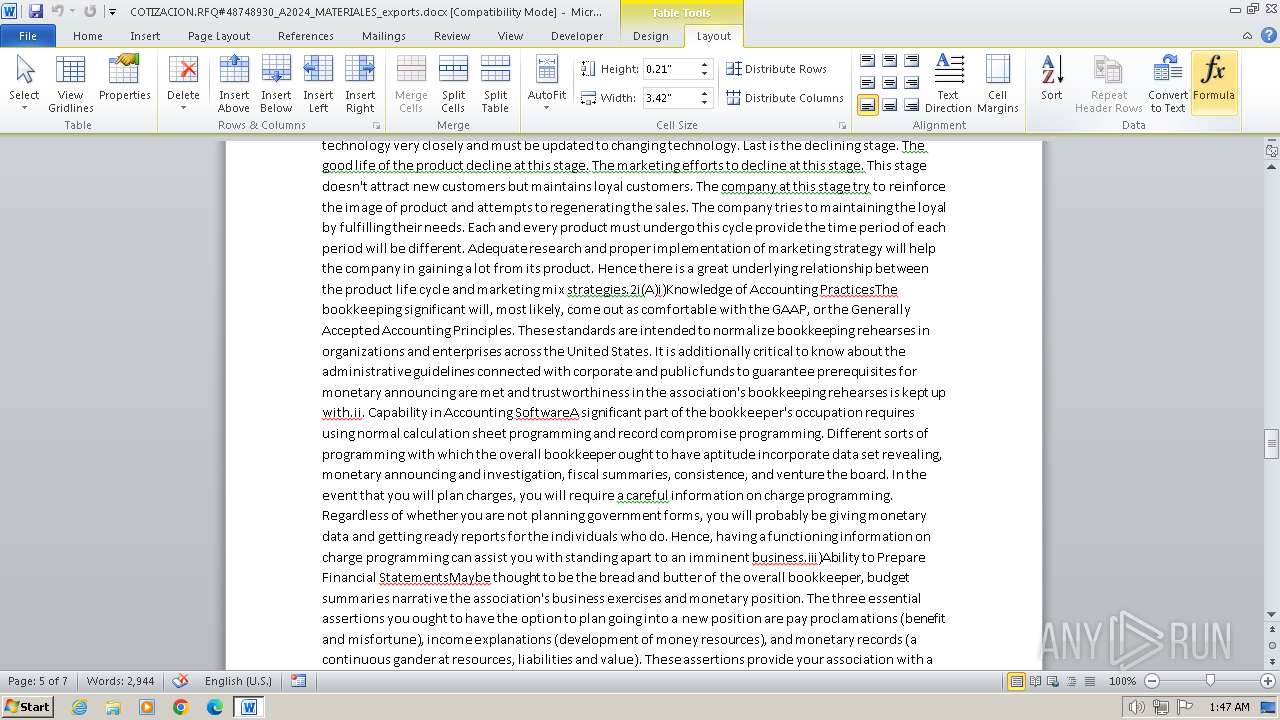
| File name: | COTIZACION.RFQ#48748930_A2024_MATERIALES_exports.docx |
| Full analysis: | https://app.any.run/tasks/4d873ba8-caa4-462d-8052-33614e38c999 |
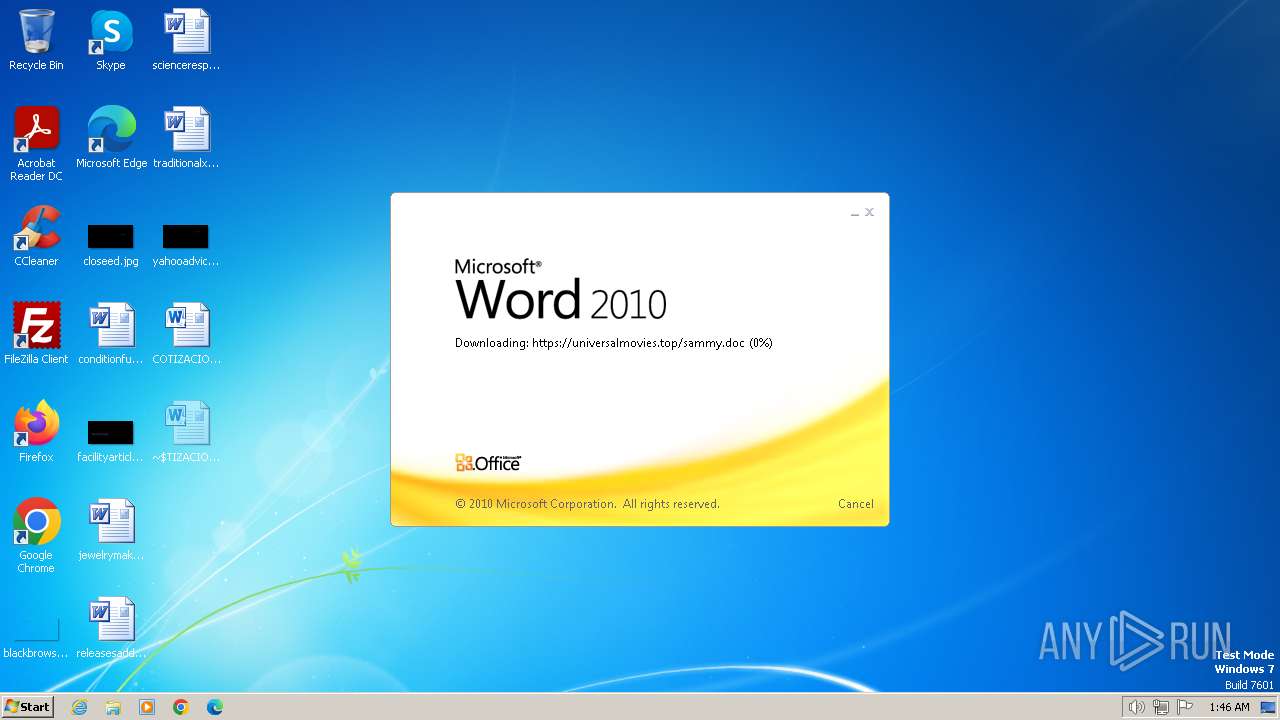
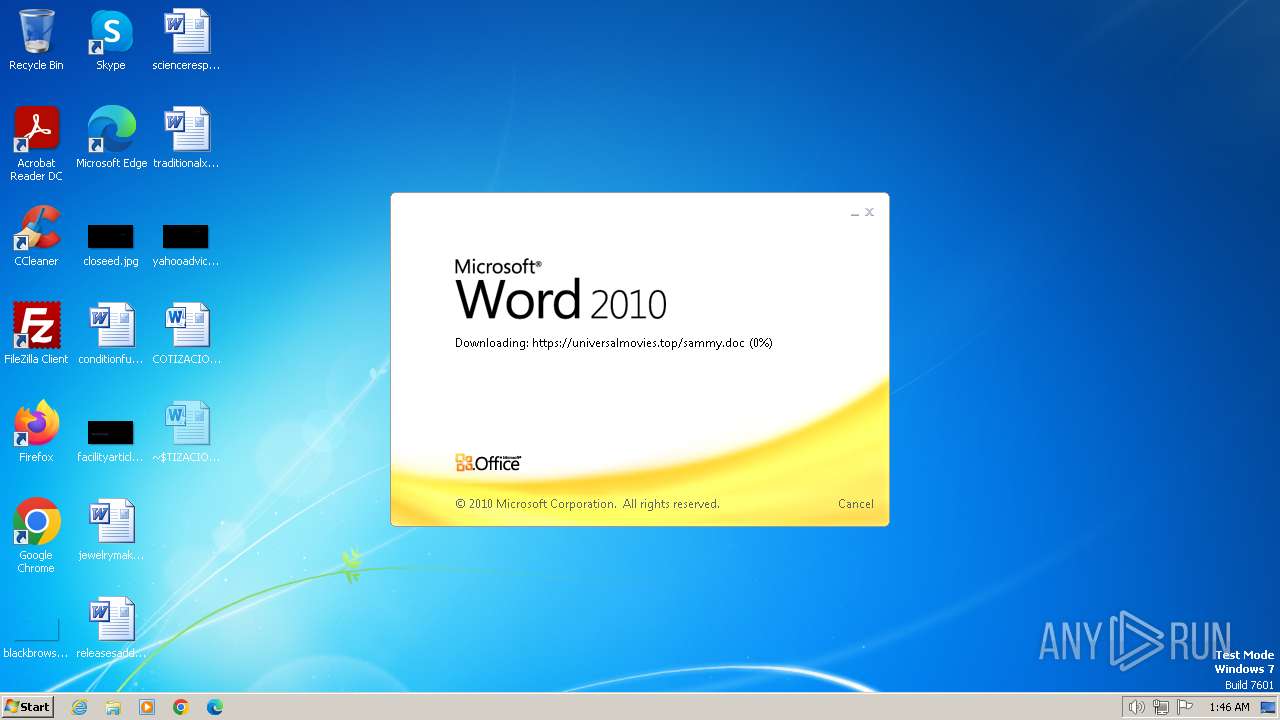
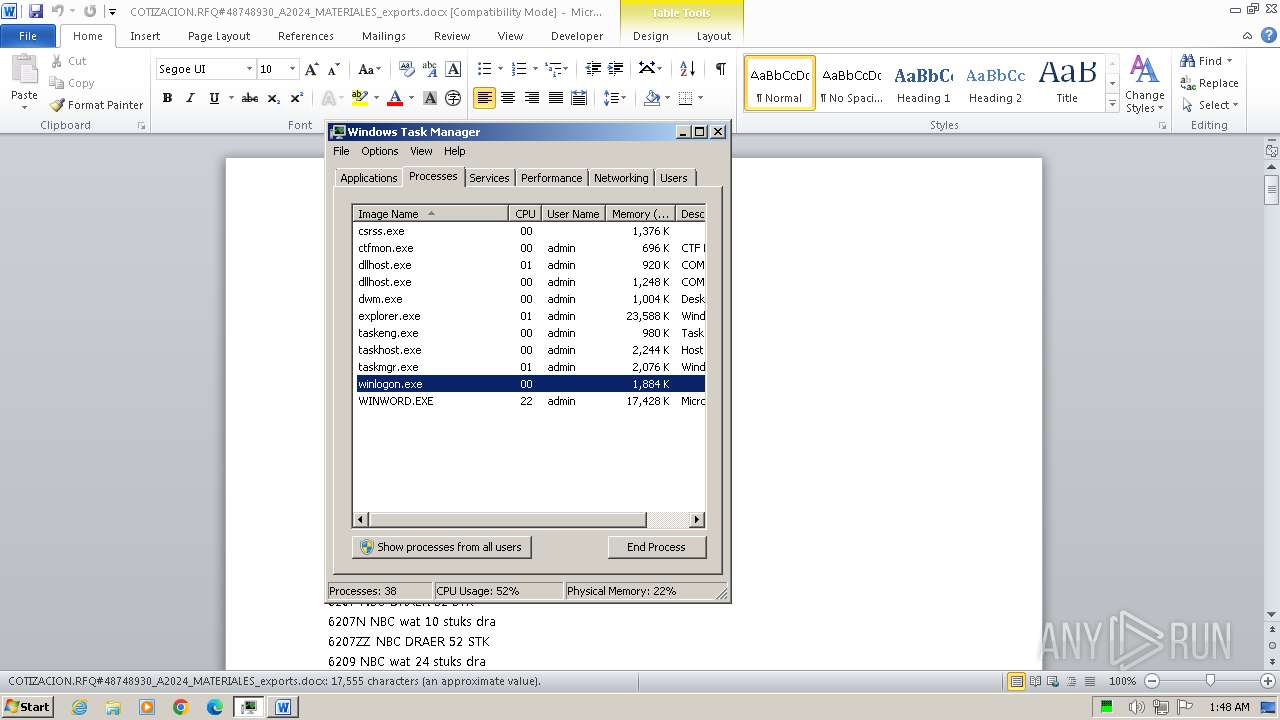
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2024, 00:46:18 |
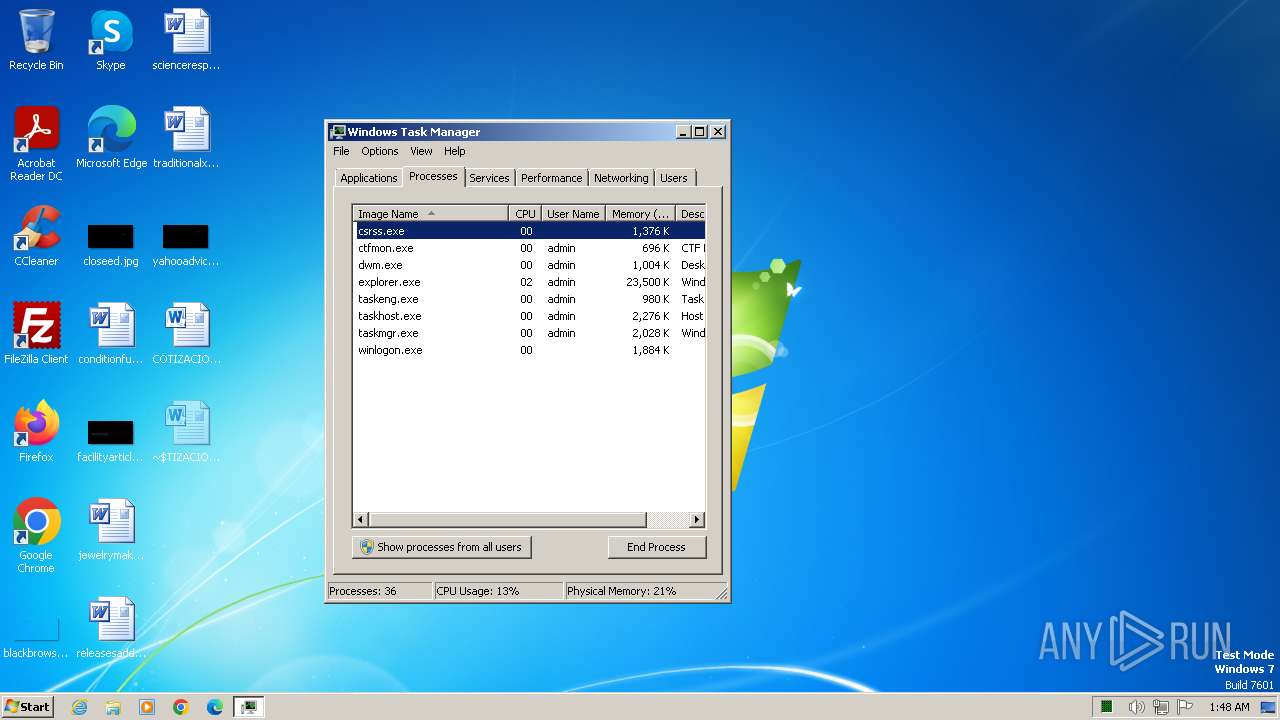
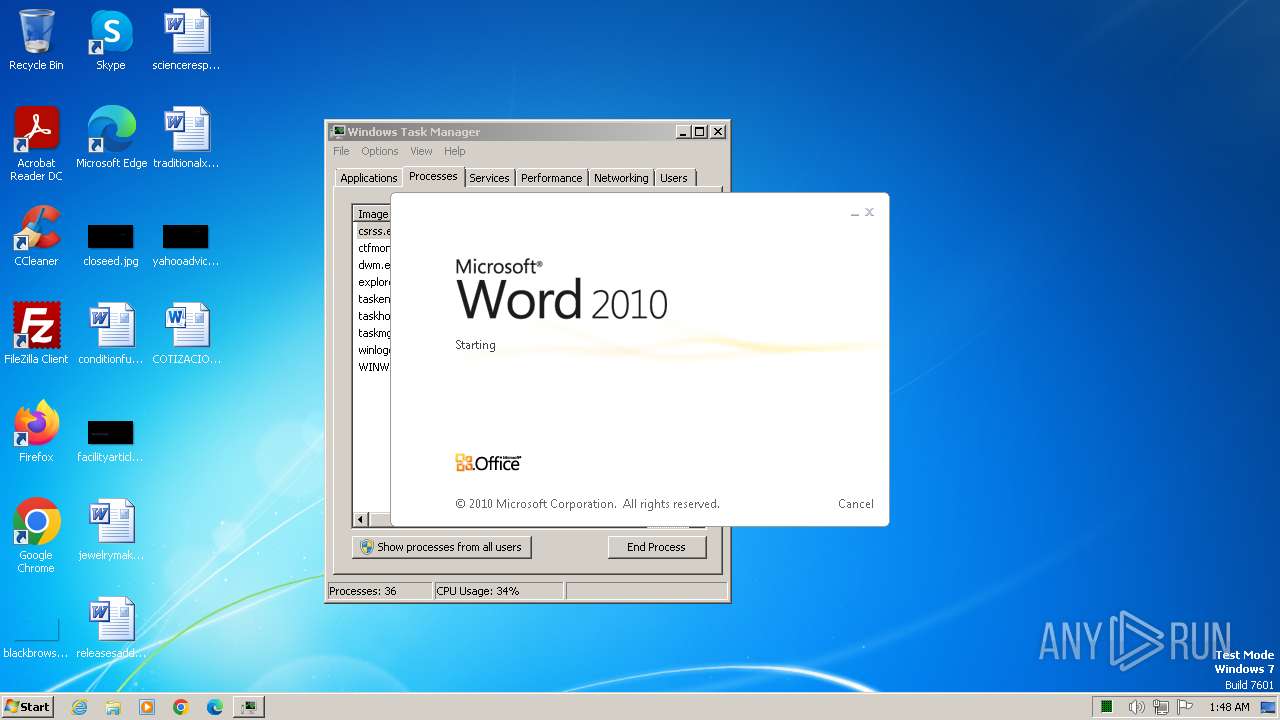
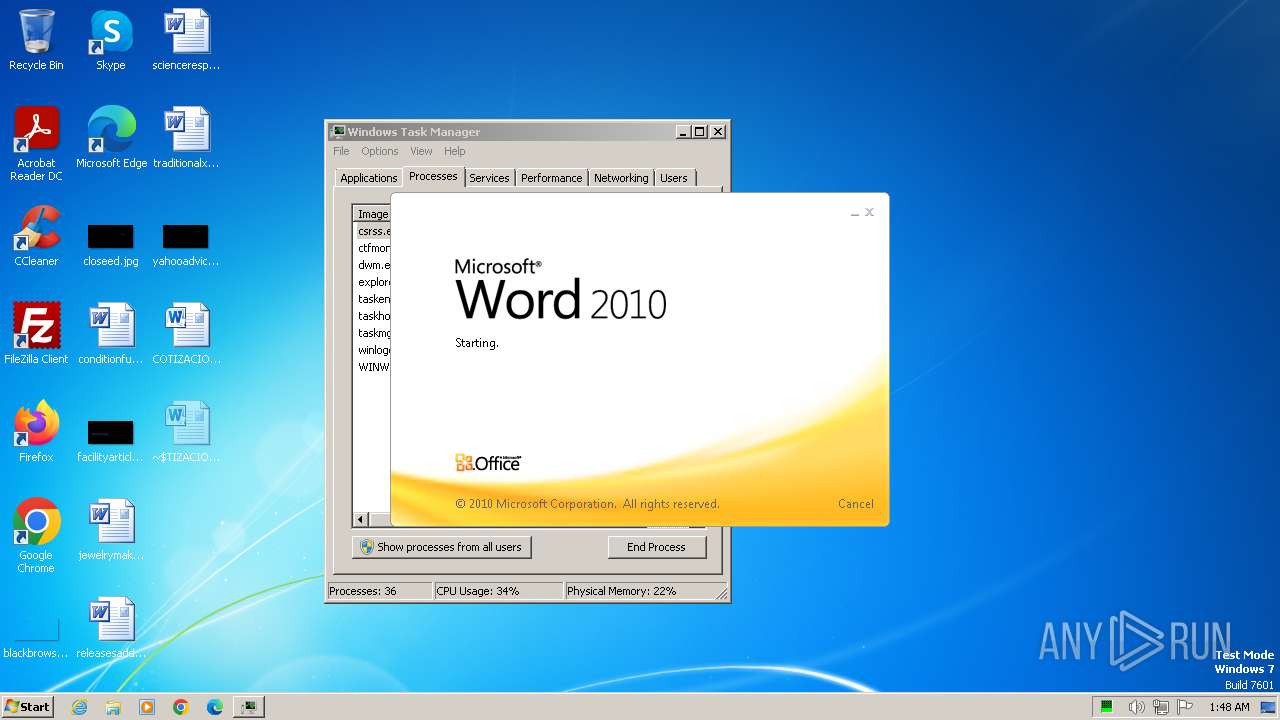
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 0F76364FC61B28CF256690EE53F4442C |
| SHA1: | CED485770B39D9D6239971A8CF1F0D640F85EE5E |
| SHA256: | B08C2A5ACDB3588DE4F64BCA0DCB14F58086BB7CFABD06D4AC2B4A7E0CA79168 |
| SSDEEP: | 384:XqF8hXNjeU2bSLSxnindXUclky/modEg7Su4fynCYhX:WoCU7LSxidXDnVig7OWCa |
MALICIOUS
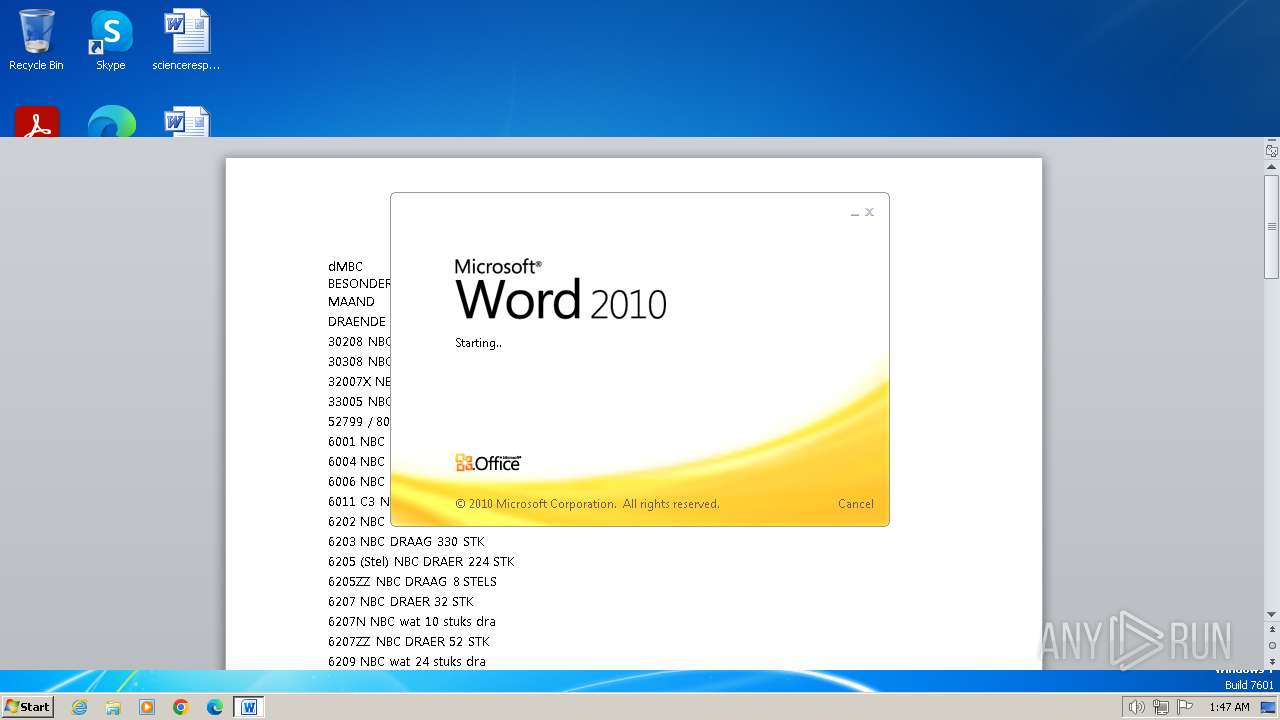
Equation Editor starts application (likely CVE-2017-11882)
- EQNEDT32.EXE (PID: 3856)
- EQNEDT32.EXE (PID: 4032)
- EQNEDT32.EXE (PID: 1816)
CVE-2017-0199 detected
- WINWORD.EXE (PID: 3700)
- WINWORD.EXE (PID: 3552)
- WINWORD.EXE (PID: 2304)
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 3856)
- EQNEDT32.EXE (PID: 4032)
- EQNEDT32.EXE (PID: 1816)
Drops the executable file immediately after the start
- EQNEDT32.EXE (PID: 3856)
SUSPICIOUS
Reads security settings of Internet Explorer
- EQNEDT32.EXE (PID: 3856)
- EQNEDT32.EXE (PID: 4032)
- EQNEDT32.EXE (PID: 1816)
Checks Windows Trust Settings
- EQNEDT32.EXE (PID: 3856)
- EQNEDT32.EXE (PID: 4032)
- EQNEDT32.EXE (PID: 1816)
Reads settings of System Certificates
- EQNEDT32.EXE (PID: 3856)
- EQNEDT32.EXE (PID: 4032)
- EQNEDT32.EXE (PID: 1816)
Reads the Internet Settings
- EQNEDT32.EXE (PID: 3856)
- EQNEDT32.EXE (PID: 4032)
- EQNEDT32.EXE (PID: 1816)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 3856)
INFO
Reads the machine GUID from the registry
- EQNEDT32.EXE (PID: 3856)
- EQNEDT32.EXE (PID: 4032)
- EQNEDT32.EXE (PID: 1816)
Checks supported languages
- EQNEDT32.EXE (PID: 3856)
- EQNEDT32.EXE (PID: 4032)
- EQNEDT32.EXE (PID: 1816)
Reads the computer name
- EQNEDT32.EXE (PID: 3856)
- EQNEDT32.EXE (PID: 4032)
- EQNEDT32.EXE (PID: 1816)
Checks proxy server information
- EQNEDT32.EXE (PID: 3856)
- EQNEDT32.EXE (PID: 4032)
- EQNEDT32.EXE (PID: 1816)
Creates files or folders in the user directory
- EQNEDT32.EXE (PID: 3856)
Reads the software policy settings
- EQNEDT32.EXE (PID: 3856)
- EQNEDT32.EXE (PID: 4032)
- EQNEDT32.EXE (PID: 1816)
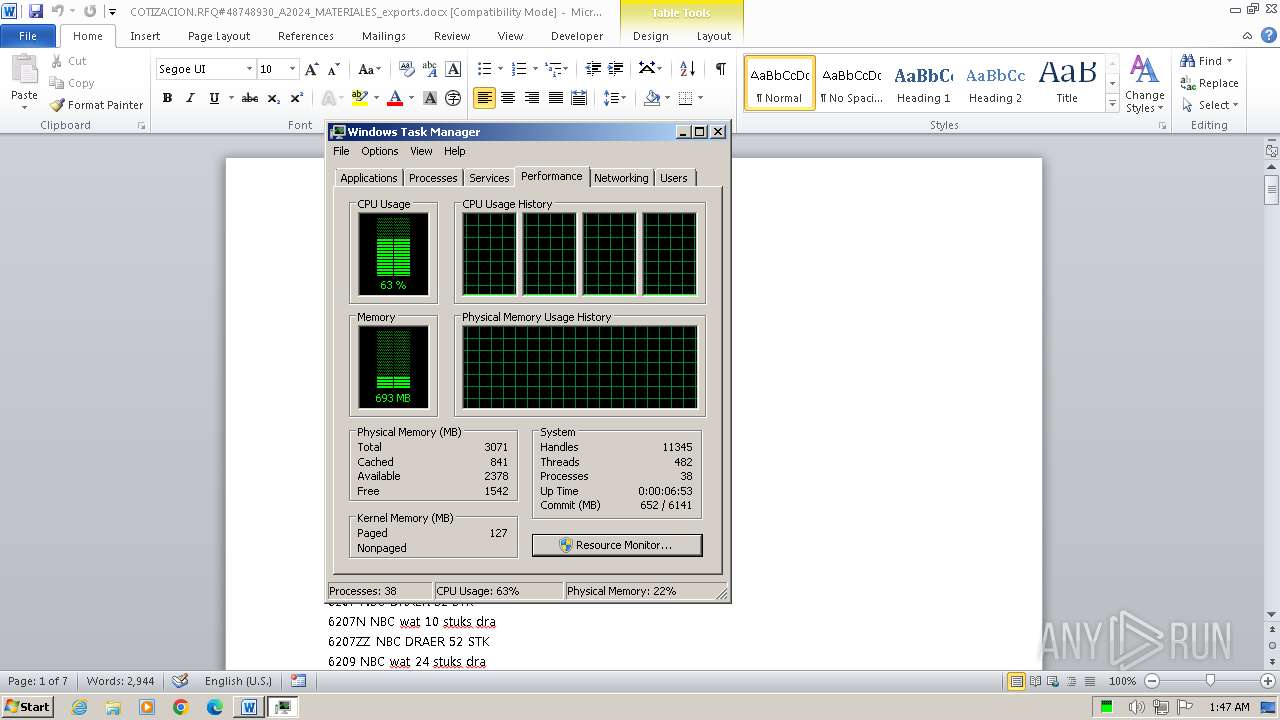
Manual execution by a user
- WINWORD.EXE (PID: 3552)
- taskmgr.exe (PID: 1168)
- WINWORD.EXE (PID: 2304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:06:20 13:28:32 |
| ZipCRC: | 0x3795fcdd |
| ZipCompressedSize: | 341 |
| ZipUncompressedSize: | 1312 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | 19 minutes |
| Pages: | 7 |
| Words: | 3177 |
| Characters: | 18113 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 150 |
| Paragraphs: | 42 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 21248 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 12 |
| LastModifiedBy: | Modexcomm |
| RevisionNumber: | 7 |
| CreateDate: | 2023:03:27 22:13:00Z |
| ModifyDate: | 2023:08:16 13:25:00Z |
XMP
| Creator: | Modexcomm |
|---|
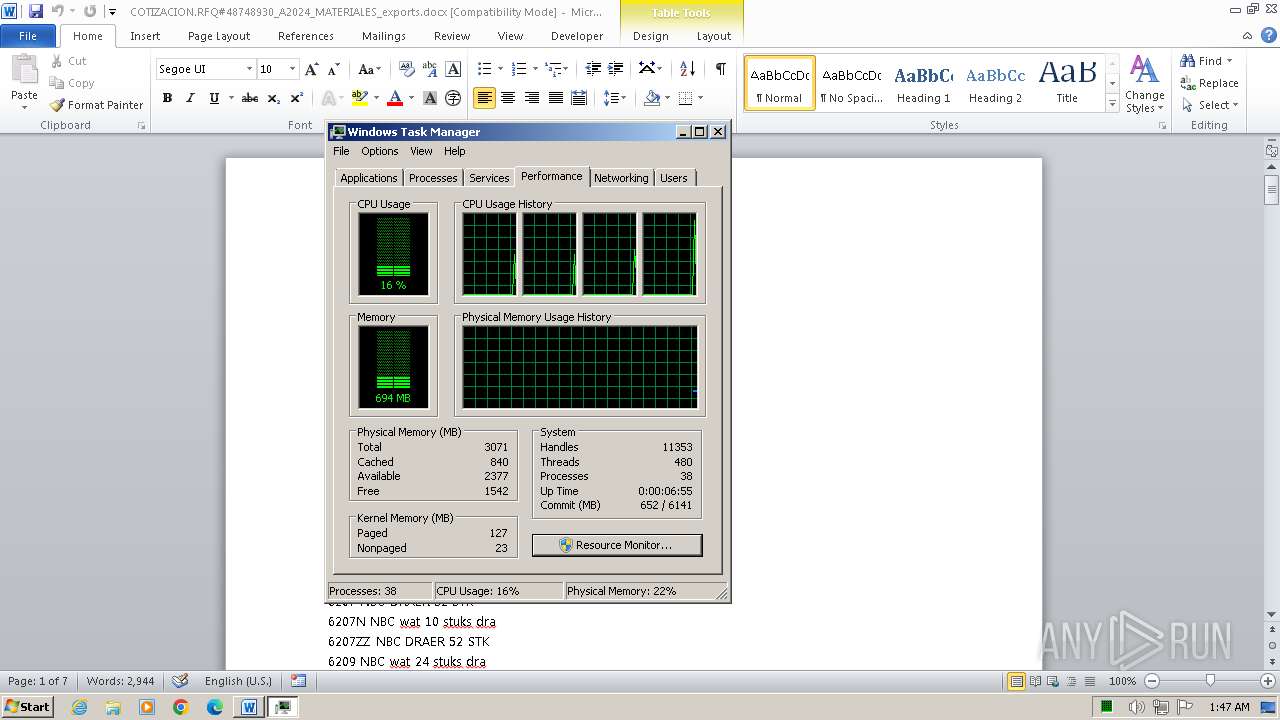
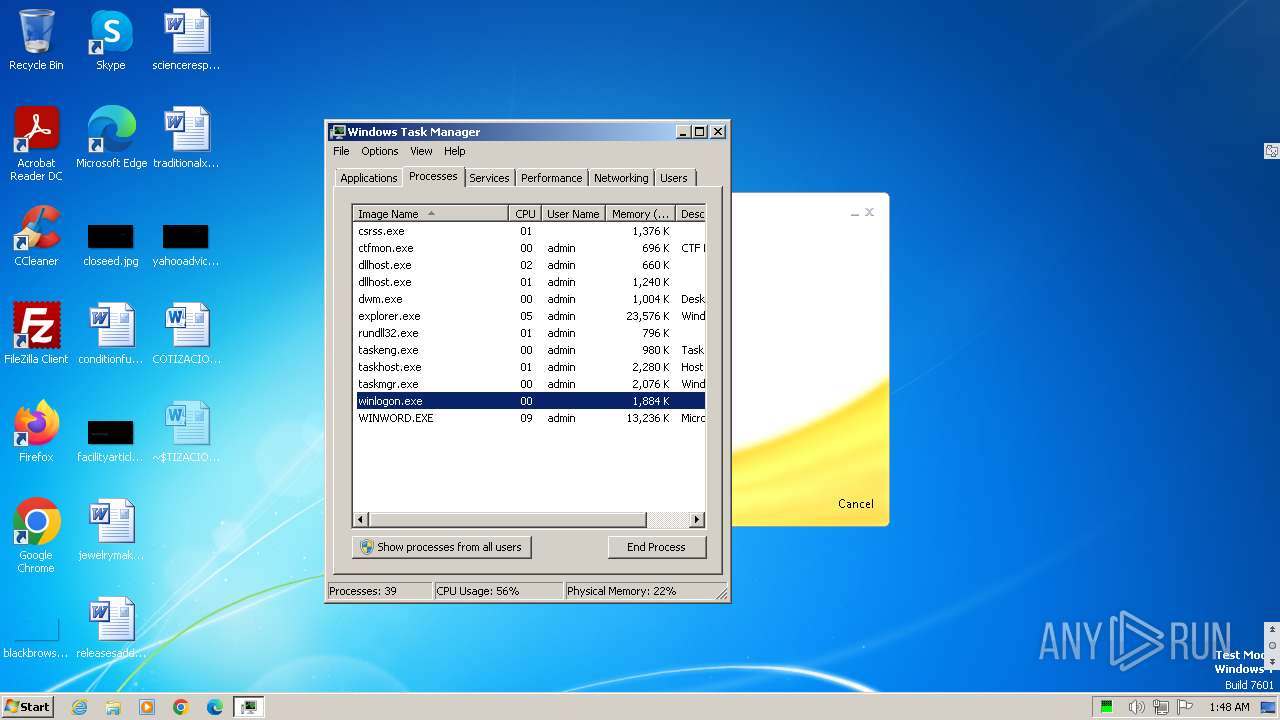
Total processes
61
Monitored processes
7
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
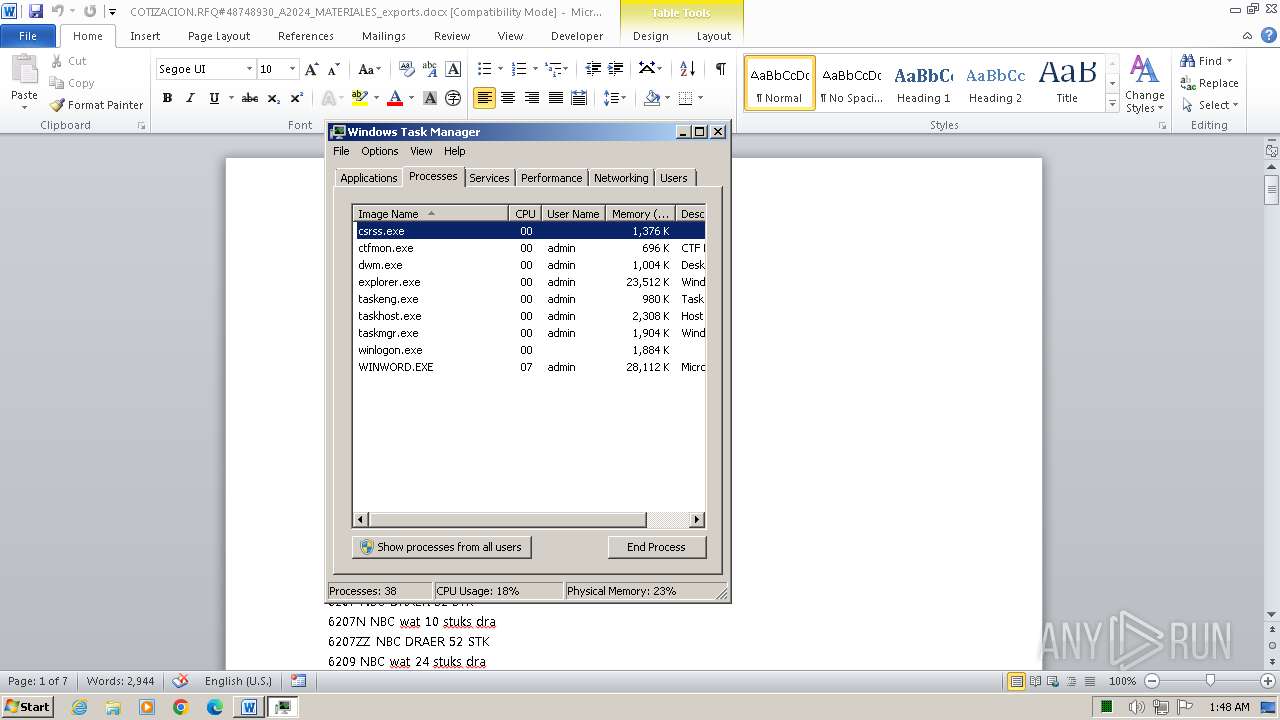
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
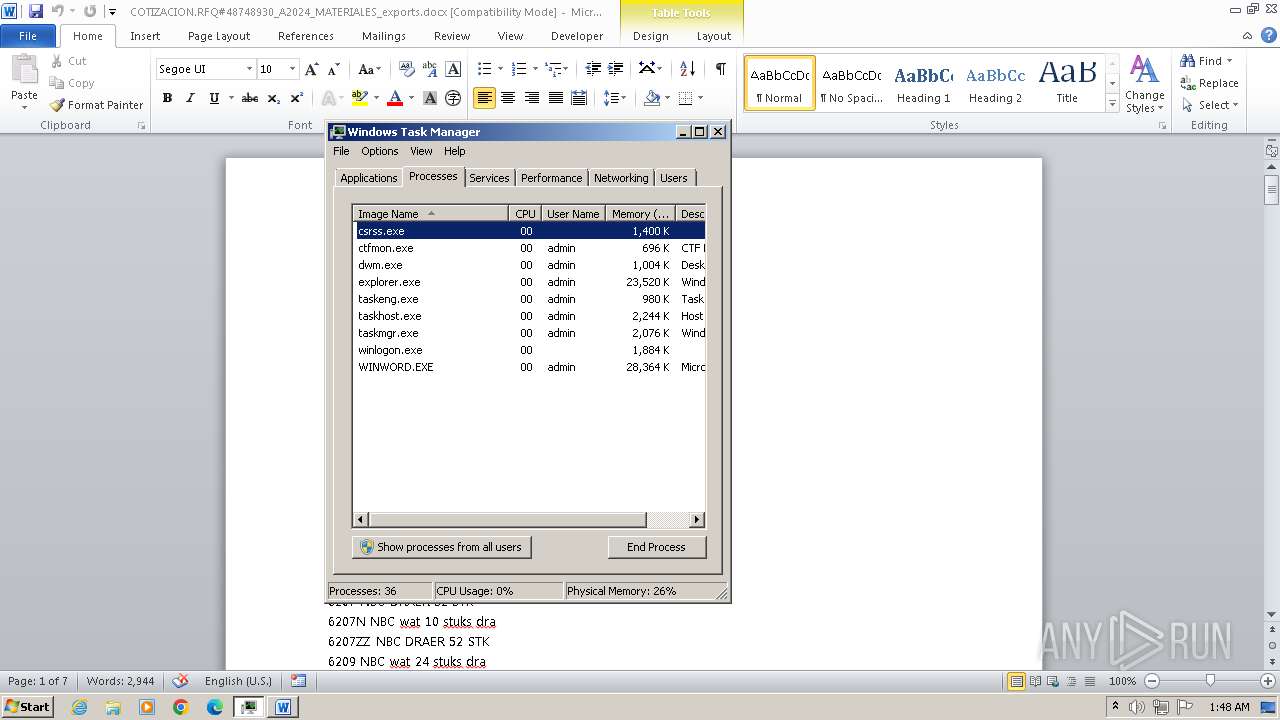
| 1168 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\COTIZACION.RFQ#48748930_A2024_MATERIALES_exports.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3552 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\COTIZACION.RFQ#48748930_A2024_MATERIALES_exports.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3700 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n C:\Users\admin\Desktop\COTIZACION.RFQ#48748930_A2024_MATERIALES_exports.docx | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3856 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 4032 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
Total events
41 736
Read events
38 771
Write events
1 970
Delete events
995
Modification events
| (PID) Process: | (3700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | *62 |
Value: 2A363200740E0000010000000000000000000000 | |||
| (PID) Process: | (3700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
35
Text files
9
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3700 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREA9B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3700 | WINWORD.EXE | C:\Users\admin\Desktop\~$TIZACION.RFQ#48748930_A2024_MATERIALES_exports.docx | pgc | |
MD5:D9AF3B1DC12E7A40058F3733C6314B31 | SHA256:E6A199D71EC4937A402B848440F32F844D3588EE6D5FD95480A3551B4A470764 | |||
| 3700 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSD-{73E77584-B3E0-420E-AD0D-9050EF2B1E1F}.FSD | binary | |
MD5:3059E8B79AEB0CA938D4D3B42D141984 | SHA256:001286B9DCBAED0915238CCD24B99AA4D13BB4BB2FE0F36AAC444CB37912E47F | |||
| 3700 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:12396A3D307D5C6BE9640D2C3C212ABC | SHA256:4E2DDBB358BC4EFE7088F6FB5055EC6FA1206823D6ACC61D93FA2081F2A5C142 | |||
| 3700 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSF-{0E1EEE64-E8C6-4E2A-9759-63CF07FD8988}.FSF | binary | |
MD5:D471A0BB5F0B8A9AC834E0172491B7F9 | SHA256:418B6AE0A39787583DCD77DA0ED040F8C3DDA03410E71D04C235EE6E736F298F | |||
| 3700 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSF-CTBL.FSF | binary | |
MD5:D471A0BB5F0B8A9AC834E0172491B7F9 | SHA256:418B6AE0A39787583DCD77DA0ED040F8C3DDA03410E71D04C235EE6E736F298F | |||
| 3700 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-CNRY.FSD | binary | |
MD5:C755048248C2CEF7911850D0D4B2FB99 | SHA256:324259B6F3FC0994CFA6339CE3EC8ED63CE4C0EE306B1AC26FBC2F8AB4CED300 | |||
| 3700 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{0E56B2DA-FA3A-40DD-B208-5F657D97727C} | binary | |
MD5:C755048248C2CEF7911850D0D4B2FB99 | SHA256:324259B6F3FC0994CFA6339CE3EC8ED63CE4C0EE306B1AC26FBC2F8AB4CED300 | |||
| 3700 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:EE2C26DF9ACB657DEDF6F069B4B3C3CF | SHA256:63B2CA212AAE33F544A1F744EB1F66890D3864D95C5026BD0AC9ED1A069BF331 | |||
| 3700 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{84438EED-8754-48DC-A4AF-CC2B880F563D} | binary | |
MD5:CC05720BB861232393DF8AA6DBE4EDF9 | SHA256:A620D8C9D5C33BBF91FB0D29902CDDBBFED132A9924D2157CDD5BC917150DE5F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
28
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3700 | WINWORD.EXE | GET | 304 | 92.122.244.41:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e2c21fccbe1fe8c2 | unknown | — | — | unknown |
3700 | WINWORD.EXE | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
3700 | WINWORD.EXE | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 92.122.244.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 23.65.29.16:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?11acddbe1ebd82b3 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.52.162.42:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3700 | WINWORD.EXE | 104.21.74.191:443 | universalmovies.top | CLOUDFLARENET | — | unknown |
3700 | WINWORD.EXE | 92.122.244.41:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3700 | WINWORD.EXE | 142.250.184.227:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
816 | svchost.exe | 104.21.74.191:443 | universalmovies.top | CLOUDFLARENET | — | unknown |
1372 | svchost.exe | 92.122.244.42:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.52.162.42:80 | www.microsoft.com | AKAMAI-AS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
universalmovies.top |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |