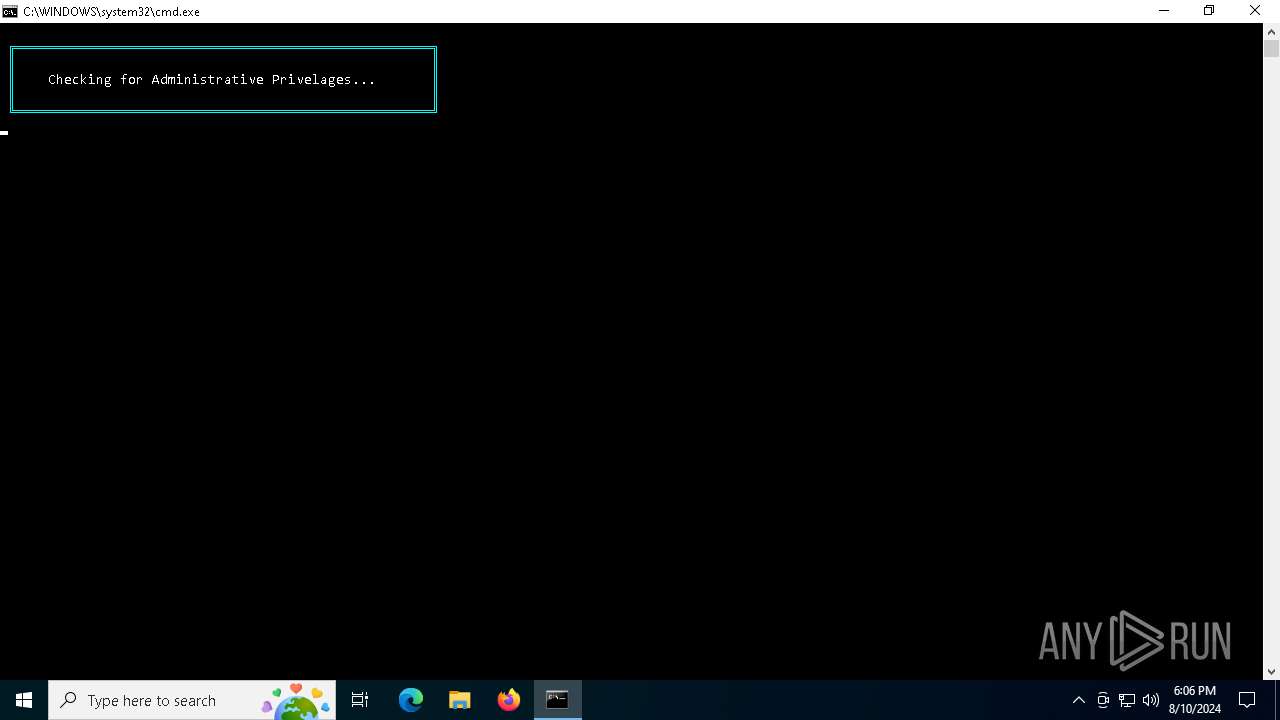
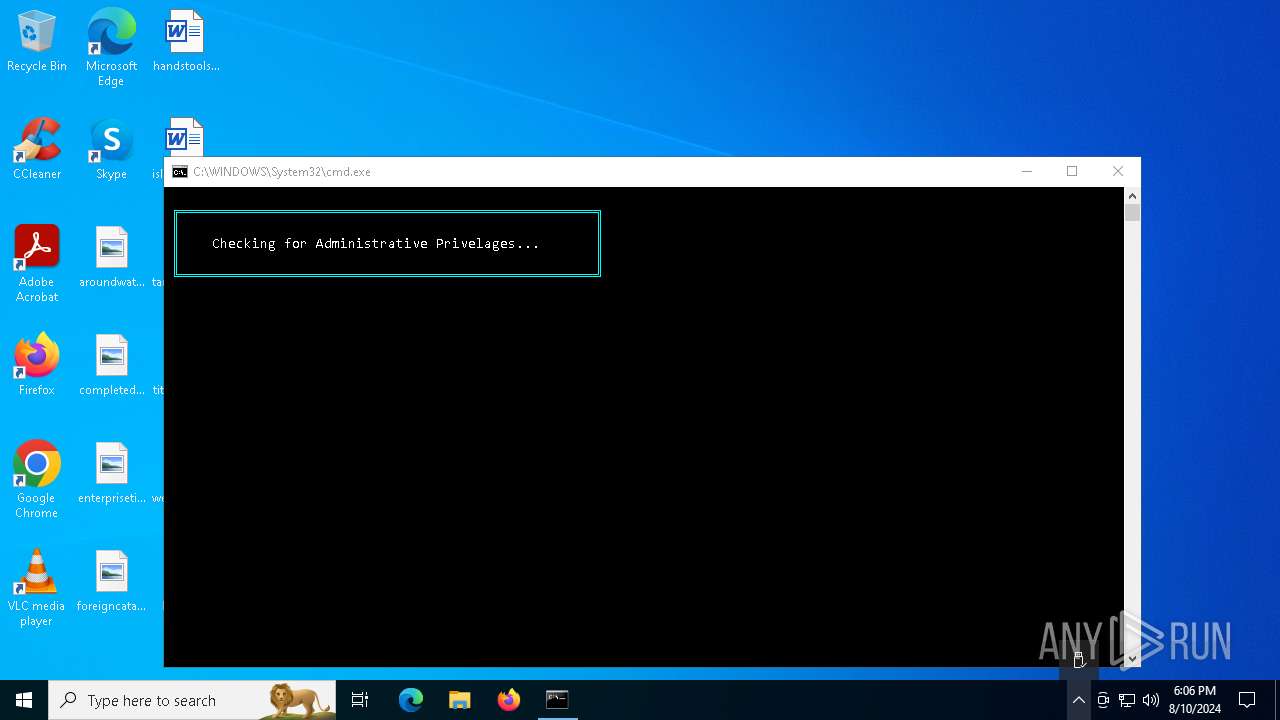
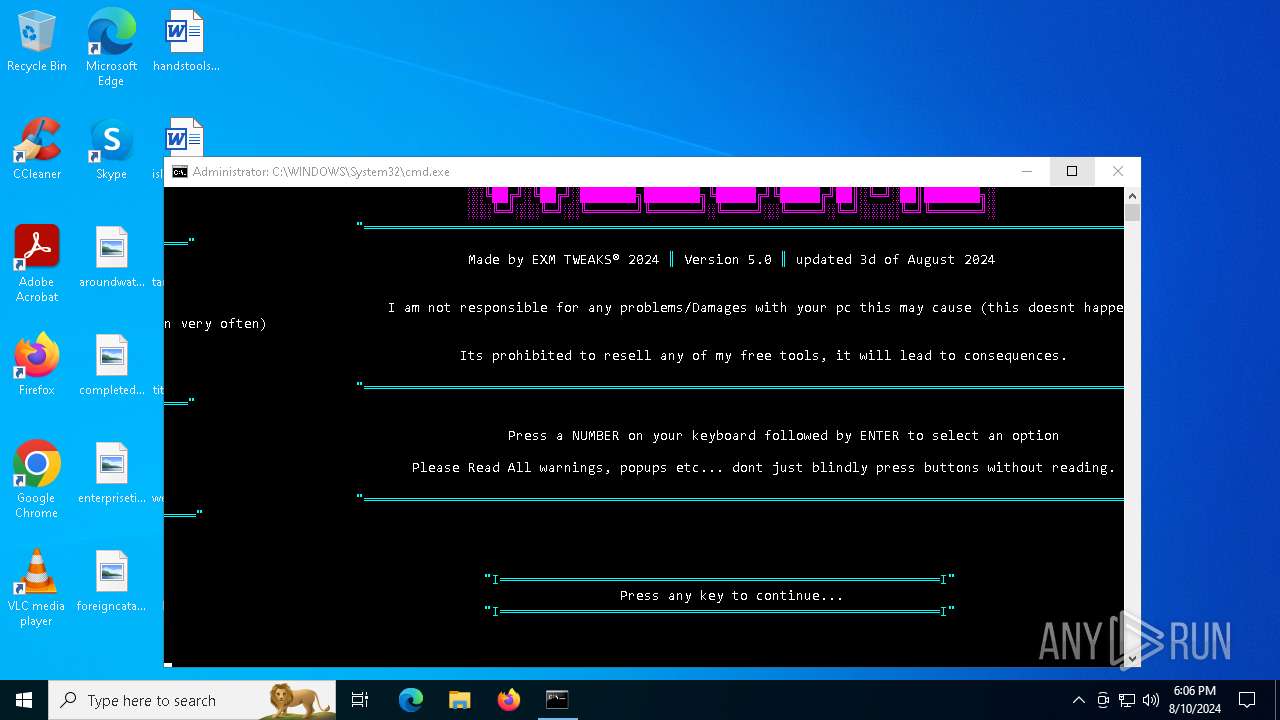
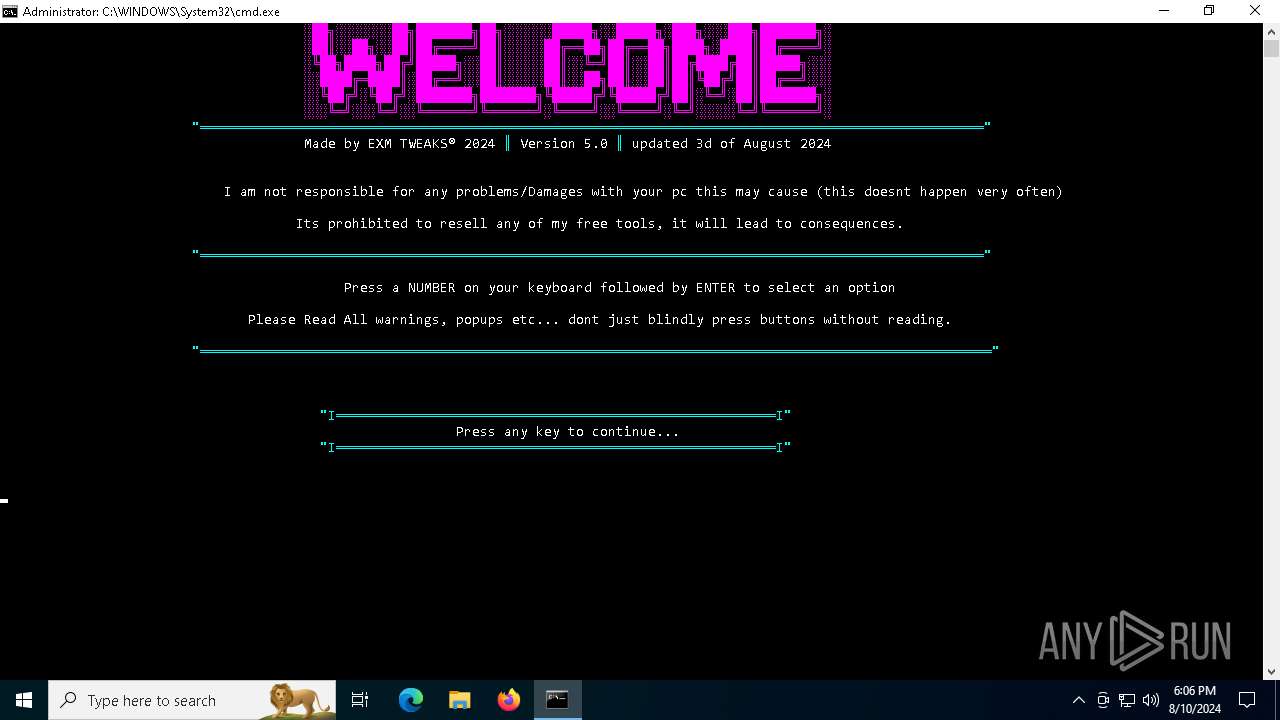
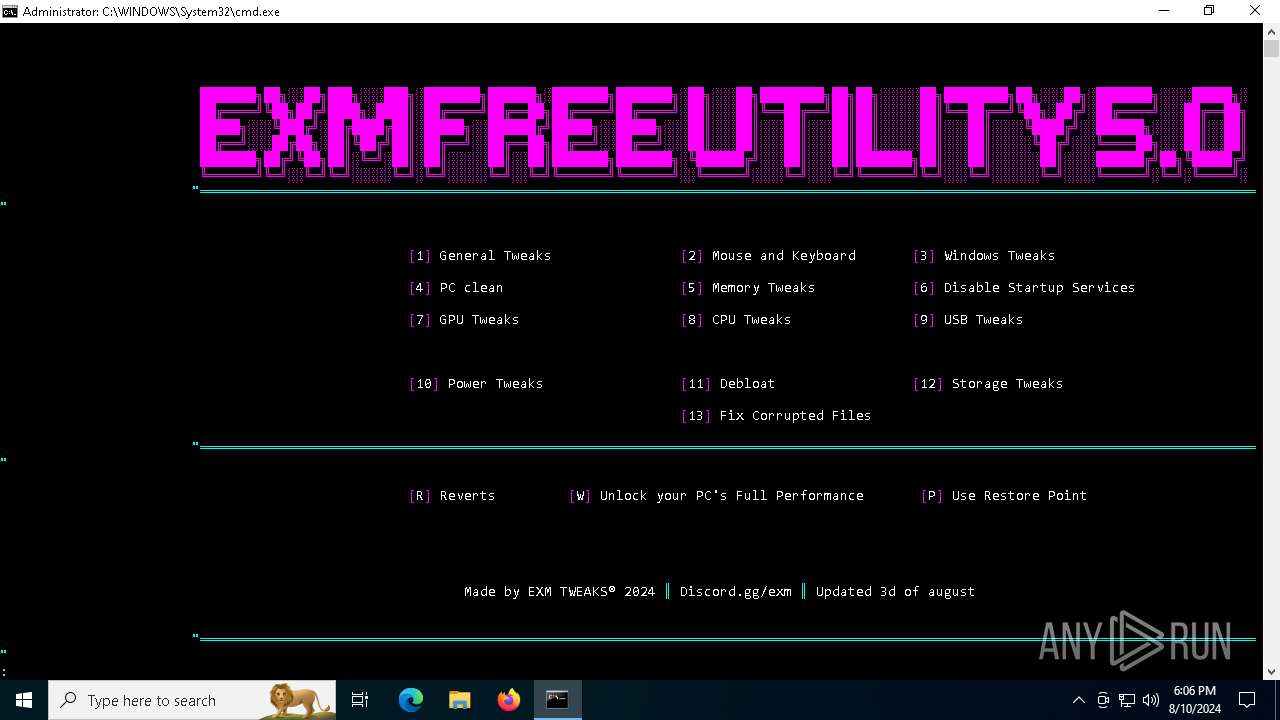
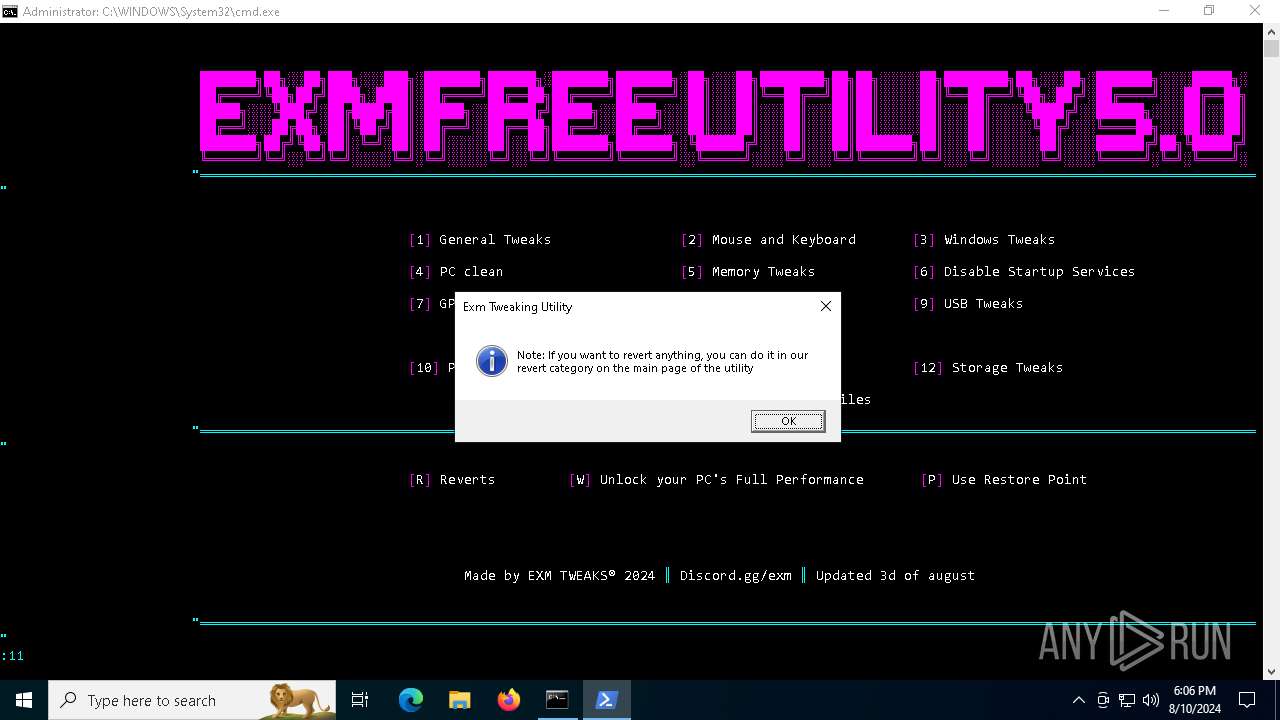
| File name: | EXM Free Tweaking Utility V5.cmd |
| Full analysis: | https://app.any.run/tasks/1a3ec8c0-c5f0-4a57-8b3c-790d827c94cf |
| Verdict: | Malicious activity |
| Analysis date: | August 10, 2024, 18:06:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, Unicode text, UTF-8 text, with very long lines (329), with CRLF line terminators, with escape sequences |
| MD5: | F3EFE94A63E4FF19F2216F5880ED49CE |
| SHA1: | A7CAE6087C383199051F3E36C349E18D1F56CED2 |
| SHA256: | B0AFE1E66BC0BAAD826B09CAB988213BCECACD372C004AC3C54A56E1B7373BD1 |
| SSDEEP: | 1536:y8HHBsY//qmWEnSC/DUm39wEszEnSC/DVr1ydkvCxM1rw2rwbH2m+Wm:FBsAs3DVDW |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 1020)
- cmd.exe (PID: 6356)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1020)
- cmd.exe (PID: 6356)
The process hide an interactive prompt from the user
- cmd.exe (PID: 6356)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6356)
- cmd.exe (PID: 1020)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6548)
- cmd.exe (PID: 1020)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6356)
- cmd.exe (PID: 1020)
Executing commands from ".cmd" file
- powershell.exe (PID: 6548)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6356)
- cmd.exe (PID: 1020)
Uses WMIC.EXE to obtain user accounts information
- cmd.exe (PID: 1104)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 6196)
Application launched itself
- cmd.exe (PID: 1020)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1104)
Potential Corporate Privacy Violation
- curl.exe (PID: 7104)
INFO
Checks supported languages
- chcp.com (PID: 6492)
- chcp.com (PID: 7084)
- chcp.com (PID: 6440)
- chcp.com (PID: 6428)
- chcp.com (PID: 3900)
- chcp.com (PID: 4844)
- curl.exe (PID: 7104)
- chcp.com (PID: 2424)
- chcp.com (PID: 964)
- chcp.com (PID: 5464)
- chcp.com (PID: 6432)
- chcp.com (PID: 5908)
- chcp.com (PID: 4168)
- chcp.com (PID: 1420)
Changes the display of characters in the console
- chcp.com (PID: 6440)
- chcp.com (PID: 6492)
- chcp.com (PID: 7084)
- chcp.com (PID: 6428)
- chcp.com (PID: 2424)
- chcp.com (PID: 4844)
- chcp.com (PID: 3900)
- chcp.com (PID: 6432)
- chcp.com (PID: 964)
- chcp.com (PID: 5908)
- chcp.com (PID: 4168)
- chcp.com (PID: 1420)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7116)
Reads the computer name
- curl.exe (PID: 7104)
Create files in a temporary directory
- curl.exe (PID: 7104)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6196)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6196)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
185
Monitored processes
47
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 964 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\EXMFRE~1.CMD" | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1104 | C:\WINDOWS\system32\cmd.exe /c wmic path Win32_UserAccount where name="admin" get sid | findstr "S-" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | powershell -NoProfile Enable-ComputerRestore -Drive 'C:\' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1288 | Reg.exe delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SystemRestore" /v "DisableConfig" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1420 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
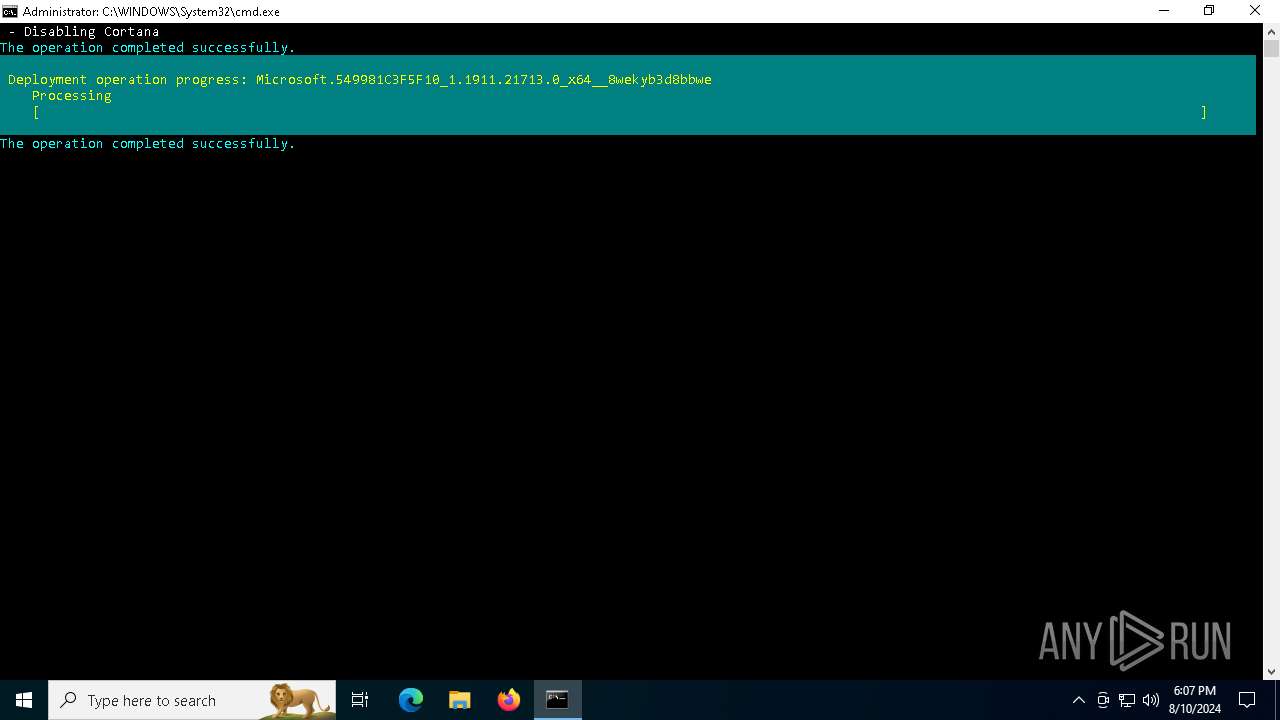
| 2240 | Powershell -Command "Get-appxpackage -allusers *Microsoft.549981C3F5F10* | Remove-AppxPackage" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2424 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3800 | timeout /t 1 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3900 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
31 089
Read events
31 065
Write events
21
Delete events
3
Modification events
| (PID) Process: | (6420) reg.exe | Key: | HKEY_CURRENT_USER\Console |
| Operation: | write | Name: | VirtualTerminalLevel |
Value: 1 | |||
| (PID) Process: | (6548) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6548) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6548) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6548) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6548) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (6548) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (6944) reg.exe | Key: | HKEY_CURRENT_USER\Console |
| Operation: | write | Name: | VirtualTerminalLevel |
Value: 1 | |||
| (PID) Process: | (6416) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP\Clients |
| Operation: | write | Name: | {09F7EDC5-294E-4180-AF6A-FB0E6A0E9513} |
Value: \\?\Volume{2f5c5e72-85a9-11eb-90a8-9a9b76358421}\:(C%3A) | |||
| (PID) Process: | (6416) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP\Leases |
| Operation: | delete value | Name: | {09F7EDC5-294E-4180-AF6A-FB0E6A0E9513} |
Value: | |||
Executable files
0
Suspicious files
1
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ewf3eot4.a12.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_o2wntbjc.hzq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gjeajwdc.gkt.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6548 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_d33uvgkh.eij.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1172 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_y12mk0bx.u5v.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dvrmblus.ezf.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1172 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ujmzlene.clk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6196 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_i1nf4aq1.jgd.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6548 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:BBDED40D24C05C72D2F6F30F7AC44D5C | SHA256:A3EAD4EDCADE03FE6193EF68F2873DE301110E43BC3C77EEFA4A5F57CFBF70F3 | |||
| 7104 | curl.exe | C:\Users\admin\AppData\Local\Temp\exm.zip | html | |
MD5:2182AB4F3A332A8C04A274C4094F7E0F | SHA256:FD7919EB535583DF7A8309A79A4CA596EE43986572557EA0A2EA82B75A1B7EF2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
44
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6636 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
6700 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4788 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 104.126.37.161:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.dropbox.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7104 | curl.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |