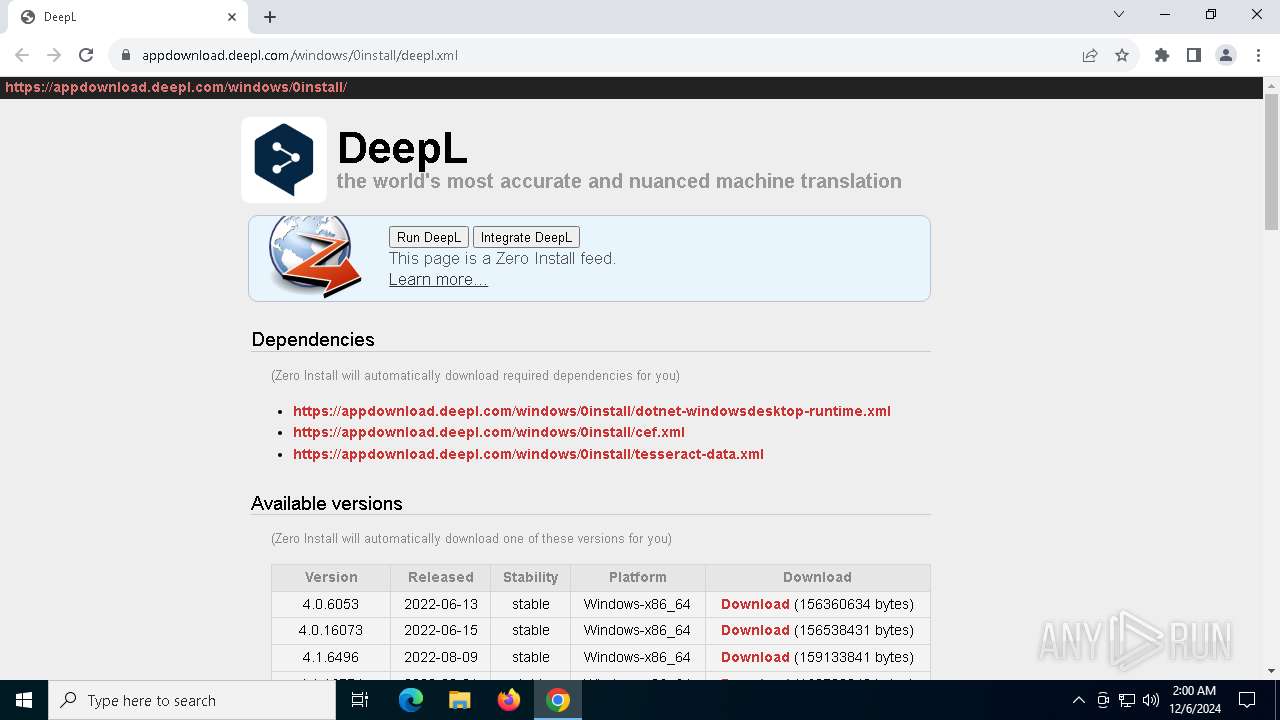
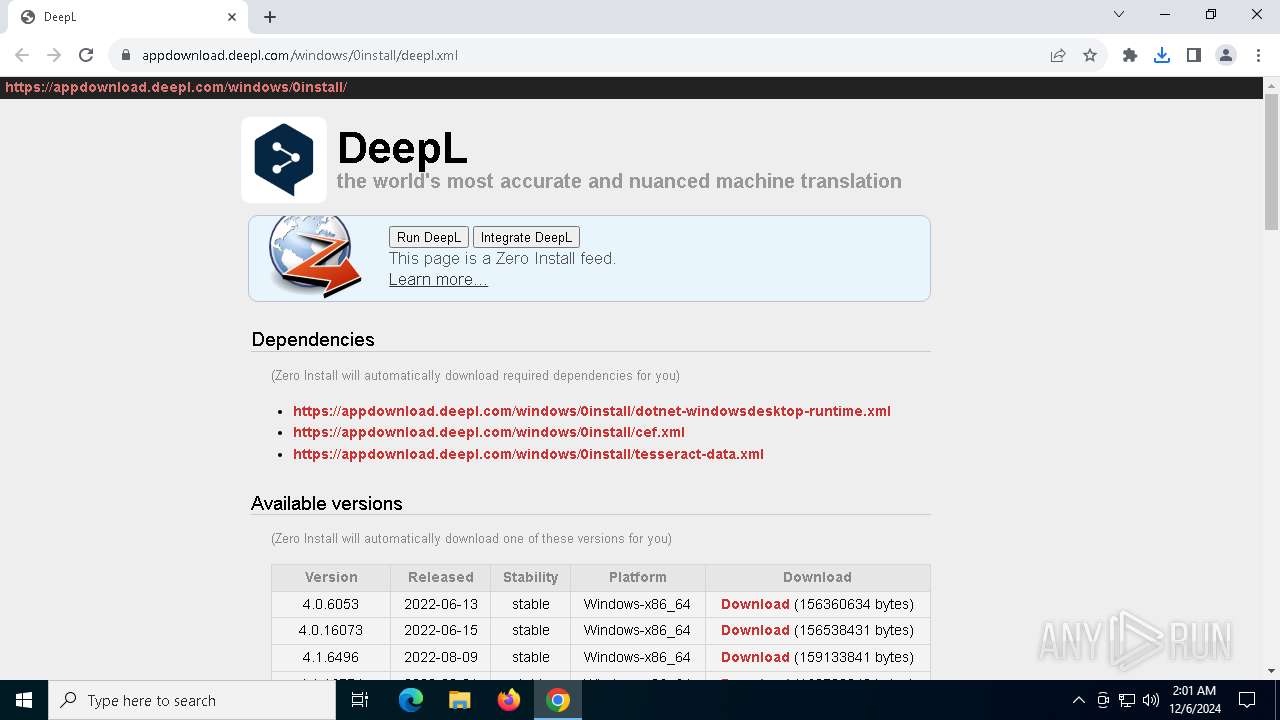
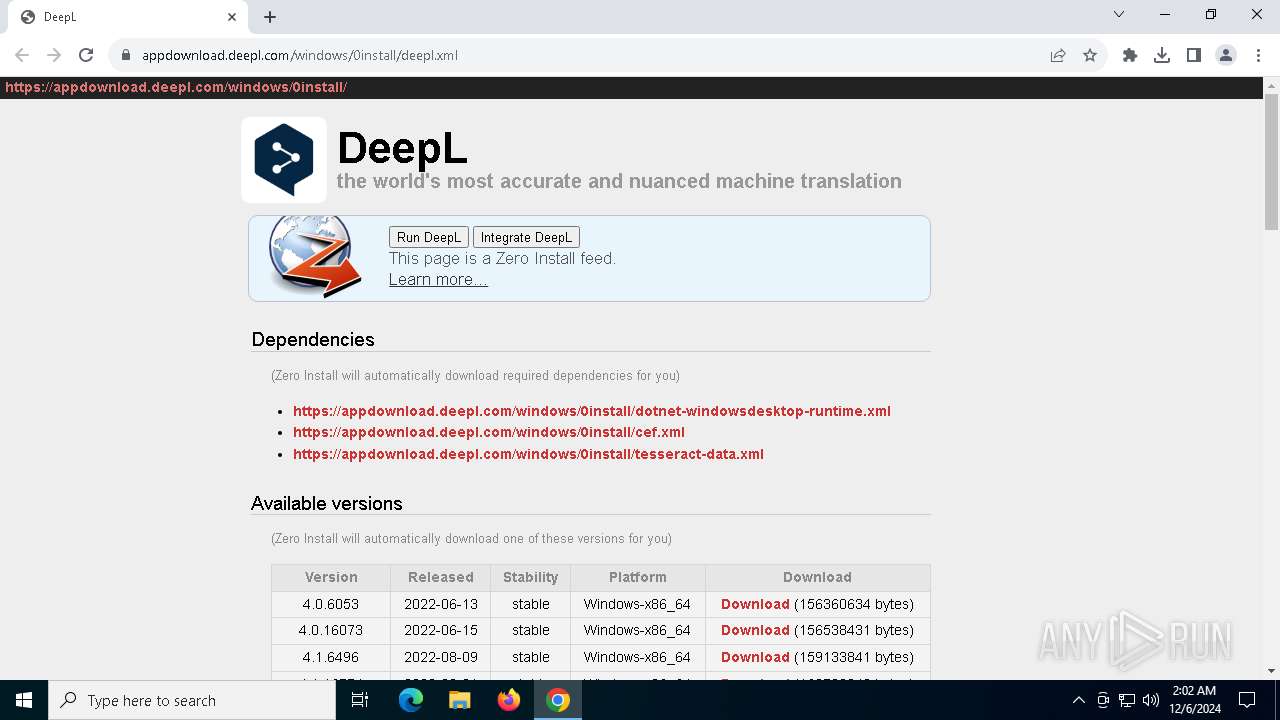
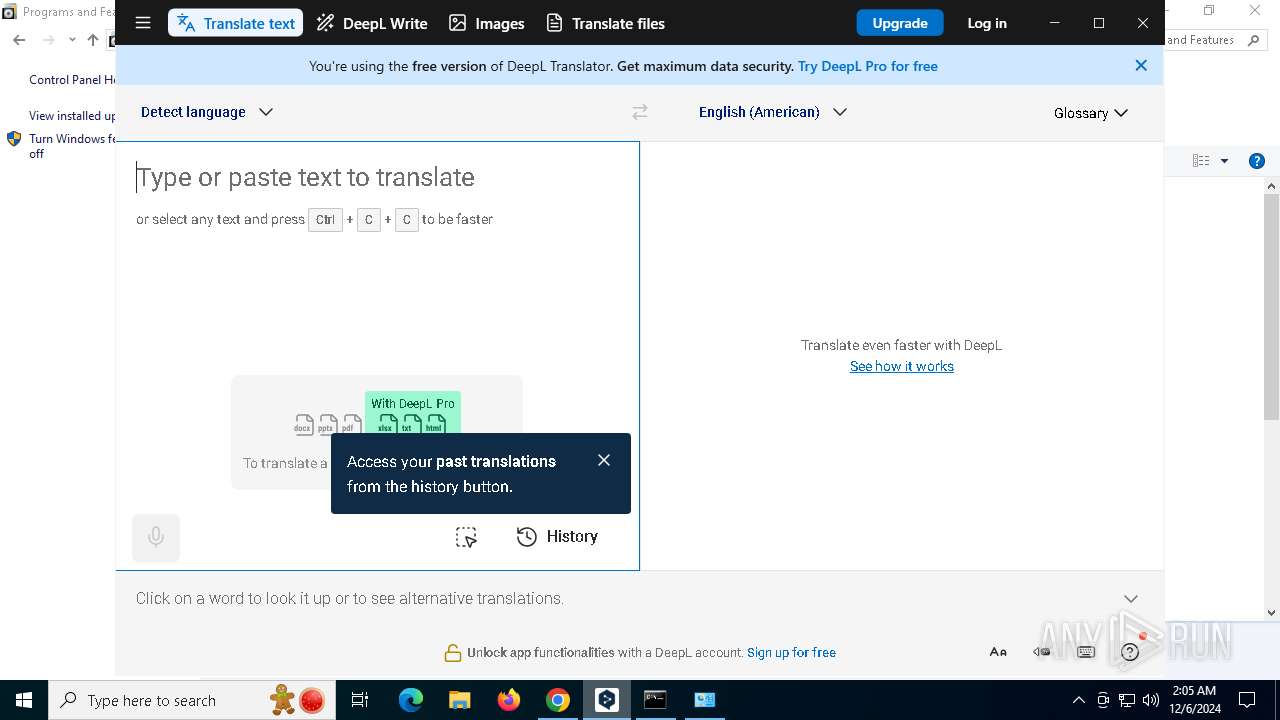
| URL: | https://appdownload.deepl.com/windows/0install/deepl.xml |
| Full analysis: | https://app.any.run/tasks/ce2a9f2c-fb11-41e4-984d-9ed0615e6167 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2024, 02:00:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 4B0E406C81176401A57320BDC2A01531 |
| SHA1: | 4637E5B319D4150B70296046B2F3EBB650B6939C |
| SHA256: | B06B67932007BF915F405696CE973A083D5E22CD5B028074BAC00FD2A646B278 |
| SSDEEP: | 3:N8a8KnjZ3SM/6J:2a3njZ3Sei |
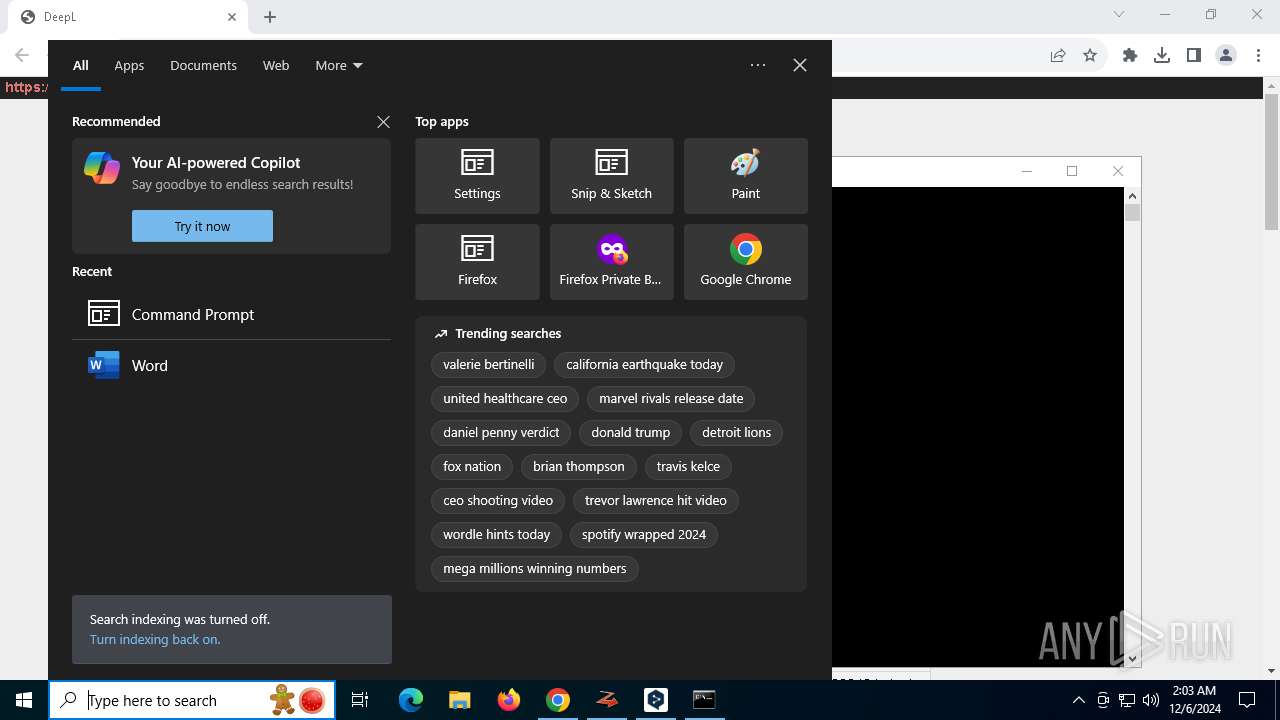
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- DeepL.exe (PID: 7144)
- 0install-win.exe (PID: 1804)
Process drops legitimate windows executable
- DeepL.exe (PID: 7144)
- 0install-win.exe (PID: 1804)
The process creates files with name similar to system file names
- DeepL.exe (PID: 7144)
- 0install-win.exe (PID: 1804)
The process drops C-runtime libraries
- 0install-win.exe (PID: 1804)
Detected use of alternative data streams (AltDS)
- 0install-win.exe (PID: 1804)
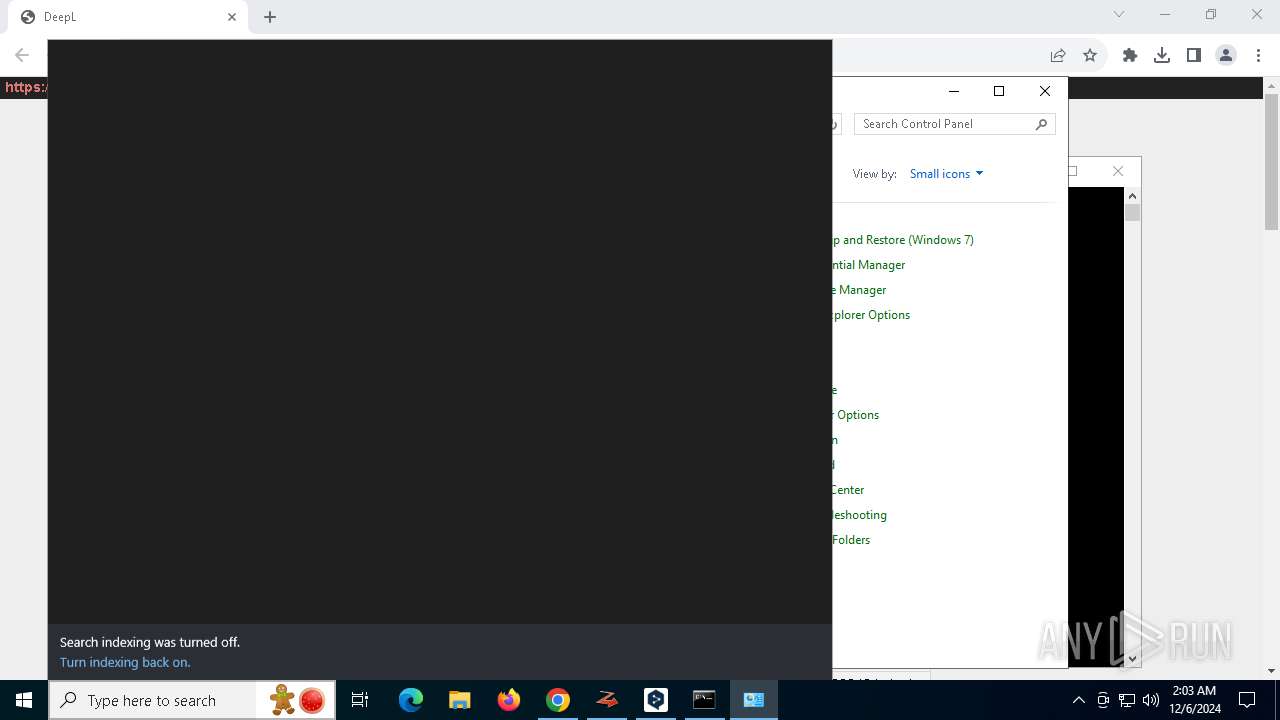
Reads security settings of Internet Explorer
- DeepL.exe (PID: 2280)
- 0install.exe (PID: 5252)
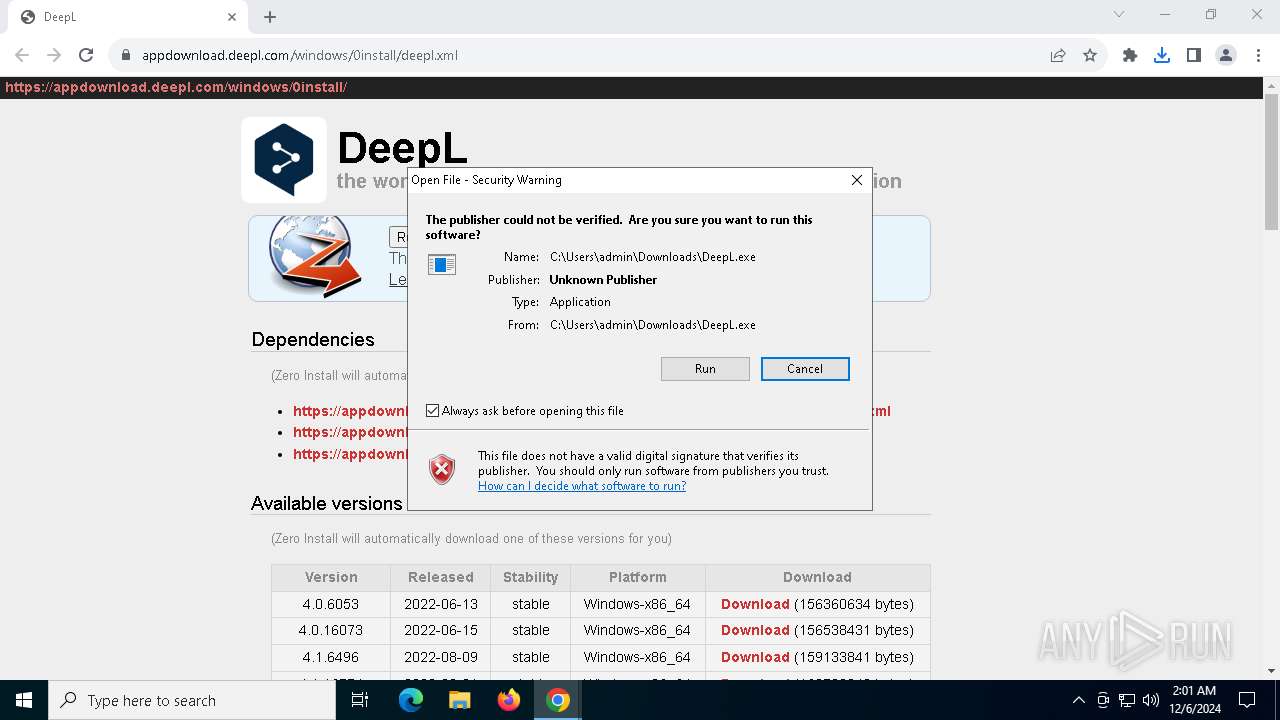
Checks Windows Trust Settings
- DeepL.exe (PID: 2280)
Reads the date of Windows installation
- 0install.exe (PID: 5252)
There is functionality for taking screenshot (YARA)
- DeepL.exe (PID: 2280)
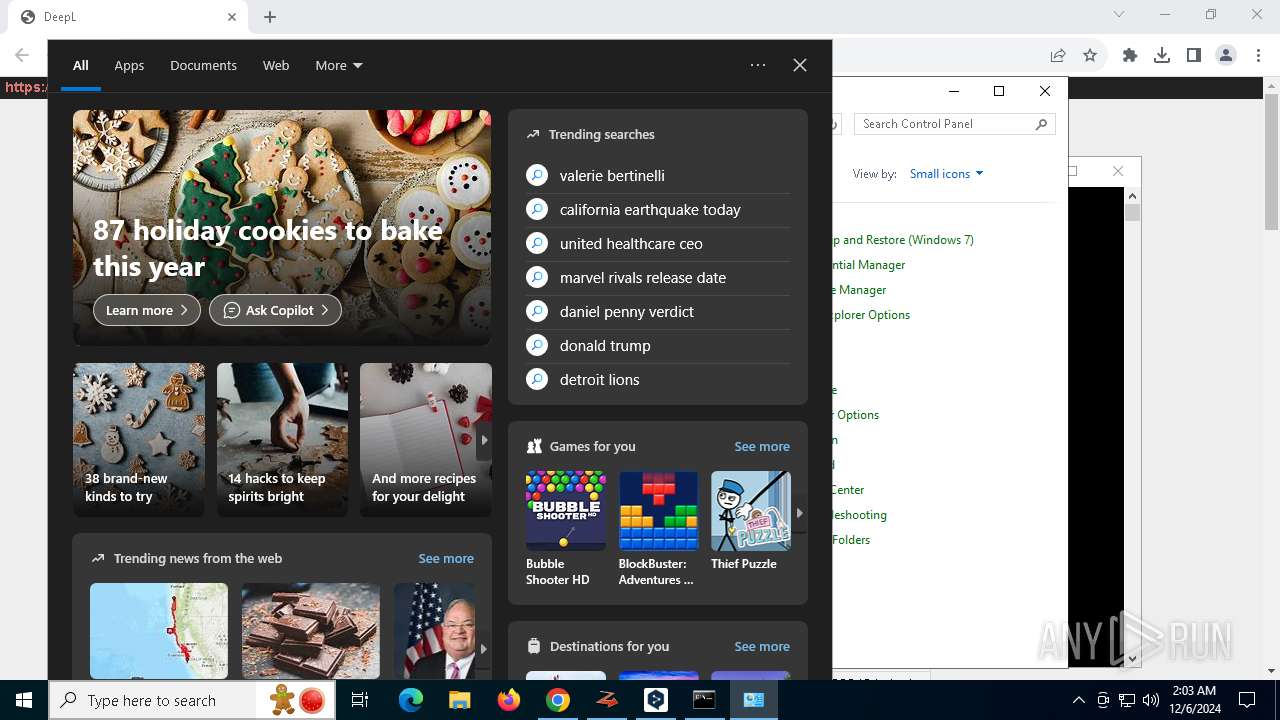
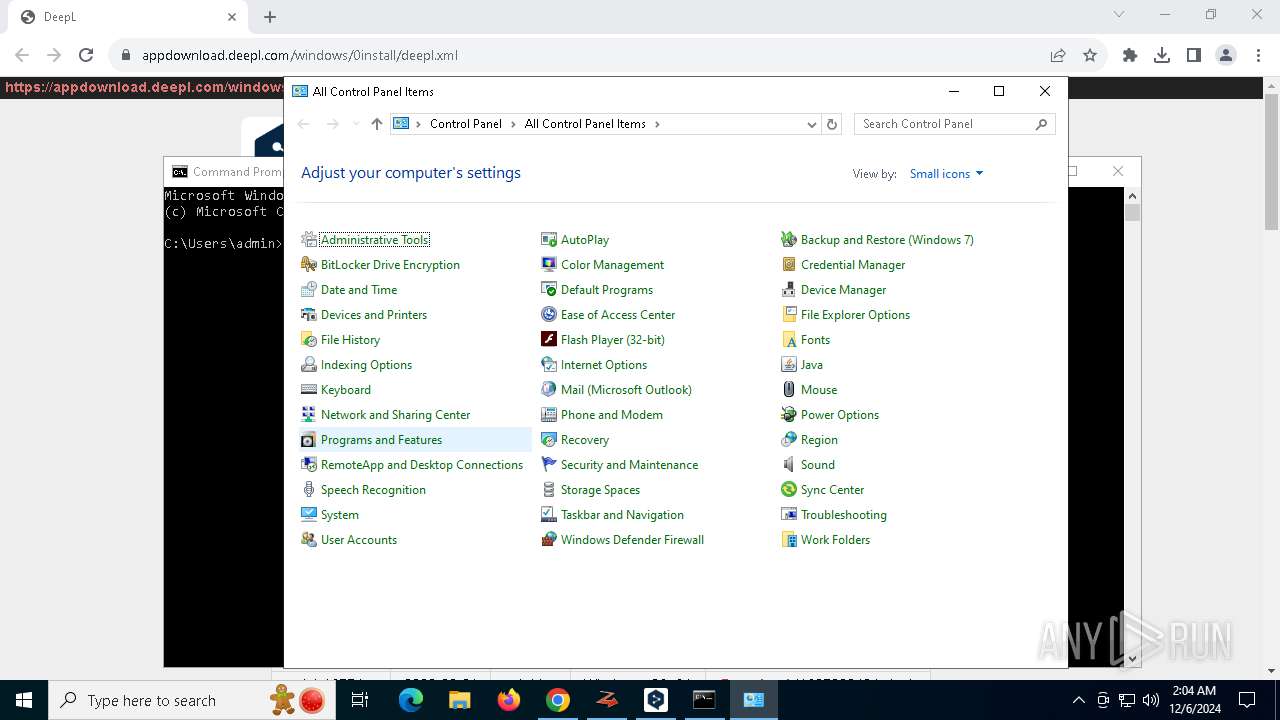
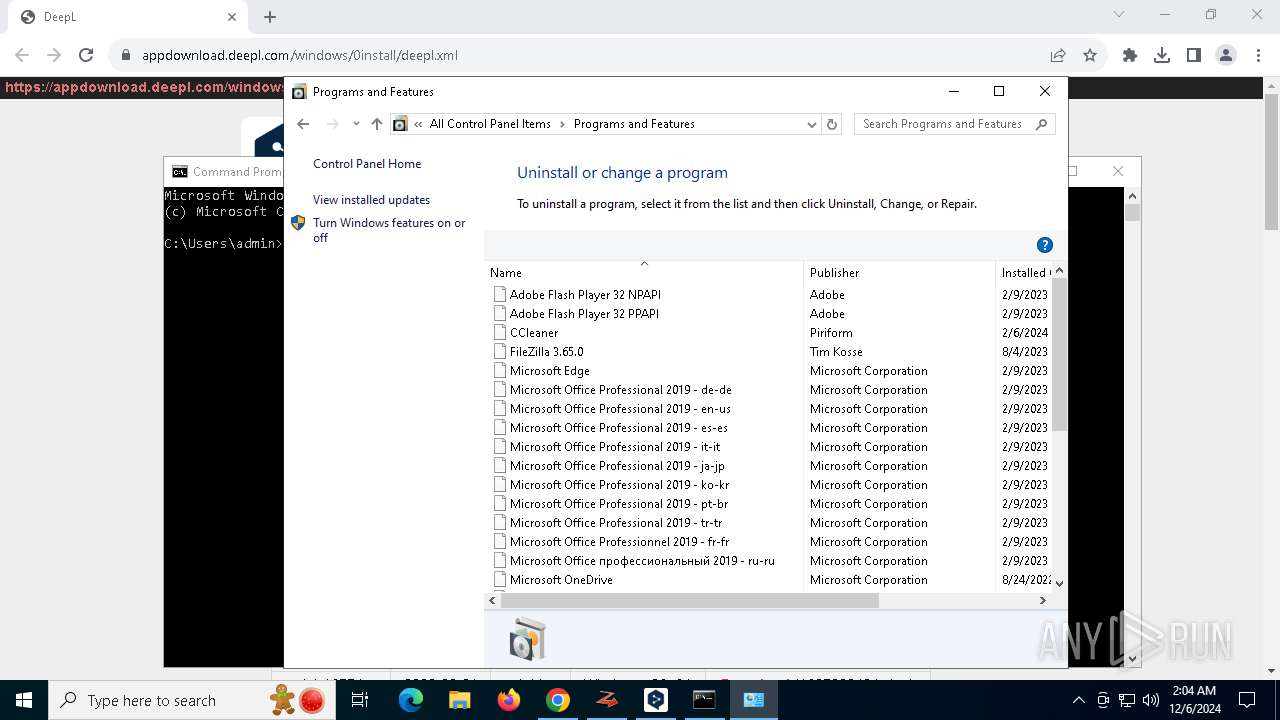
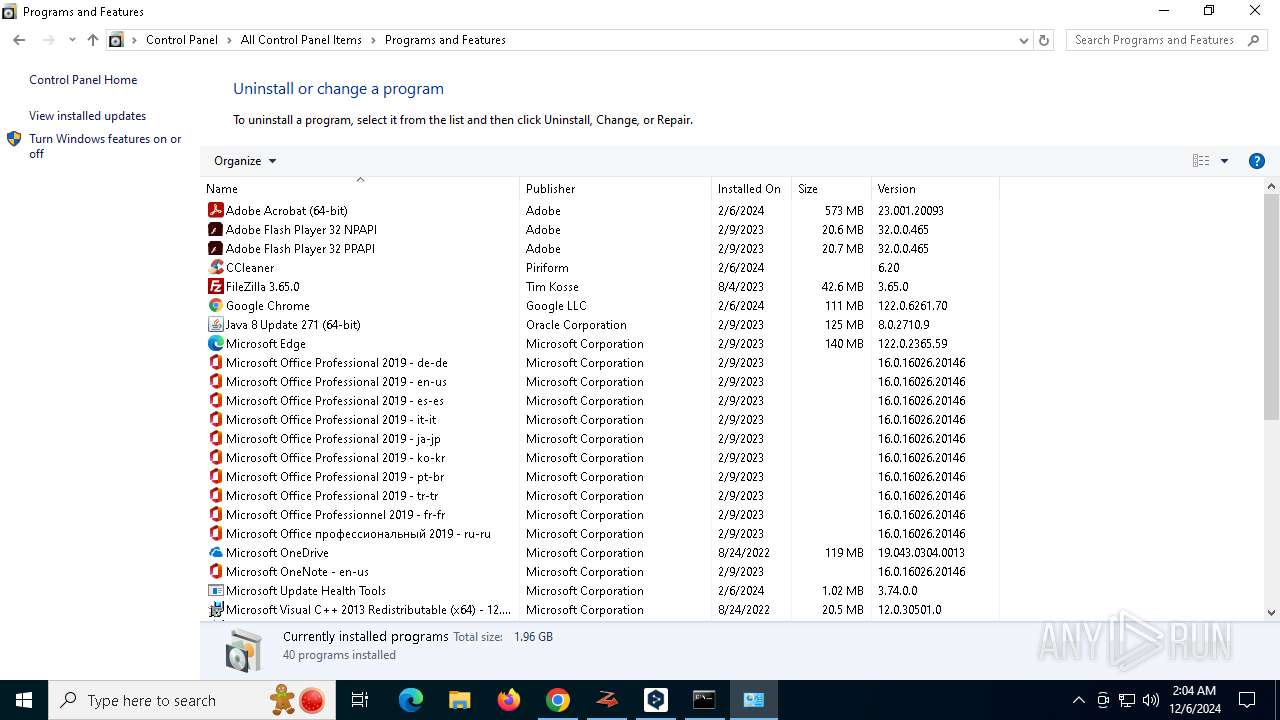
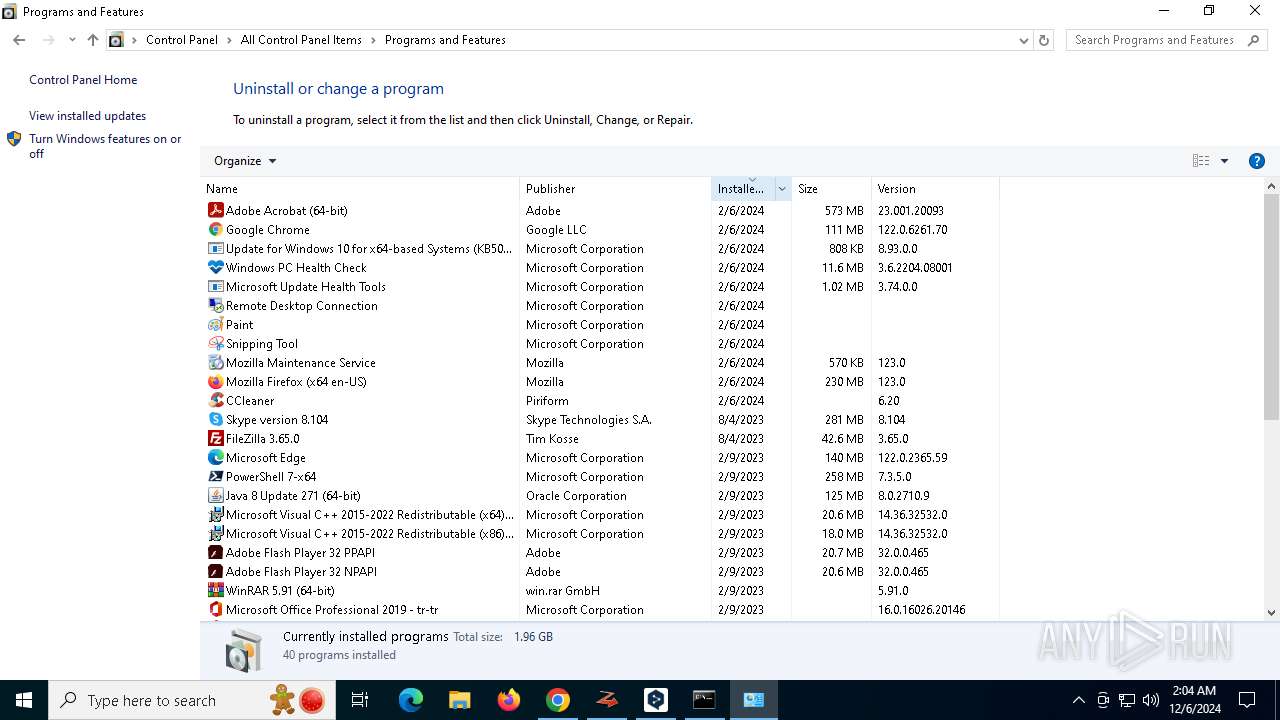
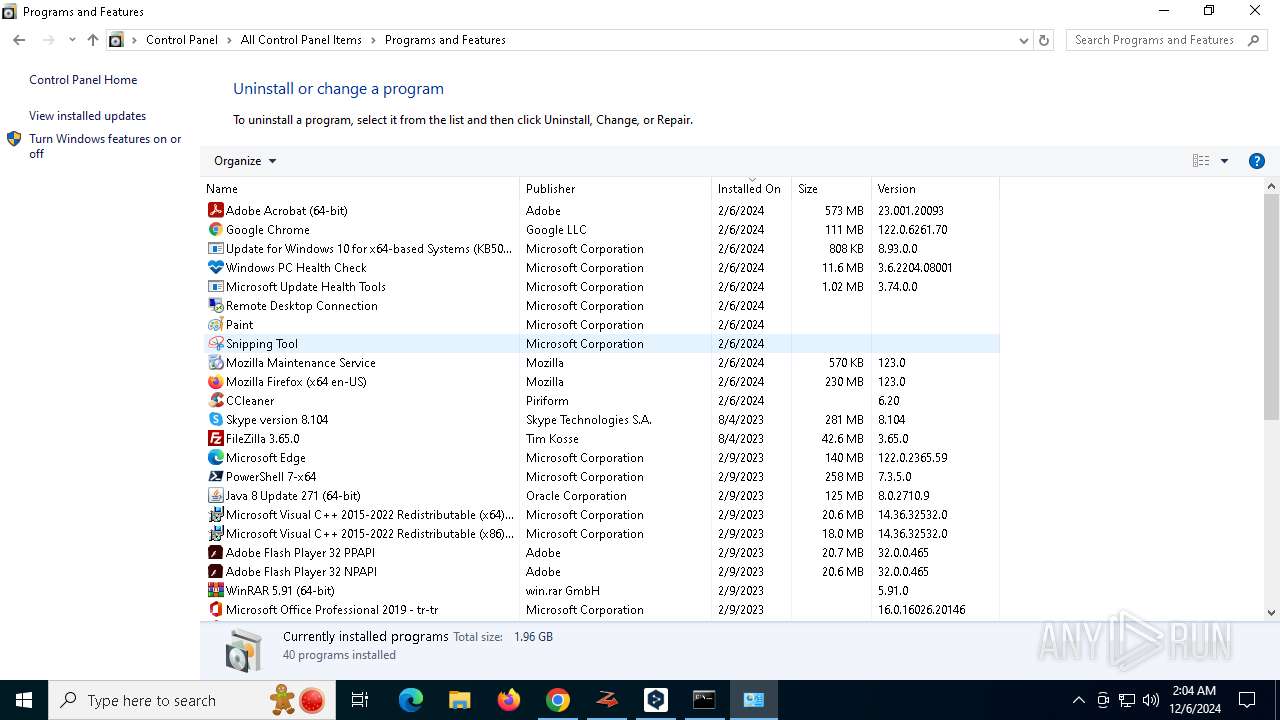
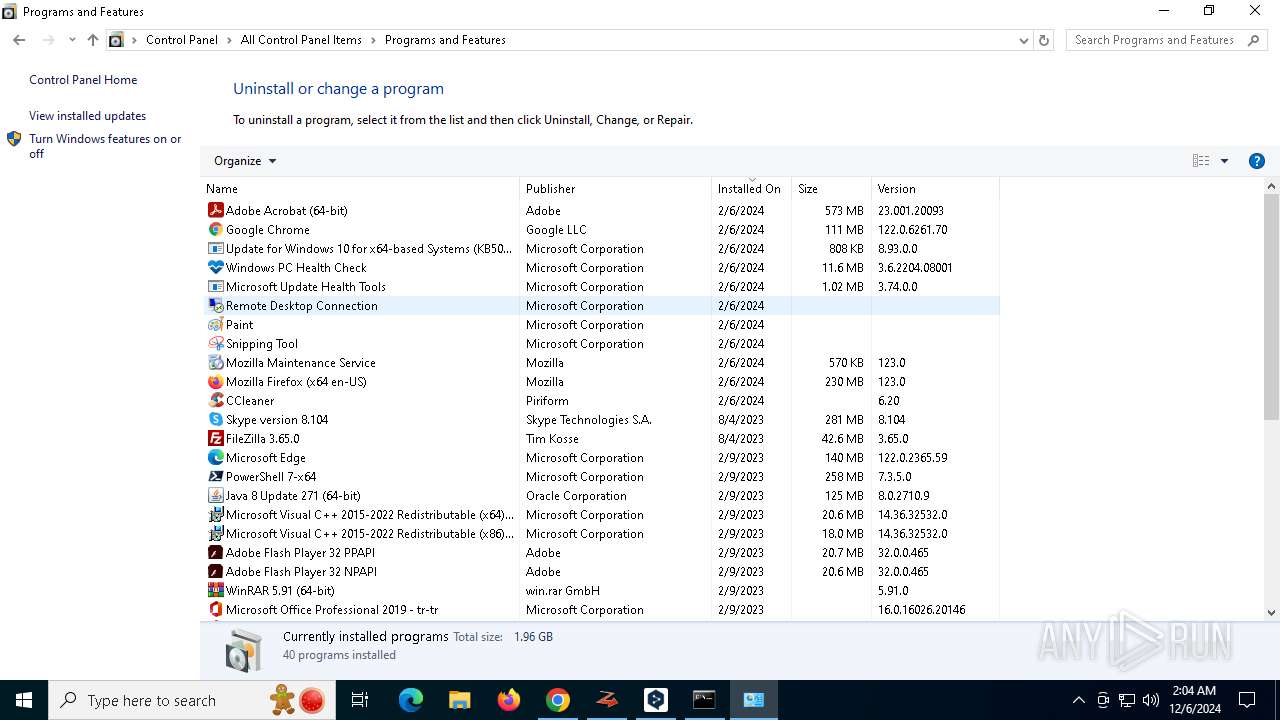
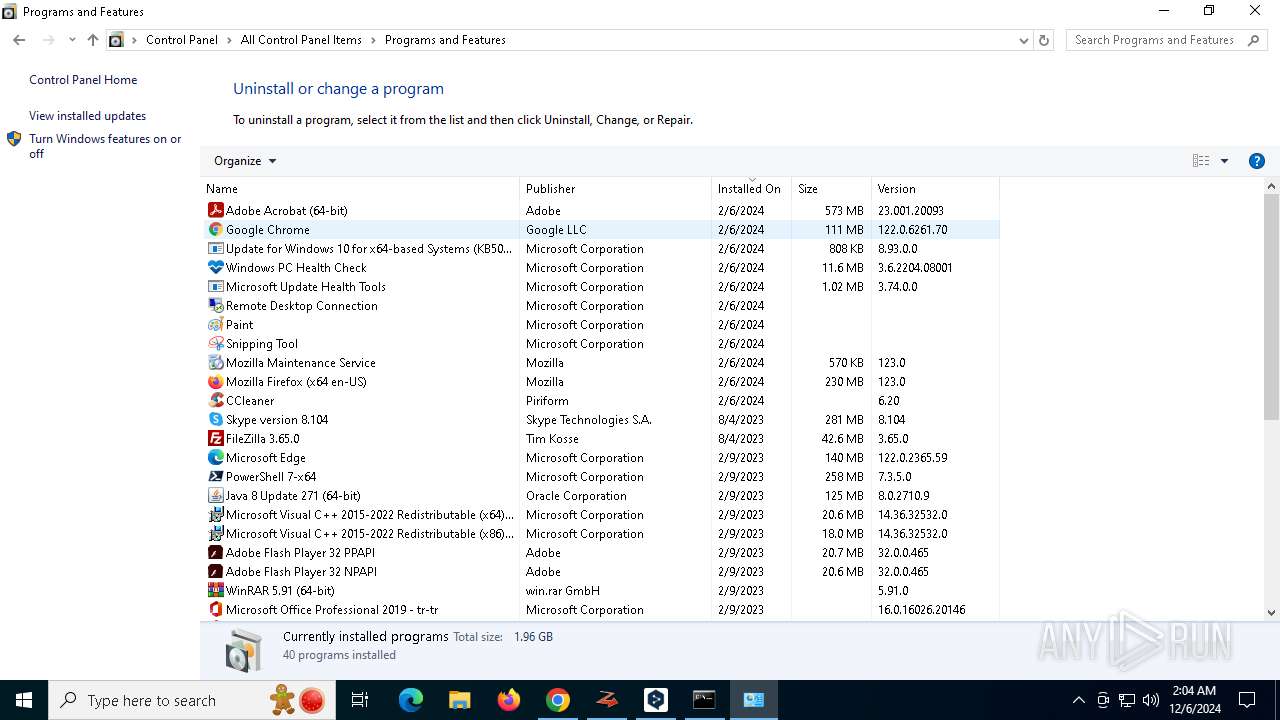
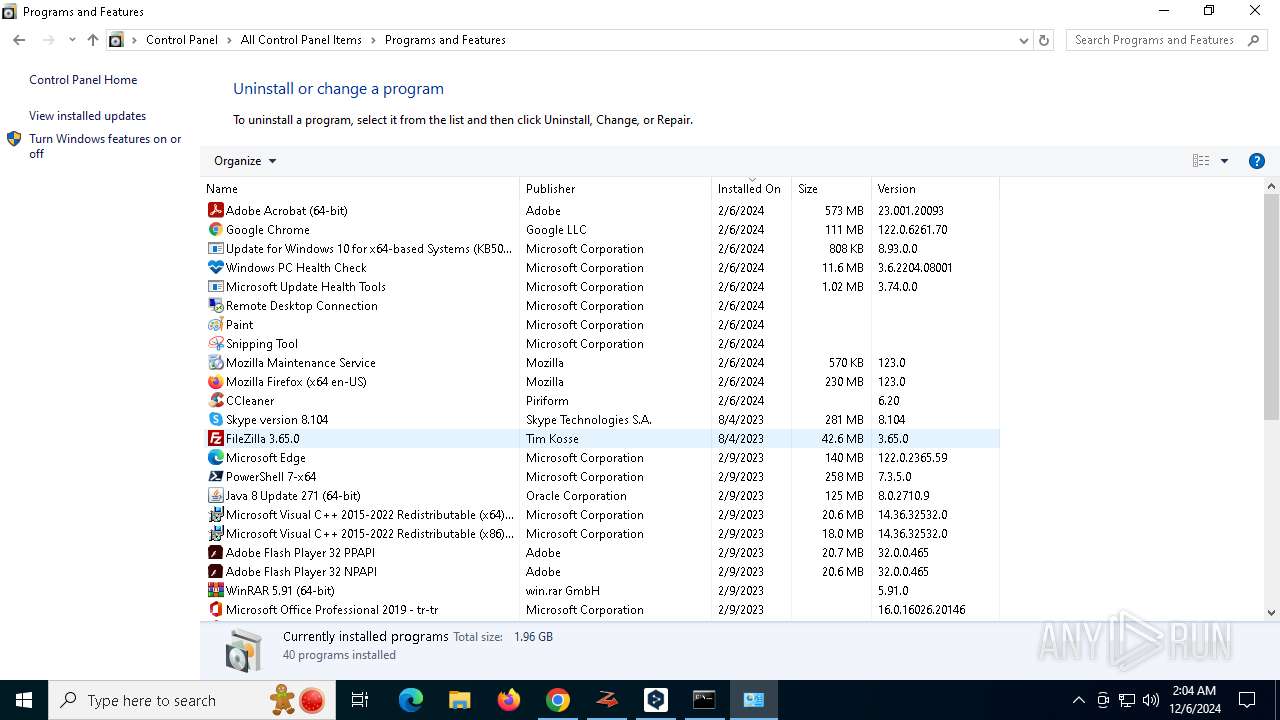
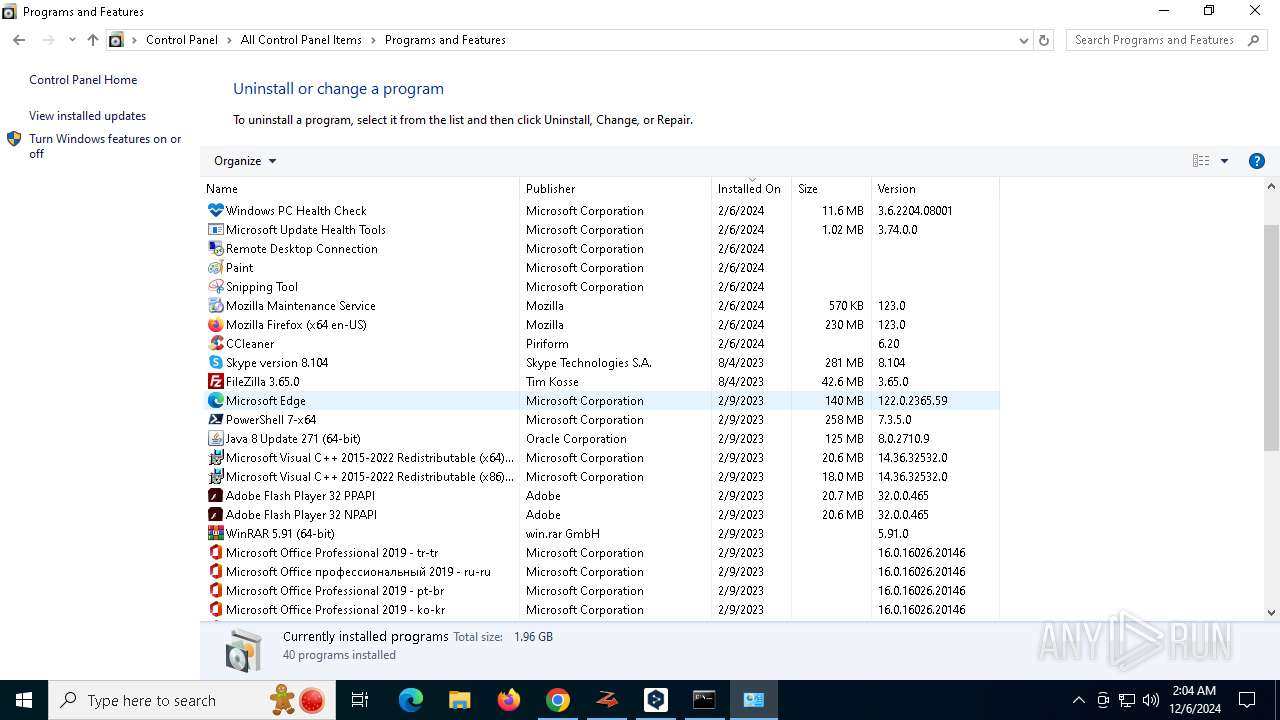
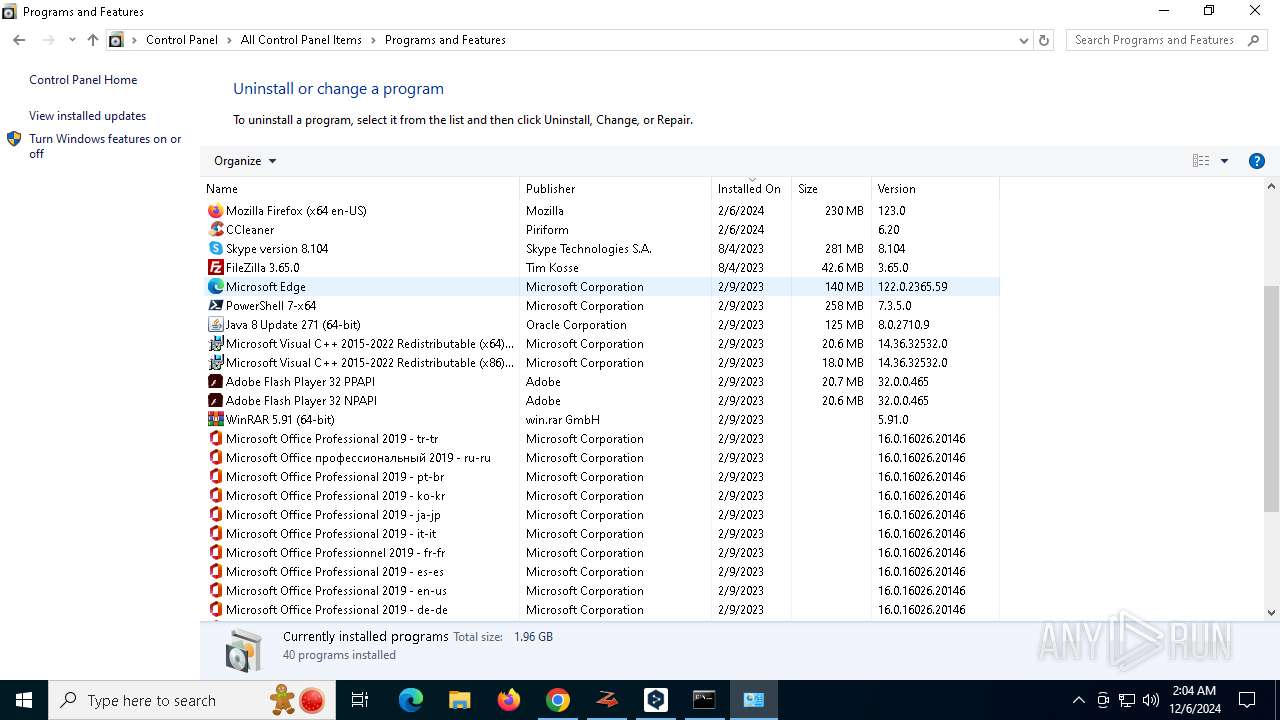
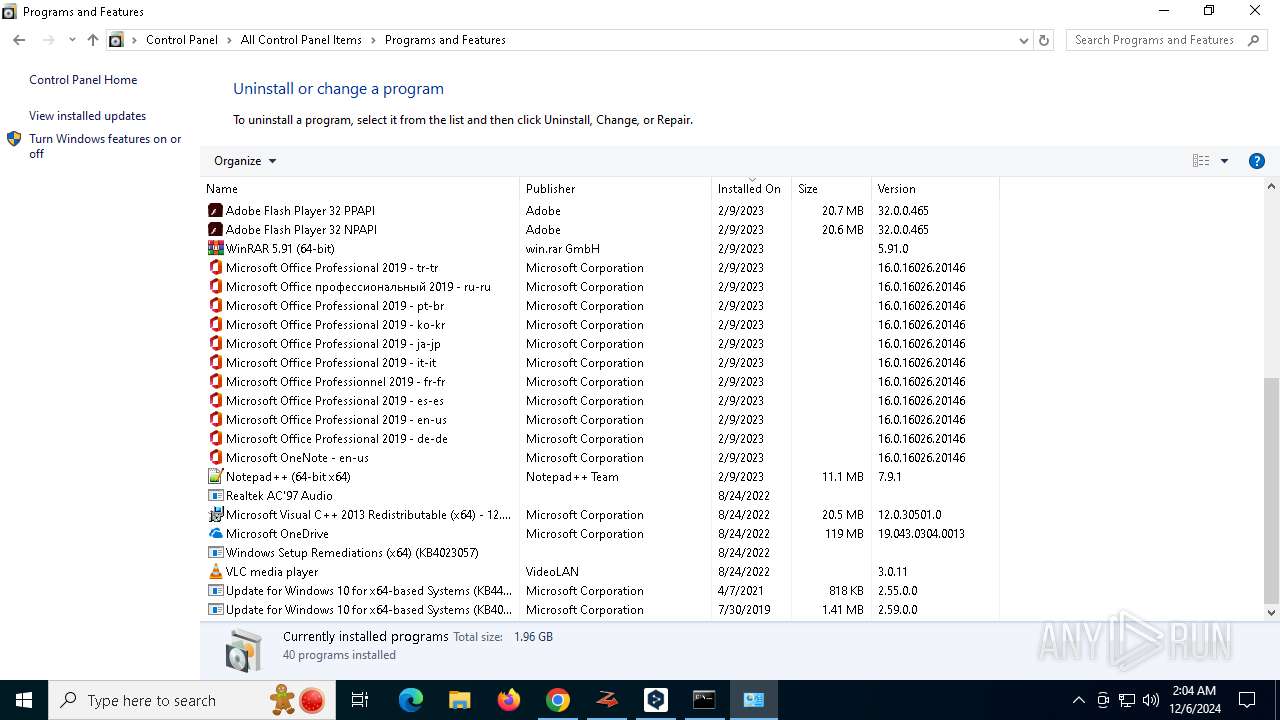
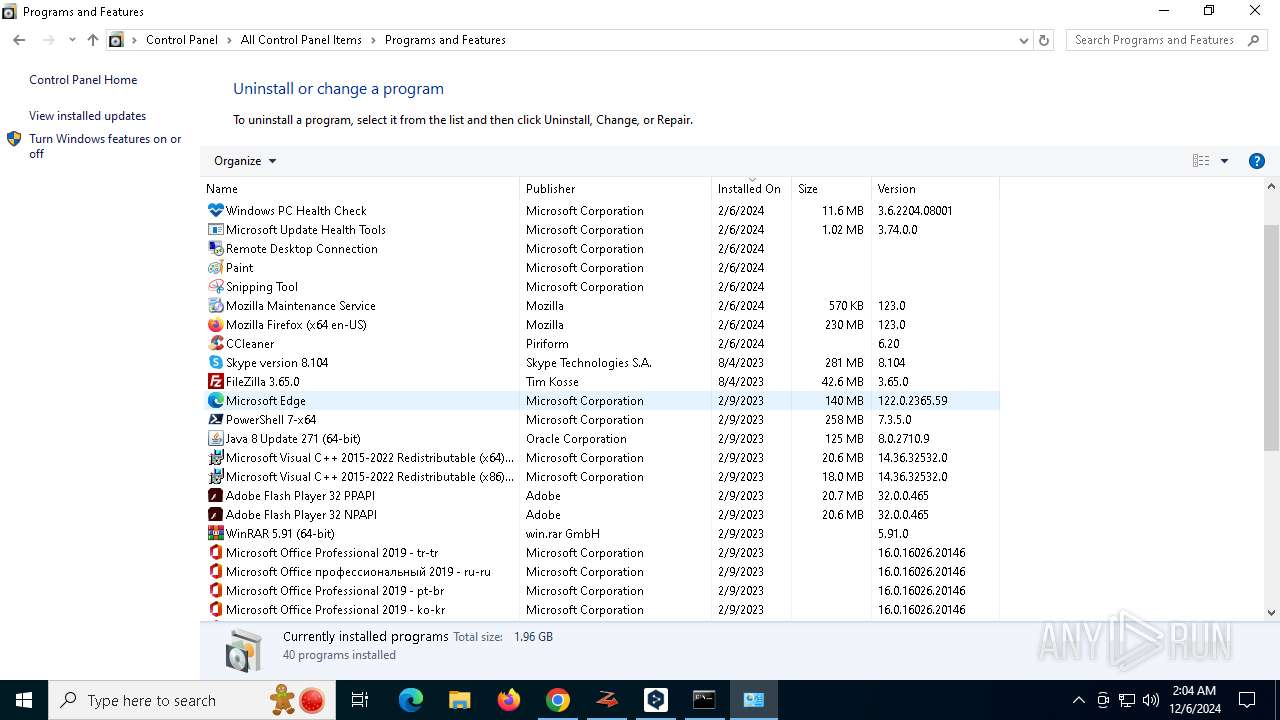
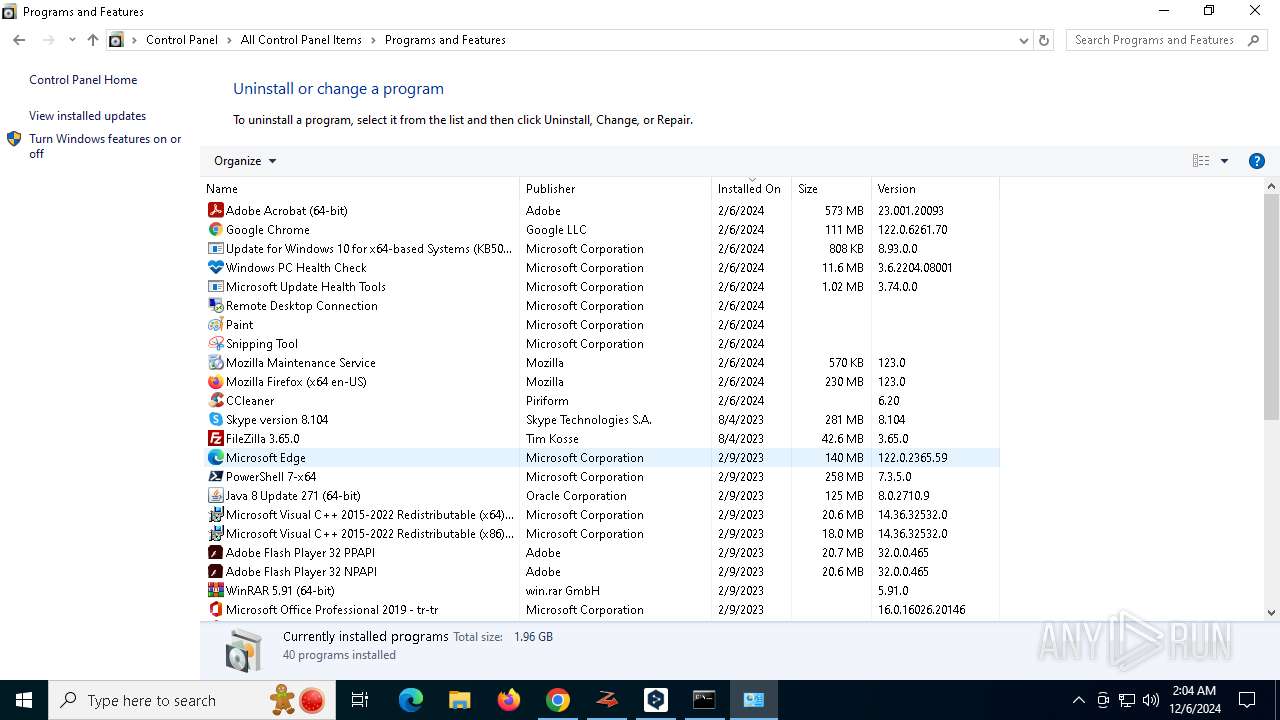
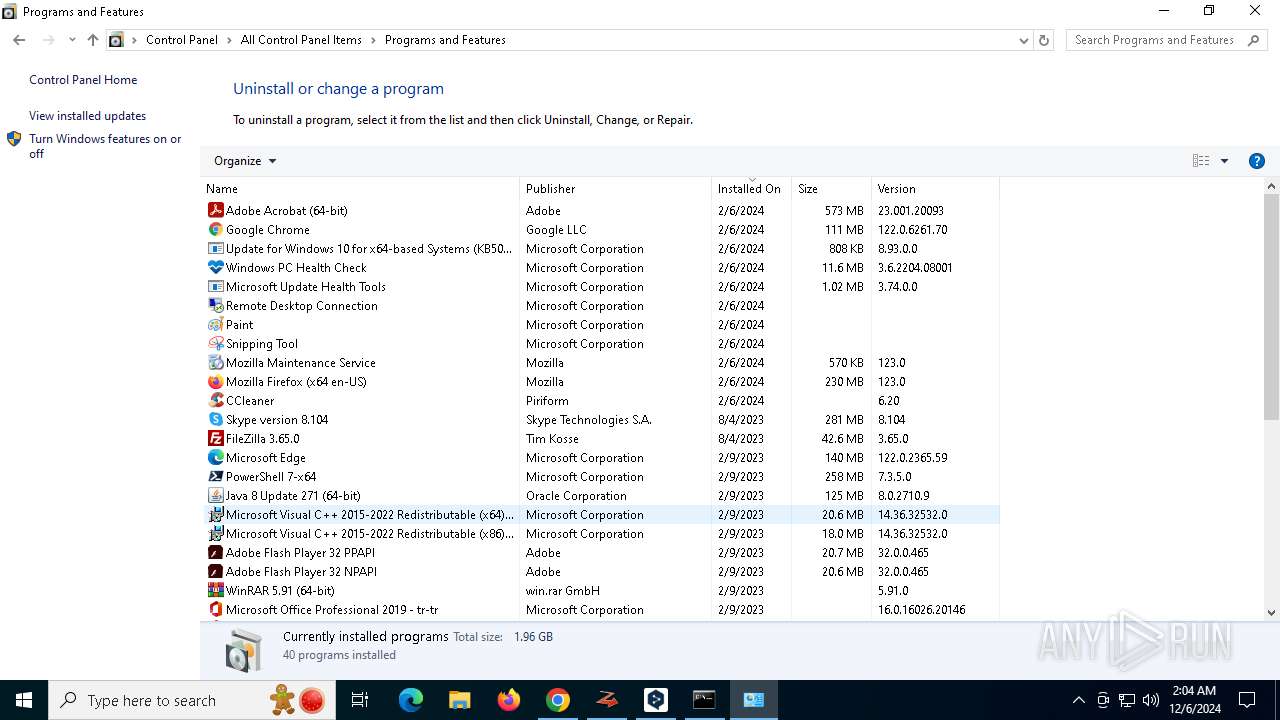
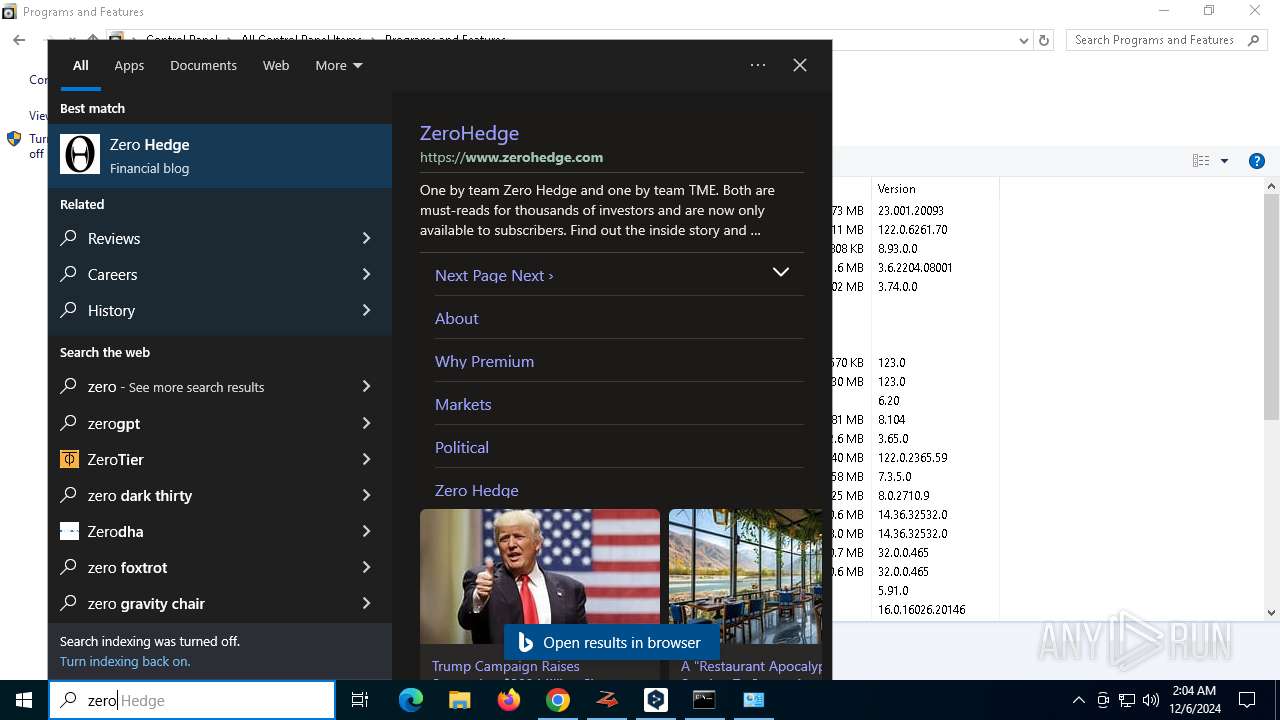
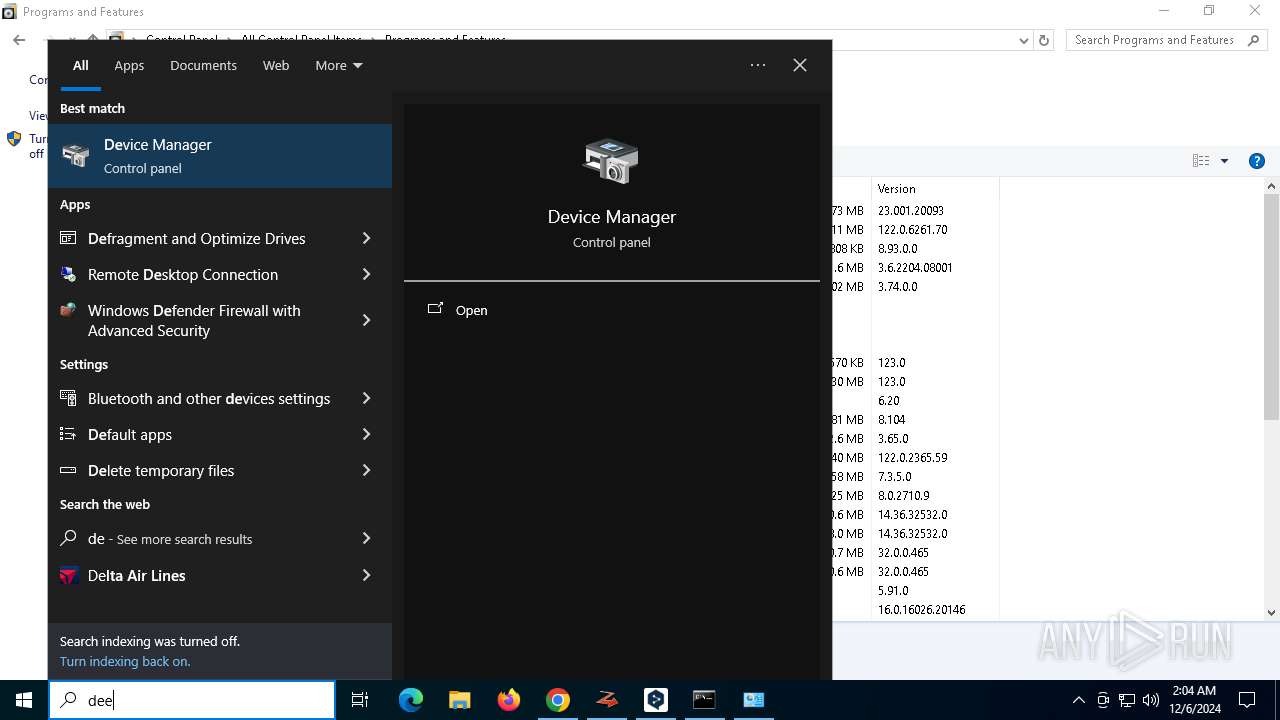
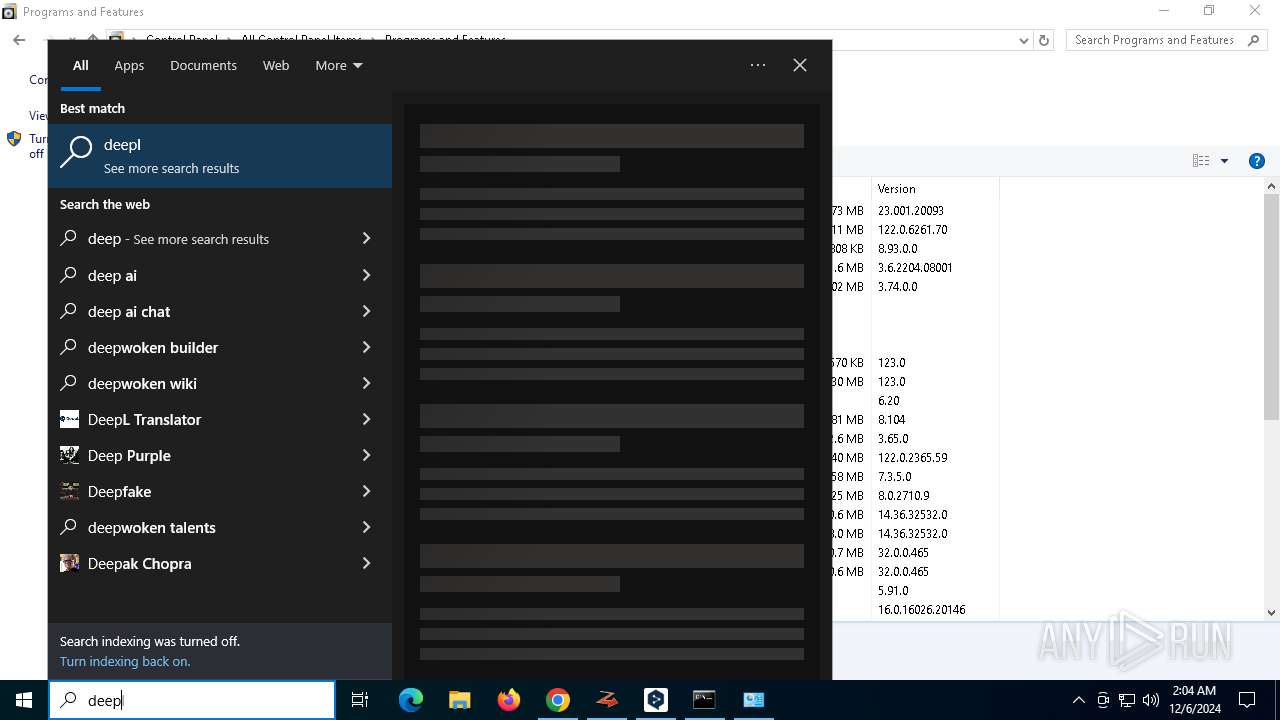
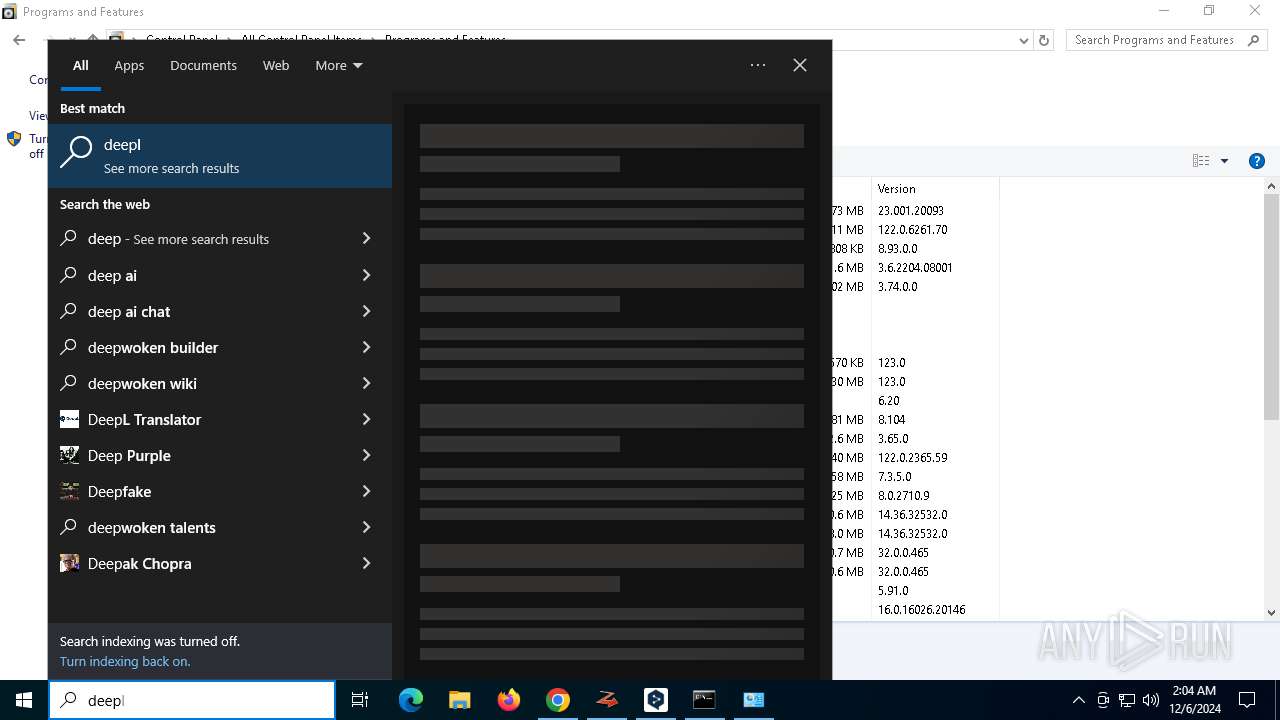
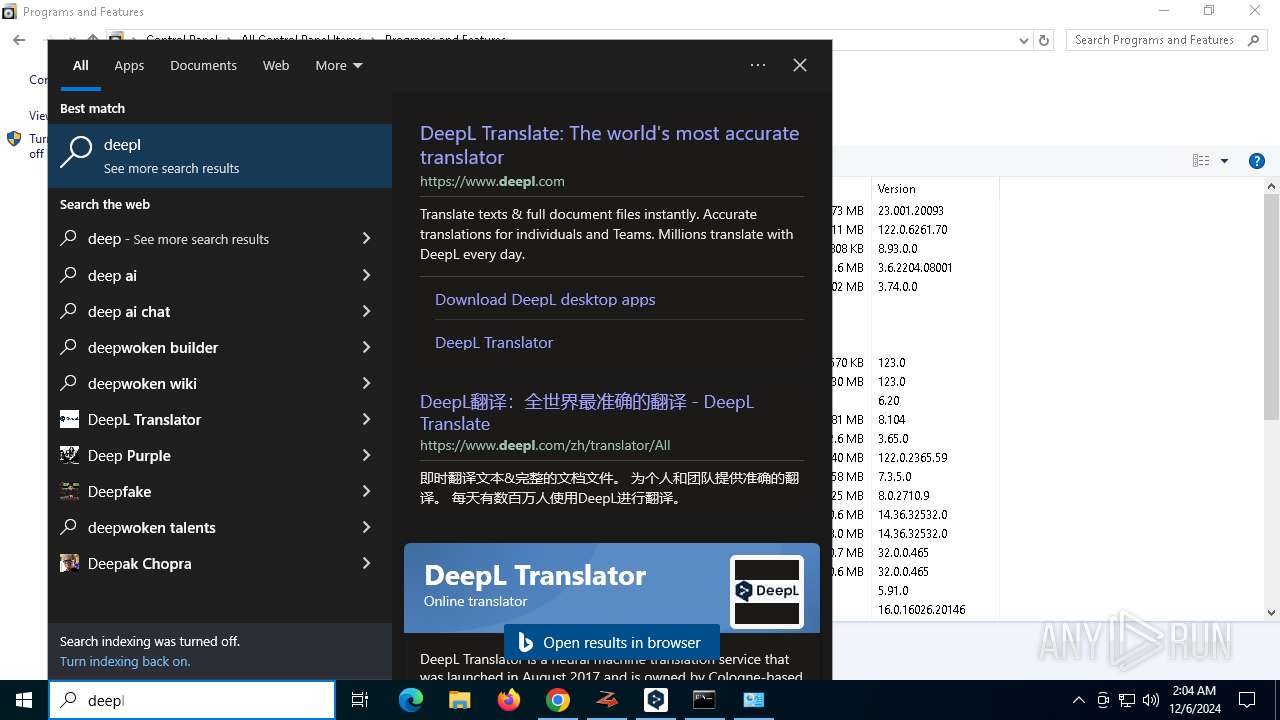
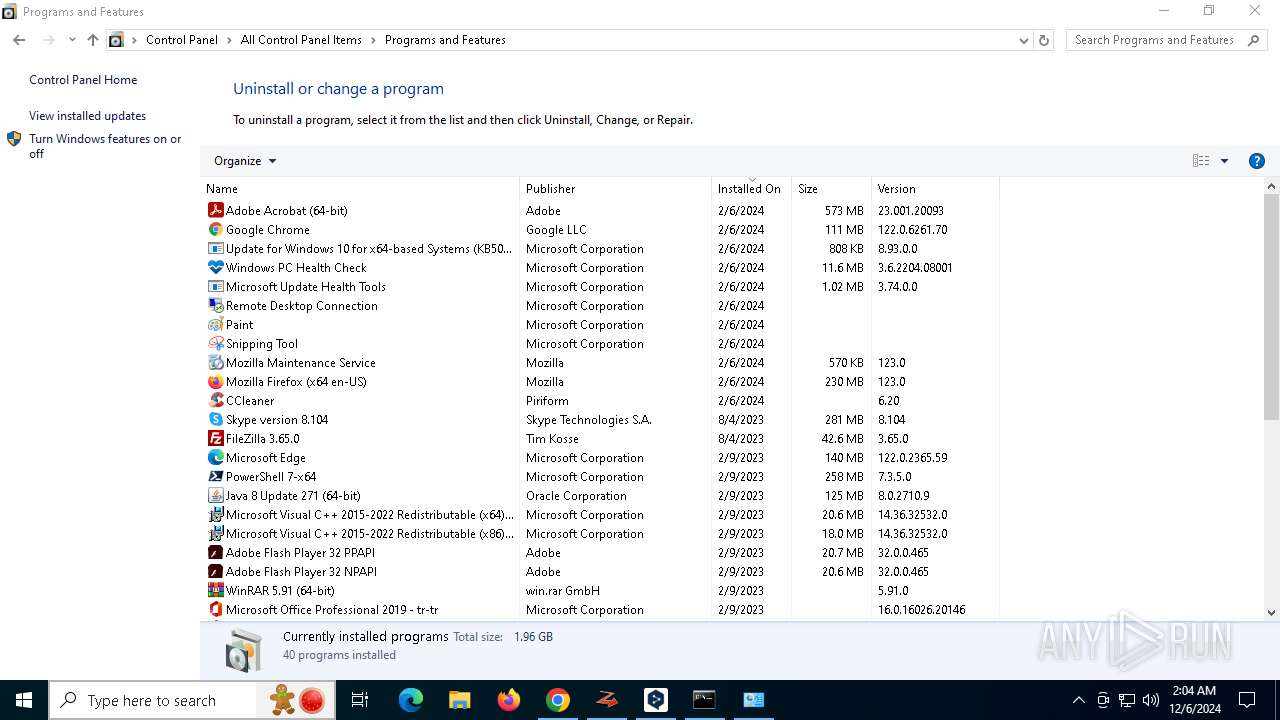
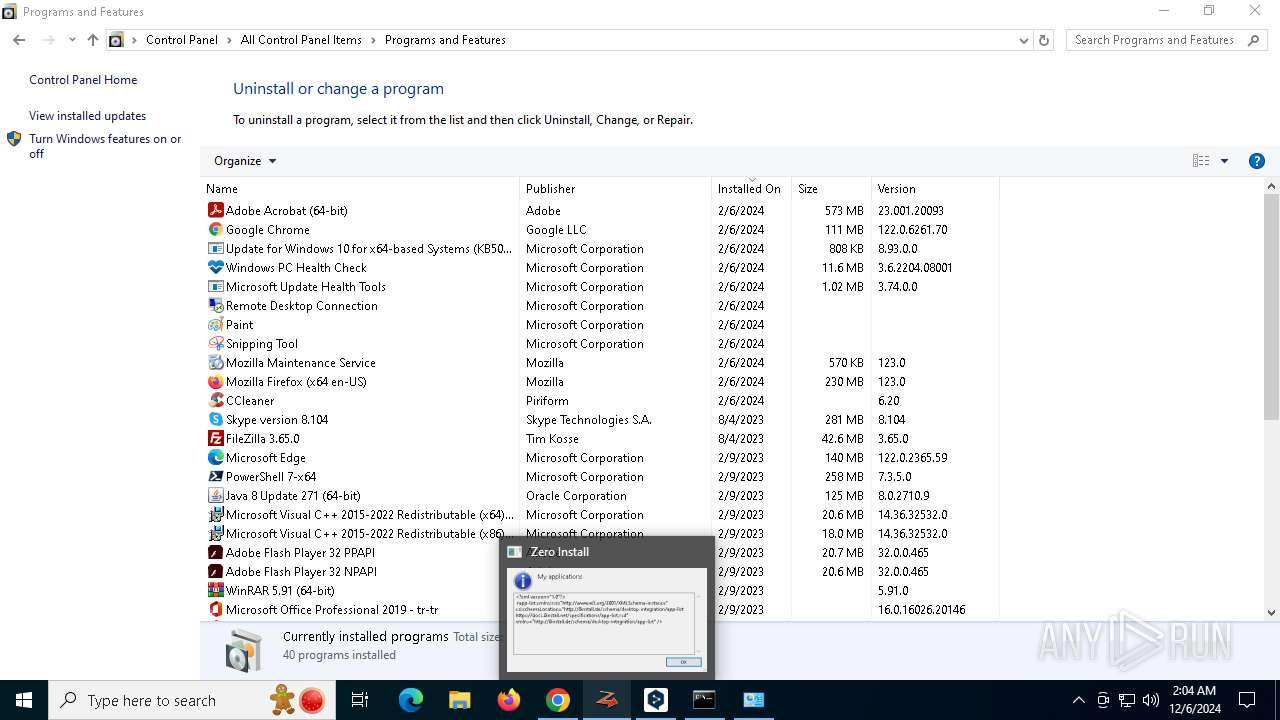
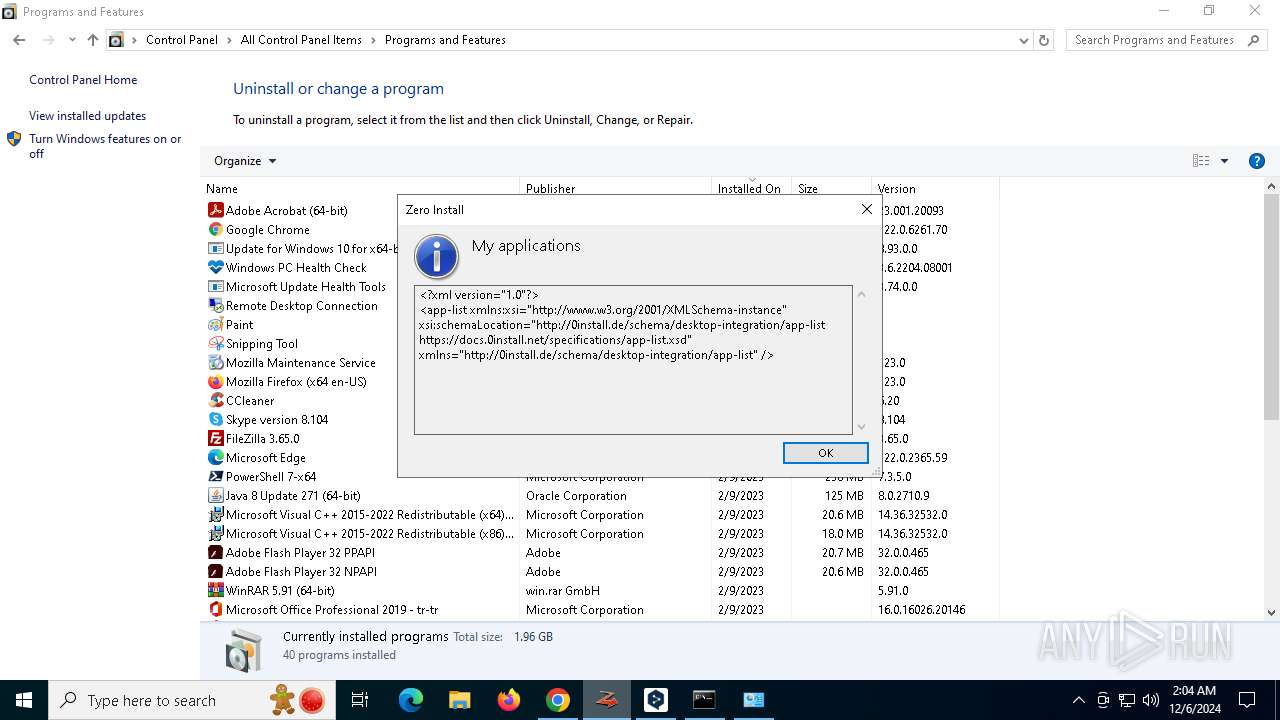
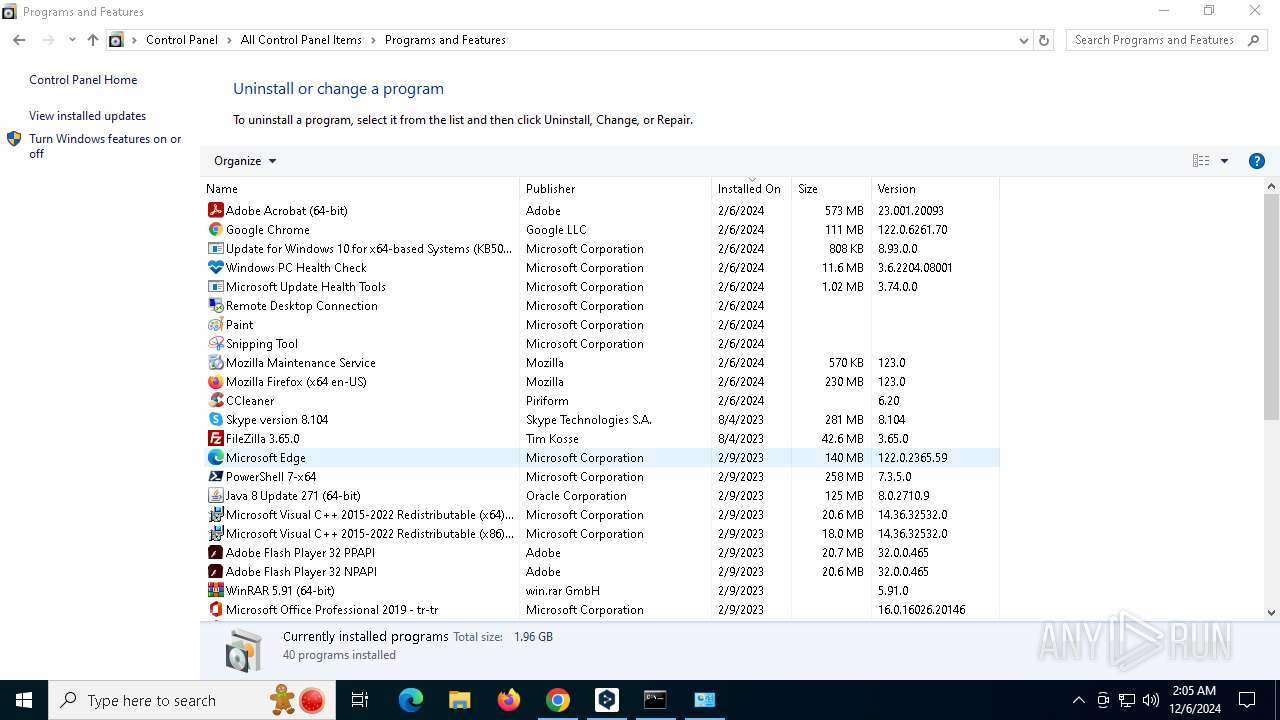
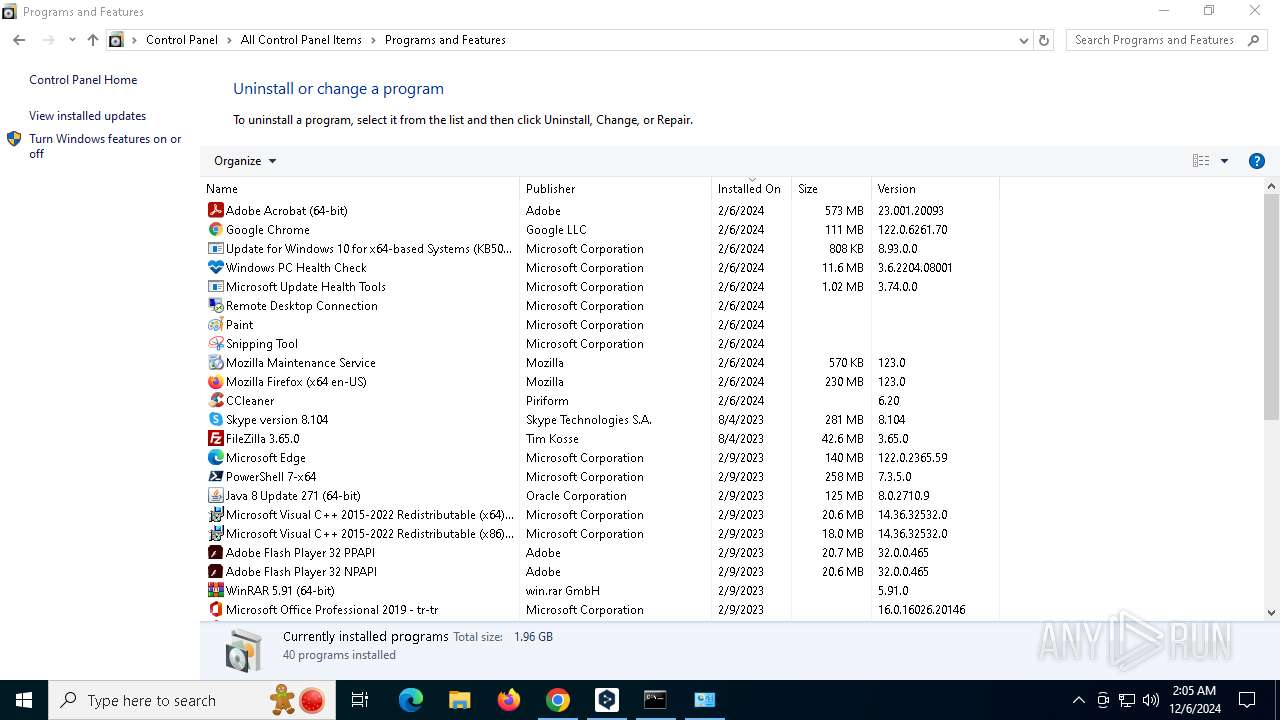
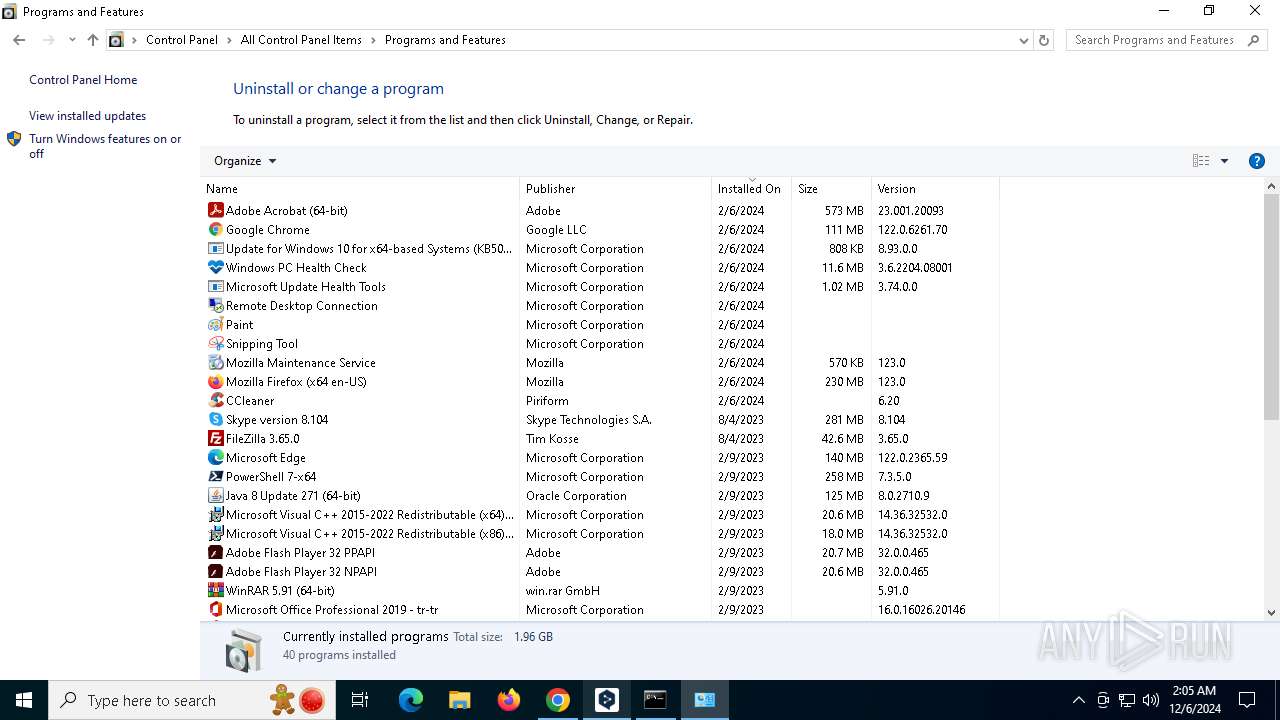
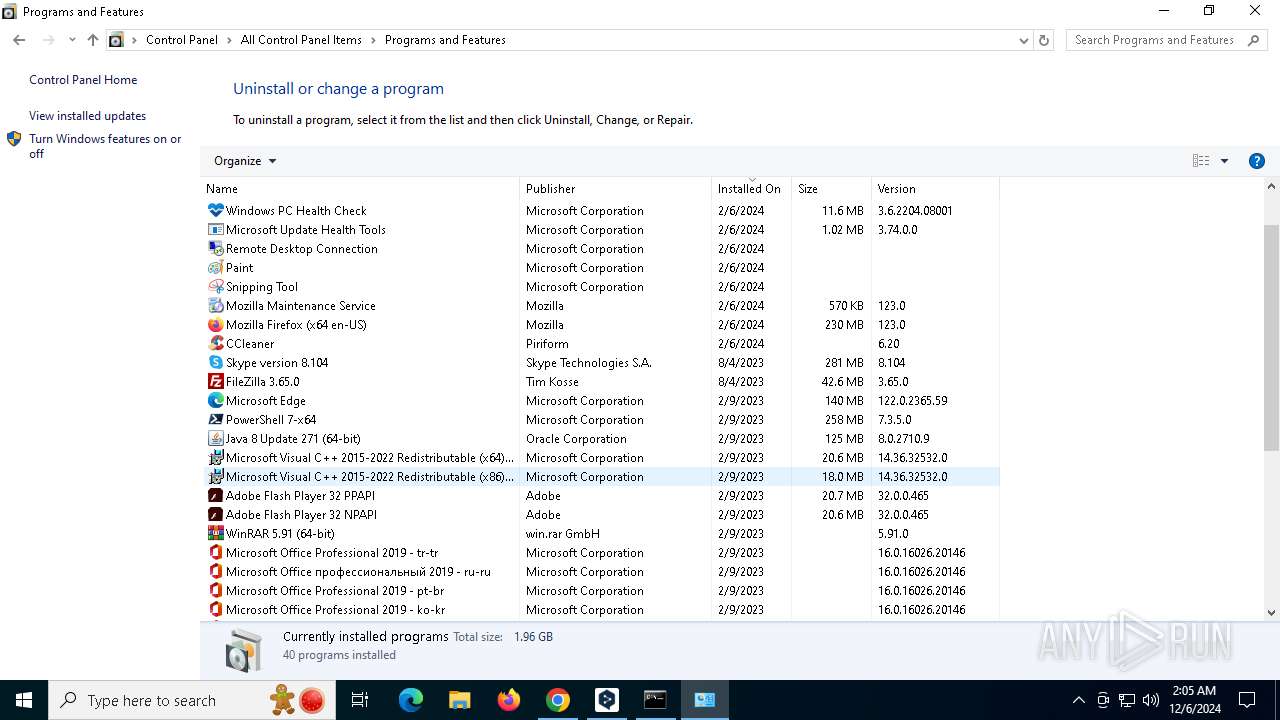
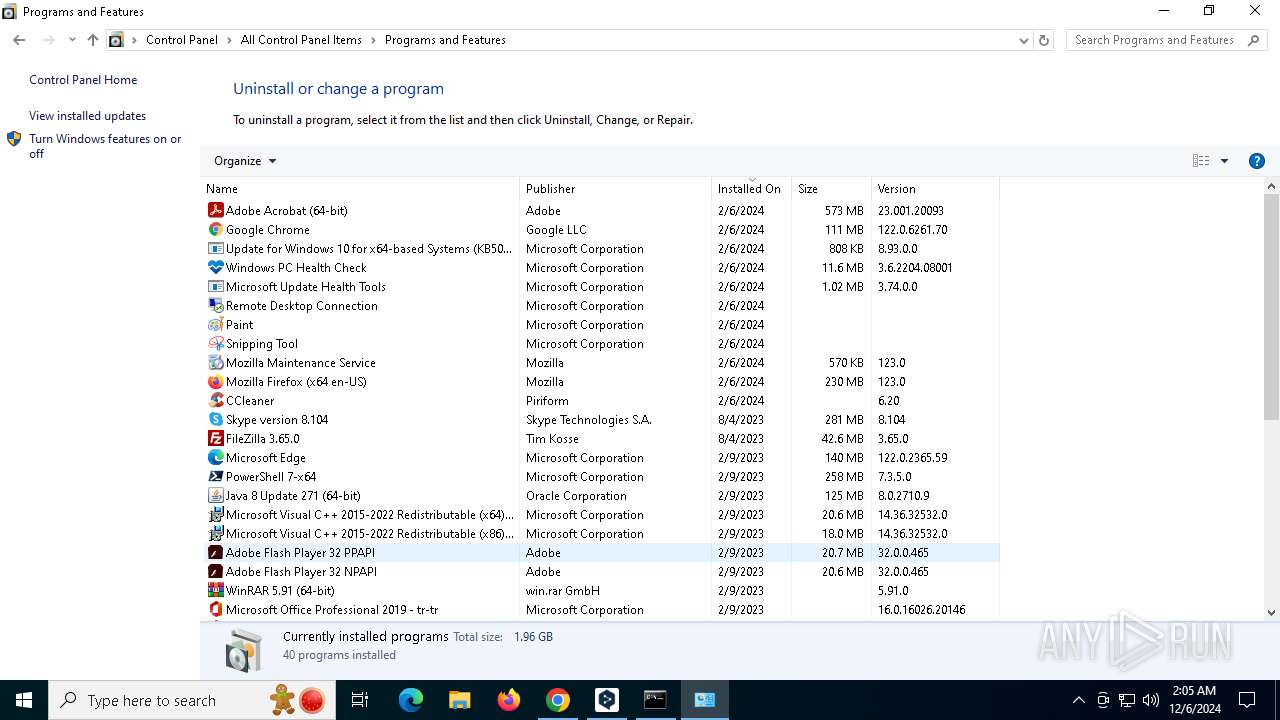
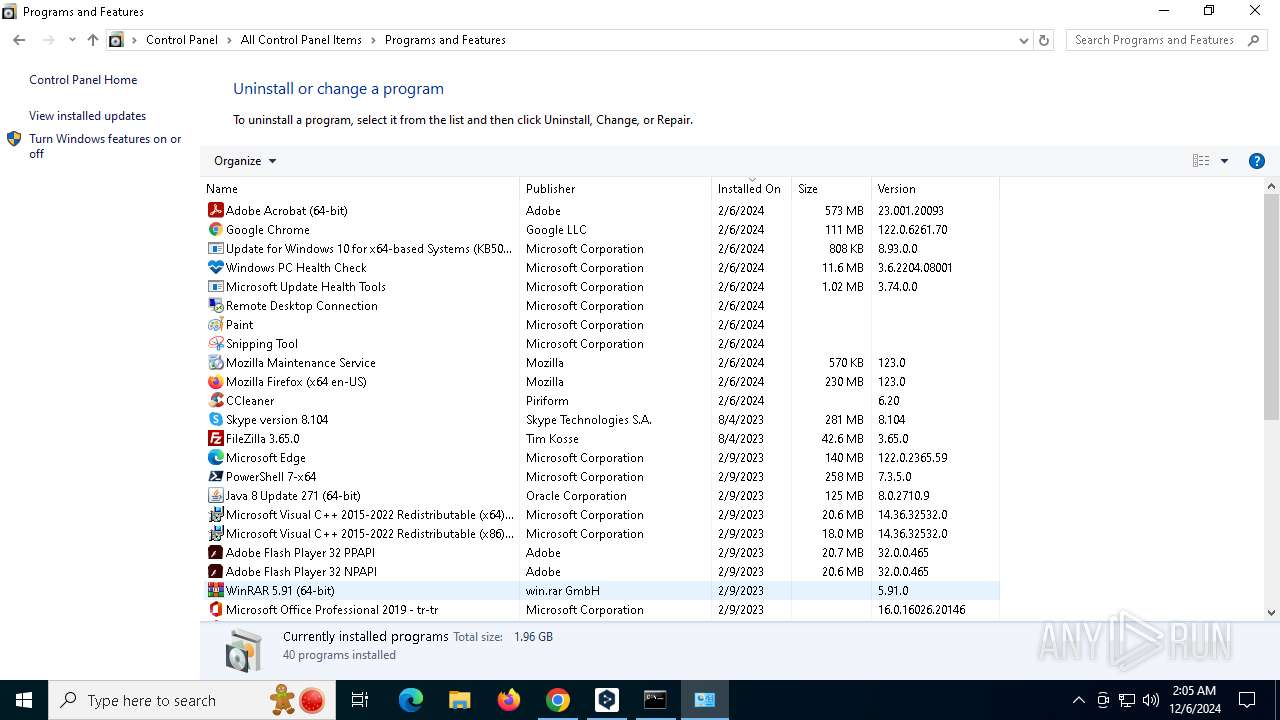
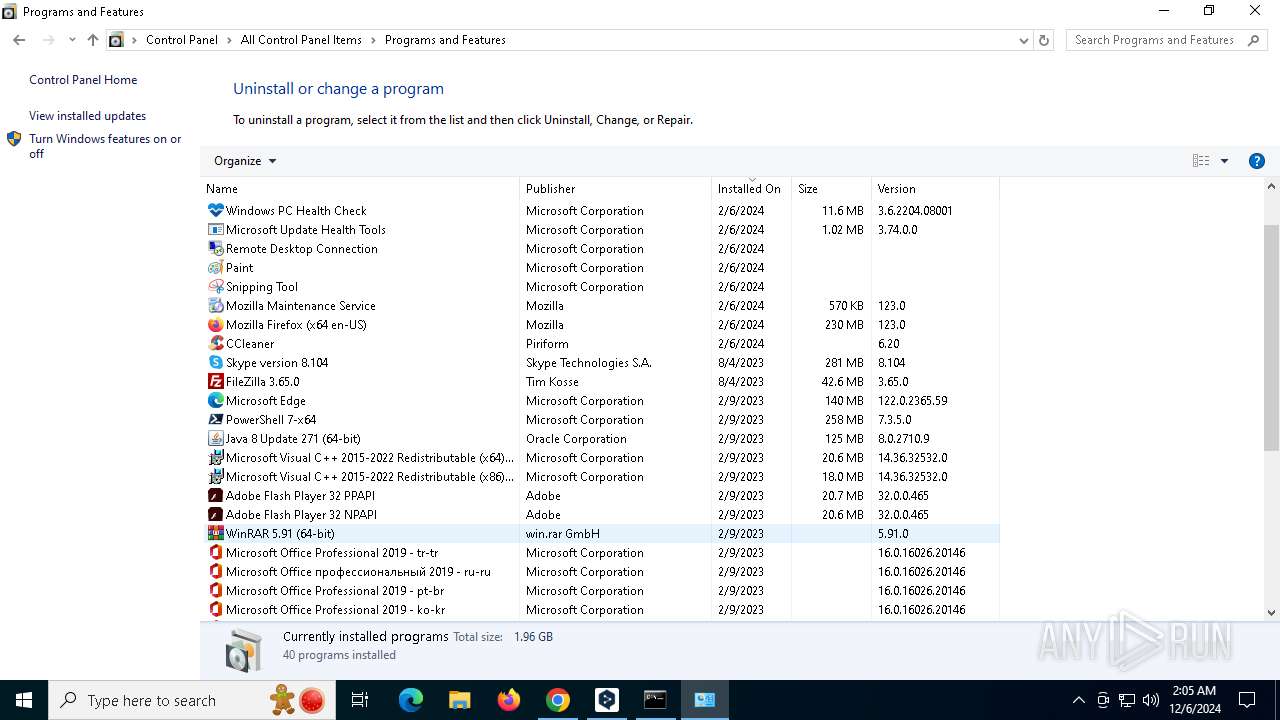
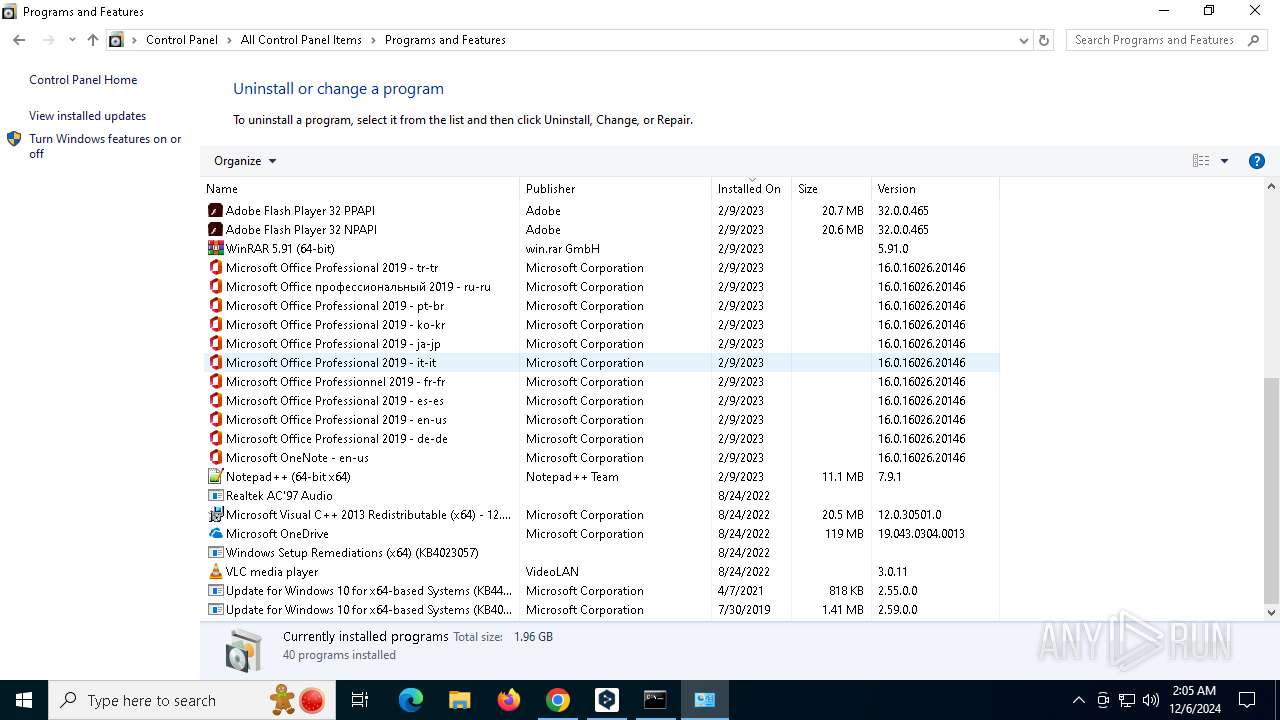
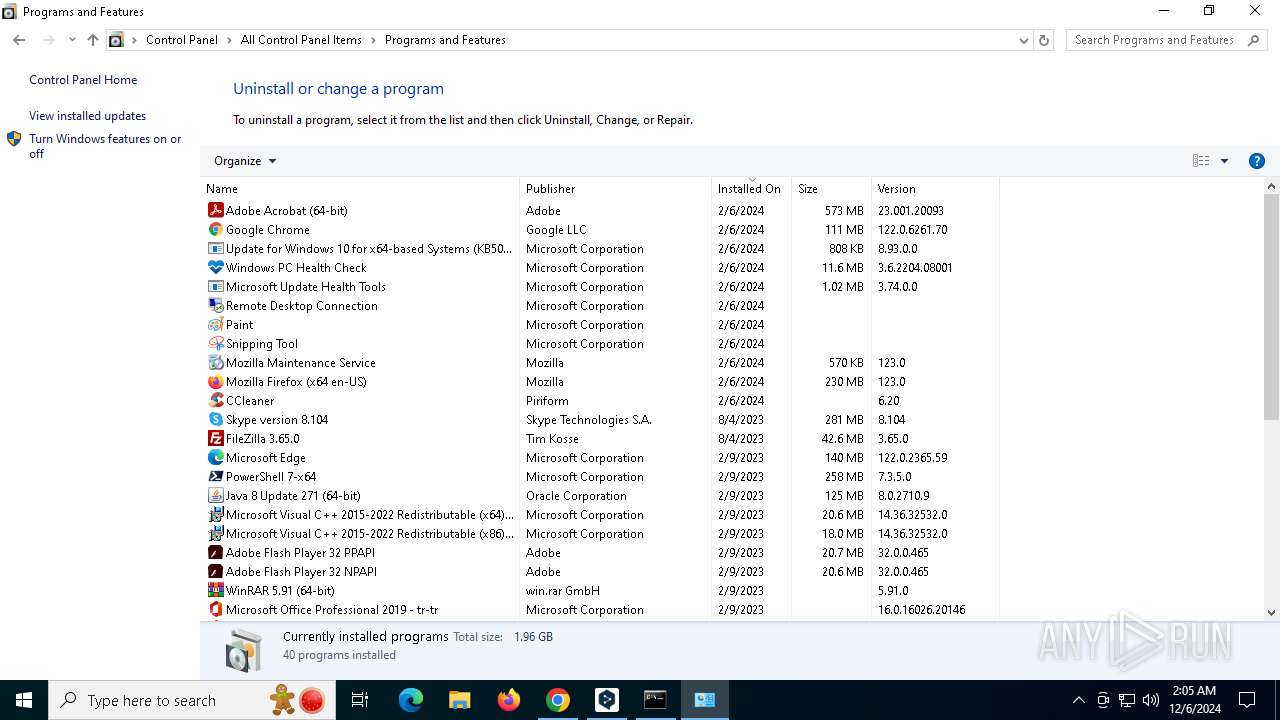
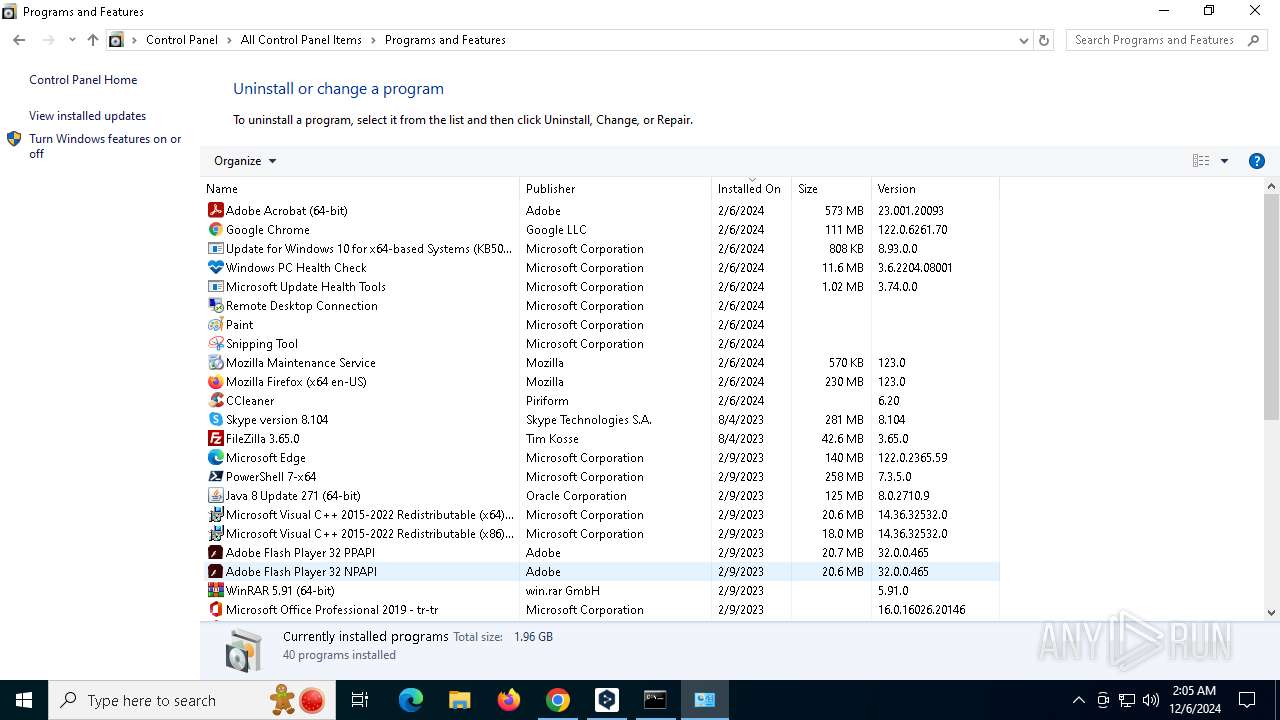
Searches for installed software
- explorer.exe (PID: 7148)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 2380)
- chrome.exe (PID: 7536)
- msedge.exe (PID: 7484)
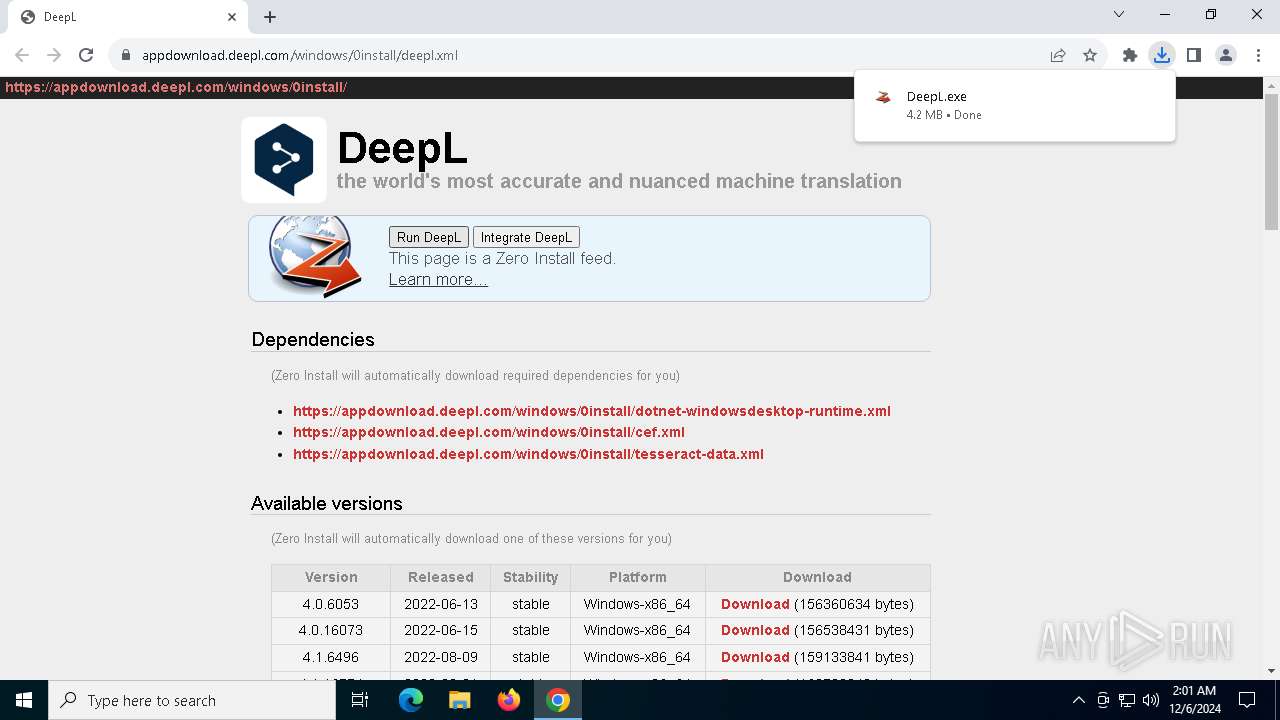
The process uses the downloaded file
- chrome.exe (PID: 2380)
- chrome.exe (PID: 4548)
- 0install.exe (PID: 5252)
Checks supported languages
- DeepL.exe (PID: 7144)
- 0install-win.exe (PID: 1804)
- DeepL.exe (PID: 2280)
- 0install.exe (PID: 3840)
- CefSharp.BrowserSubprocess.exe (PID: 1540)
- CefSharp.BrowserSubprocess.exe (PID: 2312)
- CefSharp.BrowserSubprocess.exe (PID: 3488)
- 0install.exe (PID: 5252)
- 0install-win.exe (PID: 4932)
- CefSharp.BrowserSubprocess.exe (PID: 900)
- CefSharp.BrowserSubprocess.exe (PID: 7892)
- CefSharp.BrowserSubprocess.exe (PID: 524)
- identity_helper.exe (PID: 6648)
- CefSharp.BrowserSubprocess.exe (PID: 7812)
- CefSharp.BrowserSubprocess.exe (PID: 5872)
- CefSharp.BrowserSubprocess.exe (PID: 1828)
- 0install.exe (PID: 2136)
- CefSharp.BrowserSubprocess.exe (PID: 7264)
Reads the computer name
- DeepL.exe (PID: 7144)
- 0install-win.exe (PID: 1804)
- DeepL.exe (PID: 2280)
- CefSharp.BrowserSubprocess.exe (PID: 2312)
- 0install.exe (PID: 3840)
- CefSharp.BrowserSubprocess.exe (PID: 3488)
- 0install.exe (PID: 5252)
- CefSharp.BrowserSubprocess.exe (PID: 1540)
- 0install-win.exe (PID: 4932)
- CefSharp.BrowserSubprocess.exe (PID: 900)
- CefSharp.BrowserSubprocess.exe (PID: 524)
- CefSharp.BrowserSubprocess.exe (PID: 7892)
- identity_helper.exe (PID: 6648)
- CefSharp.BrowserSubprocess.exe (PID: 7812)
- CefSharp.BrowserSubprocess.exe (PID: 1828)
- CefSharp.BrowserSubprocess.exe (PID: 5872)
- 0install.exe (PID: 2136)
- CefSharp.BrowserSubprocess.exe (PID: 7264)
Reads the machine GUID from the registry
- DeepL.exe (PID: 7144)
- 0install-win.exe (PID: 1804)
- DeepL.exe (PID: 2280)
- 0install.exe (PID: 3840)
- 0install.exe (PID: 5252)
- 0install-win.exe (PID: 4932)
- 0install.exe (PID: 2136)
Reads Environment values
- DeepL.exe (PID: 7144)
- 0install-win.exe (PID: 1804)
- 0install.exe (PID: 3840)
- 0install.exe (PID: 5252)
- 0install-win.exe (PID: 4932)
- identity_helper.exe (PID: 6648)
- 0install.exe (PID: 2136)
Disables trace logs
- DeepL.exe (PID: 7144)
- 0install-win.exe (PID: 1804)
- 0install.exe (PID: 3840)
- 0install.exe (PID: 5252)
- 0install-win.exe (PID: 4932)
- 0install.exe (PID: 2136)
Checks proxy server information
- DeepL.exe (PID: 7144)
- 0install-win.exe (PID: 1804)
- DeepL.exe (PID: 2280)
- 0install.exe (PID: 3840)
- 0install.exe (PID: 5252)
- 0install-win.exe (PID: 4932)
- 0install.exe (PID: 2136)
Create files in a temporary directory
- DeepL.exe (PID: 7144)
- 0install-win.exe (PID: 1804)
- 0install.exe (PID: 3840)
- DeepL.exe (PID: 2280)
Creates files or folders in the user directory
- DeepL.exe (PID: 7144)
- 0install-win.exe (PID: 1804)
- DeepL.exe (PID: 2280)
- 0install.exe (PID: 3840)
- CefSharp.BrowserSubprocess.exe (PID: 1540)
- 0install.exe (PID: 5252)
- 0install-win.exe (PID: 4932)
- 0install.exe (PID: 2136)
Reads the software policy settings
- DeepL.exe (PID: 7144)
- 0install-win.exe (PID: 1804)
- DeepL.exe (PID: 2280)
Application launched itself
- chrome.exe (PID: 2380)
- msedge.exe (PID: 5308)
- msedge.exe (PID: 7940)
Creates files in the program directory
- 0install-win.exe (PID: 1804)
- DeepL.exe (PID: 2280)
- 0install-win.exe (PID: 4932)
Sends debugging messages
- DeepL.exe (PID: 2280)
- CefSharp.BrowserSubprocess.exe (PID: 3488)
- CefSharp.BrowserSubprocess.exe (PID: 1540)
- CefSharp.BrowserSubprocess.exe (PID: 2312)
- CefSharp.BrowserSubprocess.exe (PID: 900)
- CefSharp.BrowserSubprocess.exe (PID: 524)
- CefSharp.BrowserSubprocess.exe (PID: 7892)
Process checks computer location settings
- DeepL.exe (PID: 2280)
- CefSharp.BrowserSubprocess.exe (PID: 2312)
- 0install.exe (PID: 5252)
- CefSharp.BrowserSubprocess.exe (PID: 900)
- CefSharp.BrowserSubprocess.exe (PID: 524)
Process checks whether UAC notifications are on
- 0install.exe (PID: 5252)
Reads security settings of Internet Explorer
- explorer.exe (PID: 7148)
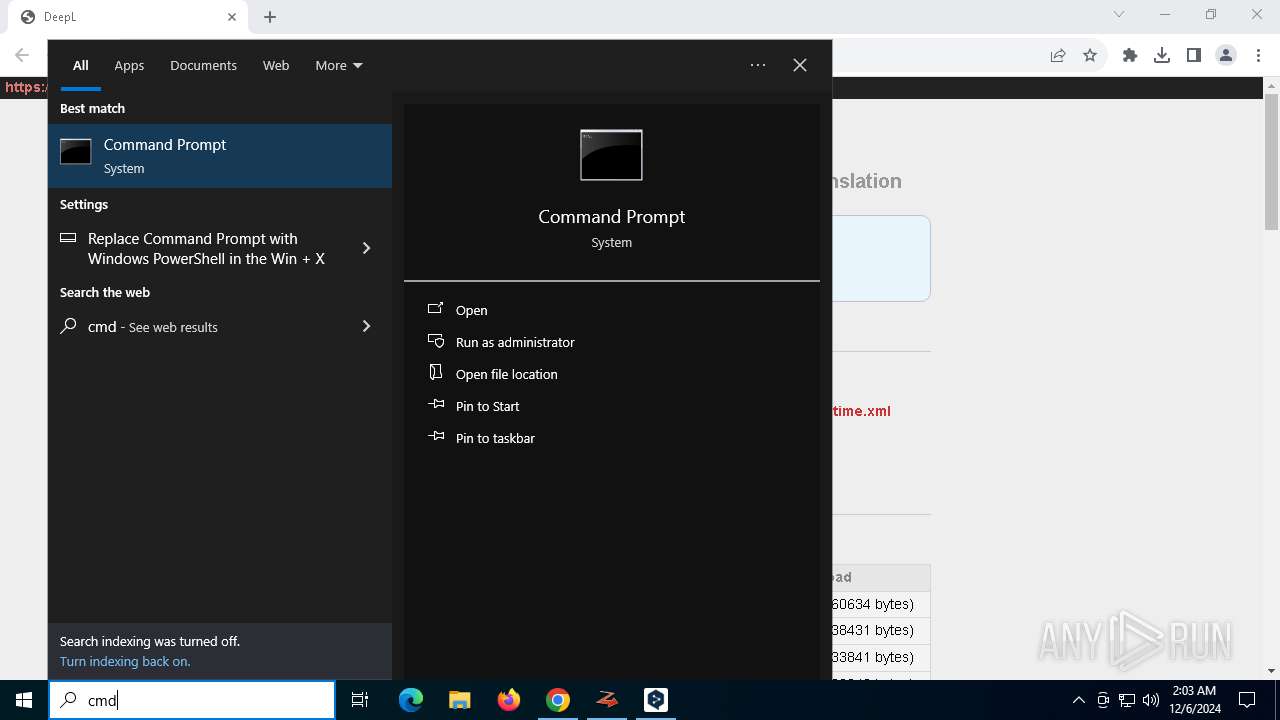
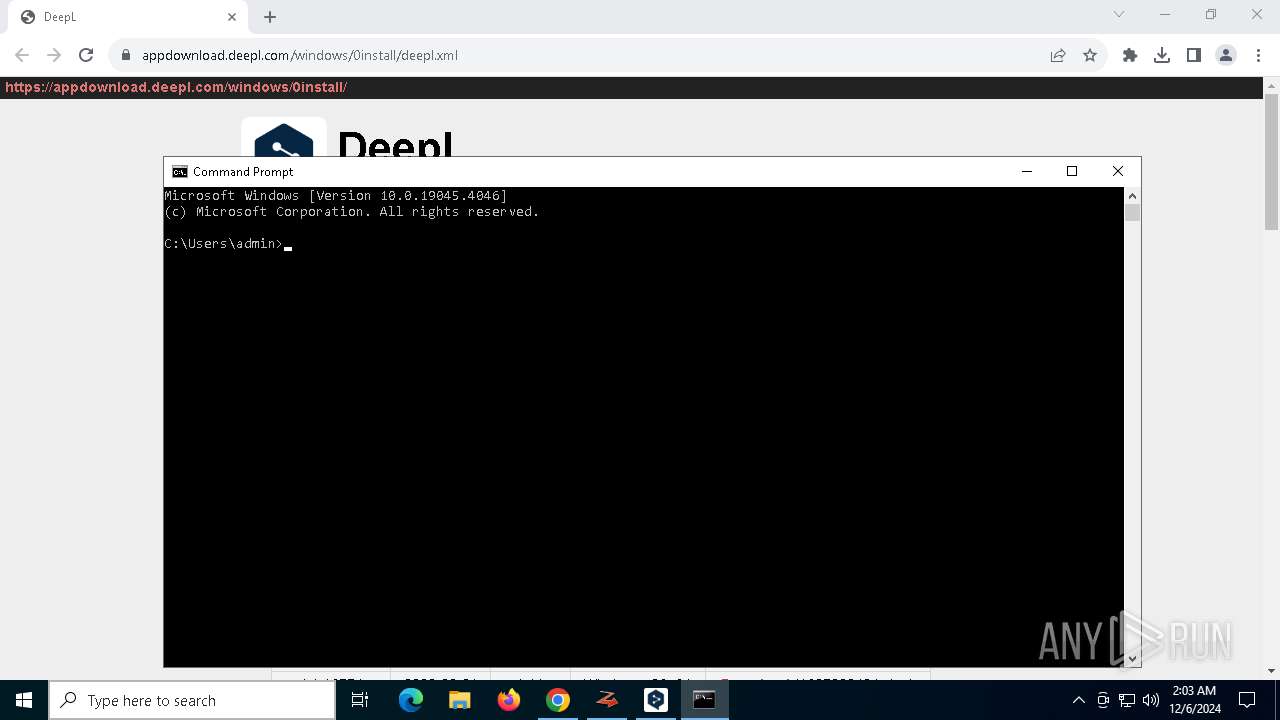
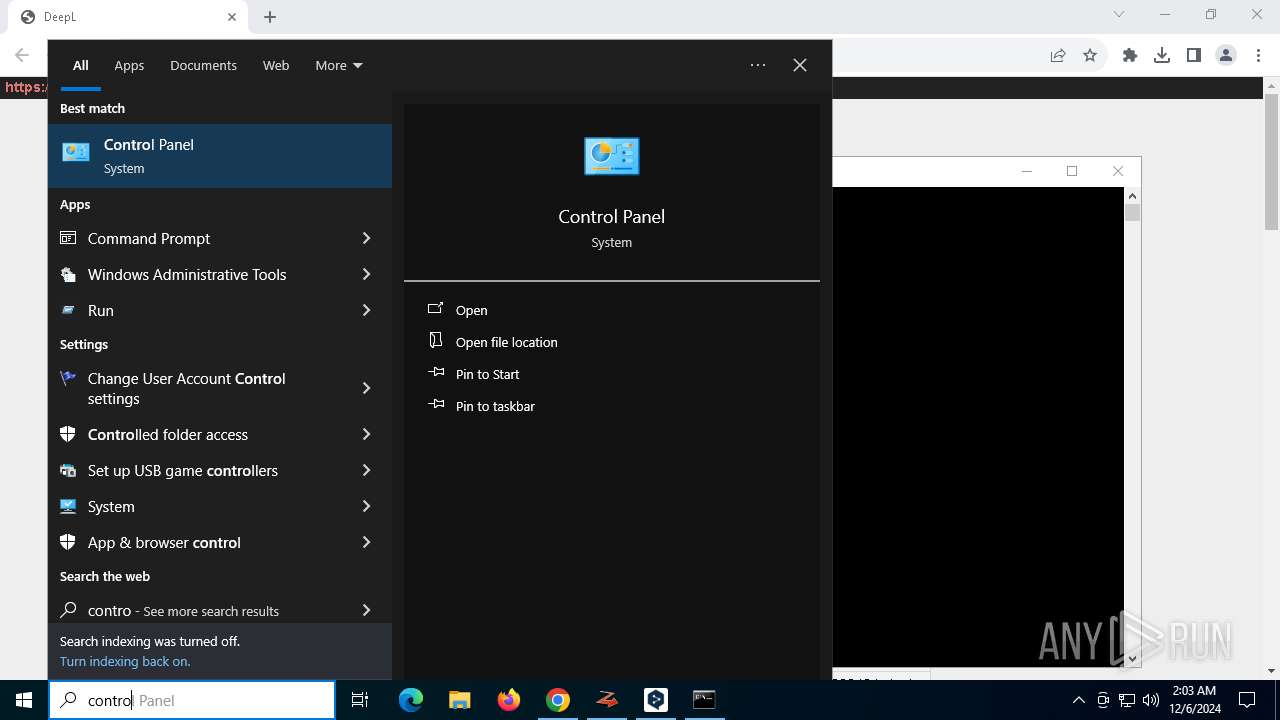
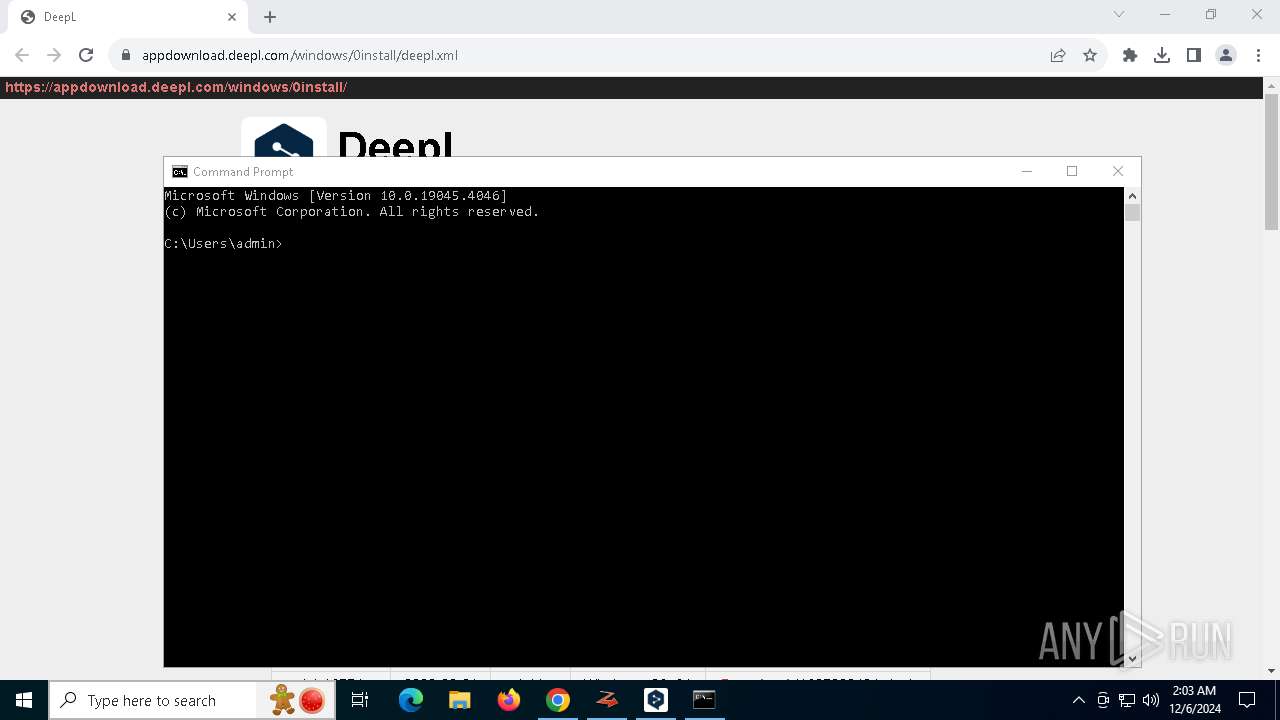
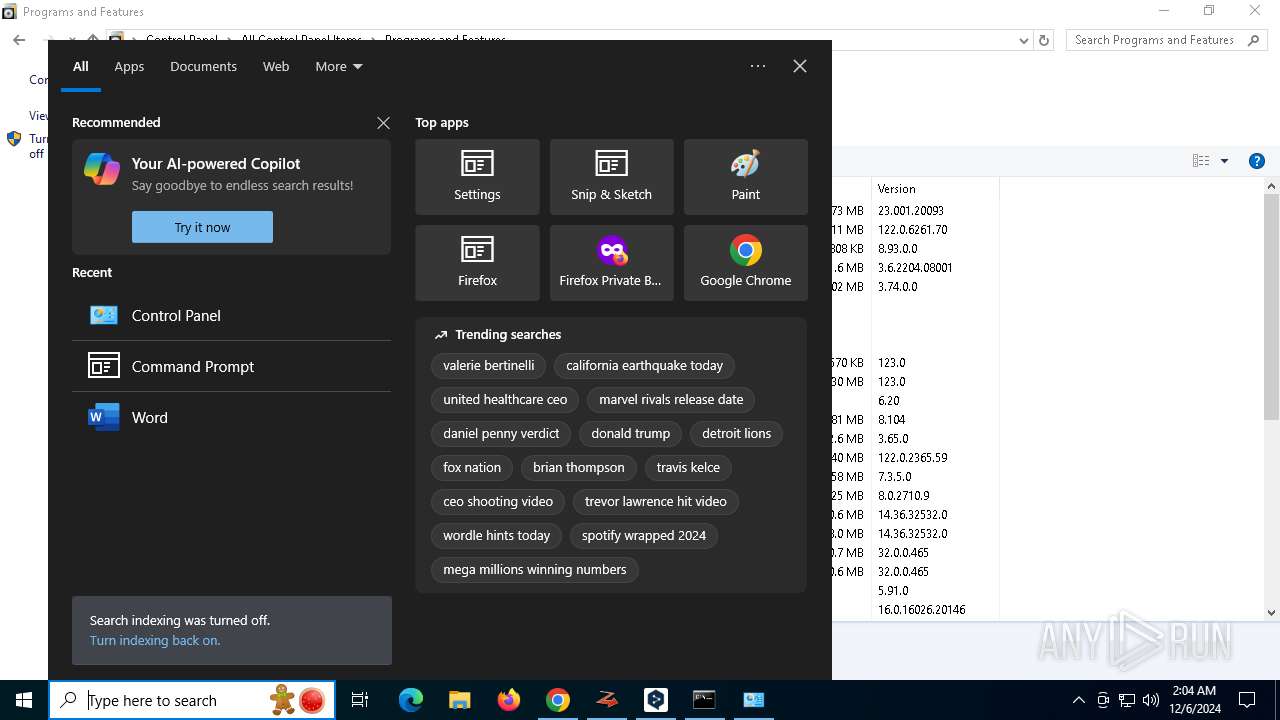
Manual execution by a user
- cmd.exe (PID: 7700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
228
Monitored processes
91
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 0install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 524 | "C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_NX54BP3MSRHNDMB5N5YOFJZWO5QE5I5W7JTPGB4XC7MEJNSXCC3A\.\CefSharp.BrowserSubprocess.exe" --type=renderer --user-agent="DeepL/24.11.4.14424 (Microsoft Windows NT 10.0.19045.0; x64)" --enable-chrome-runtime --user-data-dir="C:\Users\admin\AppData\Local\DeepL_SE\cache\e9d59275-44bd-4ca0-8075-b61f7e43b715" --uncaught-exception-stack-size=10 --cefsharpexitsub --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=7976,i,15850735997520869006,1505797016935287000,262144 --disable-features=EnableHangWatcher --variations-seed-version --enable-logging=handle --log-file=8008 --mojo-platform-channel-handle=7932 --host-process-id=2280 /prefetch:1 | C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_NX54BP3MSRHNDMB5N5YOFJZWO5QE5I5W7JTPGB4XC7MEJNSXCC3A\CefSharp.BrowserSubprocess.exe | — | DeepL.exe | |||||||||||
User: admin Company: The CefSharp Authors Integrity Level: MEDIUM Description: CefSharp.BrowserSubprocess Version: 127.3.50.0 | |||||||||||||||
| 732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5188 --field-trial-handle=2356,i,8067538781124108788,15240919217987765472,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 900 | "C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_NX54BP3MSRHNDMB5N5YOFJZWO5QE5I5W7JTPGB4XC7MEJNSXCC3A\.\CefSharp.BrowserSubprocess.exe" --type=renderer --user-agent="DeepL/24.11.4.14424 (Microsoft Windows NT 10.0.19045.0; x64)" --start-stack-profiler --enable-chrome-runtime --user-data-dir="C:\Users\admin\AppData\Local\DeepL_SE\cache\e9d59275-44bd-4ca0-8075-b61f7e43b715" --uncaught-exception-stack-size=10 --cefsharpexitsub --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=7984,i,15850735997520869006,1505797016935287000,262144 --disable-features=EnableHangWatcher --variations-seed-version --enable-logging=handle --log-file=8028 --mojo-platform-channel-handle=8012 --host-process-id=2280 /prefetch:1 | C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_NX54BP3MSRHNDMB5N5YOFJZWO5QE5I5W7JTPGB4XC7MEJNSXCC3A\CefSharp.BrowserSubprocess.exe | — | DeepL.exe | |||||||||||
User: admin Company: The CefSharp Authors Integrity Level: MEDIUM Description: CefSharp.BrowserSubprocess Version: 127.3.50.0 | |||||||||||||||
| 1356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2272 --field-trial-handle=2276,i,148209644292262102,14417046033626495600,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1540 | "C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_NX54BP3MSRHNDMB5N5YOFJZWO5QE5I5W7JTPGB4XC7MEJNSXCC3A\.\CefSharp.BrowserSubprocess.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-sandbox --user-agent="DeepL/24.11.4.14424 (Microsoft Windows NT 10.0.19045.0; x64)" --start-stack-profiler --enable-chrome-runtime --user-data-dir="C:\Users\admin\AppData\Local\DeepL_SE\cache\e9d59275-44bd-4ca0-8075-b61f7e43b715" --cefsharpexitsub --field-trial-handle=5168,i,15850735997520869006,1505797016935287000,262144 --disable-features=EnableHangWatcher --variations-seed-version --enable-logging=handle --log-file=5376 --mojo-platform-channel-handle=5368 /prefetch:3 --host-process-id=2280 | C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_NX54BP3MSRHNDMB5N5YOFJZWO5QE5I5W7JTPGB4XC7MEJNSXCC3A\CefSharp.BrowserSubprocess.exe | DeepL.exe | ||||||||||||
User: admin Company: The CefSharp Authors Integrity Level: MEDIUM Description: CefSharp.BrowserSubprocess Version: 127.3.50.0 Modules
| |||||||||||||||
| 1576 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 0install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5160 --field-trial-handle=1892,i,15224890372850925772,1088931585983696914,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1804 | "C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_3IWFAPVMB3QX4MUSWWOAWPUNRBK7NPIQUIMAJZLBBI7R2NLMVE3A\0install-win.exe" run --no-wait https://appdownload.deepl.com/windows/0install/deepl.xml | C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_3IWFAPVMB3QX4MUSWWOAWPUNRBK7NPIQUIMAJZLBBI7R2NLMVE3A\0install-win.exe | DeepL.exe | ||||||||||||
User: admin Company: 0install-win Integrity Level: MEDIUM Description: 0install-win Exit code: 2280 Version: 2.26.0.0 Modules
| |||||||||||||||
| 1828 | "C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_NX54BP3MSRHNDMB5N5YOFJZWO5QE5I5W7JTPGB4XC7MEJNSXCC3A\.\CefSharp.BrowserSubprocess.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-sandbox --user-agent="DeepL/24.11.4.14424 (Microsoft Windows NT 10.0.19045.0; x64)" --enable-chrome-runtime --user-data-dir="C:\Users\admin\AppData\Local\DeepL_SE\cache\e9d59275-44bd-4ca0-8075-b61f7e43b715" --cefsharpexitsub --field-trial-handle=3252,i,15850735997520869006,1505797016935287000,262144 --disable-features=EnableHangWatcher --variations-seed-version --enable-logging=handle --log-file=8616 --mojo-platform-channel-handle=8608 /prefetch:8 --host-process-id=2280 | C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_NX54BP3MSRHNDMB5N5YOFJZWO5QE5I5W7JTPGB4XC7MEJNSXCC3A\CefSharp.BrowserSubprocess.exe | — | DeepL.exe | |||||||||||
User: admin Company: The CefSharp Authors Integrity Level: MEDIUM Description: CefSharp.BrowserSubprocess Exit code: 0 Version: 127.3.50.0 | |||||||||||||||
Total events
44 884
Read events
44 718
Write events
156
Delete events
10
Modification events
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4548) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000C49F7BB98247DB01 | |||
| (PID) Process: | (7144) DeepL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepL_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7144) DeepL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepL_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7144) DeepL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepL_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7144) DeepL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepL_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
Executable files
1 288
Suspicious files
785
Text files
247
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF135e9e.TMP | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF135ead.TMP | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF135edc.TMP | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF135edc.TMP | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF135edc.TMP | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
118
TCP/UDP connections
158
DNS requests
145
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6068 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1416 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ads7ltfl2gw6hxwgakn3sxrkoijq_9.53.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.53.0_all_iky7dhj3jd5su3axccoshyd4xm.crx3 | unknown | — | — | whitelisted |
5496 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1416 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ads7ltfl2gw6hxwgakn3sxrkoijq_9.53.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.53.0_all_iky7dhj3jd5su3axccoshyd4xm.crx3 | unknown | — | — | whitelisted |
1416 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ads7ltfl2gw6hxwgakn3sxrkoijq_9.53.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.53.0_all_iky7dhj3jd5su3axccoshyd4xm.crx3 | unknown | — | — | whitelisted |
1416 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ads7ltfl2gw6hxwgakn3sxrkoijq_9.53.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.53.0_all_iky7dhj3jd5su3axccoshyd4xm.crx3 | unknown | — | — | whitelisted |
1416 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ads7ltfl2gw6hxwgakn3sxrkoijq_9.53.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.53.0_all_iky7dhj3jd5su3axccoshyd4xm.crx3 | unknown | — | — | whitelisted |
1416 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/pqimsfviqmgyr4j525pwxymwmu_20241127.701574589.14/obedbbhbpmojnkanicioggnmelmoomoc_20241127.701574589.14_all_ENUS500000_b4tdmiwod3oti3gfuzbwj4xrne.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6068 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6068 | svchost.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 23.212.110.154:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
2380 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6484 | chrome.exe | 104.18.36.122:443 | appdownload.deepl.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
appdownload.deepl.com |
| whitelisted |
accounts.google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
0install.net |
| unknown |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5064 | SearchApp.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
Process | Message |
|---|---|
DeepL.exe | Profiler was prevented from loading notification profiler due to app settings.
Process ID (decimal): 2280. Message ID: [0x2509].
|