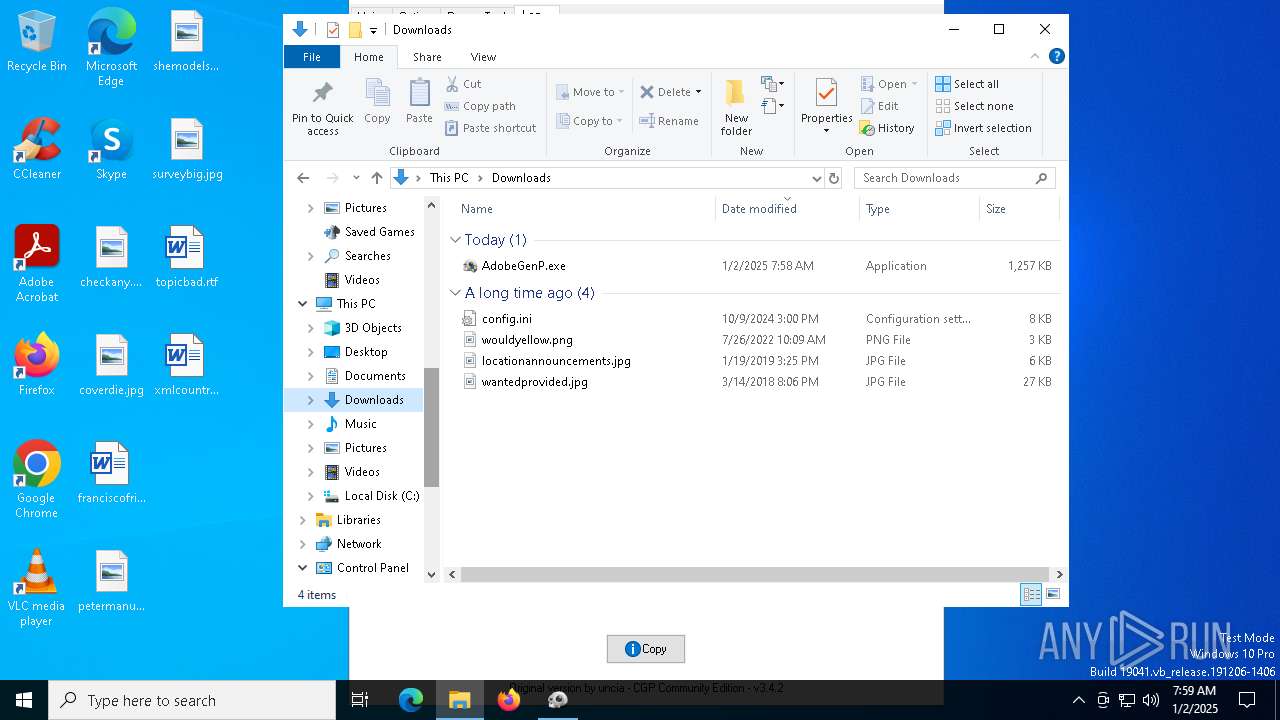
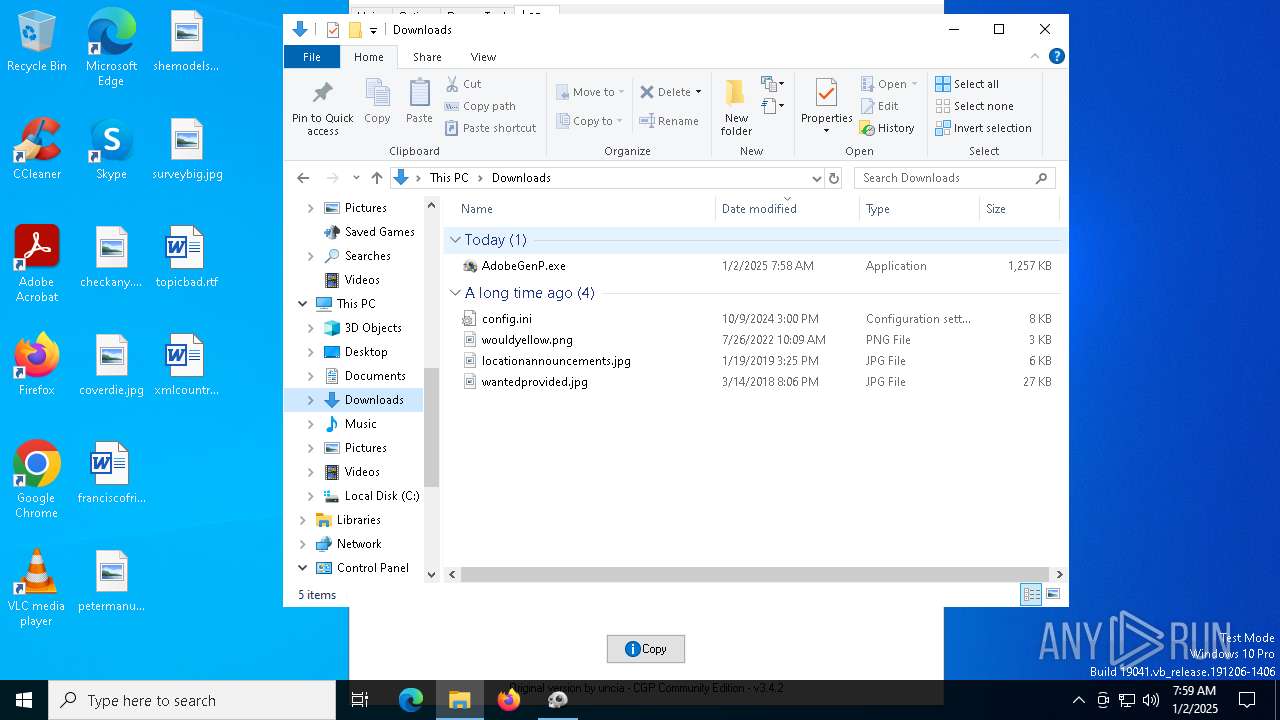
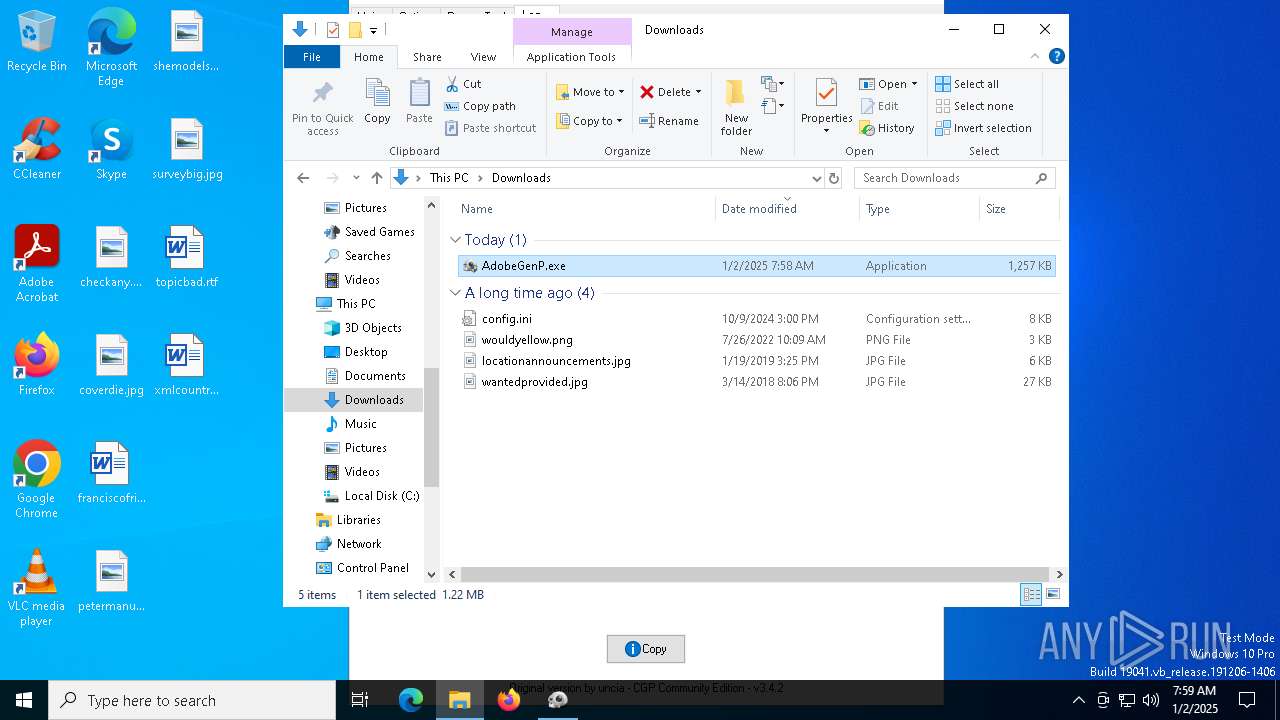
| File name: | AdobeGenP.exe |
| Full analysis: | https://app.any.run/tasks/afc3a74d-8b92-4077-82b6-8e9d385e902a |
| Verdict: | Malicious activity |
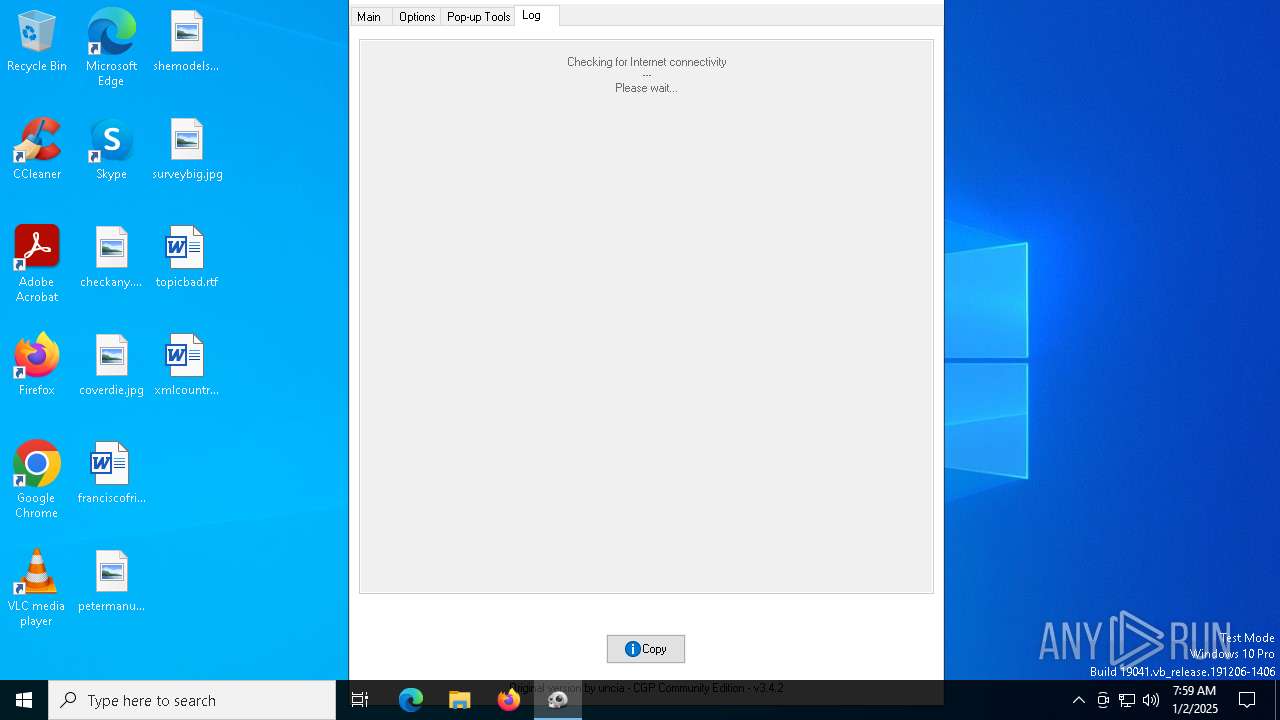
| Analysis date: | January 02, 2025, 07:58:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 6F1A436F28CB5386B19C15FB6DE09D42 |
| SHA1: | 53E90F98FDDBE728F1E10DBE60E2871804B76C6E |
| SHA256: | B09EC2AC41CC220B2B2B68B23BF120DCB518850341D8E3E088B50185EF624ED7 |
| SSDEEP: | 49152:pE/XUraxm5O9QMal0QRO8tep/QDWVocOg1:p9rem5OidCR29Q1 |
MALICIOUS
Executing a file with an untrusted certificate
- RunAsTI.exe (PID: 6940)
Changes powershell execution policy (Bypass)
- AdobeGenP.exe (PID: 7048)
Bypass execution policy to execute commands
- powershell.exe (PID: 2828)
- powershell.exe (PID: 3700)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- AdobeGenP.exe (PID: 7048)
Executable content was dropped or overwritten
- AdobeGenP.exe (PID: 6236)
Found IP address in command line
- powershell.exe (PID: 3700)
- powershell.exe (PID: 2828)
Removes files via Powershell
- powershell.exe (PID: 2828)
Probably obfuscated PowerShell command line is found
- AdobeGenP.exe (PID: 7048)
Manipulates environment variables
- powershell.exe (PID: 2828)
Application launched itself
- RunAsTI.exe (PID: 6940)
INFO
Checks supported languages
- AdobeGenP.exe (PID: 6236)
- RunAsTI.exe (PID: 6940)
- AdobeGenP.exe (PID: 7048)
- RunAsTI.exe (PID: 7000)
Reads mouse settings
- AdobeGenP.exe (PID: 6236)
- AdobeGenP.exe (PID: 7048)
Reads the computer name
- AdobeGenP.exe (PID: 6236)
- RunAsTI.exe (PID: 6940)
- AdobeGenP.exe (PID: 7048)
- RunAsTI.exe (PID: 7000)
The sample compiled with english language support
- AdobeGenP.exe (PID: 6236)
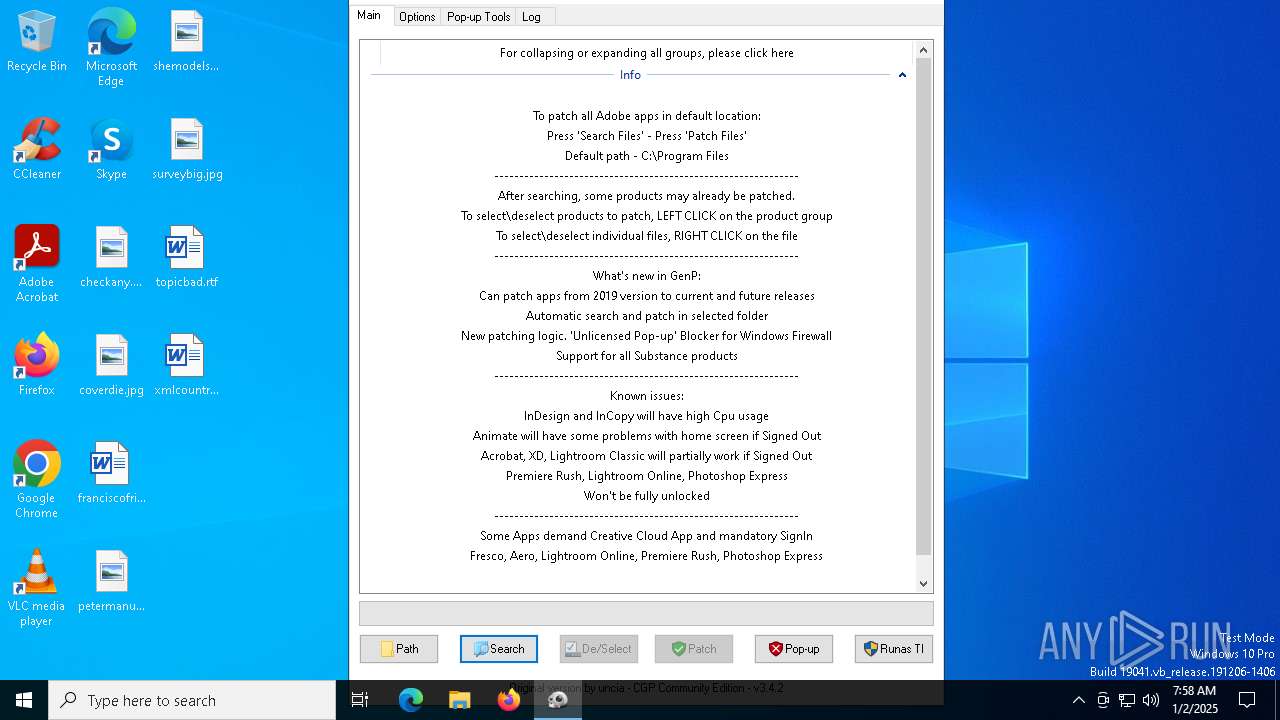
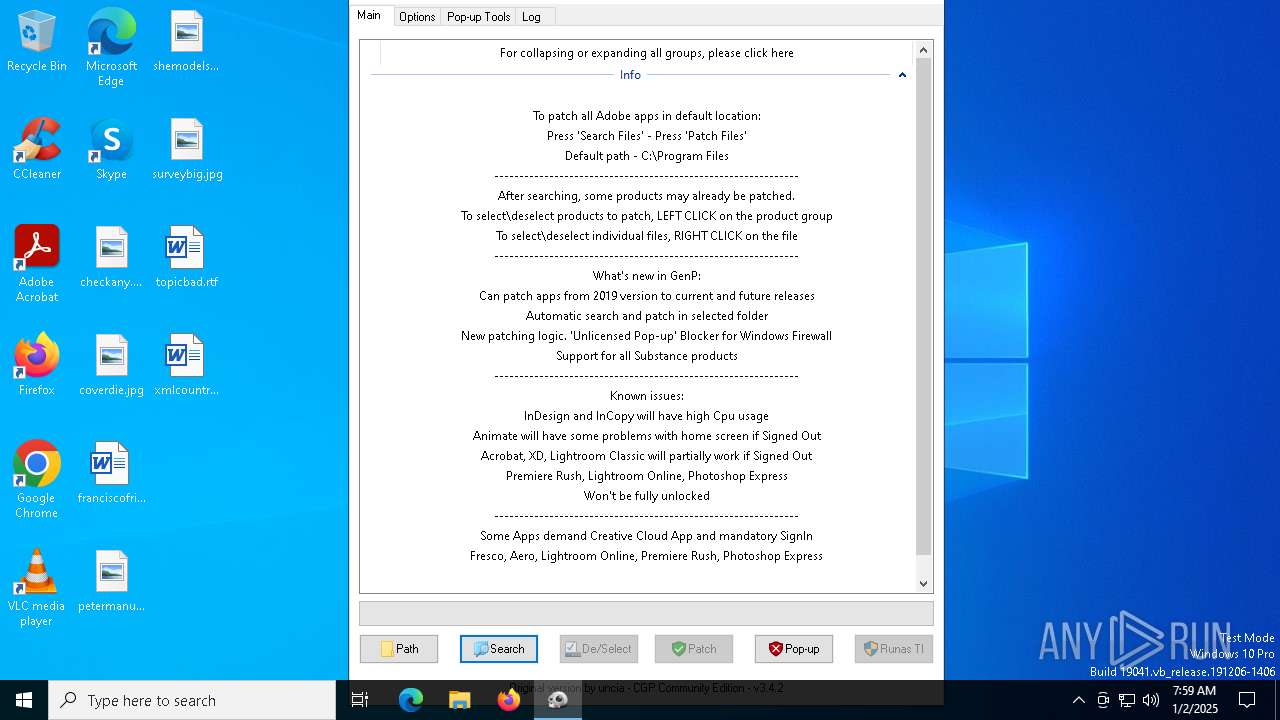
The process uses AutoIt
- AdobeGenP.exe (PID: 6236)
Create files in a temporary directory
- AdobeGenP.exe (PID: 6236)
The process uses the downloaded file
- powershell.exe (PID: 3700)
- powershell.exe (PID: 2828)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3700)
Disables trace logs
- powershell.exe (PID: 2828)
Manual execution by a user
- AdobeGenP.exe (PID: 6476)
- AdobeGenP.exe (PID: 6532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:10:09 15:00:33+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 734208 |
| InitializedDataSize: | 551936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2549c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.16.1 |
| ProductVersionNumber: | 3.3.16.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 3.3.16.1 |
| Comments: | AdobeGenP |
| FileDescription: | AdobeGenP |
| ProductName: | AdobeGenP |
| ProductVersion: | 3.3.16.1 |
| CompanyName: | AdobeGenP |
| LegalCopyright: | AdobeGenP |
| LegalTradeMarks: | AdobeGenP |
Total processes
140
Monitored processes
12
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2828 | PowerShell Set-ExecutionPolicy Bypass -scope Process -Force;$path = Join-Path -Path $env:TEMP -ChildPath pihole.txt;Invoke-WebRequest 'https://a.dove.isdumb.one/pihole.txt' -OutFile $path;$ips=@();$soa=(Resolve-DnsName -Name ic.adobe.io -Type SOA).PrimaryServer;Do{$ip=(Resolve-DnsName -Name ic.adobe.io -Server $soa).IPAddress;$ips+=$ip;If($ip -eq '0.0.0.0'){Break};If($ip -eq '127.0.0.1'){Break};$ips=$ips|Select-Object -Unique|Sort-Object}While($ips.Count -lt 8);[System.IO.File]::ReadLines($path) | ForEach-Object {if($_ -Match 'adobestats.io'){$ip=(Resolve-DnsName -Name $_).IPAddress;$ips+=$ip;}};Remove-Item $path;$ips=$ips|Select-Object -Unique|Sort-Object;$list=$ips -join ',';$list; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | AdobeGenP.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3700 | PowerShell Set-ExecutionPolicy Bypass -scope Process -Force;(Get-NetRoute | Where-Object DestinationPrefix -eq '0.0.0.0/0' | Get-NetIPInterface | Where-Object ConnectionState -eq 'Connected') -ne $null | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | AdobeGenP.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4740 | "C:\Users\admin\Downloads\AdobeGenP.exe" | C:\Users\admin\Downloads\AdobeGenP.exe | — | explorer.exe | |||||||||||
User: admin Company: AdobeGenP Integrity Level: MEDIUM Description: AdobeGenP Exit code: 3221226540 Version: 3.3.16.1 Modules
| |||||||||||||||
| 5036 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5592 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6236 | "C:\Users\admin\Downloads\AdobeGenP.exe" | C:\Users\admin\Downloads\AdobeGenP.exe | explorer.exe | ||||||||||||
User: admin Company: AdobeGenP Integrity Level: HIGH Description: AdobeGenP Exit code: 6940 Version: 3.3.16.1 Modules
| |||||||||||||||
| 6476 | "C:\Users\admin\Downloads\AdobeGenP.exe" | C:\Users\admin\Downloads\AdobeGenP.exe | — | explorer.exe | |||||||||||
User: admin Company: AdobeGenP Integrity Level: MEDIUM Description: AdobeGenP Exit code: 3221226540 Version: 3.3.16.1 Modules
| |||||||||||||||
| 6532 | "C:\Users\admin\Downloads\AdobeGenP.exe" | C:\Users\admin\Downloads\AdobeGenP.exe | explorer.exe | ||||||||||||
User: admin Company: AdobeGenP Integrity Level: HIGH Description: AdobeGenP Exit code: 0 Version: 3.3.16.1 Modules
| |||||||||||||||
| 6940 | C:\WINDOWS\Temp\RunAsTI.exe "C:\Users\admin\Downloads\AdobeGenP.exe" | C:\Windows\Temp\RunAsTI.exe | — | AdobeGenP.exe | |||||||||||
User: admin Company: Nikzzzz Soft Integrity Level: HIGH Description: Run As TrustedInstaller Exit code: 0 Version: 2020,4,15,1 Modules
| |||||||||||||||
Total events
13 351
Read events
13 351
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
3
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3700 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_bmmgnrtw.icz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3700 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_3pk2s0o4.ajc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3700 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_w5xcgkeu.wjb.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3700 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_wkx0lk2a.0vd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3700 | powershell.exe | C:\Users\Default\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:D13F17A0A2E82E8EC4F93FCB8B363C52 | SHA256:B30C68A0B031CDDE5CFE4A6D907156C46546B98A095EE39DED7B6540E5B75F1E | |||
| 6236 | AdobeGenP.exe | C:\Users\admin\Downloads\config.ini | text | |
MD5:F2EF246F608DF6970968FBDE300CA7AA | SHA256:3709022A13F41251621C34AA2AD72301AAD4D5B1CEB8A5095A3FCDAEDBD73804 | |||
| 2828 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_h2de2jyt.umu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2828 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_yq5ghprg.bfm.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2828 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_q3205qa0.uui.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6236 | AdobeGenP.exe | C:\Windows\Temp\RunAsTI.exe | executable | |
MD5:80454E70784F1DDB0C91D41469E2498D | SHA256:A3E0BA70BA908DE8A75825C3A1FF36147E02C686280993C2CAA8A9A6968764B0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
33
DNS requests
1 036
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6324 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7088 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7088 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |