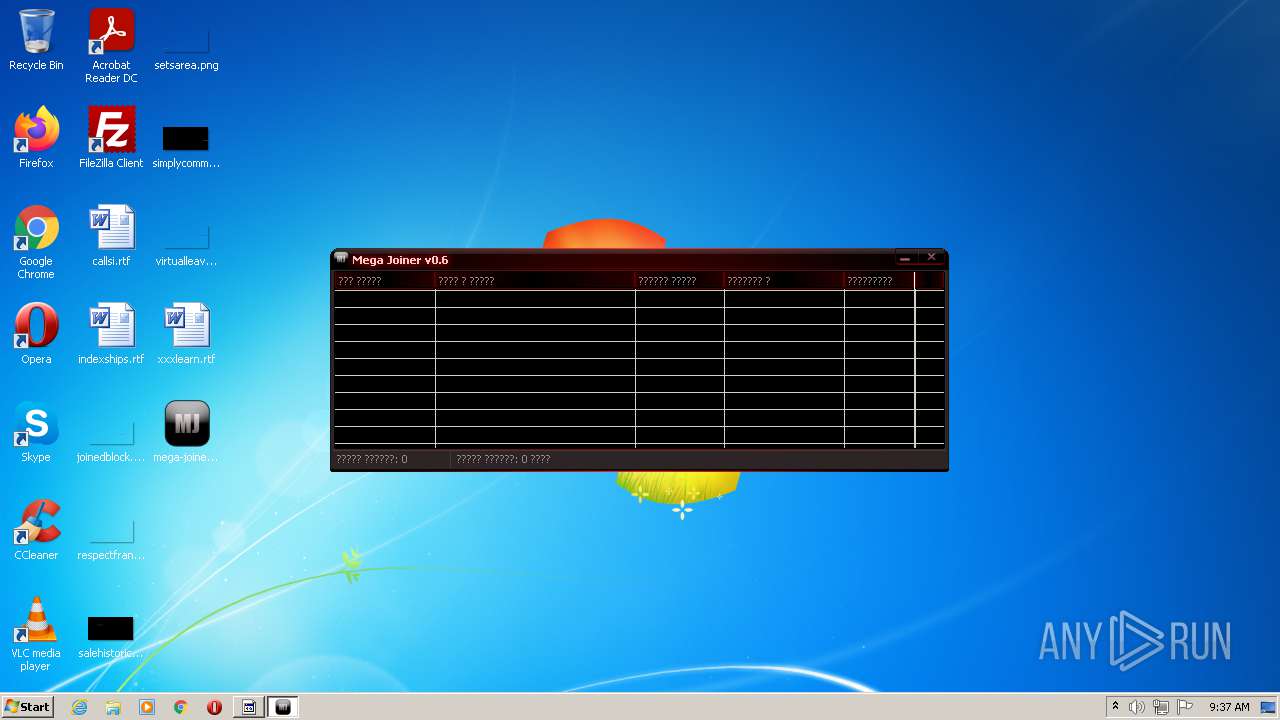
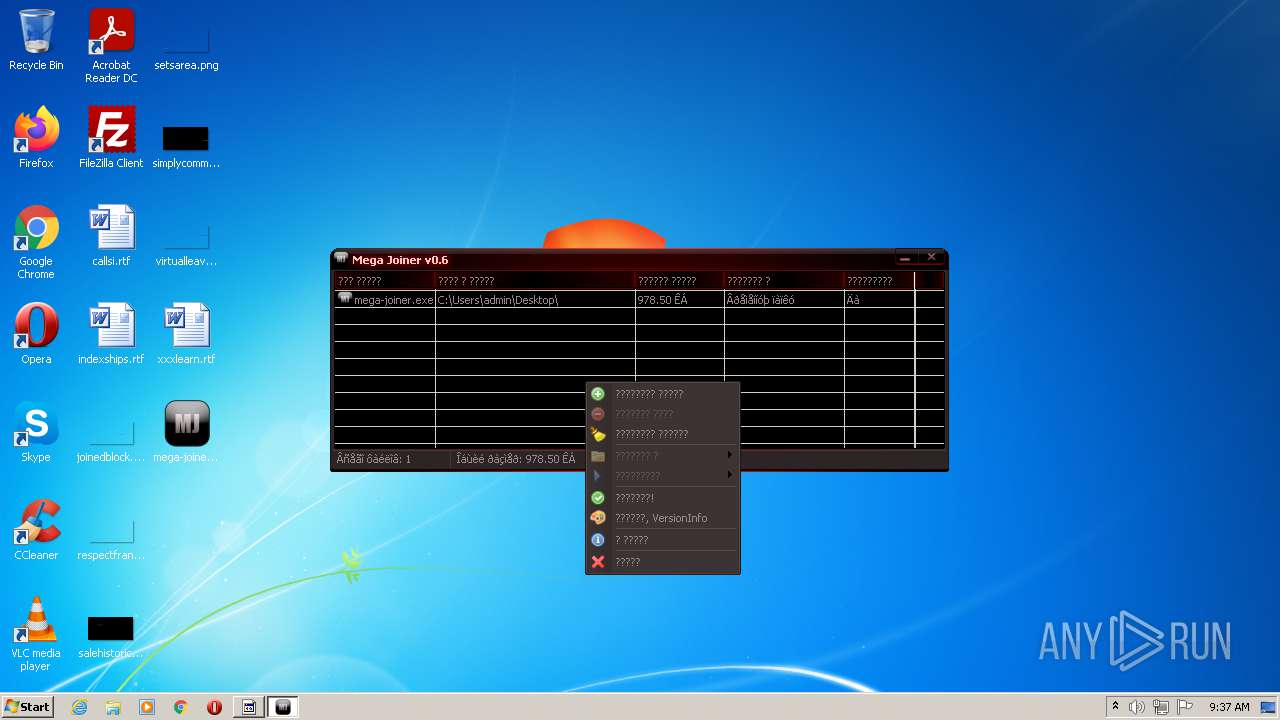
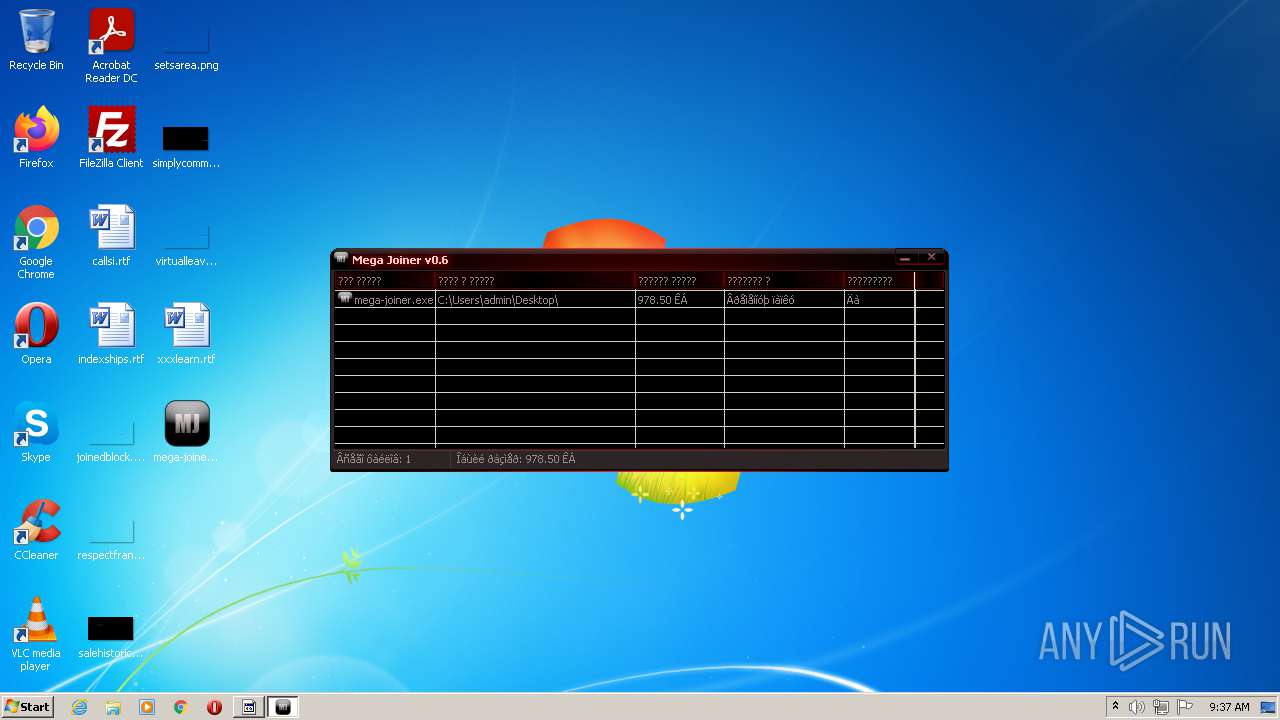
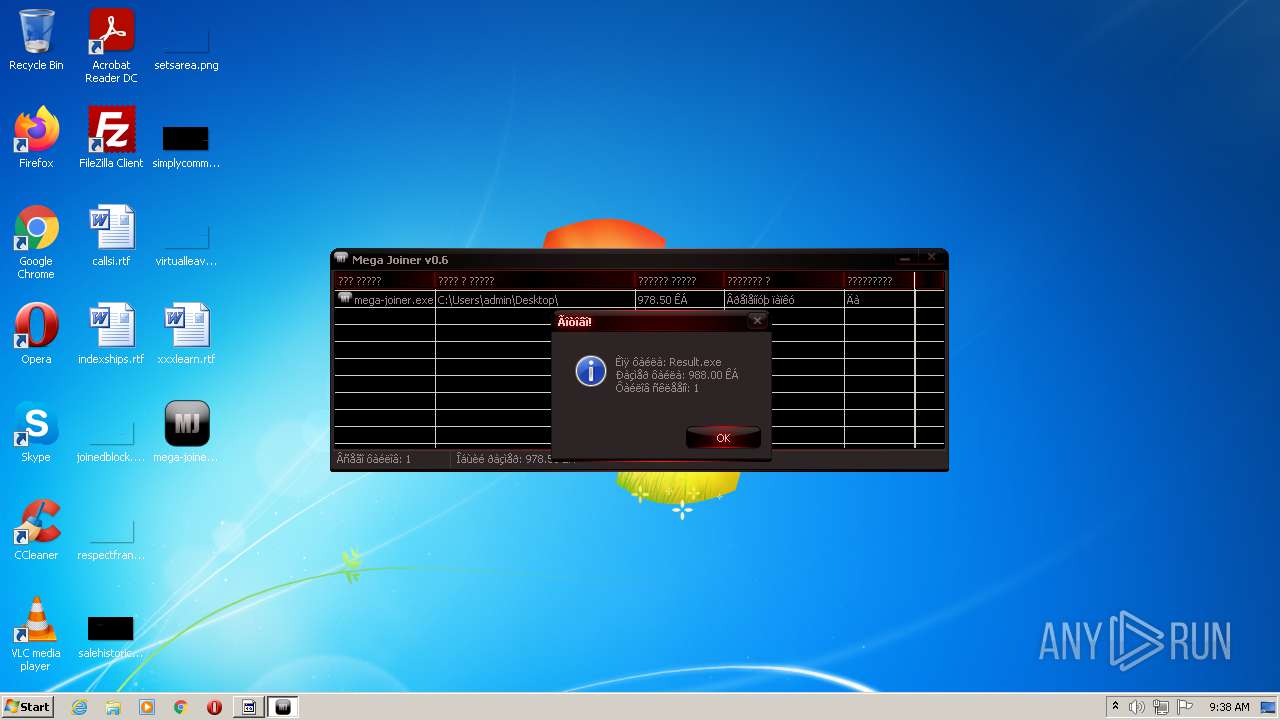
| File name: | mega-joiner.exe |
| Full analysis: | https://app.any.run/tasks/e5343069-f274-479b-9633-1019193e3725 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2021, 08:36:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A3DEF80D2E478FA796B0193F9236CA44 |
| SHA1: | F324FEC34605C8503623FAB632B745CADBE710E5 |
| SHA256: | B0318216B811C46410274E1D4DF614FF65B0CA602CA74C6895B42BD08F65CA24 |
| SSDEEP: | 24576:rAHGmI/L2YKv3k33f6E4YG05x2JnPiX8WV1o/8e:rGGmI/L2LL80aX168e |
MALICIOUS
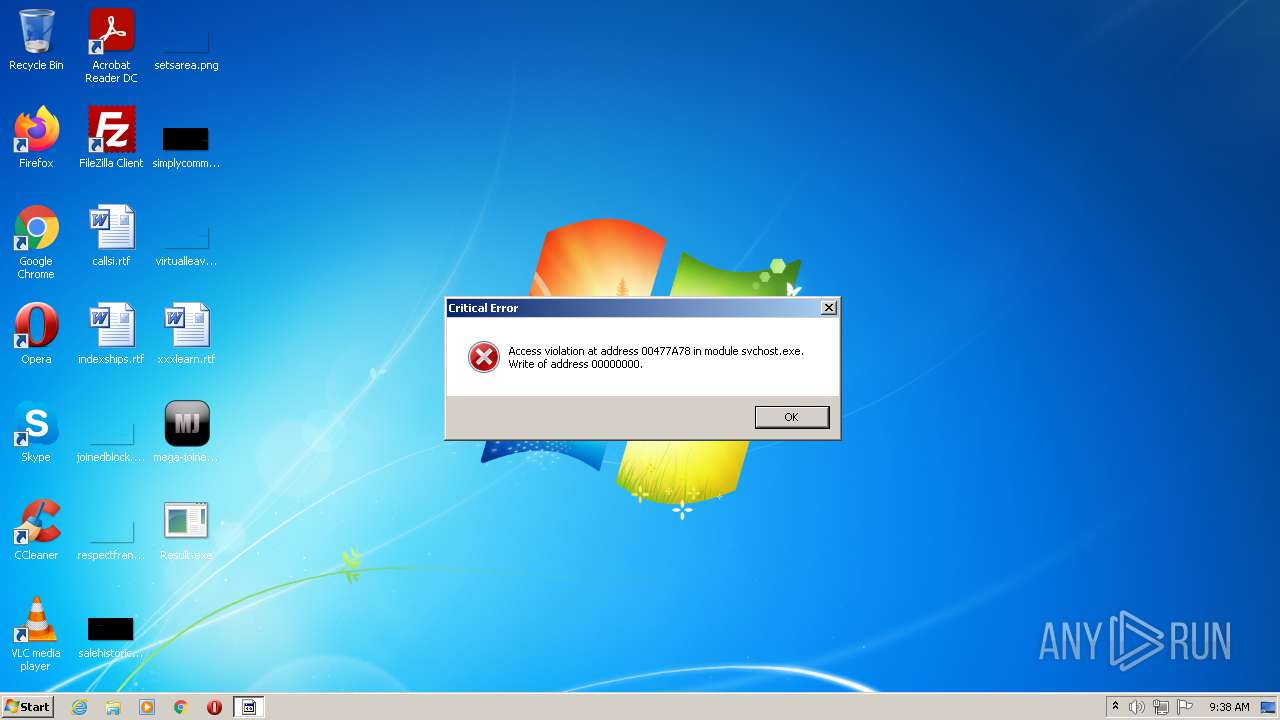
Drops executable file immediately after starts
- mega-joiner.exe (PID: 2492)
- chrome.exe (PID: 872)
Application was dropped or rewritten from another process
- joined.exe (PID: 744)
- Mega_Joiner.exe (PID: 1352)
- chrome.exe (PID: 872)
SUSPICIOUS
Executable content was dropped or overwritten
- mega-joiner.exe (PID: 2492)
- joined.exe (PID: 744)
- Mega_Joiner.exe (PID: 1352)
- chrome.exe (PID: 872)
Checks supported languages
- mega-joiner.exe (PID: 2492)
- joined.exe (PID: 744)
- Mega_Joiner.exe (PID: 1352)
- chrome.exe (PID: 872)
Drops a file with too old compile date
- mega-joiner.exe (PID: 2492)
- chrome.exe (PID: 872)
- Mega_Joiner.exe (PID: 1352)
Reads the computer name
- Mega_Joiner.exe (PID: 1352)
- mega-joiner.exe (PID: 2492)
- chrome.exe (PID: 872)
- joined.exe (PID: 744)
Reads default file associations for system extensions
- Mega_Joiner.exe (PID: 1352)
Reads the date of Windows installation
- chrome.exe (PID: 872)
INFO
Dropped object may contain Bitcoin addresses
- mega-joiner.exe (PID: 2492)
- Mega_Joiner.exe (PID: 1352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ 4.x (75) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (15.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.6) |
| .exe | | | Win32 Executable (generic) (2.5) |
| .exe | | | Win16/32 Executable Delphi generic (1.1) |
EXIF
EXE
| ProductVersion: | 0.6.0.0 |
|---|---|
| ProductName: | Mega Joiner |
| OriginalFileName: | - |
| LegalTrademarks: | - |
| LegalCopyright: | - |
| InternalName: | - |
| FileVersion: | 0.6.0.0 |
| FileDescription: | Mega Joiner |
| CompanyName: | DarkZhyK |
| CharacterSet: | Windows, Cyrillic |
| LanguageCode: | Russian |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.6.0.0 |
| FileVersionNumber: | 0.6.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1ae1 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 997376 |
| CodeSize: | 3584 |
| LinkerVersion: | 5.12 |
| PEType: | PE32 |
| TimeStamp: | 2013:06:15 18:44:28+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jun-2013 16:44:28 |
| Detected languages: |
|
| CompanyName: | DarkZhyK |
| FileDescription: | Mega Joiner |
| FileVersion: | 0.6.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | Mega Joiner |
| ProductVersion: | 0.6.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 15-Jun-2013 16:44:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000C26 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.14633 |
.rdata | 0x00002000 | 0x000004C0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.21236 |
.data | 0x00003000 | 0x0000D6F0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.72555 |
.rsrc | 0x00011000 | 0x000F2B4C | 0x000F2C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9833 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.22257 | 656 | Latin 1 / Western European | UNKNOWN | RT_VERSION |
2 | 7.99282 | 596126 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
3 | 4.94864 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.2359 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.04358 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.44414 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 4.73059 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 4.95208 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4097 | 5.5208 | 153 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
MAINICON | 2.81158 | 118 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
kernel32.dll |
shlwapi.dll |
user32.dll |
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | "C:\Users\admin\AppData\Local\Temp\joined.exe" | C:\Users\admin\AppData\Local\Temp\joined.exe | mega-joiner.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 872 | "C:\Users\admin\AppData\Local\Temp\chrome.exe" | C:\Users\admin\AppData\Local\Temp\chrome.exe | joined.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 67.0.3396.62 Modules
| |||||||||||||||
| 1352 | "C:\Users\admin\AppData\Local\Temp\Mega_Joiner.exe" | C:\Users\admin\AppData\Local\Temp\Mega_Joiner.exe | mega-joiner.exe | ||||||||||||
User: admin Company: DarkZhyK Integrity Level: MEDIUM Description: Mega Joiner Exit code: 0 Version: 0.6.0.0 Modules
| |||||||||||||||
| 2492 | "C:\Users\admin\Desktop\mega-joiner.exe" | C:\Users\admin\Desktop\mega-joiner.exe | Explorer.EXE | ||||||||||||
User: admin Company: DarkZhyK Integrity Level: MEDIUM Description: Mega Joiner Exit code: 0 Version: 0.6.0.0 Modules
| |||||||||||||||
Total events
5 757
Read events
5 477
Write events
274
Delete events
6
Modification events
| (PID) Process: | (2492) mega-joiner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2492) mega-joiner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2492) mega-joiner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2492) mega-joiner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
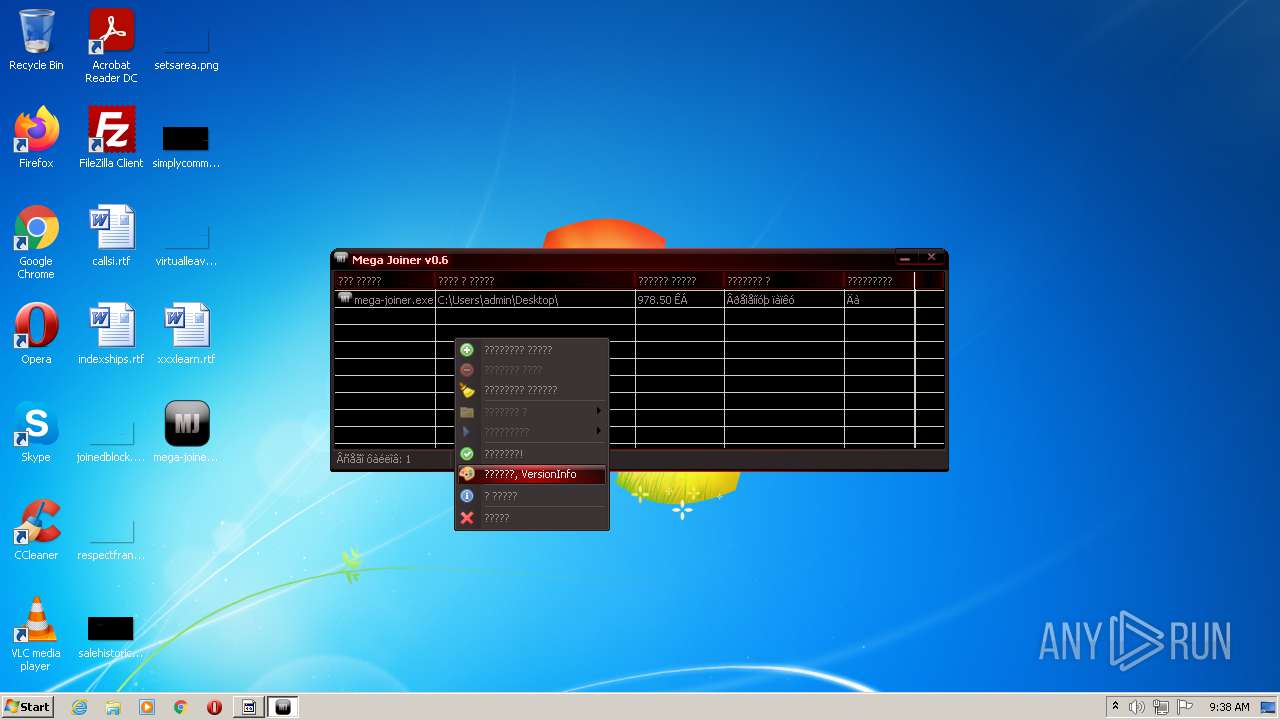
| (PID) Process: | (1352) Mega_Joiner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
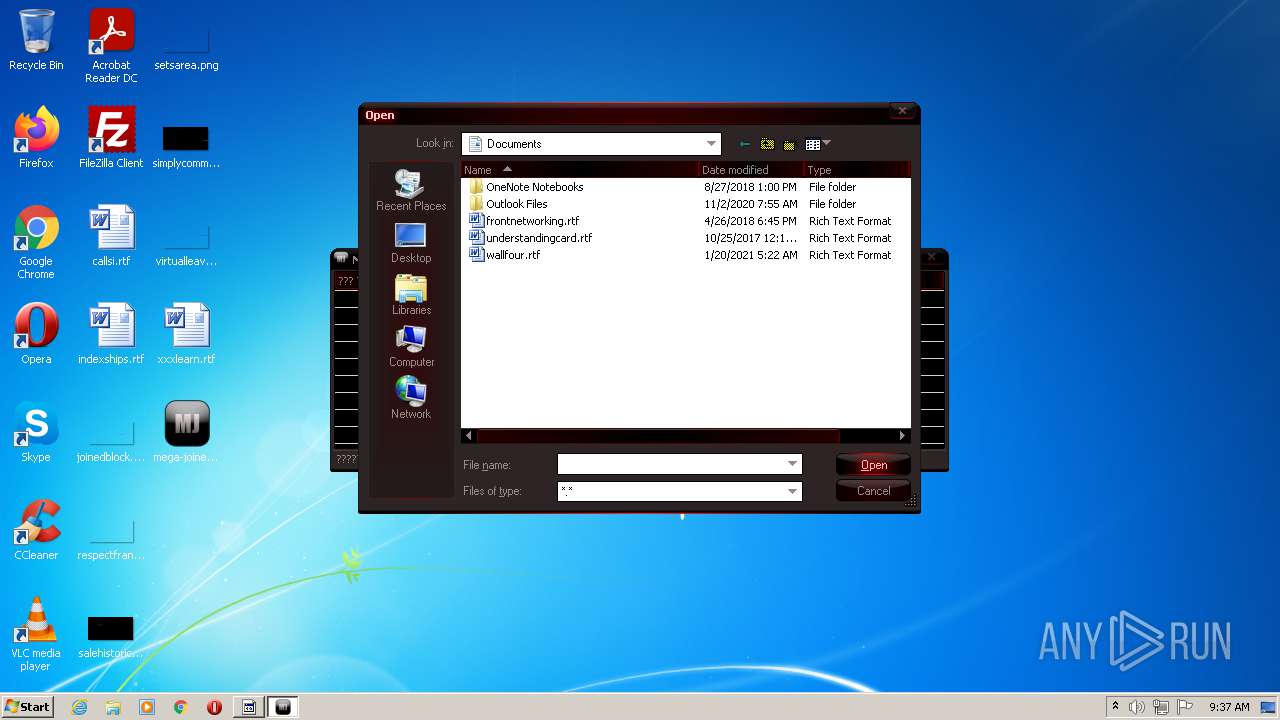
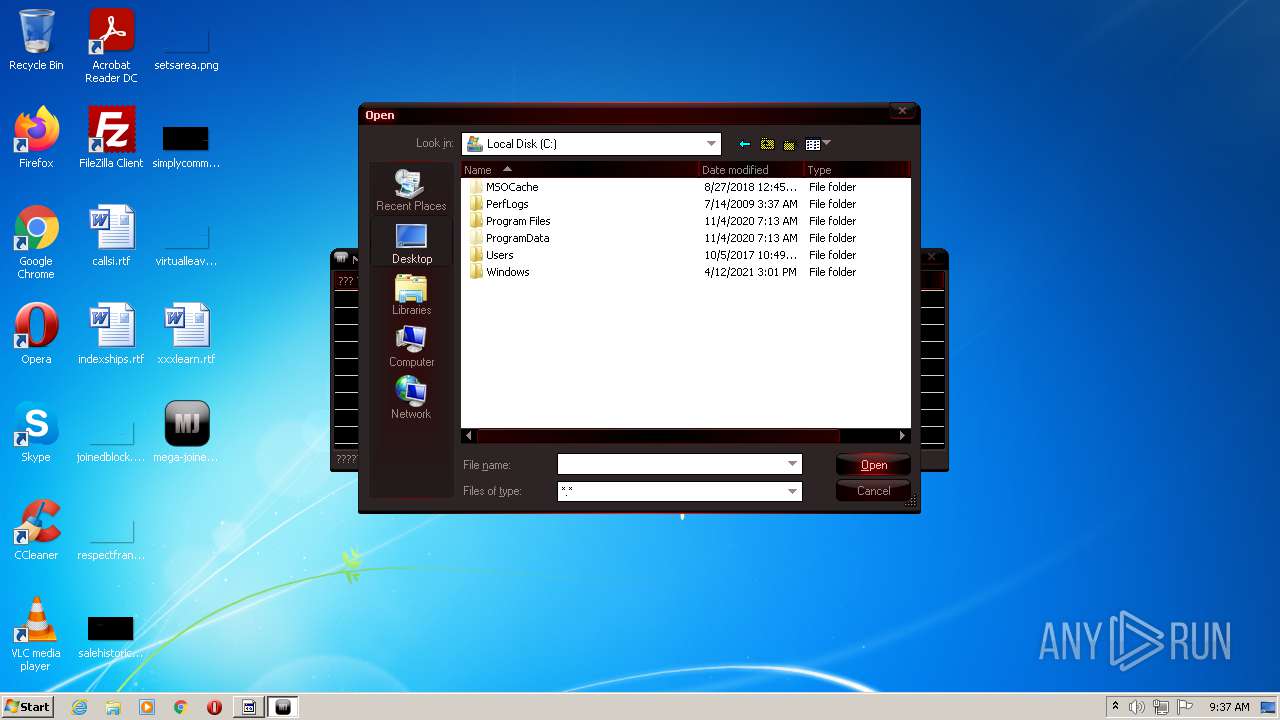
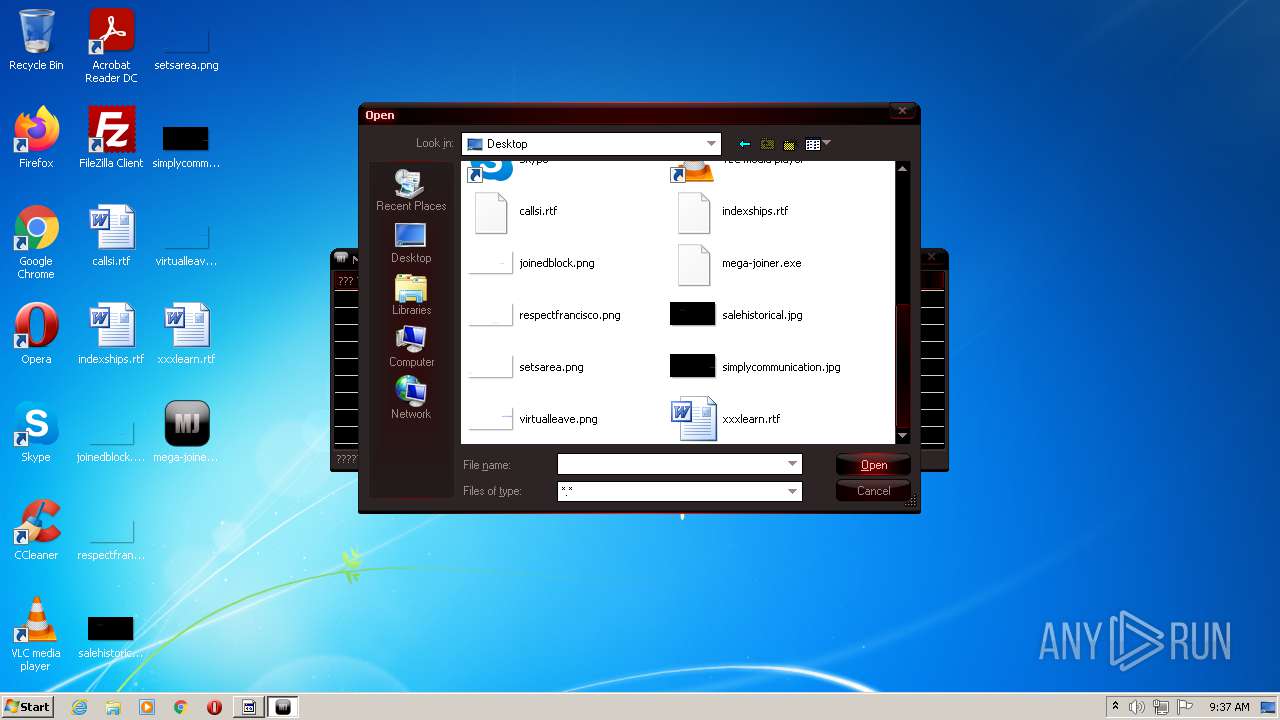
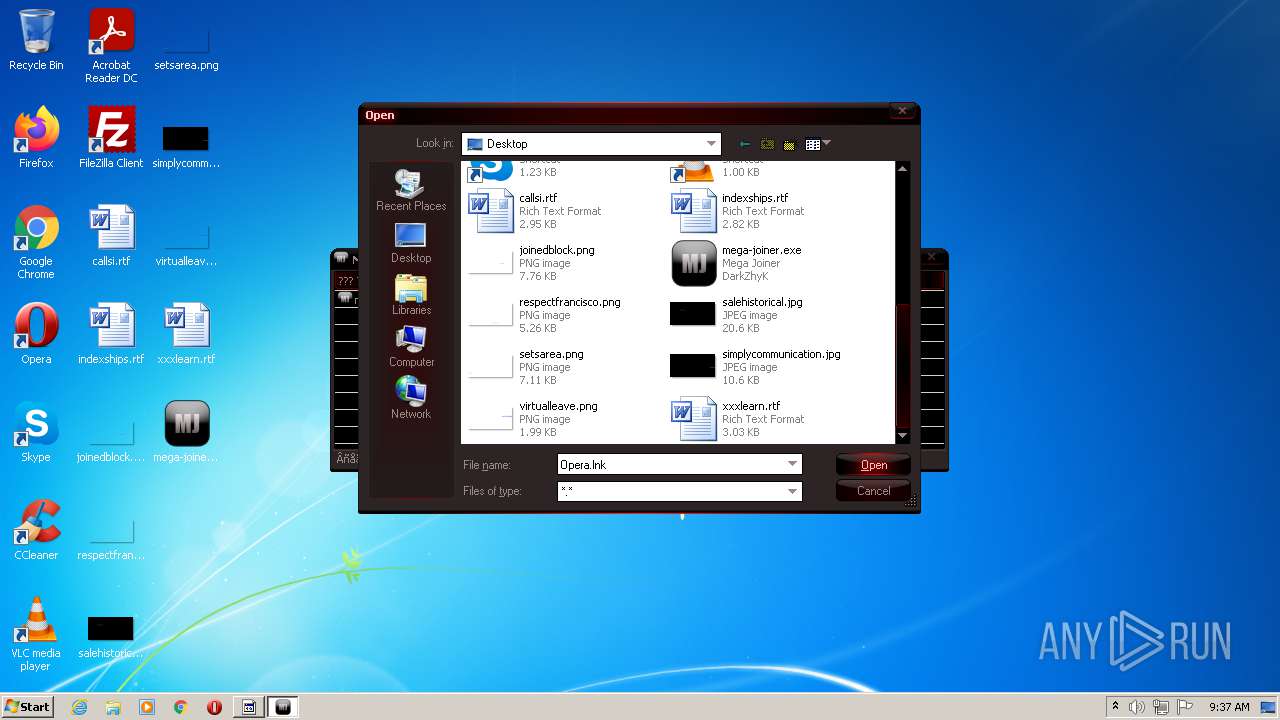
| (PID) Process: | (1352) Mega_Joiner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRULegacy |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (1352) Mega_Joiner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1352) Mega_Joiner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000100000007000000000000000B0000000C000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1352) Mega_Joiner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (1352) Mega_Joiner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
Executable files
15
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1352 | Mega_Joiner.exe | C:\Users\admin\Desktop\RCX83FE.tmp | executable | |
MD5:— | SHA256:— | |||
| 1352 | Mega_Joiner.exe | C:\Users\admin\Desktop\Result.exe | executable | |
MD5:26ABB9E459E5976F658CE80D6433F1B1 | SHA256:60CC77B5D4210CEF0A9032908B179142F212155426FDAE48055C5F72811F7A12 | |||
| 2492 | mega-joiner.exe | C:\Users\admin\AppData\Local\Temp\Mega_Joiner.exe | executable | |
MD5:2E874400C7E89085A55F8F7EC8610563 | SHA256:4EAF17B2E390F19F8BA65A63C6FAC7F6A30778160DCEECFDCFD48EA5181A4AF4 | |||
| 1352 | Mega_Joiner.exe | C:\Users\admin\Desktop\RCX83CC.tmp | executable | |
MD5:60C73880BEC03EFC1A9497FE9148DCFB | SHA256:3E031D639069BCA668262847450CA808792AB84DADF1BBB4ADC3C8EF6D5B4FCA | |||
| 744 | joined.exe | C:\Users\admin\AppData\Local\Temp\chrome.exe | executable | |
MD5:753639E16FEEDBCBA379B5FAA30376D6 | SHA256:1679D232DAB87BC6F83A5587C31FBB64EB677AA7C9D6A366F710BBB397B29D63 | |||
| 1352 | Mega_Joiner.exe | C:\Users\admin\Desktop\RCX83EE.tmp | executable | |
MD5:AC3872192A065BE68BA2C286DAF82668 | SHA256:8EC453E15E8DC1ED9BCE256EE9D2658A68888826782FCADC22A204F3E7DFB1A6 | |||
| 2492 | mega-joiner.exe | C:\Users\admin\AppData\Local\Temp\joined.exe | executable | |
MD5:763A6C7BB6BCB2BB8B21C1A2CFC09C81 | SHA256:3CDEEAD34E7B1B14457335A504CD43D6645C34A467AF2ADFBCB1C507565D7F31 | |||
| 1352 | Mega_Joiner.exe | C:\Users\admin\Desktop\RCX83BC.tmp | executable | |
MD5:5CC59F29BE936B199833D740199341CE | SHA256:942E3A4815E7E5B8E9CA679C064254846D1920939720D0842B4C5F562ED51284 | |||
| 1352 | Mega_Joiner.exe | C:\Users\admin\Desktop\RCX83DD.tmp | executable | |
MD5:4AF0532A75E602202B1A90E5ACD8C877 | SHA256:57FC80CAAF0125052CC1E713175C3D037CD920F9A359AA992507F859B7244369 | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Temp\chrome.exe.exe | executable | |
MD5:FF317550DC5C0FEFF7410C023D8DD552 | SHA256:54846FBD538DFD4D469546AD70DCD4C40543B430E8648F4CE7DFEAD8C2CBA059 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report