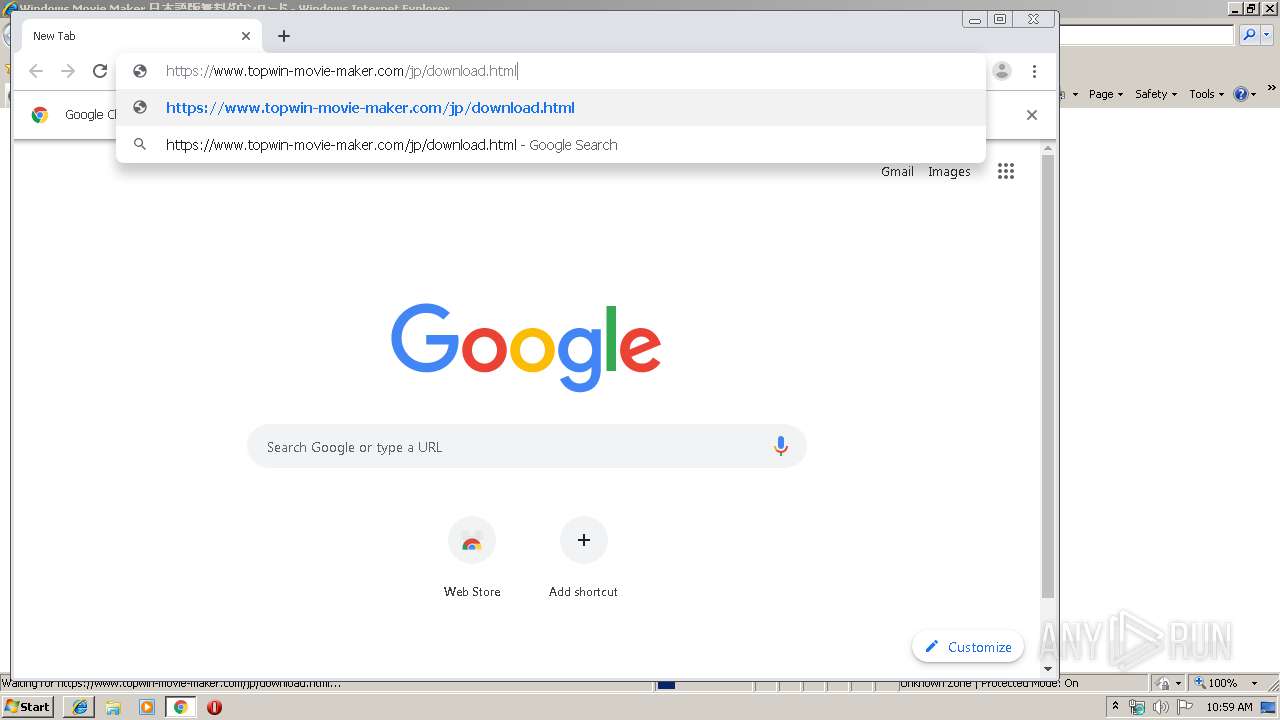
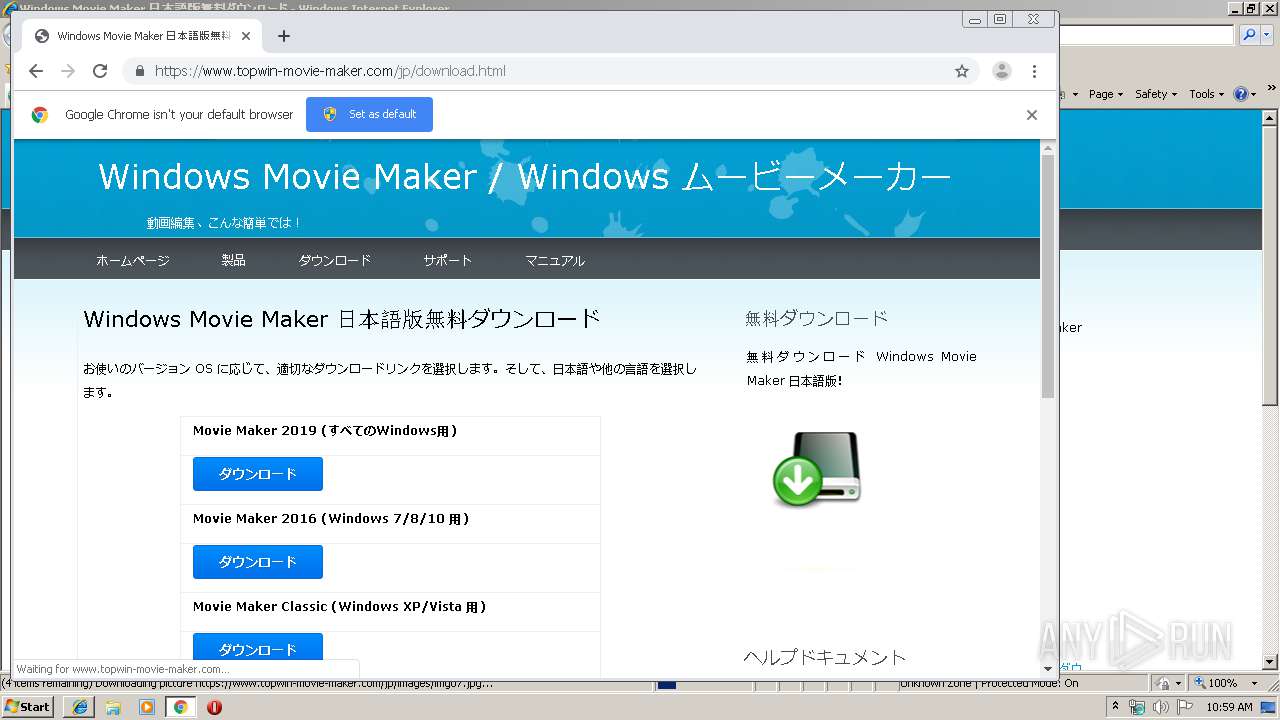
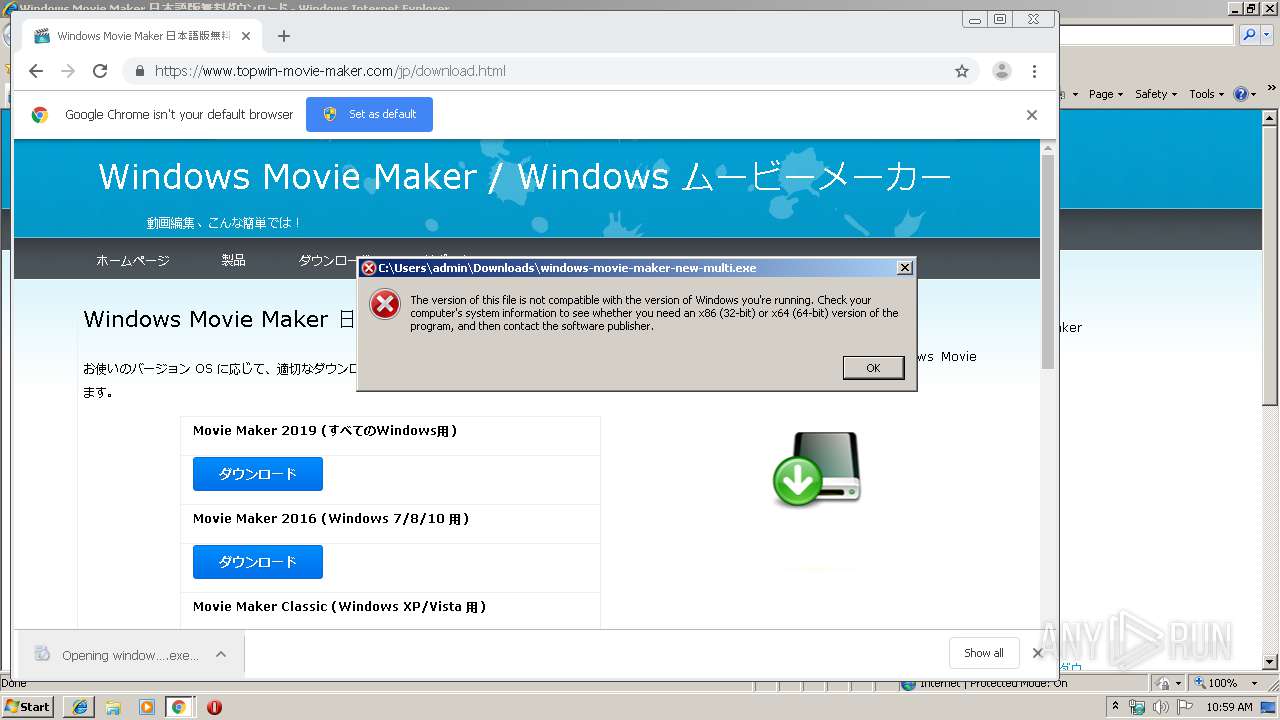
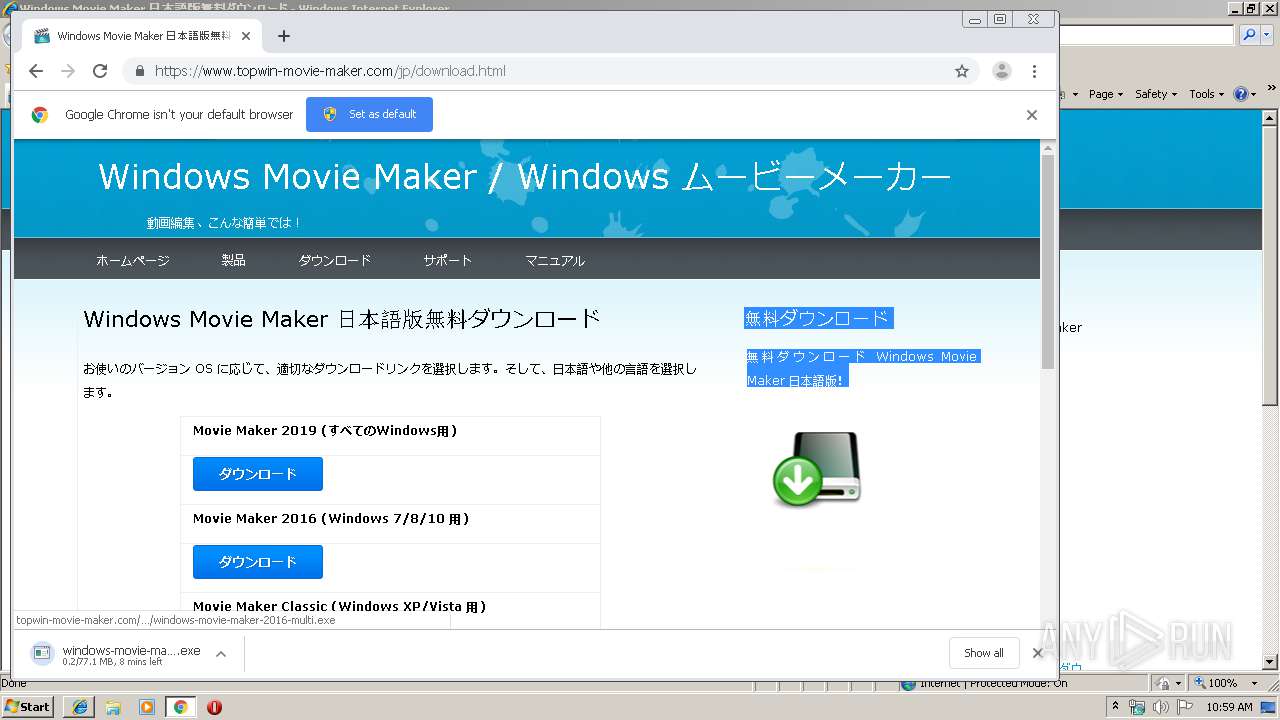
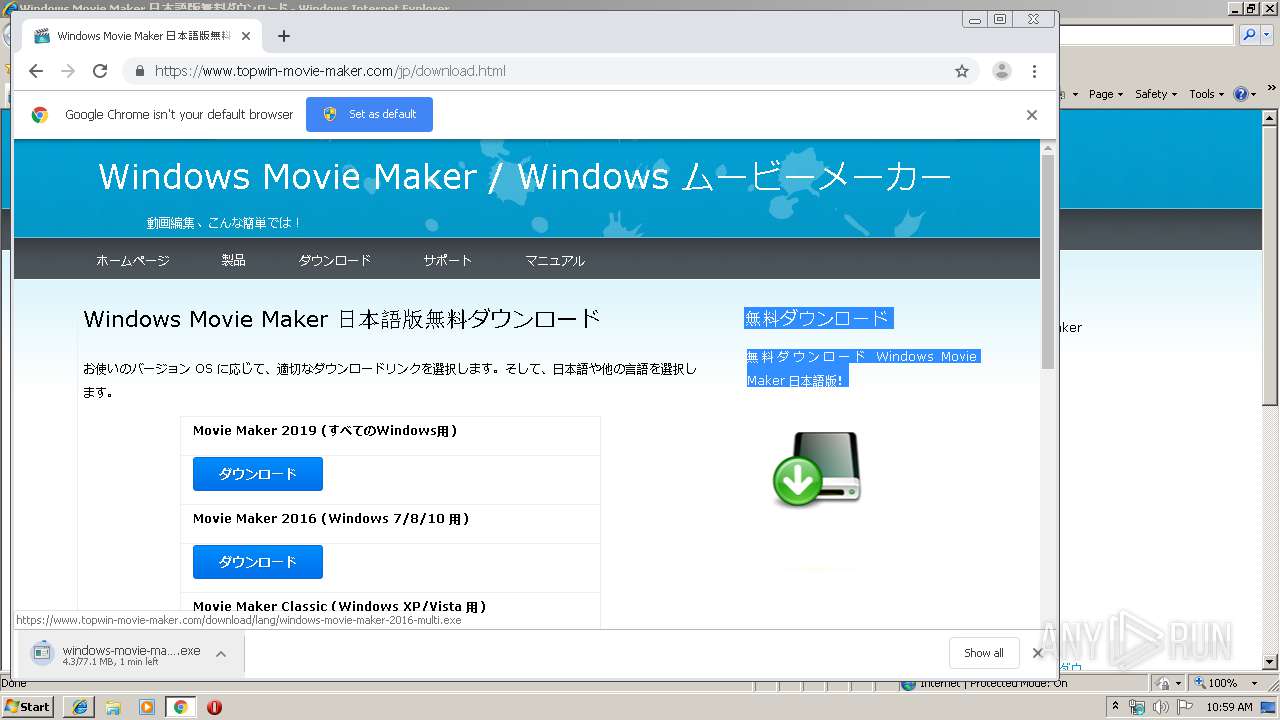
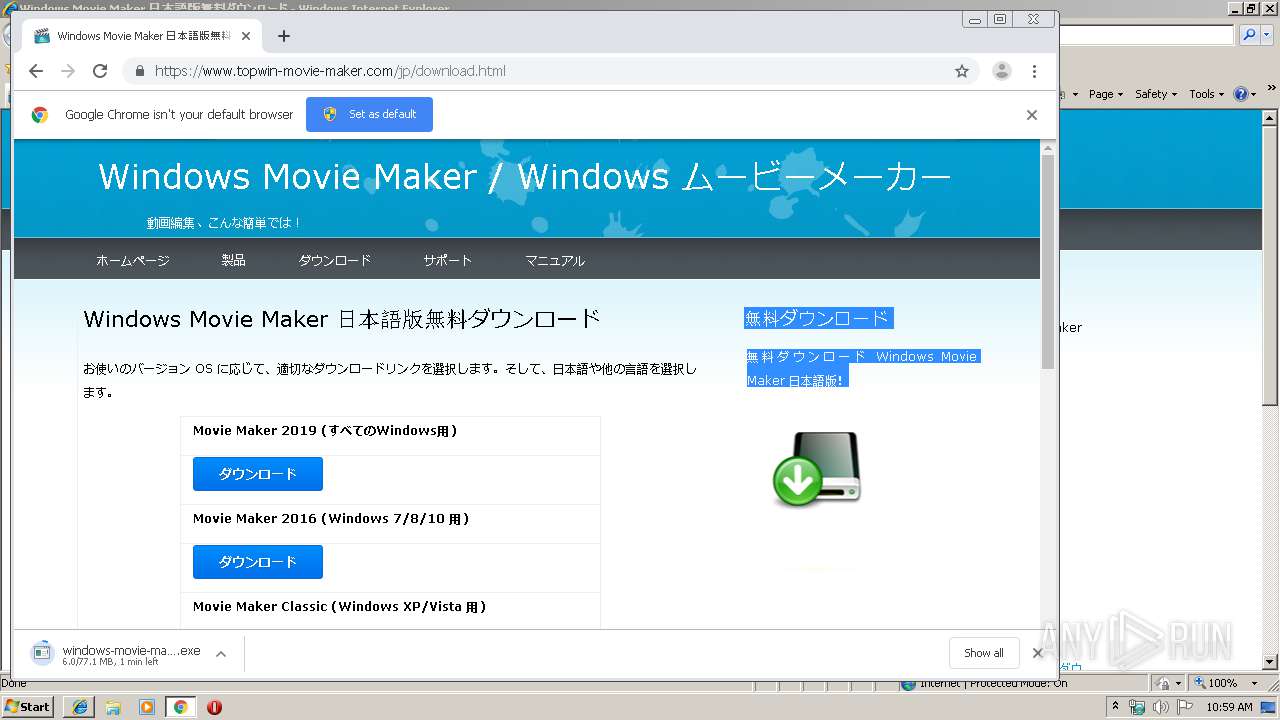
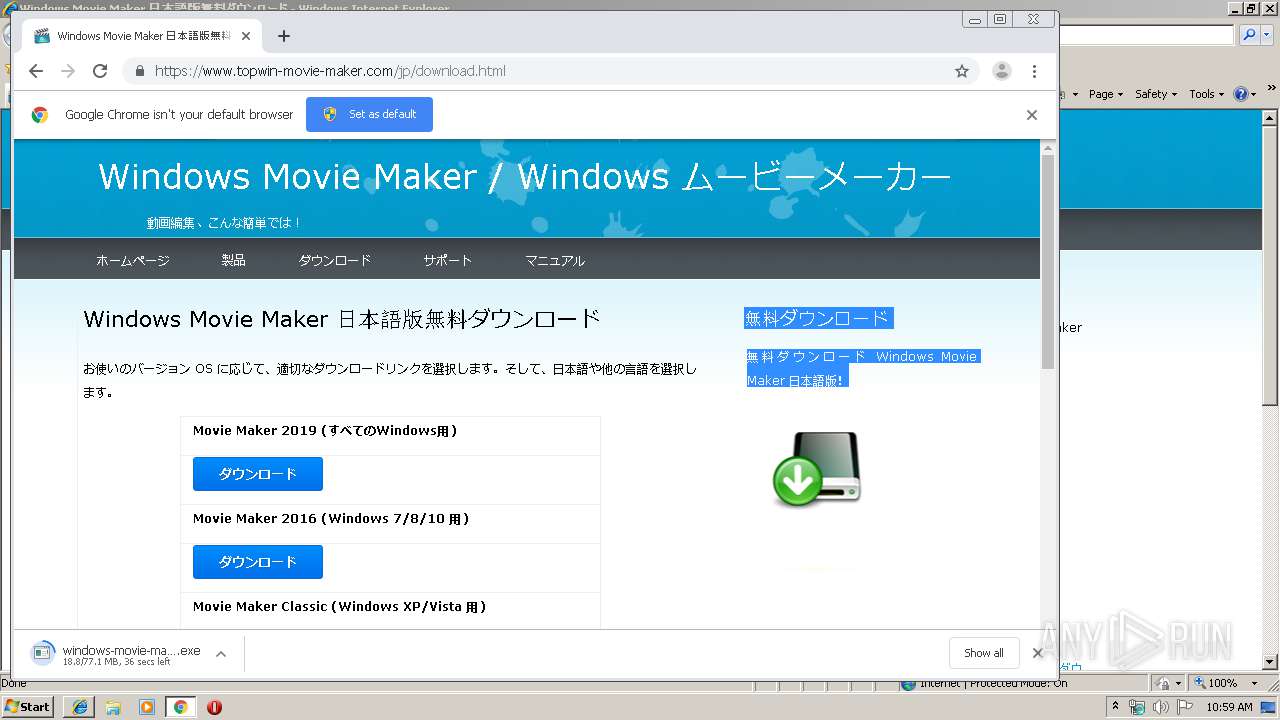
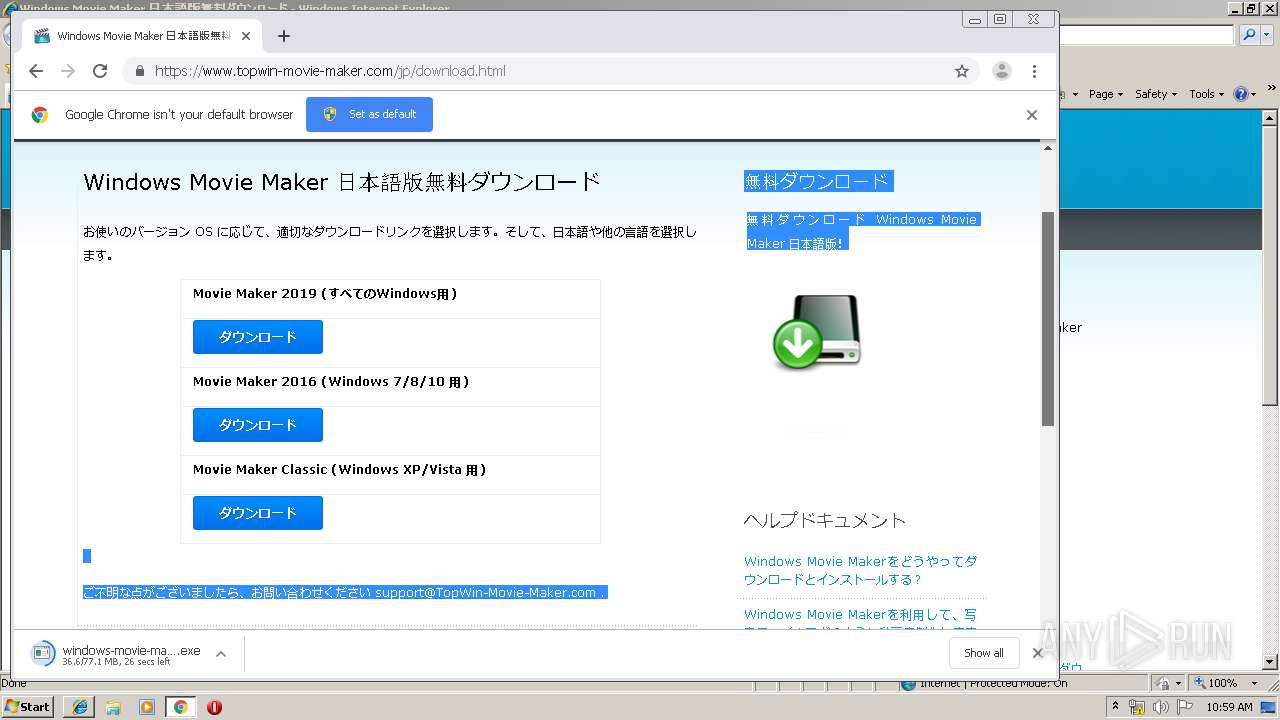
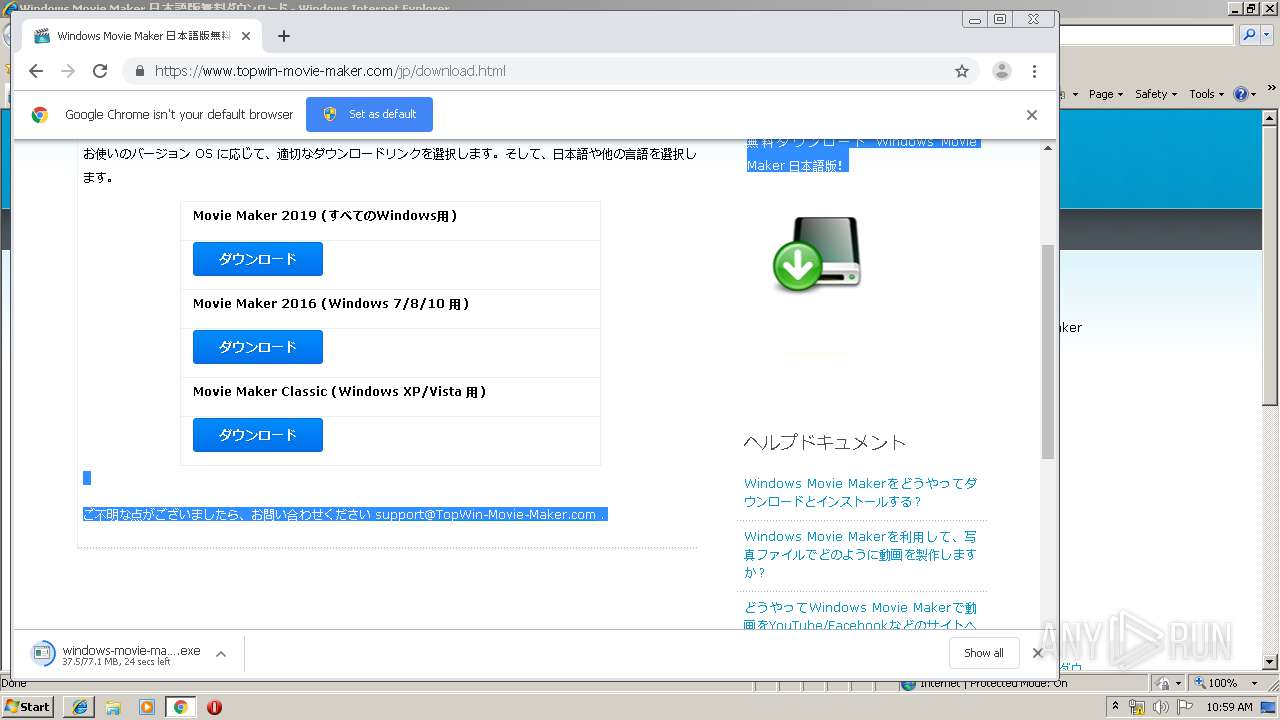
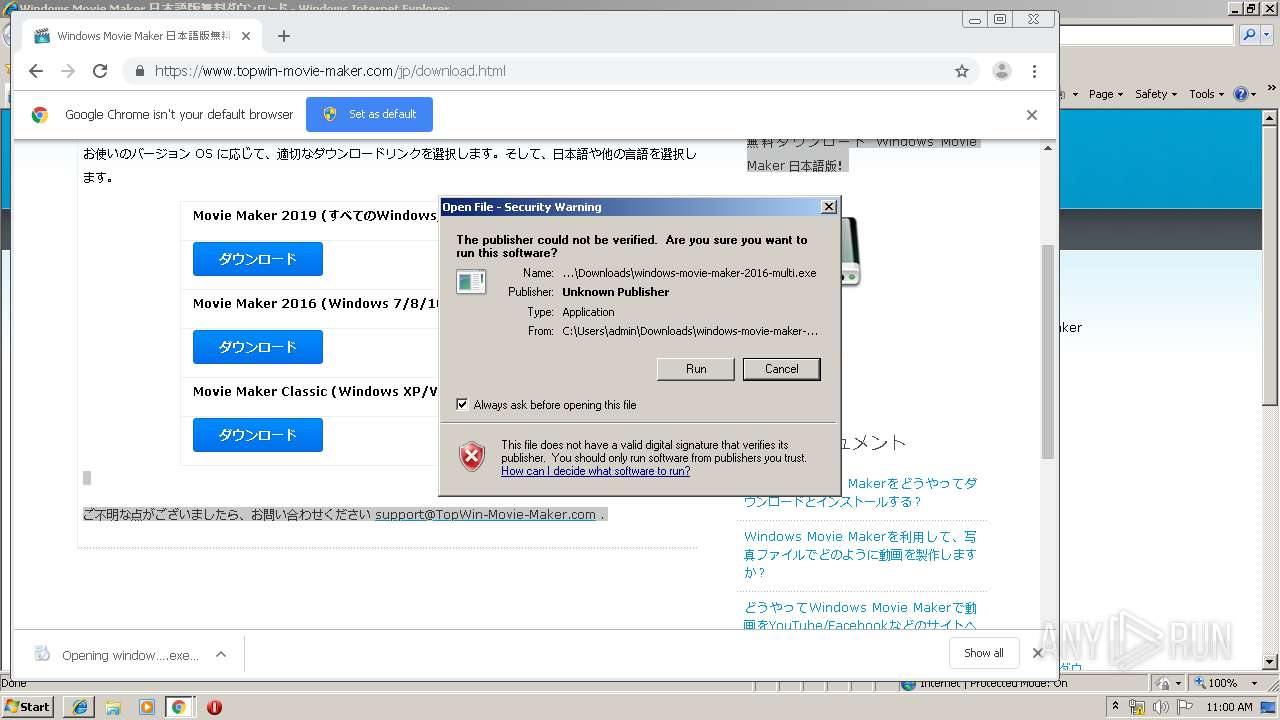
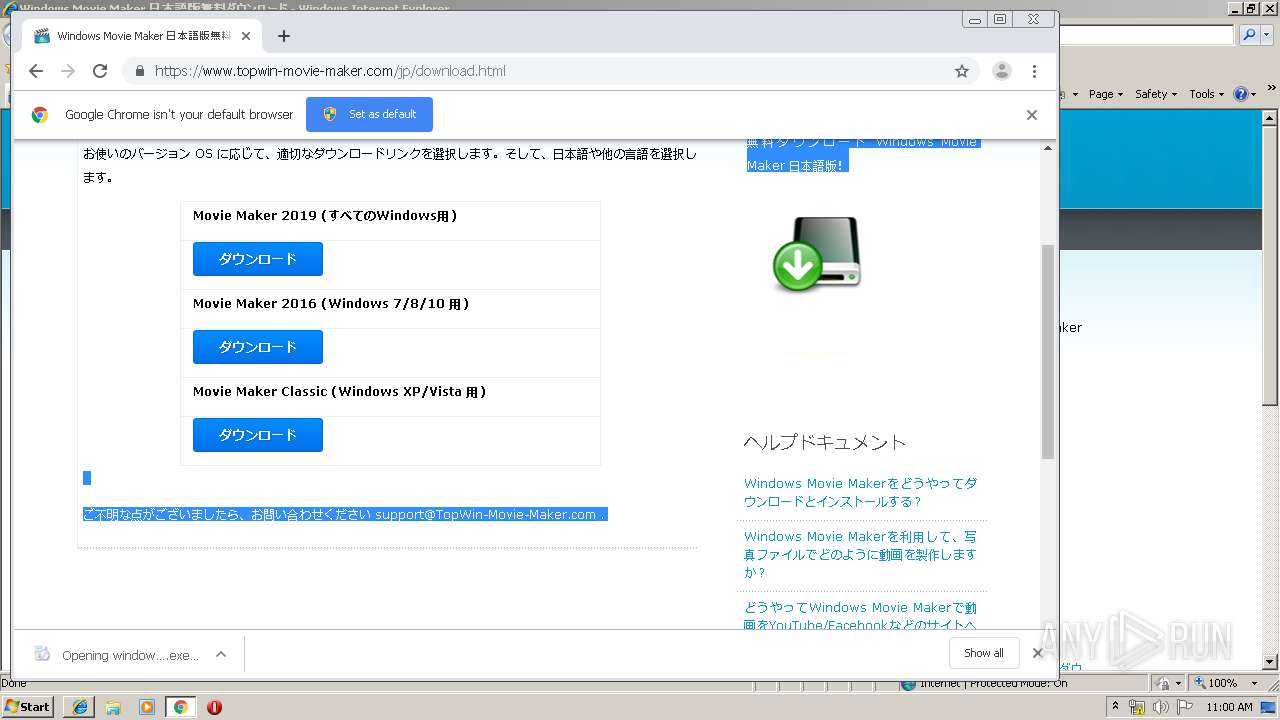
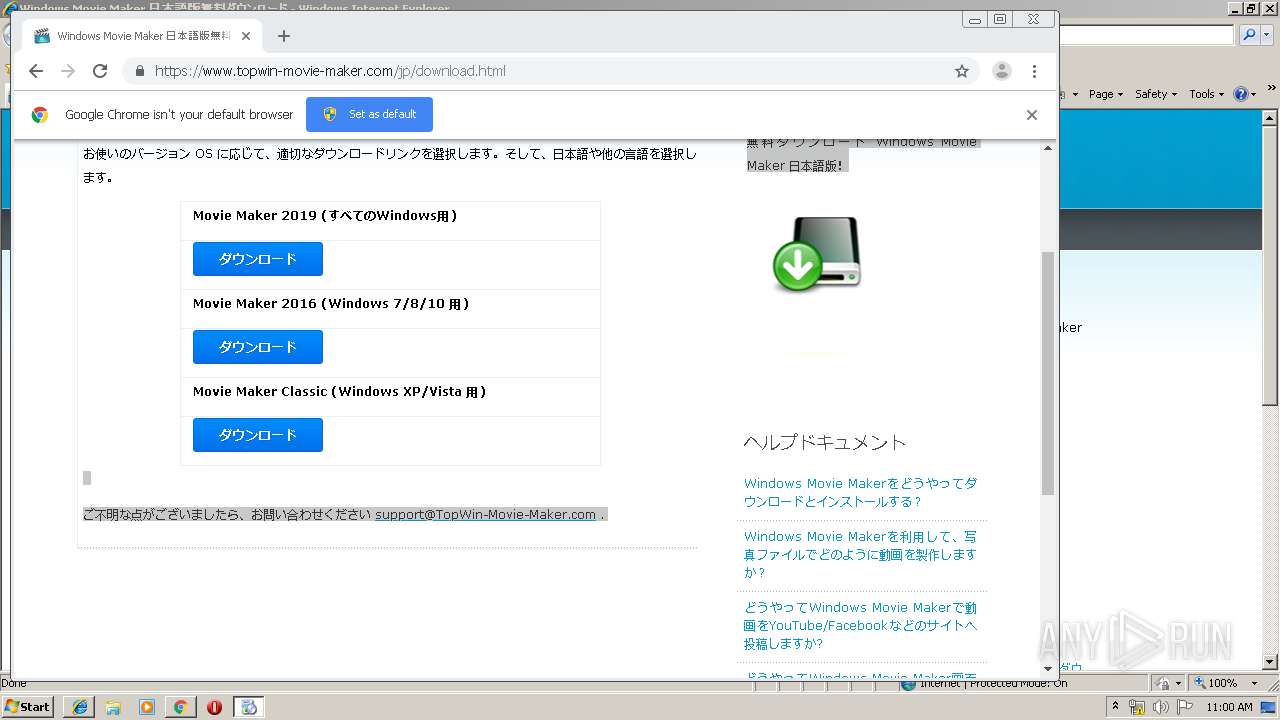
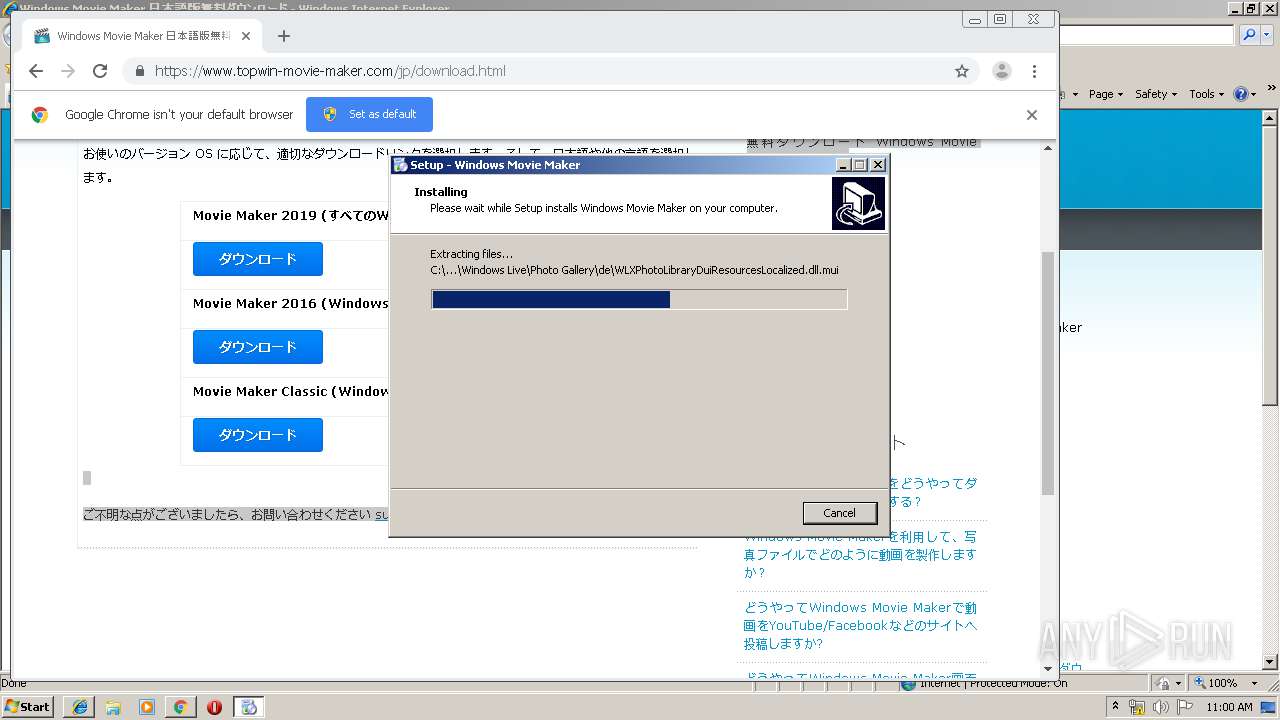
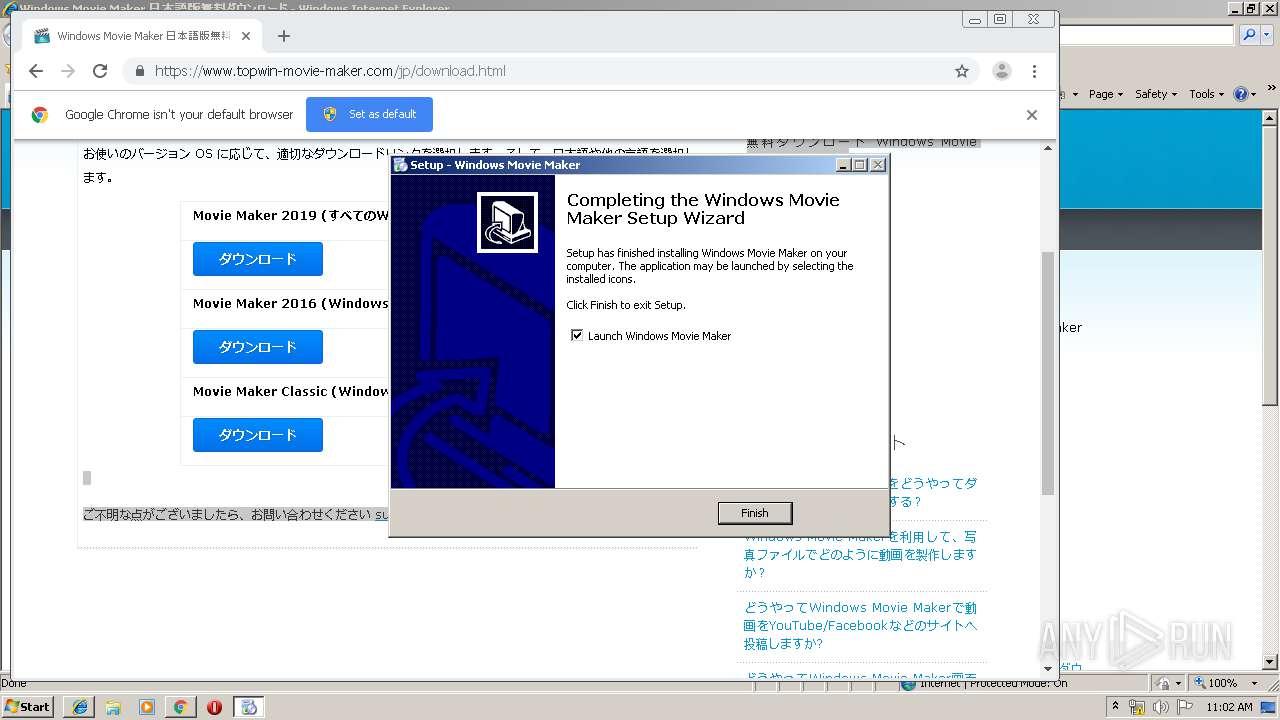
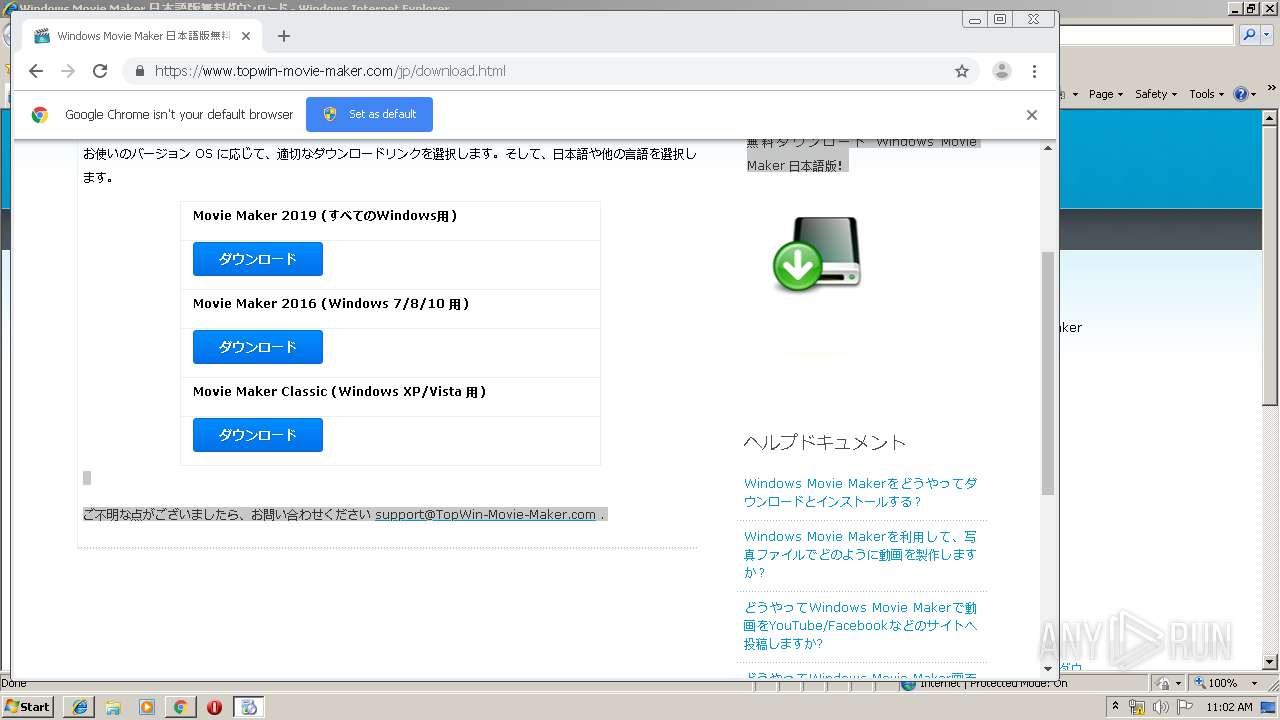
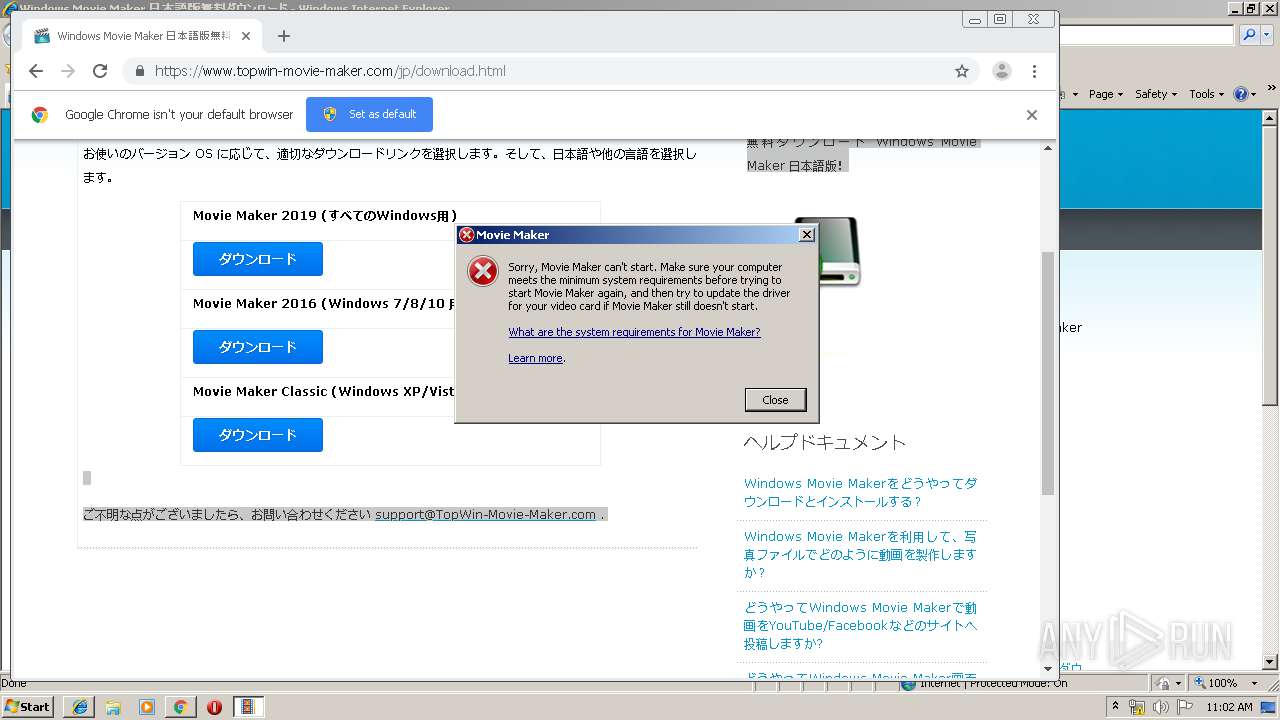
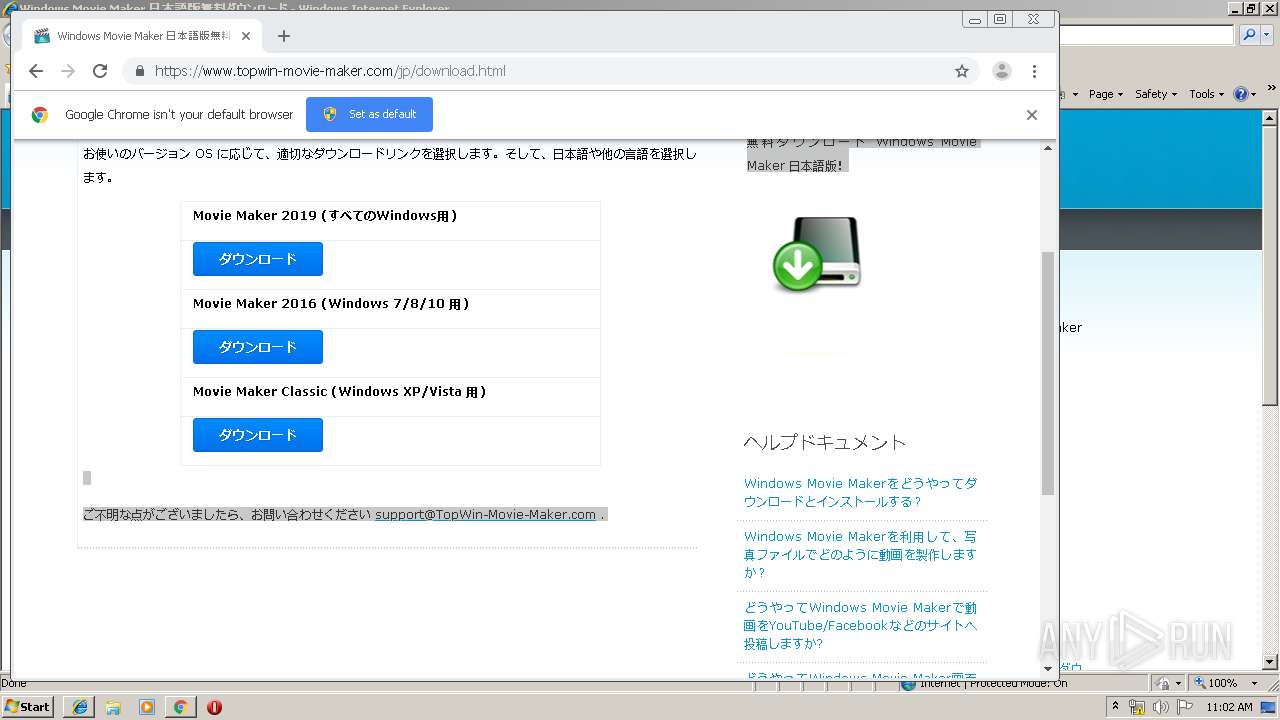
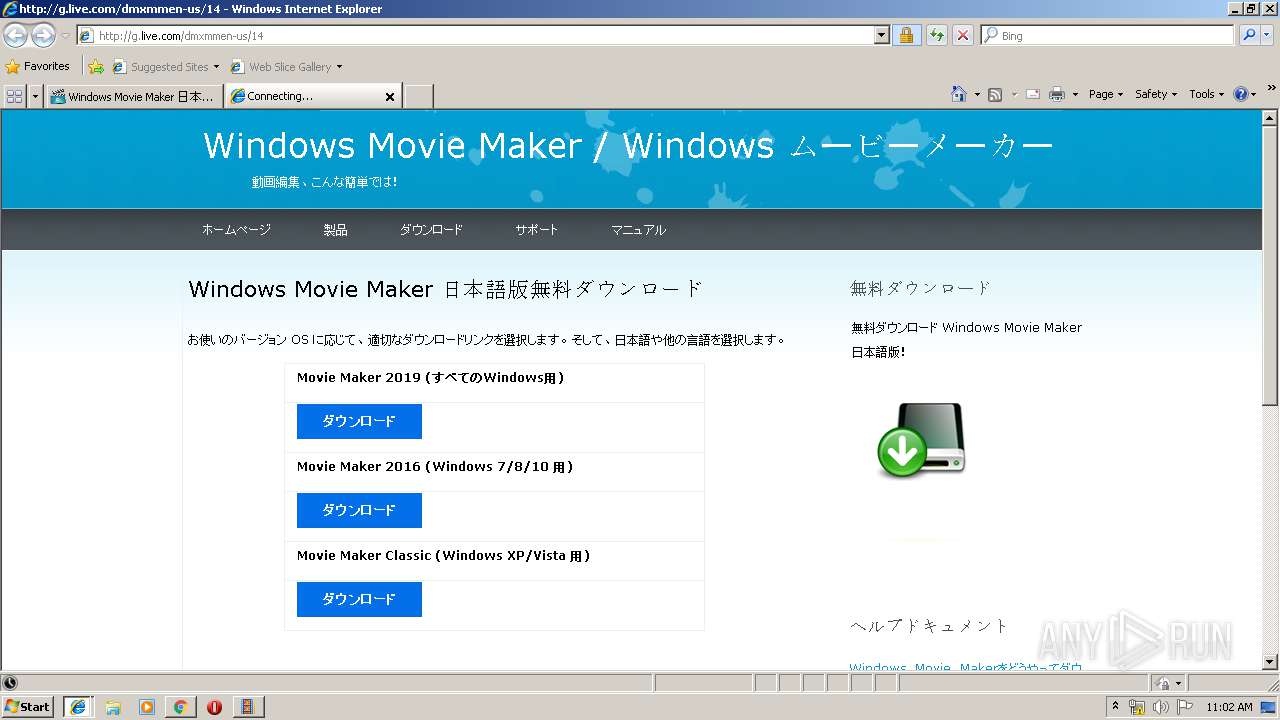
| URL: | https://www.topwin-movie-maker.com/jp/download.html |
| Full analysis: | https://app.any.run/tasks/4ec18198-0276-4520-b8e7-624789371c2e |
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2019, 10:58:31 |
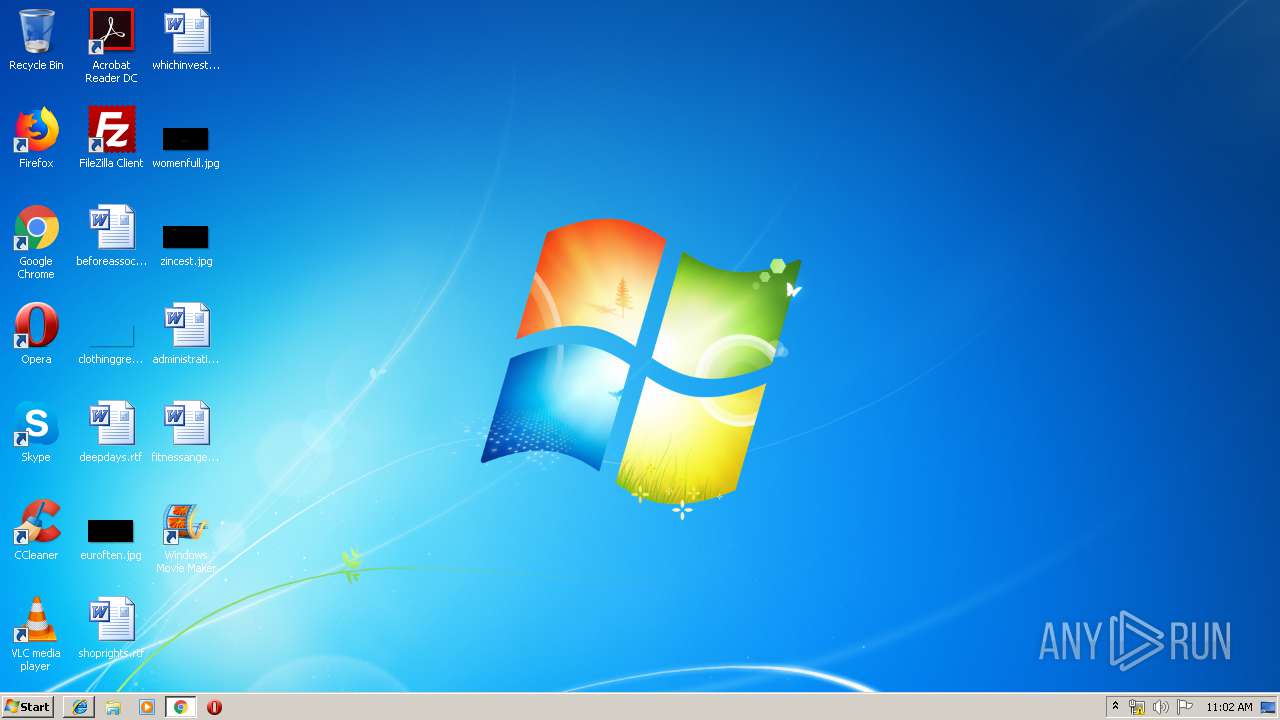
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1CE193A8F323D8A8346018A5CAF80F67 |
| SHA1: | 2CFFF354F56B3B69738F61F85EF21E7976ED9CB0 |
| SHA256: | B0DE63010A9ECE5F94437A099D573727E8DD757D880877C46B0AA528F322BFE2 |
| SSDEEP: | 3:N8DSL0yMt5vbGHBzlQ:2OLL+5qH3Q |
MALICIOUS
Application was dropped or rewritten from another process
- vcredist_x86.exe (PID: 1784)
- vcredist_x86.exe (PID: 3880)
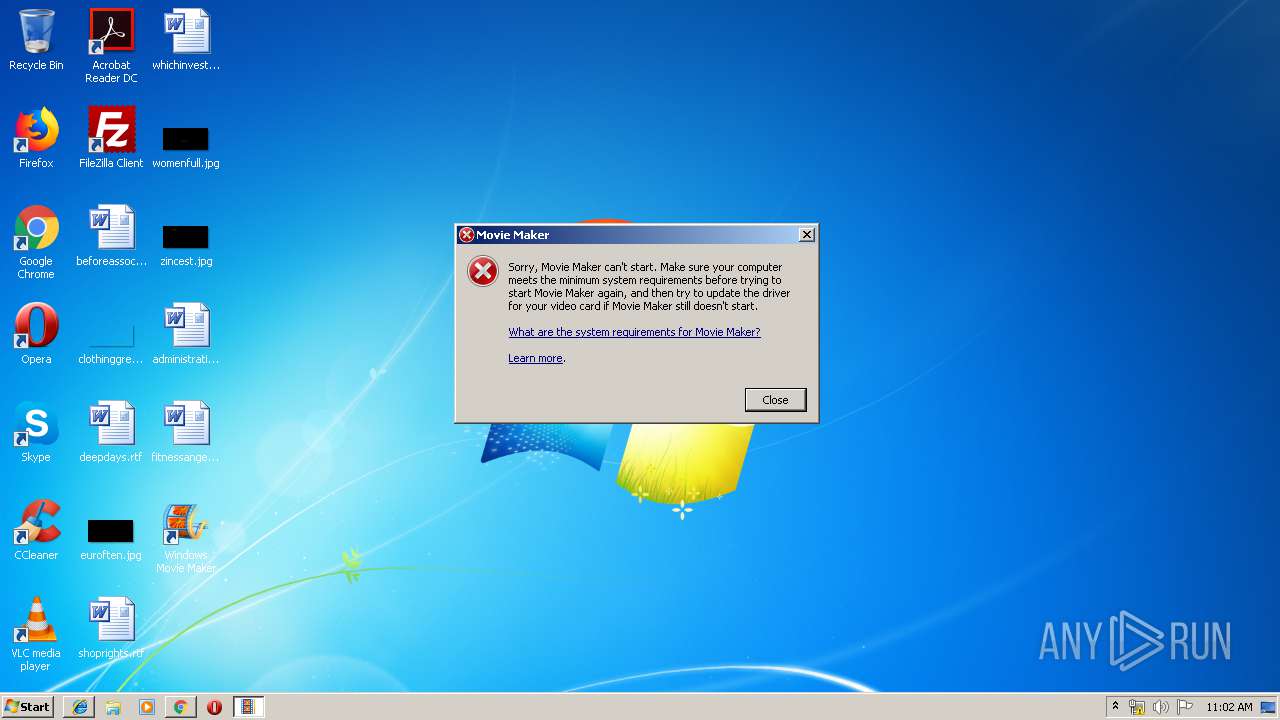
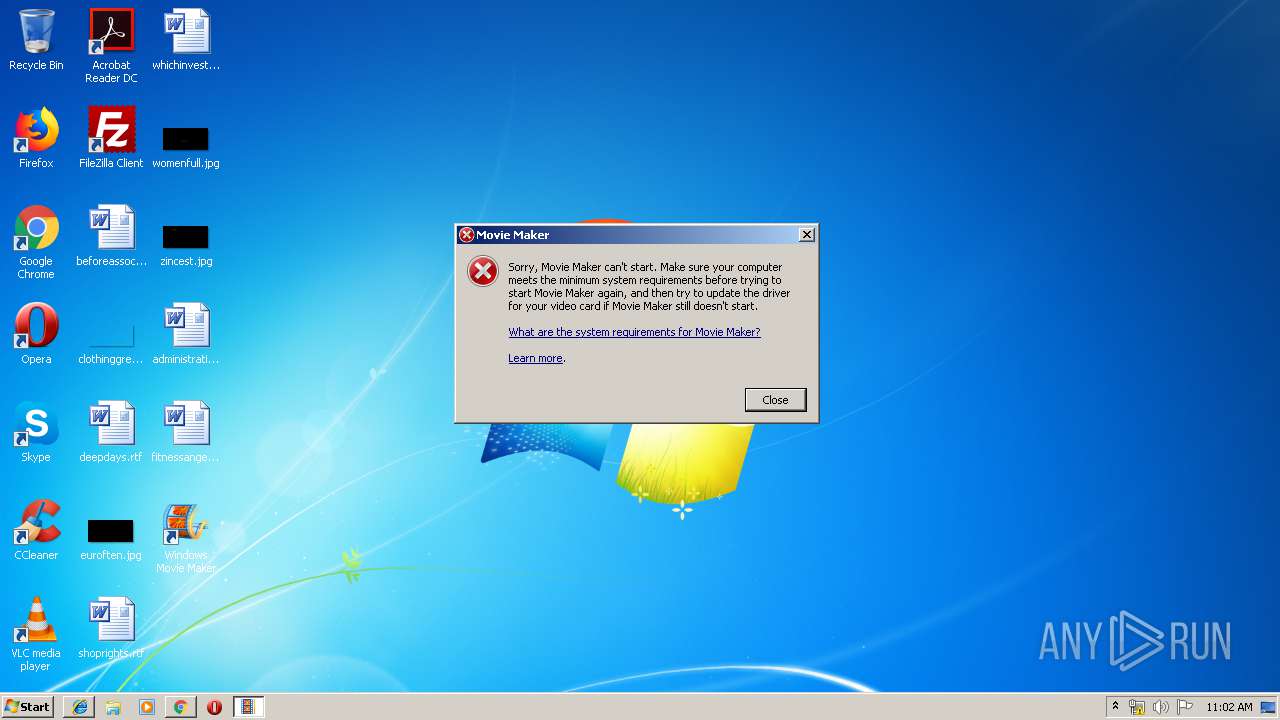
- MovieMaker.exe (PID: 2012)
- MovieMaker.exe (PID: 2760)
- MovieMaker.exe (PID: 3696)
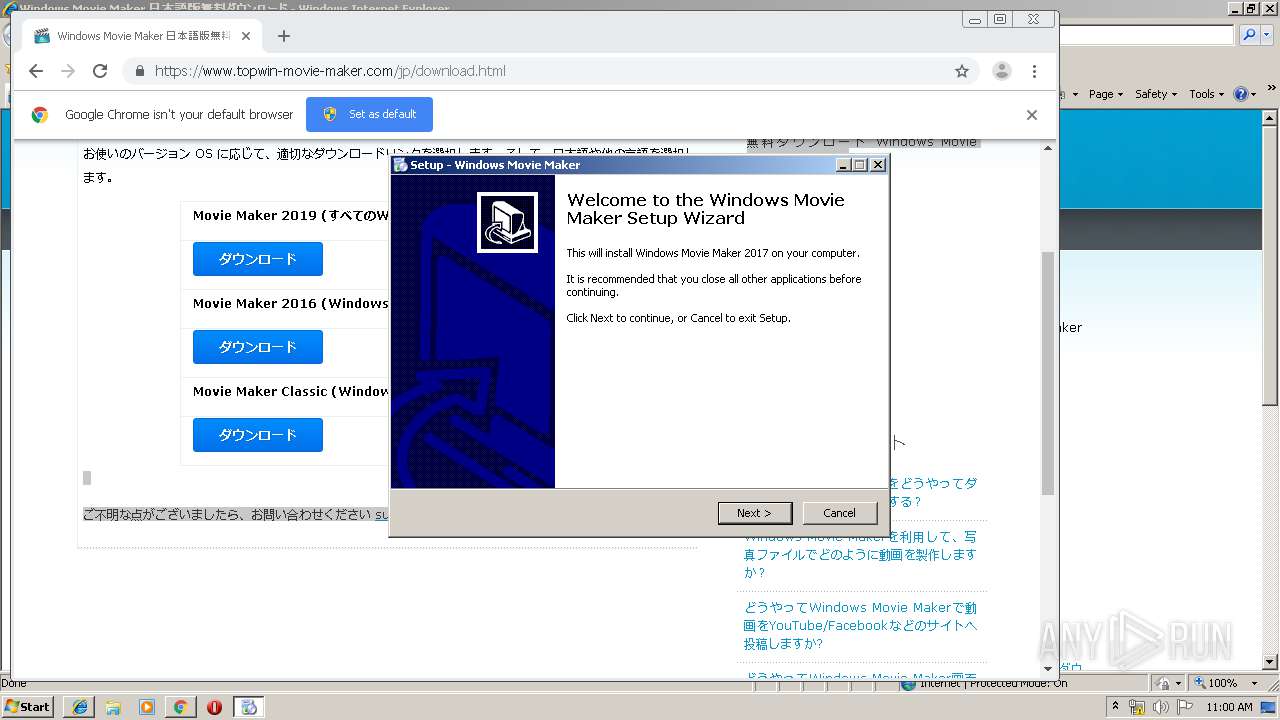
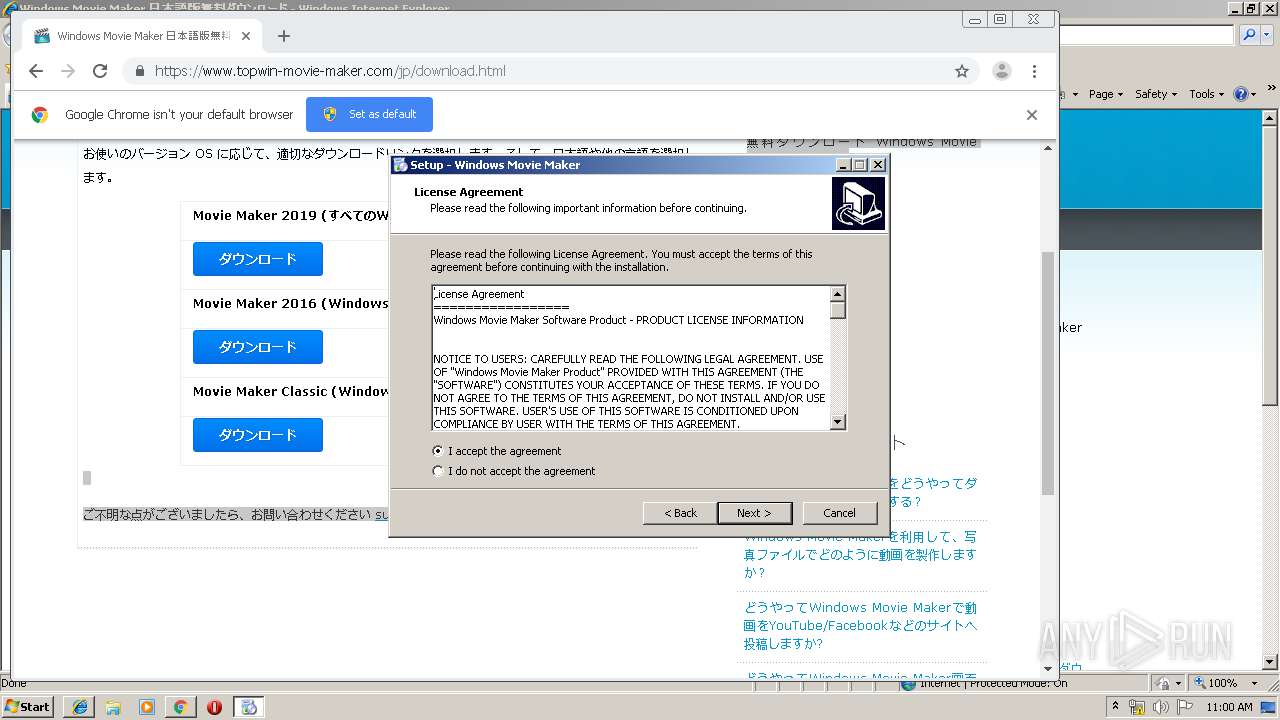
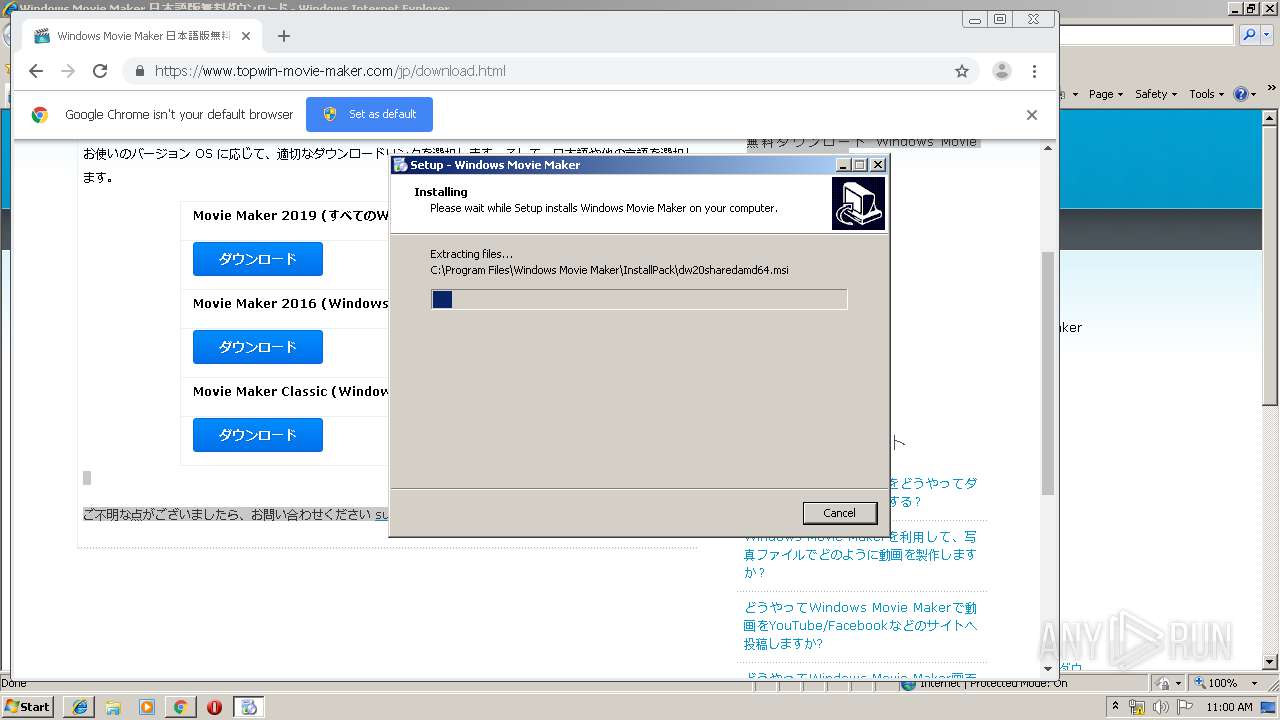
- windows-movie-maker-2016-multi.exe (PID: 976)
- windows-movie-maker-2016-multi.exe (PID: 2736)
Changes settings of System certificates
- vcredist_x86.exe (PID: 1784)
Changes the autorun value in the registry
- vcredist_x86.exe (PID: 1784)
Uses Task Scheduler to run other applications
- MsiExec.exe (PID: 3944)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2352)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3504)
- explorer.exe (PID: 352)
- MovieMaker.exe (PID: 3696)
- MovieMaker.exe (PID: 2012)
- MovieMaker.exe (PID: 2760)
- vcredist_x86.exe (PID: 3880)
SUSPICIOUS
Starts Internet Explorer
- explorer.exe (PID: 352)
Reads Internet Cache Settings
- explorer.exe (PID: 352)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3036)
Executable content was dropped or overwritten
- chrome.exe (PID: 2240)
- chrome.exe (PID: 4064)
- windows-movie-maker-2016-multi.exe (PID: 976)
- vcredist_x86.exe (PID: 3880)
- vcredist_x86.exe (PID: 1784)
- windows-movie-maker-2016-multi.tmp (PID: 3932)
- msiexec.exe (PID: 3444)
- windows-movie-maker-2016-multi.exe (PID: 2736)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2240)
Reads the Windows organization settings
- windows-movie-maker-2016-multi.tmp (PID: 3932)
Reads Windows owner or organization settings
- windows-movie-maker-2016-multi.tmp (PID: 3932)
Creates files in the user directory
- windows-movie-maker-2016-multi.tmp (PID: 3932)
Application launched itself
- vcredist_x86.exe (PID: 1784)
Searches for installed software
- vcredist_x86.exe (PID: 3880)
- vcredist_x86.exe (PID: 1784)
Executed as Windows Service
- vssvc.exe (PID: 2528)
- SearchIndexer.exe (PID: 1944)
Creates files in the program directory
- vcredist_x86.exe (PID: 1784)
- SearchIndexer.exe (PID: 1944)
Creates a software uninstall entry
- vcredist_x86.exe (PID: 1784)
Creates files in the Windows directory
- msiexec.exe (PID: 3444)
Adds / modifies Windows certificates
- vcredist_x86.exe (PID: 1784)
Starts Microsoft Installer
- windows-movie-maker-2016-multi.tmp (PID: 3932)
Removes files from Windows directory
- msiexec.exe (PID: 3444)
Modifies the open verb of a shell class
- msiexec.exe (PID: 3444)
Creates COM task schedule object
- msiexec.exe (PID: 3444)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2716)
- chrome.exe (PID: 2240)
- iexplore.exe (PID: 656)
- iexplore.exe (PID: 3820)
Application launched itself
- iexplore.exe (PID: 656)
- chrome.exe (PID: 2240)
- msiexec.exe (PID: 3444)
Reads internet explorer settings
- iexplore.exe (PID: 2716)
- iexplore.exe (PID: 3820)
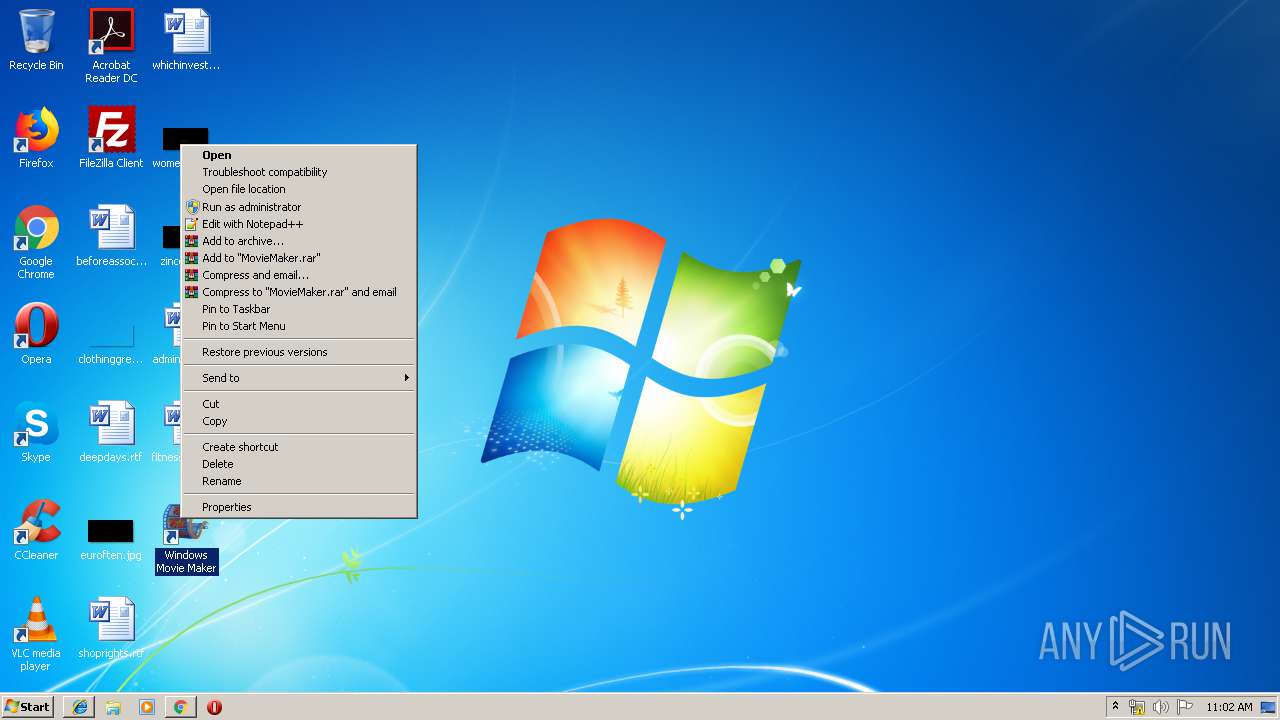
Manual execution by user
- chrome.exe (PID: 2240)
Reads the hosts file
- chrome.exe (PID: 4064)
- chrome.exe (PID: 2240)
Reads settings of System Certificates
- chrome.exe (PID: 4064)
Creates files in the user directory
- iexplore.exe (PID: 2716)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3036)
- iexplore.exe (PID: 3820)
Changes settings of System certificates
- iexplore.exe (PID: 656)
Adds / modifies Windows certificates
- iexplore.exe (PID: 656)
Changes internet zones settings
- iexplore.exe (PID: 656)
Application was dropped or rewritten from another process
- windows-movie-maker-2016-multi.tmp (PID: 3176)
- windows-movie-maker-2016-multi.tmp (PID: 3932)
Creates a software uninstall entry
- windows-movie-maker-2016-multi.tmp (PID: 3932)
- msiexec.exe (PID: 3444)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2528)
Creates files in the program directory
- windows-movie-maker-2016-multi.tmp (PID: 3932)
- msiexec.exe (PID: 3444)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3444)
Loads dropped or rewritten executable
- msiexec.exe (PID: 3444)
Starts application with an unusual extension
- msiexec.exe (PID: 3444)
Writes to a desktop.ini file (may be used to cloak folders)
- msiexec.exe (PID: 3444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
128
Monitored processes
86
Malicious processes
13
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,3702438958696035970,1608233028573953942,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14562188690334438402 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 292 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10001_ Global\UsGthrCtrlFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10001 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" "1" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 460 | "msiexec" /I "C:\Program Files\Windows Movie Maker\InstallPack\writerprod.msi" /quiet /norestart /qn | C:\Windows\system32\msiexec.exe | — | windows-movie-maker-2016-multi.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 1619 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,3702438958696035970,1608233028573953942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9434700958846799617 --mojo-platform-channel-handle=3060 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,3702438958696035970,1608233028573953942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5800797101538589286 --mojo-platform-channel-handle=3288 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,3702438958696035970,1608233028573953942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9533262675158601680 --mojo-platform-channel-handle=4512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,3702438958696035970,1608233028573953942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5648484836298963536 --mojo-platform-channel-handle=3984 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,3702438958696035970,1608233028573953942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14501493295431342915 --mojo-platform-channel-handle=4064 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
20 560
Read events
14 586
Write events
5 661
Delete events
313
Modification events
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {915828F5-0604-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
Executable files
651
Suspicious files
145
Text files
584
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 656 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 656 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabAE4B.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarAE4C.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabAE5D.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarAE5E.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabAF1B.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarAF1C.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
54
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3820 | iexplore.exe | GET | 302 | 20.36.252.129:80 | http://g.live.com/dmxmmen-us/14 | US | — | — | whitelisted |
3820 | iexplore.exe | GET | 301 | 23.38.57.214:80 | http://windows.microsoft.com/EN-US/windows/windows-essentials-2012-system-requirements | NL | — | — | whitelisted |
4064 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
4064 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
1784 | vcredist_x86.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 555 b | whitelisted |
1784 | vcredist_x86.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
2716 | iexplore.exe | GET | 200 | 8.248.113.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | US | der | 969 b | whitelisted |
656 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2716 | iexplore.exe | GET | 200 | 8.248.113.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
4064 | chrome.exe | GET | 200 | 173.194.183.103:80 | http://r2---sn-aigl6nek.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.92.25.20&mm=28&mn=sn-aigl6nek&ms=nvh&mt=1573642696&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2716 | iexplore.exe | 216.158.67.226:443 | www.topwin-movie-maker.com | WebNX, Inc. | US | unknown |
656 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2716 | iexplore.exe | 172.217.16.200:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
4064 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4064 | chrome.exe | 172.217.16.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
4064 | chrome.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4064 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4064 | chrome.exe | 216.158.67.226:443 | www.topwin-movie-maker.com | WebNX, Inc. | US | unknown |
4064 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
2716 | iexplore.exe | 8.248.113.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.topwin-movie-maker.com |
| unknown |
www.bing.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |