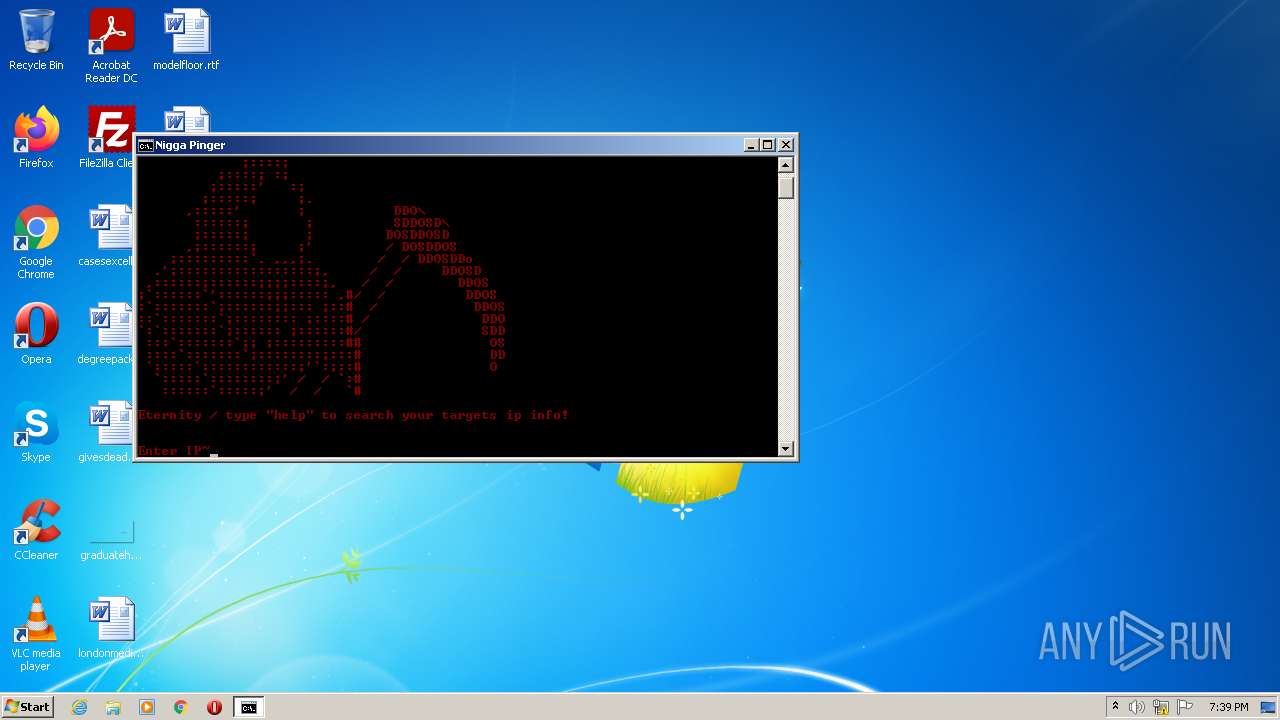
| File name: | nigga_pinger.bat |
| Full analysis: | https://app.any.run/tasks/6b6e68be-dce1-43de-9e55-f16f7ed9c6de |
| Verdict: | Malicious activity |
| Analysis date: | February 17, 2022, 19:39:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 84780022F01ACAD5533AE8480C0A66F1 |
| SHA1: | 168119E7E58EE3D8BF0D4CF8498A33007F518790 |
| SHA256: | B0AD63DC823781003EA306853820B841BE4609326641798A0D5C5E352DC39EF1 |
| SSDEEP: | 192:5f5HzNQllExv60IExv60IExv60IExv60I0Yn8iL5e0RrgYiebb/:5hHzNQDExv60IExv60IExv60IExv60IP |
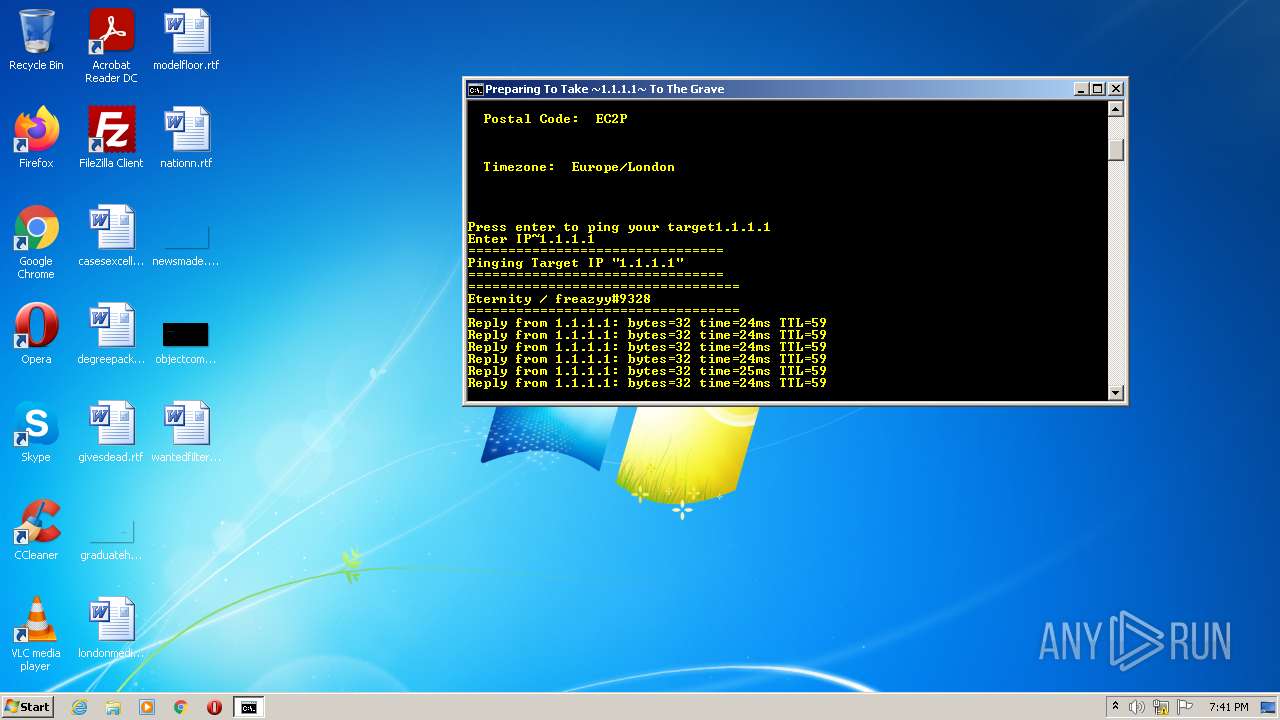
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3576)
SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 3576)
- WScript.exe (PID: 2660)
- cmd.exe (PID: 3680)
- WScript.exe (PID: 2460)
- cmd.exe (PID: 2428)
Reads the computer name
- cmd.exe (PID: 3576)
- WScript.exe (PID: 2660)
- WScript.exe (PID: 2460)
Executes scripts
- cmd.exe (PID: 3576)
Application launched itself
- cmd.exe (PID: 3576)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3576)
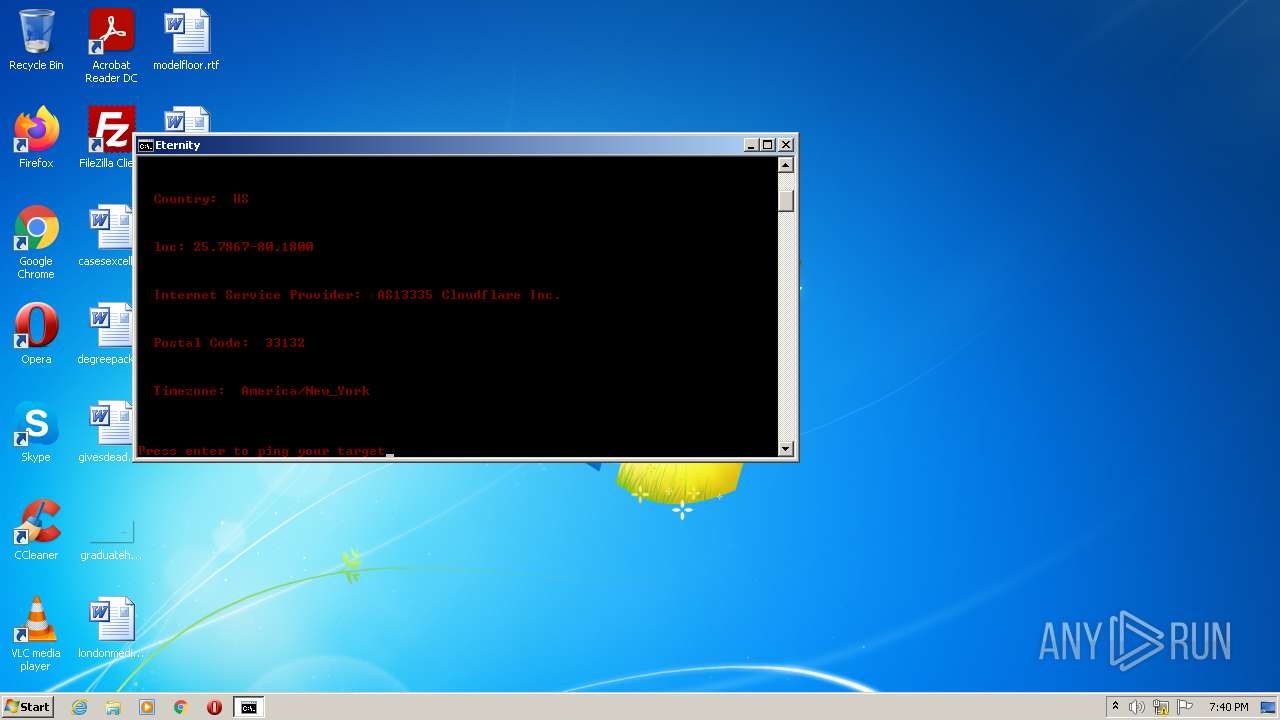
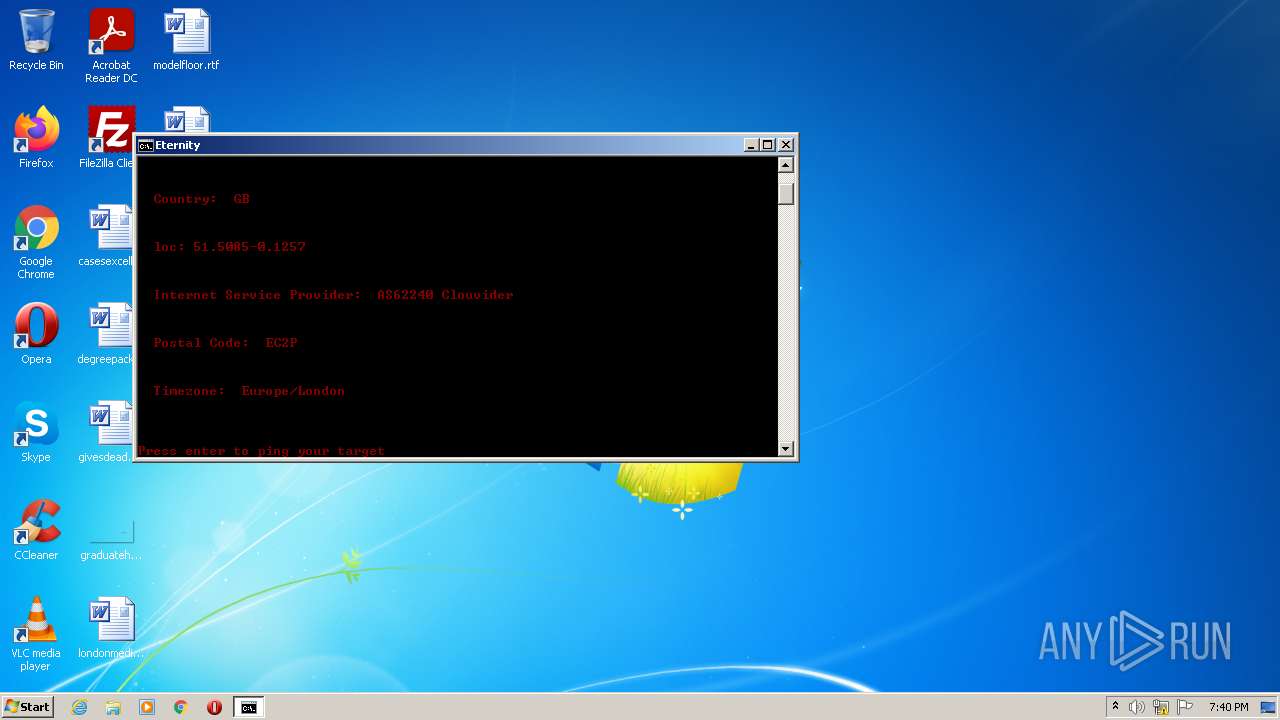
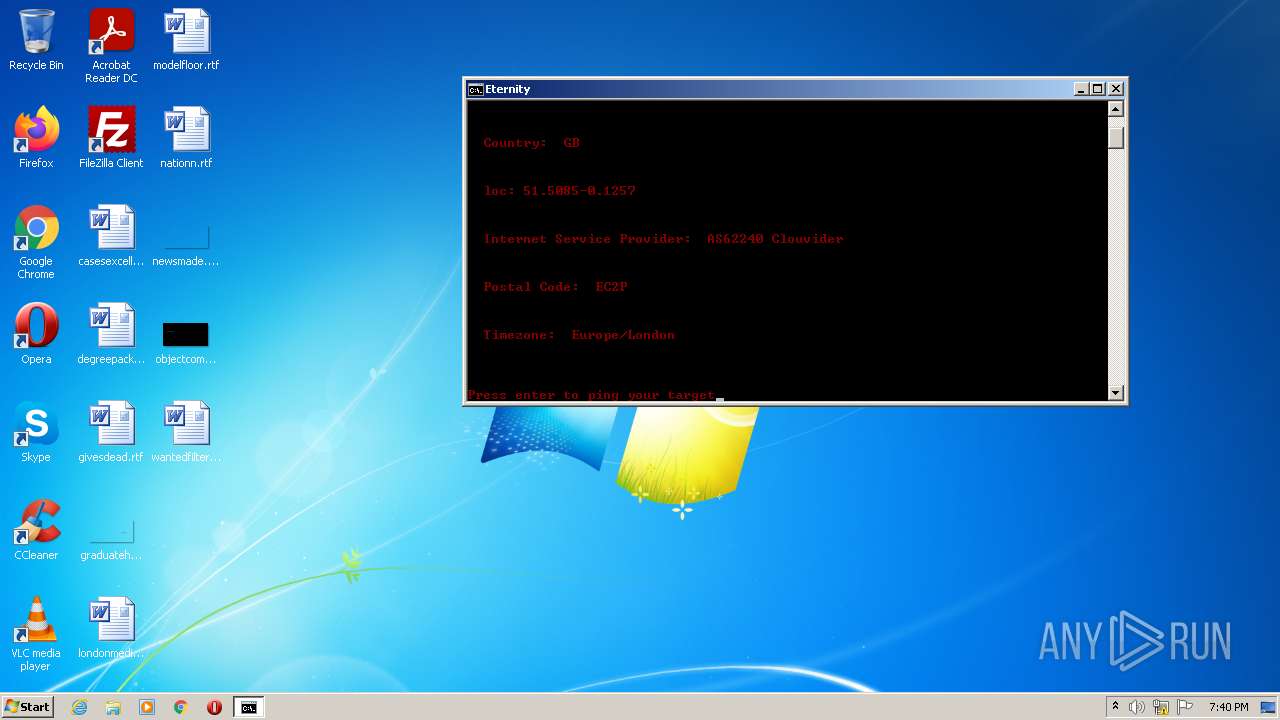
Checks for external IP
- WScript.exe (PID: 2660)
- WScript.exe (PID: 2460)
INFO
Checks supported languages
- PING.EXE (PID: 1996)
- PING.EXE (PID: 3392)
- PING.EXE (PID: 2840)
- findstr.exe (PID: 3552)
- PING.EXE (PID: 3812)
- PING.EXE (PID: 3820)
- PING.EXE (PID: 3252)
- findstr.exe (PID: 2812)
- find.exe (PID: 3396)
- PING.EXE (PID: 424)
- PING.EXE (PID: 2084)
- PING.EXE (PID: 2432)
- find.exe (PID: 456)
- find.exe (PID: 3428)
- PING.EXE (PID: 548)
- PING.EXE (PID: 3216)
- find.exe (PID: 2556)
- find.exe (PID: 2948)
- PING.EXE (PID: 832)
- find.exe (PID: 2136)
- find.exe (PID: 1464)
- opera.exe (PID: 3344)
Reads the computer name
- PING.EXE (PID: 3252)
- PING.EXE (PID: 2840)
- PING.EXE (PID: 3392)
- PING.EXE (PID: 1996)
- PING.EXE (PID: 3812)
- PING.EXE (PID: 2084)
- PING.EXE (PID: 3820)
- PING.EXE (PID: 424)
- PING.EXE (PID: 2432)
- PING.EXE (PID: 548)
- PING.EXE (PID: 3216)
- PING.EXE (PID: 832)
- opera.exe (PID: 3344)
Checks Windows Trust Settings
- WScript.exe (PID: 2660)
- WScript.exe (PID: 2460)
Creates files in the user directory
- opera.exe (PID: 3344)
Check for Java to be installed
- opera.exe (PID: 3344)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 3344)
Reads the date of Windows installation
- opera.exe (PID: 3344)
Manual execution by user
- opera.exe (PID: 3344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
27
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | PING -n 1 1.1.1.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 456 | FIND "TTL=" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 548 | PING -n 1 1.1.1.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 832 | PING -n 1 1.1.1.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1464 | FIND "TTL=" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1996 | ping 127.0.0.1 -n 2 -w 1000 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | PING -n 1 1.1.1.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | FIND "TTL=" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2428 | C:\Windows\system32\cmd.exe /c findstr /i "," C:\Users\admin\AppData\Local\Temp\response.txt | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2432 | PING -n 1 1.1.1.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 739
Read events
3 665
Write events
74
Delete events
0
Modification events
| (PID) Process: | (3576) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3576) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3576) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3576) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3344) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (3344) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
25
Text files
17
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3344 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr8026.tmp | xml | |
MD5:— | SHA256:— | |||
| 2660 | WScript.exe | C:\Users\admin\AppData\Local\Temp\response.txt | binary | |
MD5:— | SHA256:— | |||
| 3344 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr7FC7.tmp | text | |
MD5:— | SHA256:— | |||
| 3344 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 2460 | WScript.exe | C:\Users\admin\AppData\Local\Temp\response.txt | binary | |
MD5:— | SHA256:— | |||
| 3344 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 3344 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 3344 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00003.tmp | xml | |
MD5:— | SHA256:— | |||
| 3344 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5AJQRQVCB0HCEKARBLZZ.temp | binary | |
MD5:— | SHA256:— | |||
| 3576 | cmd.exe | C:\Users\admin\AppData\Local\Temp\webclient.vbs | text | |
MD5:EBEDAF6EAADCA2BC57E0D4CD2D8EAB97 | SHA256:4CC8A50CE5210E21BE29CAB3A7F8CBE41F2A36E34EFC7876B7C0D12A2EDC3BB6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
4
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3344 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
2660 | WScript.exe | GET | 200 | 34.117.59.81:80 | http://ipinfo.io/1.1.1.1/json | US | binary | 300 b | shared |
2460 | WScript.exe | GET | 200 | 34.117.59.81:80 | http://ipinfo.io/json | US | binary | 244 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3344 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3344 | opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2660 | WScript.exe | 34.117.59.81:80 | ipinfo.io | — | US | whitelisted |
— | — | 34.117.59.81:80 | ipinfo.io | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ipinfo.io |
| shared |
certs.opera.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2660 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ipinfo.io |
2460 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ipinfo.io |