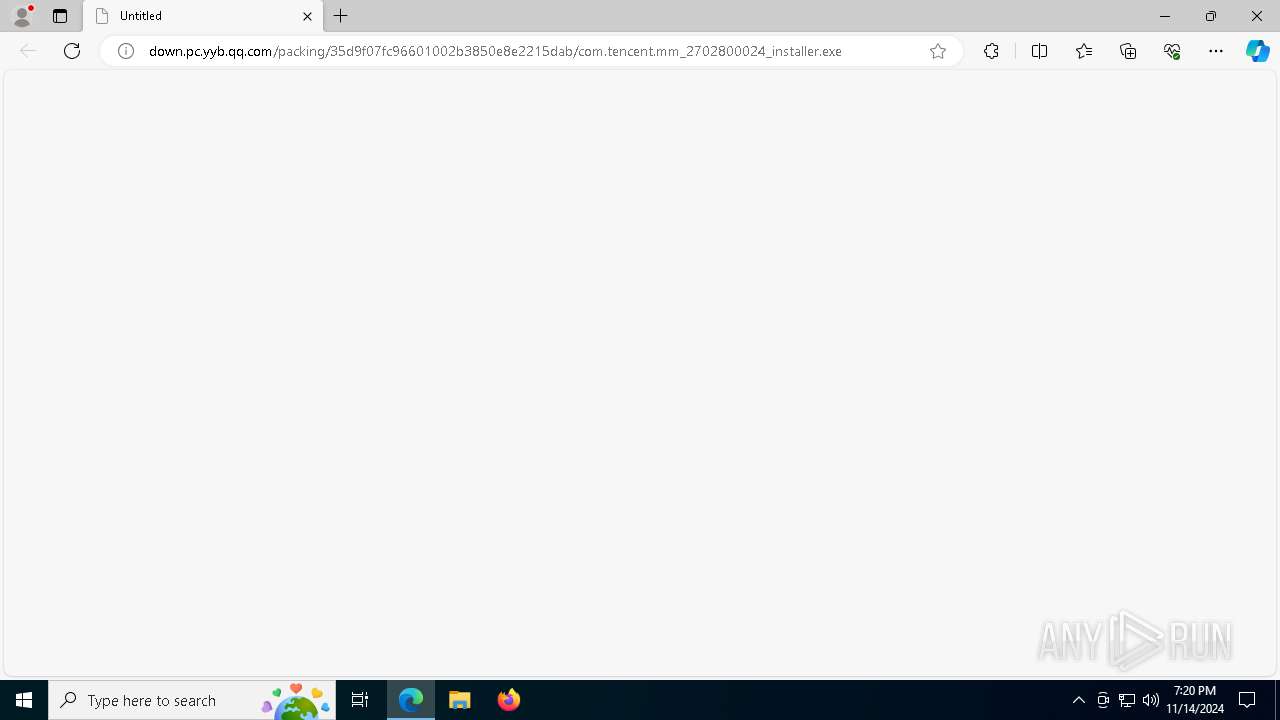
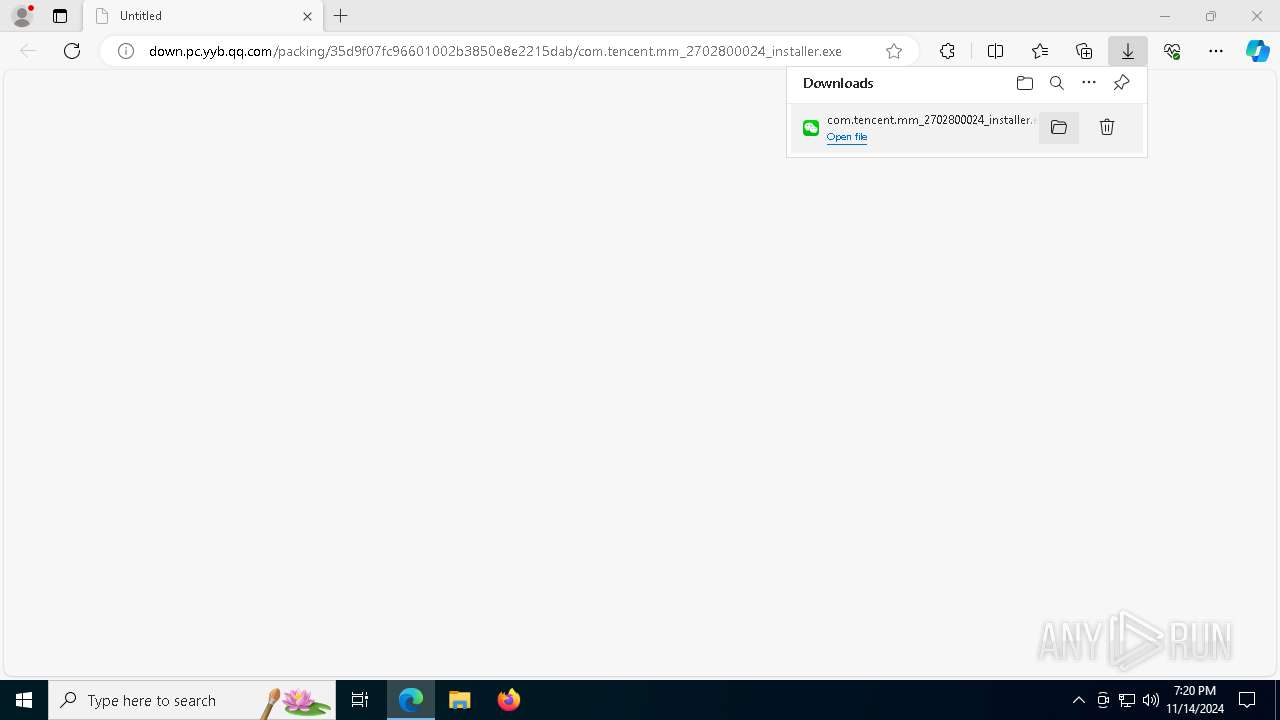
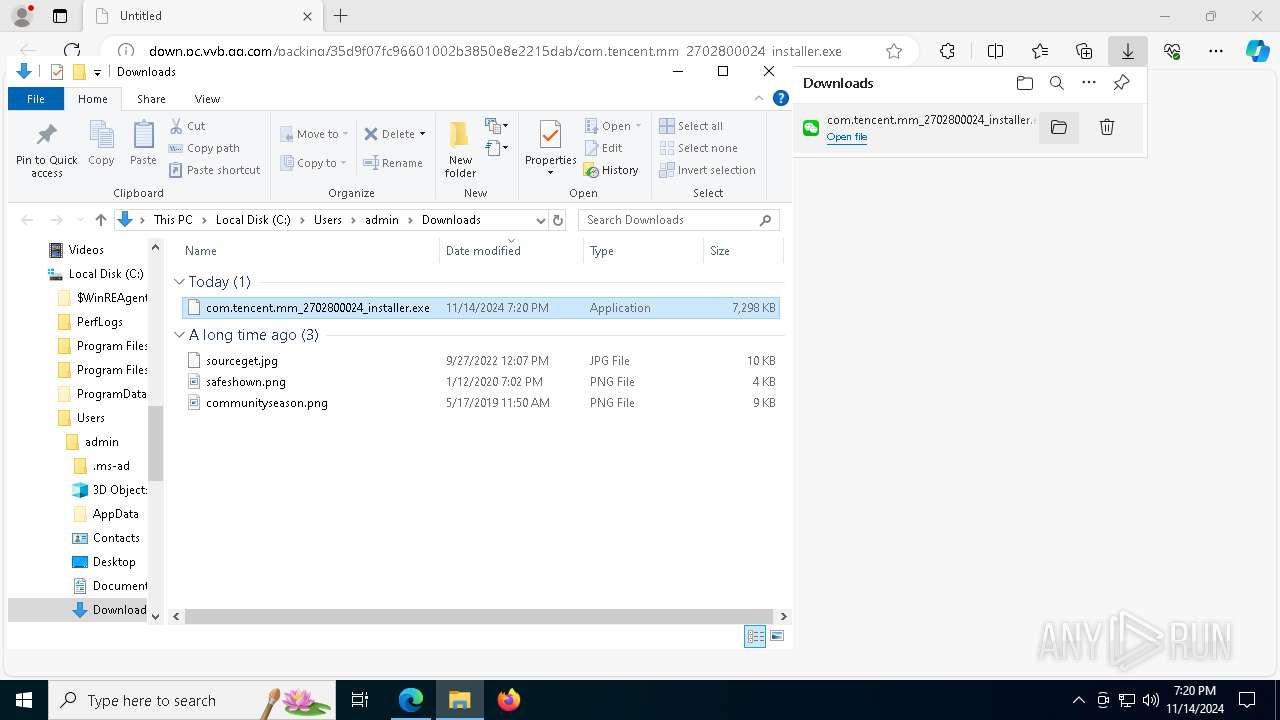
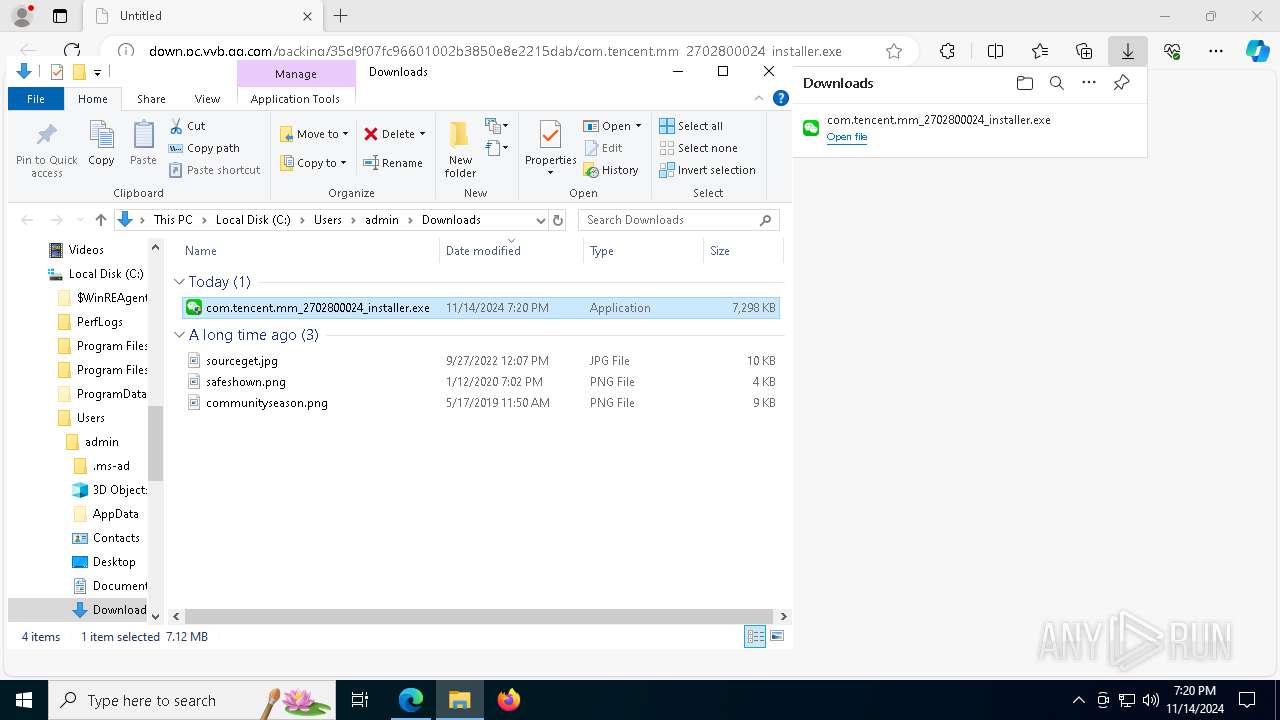
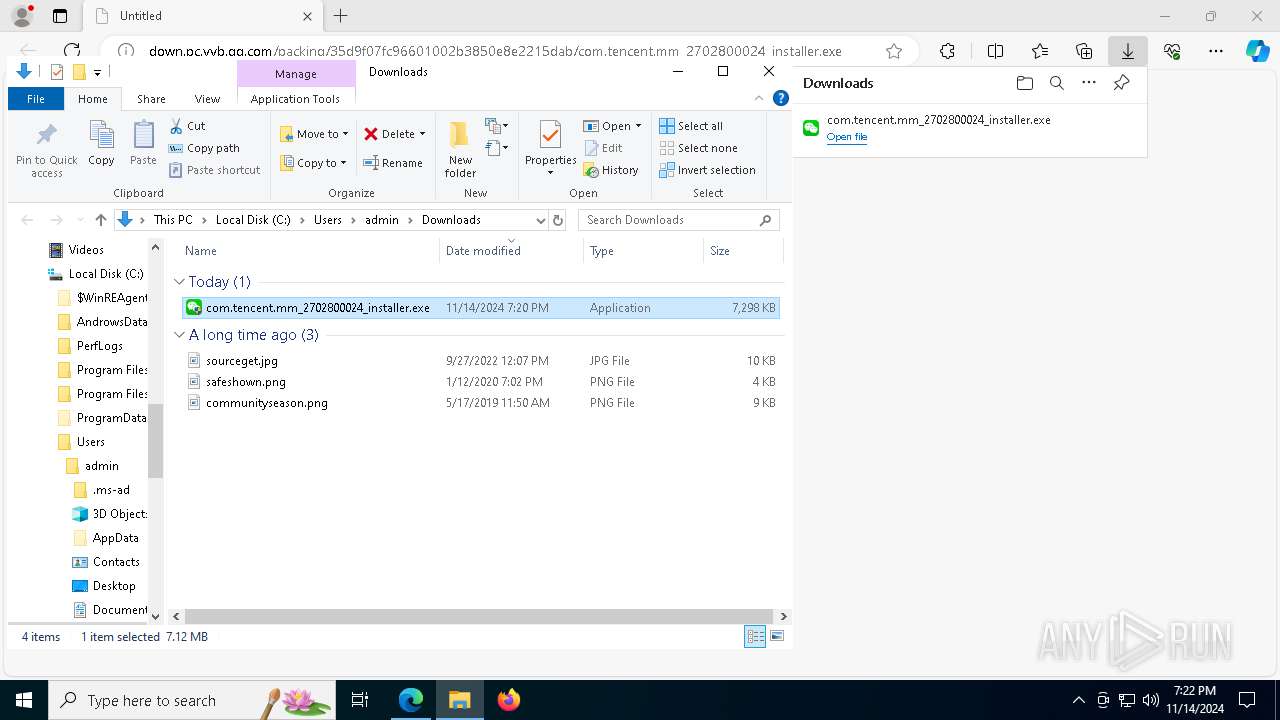
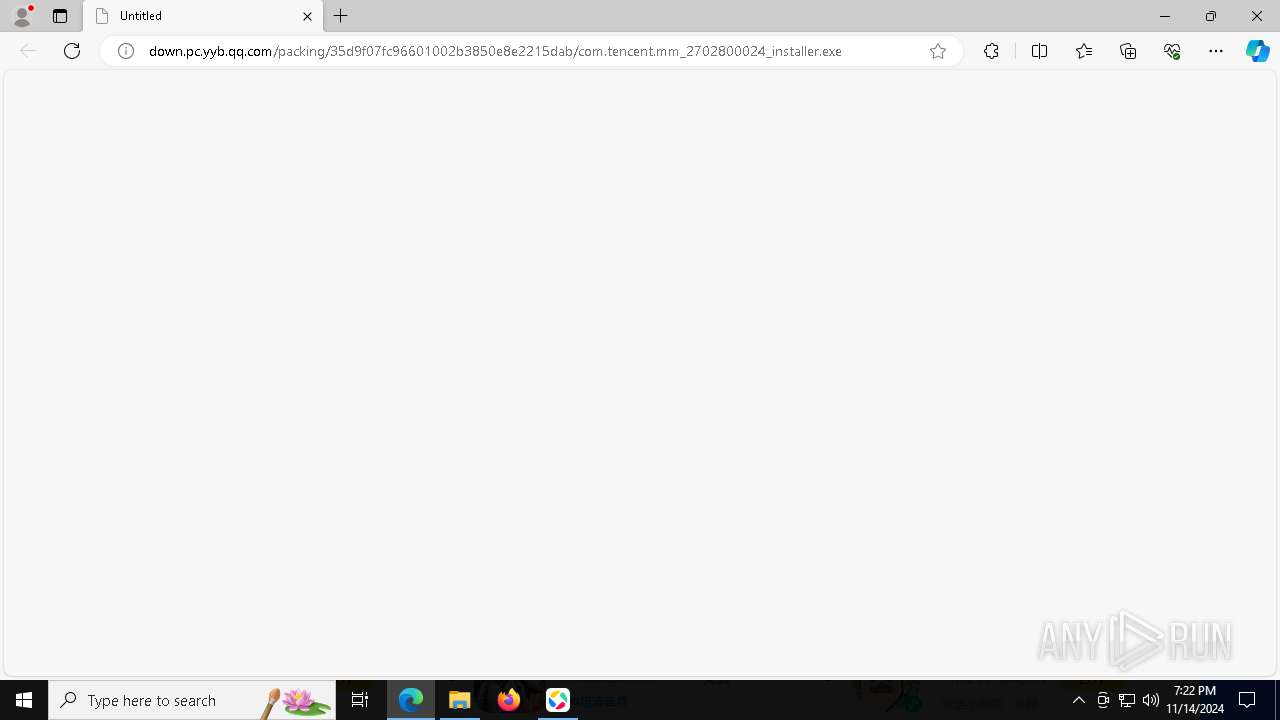
| URL: | down.pc.yyb.qq.com/packing/35d9f07fc96601002b3850e8e2215dab/com.tencent.mm_2702800024_installer.exe |
| Full analysis: | https://app.any.run/tasks/0cf8f1ff-e615-4f1a-a531-24e3b89f857f |
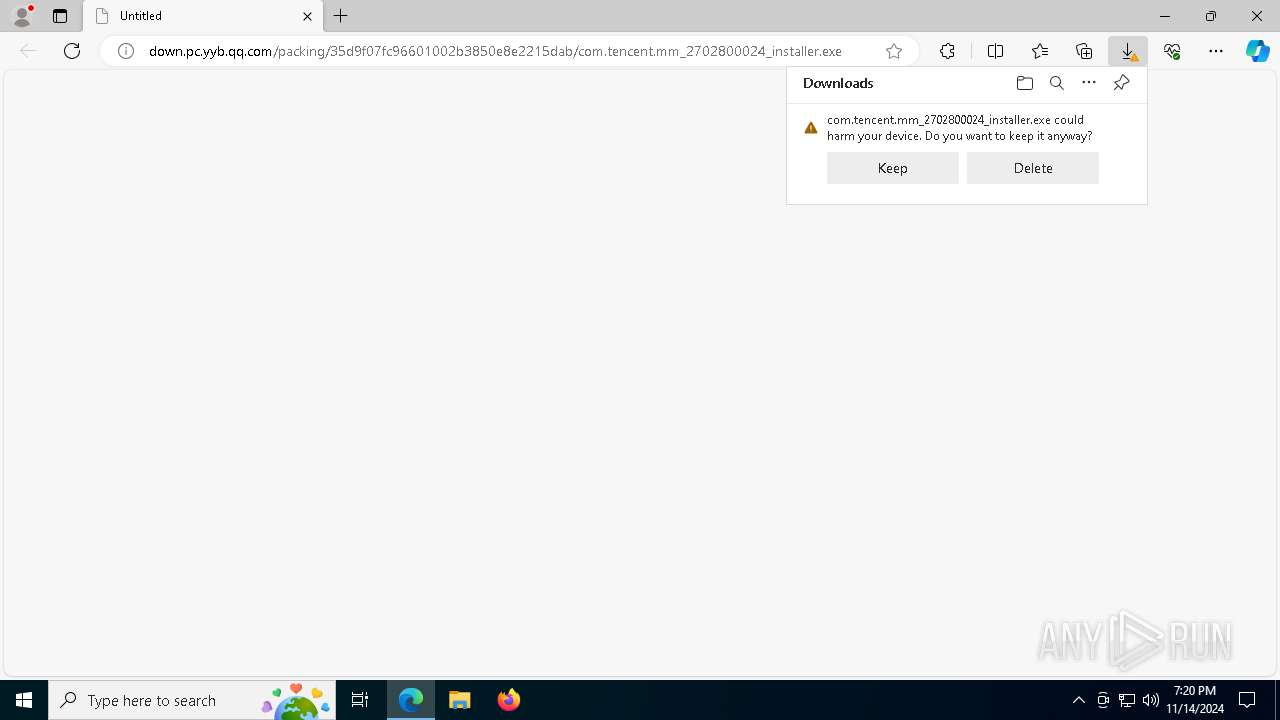
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2024, 19:20:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E75B4C0D9D1213CF5AFC17E13FD3C384 |
| SHA1: | A31D7EAAA761509E0BD752BAF16CA64AF708BF1D |
| SHA256: | B06154D548F559CAA390C6B6641112B52E52B72C804F9CDCD3CF098E30968400 |
| SSDEEP: | 3:ADyCEGOIByVSDu92dyEHdHXuRtVHV91JOXLNn:qEZRVSDc6Ul1dOXLN |
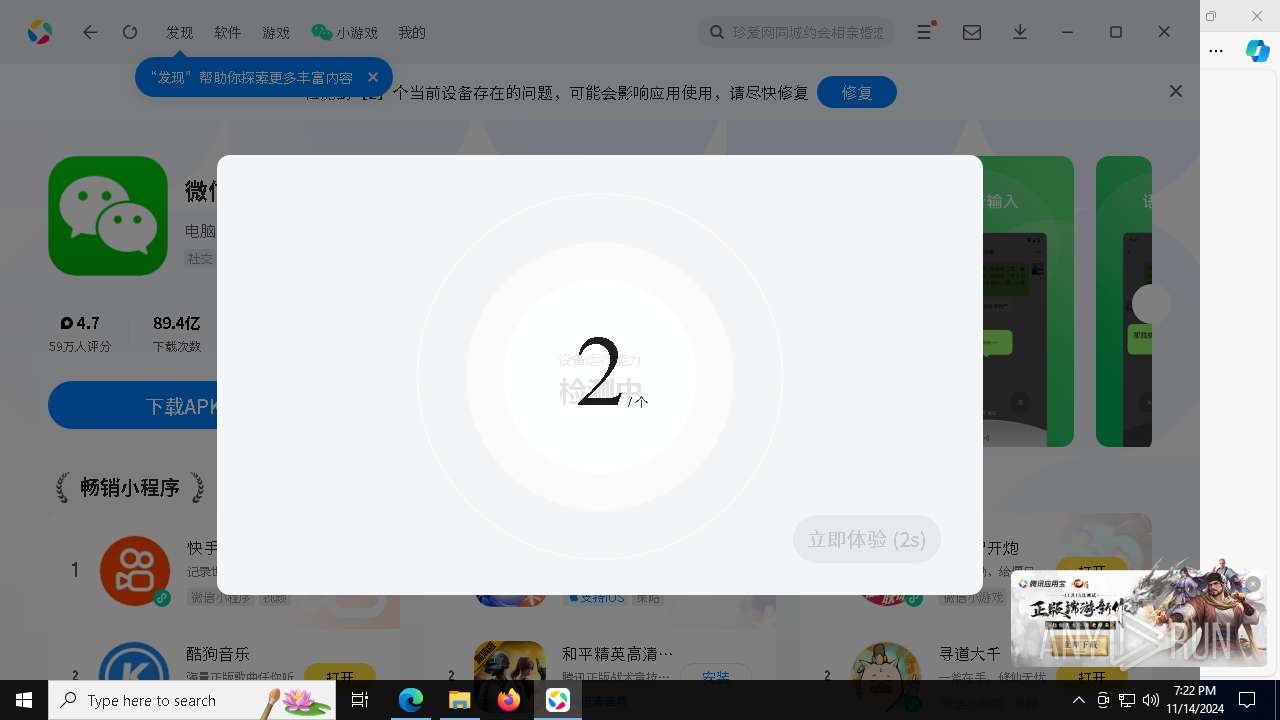
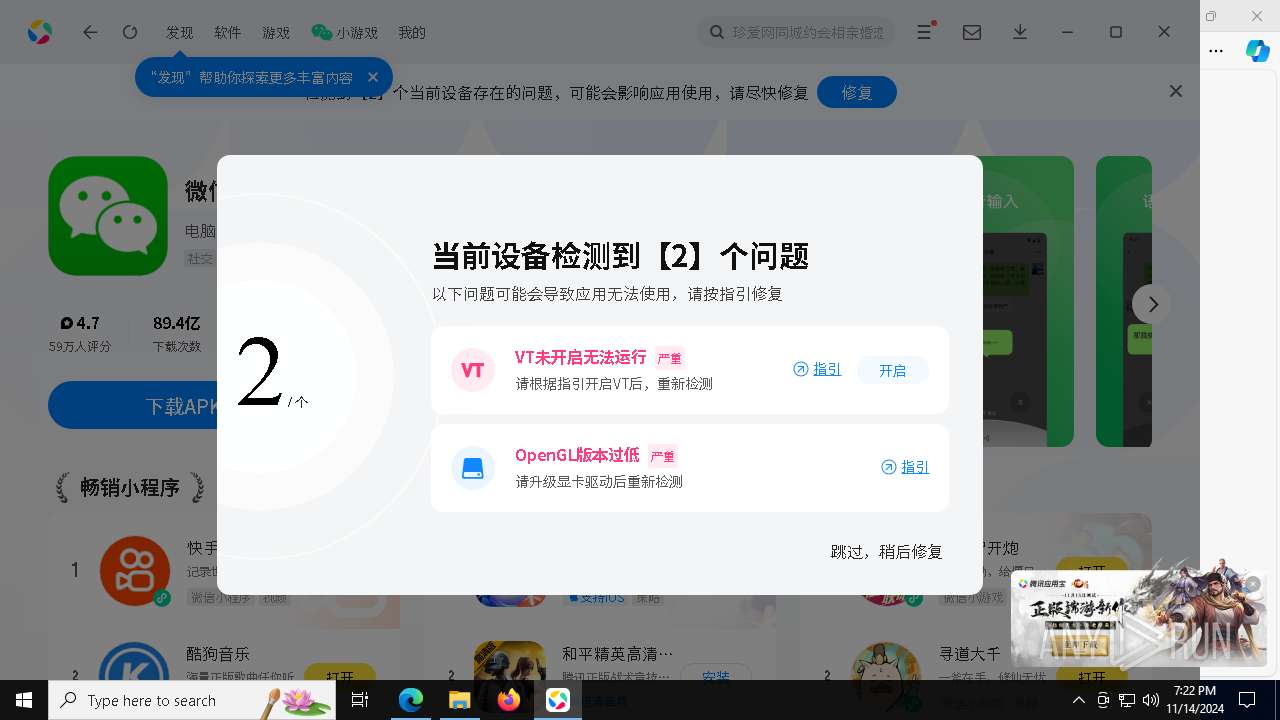
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- Setup.exe (PID: 7652)
SUSPICIOUS
Uses WMIC.EXE to obtain data on the base board management (motherboard or system board)
- com.tencent.mm_2702800024_installer.exe (PID: 7956)
- AndrowsStore.exe (PID: 3524)
Drops a system driver (possible attempt to evade defenses)
- com.tencent.mm_2702800024_installer.exe (PID: 7956)
- Setup.exe (PID: 7652)
Executable content was dropped or overwritten
- com.tencent.mm_2702800024_installer.exe (PID: 7956)
- Setup.exe (PID: 7652)
- AndrowsStore.exe (PID: 3524)
- Setup.exe (PID: 8968)
- CefRendererProcess.exe (PID: 8792)
Process drops legitimate windows executable
- com.tencent.mm_2702800024_installer.exe (PID: 7956)
- Setup.exe (PID: 7652)
- AndrowsStore.exe (PID: 3524)
- Setup.exe (PID: 8968)
Drops 7-zip archiver for unpacking
- Setup.exe (PID: 7652)
- com.tencent.mm_2702800024_installer.exe (PID: 7956)
The process drops C-runtime libraries
- com.tencent.mm_2702800024_installer.exe (PID: 7956)
- Setup.exe (PID: 7652)
- AndrowsStore.exe (PID: 3524)
Executes as Windows Service
- AndrowsSvr.exe (PID: 4080)
Starts CMD.EXE for commands execution
- Setup.exe (PID: 7652)
Starts SC.EXE for service management
- cmd.exe (PID: 2184)
Application launched itself
- WeChatAppEx.exe (PID: 2140)
- WeChatAppHost.exe (PID: 9180)
INFO
Manual execution by a user
- com.tencent.mm_2702800024_installer.exe (PID: 7956)
- com.tencent.mm_2702800024_installer.exe (PID: 6912)
Executable content was dropped or overwritten
- msedge.exe (PID: 3620)
- msedge.exe (PID: 5584)
- msedge.exe (PID: 6360)
Application launched itself
- msedge.exe (PID: 3620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
247
Monitored processes
111
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 784 | regsvr32 /s "C:\Program Files\Tencent\Androws\Application\3.0.4076.0\AndrowsAiAssistantContextMenu.dll | C:\Windows\System32\regsvr32.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 884 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6628 --field-trial-handle=2448,i,16802427057820832268,16161679691918746292,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 920 | "C:\Program Files\Tencent\Androws\Application\3.0.4076.0\crashpad_handler.exe" --no-rate-limit --database=C:\Users\admin\AppData\Local\Temp\Tencent\Androws\ --metrics-dir=C:\Users\admin\AppData\Local\Temp\Tencent\Androws\ --annotation=app_id=7ebaf51295 --annotation=app_key=3595ca0a-0ac2-42e7-988b-bb08e6767e24 --annotation=app_version=3.0.53.01 --annotation=build_id=3.0.4076.0 --annotation=bundle_id=com.tencent.androws --annotation=database=7ebaf51295 --annotation=format=minidump --annotation=is_need_attach_info=true --annotation=is_need_upload=true --annotation=is_pop_dialog=true --annotation=is_server_process=false --annotation=process_display_name=AndrowsStore --annotation=process_name=AndrowsStore --annotation=product=7ebaf51295 --annotation=version=3.0.53.01 --initial-client-data=0x4c0,0x4c4,0x4c8,0x430,0x4dc,0x7ffbca4160b8,0x7ffbca416078,0x7ffbca416088 | C:\Program Files\Tencent\Androws\Application\3.0.4076.0\crashpad_handler.exe | — | AndrowsStore.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1236 | sc start dokan2t | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Tencent\Androws\Application\AndrowsLauncher.exe" --hotfix-pull "" --launch-proc-name "AndrowsAssistant.exe" | C:\Program Files\Tencent\Androws\Application\AndrowsLauncher.exe | — | AndrowsSvr.exe | |||||||||||
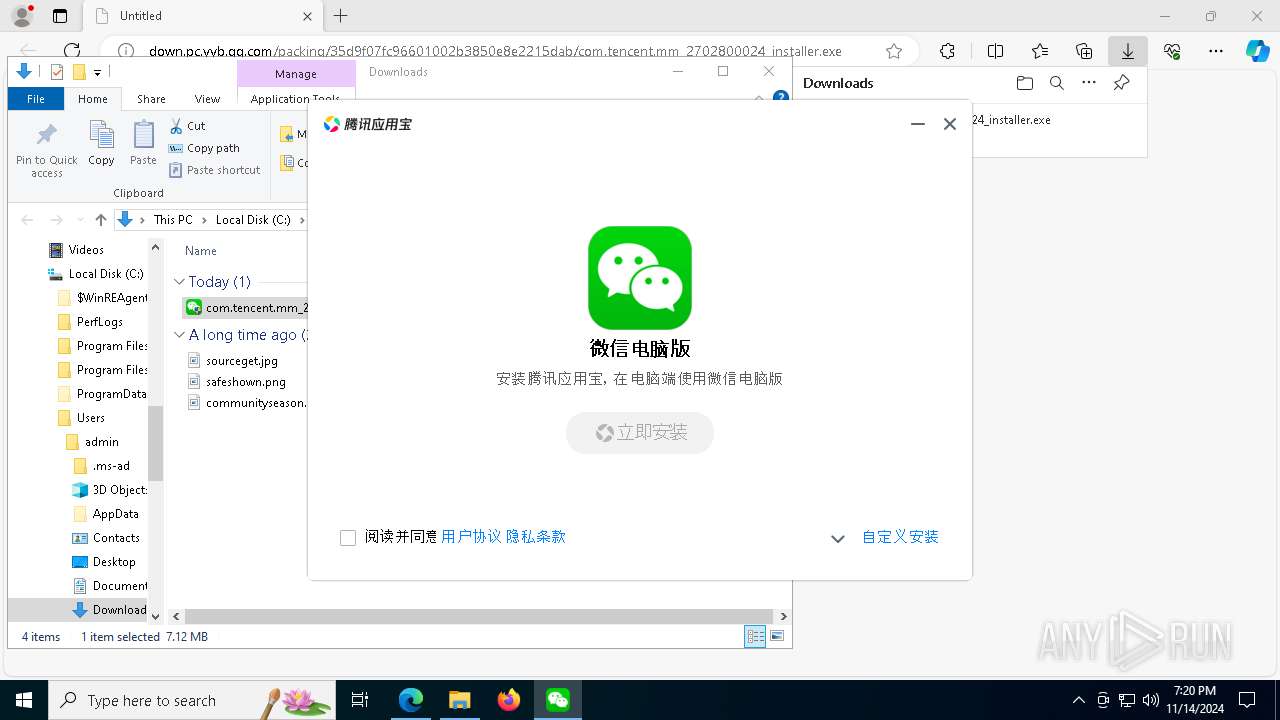
User: admin Company: Tencent Integrity Level: HIGH Description: 腾讯应用宝 Exit code: 0 Version: 3.0.4076.0 | |||||||||||||||
| 1528 | "C:\Program Files\Tencent\Androws\Application\3.0.4076.0\CefRendererProcess" --lang=en-US --locales-dir-path="C:\Program Files\Tencent\Androws\Application\3.0.4076.0\resources\locales" --log-items=pid,tid,timestamp --log-severity=disable --no-sandbox --resources-dir-path="C:\Program Files\Tencent\Androws\Application\3.0.4076.0\resources" --service-sandbox-type=service --type=utility --use-angle=swiftshader-webgl --use-gl=angle --user-agent-product="Chrome/126.0.0 CefView/1.0 (Windows; en-us) YYBAppClient/3.0.4076.0" --user-data-dir="C:\Users\admin\AppData\Roaming\Tencent\Androws\cef\CEF_AndrowsStore" --utility-sub-type=storage.mojom.StorageService --in-process-gpu --windows-job-name=CefView-Job-{f0a3c1e3-ff89-4581-8a45-f0bfd74c4bb0}-3524 --disable-extensions --disable-pdf-extension --disable-site-isolation-trials=1 --bridge-obj-name=CallBridge --field-trial-handle=4256,i,5488553997071110595,15766994232097705345,262144 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,DocumentPictureInPictureAPI --variations-seed-version --mojo-platform-channel-handle=4240 | C:\Program Files\Tencent\Androws\Application\3.0.4076.0\CefRendererProcess.exe | — | AndrowsStore.exe | |||||||||||
User: admin Integrity Level: HIGH | |||||||||||||||
| 2056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | opengl_checker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2084 | "C:\Windows\System32\regsvr32.exe" /s /u "C:\Program Files\Tencent\Androws\Application\3.0.4076.0\context_menu_ext.dll" | C:\Windows\System32\regsvr32.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Tencent\Androws\Application\3.0.4076.0\AndrowsAssistant.exe" --rid-long "CL27geGyMhABGgVwY3l5YiIDMzU1KhFwY3l5Yl90aXBzX3JlY192MjIgM2RhM2RkMDUzOGQ2NGM4NzcxNzQxMmFlZDcyZmJlNzE6CDcwOTU5MjY2Qh1hN2U1ZDQyYjE1ZjkxNDEyLWVhNGQzNjY3LTM1NUoFEgOgjQZSBzgyMjUwMTRYEWIwCQAAAAAAAElAEiUKI2NoYW5uZWxfbWFubmVyLnJlcXVlc3RfY29udGV4dF9hcHBzankJwQPWKlQCSUASEAoFYWxwaGERAAAAAAC4kEASDwoEYmV0YREAAAAAgHrrQBILCglpc19leHBvc2USEwoIY2xpY2tfcHYRAAAAAACwkEASFAoJZXhwb3NlX3B2EQAAAACAwetAEhMKCHByaW9yaXR5EQAAAAAAAElAcgB6MgowCgQyOTQ2Ihs1ZWM2YjI4N2I3OTU4NGEyLWVhNGQzNjY3IzAqC2VycF9yYW5raW5n" --show-tips "{\"BusinessId\":\"b_inner_notify\",\"Content\":\"{\\\"rid\\\":\\\"2fb23a7cbc81d5a1\\\",\\\"schema_url\\\":\\\"androws://tips/gotoDetail?pkgname=com.tencent.pcgame.tmgp.tlbbgl&raw_tips_type=1&raw_tips_task_id=8225014&rid=2fb23a7cbc81d5a1&trace_id=c3cfebd2-a2bd-11ef-8953-525400c81d60\\\",\\\"show_interval\\\":1800,\\\"system_notify\\\":{\\\"action\\\":[\\\"\\\"],\\\"action_schema\\\":{\\\"\\\":\\\"androws://tips/gotoDetail?pkgname=com.tencent.pcgame.tmgp.tlbbgl&raw_tips_type=1&raw_tips_task_id=8225014\\\"},\\\"avatar_url\\\":\\\"\\\",\\\"content\\\":\\\"\\\",\\\"inline_image_url\\\":\\\"https://static.pc.yyb.qq.com/wupload/xy/yyb_management_system/LCESxKHY.png\\\",\\\"title\\\":\\\"\\\"},\\\"timeout\\\":0,\\\"trace_id\\\":\\\"c3cfebd2-a2bd-11ef-8953-525400c81d60\\\"}\",\"EndTime\":1731715199,\"TaskId\":\"8225014_assistant_tips\",\"Type\":3001}" --androws_launcher_start_time "1731612139982" | C:\Program Files\Tencent\Androws\Application\3.0.4076.0\AndrowsAssistant.exe | — | AndrowsLauncher.exe | |||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: 腾讯应用宝 Exit code: 0 Version: 3.0.4076.0 | |||||||||||||||
| 2140 | "C:\Program Files\Tencent\Androws\WmpfRuntime\3.0.3.109\runtime\WeChatAppEx.exe" --log-level=0 --helper-handle-value=295619389 --enable-gpu-process --product-id=1007 --use-extern-crash-handler --client_version=1661404927 --wmpf_root_dir="C:\AndrowsData\wmpf_data" --mojo-platform-channel-handle=796 | C:\Program Files\Tencent\Androws\WmpfRuntime\3.0.3.109\runtime\WeChatAppEx.exe | — | WeChatAppHost.exe | |||||||||||
User: admin Company: Tencent LLC Integrity Level: HIGH Description: WeChatAppEx Version: 2.1.2.50241 | |||||||||||||||
Total events
12 196
Read events
12 110
Write events
84
Delete events
2
Modification events
| (PID) Process: | (3620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3620) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4A73B4A07A852F00 | |||
| (PID) Process: | (3620) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EF85BDA07A852F00 | |||
| (PID) Process: | (3620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262726 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {97365122-ECD2-47F7-A8CA-5BA7635E2143} | |||
| (PID) Process: | (3620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262726 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {06517292-5351-4CD3-9D48-5670A7D9955F} | |||
| (PID) Process: | (3620) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6C98F0A07A852F00 | |||
| (PID) Process: | (3620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
487
Suspicious files
1 182
Text files
700
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8b55e.TMP | — | |
MD5:— | SHA256:— | |||
| 3620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8b55e.TMP | — | |
MD5:— | SHA256:— | |||
| 3620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8b56e.TMP | — | |
MD5:— | SHA256:— | |||
| 3620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8b56e.TMP | — | |
MD5:— | SHA256:— | |||
| 3620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8b58d.TMP | — | |
MD5:— | SHA256:— | |||
| 3620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
296
DNS requests
170
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4004 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7116 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1204 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7116 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
540 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1731865032&P2=404&P3=2&P4=VsZsE%2f3hpwMDonv8k92BeJefJ5rKso%2bOcqKZcJ0ngTeheszMFlGofH97fboLRVIQ9BtEa6Sz90yKGnsDo6Yxgg%3d%3d | unknown | — | — | whitelisted |
540 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1731865032&P2=404&P3=2&P4=VsZsE%2f3hpwMDonv8k92BeJefJ5rKso%2bOcqKZcJ0ngTeheszMFlGofH97fboLRVIQ9BtEa6Sz90yKGnsDo6Yxgg%3d%3d | unknown | — | — | whitelisted |
540 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1731865032&P2=404&P3=2&P4=VsZsE%2f3hpwMDonv8k92BeJefJ5rKso%2bOcqKZcJ0ngTeheszMFlGofH97fboLRVIQ9BtEa6Sz90yKGnsDo6Yxgg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.48.23.164:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 2.23.209.167:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5584 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
down.pc.yyb.qq.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Tencent Cloud Storage Domain in DNS Lookup (myqcloud .com) |
— | — | Misc activity | ET INFO Tencent Cloud Storage Domain in DNS Lookup (myqcloud .com) |
— | — | Misc activity | ET INFO Observed Tencent Cloud Storage Domain (myqcloud .com in TLS SNI) |
— | — | Misc activity | ET INFO Observed Tencent Cloud Storage Domain (myqcloud .com in TLS SNI) |
— | — | Misc activity | ET INFO Observed Tencent Cloud Storage Domain (myqcloud .com in TLS SNI) |
— | — | Misc activity | ET INFO Observed Tencent Cloud Storage Domain (myqcloud .com in TLS SNI) |
Process | Message |
|---|---|
AndrowsSvr.exe | 11-14 19:22:14.083 [4080.2464](info)[app.launch] [boot::Initialize] (initialize.cpp:103) [Msg]: "C:\Program Files\Tencent\Androws\Application\3.0.4076.0\AndrowsSvr.exe" |
AndrowsSvr.exe | 11-14 19:22:14.083 [4080.2928](info)[app.androwsservice] [service::ServiceMain] (androws_service.cpp:142) [Msg]: [Enter][argc]: 1 |
AndrowsSvr.exe | 11-14 19:22:14.083 [4080.1764](info)[app.androwsservice] [service::Initialize::::operator()] (androws_service.cpp:194) [Msg]: Starting ServiceMain... |
AndrowsSvr.exe | 11-14 19:22:14.083 [4080.2464](info)[app.androwsservice] [WaitForExploreReady] (uac_start.cc:240) [Msg]: Waiting for explore... |
AndrowsSvr.exe | 11-14 19:22:14.083 [4080.2464](info)[app.androwsservice] [WaitForExploreReady] (uac_start.cc:250) [Msg]: Waiting for explore done. |
AndrowsSvr.exe | 11-14 19:22:14.083 [4080.2928](info)[app.androwsservice] [service::ServiceMain] (androws_service.cpp:170) [Msg]: Service Starting... |
AndrowsSvr.exe | 11-14 19:22:14.193 [4080.2464](warning)[default] [unknown] (:0) [Msg]: QObject: Cannot create children for a parent that is in a different thread.
(Parent is CLoginService(0x7ff633890510), parent's thread is QThread(0x26183a0a660), current thread is QThread(0x261839d7b90) |
AndrowsSvr.exe | 11-14 19:22:14.193 [4080.2464](info)[app.clogin] [CLoginService::Initialize] (clogin_service.cc:142) [Msg]: enter. |
AndrowsStore.exe | QCommandLineParser: call process() or parse() before value
|
AndrowsStore.exe | QCommandLineParser: call process() or parse() before isSet
|