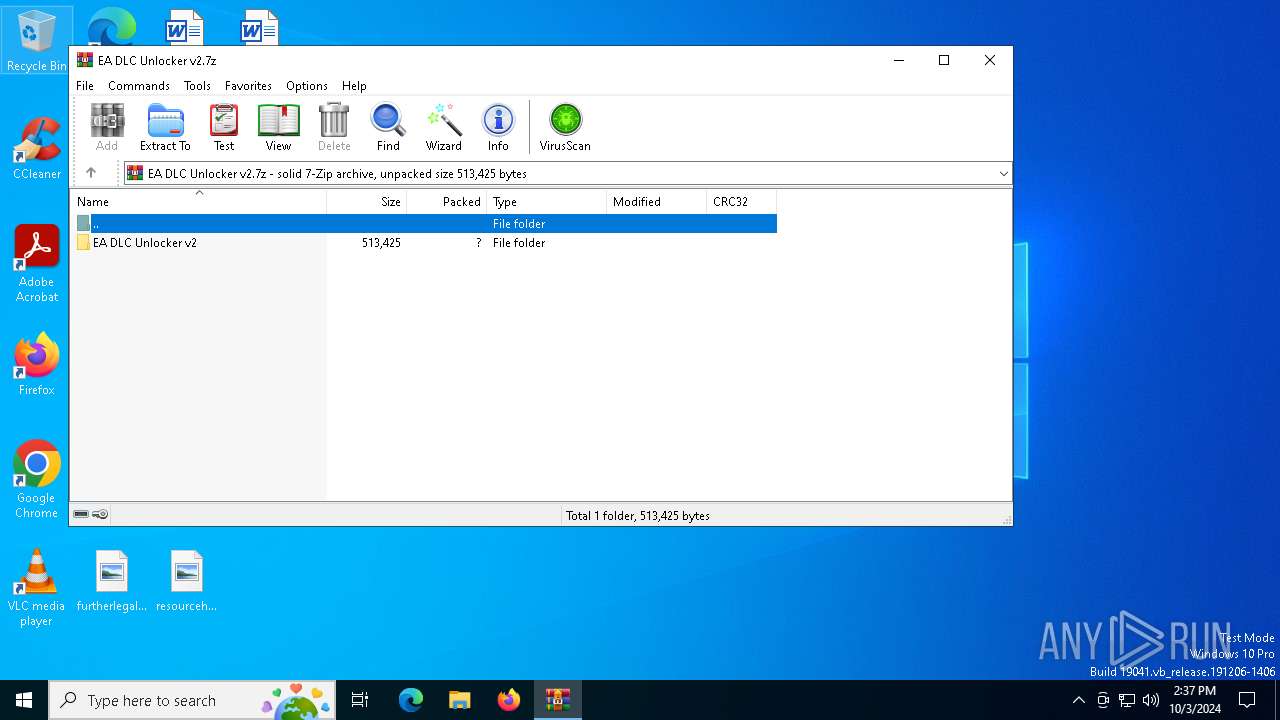
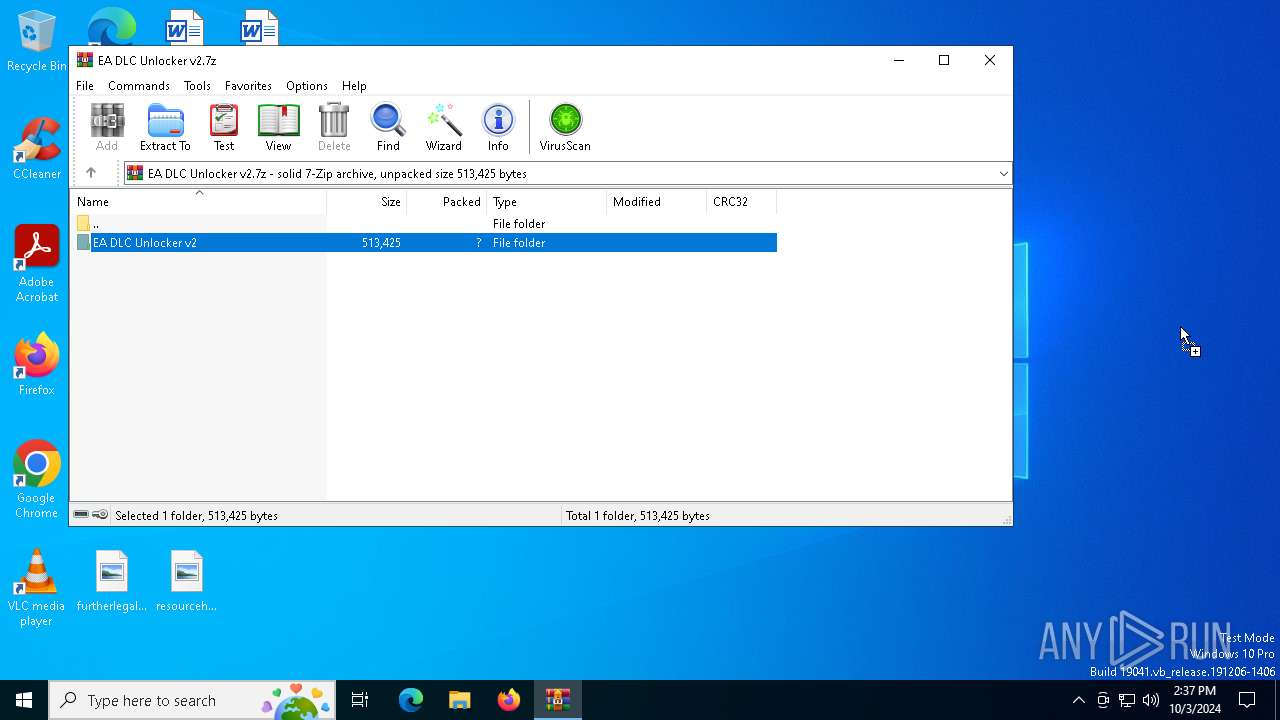
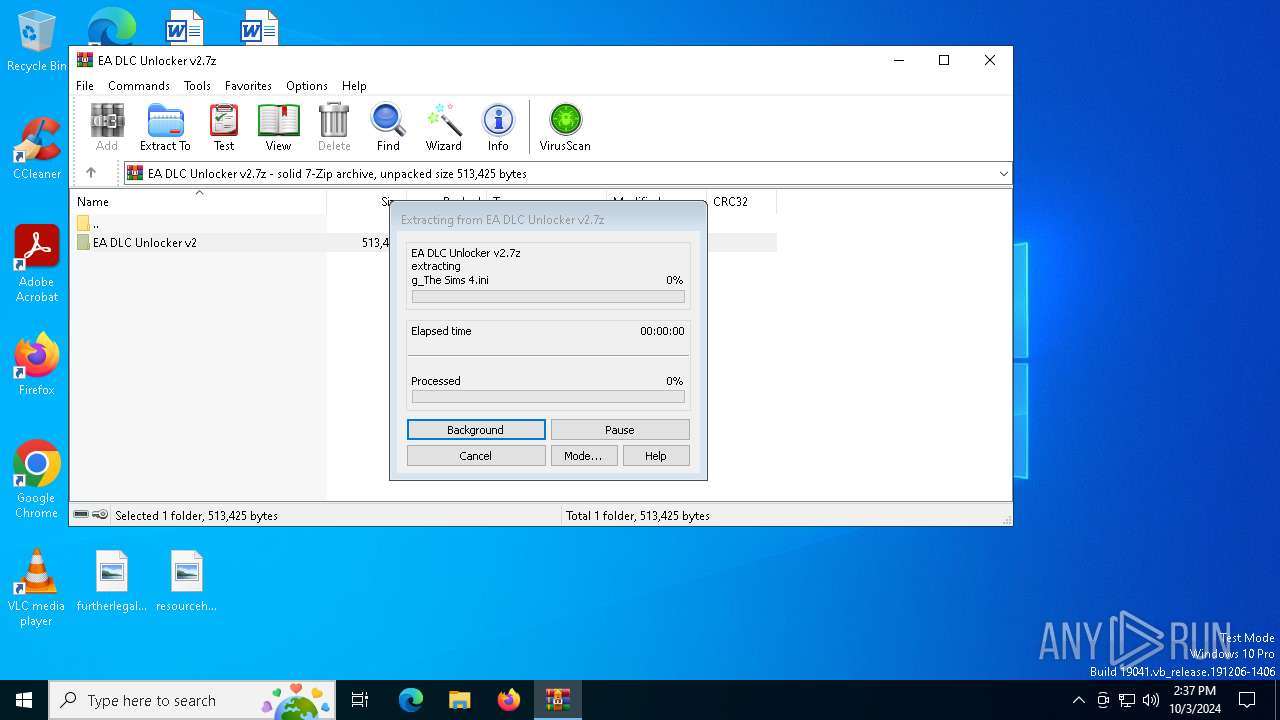
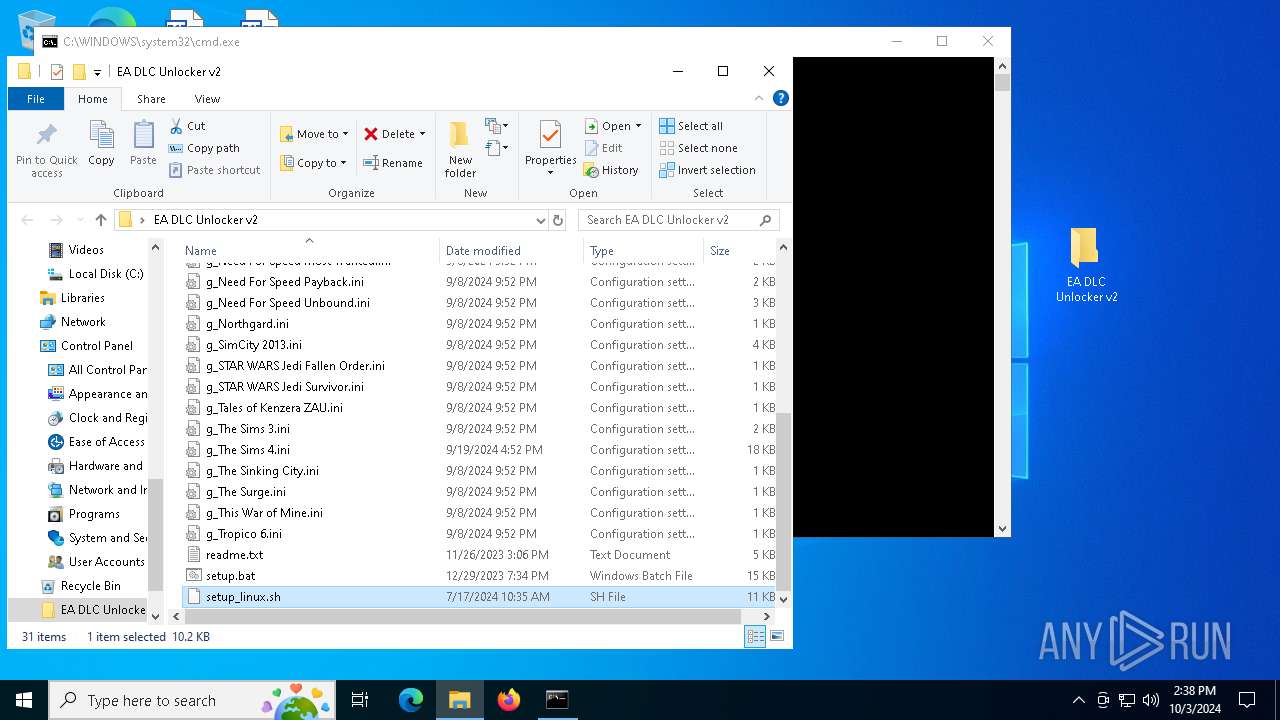
| File name: | EA DLC Unlocker v2.7z |
| Full analysis: | https://app.any.run/tasks/ab1f26a1-efc0-4f88-b3f5-50deced0fb51 |
| Verdict: | Malicious activity |
| Analysis date: | October 03, 2024, 14:37:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | B3EC91F0A176FF78AC47CD18D4E14973 |
| SHA1: | 9E61AE417AF00341EF898C4A79158EDB22639D54 |
| SHA256: | B08408BF00892E50EDB5C312A989DB4A9674074E38B20CEA8681503EFAEC1394 |
| SSDEEP: | 6144:Emc1+OLIuFYVc7kQA784g+Y8hFfz7oCSgw70Kqt+IE26O:q+O8uFUcTQ8V27fYCSXMya |
MALICIOUS
No malicious indicators.SUSPICIOUS
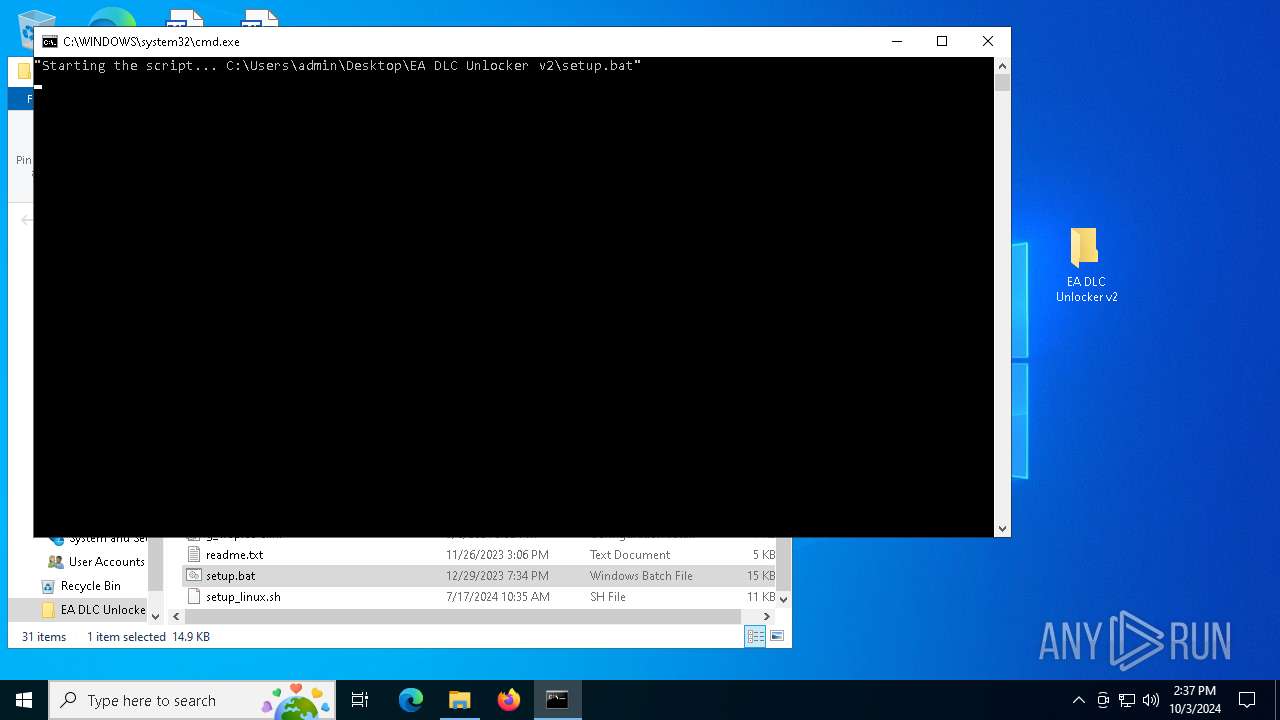
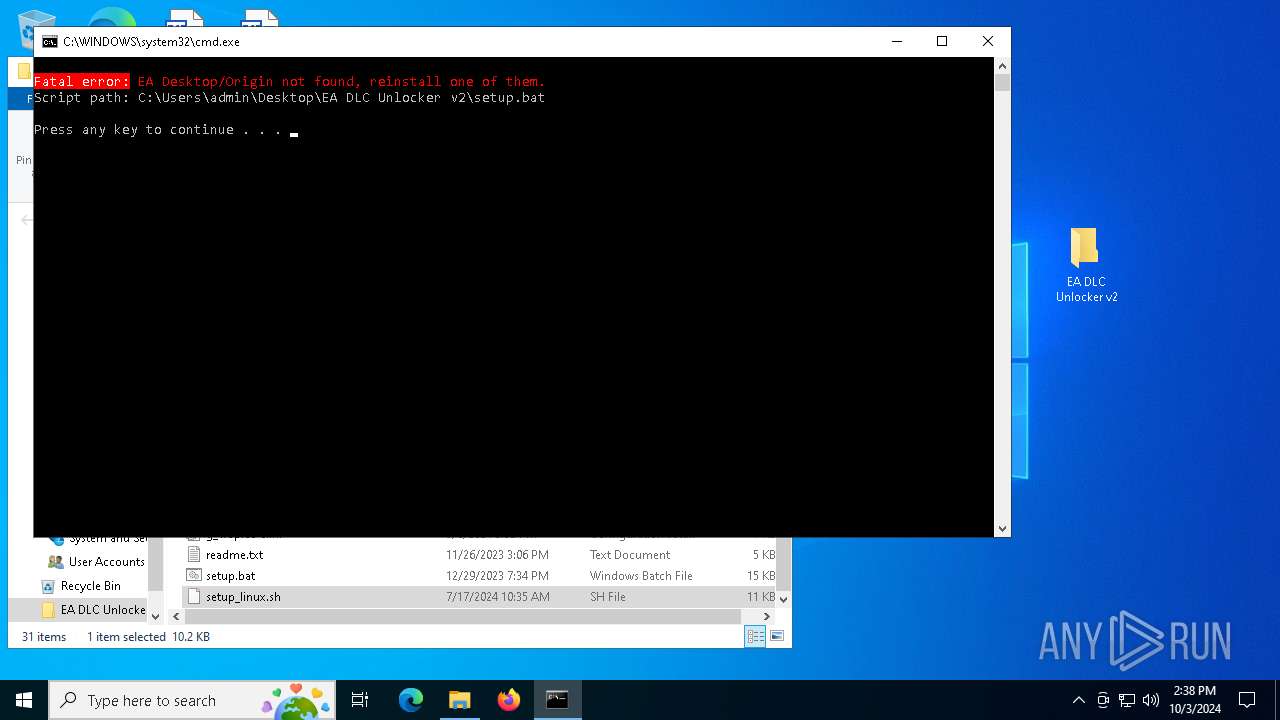
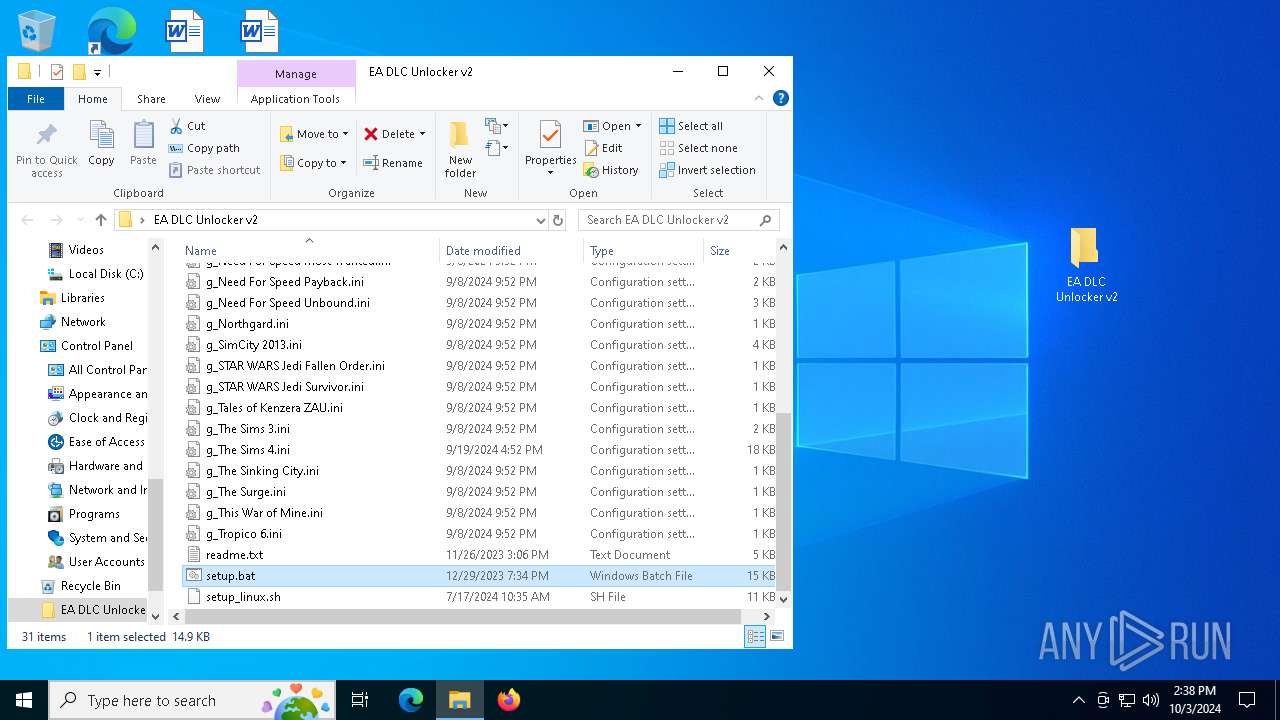
Application launched itself
- cmd.exe (PID: 6796)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6796)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6796)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6796)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 6796)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6796)
INFO
Manual execution by a user
- cmd.exe (PID: 6796)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
142
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
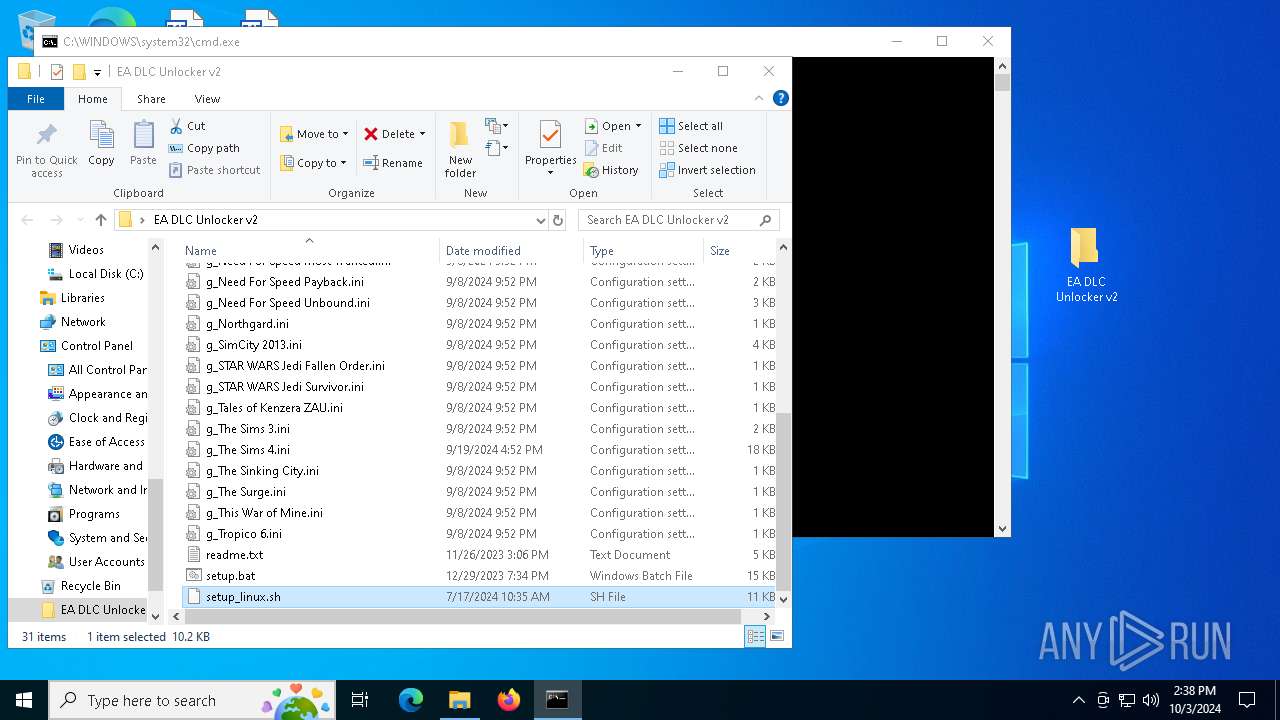
| 908 | powershell -noprofile "$_PSCommandPath = [Environment]::GetEnvironmentVariable('script_path', 'Process'); iex ((Get-Content -LiteralPath $_PSCommandPath) | out-string)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo "C:\Users\admin\Desktop\EA DLC Unlocker v2\" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1460 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo marco " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | findstr /V /C:"polo" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2776 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo marco " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4224 | findstr /C:"polo" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4248 | findstr /V /C:"C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6128 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\EA DLC Unlocker v2.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6648 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6796 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\EA DLC Unlocker v2\setup.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 578
Read events
6 562
Write events
16
Delete events
0
Modification events
| (PID) Process: | (6128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\EA DLC Unlocker v2.7z | |||
| (PID) Process: | (6128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
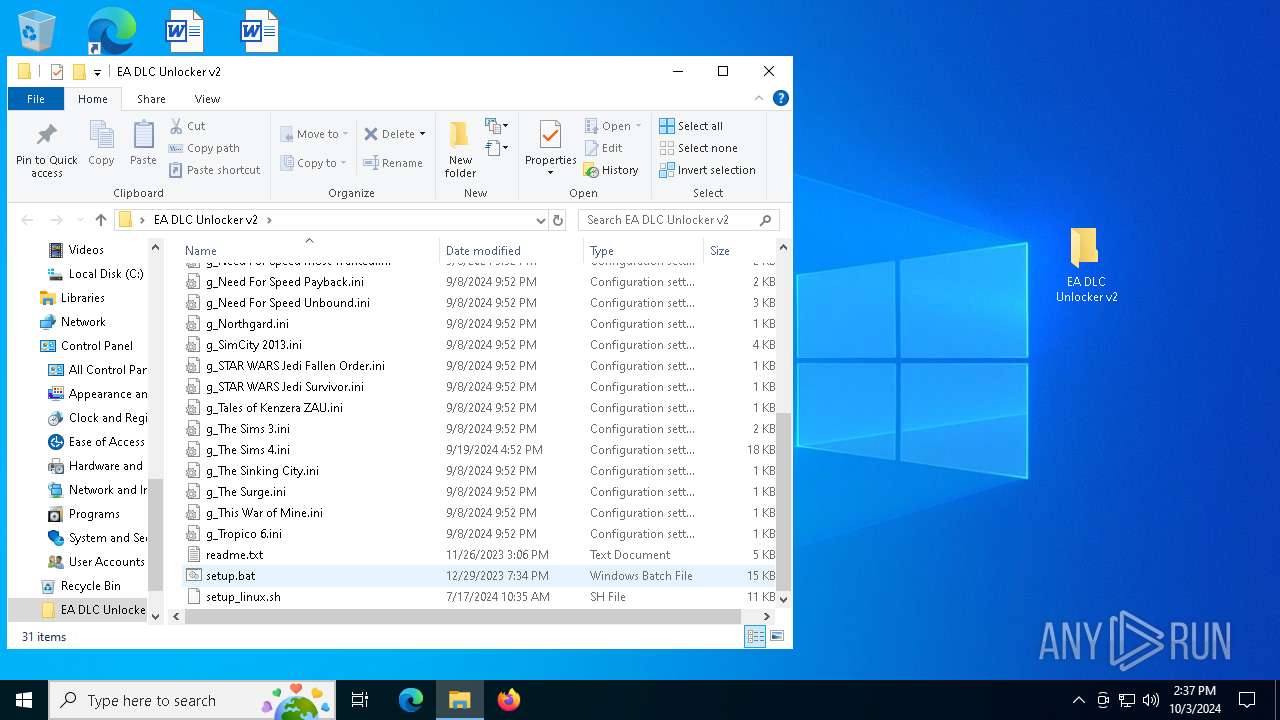
Executable files
2
Suspicious files
1
Text files
31
Unknown types
0
Dropped files
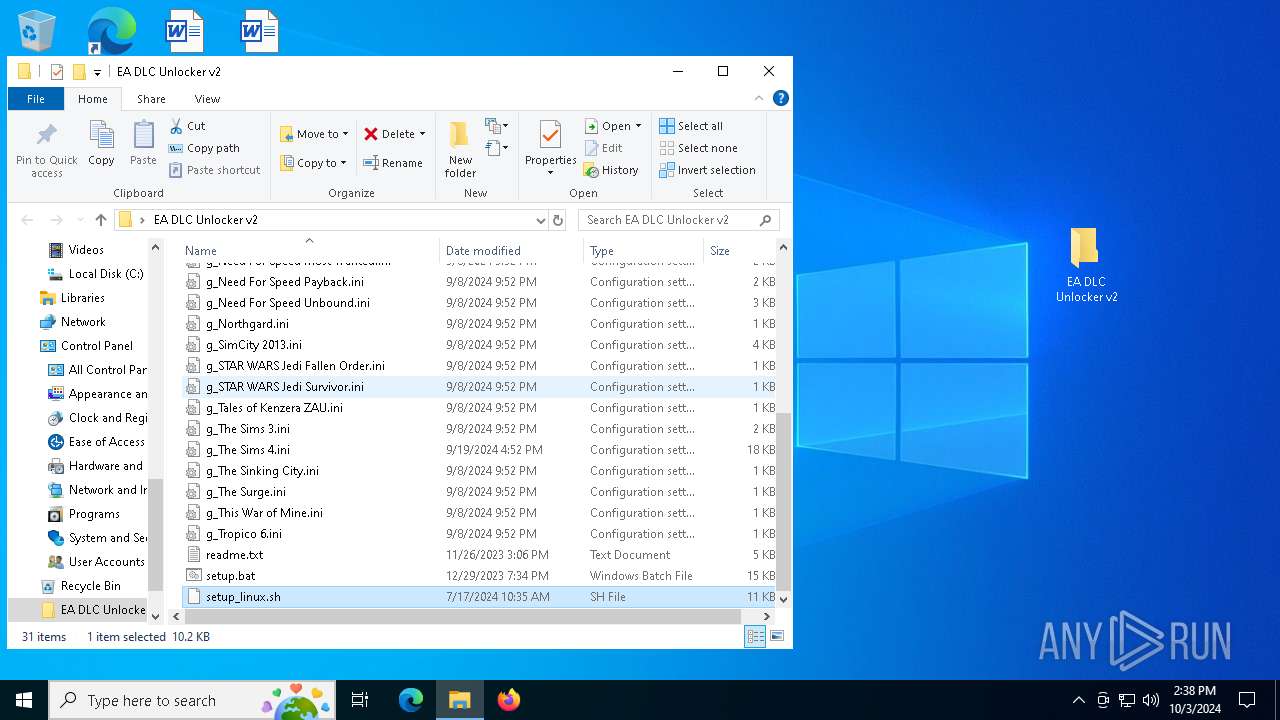
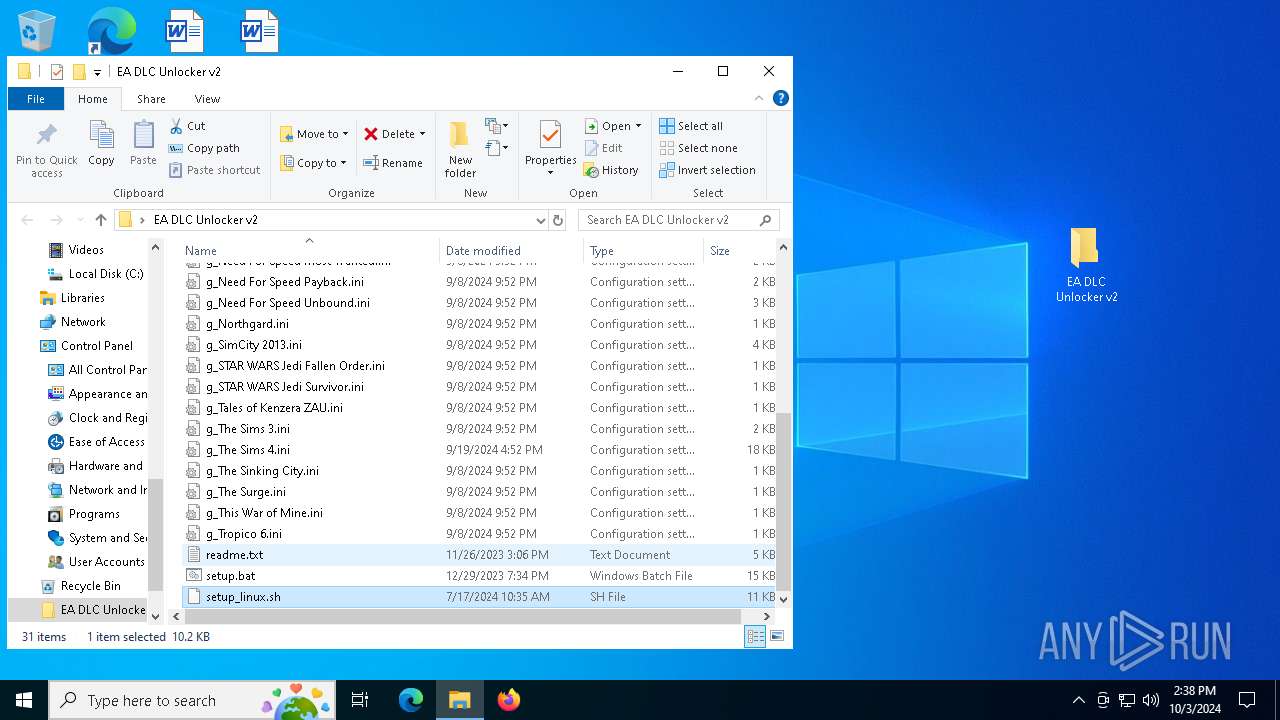
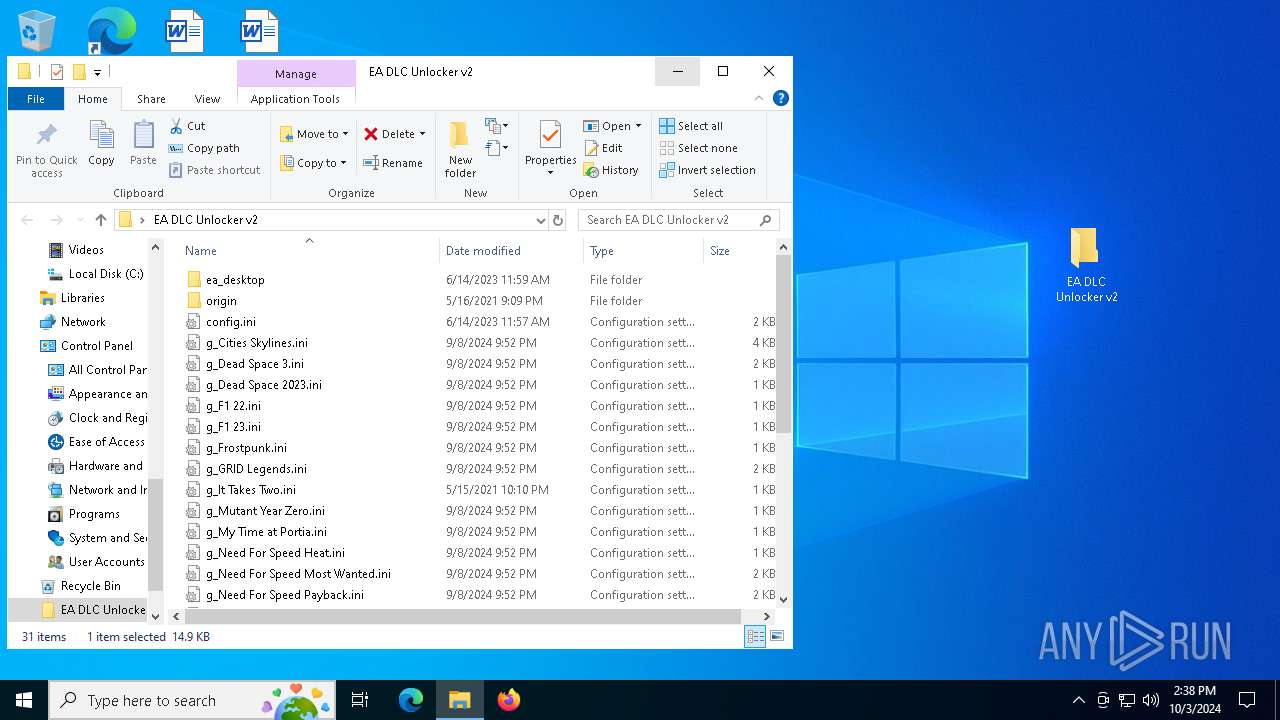
PID | Process | Filename | Type | |
|---|---|---|---|---|
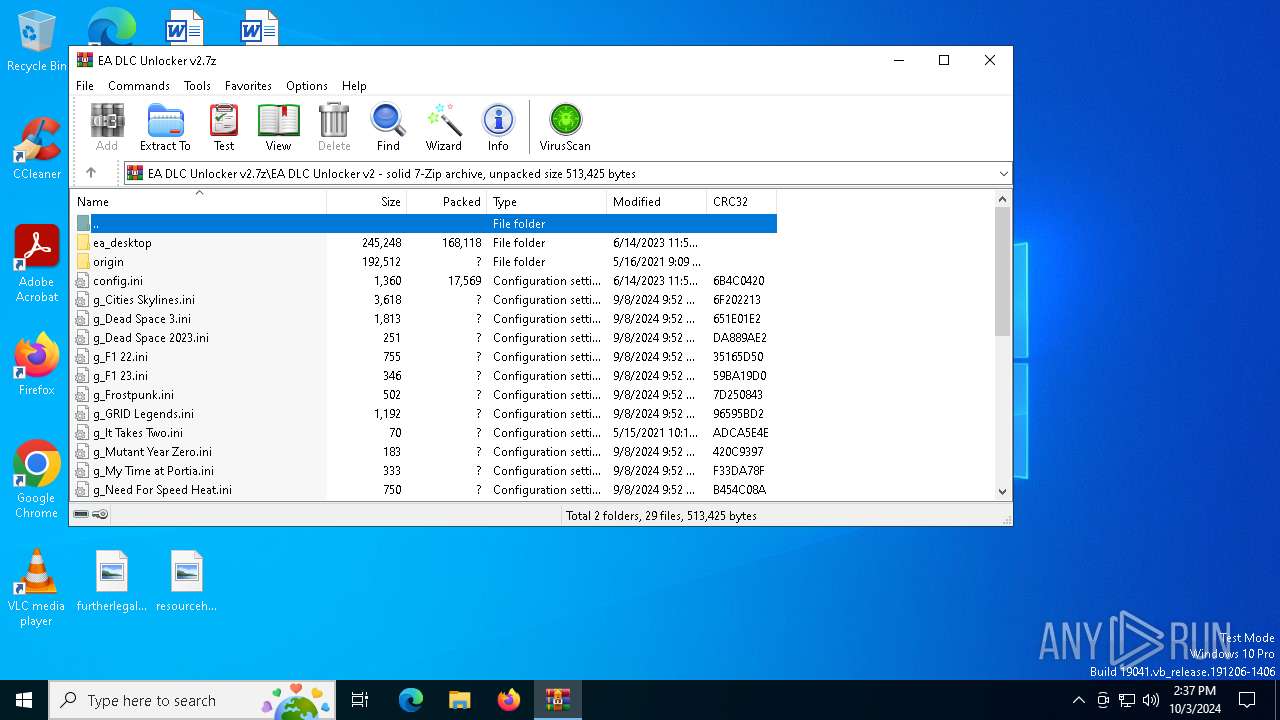
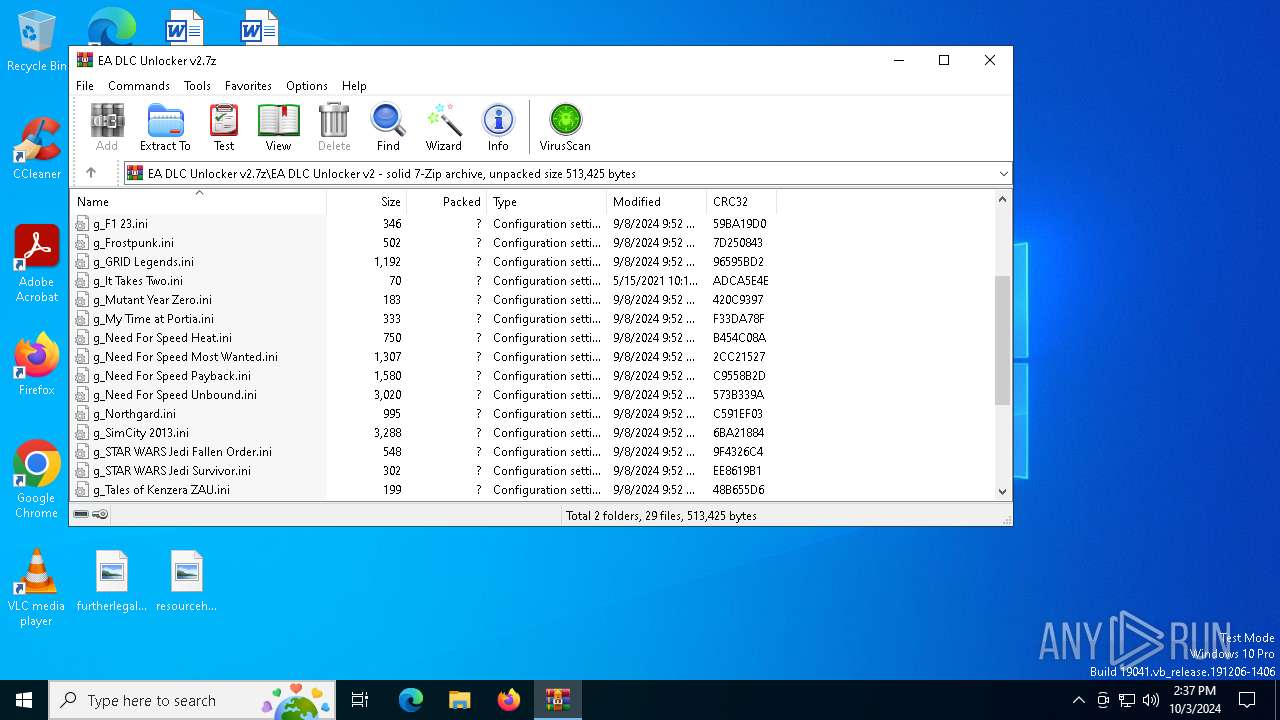
| 6128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6128.7946\EA DLC Unlocker v2\g_My Time at Portia.ini | text | |
MD5:EDE7B7058E8C95575EF5517D36784FE2 | SHA256:D7812CD7633CBC13521C9D7A862541EB13A93A8F42D1E56137D4BE8D7225F90A | |||
| 6128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6128.7946\EA DLC Unlocker v2\g_Frostpunk.ini | text | |
MD5:FB2516CAACEBCDB02E9F2194BA72DE12 | SHA256:8A28296795FC669C047ED3AFBEB82791C4C86D3160B5A6843A144D814AE578C2 | |||
| 6128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6128.7946\EA DLC Unlocker v2\g_Dead Space 3.ini | text | |
MD5:19F5DEDA4368C463D16687109ABF543D | SHA256:8996053E41CE56F0822A2A3E9449F3960FF1D395C6587ACDDB608AB306A3E6EE | |||
| 6128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6128.7946\EA DLC Unlocker v2\g_Need For Speed Heat.ini | text | |
MD5:C11C8268AA87FD021F691D4AE9529CCB | SHA256:FDA16758BDF3AA61BAA0B598BD419F1DAE695787D8F8DD9DA8FEA4629BF041D2 | |||
| 6128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6128.7946\EA DLC Unlocker v2\g_GRID Legends.ini | text | |
MD5:C2DC8A3DF7745FC6BAFB633D4EA33FB5 | SHA256:1D958849692862C419812DBF80570EDB694F7C7E1C4758B6FA897BE09C705B08 | |||
| 6128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6128.7946\EA DLC Unlocker v2\g_F1 22.ini | text | |
MD5:51FFF0FDF96929ECE2B1CA964D006550 | SHA256:8EE50A42AF9C0C5C2A9D520173B262C983E6DE716D5EB1C753687FF3170686DB | |||
| 6128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6128.7946\EA DLC Unlocker v2\g_Need For Speed Most Wanted.ini | text | |
MD5:53020D0FF8E79EE8305061D5D3964927 | SHA256:070AC609263921F4C91061F8C8DDD78A3305038EC3F13F4FE265AE715F2C0B89 | |||
| 6128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6128.7946\EA DLC Unlocker v2\g_It Takes Two.ini | text | |
MD5:31561ACF01F495280B2E03EC26B7812F | SHA256:3435BE593EE7214A75789417B0B6E90FB7939B26DC43A8CCA197620E72EC48AF | |||
| 6128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6128.7946\EA DLC Unlocker v2\g_F1 23.ini | text | |
MD5:18416EFA57D527355F065064172A821D | SHA256:CFBE14FC02F08A2B941DB25DE2379A5849CEDA301E529514004948D0088945FA | |||
| 6128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6128.7946\EA DLC Unlocker v2\g_STAR WARS Jedi Fallen Order.ini | text | |
MD5:473C794E2D9CE2A2A68879595B0E7F04 | SHA256:06C8F383E8383C4B17362710E666D76BBC90FEAB913D0B85C96588BFB8E84C02 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
41
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6200 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2508 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6200 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2088 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2280 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4324 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2280 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2088 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |