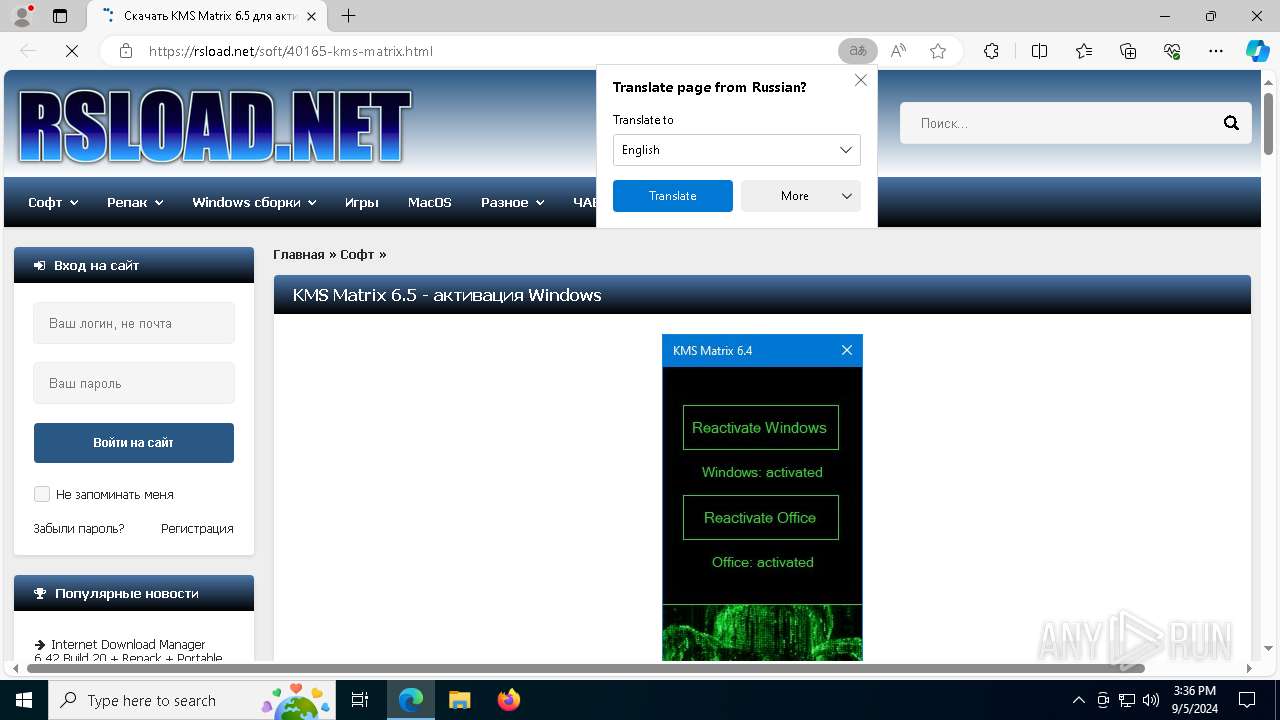
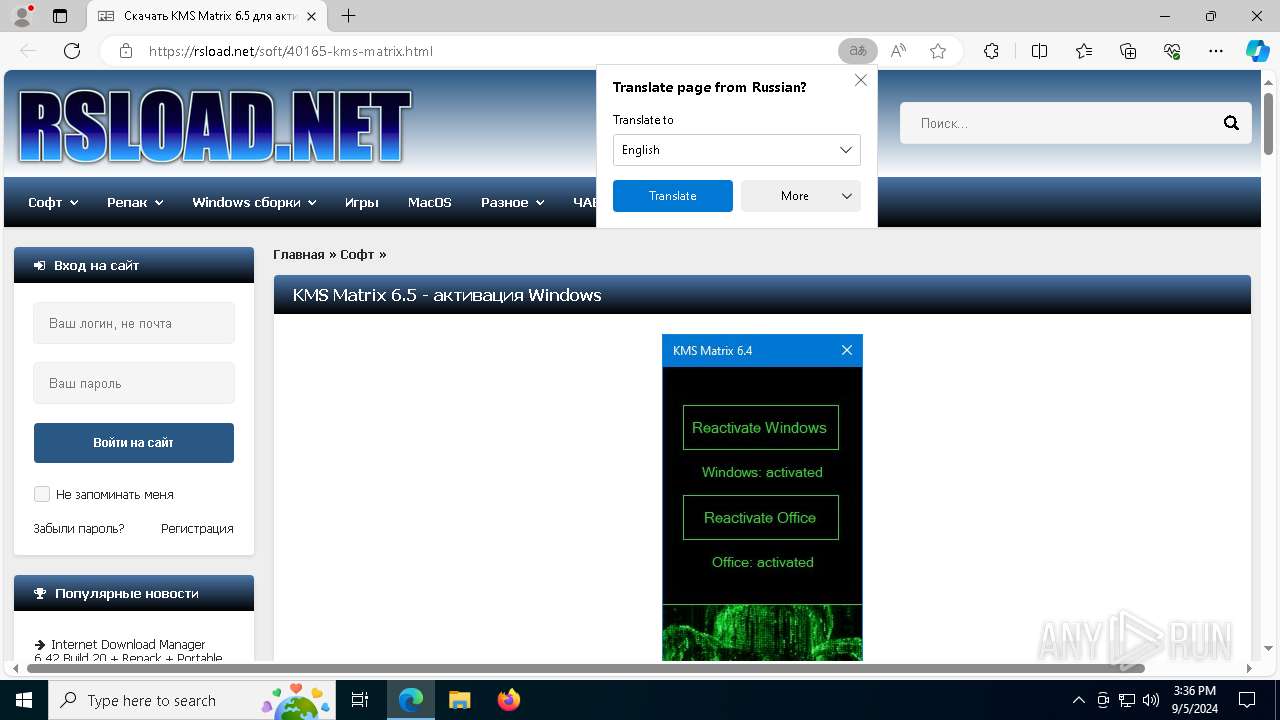
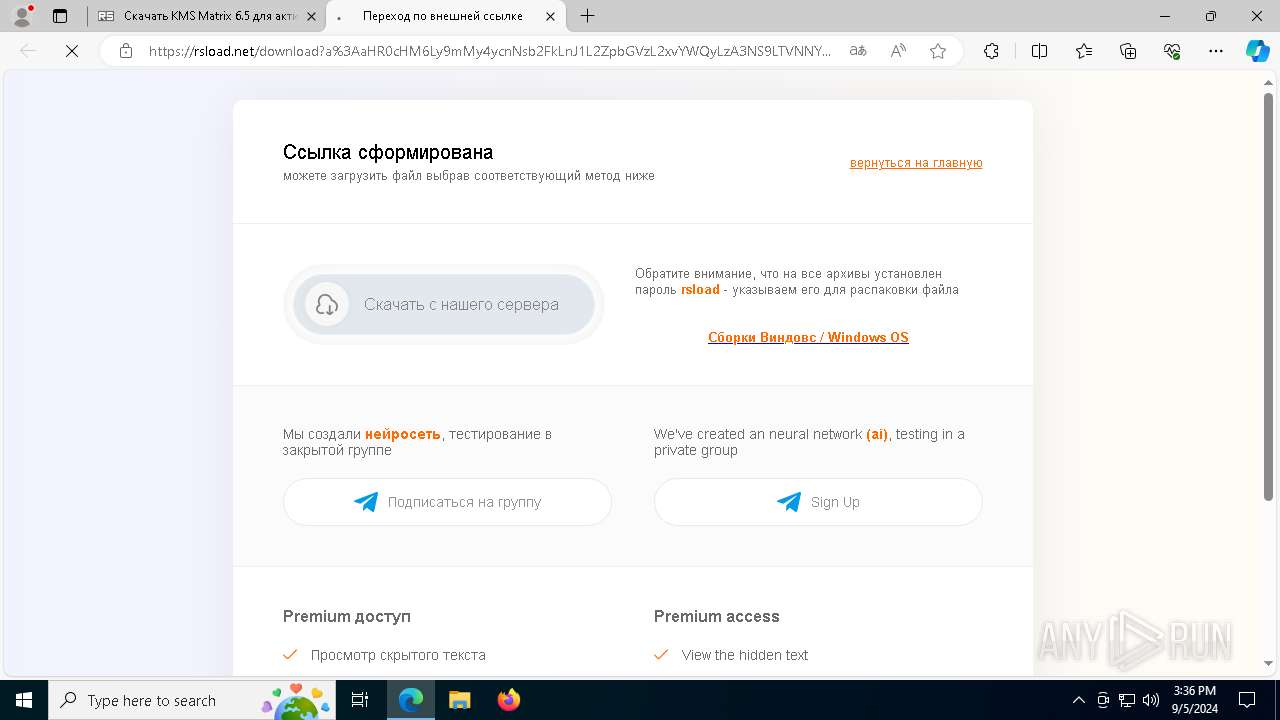
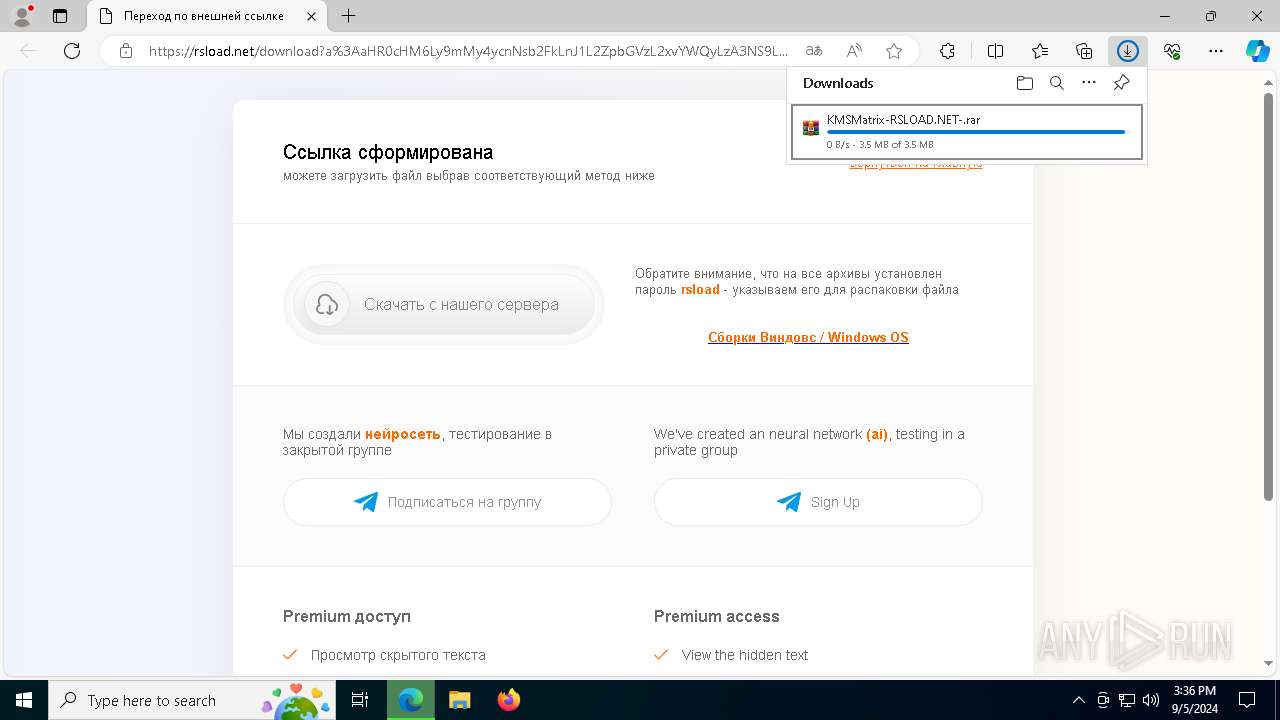
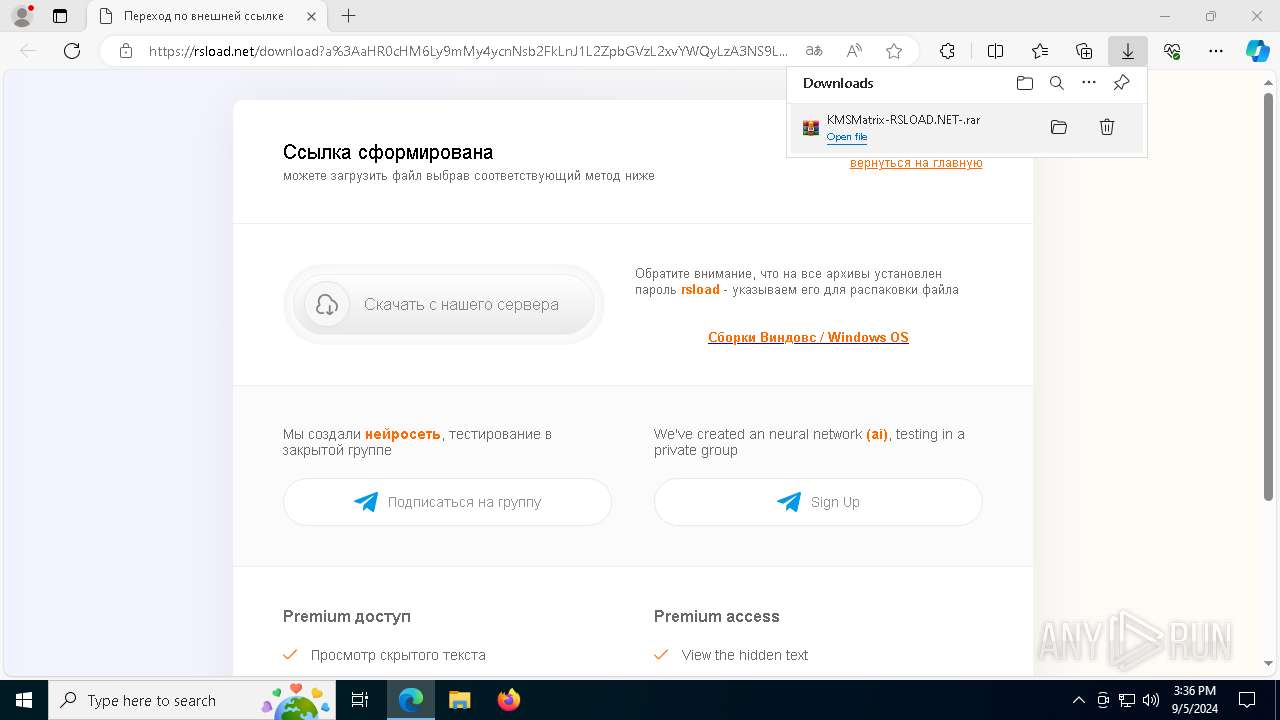
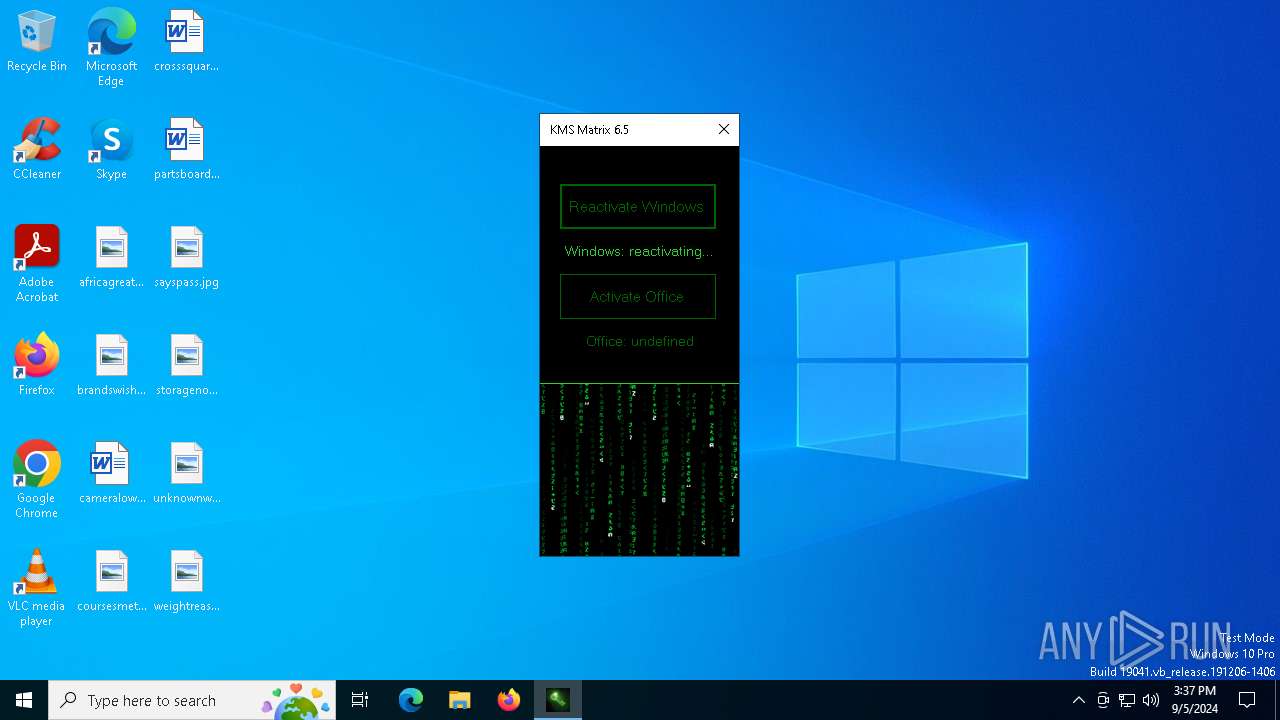
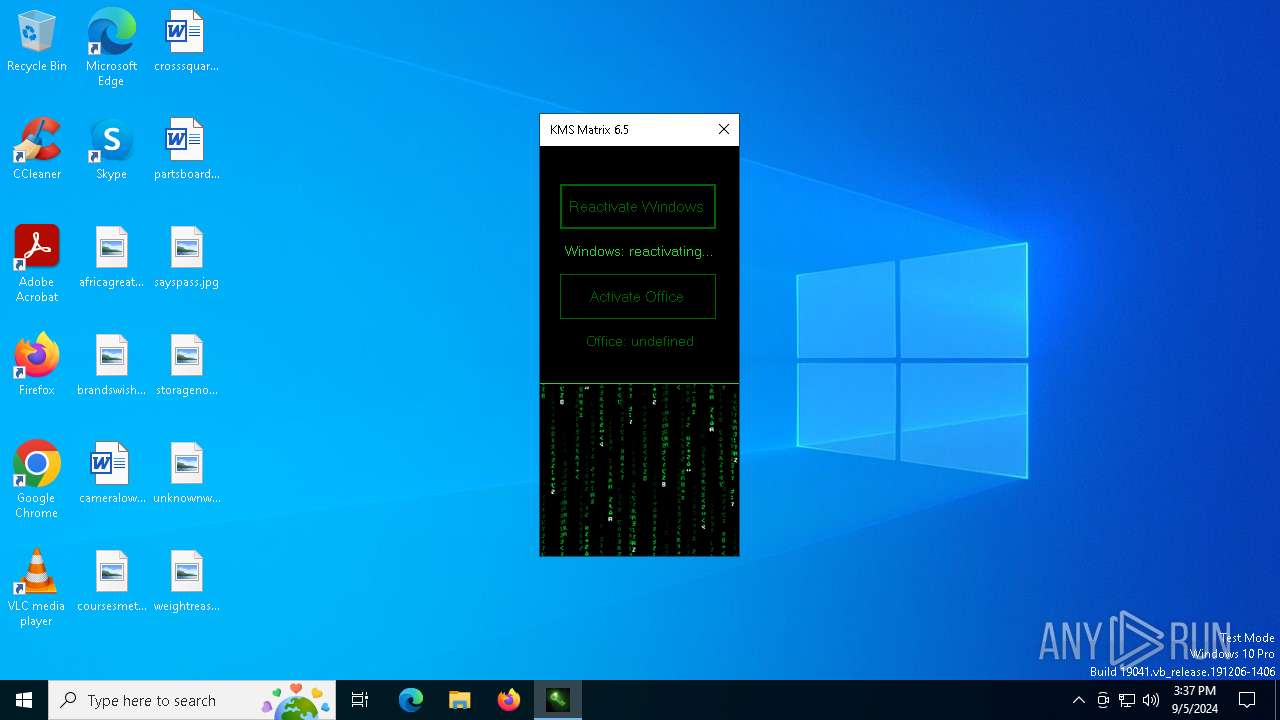
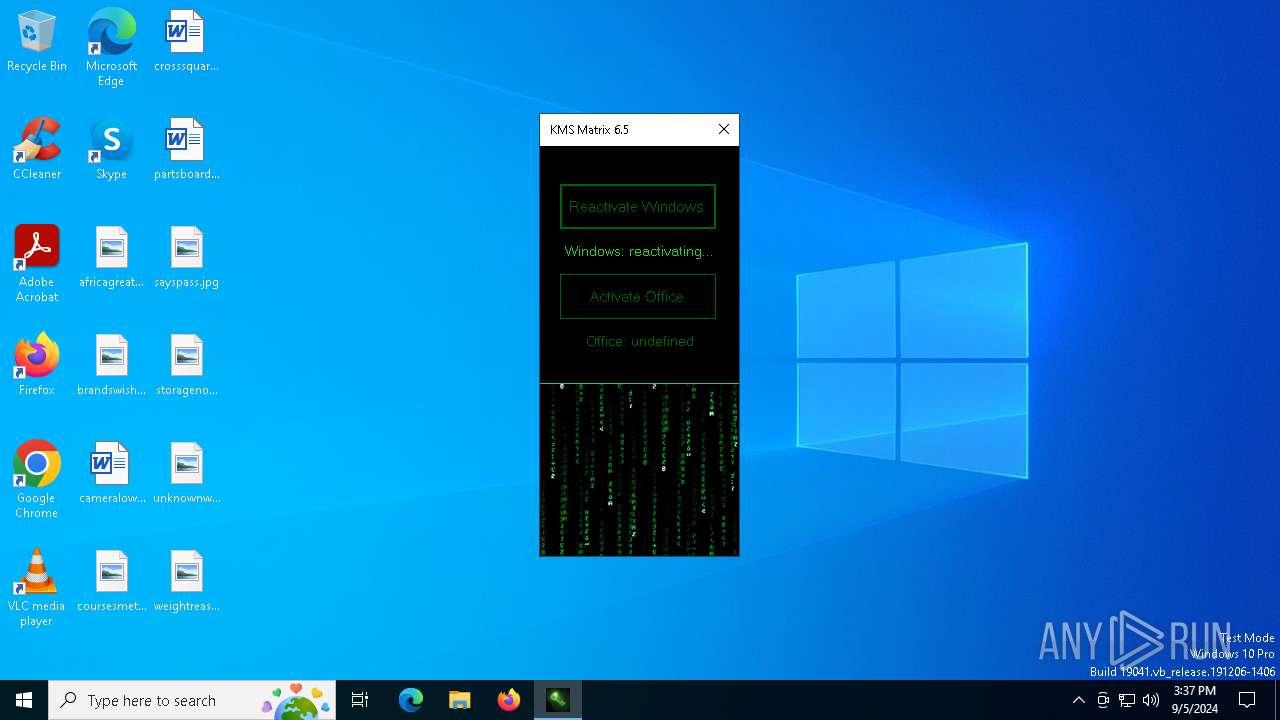
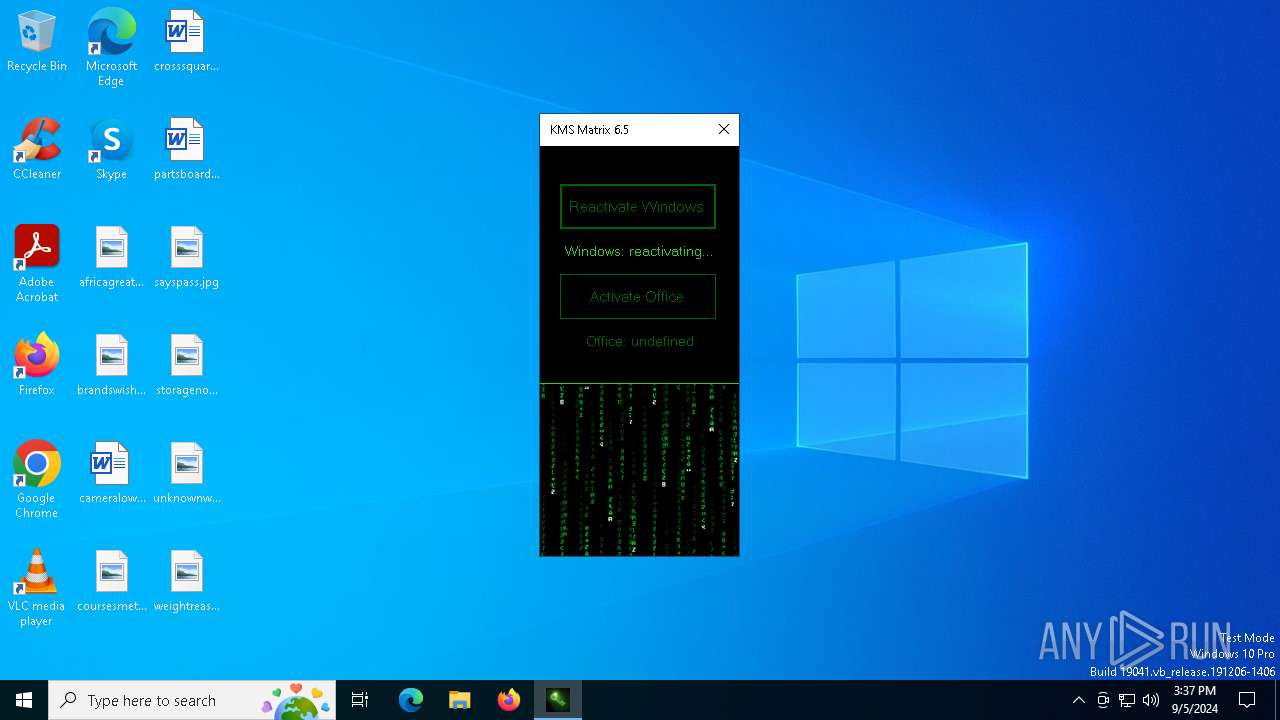
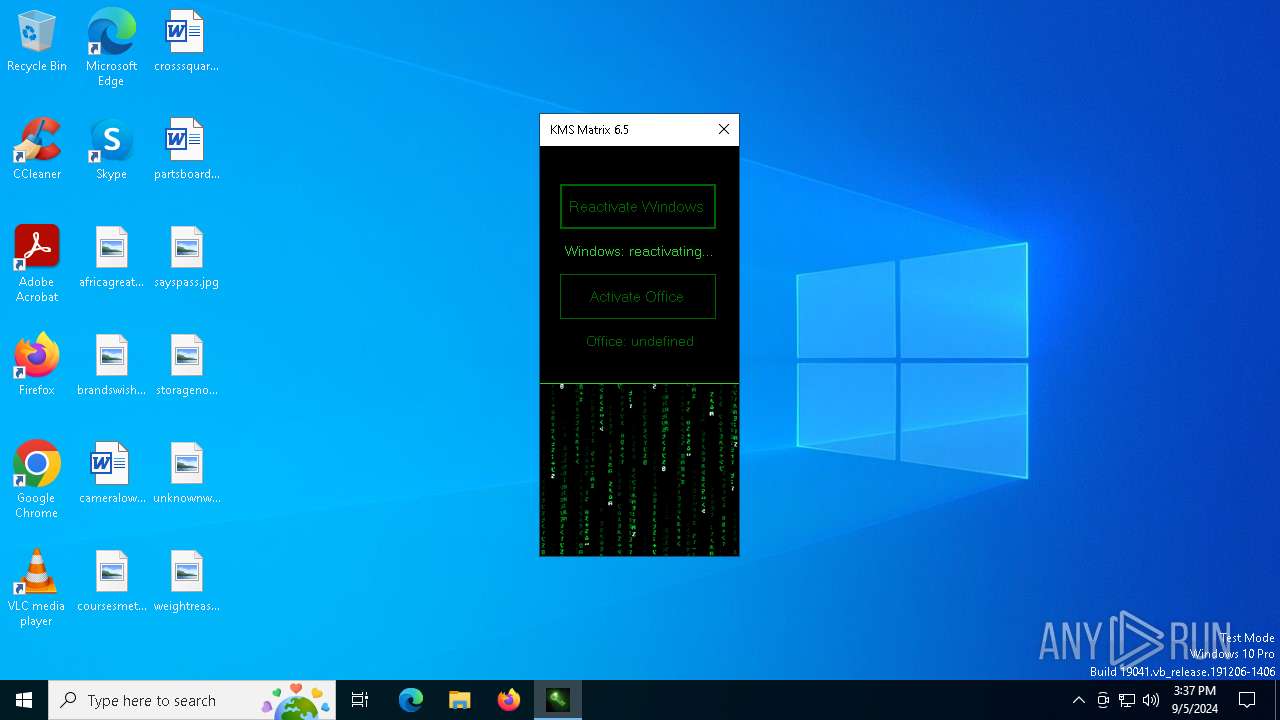
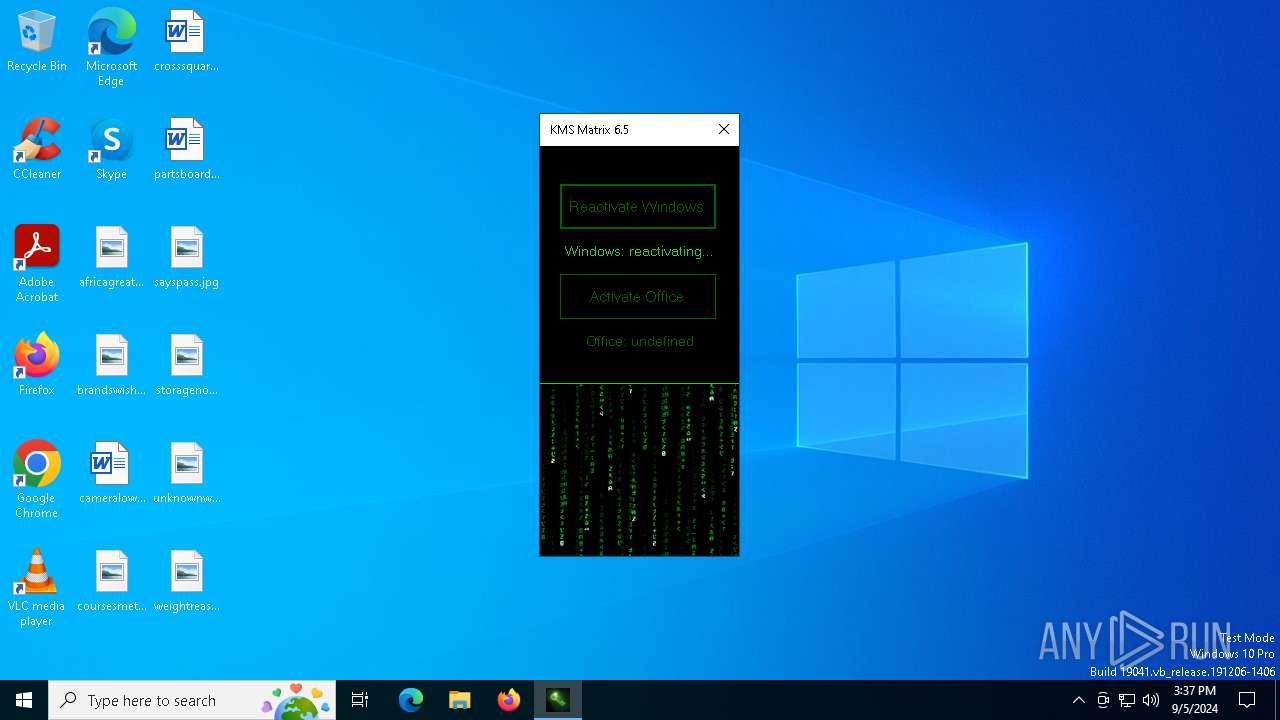
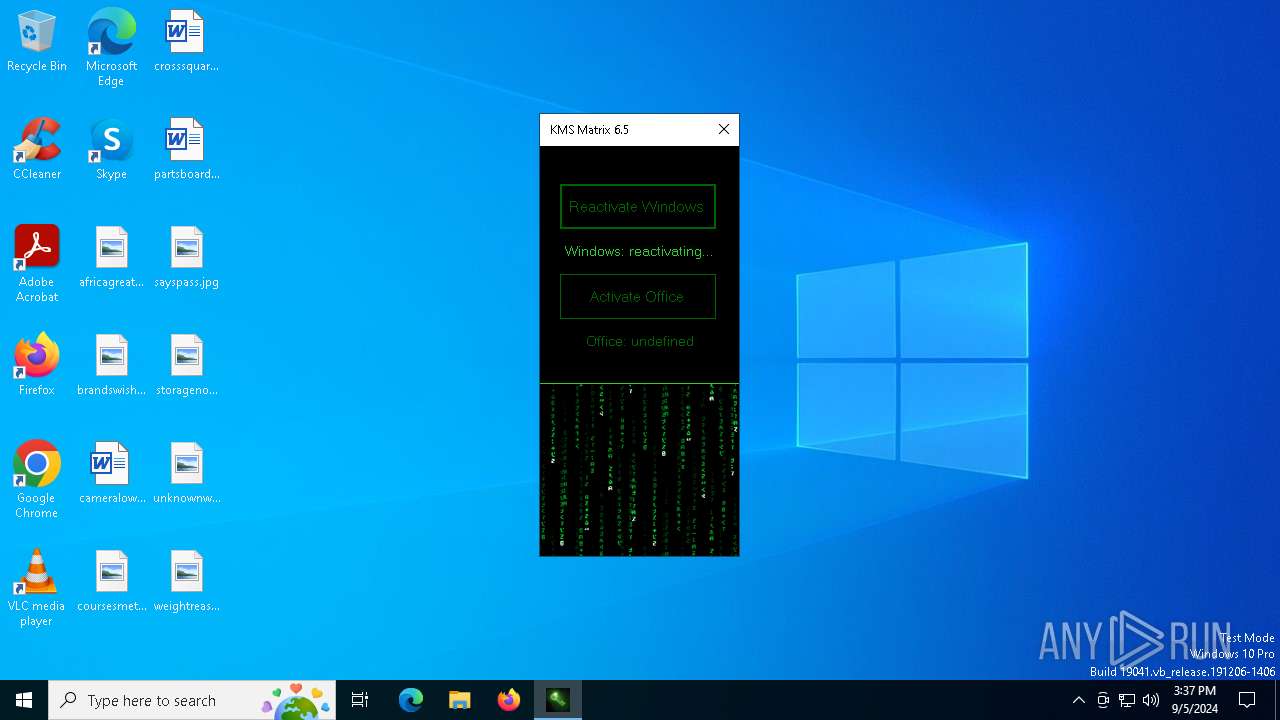
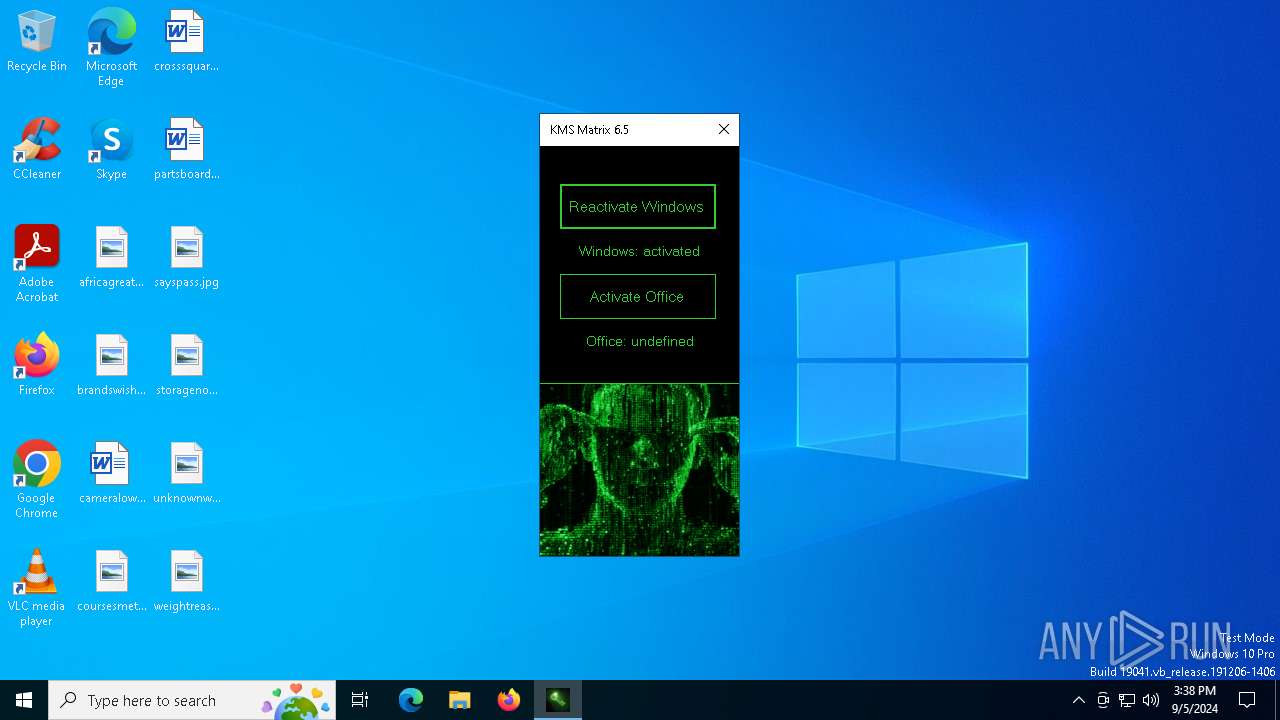
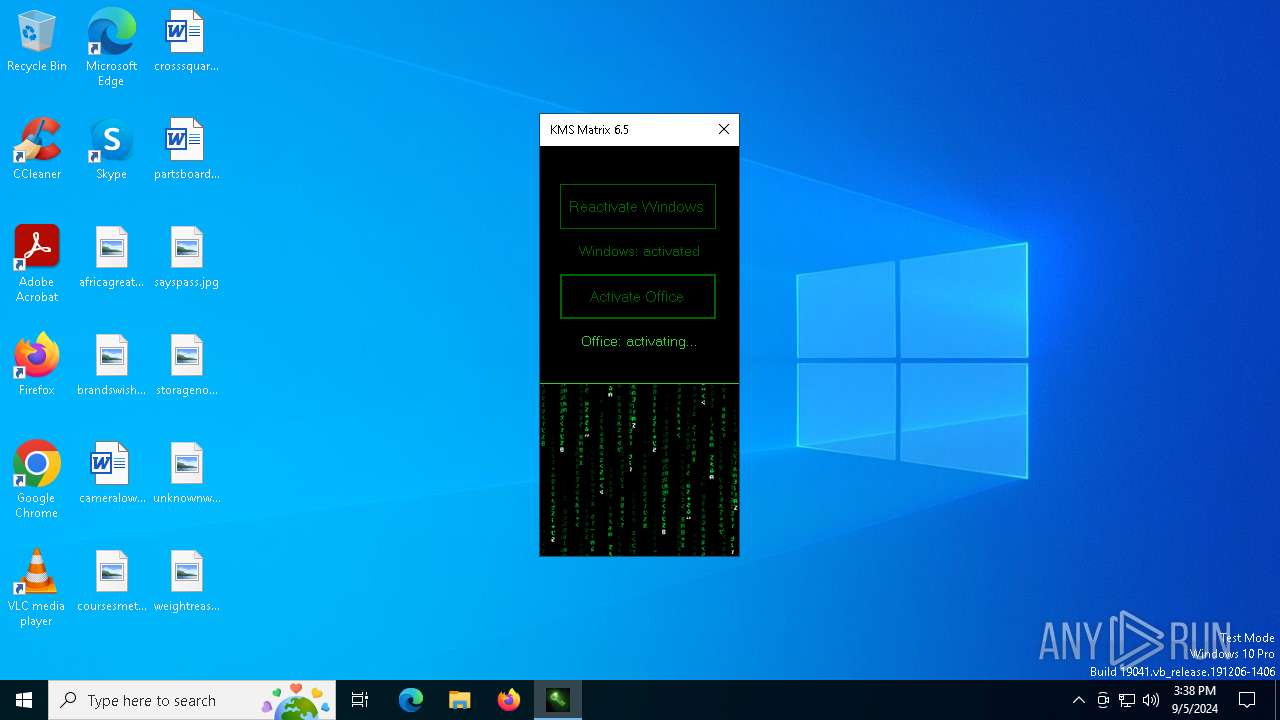
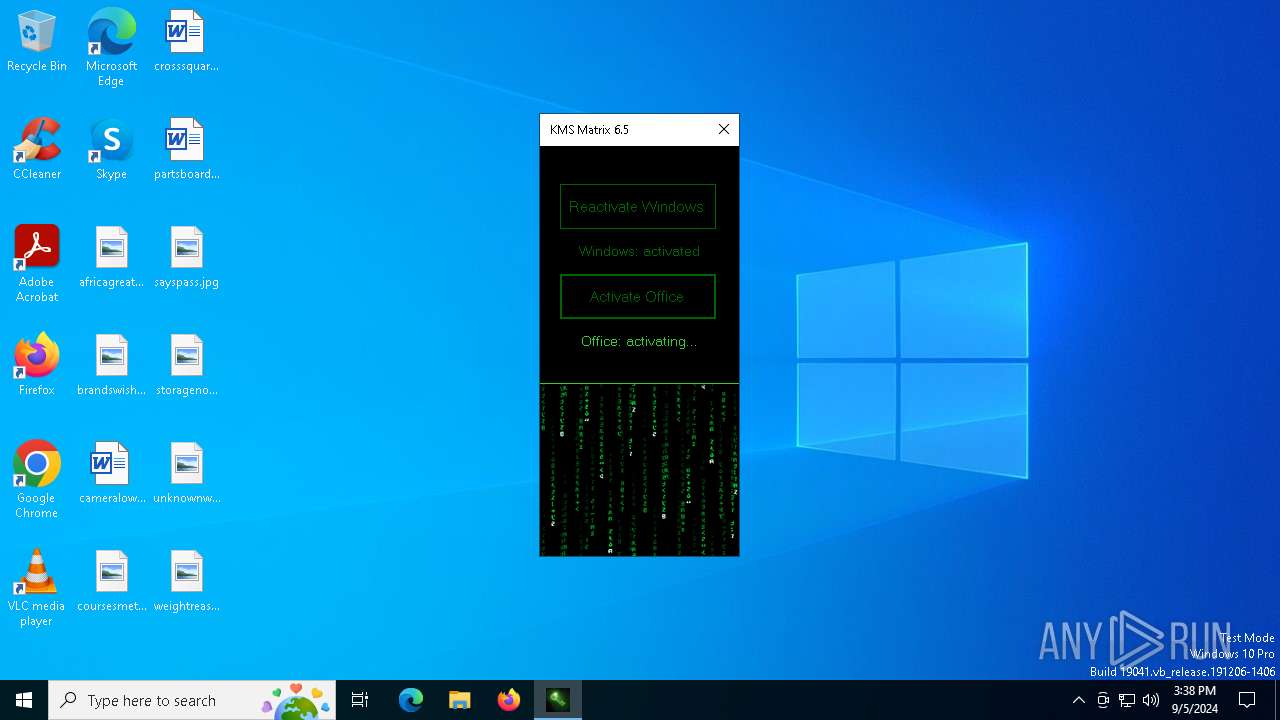
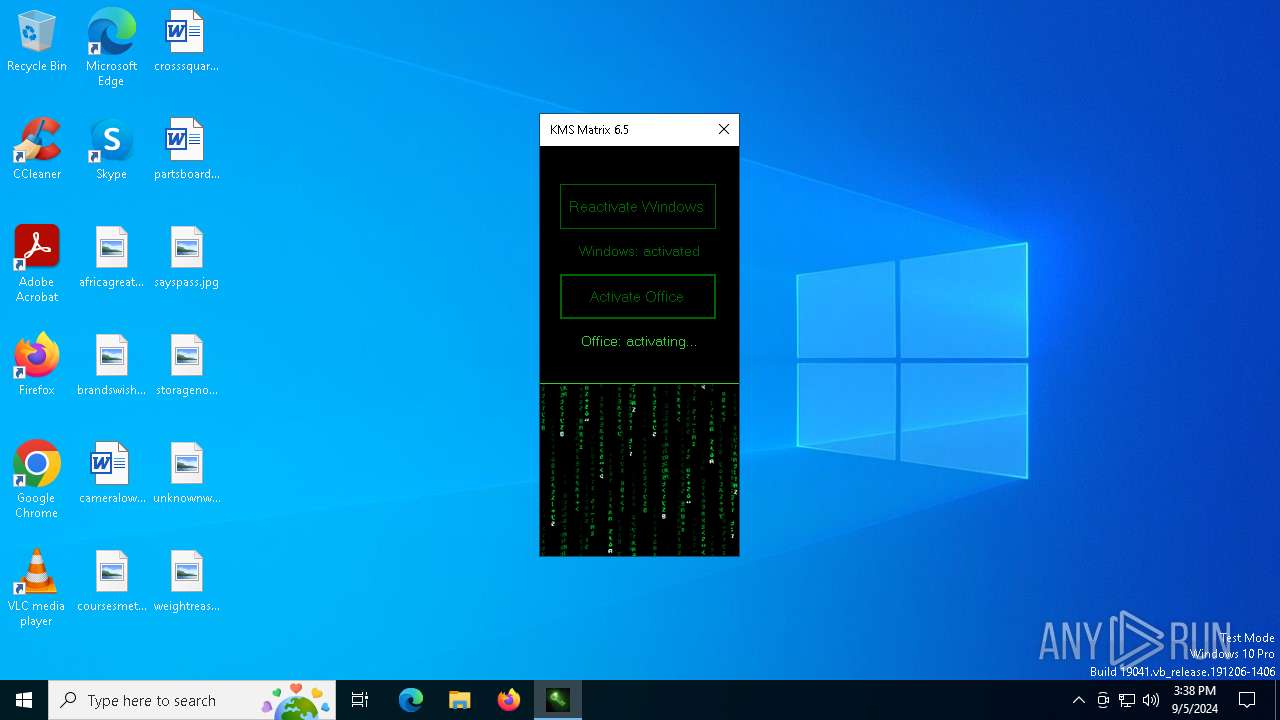
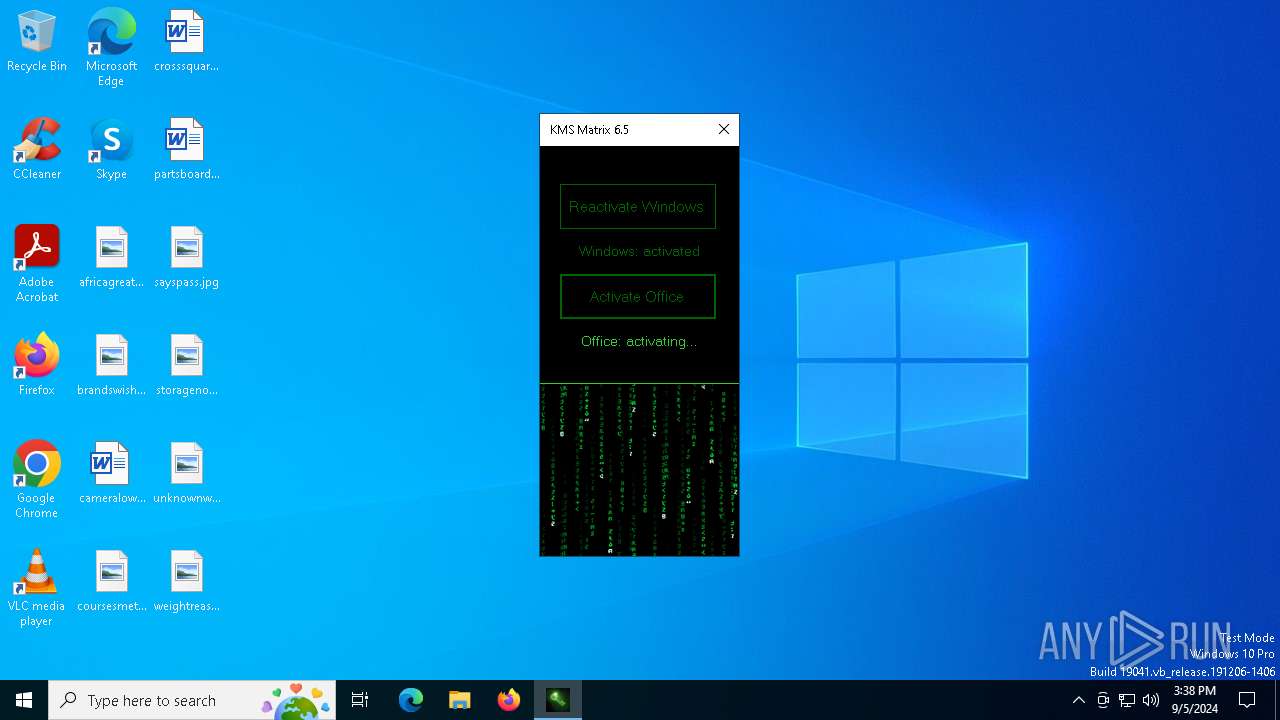
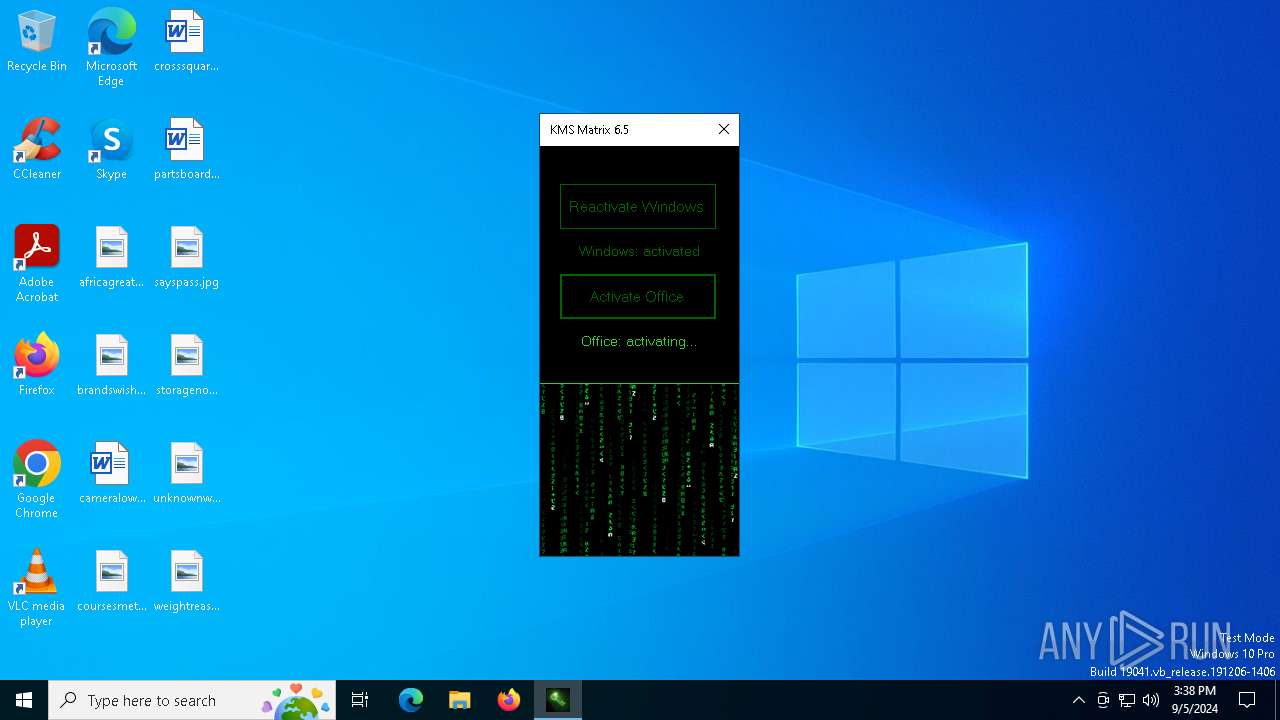
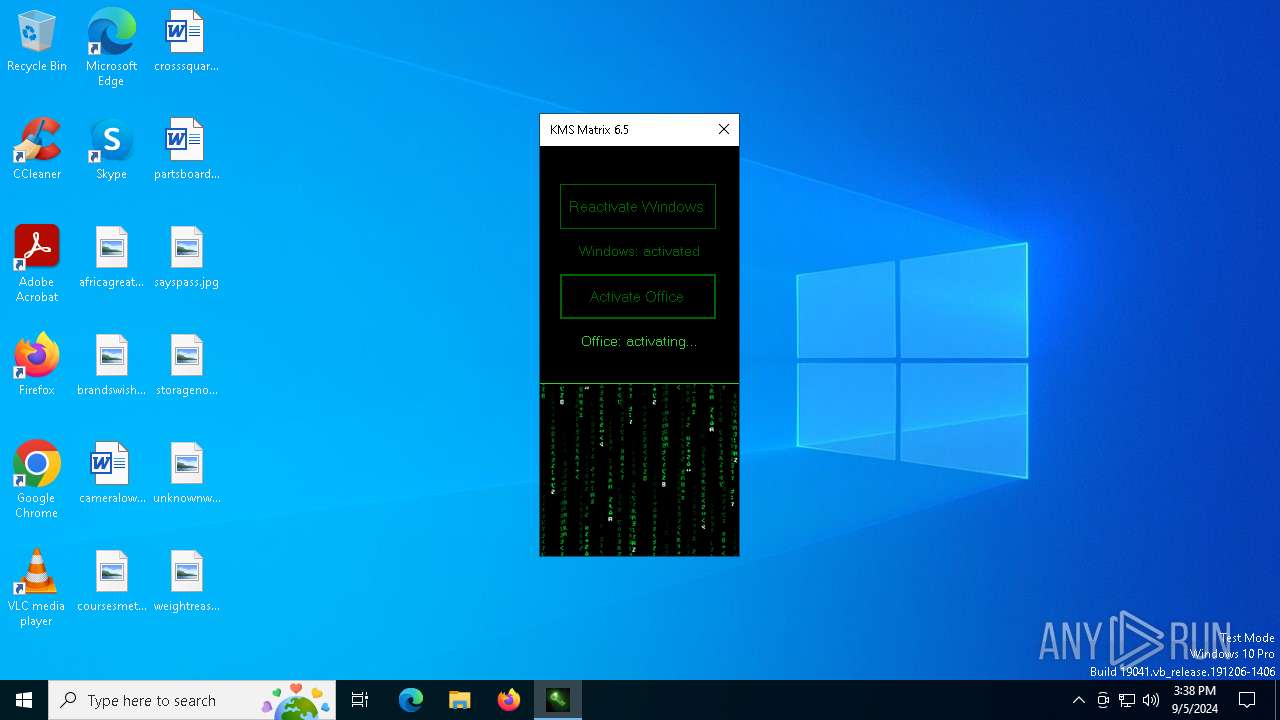
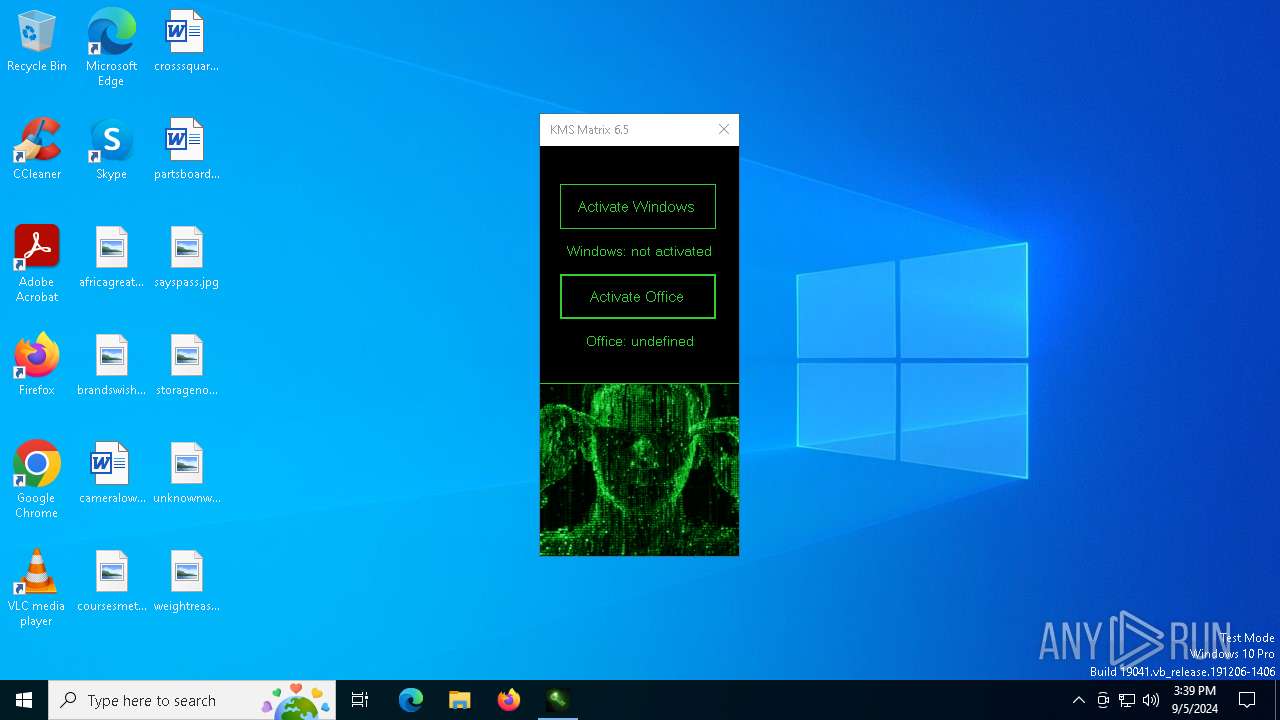
| URL: | https://rsload.net/soft/40165-kms-matrix.html |
| Full analysis: | https://app.any.run/tasks/0cc63990-35f9-4f37-b74a-5a5f51ce2f24 |
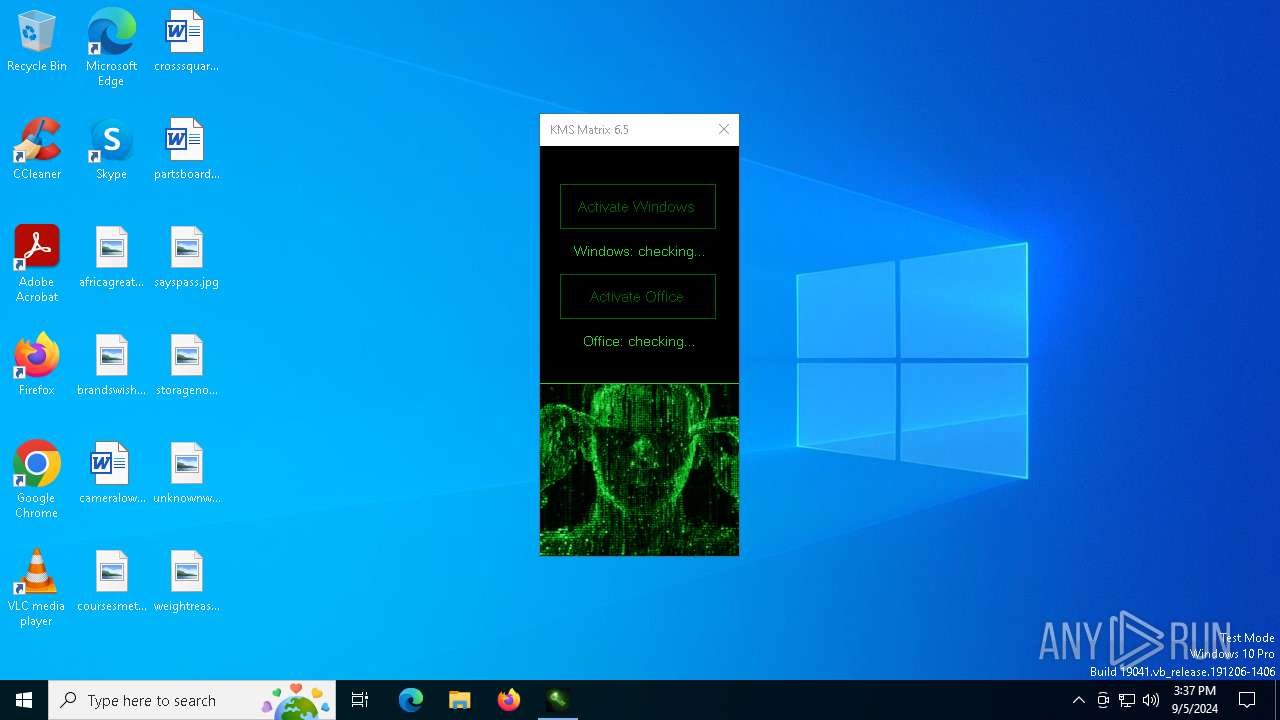
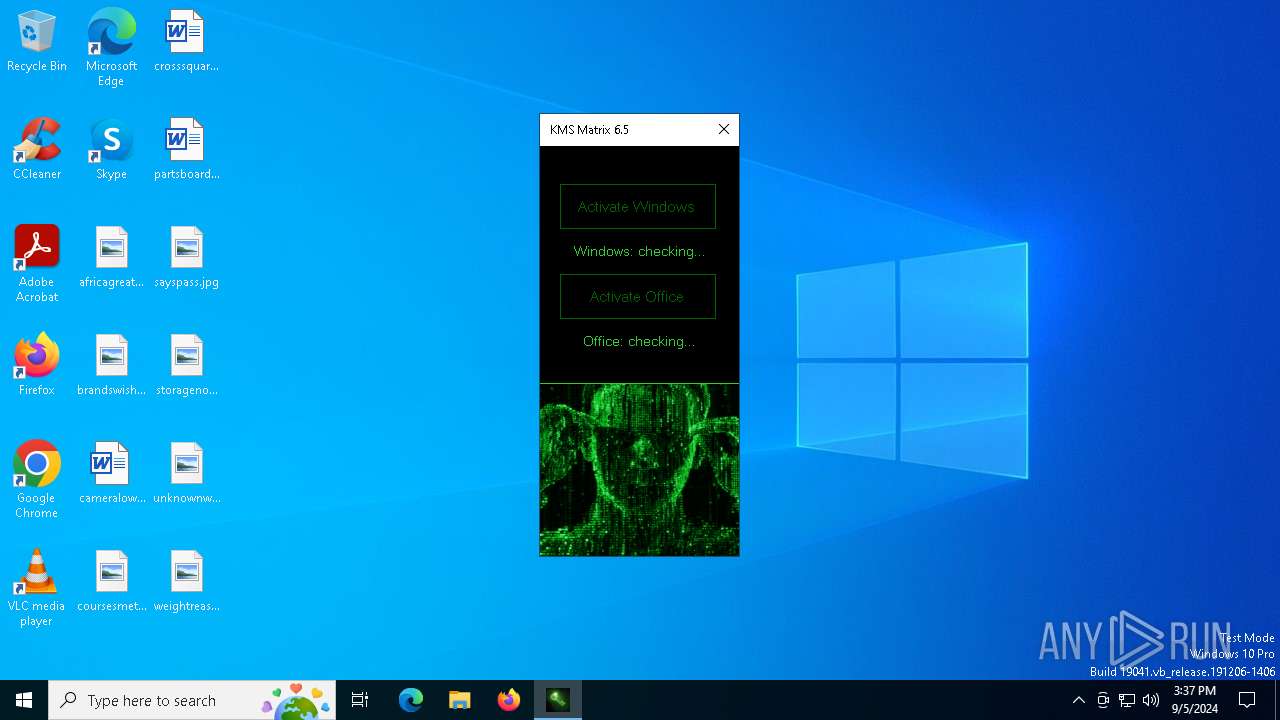
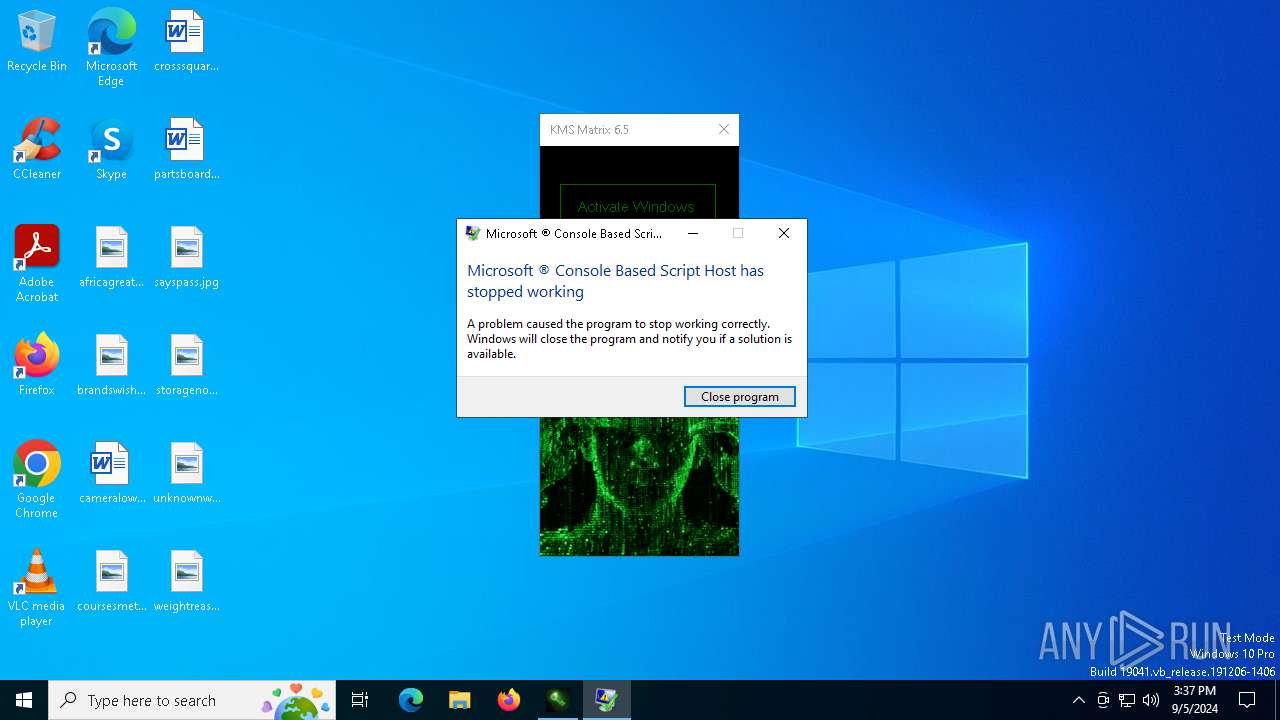
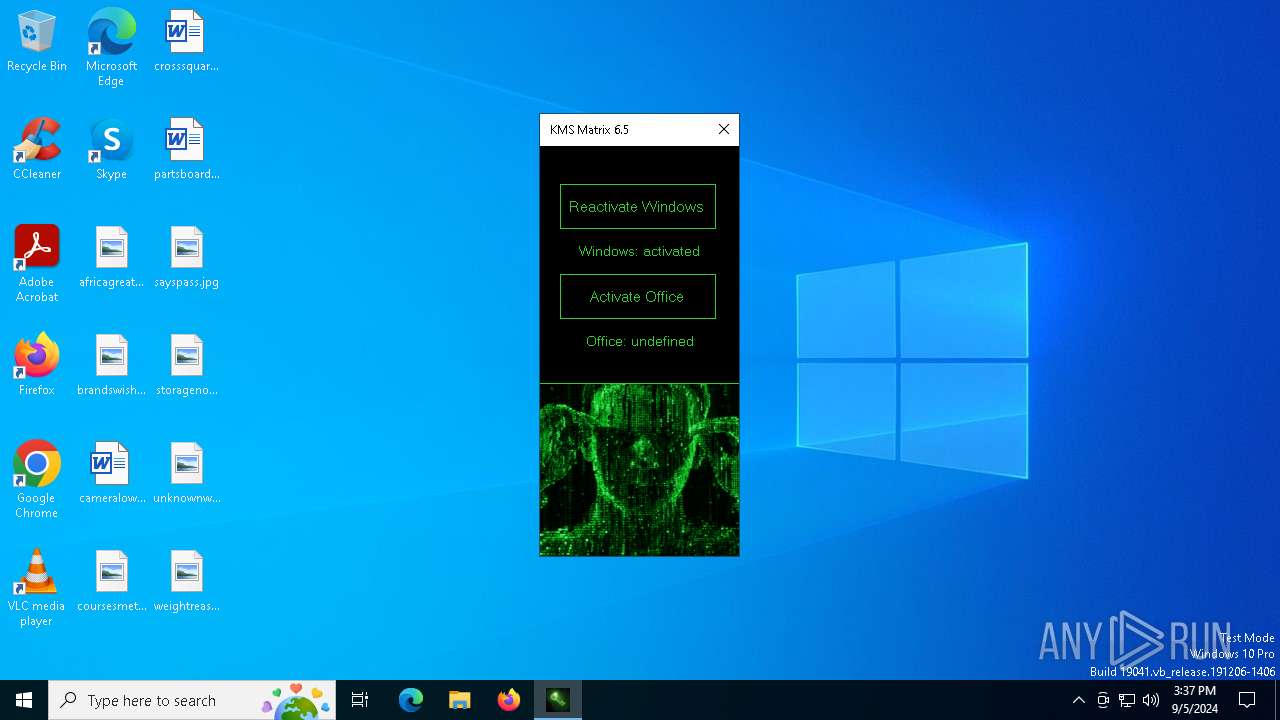
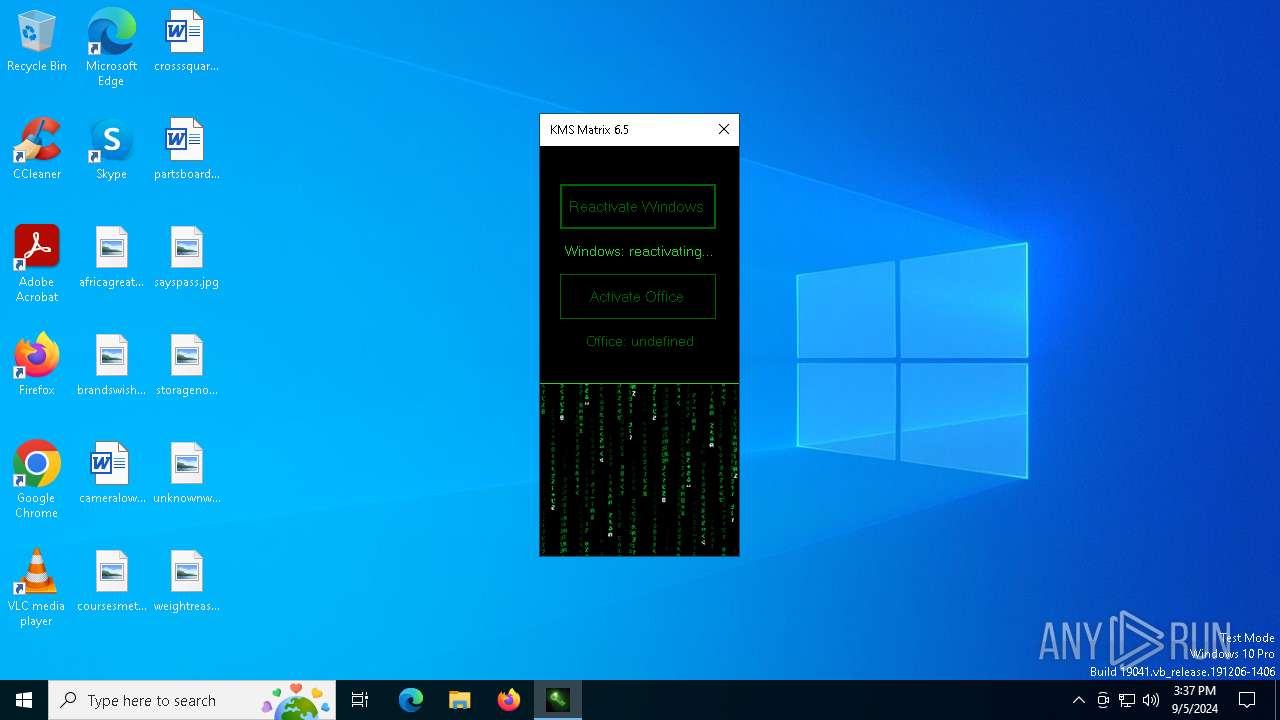
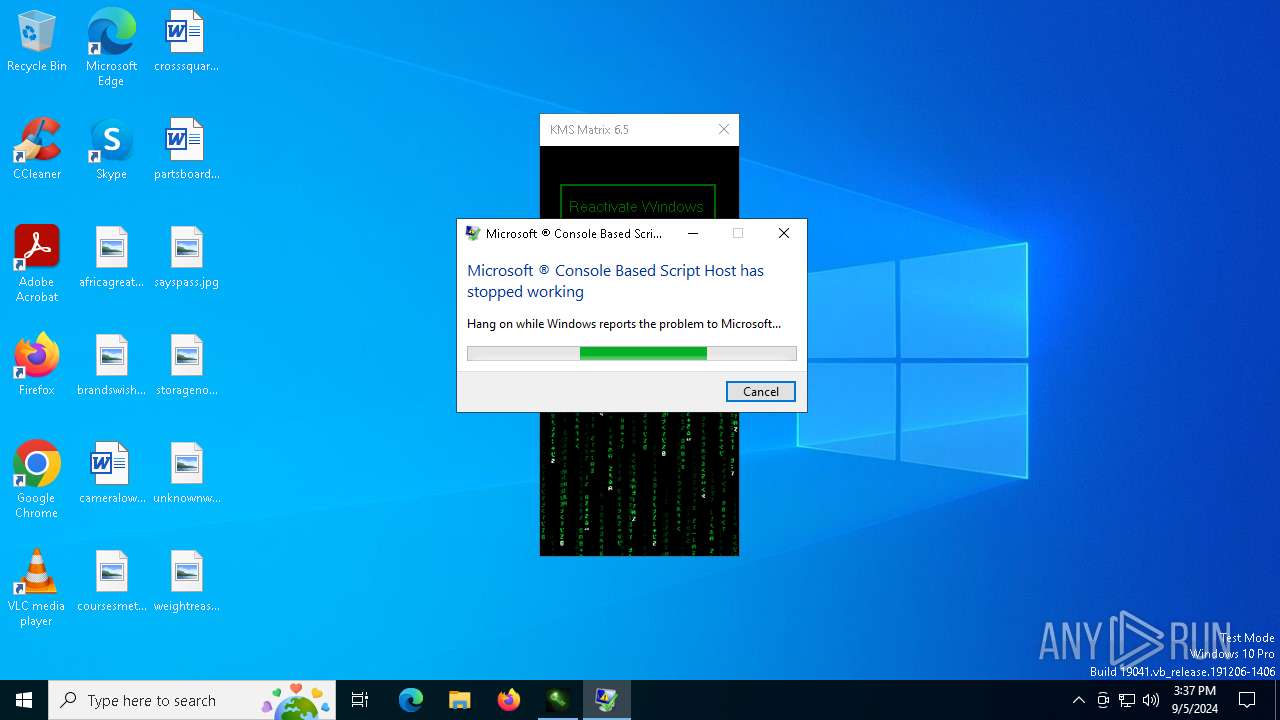
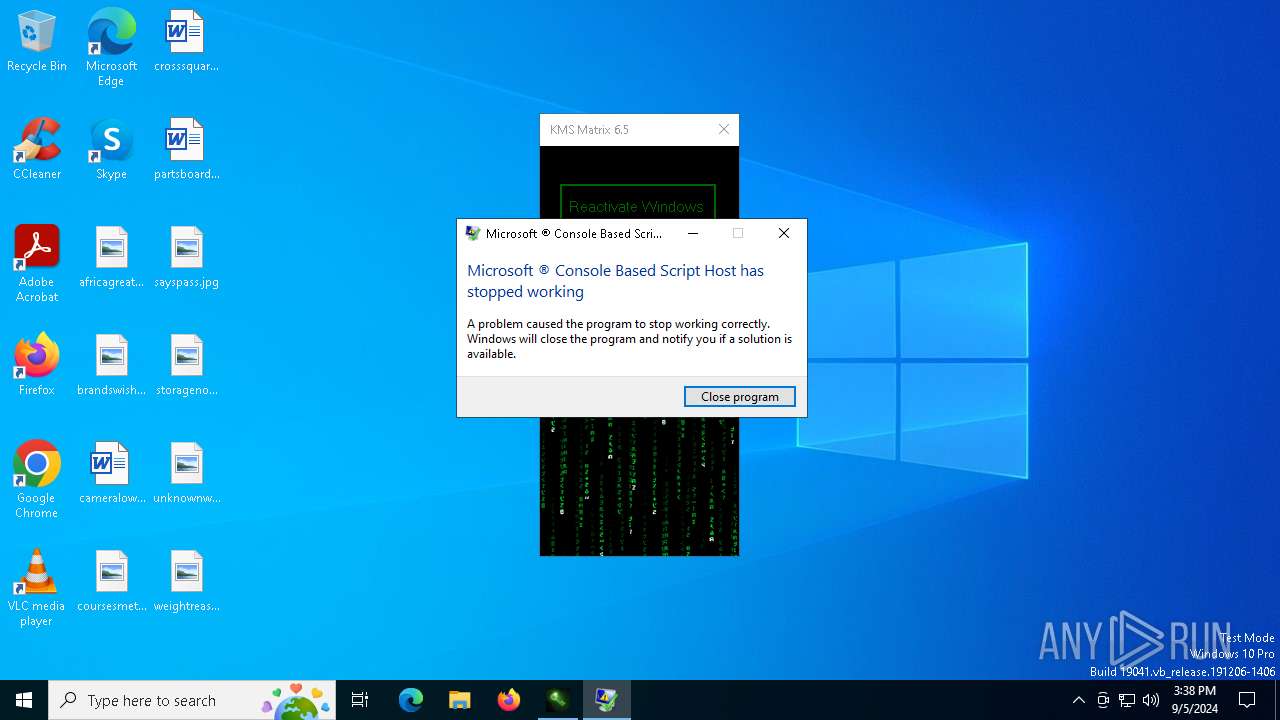
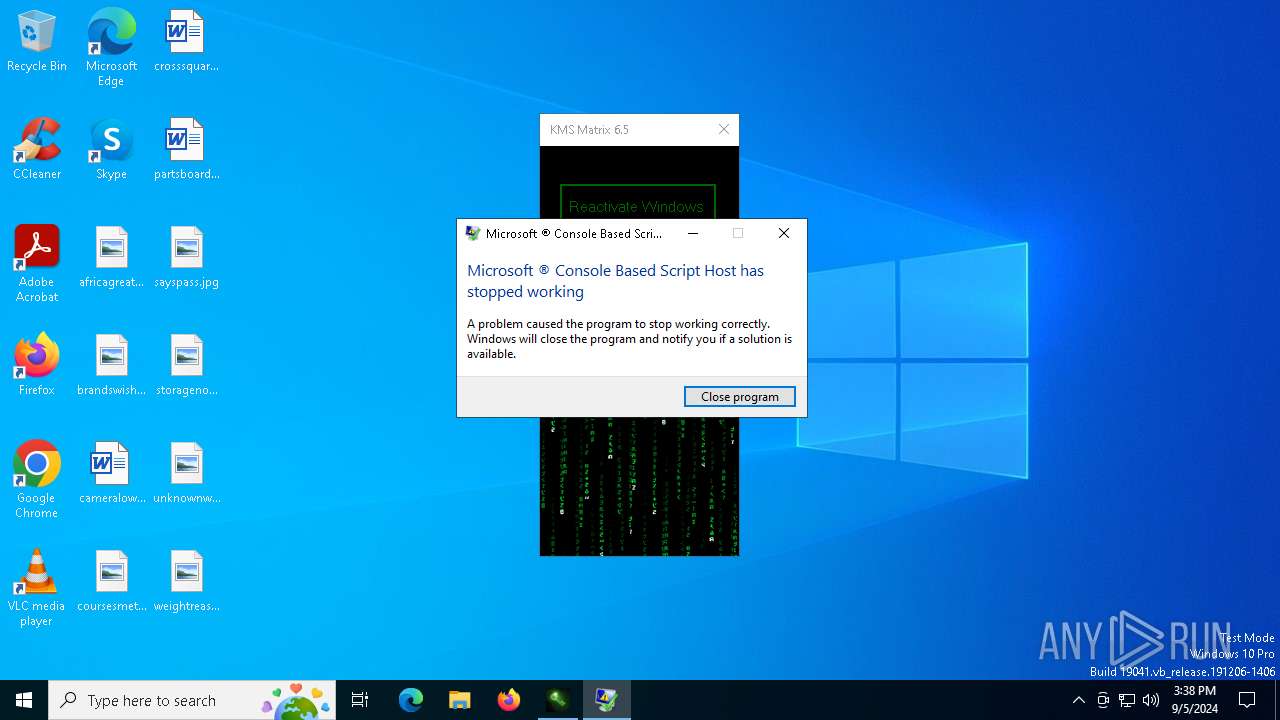
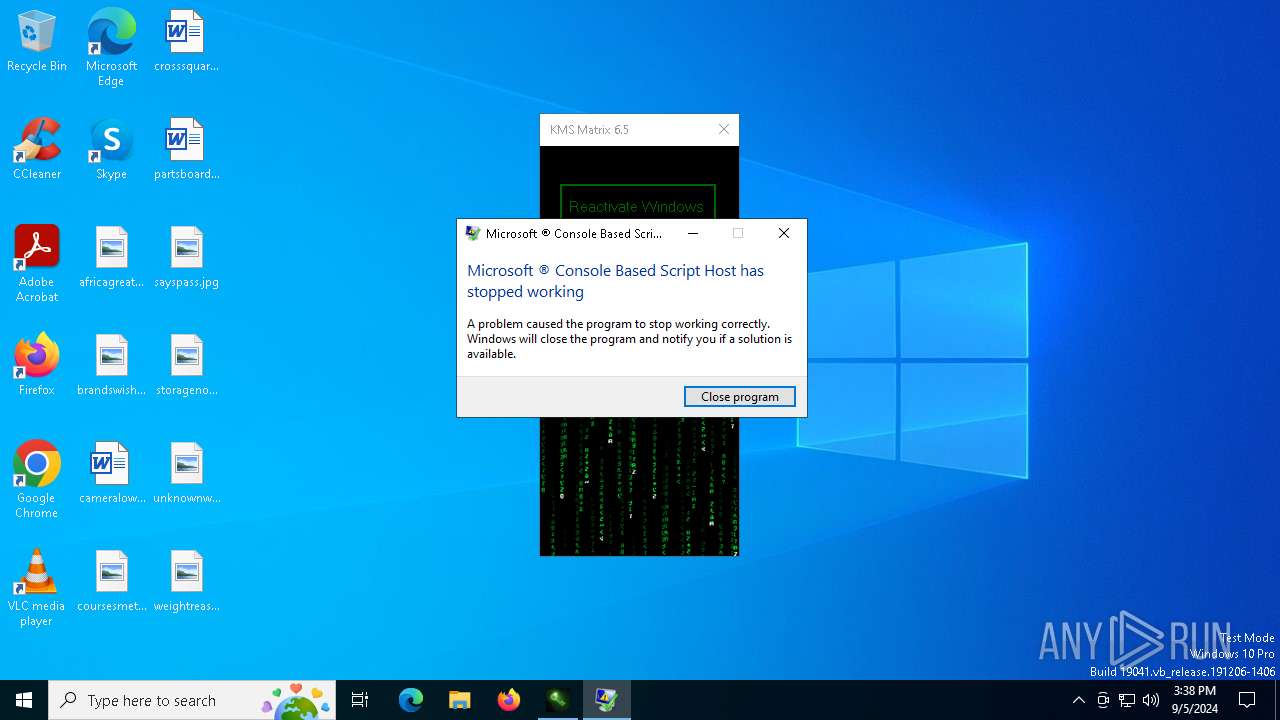
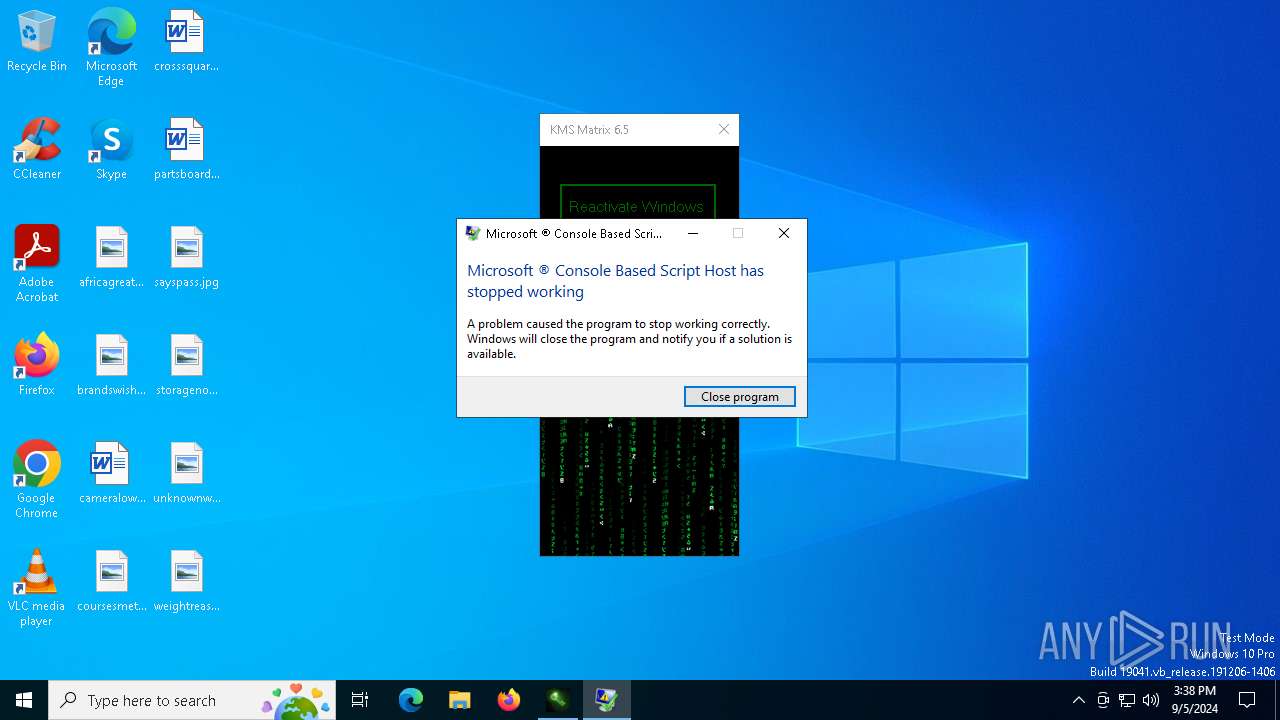
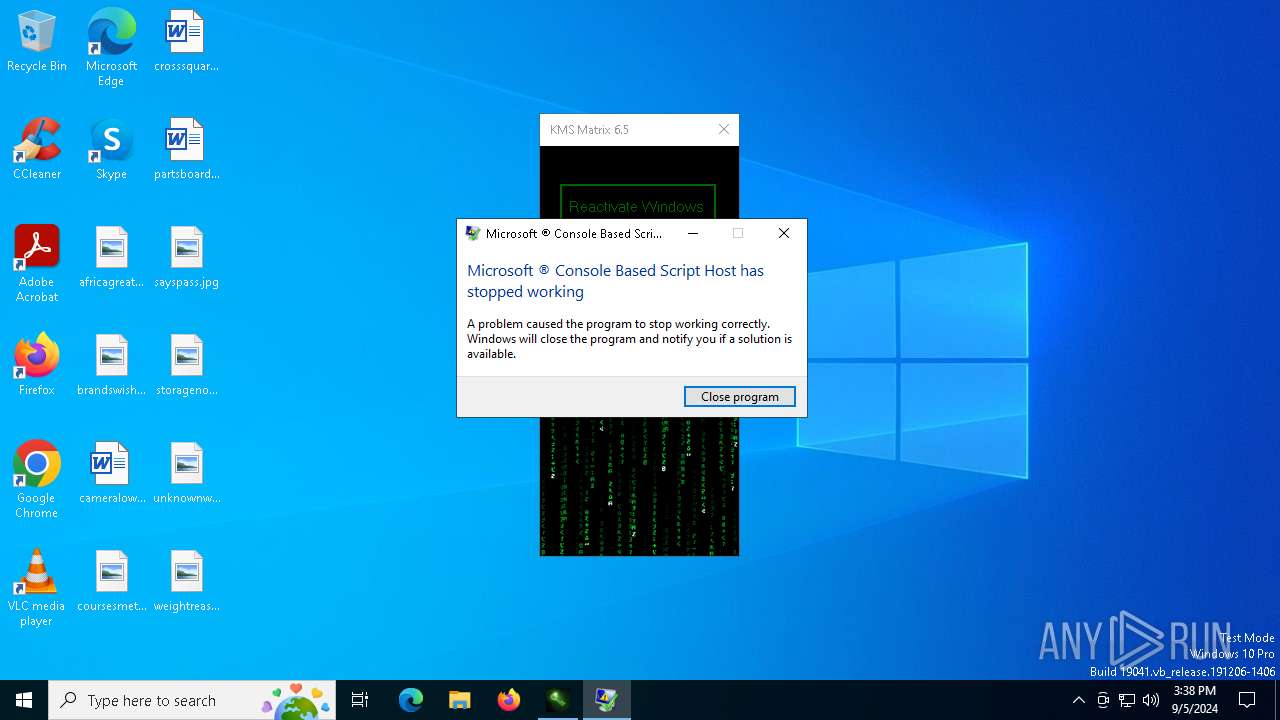
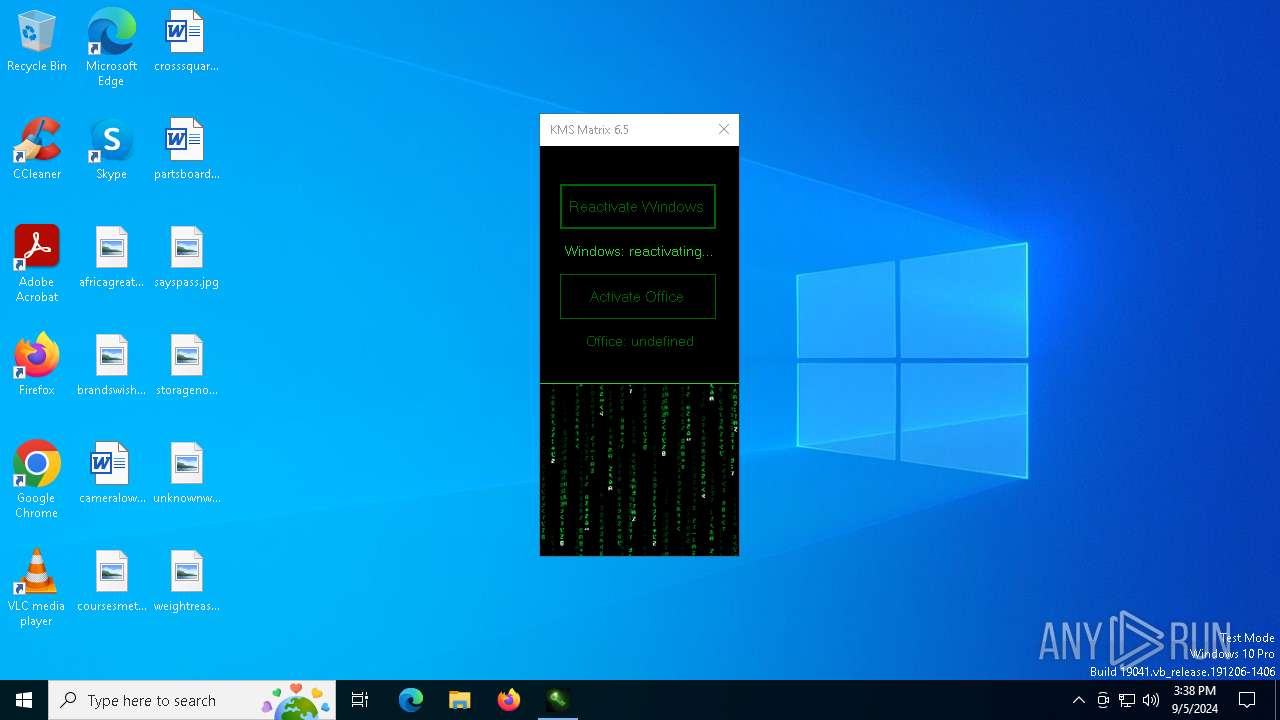
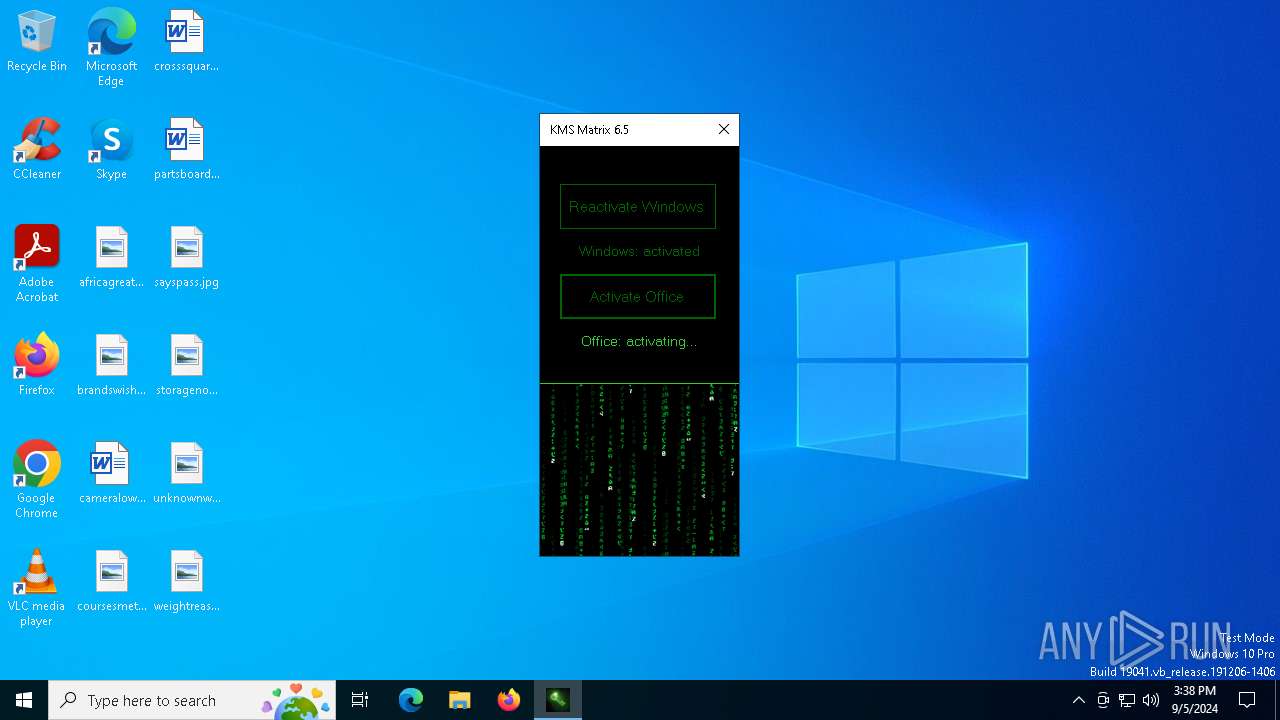
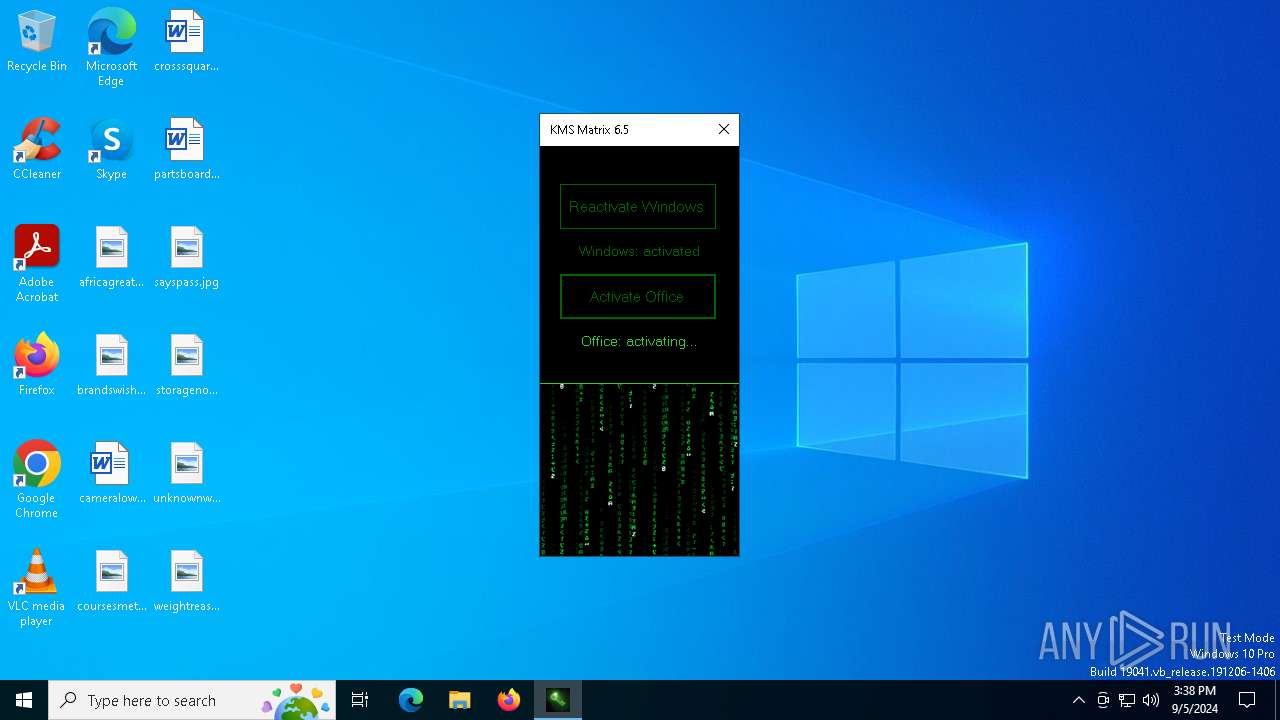
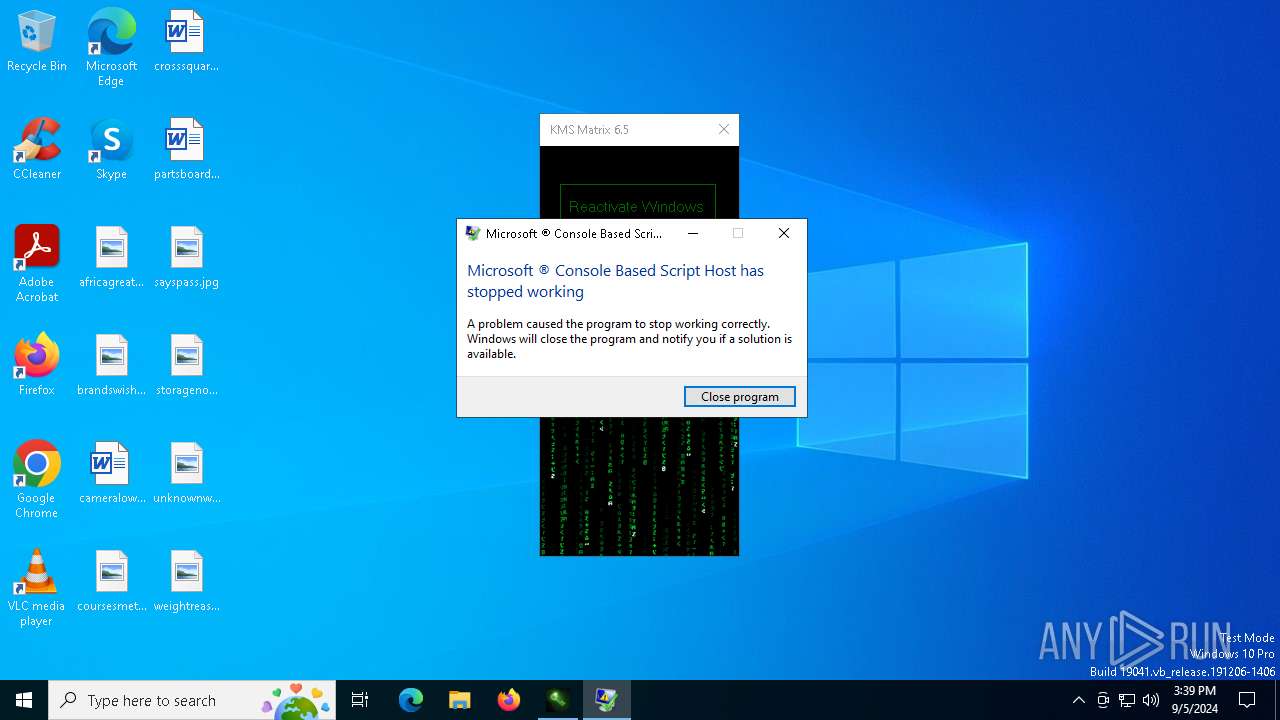
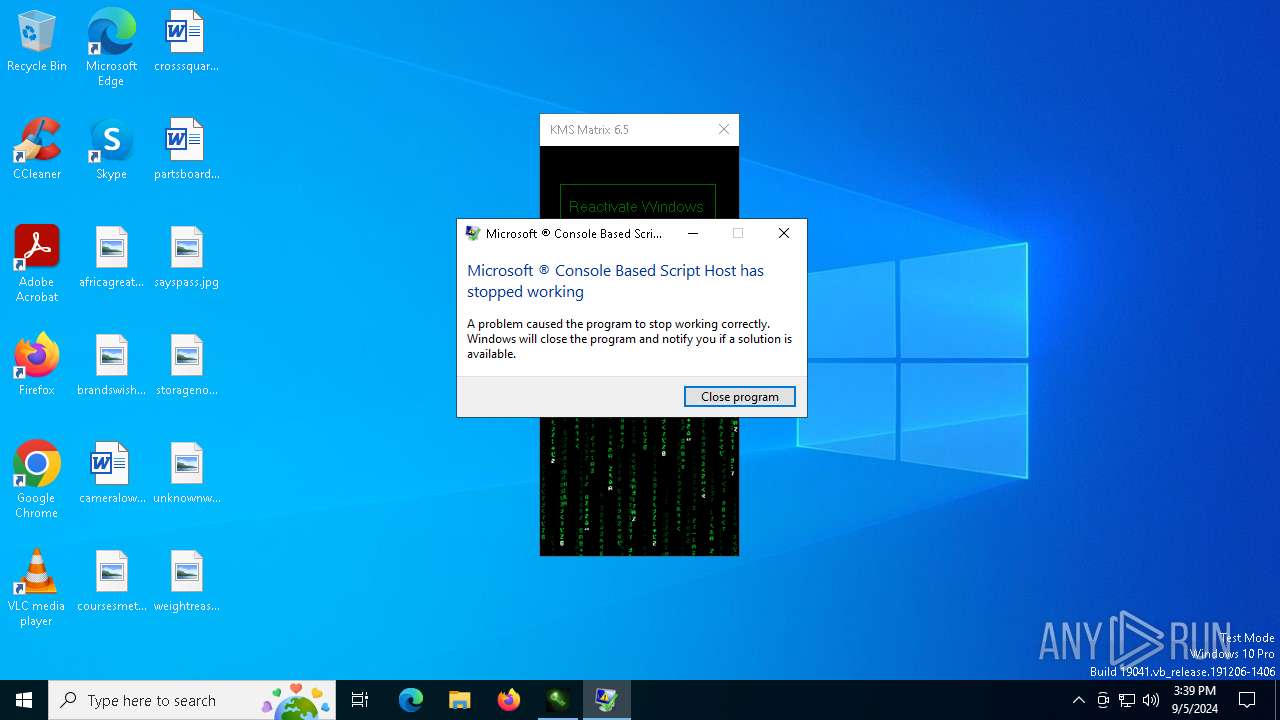
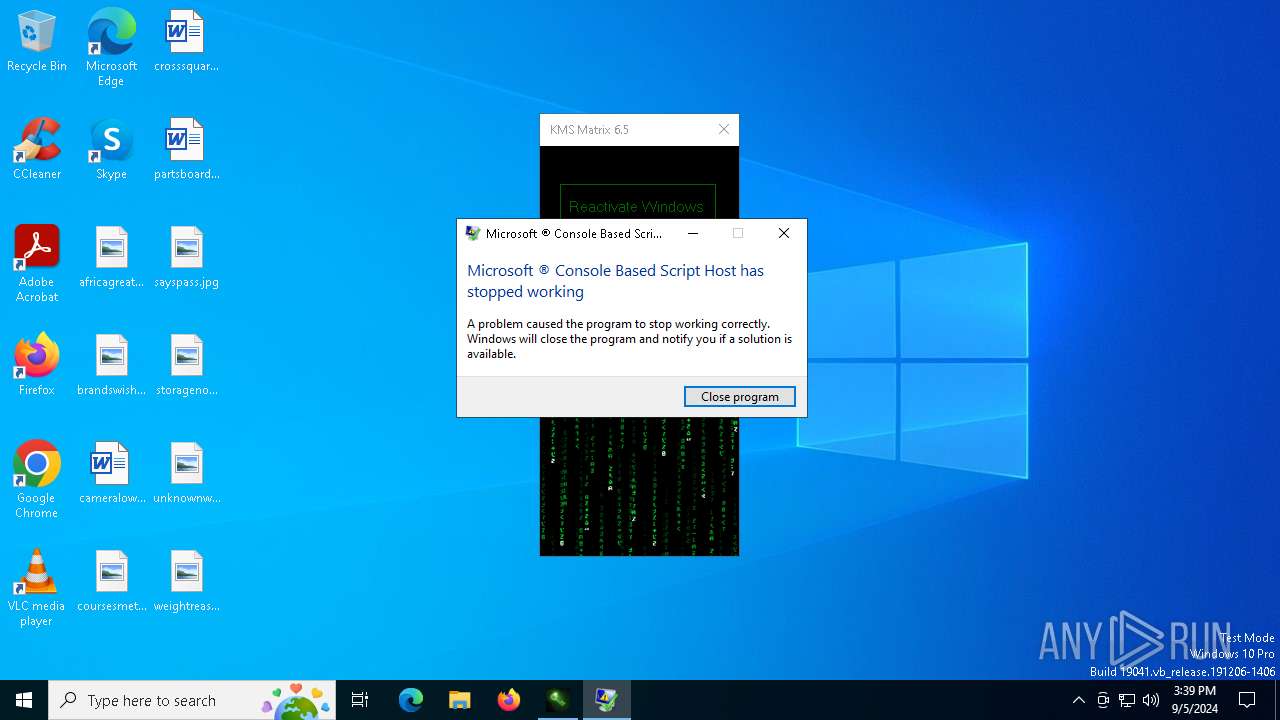
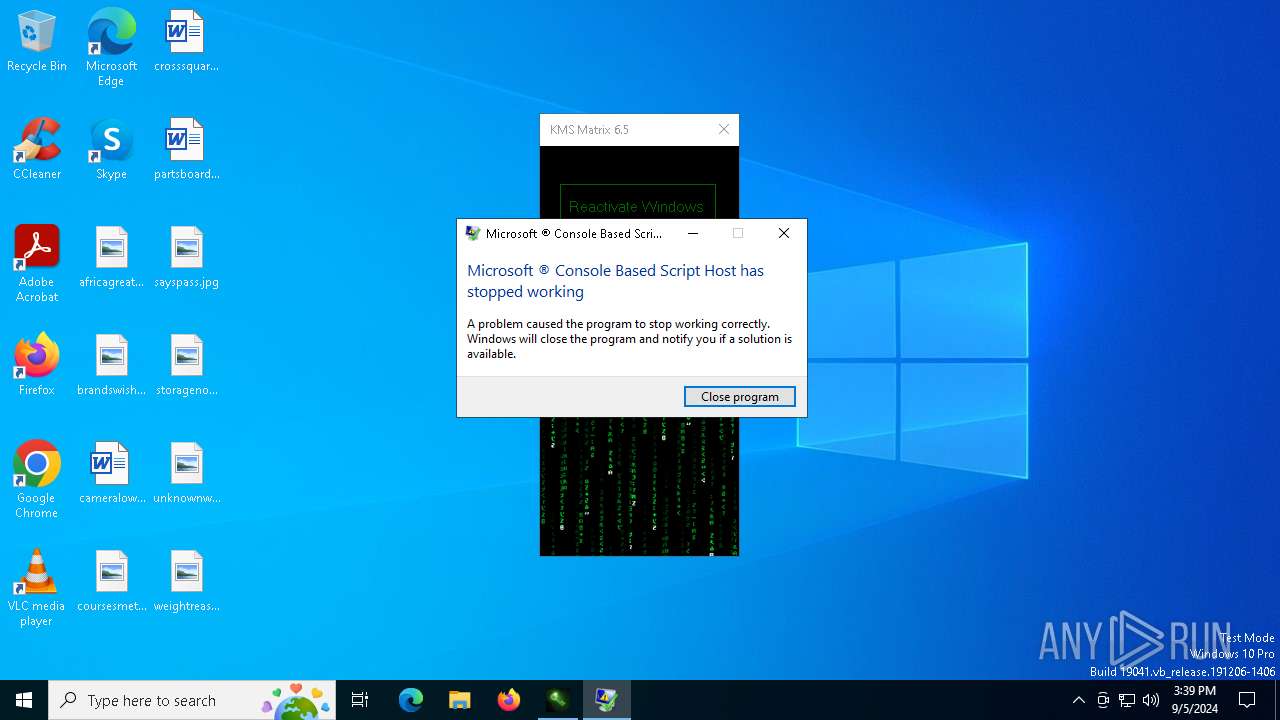
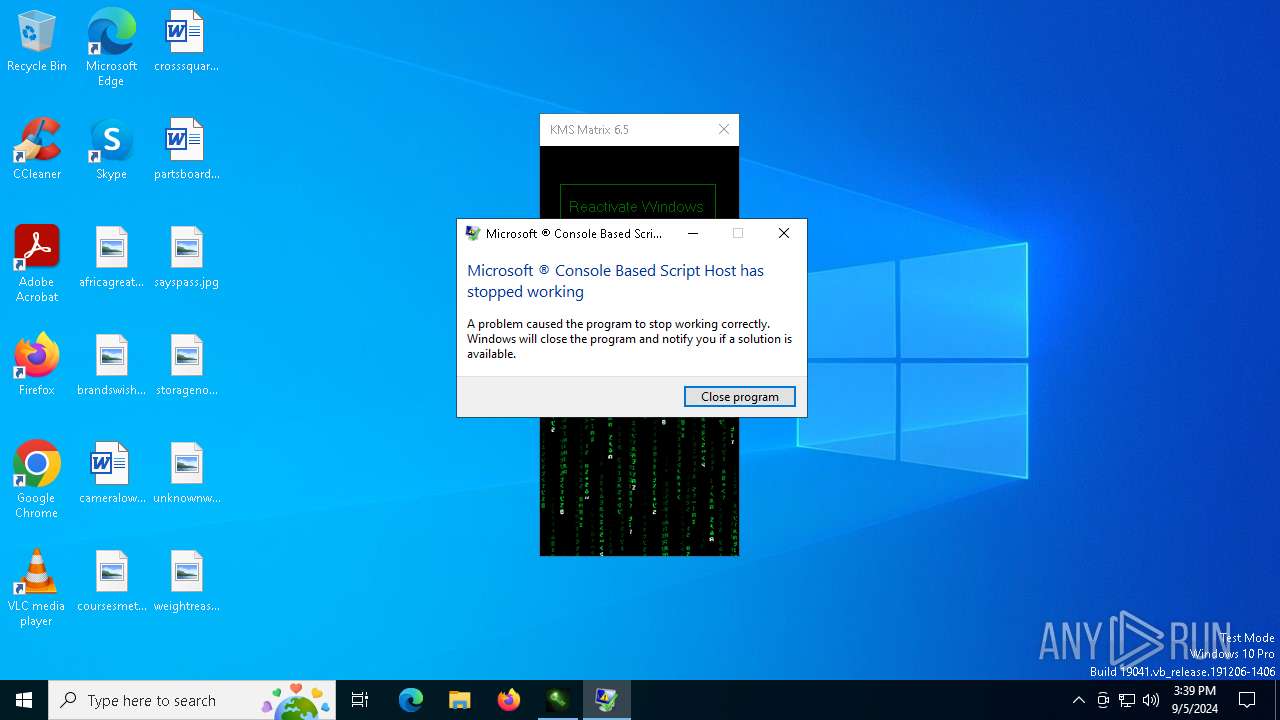
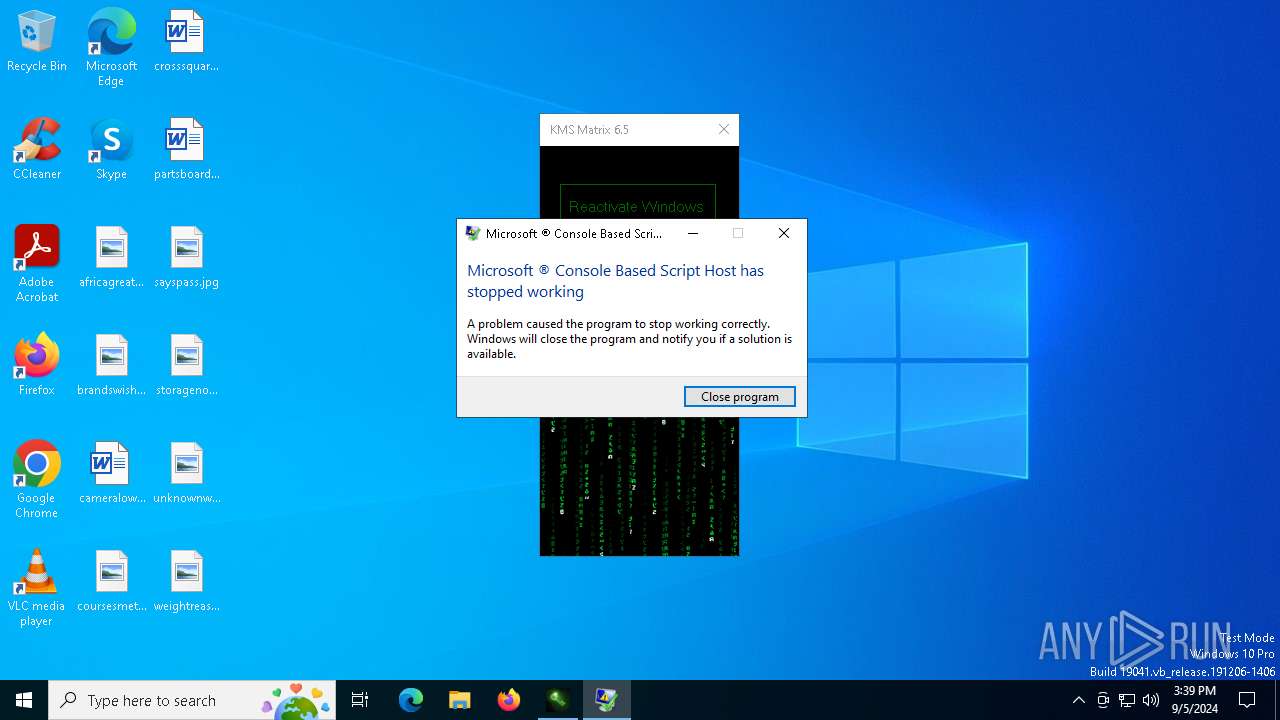
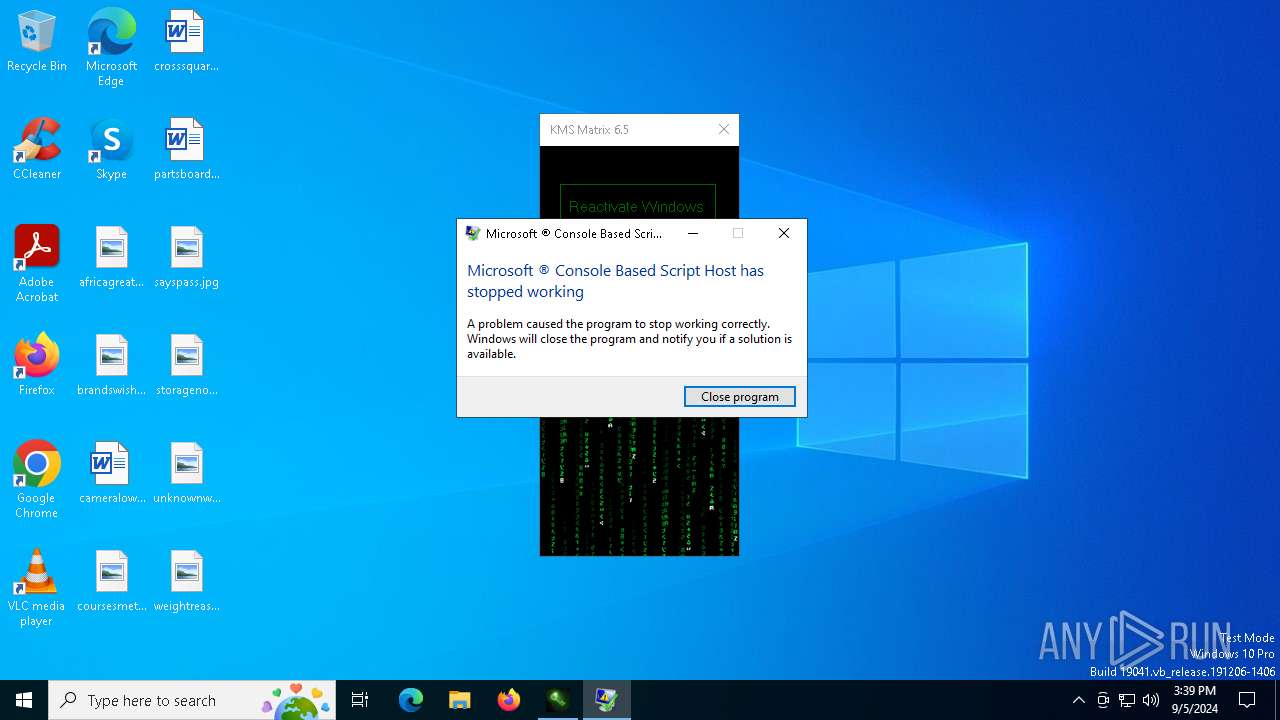
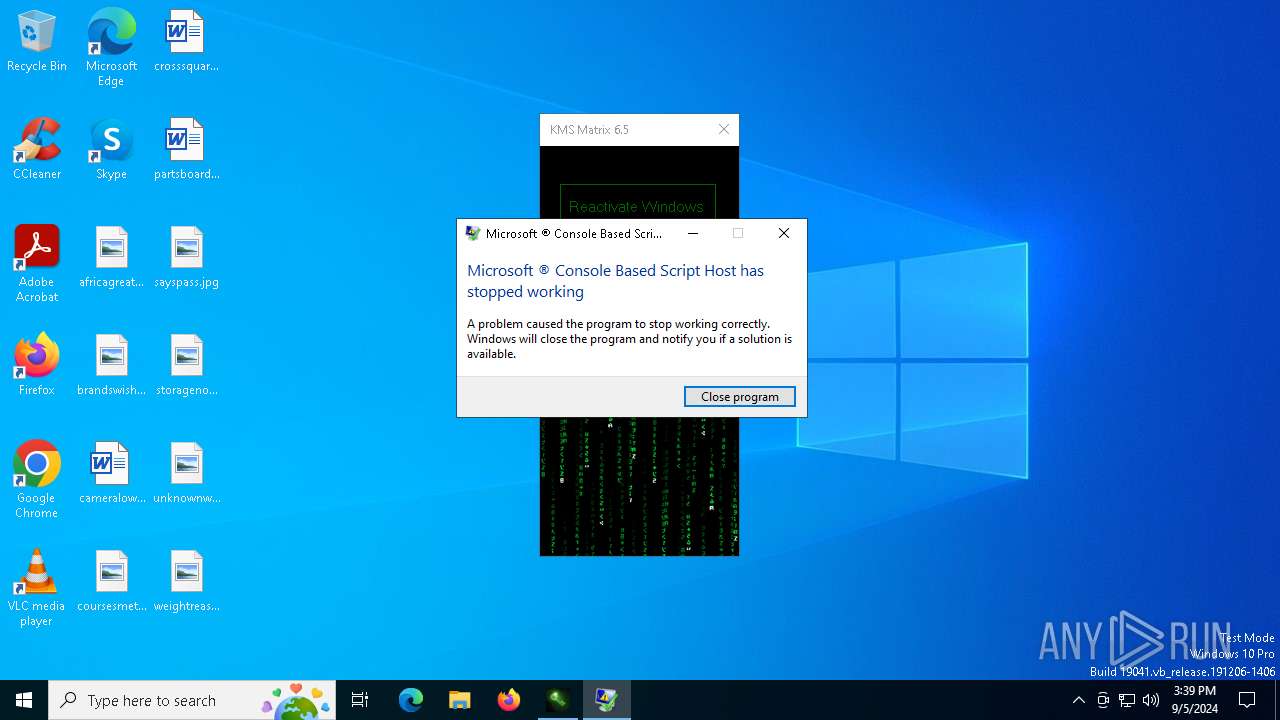
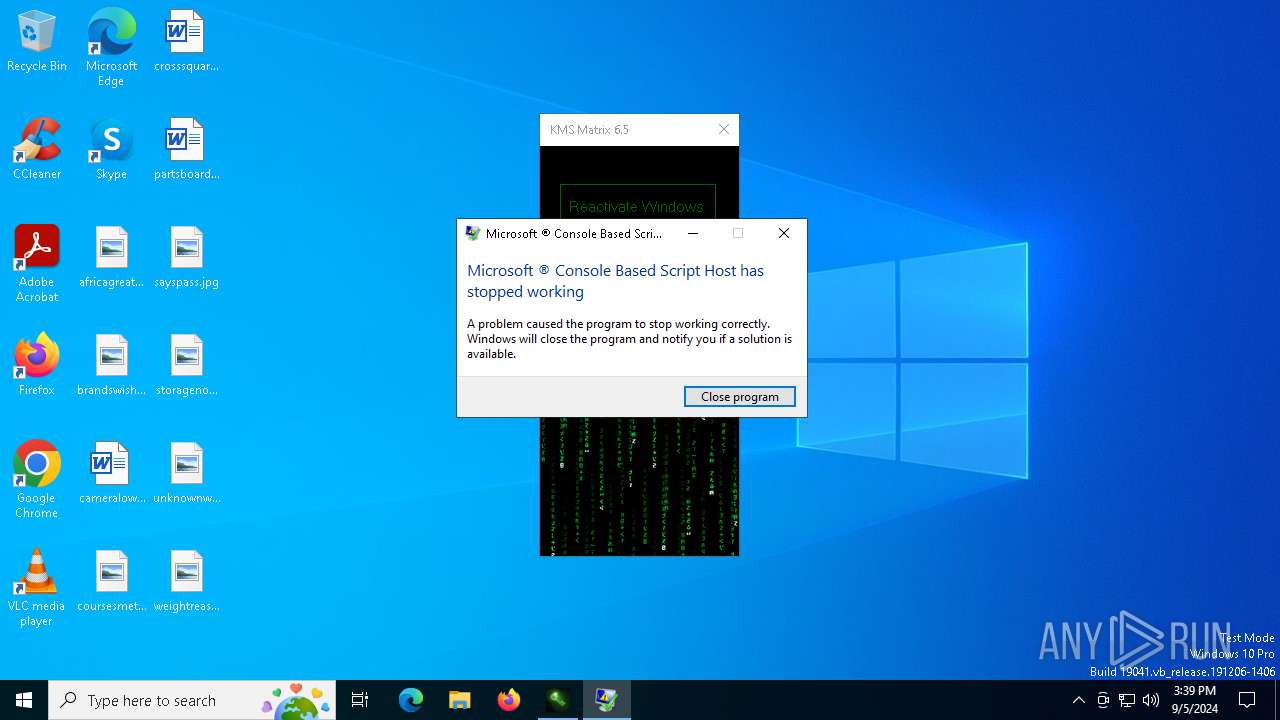
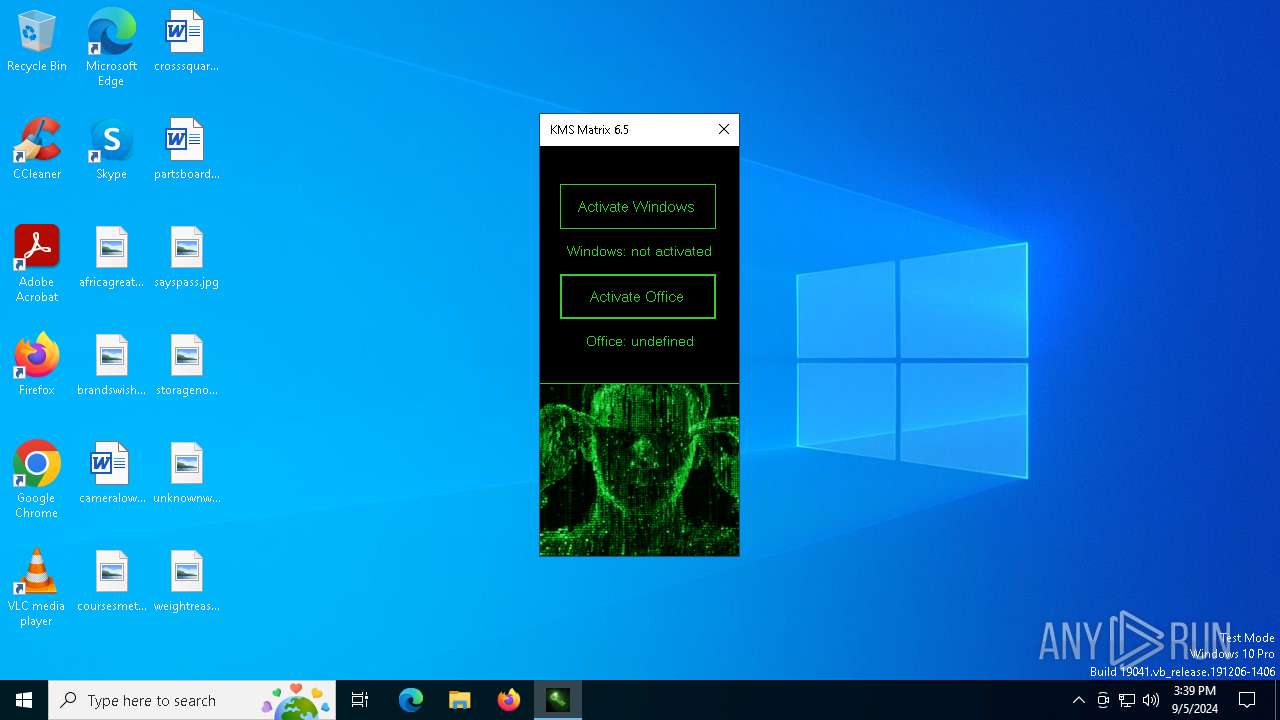
| Verdict: | Malicious activity |
| Analysis date: | September 05, 2024, 15:35:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9E7D30DF97C59BACA74E7D779E0CEAC1 |
| SHA1: | 36ED3F13018C6C49A4B4DAFA26667C86D6BF17DC |
| SHA256: | B04853E48D783BBFB5E15E56B6A0A57AD95C16F1601DDF9CA78588F8CEA52284 |
| SSDEEP: | 3:N80l0RNK8xWXMJQ:2JacJQ |
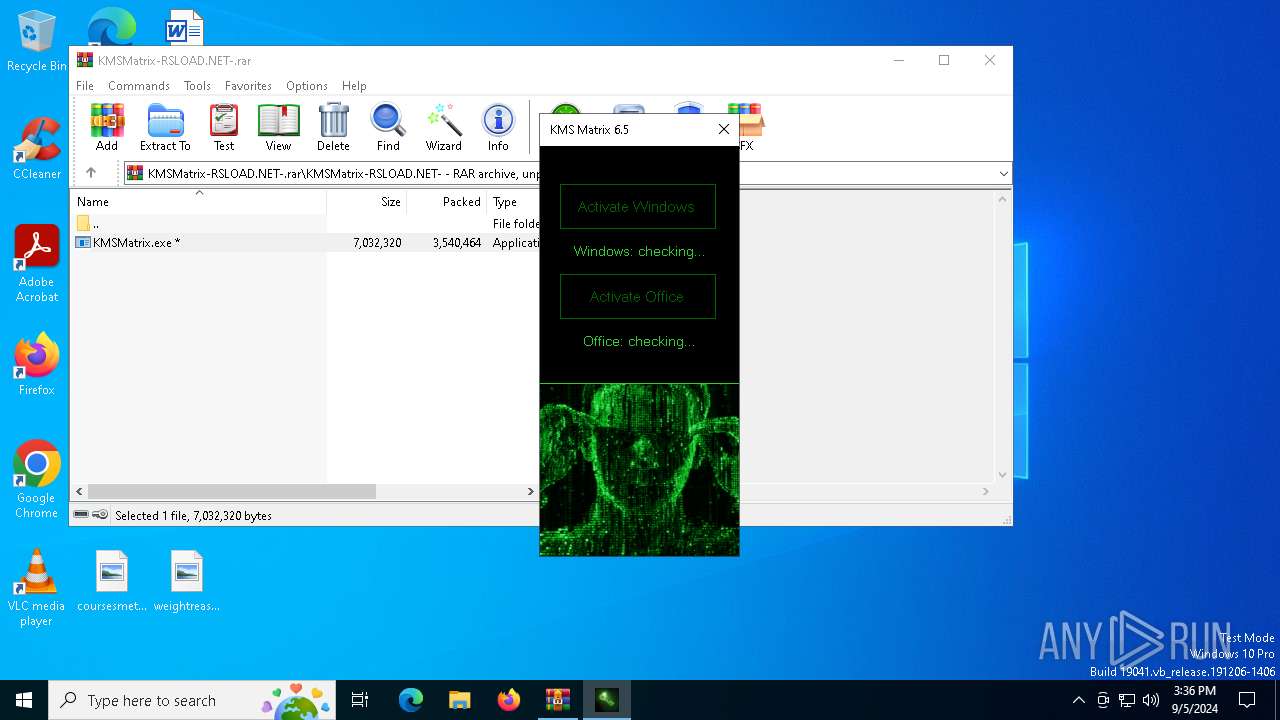
MALICIOUS
Changes powershell execution policy (Unrestricted)
- KMSMatrix.exe (PID: 5708)
Starts NET.EXE for service management
- cmd.exe (PID: 7232)
- net.exe (PID: 7016)
- net.exe (PID: 6544)
- net.exe (PID: 6884)
- cmd.exe (PID: 7976)
- net.exe (PID: 3028)
- net.exe (PID: 7864)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1828)
- KMSMatrix.exe (PID: 5708)
Reads the date of Windows installation
- KMSMatrix.exe (PID: 5708)
Executing commands from ".cmd" file
- KMSMatrix.exe (PID: 5708)
- cmd.exe (PID: 7488)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 360)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 6516)
Starts CMD.EXE for commands execution
- KMSMatrix.exe (PID: 5708)
- cmd.exe (PID: 7488)
- cmd.exe (PID: 6316)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 188)
- cmd.exe (PID: 360)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 6160)
- cmd.exe (PID: 7364)
- cmd.exe (PID: 6428)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 7976)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 8028)
- cmd.exe (PID: 7488)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 360)
- cmd.exe (PID: 6316)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 6516)
The process executes Powershell scripts
- KMSMatrix.exe (PID: 5708)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7488)
- cmd.exe (PID: 6012)
- cmd.exe (PID: 3980)
- cmd.exe (PID: 7960)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 360)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 6516)
Application launched itself
- cmd.exe (PID: 7488)
- cmd.exe (PID: 6316)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 360)
- cmd.exe (PID: 188)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 6160)
- cmd.exe (PID: 7364)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 6428)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 6568)
Uses WMIC.EXE
- cmd.exe (PID: 3784)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 6052)
- cmd.exe (PID: 6336)
- cmd.exe (PID: 8096)
The process executes VB scripts
- powershell.exe (PID: 6640)
- cmd.exe (PID: 4816)
- cmd.exe (PID: 5552)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 8072)
- cmd.exe (PID: 7948)
Starts POWERSHELL.EXE for commands execution
- KMSMatrix.exe (PID: 5708)
Get information on the list of running processes
- cmd.exe (PID: 6004)
- cmd.exe (PID: 7436)
- cmd.exe (PID: 736)
- cmd.exe (PID: 7488)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 6000)
- cmd.exe (PID: 360)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 3256)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 6516)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 6832)
- cscript.exe (PID: 6644)
- cscript.exe (PID: 1404)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 6832)
- cscript.exe (PID: 6644)
- cscript.exe (PID: 1404)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7488)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 360)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 6516)
Hides command output
- cmd.exe (PID: 6012)
- cmd.exe (PID: 3980)
- cmd.exe (PID: 7960)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 1828)
- cmd.exe (PID: 7676)
- cmd.exe (PID: 208)
- cmd.exe (PID: 7280)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 6288)
- cmd.exe (PID: 4080)
- cmd.exe (PID: 5160)
- cmd.exe (PID: 2900)
- cmd.exe (PID: 5740)
- cmd.exe (PID: 3292)
- cmd.exe (PID: 4316)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 6644)
- cmd.exe (PID: 7796)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 2608)
- cmd.exe (PID: 6616)
- cmd.exe (PID: 1640)
- cmd.exe (PID: 7744)
- cmd.exe (PID: 7760)
- cmd.exe (PID: 4668)
- cmd.exe (PID: 1176)
- cmd.exe (PID: 7864)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 6336)
- cmd.exe (PID: 6544)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 5712)
- cmd.exe (PID: 6100)
The process verifies whether the antivirus software is installed
- cmd.exe (PID: 7488)
Checks for external IP
- curl.exe (PID: 8180)
- svchost.exe (PID: 2256)
- curl.exe (PID: 6928)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7488)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 6916)
- WMIC.exe (PID: 6968)
- WMIC.exe (PID: 7100)
- WMIC.exe (PID: 7492)
- WMIC.exe (PID: 7300)
Executable content was dropped or overwritten
- curl.exe (PID: 4920)
- 7z2201.exe (PID: 7004)
The executable file from the user directory is run by the CMD process
- 7z2201.exe (PID: 7004)
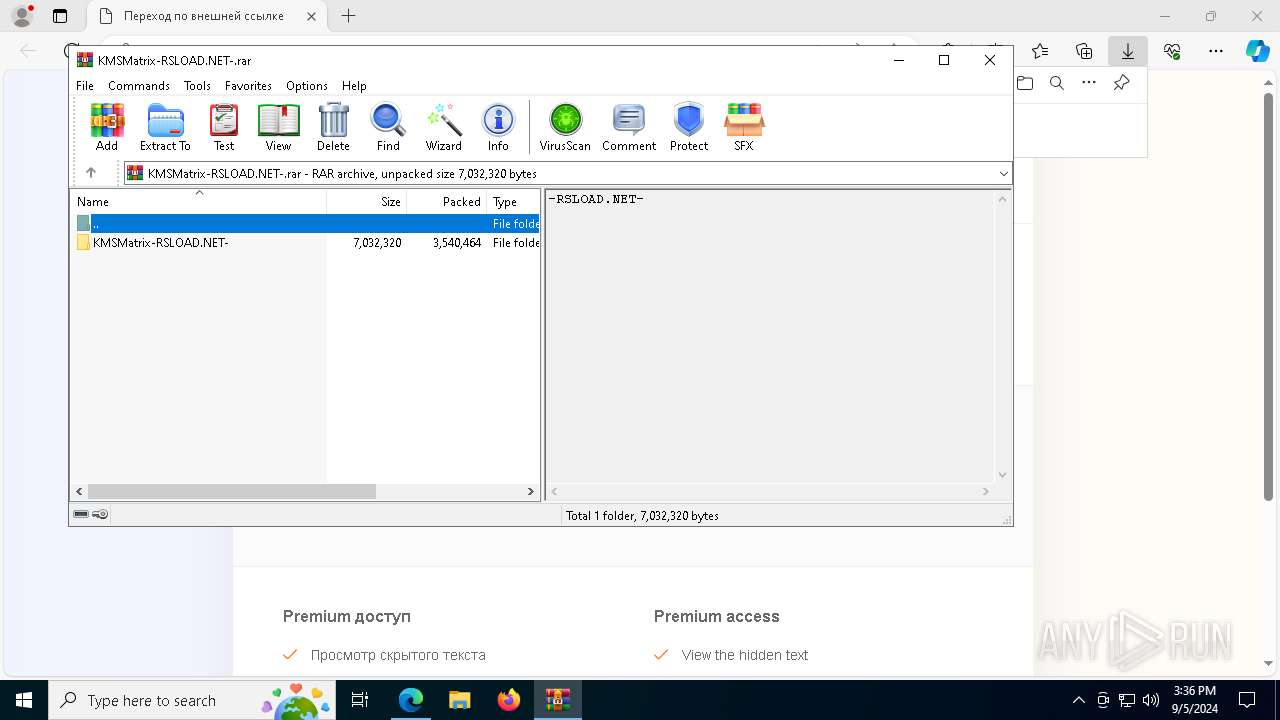
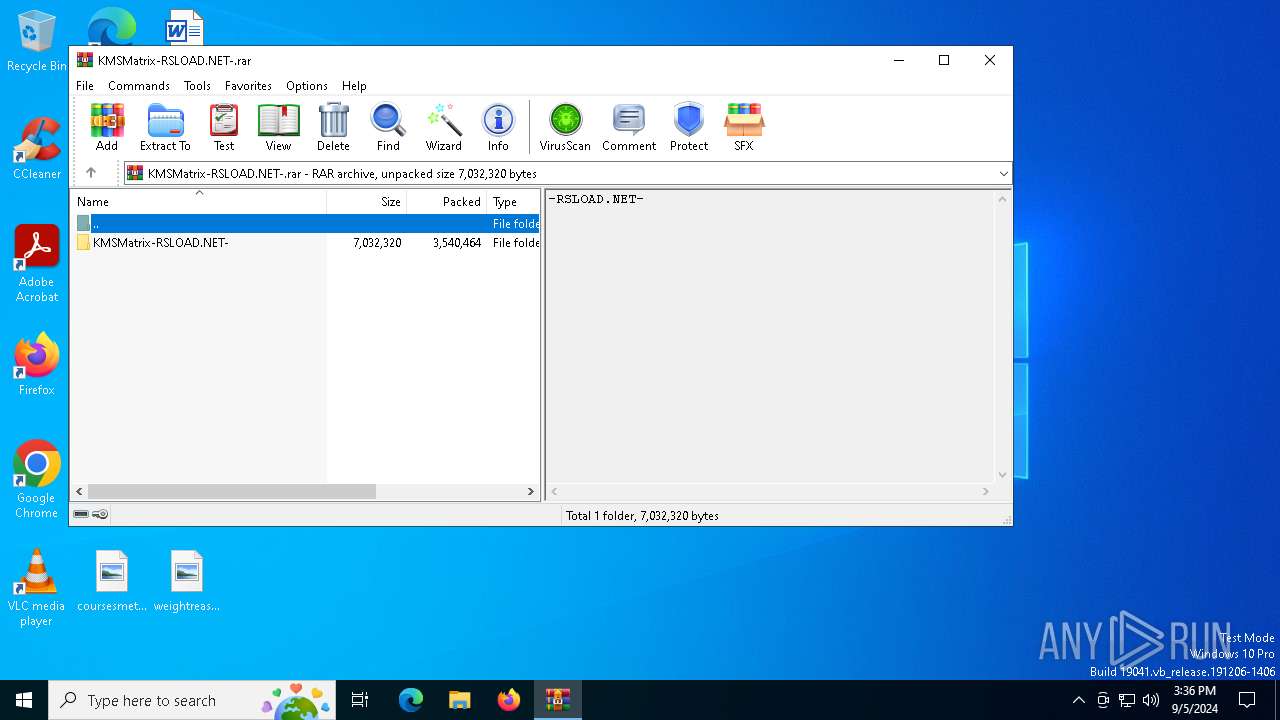
Drops 7-zip archiver for unpacking
- curl.exe (PID: 4920)
- 7z2201.exe (PID: 7004)
Gets the drive type (SCRIPT)
- cscript.exe (PID: 4980)
- cscript.exe (PID: 3980)
- cscript.exe (PID: 6168)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 4980)
- cscript.exe (PID: 6832)
- cscript.exe (PID: 6644)
- cscript.exe (PID: 3980)
- cscript.exe (PID: 1404)
- cscript.exe (PID: 6168)
Gets a collection of all available drive names (SCRIPT)
- cscript.exe (PID: 4980)
- cscript.exe (PID: 3980)
- cscript.exe (PID: 6168)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 4980)
- cscript.exe (PID: 3980)
- cscript.exe (PID: 6168)
Creates a software uninstall entry
- 7z2201.exe (PID: 7004)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- cscript.exe (PID: 4980)
- cscript.exe (PID: 3980)
- cscript.exe (PID: 6168)
Creates/Modifies COM task schedule object
- 7z2201.exe (PID: 7004)
Accesses computer name via WMI (SCRIPT)
- cscript.exe (PID: 4980)
- cscript.exe (PID: 3980)
- cscript.exe (PID: 6168)
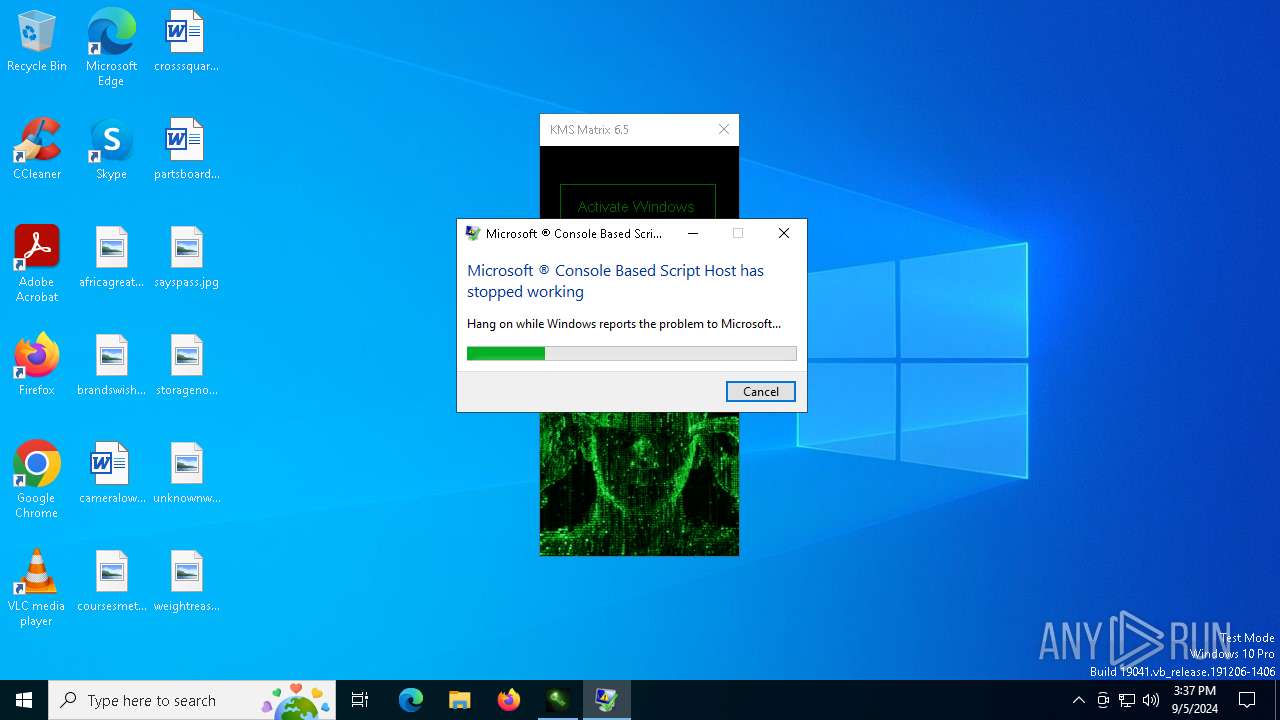
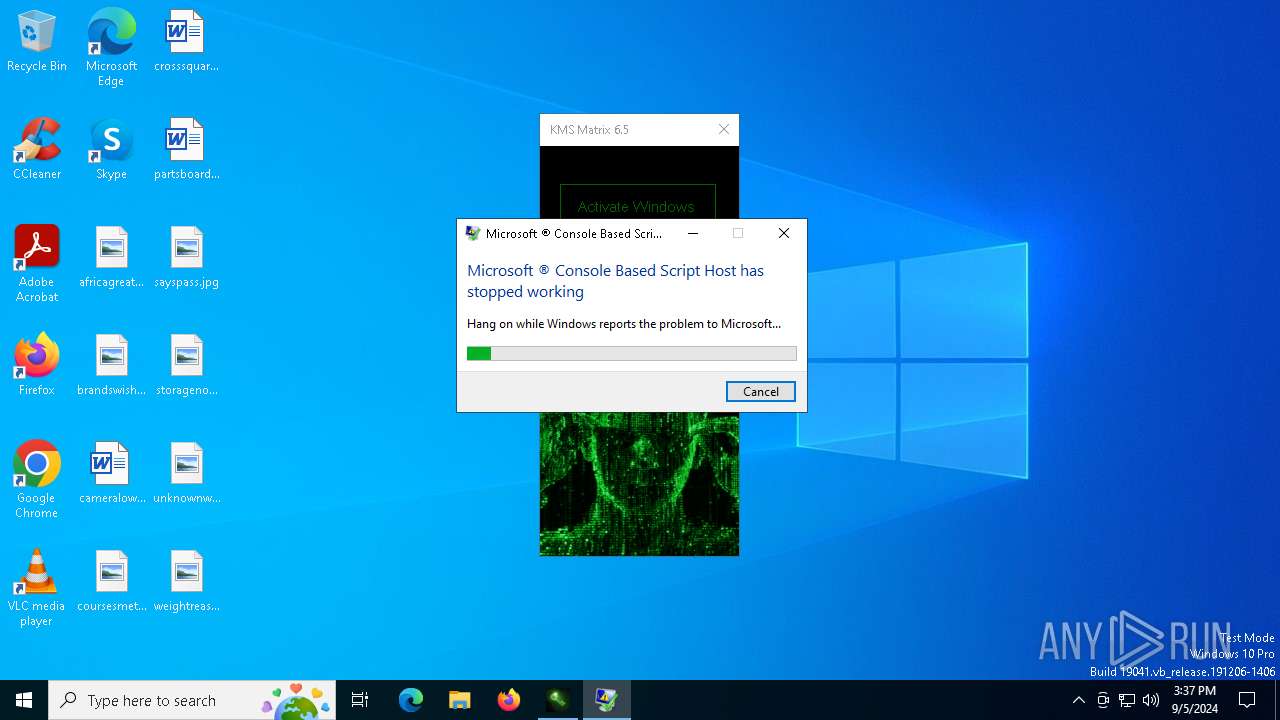
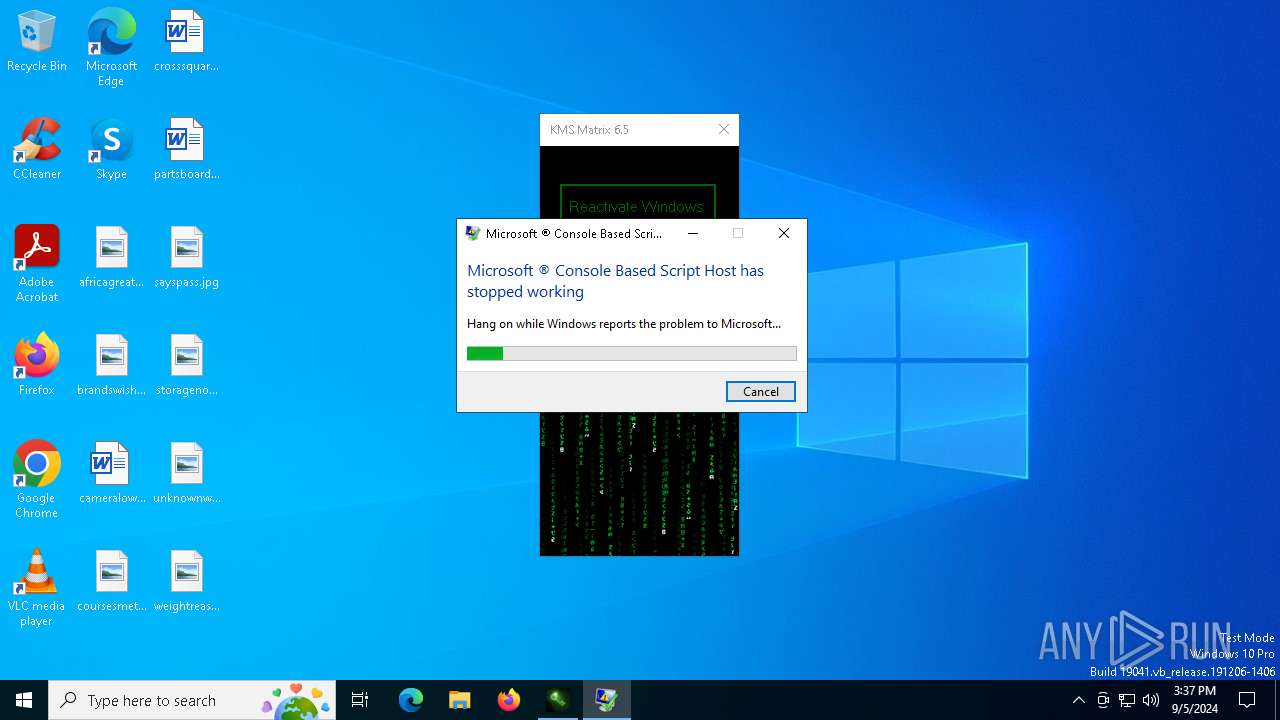
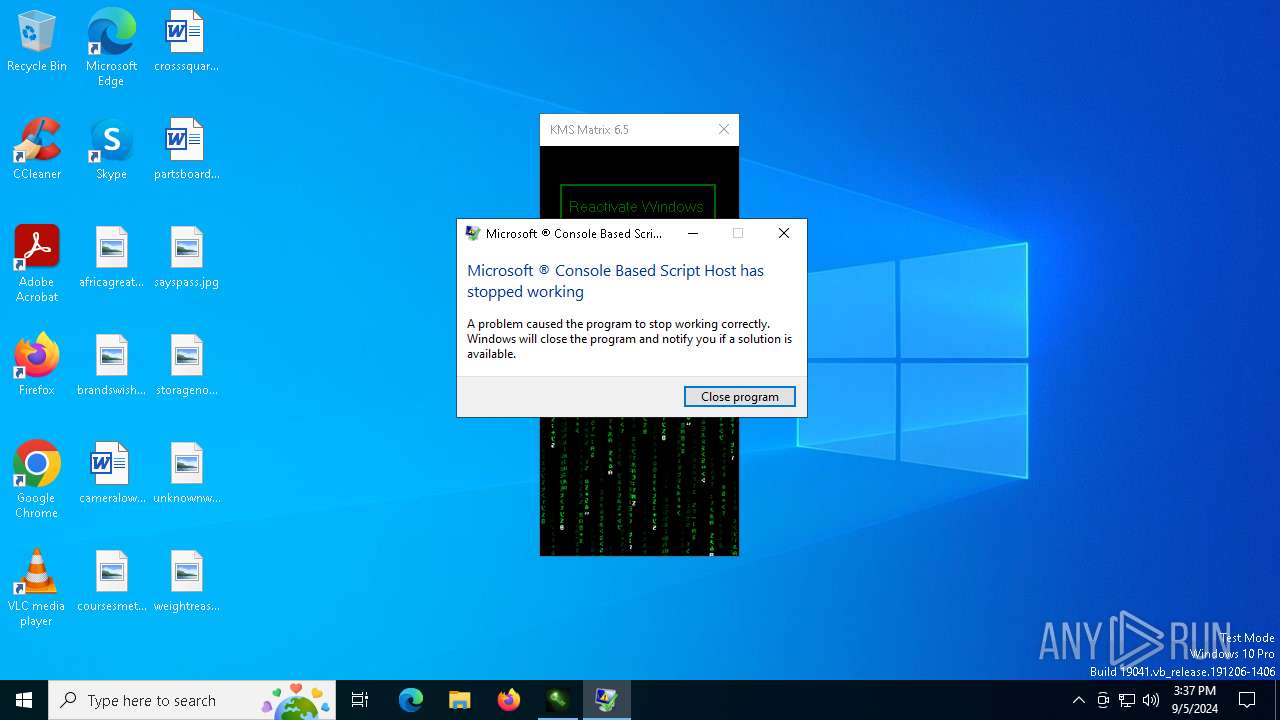
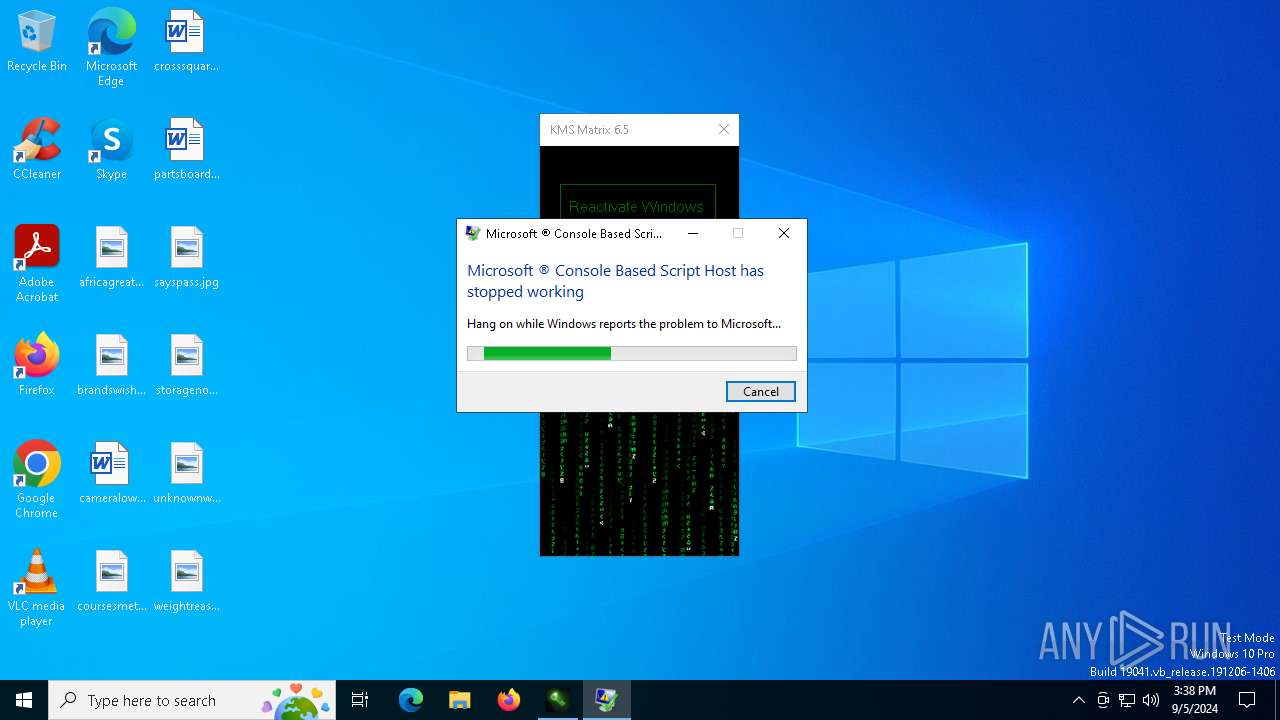
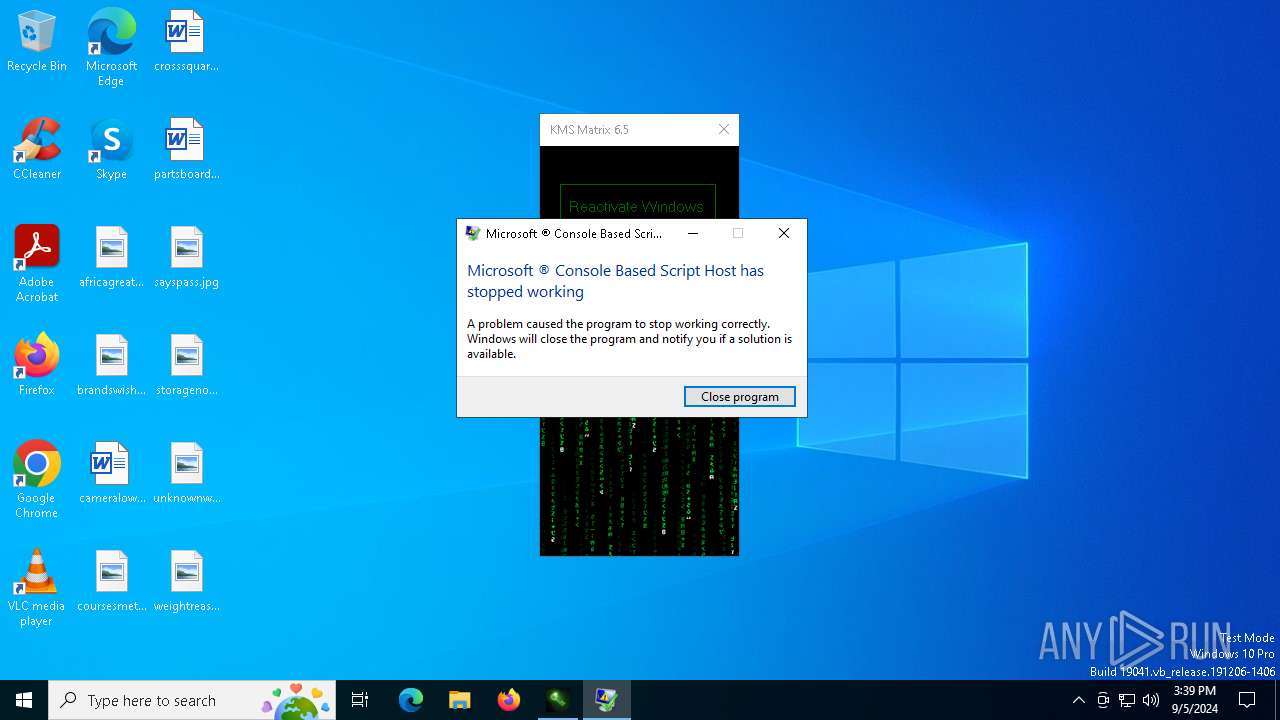
Executes application which crashes
- cscript.exe (PID: 4980)
- cscript.exe (PID: 3980)
- cscript.exe (PID: 6168)
The process creates files with name similar to system file names
- WerFault.exe (PID: 6824)
- WerFault.exe (PID: 7704)
- WerFault.exe (PID: 7684)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7232)
- cmd.exe (PID: 7976)
Starts SC.EXE for service management
- cmd.exe (PID: 7232)
- cmd.exe (PID: 7976)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 208)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 1140)
- cmd.exe (PID: 6240)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 7976)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 7788)
- cmd.exe (PID: 6836)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 7976)
INFO
The process uses the downloaded file
- msedge.exe (PID: 8020)
- WinRAR.exe (PID: 1828)
- KMSMatrix.exe (PID: 5708)
- powershell.exe (PID: 6640)
- msedge.exe (PID: 6808)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 8072)
Checks supported languages
- identity_helper.exe (PID: 7816)
- KMSMatrix.exe (PID: 5708)
- identity_helper.exe (PID: 188)
- curl.exe (PID: 6928)
- curl.exe (PID: 8180)
- curl.exe (PID: 2584)
- curl.exe (PID: 4920)
- curl.exe (PID: 5000)
- 7z2201.exe (PID: 7004)
Reads Environment values
- identity_helper.exe (PID: 188)
- identity_helper.exe (PID: 7816)
Application launched itself
- msedge.exe (PID: 6808)
- msedge.exe (PID: 5612)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1828)
Create files in a temporary directory
- KMSMatrix.exe (PID: 5708)
- curl.exe (PID: 4920)
- curl.exe (PID: 5000)
Process checks computer location settings
- KMSMatrix.exe (PID: 5708)
Reads the computer name
- identity_helper.exe (PID: 7816)
- KMSMatrix.exe (PID: 5708)
- identity_helper.exe (PID: 188)
- curl.exe (PID: 6928)
- curl.exe (PID: 8180)
- curl.exe (PID: 2584)
- curl.exe (PID: 4920)
- curl.exe (PID: 5000)
- 7z2201.exe (PID: 7004)
Reads the machine GUID from the registry
- KMSMatrix.exe (PID: 5708)
Checks operating system version
- cmd.exe (PID: 7488)
- cmd.exe (PID: 360)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 6516)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7388)
- cscript.exe (PID: 6832)
- WMIC.exe (PID: 6916)
- WMIC.exe (PID: 6968)
- WMIC.exe (PID: 7300)
- WMIC.exe (PID: 7100)
- WMIC.exe (PID: 7492)
- cscript.exe (PID: 4980)
- WMIC.exe (PID: 1812)
- WMIC.exe (PID: 7364)
- WMIC.exe (PID: 7484)
- WMIC.exe (PID: 6908)
- WMIC.exe (PID: 6664)
- WMIC.exe (PID: 5796)
- WMIC.exe (PID: 8088)
- WMIC.exe (PID: 6740)
- WMIC.exe (PID: 2608)
- WMIC.exe (PID: 4132)
- WMIC.exe (PID: 5712)
- WMIC.exe (PID: 2268)
- WMIC.exe (PID: 1104)
- WMIC.exe (PID: 5048)
- WMIC.exe (PID: 7152)
- WMIC.exe (PID: 6188)
- WMIC.exe (PID: 2520)
- WMIC.exe (PID: 8168)
- WMIC.exe (PID: 4364)
- WMIC.exe (PID: 7868)
- WMIC.exe (PID: 5140)
- WMIC.exe (PID: 4316)
- WMIC.exe (PID: 6764)
- WMIC.exe (PID: 8124)
- WMIC.exe (PID: 6420)
- WMIC.exe (PID: 6304)
- cscript.exe (PID: 6644)
- WMIC.exe (PID: 7008)
- cscript.exe (PID: 3980)
- WMIC.exe (PID: 8136)
- WMIC.exe (PID: 2464)
- WMIC.exe (PID: 6164)
- WMIC.exe (PID: 568)
- WMIC.exe (PID: 5040)
- WMIC.exe (PID: 1556)
- WMIC.exe (PID: 7860)
- WMIC.exe (PID: 6724)
- WMIC.exe (PID: 8028)
- WMIC.exe (PID: 1448)
- WMIC.exe (PID: 4680)
- WMIC.exe (PID: 3144)
- WMIC.exe (PID: 6284)
- WMIC.exe (PID: 7056)
- WMIC.exe (PID: 6124)
- WMIC.exe (PID: 1616)
- WMIC.exe (PID: 2520)
- cscript.exe (PID: 1404)
- cscript.exe (PID: 6168)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6808)
- reg.exe (PID: 5072)
- reg.exe (PID: 6472)
- reg.exe (PID: 7492)
- reg.exe (PID: 4092)
- reg.exe (PID: 5468)
- reg.exe (PID: 4060)
- reg.exe (PID: 7460)
- reg.exe (PID: 3984)
- reg.exe (PID: 4404)
- reg.exe (PID: 7704)
- reg.exe (PID: 6180)
- reg.exe (PID: 5720)
- reg.exe (PID: 6824)
- reg.exe (PID: 3552)
- reg.exe (PID: 4064)
- reg.exe (PID: 5524)
- reg.exe (PID: 7040)
- reg.exe (PID: 3908)
- reg.exe (PID: 6840)
- reg.exe (PID: 7568)
- reg.exe (PID: 1680)
- reg.exe (PID: 6660)
- reg.exe (PID: 7076)
- reg.exe (PID: 5096)
- reg.exe (PID: 7760)
- reg.exe (PID: 4440)
- reg.exe (PID: 7752)
- reg.exe (PID: 6664)
- reg.exe (PID: 8156)
- reg.exe (PID: 7464)
Disables trace logs
- powershell.exe (PID: 6640)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 8072)
Checks proxy server information
- powershell.exe (PID: 6640)
- cscript.exe (PID: 4980)
- WerFault.exe (PID: 6824)
- WerFault.exe (PID: 7704)
- powershell.exe (PID: 7620)
- WerFault.exe (PID: 7684)
- powershell.exe (PID: 8072)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6640)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 8072)
Creates files in the program directory
- 7z2201.exe (PID: 7004)
Reads the software policy settings
- cscript.exe (PID: 4980)
- WerFault.exe (PID: 6824)
- cscript.exe (PID: 3980)
- WerFault.exe (PID: 7704)
- cscript.exe (PID: 6168)
- WerFault.exe (PID: 7684)
Creates files or folders in the user directory
- cscript.exe (PID: 4980)
- WerFault.exe (PID: 6824)
- WerFault.exe (PID: 7704)
- WerFault.exe (PID: 7684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
1 094
Monitored processes
953
Malicious processes
19
Suspicious processes
13
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4880 --field-trial-handle=2392,i,16172813162686276932,3229500203969061987,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 188 | findstr /i "3f1afc82-f8ac-4f6c-8005-1d233e606eee" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | C:\WINDOWS\system32\cmd.exe /c echo prompt $E | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo "/act-o" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | find /i "R_Retail" "C:\WINDOWS\Temp\sppchk.txt" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | C:\WINDOWS\system32\cmd.exe /c "wmic path SoftwareLicensingProduct where (ApplicationID='55c92734-d682-4d71-983e-d6ec3f16059f' AND PartialProductKey is not NULL) get LicenseFamily /value" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | findstr /I /C:"ProjectStd2021Retail" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 360 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4880 --field-trial-handle=2392,i,16172813162686276932,3229500203969061987,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 360 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\m_srv.cmd" /kms" | C:\Windows\System32\cmd.exe | — | KMSMatrix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 360 | findstr /I /C:"Access2019Volume" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
101 591
Read events
101 441
Write events
131
Delete events
19
Modification events
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B99E9454F77F2F00 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CF8D9E54F77F2F00 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525118 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BBCCDA46-79B7-4C1C-914D-52DF5C39E192} | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525118 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5A9C4F28-E3A7-41C5-B5B3-AA909C1E1D00} | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525118 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {952CC111-1C0D-44E3-B187-932BC9E84370} | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525118 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {38DF8C77-BD7B-45B0-AB23-CE35FEFD1515} | |||
Executable files
11
Suspicious files
338
Text files
308
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF129fd2.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF129fd2.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF129fe2.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF12a001.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF129fd2.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
112
DNS requests
95
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6824 | WerFault.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2868 | svchost.exe | GET | 206 | 23.48.23.41:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3f7756bd-b1cc-4d5e-96d8-fd938a5c5bb6?P1=1725979143&P2=404&P3=2&P4=mYSEVBMk0pCrFXv3IosfjqQPSUTp1FcnvI6l8gmxpeJxOBei0OV6FjXXuvLLvWuoyTcO9NAELeoArPf5PITusw%3d%3d | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3716 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7620 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7620 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4980 | cscript.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
2868 | svchost.exe | GET | 206 | 23.48.23.41:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3f7756bd-b1cc-4d5e-96d8-fd938a5c5bb6?P1=1725979143&P2=404&P3=2&P4=mYSEVBMk0pCrFXv3IosfjqQPSUTp1FcnvI6l8gmxpeJxOBei0OV6FjXXuvLLvWuoyTcO9NAELeoArPf5PITusw%3d%3d | unknown | — | — | whitelisted |
4980 | cscript.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_2010-07-06.crl | unknown | — | — | whitelisted |
2868 | svchost.exe | HEAD | 200 | 23.48.23.41:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3f7756bd-b1cc-4d5e-96d8-fd938a5c5bb6?P1=1725979143&P2=404&P3=2&P4=mYSEVBMk0pCrFXv3IosfjqQPSUTp1FcnvI6l8gmxpeJxOBei0OV6FjXXuvLLvWuoyTcO9NAELeoArPf5PITusw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7072 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5524 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6808 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5524 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5524 | msedge.exe | 193.233.233.233:443 | rsload.net | LLC Baxet | RU | unknown |
5524 | msedge.exe | 94.245.104.56:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
rsload.net |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6928 | curl.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
6928 | curl.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup SSL Cert Observed (ipinfo .io) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
8180 | curl.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup SSL Cert Observed (ipinfo .io) |
8180 | curl.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |