| File name: | ProcessHackerPortable_2.39_English.paf.exe |
| Full analysis: | https://app.any.run/tasks/fdaf43c1-6839-4da9-8442-87a91af63c57 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 02:47:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | B6AB864F014D0C4A35B7641D1B586F6D |
| SHA1: | 1EEE4113978DEB0CF77EBEC21BB8FECCBBFD592D |
| SHA256: | B0668B6596578D5D918C8D29083423C8025BD49328130383841139DD575868C6 |
| SSDEEP: | 49152:a96+cwM33aKYwbHFg4kYG10DV5YnpuCQSPe/EXT+2:3nXKq4YGiw4f/8 |
MALICIOUS
Loads dropped or rewritten executable
- ProcessHackerPortable_2.39_English.paf.exe (PID: 696)
- SearchProtocolHost.exe (PID: 2932)
- ProcessHacker.exe (PID: 3664)
- ProcessHackerPortable.exe (PID: 3368)
Application was dropped or rewritten from another process
- ProcessHackerPortable.exe (PID: 3368)
- ProcessHacker.exe (PID: 3664)
Drops executable file immediately after starts
- ProcessHackerPortable.exe (PID: 3368)
- ProcessHackerPortable_2.39_English.paf.exe (PID: 696)
SUSPICIOUS
Reads the computer name
- ProcessHackerPortable_2.39_English.paf.exe (PID: 696)
- ProcessHackerPortable.exe (PID: 3368)
- ProcessHacker.exe (PID: 3664)
Checks supported languages
- ProcessHackerPortable_2.39_English.paf.exe (PID: 696)
- ProcessHackerPortable.exe (PID: 3368)
- ProcessHacker.exe (PID: 3664)
Reads default file associations for system extensions
- SearchProtocolHost.exe (PID: 2932)
Drops a file with a compile date too recent
- ProcessHackerPortable_2.39_English.paf.exe (PID: 696)
- ProcessHackerPortable.exe (PID: 3368)
Executable content was dropped or overwritten
- ProcessHackerPortable.exe (PID: 3368)
- ProcessHackerPortable_2.39_English.paf.exe (PID: 696)
Reads Environment values
- ProcessHacker.exe (PID: 3664)
INFO
Reads settings of System Certificates
- ProcessHacker.exe (PID: 3664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 2.39.0.0 |
|---|---|
| ProductName: | Process Hacker Portable |
| PortableAppscomInstallerVersion: | 3.2.0.0 |
| PortableAppscomFormatVersion: | 3.2 |
| PortableAppscomAppID: | ProcessHackerPortable |
| OriginalFileName: | ProcessHackerPortable_2.39_English.paf.exe |
| LegalTrademarks: | PortableApps.com is a registered trademark of Rare Ideas, LLC. |
| LegalCopyright: | 2007-2016 PortableApps.com, PortableApps.com Installer 3.2.0.0 |
| InternalName: | Process Hacker Portable |
| FileVersion: | 2.39.0.0 |
| FileDescription: | Process Hacker Portable |
| CompanyName: | PortableApps.com |
| Comments: | For additional details, visit PortableApps.com |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 2.39.0.0 |
| FileVersionNumber: | 2.39.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x33b6 |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 141824 |
| CodeSize: | 25088 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2015:12:27 07:26:01+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Dec-2015 06:26:01 |
| Detected languages: |
|
| Comments: | For additional details, visit PortableApps.com |
| CompanyName: | PortableApps.com |
| FileDescription: | Process Hacker Portable |
| FileVersion: | 2.39.0.0 |
| InternalName: | Process Hacker Portable |
| LegalCopyright: | 2007-2016 PortableApps.com, PortableApps.com Installer 3.2.0.0 |
| LegalTrademarks: | PortableApps.com is a registered trademark of Rare Ideas, LLC. |
| OriginalFilename: | ProcessHackerPortable_2.39_English.paf.exe |
| PortableApps.comAppID: | ProcessHackerPortable |
| PortableApps.comFormatVersion: | 3.2 |
| PortableApps.comInstallerVersion: | 3.2.0.0 |
| ProductName: | Process Hacker Portable |
| ProductVersion: | 2.39.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Dec-2015 06:26:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000615E | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45574 |
.rdata | 0x00008000 | 0x00001370 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.10215 |
.data | 0x0000A000 | 0x00020358 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.09485 |
.ndata | 0x0002B000 | 0x0002B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00056000 | 0x000199B0 | 0x00019A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.53407 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28691 | 1250 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.1717 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.50995 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.70014 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 5.6488 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 6.01856 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 5.66656 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 5.83657 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.80233 | 118 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68372 | 512 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
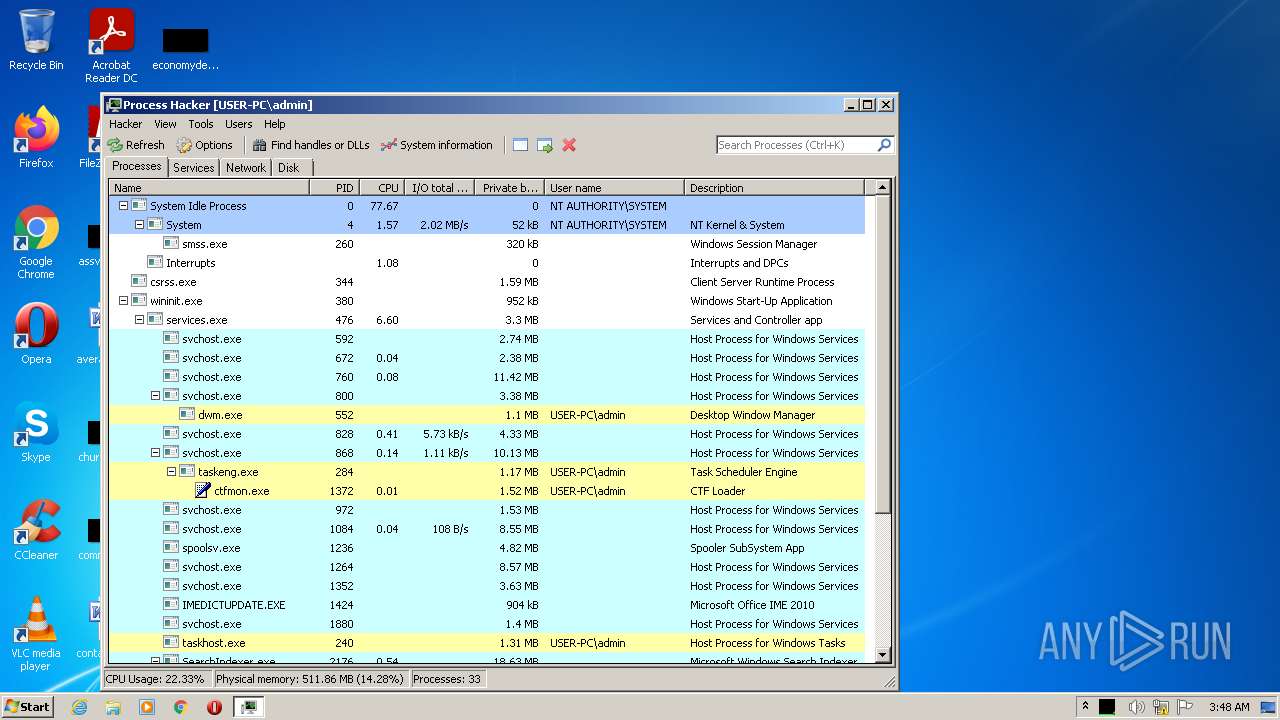
Total processes
38
Monitored processes
4
Malicious processes
4
Suspicious processes
0
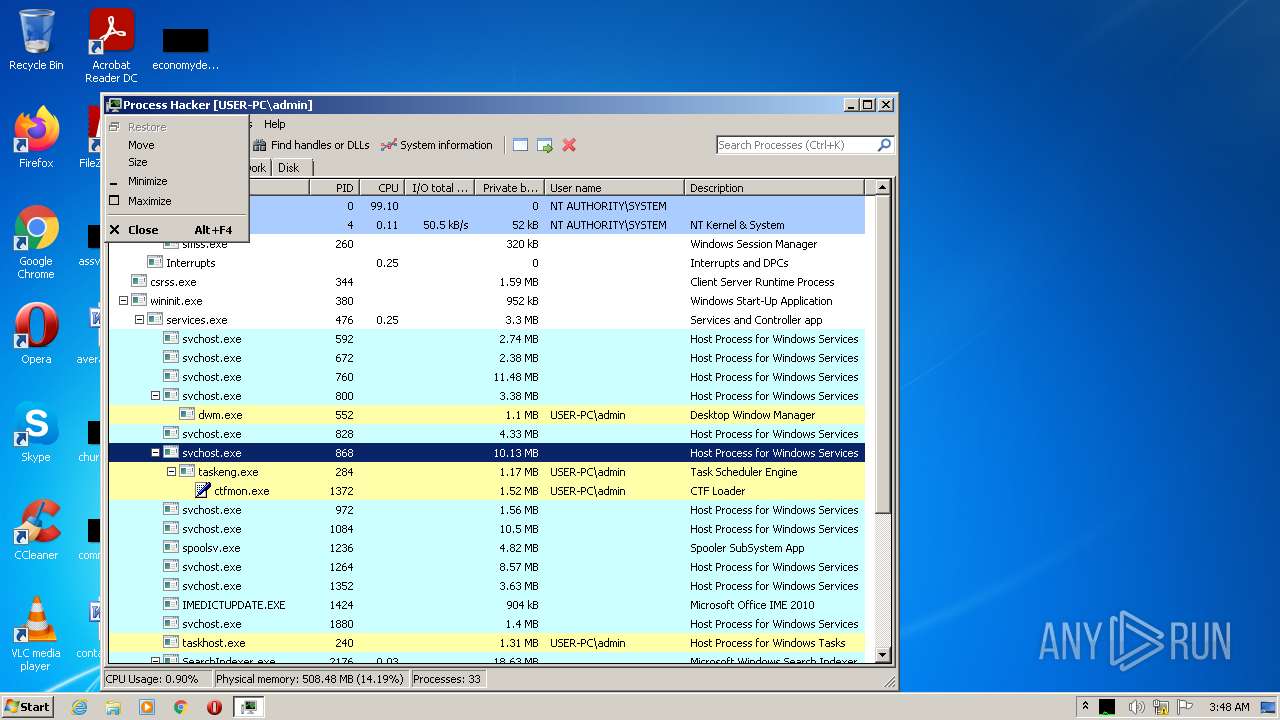
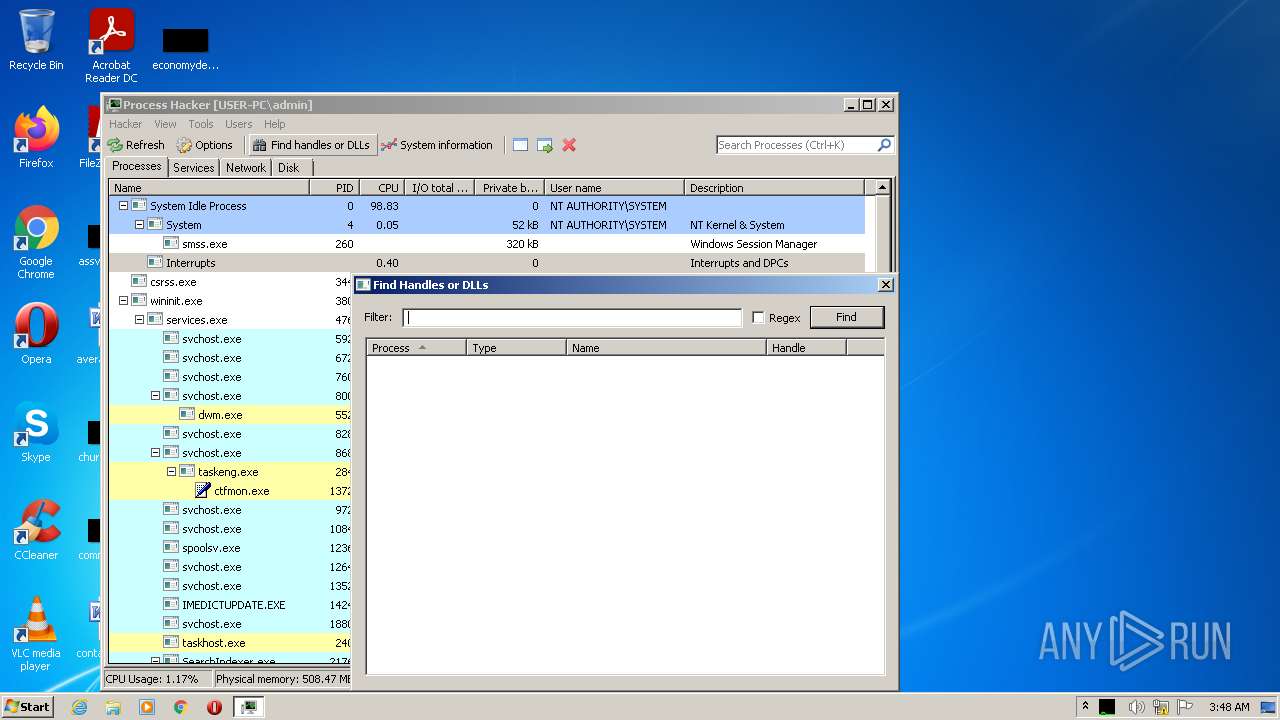
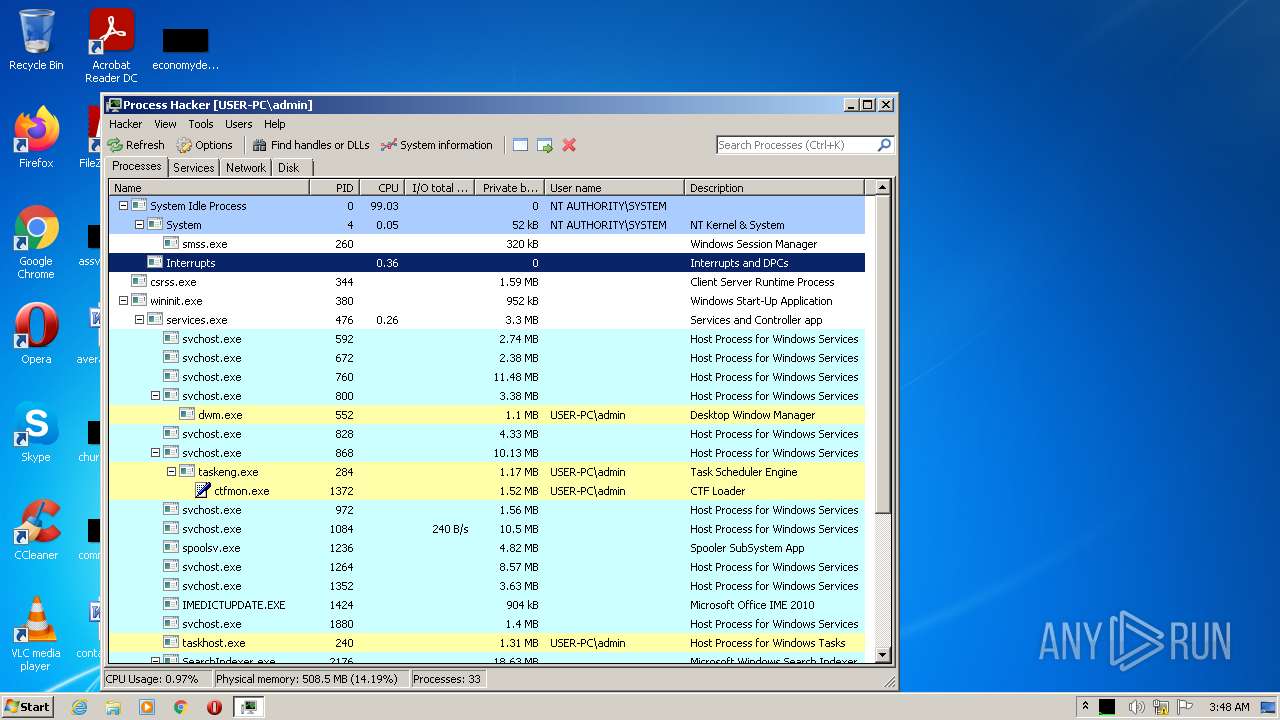
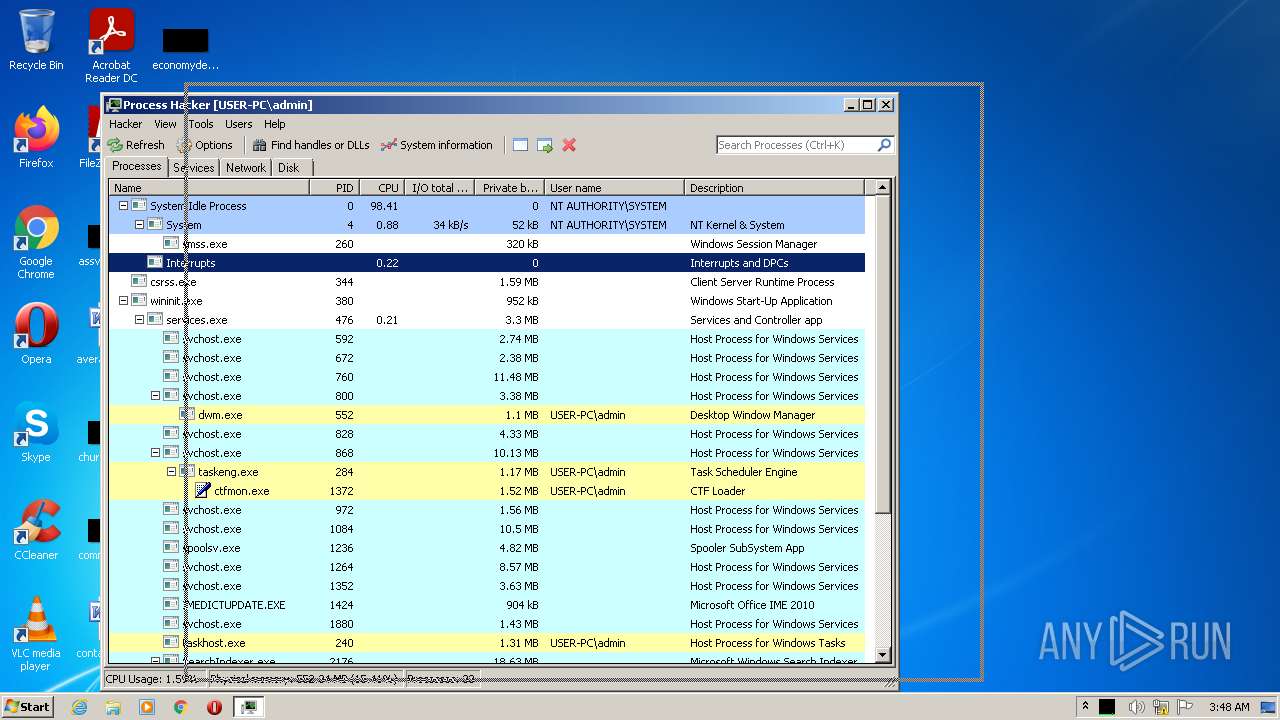
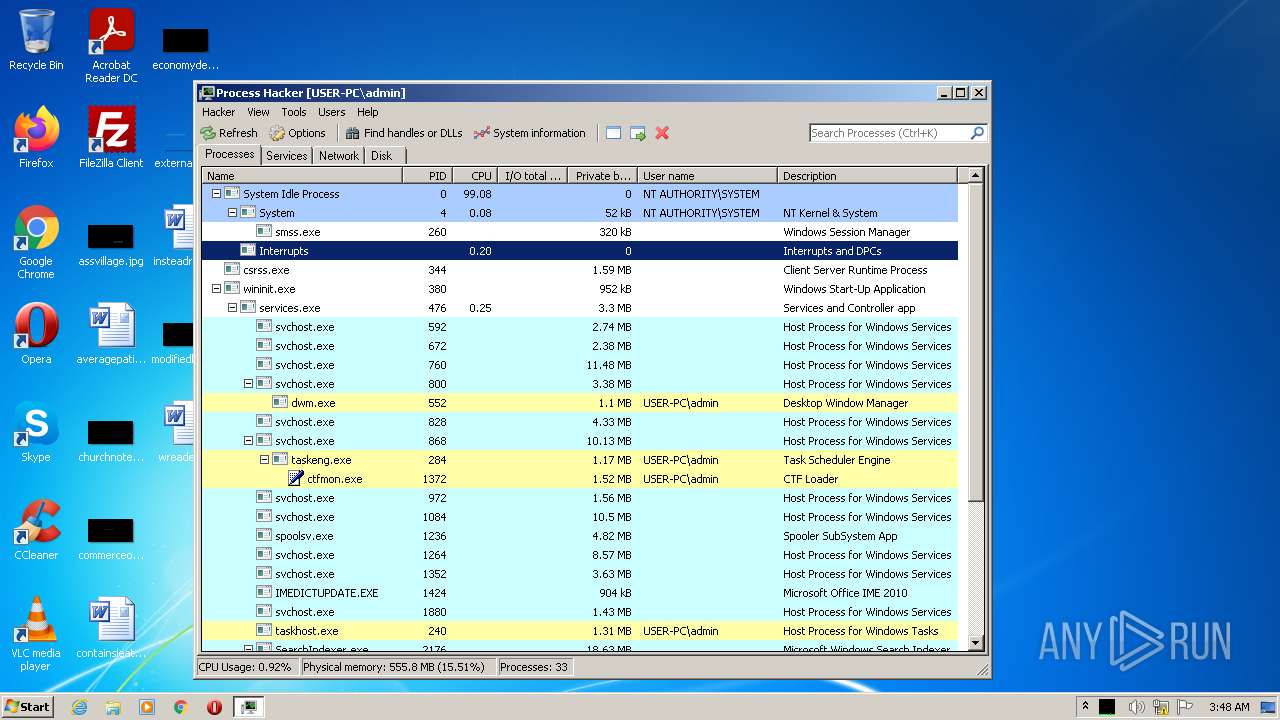
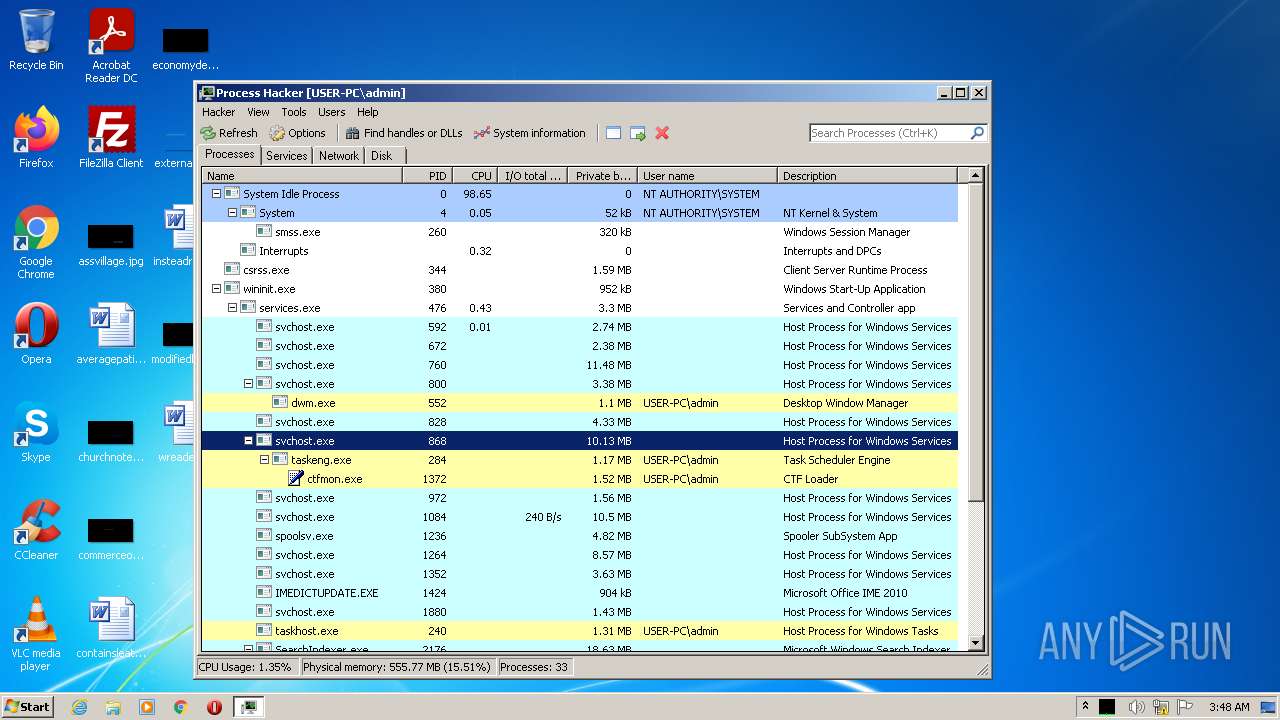
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 696 | "C:\Users\admin\AppData\Local\Temp\ProcessHackerPortable_2.39_English.paf.exe" | C:\Users\admin\AppData\Local\Temp\ProcessHackerPortable_2.39_English.paf.exe | Explorer.EXE | ||||||||||||
User: admin Company: PortableApps.com Integrity Level: MEDIUM Description: Process Hacker Portable Exit code: 0 Version: 2.39.0.0 Modules
| |||||||||||||||
| 2932 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
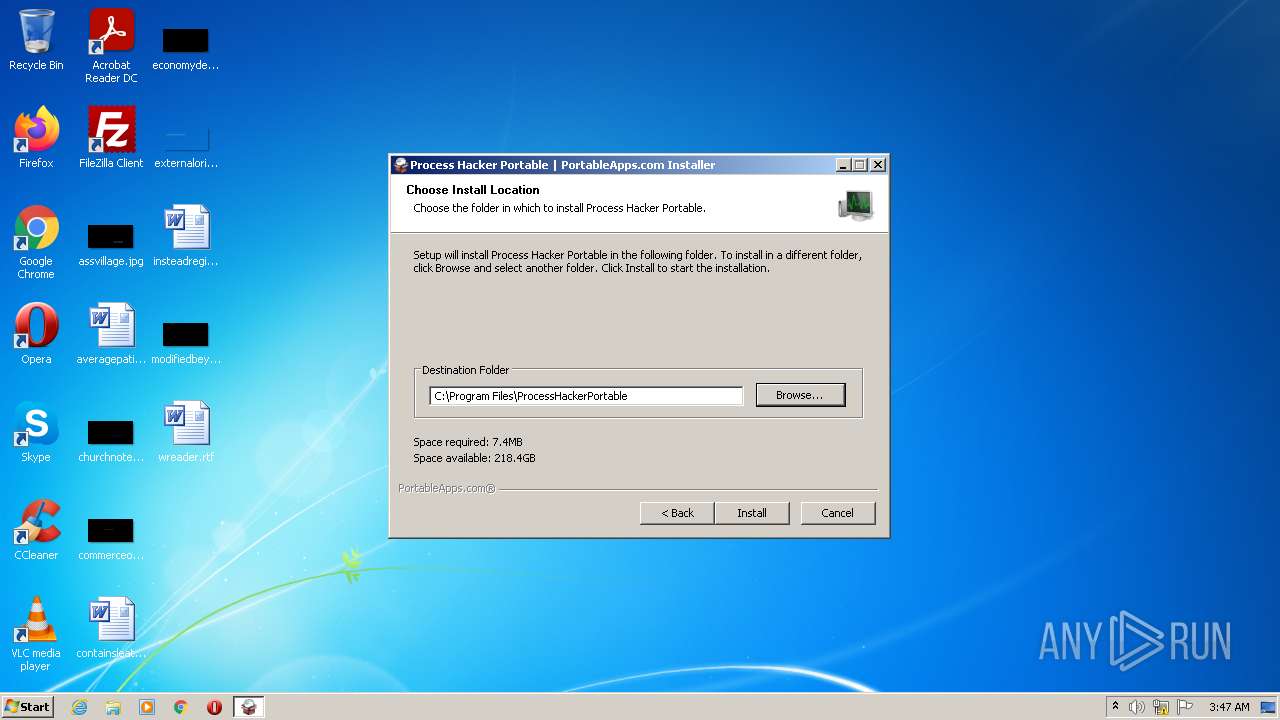
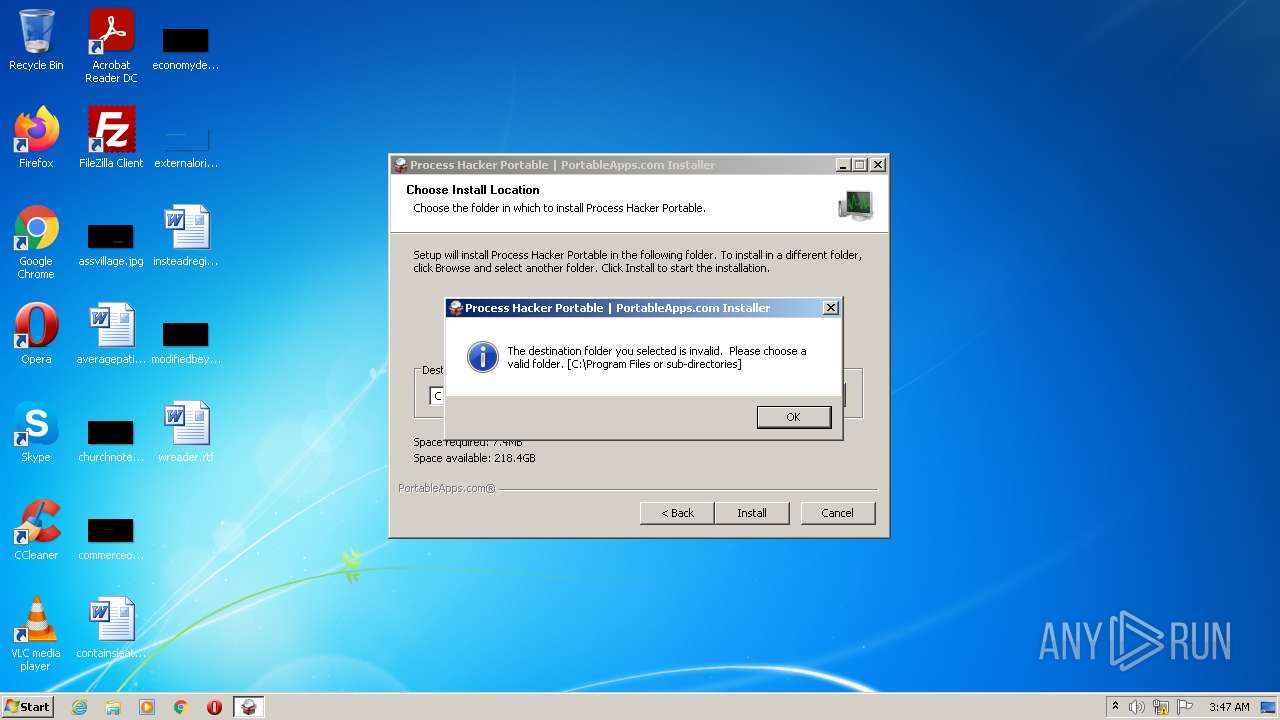
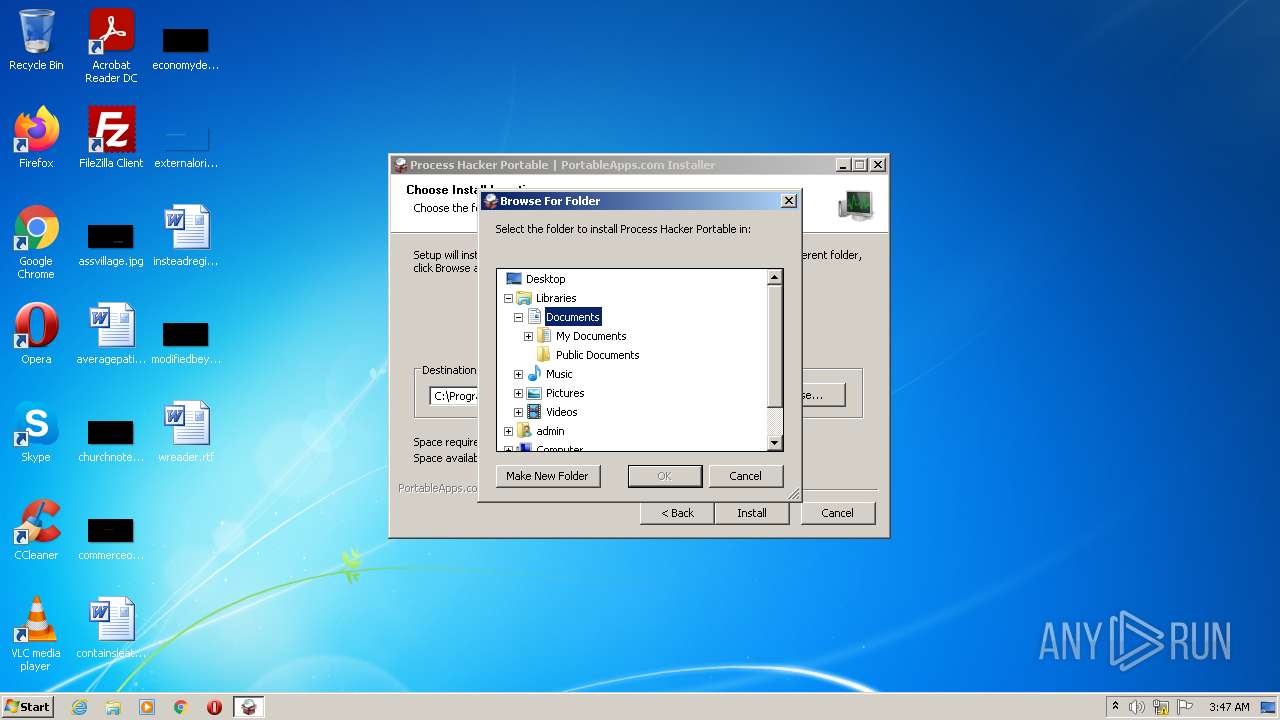
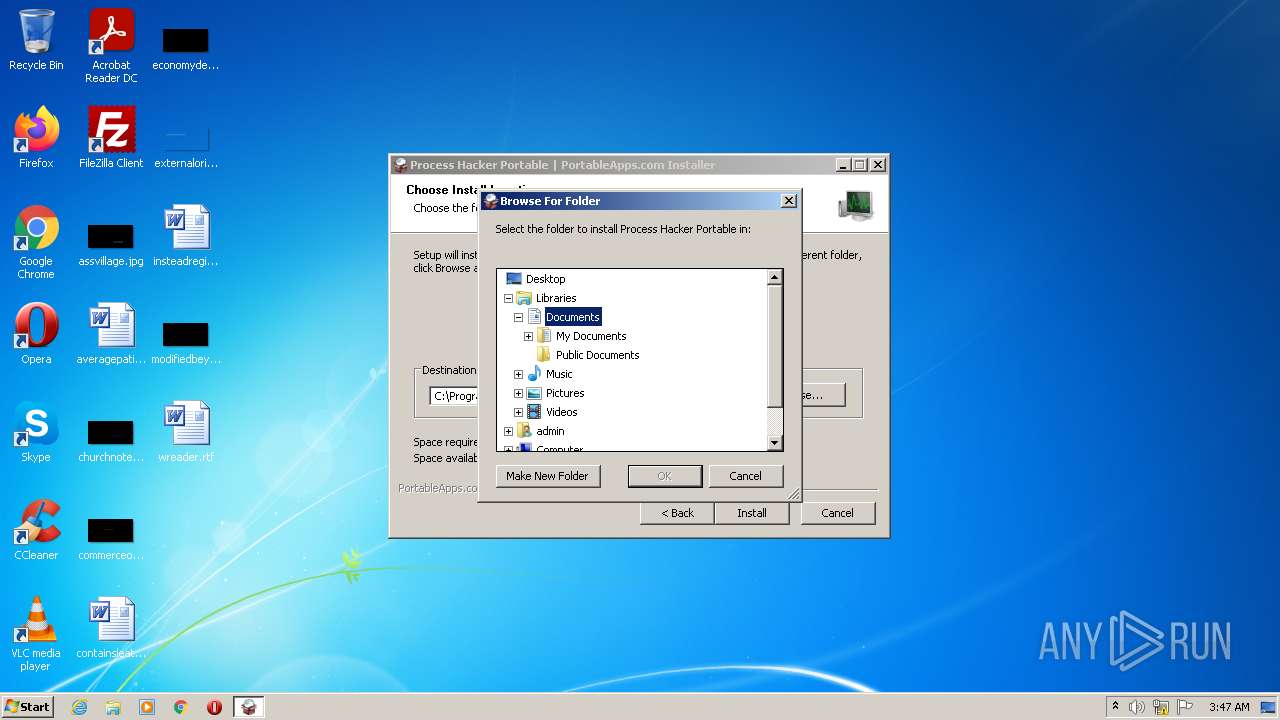
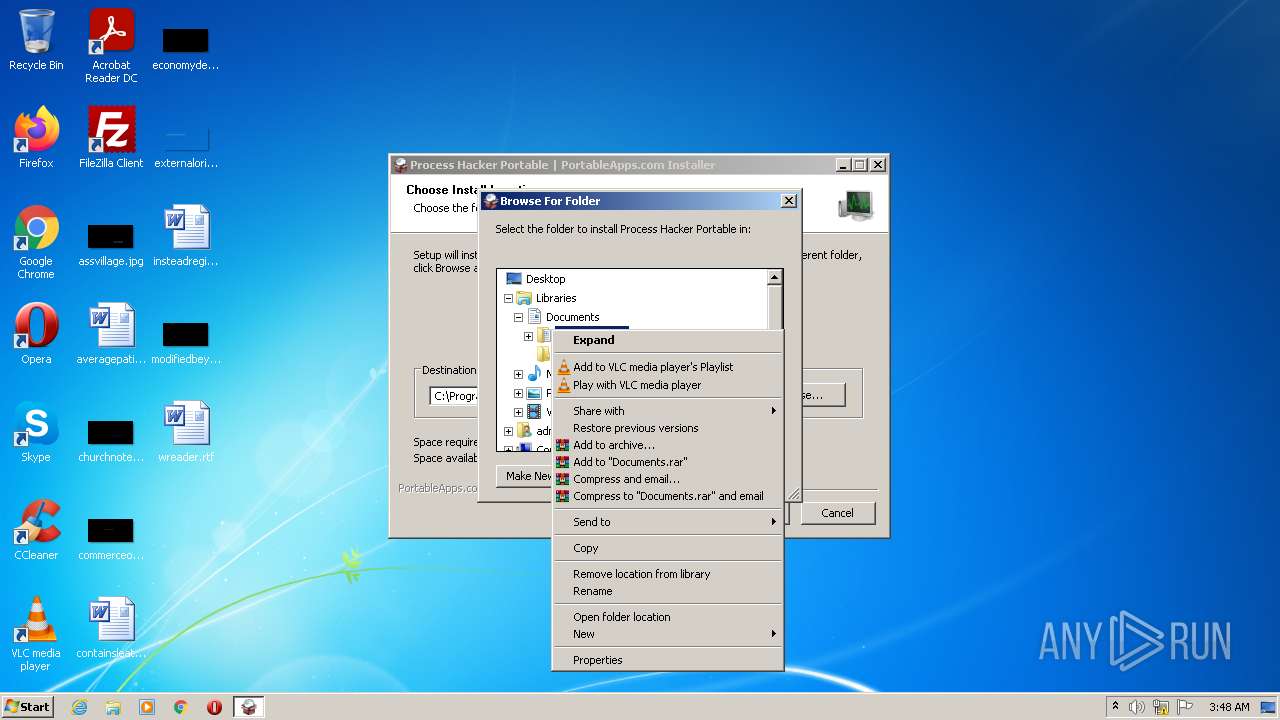
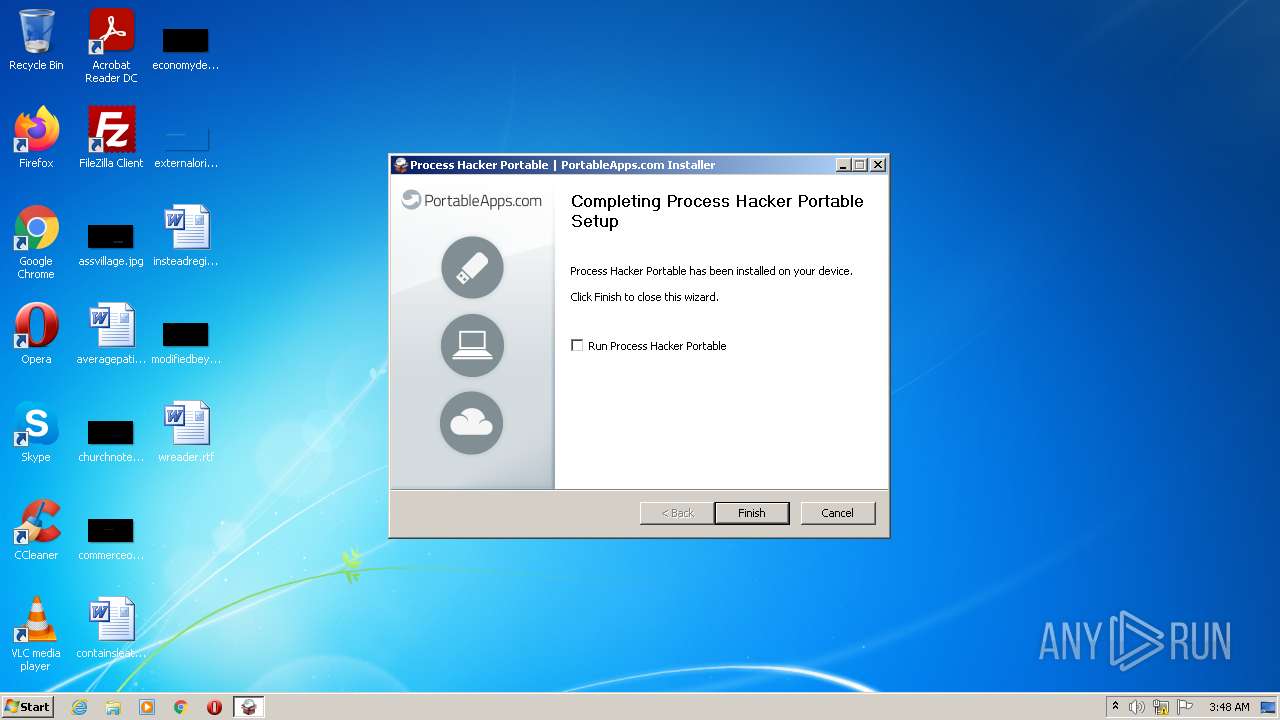
| 3368 | "C:\Users\Public\Documents\ProcessHackerPortable\ProcessHackerPortable.exe" | C:\Users\Public\Documents\ProcessHackerPortable\ProcessHackerPortable.exe | ProcessHackerPortable_2.39_English.paf.exe | ||||||||||||
User: admin Company: PortableApps.com Integrity Level: MEDIUM Description: Process Hacker Portable (PortableApps.com Launcher) Exit code: 0 Version: 2.2.0.0 Modules
| |||||||||||||||
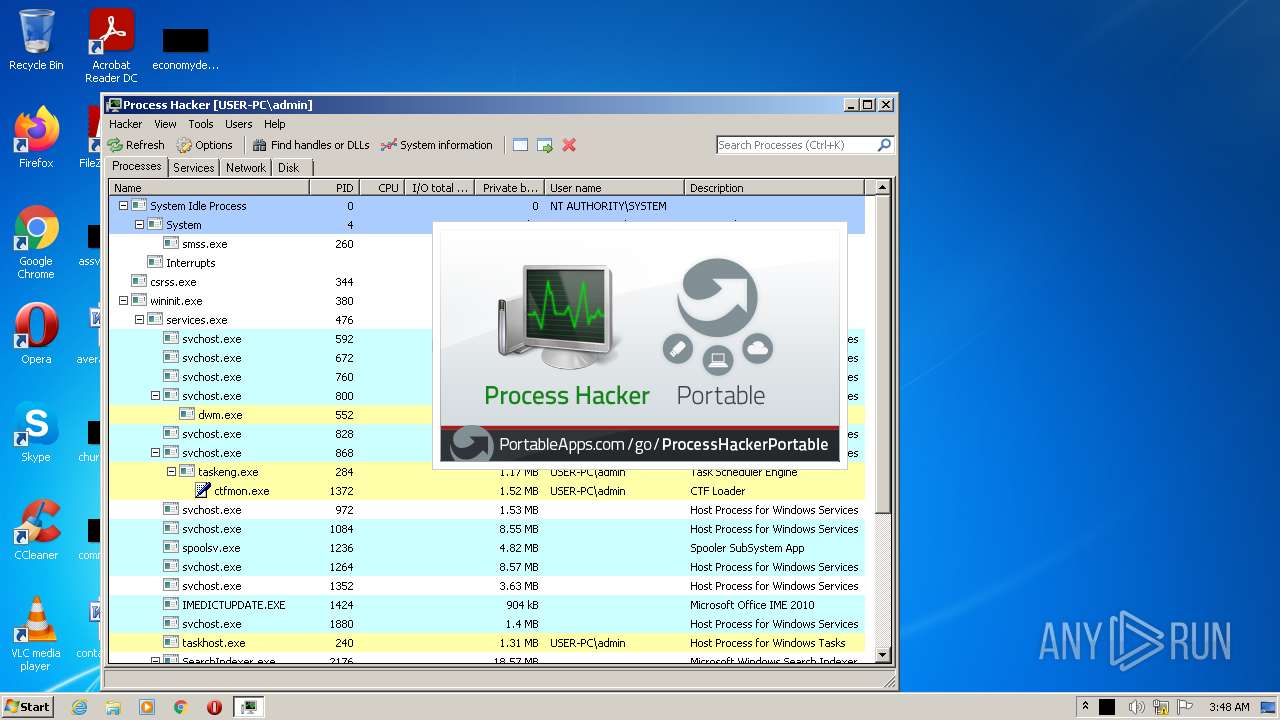
| 3664 | "C:\Users\Public\Documents\ProcessHackerPortable\App\ProcessHacker\x86\ProcessHacker.exe" -nokph -settings "C:\Users\Public\Documents\ProcessHackerPortable\Data\ProcessHacker.exe.settings.xml" | C:\Users\Public\Documents\ProcessHackerPortable\App\ProcessHacker\x86\ProcessHacker.exe | ProcessHackerPortable.exe | ||||||||||||
User: admin Company: wj32 Integrity Level: MEDIUM Description: Process Hacker Exit code: 0 Version: 2.39.0.124 Modules
| |||||||||||||||
Total events
7 125
Read events
7 072
Write events
53
Delete events
0
Modification events
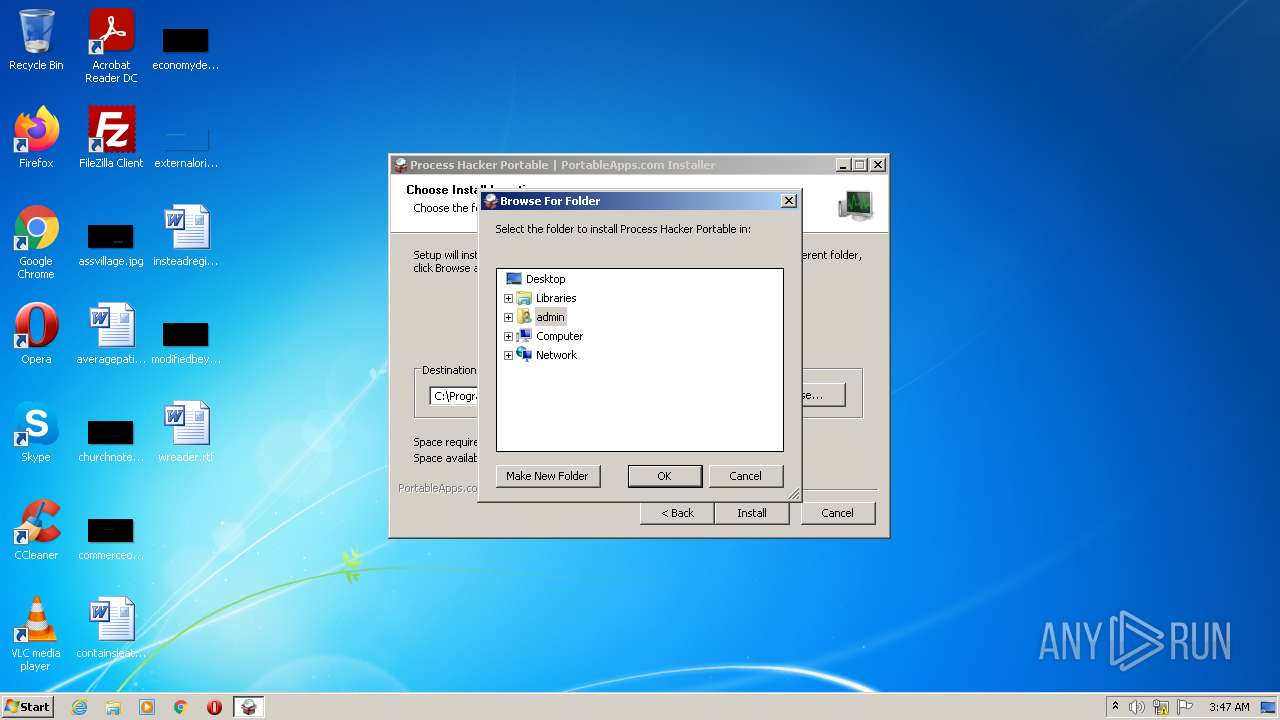
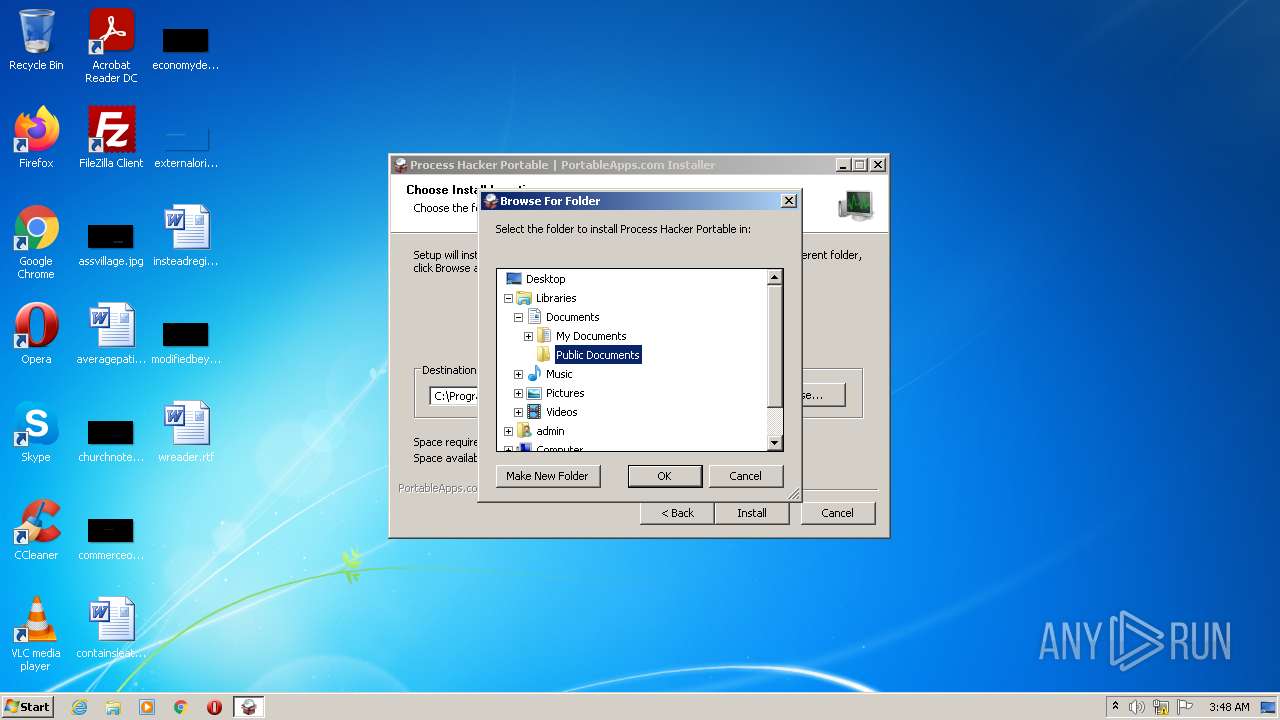
| (PID) Process: | (696) ProcessHackerPortable_2.39_English.paf.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (696) ProcessHackerPortable_2.39_English.paf.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-2 |
Value: Access the computers and devices that are on your network. | |||
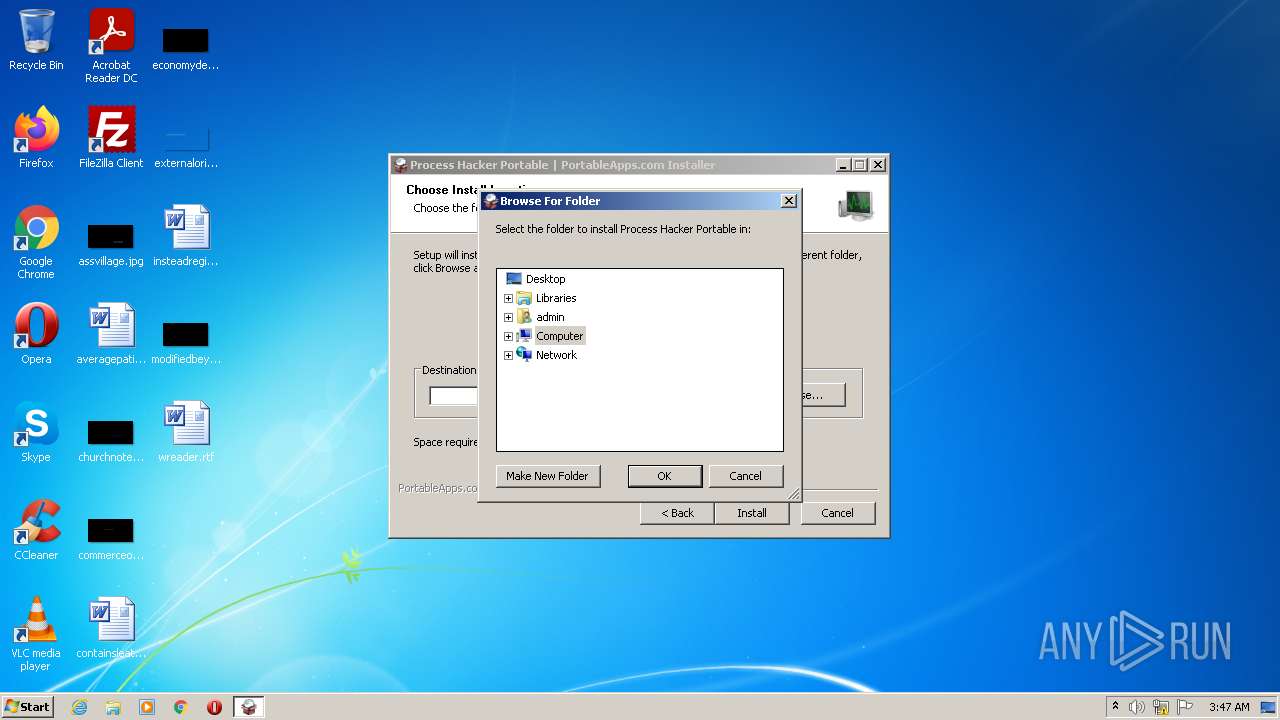
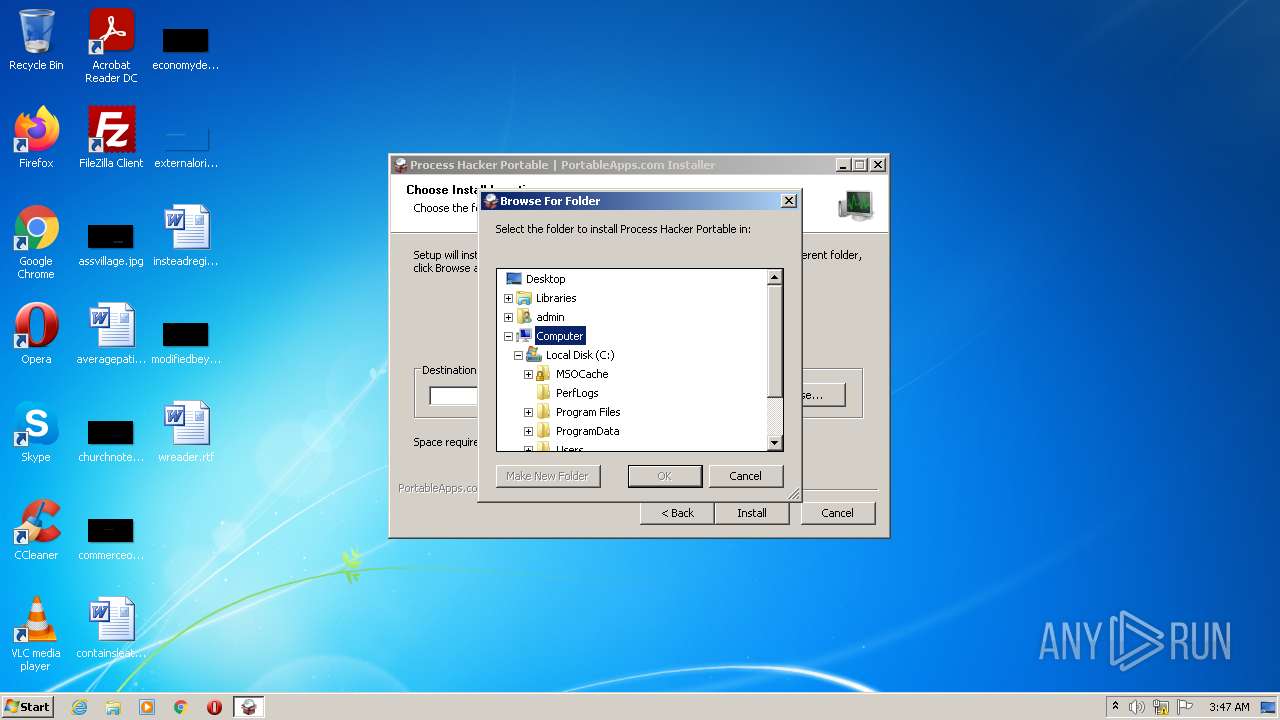
| (PID) Process: | (696) ProcessHackerPortable_2.39_English.paf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (696) ProcessHackerPortable_2.39_English.paf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (2932) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2932) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (2932) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msxml3r.dll,-1 |
Value: XML Document | |||
| (PID) Process: | (2932) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\ieframe.dll,-912 |
Value: HTML Document | |||
| (PID) Process: | (3368) ProcessHackerPortable.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3368) ProcessHackerPortable.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
39
Suspicious files
4
Text files
33
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 696 | ProcessHackerPortable_2.39_English.paf.exe | C:\Users\admin\AppData\Local\Temp\nsi9A64.tmp\FindProcDLL.dll | executable | |
MD5:BA4C1DFE226D573D516C0529F263011E | SHA256:2FFE1AC2555E822B4A383996168031E456F09F9CF3BB763FCCEE35BE178CF58A | |||
| 696 | ProcessHackerPortable_2.39_English.paf.exe | C:\Users\admin\AppData\Local\Temp\nsi9A64.tmp\System.dll | executable | |
MD5:EE260C45E97B62A5E42F17460D406068 | SHA256:E94A1F7BCD7E0D532B660D0AF468EB3321536C3EFDCA265E61F9EC174B1AEF27 | |||
| 696 | ProcessHackerPortable_2.39_English.paf.exe | C:\Users\Public\Documents\ProcessHackerPortable\App\AppInfo\appicon_16.png | image | |
MD5:441522248FD78B731259A738191FF6F2 | SHA256:68F4B47A99550472F0474974CC302B887763F0D5C33F9B1592436121AFC485F6 | |||
| 696 | ProcessHackerPortable_2.39_English.paf.exe | C:\Users\Public\Documents\ProcessHackerPortable\ProcessHackerPortable.exe | executable | |
MD5:C461E898FA55D37618B6D8B9AF0448C5 | SHA256:D6EEA8EB72D166B3DEE65E632581A4FE27E91BA68386A98ED10CC618D258CB2A | |||
| 696 | ProcessHackerPortable_2.39_English.paf.exe | C:\Users\Public\Documents\ProcessHackerPortable\App\AppInfo\appicon_75.png | image | |
MD5:1EF4C789ED875BC1BE3A2B5EC74EA040 | SHA256:602D54C15A34F5BDB85F1BA9A7709A10CA07CC26FCDA2ABE7CBBE59C2F2079F9 | |||
| 696 | ProcessHackerPortable_2.39_English.paf.exe | C:\Users\Public\Documents\ProcessHackerPortable\App\AppInfo\appicon_128.png | image | |
MD5:F8C95EE6871E19352D0C634E43C3E5B0 | SHA256:9927C67E24BDF728FB4E1DB0A16CA33DB966F8557B406DCB56A248ED11966C70 | |||
| 696 | ProcessHackerPortable_2.39_English.paf.exe | C:\Users\Public\Documents\ProcessHackerPortable\App\AppInfo\Launcher\ProcessHackerPortable.ini | ini | |
MD5:CC9BA08DC1A46E31649D31BF13AFD14C | SHA256:4F891ADC5DDBE4391F603DBDFE1682D2CE5C2D282CC159A086F83949FCB4D079 | |||
| 696 | ProcessHackerPortable_2.39_English.paf.exe | C:\Users\admin\AppData\Local\Temp\nsi9A64.tmp\w7tbp.dll | executable | |
MD5:9A3031CC4CEF0DBA236A28EECDF0AFB5 | SHA256:53BB519E3293164947AC7CBD7E612F637D77A7B863E3534BA1A7E39B350D3C00 | |||
| 696 | ProcessHackerPortable_2.39_English.paf.exe | C:\Users\Public\Documents\ProcessHackerPortable\help.html | html | |
MD5:01DA68836843D30EE41ECADB263379BA | SHA256:15D9F090B980DC2D475CC5B9E86F5721BD6A18EC9301F45963EDBA433F9E09A9 | |||
| 696 | ProcessHackerPortable_2.39_English.paf.exe | C:\Users\Public\Documents\ProcessHackerPortable\App\AppInfo\appinfo.ini | ini | |
MD5:1657DCA555FDE01ADAB6BDA6395A751F | SHA256:6EC518995BA3BB7C04BC6BAD343B2CC6F7CACD056DE609080C3ED3537AB52A4A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3664 | ProcessHacker.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?332261a1467f5b2e | US | compressed | 60.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3664 | ProcessHacker.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3664 | ProcessHacker.exe | 162.243.25.33:443 | wj32.org | Digital Ocean, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| shared |
wj32.org |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |