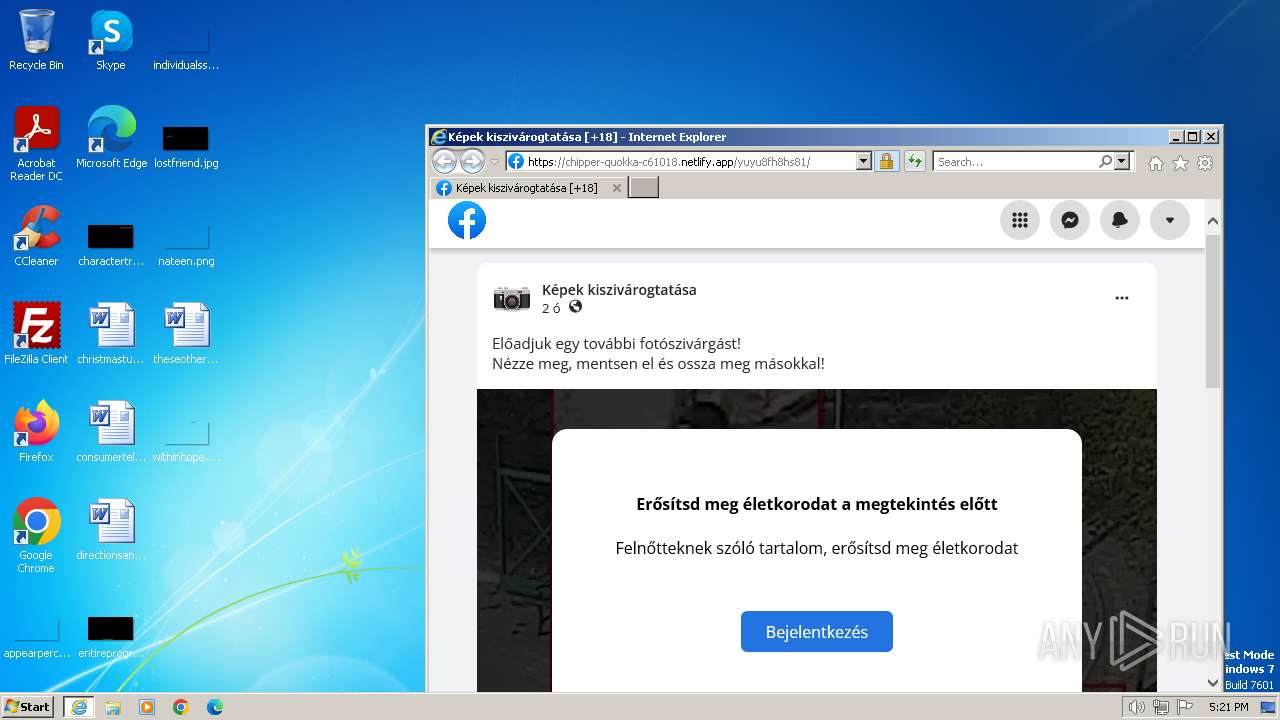
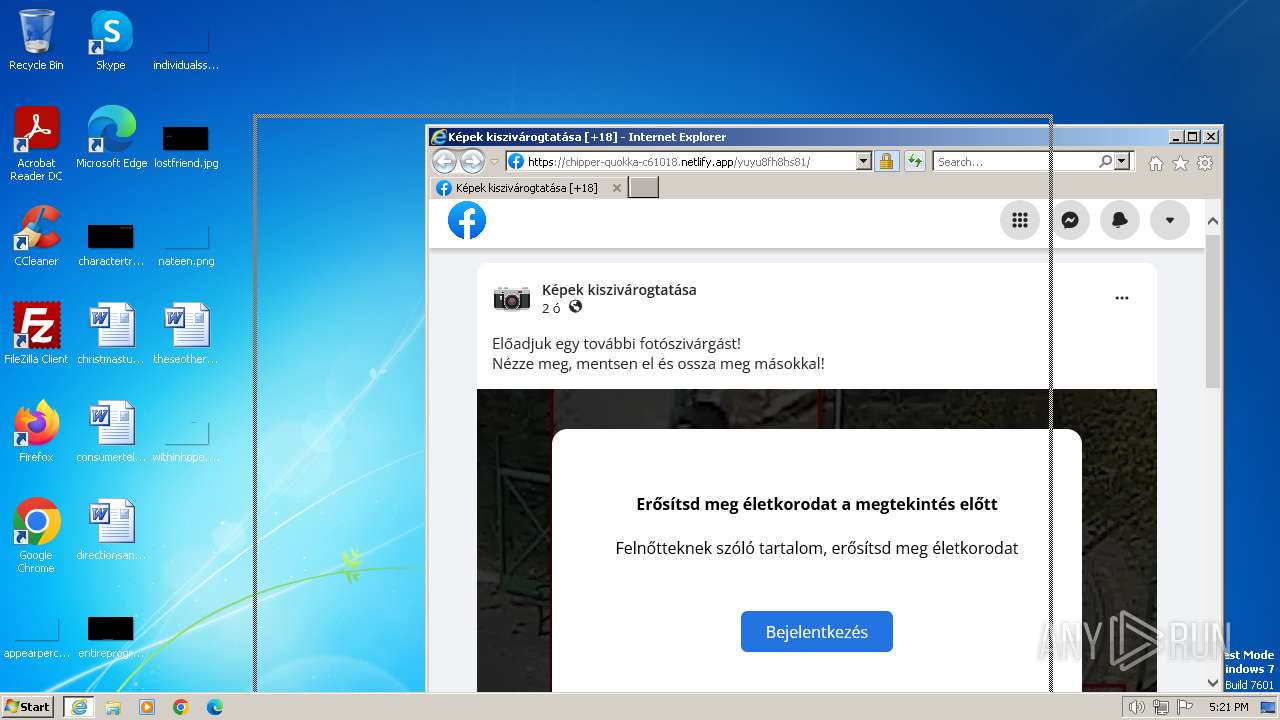
| URL: | https://l.messenger.com/l.php?u=http%3A%2F%2Fcoastalresiliencedev-ucsc.org%2FTgh8Xh5U%2Fprofile719%2F98268581729527%3F%253F754664%3D565737&h=AT1CJAyeQLrGUWQ8My0qogs8v72nBJzz8u-o5YfmTgDxAPB-Dgatc9CawIbrlXuAxJYiQSgYNpJ6sjsrgGWJfc5yNcfmu4EDWHH-Ck71I69MMxJqX0a5p3lSCJ03SVVMeKxfYA |
| Full analysis: | https://app.any.run/tasks/a45c3d73-bf68-4e32-a862-ec0c2c74063d |
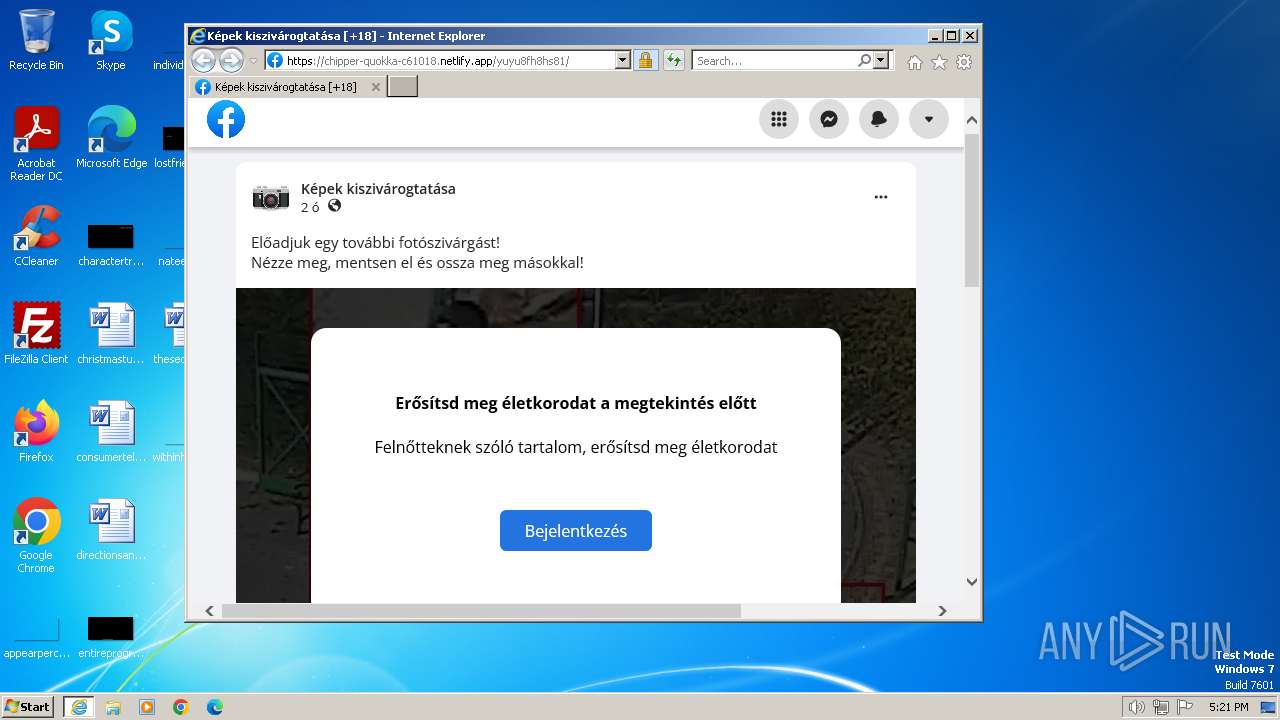
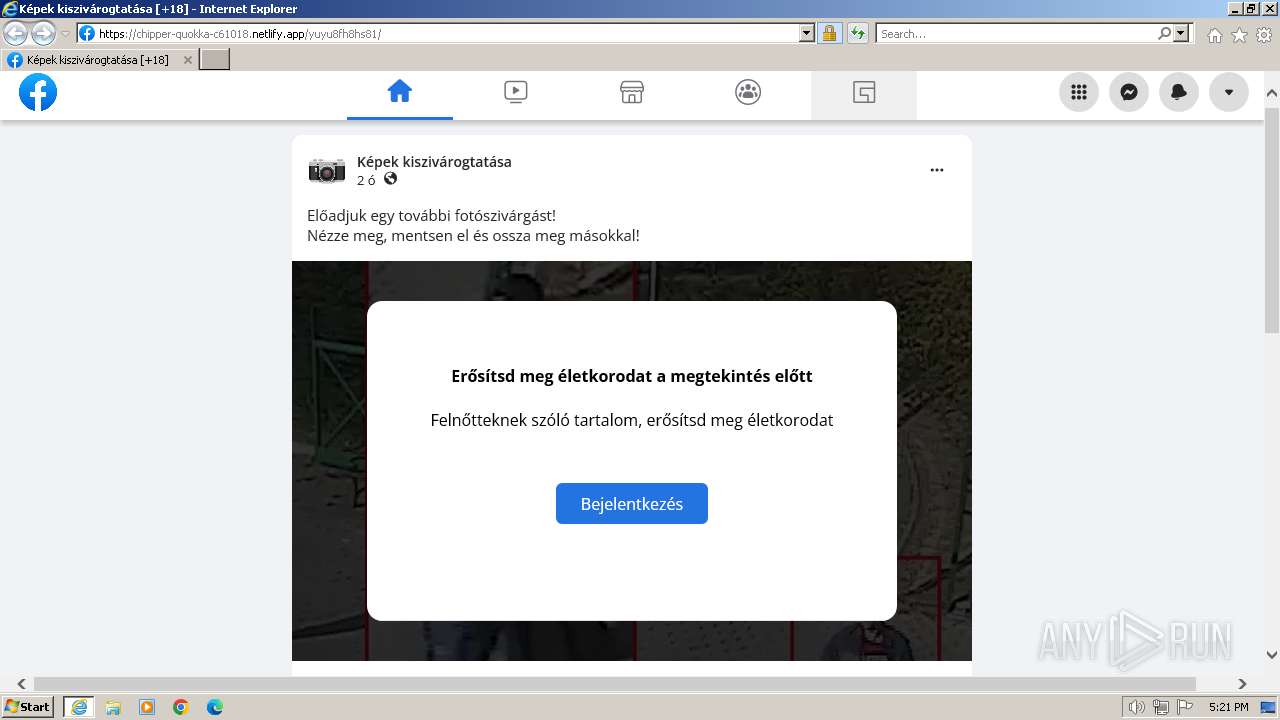
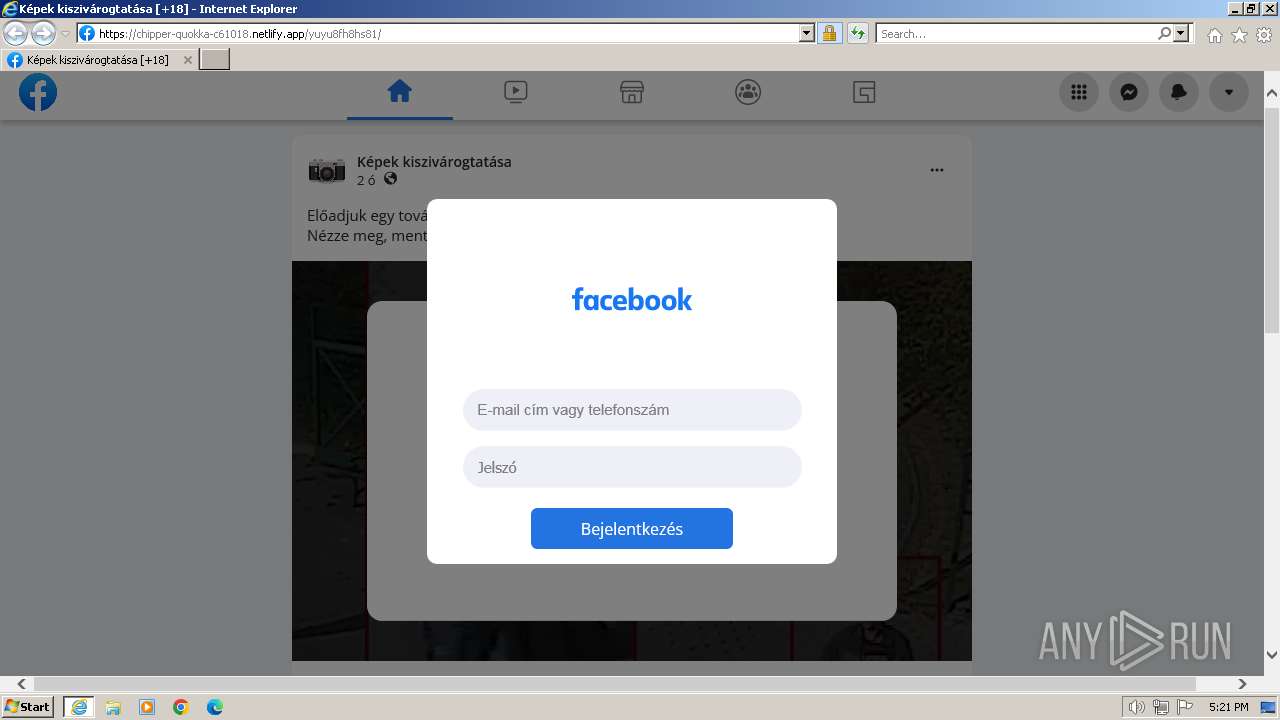
| Verdict: | Malicious activity |
| Analysis date: | December 24, 2023, 17:20:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 95F8262023AF3C54F6A25D1DFF643BF9 |
| SHA1: | E243C8444263612A99ECC1622911D171FBA4C665 |
| SHA256: | B0302BD8421F9DCA8073A36E7814DE5B356A593E49DE0DC4B41CBE2FBBBF2143 |
| SSDEEP: | 6:2jA2QVafszgQ72CpjxK6jhCabvDZJnHa5UxGZ3N84wtcSZc1dMQS1:282Xsn6CVxK6wcDfHsUxiXYc/M71 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://l.messenger.com/l.php?u=http%3A%2F%2Fcoastalresiliencedev-ucsc.org%2FTgh8Xh5U%2Fprofile719%2F98268581729527%3F%253F754664%3D565737&h=AT1CJAyeQLrGUWQ8My0qogs8v72nBJzz8u-o5YfmTgDxAPB-Dgatc9CawIbrlXuAxJYiQSgYNpJ6sjsrgGWJfc5yNcfmu4EDWHH-Ck71I69MMxJqX0a5p3lSCJ03SVVMeKxfYA" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 324 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:128 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
15 556
Read events
15 489
Write events
65
Delete events
2
Modification events
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
43
Text files
50
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:D56BECCACEEC1B933B041F21079830AC | SHA256:53A28C5EE034509ADD6117E3CE70D8E3E7816F20EC26F468973B466B9AA5E200 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_9F6005AF34C7906F717D420F892FD6D0 | binary | |
MD5:892641F9EF3D225D11CE2DF024784614 | SHA256:246C95193D422EA53CD1F113963690059E5659A677B2C613162A8DAC0D025E09 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:3390BA53CC268658B397093816700945 | SHA256:EAF0E9A9AC92C1109FD8DB4919D4EFC31758C7B754FD48030AE3A8433E28F775 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35DDEDF268117918D1D277A171D8DF7B_6CC8D09A86A83ACDA53960C08723A0F9 | binary | |
MD5:E7543EE8EC9B9CB12E0CDF6F74F6B847 | SHA256:1DBA83B9C5292BCD2564D65EECA2918D3EF28A63F6FD638A3B7AEB9DC202D76F | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:A56045D67FF95A6DB8E341781A5BAA71 | SHA256:35039DE899B80BA4CBE1B115F34F9DE6AA3B2F9C37E060498FE3306C5514E9AD | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\l[1].htm | html | |
MD5:60DCB62789A647EB7E1C34B2AEA70592 | SHA256:0FE2CF057872E0A0C6F981CC75039F27F65CD5A9D6FD3C29B257B2C8CA6161A8 | |||
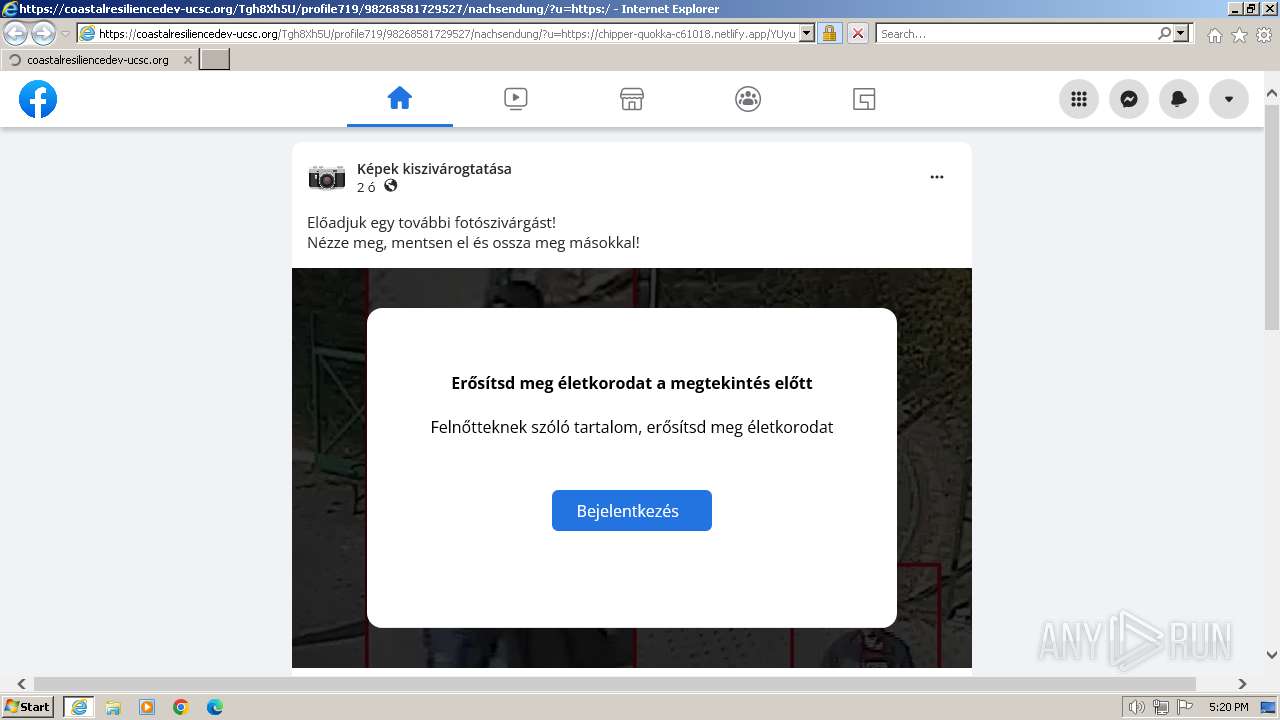
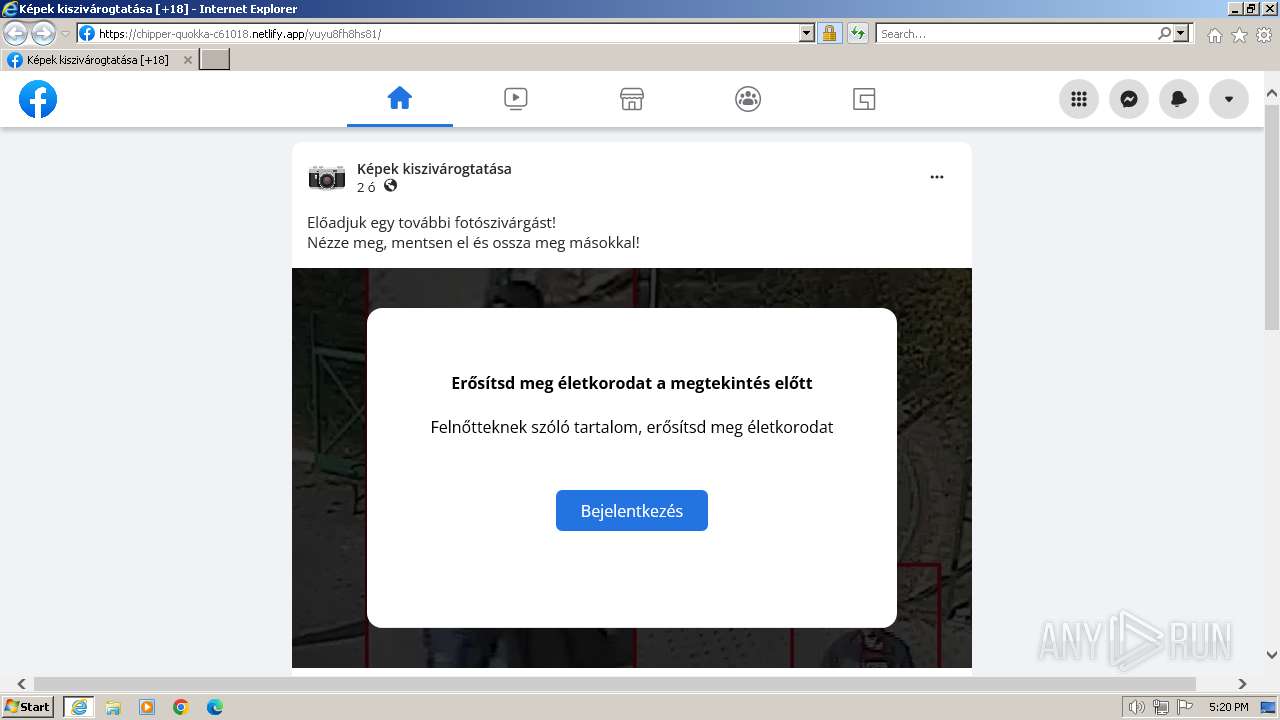
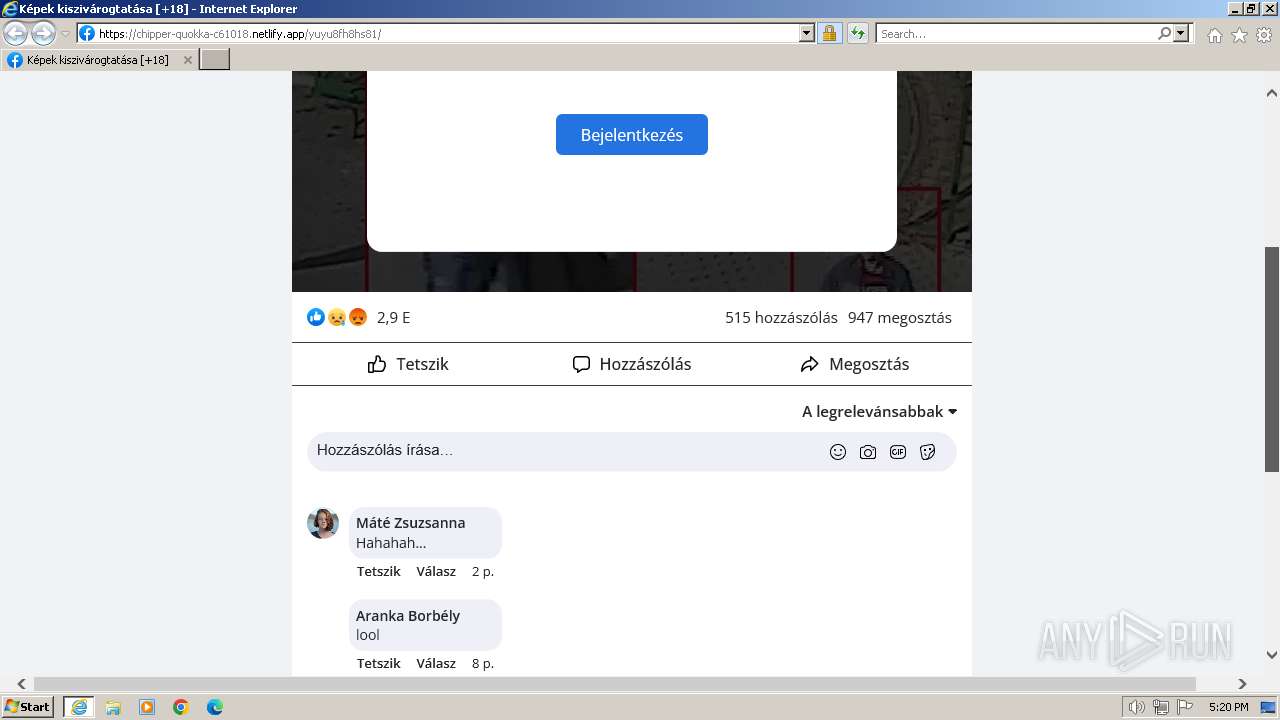
| 324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\nachsendung[1].htm | html | |
MD5:8D130779AB4E22BB0F994835B8A66F4C | SHA256:2636D751626C32A8481525BA56768BAA98F8E34205EE563E9670EB431310A171 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\l[1].htm | html | |
MD5:CB172361A09B6D8AC7DF6202F45B874D | SHA256:F9E8A13FA3C617410B2E83FAE200C87E5AEADF46E482730A51FF34A98E346642 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\l[1].htm | html | |
MD5:1B4D8A9EEADF68AD0D9BA32CE50590B5 | SHA256:7EEF0D23F304039A4F718B7776A836DAE2795DD90016F246516B2B00180964DE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
53
DNS requests
23
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
324 | iexplore.exe | GET | 200 | 184.24.77.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?129d20c84d8c4223 | unknown | compressed | 4.66 Kb | unknown |
324 | iexplore.exe | GET | 200 | 184.24.77.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?53bfb7cf8a6cf97e | unknown | compressed | 4.66 Kb | unknown |
324 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | unknown | binary | 471 b | unknown |
324 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAQuwRbaL5ZEC1WBcSasu8Q%3D | unknown | binary | 471 b | unknown |
324 | iexplore.exe | GET | 301 | 157.240.252.10:80 | http://l.messenger.com/l.php?u=http%3A%2F%2Fcoastalresiliencedev-ucsc.org%2FTgh8Xh5U%2Fprofile719%2F98268581729527%3F%253F754664%3D565737&h=AT2bTStrV8QjYwgLjdMLxLJmoxJYtL2M9xw_4jTnnmIggEolzpGJ2cEn9Hp2CTHkjFR2CSVMRvIodIVqKM9YVKMWO5doIEE51udIynZQ4VWq6MHaE_XHZstRWKK_oYO0390iXMqikQ | unknown | — | — | unknown |
324 | iexplore.exe | GET | 301 | 157.240.252.10:80 | http://l.messenger.com/l.php?u=http%3A%2F%2Fcoastalresiliencedev-ucsc.org%2FTgh8Xh5U%2Fprofile719%2F98268581729527%3F%253F754664%3D565737&h=AT3TKPWSbaSVozuIof5Pbia0bboufjovGuHYbpaJs8SFbBMcB41Dgld14ScnpqKLD6w4PGNUsOnHSNTv6Z-RB_5Dr_qOX1e2cYY8VfxgR5t2TbhGB64cNDY4rVLJfaeZsvGJ0Y5RAw | unknown | — | — | unknown |
324 | iexplore.exe | GET | 301 | 157.240.252.10:80 | http://l.messenger.com/l.php?u=http%3A%2F%2Fcoastalresiliencedev-ucsc.org%2FTgh8Xh5U%2Fprofile719%2F98268581729527%3F%253F754664%3D565737&h=AT2zKMAEO7PYcGSzqOheT-07hhMiMM7iXfbEaG6LLD4RiXoeybAwG4-2QGZef0B1RY_FF4F5-Jc-mkbTvf3ATi7EBexVPPNXb1VyEneozPFsS2ywS7ztSIDTHkKDLtax1GFnthARmQ | unknown | — | — | unknown |
324 | iexplore.exe | GET | 301 | 4.232.99.1:80 | http://coastalresiliencedev-ucsc.org/Tgh8Xh5U/profile719/98268581729527?%3F754664=565737 | unknown | — | — | unknown |
324 | iexplore.exe | GET | 301 | 4.232.99.1:80 | http://coastalresiliencedev-ucsc.org/Tgh8Xh5U/profile719/98268581729527/?%3F754664=565737 | unknown | — | — | unknown |
324 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEA9iL28hwv9dUh9yOh1H1i0%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
324 | iexplore.exe | 157.240.252.10:443 | l.messenger.com | FACEBOOK | DE | unknown |
324 | iexplore.exe | 184.24.77.202:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
324 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
324 | iexplore.exe | 157.240.252.10:80 | l.messenger.com | FACEBOOK | DE | unknown |
324 | iexplore.exe | 4.232.99.1:80 | coastalresiliencedev-ucsc.org | MICROSOFT-CORP-MSN-AS-BLOCK | IT | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
324 | iexplore.exe | 4.232.99.1:443 | coastalresiliencedev-ucsc.org | MICROSOFT-CORP-MSN-AS-BLOCK | IT | unknown |
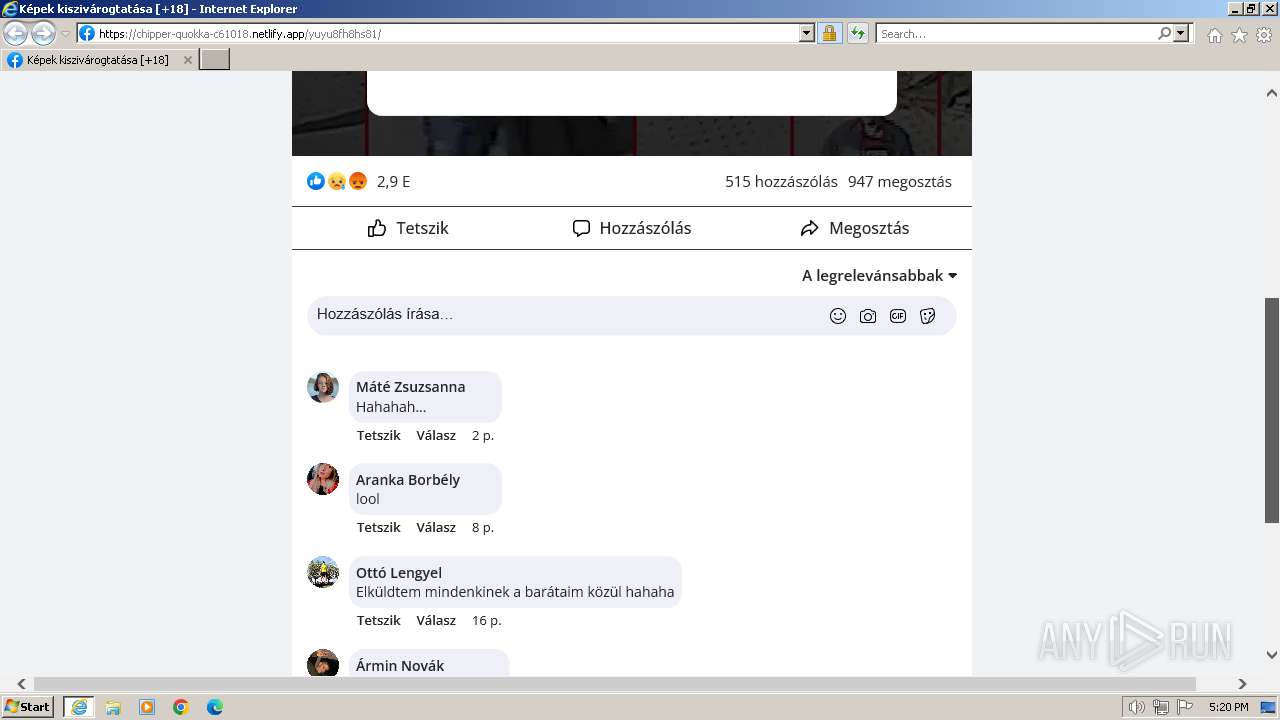
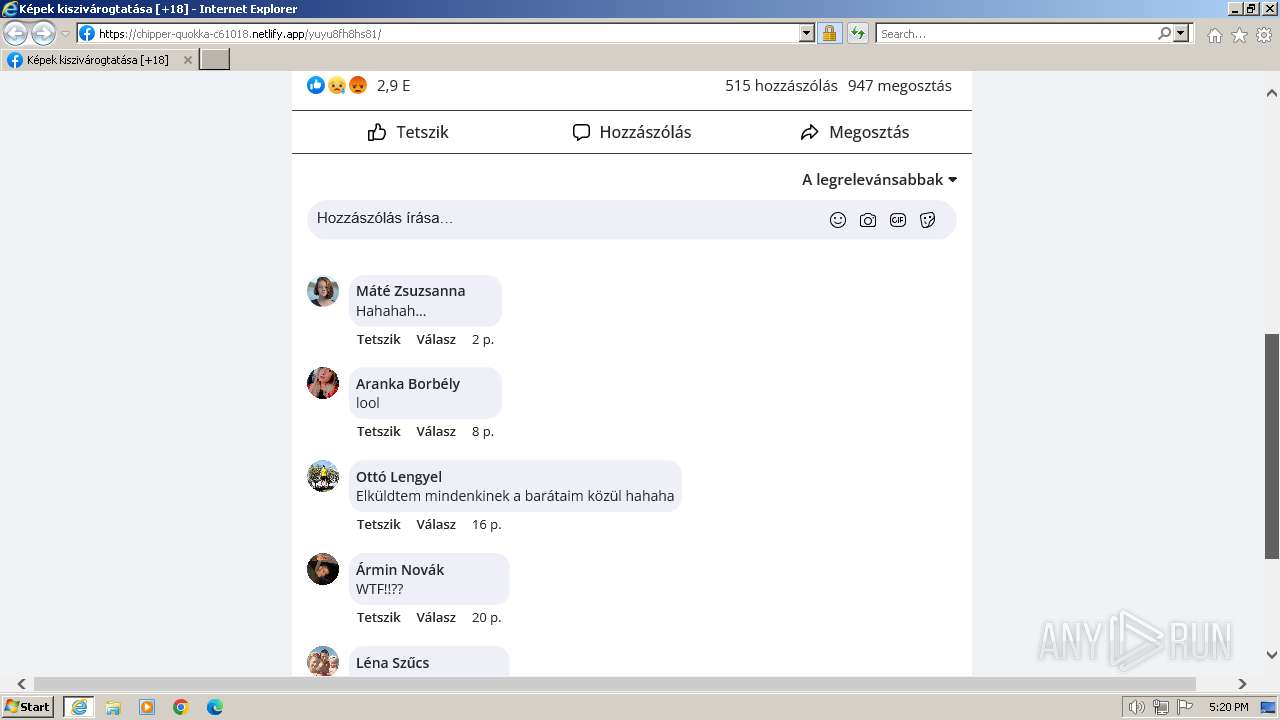
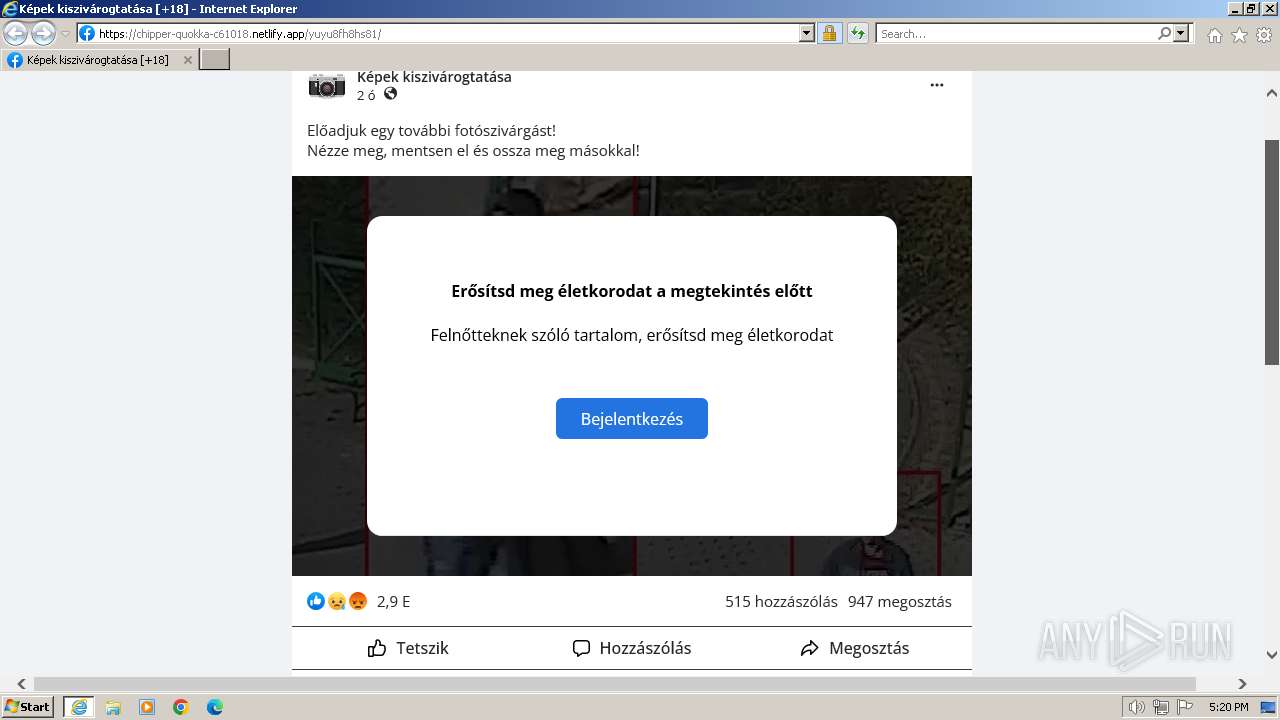
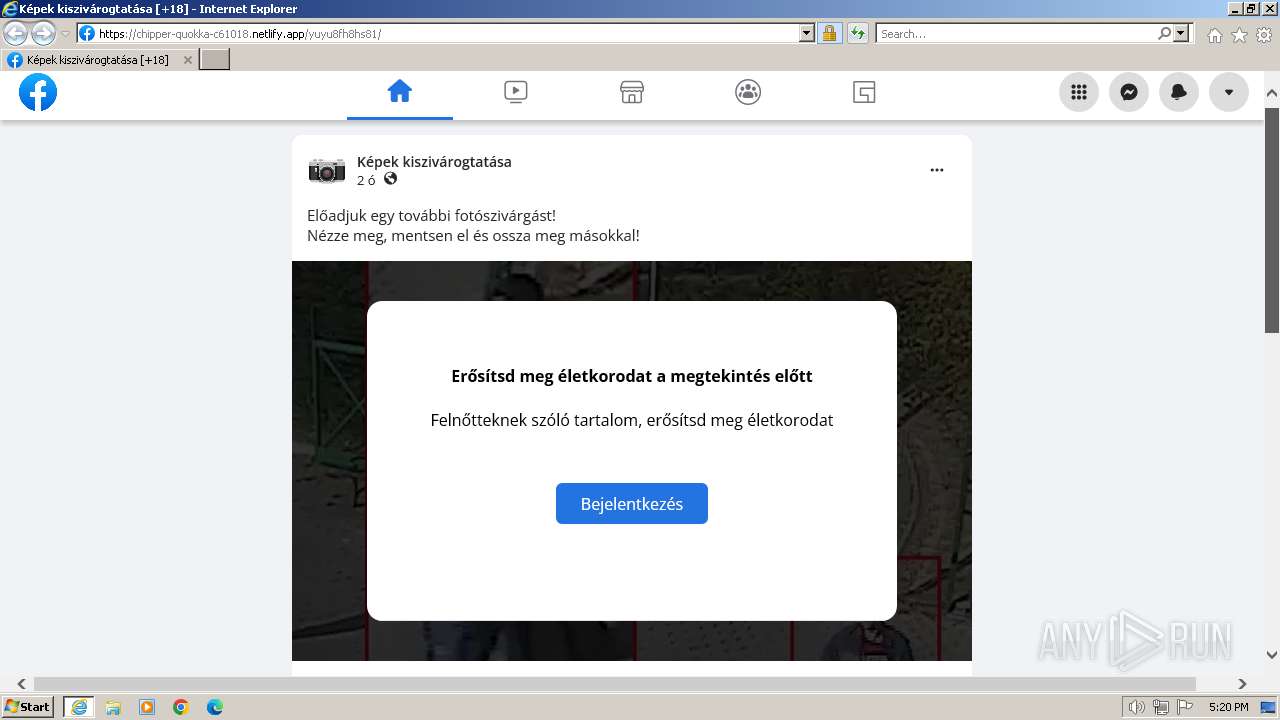
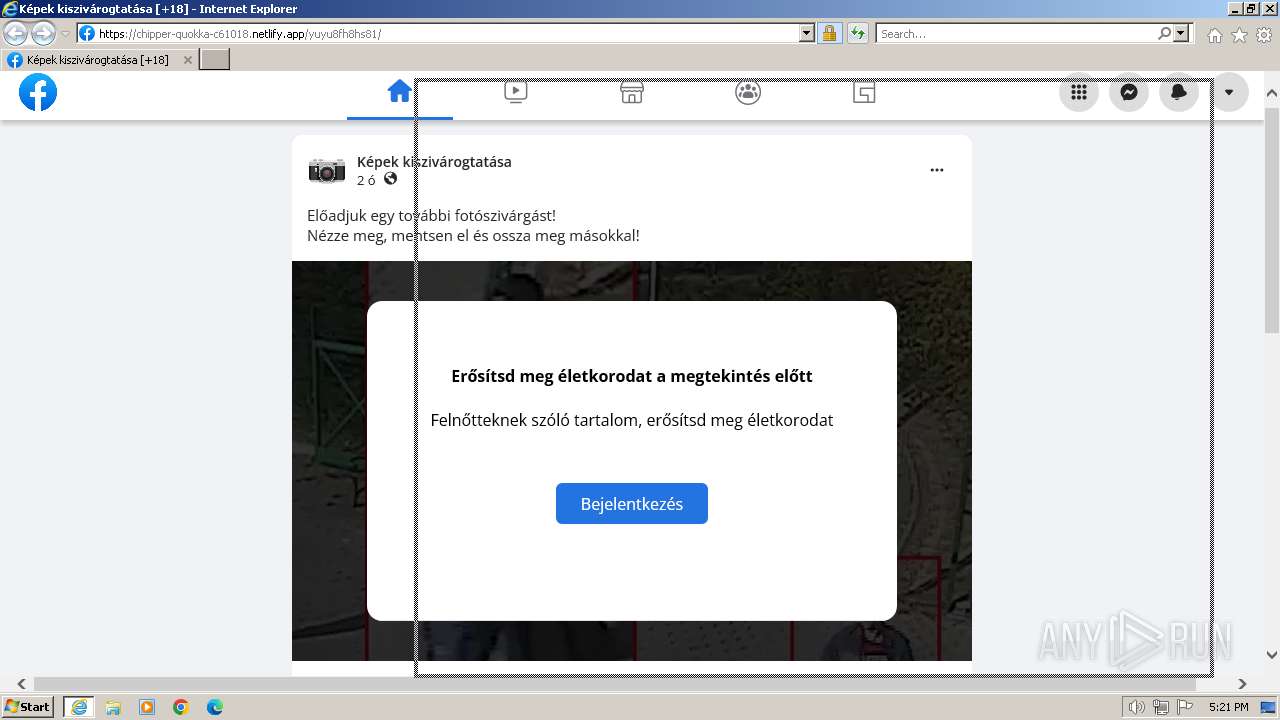
324 | iexplore.exe | 18.192.94.96:443 | chipper-quokka-c61018.netlify.app | AMAZON-02 | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
l.messenger.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
coastalresiliencedev-ucsc.org |
| unknown |
chipper-quokka-c61018.netlify.app |
| unknown |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
code.jquery.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
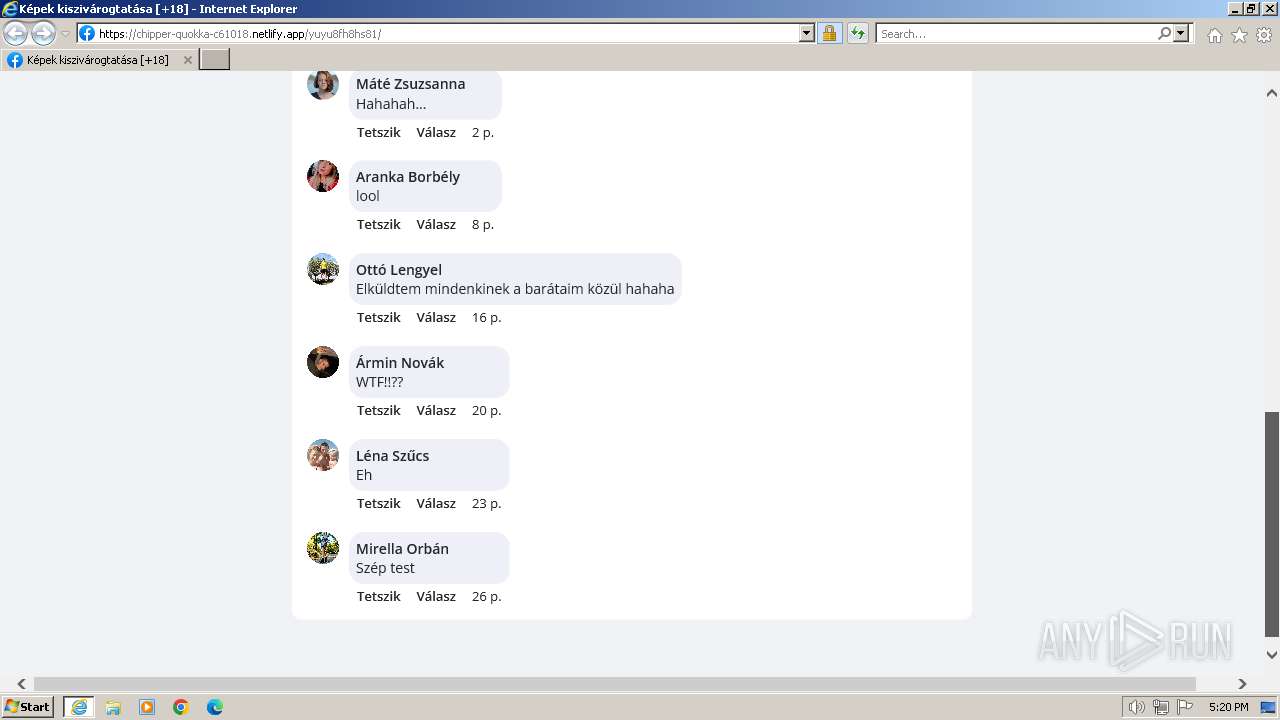
1080 | svchost.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Netlify Hosted DNS Request - Possible Phishing Landing |
324 | iexplore.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Netlify Hosted TLS SNI Request - Possible Phishing Landing |
324 | iexplore.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Netlify Hosted TLS SNI Request - Possible Phishing Landing |
324 | iexplore.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Netlify Hosted TLS SNI Request - Possible Phishing Landing |
324 | iexplore.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Netlify Hosted TLS SNI Request - Possible Phishing Landing |
324 | iexplore.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Netlify Hosted TLS SNI Request - Possible Phishing Landing |
324 | iexplore.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Netlify Hosted TLS SNI Request - Possible Phishing Landing |
324 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |
324 | iexplore.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Netlify Hosted TLS SNI Request - Possible Phishing Landing |
324 | iexplore.exe | Possible Social Engineering Attempted | ET HUNTING Suspicious Netlify Hosted TLS SNI Request - Possible Phishing Landing |