| File name: | PC_Cleaner.exe |
| Full analysis: | https://app.any.run/tasks/09481824-6d45-4990-ab28-8b99df73db30 |
| Verdict: | Malicious activity |
| Analysis date: | February 08, 2022, 09:58:49 |
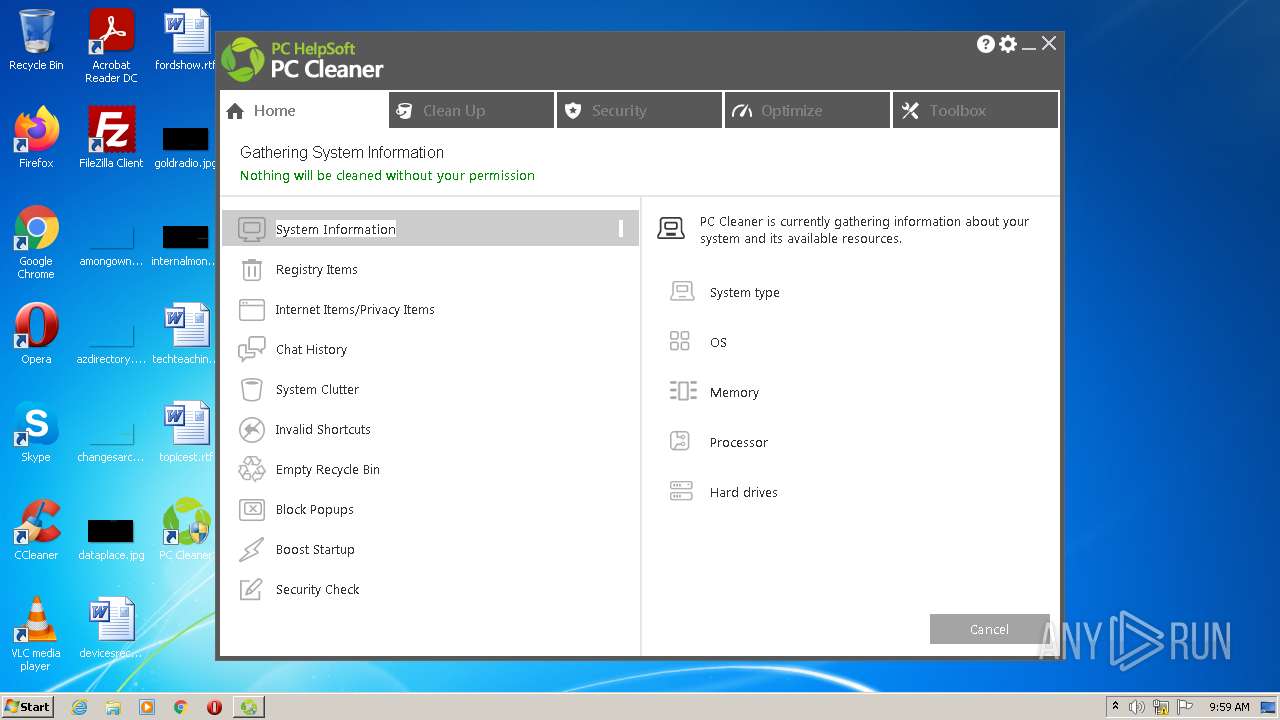
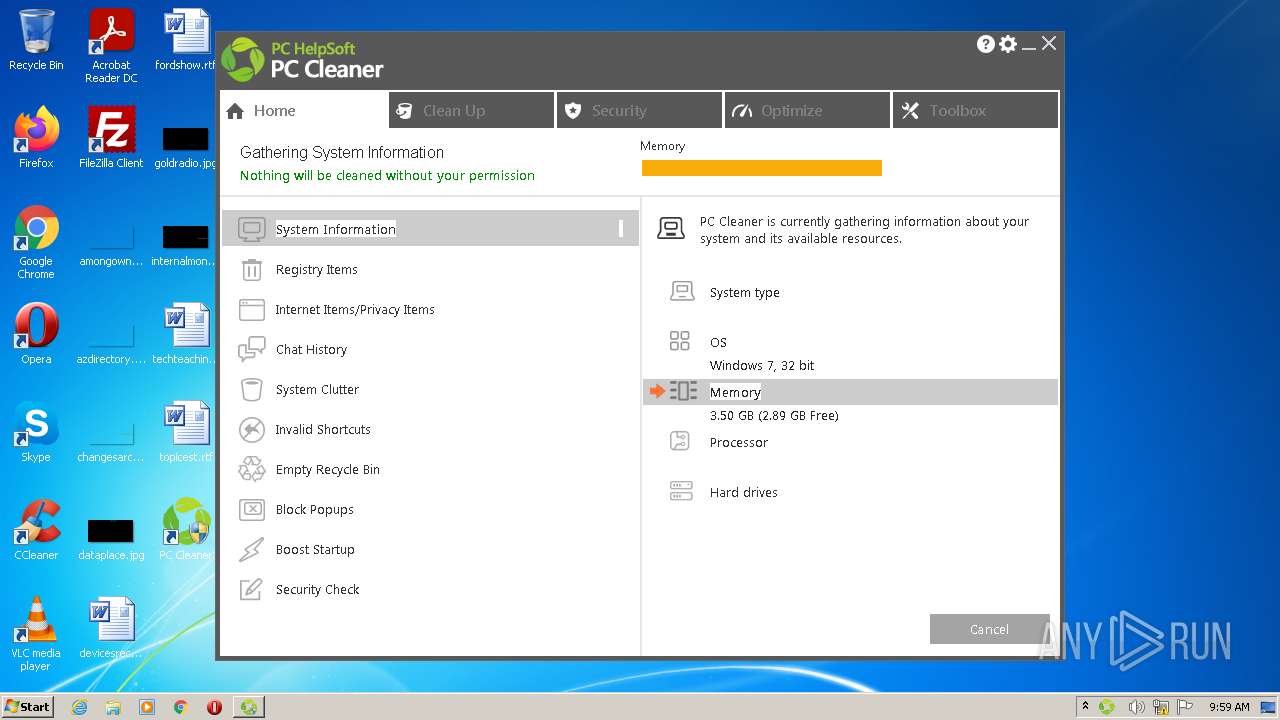
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1BA29138F76C325FC752D2FA70A2AC67 |
| SHA1: | 5FCEDCA91683CF4B2FACE7A5AACCEECA2F1FDB21 |
| SHA256: | B0A53C64323C54E12D914C5EDB290FFD6F27B603A9C1B6224904F61A2AF1A60A |
| SSDEEP: | 98304:dSijgXHgx126qSRpOpqxxVnUjGG8BsEBr92JEXAhJkXMWtbtErCS/TRR46jXilLl:Rgb0wQnUqDBHnX/XPbtErC6TR2ASlB |
MALICIOUS
Drops executable file immediately after starts
- PC_Cleaner.exe (PID: 3776)
- PC_Cleaner.exe (PID: 2916)
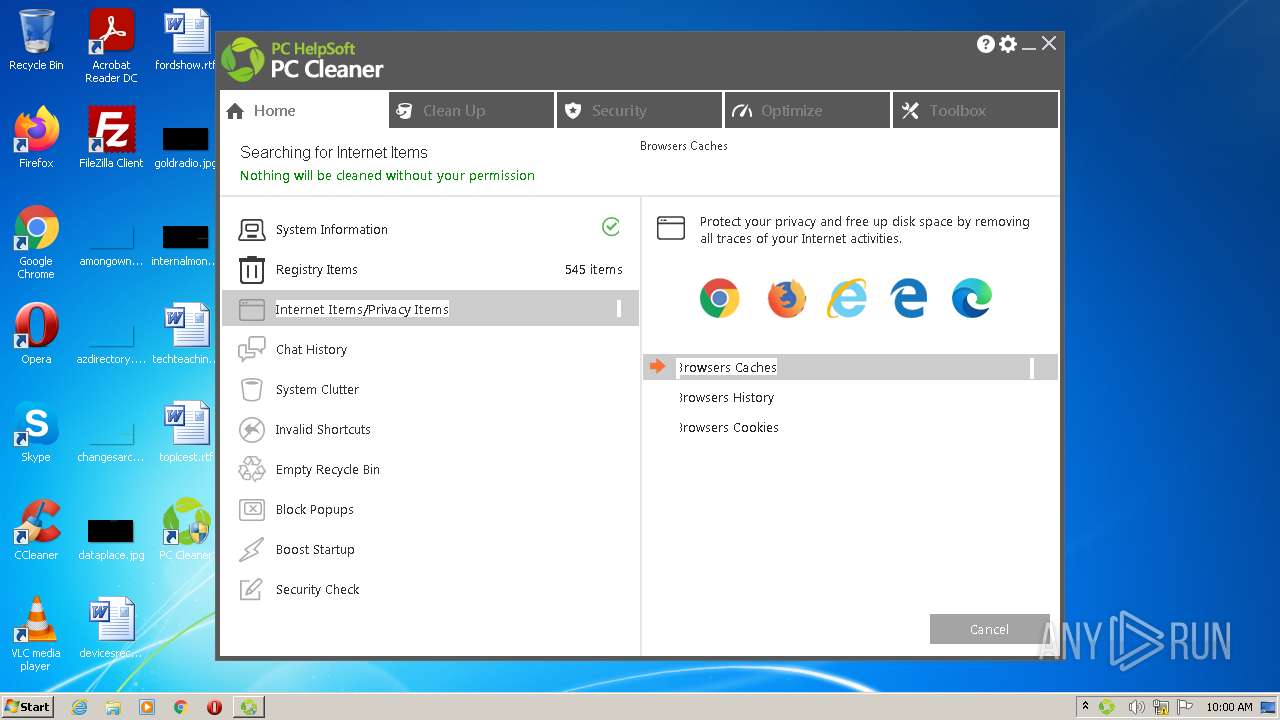
Steals credentials from Web Browsers
- PCCNotifications.exe (PID: 3240)
- PCCleaner.exe (PID: 3320)
Actions looks like stealing of personal data
- PCCNotifications.exe (PID: 3240)
- PCCleaner.exe (PID: 3320)
Application was dropped or rewritten from another process
- PCCleaner.exe (PID: 3320)
- PCCNotifications.exe (PID: 3240)
Loads the Task Scheduler COM API
- PCCleaner.exe (PID: 3320)
Changes settings of System certificates
- PCCleaner.exe (PID: 3320)
SUSPICIOUS
Checks supported languages
- PC_Cleaner.exe (PID: 3776)
- PC_Cleaner.exe (PID: 2916)
- PC_Cleaner.tmp (PID: 2056)
- PC_Cleaner.tmp (PID: 2112)
- PCCNotifications.exe (PID: 3240)
- PCCleaner.exe (PID: 3320)
Reads the computer name
- PC_Cleaner.tmp (PID: 2112)
- PC_Cleaner.tmp (PID: 2056)
- PCCleaner.exe (PID: 3320)
- PCCNotifications.exe (PID: 3240)
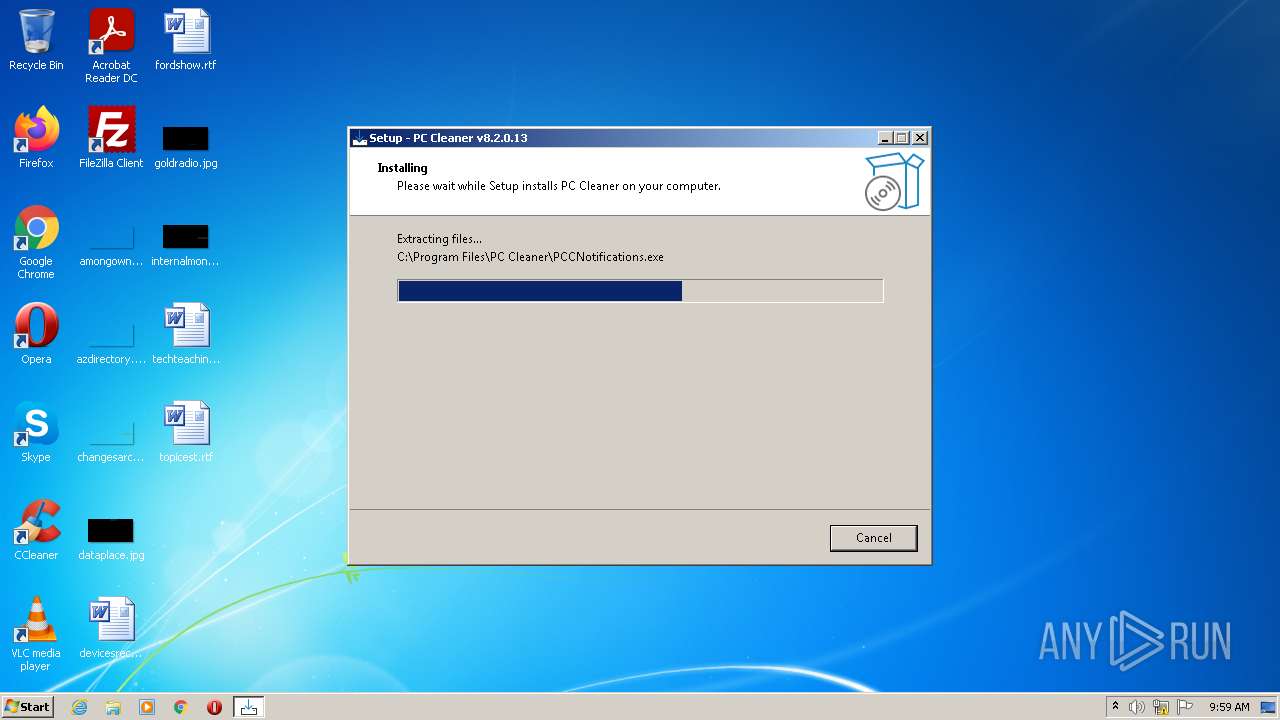
Executable content was dropped or overwritten
- PC_Cleaner.exe (PID: 3776)
- PC_Cleaner.exe (PID: 2916)
- PC_Cleaner.tmp (PID: 2056)
Reads the Windows organization settings
- PC_Cleaner.tmp (PID: 2056)
Reads Windows owner or organization settings
- PC_Cleaner.tmp (PID: 2056)
Drops a file with a compile date too recent
- PC_Cleaner.tmp (PID: 2056)
Drops a file that was compiled in debug mode
- PC_Cleaner.tmp (PID: 2056)
Creates a directory in Program Files
- PC_Cleaner.tmp (PID: 2056)
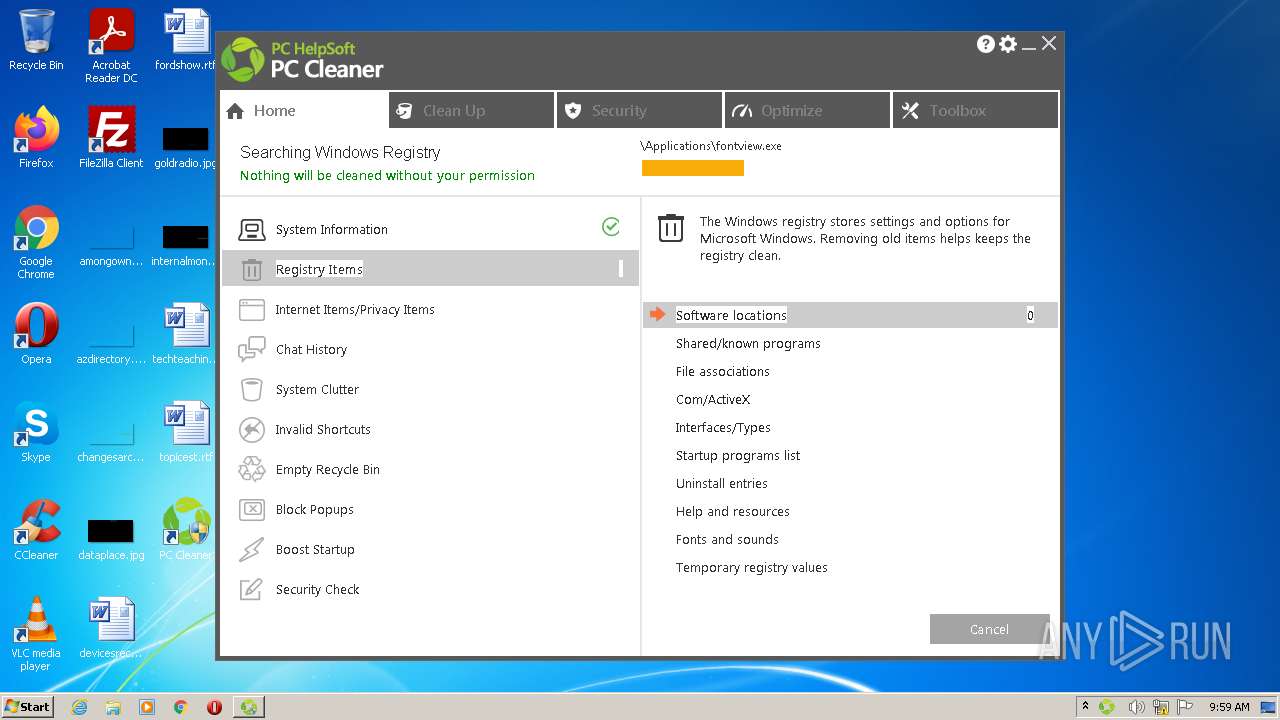
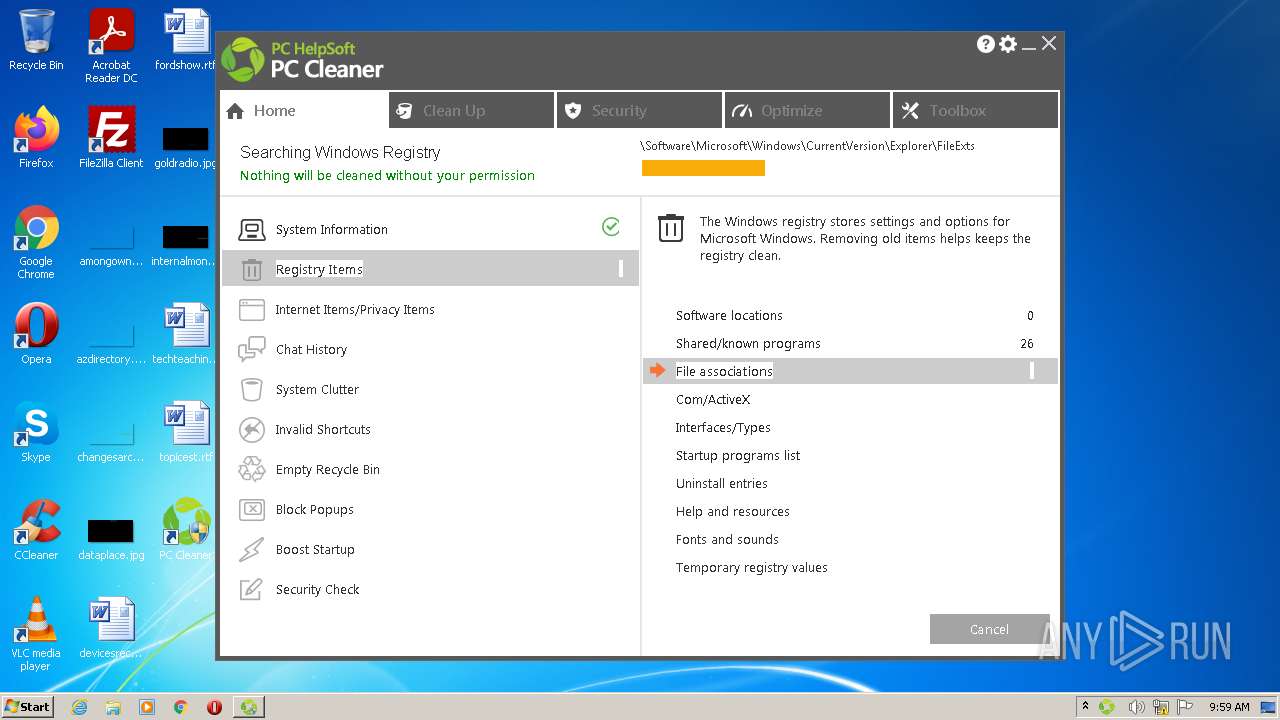
Changes default file association
- PCCleaner.exe (PID: 3320)
Creates files in the program directory
- PCCleaner.exe (PID: 3320)
- PCCNotifications.exe (PID: 3240)
Reads CPU info
- PCCleaner.exe (PID: 3320)
Creates files in the user directory
- PCCleaner.exe (PID: 3320)
Reads the cookies of Mozilla Firefox
- PCCleaner.exe (PID: 3320)
Reads the cookies of Google Chrome
- PCCleaner.exe (PID: 3320)
Adds / modifies Windows certificates
- PCCleaner.exe (PID: 3320)
Reads Windows Product ID
- PCCNotifications.exe (PID: 3240)
- PCCleaner.exe (PID: 3320)
Check for Java to be installed
- PCCleaner.exe (PID: 3320)
Searches for installed software
- PCCNotifications.exe (PID: 3240)
- PCCleaner.exe (PID: 3320)
INFO
Creates files in the program directory
- PC_Cleaner.tmp (PID: 2056)
Creates a software uninstall entry
- PC_Cleaner.tmp (PID: 2056)
Application was dropped or rewritten from another process
- PC_Cleaner.tmp (PID: 2056)
- PC_Cleaner.tmp (PID: 2112)
Checks Windows Trust Settings
- PCCleaner.exe (PID: 3320)
Reads settings of System Certificates
- PCCleaner.exe (PID: 3320)
- PCCNotifications.exe (PID: 3240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
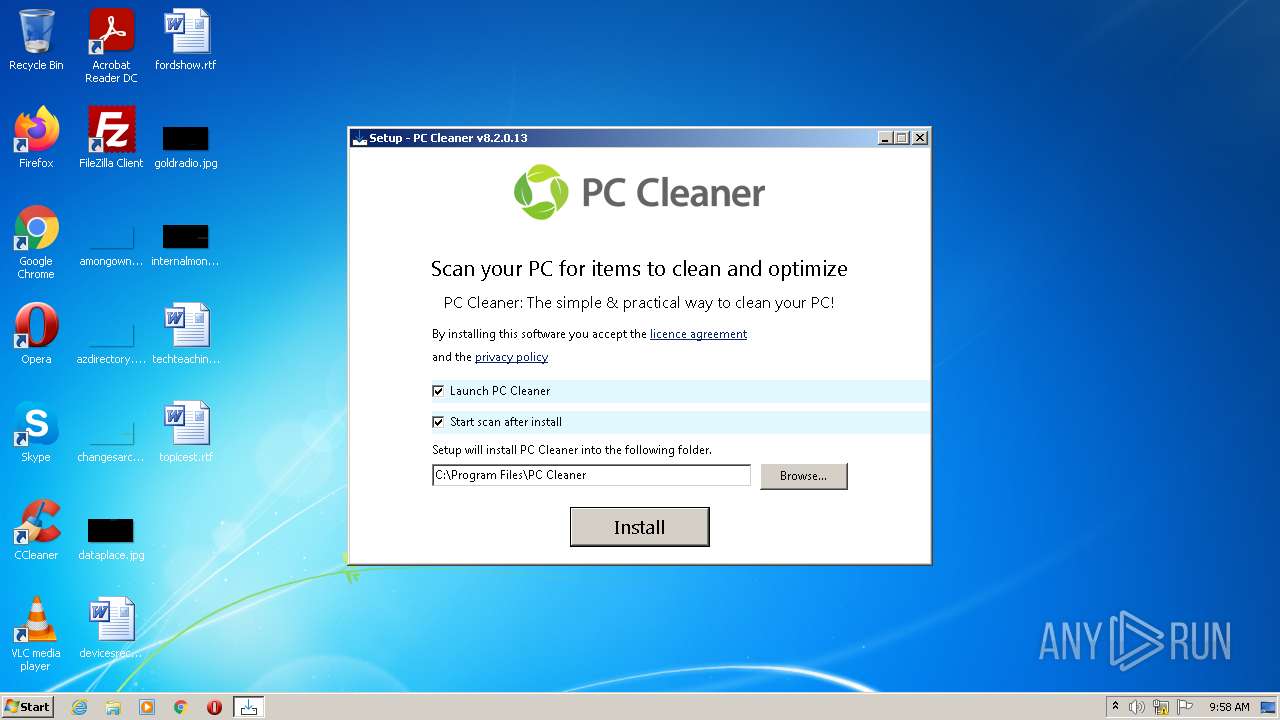
| ProductVersion: | 8.2.0.13 |
|---|---|
| ProductName: | PC Cleaner |
| OriginalFileName: | |
| LegalCopyright: | PC Helpsoft |
| FileVersion: | 8.2.0.13 |
| FileDescription: | PC Cleaner |
| CompanyName: | PC Helpsoft |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 8.2.0.13 |
| FileVersionNumber: | 8.2.0.13 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6.1 |
| ImageVersion: | 6 |
| OSVersion: | 6.1 |
| EntryPoint: | 0xb5eec |
| UninitializedDataSize: | - |
| InitializedDataSize: | 89088 |
| CodeSize: | 741376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2021:06:03 10:09:11+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jun-2021 08:09:11 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | PC Helpsoft |
| FileDescription: | PC Cleaner |
| FileVersion: | 8.2.0.13 |
| LegalCopyright: | PC Helpsoft |
| OriginalFileName: | - |
| ProductName: | PC Cleaner |
| ProductVersion: | 8.2.0.13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 03-Jun-2021 08:09:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B361C | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35606 |
.itext | 0x000B5000 | 0x00001688 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97275 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0444 |
.bss | 0x000BB000 | 0x00006DE8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x00010E00 | 0x00010E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.71194 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.98658 | 1640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.01586 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 2.1704 | 296 | UNKNOWN | English - United States | RT_ICON |
5 | 1.912 | 5672 | UNKNOWN | English - United States | RT_ICON |
6 | 1.8663 | 3752 | UNKNOWN | English - United States | RT_ICON |
7 | 1.49649 | 2216 | UNKNOWN | English - United States | RT_ICON |
8 | 0.972379 | 1384 | UNKNOWN | English - United States | RT_ICON |
9 | 7.68913 | 4837 | UNKNOWN | English - United States | RT_ICON |
10 | 2.03031 | 16936 | UNKNOWN | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054060 |
Total processes
45
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2056 | "C:\Users\admin\AppData\Local\Temp\is-LGQIS.tmp\PC_Cleaner.tmp" /SL5="$20140,5961512,831488,C:\Users\admin\AppData\Local\Temp\PC_Cleaner.exe" /SPAWNWND=$1013E /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-LGQIS.tmp\PC_Cleaner.tmp | PC_Cleaner.exe | |
User: admin Company: PC Helpsoft Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 | ||||
| 2112 | "C:\Users\admin\AppData\Local\Temp\is-U6AGO.tmp\PC_Cleaner.tmp" /SL5="$20138,5961512,831488,C:\Users\admin\AppData\Local\Temp\PC_Cleaner.exe" | C:\Users\admin\AppData\Local\Temp\is-U6AGO.tmp\PC_Cleaner.tmp | — | PC_Cleaner.exe |
User: admin Company: PC Helpsoft Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 | ||||
| 2916 | "C:\Users\admin\AppData\Local\Temp\PC_Cleaner.exe" /SPAWNWND=$1013E /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\PC_Cleaner.exe | PC_Cleaner.tmp | |
User: admin Company: PC Helpsoft Integrity Level: HIGH Description: PC Cleaner Exit code: 0 Version: 8.2.0.13 | ||||
| 3240 | "C:\Program Files\PC Cleaner\PCCNotifications.exe" | C:\Program Files\PC Cleaner\PCCNotifications.exe | PC_Cleaner.tmp | |
User: admin Company: PC Helpsoft Integrity Level: HIGH Description: PC Cleaner automatic scan and notifications Exit code: 0 Version: 8.2.0.0 | ||||
| 3320 | "C:\Program Files\PC Cleaner\PCCleaner" /START | C:\Program Files\PC Cleaner\PCCleaner.exe | PC_Cleaner.tmp | |
User: admin Company: PC Helpsoft Integrity Level: HIGH Description: PC Cleaner Exit code: 0 Version: 8.2.0.0 | ||||
| 3776 | "C:\Users\admin\AppData\Local\Temp\PC_Cleaner.exe" | C:\Users\admin\AppData\Local\Temp\PC_Cleaner.exe | Explorer.EXE | |
User: admin Company: PC Helpsoft Integrity Level: MEDIUM Description: PC Cleaner Exit code: 0 Version: 8.2.0.13 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
12
Suspicious files
17
Text files
61
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2916 | PC_Cleaner.exe | C:\Users\admin\AppData\Local\Temp\is-LGQIS.tmp\PC_Cleaner.tmp | executable | |
MD5:— | SHA256:— | |||
| 2056 | PC_Cleaner.tmp | C:\Program Files\PC Cleaner\unins000.exe | executable | |
MD5:— | SHA256:— | |||
| 2056 | PC_Cleaner.tmp | C:\Program Files\PC Cleaner\is-E55SI.tmp | executable | |
MD5:— | SHA256:— | |||
| 2056 | PC_Cleaner.tmp | C:\Program Files\PC Cleaner\is-SRDB7.tmp | executable | |
MD5:— | SHA256:— | |||
| 2056 | PC_Cleaner.tmp | C:\Program Files\PC Cleaner\is-CR1DF.tmp | executable | |
MD5:— | SHA256:— | |||
| 3776 | PC_Cleaner.exe | C:\Users\admin\AppData\Local\Temp\is-U6AGO.tmp\PC_Cleaner.tmp | executable | |
MD5:— | SHA256:— | |||
| 2056 | PC_Cleaner.tmp | C:\Program Files\PC Cleaner\PCCleaner.exe | executable | |
MD5:— | SHA256:— | |||
| 2056 | PC_Cleaner.tmp | C:\Program Files\PC Cleaner\PCCNotifications.exe | executable | |
MD5:— | SHA256:— | |||
| 2056 | PC_Cleaner.tmp | C:\Program Files\PC Cleaner\is-PD4T7.tmp | text | |
MD5:F3FEFEA25538FFC9859E823F99A5B7DB | SHA256:602D65459DCFDB621AB52082943DDA2843A83B3077F98D7876887DBAC5CE66C9 | |||
| 2056 | PC_Cleaner.tmp | C:\Users\admin\AppData\Local\Temp\is-C76S0.tmp\PCCleaner.bmp | image | |
MD5:4E2EE28B4E87193919ED0CA8CACF1093 | SHA256:9B1509867DBAD1CA41D718BA7D1BD3EE799BDC165C38088BB807B34EDB7BB838 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
20
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3320 | PCCleaner.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | US | der | 1.40 Kb | whitelisted |
3320 | PCCleaner.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDCPdbqctmTejOYZsLw%3D%3D | US | der | 1.41 Kb | whitelisted |
3320 | PCCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3320 | PCCleaner.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b1c9d3f71a4720b3 | US | compressed | 4.70 Kb | whitelisted |
3320 | PCCleaner.exe | GET | 302 | 217.195.25.242:80 | http://webtools.pchelpsoft.com/install_success.cfm?redirectId=pchelpsoft/pc_cleaner_tracked.htm&target=https://www.pchelpsoft.com&&purl=1&mkey1=DEFAULT_REDIRECT_TRACKING&mkey10=DEFAULT_REDIRECT_TRACKING | FR | text | 89 b | unknown |
3320 | PCCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAgI4ZIEOW%2FBXbKGGdaUa0s%3D | US | der | 279 b | whitelisted |
3320 | PCCleaner.exe | GET | 302 | 217.195.25.242:80 | http://webtools.pchelpsoft.com/install_success.cfm?redirectId=pchelpsoft/pc_cleaner_tracked.htm&target=https://www.pchelpsoft.com&&purl=1&mkey1=DEFAULT_REDIRECT_TRACKING&mkey10=DEFAULT_REDIRECT_TRACKING | FR | text | 89 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3320 | PCCleaner.exe | 217.195.25.241:443 | webtools.avanquest.com | SPIE Cloud Services SAS | FR | malicious |
3320 | PCCleaner.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
3320 | PCCleaner.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
3240 | PCCNotifications.exe | 116.203.251.147:443 | collect.avqtools.com | 334,Udyog Vihar | IN | suspicious |
3320 | PCCleaner.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3240 | PCCNotifications.exe | 172.66.43.147:443 | www.pchelpsoft.com | — | US | suspicious |
— | — | 116.203.251.147:443 | collect.avqtools.com | 334,Udyog Vihar | IN | suspicious |
3320 | PCCleaner.exe | 116.203.251.147:443 | collect.avqtools.com | 334,Udyog Vihar | IN | suspicious |
3320 | PCCleaner.exe | 172.66.43.147:443 | www.pchelpsoft.com | — | US | suspicious |
3320 | PCCleaner.exe | 217.195.25.242:80 | webtools.pchelpsoft.com | SPIE Cloud Services SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
webtools.avanquest.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
collect.avqtools.com |
| suspicious |
ocsp.globalsign.com |
| whitelisted |
webtools.pchelpsoft.com |
| unknown |
www.pchelpsoft.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |