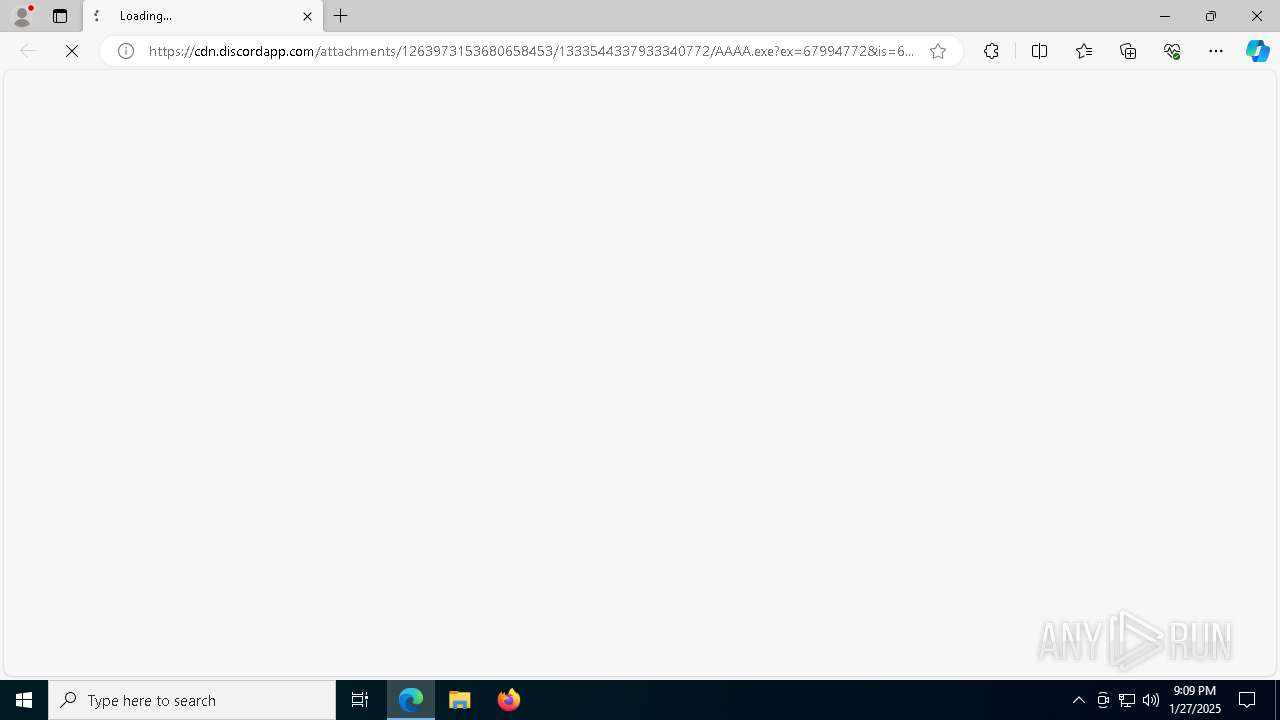
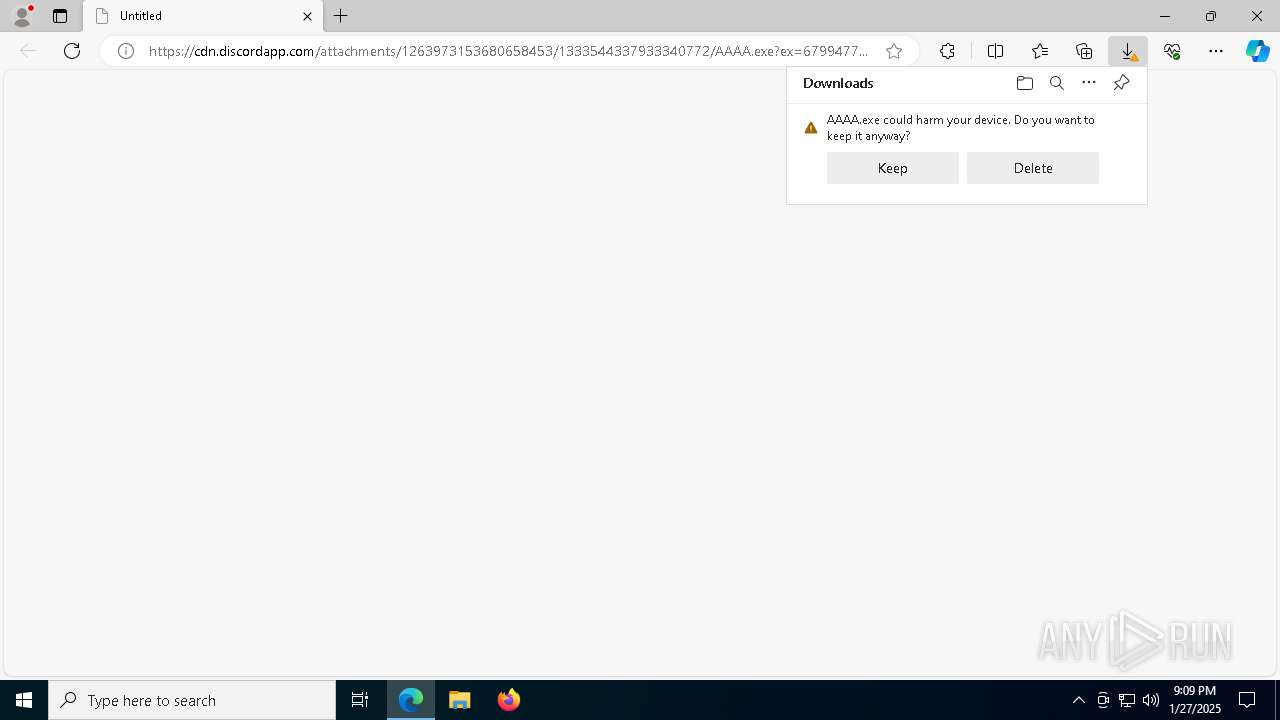
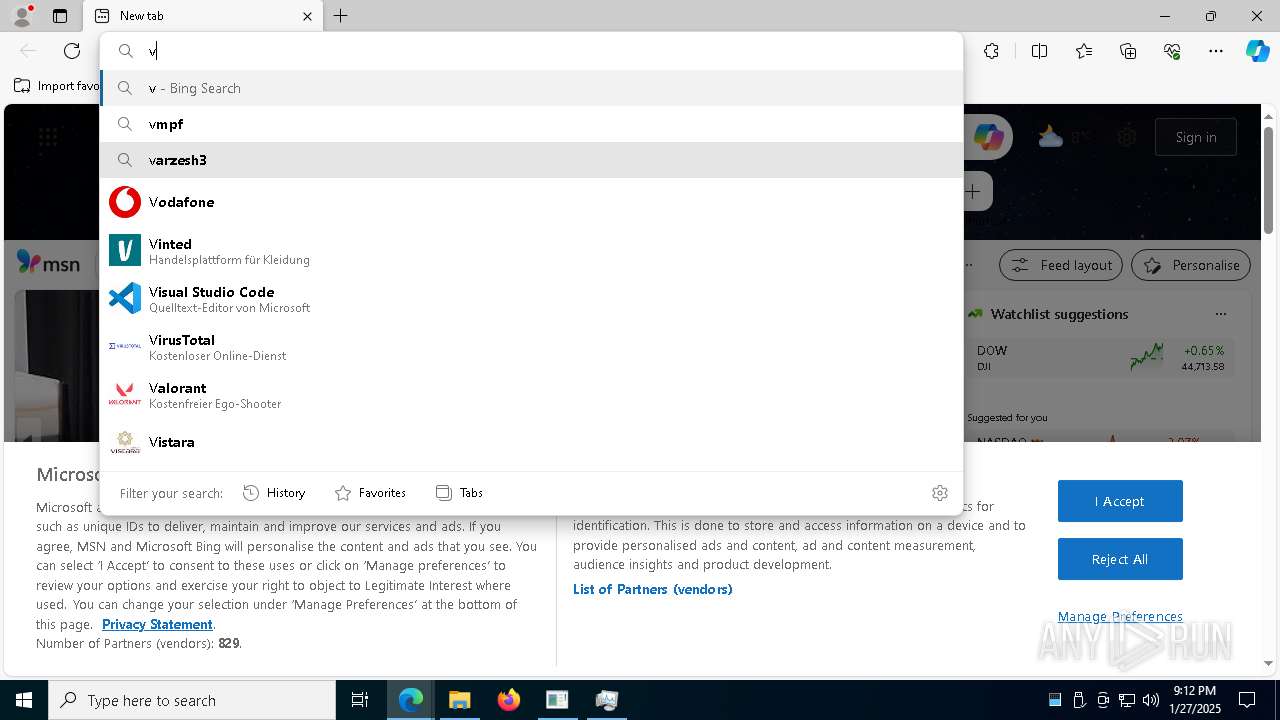
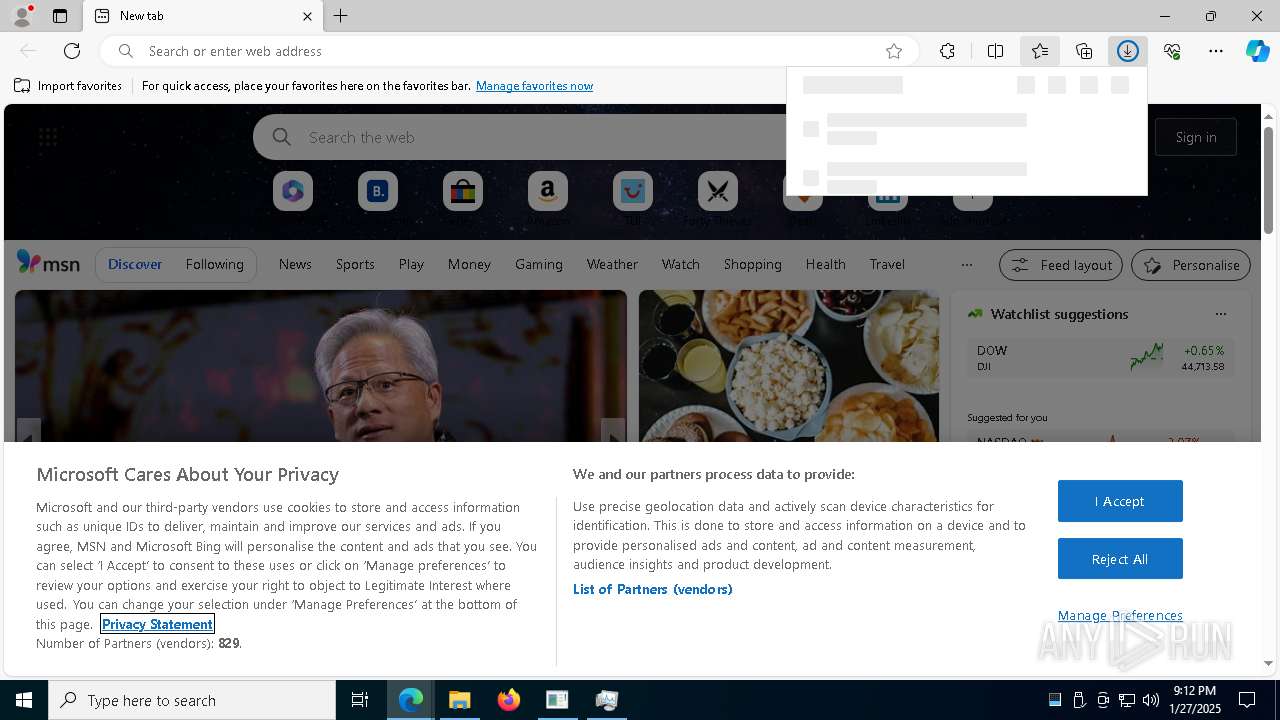
| URL: | https://cdn.discordapp.com/attachments/1263973153680658453/1333544337933340772/AAAA.exe?ex=67994772&is=6797f5f2&hm=ca2c57565df7cd6f0ba7dfa2de3599f46b9dbfc4e503586740e3595c121fd7dc& |
| Full analysis: | https://app.any.run/tasks/eb6befcd-38df-4bbb-9cbb-27abdf933020 |
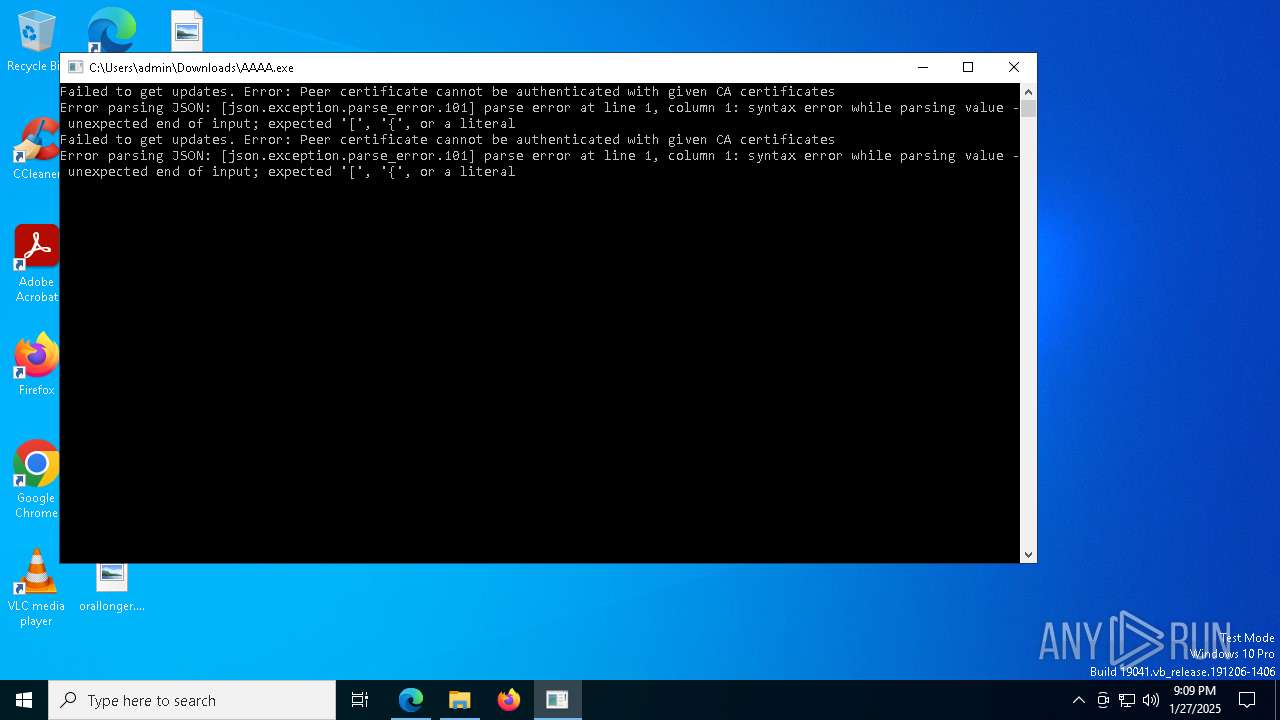
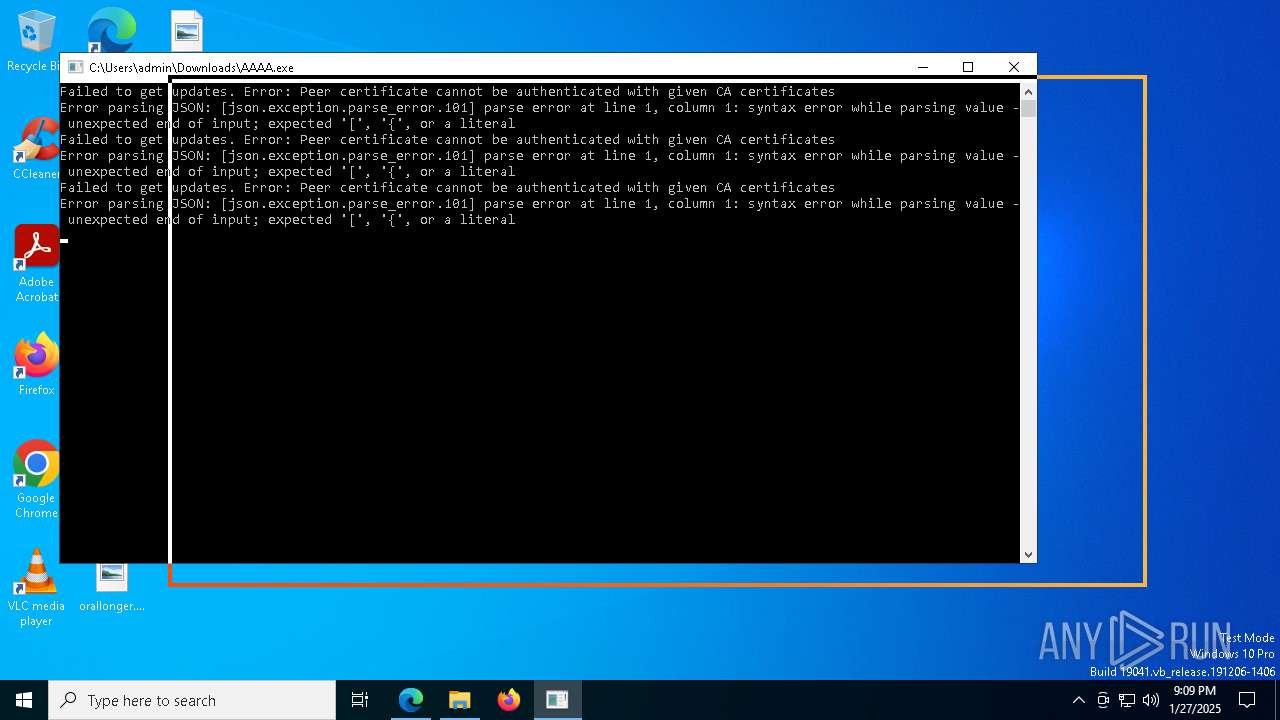
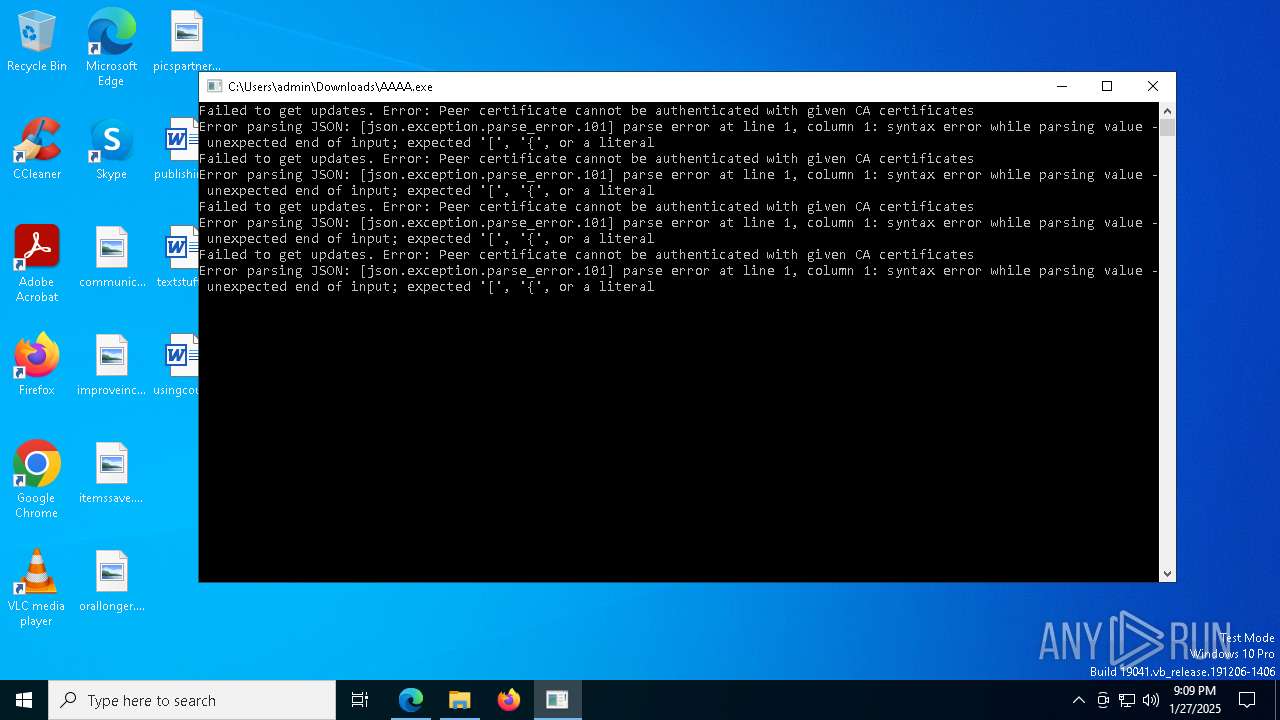
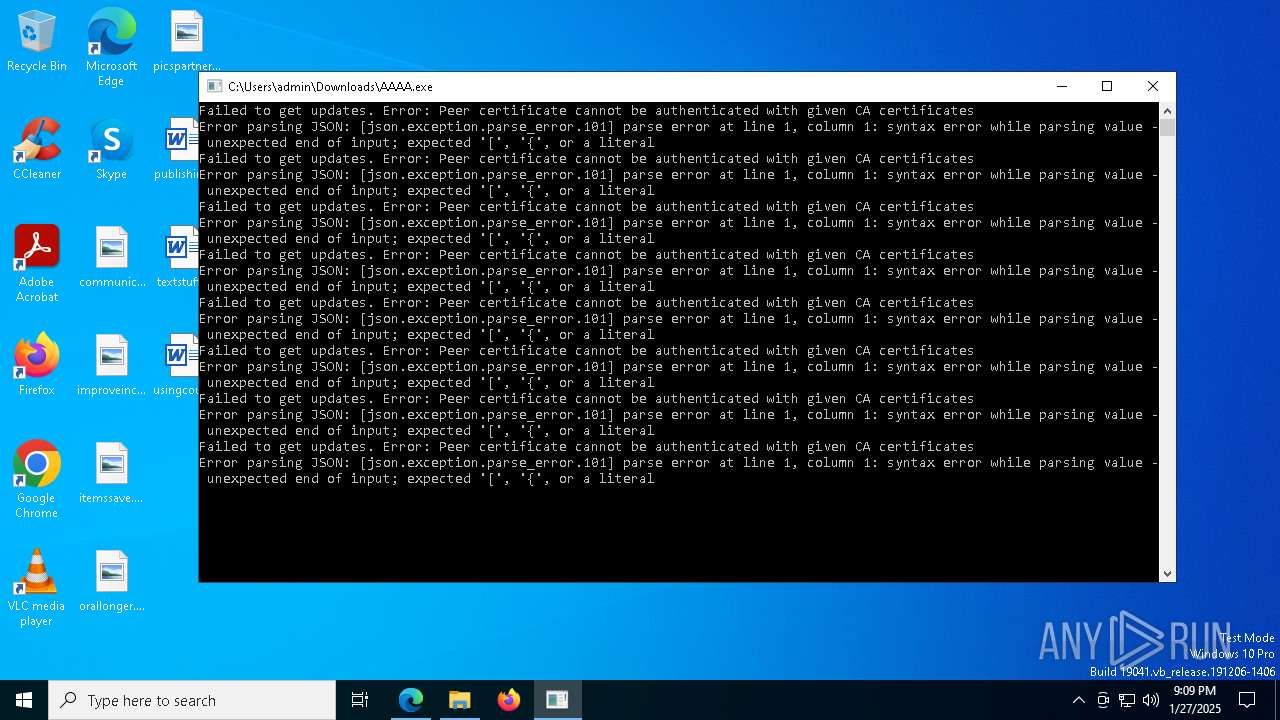
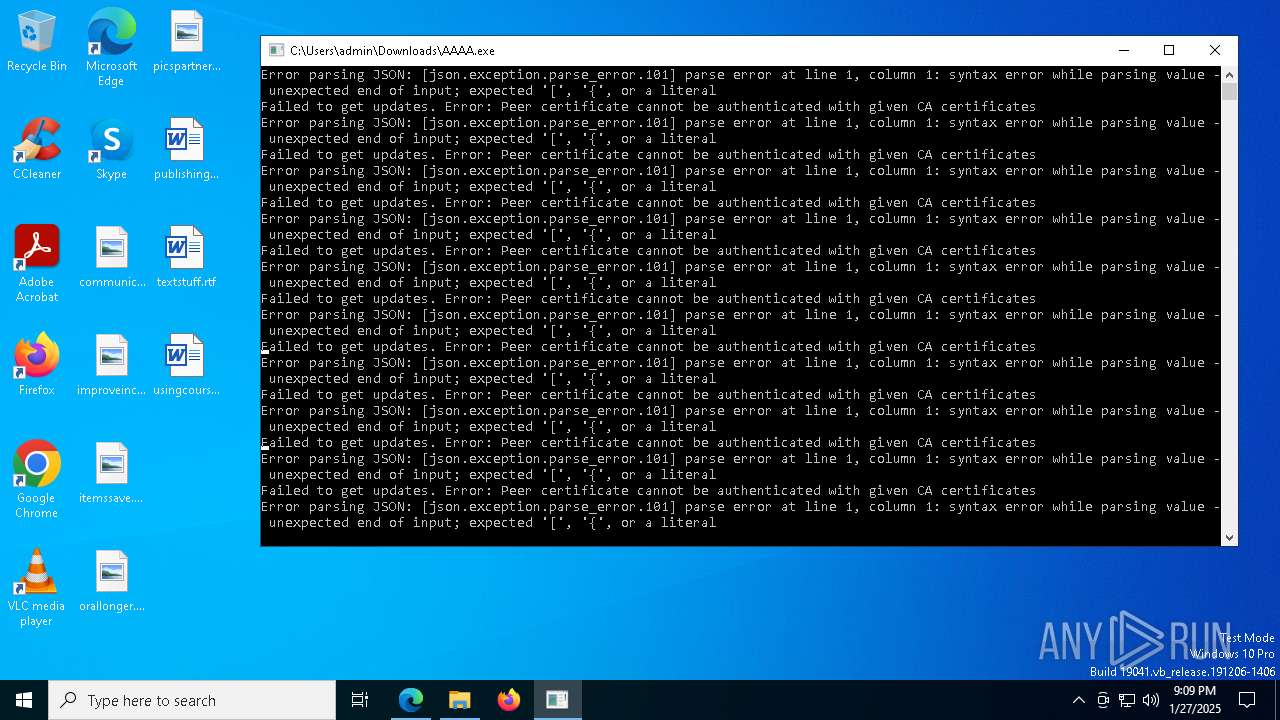
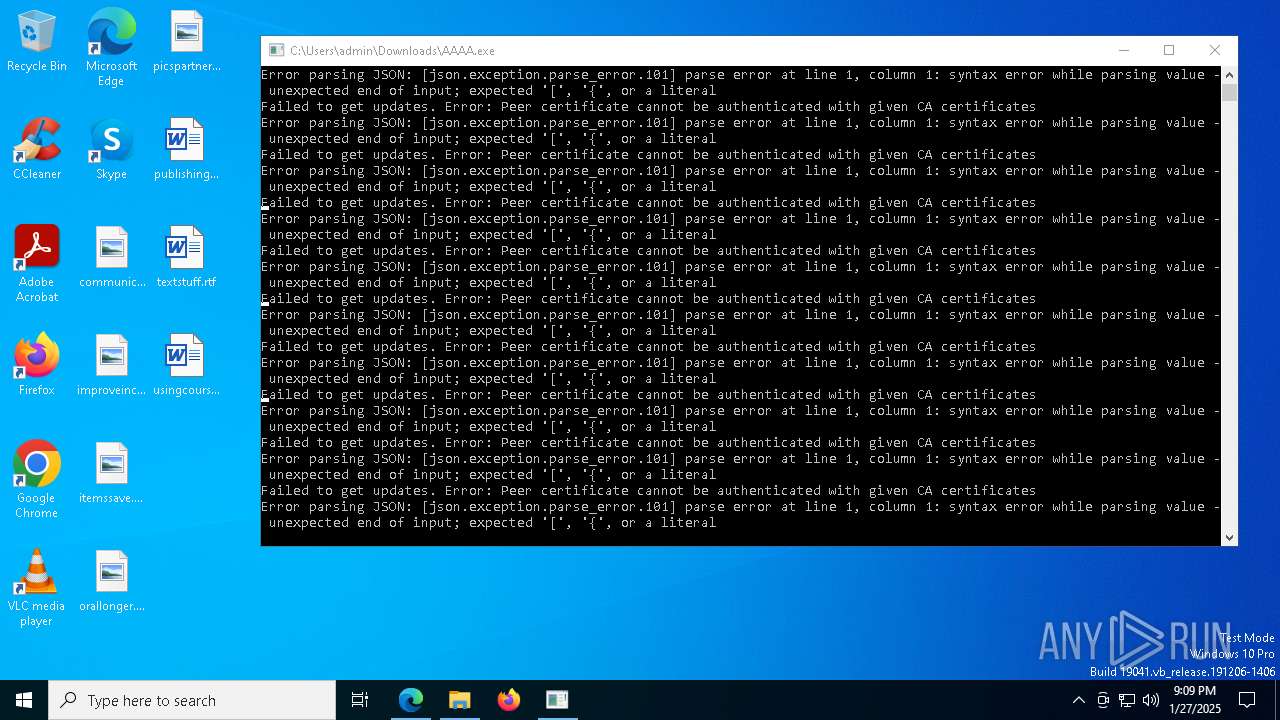
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2025, 21:09:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7FE14DFA79BEA041249FA2EBFCEBACC5 |
| SHA1: | B489A5E56CFDD81FB089CC61AF13780E5FB7A812 |
| SHA256: | B0781A6D577075E7D1257C4FD4AAFE090BBE455BD59EA03EE182D9963B272A0C |
| SSDEEP: | 3:N8cCWdy6//OvNMWWR4DkW0+aDUDXYe/WaYTXGQj1W1ERGbQG1BRiqRGUEQwDn:2cry6Xz344W0OYssWYYEcbQABDgQ2 |
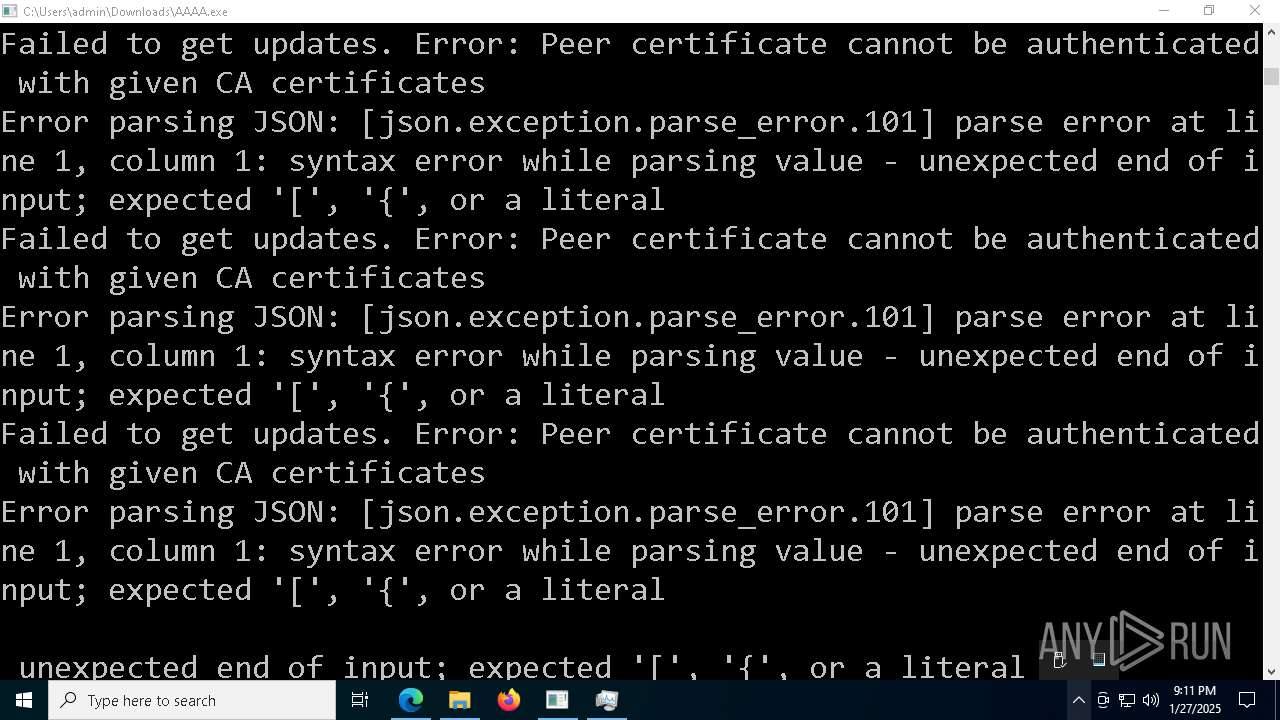
MALICIOUS
No malicious indicators.SUSPICIOUS
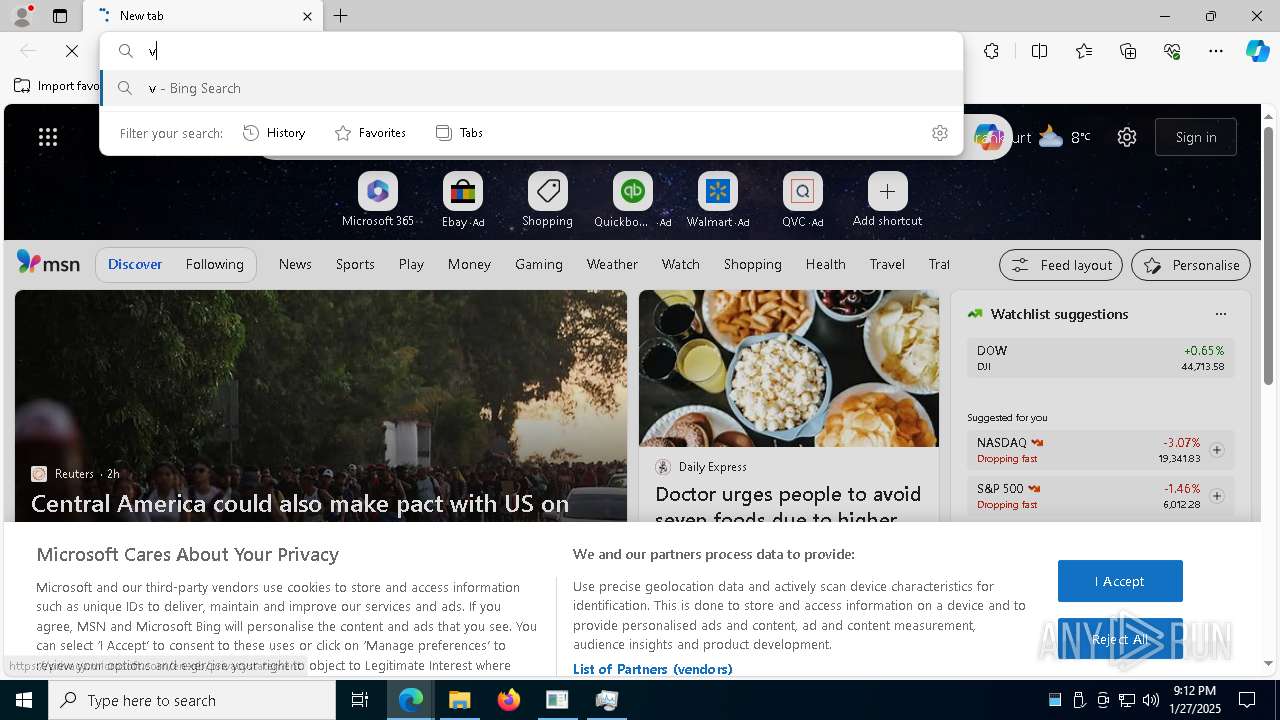
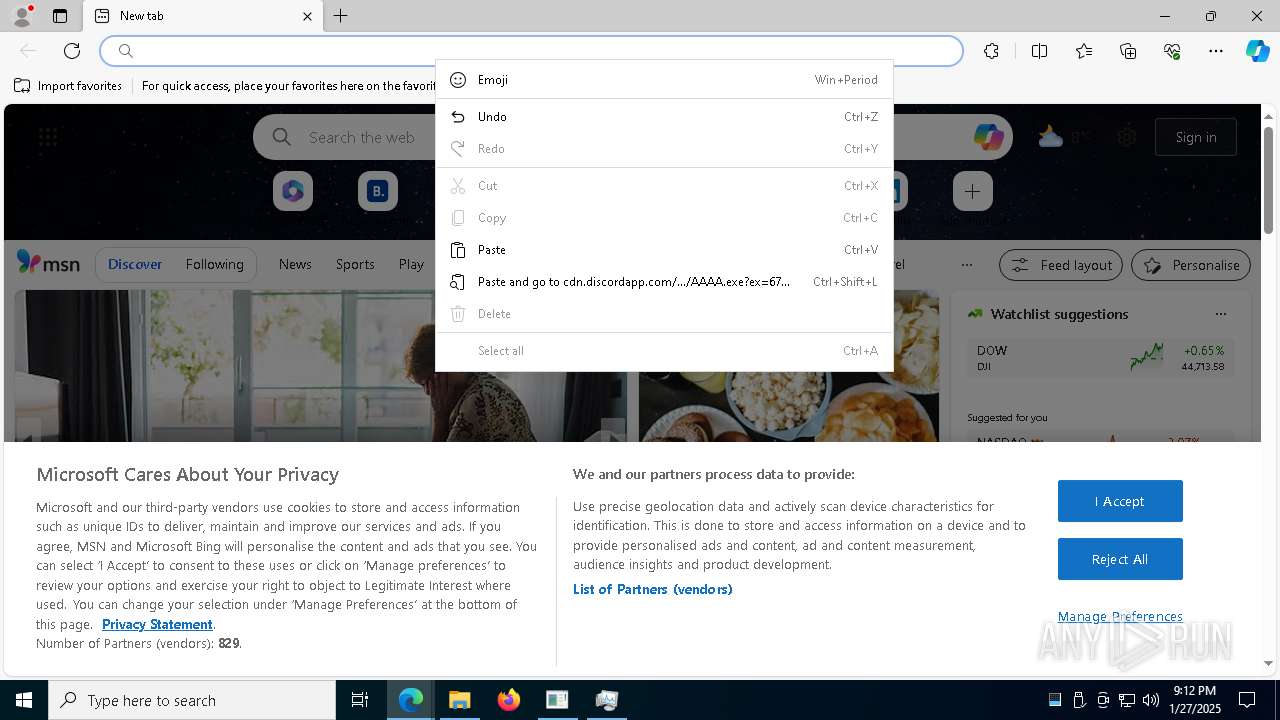
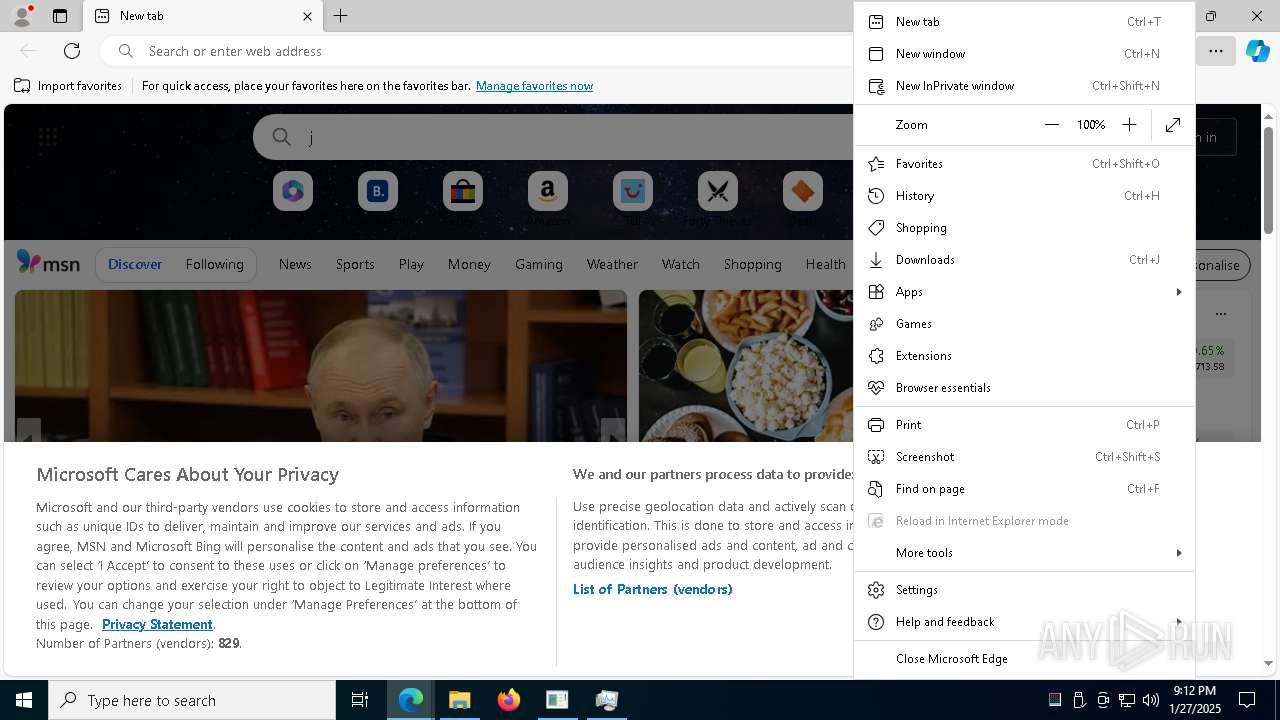
Discord domain found in command line (probably downloading payload)
- msedge.exe (PID: 6292)
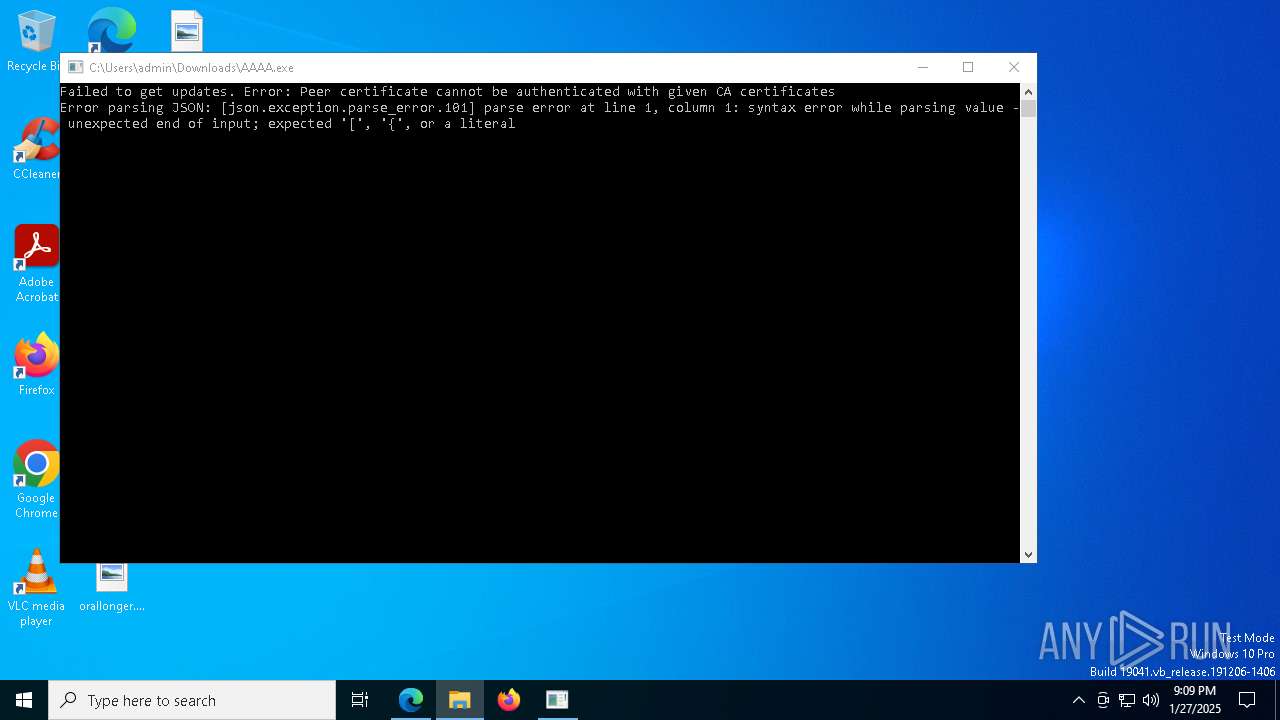
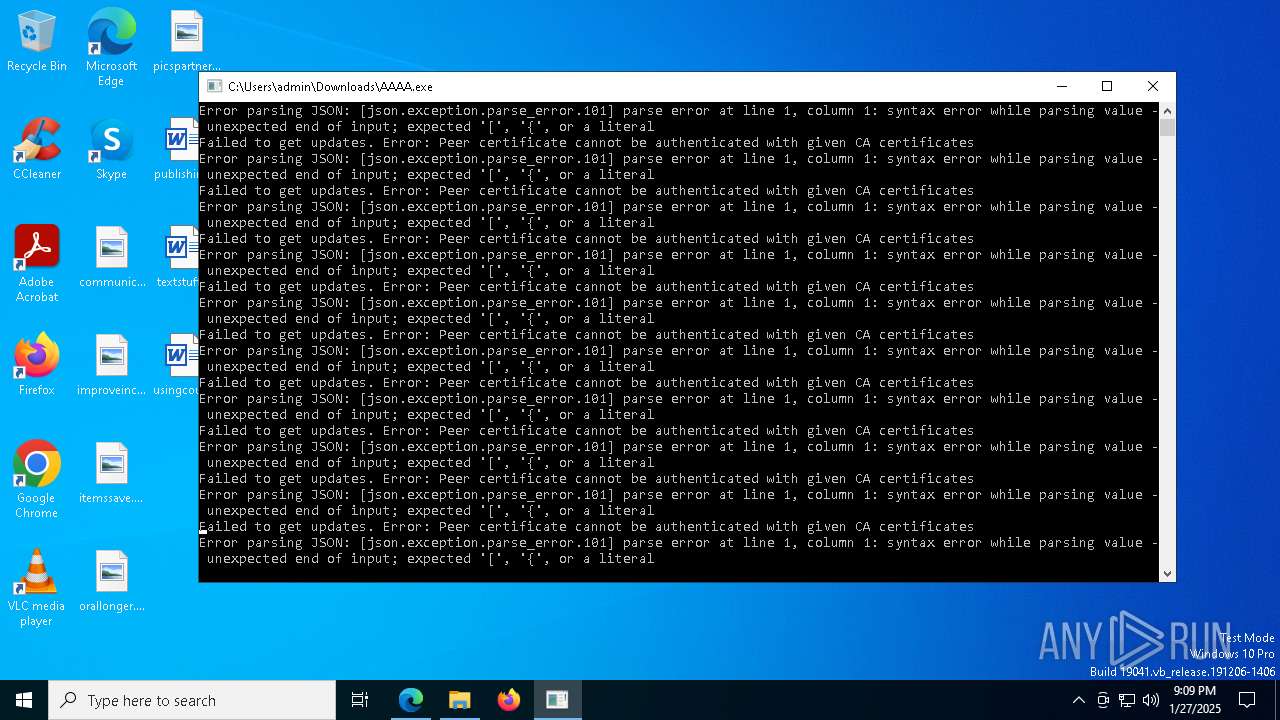
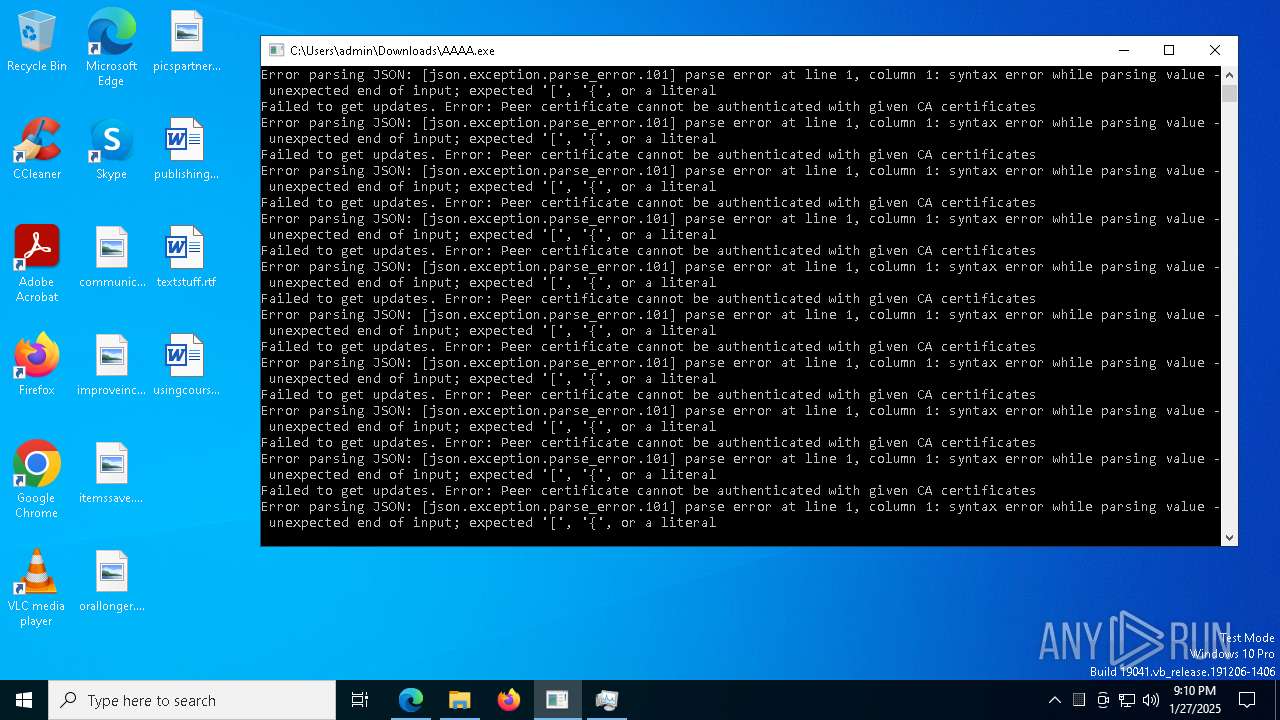
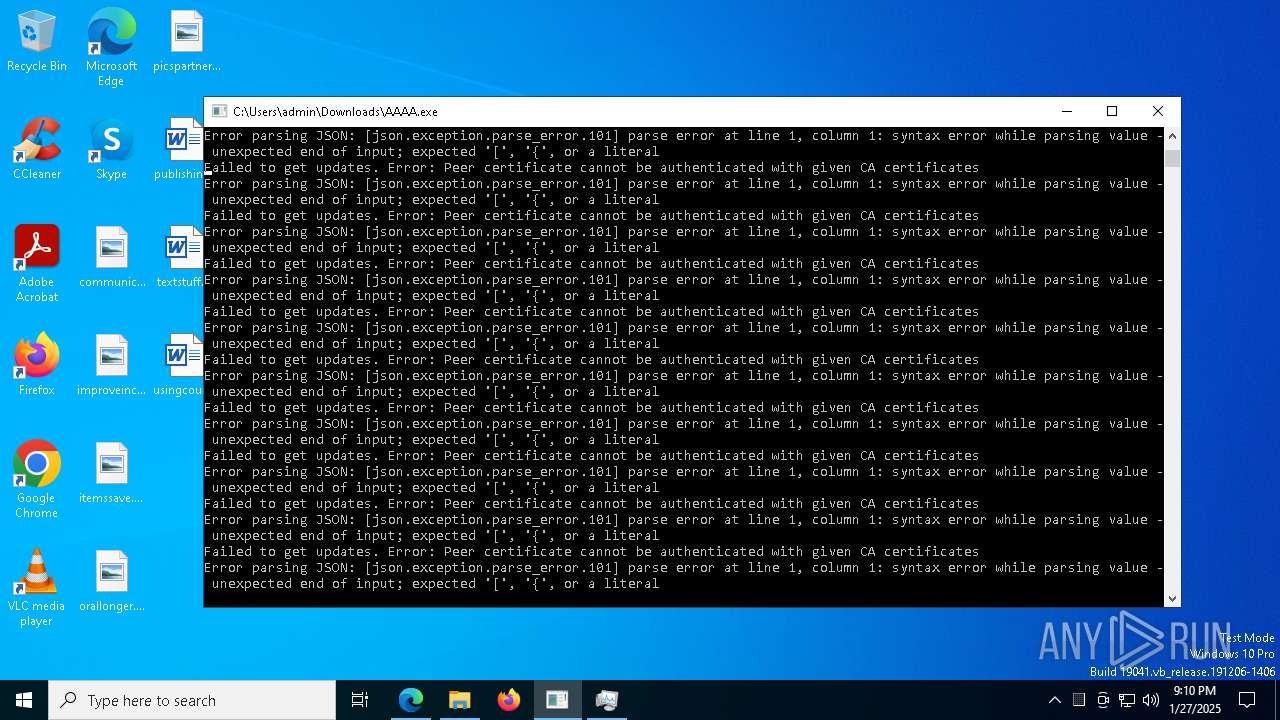
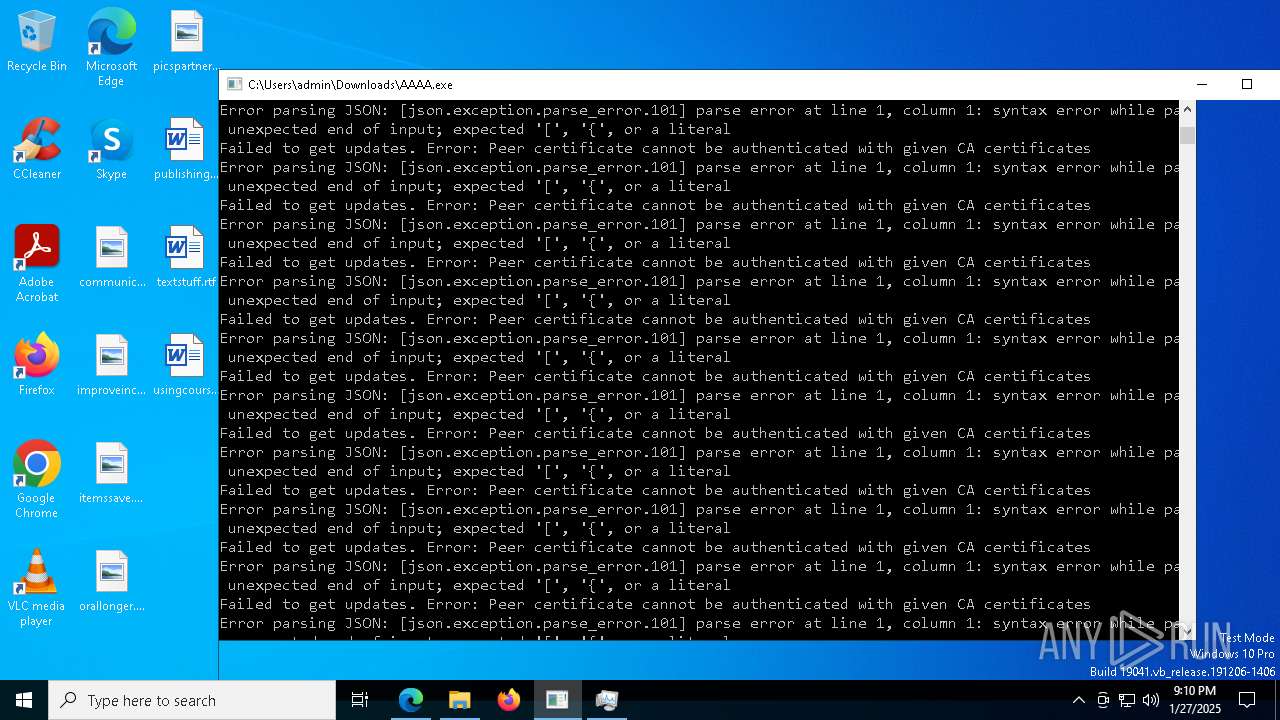
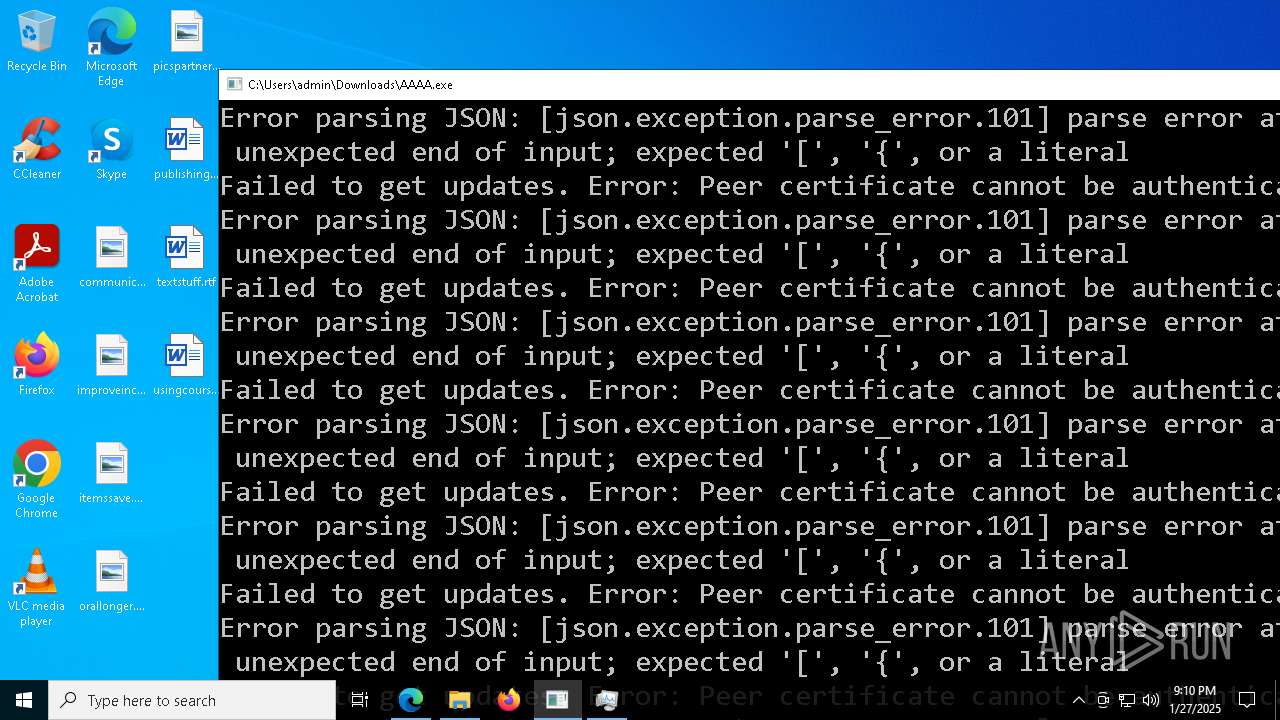
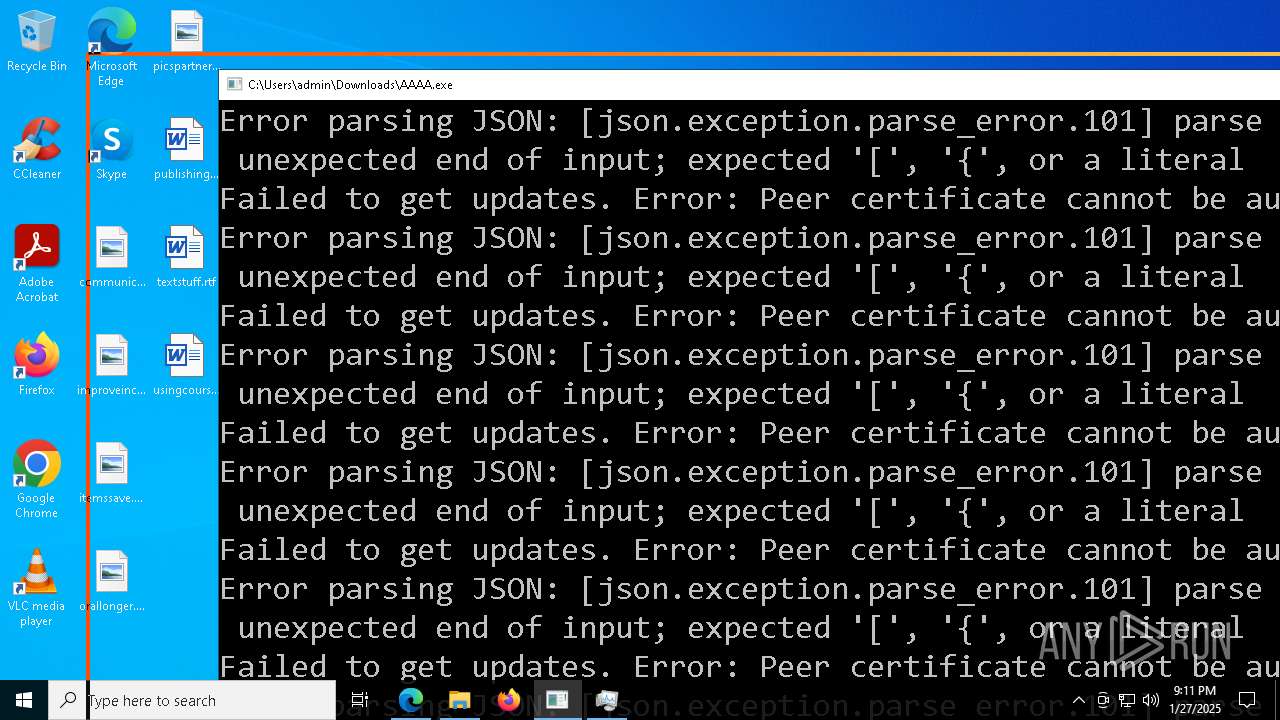
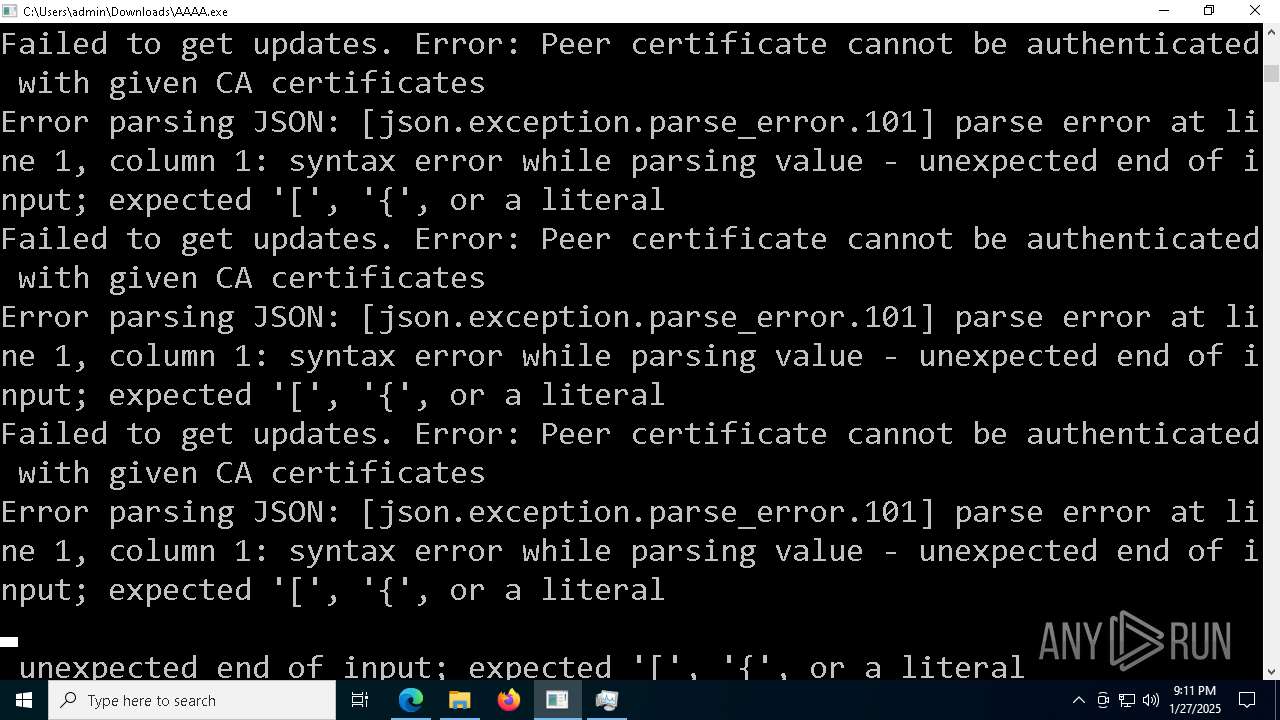
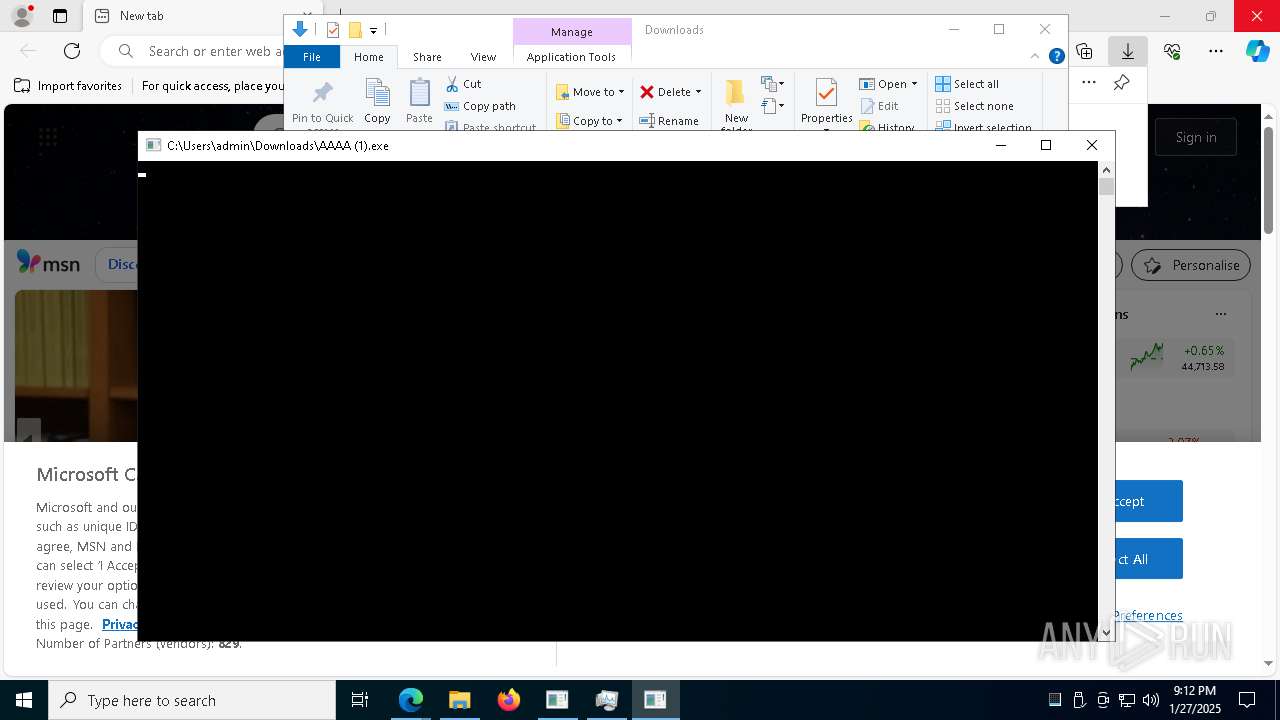
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- AAAA.exe (PID: 2928)
- AAAA (1).exe (PID: 4300)
- AAAA (1).exe (PID: 7988)
- AAAA (1).exe (PID: 2380)
Possible usage of Discord/Telegram API has been detected (YARA)
- AAAA.exe (PID: 2928)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 2092)
INFO
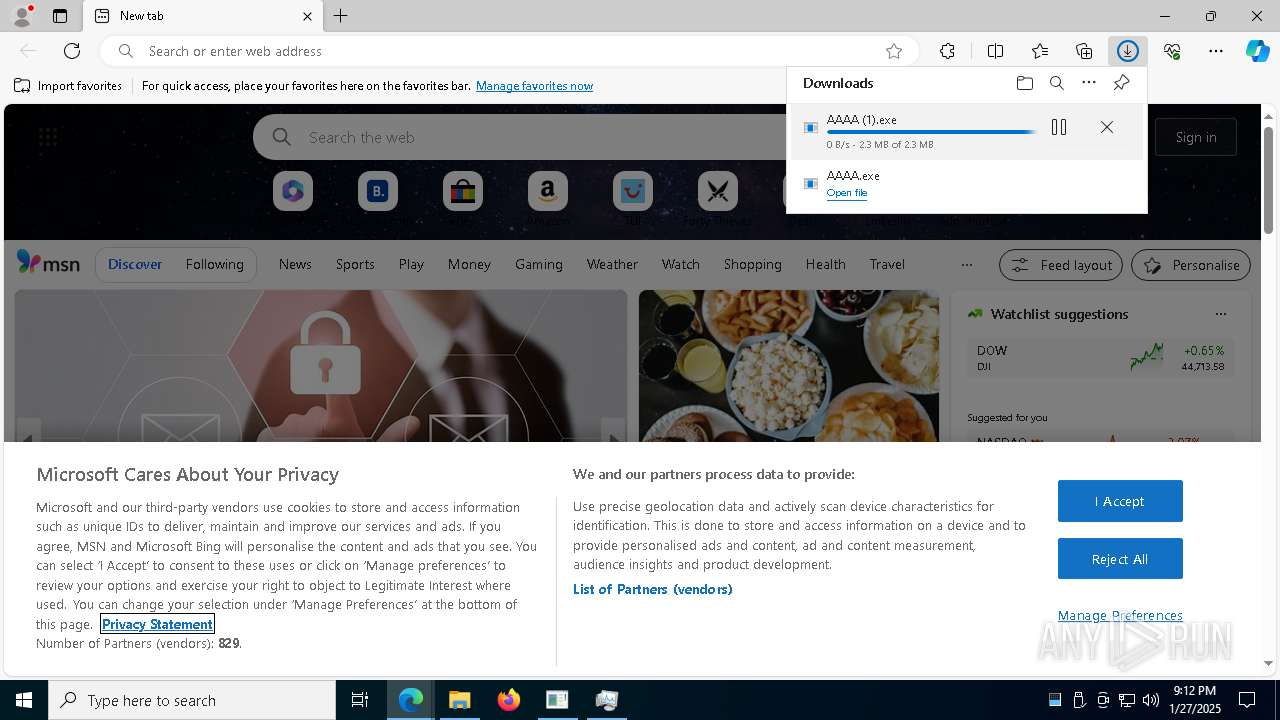
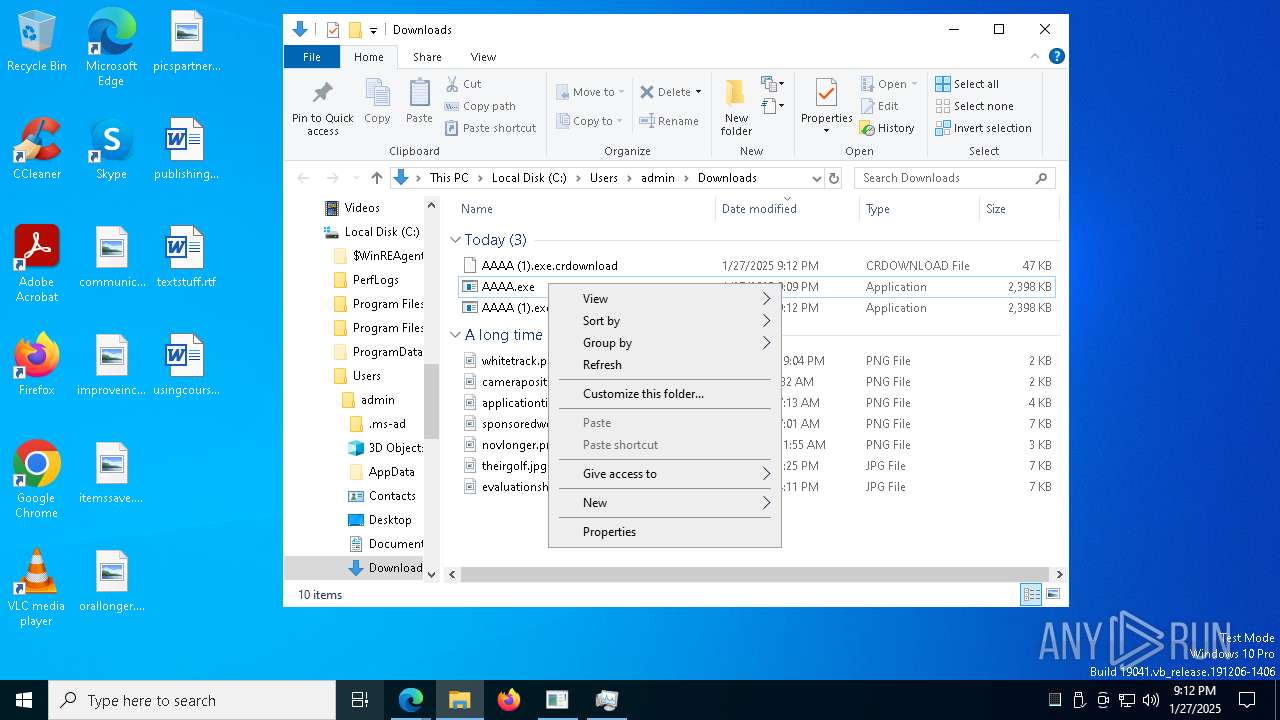
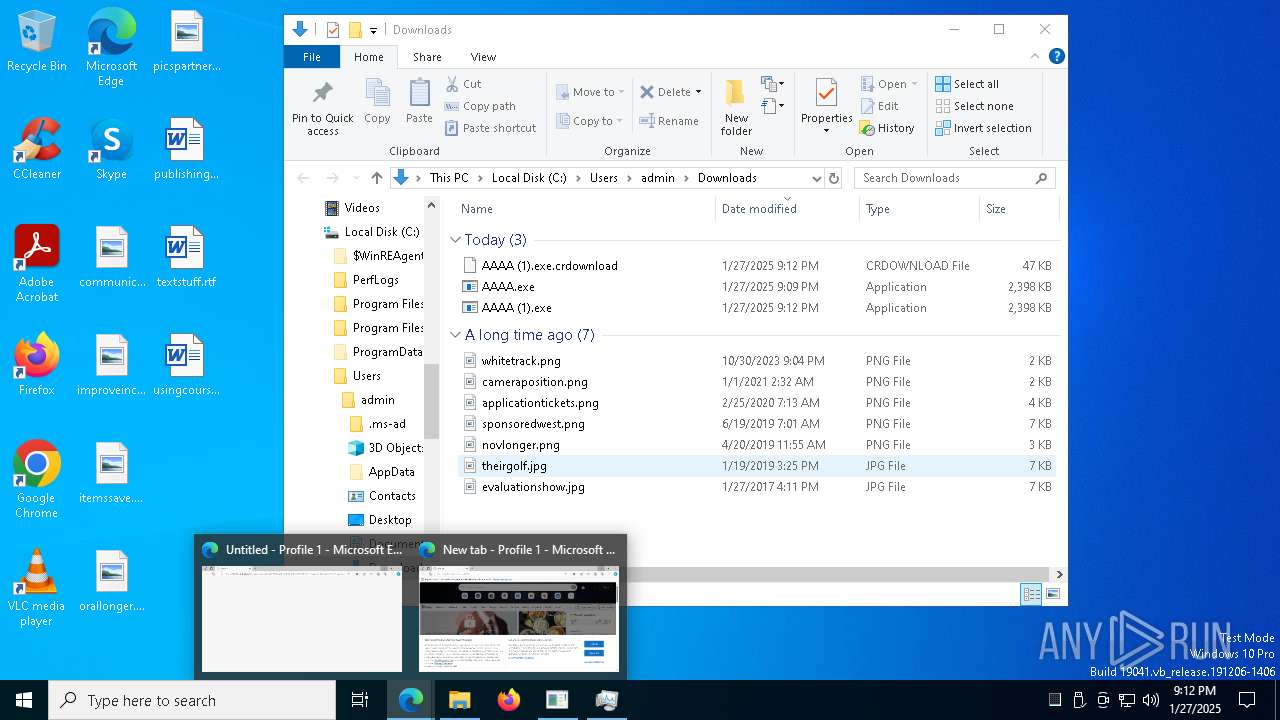
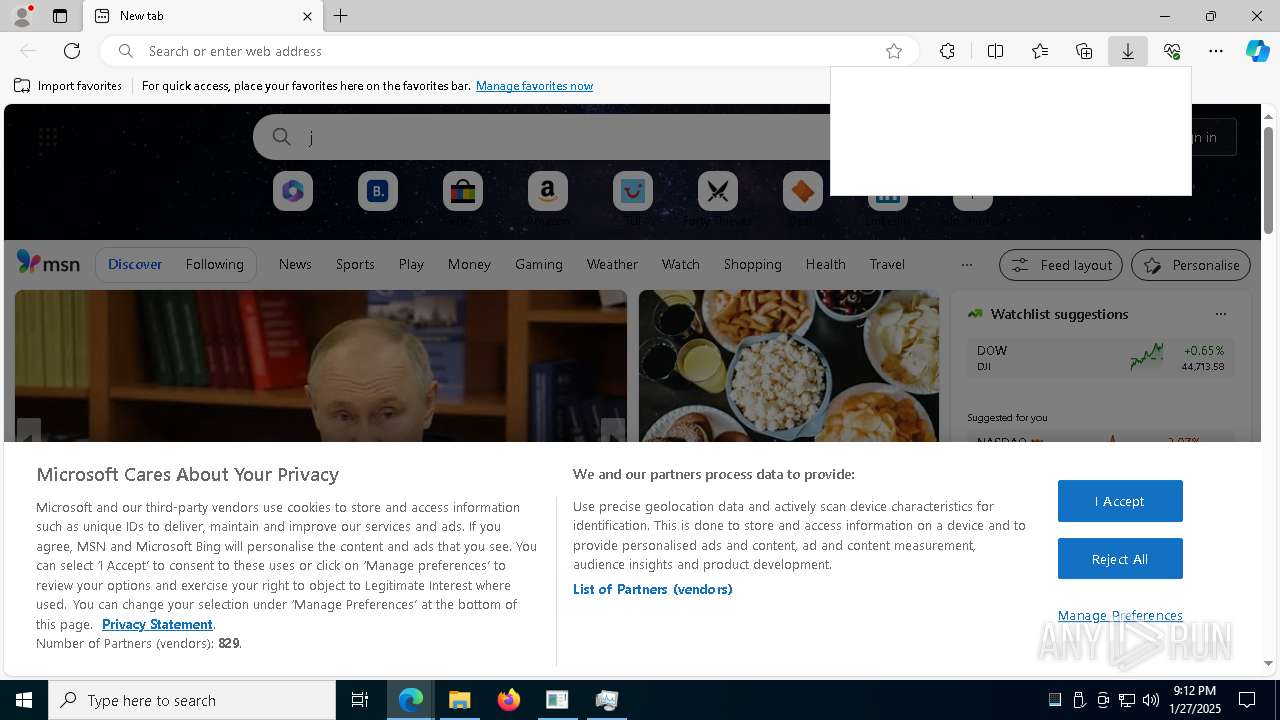
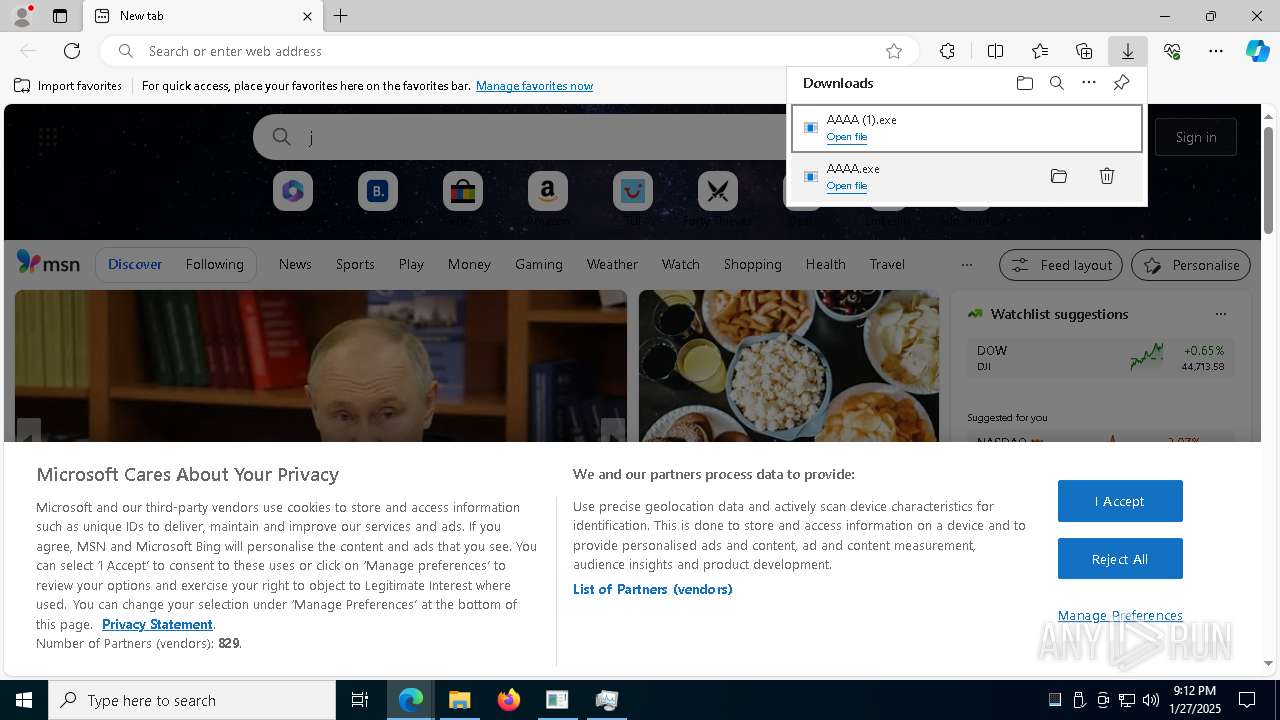
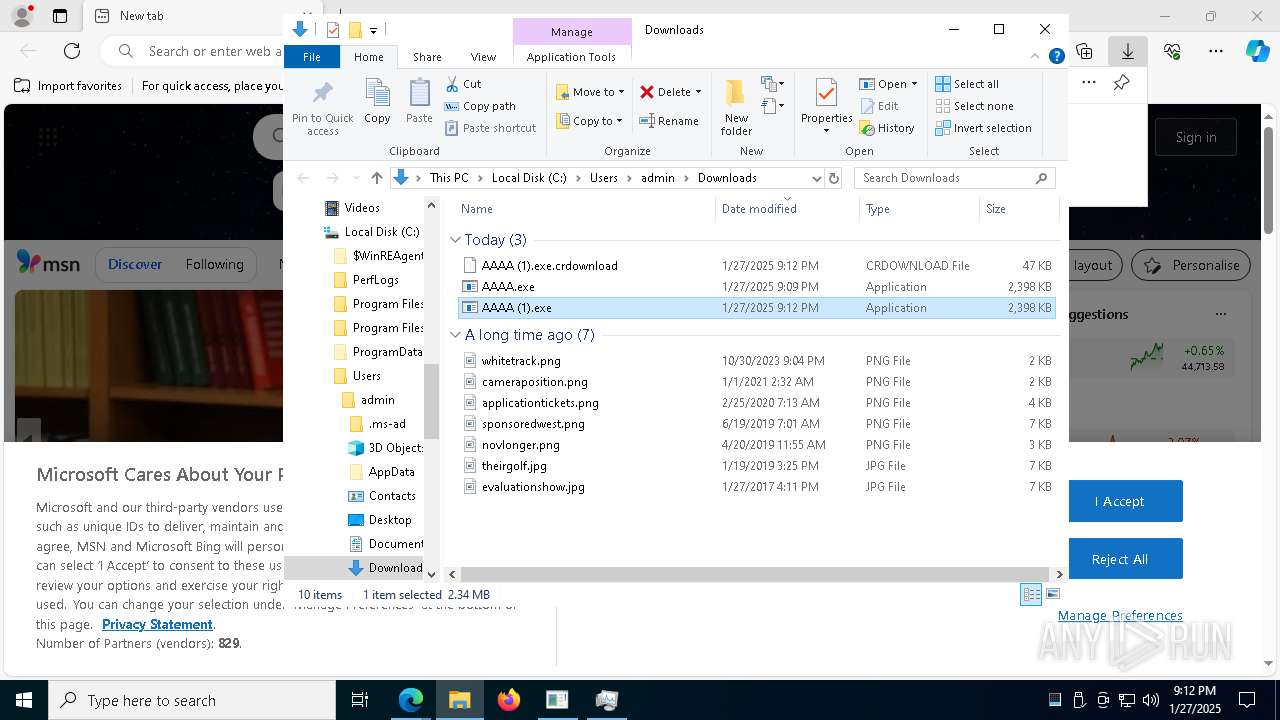
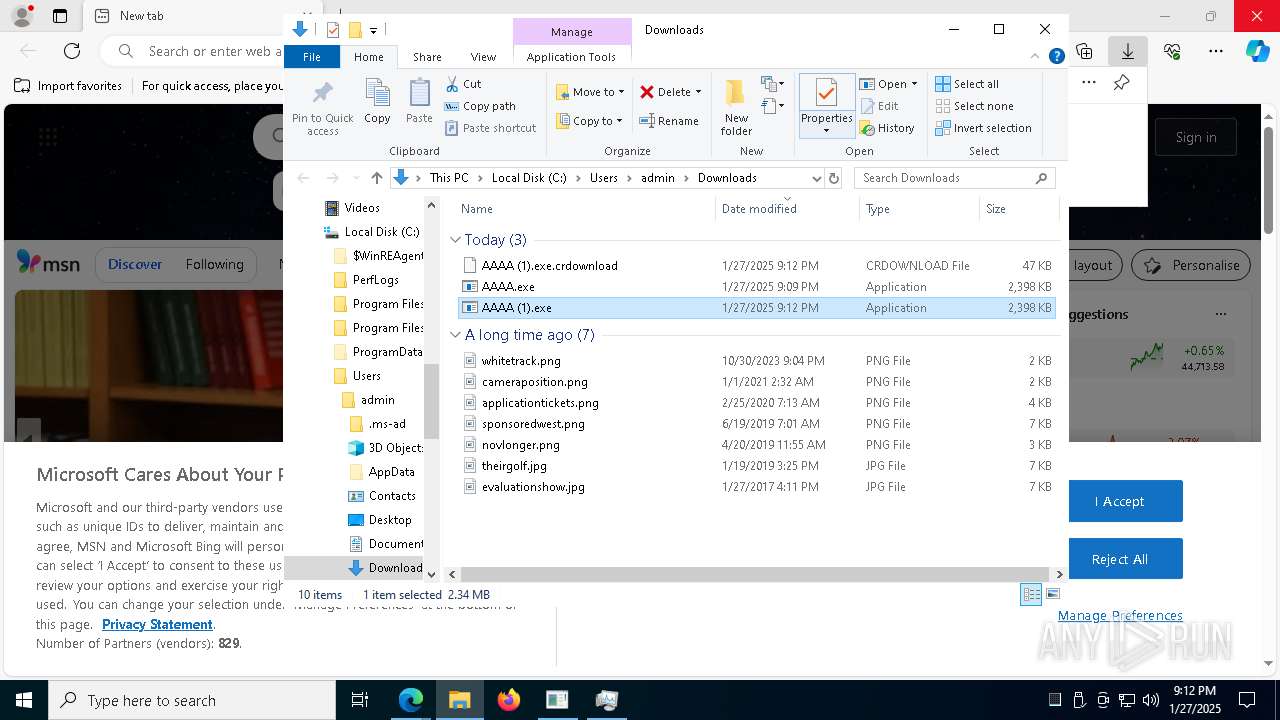
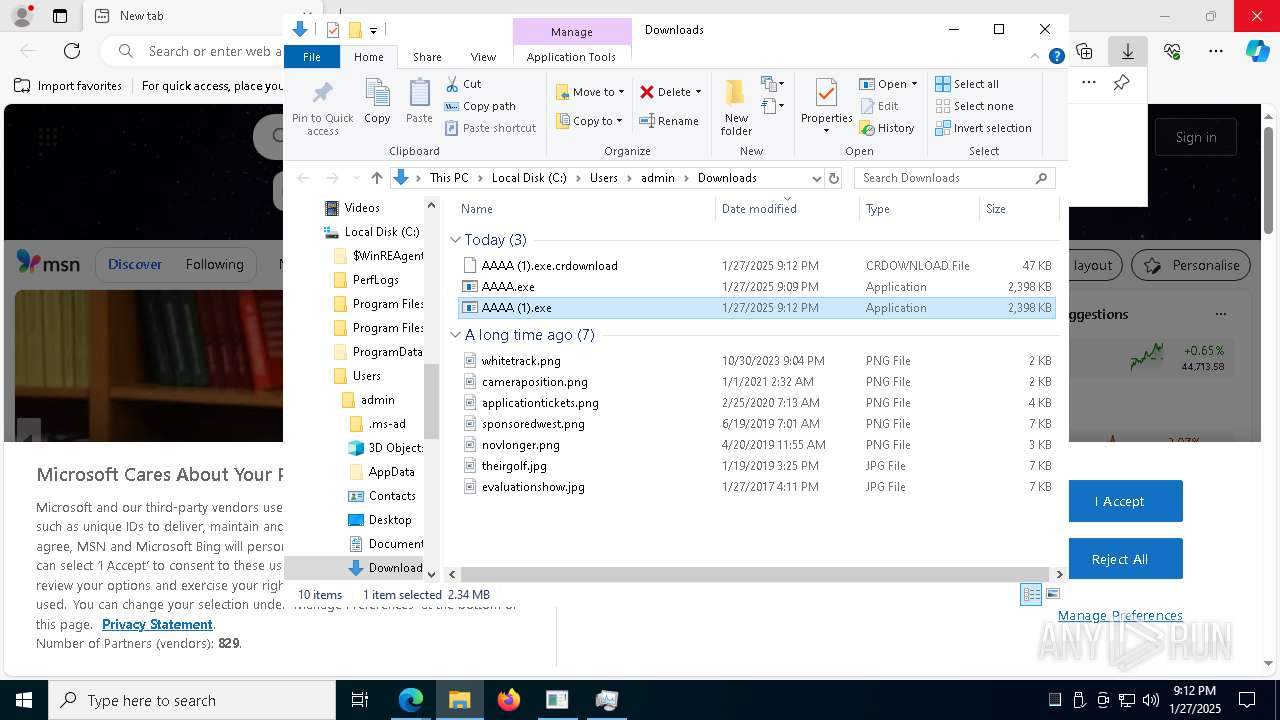
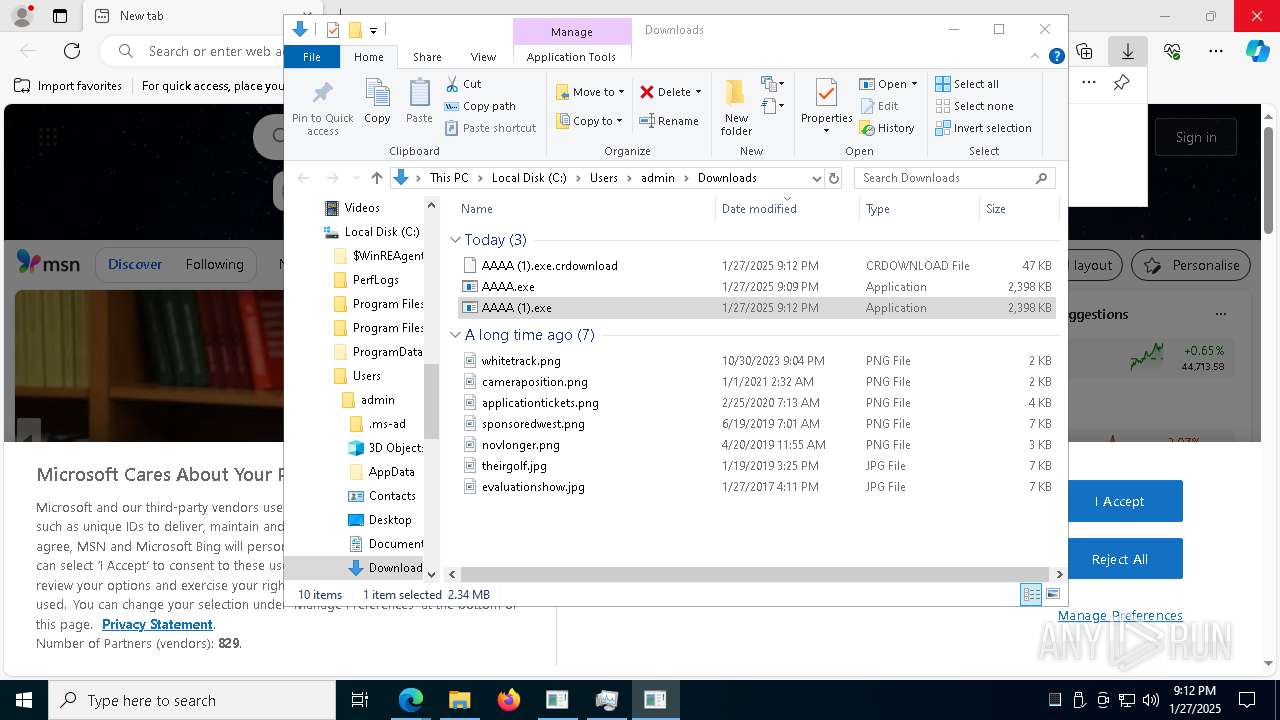
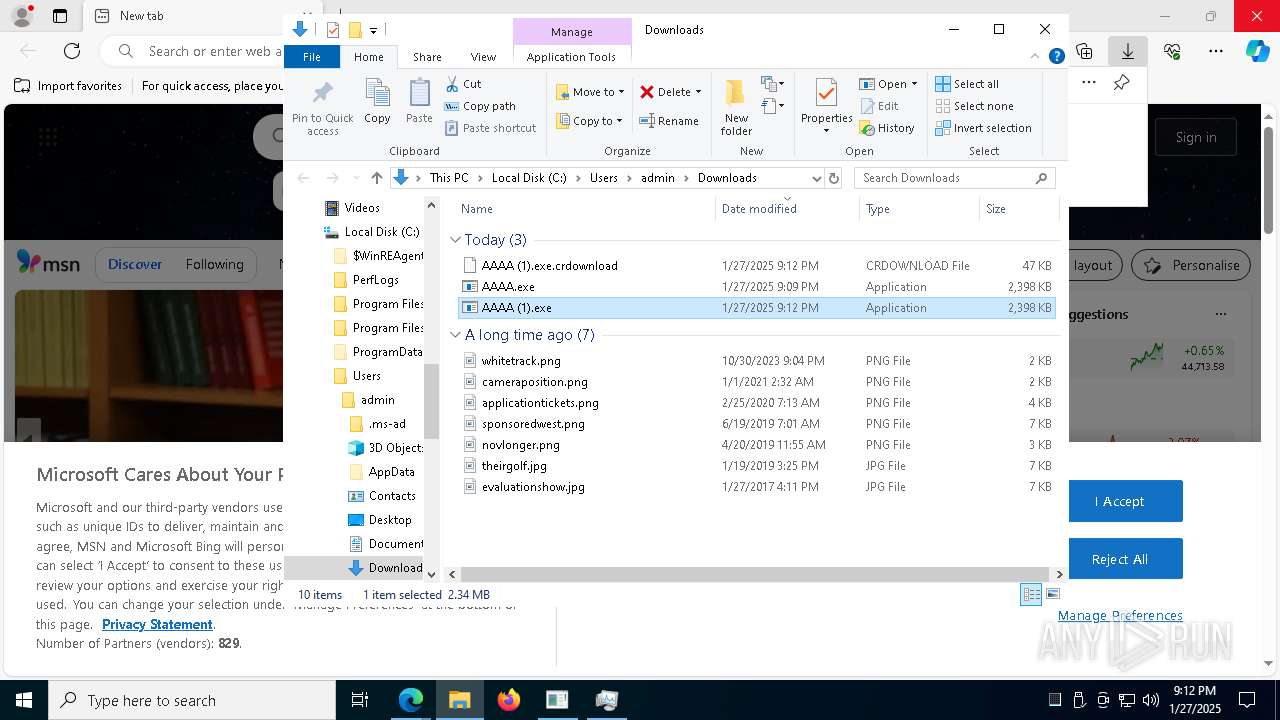
Executable content was dropped or overwritten
- msedge.exe (PID: 6772)
- msedge.exe (PID: 6292)
- msedge.exe (PID: 4512)
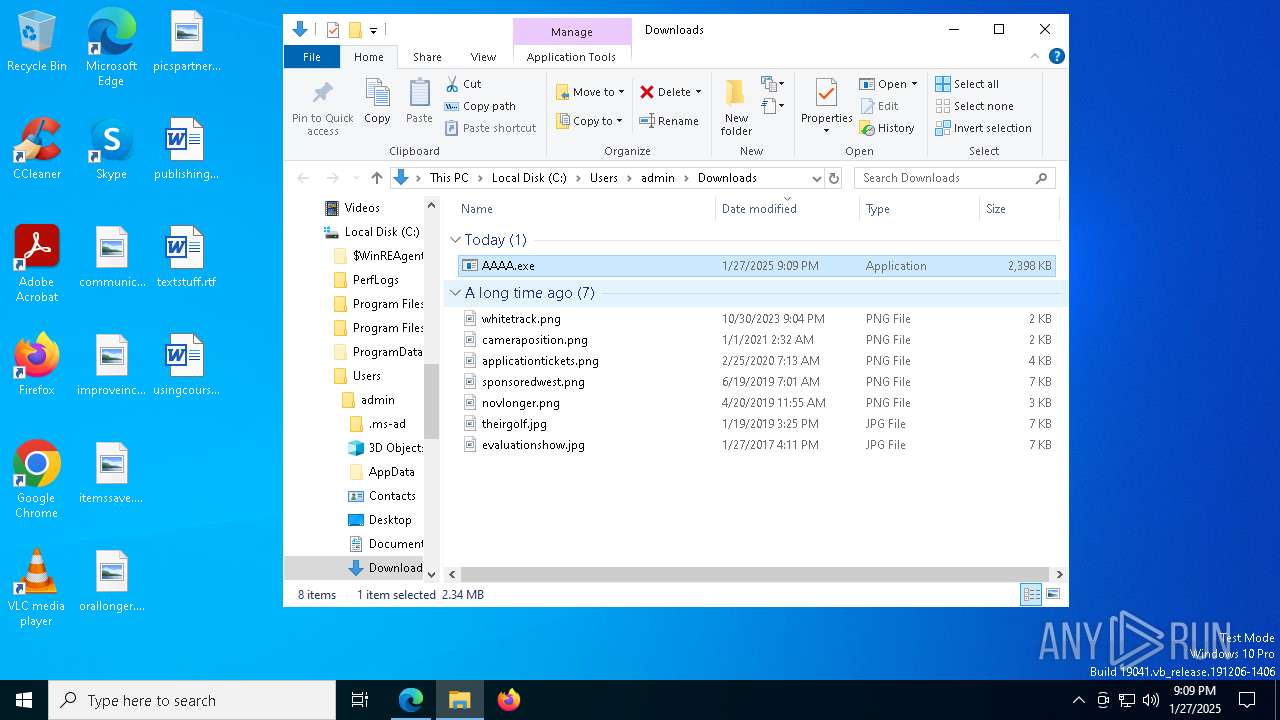
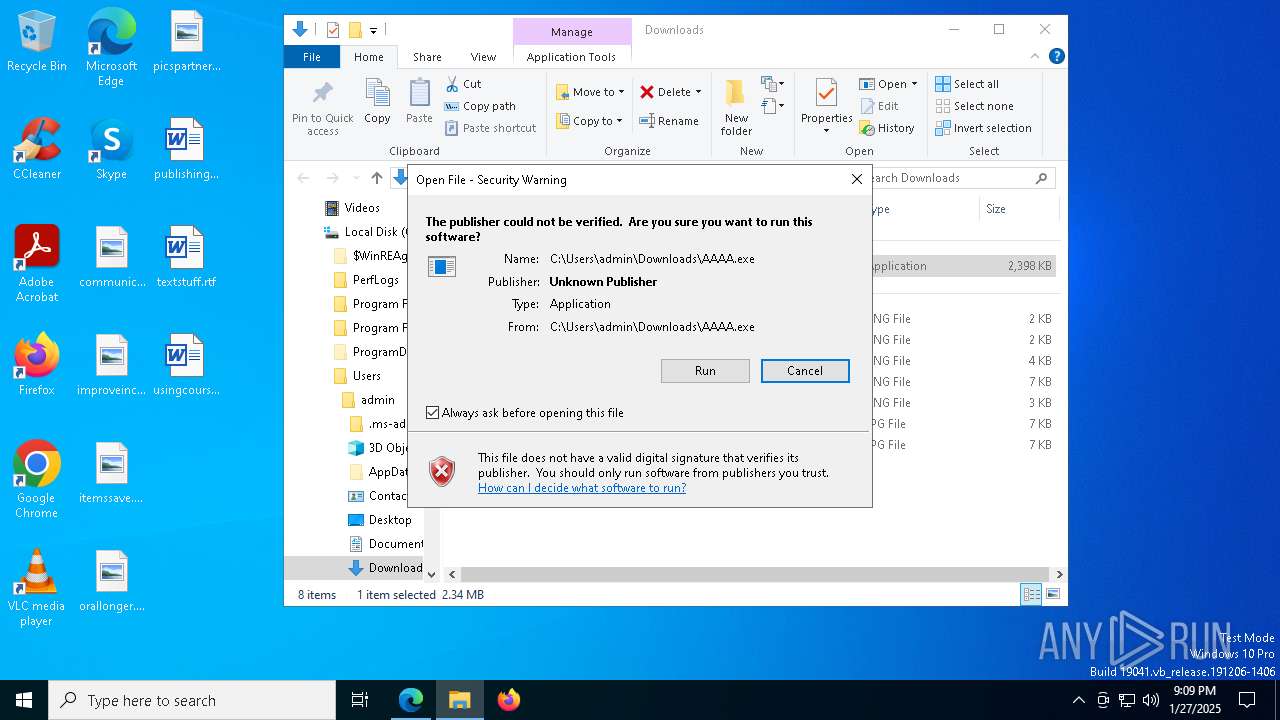
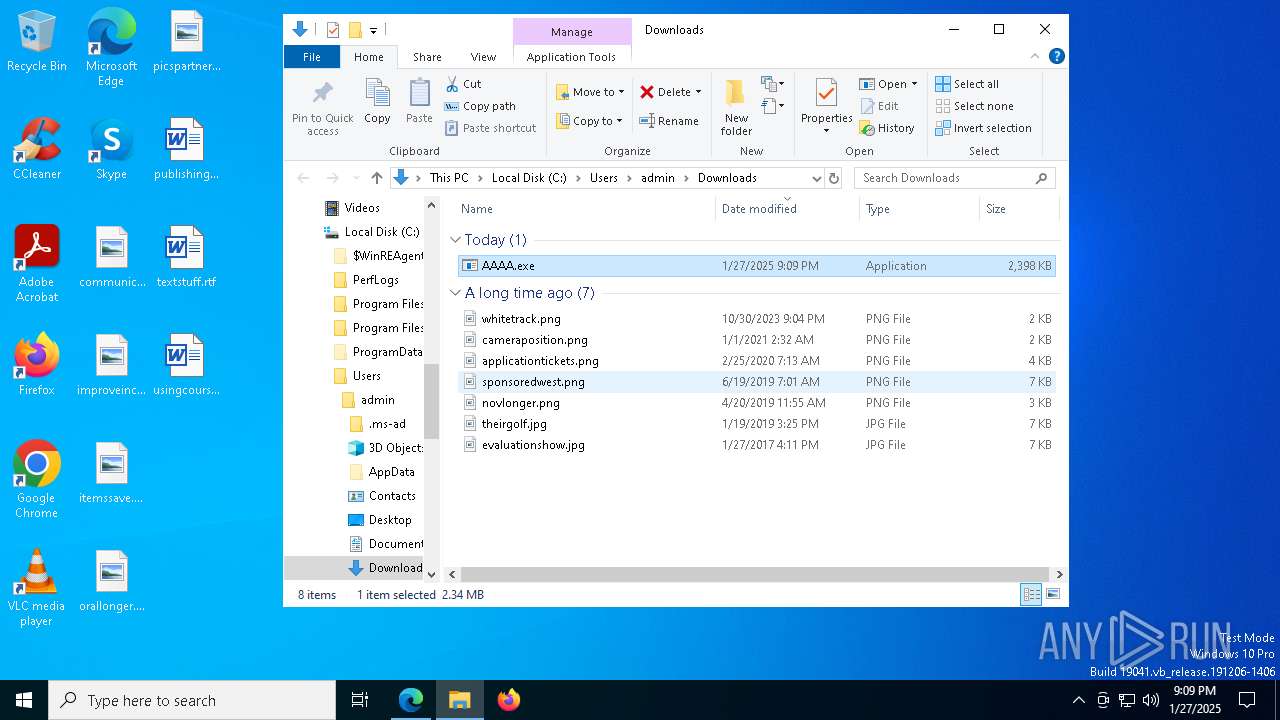
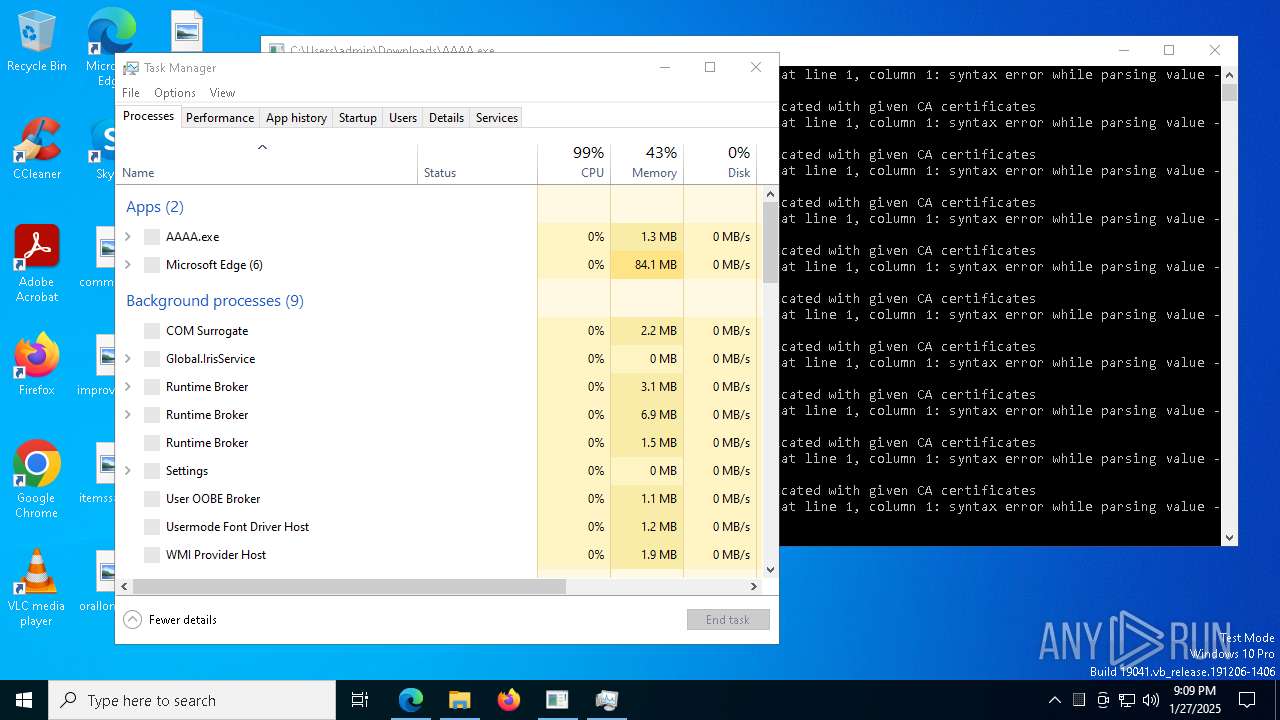
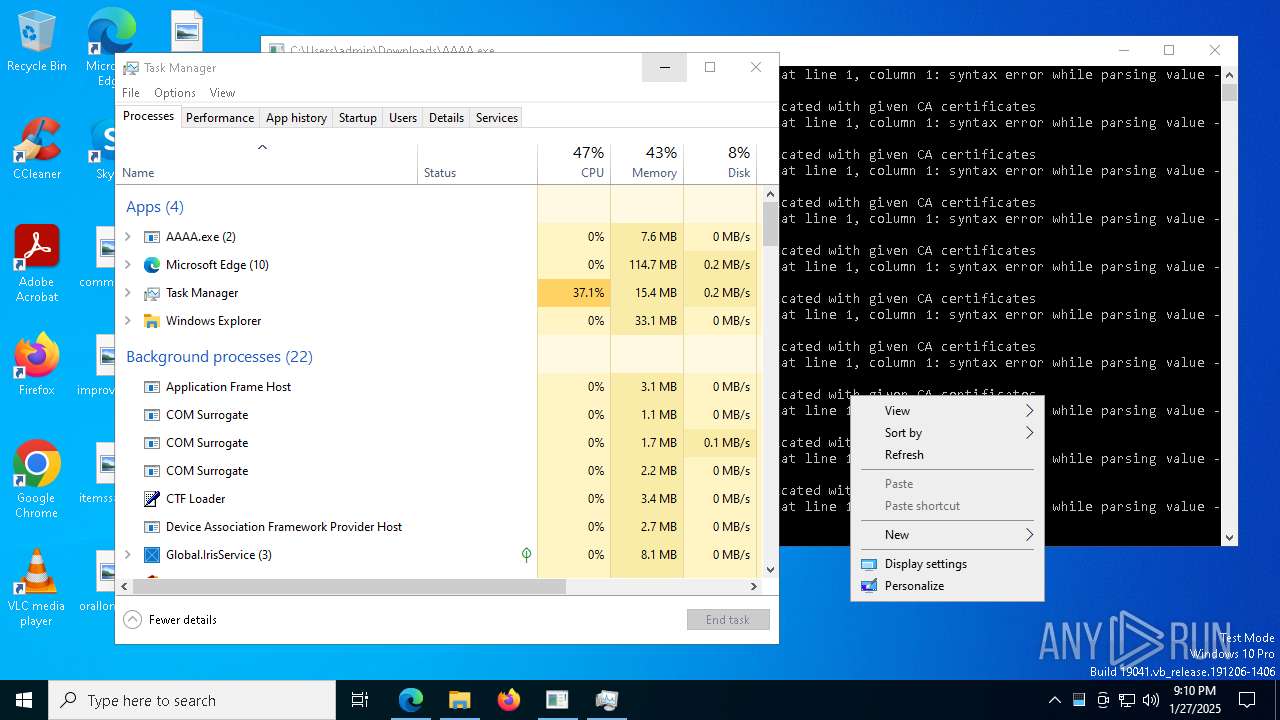
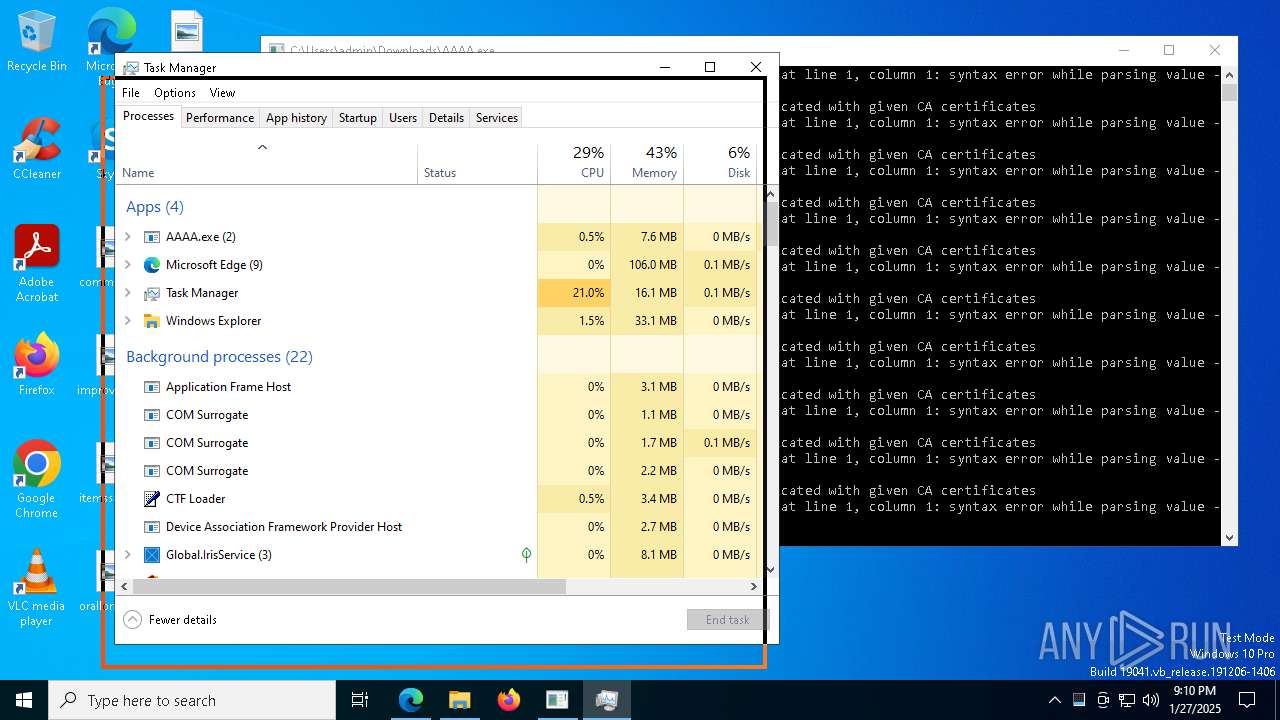
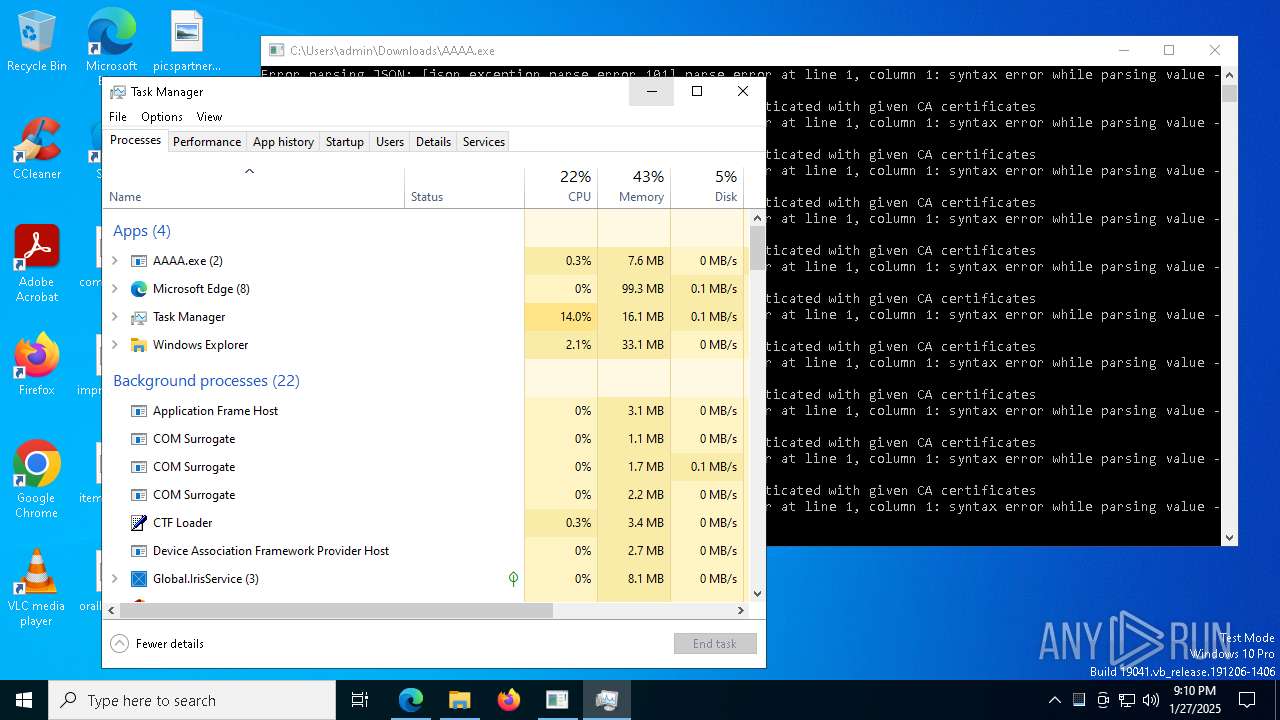
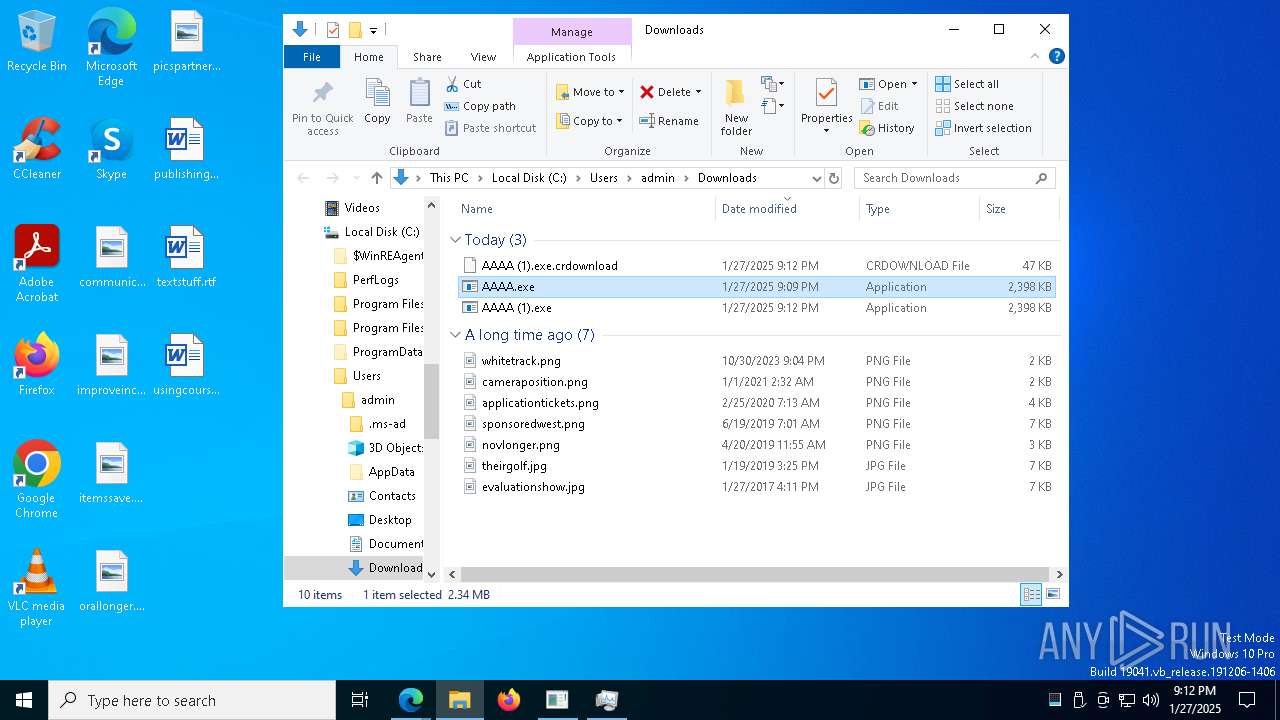
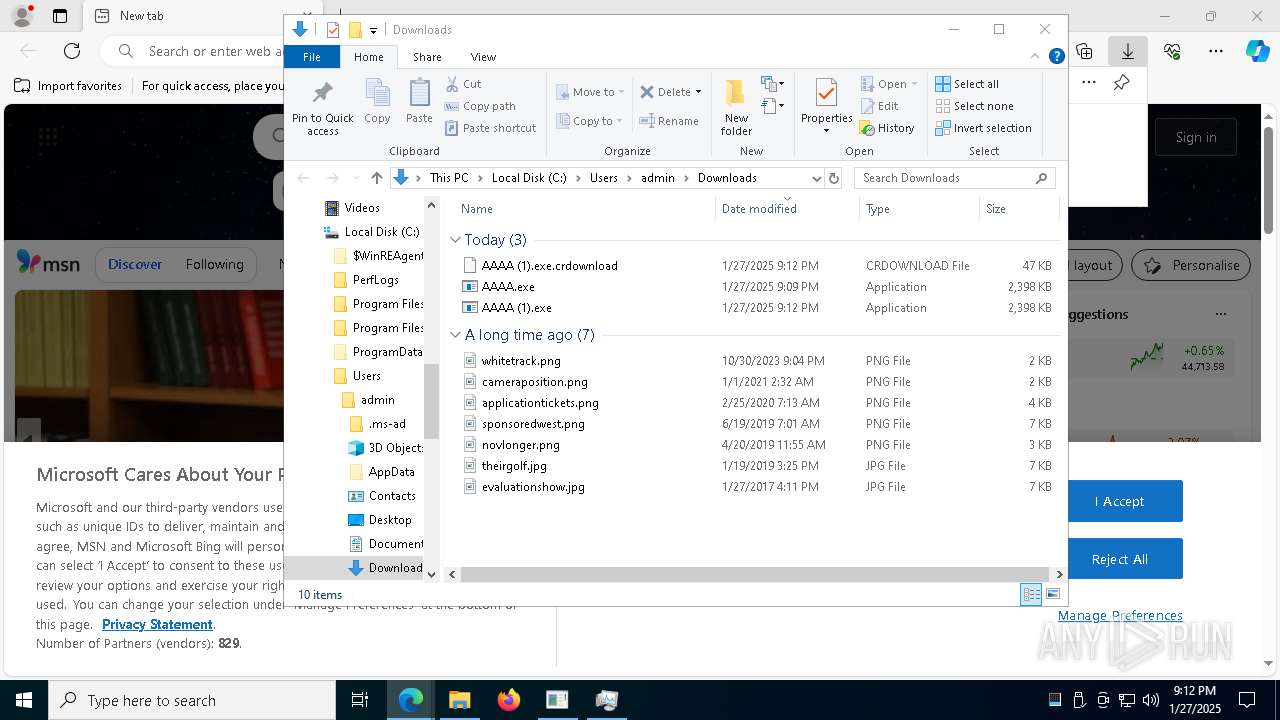
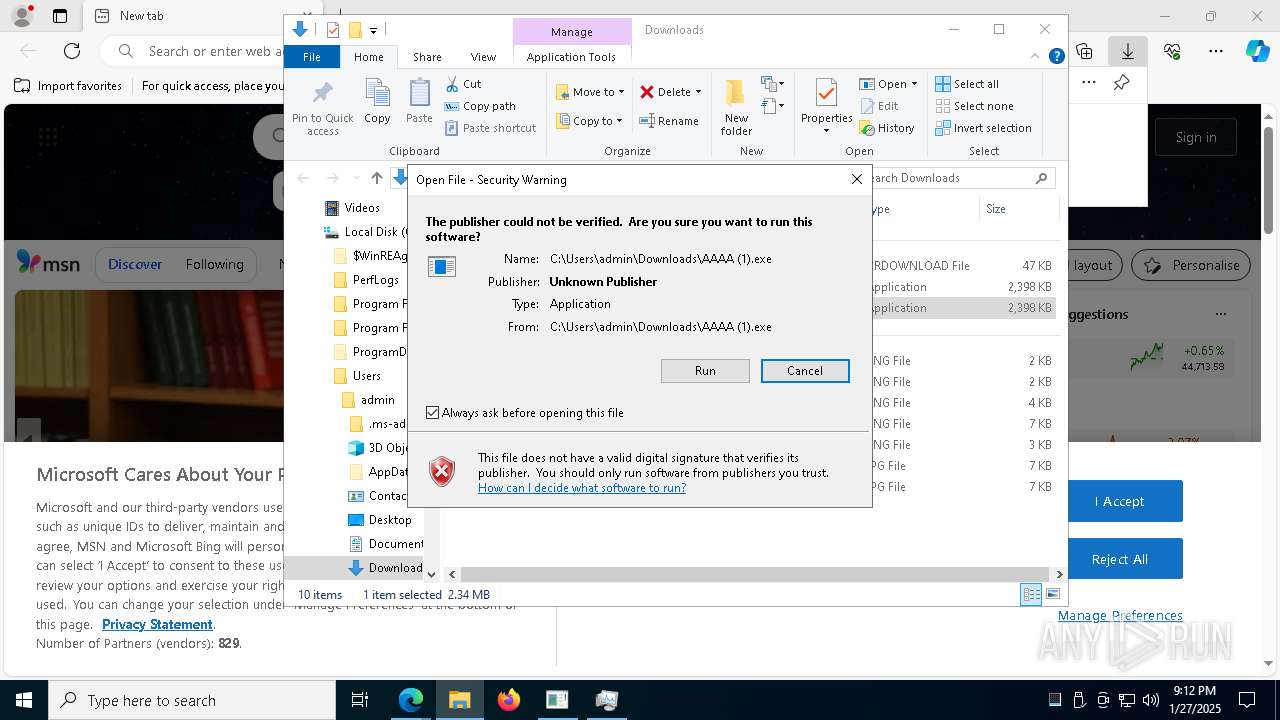
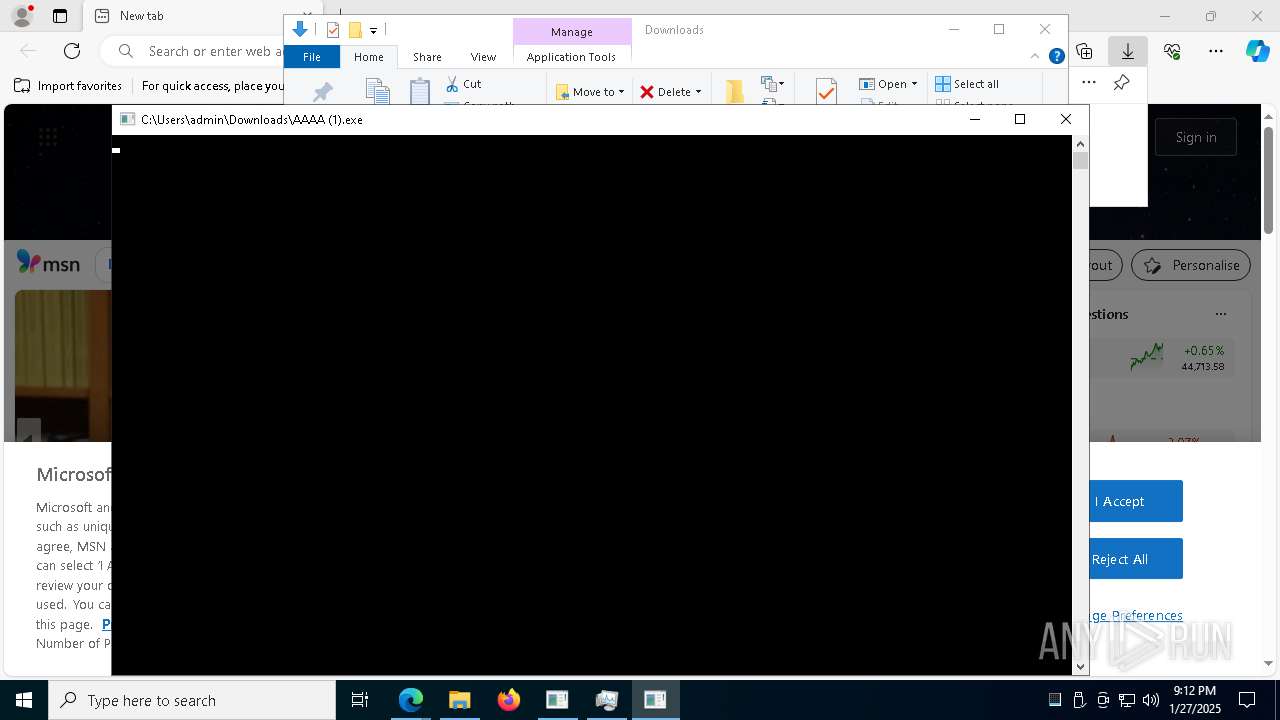
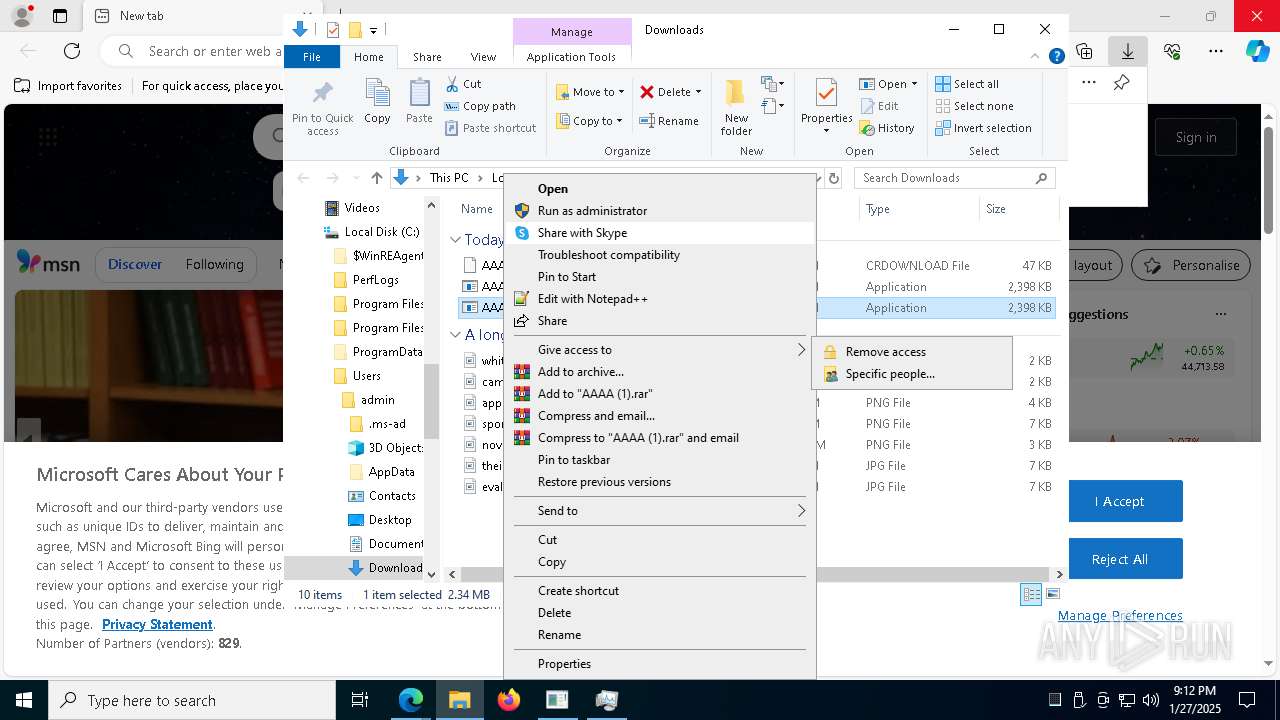
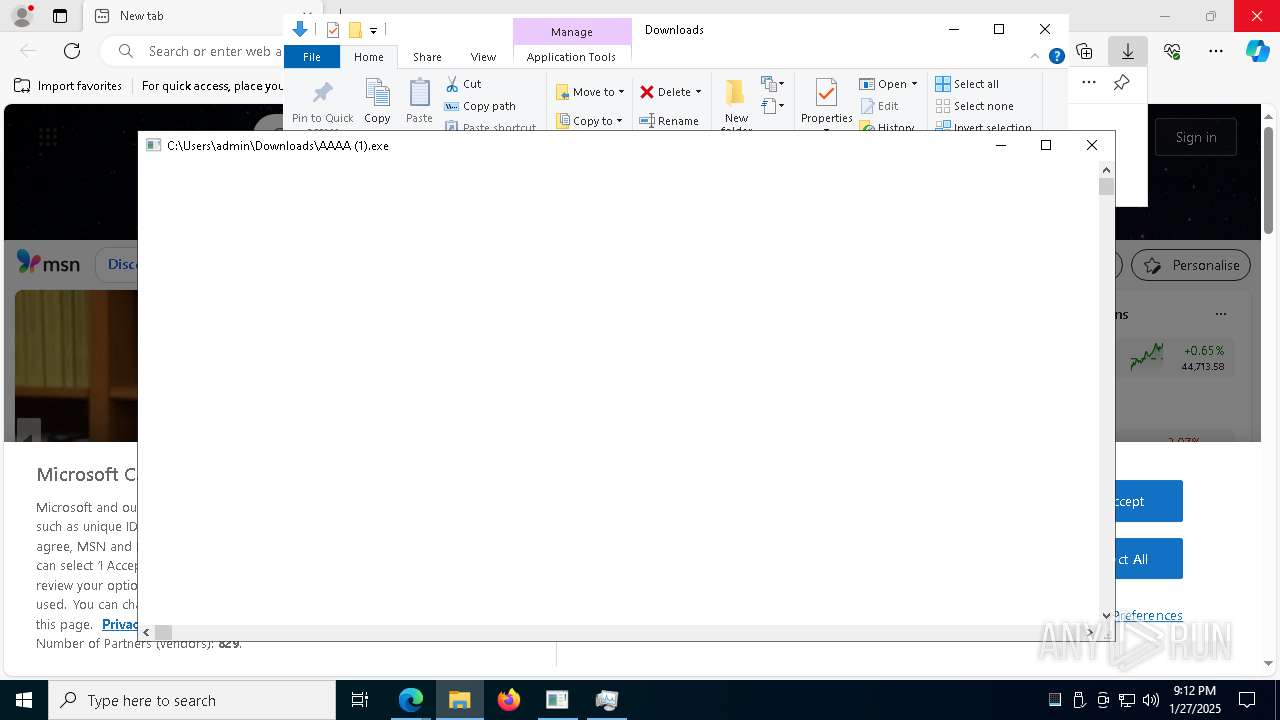
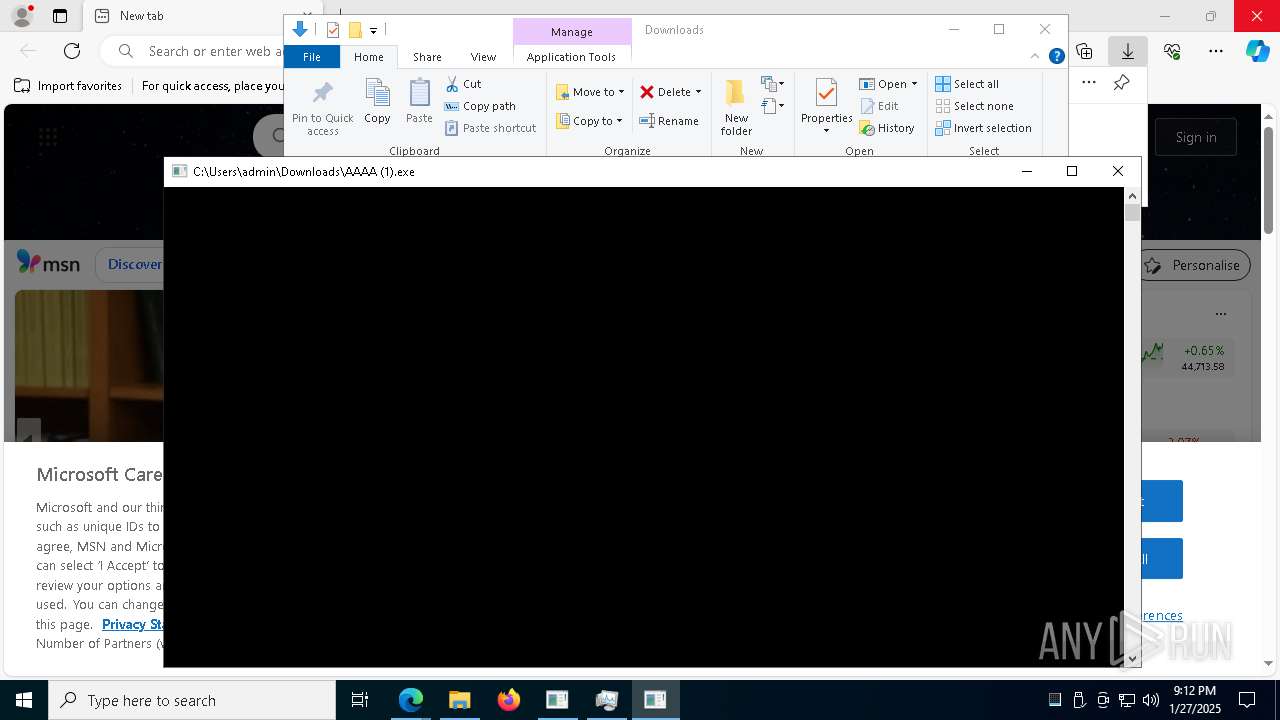
Manual execution by a user
- AAAA.exe (PID: 2928)
- Taskmgr.exe (PID: 1356)
- Taskmgr.exe (PID: 7176)
- AAAA (1).exe (PID: 4300)
- AAAA (1).exe (PID: 7988)
- AAAA (1).exe (PID: 2380)
- msedge.exe (PID: 4624)
Checks supported languages
- identity_helper.exe (PID: 7748)
- AAAA.exe (PID: 2928)
- identity_helper.exe (PID: 1544)
- AAAA (1).exe (PID: 4300)
- AAAA (1).exe (PID: 7988)
- AAAA (1).exe (PID: 2380)
- ShellExperienceHost.exe (PID: 2092)
Reads the computer name
- AAAA.exe (PID: 2928)
- identity_helper.exe (PID: 7748)
- identity_helper.exe (PID: 1544)
- AAAA (1).exe (PID: 4300)
- AAAA (1).exe (PID: 7988)
- AAAA (1).exe (PID: 2380)
- ShellExperienceHost.exe (PID: 2092)
Reads Environment values
- identity_helper.exe (PID: 7748)
- identity_helper.exe (PID: 1544)
Reads the machine GUID from the registry
- AAAA.exe (PID: 2928)
- AAAA (1).exe (PID: 4300)
- AAAA (1).exe (PID: 7988)
- AAAA (1).exe (PID: 2380)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7176)
Application launched itself
- msedge.exe (PID: 6292)
The sample compiled with english language support
- msedge.exe (PID: 4512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(2928) AAAA.exe
Telegram-Tokens (1)7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c
Telegram-Info-Links
7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c
Get info about bothttps://api.telegram.org/bot7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c/getMe
Get incoming updateshttps://api.telegram.org/bot7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c/getUpdates
Get webhookhttps://api.telegram.org/bot7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c
End-PointgetUpdates
Args
offset (1)0
Telegram-Tokens (1)7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c
Telegram-Info-Links
7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c
Get info about bothttps://api.telegram.org/bot7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c/getMe
Get incoming updateshttps://api.telegram.org/bot7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c/getUpdates
Get webhookhttps://api.telegram.org/bot7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7712885736:AAFYmn06okeM1sMcSj5nRHb1fsJJ0WEsf_c/deleteWebhook?drop_pending_updates=true
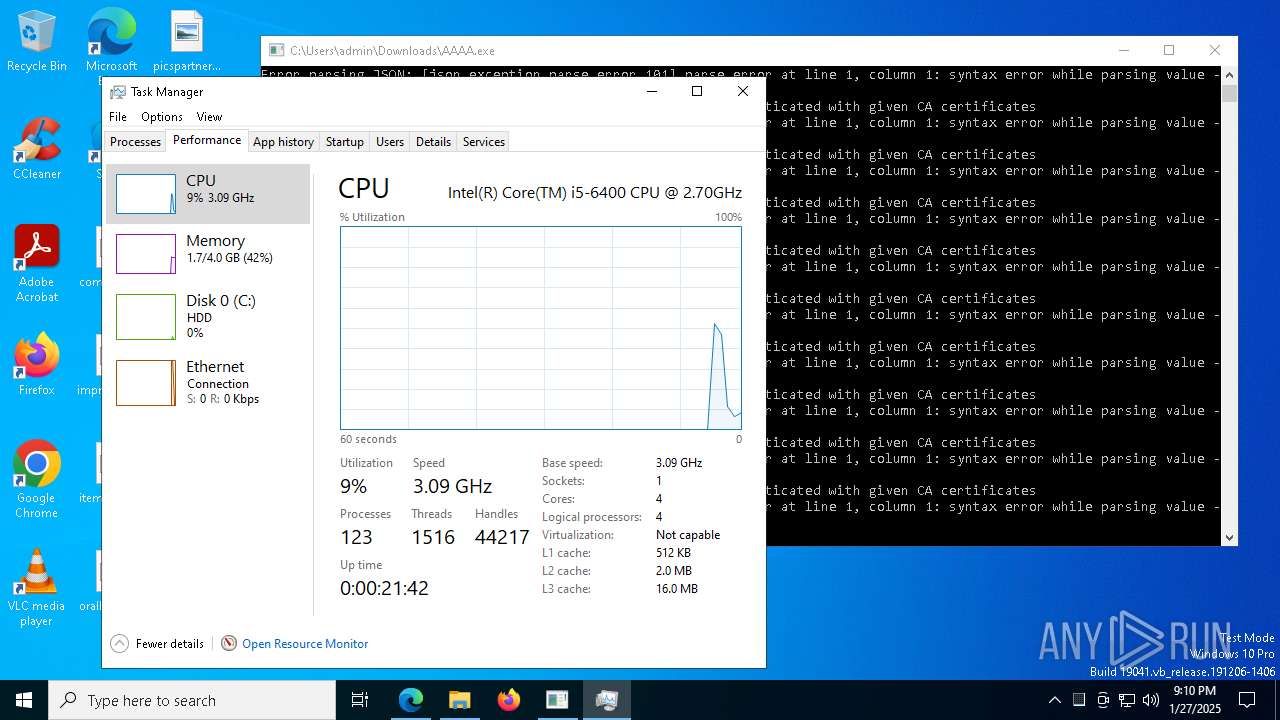
Total processes
207
Monitored processes
68
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4140 --field-trial-handle=2292,i,11125778288752874009,17488054750627696279,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=1528 --field-trial-handle=2292,i,11125778288752874009,17488054750627696279,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6168 --field-trial-handle=2292,i,11125778288752874009,17488054750627696279,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=5848 --field-trial-handle=2292,i,11125778288752874009,17488054750627696279,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AAAA (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1544 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3740 --field-trial-handle=2292,i,11125778288752874009,17488054750627696279,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2092 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4380 --field-trial-handle=2292,i,11125778288752874009,17488054750627696279,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2092 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\Downloads\AAAA (1).exe" | C:\Users\admin\Downloads\AAAA (1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
48 247
Read events
48 201
Write events
27
Delete events
19
Modification events
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 73EB6CC64C8B2F00 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F4C484C64C8B2F00 | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328358 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7D2429AC-D87E-4D7B-94B7-A2161430377F} | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328358 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7C856C93-5DA5-4DAE-B67F-273107A464B8} | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (6292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
54
Suspicious files
615
Text files
121
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1356dd.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1356dd.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1356ed.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1356ed.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1356ed.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
333
DNS requests
148
Threats
476
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6484 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7788 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7788 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7964 | svchost.exe | GET | 206 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738130604&P2=404&P3=2&P4=N0iPD38%2fEiM%2fYS9CkM%2ftS9eBFdAHDn9mb34mObNvV48TDD7%2br6dpQ%2fPlZZznqSVTwFnL7okABVUVN8sU4tBOEg%3d%3d | unknown | — | — | whitelisted |
7964 | svchost.exe | GET | 206 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738130604&P2=404&P3=2&P4=N0iPD38%2fEiM%2fYS9CkM%2ftS9eBFdAHDn9mb34mObNvV48TDD7%2br6dpQ%2fPlZZznqSVTwFnL7okABVUVN8sU4tBOEg%3d%3d | unknown | — | — | whitelisted |
7964 | svchost.exe | GET | 206 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738130604&P2=404&P3=2&P4=N0iPD38%2fEiM%2fYS9CkM%2ftS9eBFdAHDn9mb34mObNvV48TDD7%2br6dpQ%2fPlZZznqSVTwFnL7okABVUVN8sU4tBOEg%3d%3d | unknown | — | — | whitelisted |
7964 | svchost.exe | HEAD | 200 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738130604&P2=404&P3=2&P4=N0iPD38%2fEiM%2fYS9CkM%2ftS9eBFdAHDn9mb34mObNvV48TDD7%2br6dpQ%2fPlZZznqSVTwFnL7okABVUVN8sU4tBOEg%3d%3d | unknown | — | — | whitelisted |
7964 | svchost.exe | GET | 206 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738130604&P2=404&P3=2&P4=N0iPD38%2fEiM%2fYS9CkM%2ftS9eBFdAHDn9mb34mObNvV48TDD7%2br6dpQ%2fPlZZznqSVTwFnL7okABVUVN8sU4tBOEg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
6772 | msedge.exe | 162.159.129.233:443 | cdn.discordapp.com | — | — | whitelisted |
6772 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6292 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6772 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6772 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6772 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
cdn.discordapp.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6772 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6772 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
2192 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
2928 | AAAA.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
2928 | AAAA.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
2928 | AAAA.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
2928 | AAAA.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
2928 | AAAA.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
2928 | AAAA.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
2928 | AAAA.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |