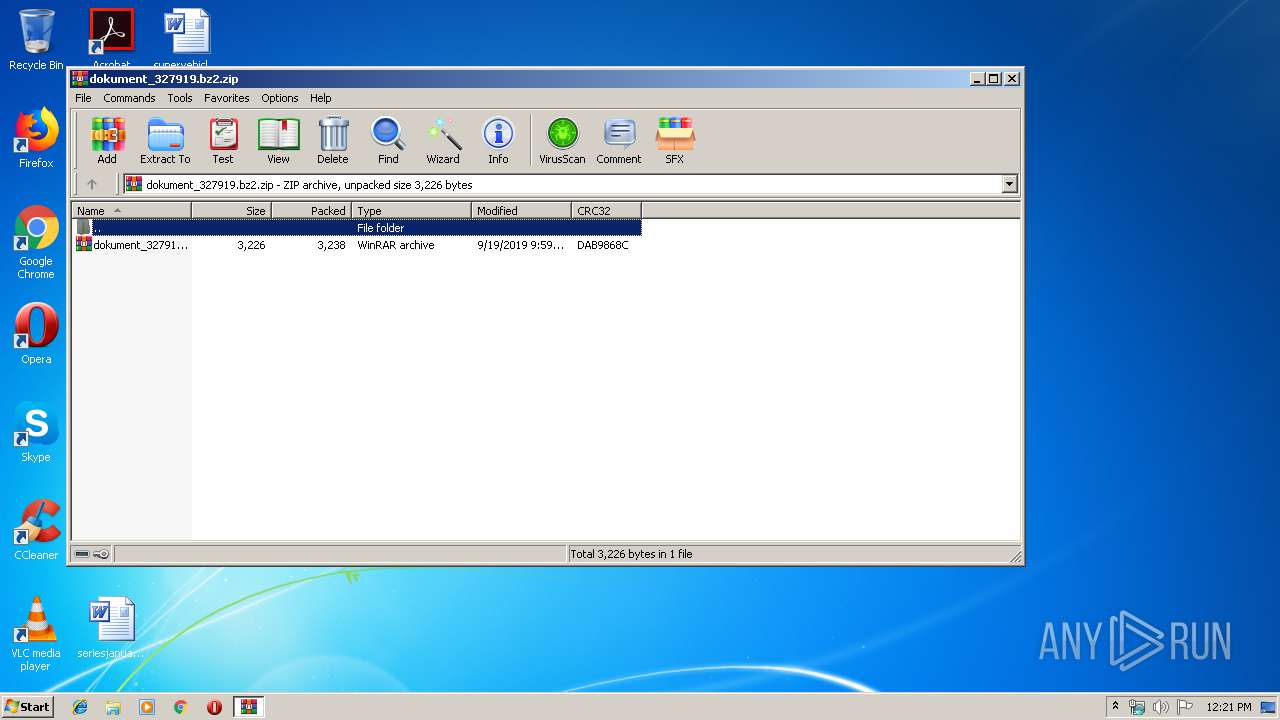
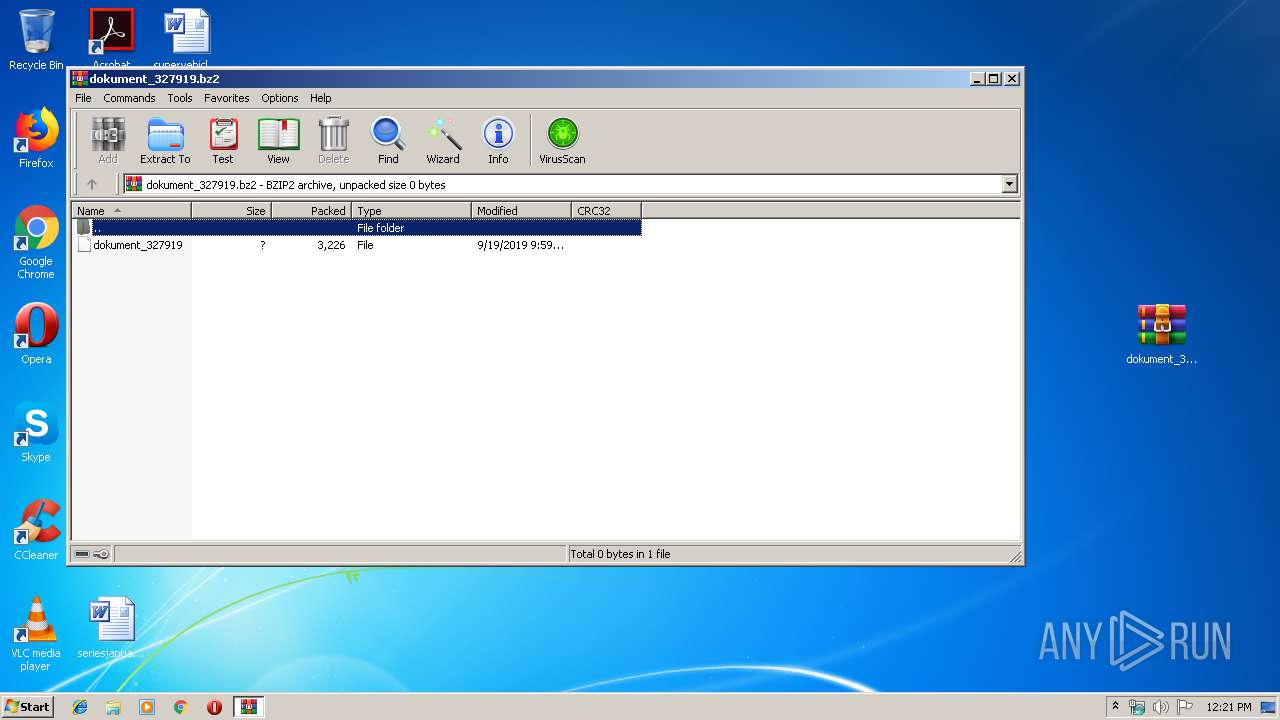
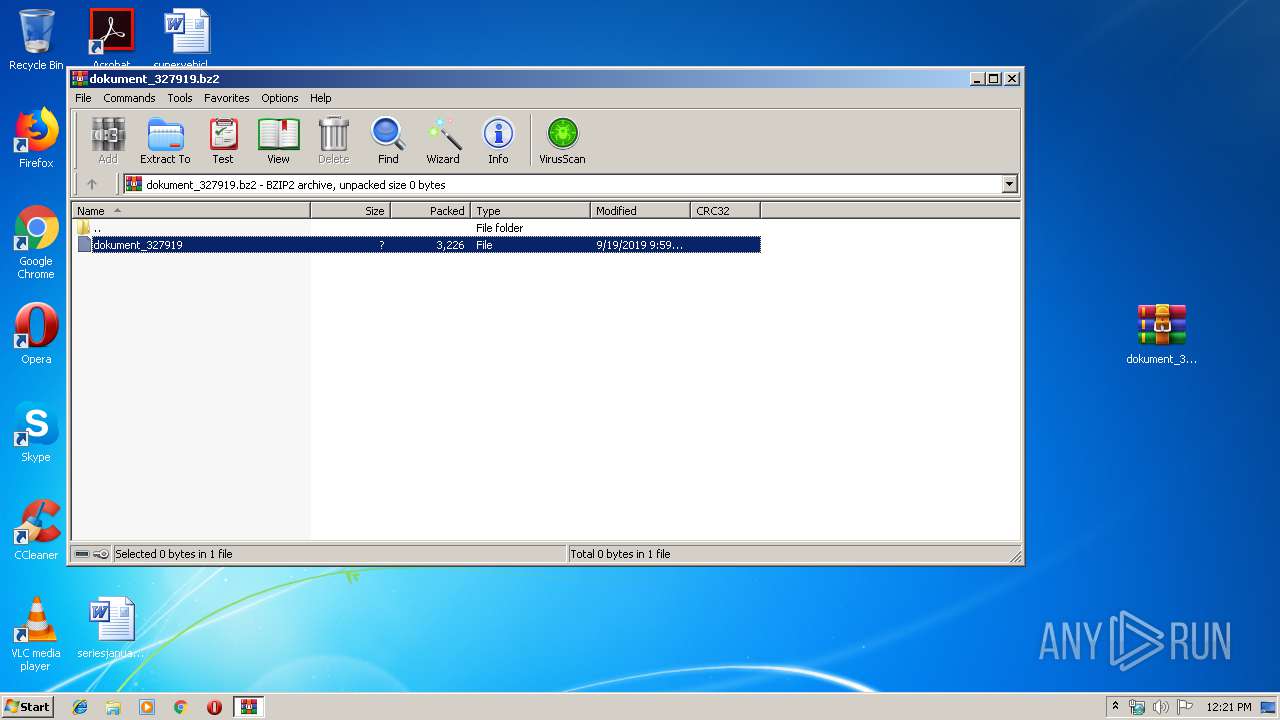
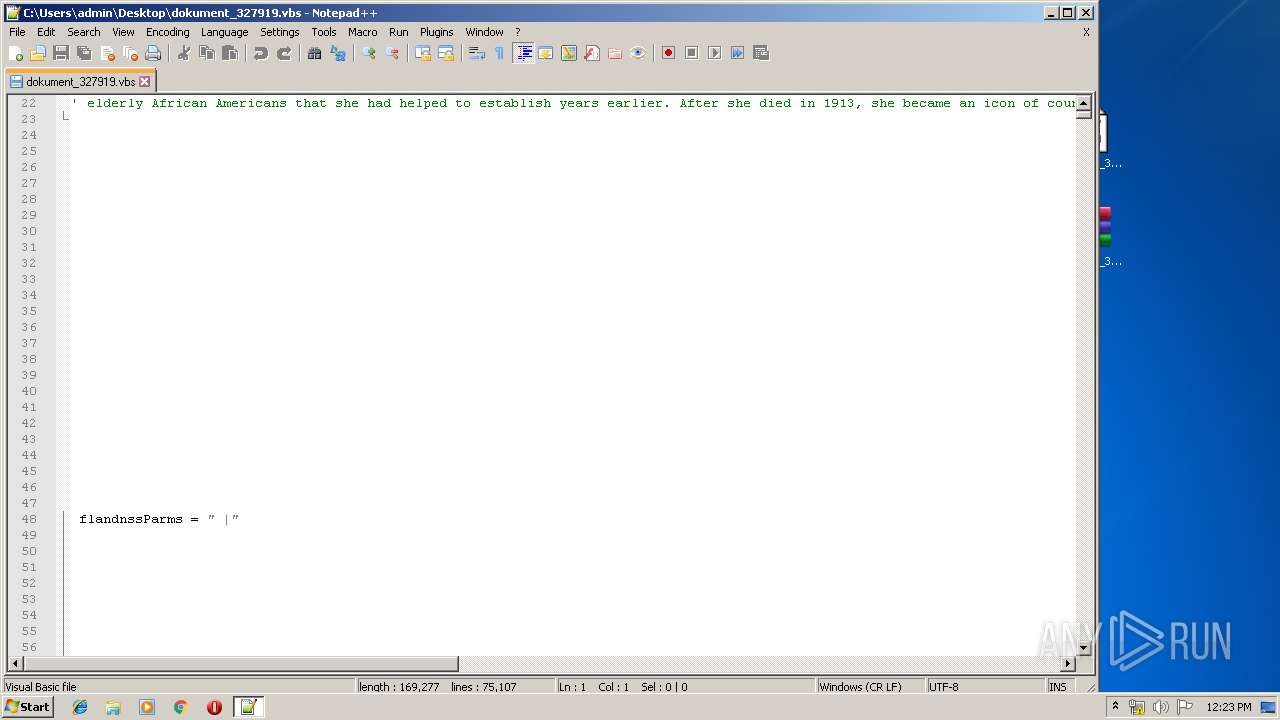
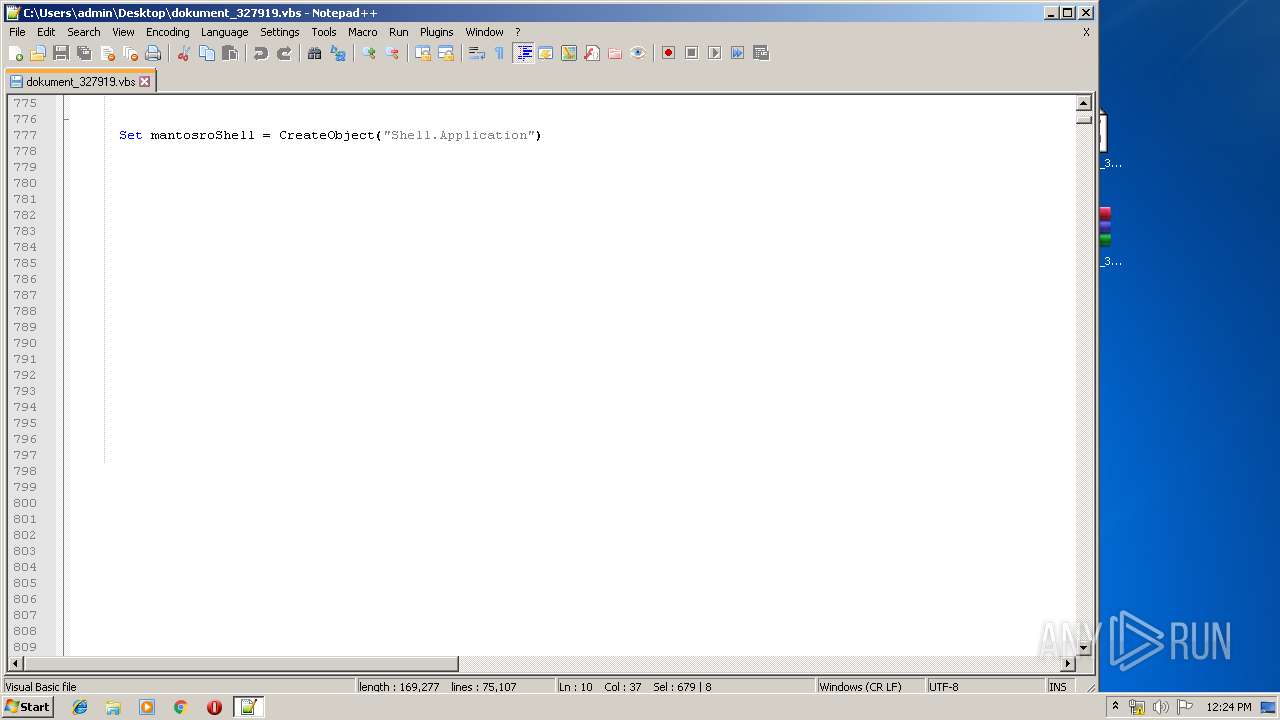
| File name: | dokument_327919.bz2.zip |
| Full analysis: | https://app.any.run/tasks/8c8bc8c0-af58-4f06-b46c-1894127ae90a |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 11:20:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 270A47640AB70943D246B65FB2757D9C |
| SHA1: | 875EB58A974FD43E82CF37FD9211E6F033FEA783 |
| SHA256: | B0AE352A5FB6C1CEC12FA36051B041296270C1C97F946DCCBD6BEB28DF314E31 |
| SSDEEP: | 96:JMTaqGlBVe954L4qhVZHwd6DJFVR54+jPxj4pq4TAj5/Y7:pAX4MqhVZHwgDJFVvtkpq4E16 |
MALICIOUS
No malicious indicators.SUSPICIOUS
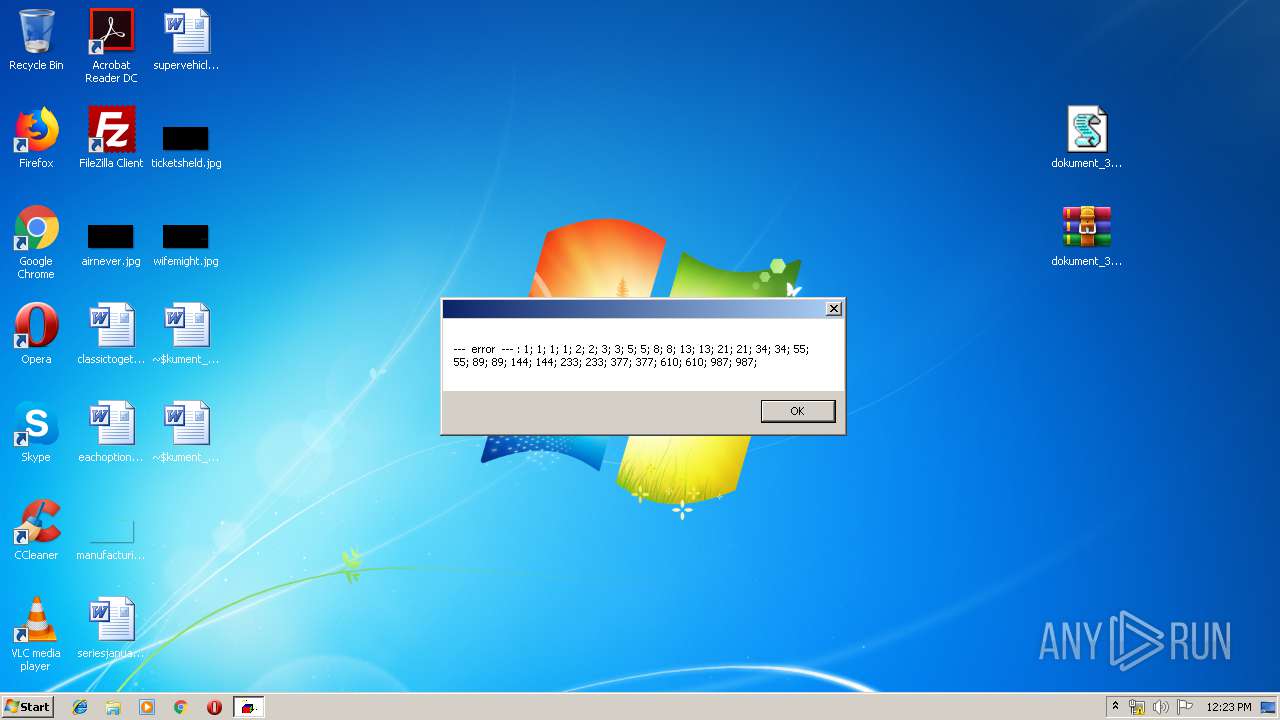
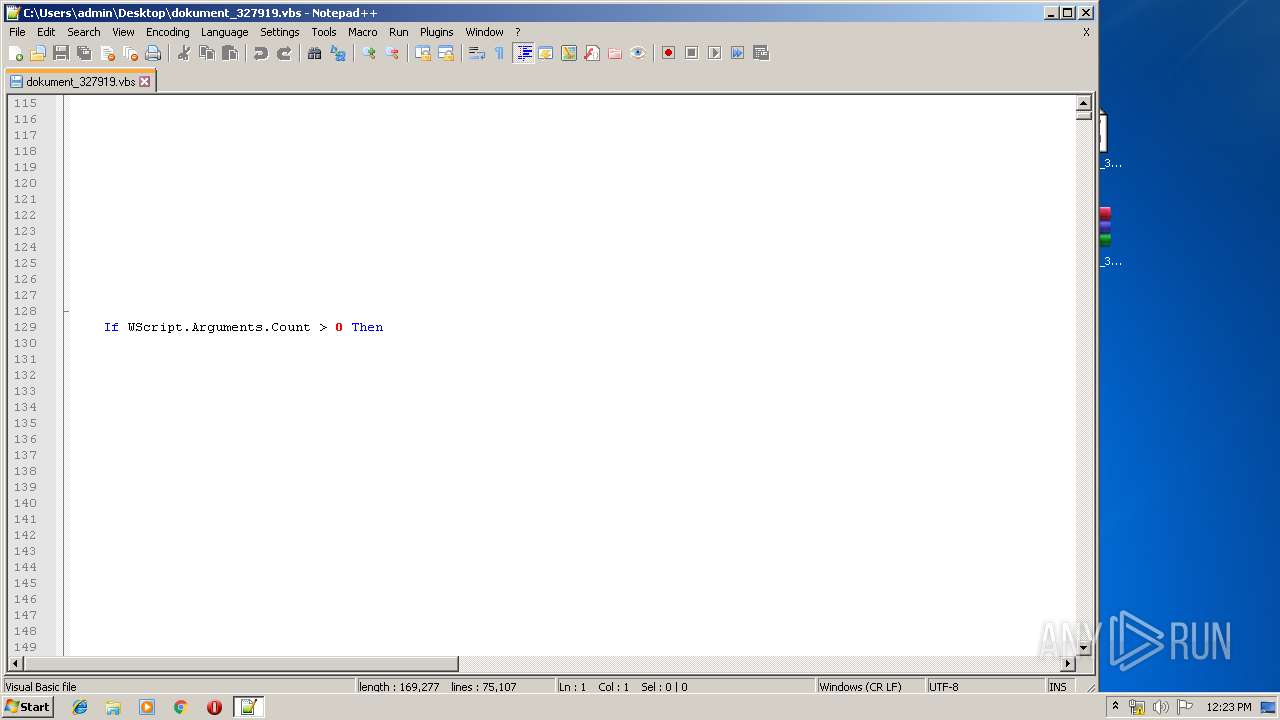
Application launched itself
- wscript.exe (PID: 1344)
- wscript.exe (PID: 3548)
- wscript.exe (PID: 3932)
- wscript.exe (PID: 2468)
- wscript.exe (PID: 2096)
- wscript.exe (PID: 2320)
- wscript.exe (PID: 3432)
- wscript.exe (PID: 3800)
- wscript.exe (PID: 1252)
- wscript.exe (PID: 2832)
- wscript.exe (PID: 2292)
- wscript.exe (PID: 2204)
Executes scripts
- wscript.exe (PID: 1344)
- WScript.exe (PID: 708)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 2076)
- wscript.exe (PID: 3548)
- wscript.exe (PID: 3932)
- wscript.exe (PID: 3028)
- wscript.exe (PID: 2204)
- wscript.exe (PID: 3368)
- wscript.exe (PID: 3676)
- wscript.exe (PID: 3432)
- wscript.exe (PID: 2320)
- wscript.exe (PID: 2468)
- wscript.exe (PID: 2096)
- wscript.exe (PID: 636)
- wscript.exe (PID: 2364)
- wscript.exe (PID: 2724)
- wscript.exe (PID: 3484)
- wscript.exe (PID: 2832)
- wscript.exe (PID: 1252)
- wscript.exe (PID: 3728)
- wscript.exe (PID: 3800)
- wscript.exe (PID: 3132)
- wscript.exe (PID: 2292)
Creates files in the user directory
- notepad++.exe (PID: 3936)
INFO
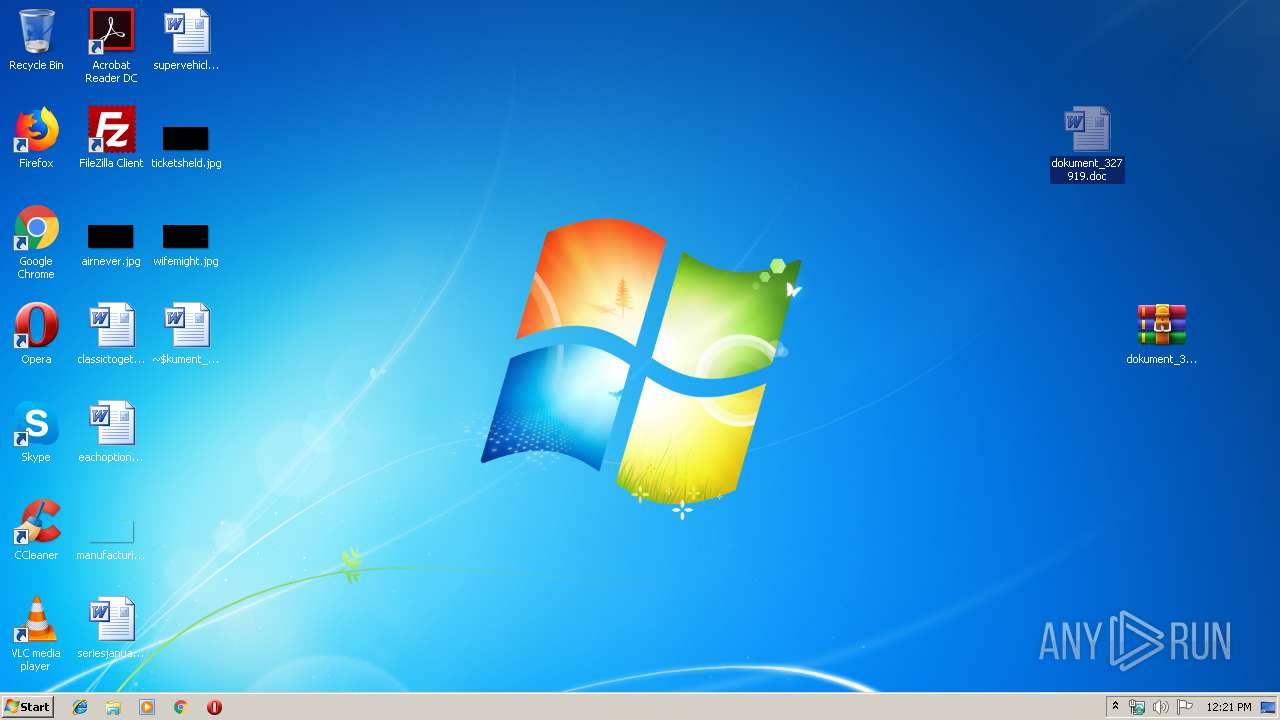
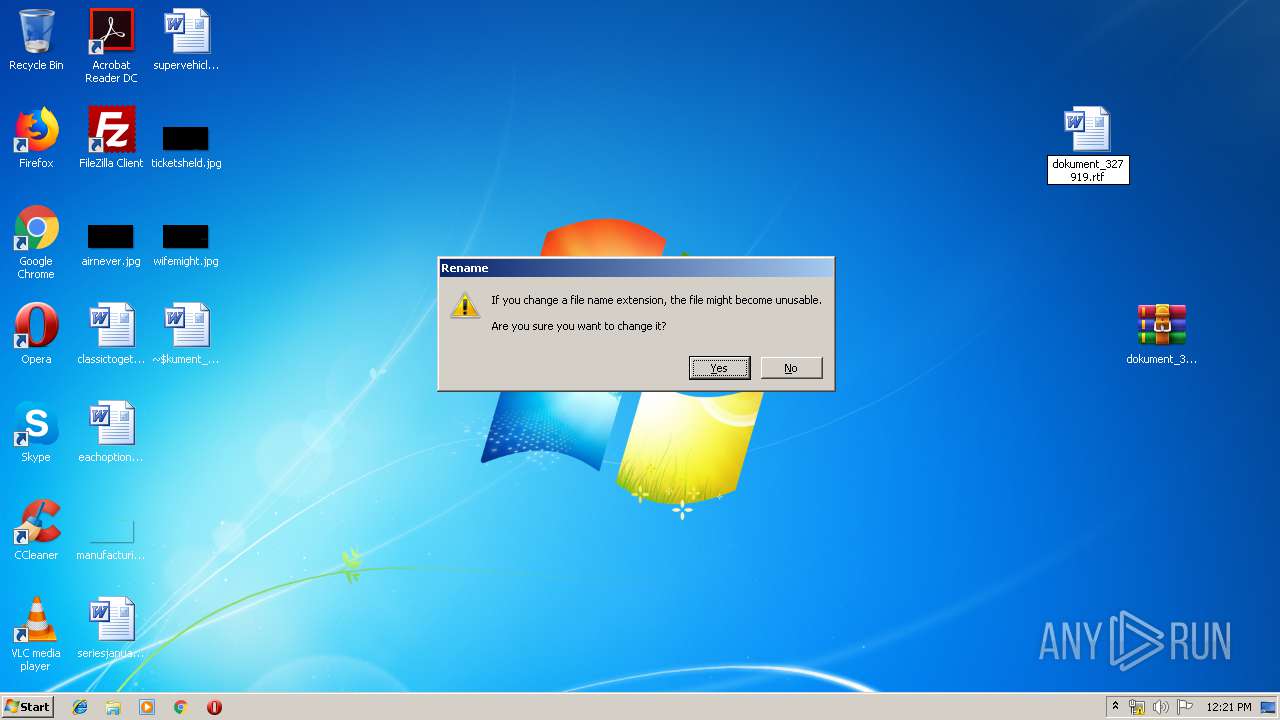
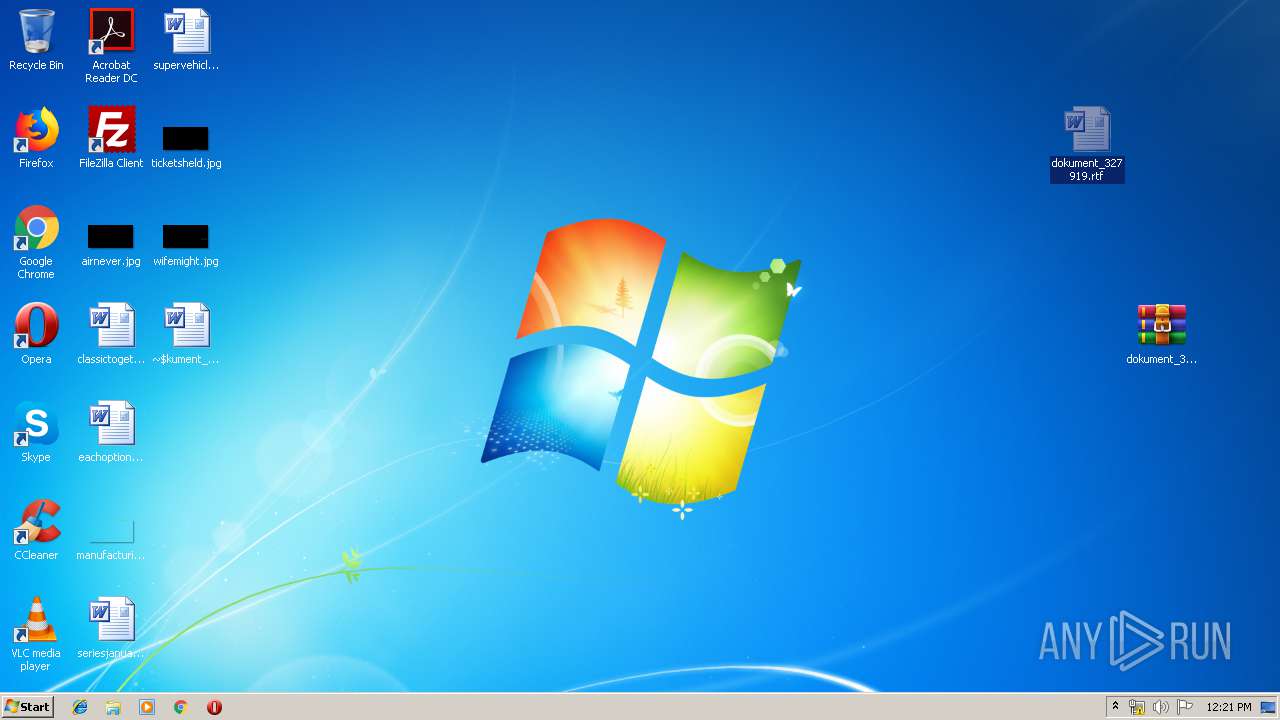
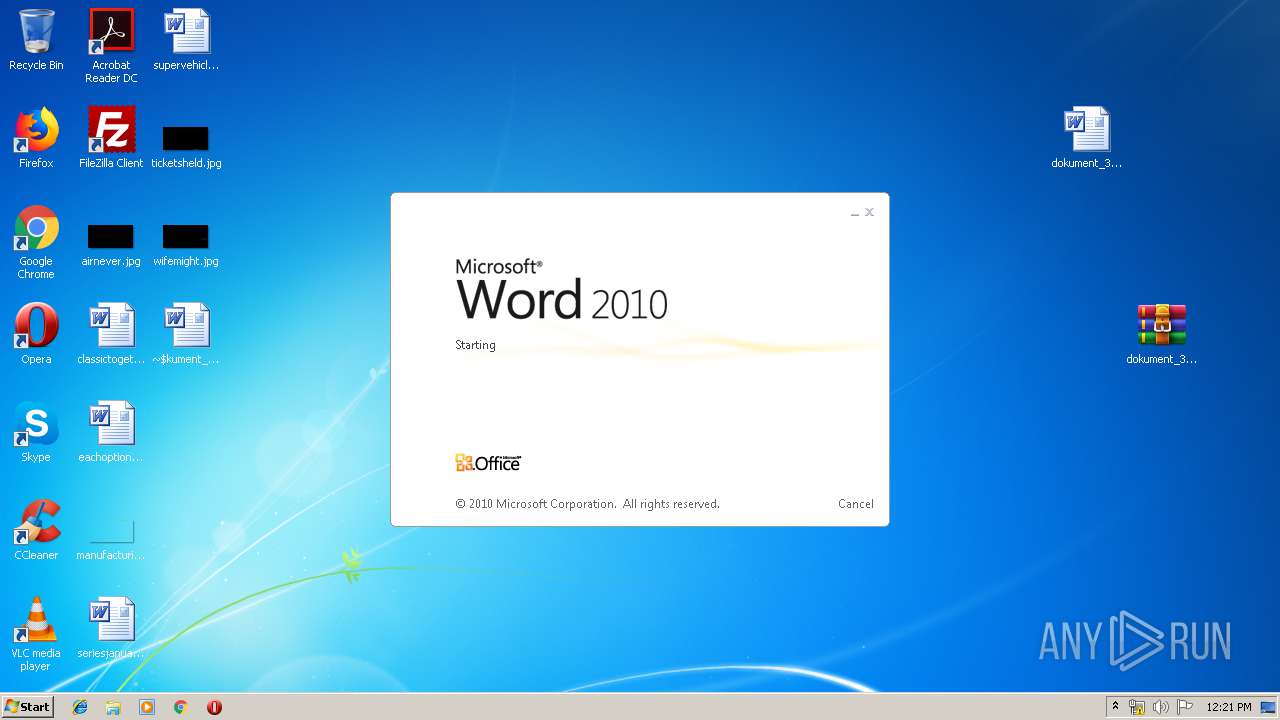
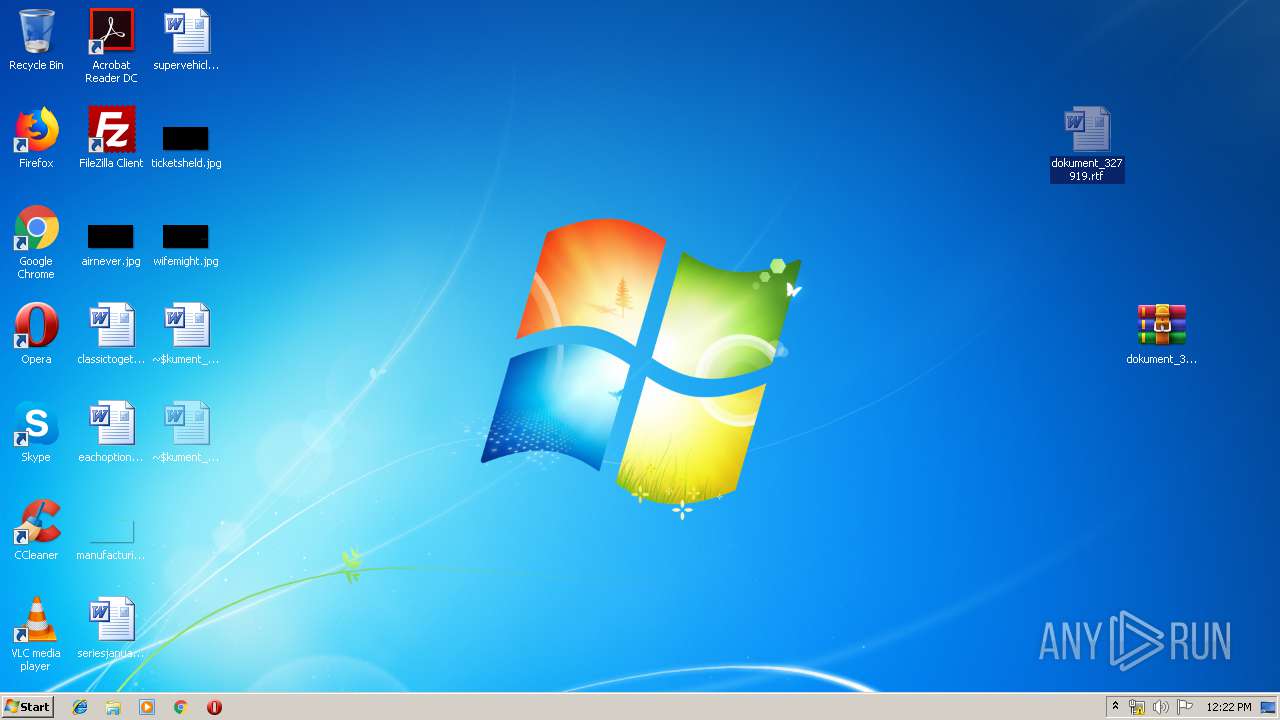
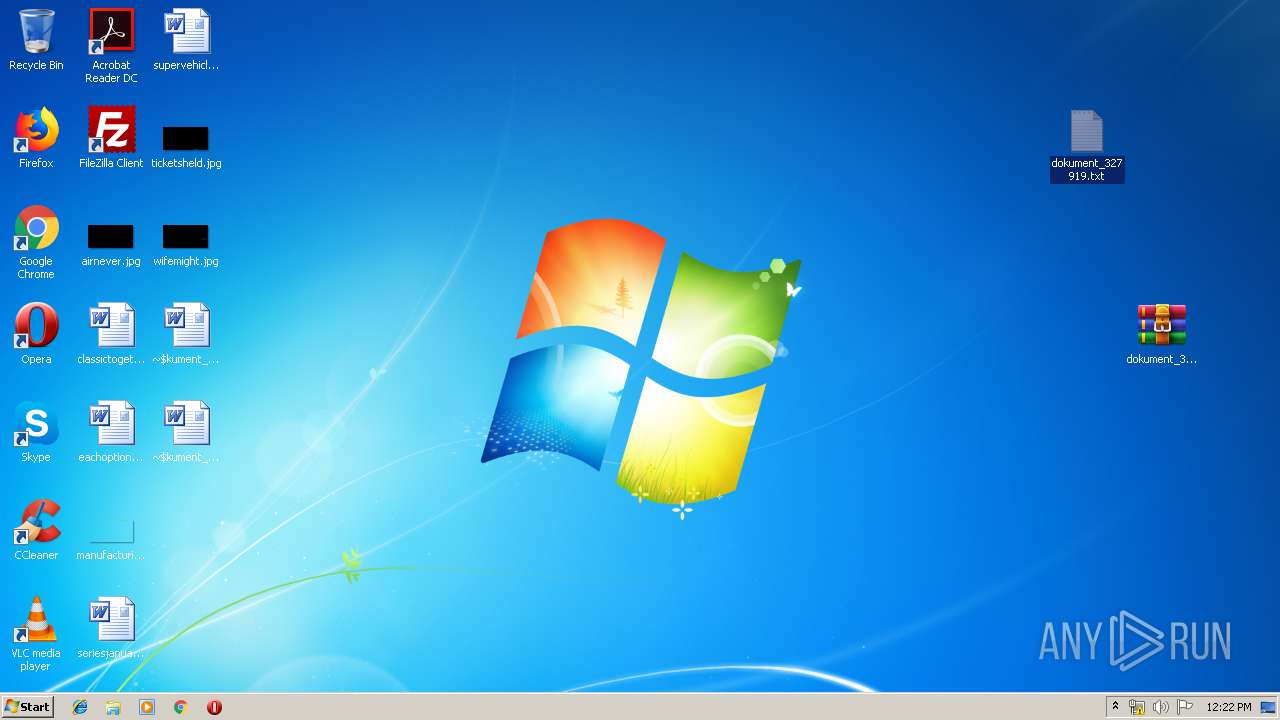
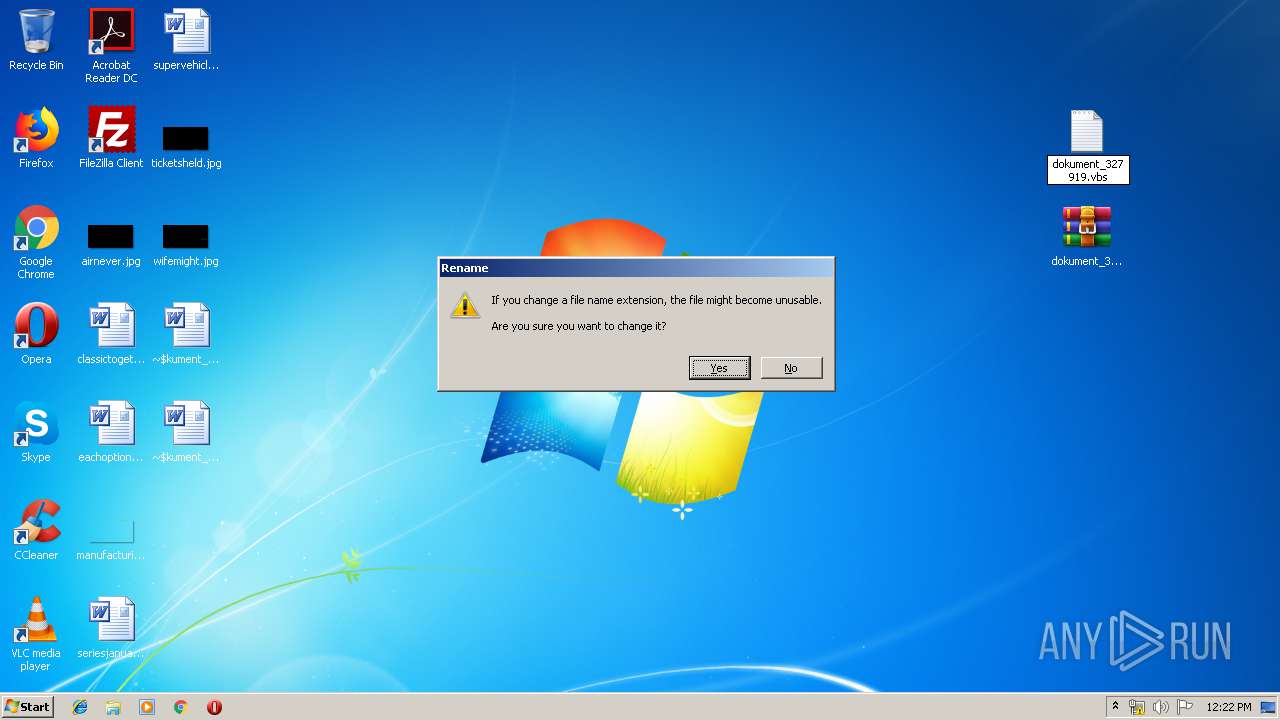
Manual execution by user
- WINWORD.EXE (PID: 3440)
- WINWORD.EXE (PID: 2308)
- WinRAR.exe (PID: 3688)
- NOTEPAD.EXE (PID: 3380)
- WScript.exe (PID: 708)
- Notepad.exe (PID: 4016)
Creates files in the user directory
- WINWORD.EXE (PID: 2308)
- WINWORD.EXE (PID: 3440)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2308)
- WINWORD.EXE (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | None |
| ZipModifyDate: | 2019:09:19 10:59:01 |
| ZipCRC: | 0xdab9868c |
| ZipCompressedSize: | 3238 |
| ZipUncompressedSize: | 3238 |
| ZipFileName: | dokument_327919.bz2 |
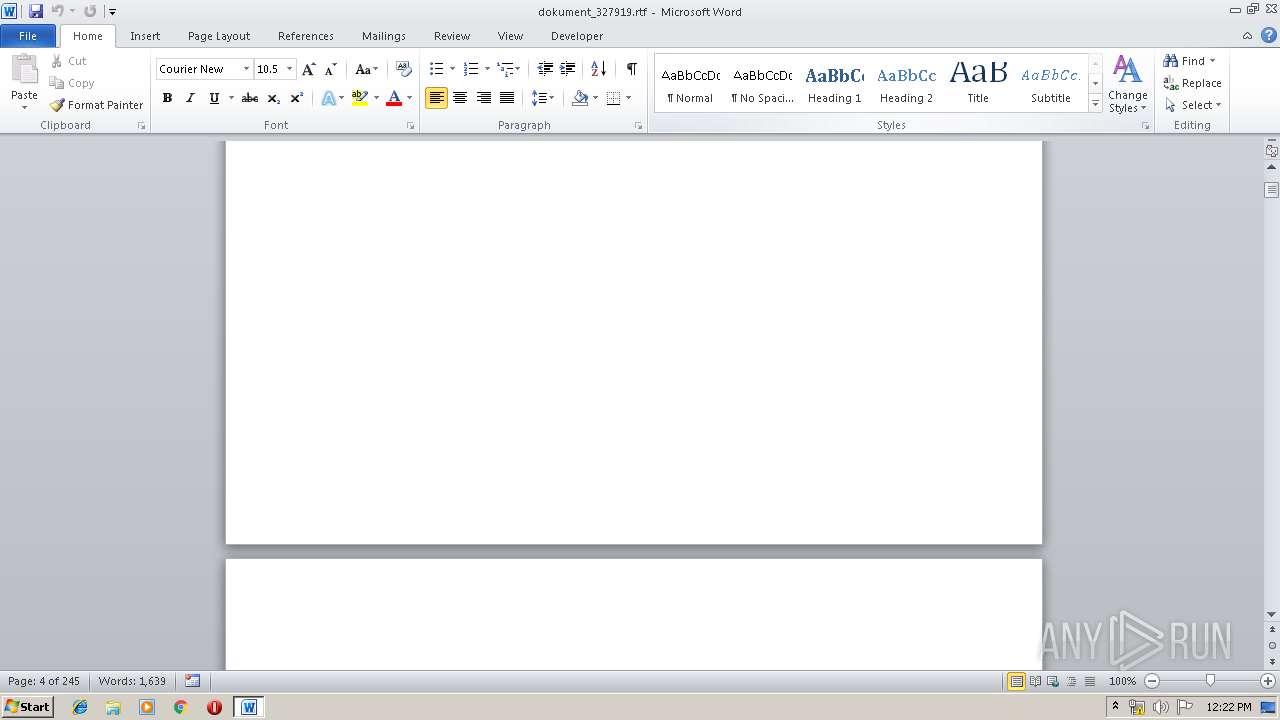
Total processes
74
Monitored processes
33
Malicious processes
17
Suspicious processes
5
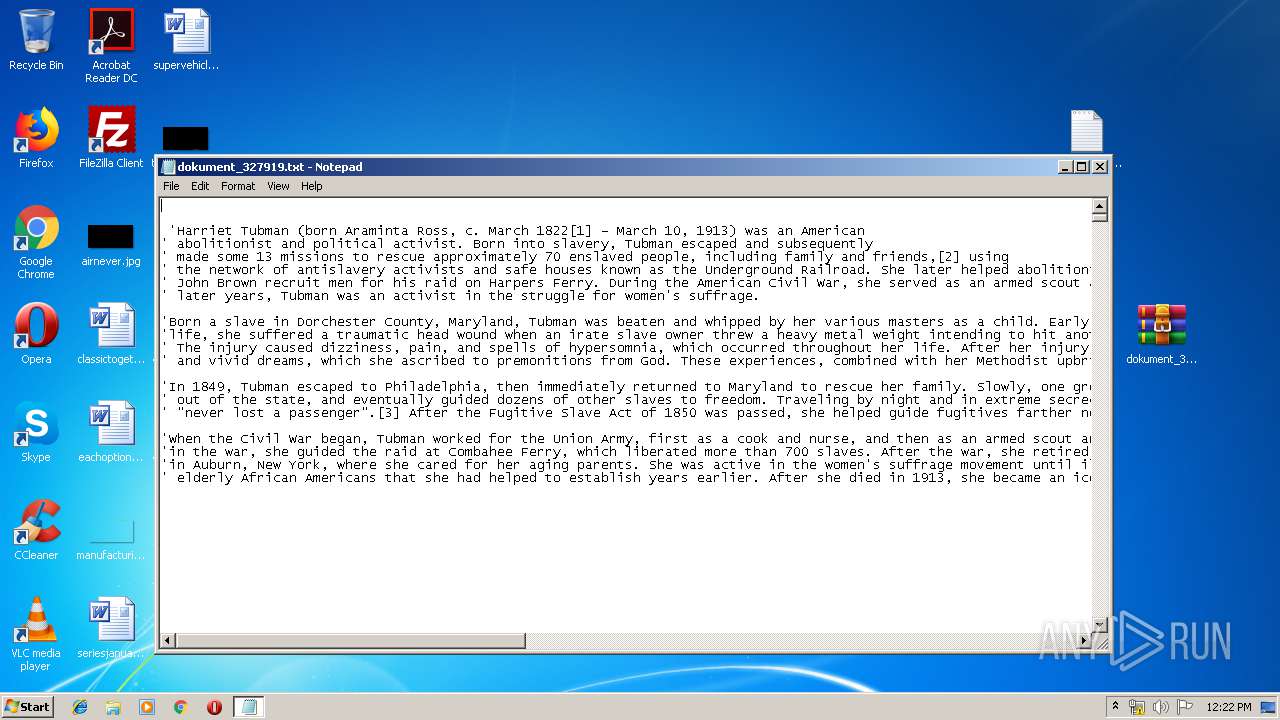
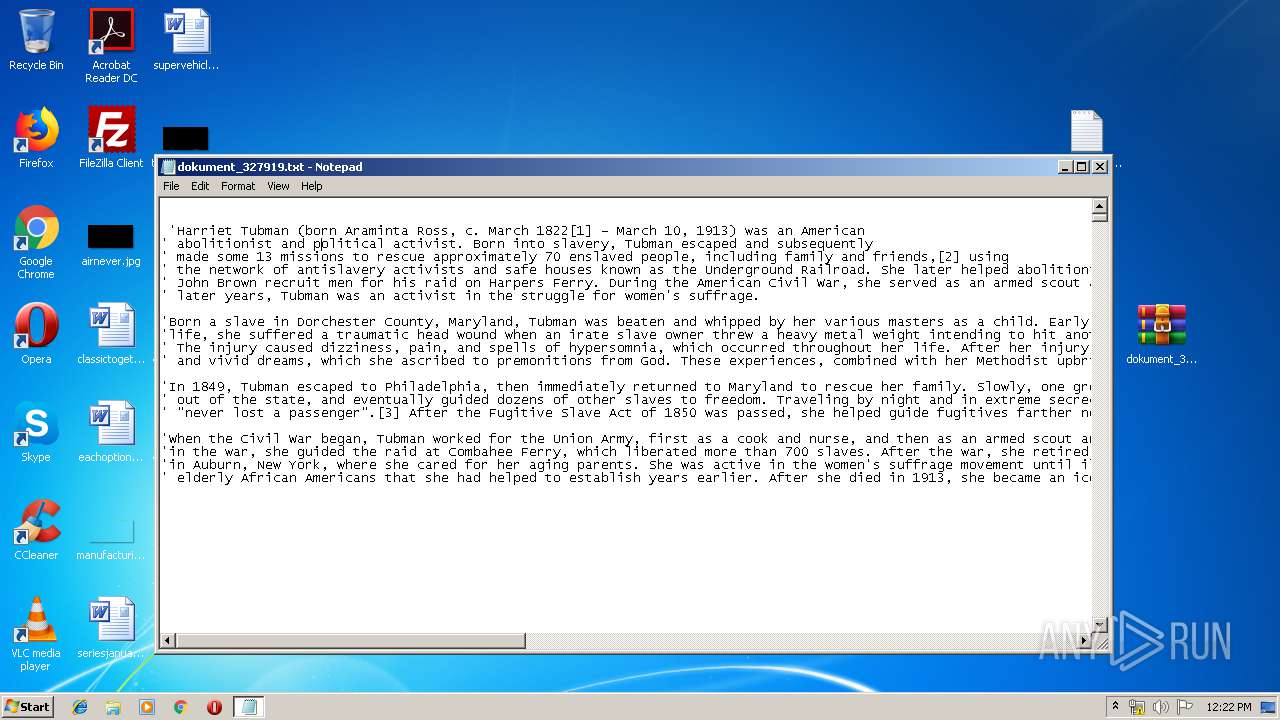
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
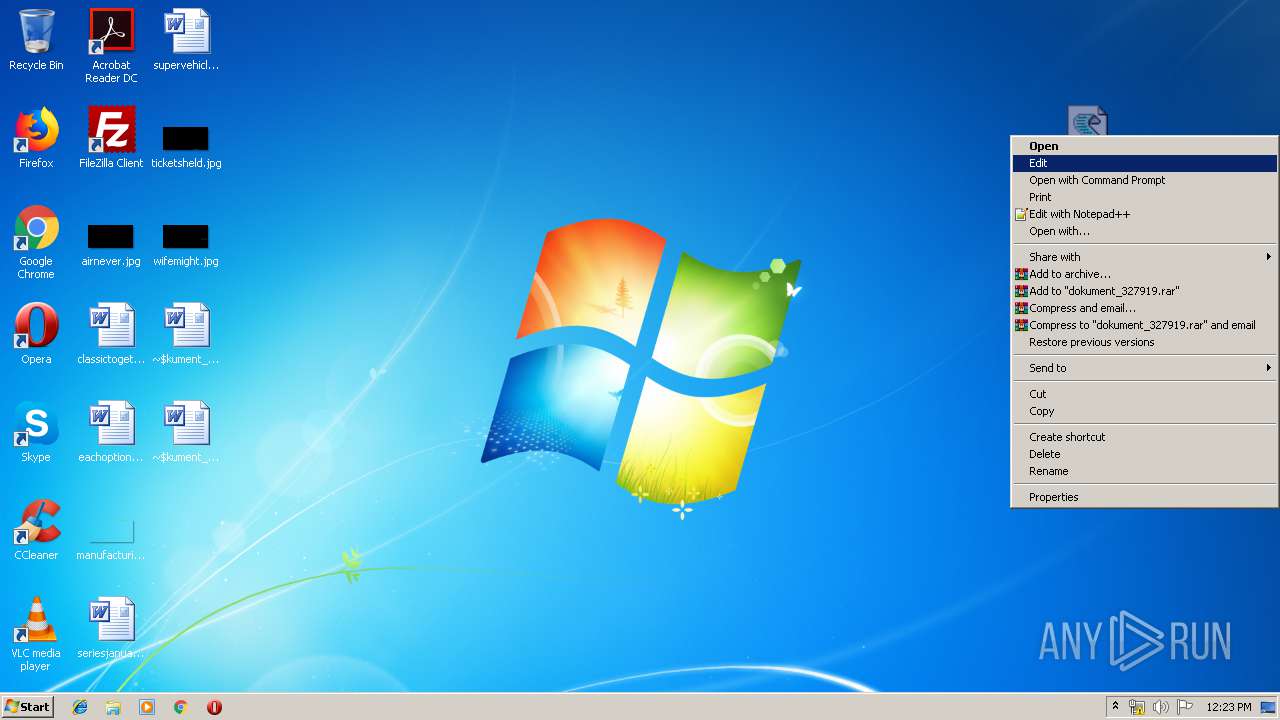
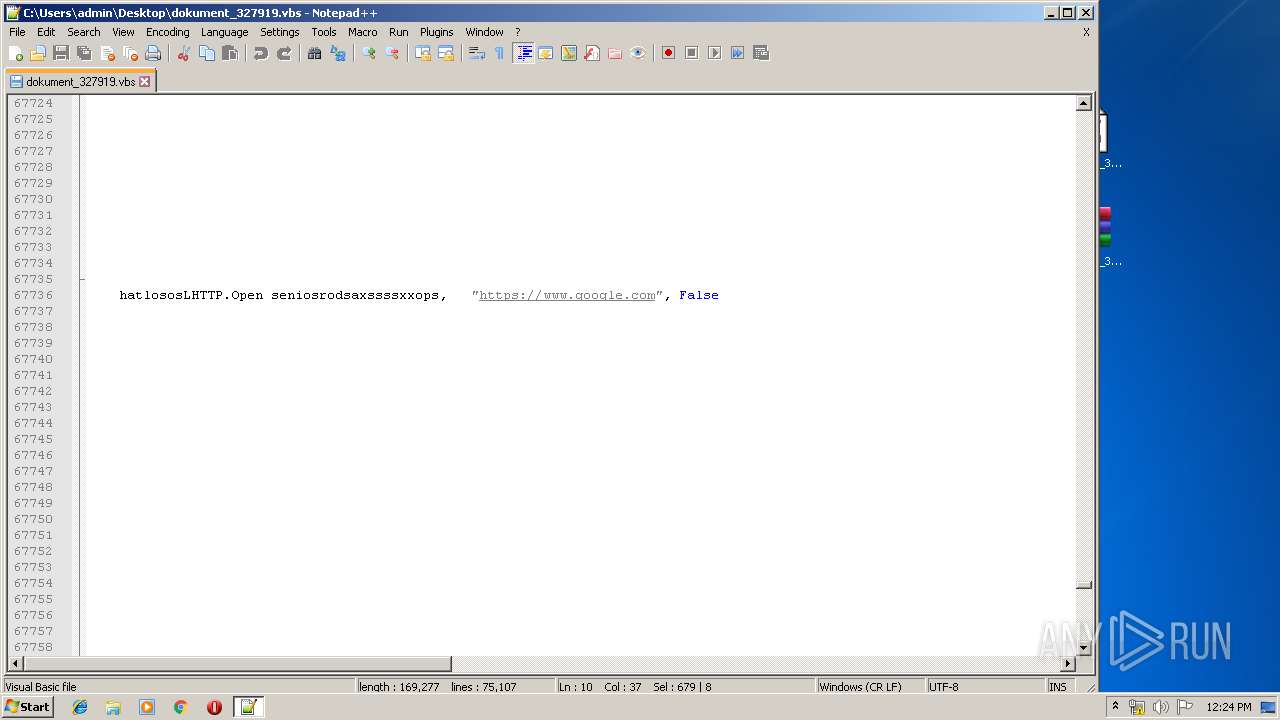
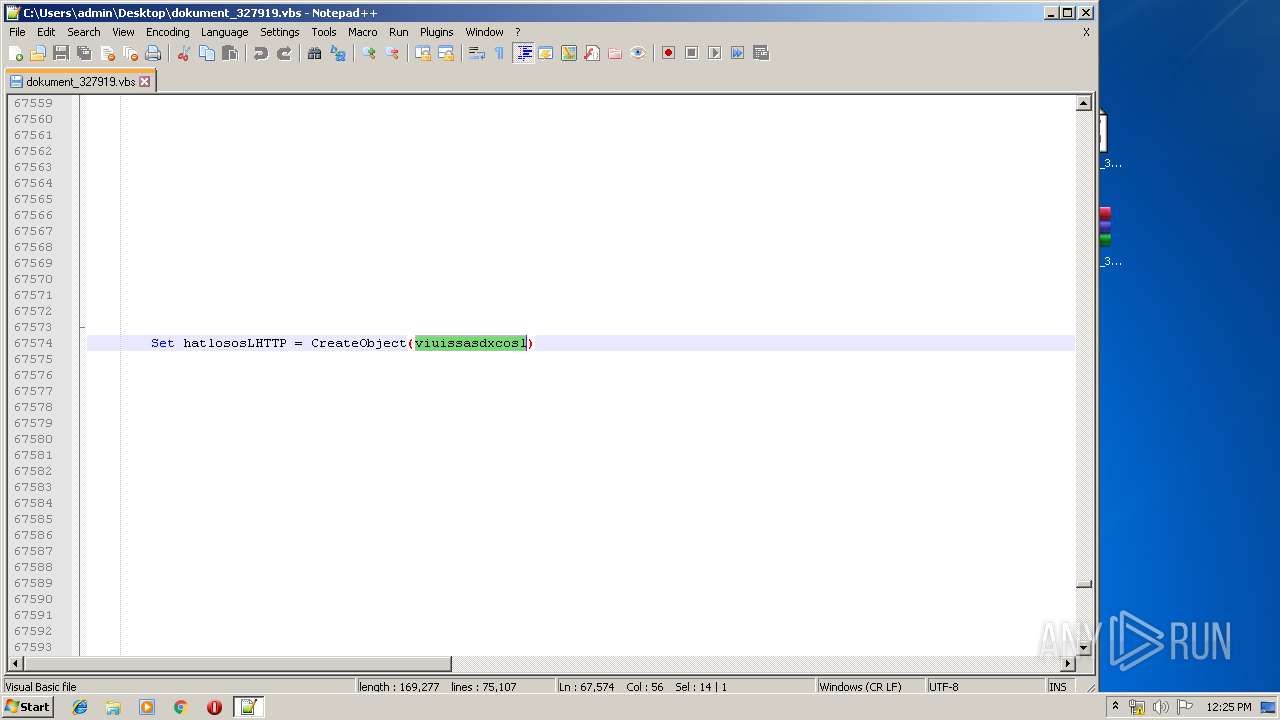
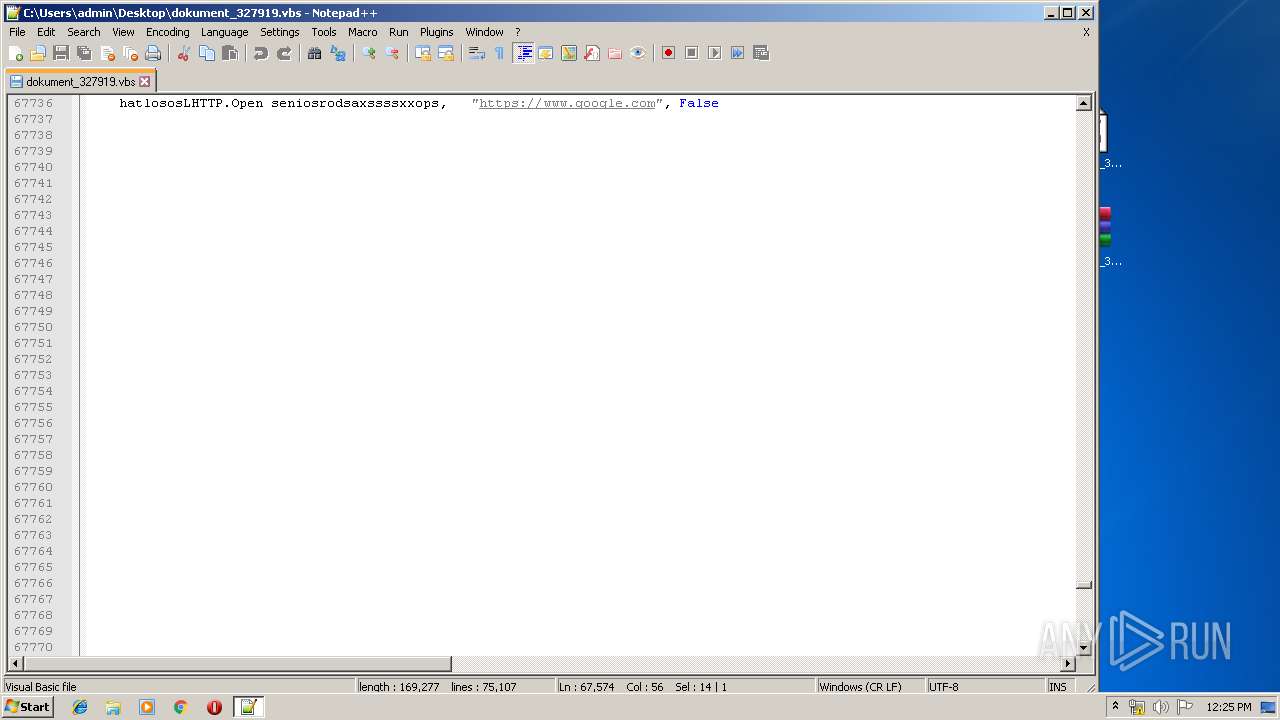
| 636 | "C:\Windows\System32\wscript.exe" C:\Users\admin\Desktop\dokument_327919.vbs | | | | | | | | | | | | | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 708 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\dokument_327919.vbs" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1252 | "C:\Windows\System32\wscript.exe" C:\Users\admin\Desktop\dokument_327919.vbs | | | | | | | | | | | | | | | | | | | | | | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1344 | "C:\Windows\System32\wscript.exe" C:\Users\admin\Desktop\dokument_327919.vbs | | C:\Windows\System32\wscript.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2076 | "C:\Windows\System32\wscript.exe" C:\Users\admin\Desktop\dokument_327919.vbs | | | | | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2096 | "C:\Windows\System32\wscript.exe" C:\Users\admin\Desktop\dokument_327919.vbs | | | | | | | | | | | | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2204 | "C:\Windows\System32\wscript.exe" C:\Users\admin\Desktop\dokument_327919.vbs | | | | | | | | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2292 | "C:\Windows\System32\wscript.exe" C:\Users\admin\Desktop\dokument_327919.vbs | | | | | | | | | | | | | | | | | | | | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\dokument_327919.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2320 | "C:\Windows\System32\wscript.exe" C:\Users\admin\Desktop\dokument_327919.vbs | | | | | | | | | | | | | | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
3 923
Read events
3 677
Write events
229
Delete events
17
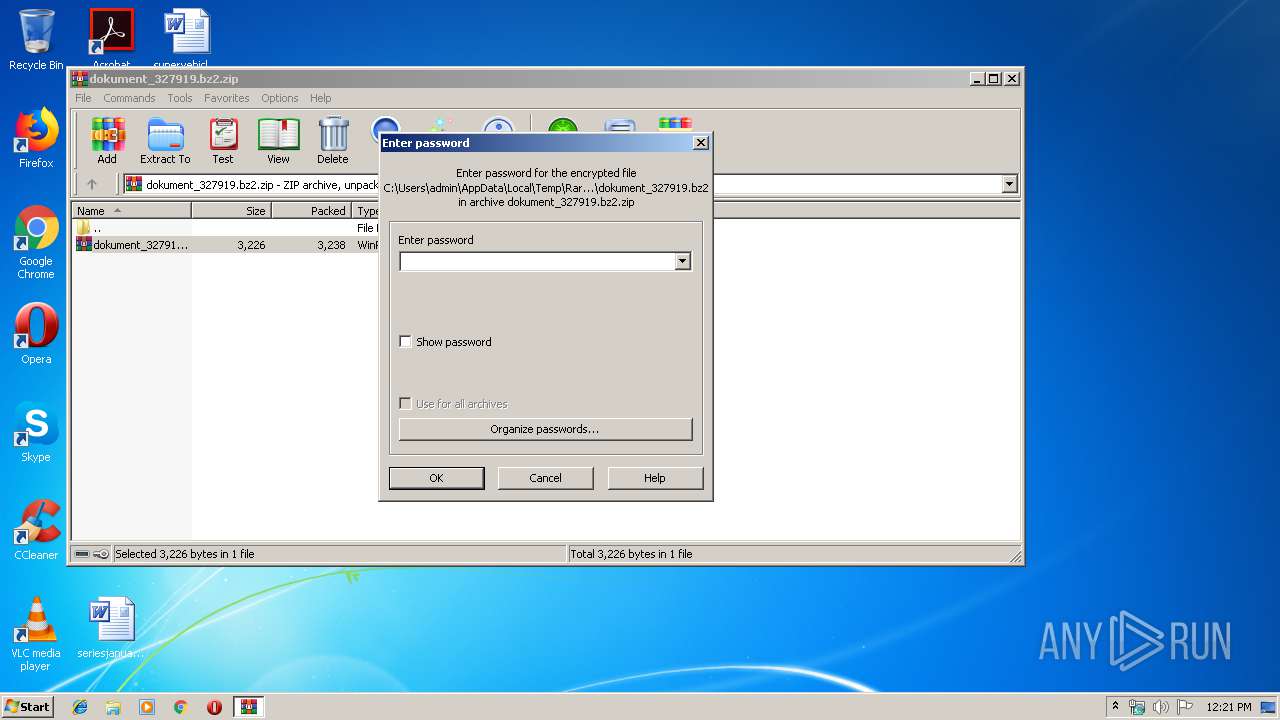
Modification events
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\dokument_327919.bz2.zip | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
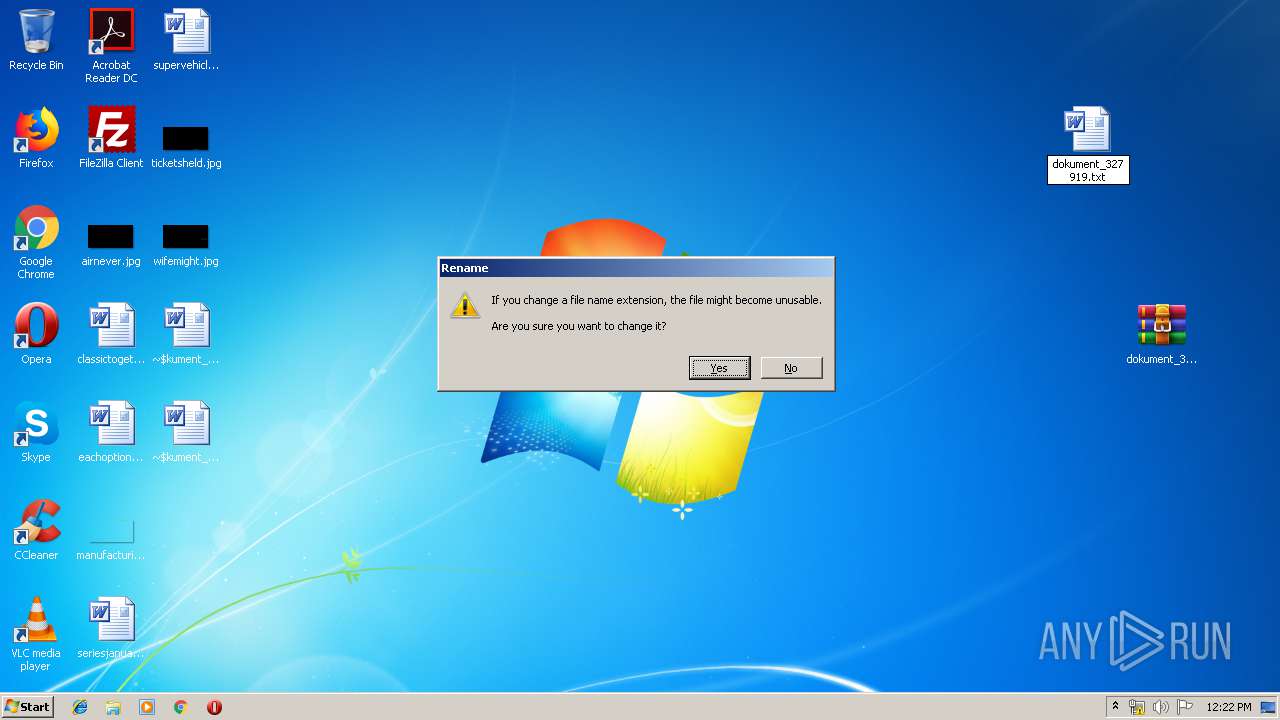
Executable files
0
Suspicious files
0
Text files
5
Unknown types
5
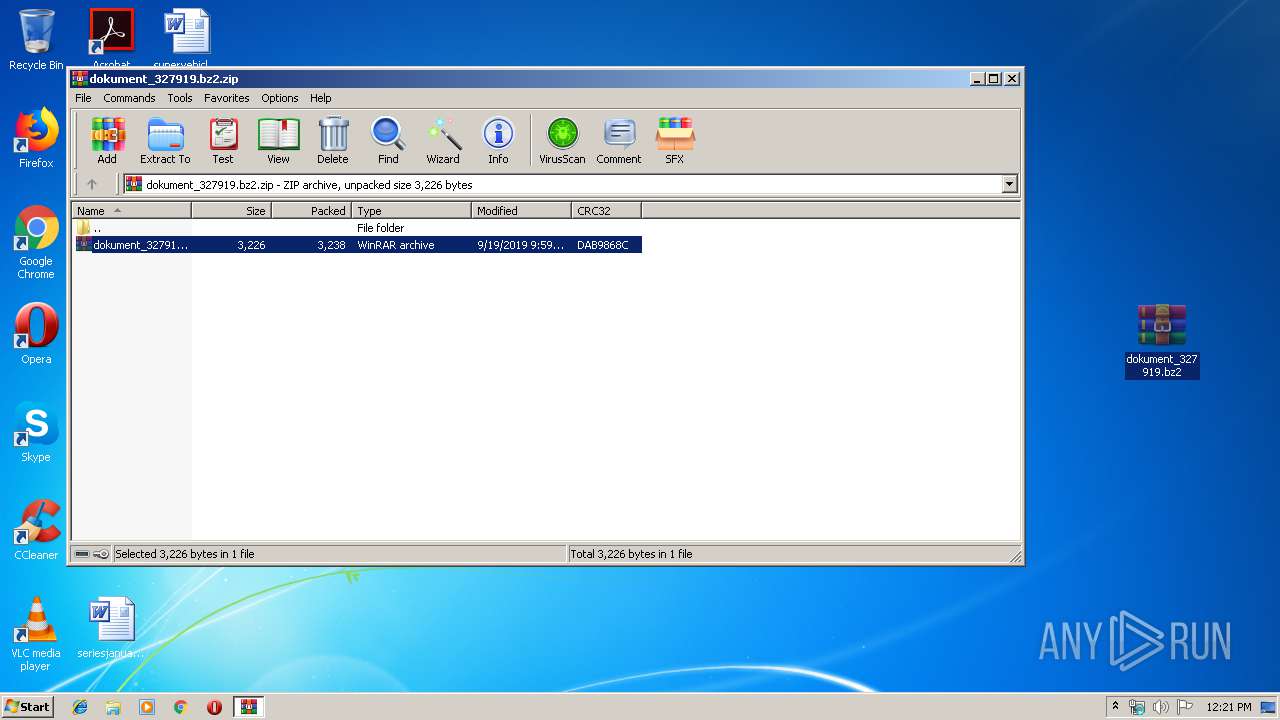
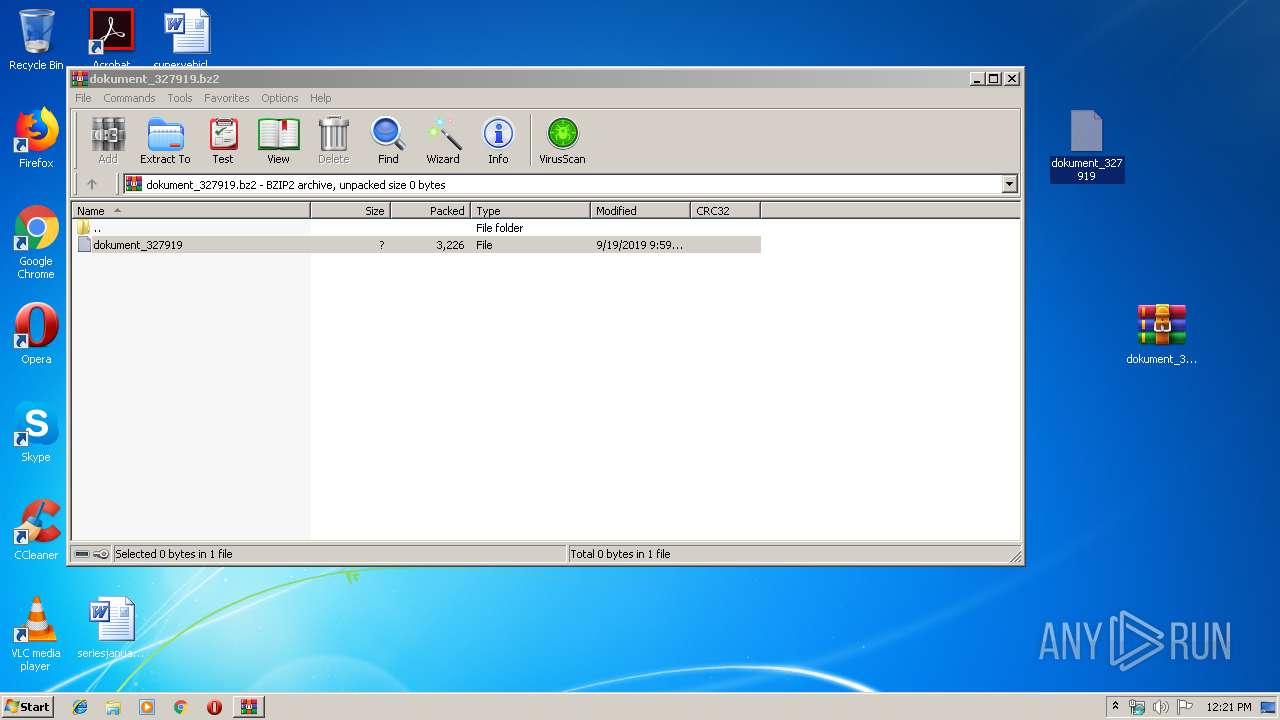
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3552.6595\dokument_327919.bz2 | — | |
MD5:— | SHA256:— | |||
| 3688 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3688.8203\dokument_327919 | — | |
MD5:— | SHA256:— | |||
| 2308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1BF4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0000.doc | — | |
MD5:— | SHA256:— | |||
| 2308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0001.doc | — | |
MD5:— | SHA256:— | |||
| 2308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{4DC6F9E8-41A0-42B2-ACB2-3CFD17FA06FC}.tmp | — | |
MD5:— | SHA256:— | |||
| 2308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{0BC1D1D0-728B-40E5-AD5C-3A5C53D83690}.tmp | — | |
MD5:— | SHA256:— | |||
| 3440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8155.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0003.doc | — | |
MD5:— | SHA256:— | |||
| 3440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0002.doc | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3304 | gup.exe | 104.31.89.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
— | — | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 194.32.78.85:443 | findepolsks.xyz | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
findepolsks.xyz |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|