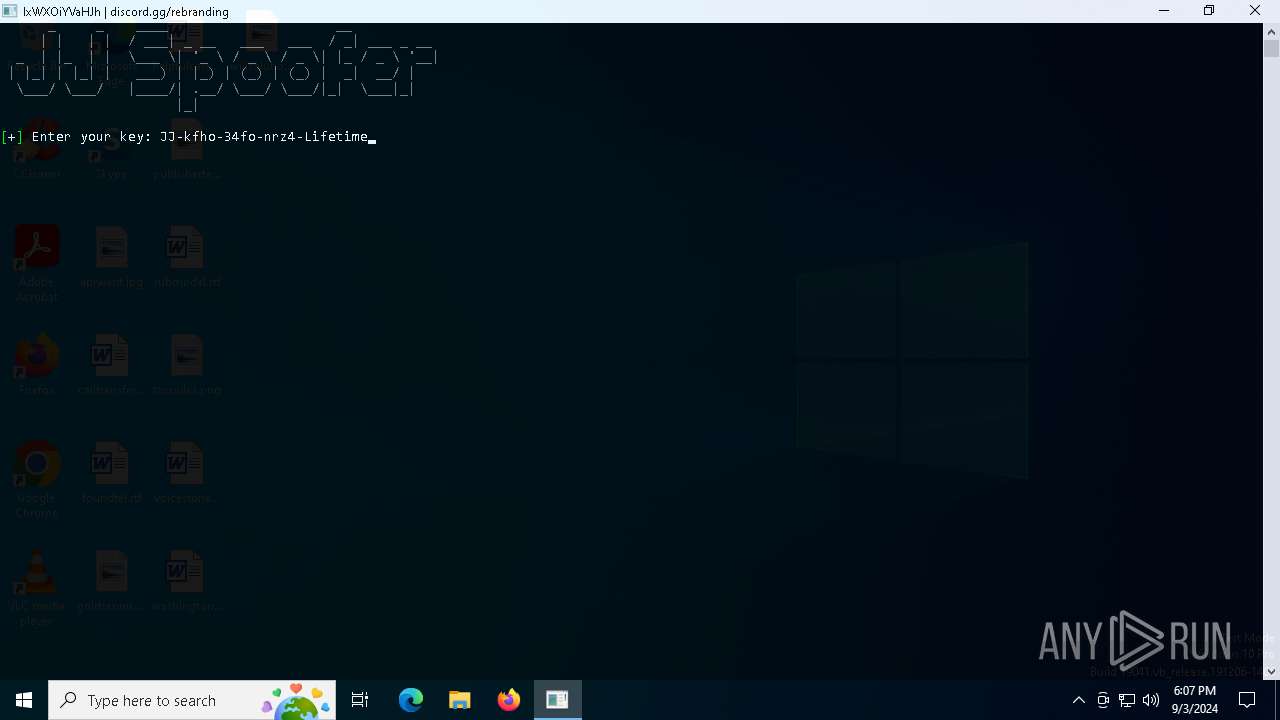
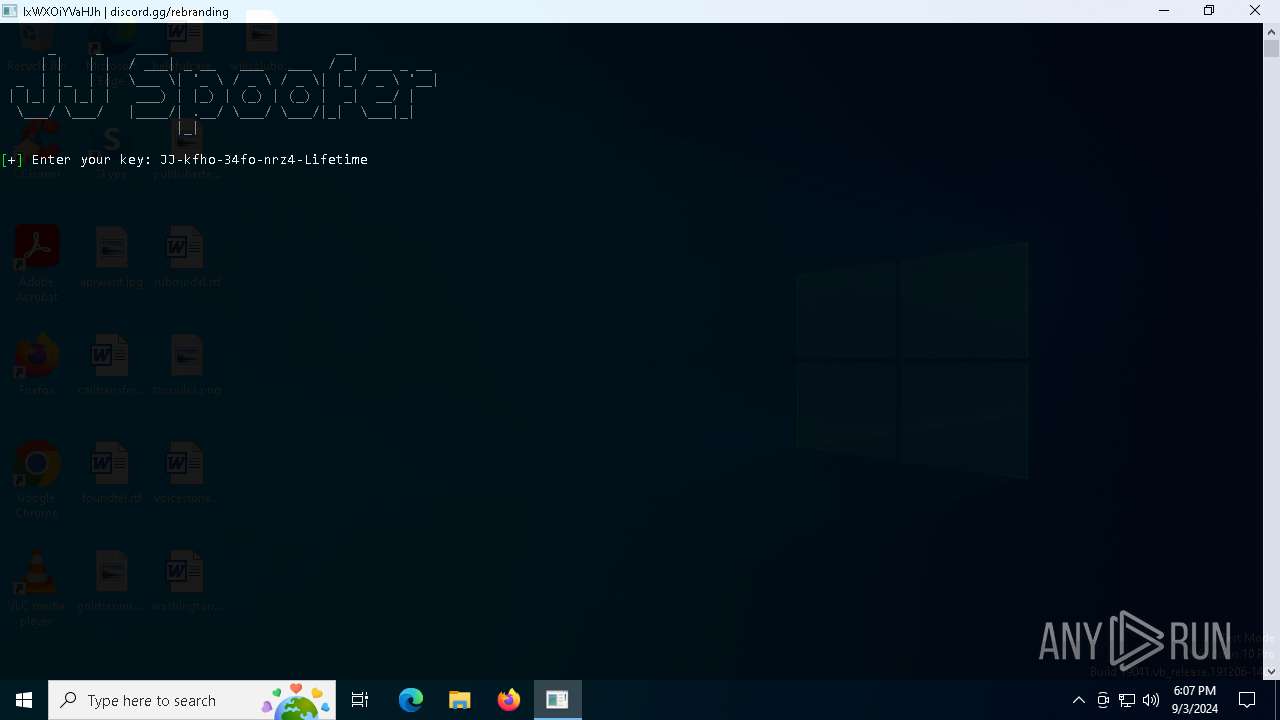
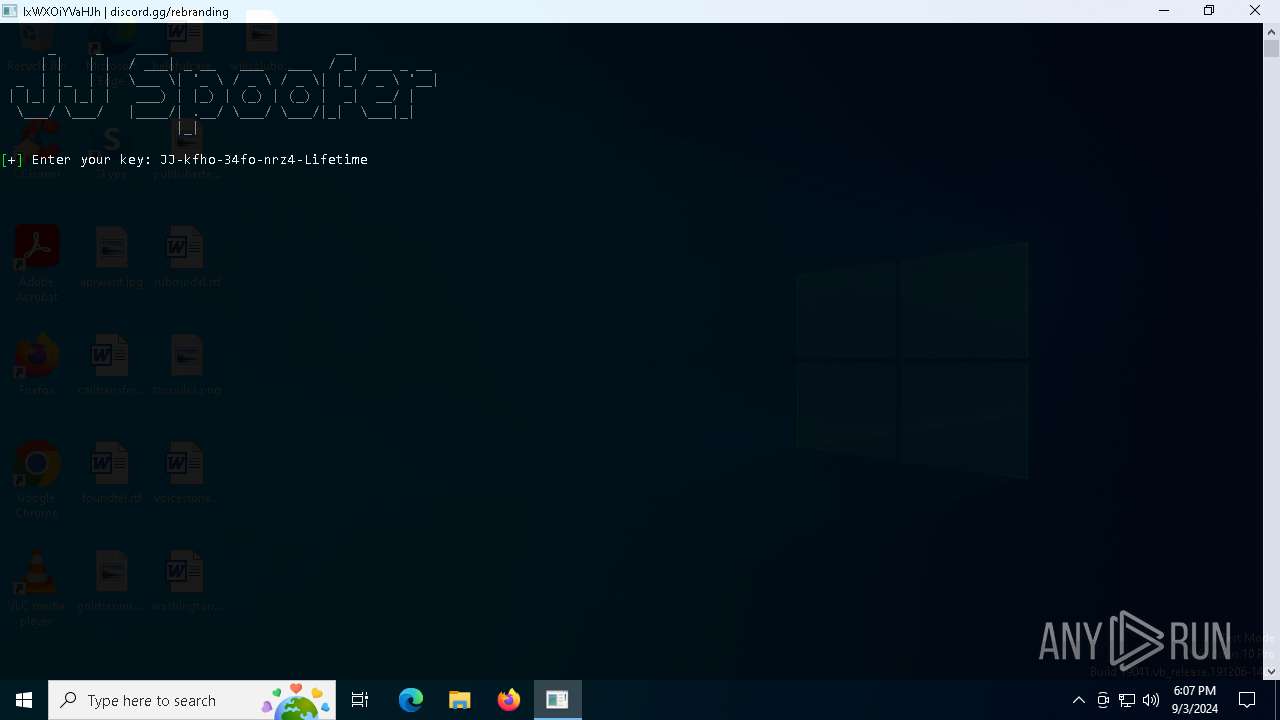
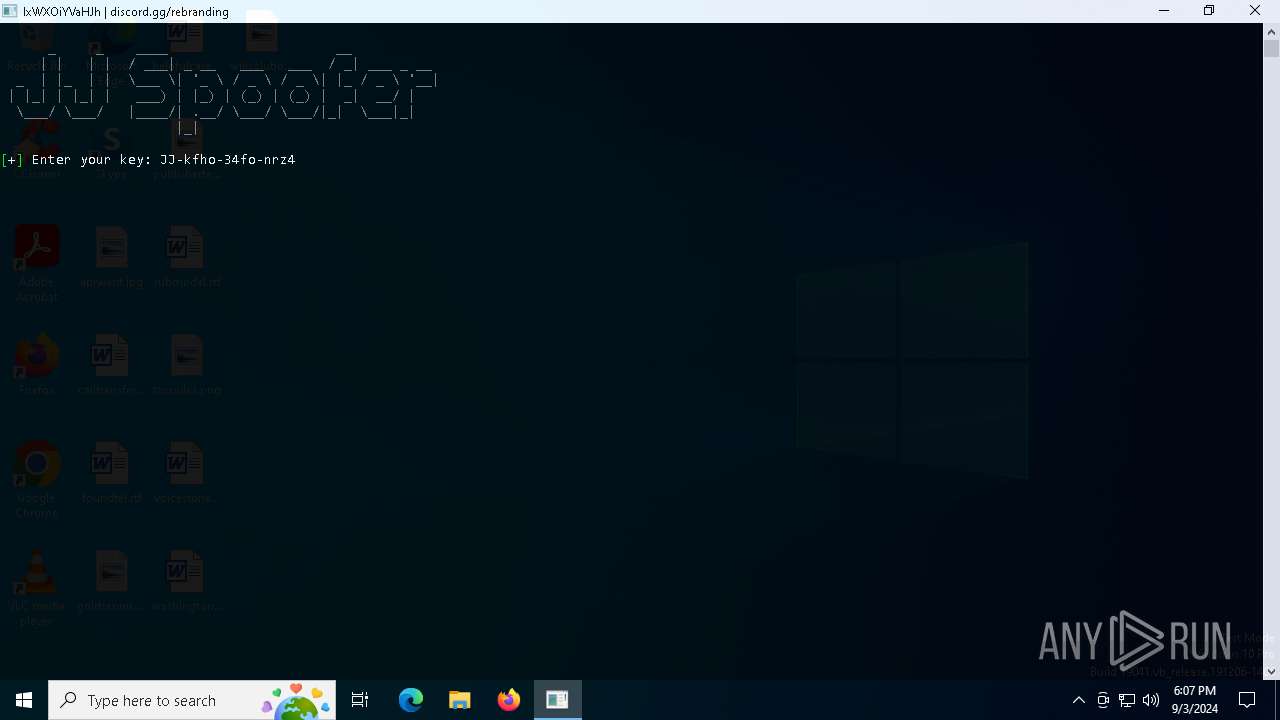
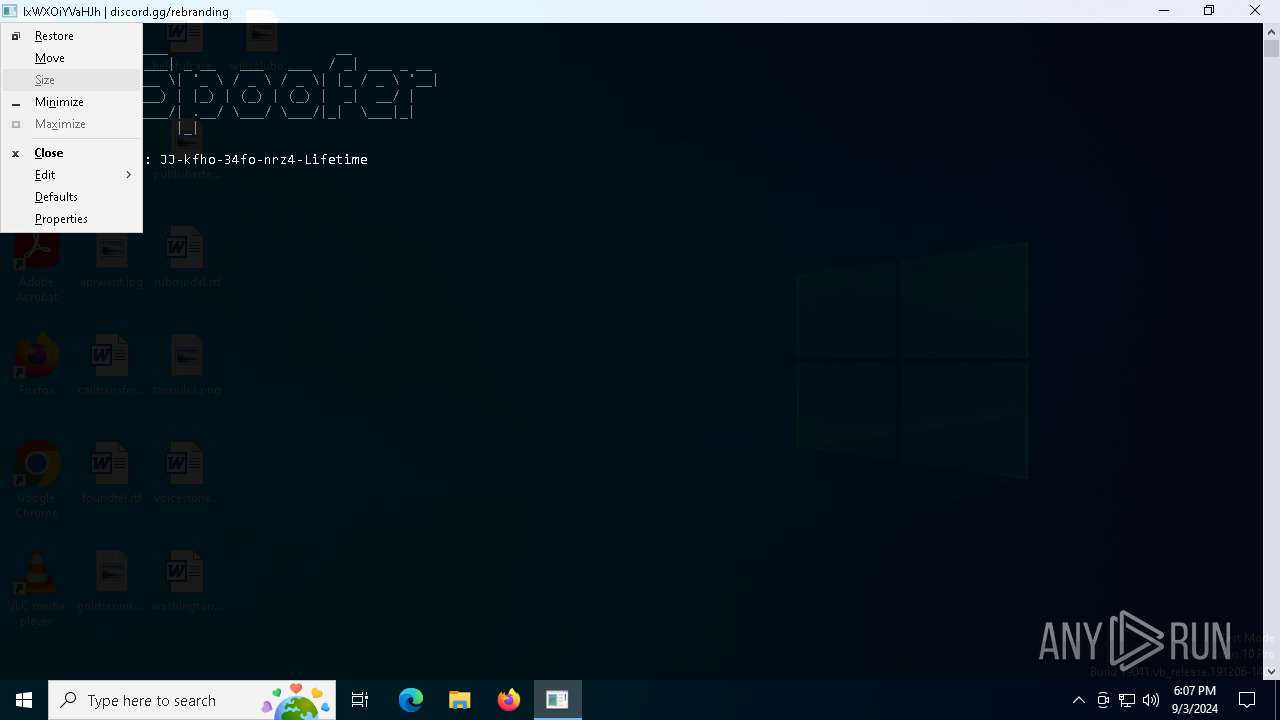
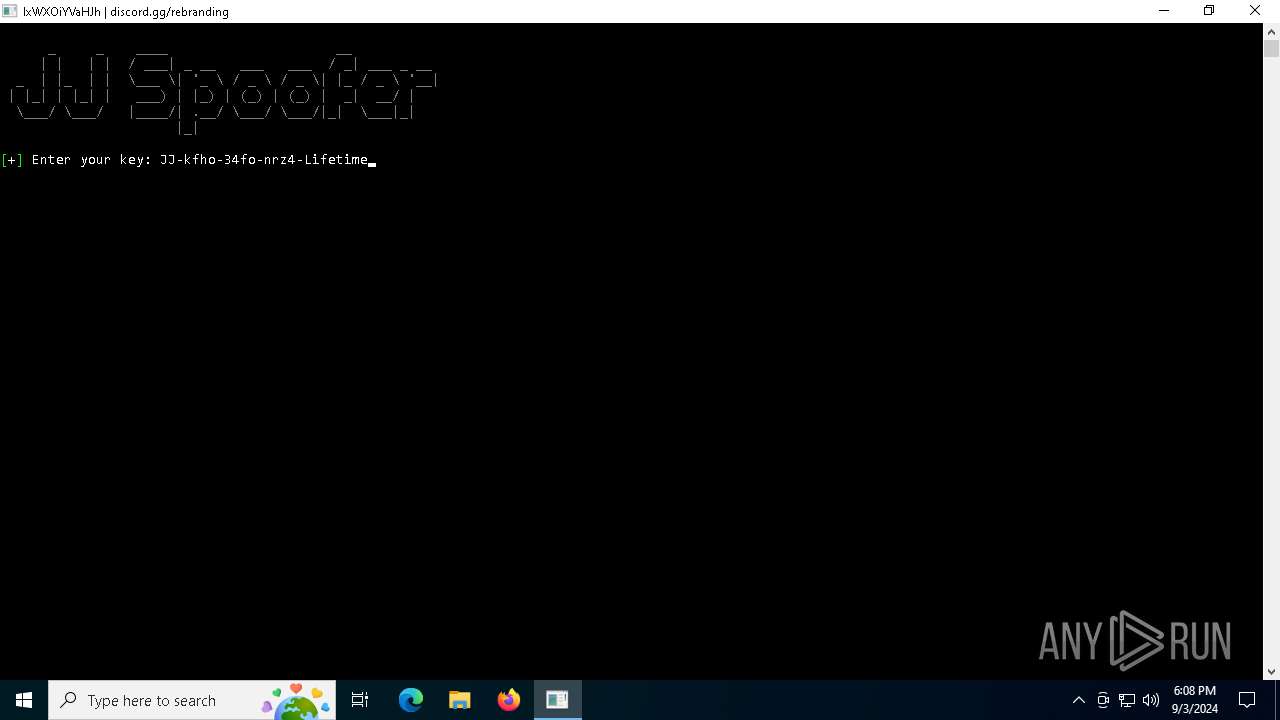
| File name: | JJ-Spoofer.exe |
| Full analysis: | https://app.any.run/tasks/b498e7d2-b2be-46db-95af-411edf9037bf |
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2024, 18:05:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 988715DB3572C72F239E1533E4F4E1F5 |
| SHA1: | B84003FFF7A01FADC37B055B589D599CD50ED7AD |
| SHA256: | B05F2E8CED41EC1900208B80CC016E8534E16F2775D7A2AD3E534743F0A63619 |
| SSDEEP: | 98304:PLBOVZLT0/96PN+eWkxaohh2vKBfPzm3SC5gGpRv4ib8V6AMvODleS9kP5vn62tb:aJxXmIbJDYu |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- JJ-Spoofer.exe (PID: 5768)
INFO
Creates files in the program directory
- JJ-Spoofer.exe (PID: 5768)
Reads the computer name
- JJ-Spoofer.exe (PID: 5768)
Checks supported languages
- JJ-Spoofer.exe (PID: 5768)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 6936)
Reads the software policy settings
- slui.exe (PID: 2724)
- slui.exe (PID: 3112)
Checks proxy server information
- slui.exe (PID: 3112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:08:12 14:22:59+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.38 |
| CodeSize: | 761344 |
| InitializedDataSize: | 218112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9dfeda |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
138
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | find /i /v "certutil" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2520 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2724 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3112 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
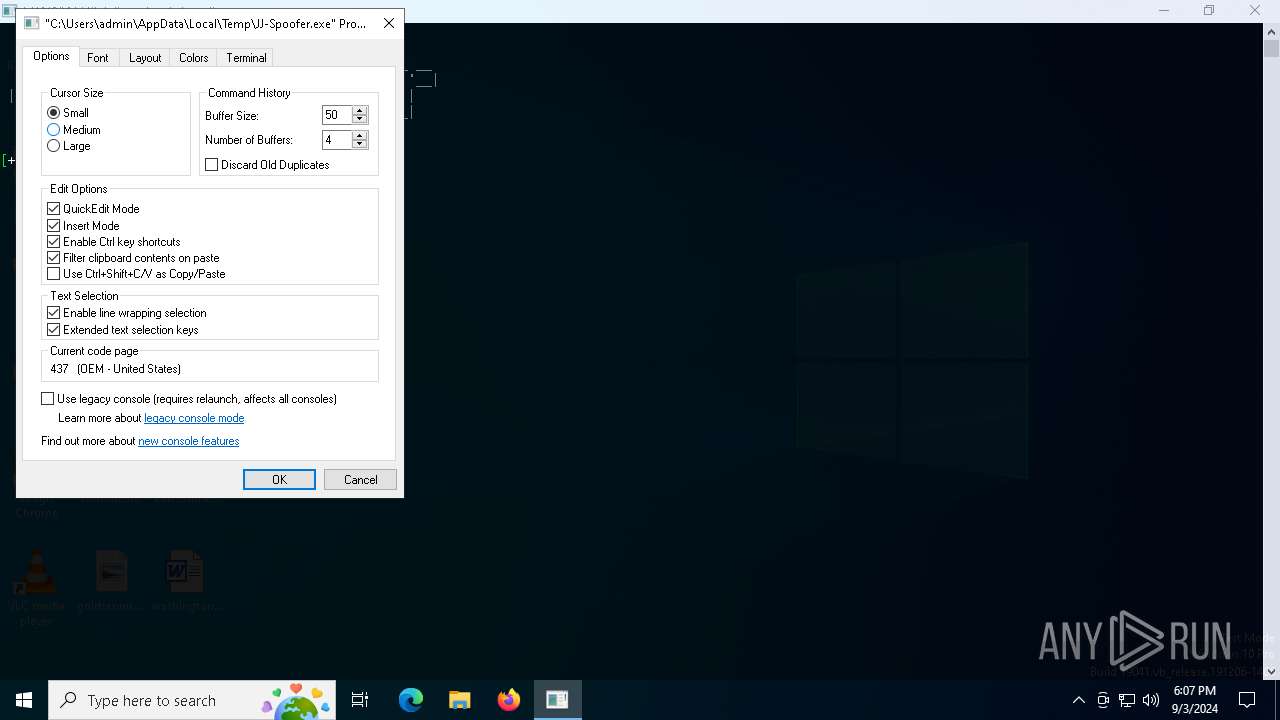
| 5124 | "C:\Users\admin\AppData\Local\Temp\JJ-Spoofer.exe" | C:\Users\admin\AppData\Local\Temp\JJ-Spoofer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
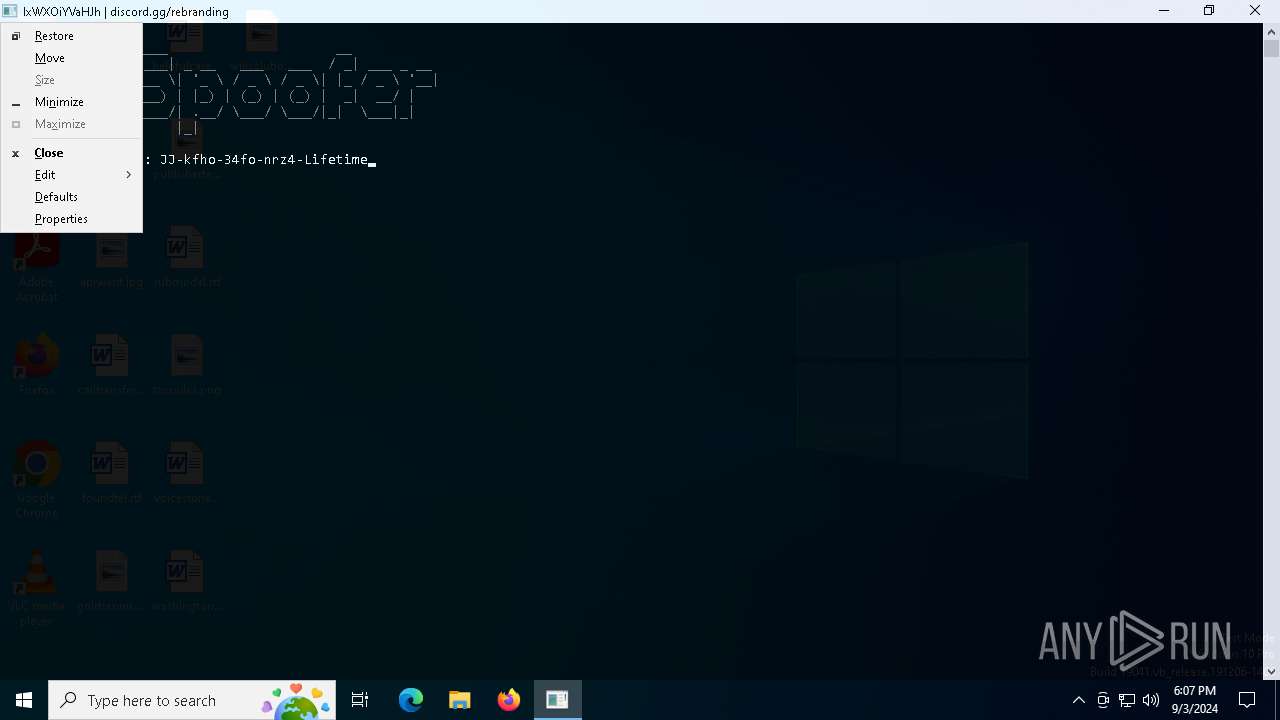
| 5244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | JJ-Spoofer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5492 | C:\WINDOWS\system32\cmd.exe /c certutil -hashfile "C:\Users\admin\AppData\Local\Temp\JJ-Spoofer.exe" MD5 | find /i /v "md5" | find /i /v "certutil" | C:\Windows\System32\cmd.exe | — | JJ-Spoofer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5768 | "C:\Users\admin\AppData\Local\Temp\JJ-Spoofer.exe" | C:\Users\admin\AppData\Local\Temp\JJ-Spoofer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6936 | certutil -hashfile "C:\Users\admin\AppData\Local\Temp\JJ-Spoofer.exe" MD5 | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 221
Read events
2 171
Write events
16
Delete events
34
Modification events
| (PID) Process: | (6936) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.1!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_AUTO_UPDATE_CA_REVOCATION | |||
| (PID) Process: | (6936) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.2!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_AUTO_UPDATE_END_REVOCATION | |||
| (PID) Process: | (6936) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.3!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_NO_OCSP_FAILOVER_TO_CRL | |||
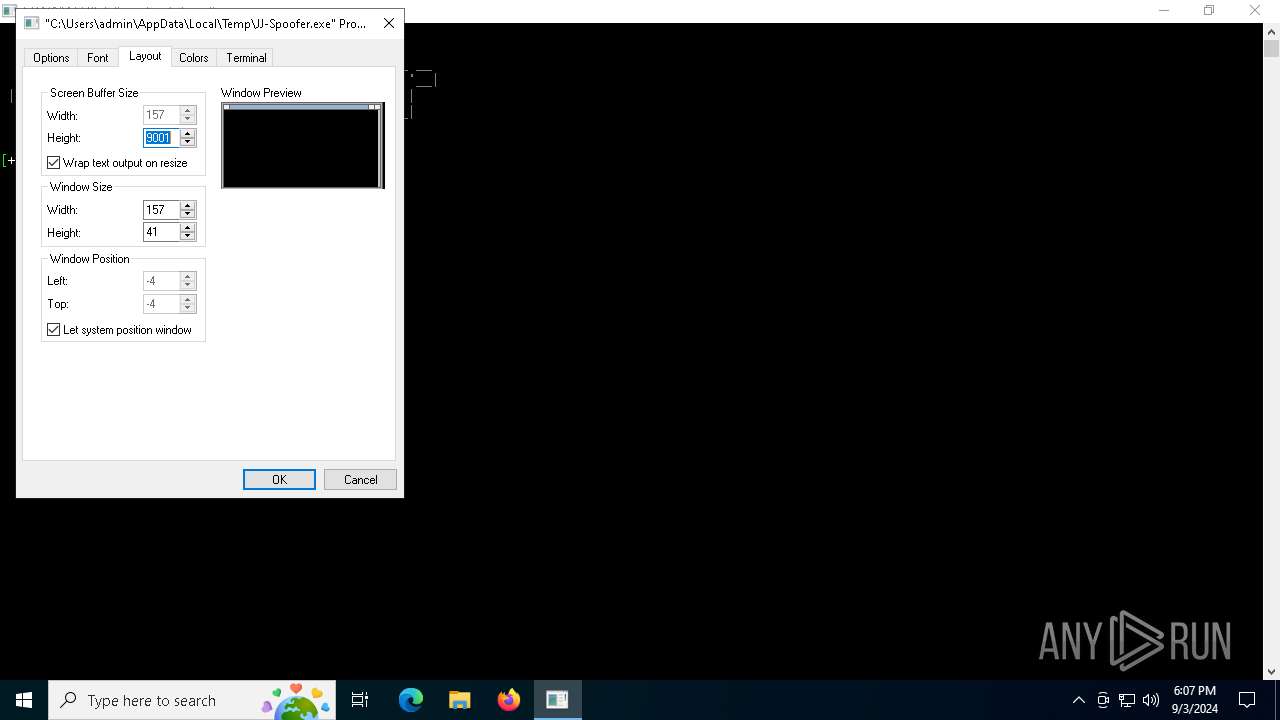
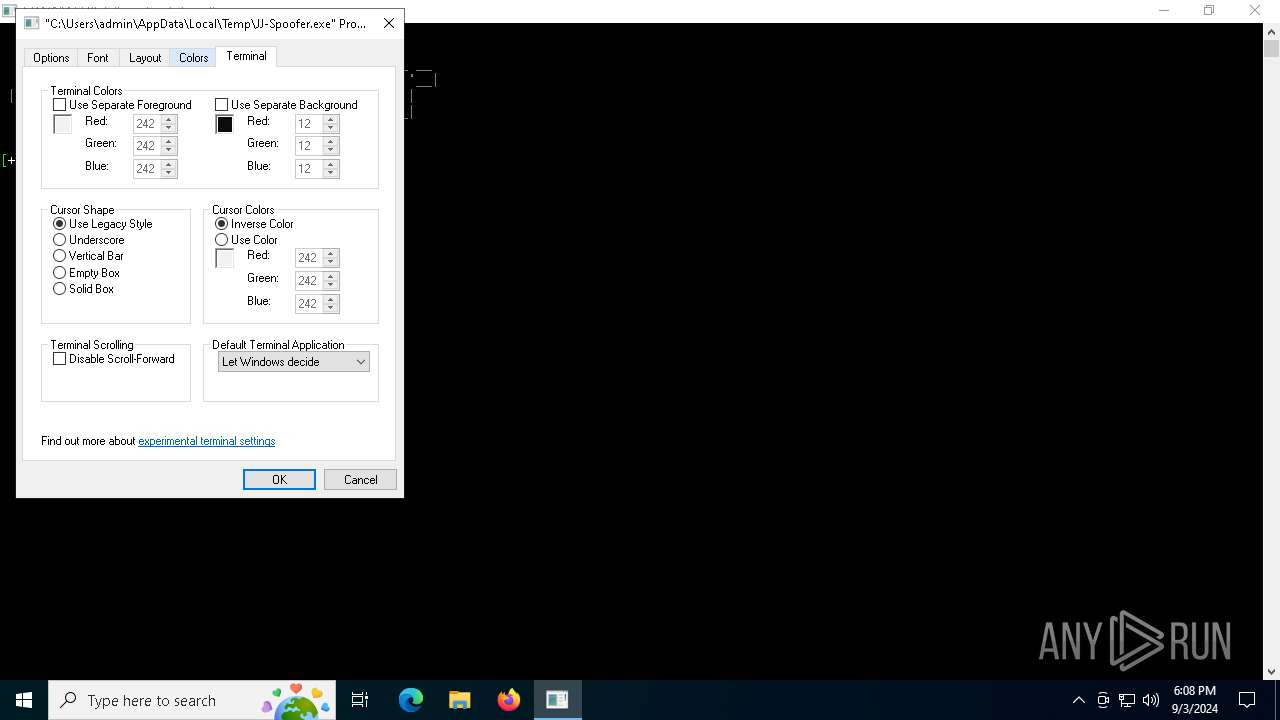
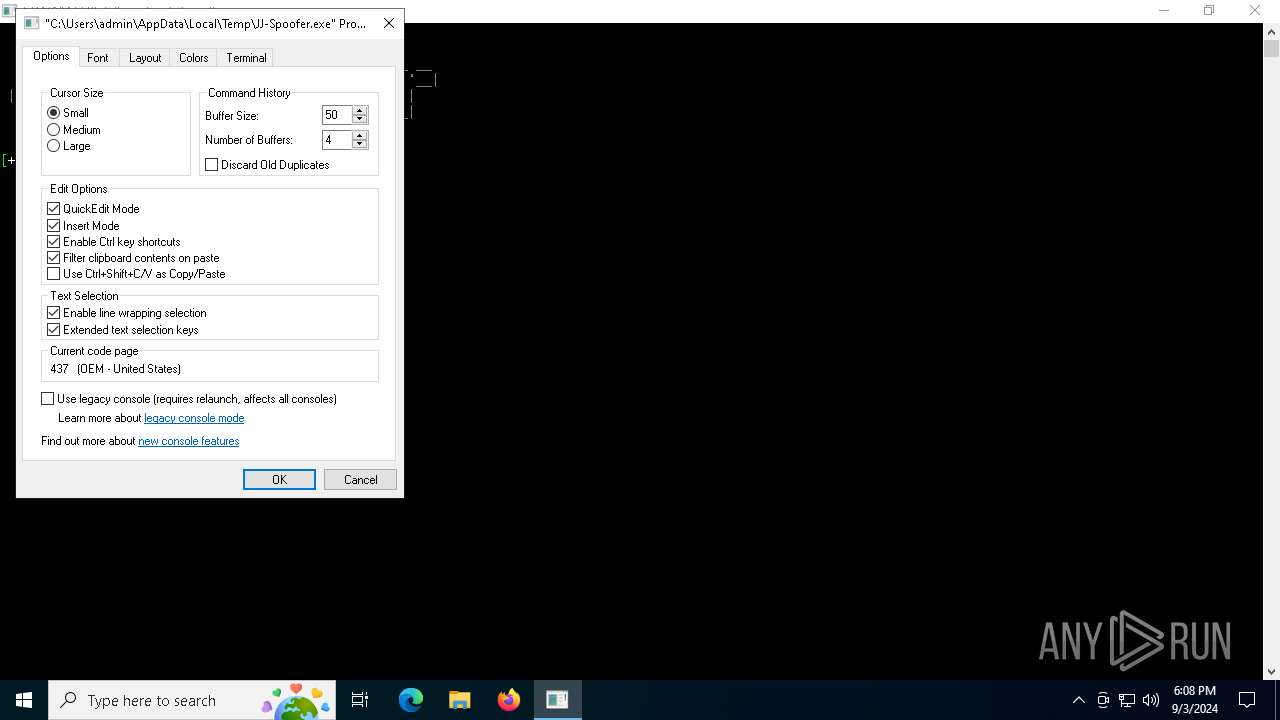
| (PID) Process: | (5244) conhost.exe | Key: | HKEY_CURRENT_USER\Console\%%Startup |
| Operation: | write | Name: | DelegationConsole |
Value: {00000000-0000-0000-0000-000000000000} | |||
| (PID) Process: | (5244) conhost.exe | Key: | HKEY_CURRENT_USER\Console\%%Startup |
| Operation: | write | Name: | DelegationTerminal |
Value: {00000000-0000-0000-0000-000000000000} | |||
| (PID) Process: | (5244) conhost.exe | Key: | HKEY_CURRENT_USER\Console |
| Operation: | write | Name: | CurrentPage |
Value: 0 | |||
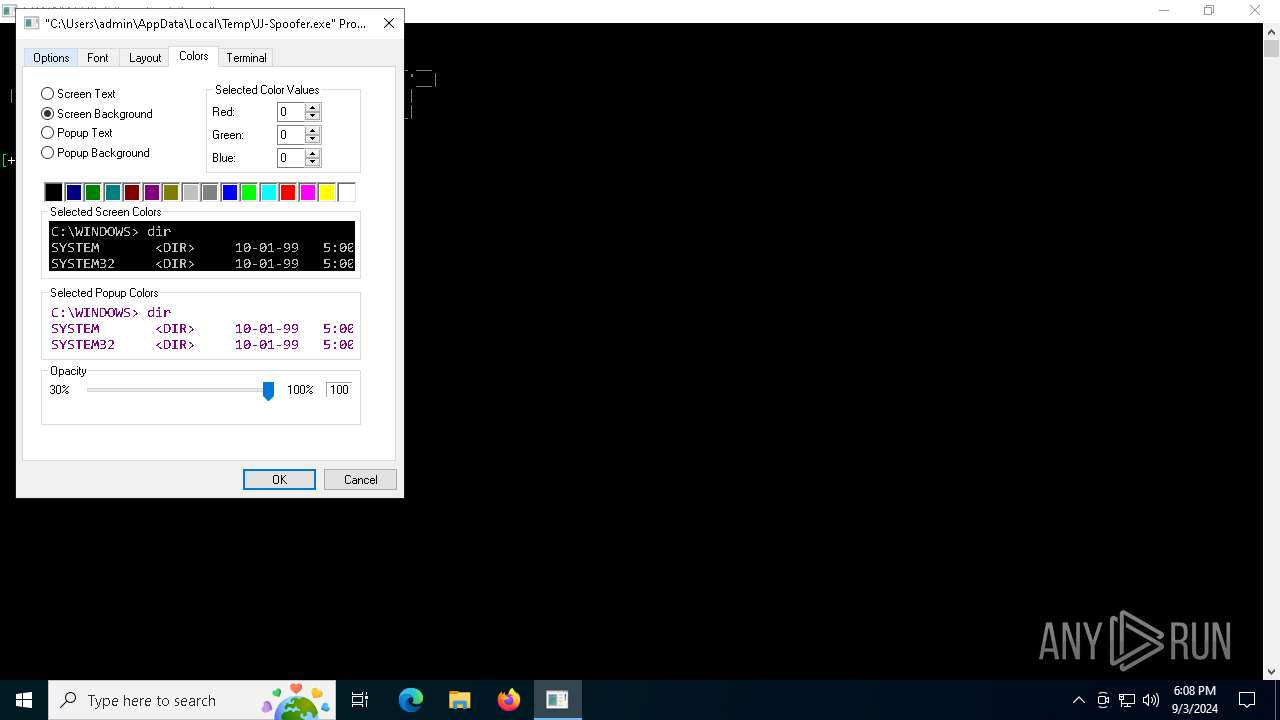
| (PID) Process: | (5244) conhost.exe | Key: | HKEY_CURRENT_USER\Console\C:_Users_admin_AppData_Local_Temp_JJ-Spoofer.exe |
| Operation: | delete value | Name: | ScreenColors |
Value: | |||
| (PID) Process: | (5244) conhost.exe | Key: | HKEY_CURRENT_USER\Console\C:_Users_admin_AppData_Local_Temp_JJ-Spoofer.exe |
| Operation: | delete value | Name: | PopupColors |
Value: | |||
| (PID) Process: | (5244) conhost.exe | Key: | HKEY_CURRENT_USER\Console\C:_Users_admin_AppData_Local_Temp_JJ-Spoofer.exe |
| Operation: | delete value | Name: | ColorTable00 |
Value: | |||
| (PID) Process: | (5244) conhost.exe | Key: | HKEY_CURRENT_USER\Console\C:_Users_admin_AppData_Local_Temp_JJ-Spoofer.exe |
| Operation: | delete value | Name: | ColorTable01 |
Value: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
30
DNS requests
18
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2968 | svchost.exe | GET | 304 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
5128 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5128 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3296 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6256 | RUXIMICS.exe | 52.191.219.104:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2120 | MoUsoCoreWorker.exe | 52.191.219.104:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1356 | svchost.exe | 52.191.219.104:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
5768 | JJ-Spoofer.exe | 172.67.72.57:443 | keyauth.win | CLOUDFLARENET | US | malicious |
1356 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3296 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3296 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
keyauth.win |
| malicious |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
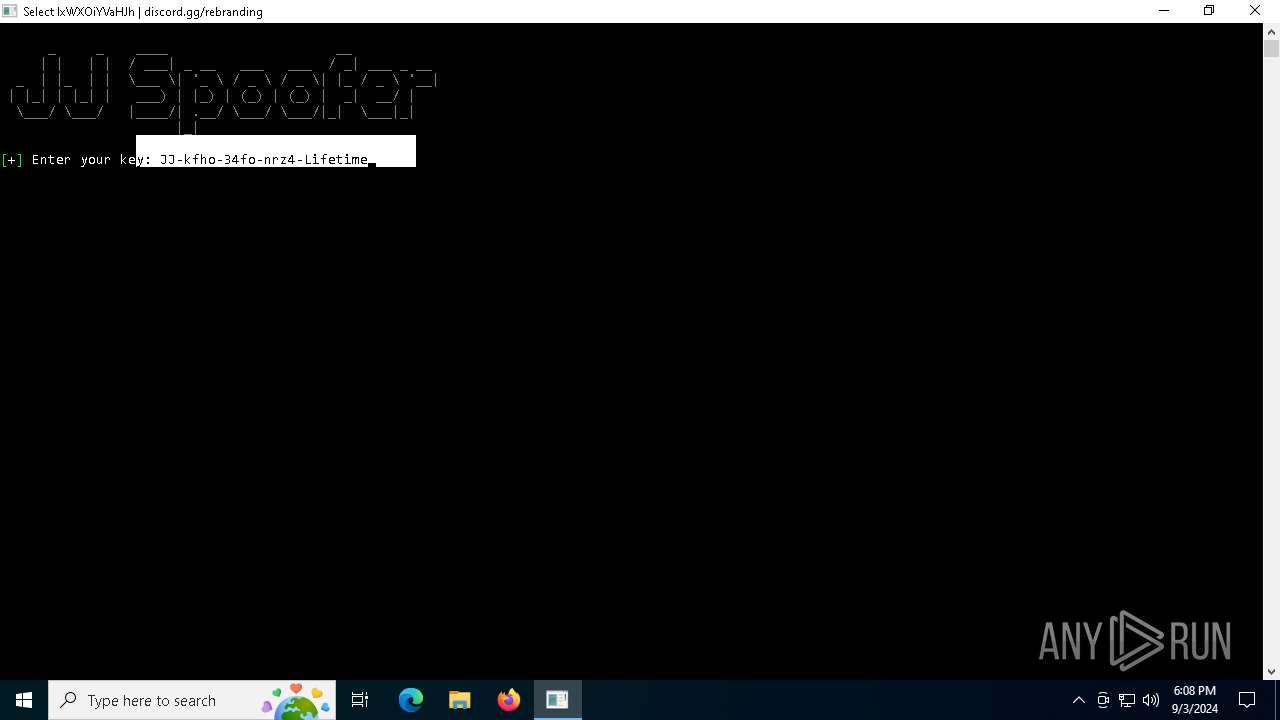
2256 | svchost.exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain in DNS Lookup (keyauth .win) |
5768 | JJ-Spoofer.exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain (keyauth .win) in TLS SNI |