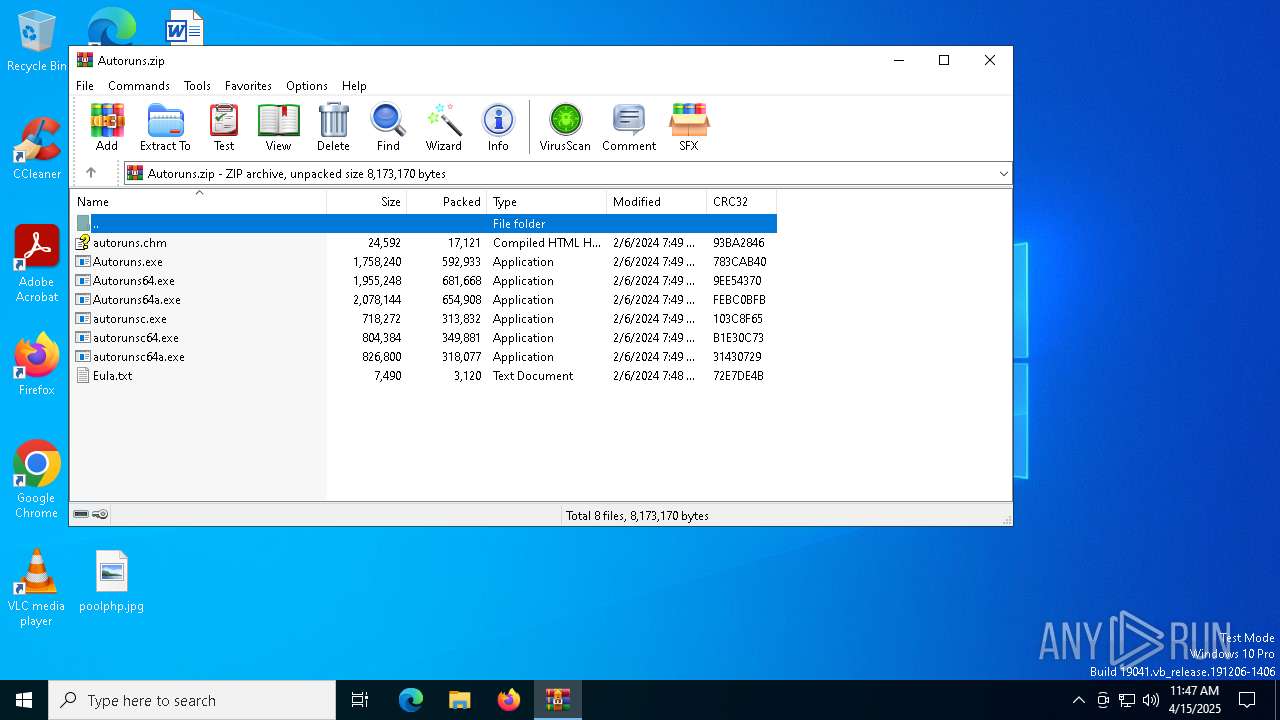
| File name: | Autoruns.zip |
| Full analysis: | https://app.any.run/tasks/ee0c99b6-2c65-4655-abbd-8e1da1521808 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2025, 11:47:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 09AA3A18F9DBF8588B0A3489F5C752F4 |
| SHA1: | 130A744A421CA914F2809685AF8262C468F4177A |
| SHA256: | B04D2AC6DCC287A4B01A9CDC5BD9580A38DF8A3379E03698CF7B888CDAB7EA0F |
| SSDEEP: | 98304:mnE3PEmieumhnfvez4GzcFw9FEz1fnbaSbaqRJx5TkZ4d/9PrZEiQSMes9EmY0zZ:uBCu5ic |
MALICIOUS
No malicious indicators.SUSPICIOUS
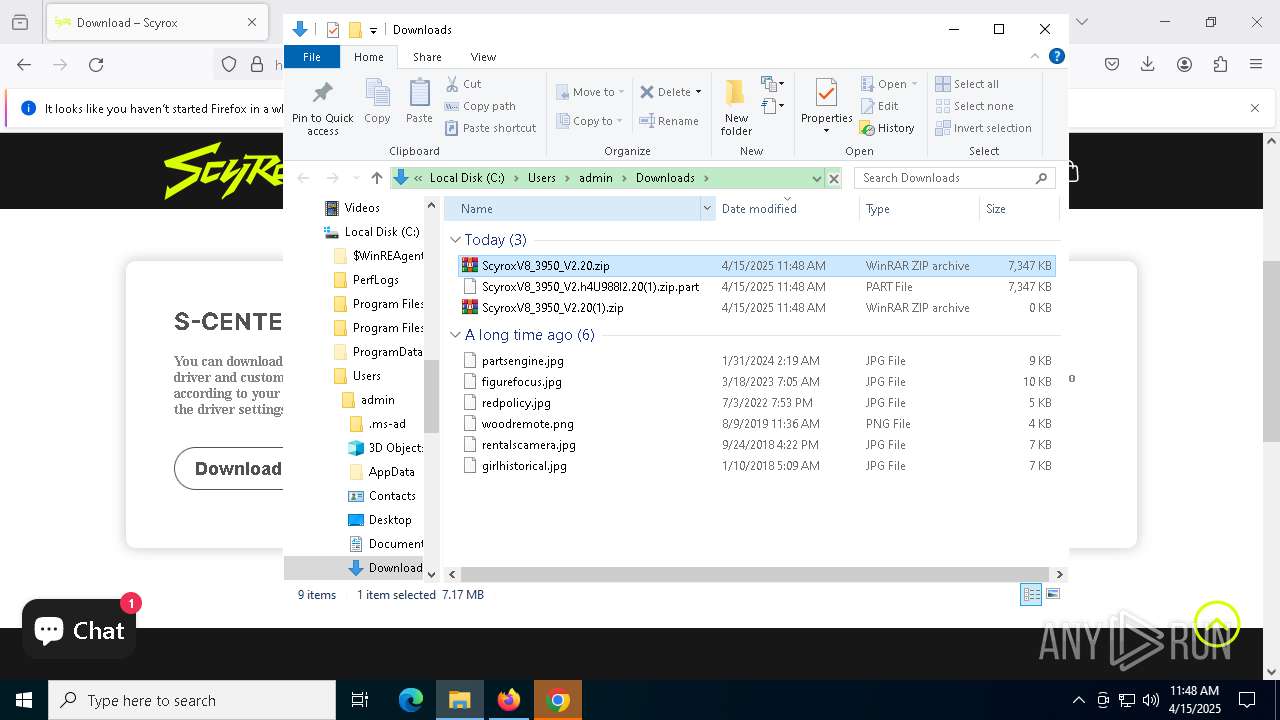
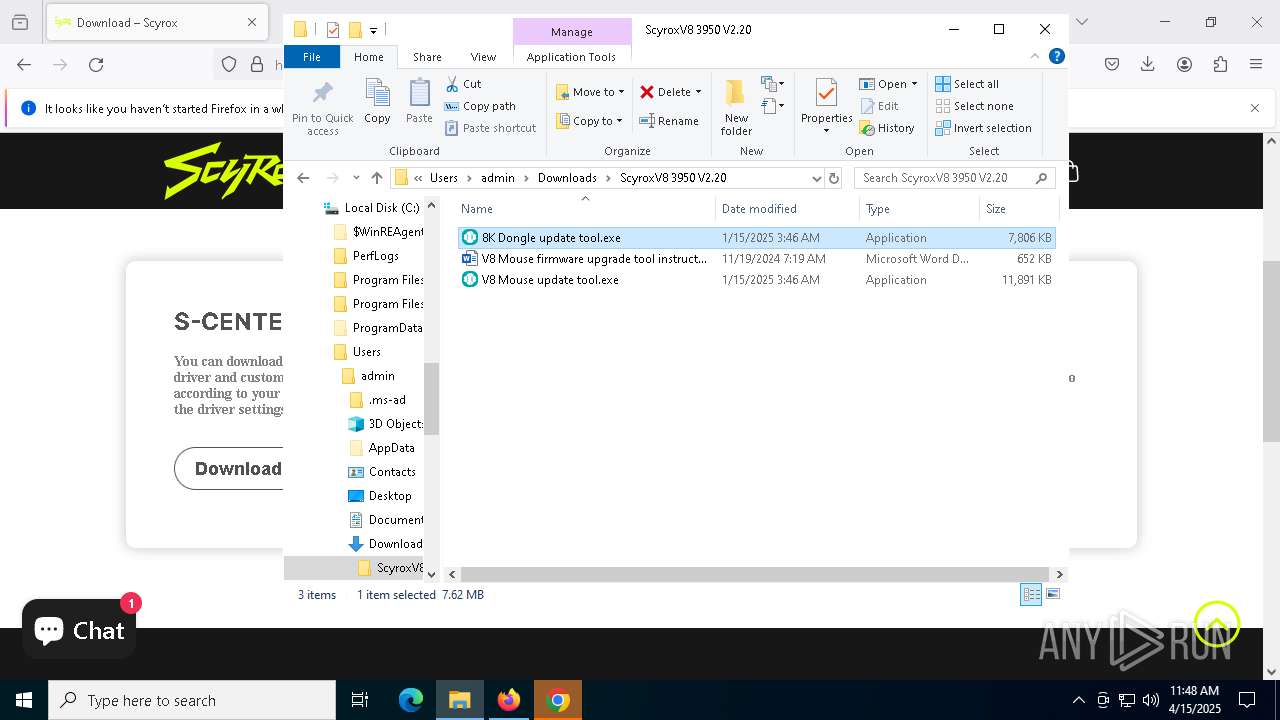
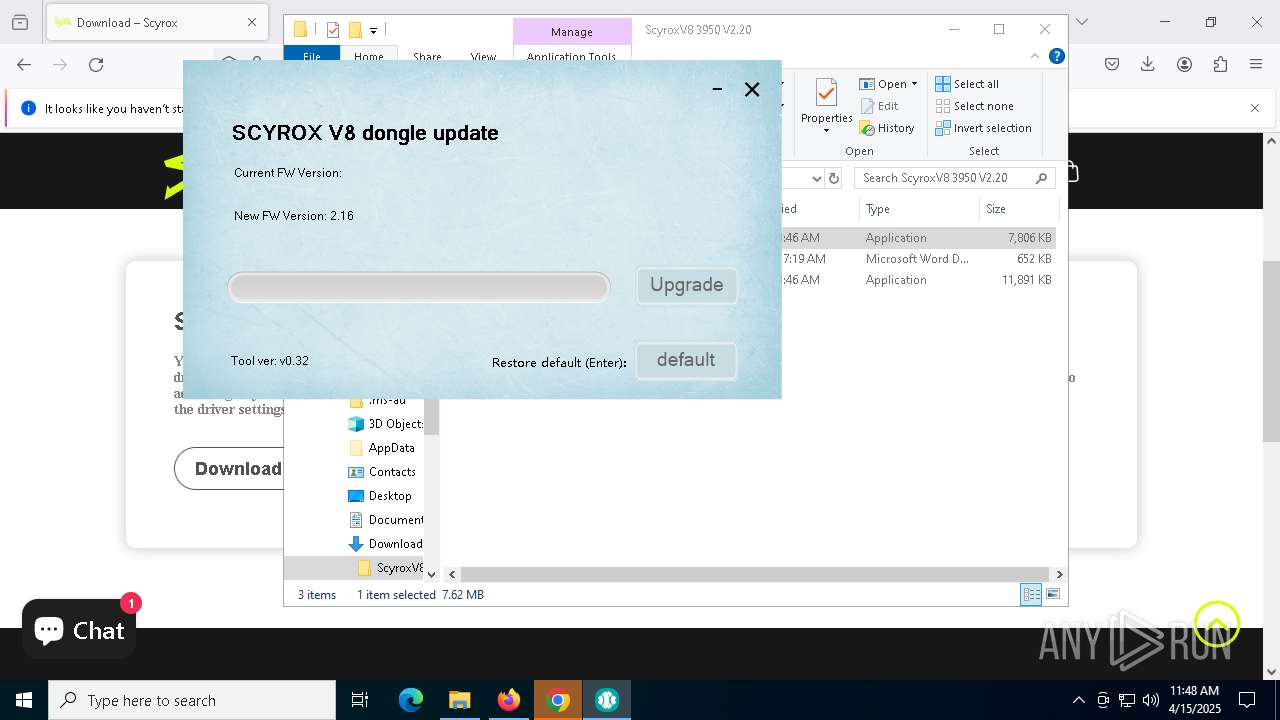
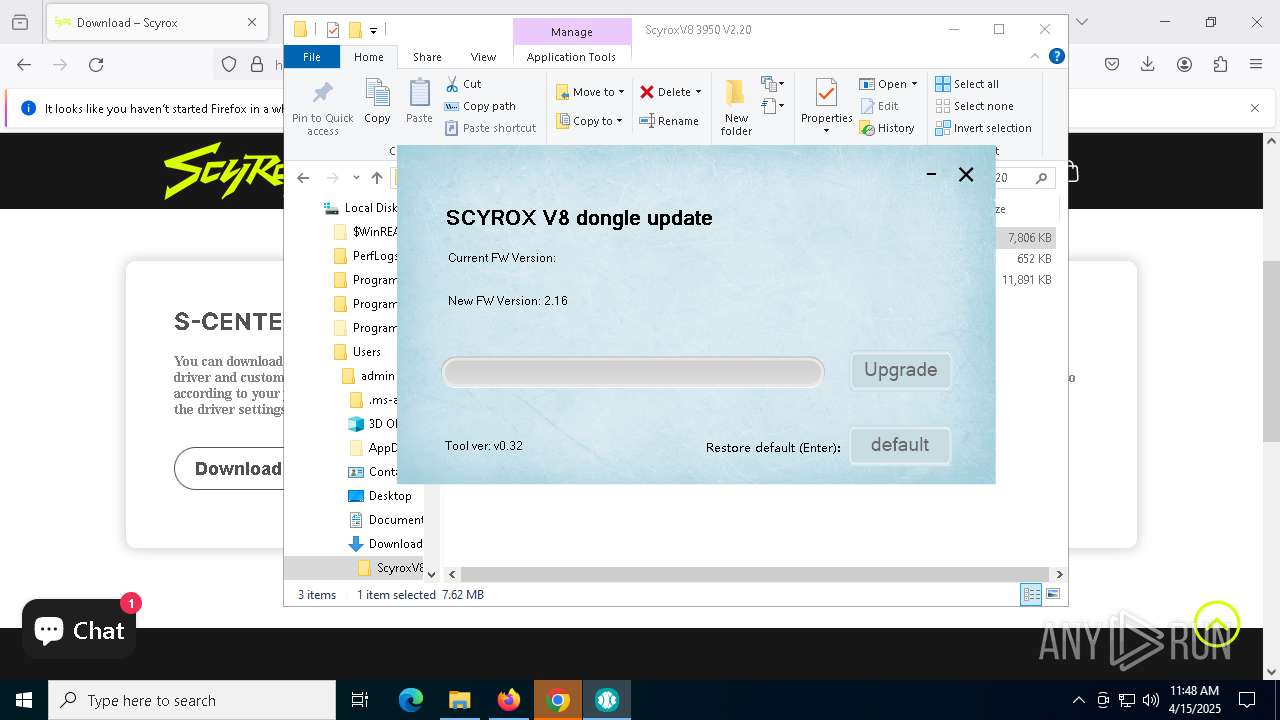
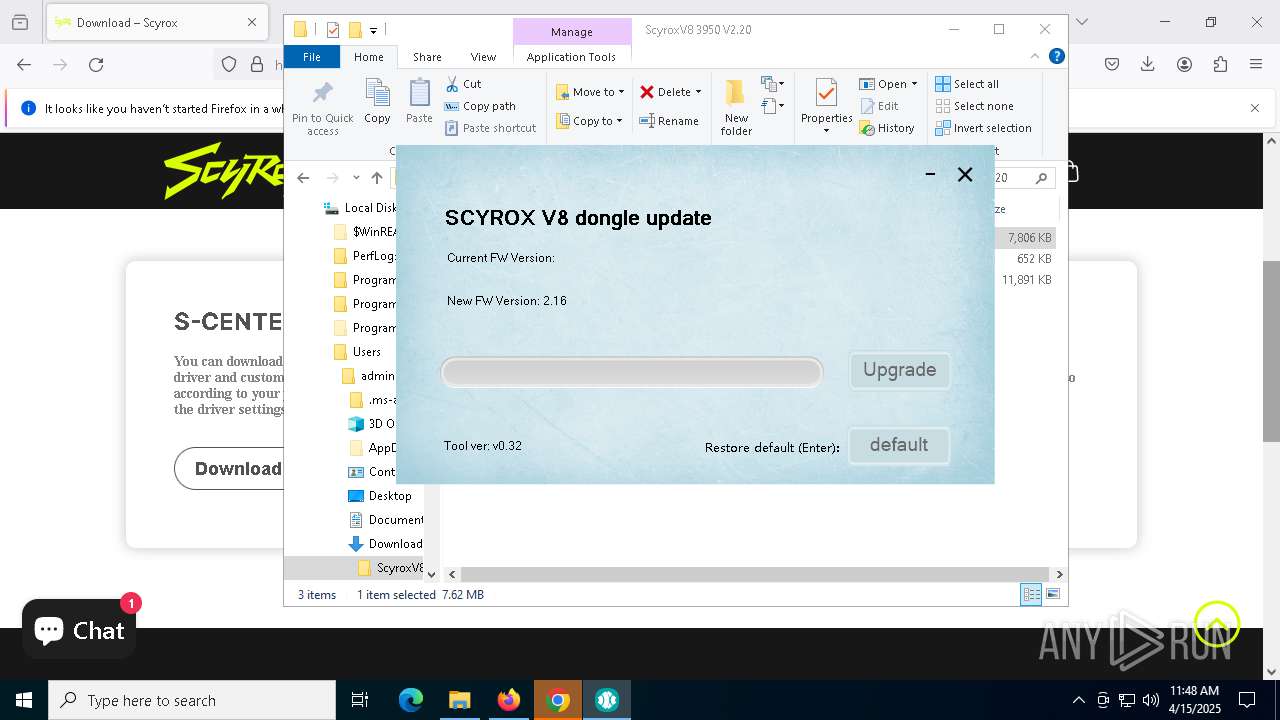
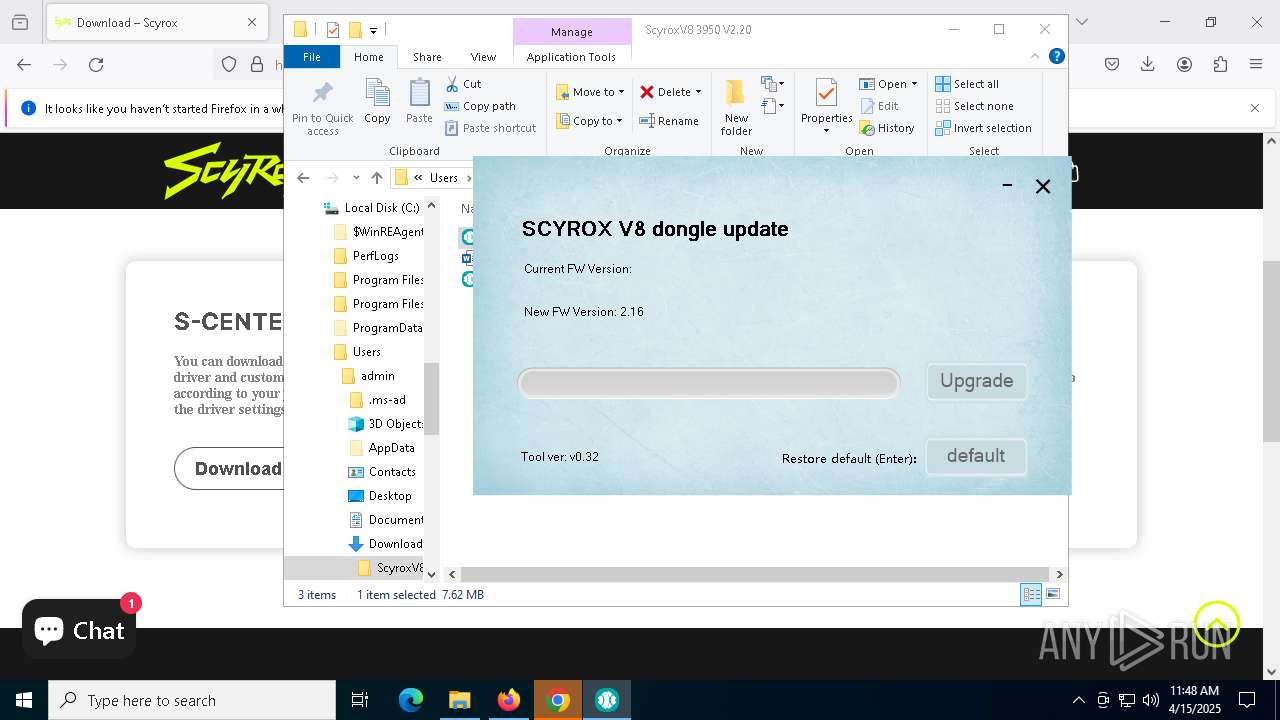
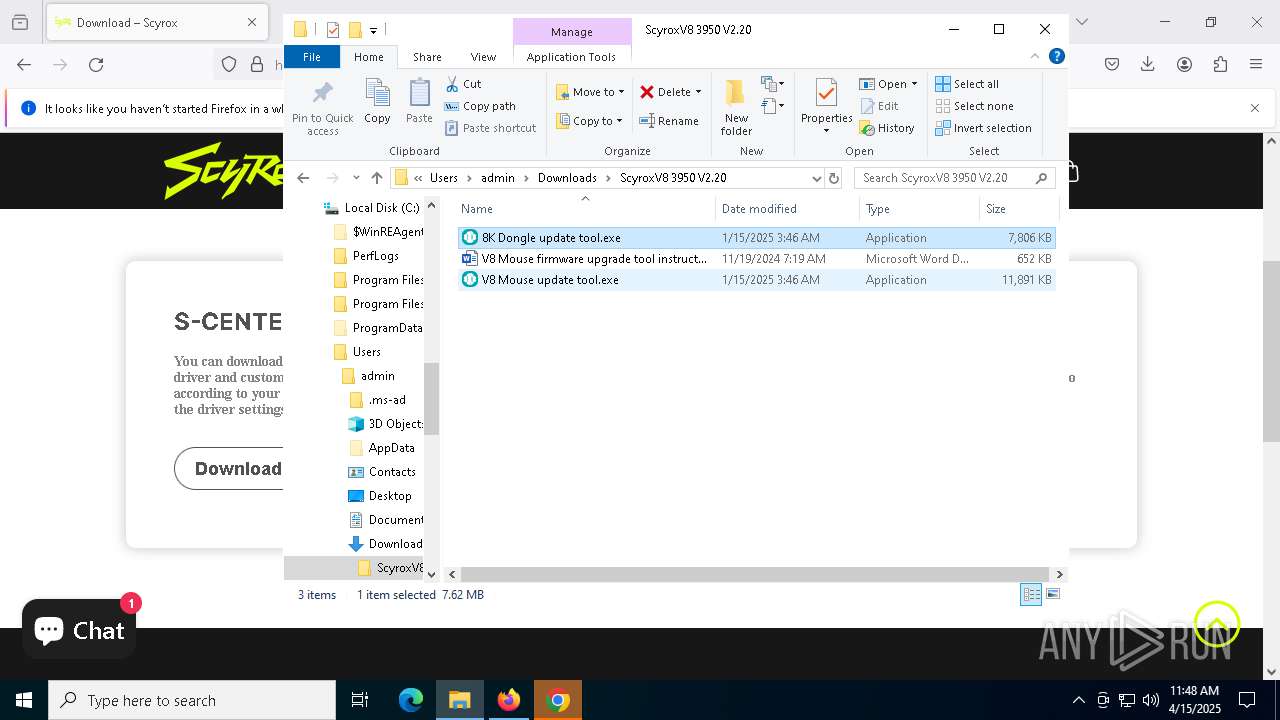
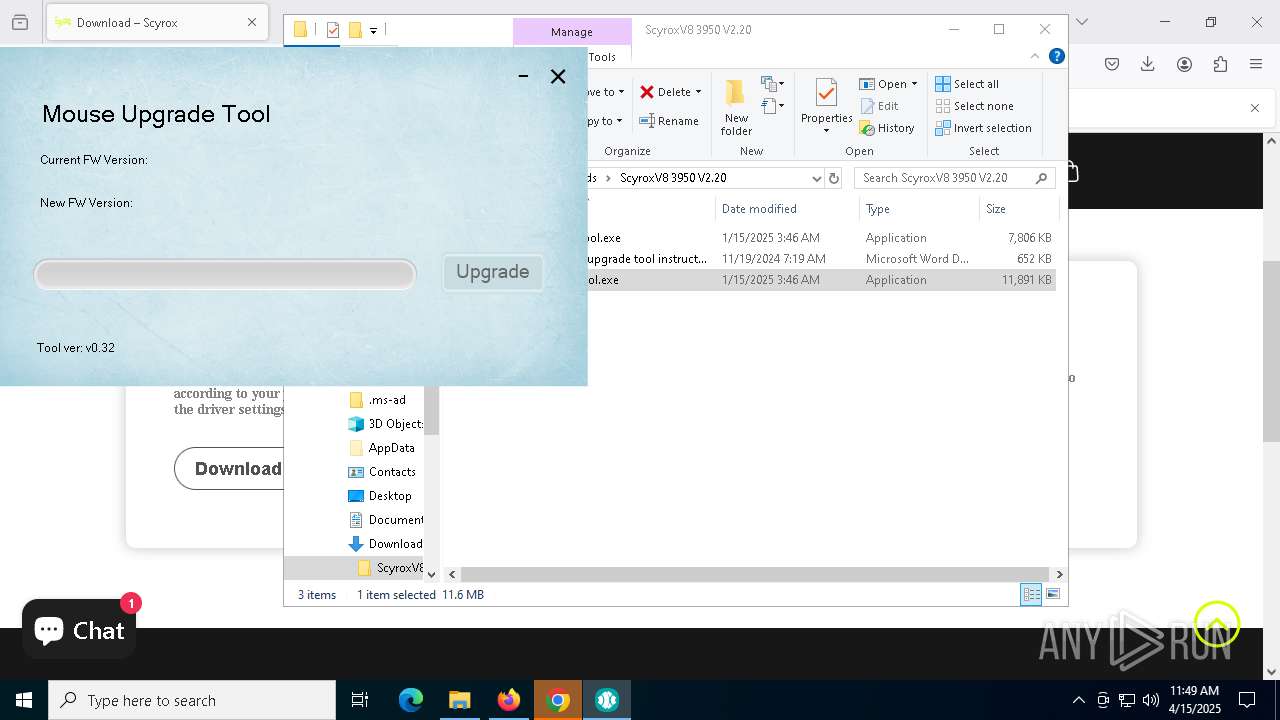
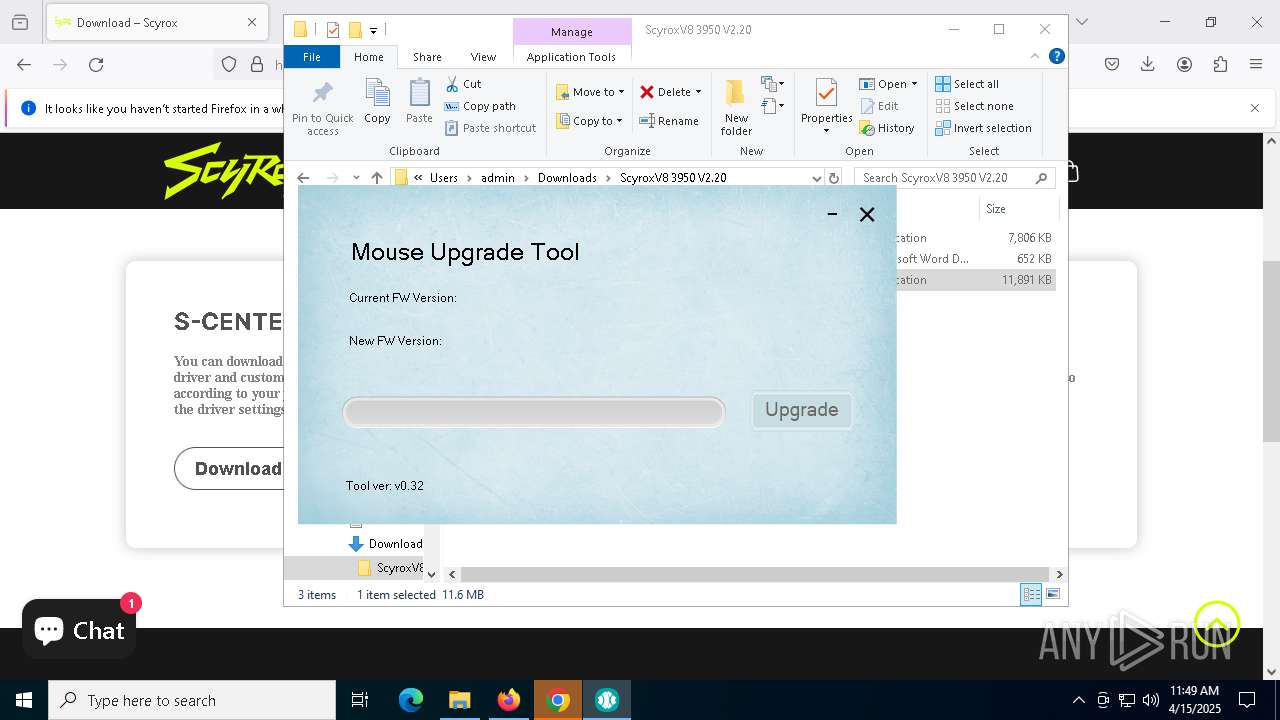
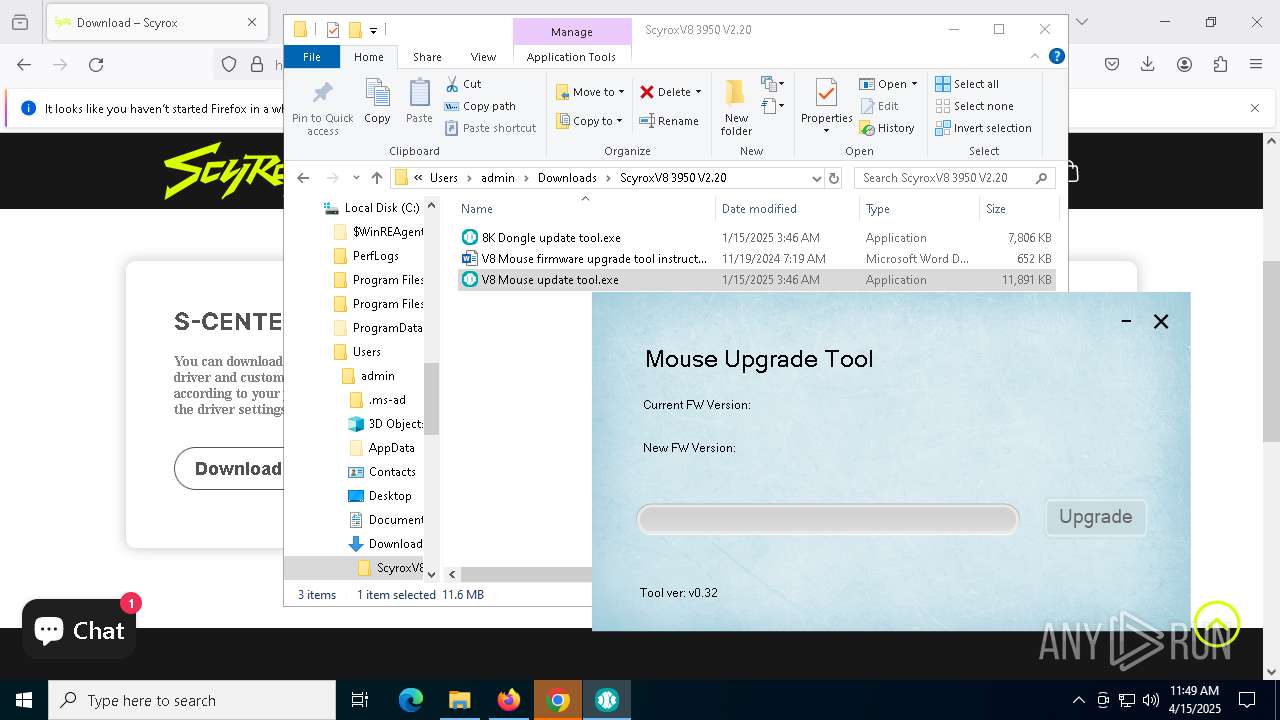
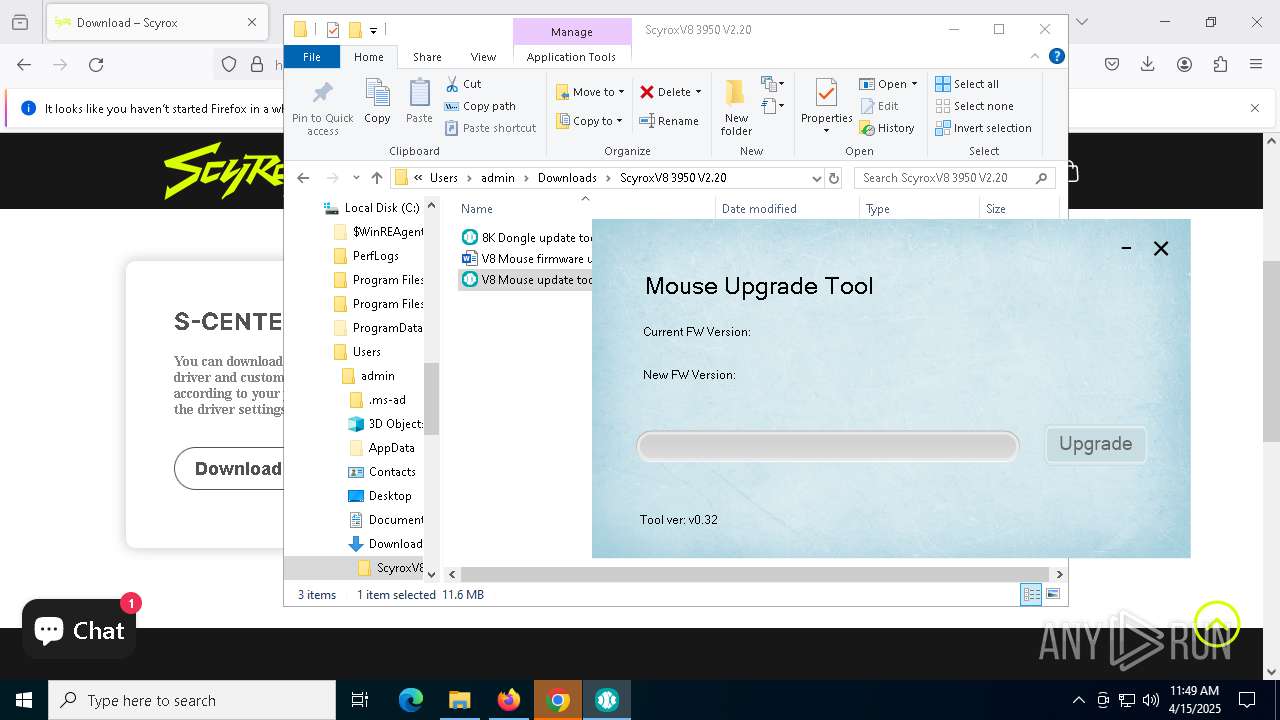
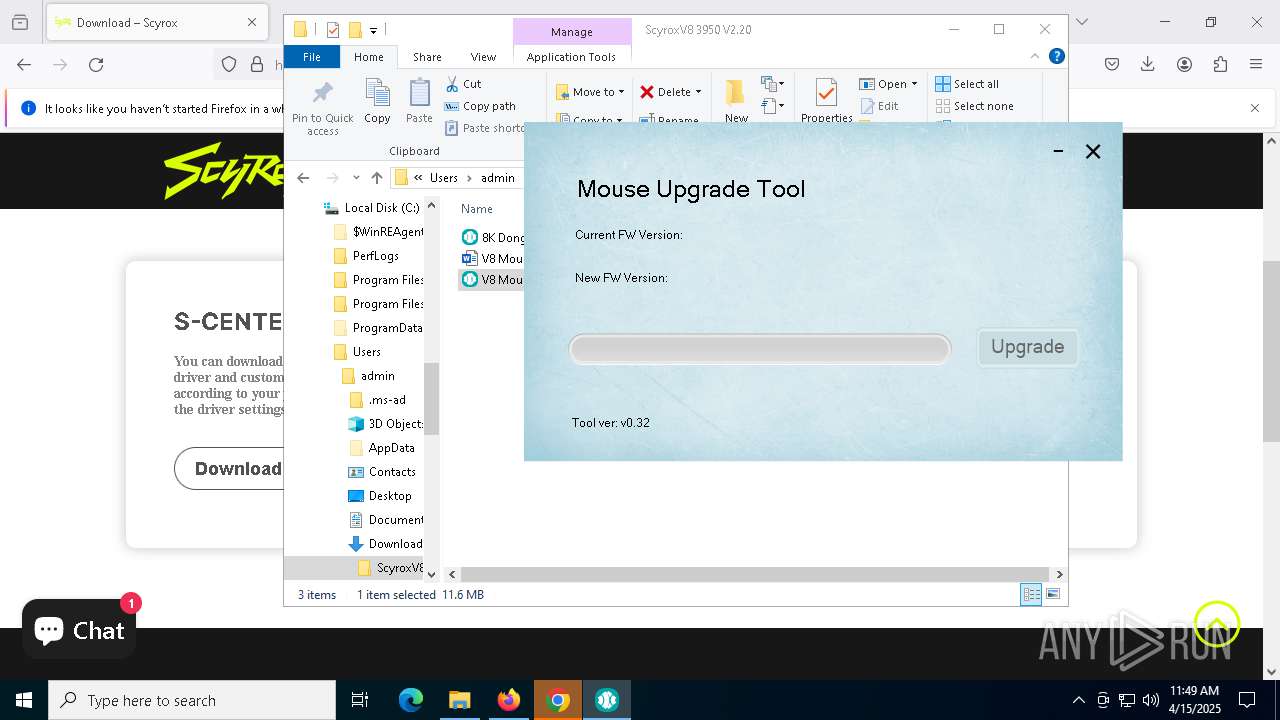
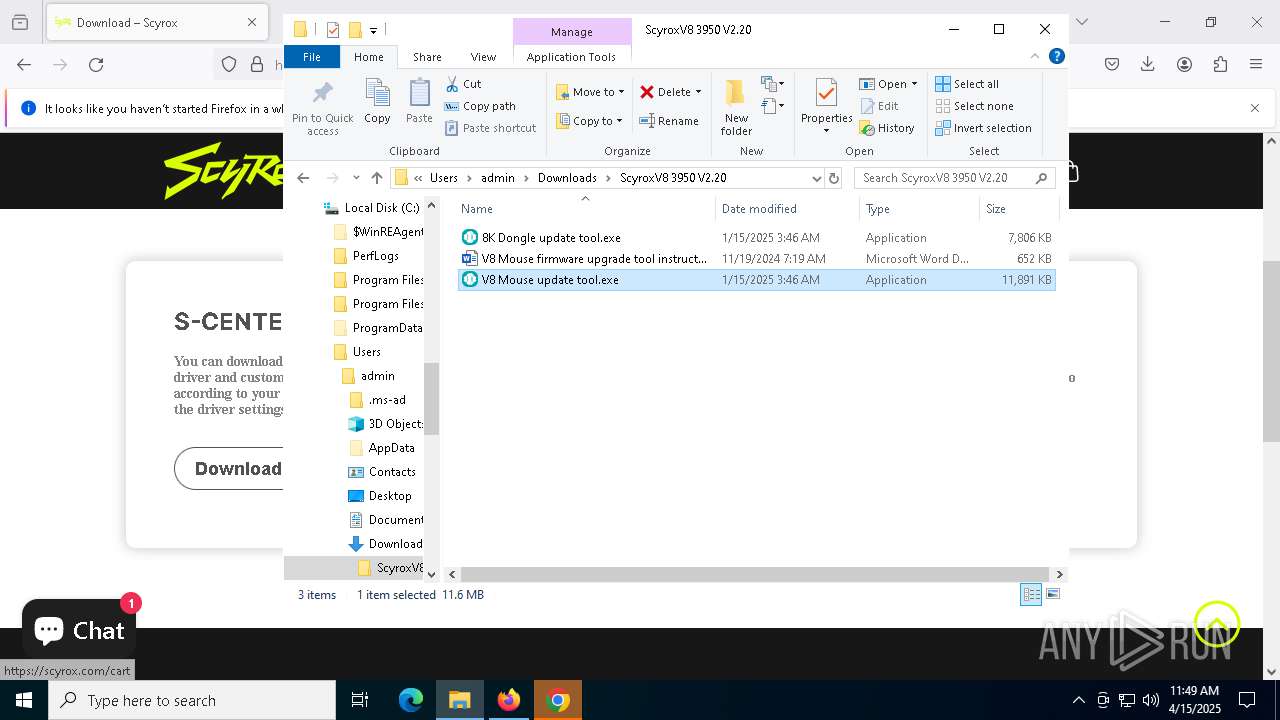
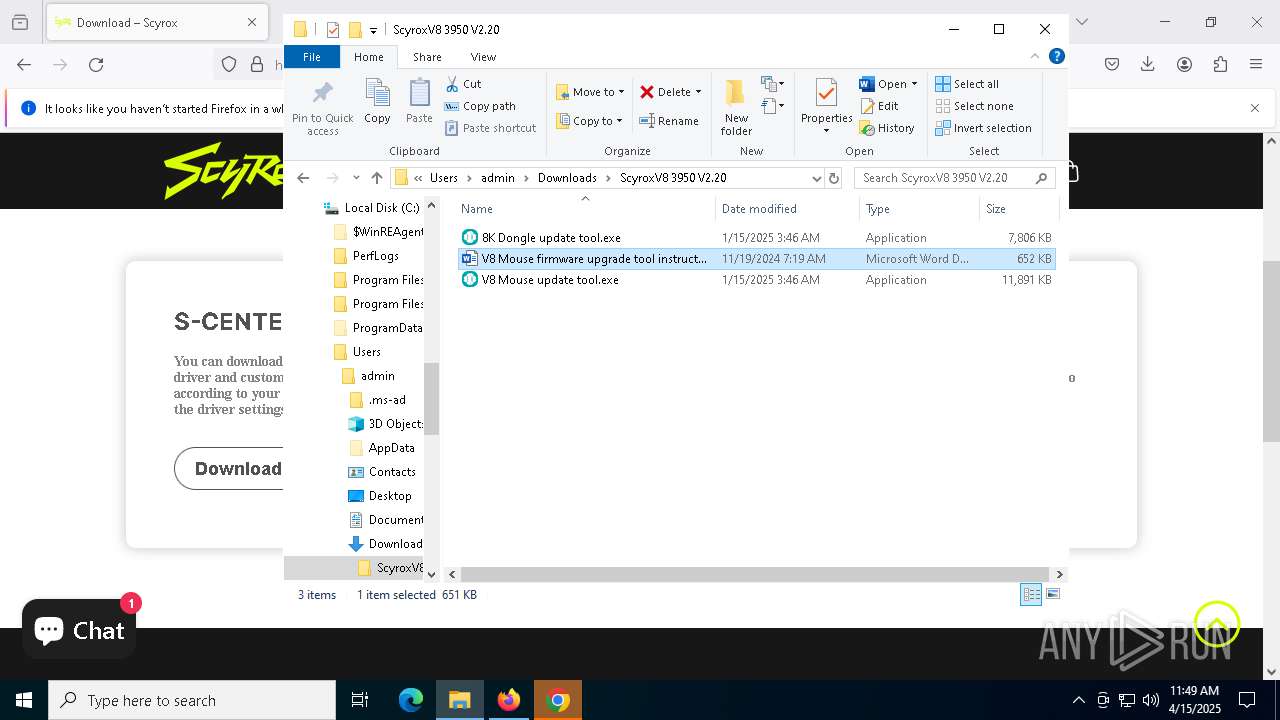
Executable content was dropped or overwritten
- 8K Dongle update tool.exe (PID: 5256)
- V8 Mouse update tool.exe (PID: 8468)
Process drops legitimate windows executable
- 8K Dongle update tool.exe (PID: 5256)
- V8 Mouse update tool.exe (PID: 8468)
The process drops C-runtime libraries
- 8K Dongle update tool.exe (PID: 5256)
- V8 Mouse update tool.exe (PID: 8468)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 5332)
- 8K Dongle update tool.exe (PID: 5256)
- V8 Mouse update tool.exe (PID: 8468)
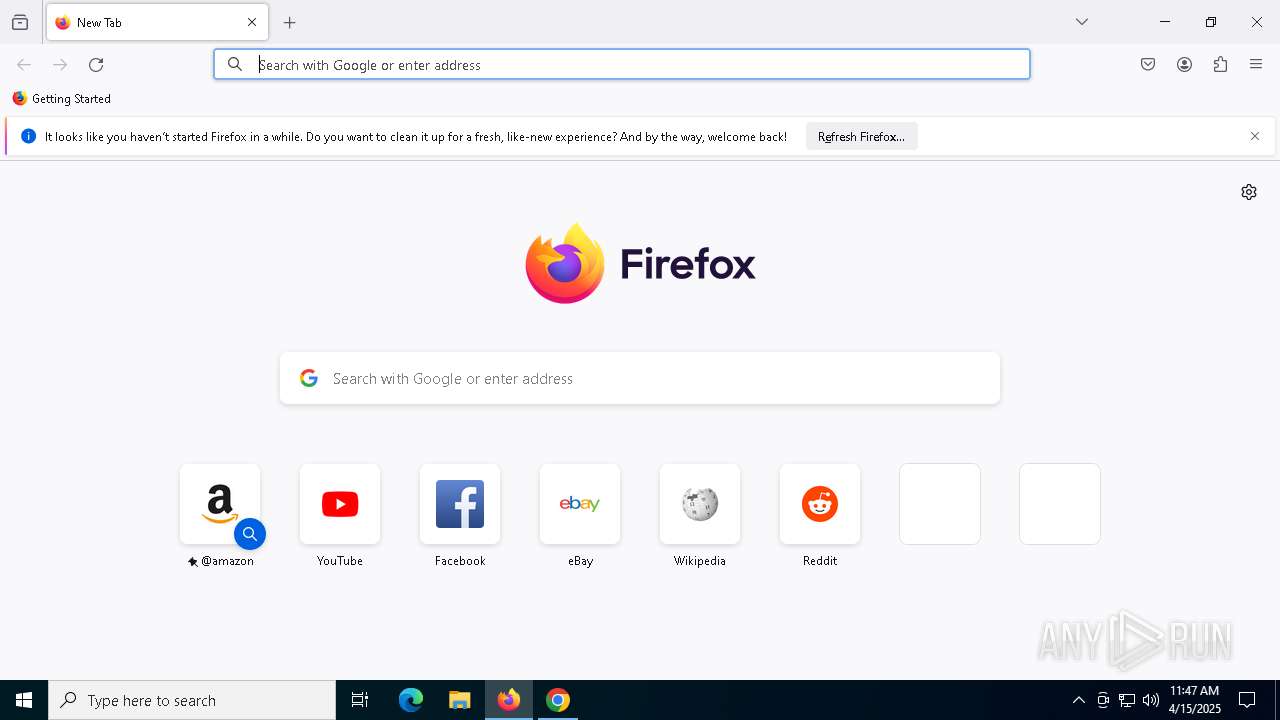
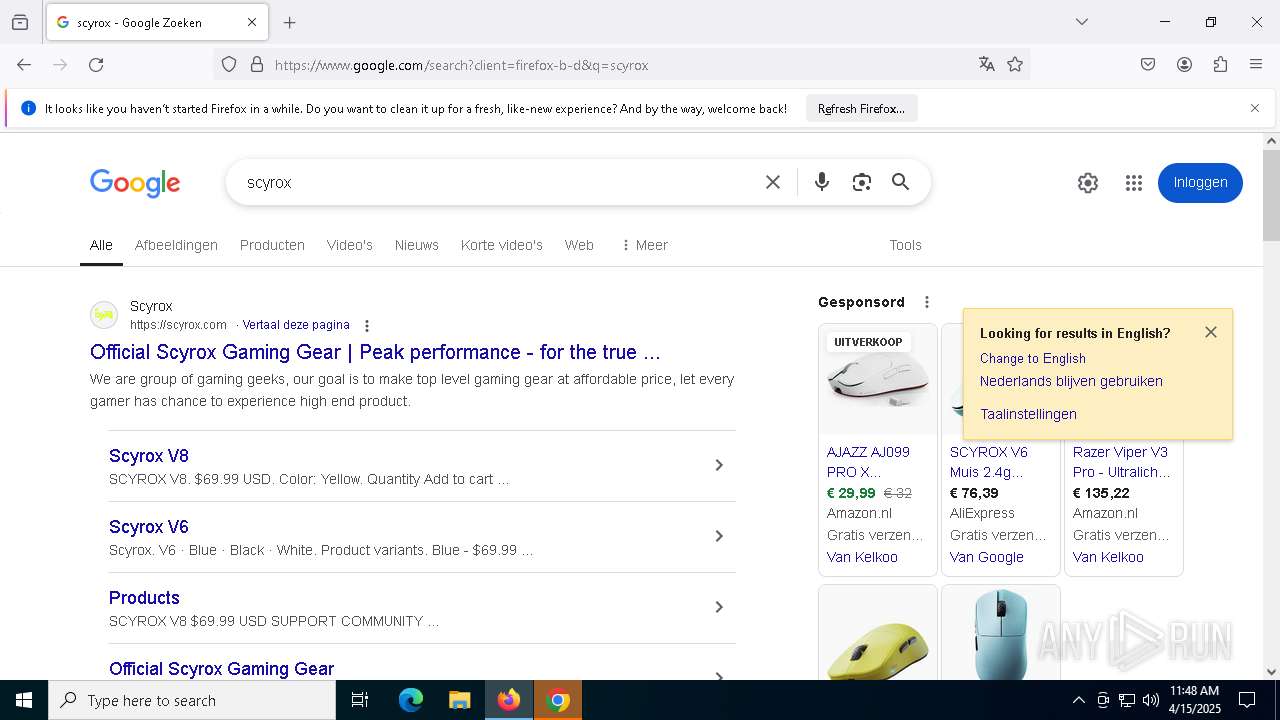
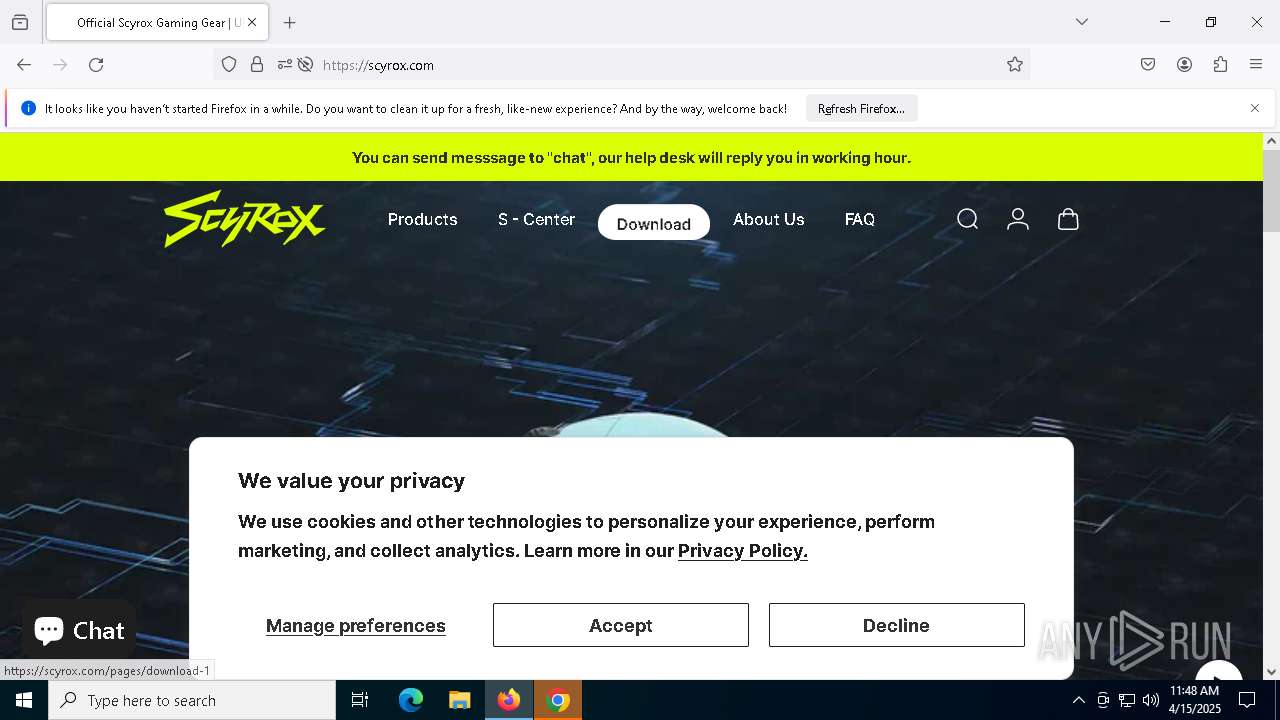
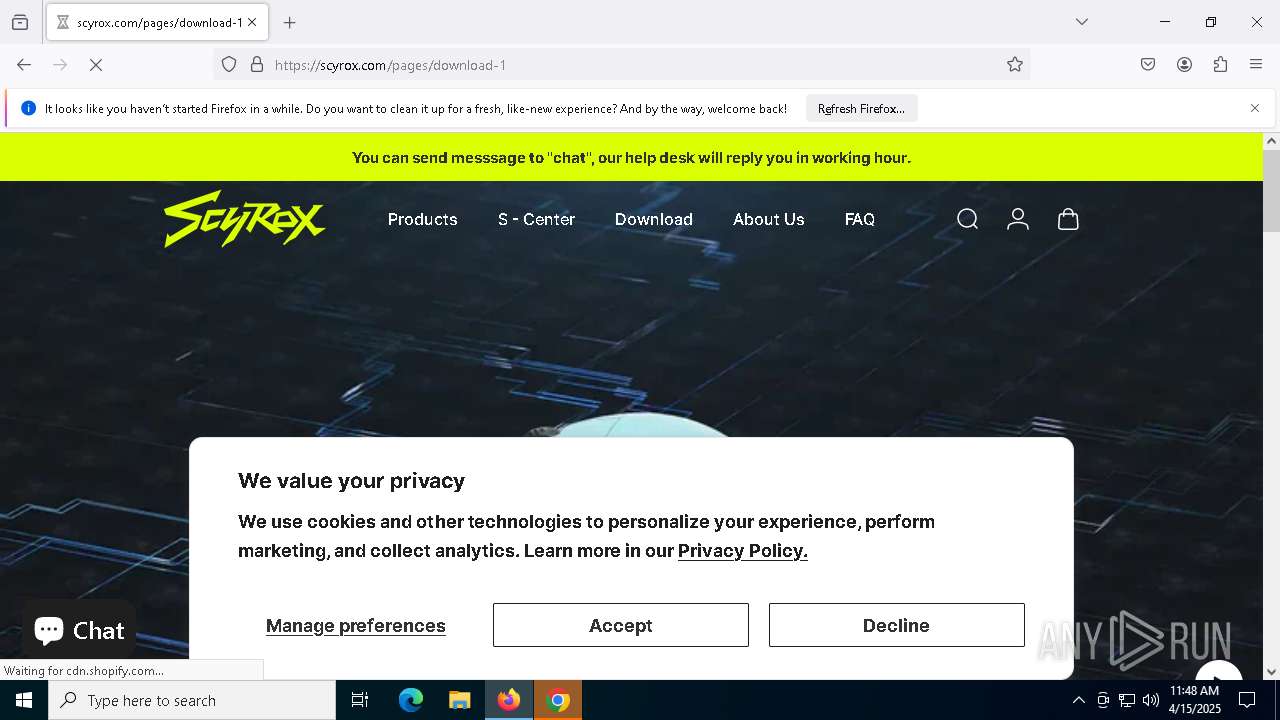
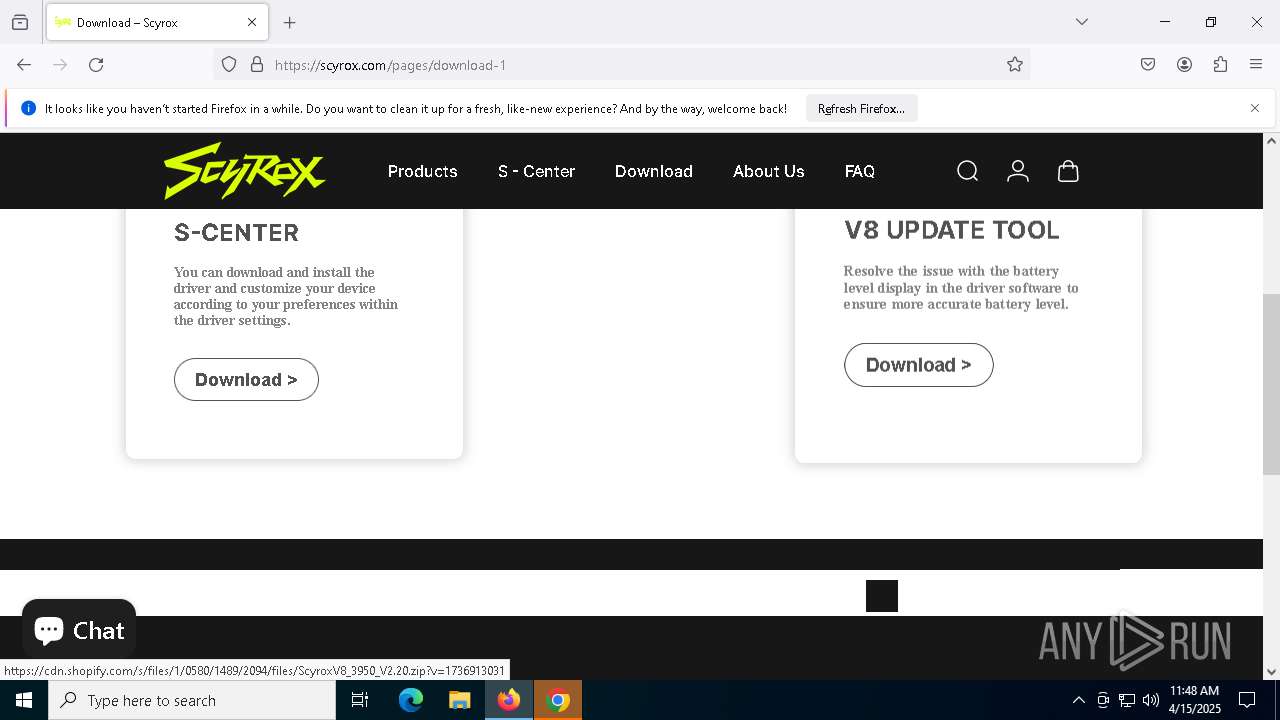
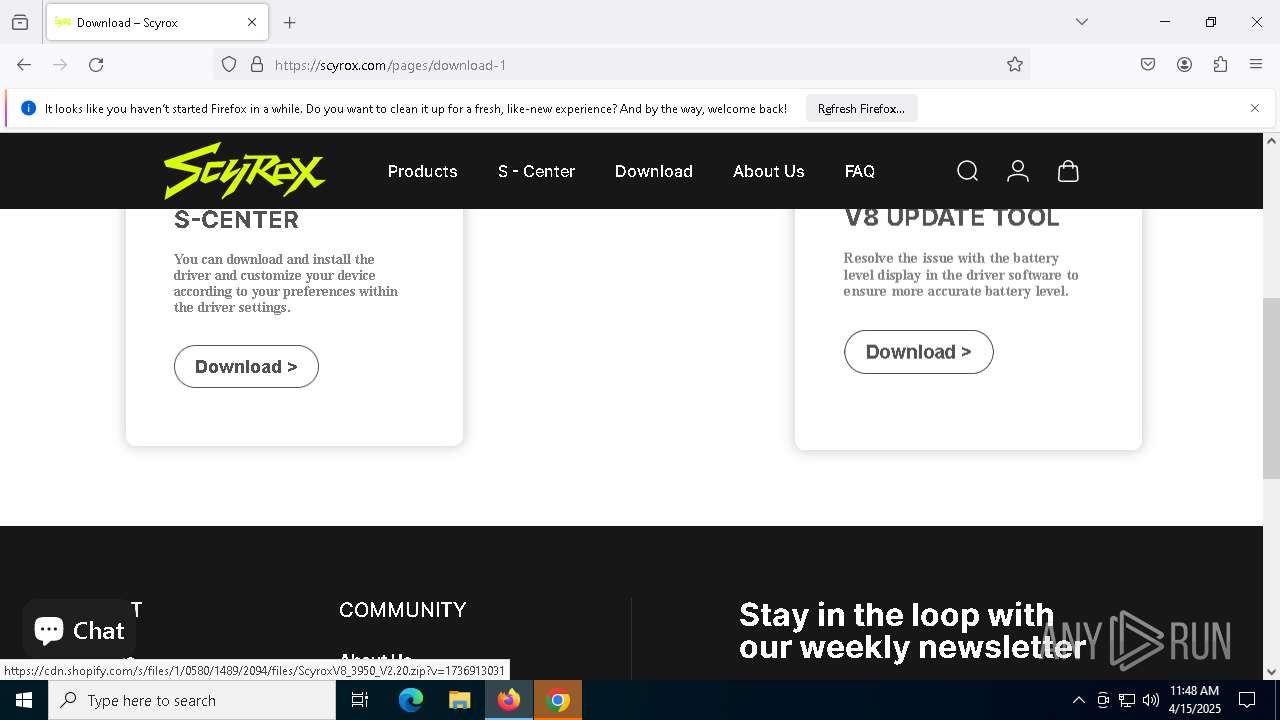
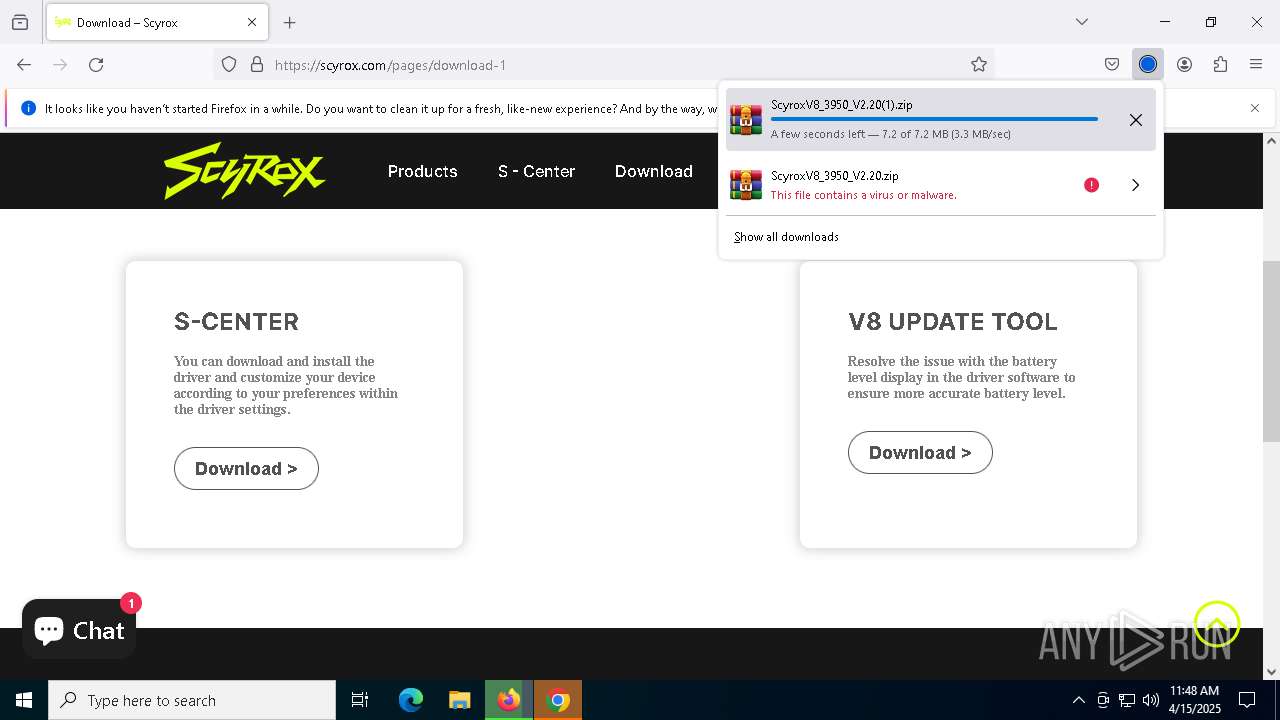
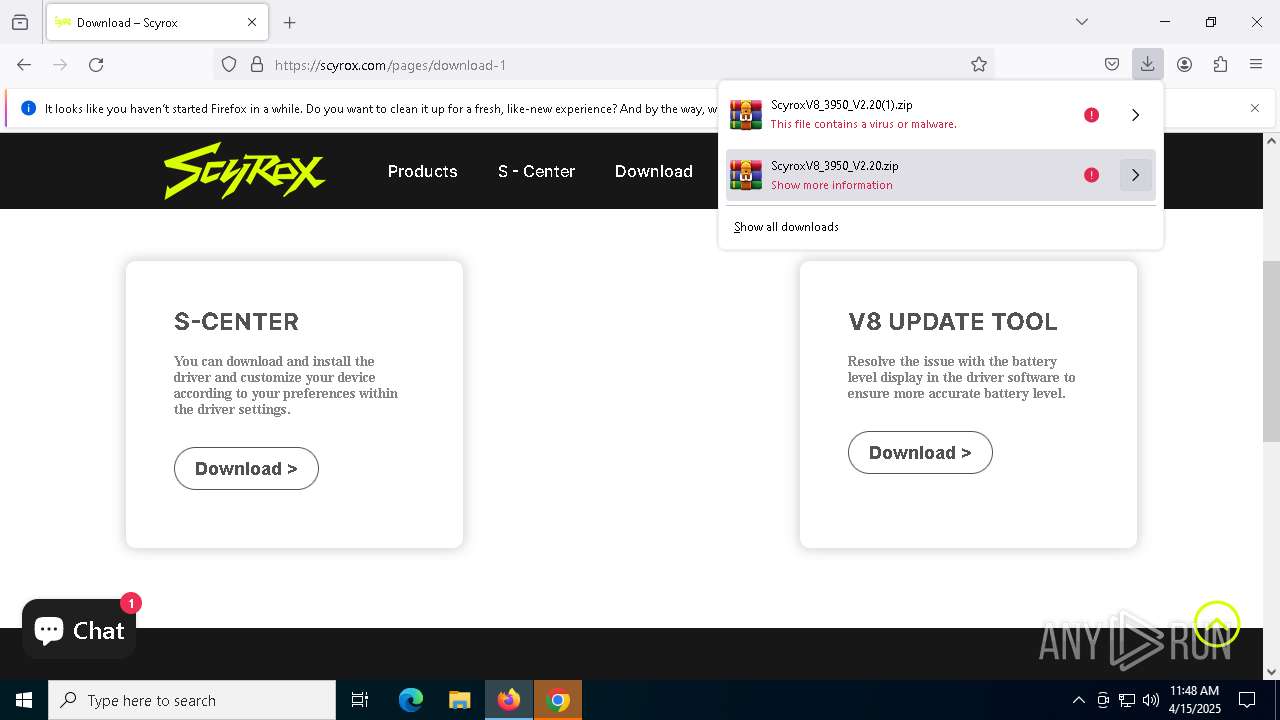
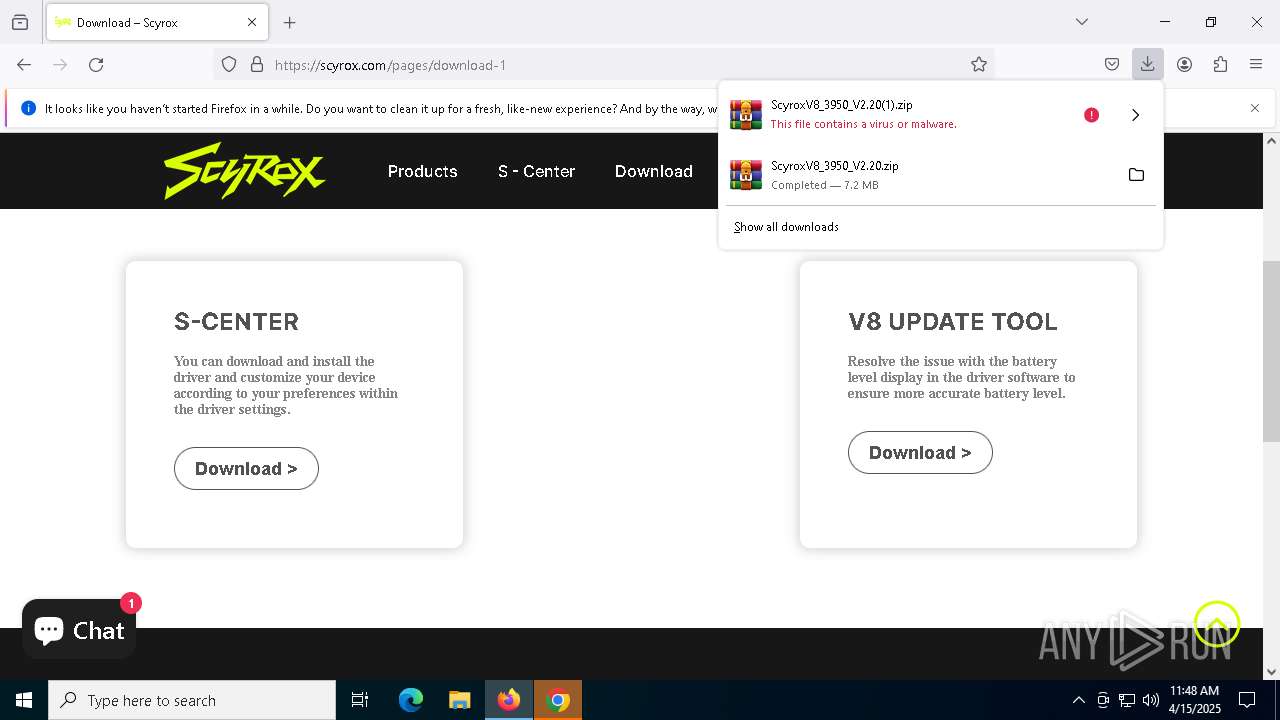
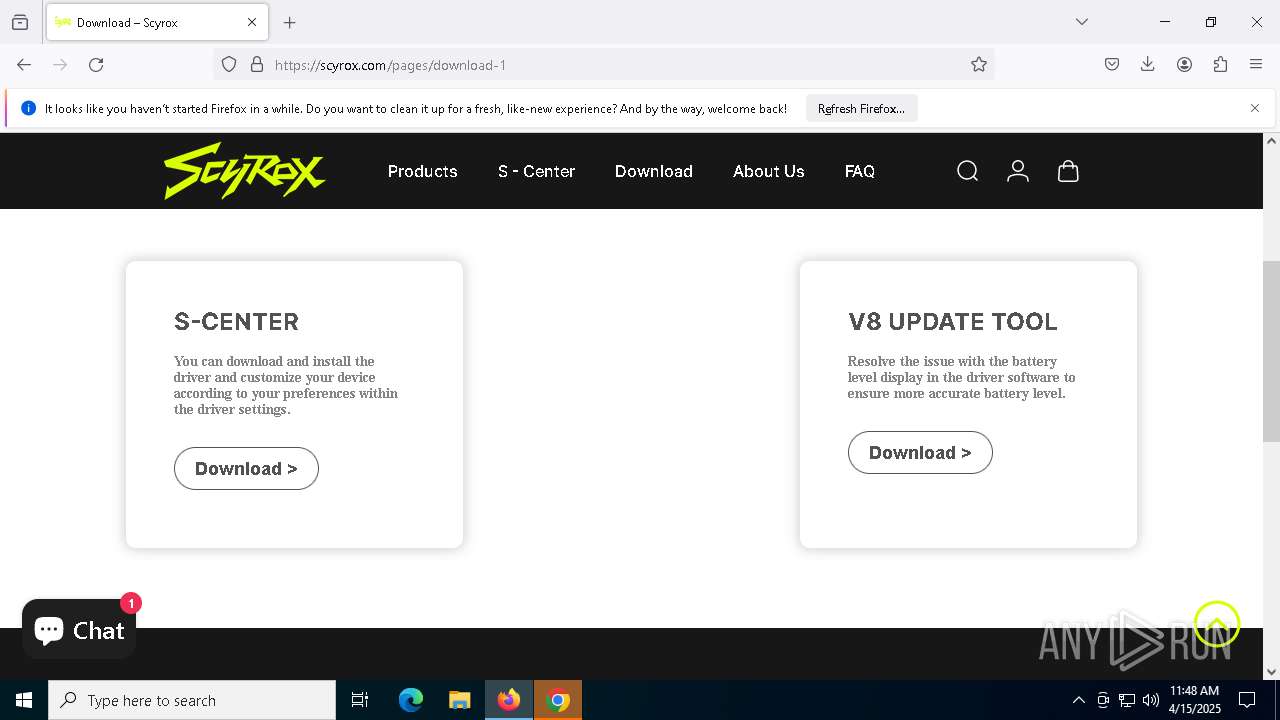
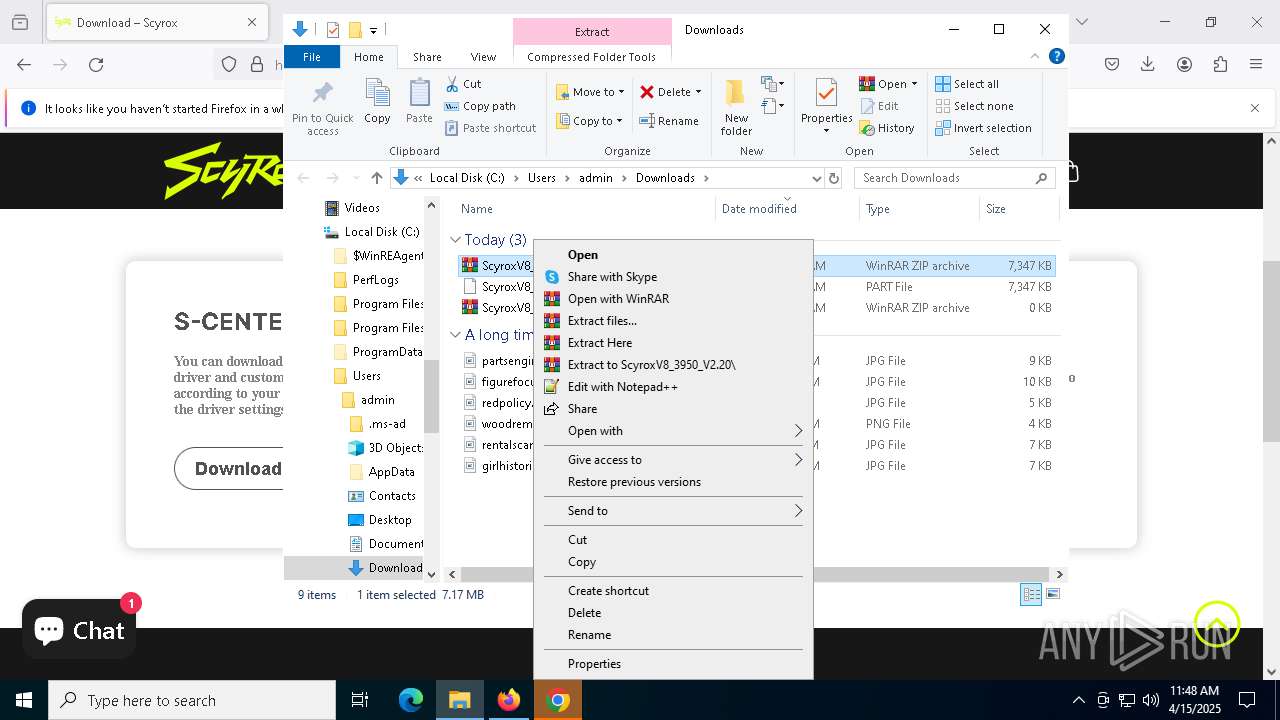
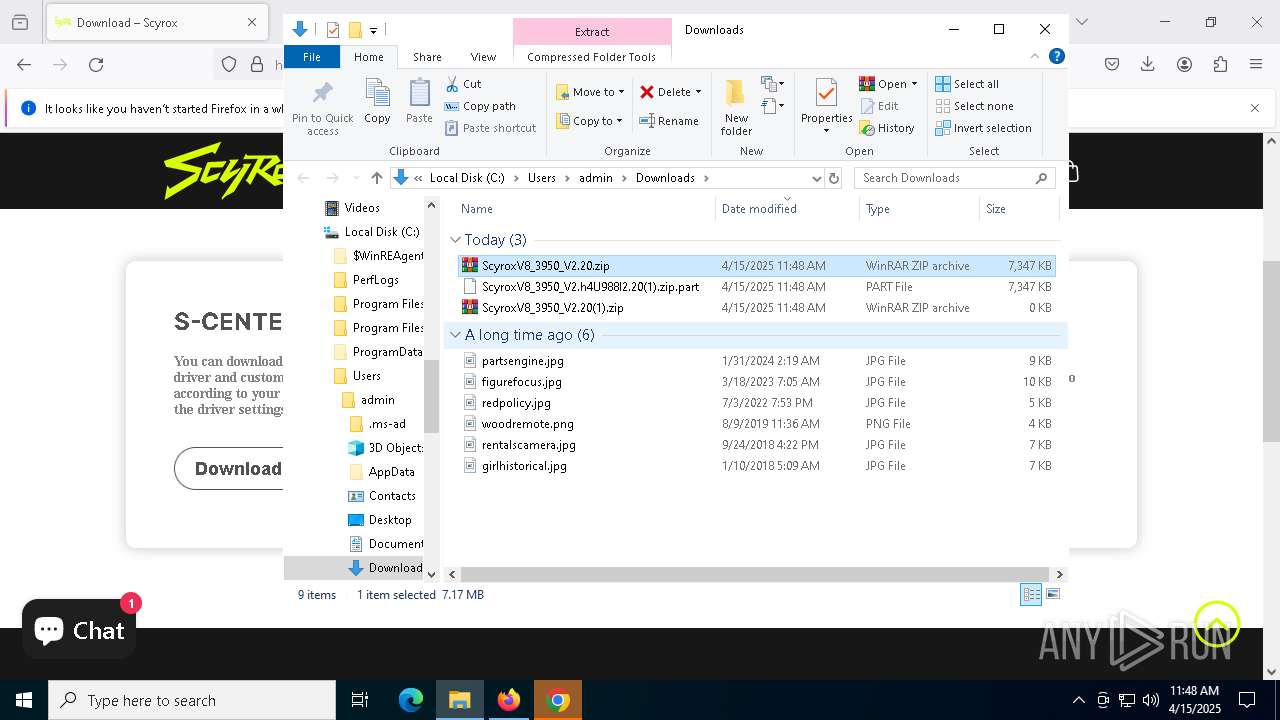
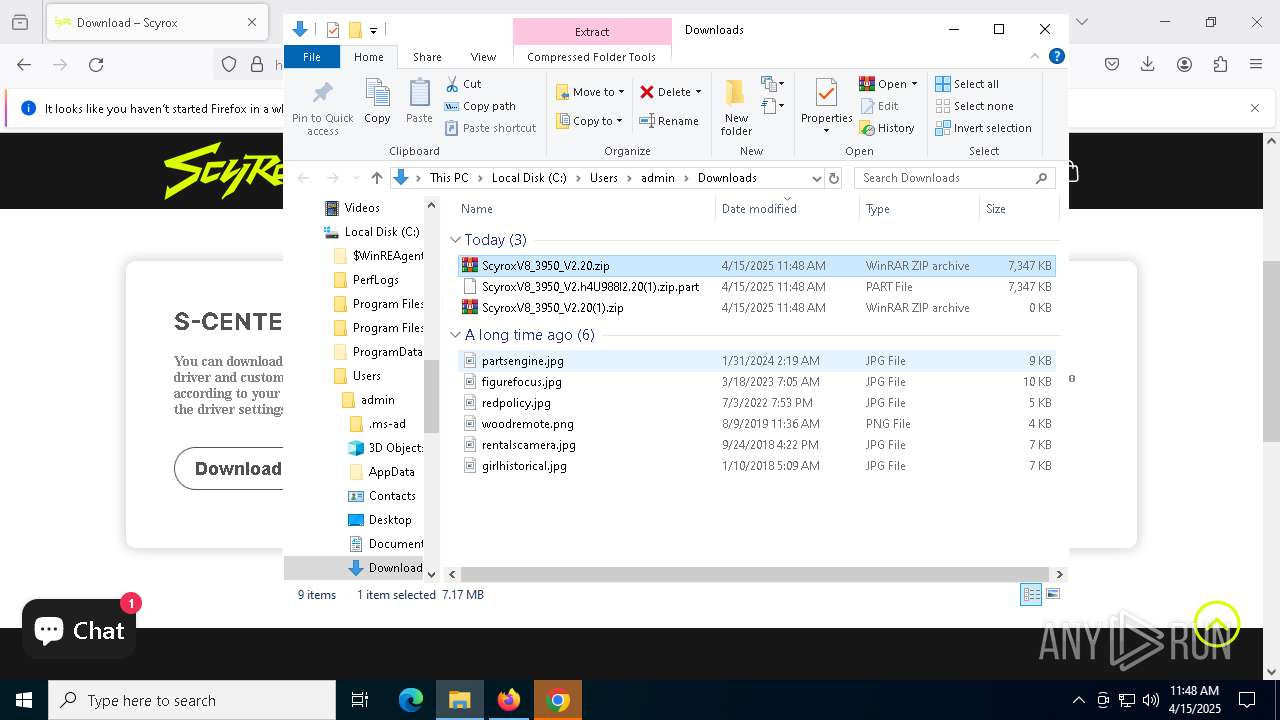
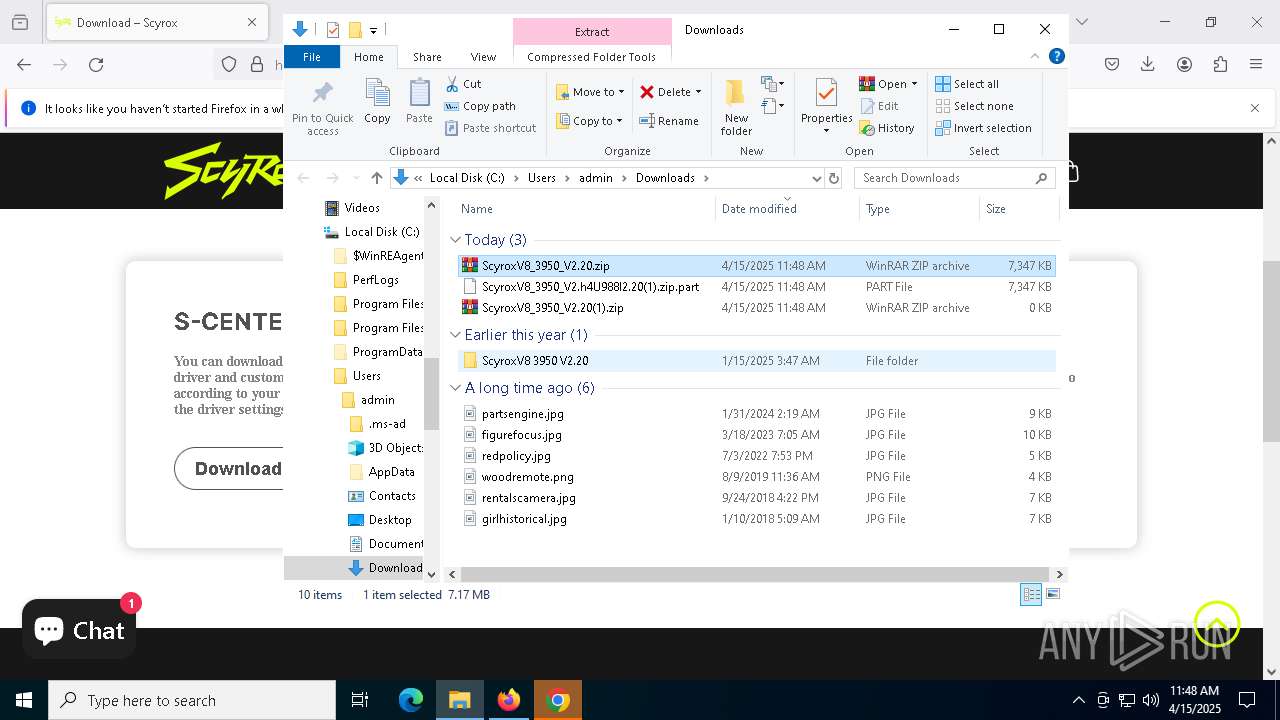
Manual execution by a user
- chrome.exe (PID: 7576)
- WinRAR.exe (PID: 9204)
- 8K Dongle update tool.exe (PID: 5256)
- firefox.exe (PID: 7656)
- V8 Mouse update tool.exe (PID: 8468)
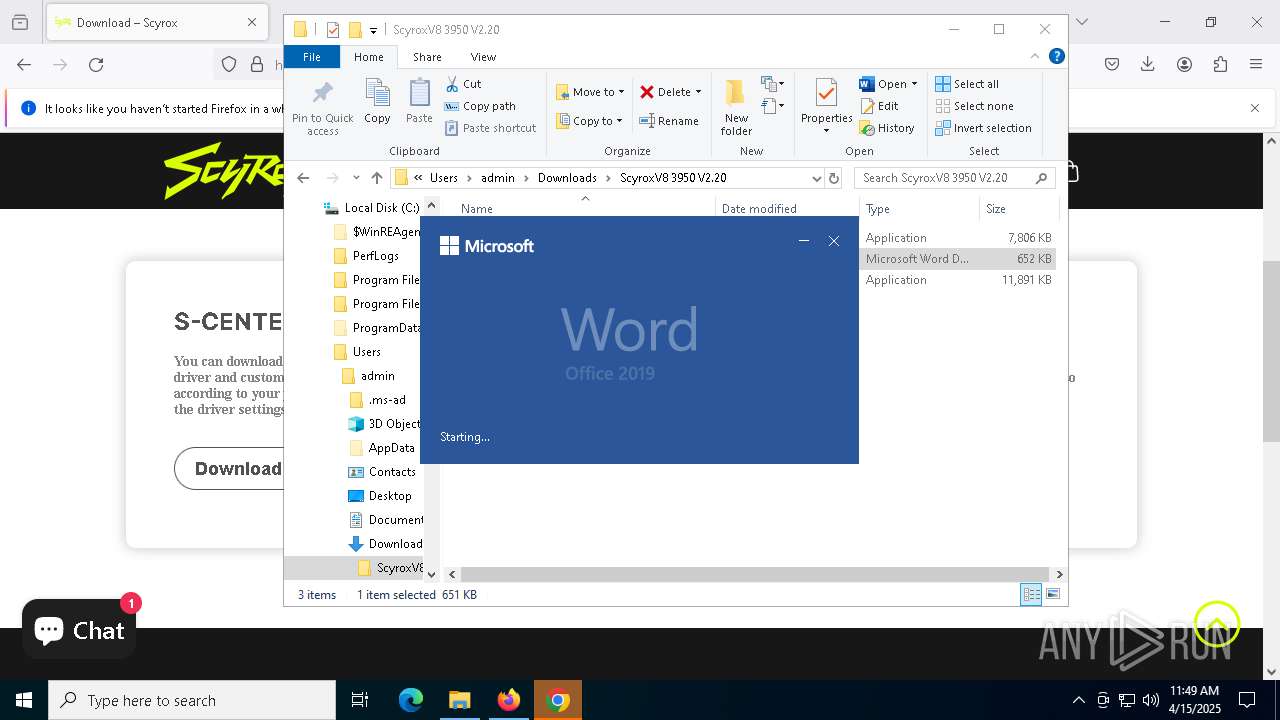
- WINWORD.EXE (PID: 8764)
Application launched itself
- firefox.exe (PID: 7700)
- chrome.exe (PID: 7576)
- firefox.exe (PID: 7656)
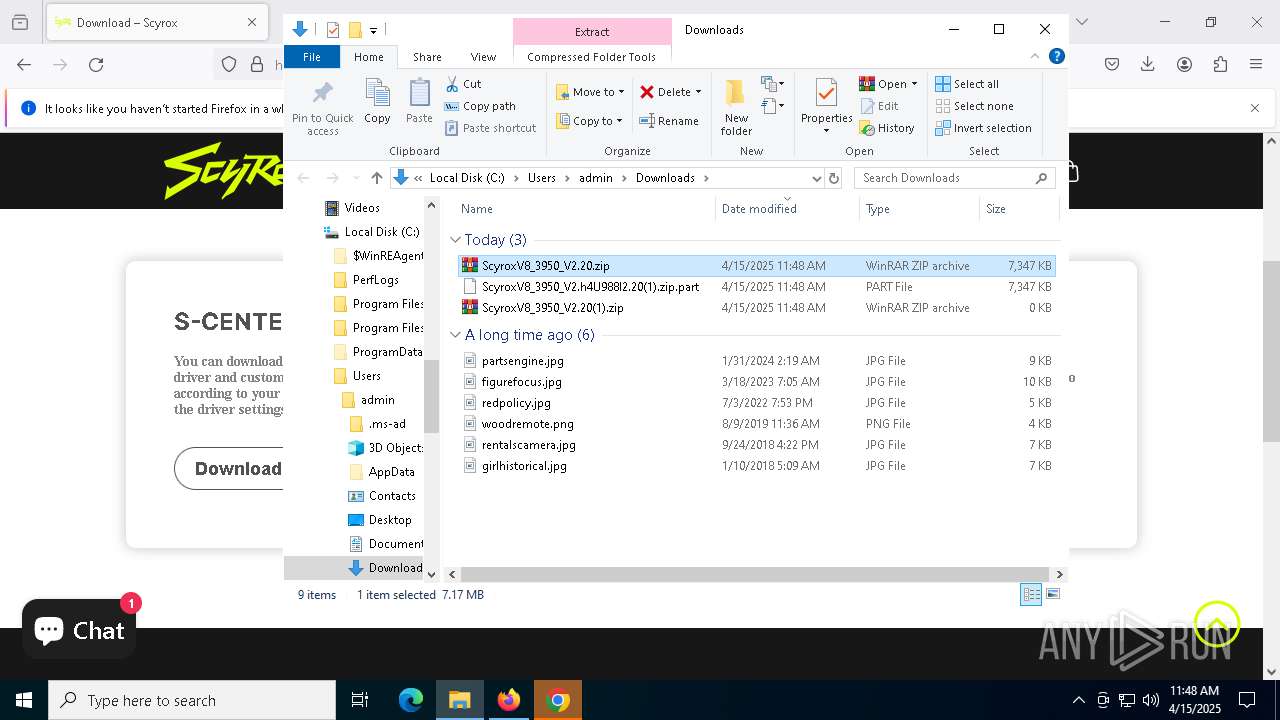
Executable content was dropped or overwritten
- WinRAR.exe (PID: 9204)
Checks supported languages
- 8K Dongle update tool.exe (PID: 5256)
- V8 Mouse update tool.exe (PID: 8468)
The sample compiled with chinese language support
- 8K Dongle update tool.exe (PID: 5256)
Create files in a temporary directory
- 8K Dongle update tool.exe (PID: 5256)
- V8 Mouse update tool.exe (PID: 8468)
Reads the machine GUID from the registry
- 8K Dongle update tool.exe (PID: 5256)
- V8 Mouse update tool.exe (PID: 8468)
Reads the software policy settings
- slui.exe (PID: 7256)
Reads the computer name
- V8 Mouse update tool.exe (PID: 8468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:02:06 19:49:02 |
| ZipCRC: | 0x783cab40 |
| ZipCompressedSize: | 592933 |
| ZipUncompressedSize: | 1758240 |
| ZipFileName: | Autoruns.exe |
Total processes
164
Monitored processes
34
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1228 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5052 -childID 4 -isForBrowser -prefsHandle 5044 -prefMapHandle 5036 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1424 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2ef0c3e4-a498-4e05-911c-69dc60e7765e} 7700 "\\.\pipe\gecko-crash-server-pipe.7700" 11645996f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5100 -childID 5 -isForBrowser -prefsHandle 5108 -prefMapHandle 5112 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1424 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2a4a38c8-556f-4f3e-8f88-1cfc9d0005ce} 7700 "\\.\pipe\gecko-crash-server-pipe.7700" 11645d9c150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2920 -childID 1 -isForBrowser -prefsHandle 2660 -prefMapHandle 2952 -prefsLen 31447 -prefMapSize 244583 -jsInitHandle 1424 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {43b3cbee-bddd-450d-a8a8-f5d1c9304c26} 7700 "\\.\pipe\gecko-crash-server-pipe.7700" 11640ef0bd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3196 --field-trial-handle=1904,i,16761855588931390148,12954327291661577478,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3164 --field-trial-handle=1904,i,16761855588931390148,12954327291661577478,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
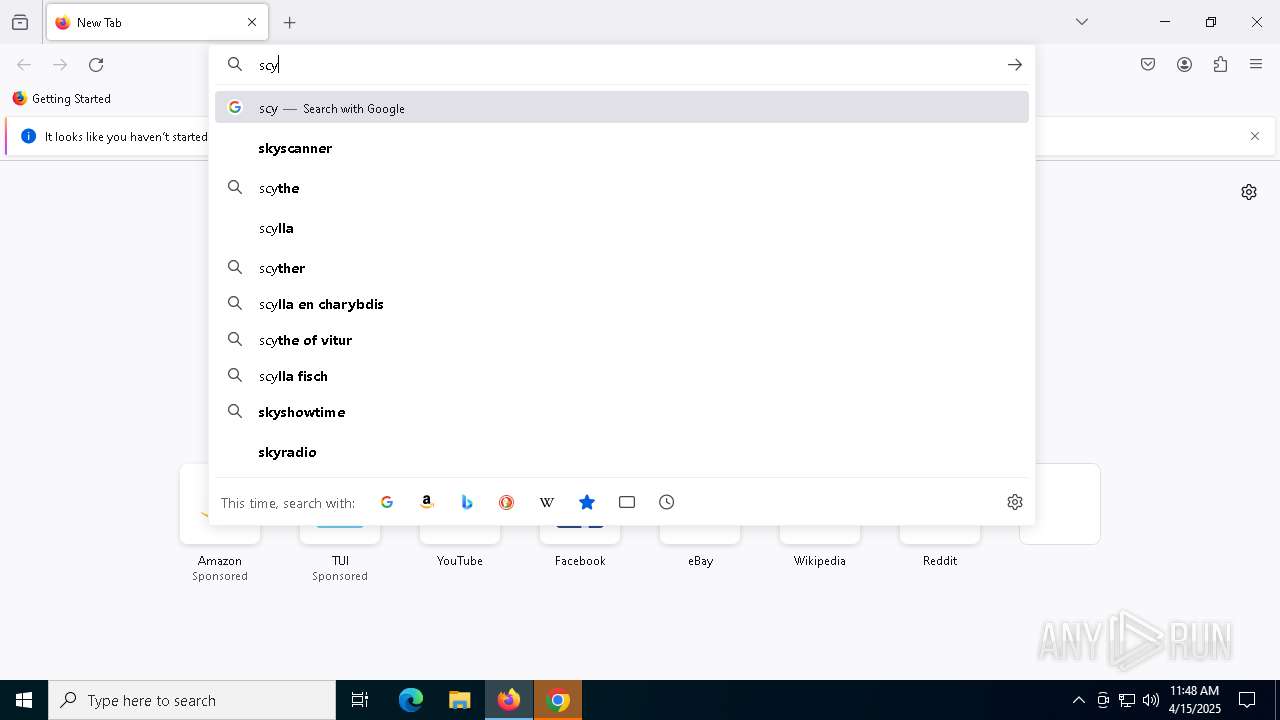
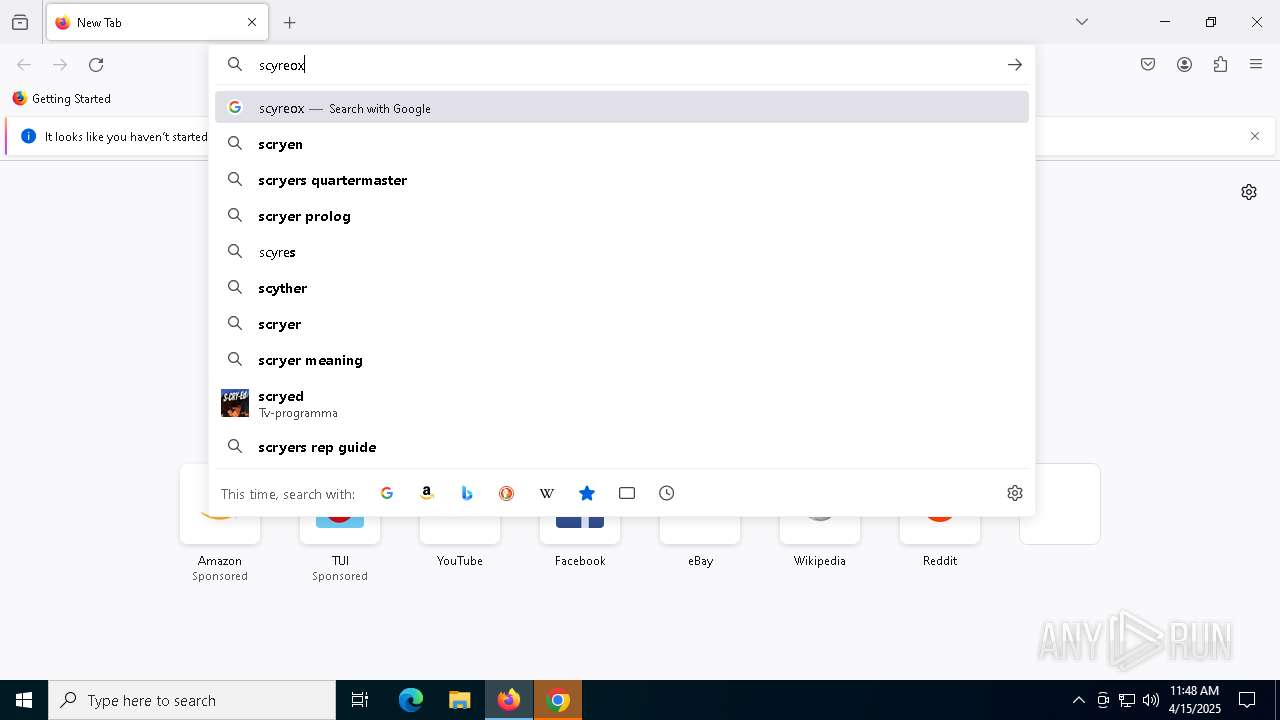
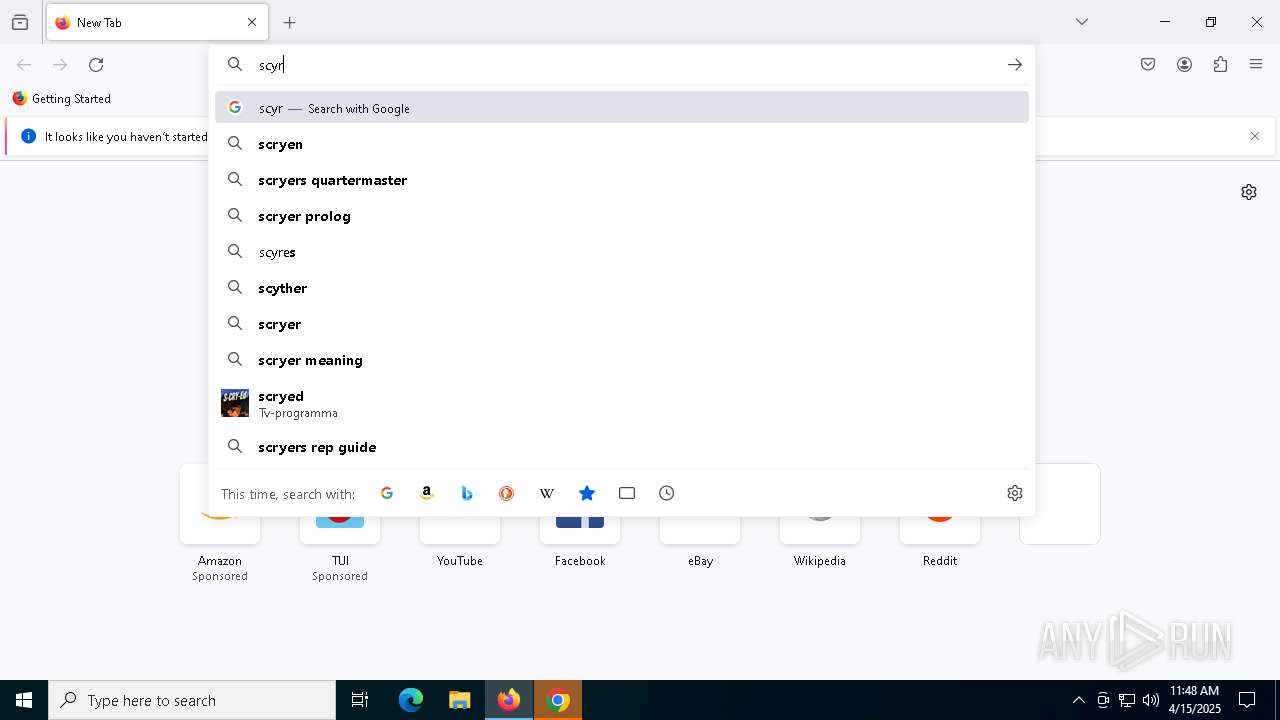
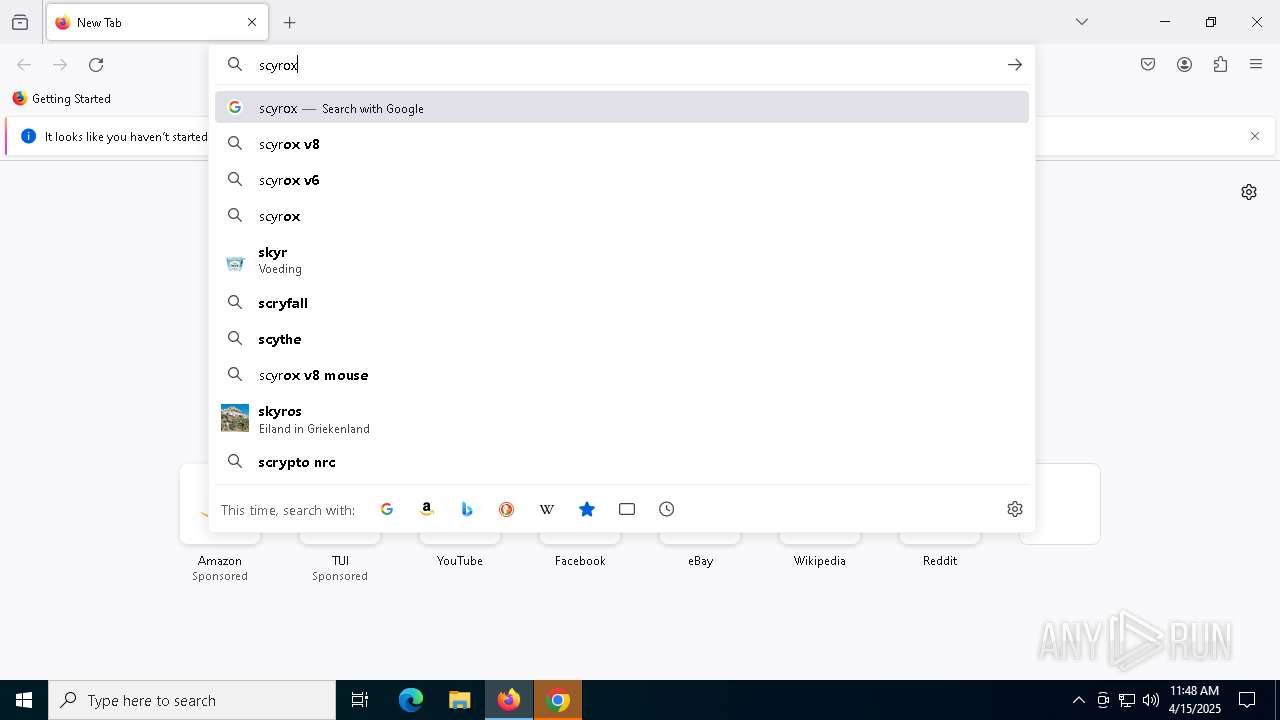
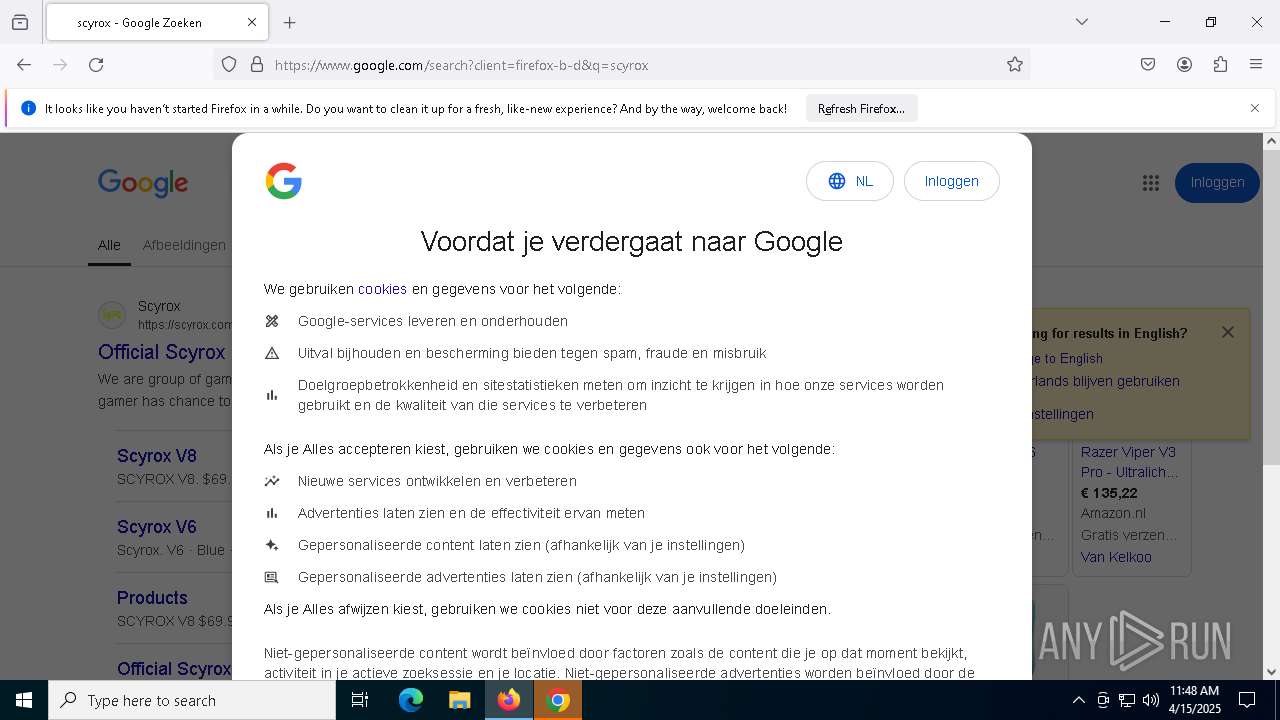
| 5256 | "C:\Users\admin\Downloads\ScyroxV8 3950 V2.20\8K Dongle update tool.exe" | C:\Users\admin\Downloads\ScyroxV8 3950 V2.20\8K Dongle update tool.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: USBToolLite Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
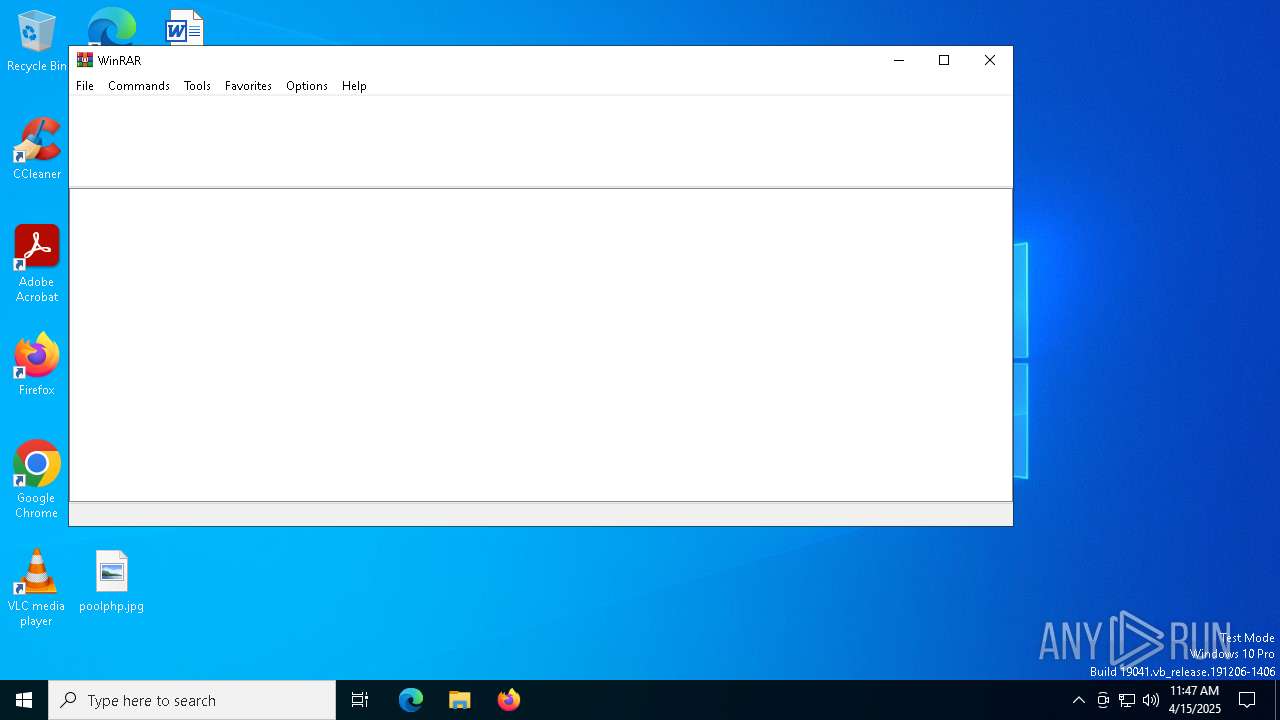
| 5332 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Autoruns.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6208 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "F33EDEB4-4021-4E97-91AD-F57F65692CA5" "C7648018-368D-4DB0-936F-6E06E91CFEA3" "8764" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 6424 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3700 --field-trial-handle=1904,i,16761855588931390148,12954327291661577478,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
27 850
Read events
27 570
Write events
264
Delete events
16
Modification events
| (PID) Process: | (5332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Autoruns.zip | |||
| (PID) Process: | (5332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (5332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
15
Suspicious files
247
Text files
45
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10e735.TMP | — | |
MD5:— | SHA256:— | |||
| 7576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10e735.TMP | — | |
MD5:— | SHA256:— | |||
| 7576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10e735.TMP | — | |
MD5:— | SHA256:— | |||
| 7576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10e745.TMP | — | |
MD5:— | SHA256:— | |||
| 7576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10e745.TMP | — | |
MD5:— | SHA256:— | |||
| 7576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
199
DNS requests
239
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7700 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://o.pki.goog/s/wr3/UTA | unknown | — | — | whitelisted |
7700 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7700 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7700 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7700 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7700 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7700 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7700 | firefox.exe | POST | 200 | 184.24.77.50:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7896 | chrome.exe | 142.250.185.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
7576 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7896 | chrome.exe | 142.250.145.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud Application Platform (.herokuapp .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud Application Platform (.herokuapp .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud Application Platform (.herokuapp .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud Application Platform (.herokuapp .com) |