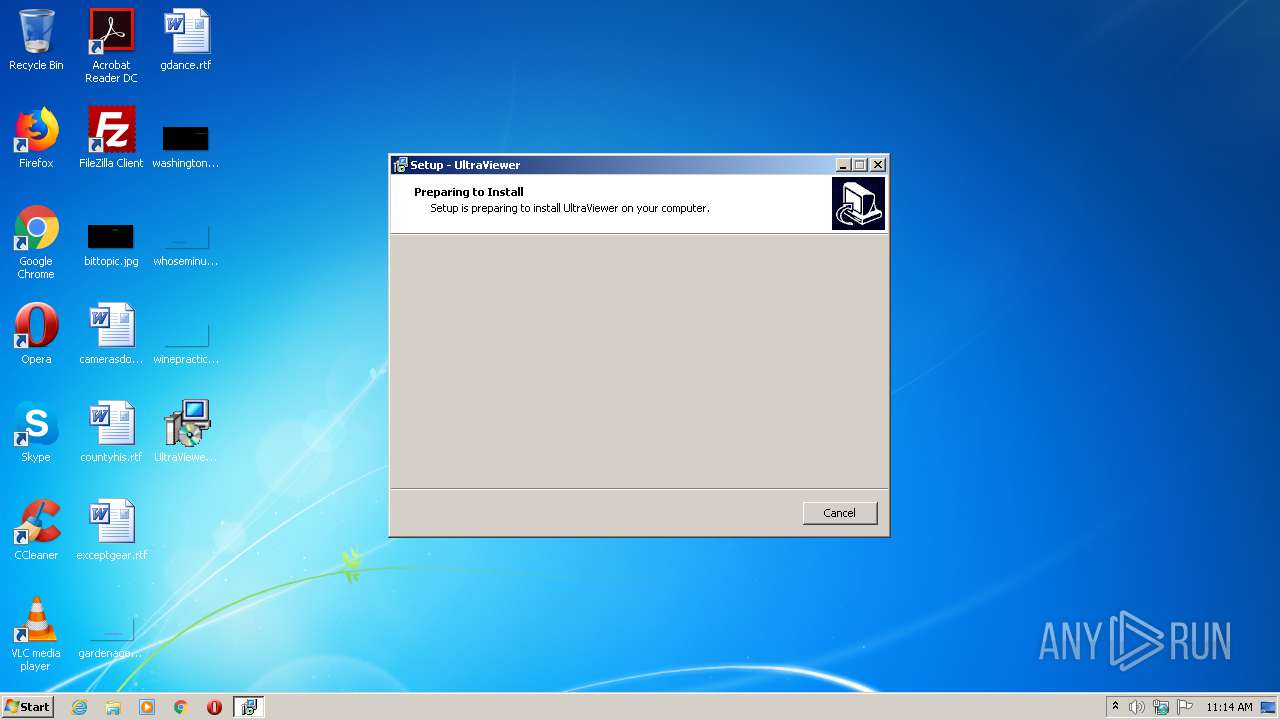
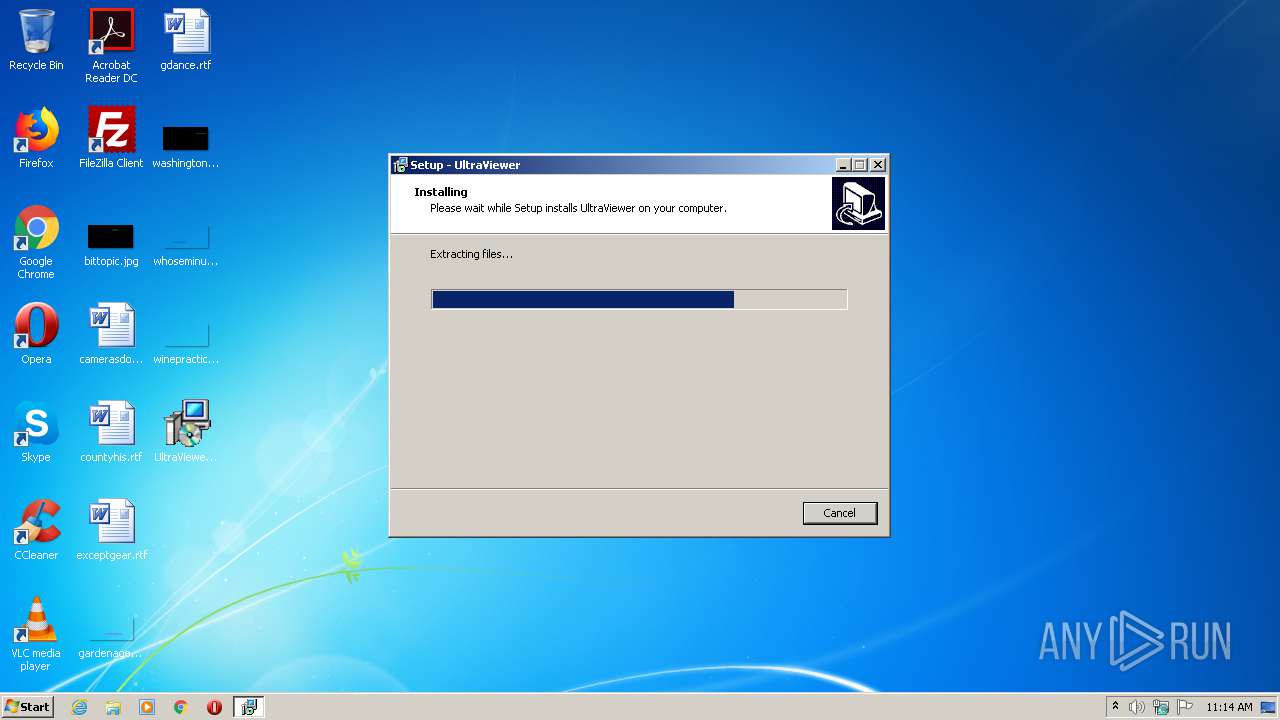
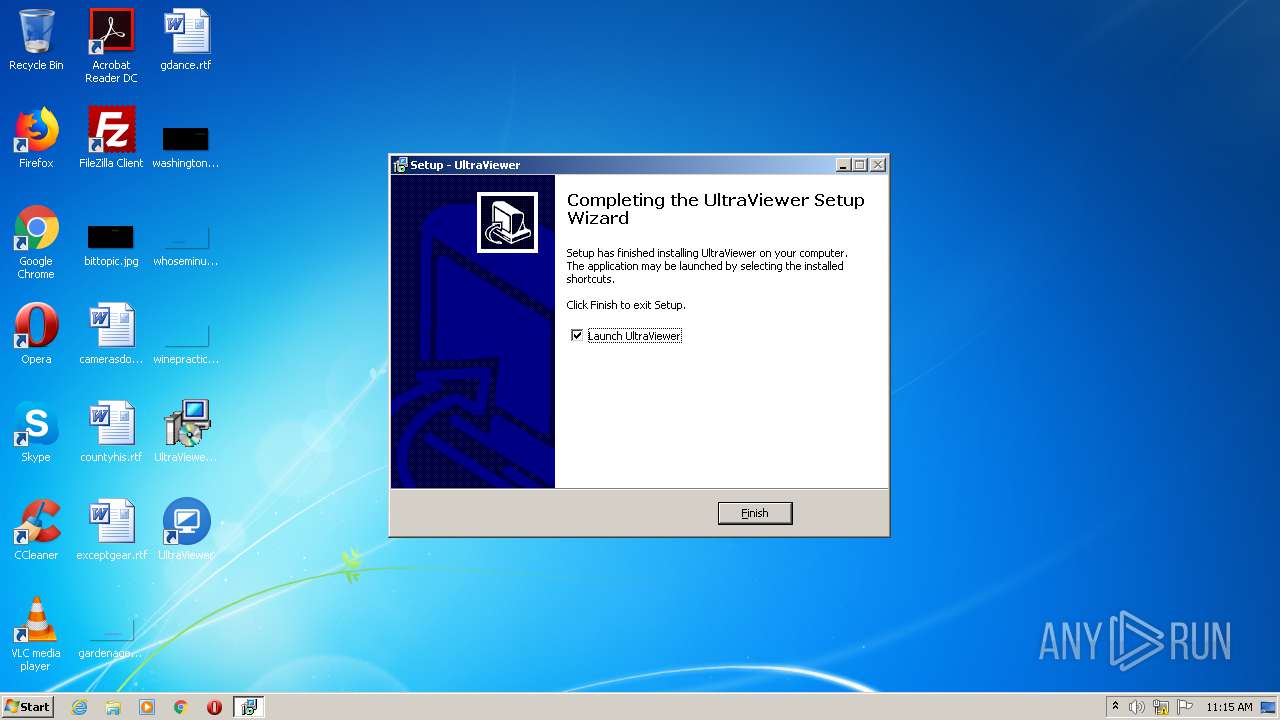
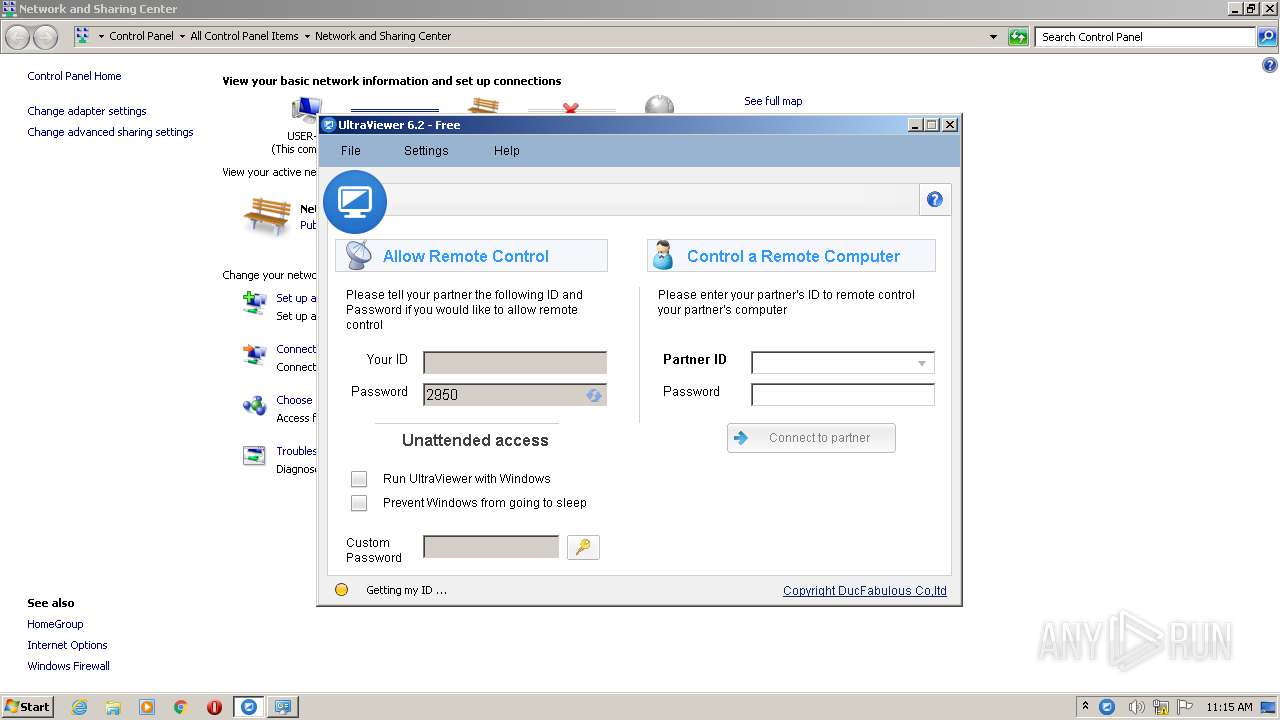
| File name: | UltraViewer_setup_6.2_en.exe |
| Full analysis: | https://app.any.run/tasks/f41d89a5-2ce4-4d2f-9f37-c57e9a26fb03 |
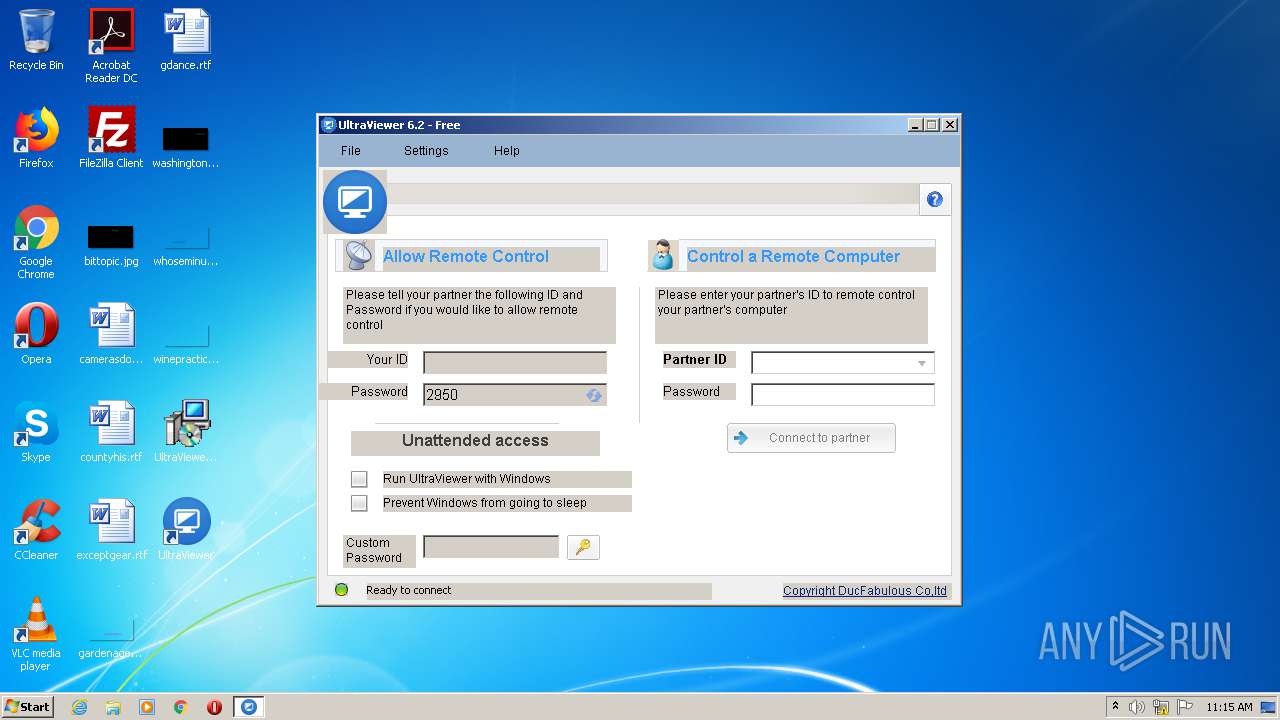
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 10:13:43 |
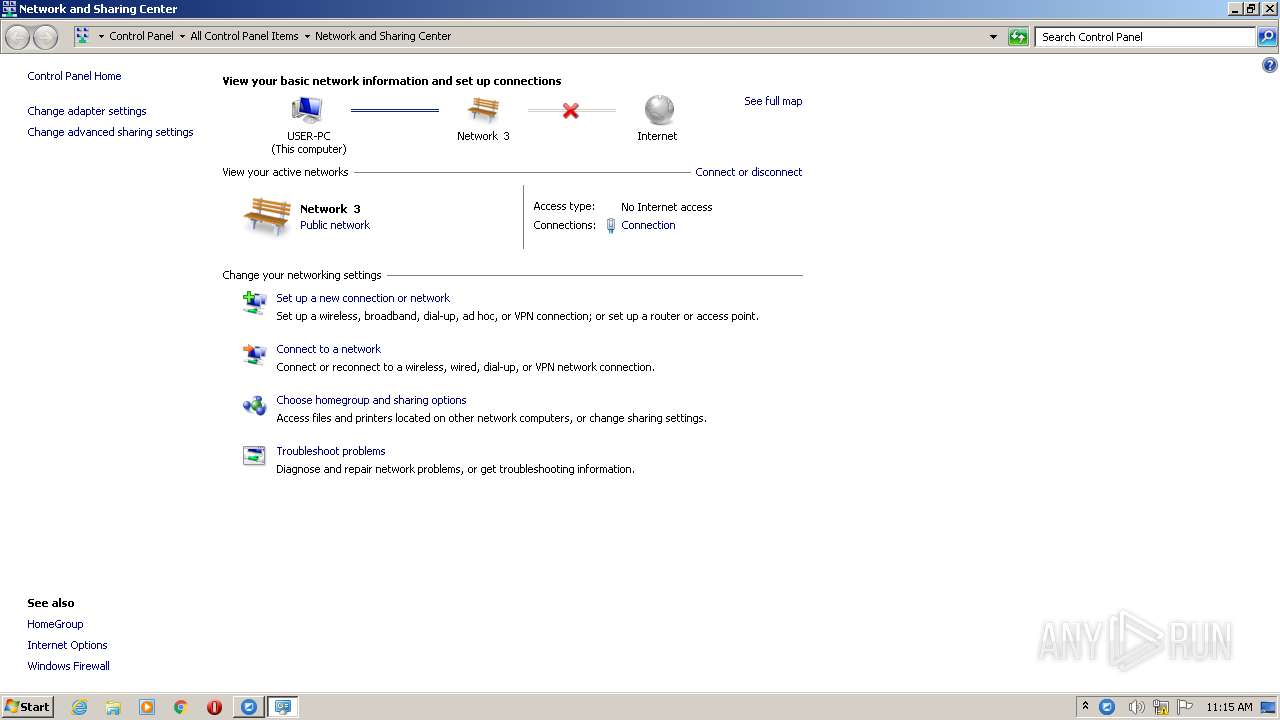
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B486FC29C5B6E30CE880795A5C91DCCB |
| SHA1: | 266A39E10735AB82EEEFA6D7A52E0D29C0215162 |
| SHA256: | B07BAEE9B2D75E3F53366FD716C127F32A302DEDC7B8A9FE3E01704688ACE5A1 |
| SSDEEP: | 49152:c454R8WCa3CTb9x0SxQimDVwJdTGSFLJYNEHyLeHBT9o7awlJW6ylqnLSKhj0C:j54JCoONQi4MdqgLJYeSkBTKWwDqlqLP |
MALICIOUS
Starts NET.EXE for service management
- UltraViewer_setup_6.2_en.tmp (PID: 3404)
Loads dropped or rewritten executable
- regasm.exe (PID: 2224)
- UltraViewer_Desktop.exe (PID: 2240)
- UltraViewer_Desktop.exe (PID: 4044)
- RegAsm.exe (PID: 2404)
- RegAsm.exe (PID: 3952)
- taskhost.exe (PID: 1960)
- ctfmon.exe (PID: 576)
- UltraViewer_Desktop.exe (PID: 2680)
- UltraViewer_Desktop.exe (PID: 3580)
- taskeng.exe (PID: 1976)
- dwm.exe (PID: 2036)
- msdt.exe (PID: 2164)
- conhost.exe (PID: 3152)
- explorer.exe (PID: 324)
- ipconfig.exe (PID: 2352)
- UltraViewer_Desktop.exe (PID: 2276)
- regasm.exe (PID: 3436)
Application was dropped or rewritten from another process
- UltraViewer_Desktop.exe (PID: 2240)
- UltraViewer_Desktop.exe (PID: 4044)
- UltraViewer_Service.exe (PID: 2896)
- UltraViewer_Desktop.exe (PID: 2276)
- UltraViewer_Desktop.exe (PID: 2680)
- UltraViewer_Desktop.exe (PID: 3580)
Starts Visual C# compiler
- sdiagnhost.exe (PID: 3960)
SUSPICIOUS
Reads the Windows organization settings
- UltraViewer_setup_6.2_en.tmp (PID: 3404)
Executable content was dropped or overwritten
- UltraViewer_setup_6.2_en.exe (PID: 3584)
- UltraViewer_setup_6.2_en.exe (PID: 3060)
- UltraViewer_setup_6.2_en.tmp (PID: 3404)
- msdt.exe (PID: 2164)
Reads Windows owner or organization settings
- UltraViewer_setup_6.2_en.tmp (PID: 3404)
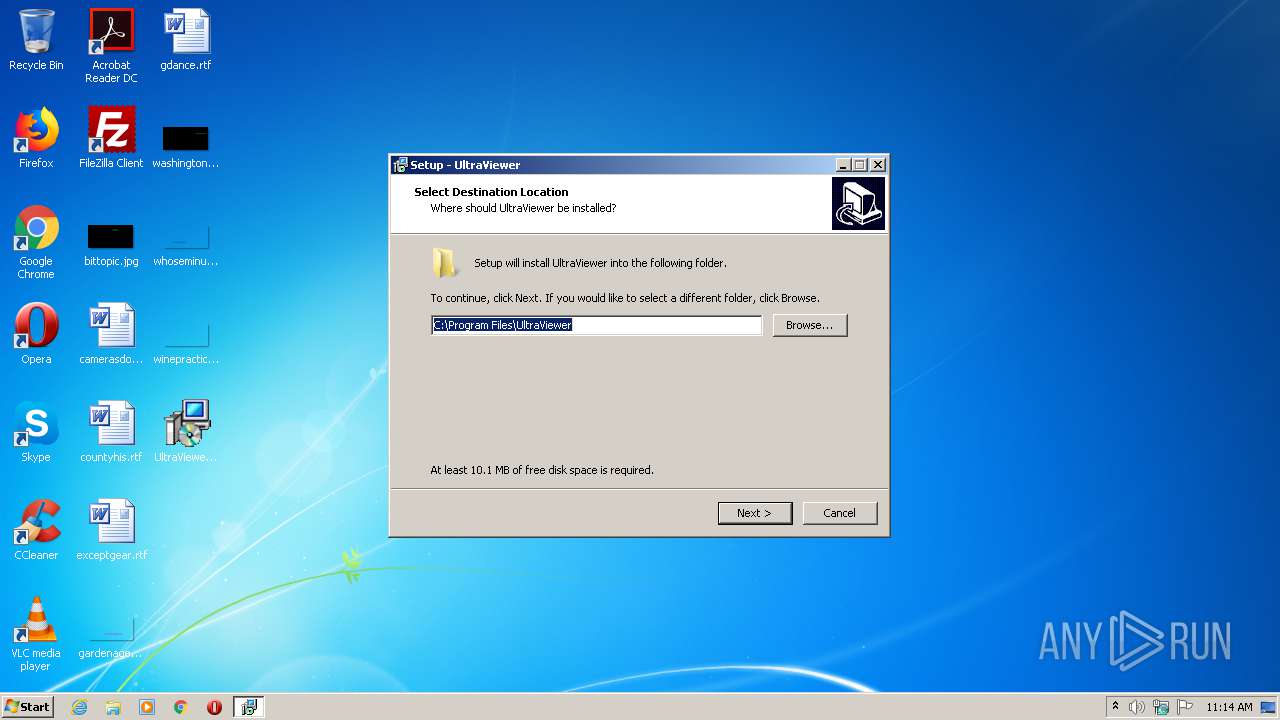
Creates files in the program directory
- regasm.exe (PID: 2224)
- UltraViewer_Service.exe (PID: 2896)
- regasm.exe (PID: 3436)
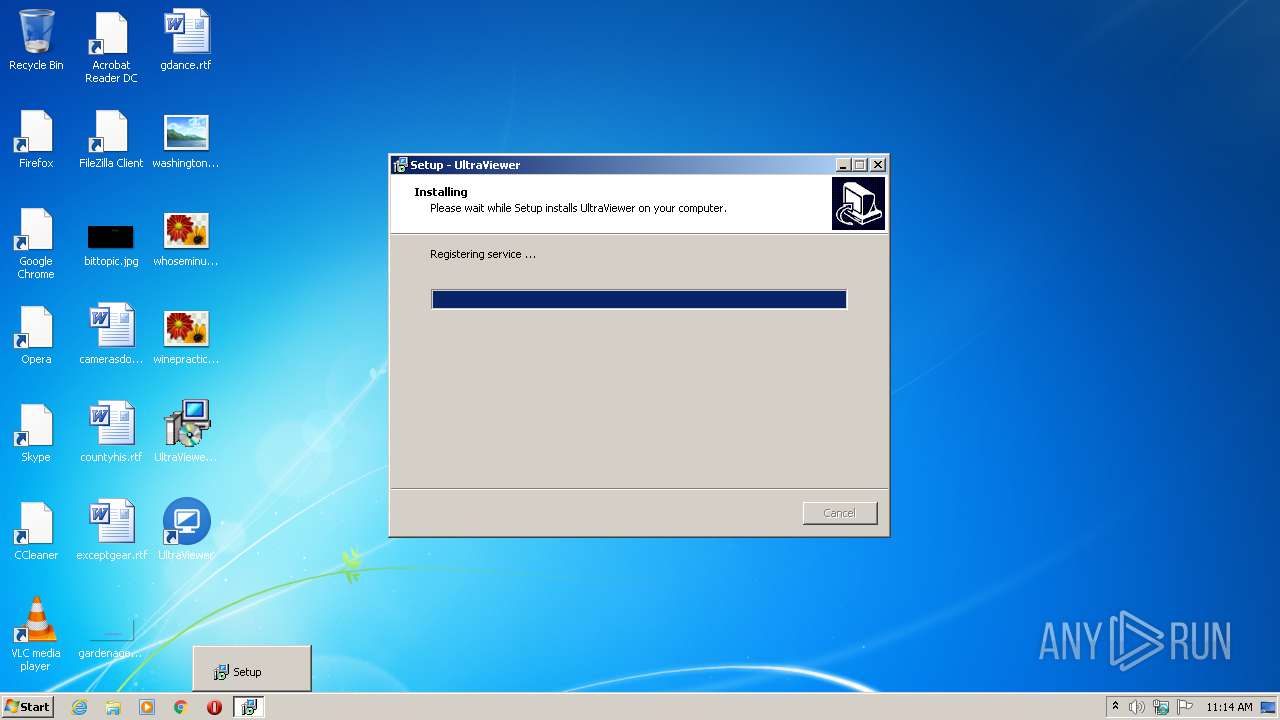
Starts SC.EXE for service management
- UltraViewer_Desktop.exe (PID: 2240)
- UltraViewer_setup_6.2_en.tmp (PID: 3404)
Executed as Windows Service
- UltraViewer_Service.exe (PID: 2896)
- UI0Detect.exe (PID: 3124)
Modifies the open verb of a shell class
- UltraViewer_Desktop.exe (PID: 2240)
Application launched itself
- UI0Detect.exe (PID: 3124)
Creates COM task schedule object
- RegAsm.exe (PID: 2404)
- RegAsm.exe (PID: 3952)
- regasm.exe (PID: 3436)
Reads internet explorer settings
- UltraViewer_Desktop.exe (PID: 2680)
Low-level read access rights to disk partition
- UltraViewer_Service.exe (PID: 2896)
Creates files in the user directory
- UltraViewer_Desktop.exe (PID: 2680)
- explorer.exe (PID: 324)
Creates files in the Windows directory
- UltraViewer_Desktop.exe (PID: 3580)
Reads Environment values
- UltraViewer_Desktop.exe (PID: 2680)
Changes settings of the software policy
- UltraViewer_Desktop.exe (PID: 3580)
Executed via COM
- sdiagnhost.exe (PID: 3960)
Reads Internet Cache Settings
- taskhost.exe (PID: 1960)
Uses IPCONFIG.EXE to discover IP address
- sdiagnhost.exe (PID: 3960)
Uses TASKKILL.EXE to kill process
- UltraViewer_setup_6.2_en.tmp (PID: 3404)
INFO
Application was dropped or rewritten from another process
- UltraViewer_setup_6.2_en.tmp (PID: 2784)
- UltraViewer_setup_6.2_en.tmp (PID: 3404)
Loads dropped or rewritten executable
- UltraViewer_setup_6.2_en.tmp (PID: 3404)
Creates files in the program directory
- UltraViewer_setup_6.2_en.tmp (PID: 3404)
Creates a software uninstall entry
- UltraViewer_setup_6.2_en.tmp (PID: 3404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
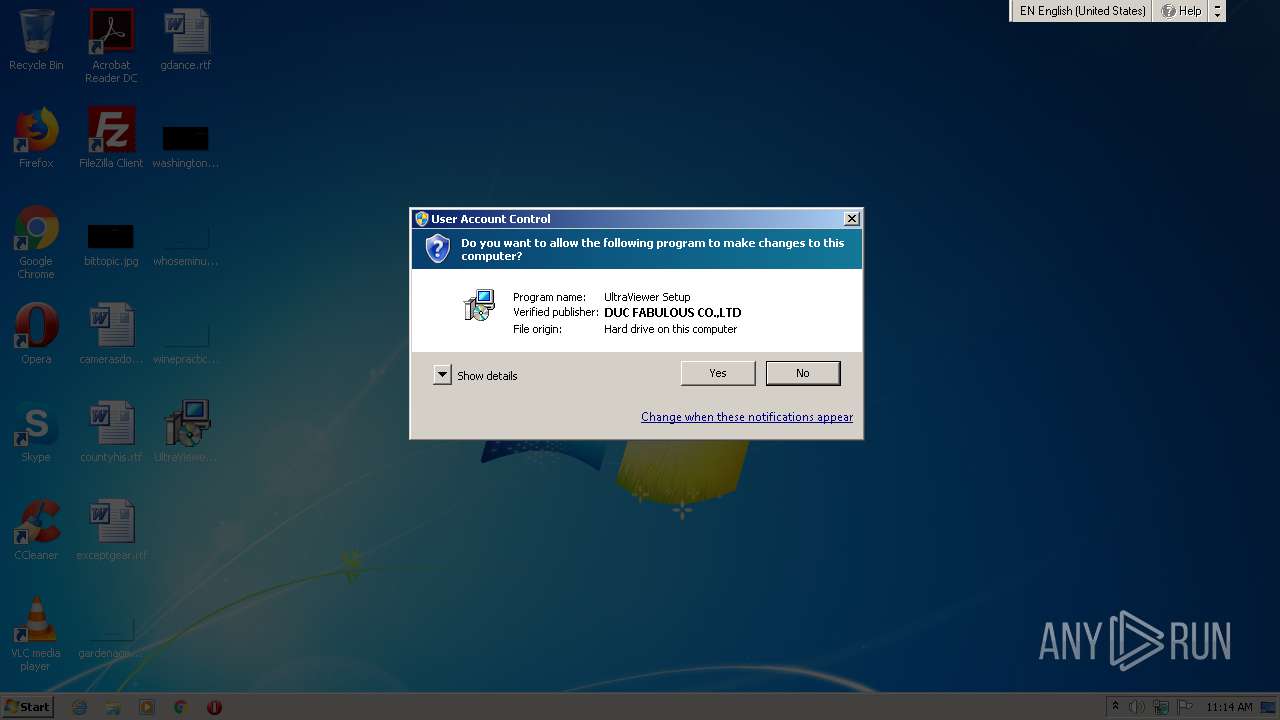
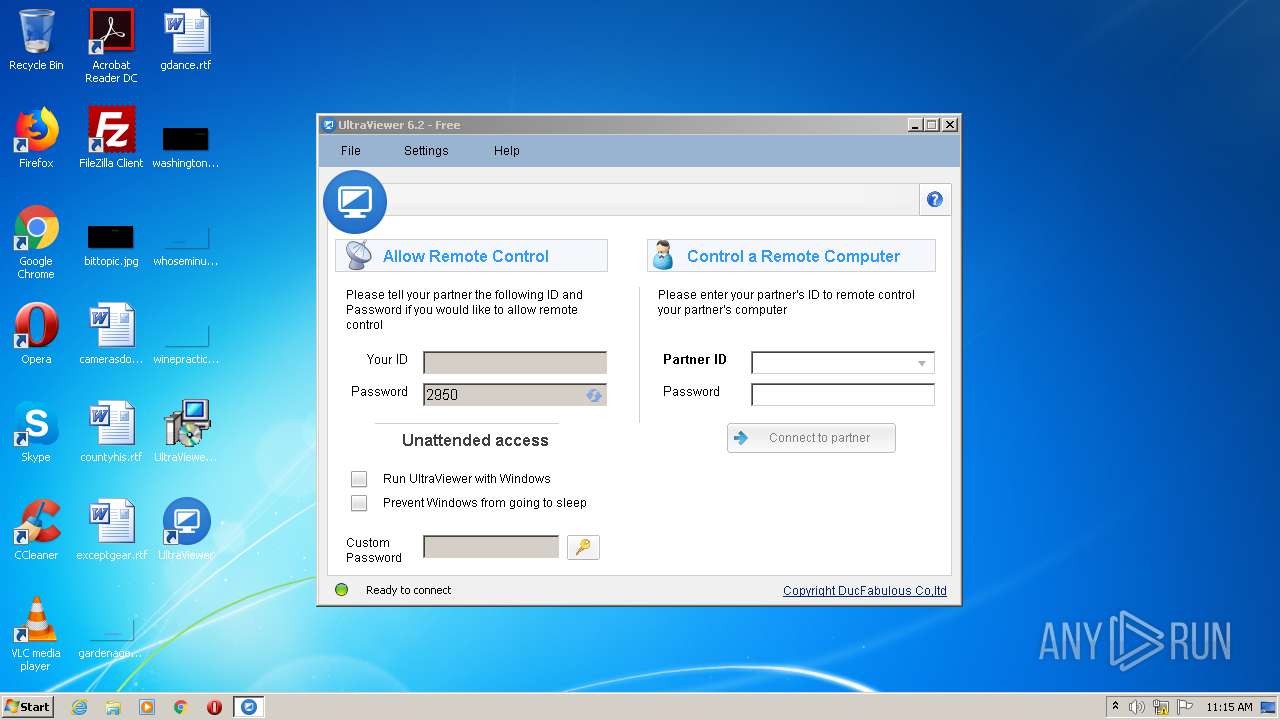
| CompanyName: | DucFabulous |
| FileDescription: | UltraViewer Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | UltraViewer |
| ProductVersion: | 6.2.98 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | DucFabulous |
| FileDescription: | UltraViewer Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | UltraViewer |
| ProductVersion: | 6.2.98 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.14096 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
244
Monitored processes
118
Malicious processes
15
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "taskkill.exe" /f /im "UltraViewer_Desktop.exe" | C:\Windows\system32\taskkill.exe | — | UltraViewer_setup_6.2_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 704 | "taskkill.exe" /f /im "UltraViewer_Desktop.exe" | C:\Windows\system32\taskkill.exe | — | UltraViewer_setup_6.2_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 792 | "taskkill.exe" /f /im "UltraViewer_Desktop.exe" | C:\Windows\system32\taskkill.exe | — | UltraViewer_setup_6.2_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1084 | "taskkill.exe" /f /im "UltraViewer_Desktop.exe" | C:\Windows\system32\taskkill.exe | — | UltraViewer_setup_6.2_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | "taskkill.exe" /f /im "UltraViewer_Desktop.exe" | C:\Windows\system32\taskkill.exe | — | UltraViewer_setup_6.2_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1564 | "taskkill.exe" /f /im "UltraViewer_Desktop.exe" | C:\Windows\system32\taskkill.exe | — | UltraViewer_setup_6.2_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1960 | "taskhost.exe" | C:\Windows\System32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1976 | taskeng.exe {FB2255A4-DCBF-45C3-86D6-8343D8697C84} | C:\Windows\System32\taskeng.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 900
Read events
6 493
Write events
4 396
Delete events
11
Modification events
| (PID) Process: | (3404) UltraViewer_setup_6.2_en.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 4C0D0000F68DFBBFC9A6D601 | |||
| (PID) Process: | (3404) UltraViewer_setup_6.2_en.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 19F98A6512D2C4D995A187B5E3A7B3A91324EEF1F3DD7E51EBA3C7D6B247DE8C | |||
| (PID) Process: | (3404) UltraViewer_setup_6.2_en.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3404) UltraViewer_setup_6.2_en.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\UltraViewer\HtmlAgilityPack.dll | |||
| (PID) Process: | (3404) UltraViewer_setup_6.2_en.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 2B1C71F3C68080A7251A0A17347354943008B7EA69CFE13C1CD4DA4F70901591 | |||
| (PID) Process: | (3436) regasm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3436) regasm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3436) regasm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\RemoteControl.ComRegistrationException |
| Operation: | write | Name: | (default) |
Value: RemoteControl.ComRegistrationException | |||
| (PID) Process: | (3436) regasm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\RemoteControl.ComRegistrationException\CLSID |
| Operation: | write | Name: | (default) |
Value: {1CA5DE22-F295-3F03-8D69-018007836F60} | |||
| (PID) Process: | (3436) regasm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{1CA5DE22-F295-3F03-8D69-018007836F60} |
| Operation: | write | Name: | (default) |
Value: RemoteControl.ComRegistrationException | |||
Executable files
19
Suspicious files
6
Text files
110
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3404 | UltraViewer_setup_6.2_en.tmp | C:\Program Files\UltraViewer\is-BIRS8.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | UltraViewer_setup_6.2_en.tmp | C:\Program Files\UltraViewer\is-HPHS6.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | UltraViewer_setup_6.2_en.tmp | C:\Program Files\UltraViewer\is-MMU03.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | UltraViewer_setup_6.2_en.tmp | C:\Program Files\UltraViewer\is-J1P8U.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | UltraViewer_setup_6.2_en.tmp | C:\Program Files\UltraViewer\is-RD2VE.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | UltraViewer_setup_6.2_en.tmp | C:\Program Files\UltraViewer\is-Q1232.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | UltraViewer_setup_6.2_en.tmp | C:\Program Files\UltraViewer\is-H9ELI.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | UltraViewer_setup_6.2_en.tmp | C:\Program Files\UltraViewer\is-HIAJ9.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | UltraViewer_setup_6.2_en.tmp | C:\Program Files\UltraViewer\is-12FE4.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | UltraViewer_setup_6.2_en.tmp | C:\Program Files\UltraViewer\is-OKDJI.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
3
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
832 | svchost.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/ | US | html | 1020 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
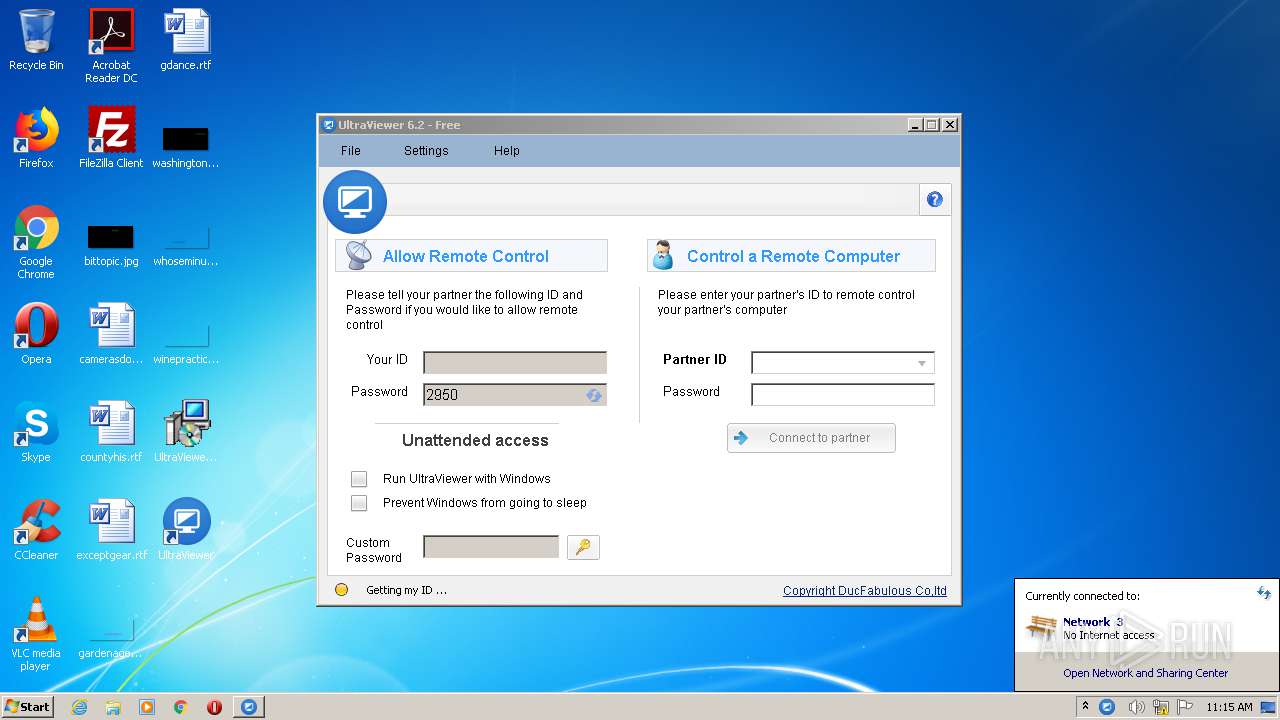
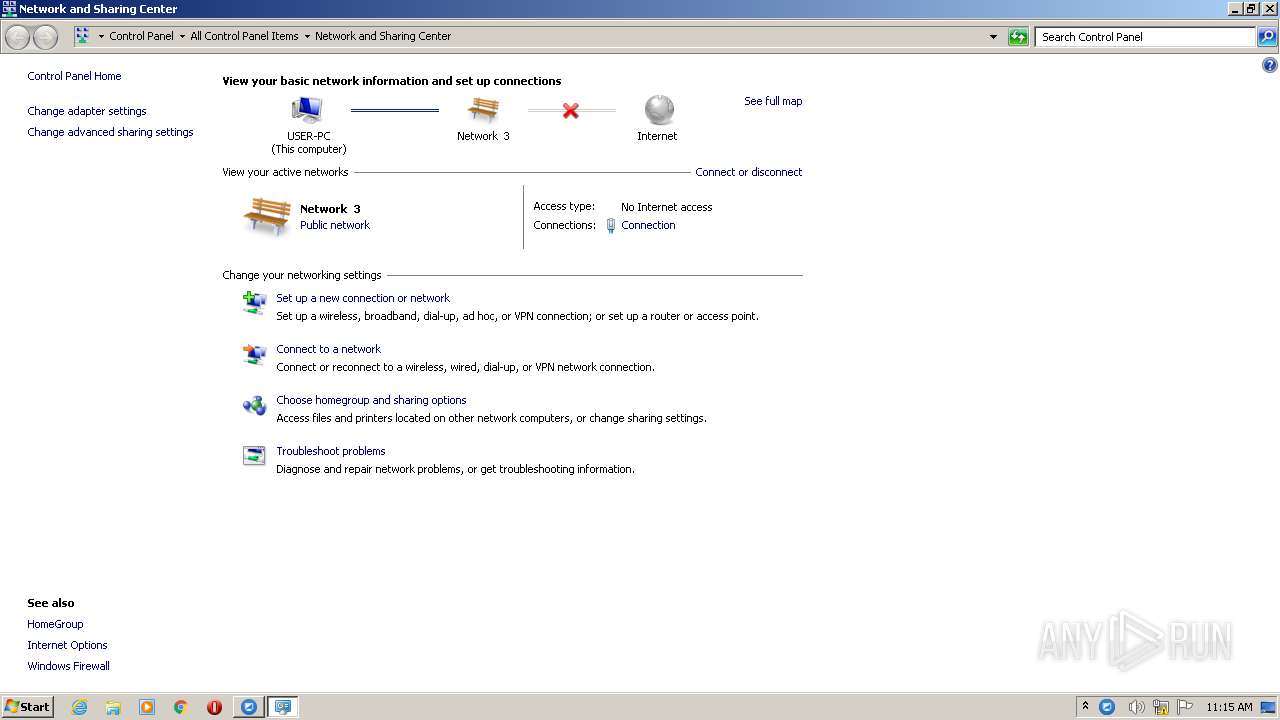
2896 | UltraViewer_Service.exe | 103.74.123.128:443 | update.ultraviewer.net | The Corporation for Financing & Promoting Technology | VN | unknown |
832 | svchost.exe | 104.79.89.142:80 | www.microsoft.com | Time Warner Cable Internet LLC | US | unknown |
2680 | UltraViewer_Desktop.exe | 118.69.172.224:443 | functions3.ultraviewer.net | The Corporation for Financing & Promoting Technology | VN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.ultraviewer.net |
| suspicious |
functions3.ultraviewer.net |
| suspicious |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
832 | svchost.exe | A Network Trojan was detected | ET POLICY Microsoft user-agent automated process response to automated request |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
UltraViewer_Desktop.exe | uvh - 2680 - 66096
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|