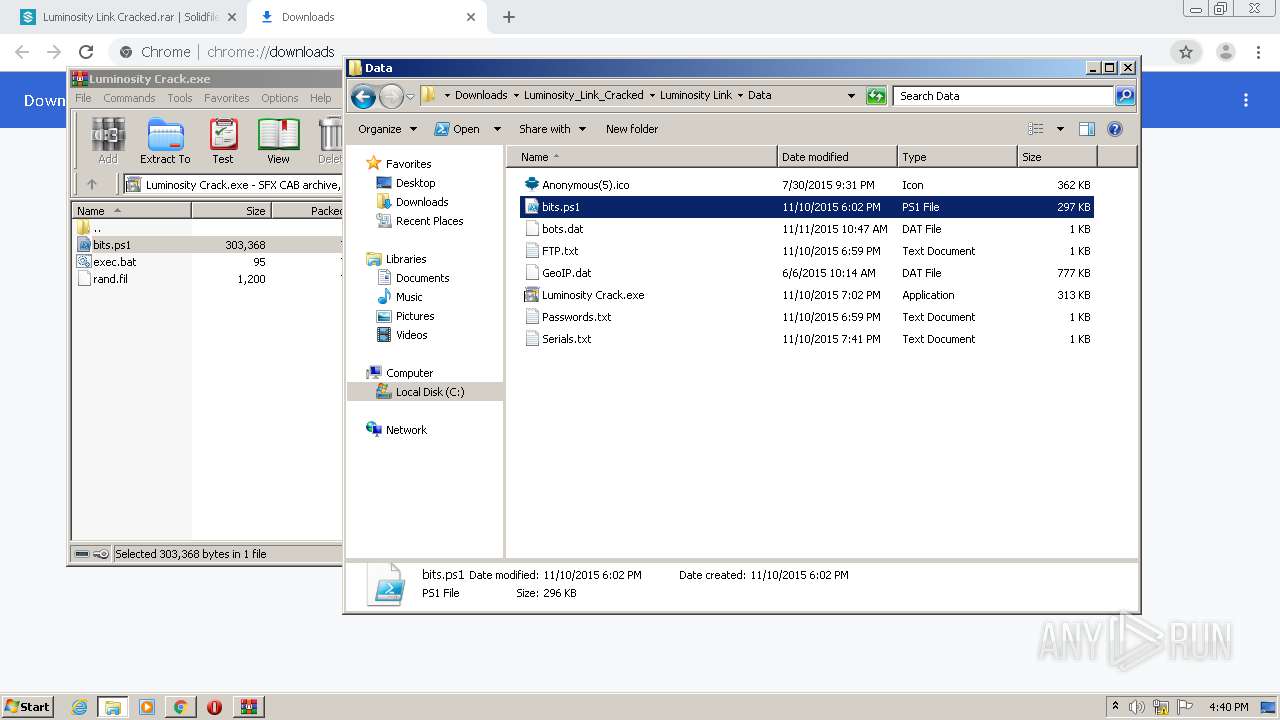
- powershell.exe (PID: 3088)
- powershell.exe (PID: 1392)
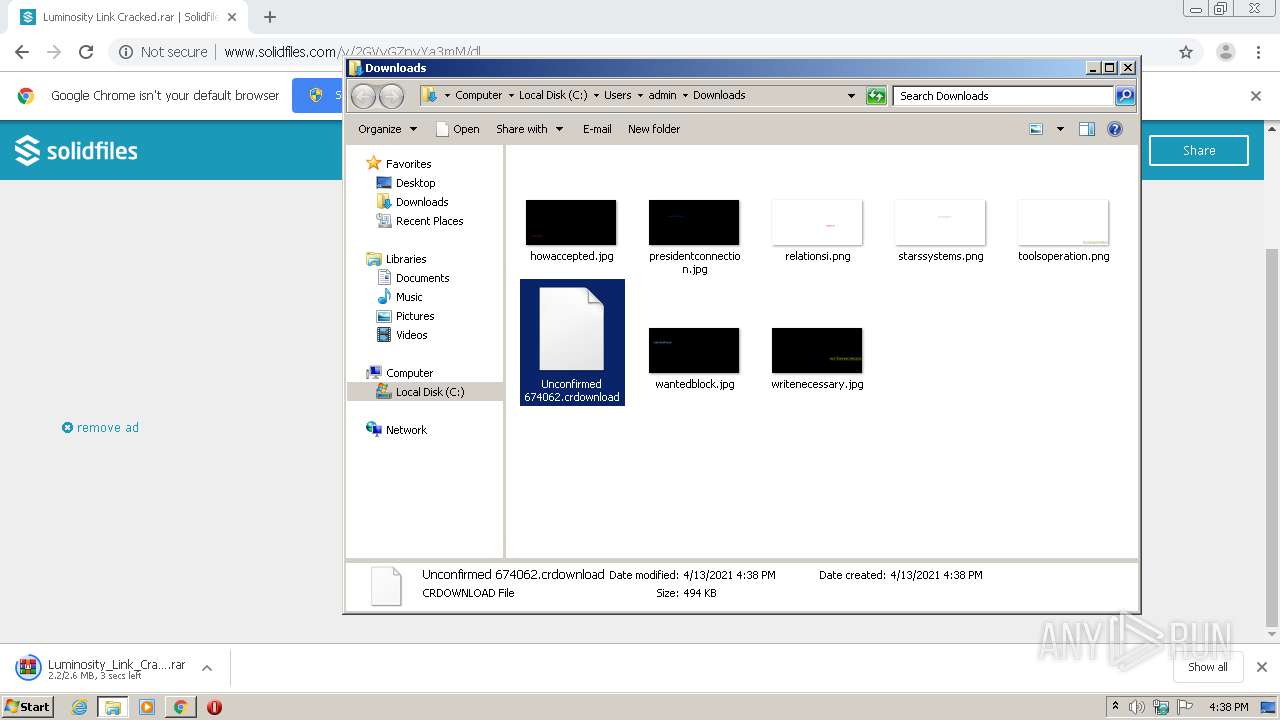
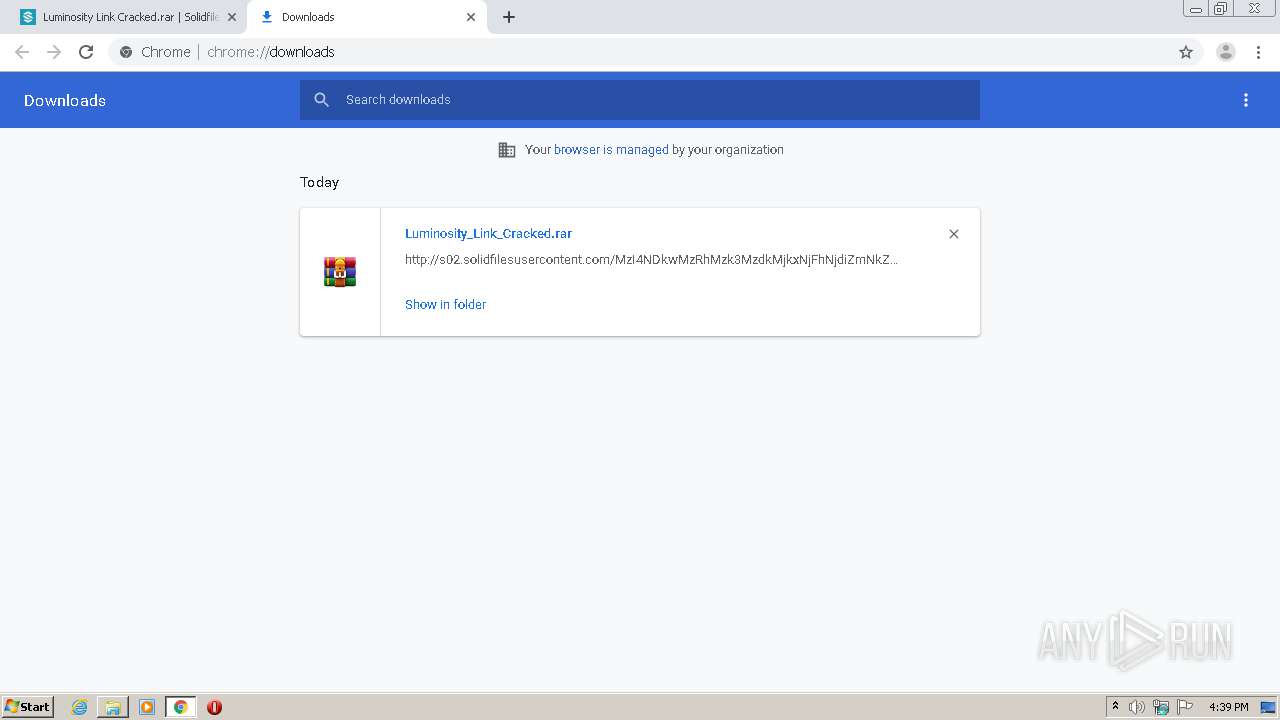
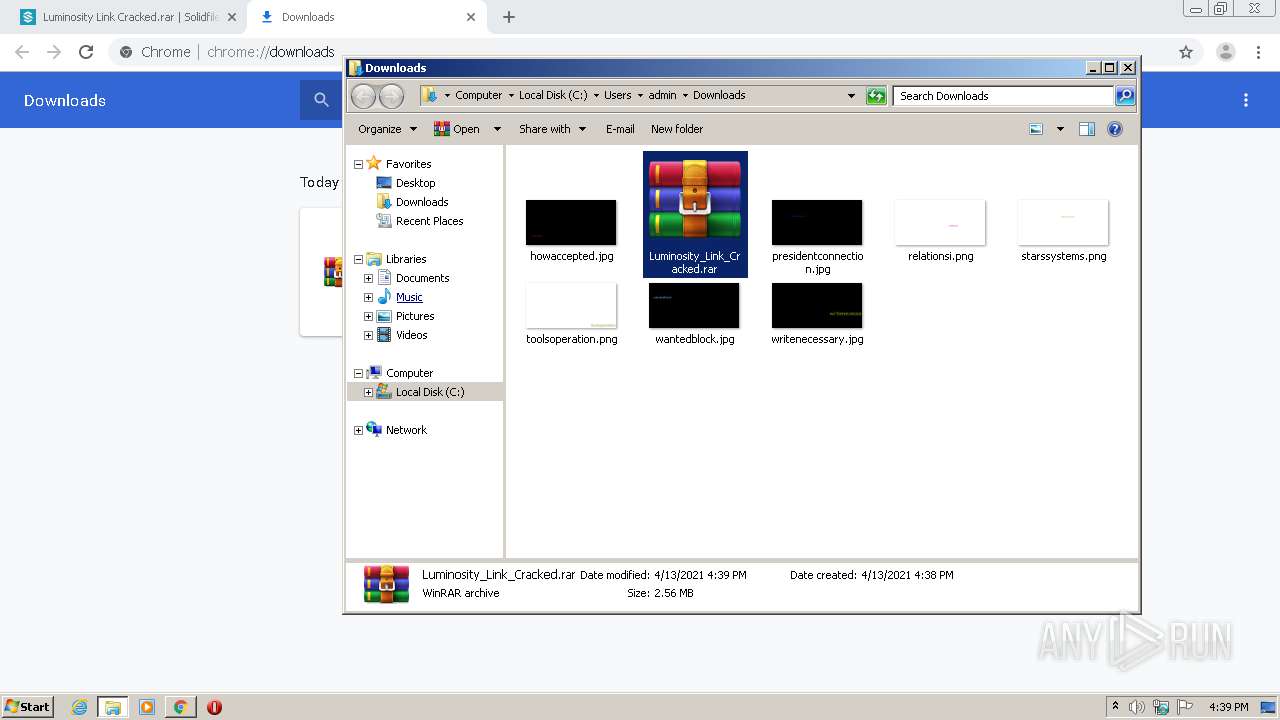
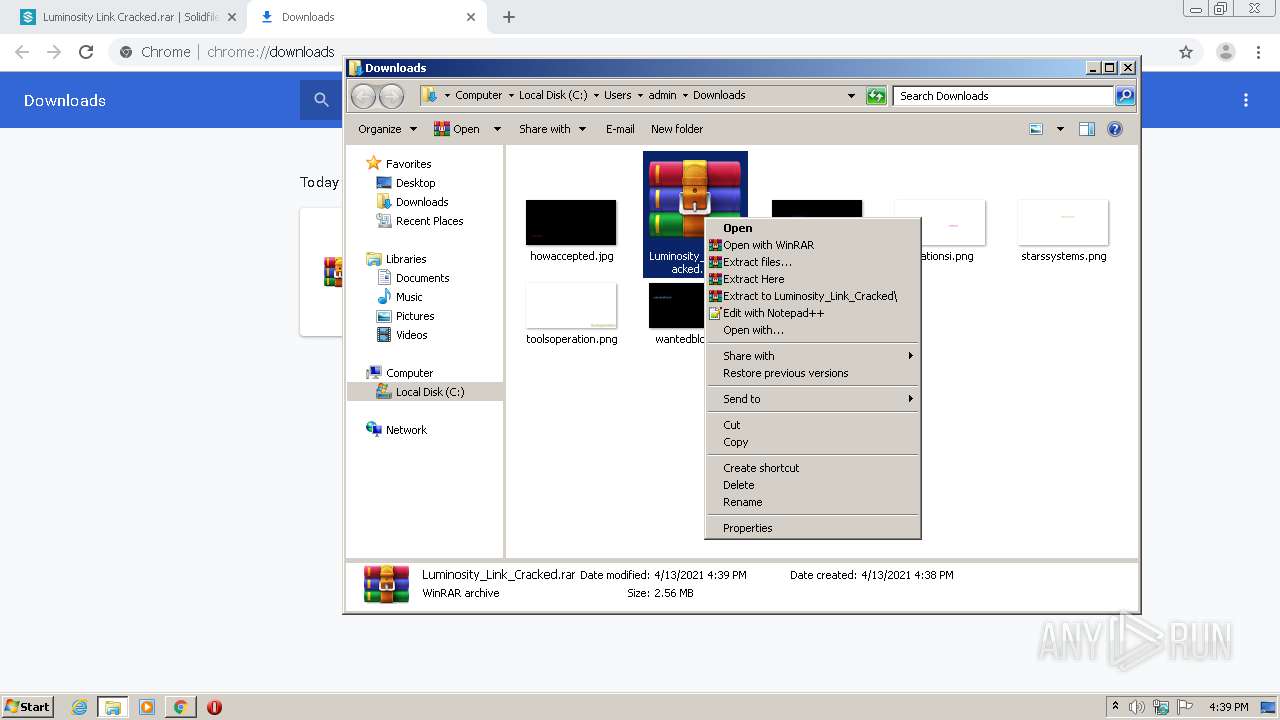
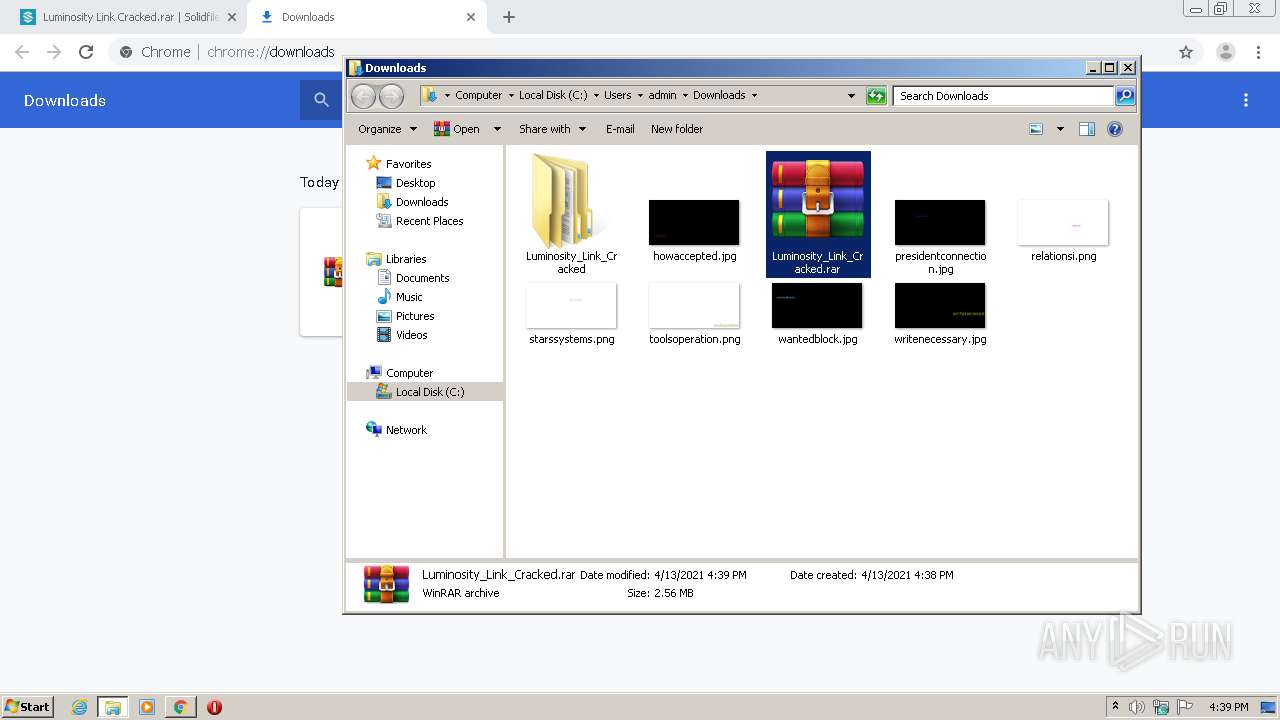
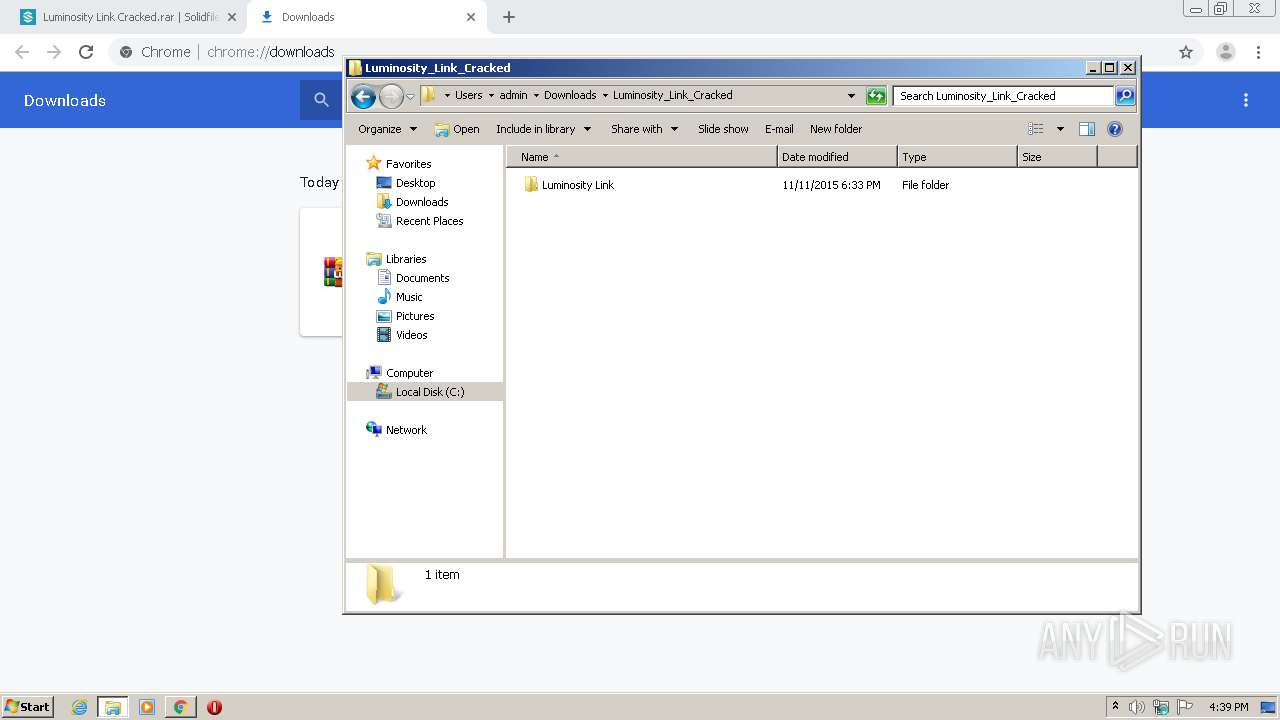
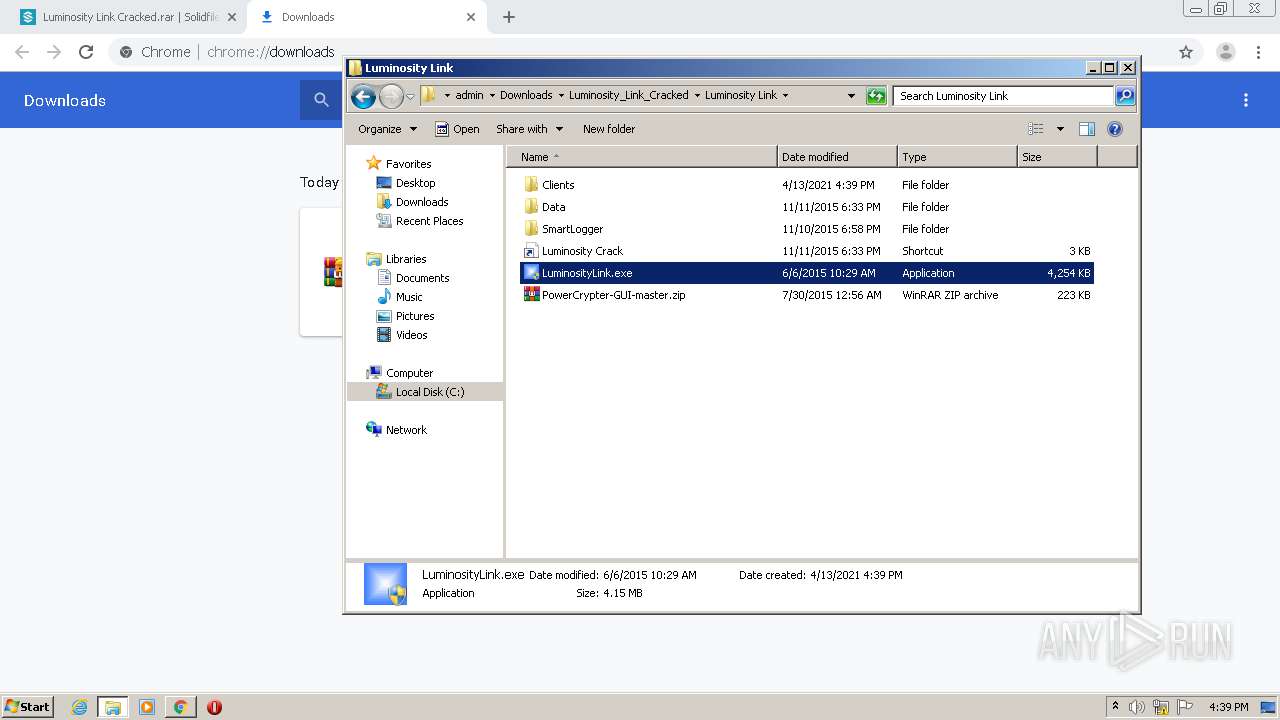
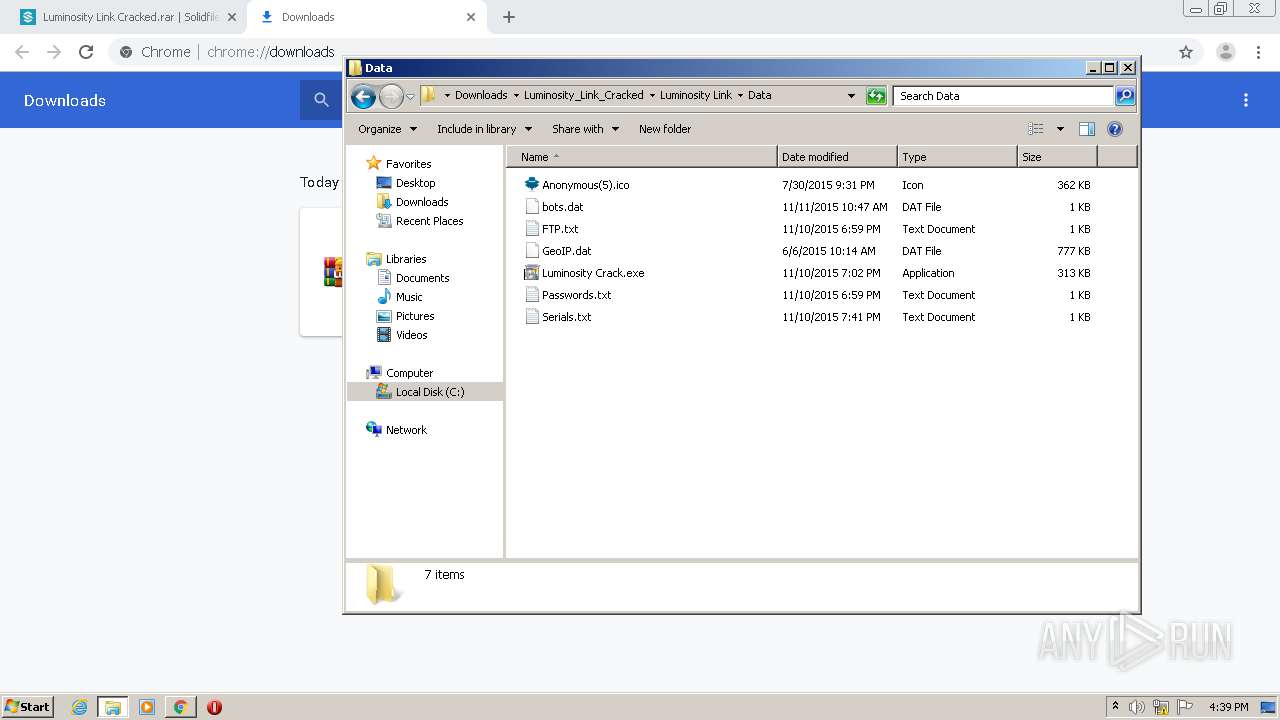
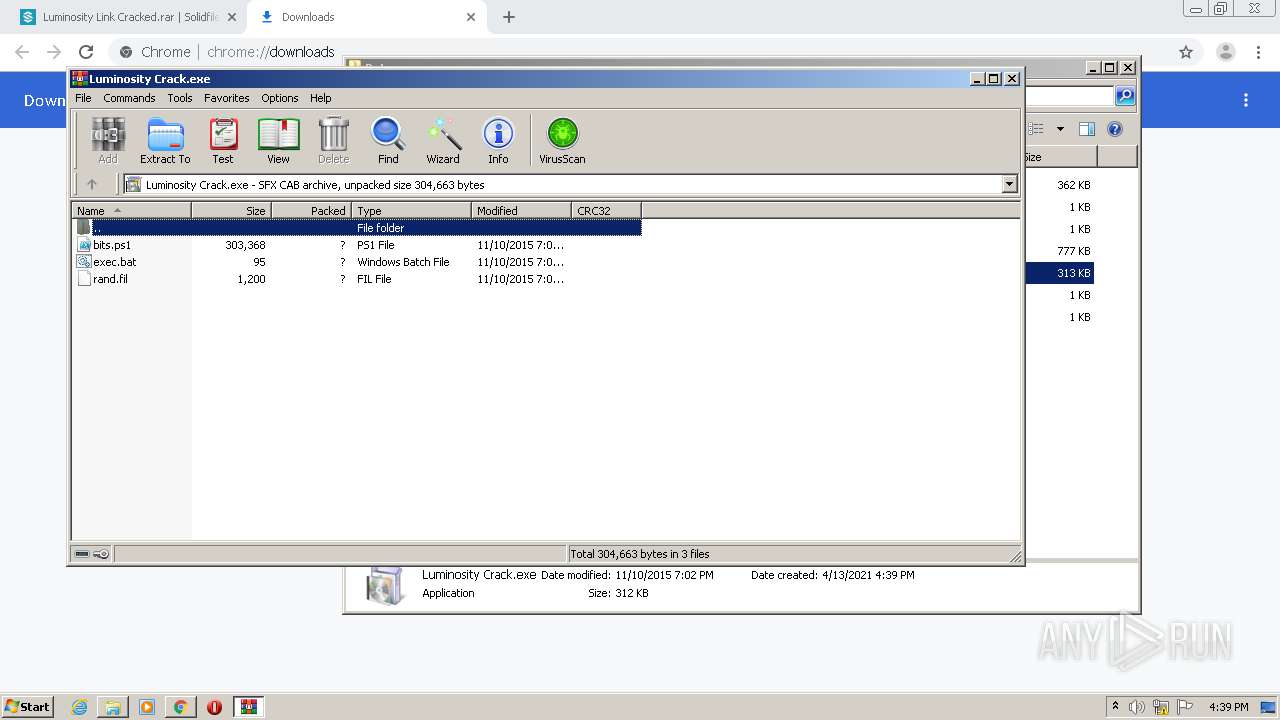
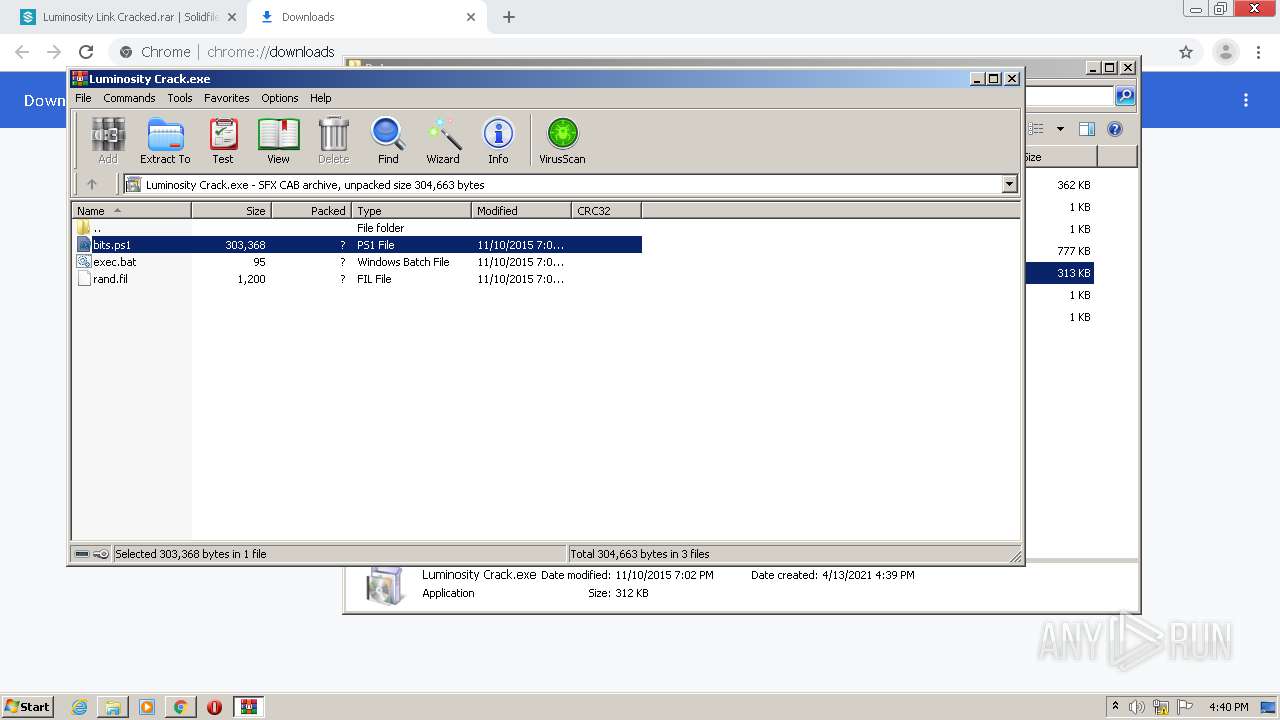
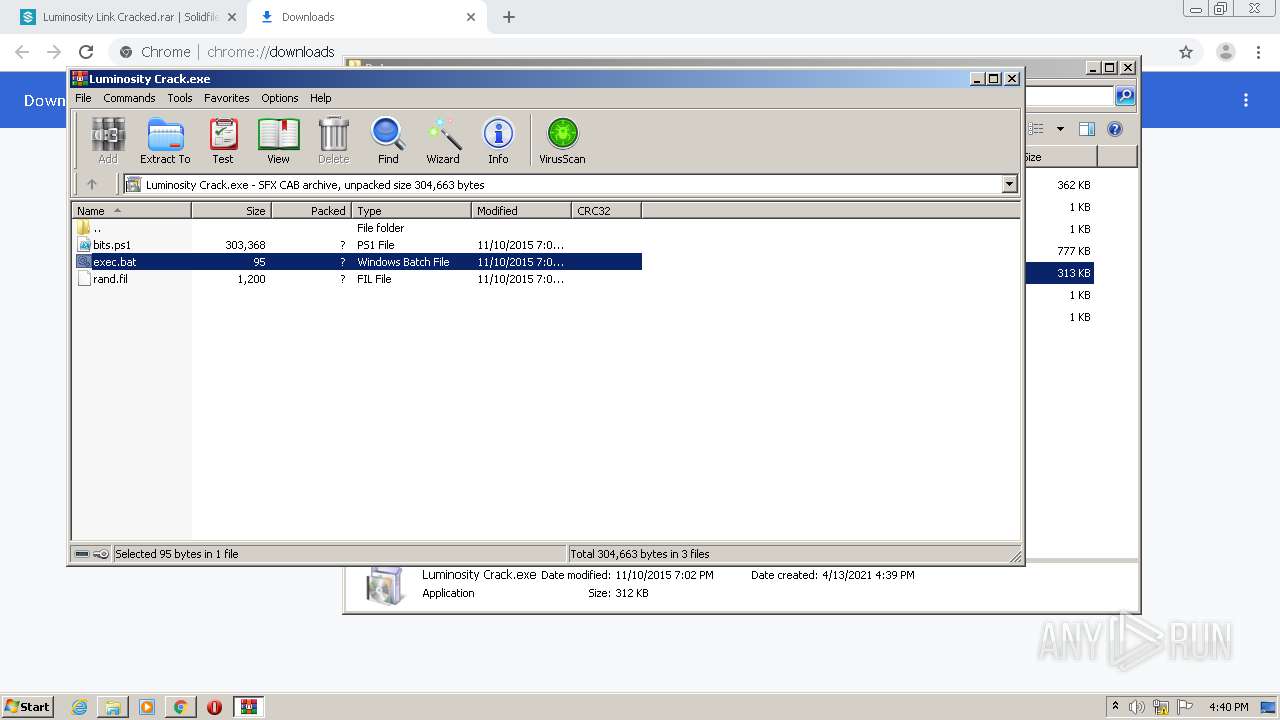
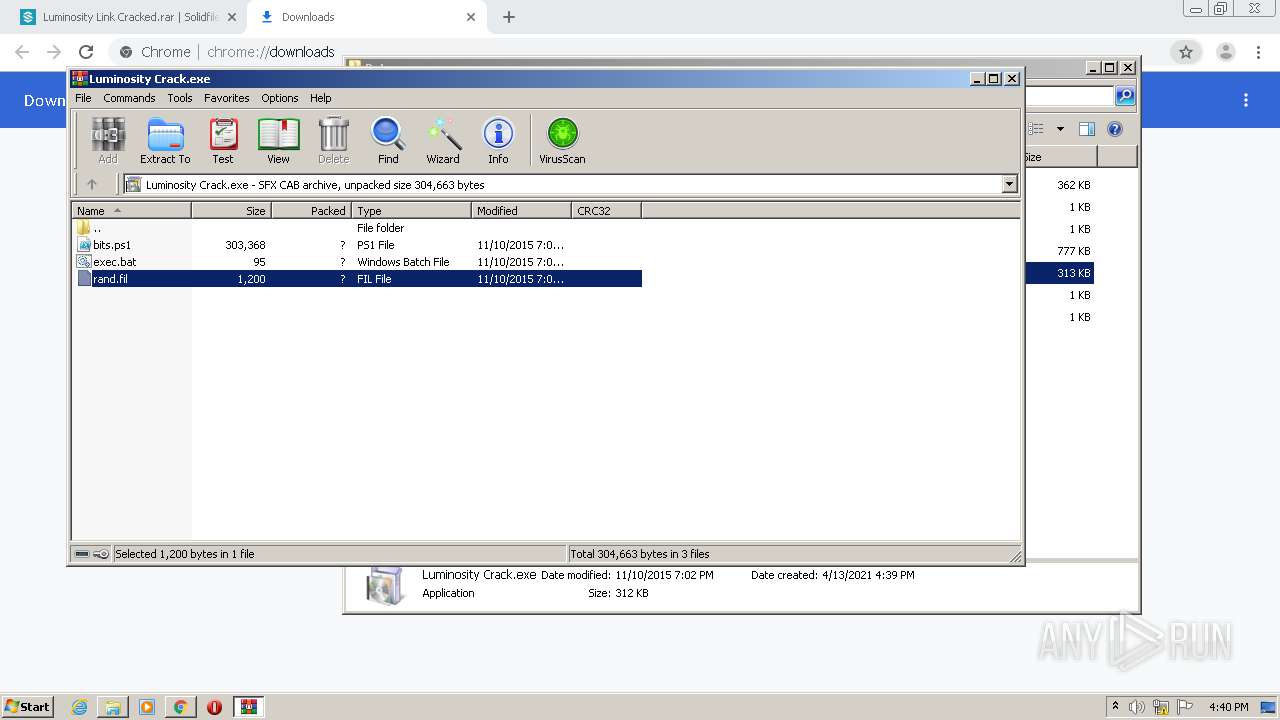
Executable content was dropped or overwritten
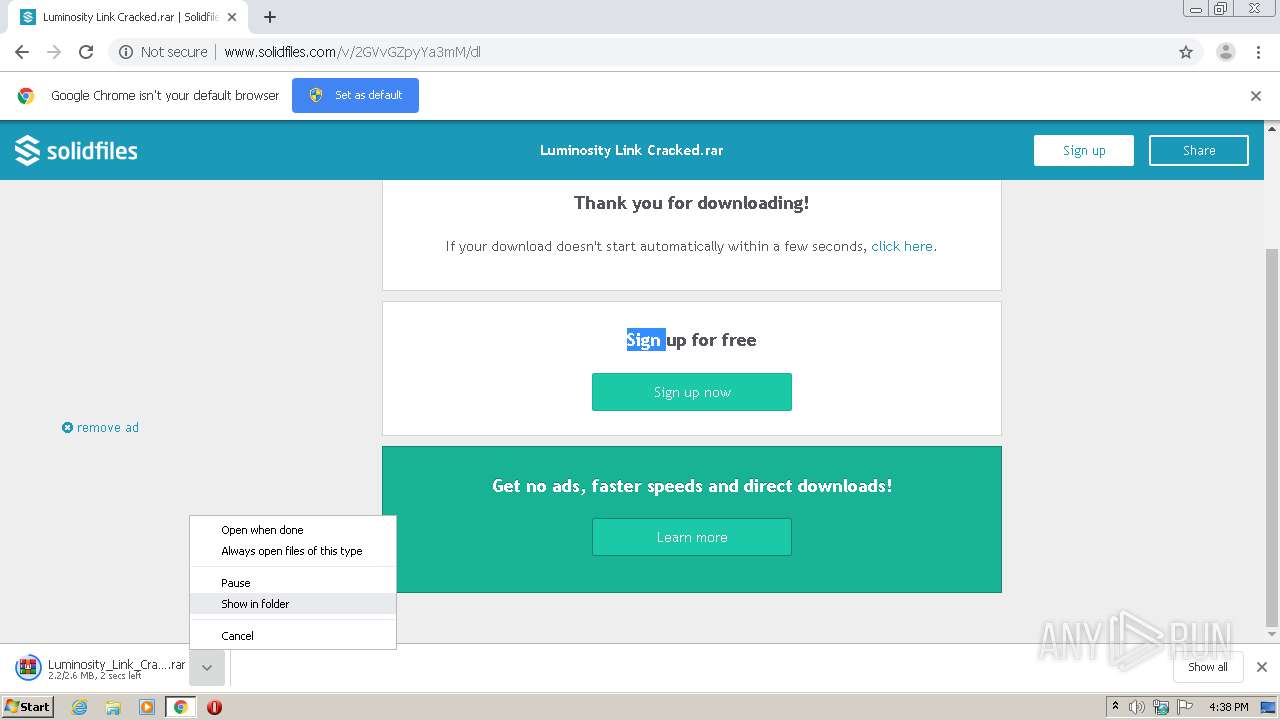
- WinRAR.exe (PID: 3972)
- powershell.exe (PID: 1392)
- 738361784.exe (PID: 2364)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3972)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 1784)
Application launched itself
- powershell.exe (PID: 3088)
Executes PowerShell scripts
- powershell.exe (PID: 3088)
Creates files in the program directory
- 738361784.exe (PID: 2364)
- sysmon.exe (PID: 2980)
Starts itself from another location
- 738361784.exe (PID: 2364)
INFO
Application launched itself
- chrome.exe (PID: 1804)
Reads the hosts file
- chrome.exe (PID: 1804)
- chrome.exe (PID: 3764)
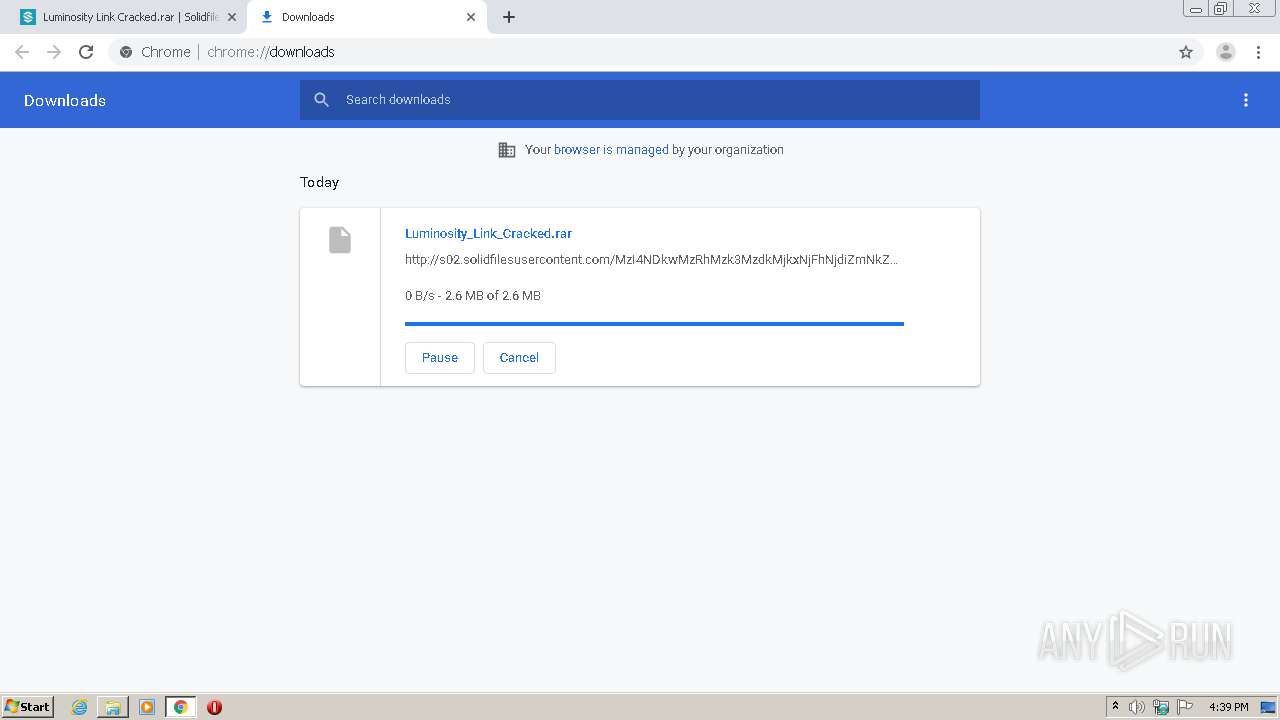
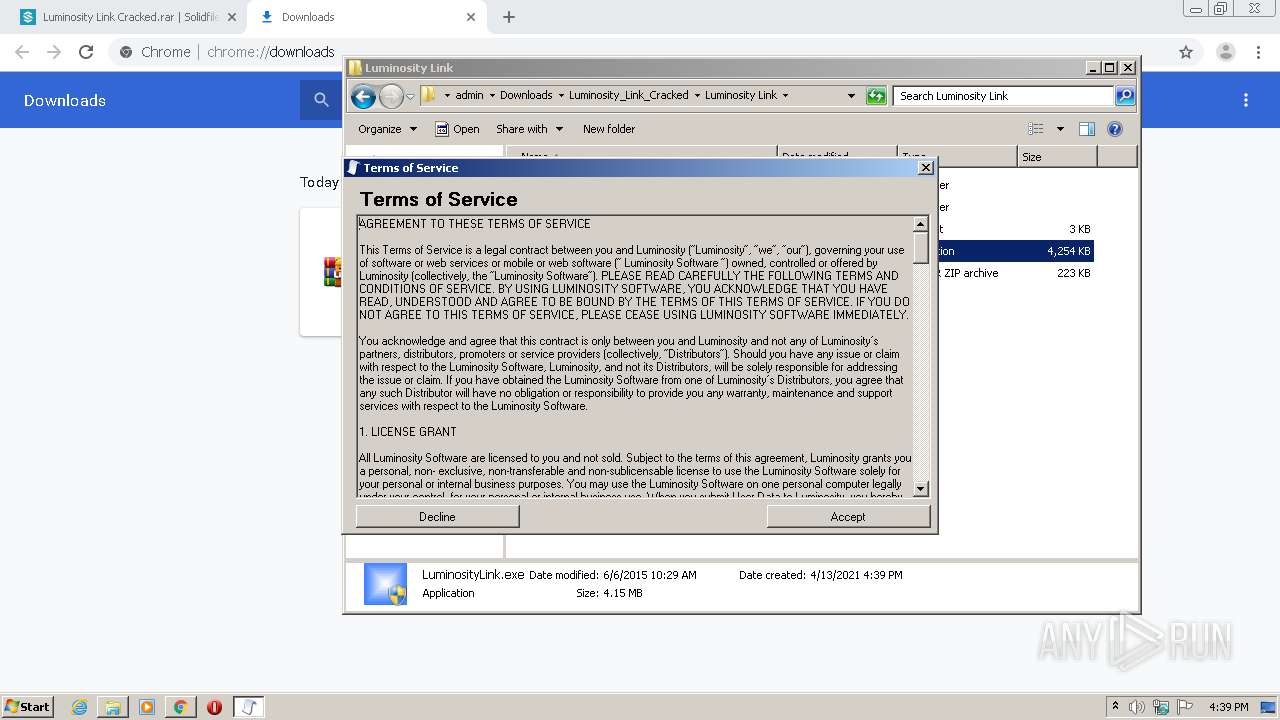
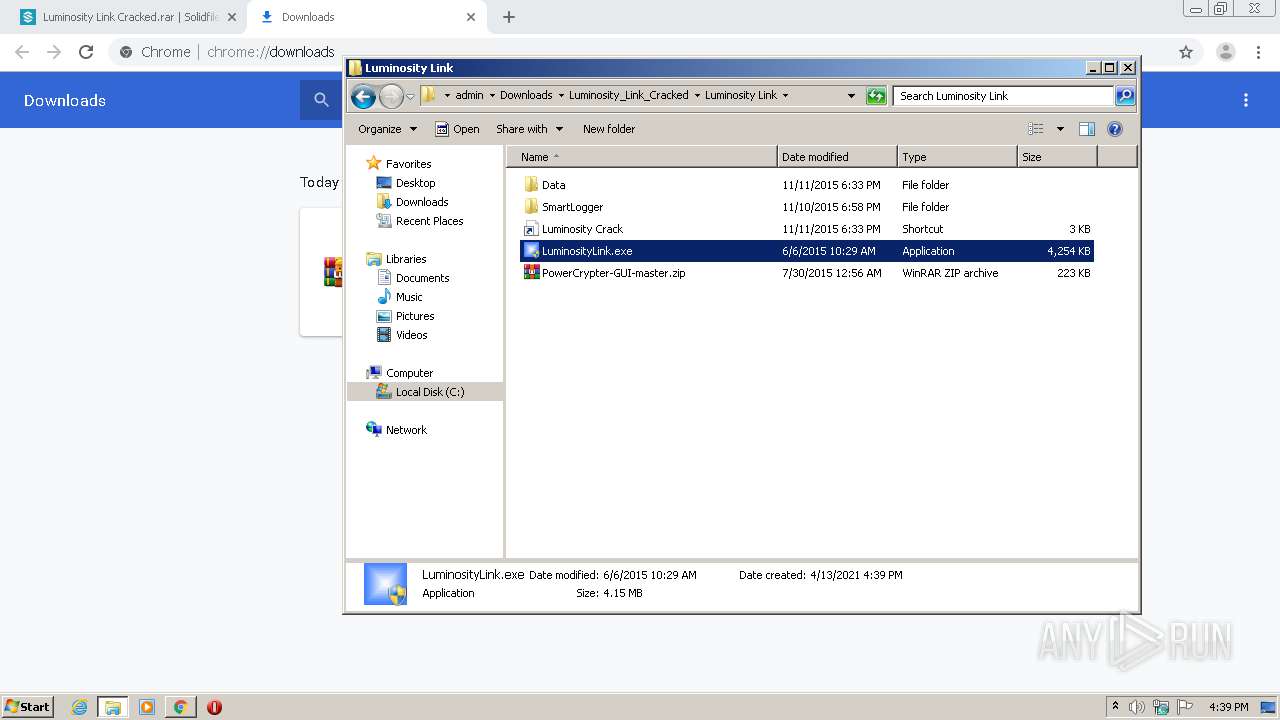
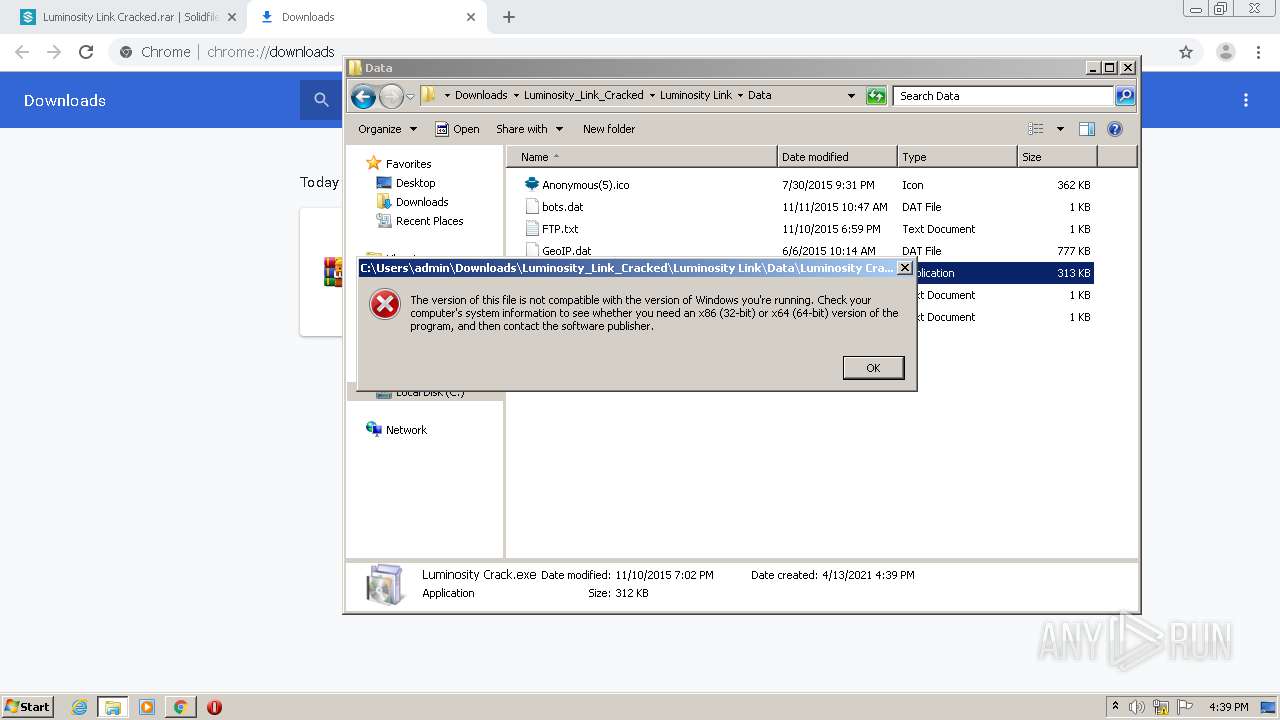
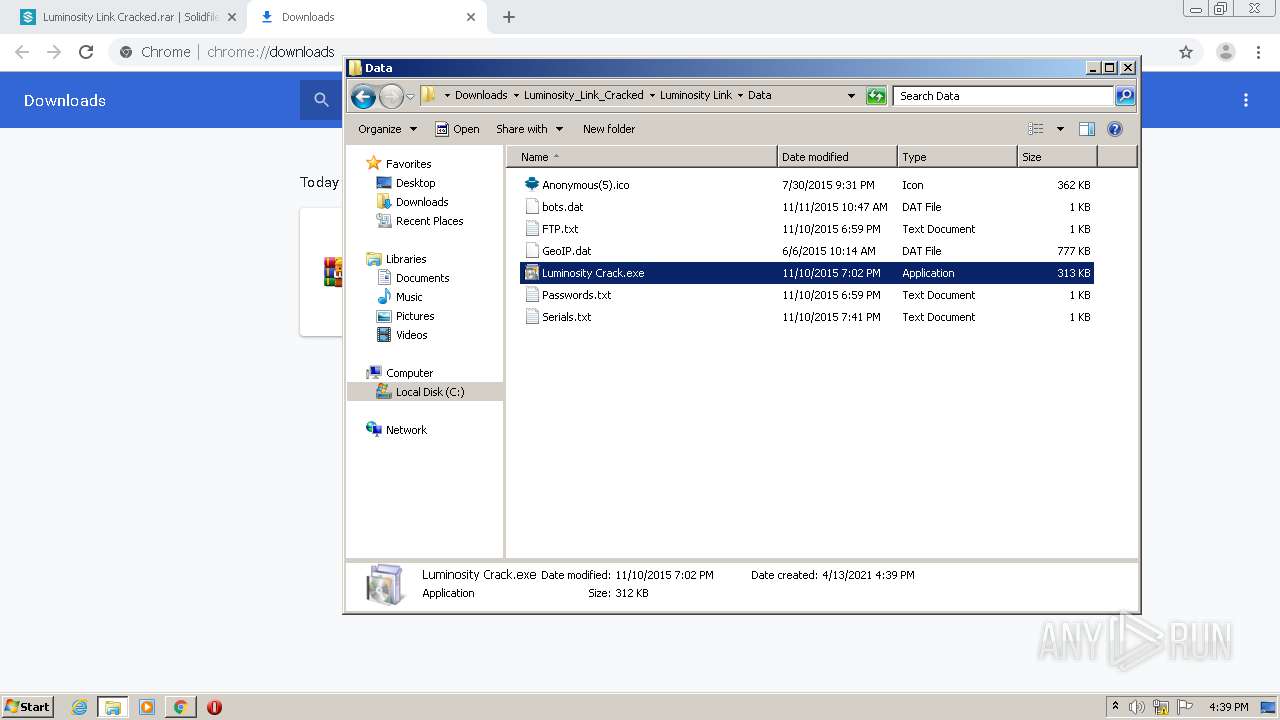
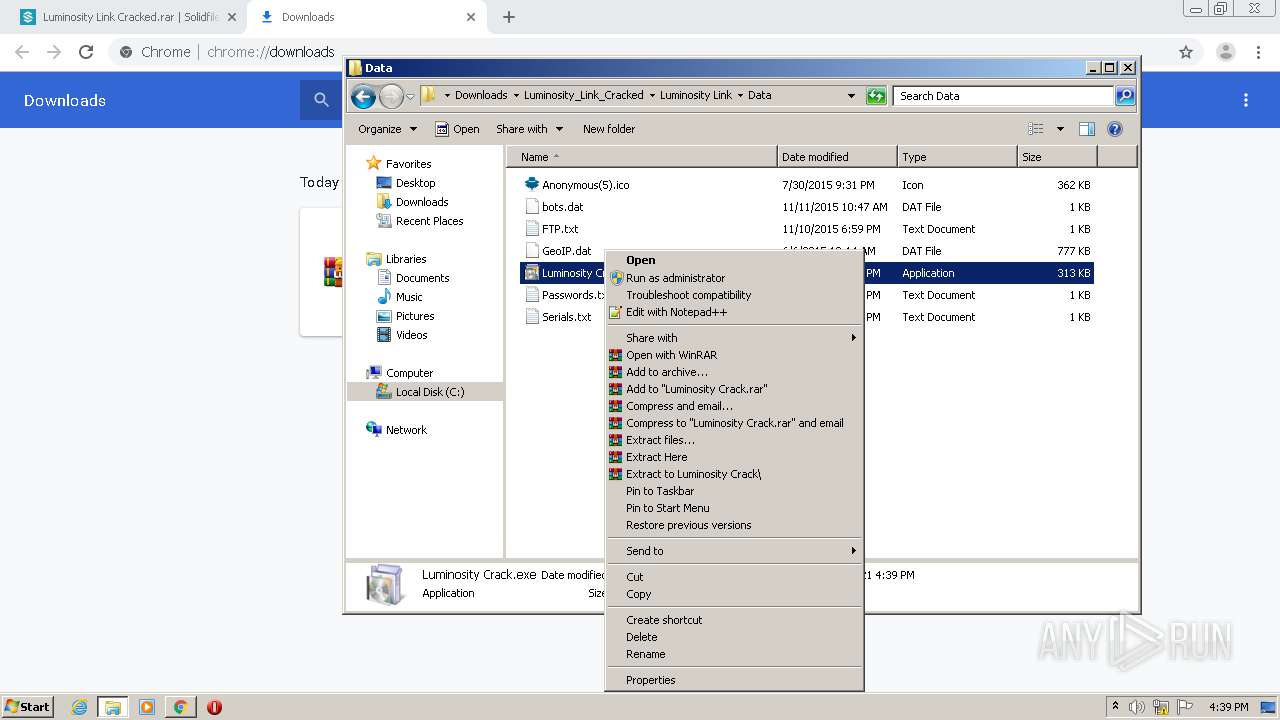
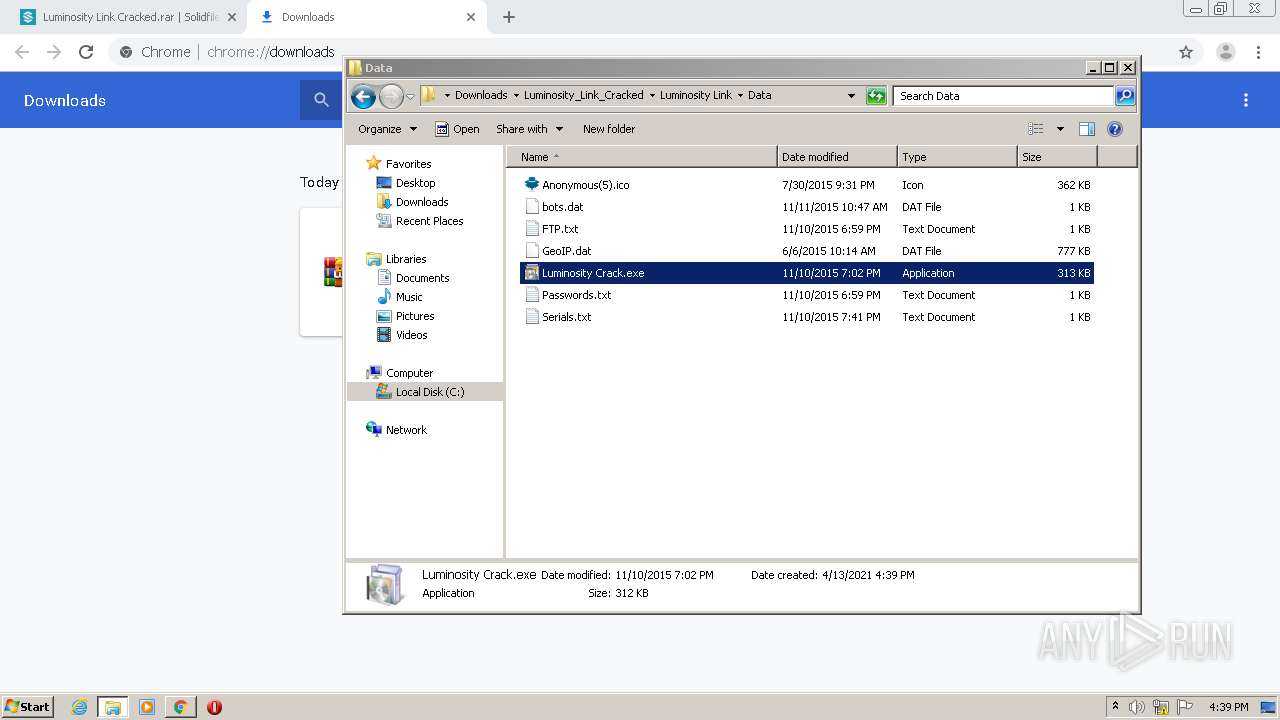
Manual execution by user
- WinRAR.exe (PID: 3972)
- LuminosityLink.exe (PID: 480)
- LuminosityLink.exe (PID: 1060)
- WinRAR.exe (PID: 2472)
- cmd.exe (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
51
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,10862208202704273039,18156094936168795030,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2092716118855577914 --mojo-platform-channel-handle=3172 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,10862208202704273039,18156094936168795030,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14138762841172587997 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 480 | "C:\Users\admin\Downloads\Luminosity_Link_Cracked\Luminosity Link\LuminosityLink.exe" | C:\Users\admin\Downloads\Luminosity_Link_Cracked\Luminosity Link\LuminosityLink.exe | — | explorer.exe | |||||||||||
User: admin Company: Luminosity.Link Integrity Level: MEDIUM Description: LuminosityLink Exit code: 3221226540 Version: 1.1.0.0 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,10862208202704273039,18156094936168795030,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15824327190407440110 --mojo-platform-channel-handle=4076 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1060 | "C:\Users\admin\Downloads\Luminosity_Link_Cracked\Luminosity Link\LuminosityLink.exe" | C:\Users\admin\Downloads\Luminosity_Link_Cracked\Luminosity Link\LuminosityLink.exe | explorer.exe | ||||||||||||
User: admin Company: Luminosity.Link Integrity Level: HIGH Description: LuminosityLink Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,10862208202704273039,18156094936168795030,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16859321390527645635 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,10862208202704273039,18156094936168795030,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6379848485576588729 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" .\bits.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,10862208202704273039,18156094936168795030,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6328191859268210572 --mojo-platform-channel-handle=3148 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,10862208202704273039,18156094936168795030,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7638303805249901762 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4972 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 832
Read events
3 186
Write events
641
Delete events
5
Modification events
| (PID) Process: | (1804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1804-13262801912257250 |
Value: 259 | |||
| (PID) Process: | (1804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1804) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
5
Suspicious files
58
Text files
264
Unknown types
13
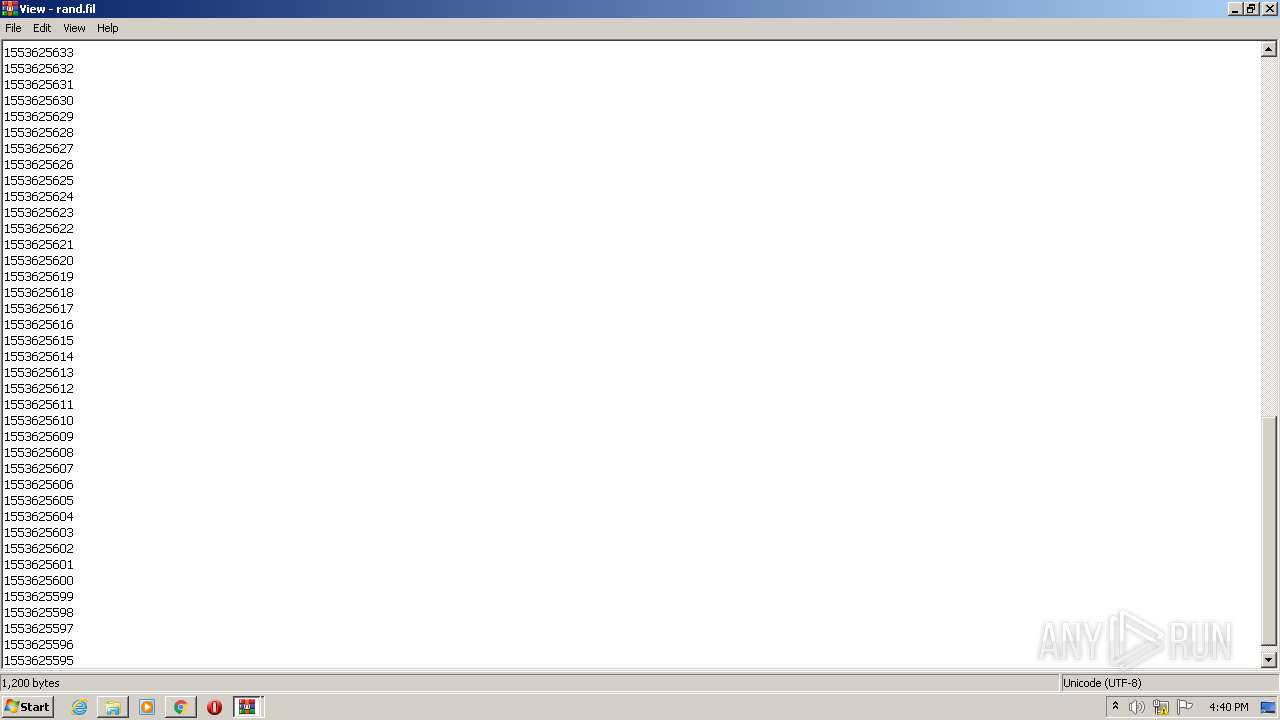
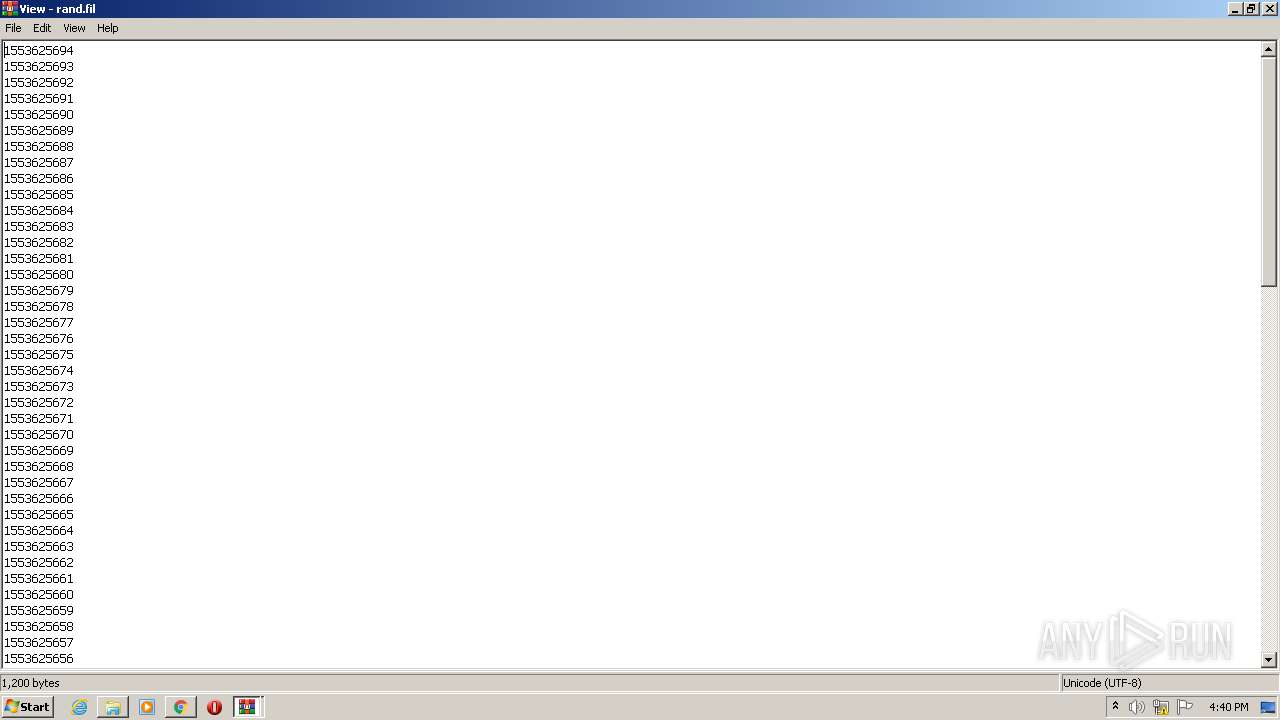
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6075BAF9-70C.pma | — | |
MD5:— | SHA256:— | |||
| 1804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7b5c3f8a-4c4f-4a6e-bf51-a45357a660f7.tmp | — | |
MD5:— | SHA256:— | |||
| 1804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 1804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RFe7a2d.TMP | — | |
MD5:— | SHA256:— | |||
| 1804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe7962.TMP | text | |
MD5:— | SHA256:— | |||
| 1804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe7991.TMP | text | |
MD5:— | SHA256:— | |||
| 1804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe7be2.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
47
DNS requests
28
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3764 | chrome.exe | GET | 200 | 37.221.163.214:80 | http://www.solidfiles.com/v/2GVvGZpyYa3mM | RO | html | 14.9 Kb | suspicious |
3764 | chrome.exe | POST | — | 37.221.163.214:80 | http://www.solidfiles.com/v/2GVvGZpyYa3mM/dl | RO | — | — | suspicious |
3764 | chrome.exe | GET | 200 | 185.60.216.19:80 | http://connect.facebook.net/en_US/all.js | IE | text | 1.74 Kb | whitelisted |
3764 | chrome.exe | GET | 200 | 151.101.12.157:80 | http://platform.twitter.com/widgets.js | US | text | 28.0 Kb | whitelisted |
3764 | chrome.exe | POST | 200 | 37.221.163.214:80 | http://www.solidfiles.com/v/2GVvGZpyYa3mM/dl | RO | html | 13.9 Kb | suspicious |
3764 | chrome.exe | GET | 200 | 93.115.87.59:80 | http://s02.solidfilesusercontent.com/MzI4NDkwMzRhMzk3MzdkMjkxNjFhNjdiZmNkZWI1YjViZWNiZDViNDoxbFdMN2E6dzFtZnZZS1RkazZiVzUtcmNQNUMzNS1IbVJn/2GVvGZpyYa3mM/Luminosity_Link_Cracked.rar | RO | compressed | 2.57 Mb | suspicious |
3764 | chrome.exe | GET | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
3764 | chrome.exe | GET | 200 | 142.250.185.74:80 | http://ajax.googleapis.com/ajax/libs/jquery/2.1.1/jquery.min.js | US | text | 28.9 Kb | whitelisted |
3764 | chrome.exe | POST | 200 | 37.221.163.214:80 | http://www.solidfiles.com/api/nodes/1431272091252610013/downloads | RO | text | 15 b | suspicious |
3764 | chrome.exe | GET | 200 | 74.125.11.26:80 | http://r4---sn-4g5ednee.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=45.92.228.8&mm=28&mn=sn-4g5ednee&ms=nvh&mt=1618328182&mv=m&mvi=4&pl=25&shardbypass=yes | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3764 | chrome.exe | 104.18.11.207:443 | maxcdn.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
3764 | chrome.exe | 142.250.185.74:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 172.217.23.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 185.60.216.19:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3764 | chrome.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
— | — | 151.101.12.157:443 | platform.twitter.com | Fastly | US | suspicious |
3764 | chrome.exe | 104.244.42.136:443 | syndication.twitter.com | Twitter Inc. | US | unknown |
3764 | chrome.exe | 93.115.87.59:80 | s02.solidfilesusercontent.com | Voxility S.R.L. | RO | suspicious |
— | — | 93.115.87.59:80 | s02.solidfilesusercontent.com | Voxility S.R.L. | RO | suspicious |
3764 | chrome.exe | 142.250.186.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.solidfiles.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
solidfilescdn.com |
| malicious |
maxcdn.bootstrapcdn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.google.com |
| malicious |
outdatedbrowser.com |
| suspicious |
twitter.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3764 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
1040 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a Suspicious no-ip Domain |
1040 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |