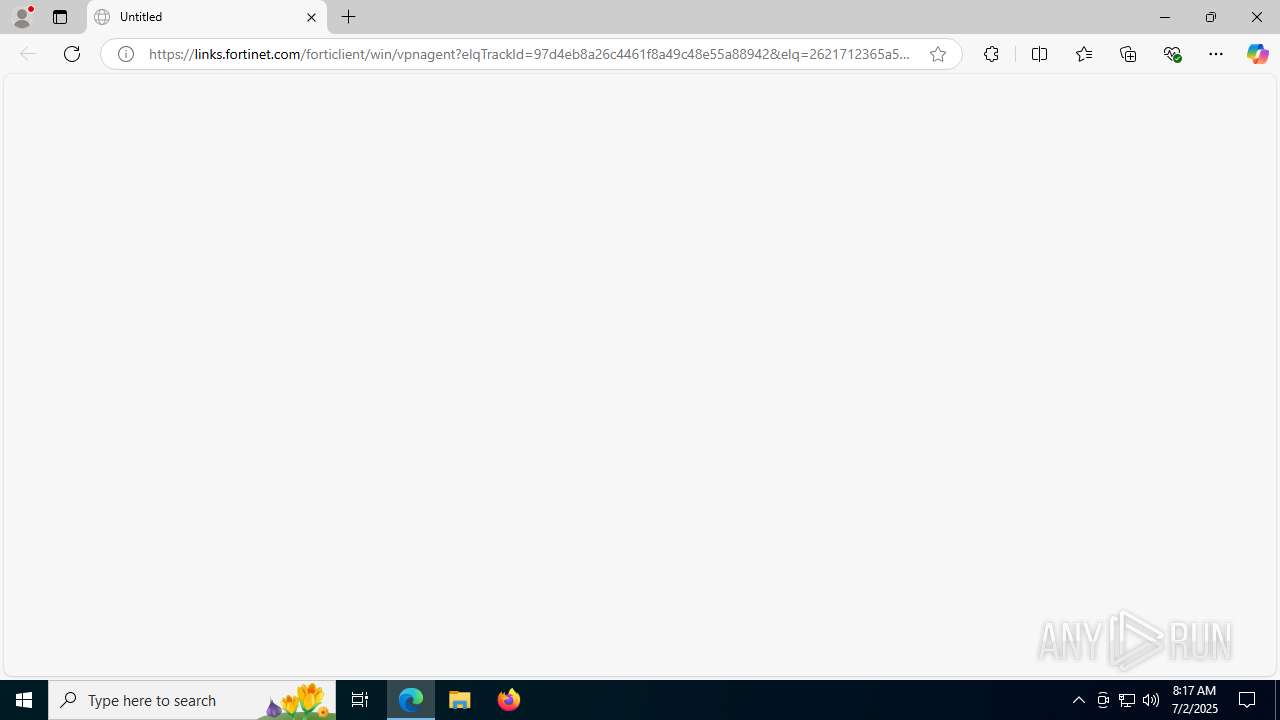
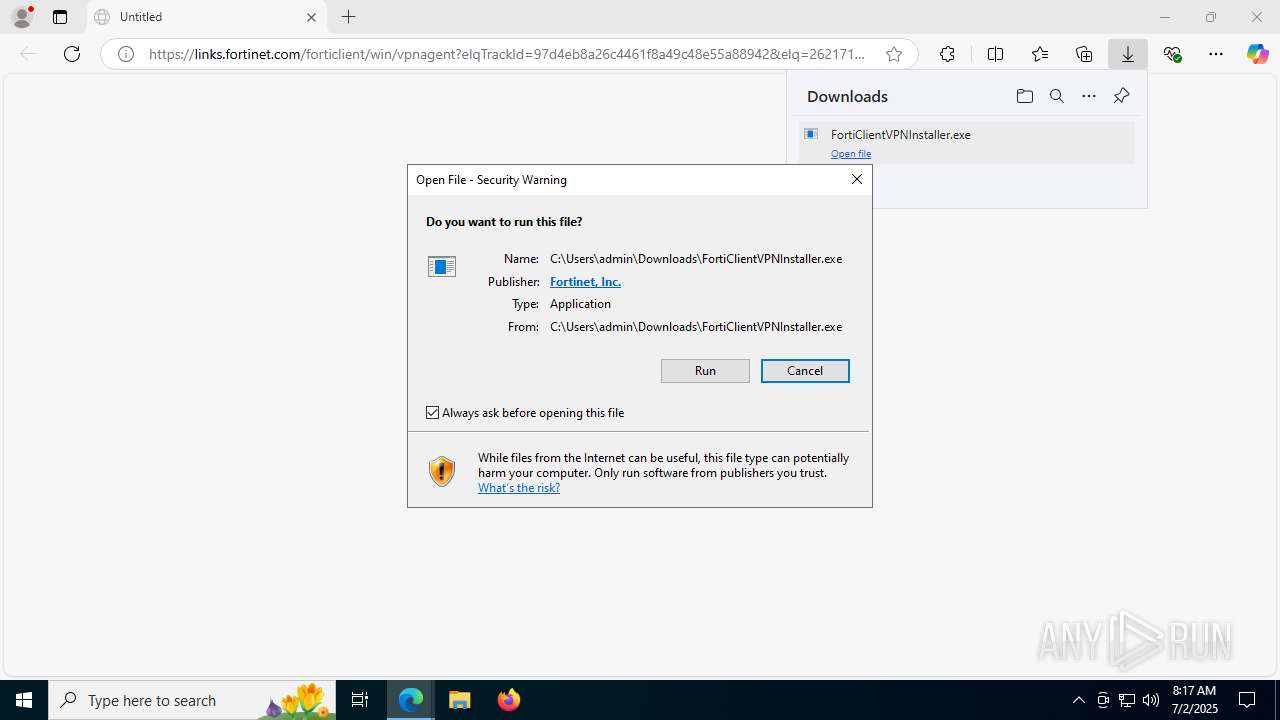
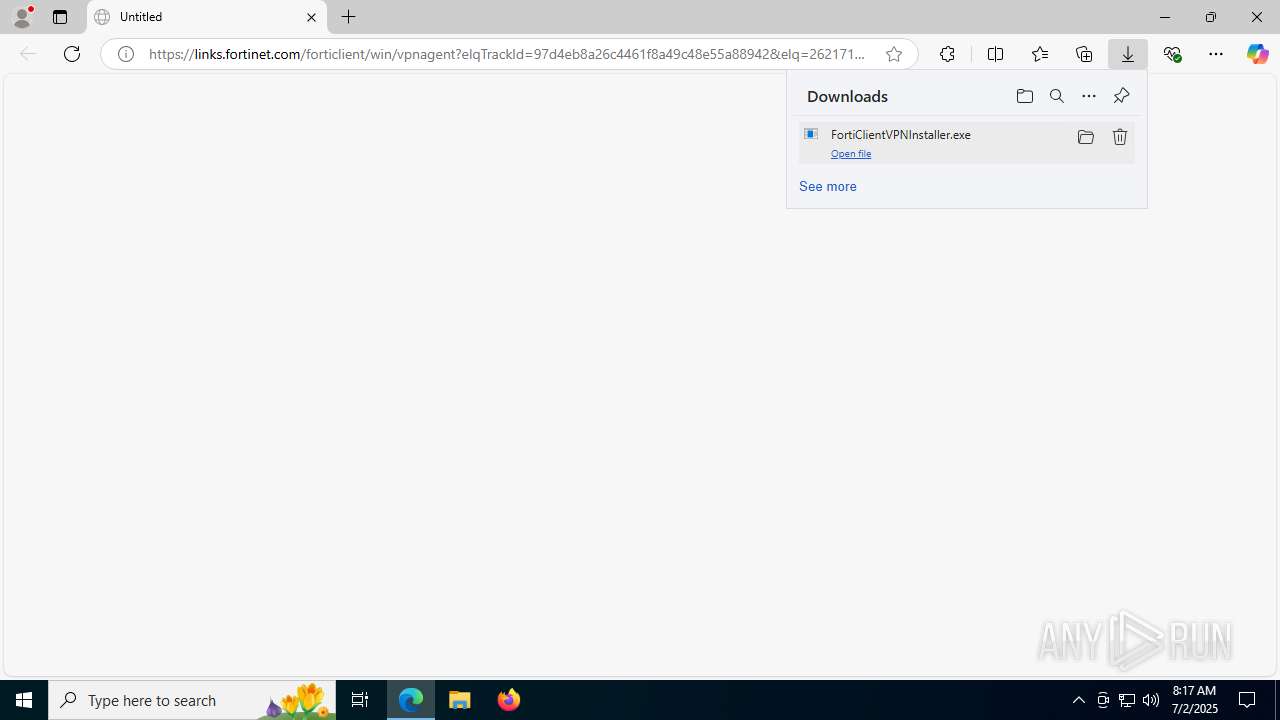
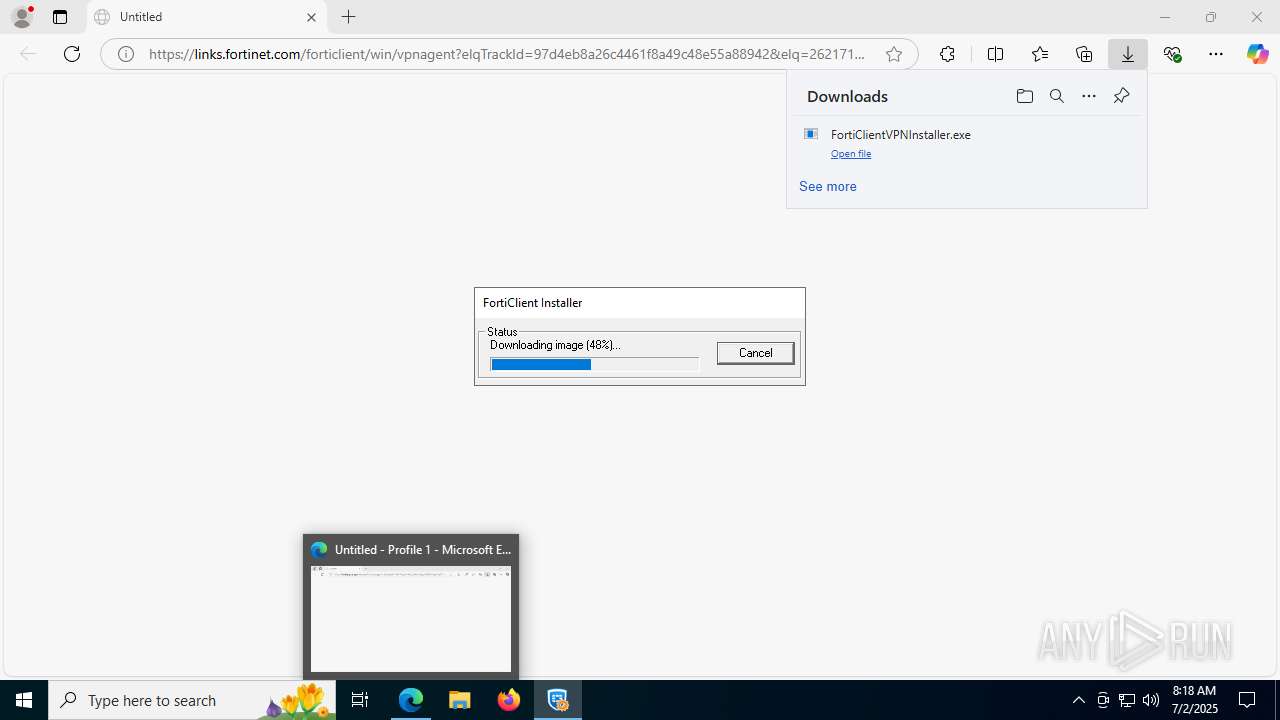
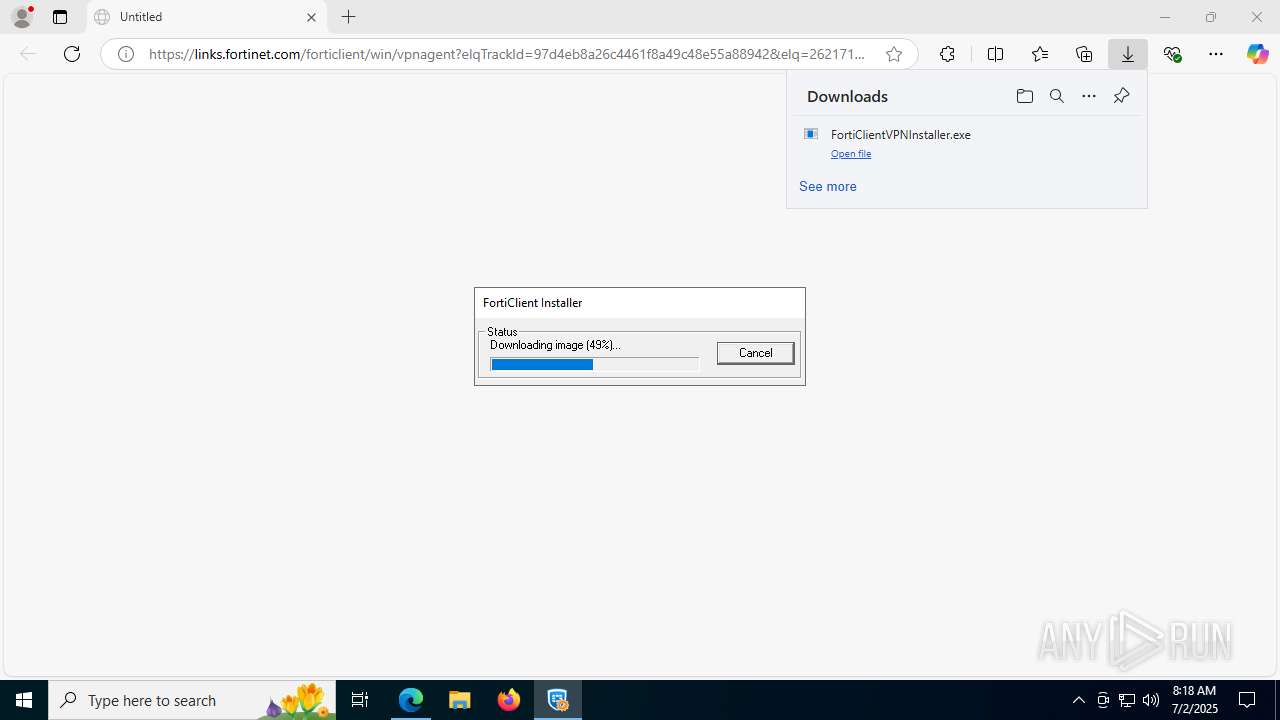
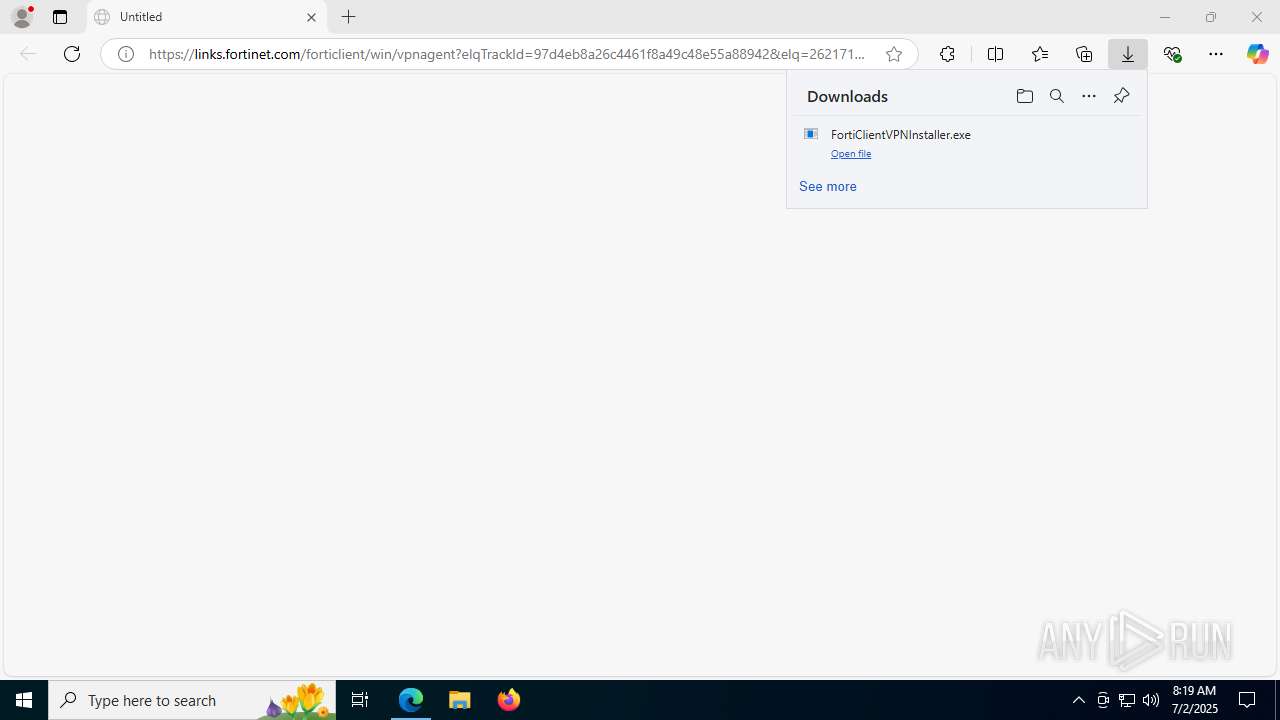
| URL: | https://links.fortinet.com/forticlient/win/vpnagent?elqTrackId=97d4eb8a26c4461f8a49c48e55a88942&elq=2621712365a540c3bd12548e6a8e1ab1&elqaid=26158&elqat=1&elqCampaignId=&elqak=8AF56AC463A04B79CAE1DDFC3A418134094E027D49205D5E1DF70BFCC7F67683DECD |
| Full analysis: | https://app.any.run/tasks/3a99bb78-0522-48a9-a0b8-0563bbc7b3eb |
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2025, 08:17:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | AFD19650FAA99F9B2AFD0E79635F59B2 |
| SHA1: | CF10821B46B52759DE111A8AA0134F148F0F3D18 |
| SHA256: | B03823EC31BD770C4399BCDEB713CC84FA9C140977A887C5825247C44F52F7D1 |
| SSDEEP: | 6:2MaA9/wSrJd+ZsGiFa1GTPnLWDLgPJOzm7vss02skzn:2MDNJdMsFlvLWXuOueBkzn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- FortiClientVPNInstaller.exe (PID: 7404)
- FortiClientVPNInstaller.exe (PID: 7712)
- FortiClientVPN.exe (PID: 7460)
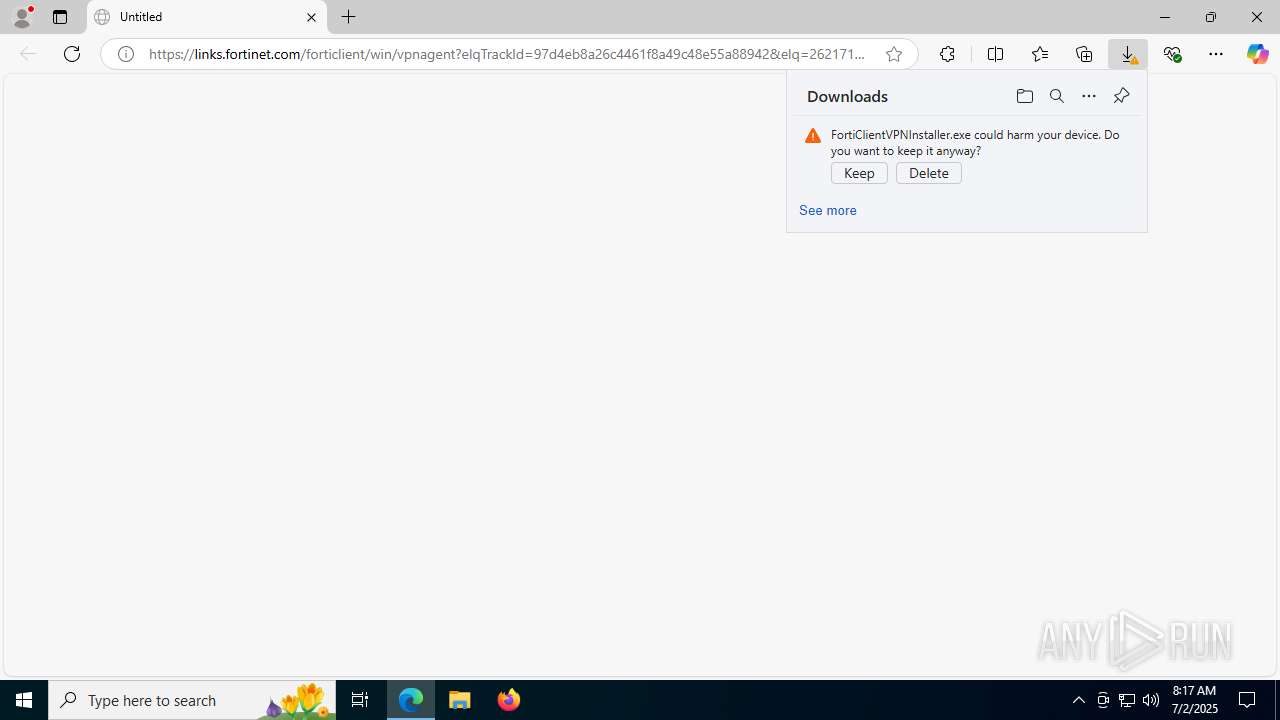
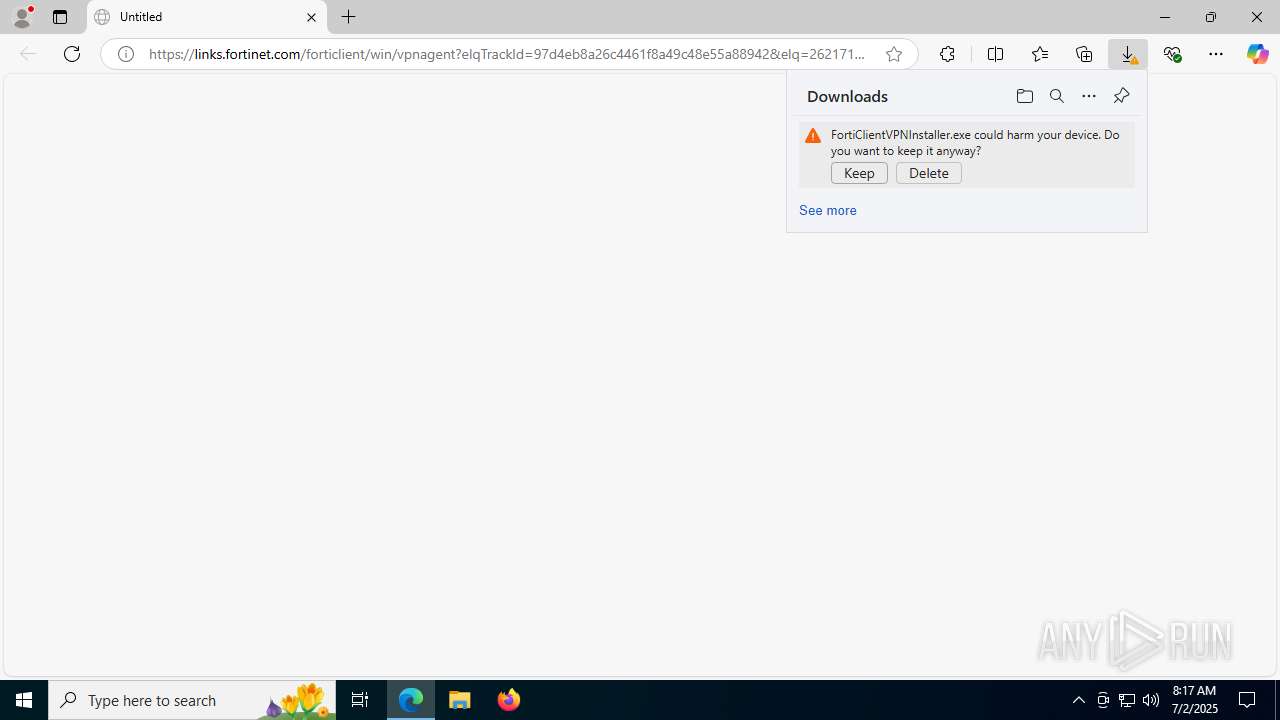
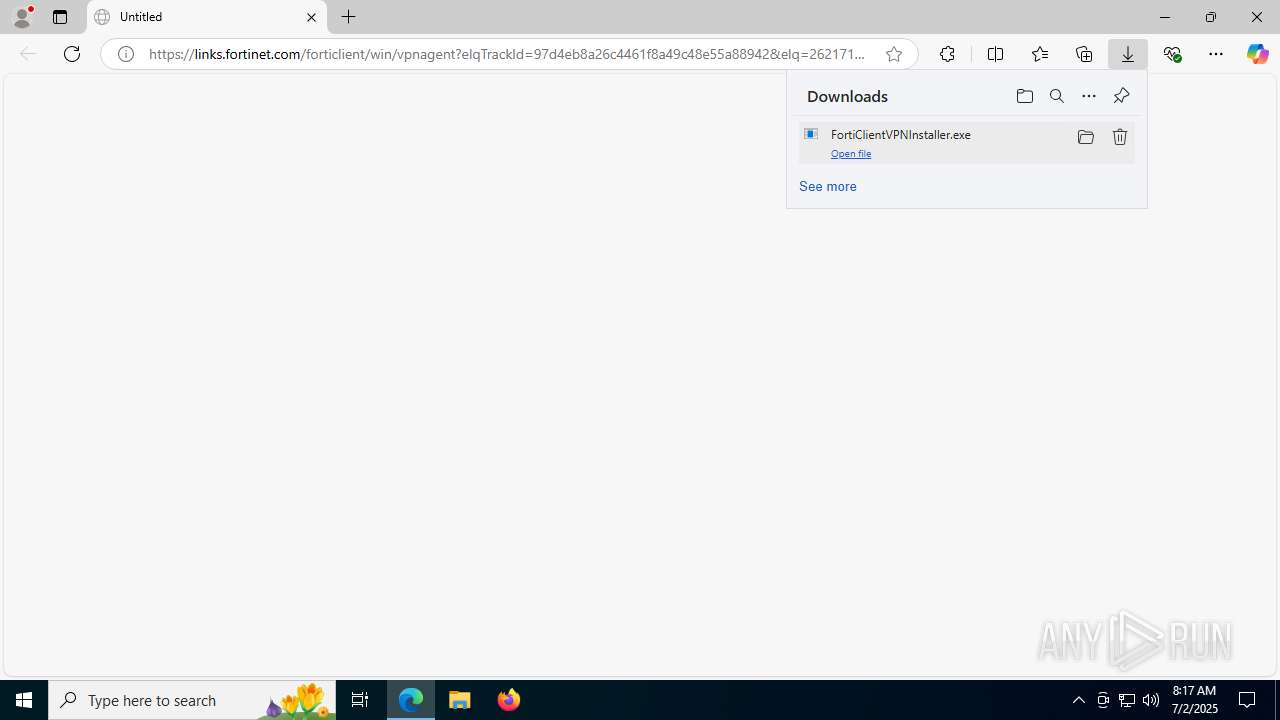
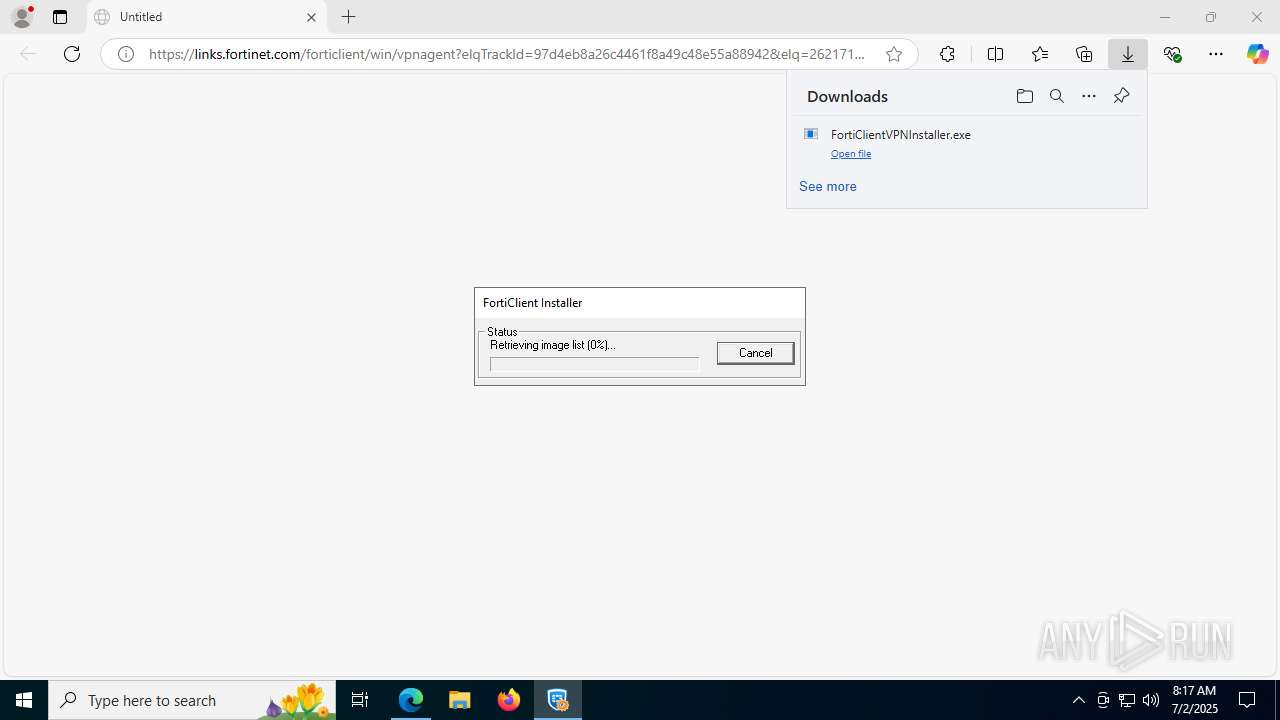
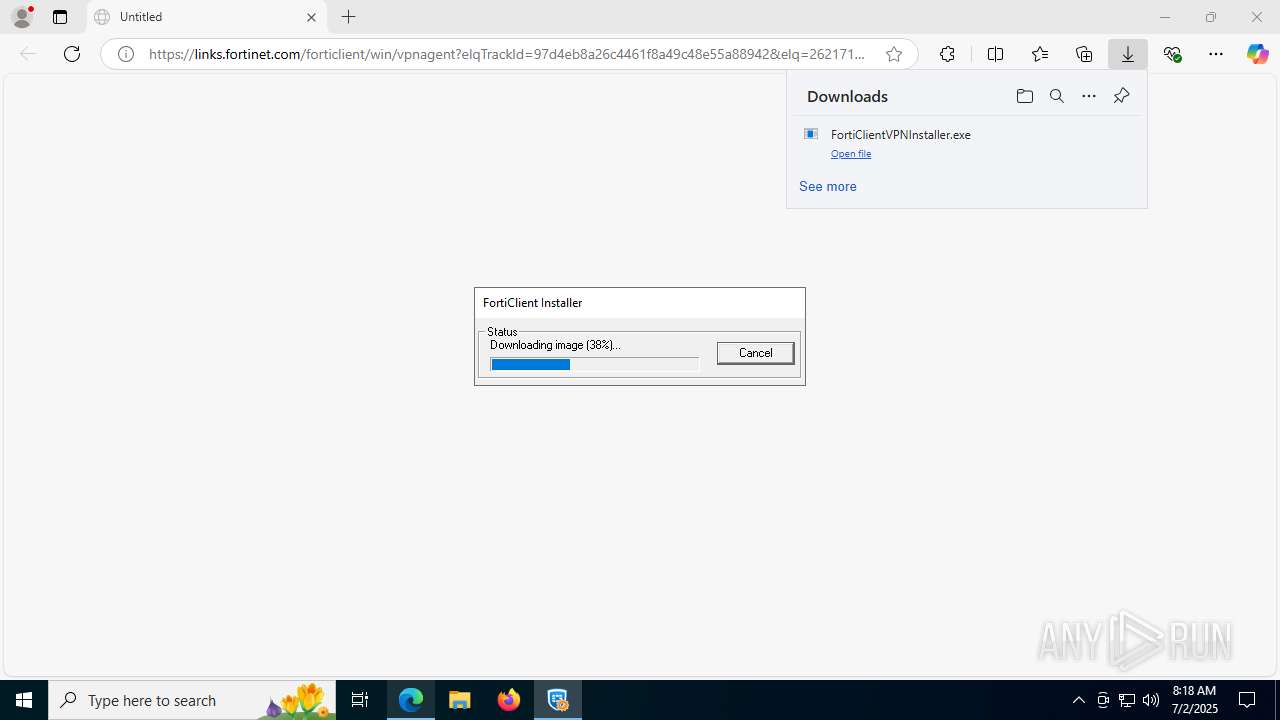
Executable content was dropped or overwritten
- FortiClientVPNInstaller.exe (PID: 7404)
- FortiClientVPN.exe (PID: 7460)
Connects to the server without a host name
- FortiClientVPNInstaller.exe (PID: 7712)
Creates/Modifies COM task schedule object
- FortiClientVPNInstaller.exe (PID: 7712)
Starts itself from another location
- FortiClientVPNInstaller.exe (PID: 7404)
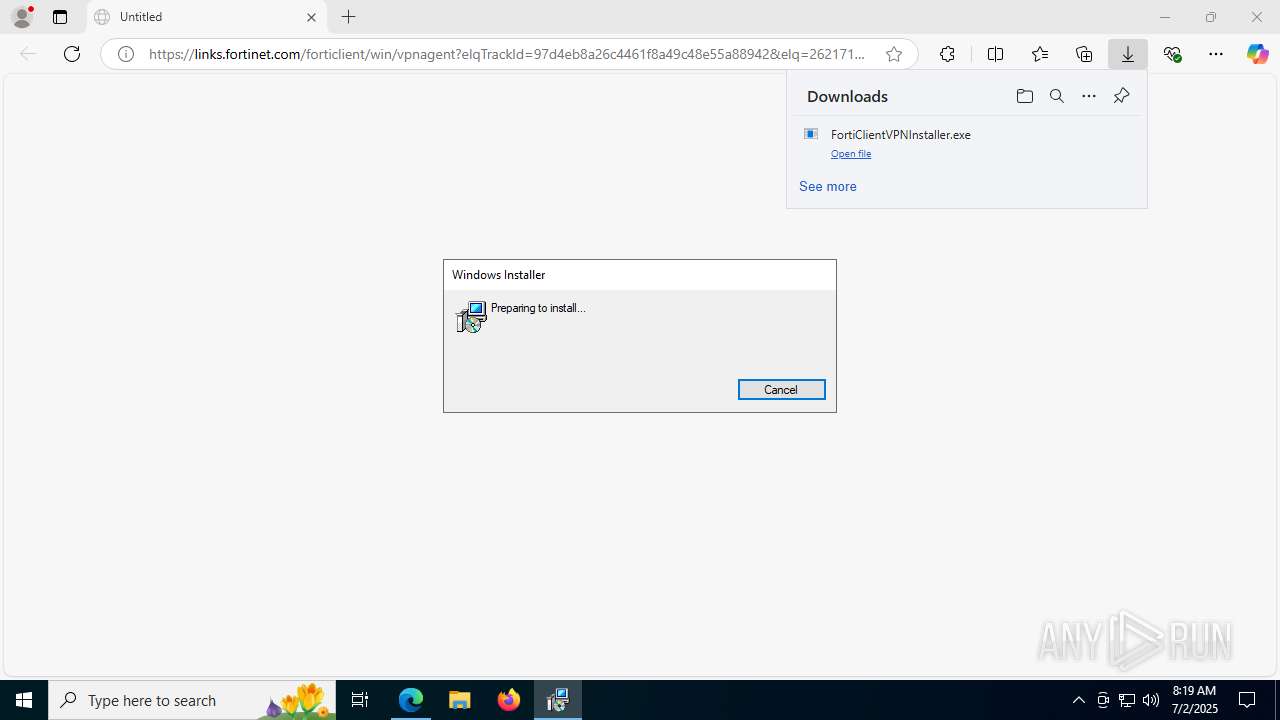
Application launched itself
- msiexec.exe (PID: 3924)
Reads the Windows owner or organization settings
- FortiClientVPN.exe (PID: 7460)
- msiexec.exe (PID: 3924)
INFO
Reads the computer name
- identity_helper.exe (PID: 7500)
- FortiClientVPNInstaller.exe (PID: 7404)
- FortiClientVPNInstaller.exe (PID: 7712)
- FortiClientVPN.exe (PID: 7460)
- msiexec.exe (PID: 3924)
- msiexec.exe (PID: 6260)
- msiexec.exe (PID: 7976)
Executable content was dropped or overwritten
- msedge.exe (PID: 3752)
- msedge.exe (PID: 2972)
- msiexec.exe (PID: 3924)
The sample compiled with english language support
- msedge.exe (PID: 2972)
- msedge.exe (PID: 3752)
- FortiClientVPNInstaller.exe (PID: 7404)
- FortiClientVPN.exe (PID: 7460)
- msiexec.exe (PID: 3924)
Create files in a temporary directory
- FortiClientVPNInstaller.exe (PID: 7404)
- FortiClientVPNInstaller.exe (PID: 7712)
- FortiClientVPN.exe (PID: 7460)
Checks supported languages
- FortiClientVPNInstaller.exe (PID: 7404)
- identity_helper.exe (PID: 7500)
- FortiClientVPNInstaller.exe (PID: 7712)
- FortiClientVPN.exe (PID: 7460)
- msiexec.exe (PID: 3924)
- msiexec.exe (PID: 6260)
- msiexec.exe (PID: 7976)
Application launched itself
- msedge.exe (PID: 2972)
Process checks whether UAC notifications are on
- FortiClientVPNInstaller.exe (PID: 7404)
Reads Environment values
- identity_helper.exe (PID: 7500)
- msiexec.exe (PID: 6260)
- msiexec.exe (PID: 7976)
Reads the machine GUID from the registry
- FortiClientVPNInstaller.exe (PID: 7712)
- FortiClientVPN.exe (PID: 7460)
- msiexec.exe (PID: 3924)
Reads the software policy settings
- FortiClientVPNInstaller.exe (PID: 7712)
- FortiClientVPN.exe (PID: 7460)
- slui.exe (PID: 8076)
- msiexec.exe (PID: 3924)
Creates files in the program directory
- FortiClientVPN.exe (PID: 7460)
Checks proxy server information
- slui.exe (PID: 8076)
Process checks computer location settings
- FortiClientVPNInstaller.exe (PID: 7404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
175
Monitored processes
33
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 868 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7884,i,17234938295112267334,5285718668794699844,262144 --variations-seed-version --mojo-platform-channel-handle=1508 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc4448f208,0x7ffc4448f214,0x7ffc4448f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2972 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://links.fortinet.com/forticlient/win/vpnagent?elqTrackId=97d4eb8a26c4461f8a49c48e55a88942&elq=2621712365a540c3bd12548e6a8e1ab1&elqaid=26158&elqat=1&elqCampaignId=&elqak=8AF56AC463A04B79CAE1DDFC3A418134094E027D49205D5E1DF70BFCC7F67683DECD" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2996 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2340,i,17234938295112267334,5285718668794699844,262144 --variations-seed-version --mojo-platform-channel-handle=2336 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2228,i,17234938295112267334,5285718668794699844,262144 --variations-seed-version --mojo-platform-channel-handle=2420 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4272,i,17234938295112267334,5285718668794699844,262144 --variations-seed-version --mojo-platform-channel-handle=4296 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3924 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4520 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3568,i,17234938295112267334,5285718668794699844,262144 --variations-seed-version --mojo-platform-channel-handle=3660 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4824 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3260,i,17234938295112267334,5285718668794699844,262144 --variations-seed-version --mojo-platform-channel-handle=3688 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2804,i,17234938295112267334,5285718668794699844,262144 --variations-seed-version --mojo-platform-channel-handle=2788 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
20 217
Read events
20 201
Write events
16
Delete events
0
Modification events
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 213F2B2D84972F00 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524860 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EF462CF0-D0FE-413E-8108-81ACF156DDBF} | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
14
Suspicious files
214
Text files
56
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175e2d.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF175e3d.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF175e8b.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175e8b.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF175e8b.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175e8b.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
62
DNS requests
57
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3752 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:h-tBV8NtCmv2C2Ew1a6RCjx3NDKjs2TqqRI94xIdT-c&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2972 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7712 | FortiClientVPNInstaller.exe | POST | 200 | 209.40.106.66:80 | http://209.40.106.66/fdsupdate | unknown | — | — | unknown |
4156 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
320 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751762398&P2=404&P3=2&P4=Tzrg9gqr%2f%2baQ%2fxaDLhJ7Ztu%2bOwONHCXD4UOREcYZOF0RMnMQO17zyVjTk0QN9RwX%2b0B3wvwM0uxGZ9Y6pdNRiA%3d%3d | unknown | — | — | whitelisted |
2972 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
320 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751765999&P2=404&P3=2&P4=m6T%2f%2f0iC3UUUZtGERk7MsB3hrJjXZeWUF6c5ln9cZsmbCSY0h%2fqvyW6tL%2fBf8NCEAmrDNwmpvmf9WYMDquTpHw%3d%3d | unknown | — | — | whitelisted |
7764 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3964 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1268 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3752 | msedge.exe | 52.123.243.64:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | DE | whitelisted |
3752 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3752 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3752 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
3752 | msedge.exe | 154.52.2.213:443 | links.fortinet.com | FORTINET | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
links.fortinet.com |
| malicious |
copilot.microsoft.com |
| whitelisted |
filestore.fortinet.com |
| malicious |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |