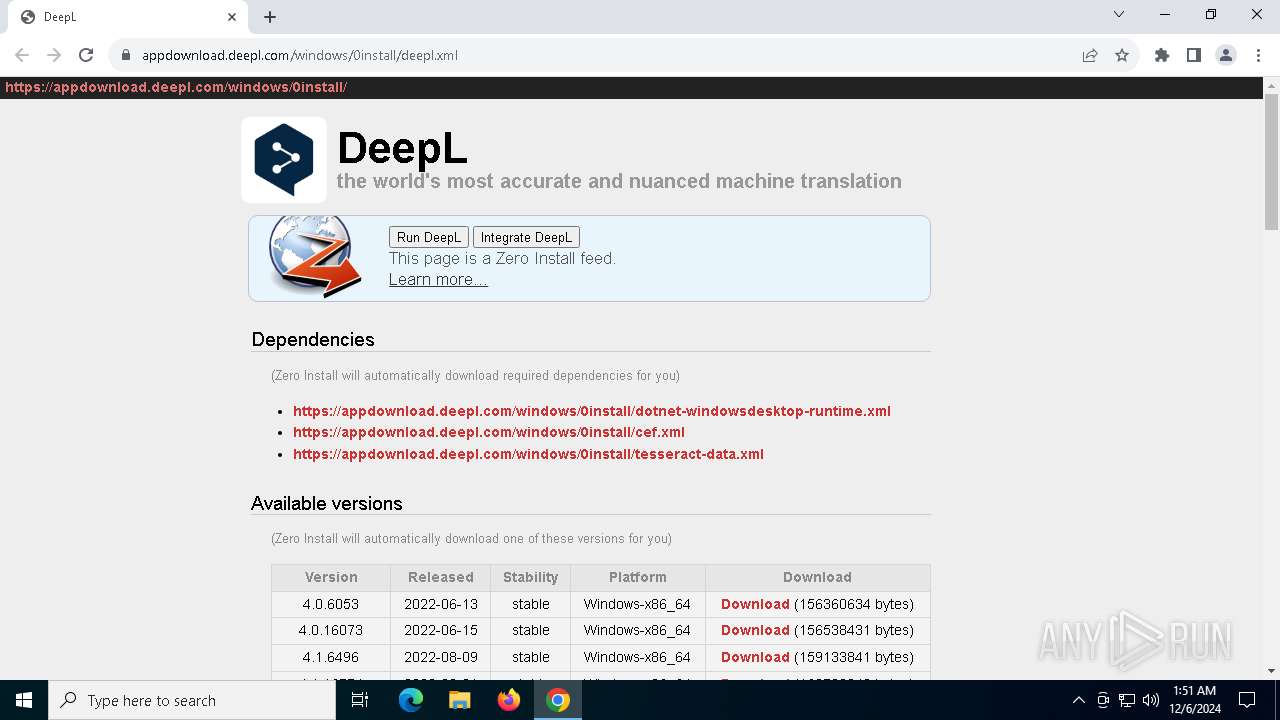
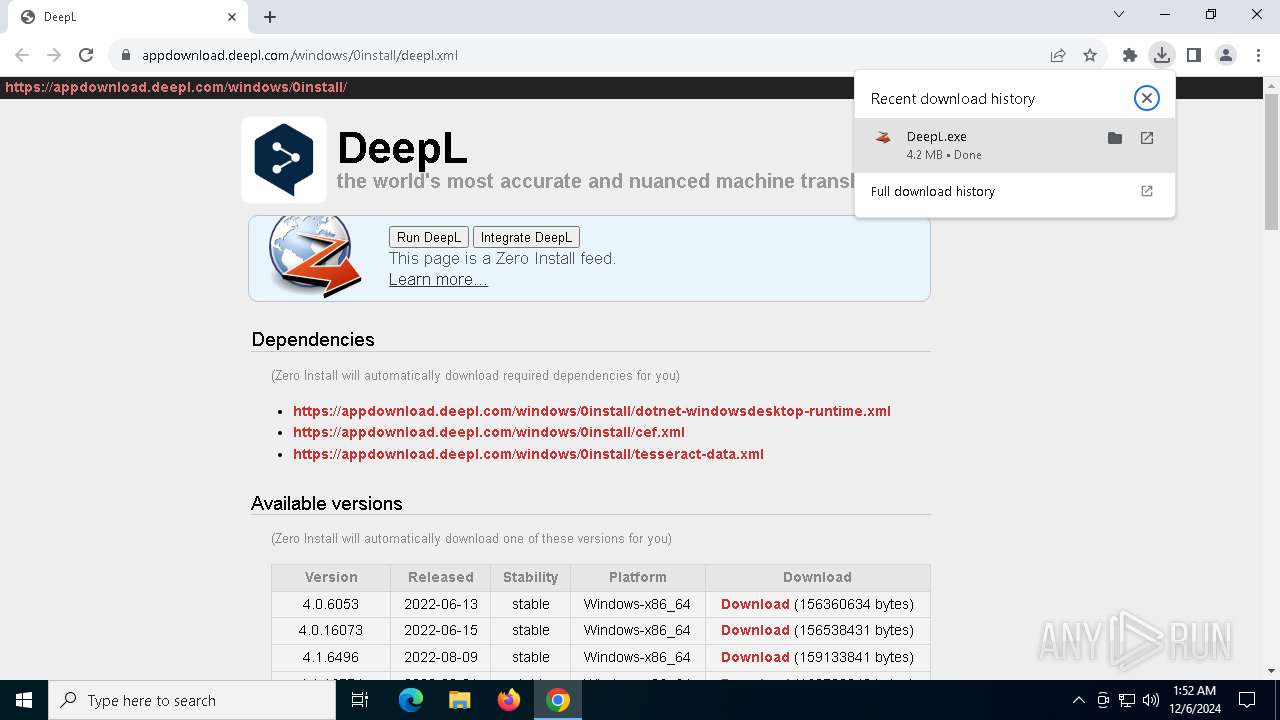
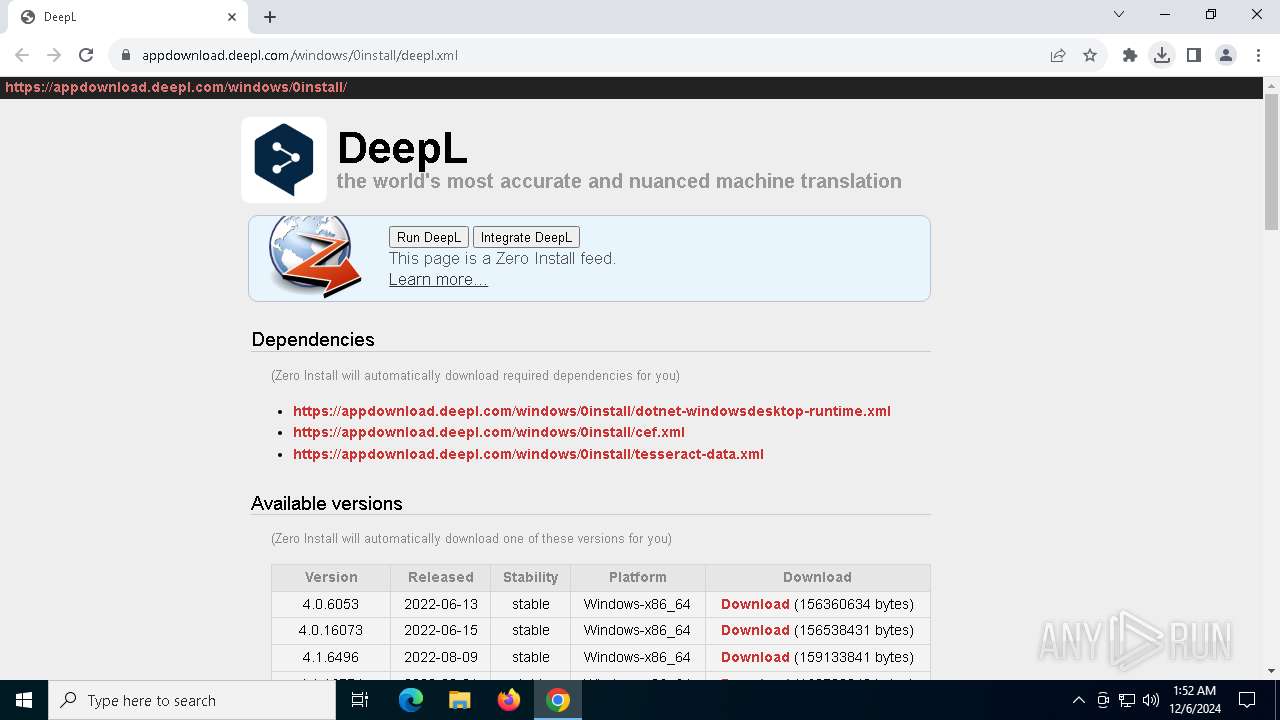
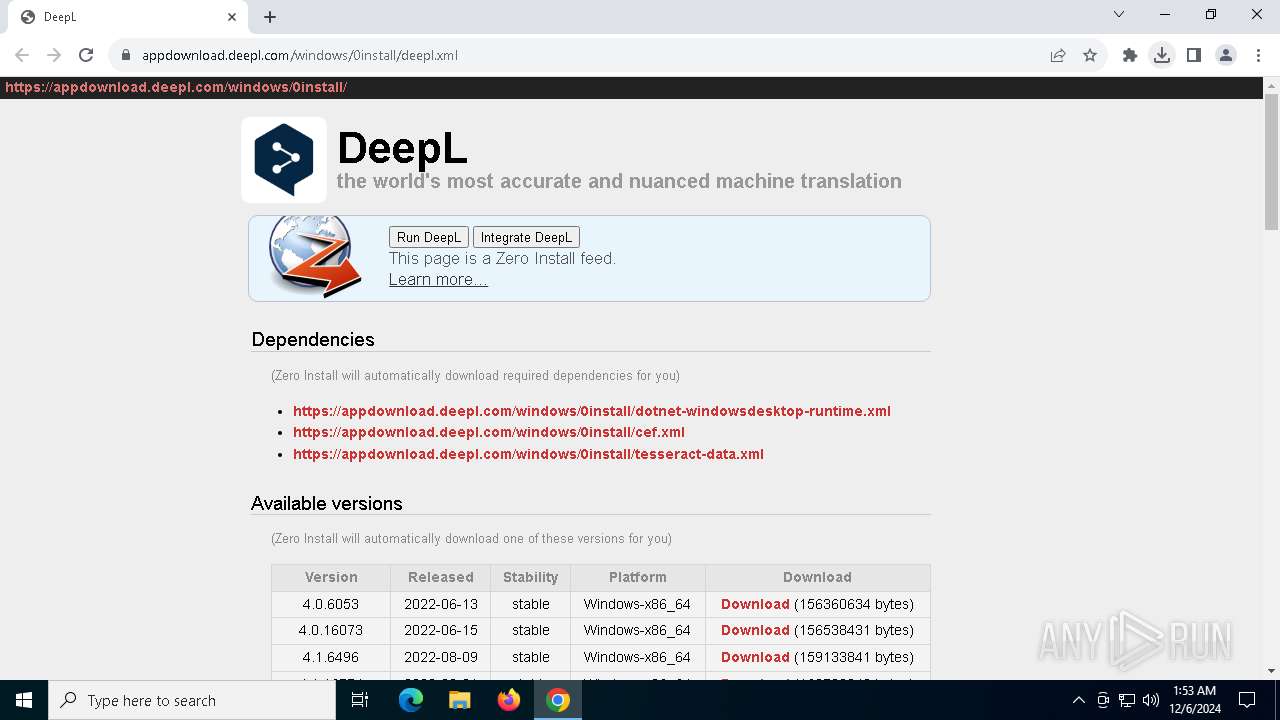
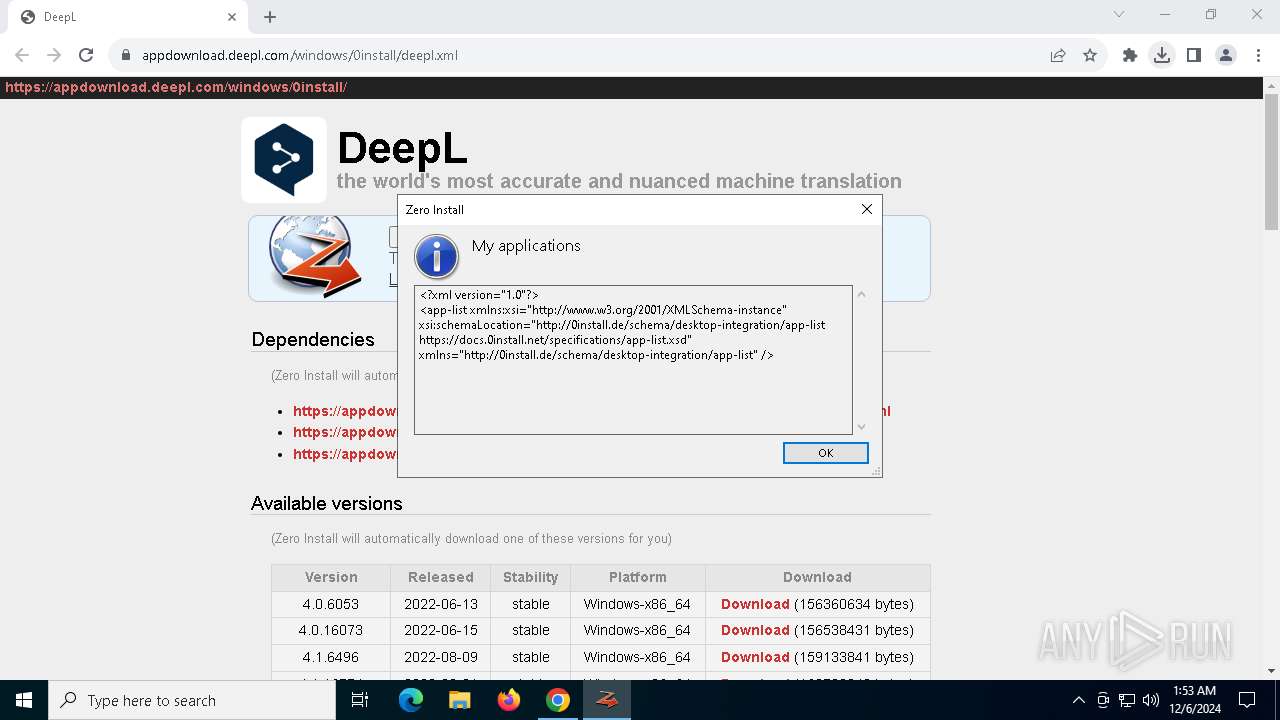
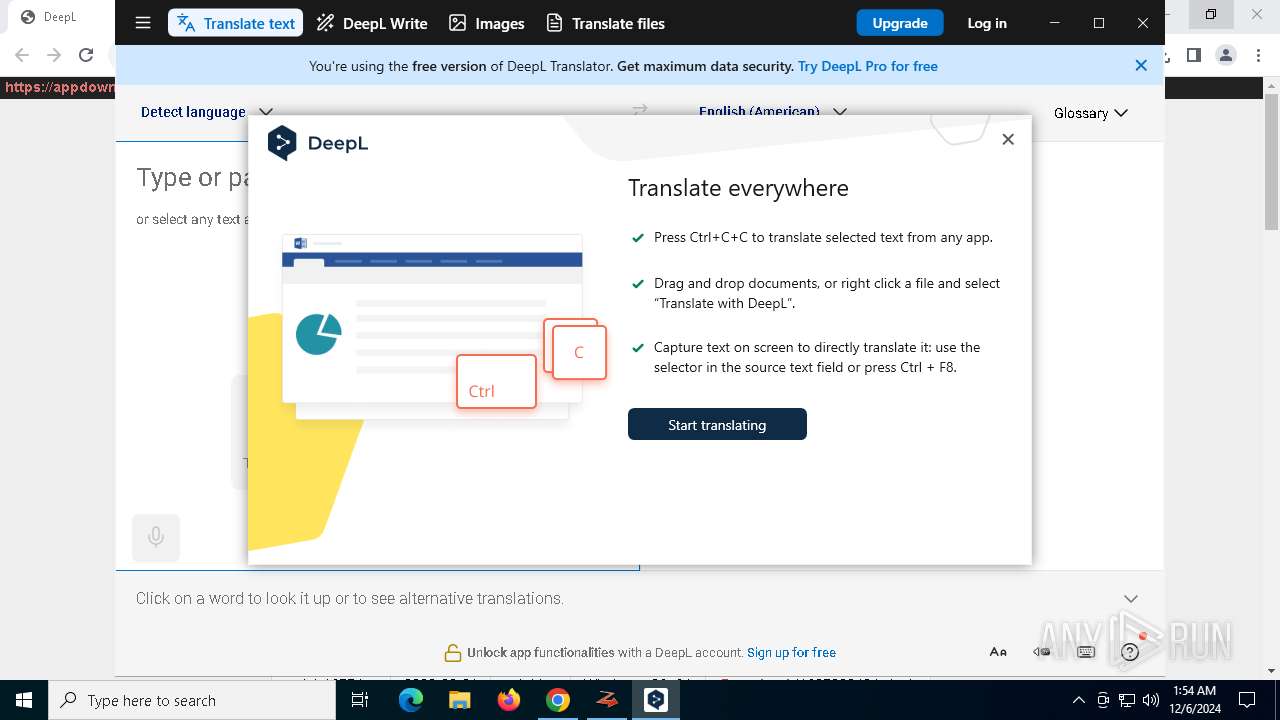
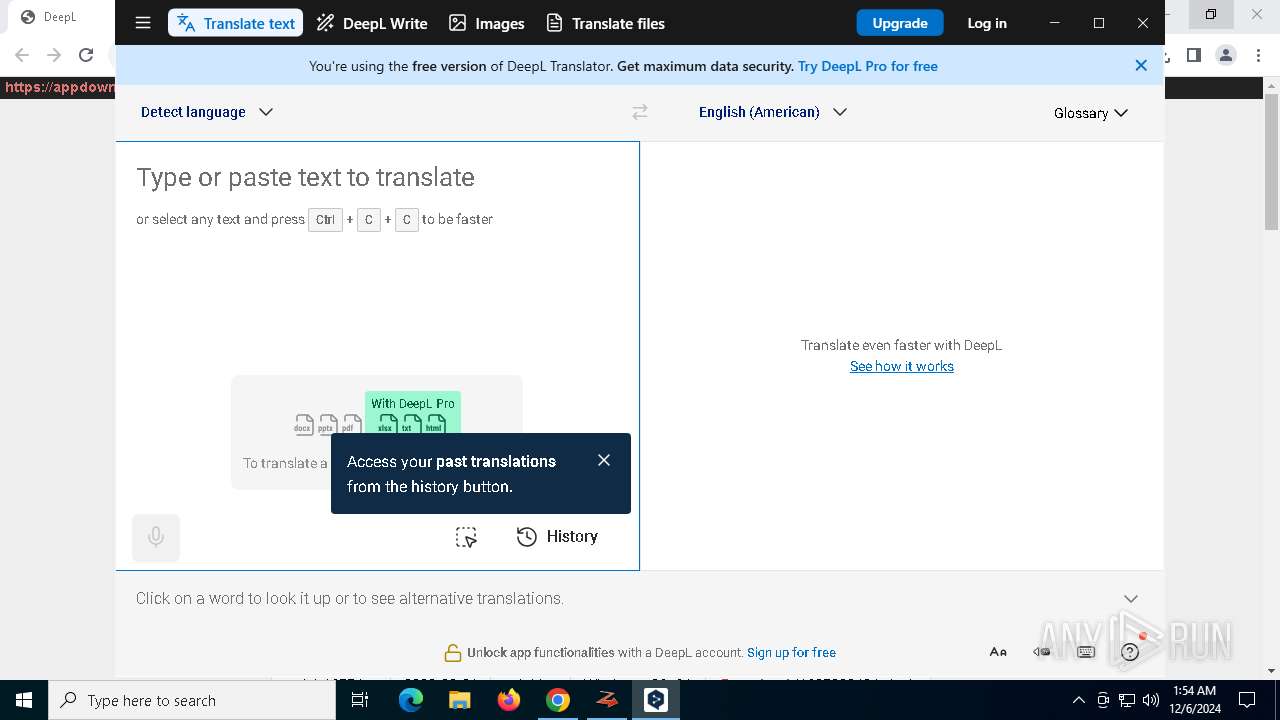
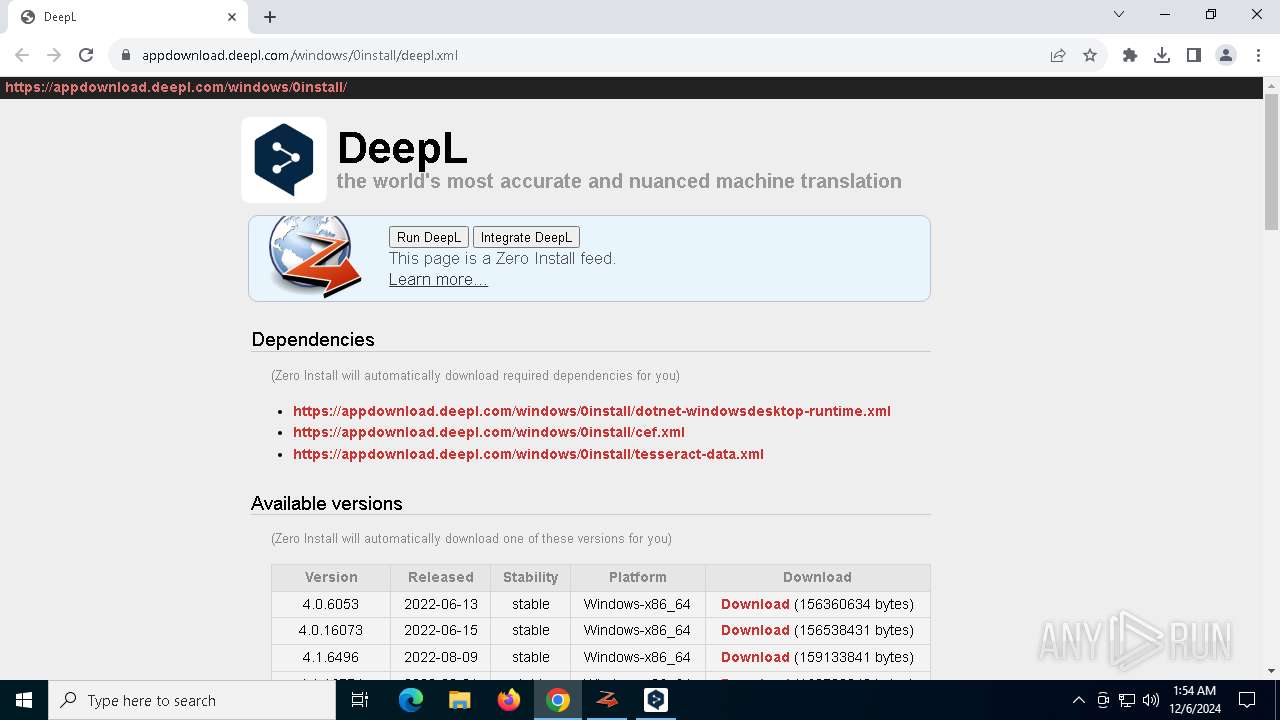
| URL: | https://appdownload.deepl.com/windows/0install/deepl.xml |
| Full analysis: | https://app.any.run/tasks/6f7dd5d2-a735-4974-aa7c-65e9e71523bd |
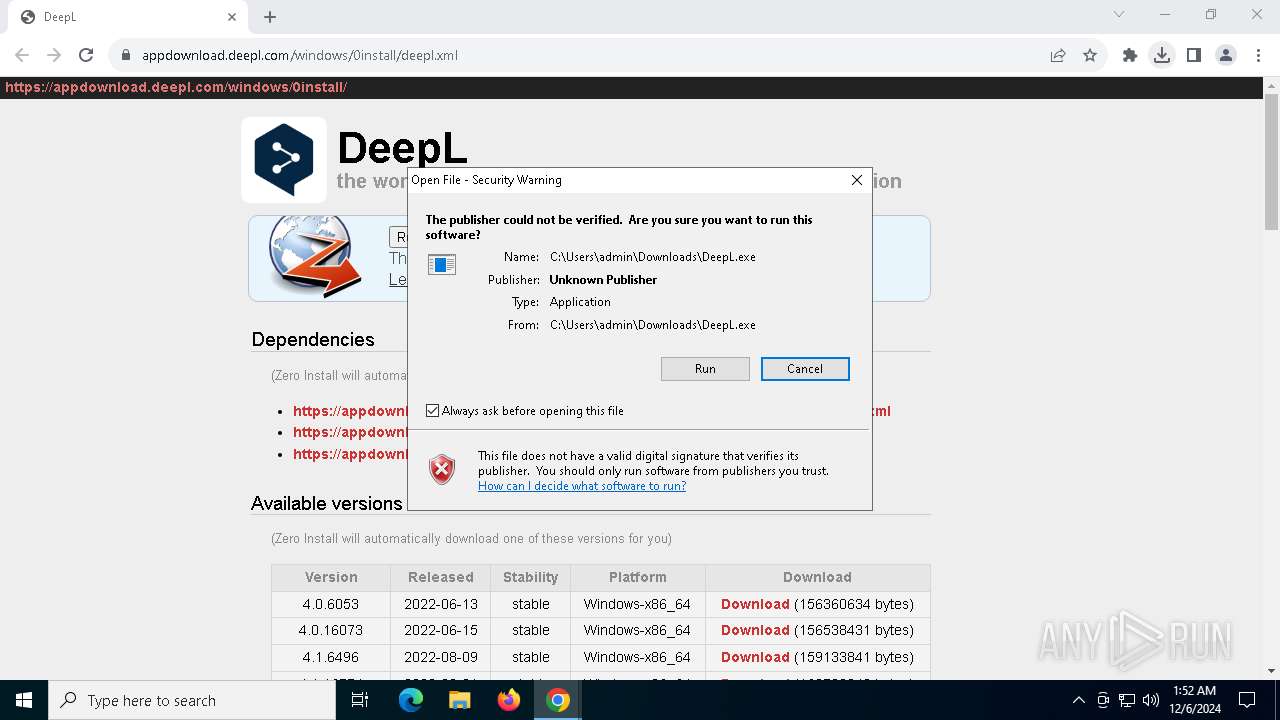
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2024, 01:51:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 4B0E406C81176401A57320BDC2A01531 |
| SHA1: | 4637E5B319D4150B70296046B2F3EBB650B6939C |
| SHA256: | B06B67932007BF915F405696CE973A083D5E22CD5B028074BAC00FD2A646B278 |
| SSDEEP: | 3:N8a8KnjZ3SM/6J:2a3njZ3Sei |
MALICIOUS
No malicious indicators.SUSPICIOUS
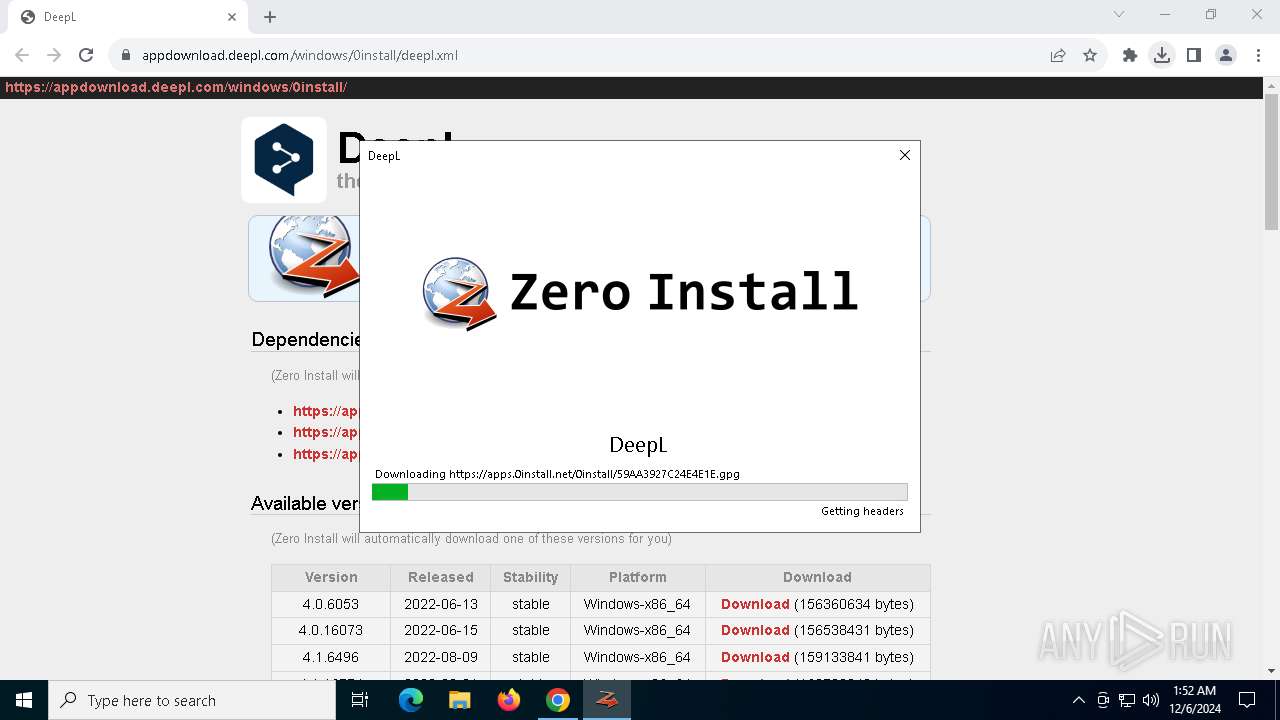
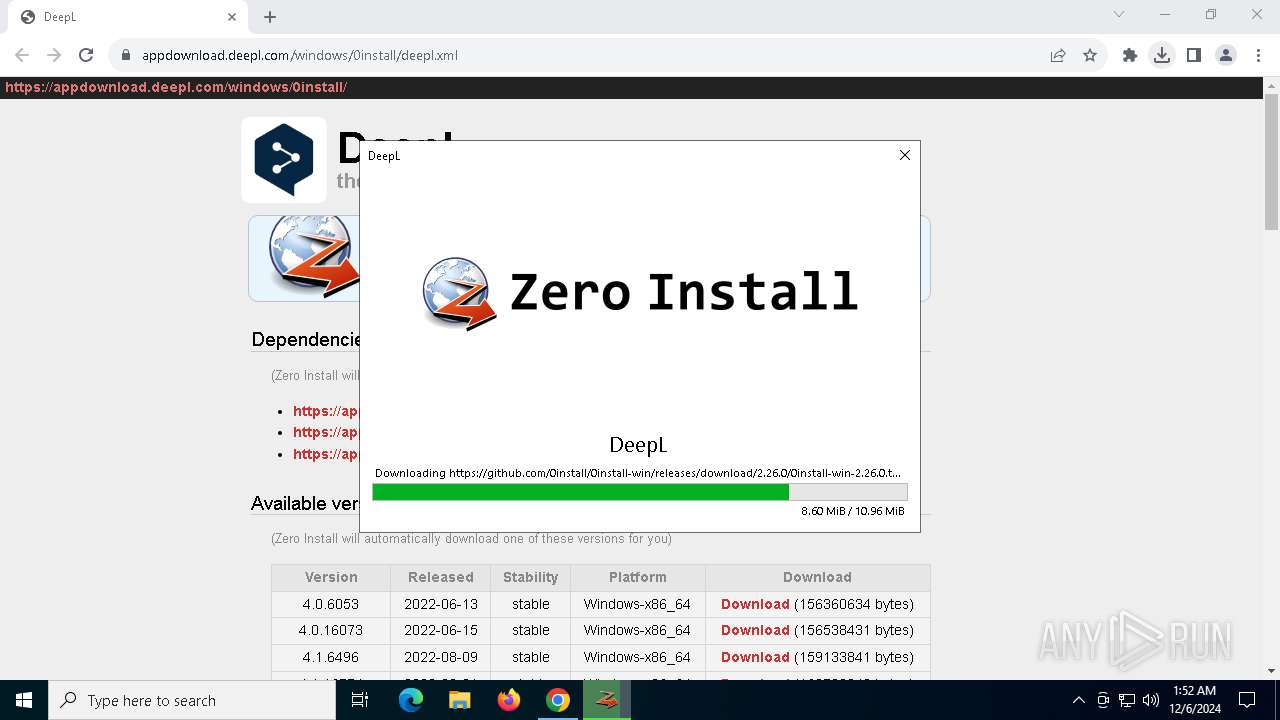
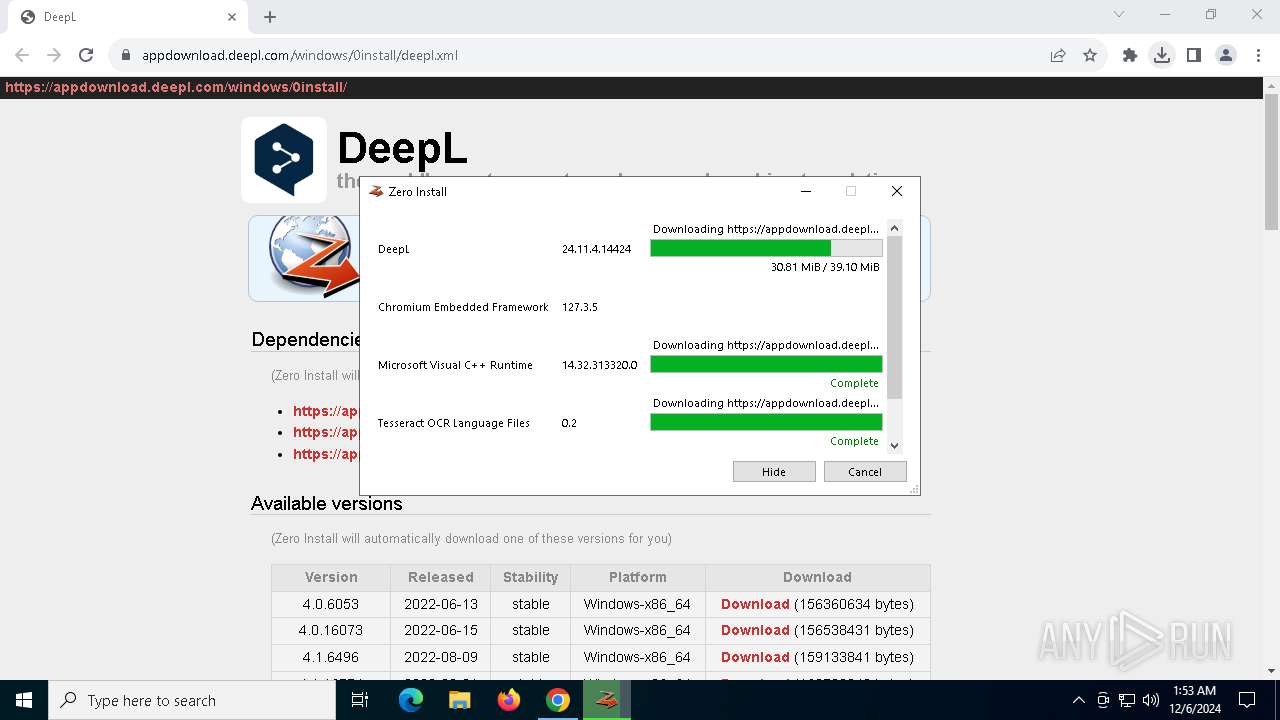
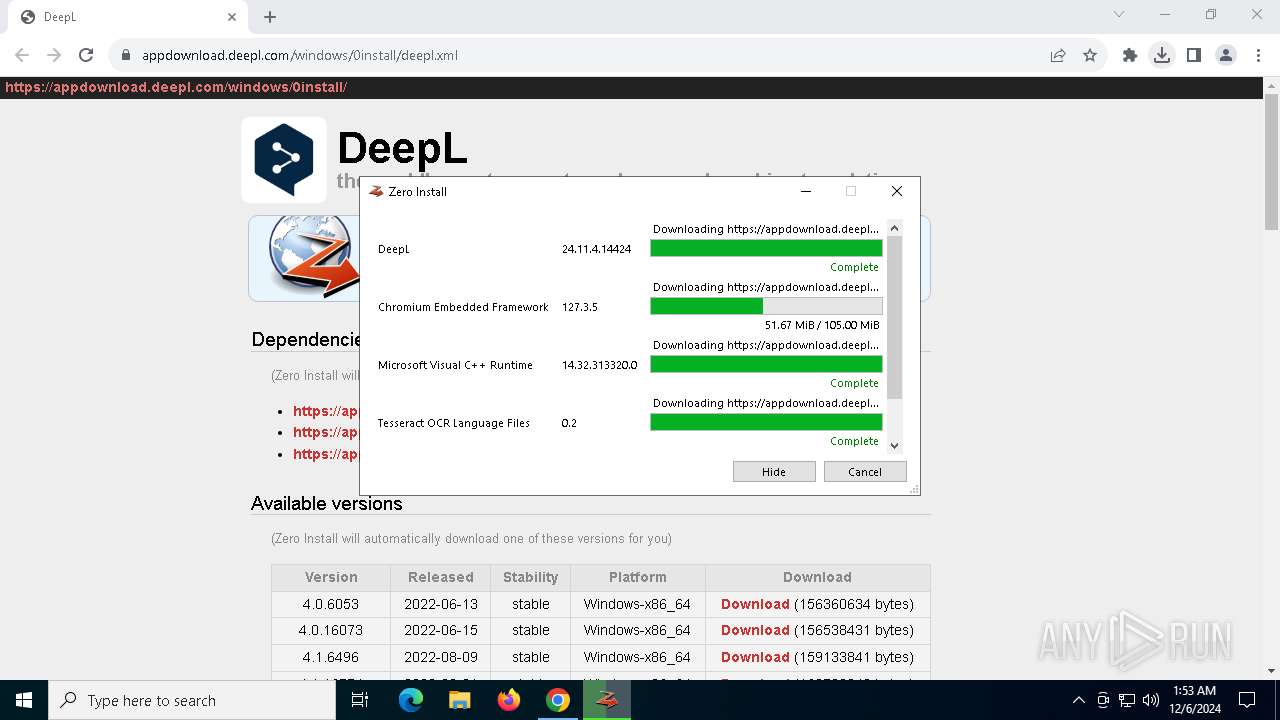
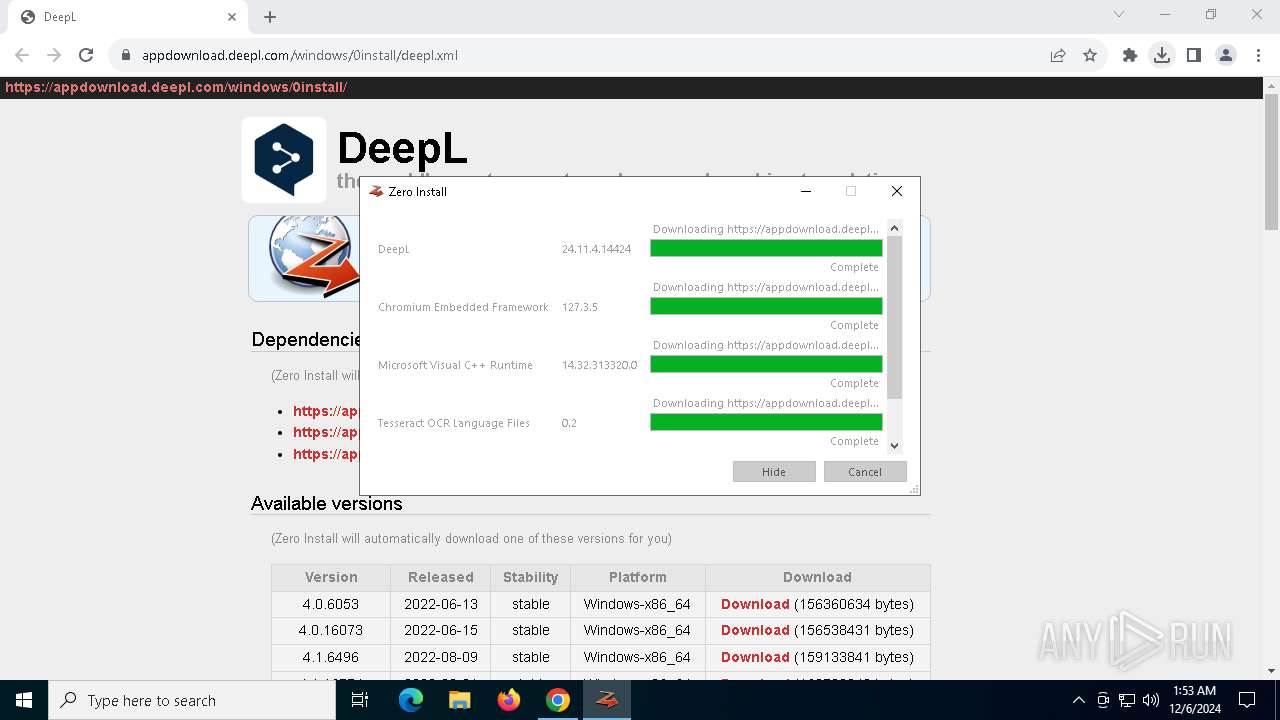
Executable content was dropped or overwritten
- DeepL.exe (PID: 2008)
- 0install-win.exe (PID: 5320)
The process creates files with name similar to system file names
- DeepL.exe (PID: 2008)
- 0install-win.exe (PID: 5320)
Process drops legitimate windows executable
- DeepL.exe (PID: 2008)
- 0install-win.exe (PID: 5320)
Detected use of alternative data streams (AltDS)
- 0install-win.exe (PID: 5320)
The process drops C-runtime libraries
- 0install-win.exe (PID: 5320)
Checks Windows Trust Settings
- DeepL.exe (PID: 5892)
Reads security settings of Internet Explorer
- DeepL.exe (PID: 5892)
- 0install.exe (PID: 5912)
Reads the date of Windows installation
- 0install.exe (PID: 5912)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 6056)
- chrome.exe (PID: 5712)
The process uses the downloaded file
- chrome.exe (PID: 4264)
- chrome.exe (PID: 6056)
- 0install.exe (PID: 5912)
Checks supported languages
- DeepL.exe (PID: 2008)
- 0install-win.exe (PID: 5320)
- DeepL.exe (PID: 5892)
- 0install.exe (PID: 3052)
- CefSharp.BrowserSubprocess.exe (PID: 1856)
- CefSharp.BrowserSubprocess.exe (PID: 3092)
- 0install.exe (PID: 5912)
- 0install-win.exe (PID: 6416)
- CefSharp.BrowserSubprocess.exe (PID: 7128)
- CefSharp.BrowserSubprocess.exe (PID: 5432)
- identity_helper.exe (PID: 648)
- identity_helper.exe (PID: 7232)
- CefSharp.BrowserSubprocess.exe (PID: 5936)
- CefSharp.BrowserSubprocess.exe (PID: 3836)
- CefSharp.BrowserSubprocess.exe (PID: 7824)
- CefSharp.BrowserSubprocess.exe (PID: 6436)
- CefSharp.BrowserSubprocess.exe (PID: 5872)
- CefSharp.BrowserSubprocess.exe (PID: 7776)
Disables trace logs
- DeepL.exe (PID: 2008)
- 0install-win.exe (PID: 5320)
- 0install.exe (PID: 3052)
- 0install.exe (PID: 5912)
- 0install-win.exe (PID: 6416)
Reads the computer name
- DeepL.exe (PID: 2008)
- 0install-win.exe (PID: 5320)
- 0install.exe (PID: 3052)
- DeepL.exe (PID: 5892)
- 0install.exe (PID: 5912)
- CefSharp.BrowserSubprocess.exe (PID: 1856)
- CefSharp.BrowserSubprocess.exe (PID: 3092)
- 0install-win.exe (PID: 6416)
- CefSharp.BrowserSubprocess.exe (PID: 5432)
- CefSharp.BrowserSubprocess.exe (PID: 7824)
- identity_helper.exe (PID: 648)
- CefSharp.BrowserSubprocess.exe (PID: 5936)
- identity_helper.exe (PID: 7232)
- CefSharp.BrowserSubprocess.exe (PID: 7128)
- CefSharp.BrowserSubprocess.exe (PID: 3836)
- CefSharp.BrowserSubprocess.exe (PID: 6436)
- CefSharp.BrowserSubprocess.exe (PID: 5872)
- CefSharp.BrowserSubprocess.exe (PID: 7776)
Checks proxy server information
- DeepL.exe (PID: 2008)
- 0install-win.exe (PID: 5320)
- 0install.exe (PID: 3052)
- DeepL.exe (PID: 5892)
- 0install.exe (PID: 5912)
- 0install-win.exe (PID: 6416)
Create files in a temporary directory
- DeepL.exe (PID: 2008)
- 0install-win.exe (PID: 5320)
- DeepL.exe (PID: 5892)
- 0install.exe (PID: 3052)
Creates files or folders in the user directory
- DeepL.exe (PID: 2008)
- 0install-win.exe (PID: 5320)
- DeepL.exe (PID: 5892)
- 0install.exe (PID: 5912)
- 0install.exe (PID: 3052)
- CefSharp.BrowserSubprocess.exe (PID: 5432)
- 0install-win.exe (PID: 6416)
Reads the machine GUID from the registry
- DeepL.exe (PID: 2008)
- 0install-win.exe (PID: 5320)
- DeepL.exe (PID: 5892)
- 0install.exe (PID: 3052)
- 0install.exe (PID: 5912)
- 0install-win.exe (PID: 6416)
Reads Environment values
- DeepL.exe (PID: 2008)
- 0install-win.exe (PID: 5320)
- 0install.exe (PID: 3052)
- 0install.exe (PID: 5912)
- 0install-win.exe (PID: 6416)
- identity_helper.exe (PID: 648)
- identity_helper.exe (PID: 7232)
Reads the software policy settings
- DeepL.exe (PID: 2008)
- DeepL.exe (PID: 5892)
- 0install-win.exe (PID: 5320)
Creates files in the program directory
- 0install-win.exe (PID: 5320)
- DeepL.exe (PID: 5892)
- 0install-win.exe (PID: 6416)
Application launched itself
- chrome.exe (PID: 6056)
- msedge.exe (PID: 7680)
- msedge.exe (PID: 4140)
Sends debugging messages
- DeepL.exe (PID: 5892)
Process checks computer location settings
- DeepL.exe (PID: 5892)
- CefSharp.BrowserSubprocess.exe (PID: 3092)
- 0install.exe (PID: 5912)
- CefSharp.BrowserSubprocess.exe (PID: 7128)
- CefSharp.BrowserSubprocess.exe (PID: 3836)
Process checks whether UAC notifications are on
- 0install.exe (PID: 5912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
222
Monitored processes
87
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 648 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6720 --field-trial-handle=2408,i,15705558025493475200,3681572902594501899,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1856 | "C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_NX54BP3MSRHNDMB5N5YOFJZWO5QE5I5W7JTPGB4XC7MEJNSXCC3A\.\CefSharp.BrowserSubprocess.exe" --type=gpu-process --no-sandbox --disable-gpu-vsync --user-agent="DeepL/24.11.4.14424 (Microsoft Windows NT 10.0.19045.0; x64)" --start-stack-profiler --enable-chrome-runtime --user-data-dir="C:\Users\admin\AppData\Local\DeepL_SE\cache\2c3872b8-ffea-4b4e-b011-fa51e99d26a1" --cefsharpexitsub --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --use-gl=angle --use-angle=swiftshader-webgl --field-trial-handle=5344,i,2459228405133195572,11502566937055217412,262144 --disable-features=EnableHangWatcher --variations-seed-version --enable-logging=handle --log-file=5348 --mojo-platform-channel-handle=5340 /prefetch:2 --host-process-id=5892 | C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_NX54BP3MSRHNDMB5N5YOFJZWO5QE5I5W7JTPGB4XC7MEJNSXCC3A\CefSharp.BrowserSubprocess.exe | — | DeepL.exe | |||||||||||
User: admin Company: The CefSharp Authors Integrity Level: MEDIUM Description: CefSharp.BrowserSubprocess Version: 127.3.50.0 | |||||||||||||||
| 2008 | "C:\Users\admin\Downloads\DeepL.exe" | C:\Users\admin\Downloads\DeepL.exe | chrome.exe | ||||||||||||
User: admin Company: zero-install Integrity Level: MEDIUM Description: zero-install Exit code: 5892 Version: 2.26.0.0 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5724 --field-trial-handle=1836,i,13089669516828478135,14223100464495427867,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 2452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4952 --field-trial-handle=1836,i,13089669516828478135,14223100464495427867,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 2676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4640 --field-trial-handle=1836,i,13089669516828478135,14223100464495427867,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3052 | "C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_3IWFAPVMB3QX4MUSWWOAWPUNRBK7NPIQUIMAJZLBBI7R2NLMVE3A\0install.exe" list-apps --batch --xml https://appdownload.deepl.com/windows/0install/deepl.xml | C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_3IWFAPVMB3QX4MUSWWOAWPUNRBK7NPIQUIMAJZLBBI7R2NLMVE3A\0install.exe | — | DeepL.exe | |||||||||||
User: admin Company: Bastian Eicher Integrity Level: MEDIUM Description: 0install Exit code: 0 Version: 2.26.0.0 | |||||||||||||||
| 3092 | "C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_NX54BP3MSRHNDMB5N5YOFJZWO5QE5I5W7JTPGB4XC7MEJNSXCC3A\.\CefSharp.BrowserSubprocess.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-sandbox --user-agent="DeepL/24.11.4.14424 (Microsoft Windows NT 10.0.19045.0; x64)" --enable-chrome-runtime --user-data-dir="C:\Users\admin\AppData\Local\DeepL_SE\cache\2c3872b8-ffea-4b4e-b011-fa51e99d26a1" --cefsharpexitsub --field-trial-handle=5492,i,2459228405133195572,11502566937055217412,262144 --disable-features=EnableHangWatcher --variations-seed-version --enable-logging=handle --log-file=5504 --mojo-platform-channel-handle=5500 /prefetch:8 --host-process-id=5892 | C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_NX54BP3MSRHNDMB5N5YOFJZWO5QE5I5W7JTPGB4XC7MEJNSXCC3A\CefSharp.BrowserSubprocess.exe | — | DeepL.exe | |||||||||||
User: admin Company: The CefSharp Authors Integrity Level: MEDIUM Description: CefSharp.BrowserSubprocess Version: 127.3.50.0 | |||||||||||||||
| 3128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4700 --field-trial-handle=1836,i,13089669516828478135,14223100464495427867,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3524 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffff3385fd8,0x7ffff3385fe4,0x7ffff3385ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
Total events
23 627
Read events
23 500
Write events
119
Delete events
8
Modification events
| (PID) Process: | (6056) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6056) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6056) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6056) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6056) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4264) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000EA99C3738147DB01 | |||
| (PID) Process: | (2008) DeepL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepL_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2008) DeepL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepL_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2008) DeepL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepL_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2008) DeepL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepL_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
Executable files
1 278
Suspicious files
752
Text files
257
Unknown types
68
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF135f69.TMP | — | |
MD5:— | SHA256:— | |||
| 6056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF135f79.TMP | — | |
MD5:— | SHA256:— | |||
| 6056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF135f69.TMP | — | |
MD5:— | SHA256:— | |||
| 6056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF135f79.TMP | — | |
MD5:— | SHA256:— | |||
| 6056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF135f79.TMP | — | |
MD5:— | SHA256:— | |||
| 6056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF135f79.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
130
DNS requests
121
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5856 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5856 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4668 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4716 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4716 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6376 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4668 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4668 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4668 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5856 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5856 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6056 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1076 | svchost.exe | 23.32.186.57:443 | go.microsoft.com | AKAMAI-AS | BR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
appdownload.deepl.com |
| whitelisted |
accounts.google.com |
| whitelisted |
0install.net |
| unknown |
Threats
Process | Message |
|---|---|
DeepL.exe | Profiler was prevented from loading notification profiler due to app settings.
Process ID (decimal): 5892. Message ID: [0x2509].
|
DeepL.exe | [01:53:41 WRN] Exception during loading options: System.IO.DirectoryNotFoundException: Could not find a part of the path 'C:\Users\admin\AppData\Roaming\DeepL_SE\settings.json'.
at Microsoft.Win32.SafeHandles.SafeFileHandle.CreateFile(String fullPath, FileMode mode, FileAccess access, FileShare share, FileOptions options)
at Microsoft.Win32.SafeHandles.SafeFileHandle.Open(String fullPath, FileMode mode, FileAccess access, FileShare share, FileOptions options, Int64 preallocationSize)
at System.IO.Strategies.OSFileStreamStrategy..ctor(String path, FileMode mode, FileAccess access, FileShare share, FileOptions options, Int64 preallocationSize)
at System.IO.Strategies.FileStreamHelpers.ChooseStrategyCore(String path, FileMode mode, FileAccess access, FileShare share, FileOptions options, Int64 preallocationSize)
at System.IO.Strategies.FileStreamHelpers.ChooseStrategy(FileStream fileStream, String path, FileMode mode, FileAccess access, FileShare share, Int32 bufferSize, FileOptions options, Int64 preallocationSize)
at System.IO.FileStream..ctor(String path, FileMode mode, FileAccess access, FileShare share)
at DeepL.Persistence.FileStreamProvider.GetStream(StreamModes modes)
at DeepL.Persistence.RepositoryBase`1.LoadCore()
at DeepL.Persistence.RepositoryBase`1.Load()
|
DeepL.exe | [01:53:41 INF] Read app configuration (LocalSettings): proxy.active = False
|
DeepL.exe | [01:53:41 INF] Loaded user settings: {"schema_version":2,"version":"24.11.4.14424","configuration":{"dialog":{"is_manual_first_start":false,"has_document_translation_onboarding_been_shown":false,"wants_to_show_onboarding":false,"wants_to_show_translation_history_opt_in":false,"has_onboarding_screen_been_shown_at_start":false,"has_desktop_survey_baloon_been_shown":false,"has_translation_history_privacy_hint_been_shown":false,"last_stay_logged_in":true,"visited_features_modal_page_identifiers":[],"has_image_translation_nudge_been_shown":false,"walled_state":1,"last_preferences_page_index":0,"has_assistant_nudge_been_shown":false,"text_translator_tab_promotion_banner_close_timestamp":"0001-01-01T00:00:00+00:00","write_tab_promotion_banner_close_timestamp":"0001-01-01T00:00:00+00:00","image_translator_tab_promotion_banner_close_timestamp":"0001-01-01T00:00:00+00:00","document_translation_tab_promotion_banner_close_timestamp":"0001-01-01T00:00:00+00:00","has_quick_translate_nudge_been_shown":false,"has_new_global_saved_translations_prompt_been_shown":false,"has_quick_write_nudge_been_shown":false},"window":{"last_window_state":0,"window_left":null,"window_top":null,"window_height":null,"window_width":null,"set_default_window_size":false},"app":{"updated_from_version":null,"updated_to_version":null,"install_voice_at_startup":null}},"UserPreferences":{"exit_from_menu_without_prompt":false,"custom_shortcut":{},"is_custom_shortcut_enabled":false,"is_shortcut_disabled":false,"screen_capture_shortcut":{},"is_screen_capture_enabled":false,"screen_capture_languages":["de","en"],"doc_trans_save_folder_strategy":0,"doc_trans_last_target_language":"","doc_trans_last_source_language":"","recently_used_doc_trans_target_languages":[],"recently_used_doc_trans_source_languages":[],"doc_trans_last_formality":3,"proxy_preferences":{"use_proxy":false},"user_ui_theme":1,"last_quick_translate_target_language":"","recently_used_quick_translate_target_languages":[],"use_quick_translate_on_shortcut":true,"use_app_on_shortcut":false,"image_translation_last_source_language":"","image_translation_last_target_language":"","image_translation_last_formality":3,"use_assistant":true,"general_preferences":{"behaviour_on_closing":0},"is_rewrite_text_enabled":true,"rewrite_text_shortcut":{},"last_used_quick_write_style":"","use_document_translation_web_view":true},"account_preferences":{},"web_view_configuration":{},"write_configuration":{},"doc_trans_configuration":{}}
|
DeepL.exe | [01:53:42 INF] No webproxy for http request handler in use
|
DeepL.exe | [01:53:42 INF] Attempting to replace httpclient after current user change detected.
|
DeepL.exe | [01:53:42 INF] No webproxy for http request handler in use
|
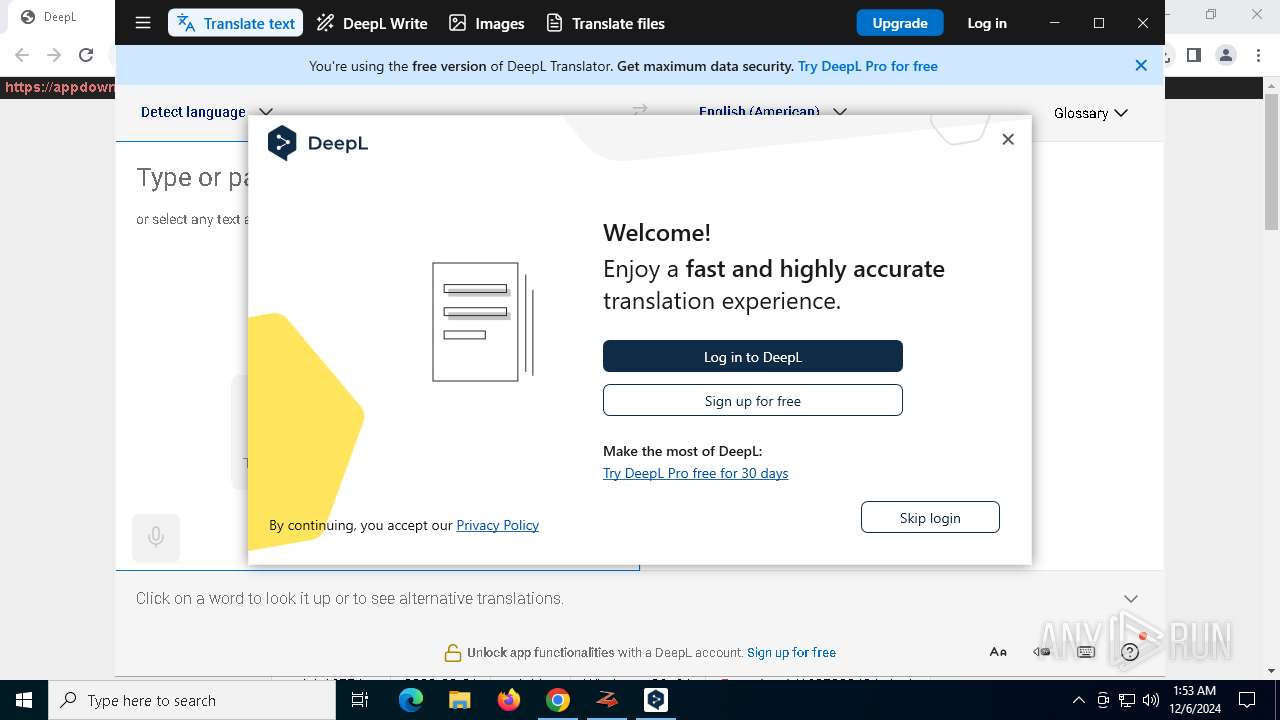
DeepL.exe | [01:53:42 INF] Created new gRPC channel for 'https://s.deepl.com/'
|
DeepL.exe | [01:53:42 INF] Using GRPC address for AbExperimentationRpc: https://s.deepl.com/
|
DeepL.exe | [01:53:42 INF] New session "82d5b6f4-20c1-4446-86a6-c38653e904e9"
|