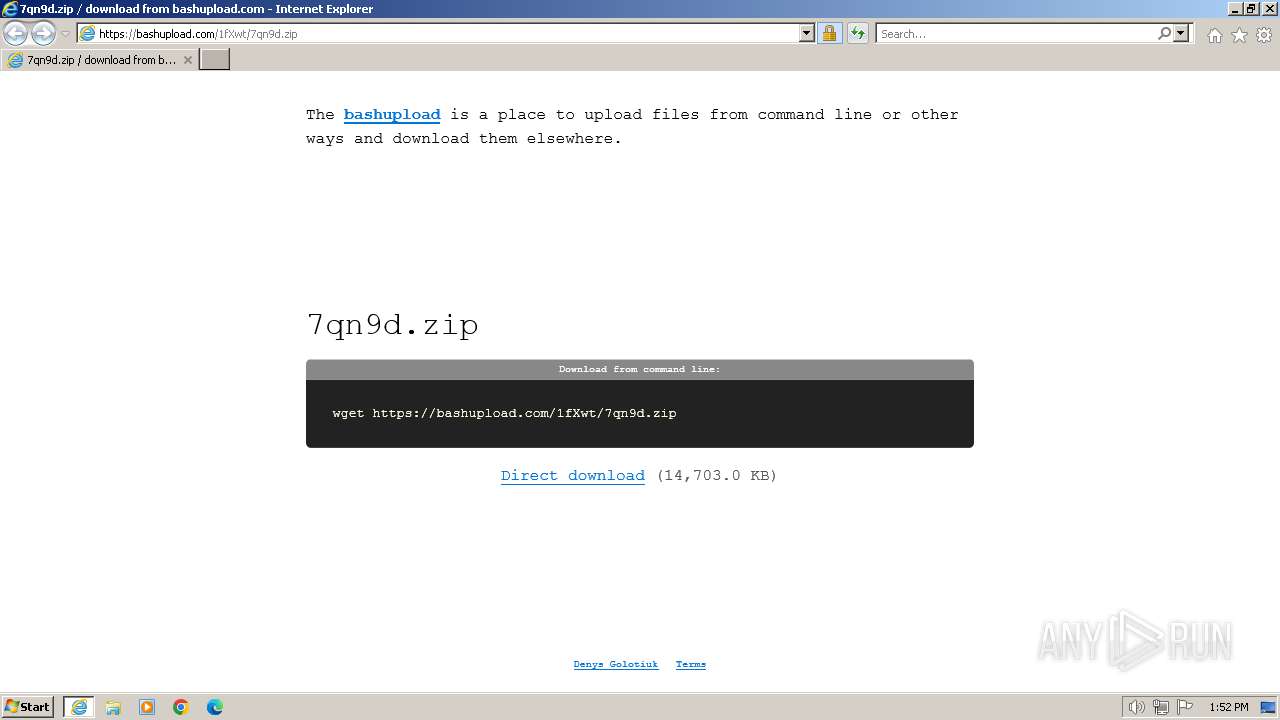
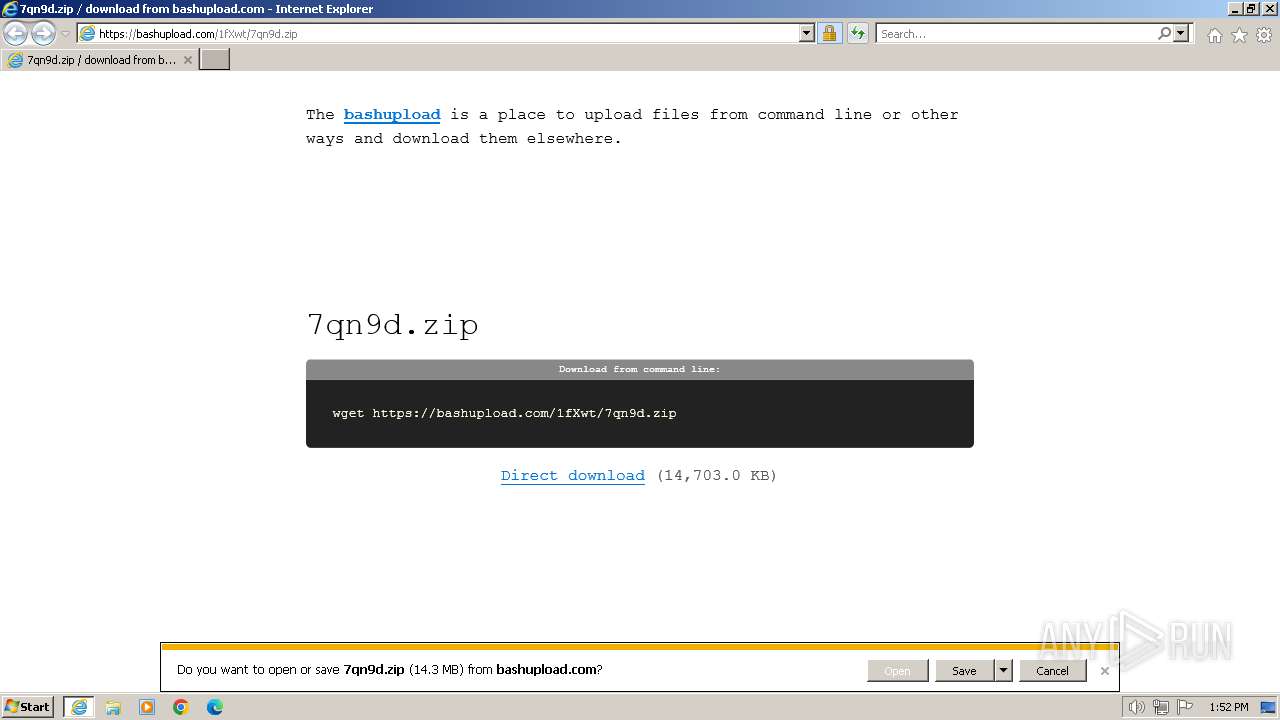
| URL: | https://bashupload.com/1fXwt/7qn9d.zip |
| Full analysis: | https://app.any.run/tasks/395b3f52-3d7b-47c2-97a4-a560410db23f |
| Verdict: | Malicious activity |
| Analysis date: | January 12, 2024, 13:52:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DF3751B6C84EB9AA274CEF0941838177 |
| SHA1: | CF958AF813E8AB5A55DDA8BEE3F7A88C4BCC1D40 |
| SHA256: | B05E80A6B7AAE6746EF7B288A0F01E9789F51D9B73B910C1E29D3A5A4D2A5AC7 |
| SSDEEP: | 3:N84JfU7wsLcB4:2EM7wGw4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- RidenPowerSupply.exe (PID: 2480)
Process requests binary or script from the Internet
- RidenPowerSupply.exe (PID: 2480)
Process drops legitimate windows executable
- WinRAR.exe (PID: 1736)
INFO
Reads the computer name
- RidenPowerSupply.exe (PID: 2480)
- wmpnscfg.exe (PID: 1732)
Manual execution by a user
- wmpnscfg.exe (PID: 1732)
The process uses the downloaded file
- iexplore.exe (PID: 116)
- WinRAR.exe (PID: 1736)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1736)
Application launched itself
- iexplore.exe (PID: 116)
Reads Environment values
- RidenPowerSupply.exe (PID: 2480)
Checks supported languages
- RidenPowerSupply.exe (PID: 2480)
- wmpnscfg.exe (PID: 1732)
Reads the machine GUID from the registry
- RidenPowerSupply.exe (PID: 2480)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://bashupload.com/1fXwt/7qn9d.zip" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
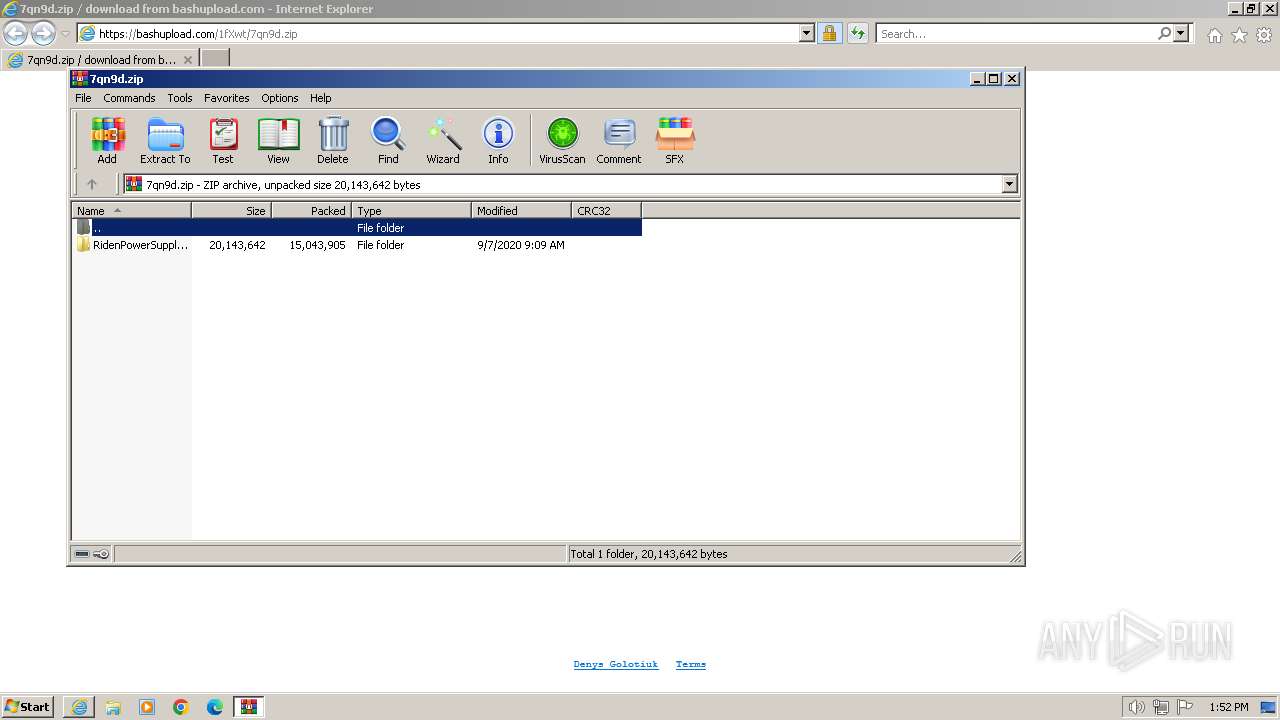
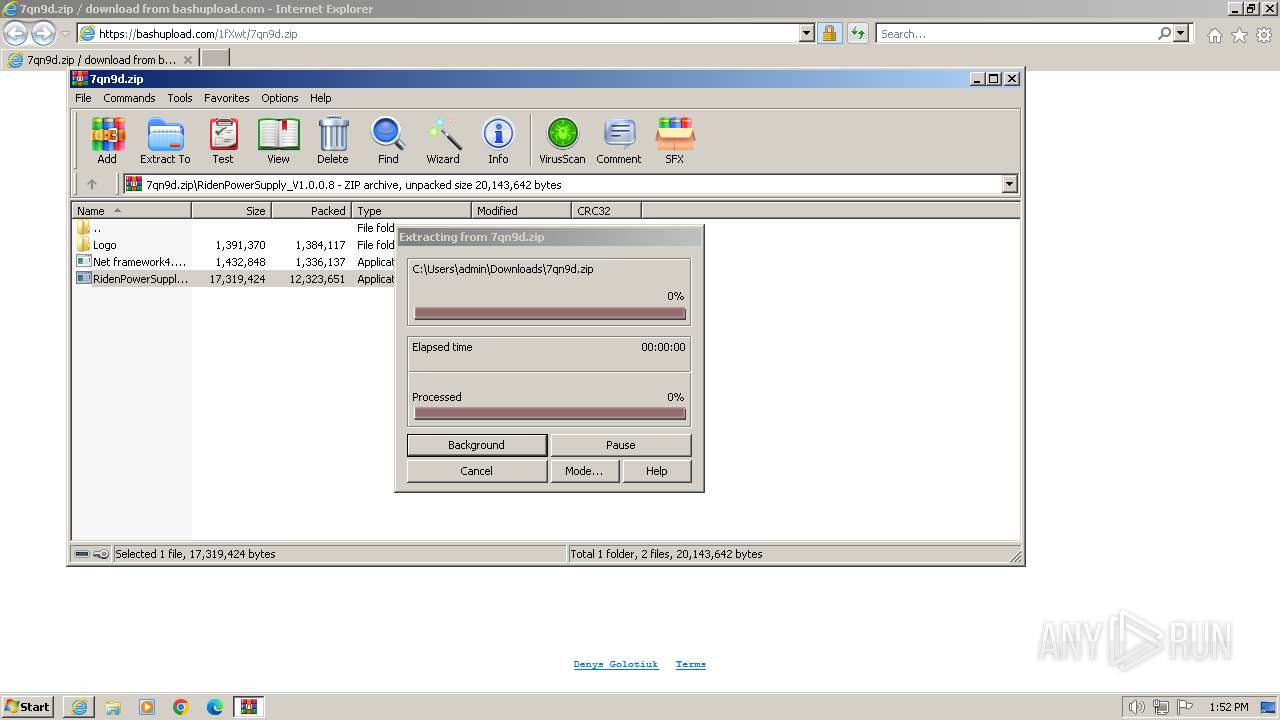
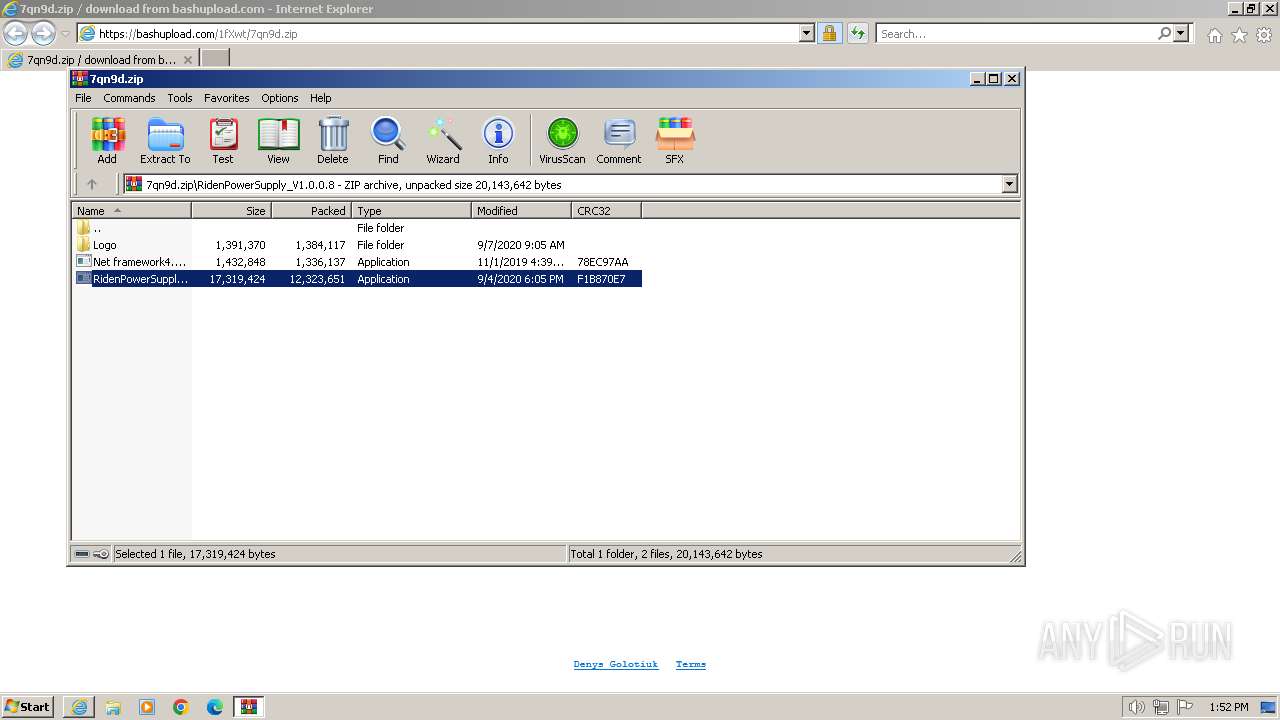
| 1736 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\7qn9d.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:116 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
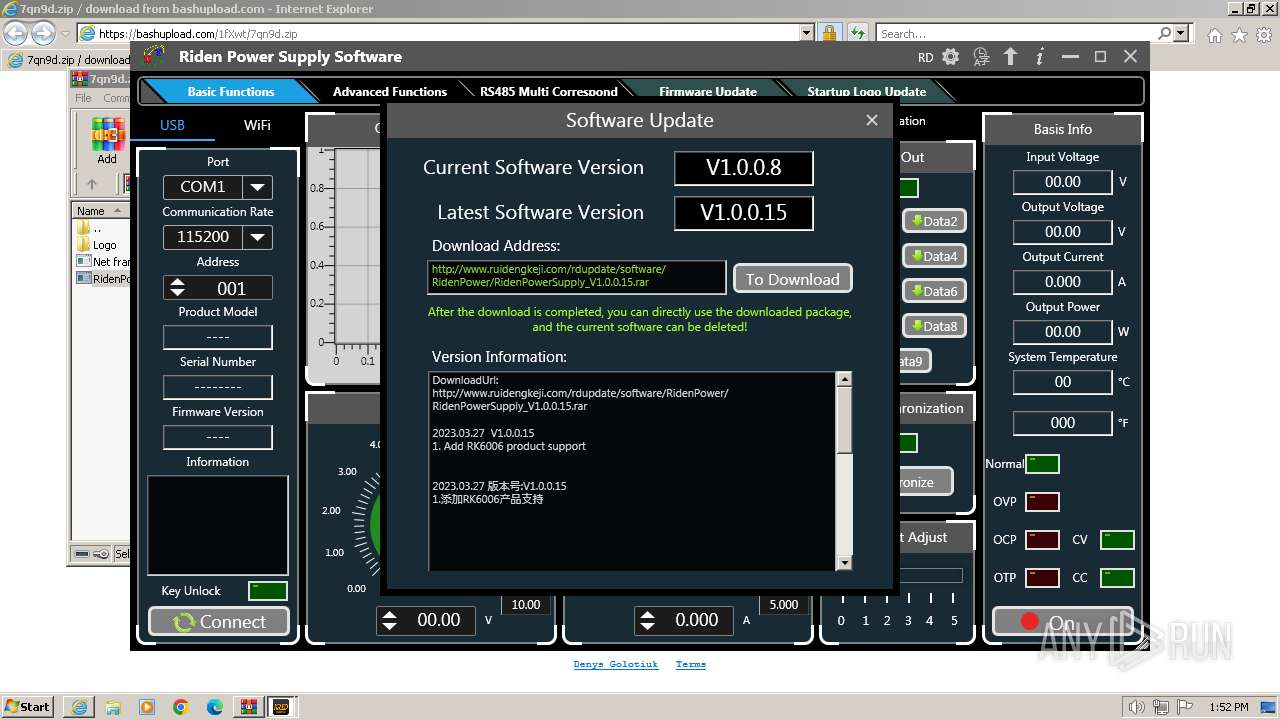
| 2480 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1736.3246\RidenPowerSupply_V1.0.0.8\RidenPowerSupply.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1736.3246\RidenPowerSupply_V1.0.0.8\RidenPowerSupply.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RidenPowerSupply Exit code: 0 Version: 1.0.0.8 Modules
| |||||||||||||||
Total events
20 989
Read events
20 891
Write events
94
Delete events
4
Modification events
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
19
Text files
58
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF9C4.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F66B4FB859E2F94D27A9C5170952F3A5 | binary | |
MD5:705CC60C256451D6ABAFAF4C502B82ED | SHA256:F7F8D8A5F2591E89194531F4148331F83618BE41EAB83D292F7D00DC6C1D65F5 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\7qn9d[1].htm | html | |
MD5:8E6867606CC5D3DCAC4298AFFA37FE84 | SHA256:A5F73DA391E24058064C158796457A6632AAEBB8CDE8363694FB517BD9406AD2 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\7qn9d[1].zip | compressed | |
MD5:76E18FDCE62A5742F1678BBAB5B8DEE1 | SHA256:C05F72734211E3444FC70EF7FB3361093BDAB782B94AD45ECE40C7145693FF05 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\script[1].js | text | |
MD5:E366D6BE7860F1094CACDE7746B3BEFB | SHA256:C6154E5ECC5C76EA73F91D28ADB6C8ABEBCBFD05D52C80A1F41B7F29AF181E09 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF975.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF9C5.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
21
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2032 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6243fee378382ed7 | unknown | compressed | 4.66 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?68d4da50f383ffdc | unknown | compressed | 65.2 Kb | unknown |
2480 | RidenPowerSupply.exe | GET | 200 | 120.55.56.54:80 | http://www.ruidengkeji.com/rdupdate/software/RidenPower/RidenPower.json | unknown | binary | 949 b | unknown |
116 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
2032 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?608cb4ab6d3f68d3 | unknown | compressed | 65.2 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f6bf34dbb61e71d7 | unknown | compressed | 4.66 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 2.19.105.18:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2032 | iexplore.exe | GET | 200 | 95.101.54.107:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRfkK9mvv05diNH4Pgi3%2BwSNQ%3D%3D | unknown | binary | 503 b | unknown |
116 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?67308e0939100114 | unknown | — | — | unknown |
116 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d8f761b8c0f86c21 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2032 | iexplore.exe | 116.203.186.178:443 | bashupload.com | Hetzner Online GmbH | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2032 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2032 | iexplore.exe | 2.19.105.18:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
2032 | iexplore.exe | 95.101.54.107:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
116 | iexplore.exe | 116.203.186.178:443 | bashupload.com | Hetzner Online GmbH | DE | unknown |
116 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
116 | iexplore.exe | 23.15.178.162:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bashupload.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.ruidengkeji.com |
| unknown |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |