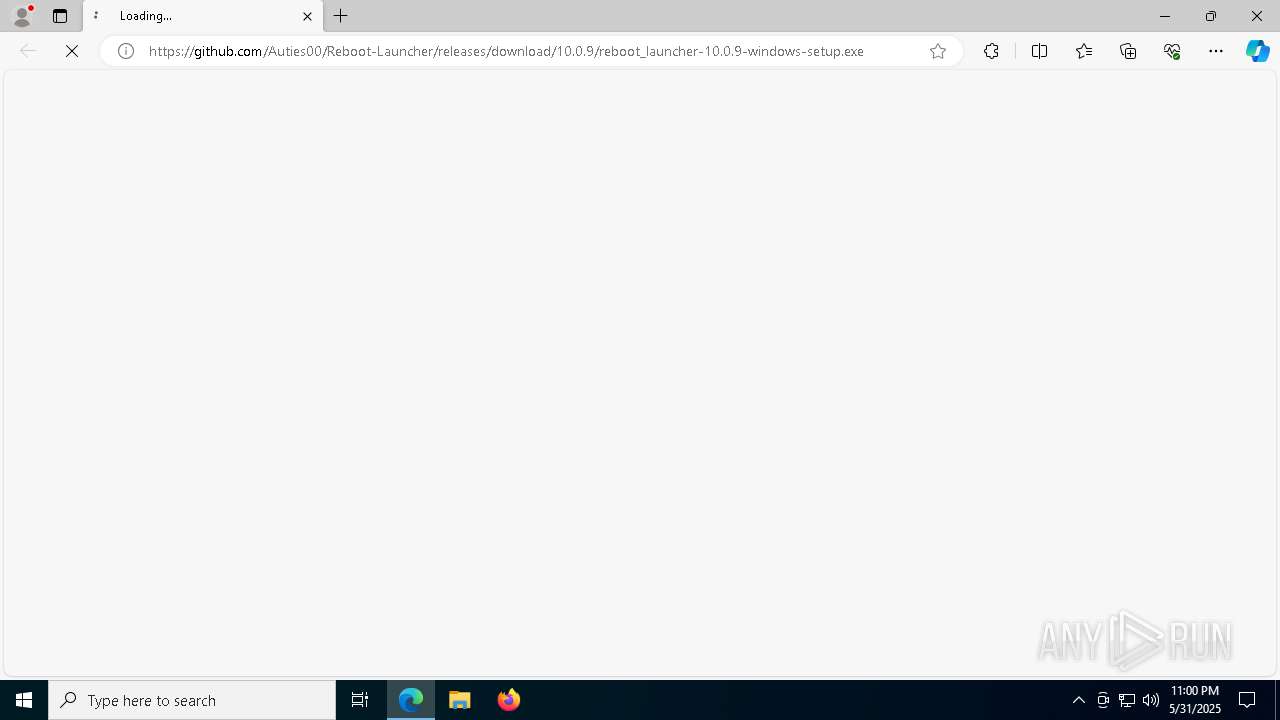
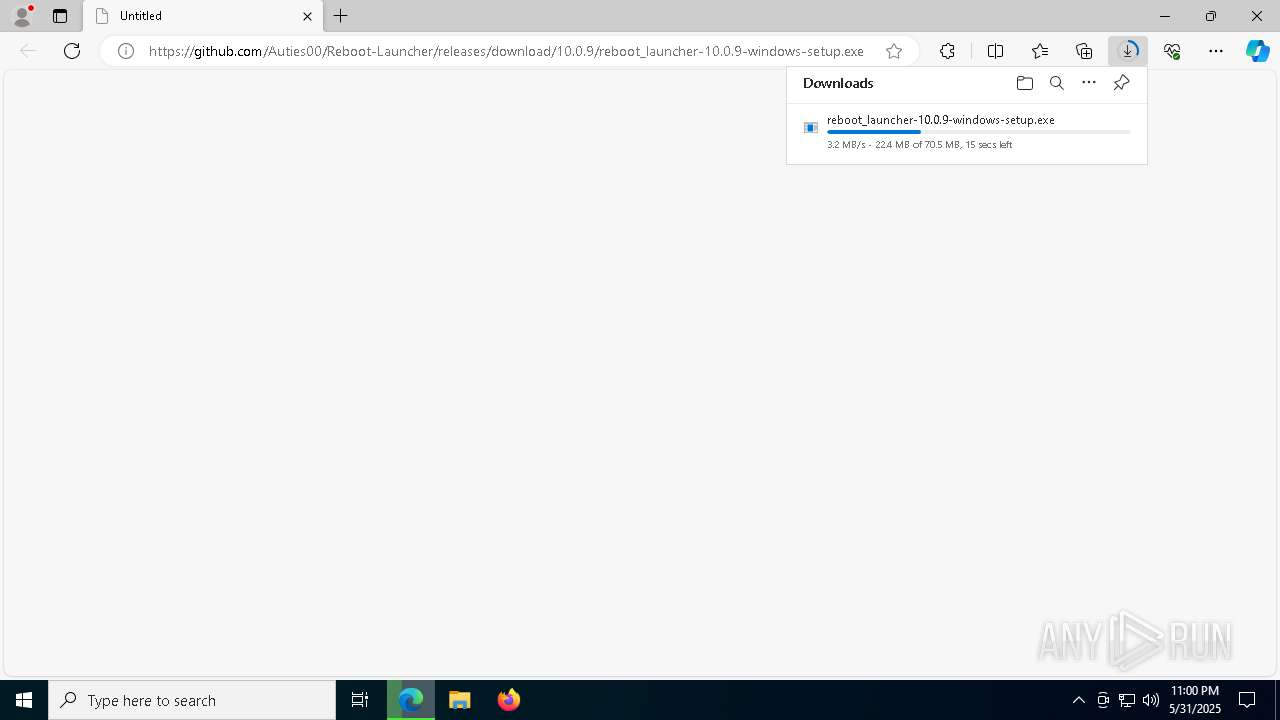
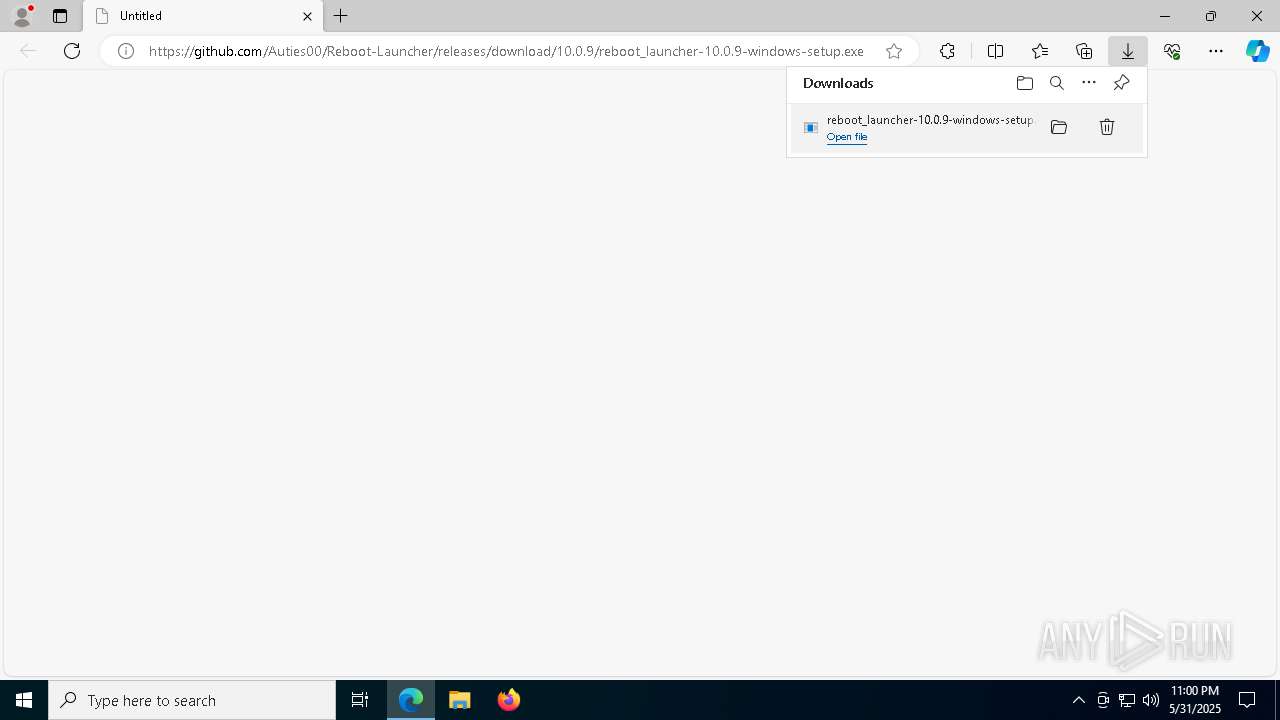
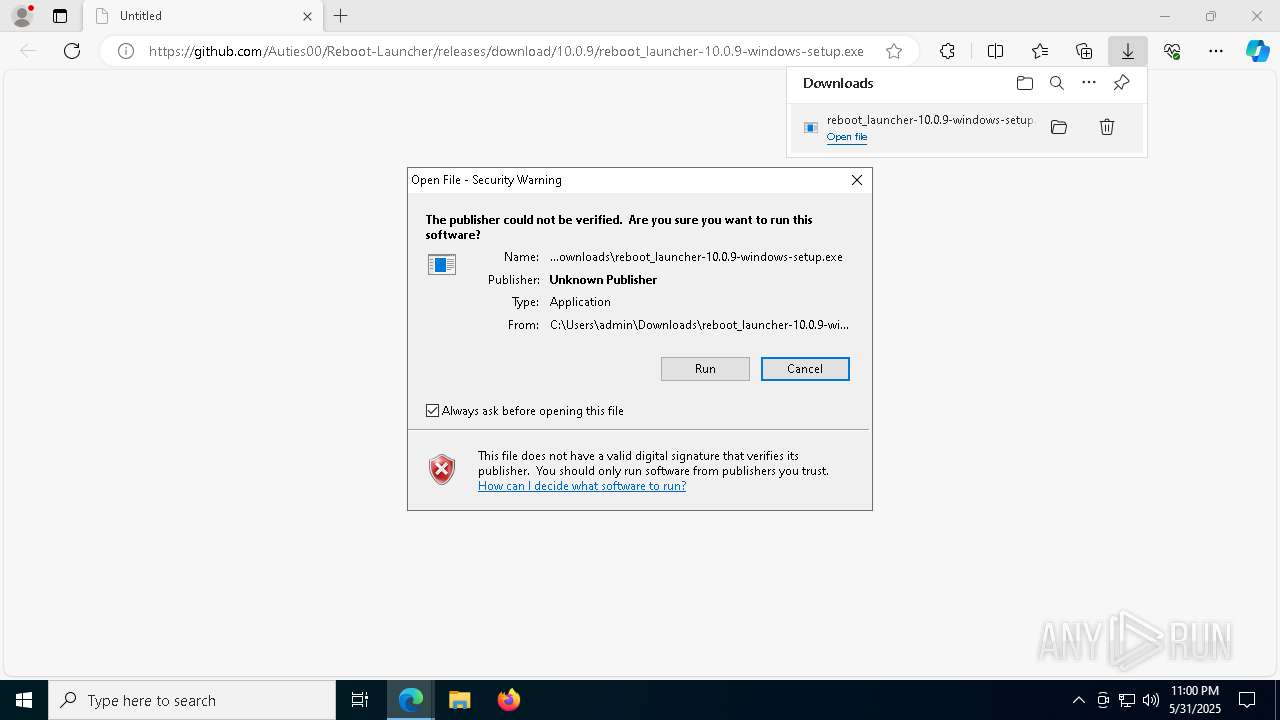
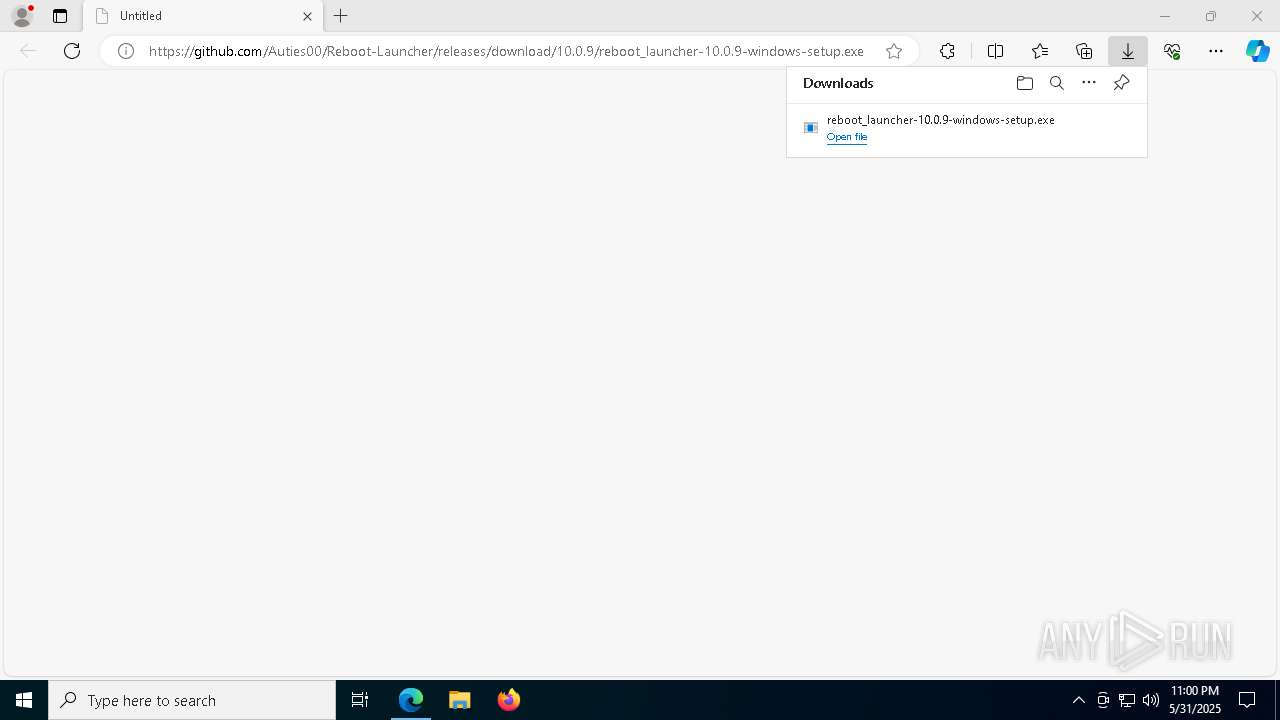
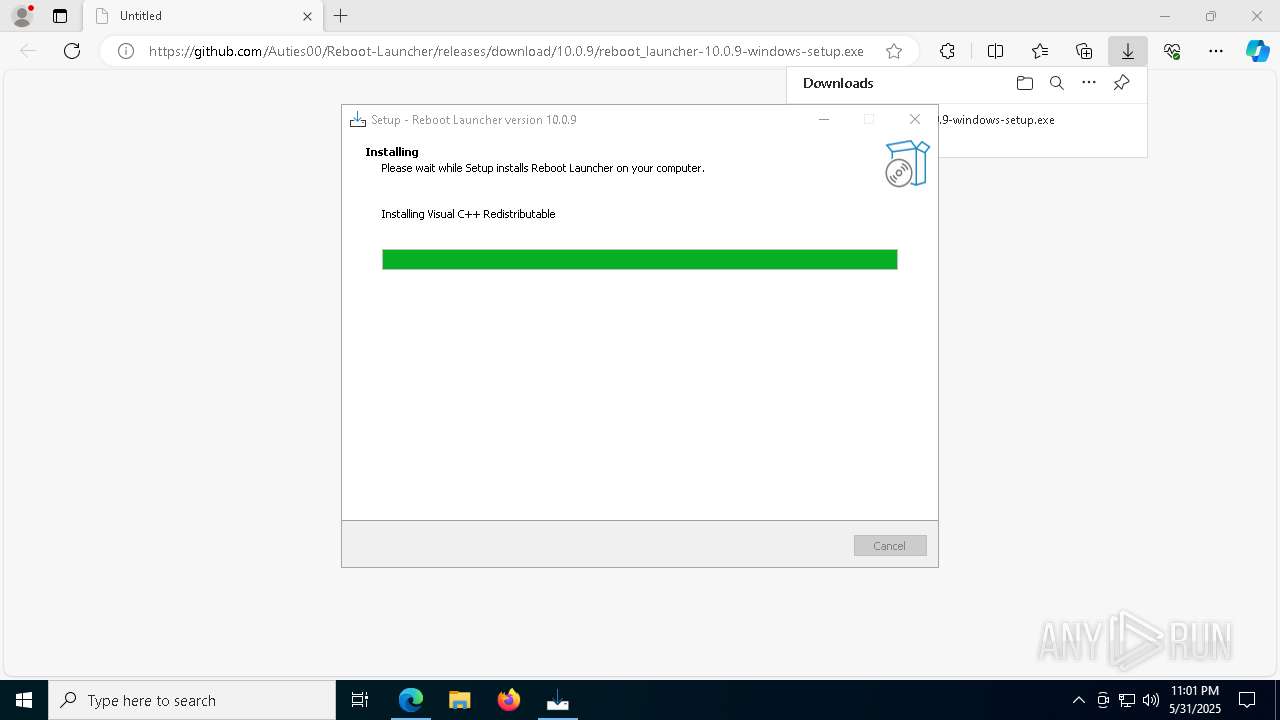
| URL: | https://github.com/Auties00/Reboot-Launcher/releases/download/10.0.9/reboot_launcher-10.0.9-windows-setup.exe |
| Full analysis: | https://app.any.run/tasks/78365464-b748-45b9-b33d-7430530d9042 |
| Verdict: | Malicious activity |
| Analysis date: | May 31, 2025, 23:00:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D6BCAFA49231A095D3ABDB84C27EC80E |
| SHA1: | 4175645EAC8DE80B0AA8C125CB16FACE115B565D |
| SHA256: | B0D5096E54C95CDDB8E0427FB358BCDC9E3321FEEFC6FEBF11E8EEFEE41CB5C9 |
| SSDEEP: | 3:N8tEdfB9yRRL1E2kCUDgAf/h/KSXA:2udvoL1r6DFCSXA |
MALICIOUS
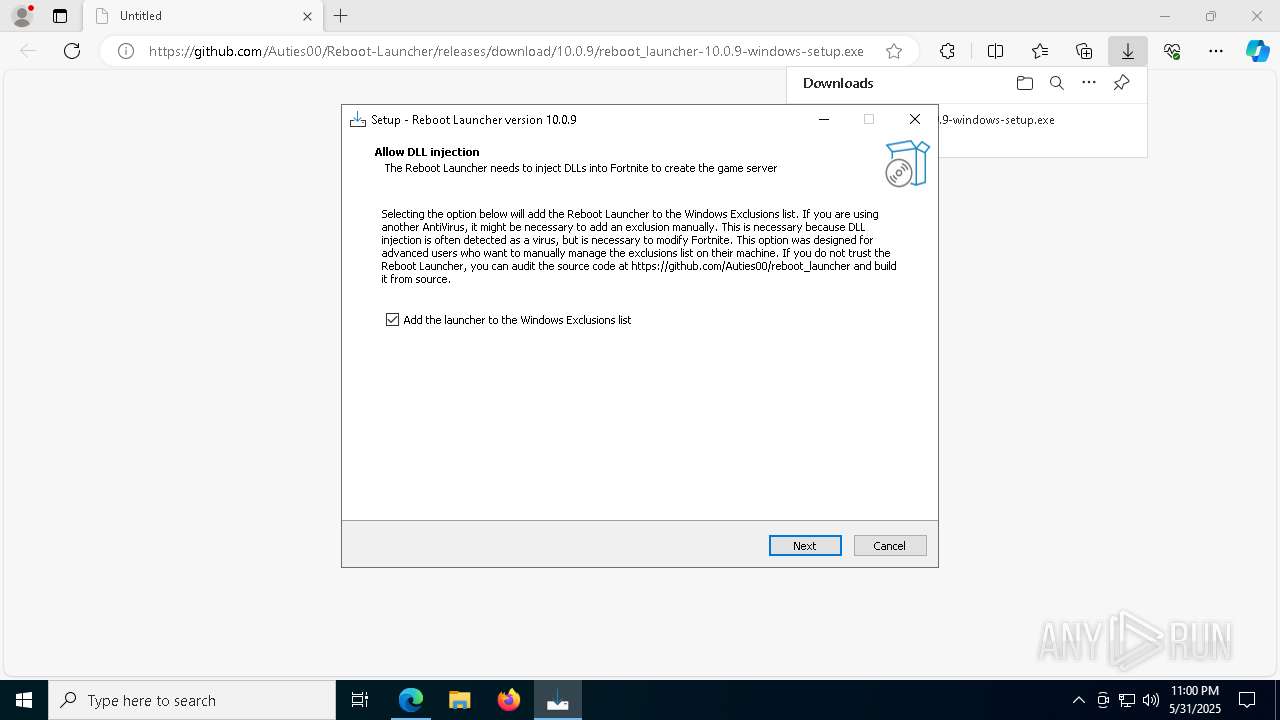
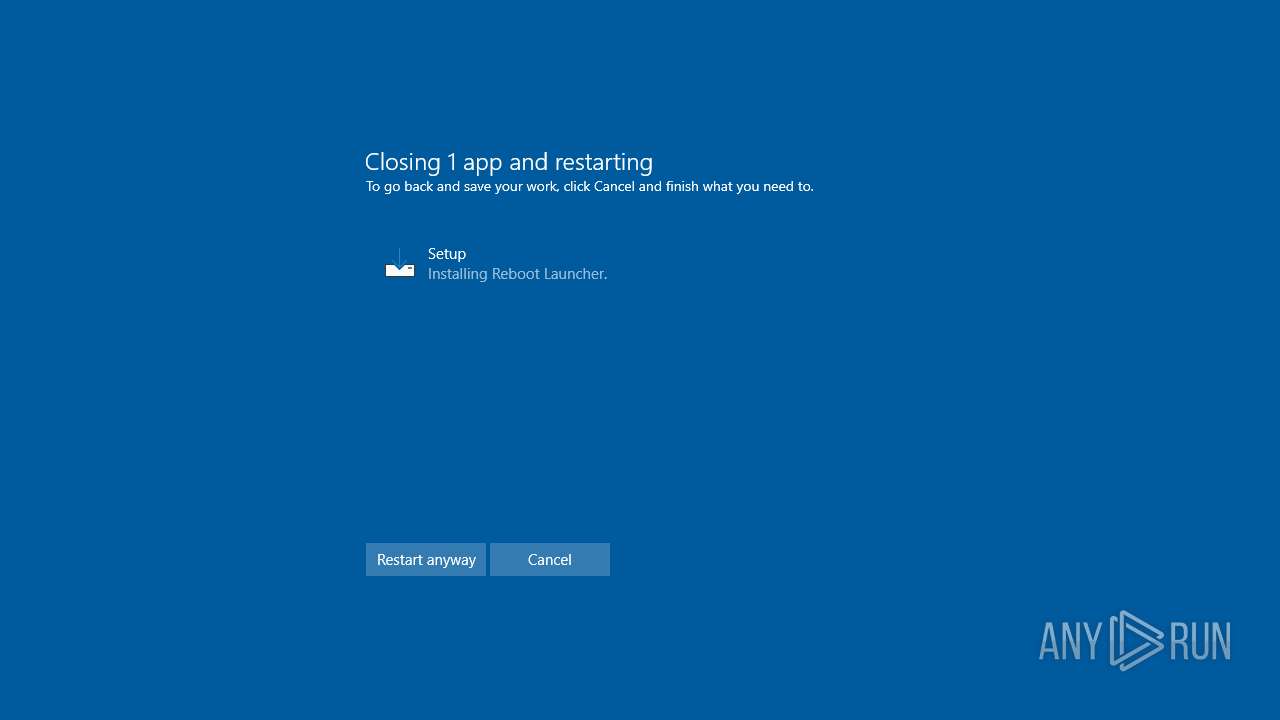
Changes powershell execution policy (Bypass)
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
Changes Windows Defender settings
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
Adds path to the Windows Defender exclusion list
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
Bypass execution policy to execute commands
- powershell.exe (PID: 3784)
SUSPICIOUS
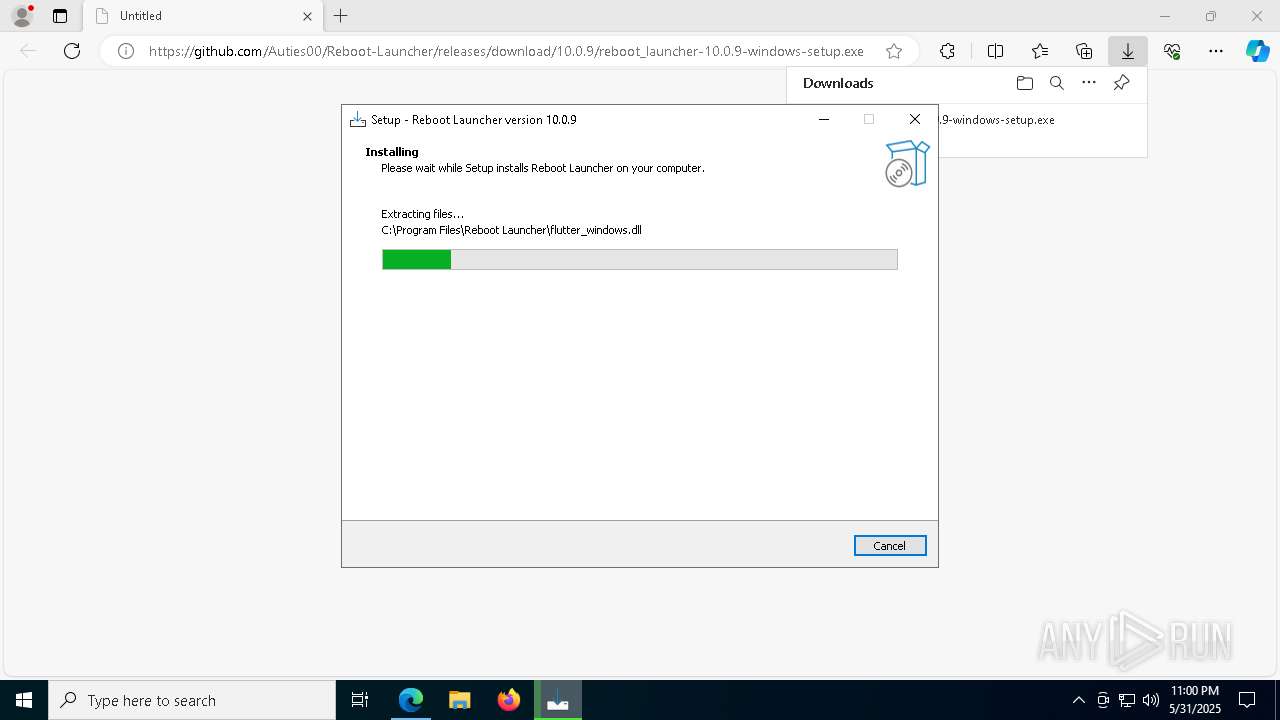
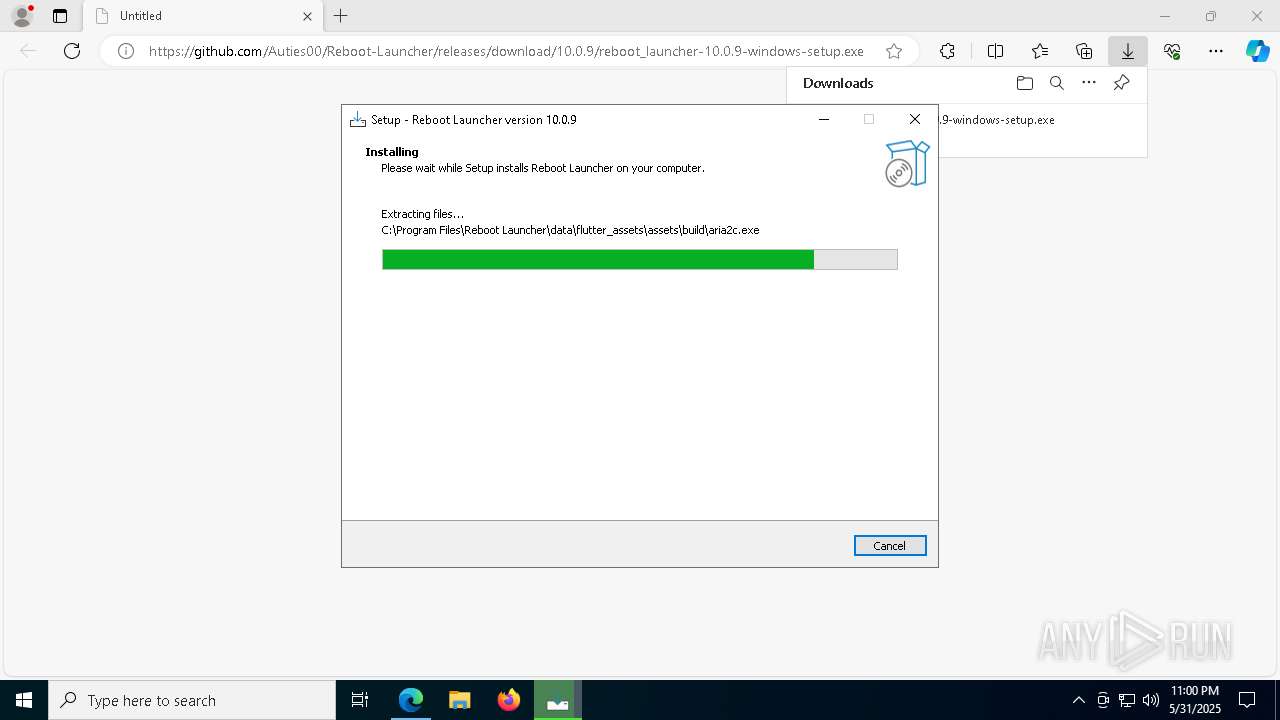
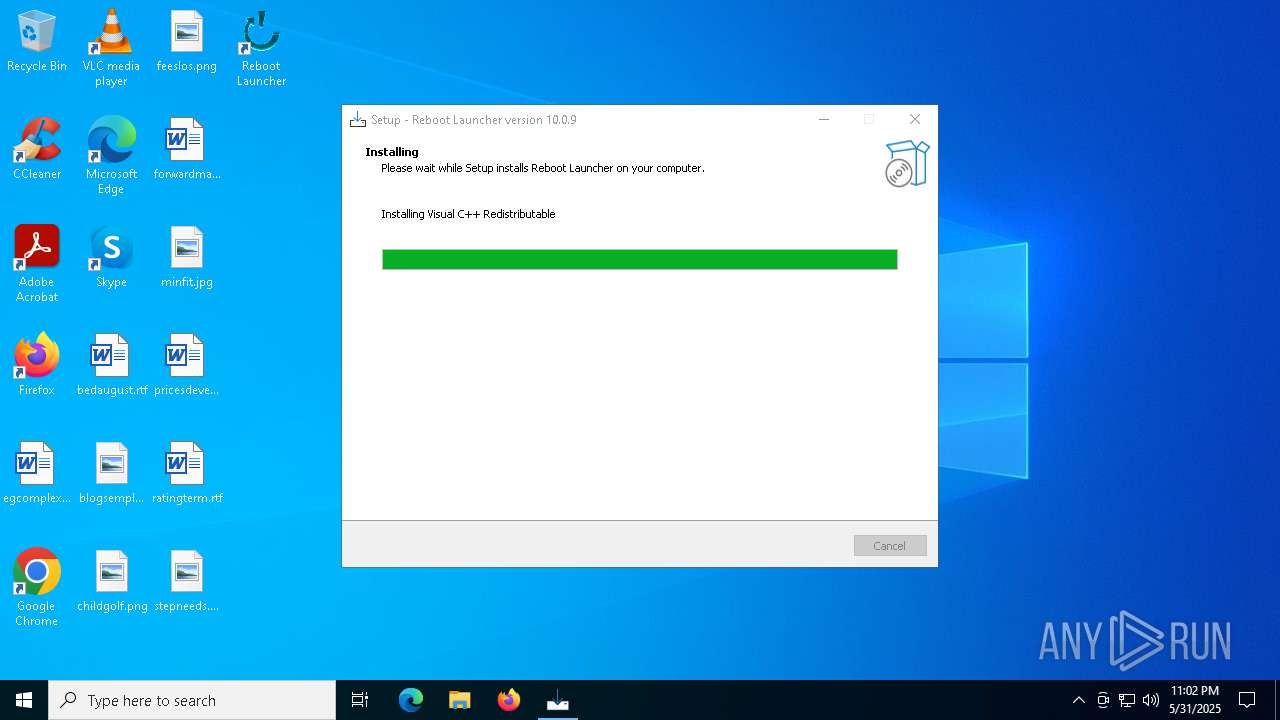
Executable content was dropped or overwritten
- reboot_launcher-10.0.9-windows-setup.exe (PID: 2984)
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
- reboot_launcher-10.0.9-windows-setup.exe (PID: 7524)
- VC_redist.x64.exe (PID: 2892)
- VC_redist.x64.exe (PID: 864)
- VC_redist.x64.exe (PID: 8048)
- VC_redist.x64.exe (PID: 7316)
- VC_redist.x64.exe (PID: 5968)
Reads security settings of Internet Explorer
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 7312)
- VC_redist.x64.exe (PID: 864)
Reads the Windows owner or organization settings
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
Drops 7-zip archiver for unpacking
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
Starts a Microsoft application from unusual location
- VC_redist.x64.exe (PID: 2892)
- VC_redist.x64.exe (PID: 864)
- VC_redist.x64.exe (PID: 8048)
Process drops legitimate windows executable
- VC_redist.x64.exe (PID: 2892)
- VC_redist.x64.exe (PID: 8048)
- msiexec.exe (PID: 7968)
- VC_redist.x64.exe (PID: 5968)
- VC_redist.x64.exe (PID: 864)
Starts itself from another location
- VC_redist.x64.exe (PID: 864)
Executes as Windows Service
- VSSVC.exe (PID: 3192)
Searches for installed software
- VC_redist.x64.exe (PID: 864)
- dllhost.exe (PID: 5428)
The process drops C-runtime libraries
- msiexec.exe (PID: 7968)
Application launched itself
- VC_redist.x64.exe (PID: 6240)
- VC_redist.x64.exe (PID: 7316)
Script adds exclusion path to Windows Defender
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
Starts POWERSHELL.EXE for commands execution
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
INFO
Application launched itself
- msedge.exe (PID: 7752)
- msedge.exe (PID: 8128)
Create files in a temporary directory
- reboot_launcher-10.0.9-windows-setup.exe (PID: 2984)
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
- reboot_launcher-10.0.9-windows-setup.exe (PID: 7524)
- VC_redist.x64.exe (PID: 864)
Reads the computer name
- identity_helper.exe (PID: 7744)
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 7312)
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
- VC_redist.x64.exe (PID: 864)
- VC_redist.x64.exe (PID: 8048)
Process checks computer location settings
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 7312)
- VC_redist.x64.exe (PID: 864)
Executable content was dropped or overwritten
- msedge.exe (PID: 7752)
- msiexec.exe (PID: 7968)
Checks supported languages
- identity_helper.exe (PID: 7744)
- reboot_launcher-10.0.9-windows-setup.exe (PID: 2984)
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 7312)
- reboot_launcher-10.0.9-windows-setup.exe (PID: 7524)
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
- _setup64.tmp (PID: 6840)
- VC_redist.x64.exe (PID: 8048)
- VC_redist.x64.exe (PID: 864)
- VC_redist.x64.exe (PID: 2892)
Reads Environment values
- identity_helper.exe (PID: 7744)
Detects InnoSetup installer (YARA)
- reboot_launcher-10.0.9-windows-setup.exe (PID: 2984)
- reboot_launcher-10.0.9-windows-setup.exe (PID: 7524)
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 7312)
Compiled with Borland Delphi (YARA)
- reboot_launcher-10.0.9-windows-setup.exe (PID: 2984)
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 7312)
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
- reboot_launcher-10.0.9-windows-setup.exe (PID: 7524)
The sample compiled with english language support
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
- VC_redist.x64.exe (PID: 2892)
- VC_redist.x64.exe (PID: 864)
- VC_redist.x64.exe (PID: 8048)
- msiexec.exe (PID: 7968)
- VC_redist.x64.exe (PID: 7316)
- VC_redist.x64.exe (PID: 5968)
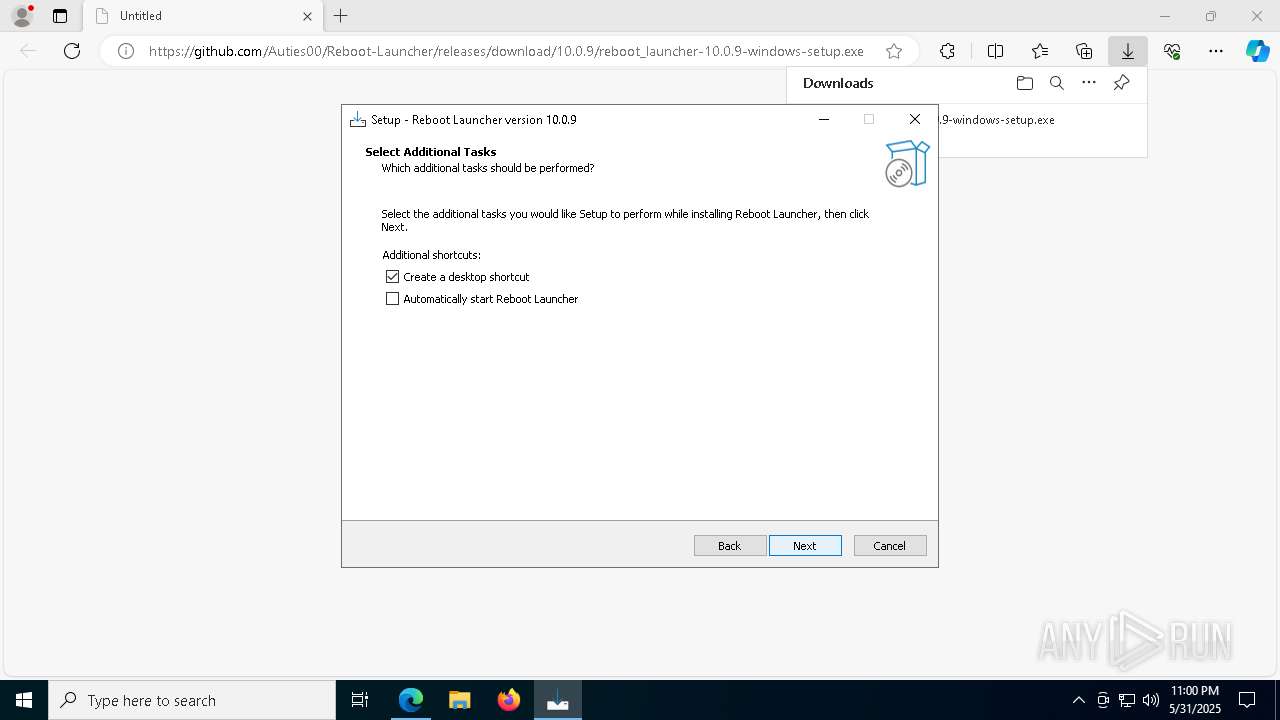
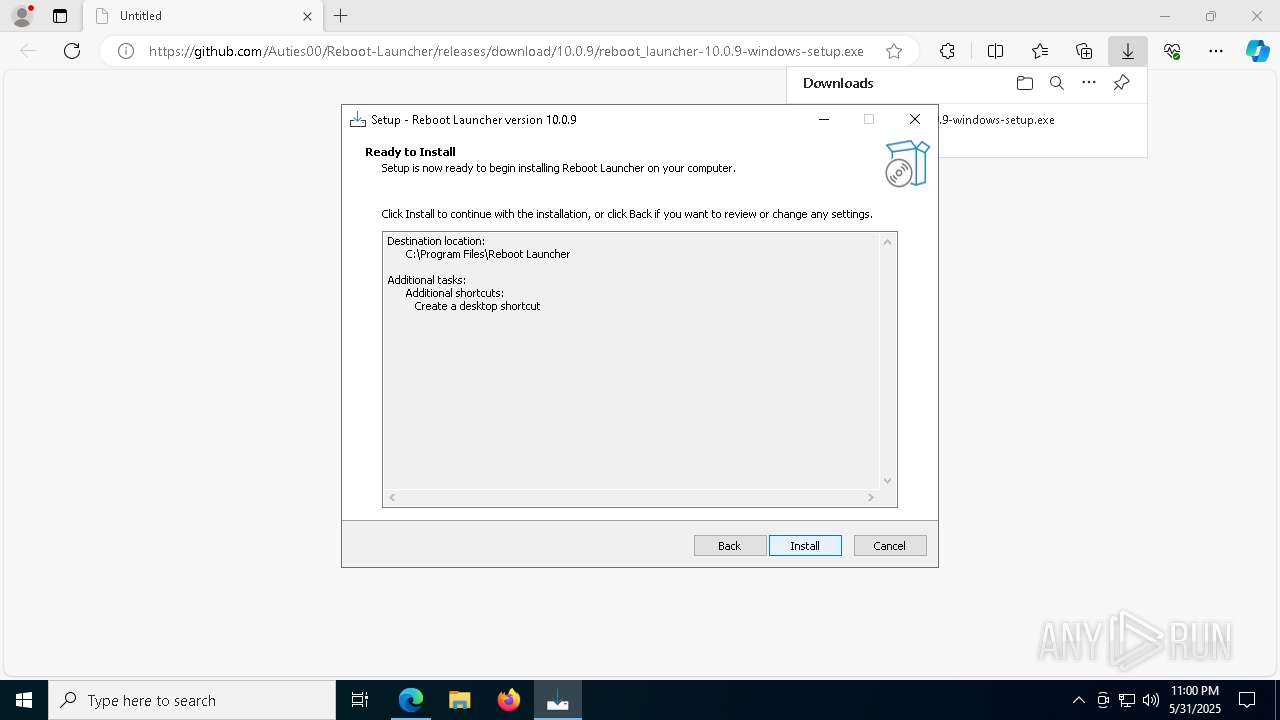
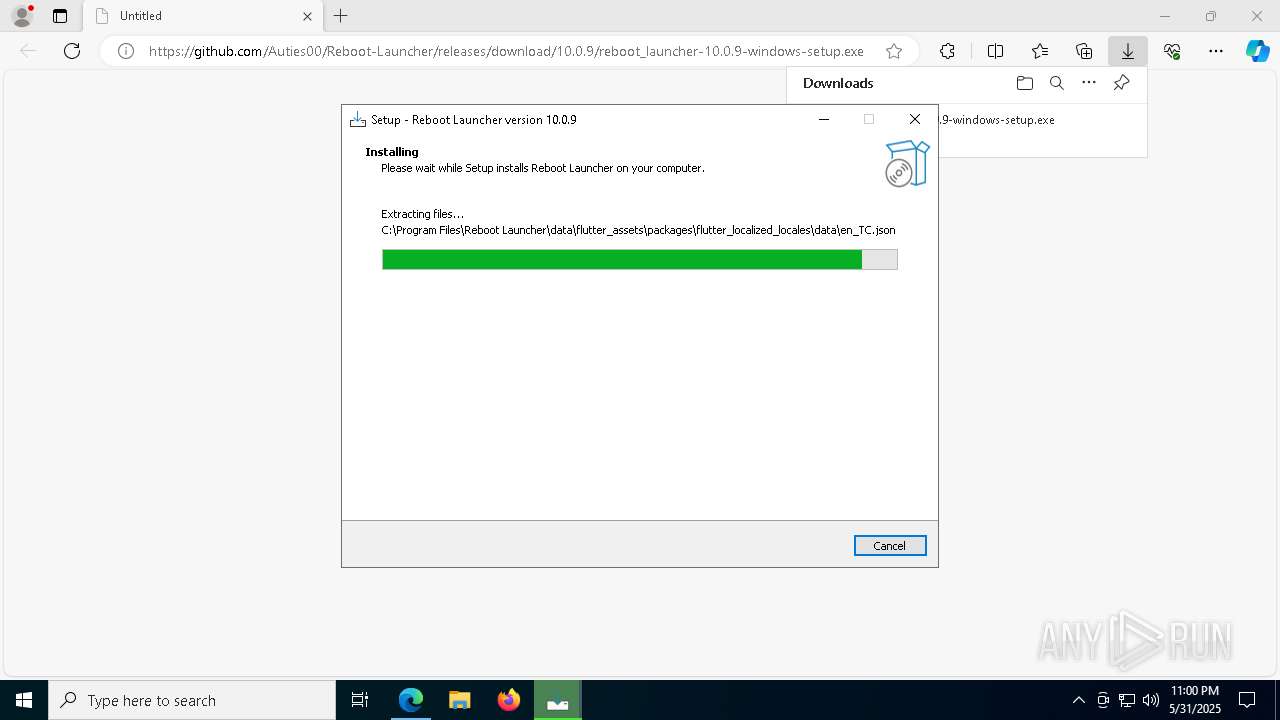
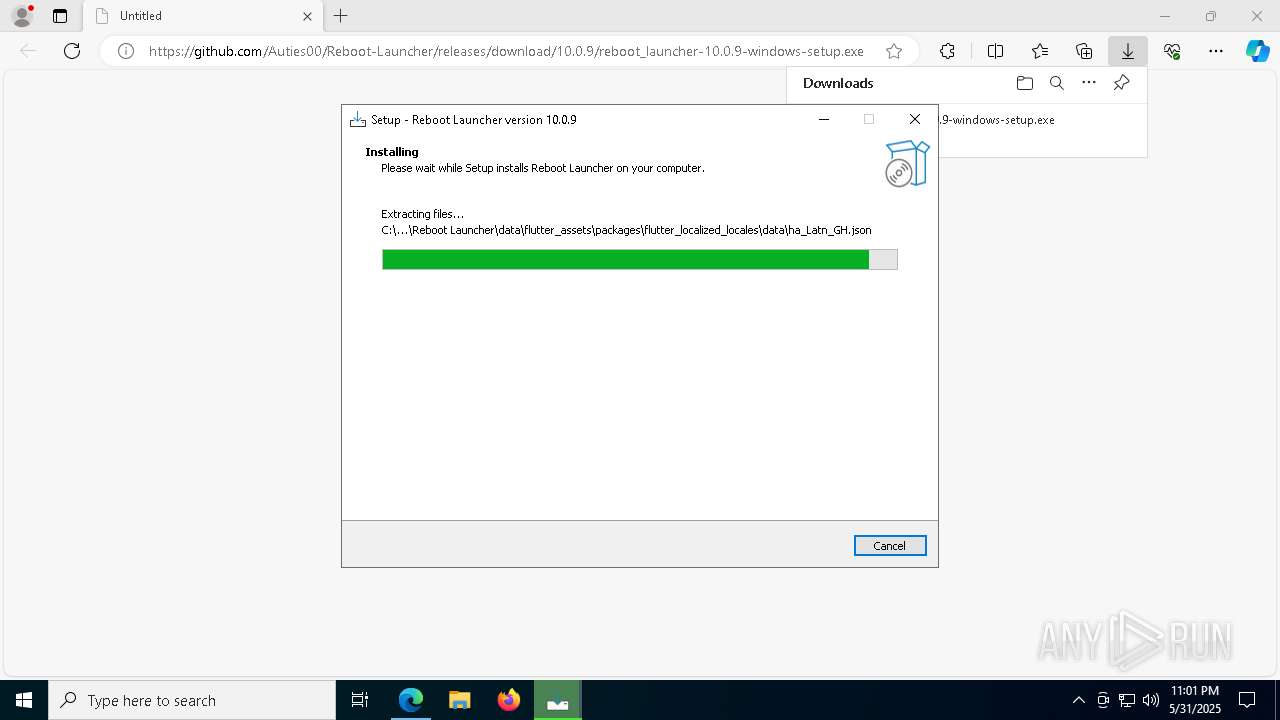
Creates files in the program directory
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
Creates a software uninstall entry
- reboot_launcher-10.0.9-windows-setup.tmp (PID: 8148)
Reads the software policy settings
- slui.exe (PID: 8144)
Manages system restore points
- SrTasks.exe (PID: 4404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
204
Monitored processes
69
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=7260 --field-trial-handle=2328,i,9183749702355331453,7850713482027038168,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2584 --field-trial-handle=2324,i,16544591966232213932,13890317247122900357,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5032 --field-trial-handle=2324,i,16544591966232213932,13890317247122900357,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | "C:\WINDOWS\Temp\{028F11BC-12BA-468B-9E14-E62CCE571B7E}\.cr\VC_redist.x64.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\is-D5OK7.tmp\VC_redist.x64.exe" -burn.filehandle.attached=772 -burn.filehandle.self=780 /quiet | C:\Windows\Temp\{028F11BC-12BA-468B-9E14-E62CCE571B7E}\.cr\VC_redist.x64.exe | VC_redist.x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.40.33810 Exit code: 3010 Version: 14.40.33810.0 Modules
| |||||||||||||||
| 1472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6128 --field-trial-handle=2328,i,9183749702355331453,7850713482027038168,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1680 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | _setup64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6084 --field-trial-handle=2328,i,9183749702355331453,7850713482027038168,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2596 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5460 --field-trial-handle=2328,i,9183749702355331453,7850713482027038168,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2600 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x304,0x308,0x30c,0x300,0x314,0x7ffc89e75fd8,0x7ffc89e75fe4,0x7ffc89e75ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
20 672
Read events
19 657
Write events
647
Delete events
368
Modification events
| (PID) Process: | (7752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7752) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 757501C70C952F00 | |||
| (PID) Process: | (7752) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E11008C70C952F00 | |||
| (PID) Process: | (7752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656050 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C5FC17E2-CE40-4271-A77F-AB3518F9F48F} | |||
| (PID) Process: | (7752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656050 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B9434C1F-5398-4111-B243-0669A3FDF053} | |||
| (PID) Process: | (7752) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 00FF41C70C952F00 | |||
| (PID) Process: | (7752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
124
Suspicious files
1 471
Text files
128
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f615.TMP | — | |
MD5:— | SHA256:— | |||
| 7752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF11f634.TMP | — | |
MD5:— | SHA256:— | |||
| 7752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11f644.TMP | — | |
MD5:— | SHA256:— | |||
| 7752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11f644.TMP | — | |
MD5:— | SHA256:— | |||
| 7752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11f653.TMP | — | |
MD5:— | SHA256:— | |||
| 7752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF11f653.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
82
DNS requests
69
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7196 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2796 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748969517&P2=404&P3=2&P4=gWW0APBIVM%2bp2RyZW2%2buOaAwNPrttWFuGSxdkQ5SpT%2bjR5phvtdryWlvDFevEW7GbT29wnhMtHmzjgiCKgxfZA%3d%3d | unknown | — | — | whitelisted |
2796 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748969517&P2=404&P3=2&P4=gWW0APBIVM%2bp2RyZW2%2buOaAwNPrttWFuGSxdkQ5SpT%2bjR5phvtdryWlvDFevEW7GbT29wnhMtHmzjgiCKgxfZA%3d%3d | unknown | — | — | whitelisted |
2796 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748969517&P2=404&P3=2&P4=gWW0APBIVM%2bp2RyZW2%2buOaAwNPrttWFuGSxdkQ5SpT%2bjR5phvtdryWlvDFevEW7GbT29wnhMtHmzjgiCKgxfZA%3d%3d | unknown | — | — | whitelisted |
2796 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c02ba7ad-8ae4-470f-ad2e-eee6ff1f6a23?P1=1748985121&P2=404&P3=2&P4=OuNJZ3REhw0gYEJioPwyB0Or%2bDNnSXMss8SGJ73EQXzx7G2LHhHtGOjRKEX%2brJpINZ4kK%2bi8ZqqUq3aM9PmMdA%3d%3d | unknown | — | — | whitelisted |
2796 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748969517&P2=404&P3=2&P4=gWW0APBIVM%2bp2RyZW2%2buOaAwNPrttWFuGSxdkQ5SpT%2bjR5phvtdryWlvDFevEW7GbT29wnhMtHmzjgiCKgxfZA%3d%3d | unknown | — | — | whitelisted |
2796 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c02ba7ad-8ae4-470f-ad2e-eee6ff1f6a23?P1=1748985121&P2=404&P3=2&P4=OuNJZ3REhw0gYEJioPwyB0Or%2bDNnSXMss8SGJ73EQXzx7G2LHhHtGOjRKEX%2brJpINZ4kK%2bi8ZqqUq3aM9PmMdA%3d%3d | unknown | — | — | whitelisted |
2796 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c02ba7ad-8ae4-470f-ad2e-eee6ff1f6a23?P1=1748985121&P2=404&P3=2&P4=OuNJZ3REhw0gYEJioPwyB0Or%2bDNnSXMss8SGJ73EQXzx7G2LHhHtGOjRKEX%2brJpINZ4kK%2bi8ZqqUq3aM9PmMdA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4164 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3760 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7752 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5956 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5956 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
5956 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Supabase Development Platform Related Domain in DNS Lookup |
— | — | Misc activity | ET INFO Observed Online Application Hosting Domain (supabase .co in TLS SNI) |
— | — | Misc activity | ET INFO Observed Online Application Hosting Domain (supabase .co in TLS SNI) |
— | — | Misc activity | ET INFO Observed Online Application Hosting Domain (supabase .co in TLS SNI) |
— | — | Misc activity | ET INFO Supabase Development Platform Related Domain in DNS Lookup |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|