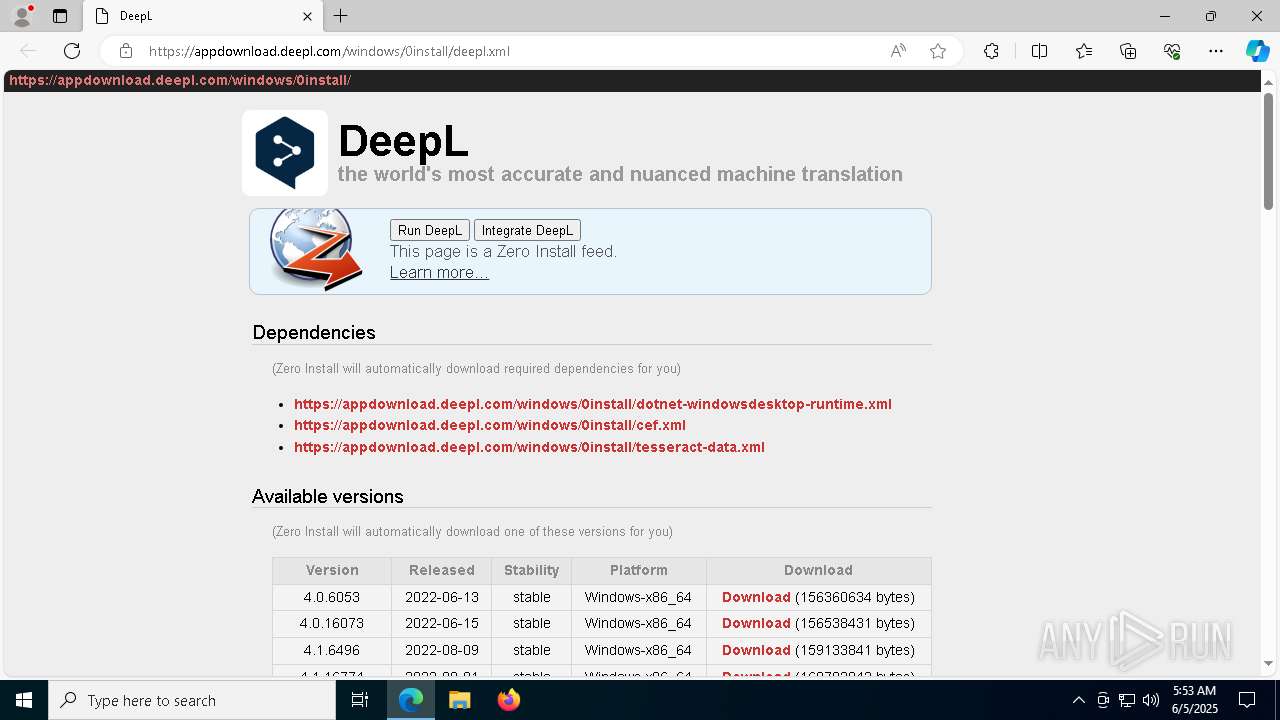
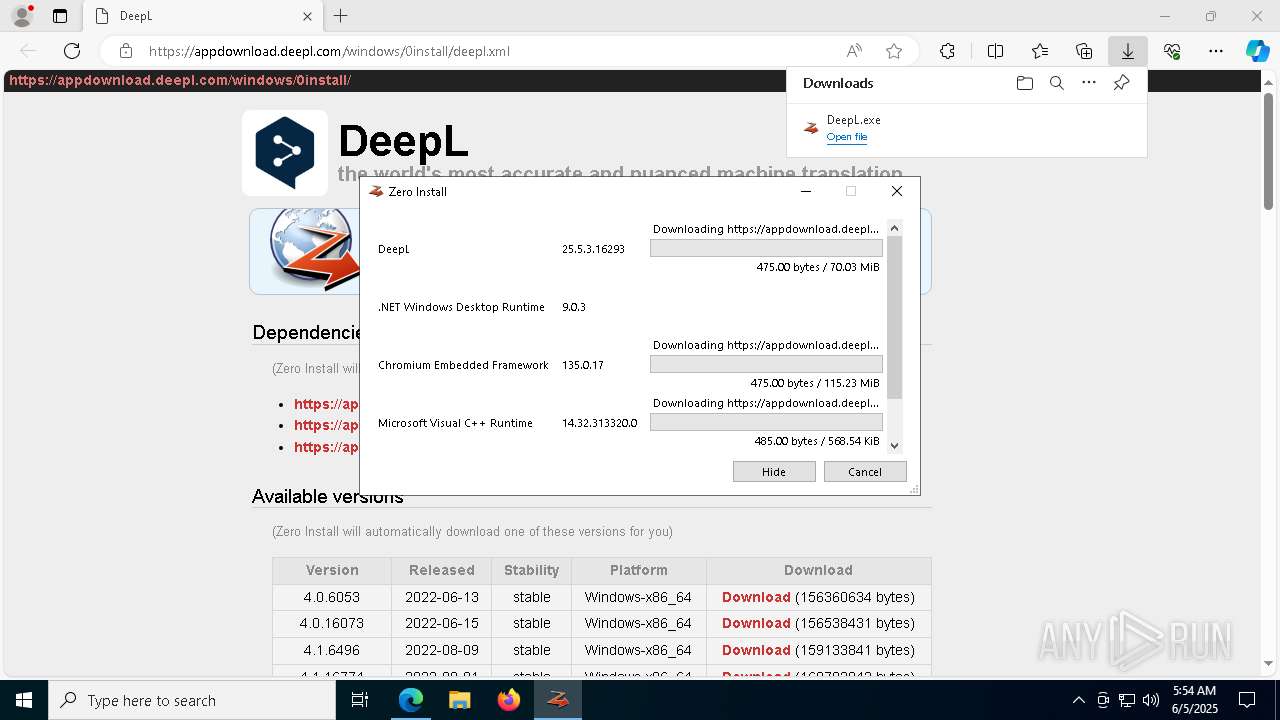
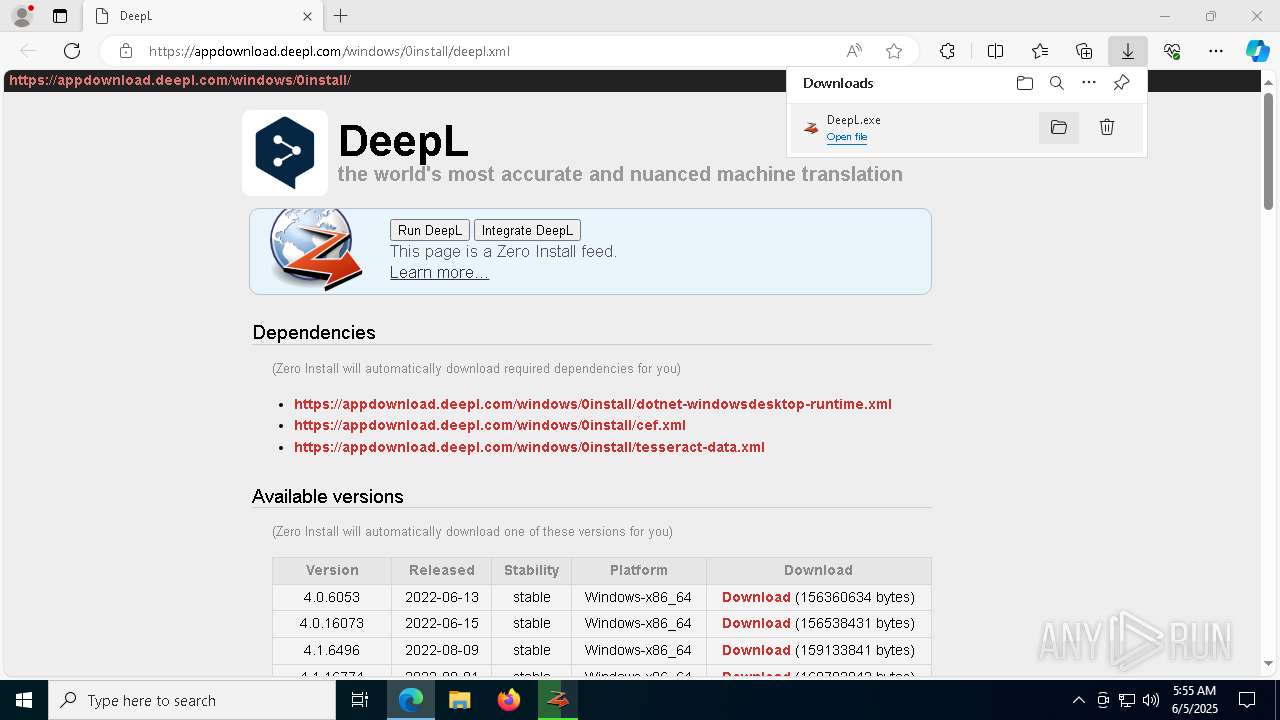
| URL: | https://appdownload.deepl.com/windows/0install/deepl.xml |
| Full analysis: | https://app.any.run/tasks/24c8481d-5bb8-4d1f-a986-0f63e20c57fc |
| Verdict: | Malicious activity |
| Analysis date: | June 05, 2025, 05:53:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
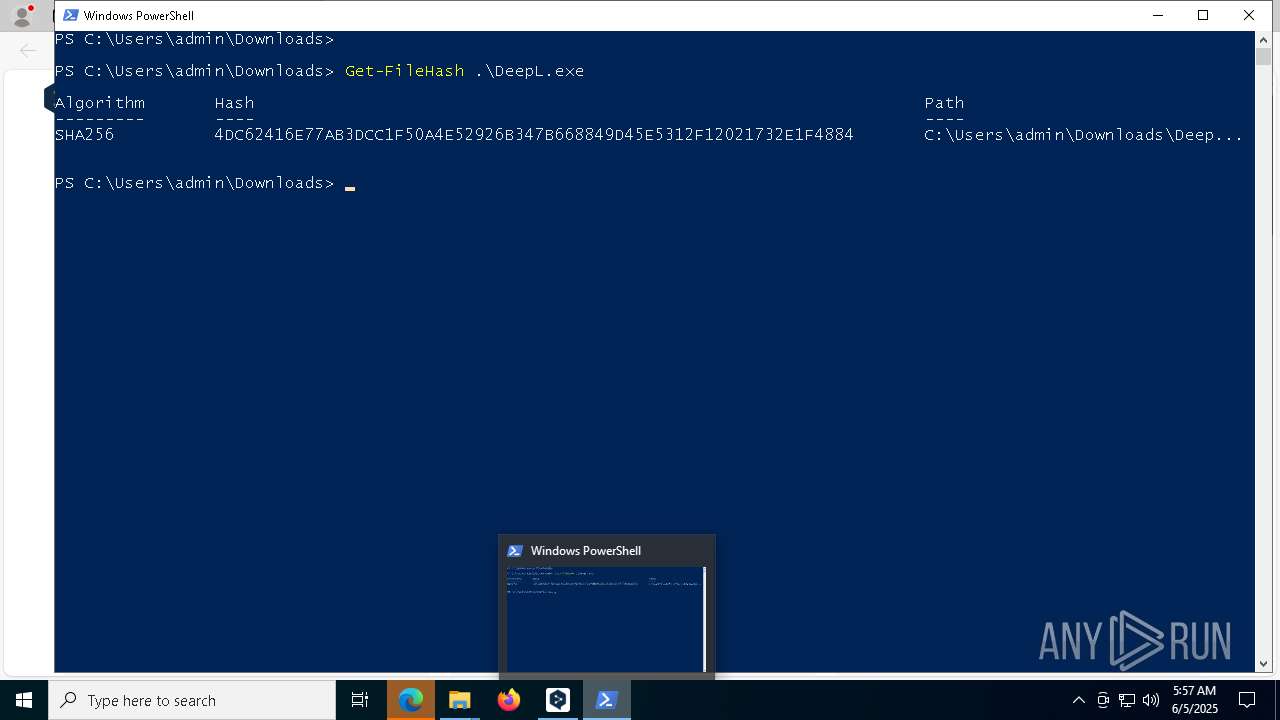
| MD5: | 4B0E406C81176401A57320BDC2A01531 |
| SHA1: | 4637E5B319D4150B70296046B2F3EBB650B6939C |
| SHA256: | B06B67932007BF915F405696CE973A083D5E22CD5B028074BAC00FD2A646B278 |
| SSDEEP: | 3:N8a8KnjZ3SM/6J:2a3njZ3Sei |
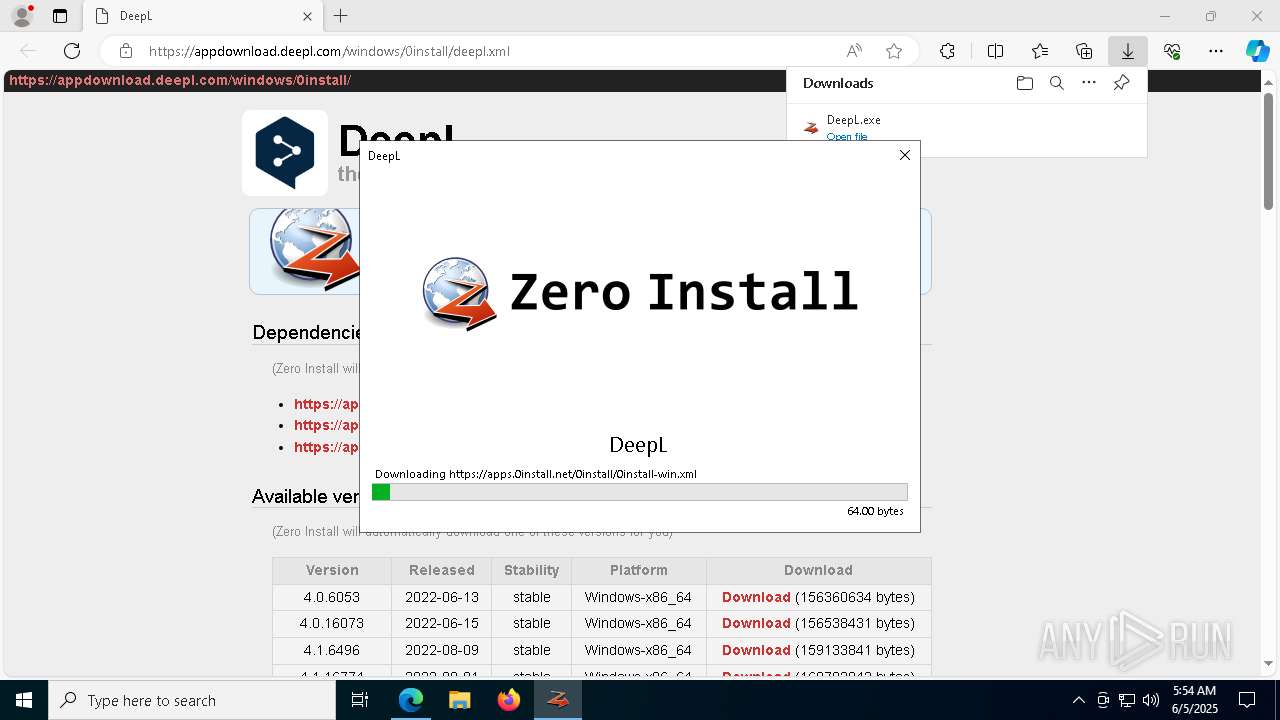
MALICIOUS
No malicious indicators.SUSPICIOUS
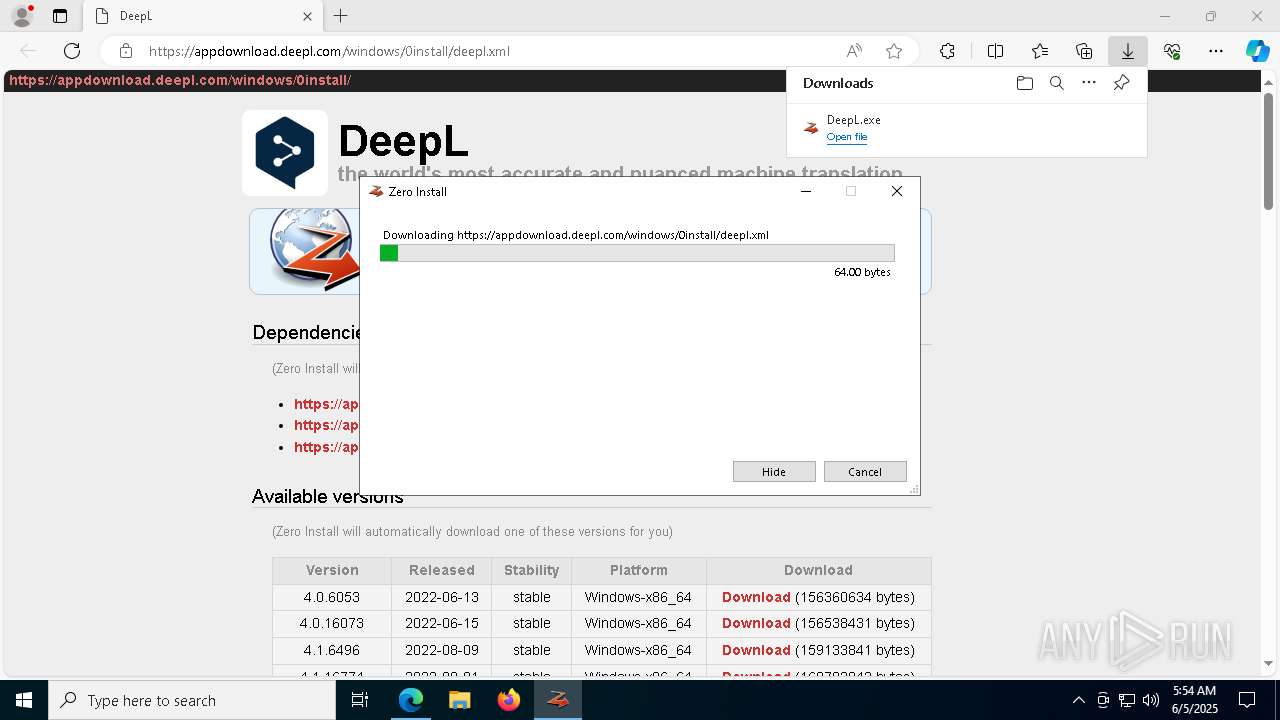
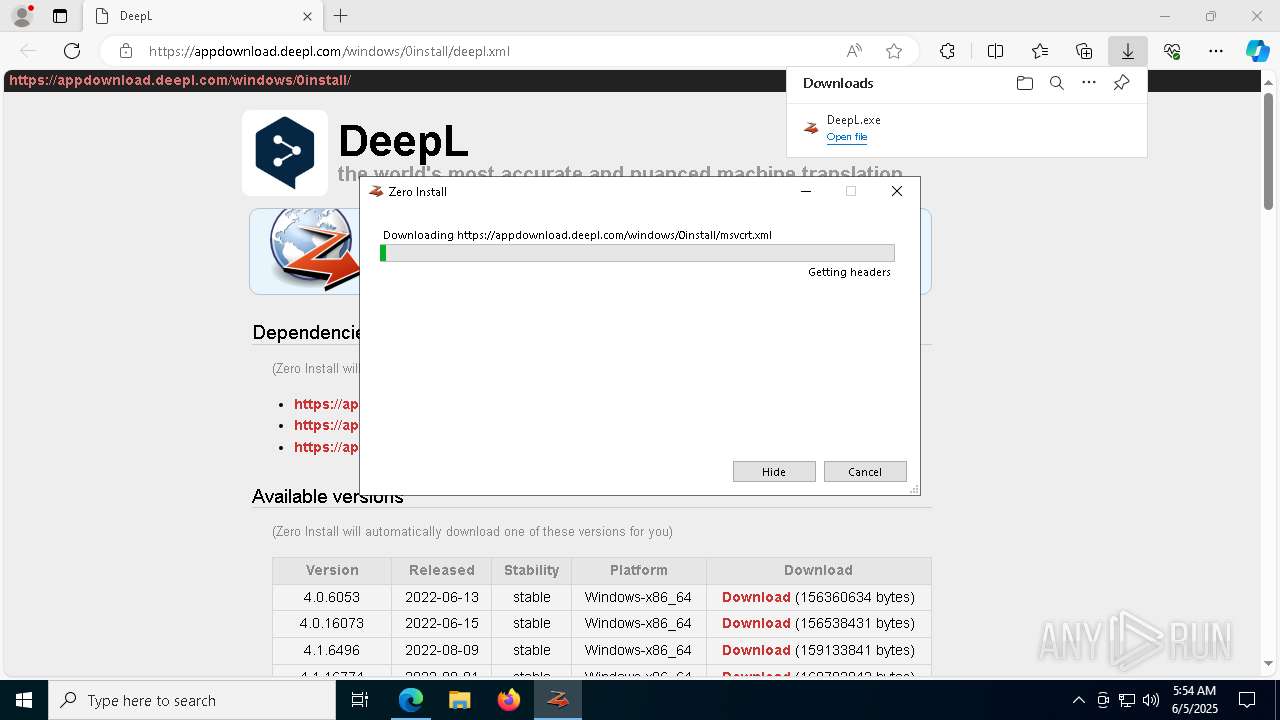
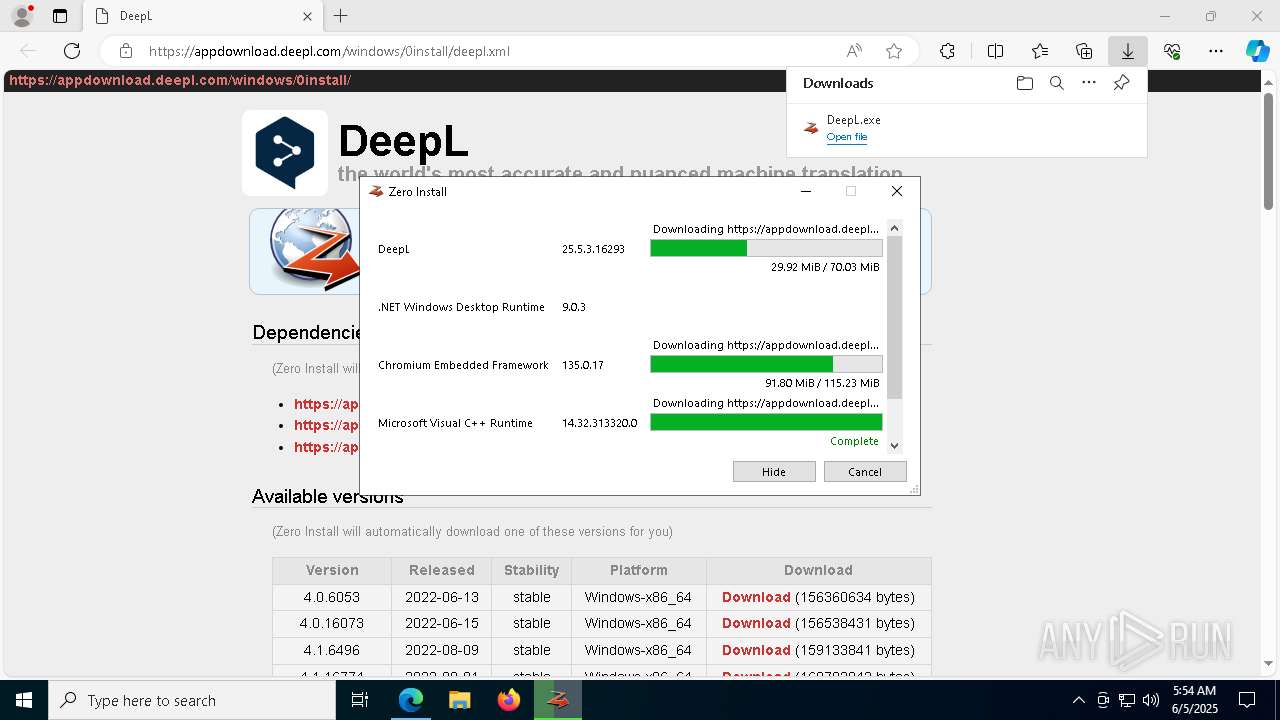
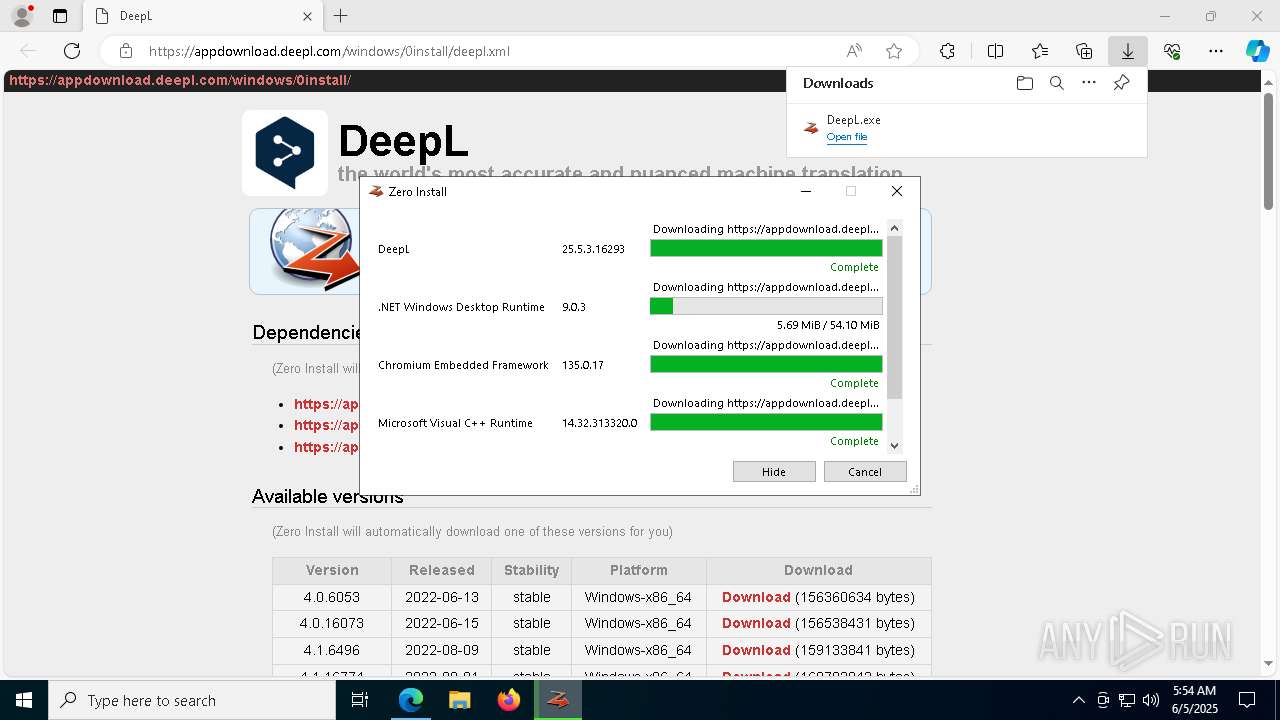
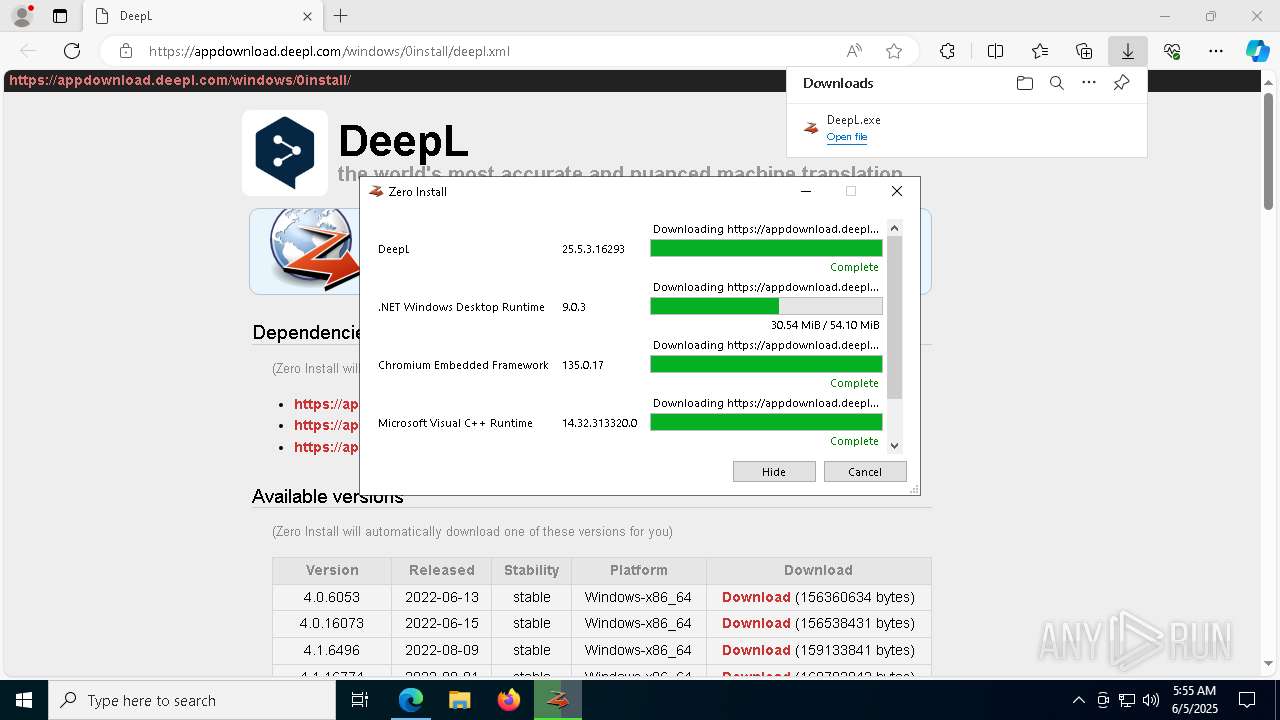
Executable content was dropped or overwritten
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
Process drops legitimate windows executable
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
The process creates files with name similar to system file names
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
Detected use of alternative data streams (AltDS)
- 0install-win.exe (PID: 3208)
The process drops C-runtime libraries
- 0install-win.exe (PID: 3208)
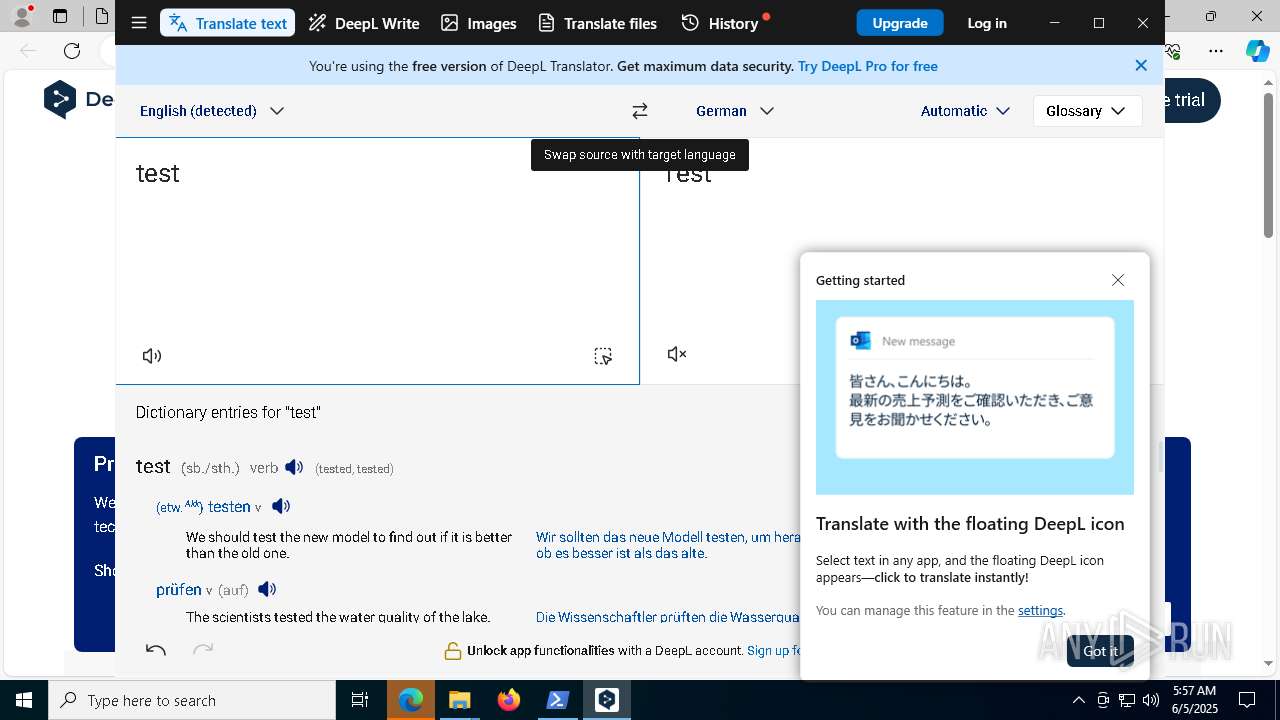
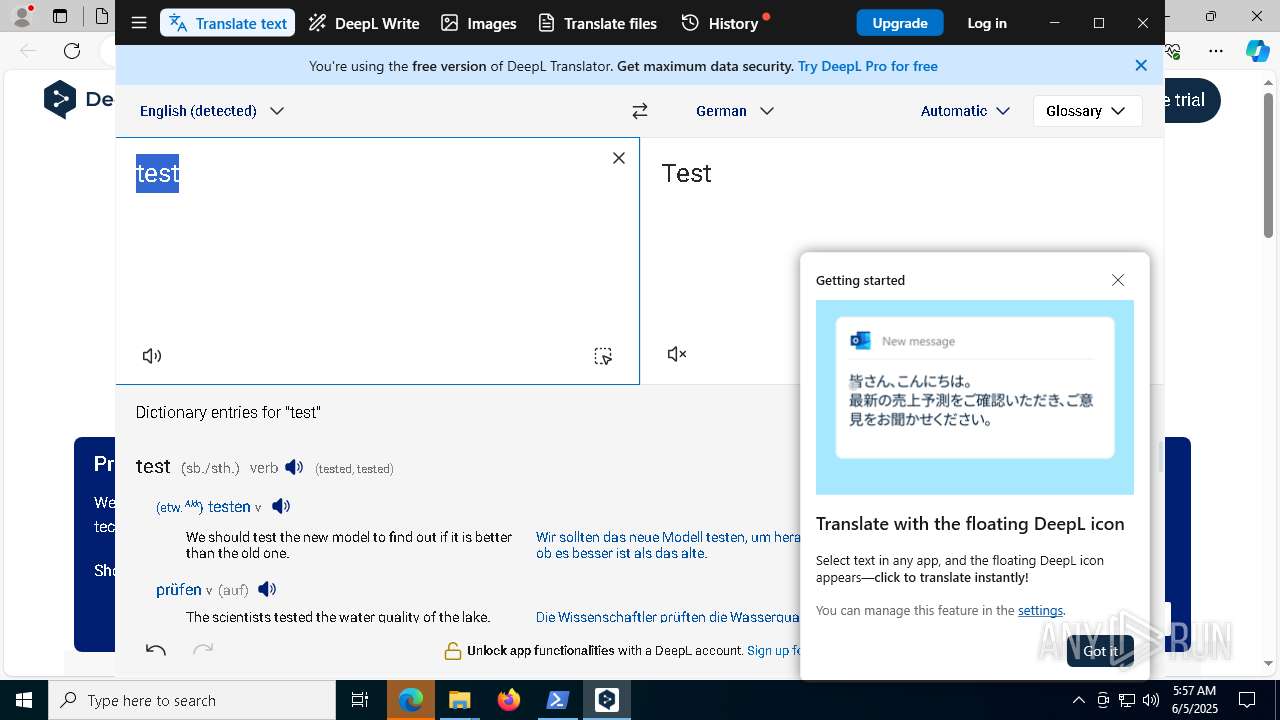
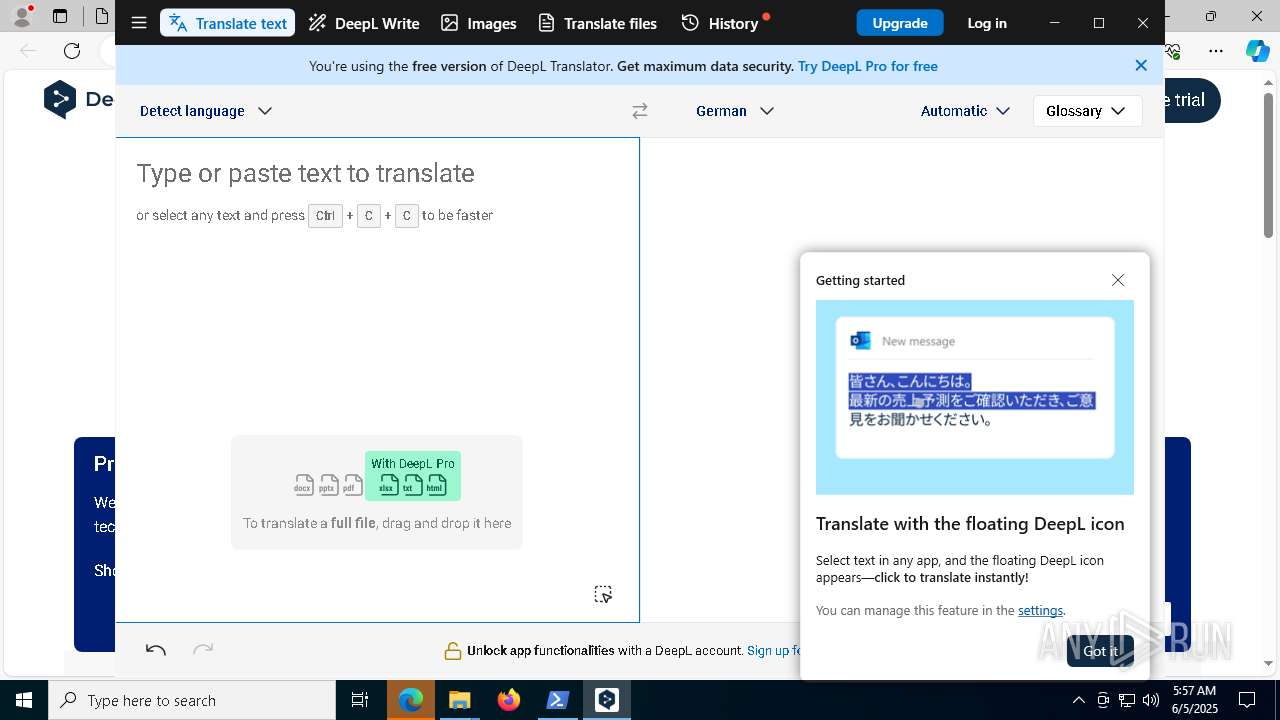
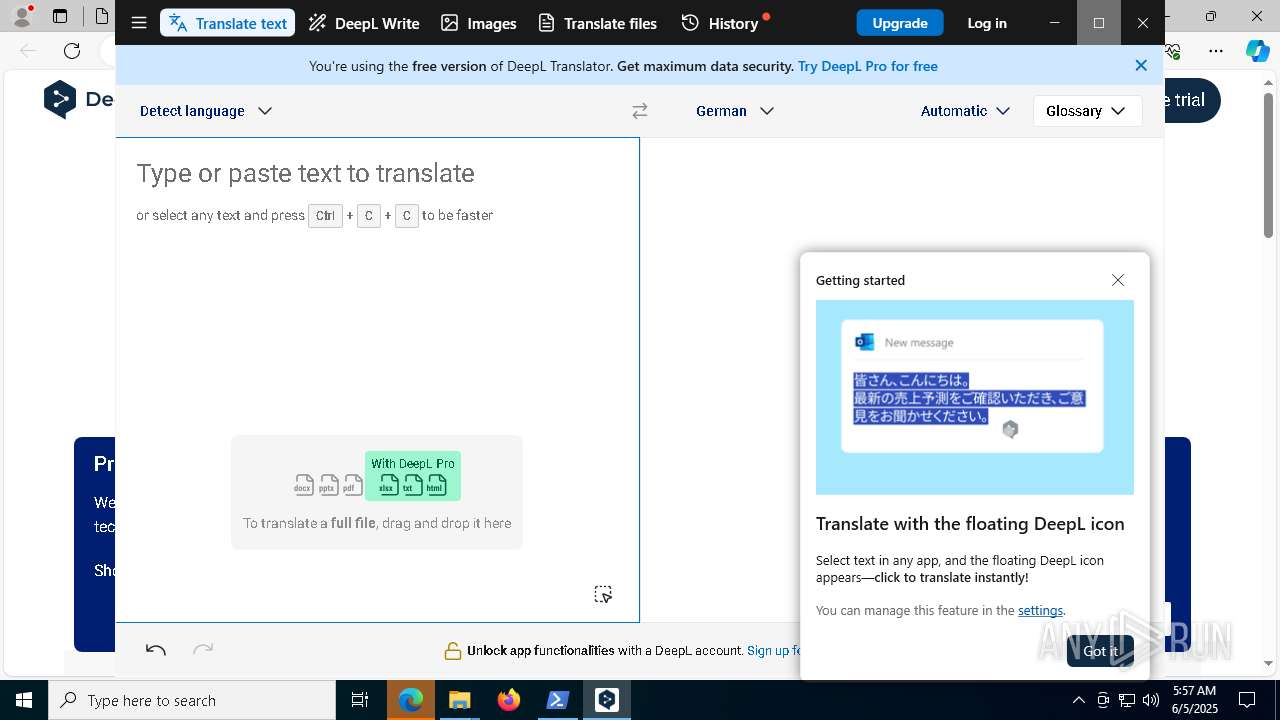
There is functionality for taking screenshot (YARA)
- DeepL.exe (PID: 1244)
- DeepL.exe (PID: 8020)
INFO
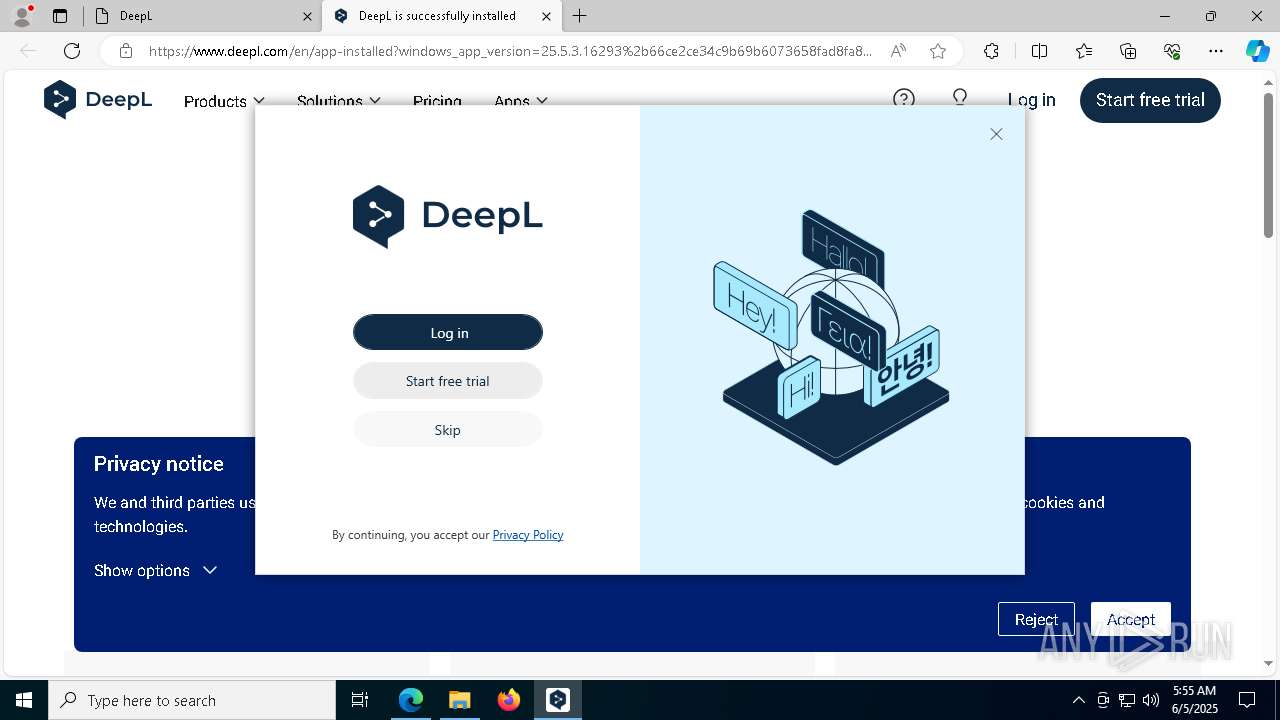
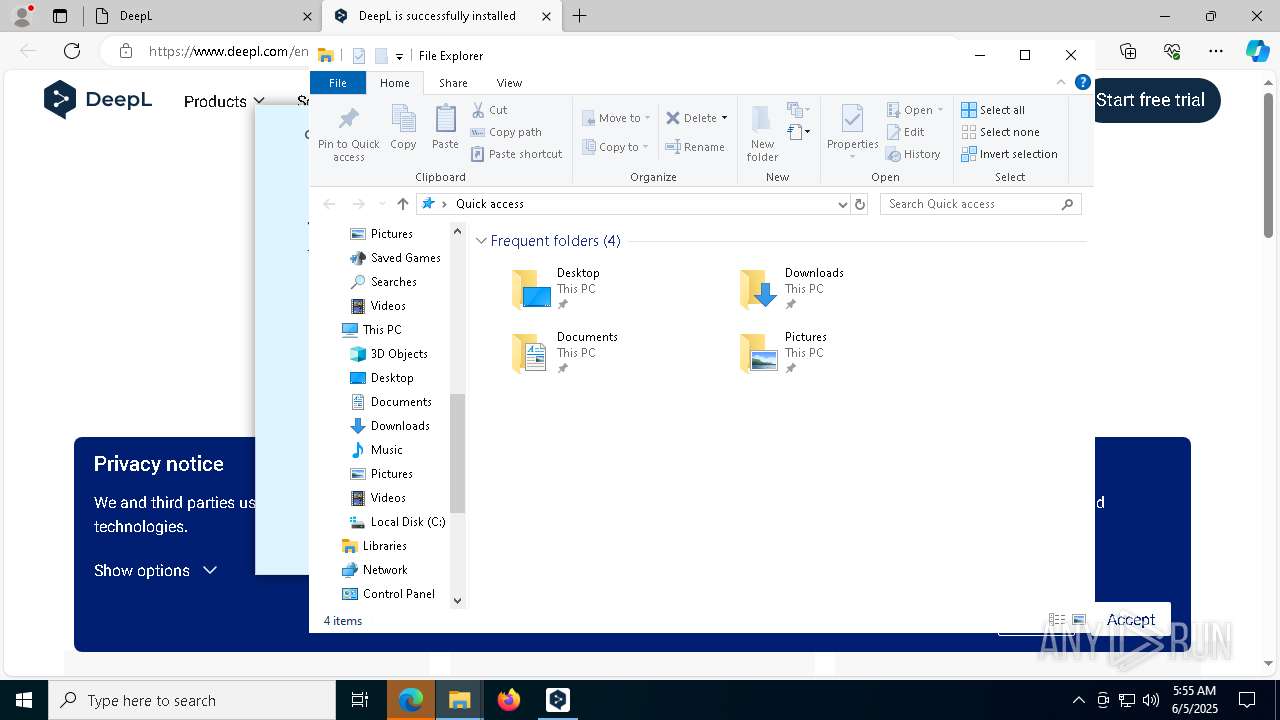
Application launched itself
- msedge.exe (PID: 4620)
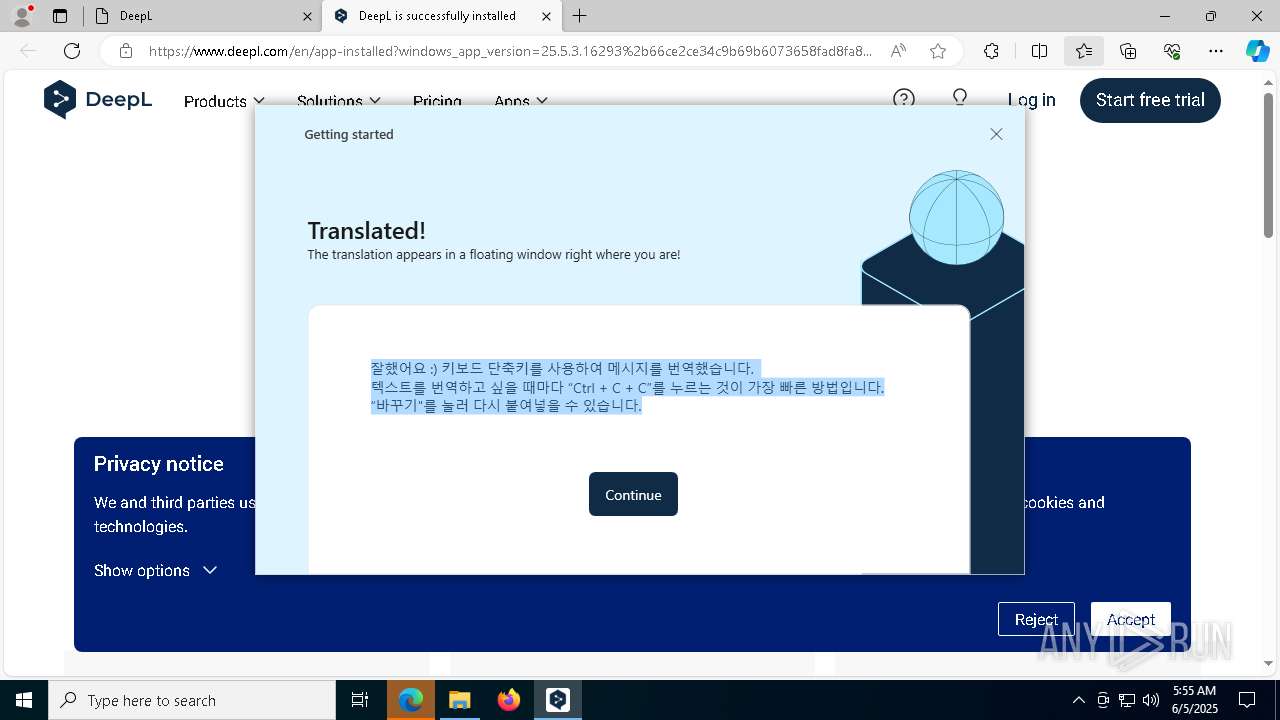
Checks supported languages
- identity_helper.exe (PID: 2140)
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
Reads Environment values
- identity_helper.exe (PID: 2140)
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
Reads the computer name
- identity_helper.exe (PID: 2140)
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
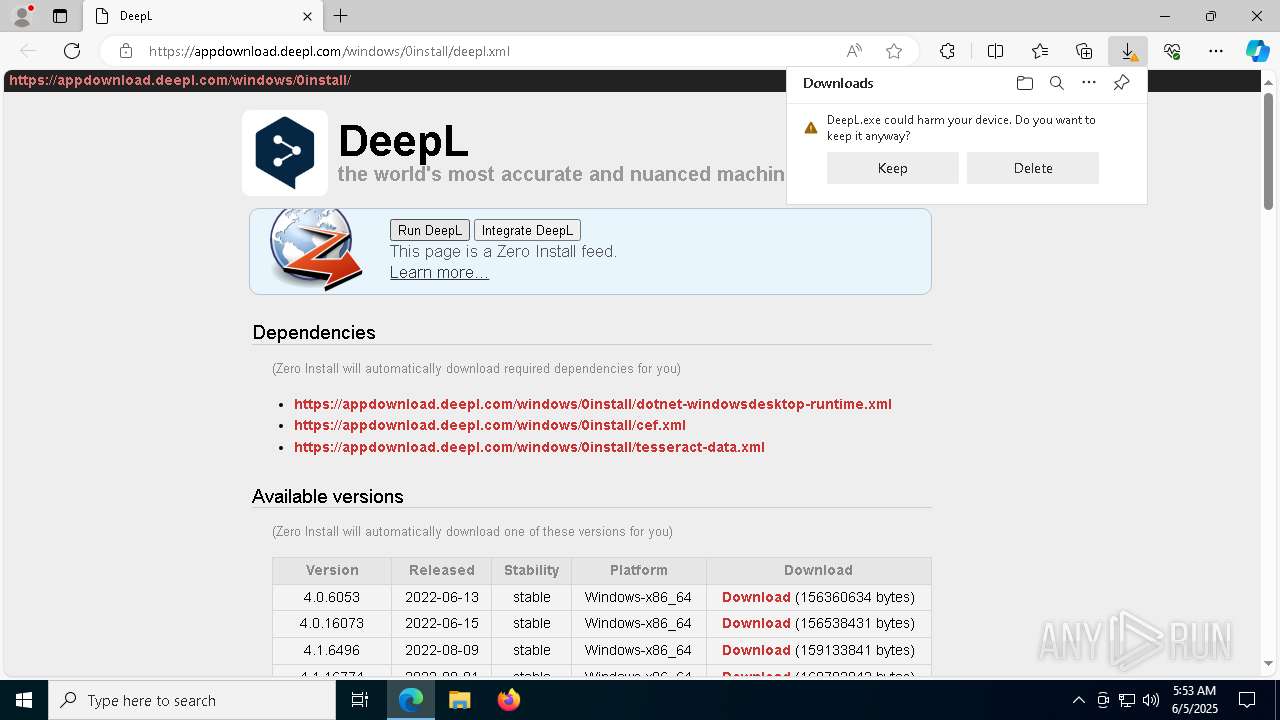
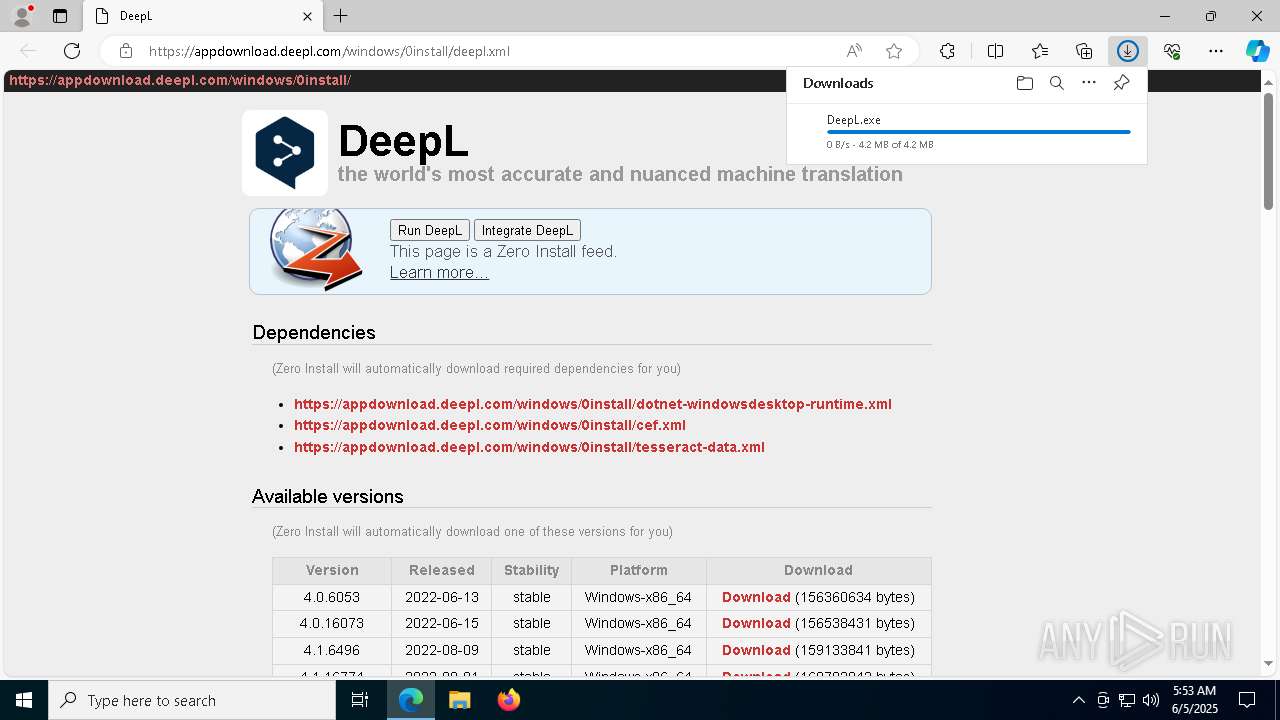
Executable content was dropped or overwritten
- msedge.exe (PID: 4620)
- msedge.exe (PID: 2516)
- msedge.exe (PID: 7908)
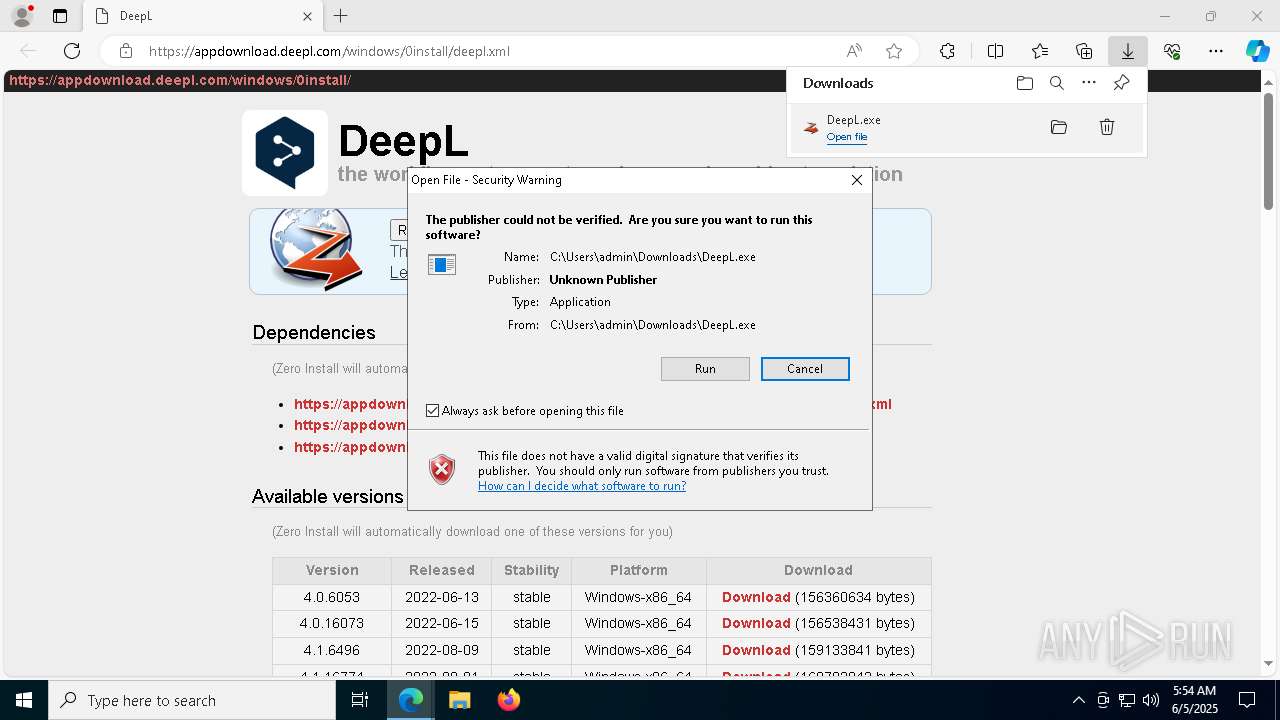
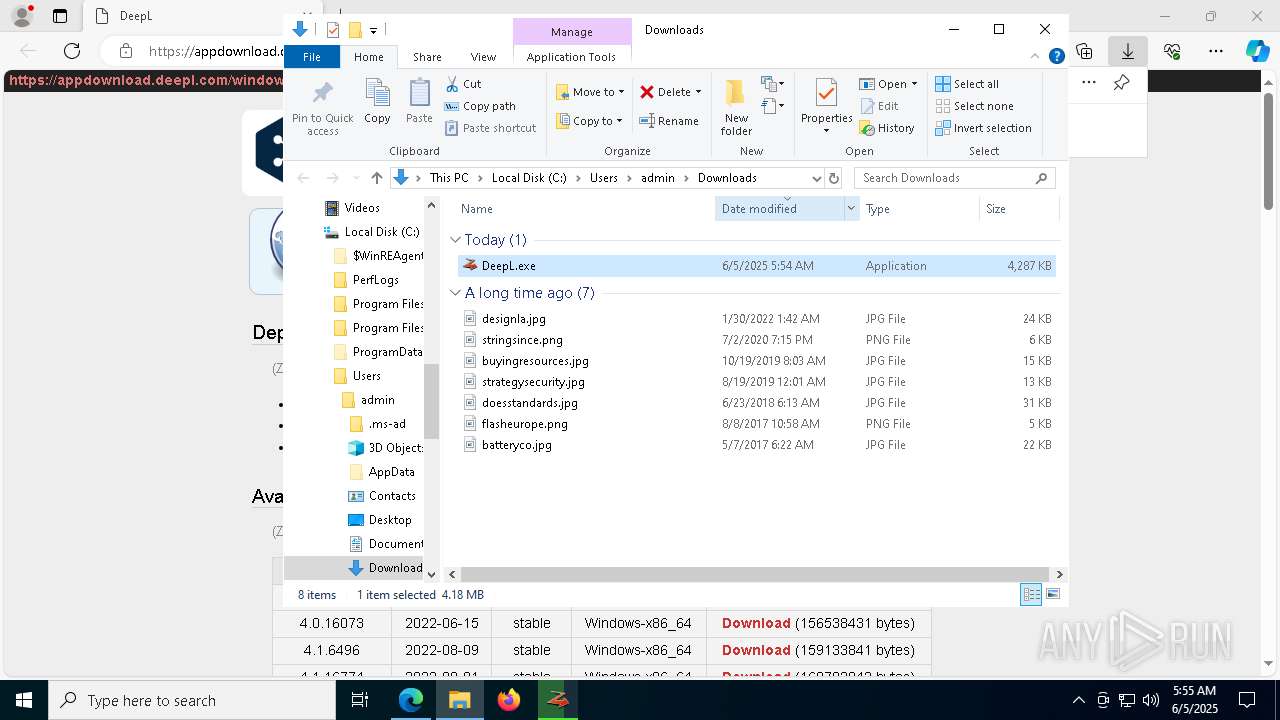
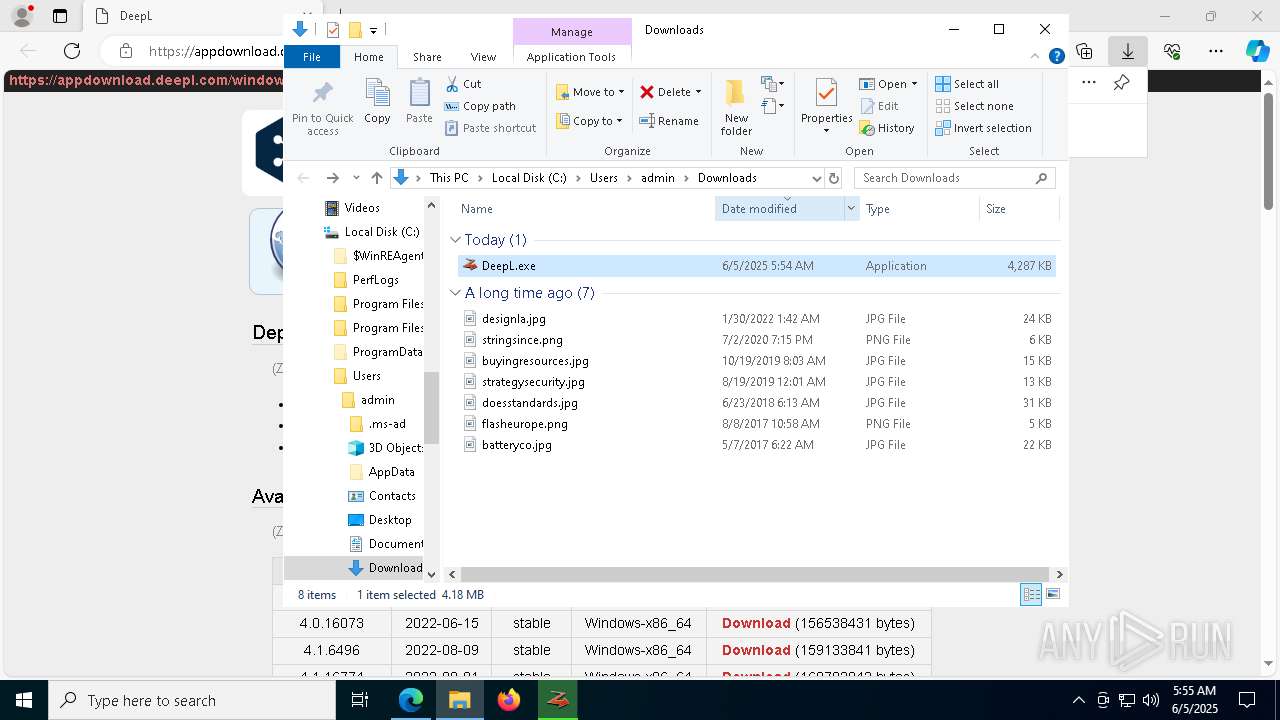
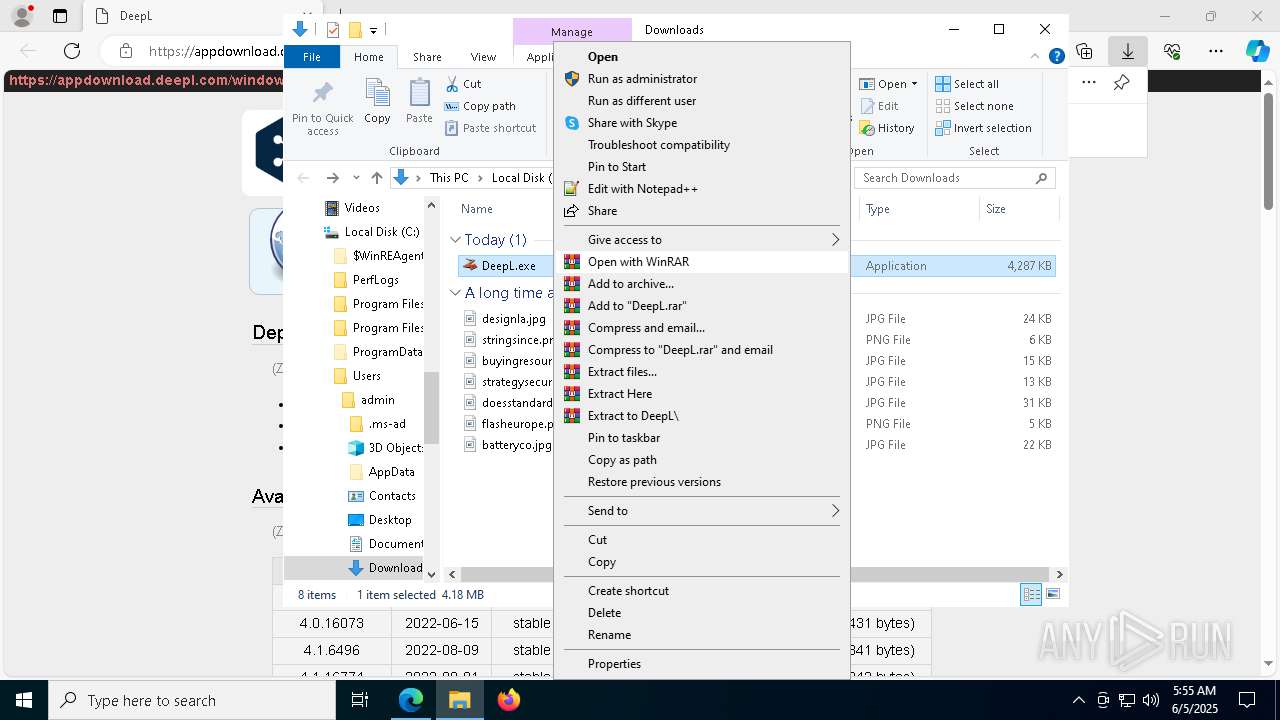
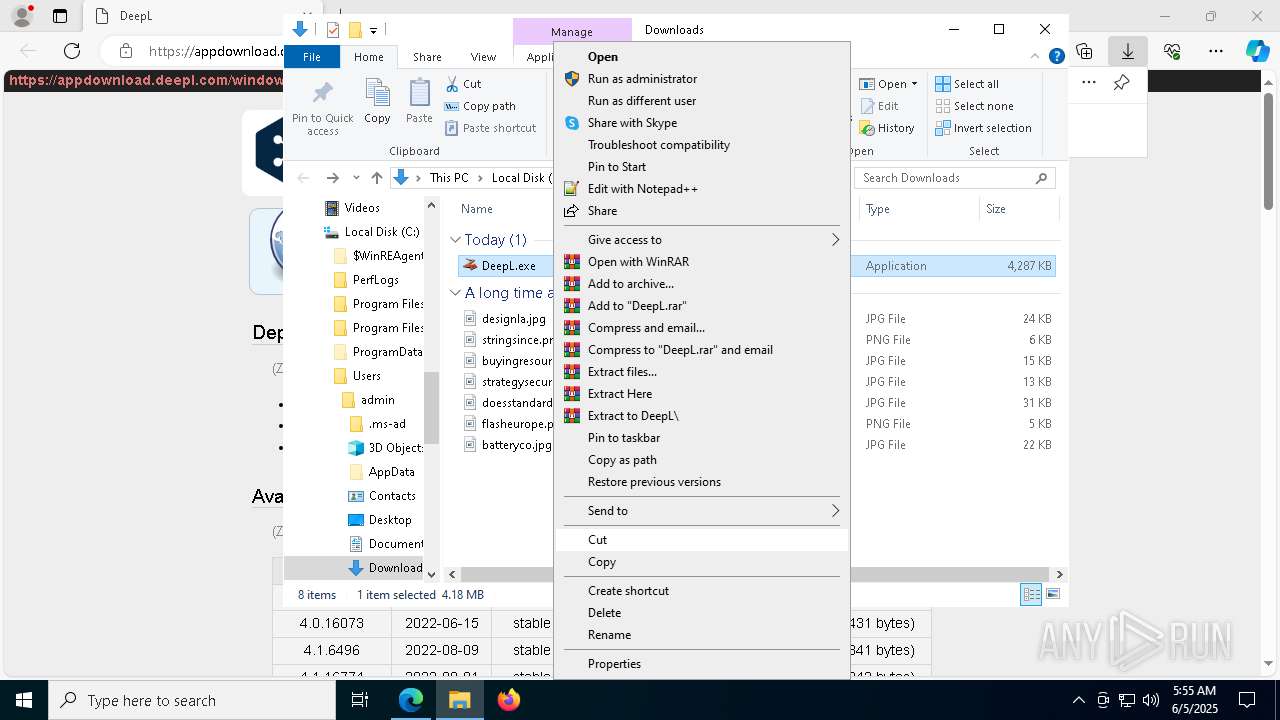
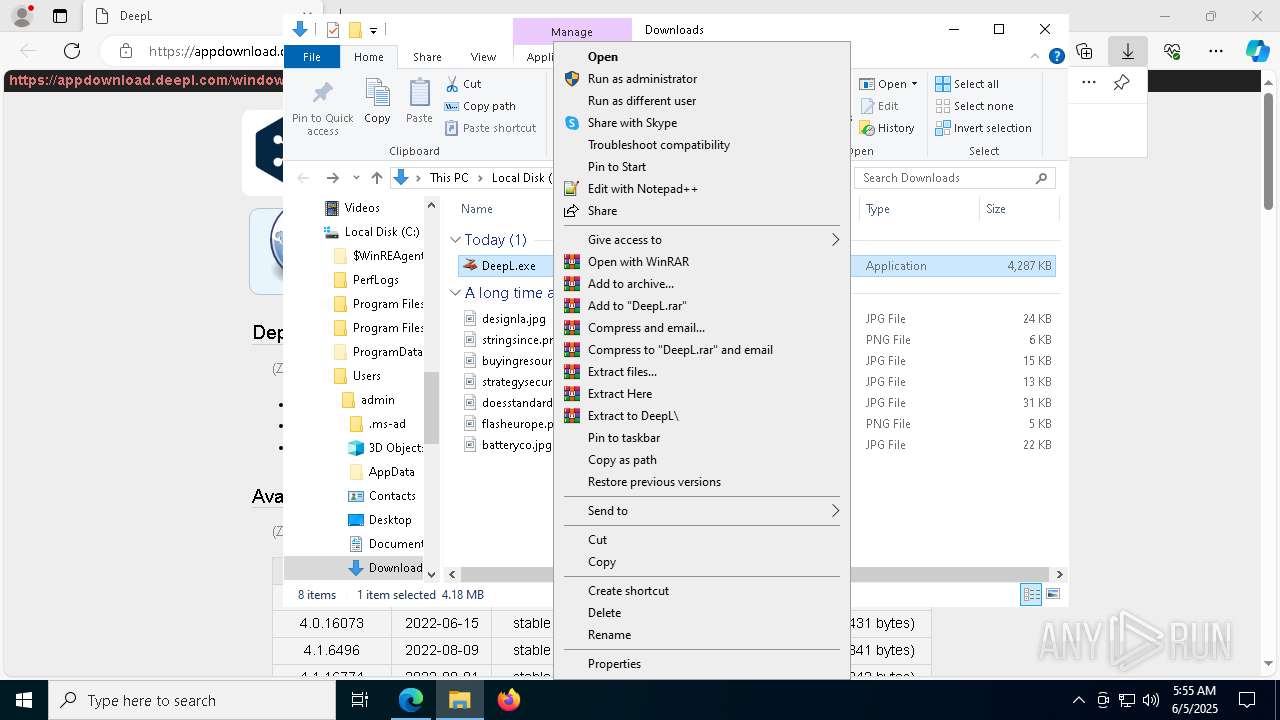
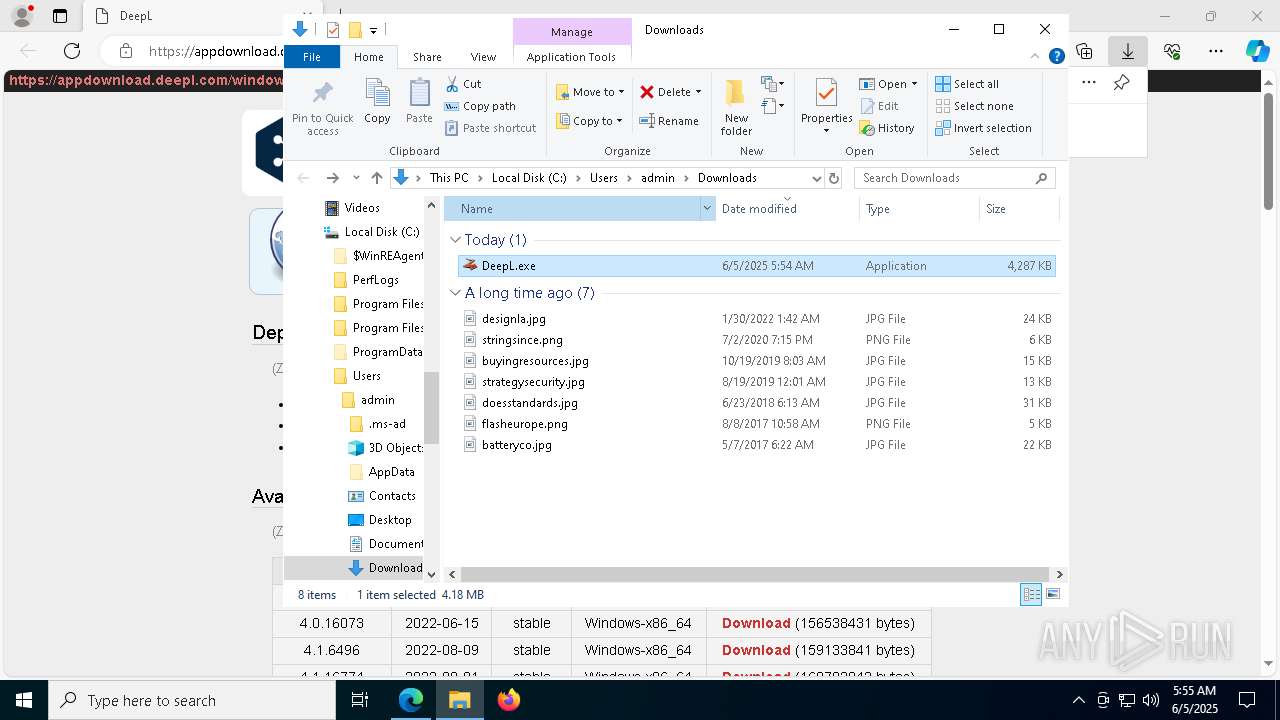
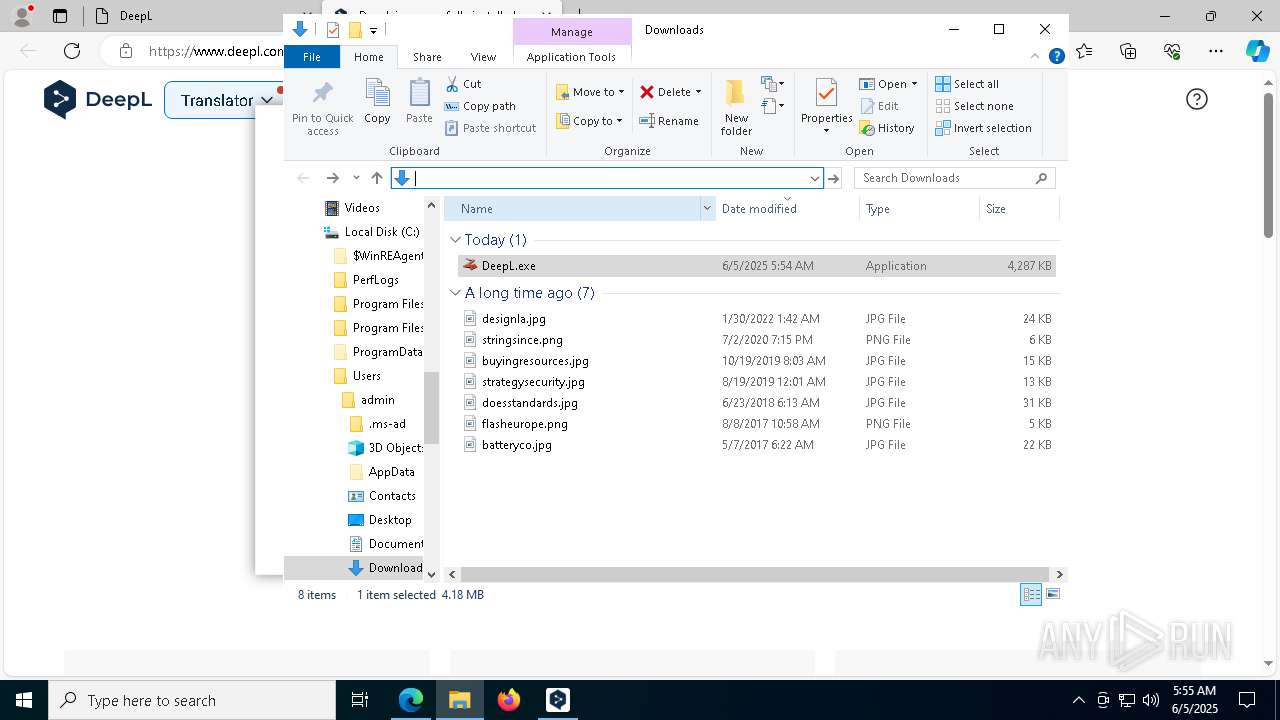
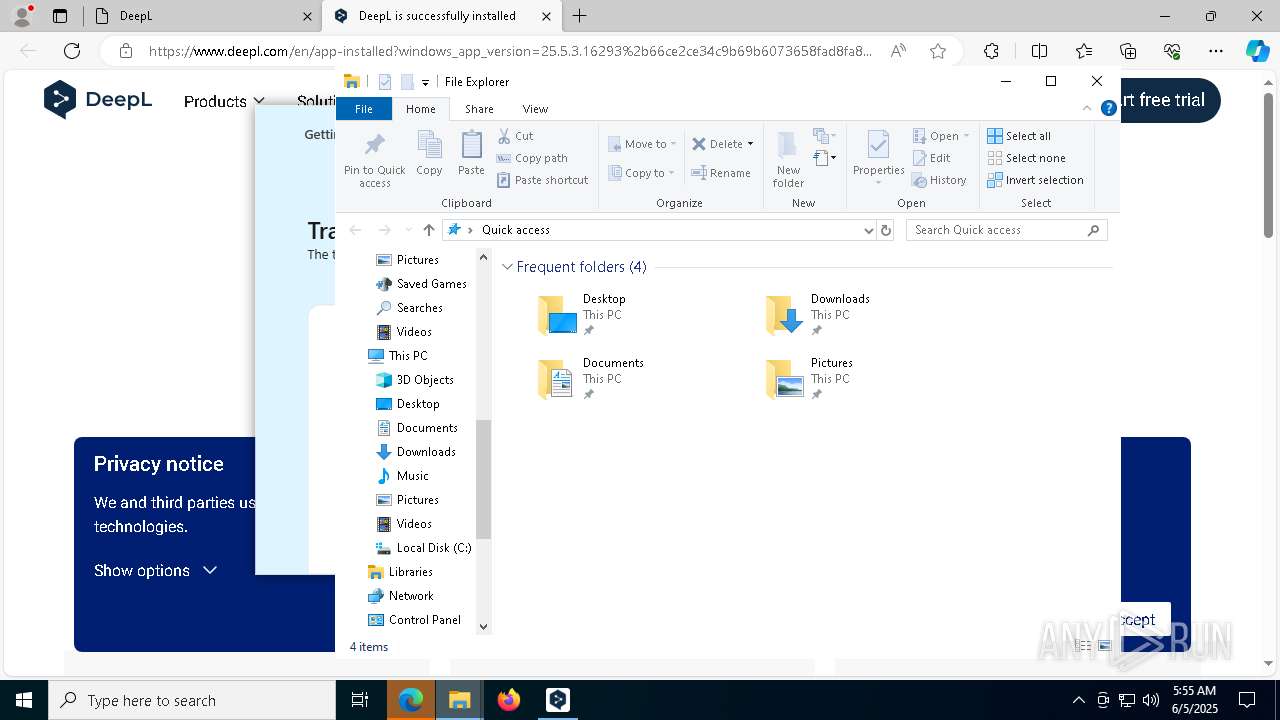
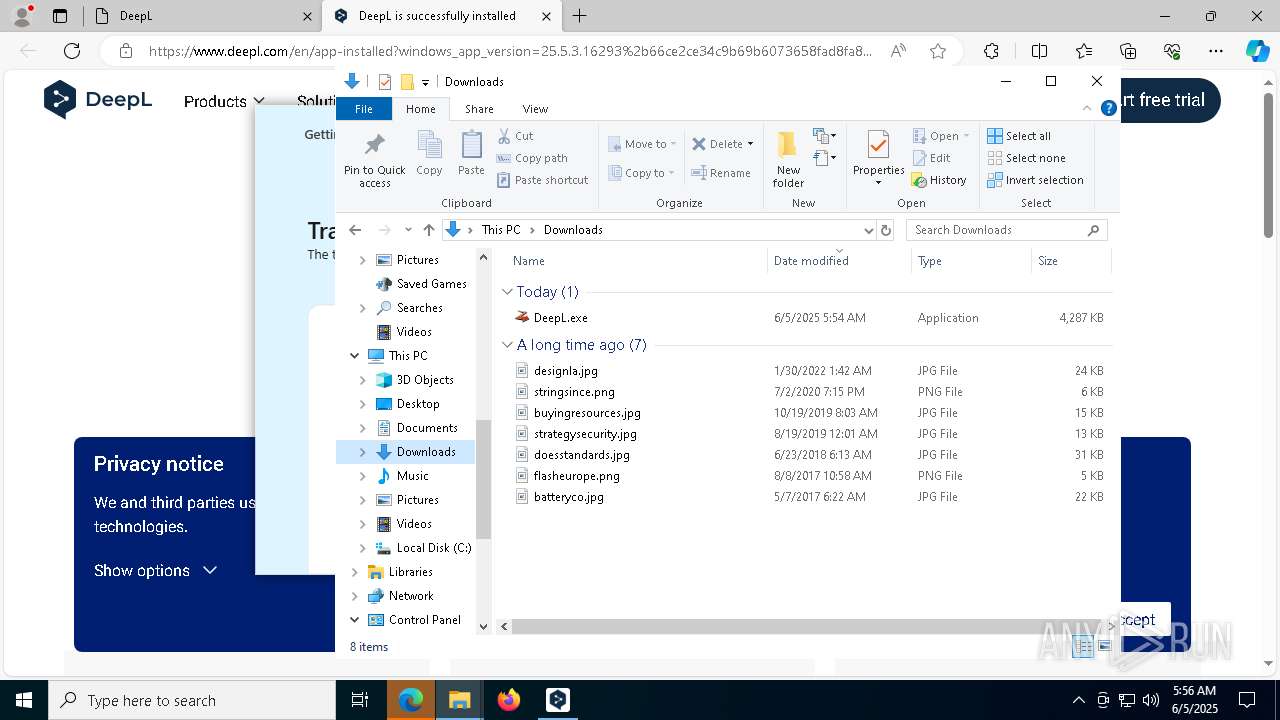
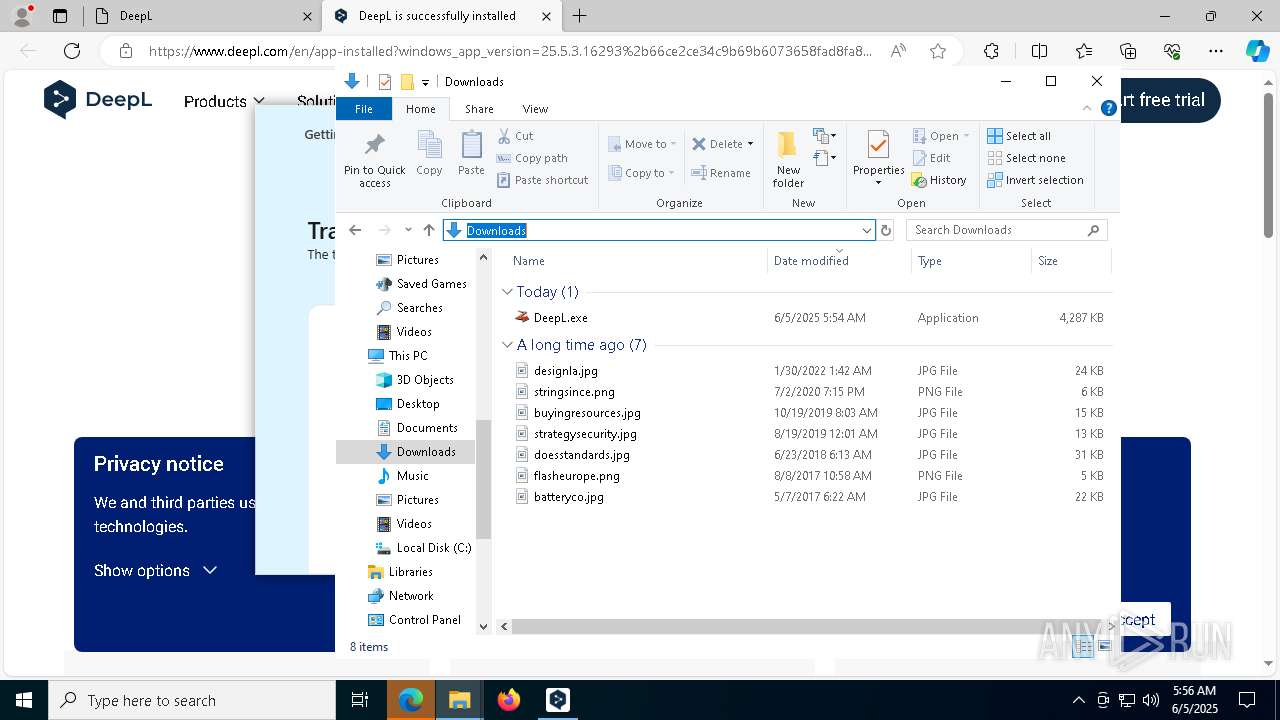
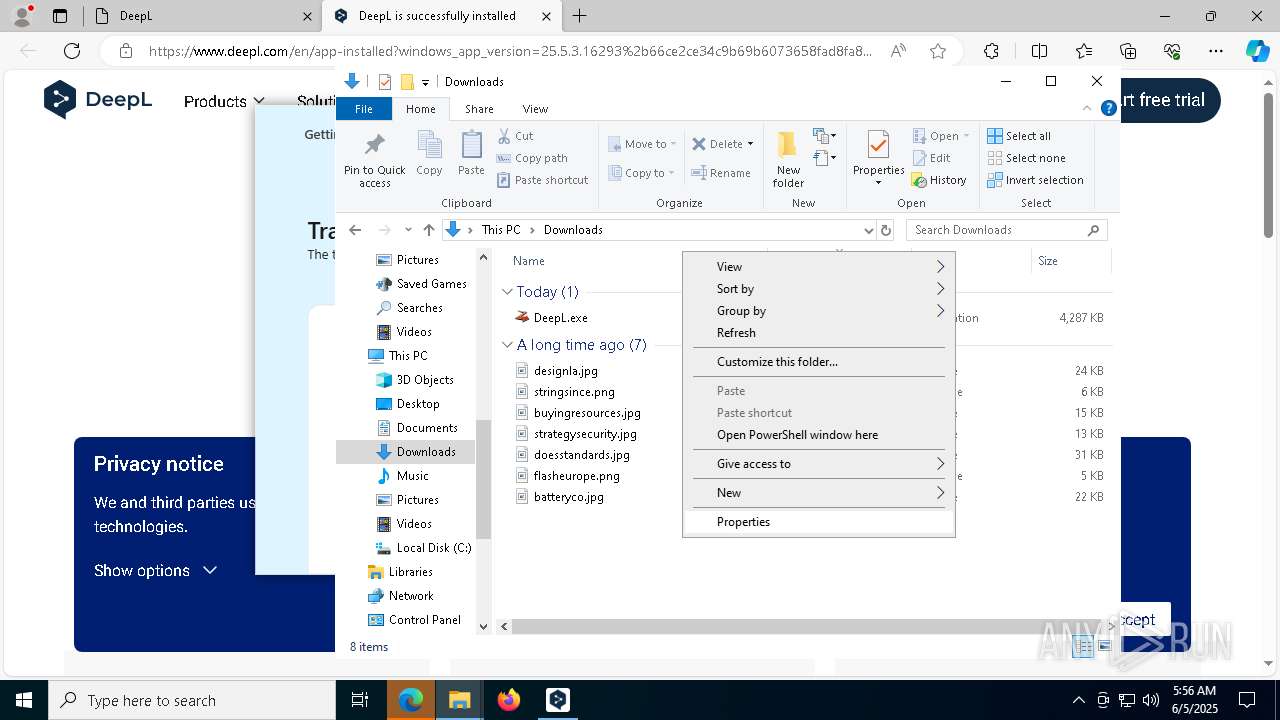
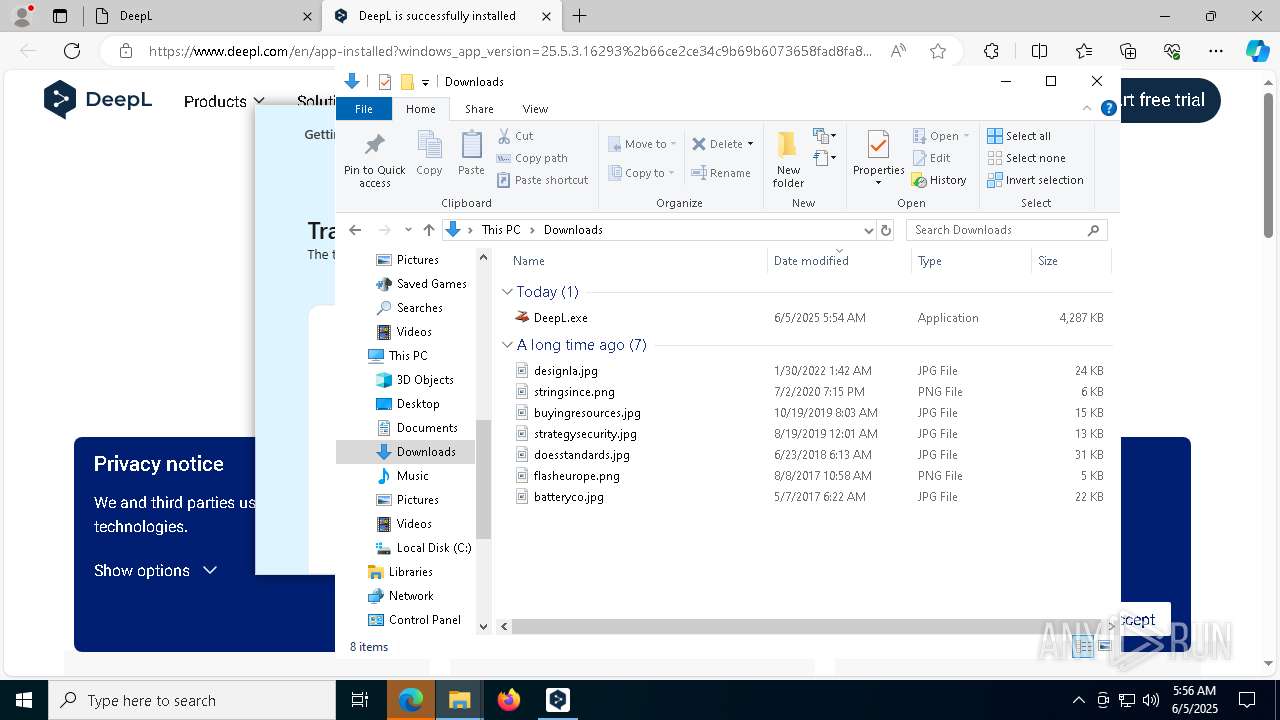
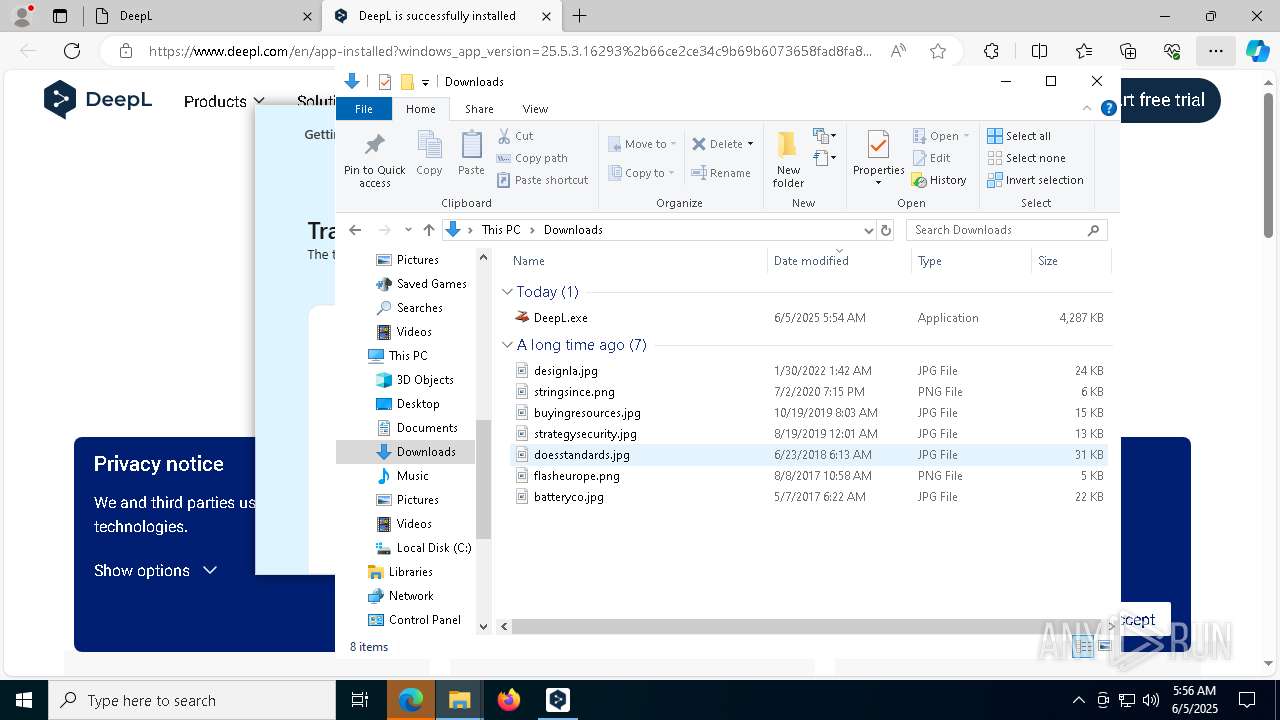
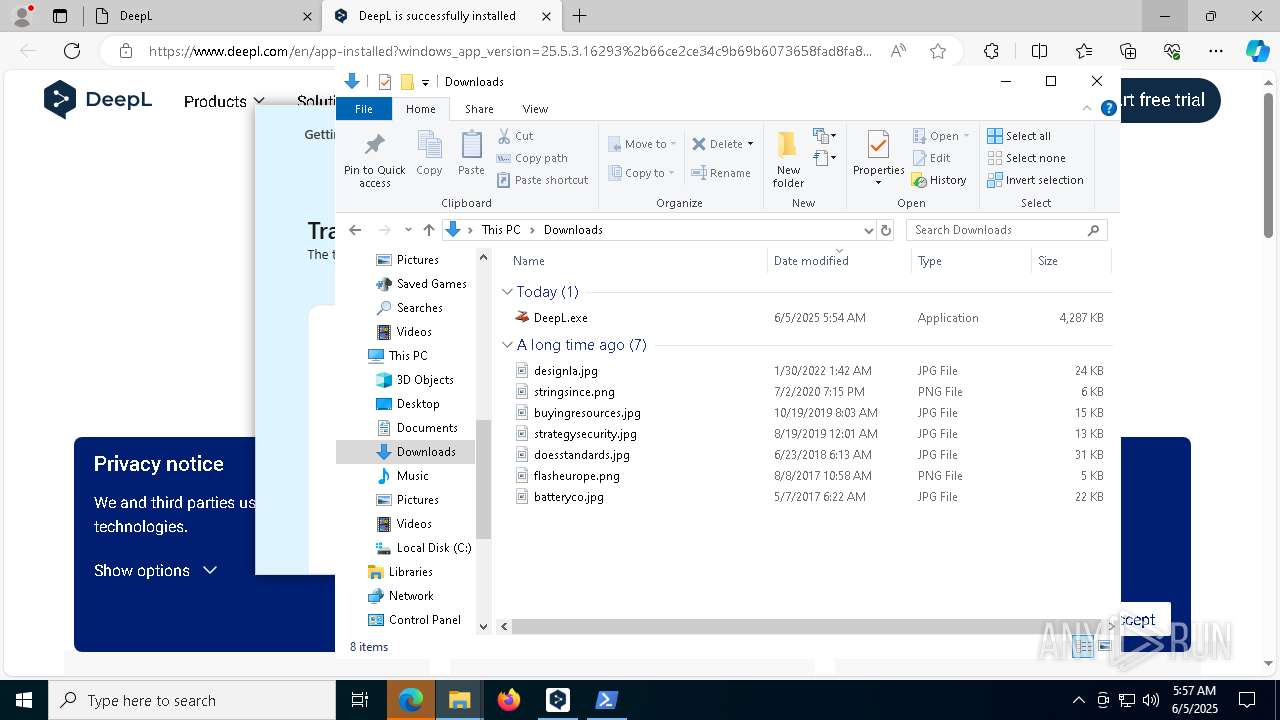
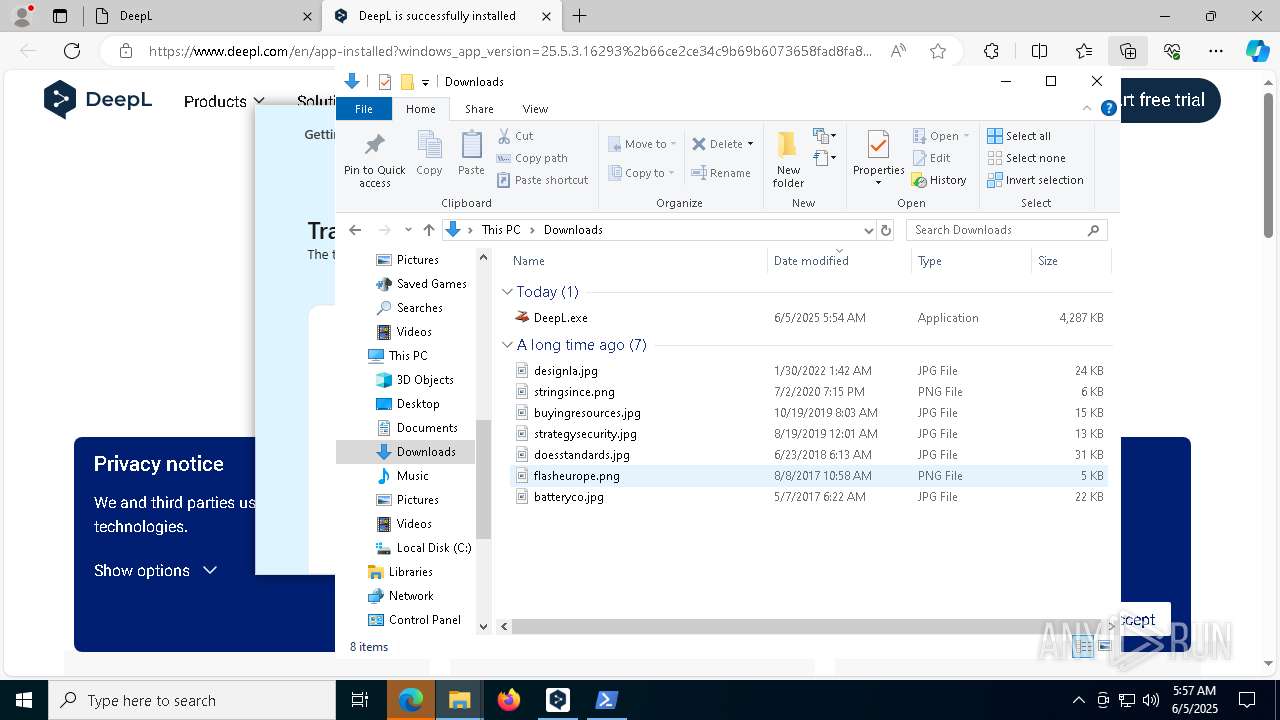
Launching a file from the Downloads directory
- msedge.exe (PID: 4620)
Disables trace logs
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
Checks proxy server information
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
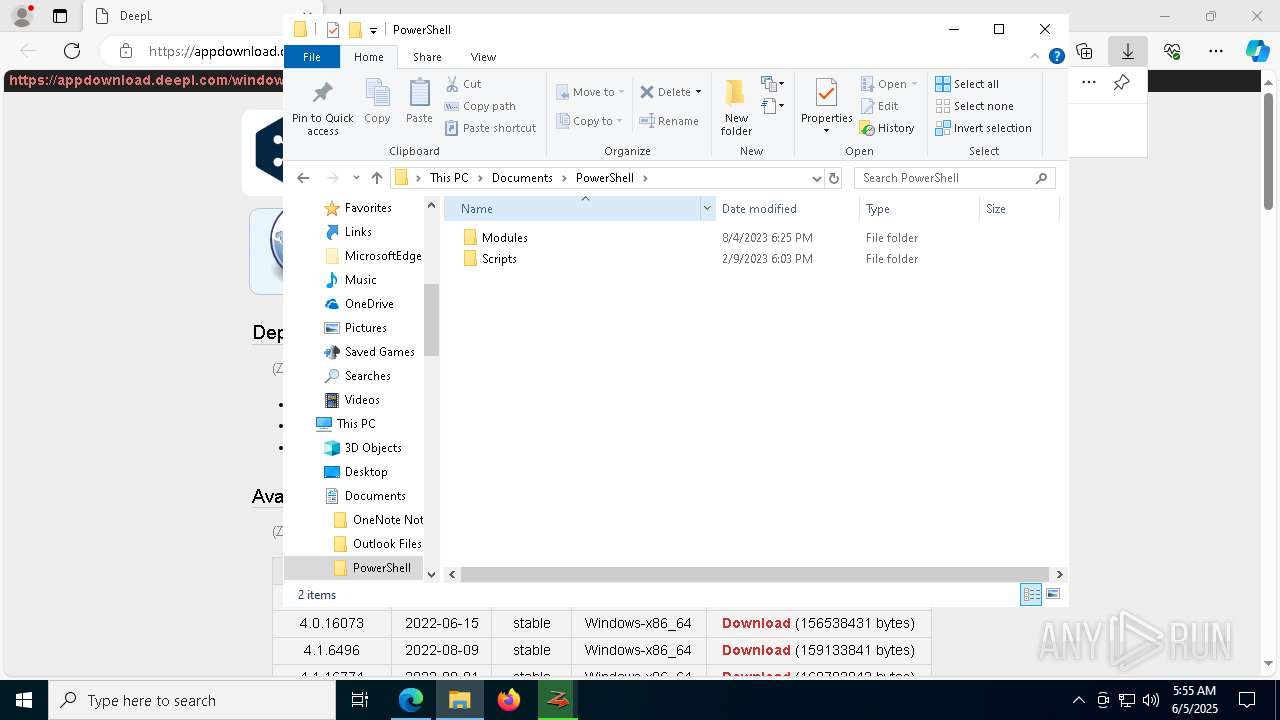
Creates files or folders in the user directory
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
ZEROINSTALL mutex has been found
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
Reads the machine GUID from the registry
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
Create files in a temporary directory
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
Reads the software policy settings
- DeepL.exe (PID: 1244)
- 0install-win.exe (PID: 3208)
- slui.exe (PID: 7456)
Creates files in the program directory
- 0install-win.exe (PID: 3208)
The sample compiled with english language support
- 0install-win.exe (PID: 3208)
- msedge.exe (PID: 7908)
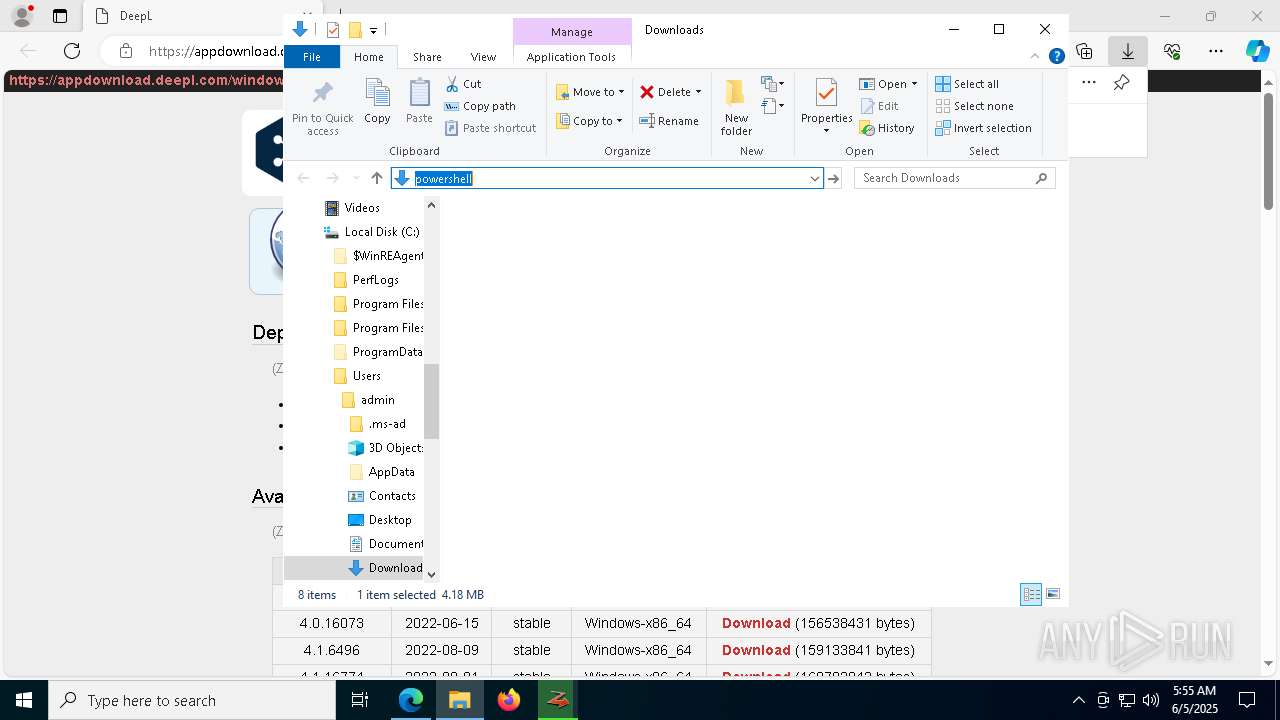
Manual execution by a user
- powershell.exe (PID: 6040)
- powershell.exe (PID: 6464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
219
Monitored processes
80
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc8a075fd8,0x7ffc8a075fe4,0x7ffc8a075ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_H67O372KOK36D5LXBF3S5XAZ2PMSQJOSNIIN6IH3TLUBOZGLEEFQ\0install.exe" list-apps --batch --xml https://appdownload.deepl.com/windows/0install/deepl.xml --machine | C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_H67O372KOK36D5LXBF3S5XAZ2PMSQJOSNIIN6IH3TLUBOZGLEEFQ\0install.exe | — | DeepL.exe | |||||||||||
User: admin Company: Bastian Eicher Integrity Level: MEDIUM Description: 0install Exit code: 0 Version: 2.26.6.0 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4876 --field-trial-handle=2344,i,16423604483655921507,240239933772561518,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5508 --field-trial-handle=2344,i,16423604483655921507,240239933772561518,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | "C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_BKTKEWCIR7C4BCMWF3GJC2FQGDNFGNL34Z4LRSEAN3K6LCCTSV7A\.\CefSharp.BrowserSubprocess.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --no-sandbox --user-agent="DeepL/25.5.3.16293 (Microsoft Windows NT 10.0.19045.0; x64)" --user-data-dir="C:\Users\admin\AppData\Local\DeepL_SE\cache" --cefsharpexitsub --field-trial-handle=4868,i,18090154221070075051,14430608985406899621,262144 --disable-features=EnableHangWatcher --variations-seed-version --enable-logging=handle --log-file=8820 --mojo-platform-channel-handle=8752 /prefetch:8 --host-process-id=8020 | C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_BKTKEWCIR7C4BCMWF3GJC2FQGDNFGNL34Z4LRSEAN3K6LCCTSV7A\CefSharp.BrowserSubprocess.exe | — | DeepL.exe | |||||||||||
User: admin Company: The CefSharp Authors Integrity Level: MEDIUM Description: CefSharp.BrowserSubprocess Exit code: 0 Version: 135.0.170.0 Modules
| |||||||||||||||
| 1240 | "C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_BKTKEWCIR7C4BCMWF3GJC2FQGDNFGNL34Z4LRSEAN3K6LCCTSV7A\.\CefSharp.BrowserSubprocess.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-sandbox --user-agent="DeepL/25.5.3.16293 (Microsoft Windows NT 10.0.19045.0; x64)" --user-data-dir="C:\Users\admin\AppData\Local\DeepL_SE\cache" --cefsharpexitsub --field-trial-handle=4868,i,18090154221070075051,14430608985406899621,262144 --disable-features=EnableHangWatcher --variations-seed-version --enable-logging=handle --log-file=9544 --mojo-platform-channel-handle=9556 /prefetch:8 --host-process-id=8020 | C:\Users\admin\AppData\Local\0install.net\implementations\sha256new_BKTKEWCIR7C4BCMWF3GJC2FQGDNFGNL34Z4LRSEAN3K6LCCTSV7A\CefSharp.BrowserSubprocess.exe | — | DeepL.exe | |||||||||||
User: admin Company: The CefSharp Authors Integrity Level: MEDIUM Description: CefSharp.BrowserSubprocess Exit code: 0 Version: 135.0.170.0 Modules
| |||||||||||||||
| 1244 | "C:\Users\admin\Downloads\DeepL.exe" | C:\Users\admin\Downloads\DeepL.exe | msedge.exe | ||||||||||||
User: admin Company: zero-install Integrity Level: MEDIUM Description: zero-install Exit code: 8020 Version: 2.26.5.0 Modules
| |||||||||||||||
| 1300 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6204 --field-trial-handle=2344,i,16423604483655921507,240239933772561518,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2108 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8120 --field-trial-handle=2344,i,16423604483655921507,240239933772561518,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
24 363
Read events
24 257
Write events
104
Delete events
2
Modification events
| (PID) Process: | (4620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4620) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7F71CE0463952F00 | |||
| (PID) Process: | (4620) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F01CD50463952F00 | |||
| (PID) Process: | (4620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1778A1C1-0A27-4F28-BCDA-35097EA6E583} | |||
| (PID) Process: | (4620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {10DE8922-8AB0-49A5-AF27-C4C272D18B7D} | |||
| (PID) Process: | (4620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6061804E-6836-4947-A85A-81E1363FAA4B} | |||
| (PID) Process: | (4620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
1 266
Suspicious files
1 183
Text files
216
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10a606.TMP | — | |
MD5:— | SHA256:— | |||
| 4620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10a615.TMP | — | |
MD5:— | SHA256:— | |||
| 4620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10a606.TMP | — | |
MD5:— | SHA256:— | |||
| 4620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10a635.TMP | — | |
MD5:— | SHA256:— | |||
| 4620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10a654.TMP | — | |
MD5:— | SHA256:— | |||
| 4620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
94
DNS requests
113
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5452 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5452 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1284 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1749576397&P2=404&P3=2&P4=gZ9U2D4fPok8PtG9acH0wdNqpEfIcRx73mi%2b%2fR7JjZuteNs1HSm4j2d4%2fxN8xC5Ke0VNwjNyrqCiFwFzGV4ULw%3d%3d | unknown | — | — | whitelisted |
1284 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1749576397&P2=404&P3=2&P4=gZ9U2D4fPok8PtG9acH0wdNqpEfIcRx73mi%2b%2fR7JjZuteNs1HSm4j2d4%2fxN8xC5Ke0VNwjNyrqCiFwFzGV4ULw%3d%3d | unknown | — | — | whitelisted |
1284 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1749576397&P2=404&P3=2&P4=gZ9U2D4fPok8PtG9acH0wdNqpEfIcRx73mi%2b%2fR7JjZuteNs1HSm4j2d4%2fxN8xC5Ke0VNwjNyrqCiFwFzGV4ULw%3d%3d | unknown | — | — | whitelisted |
1284 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1749576397&P2=404&P3=2&P4=gZ9U2D4fPok8PtG9acH0wdNqpEfIcRx73mi%2b%2fR7JjZuteNs1HSm4j2d4%2fxN8xC5Ke0VNwjNyrqCiFwFzGV4ULw%3d%3d | unknown | — | — | whitelisted |
1284 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1749576397&P2=404&P3=2&P4=gZ9U2D4fPok8PtG9acH0wdNqpEfIcRx73mi%2b%2fR7JjZuteNs1HSm4j2d4%2fxN8xC5Ke0VNwjNyrqCiFwFzGV4ULw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5796 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2560 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4620 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2516 | msedge.exe | 172.64.151.134:443 | appdownload.deepl.com | — | — | whitelisted |
2516 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
appdownload.deepl.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7948 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7948 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7948 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7948 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7948 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7948 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7948 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7948 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7948 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7948 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |