| File name: | invoice4806.doc |
| Full analysis: | https://app.any.run/tasks/f754c32e-b487-4526-924c-67d1e58d7804 |
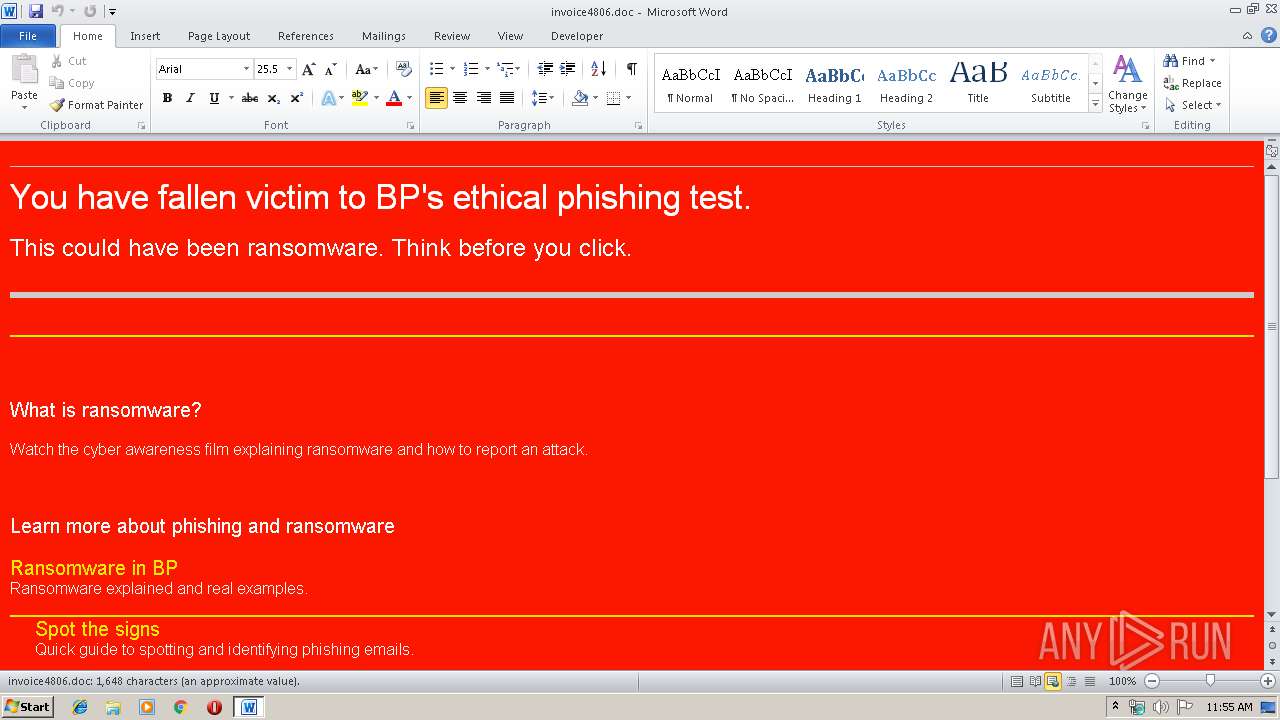
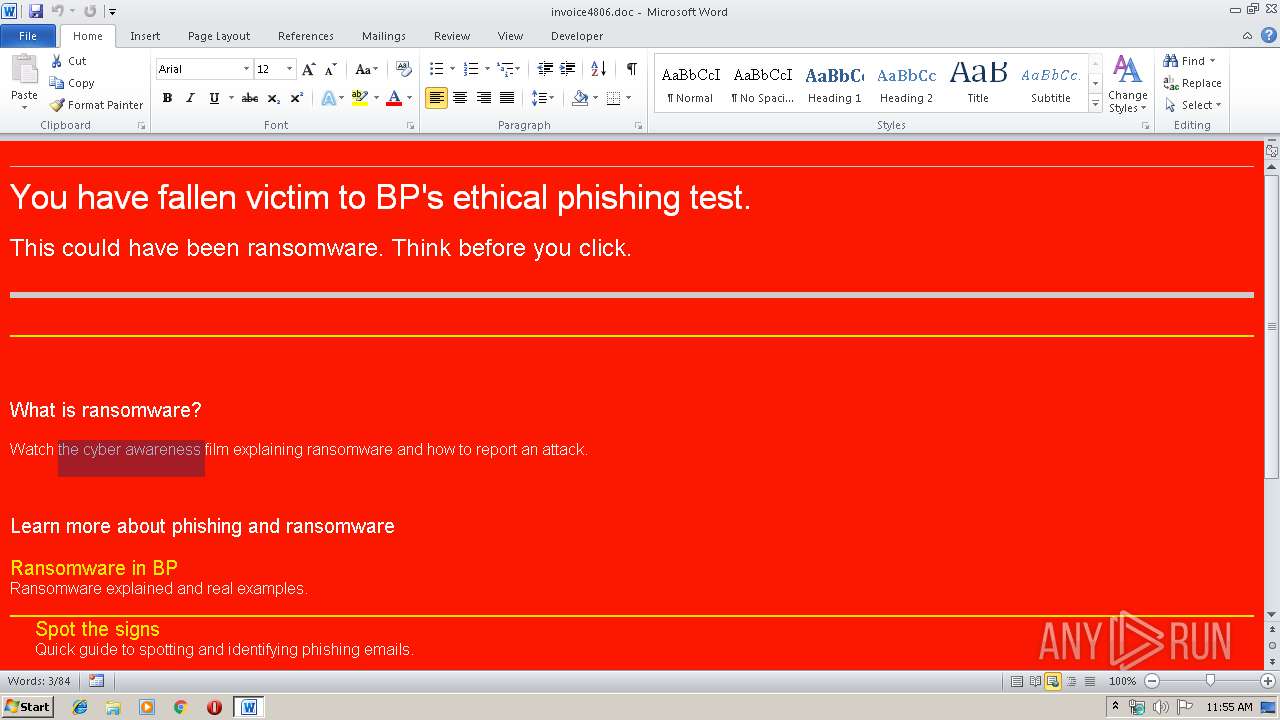
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 10:55:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF line terminators |
| MD5: | 1F6F0C6C32FEF470DFFDF94B63896DBB |
| SHA1: | DF4107E2B33B93B729213BCDCBA85FF7313CEF97 |
| SHA256: | B0B22BAB86D1B627B94184B6D514985A188F2748F383D943A311826655F17D66 |
| SSDEEP: | 96:aCsDL6MIxDplRqq2yYXdjWNicXJ11CKjR5APsgIwTlhva63PpIw/ERwRswMM:aCsv6PpsDLcXVC+FgIGlhva0pIEERWMM |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3548)
Creates files in the user directory
- WINWORD.EXE (PID: 3548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| ContentType: | text/html; charset=UTF-8 |
|---|---|
| Title: | Untitled Document |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3548 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\invoice4806.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 096
Read events
761
Write events
330
Delete events
5
Modification events
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2z$ |
Value: 327A2400DC0D0000010000000000000000000000 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328218142 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328218256 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328218257 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: DC0D000018153A658F68D50100000000 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | <{$ |
Value: 3C7B2400DC0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | <{$ |
Value: 3C7B2400DC0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
24
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9A02.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{824B50BB-356C-467E-AD6D-FA8C0A568D9B} | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{6D23196D-3327-4D68-AB20-713A2065ACB5} | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1EE21EB6.png | — | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$voice4806.doc | pgc | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSF-CTBL.FSF | binary | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-{388C02CF-D2CC-42FB-9C9D-422CAD53DD17}.FSD | binary | |
MD5:— | SHA256:— | |||
| 3548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSF-{0E1EEE64-E8C6-4E2A-9759-63CF07FD8988}.FSF | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3548 | WINWORD.EXE | OPTIONS | 403 | 54.83.101.48:80 | http://hbm5g0fj5xh.lucrativehiring.com/ | US | text | 16 b | malicious |
3548 | WINWORD.EXE | OPTIONS | 403 | 54.83.101.48:80 | http://hbm5g0fj5xh.lucrativehiring.com/ | US | text | 16 b | malicious |
3548 | WINWORD.EXE | OPTIONS | 403 | 54.83.101.48:80 | http://hbm5g0fj5xh.lucrativehiring.com/ | US | text | 16 b | malicious |
3548 | WINWORD.EXE | OPTIONS | 403 | 54.83.101.48:80 | http://hbm5g0fj5xh.lucrativehiring.com/ | US | text | 16 b | malicious |
3548 | WINWORD.EXE | GET | 200 | 54.83.101.48:80 | http://hbm5g0fj5xh.lucrativehiring.com/0785dc3b-17a0-43fb-8b7b-baf806dd02bd.png | US | image | 68 b | malicious |
3548 | WINWORD.EXE | GET | 200 | 54.83.101.48:80 | http://hbm5g0fj5xh.lucrativehiring.com/0785dc3b-17a0-43fb-8b7b-baf806dd02bd.png | US | image | 68 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3548 | WINWORD.EXE | 54.83.101.48:80 | hbm5g0fj5xh.lucrativehiring.com | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hbm5g0fj5xh.lucrativehiring.com |
| malicious |