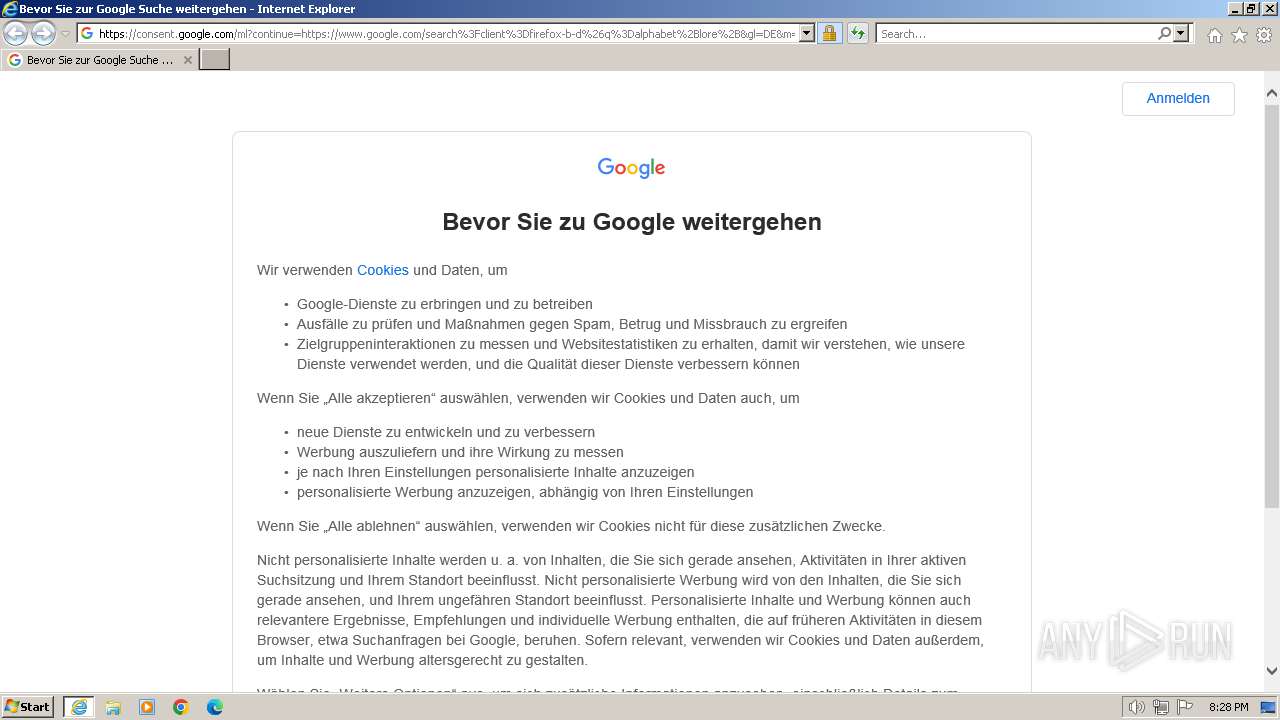
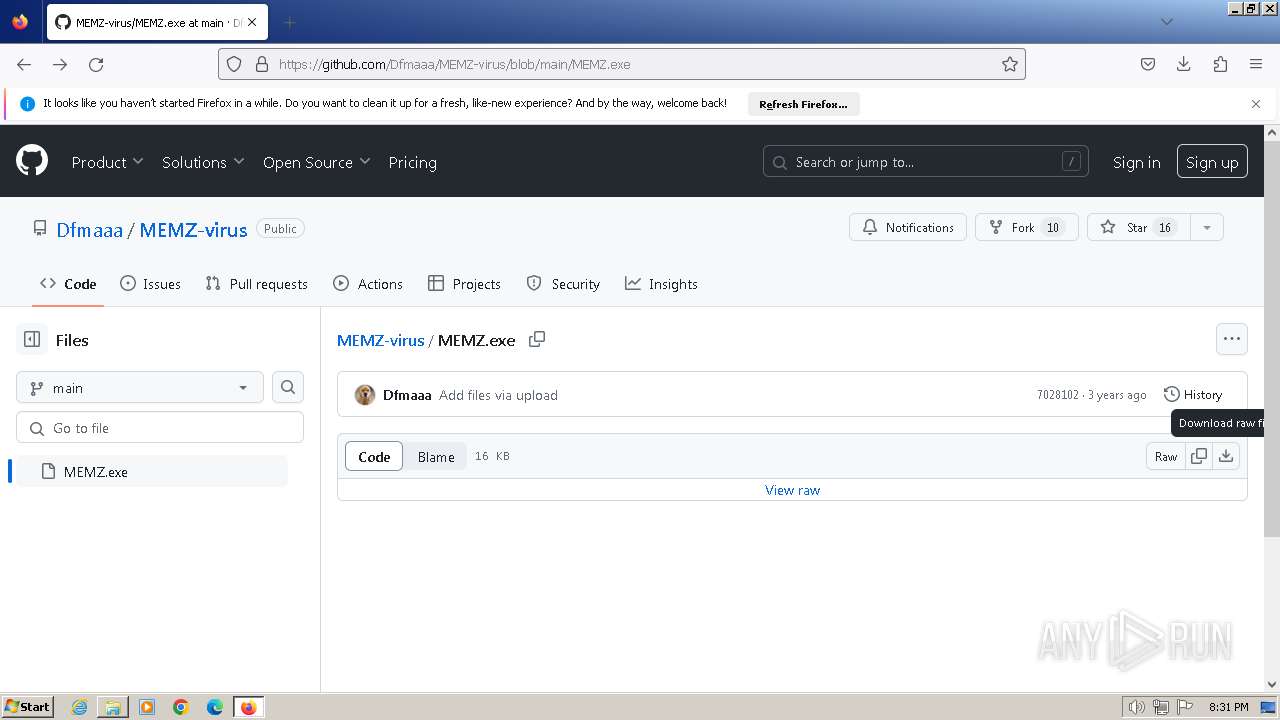
| URL: | https://www.google.com/search?client=firefox-b-d&q=alphabet+lore+ |
| Full analysis: | https://app.any.run/tasks/6e134324-e428-4cb4-9fa1-79d1e173861f |
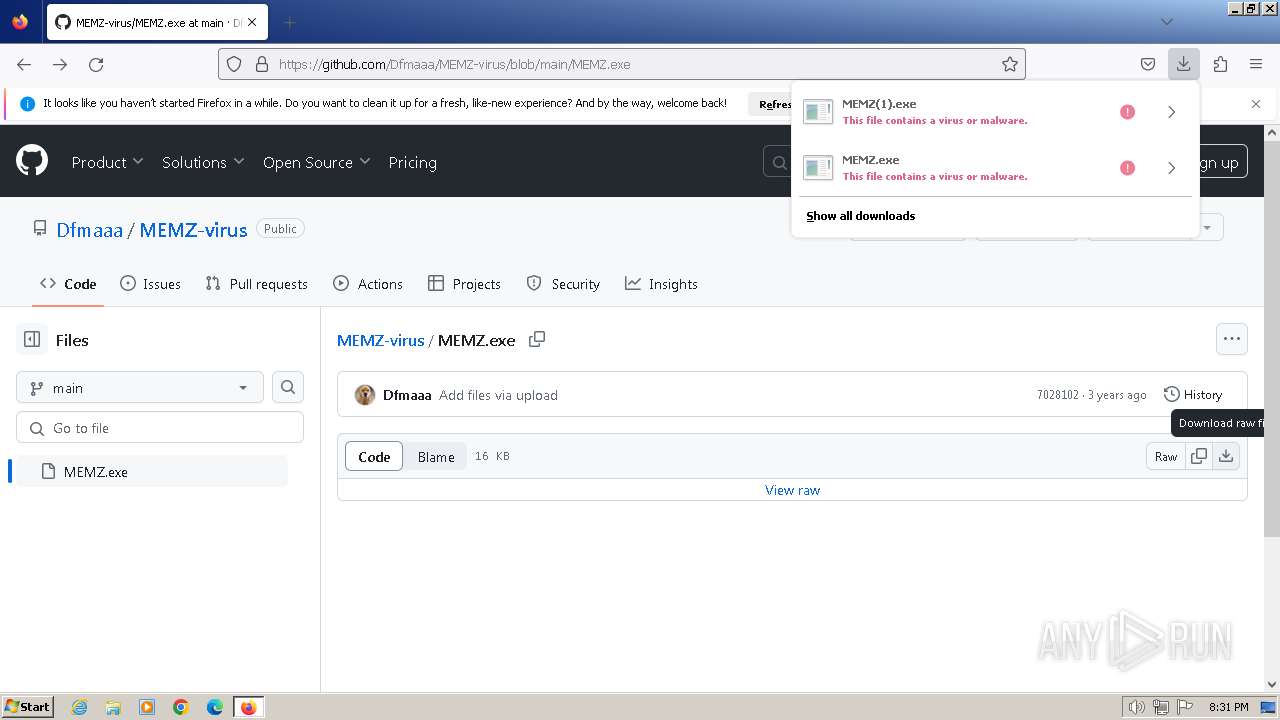
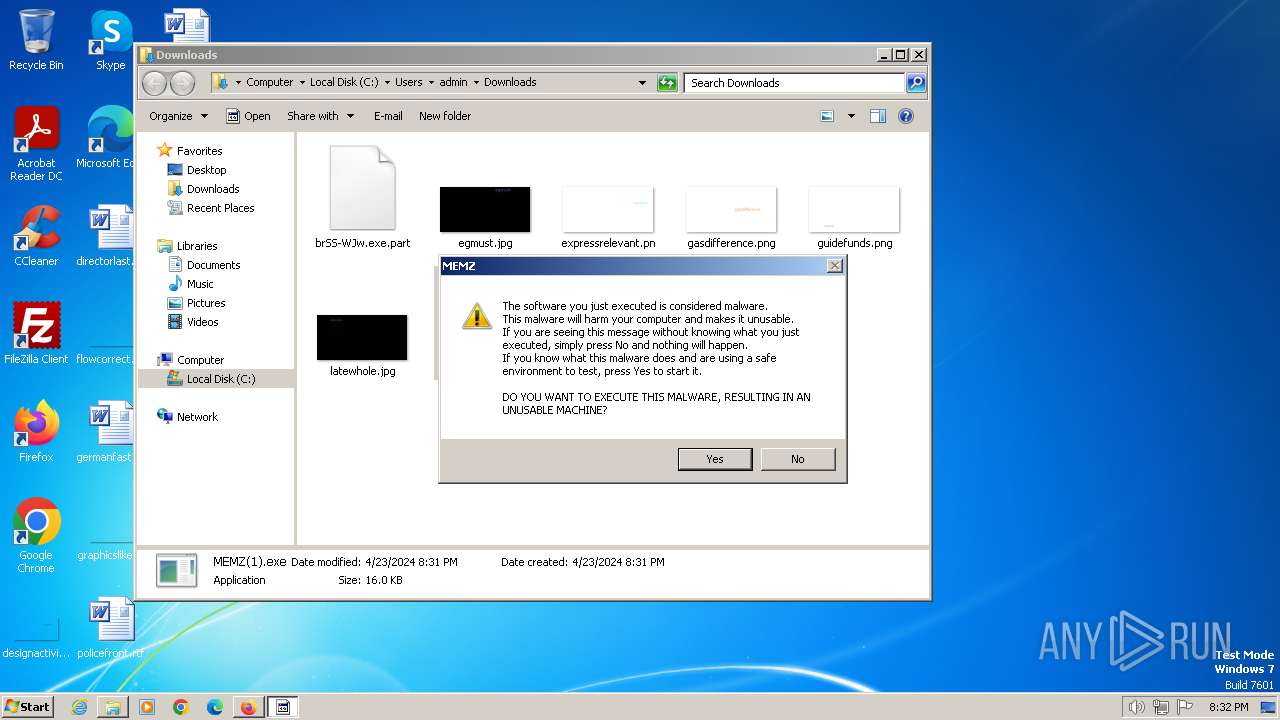
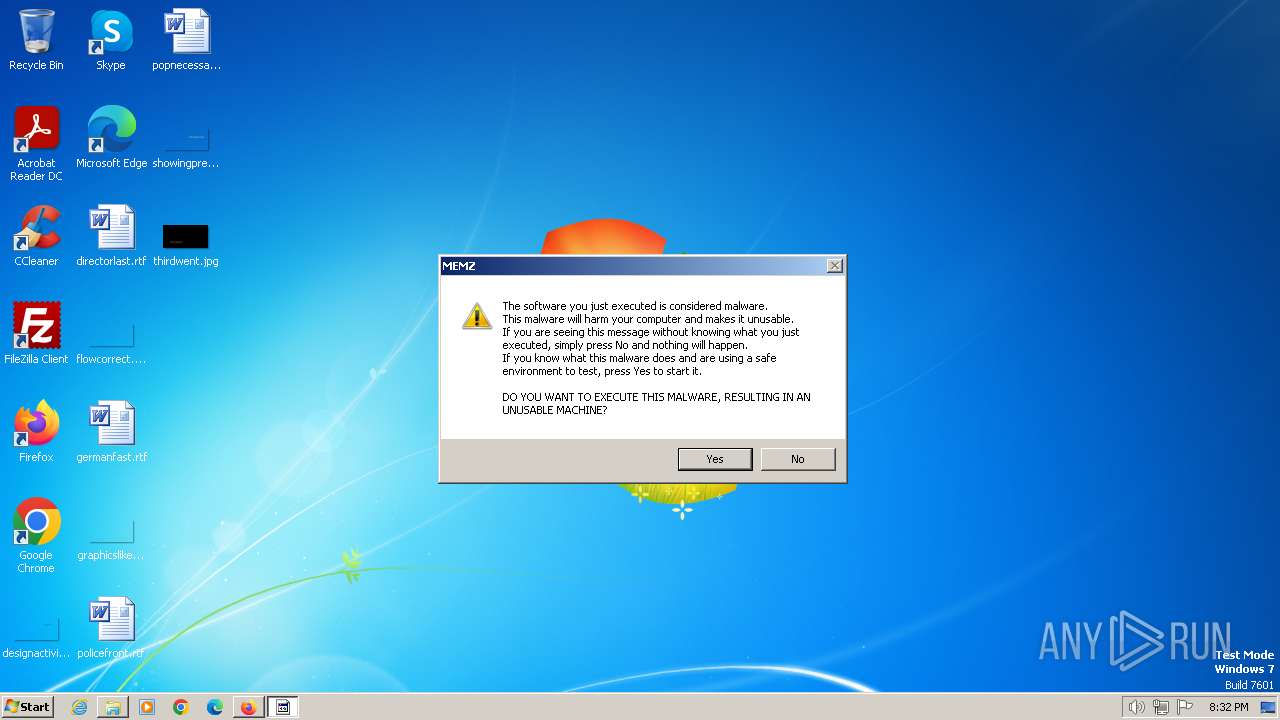
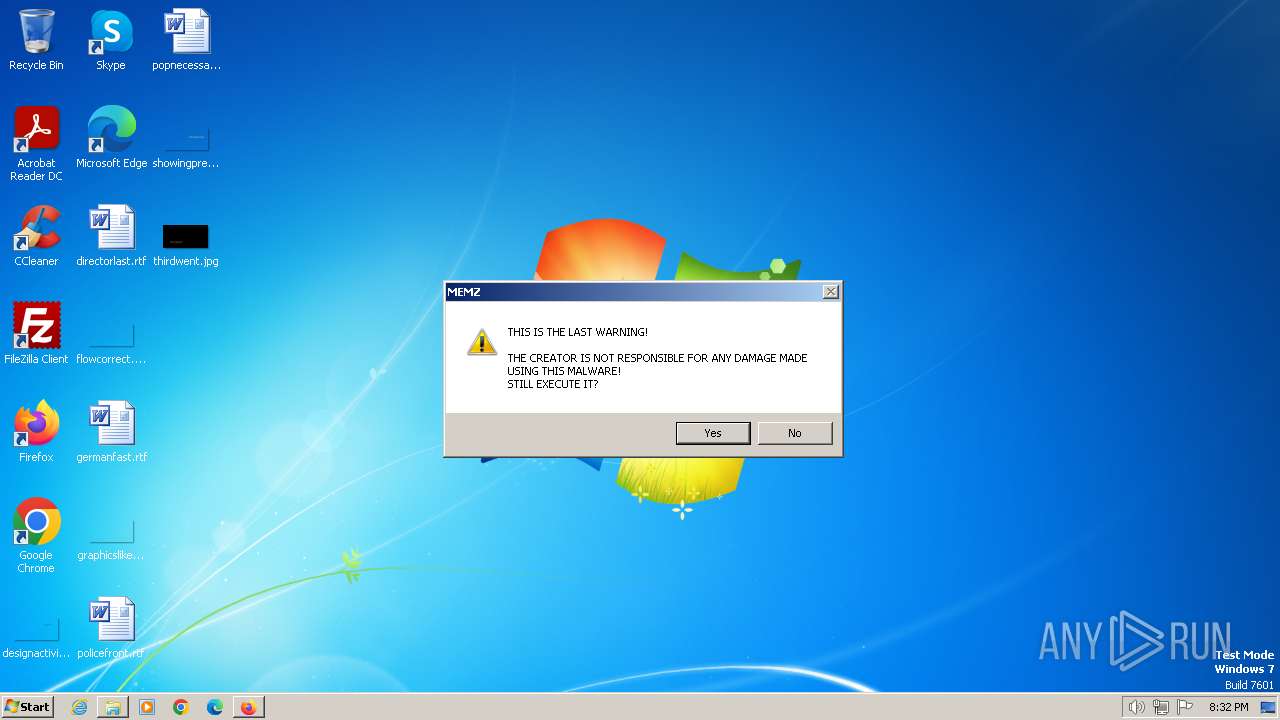
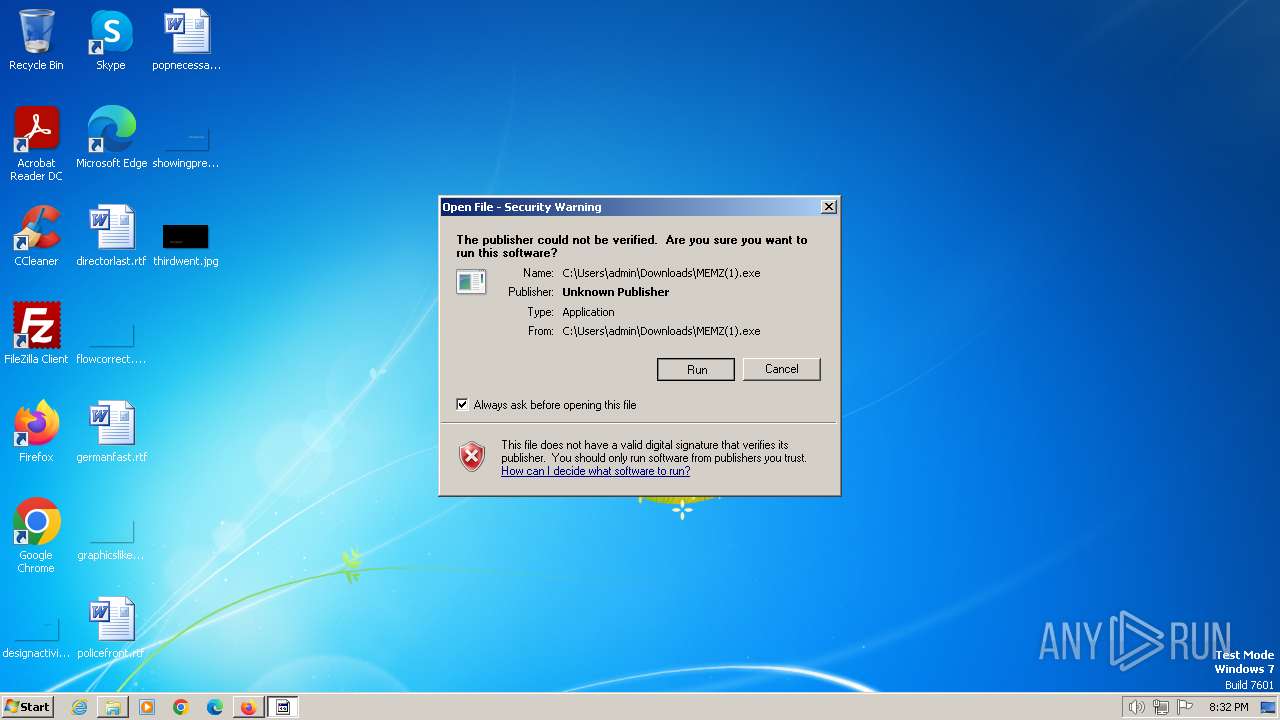
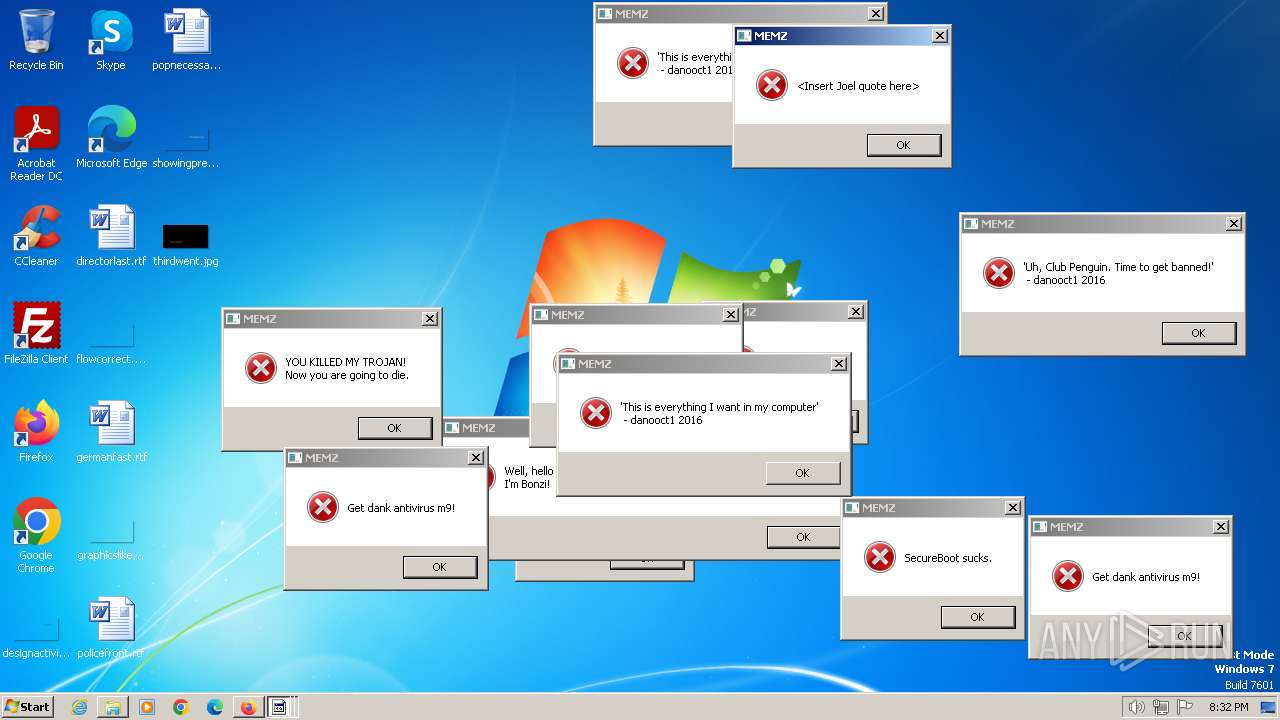
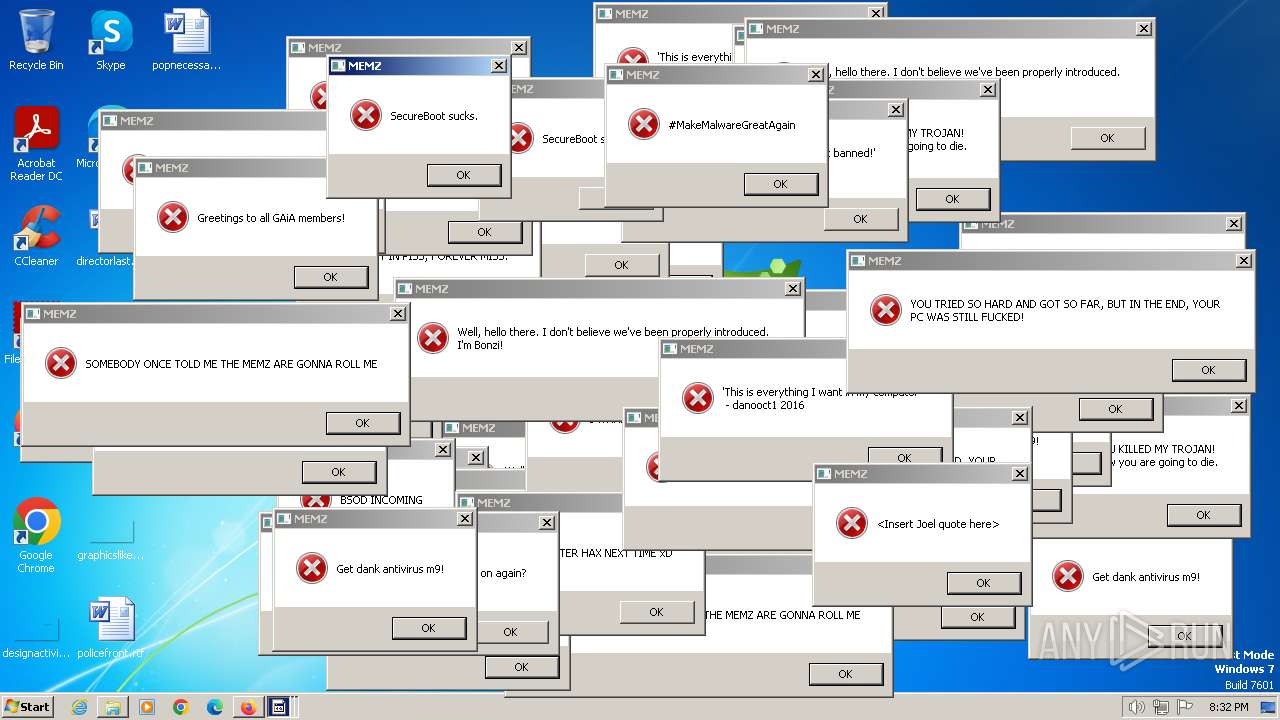
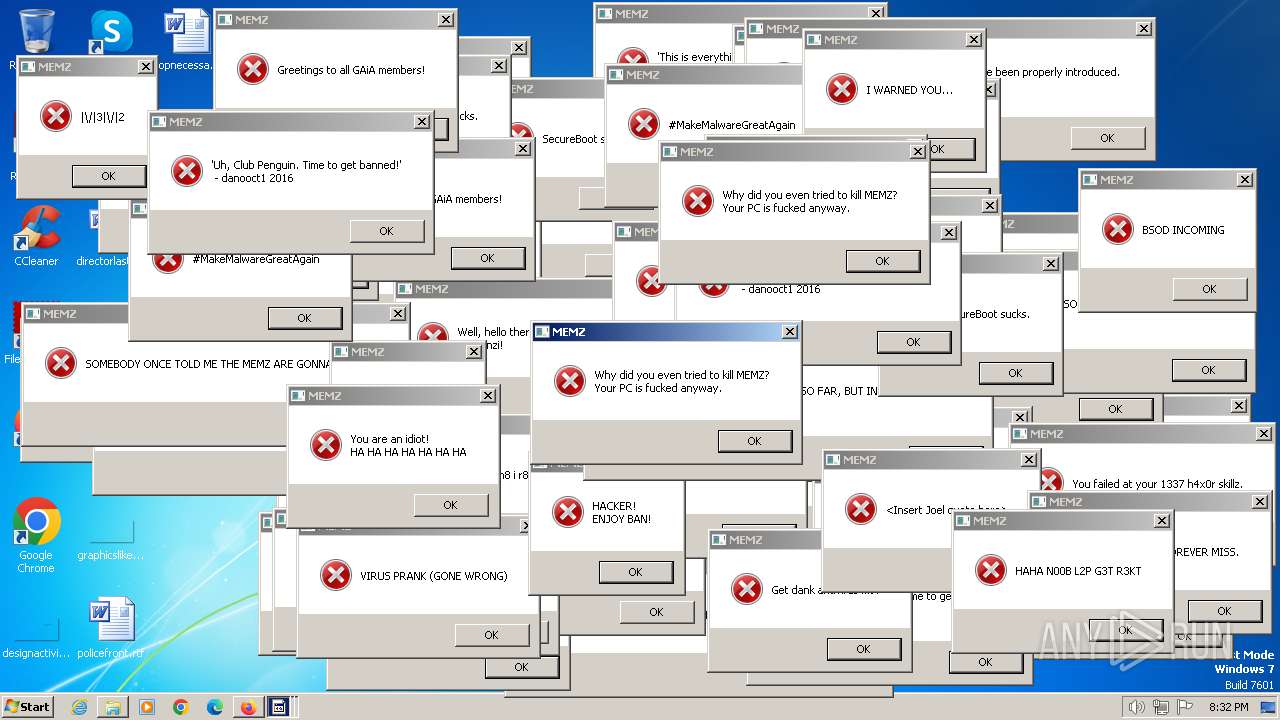
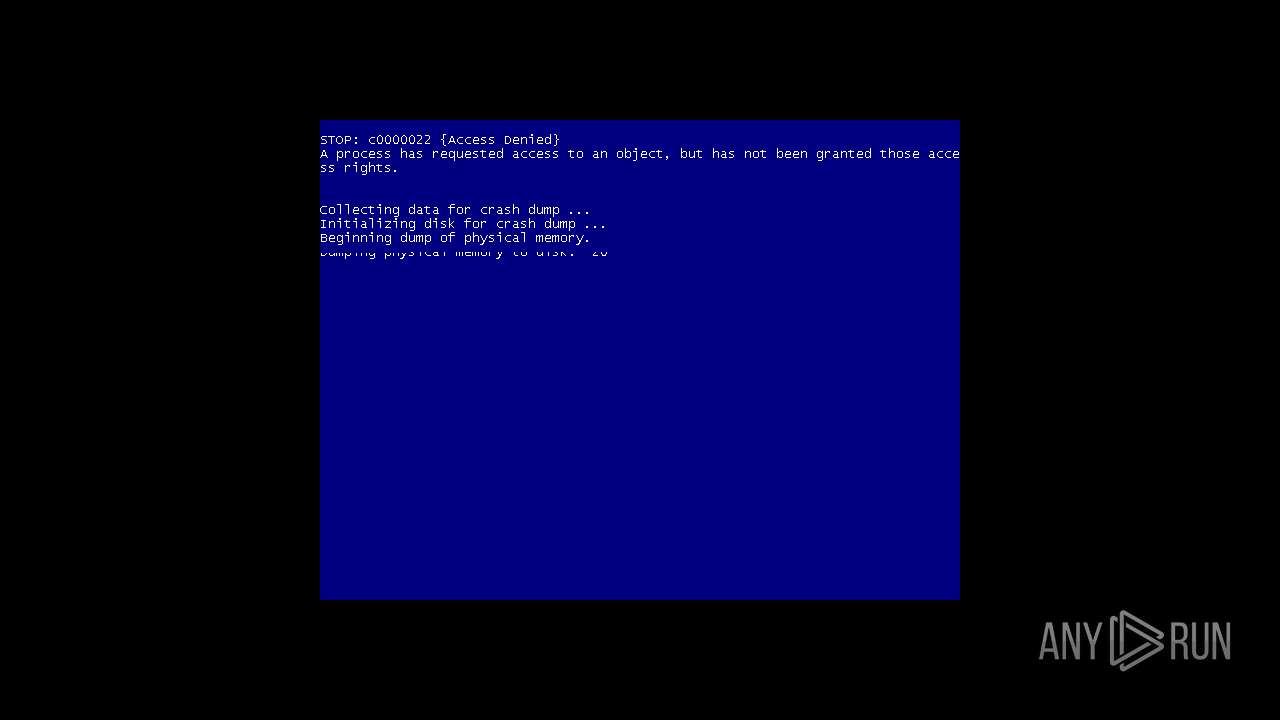
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2024, 19:28:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A513F332DC7C2FE55902EE33831E4BFD |
| SHA1: | D27406F041D957AA385362DBD3AB8767735C1829 |
| SHA256: | B02B9C9C2DD6A0D431FD5CBABA71C9D0D584AEC45312BF866AF666D9F717A081 |
| SSDEEP: | 3:N8DSLIwAEXG7Cj2d6IHQNEgUKb:2OLIwBGeCd6IwlUKb |
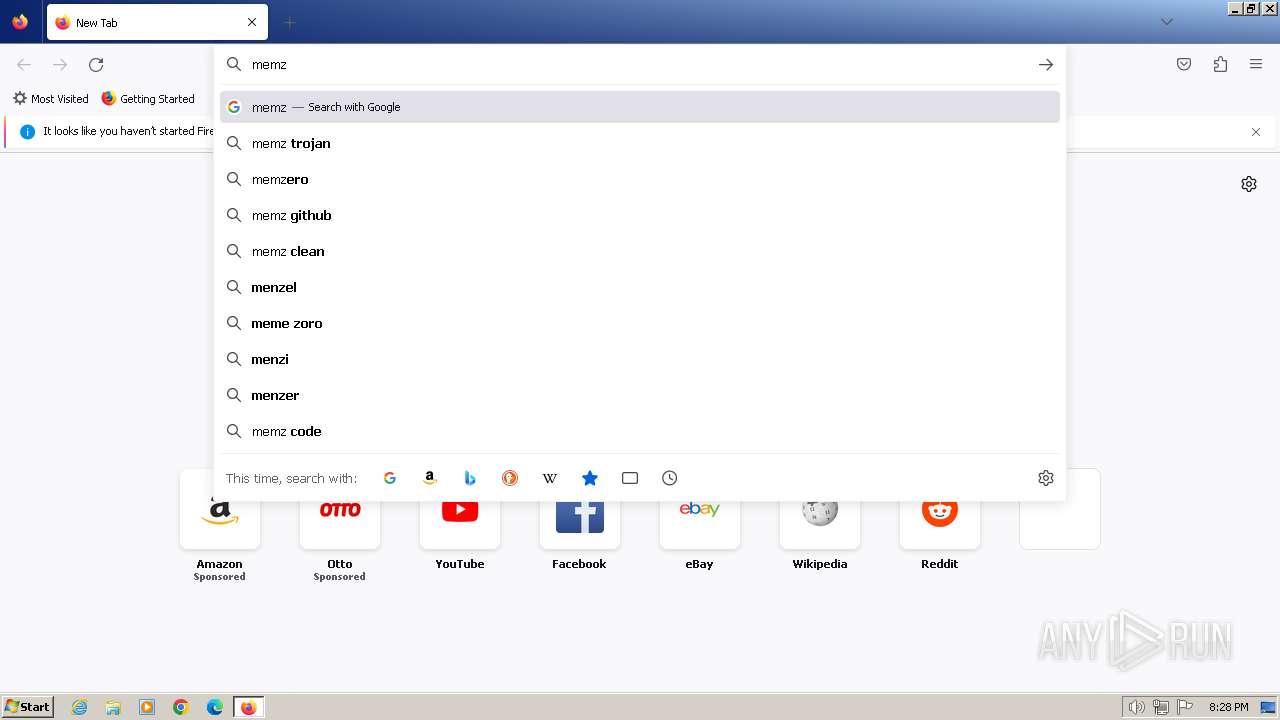
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- MEMZ(1).exe (PID: 1072)
- sipnotify.exe (PID: 1464)
- runonce.exe (PID: 1216)
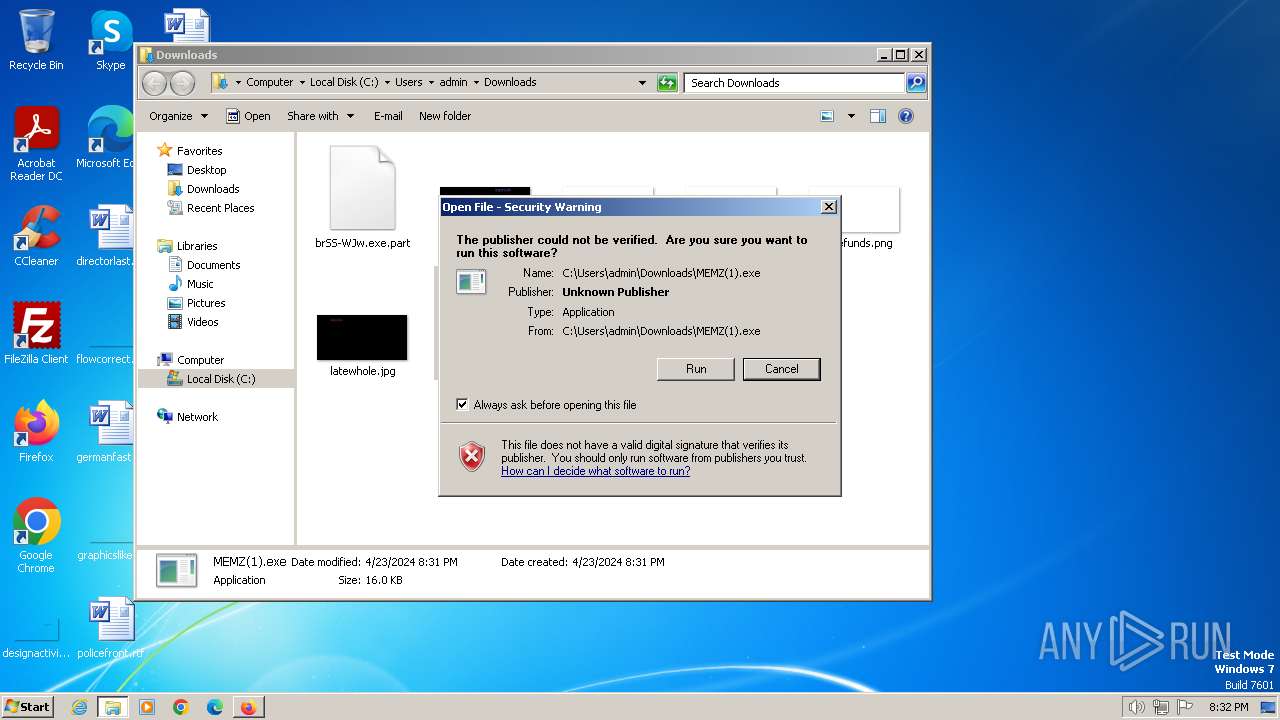
Checks Windows Trust Settings
- MEMZ(1).exe (PID: 1072)
The process executes via Task Scheduler
- sipnotify.exe (PID: 1464)
- ctfmon.exe (PID: 1552)
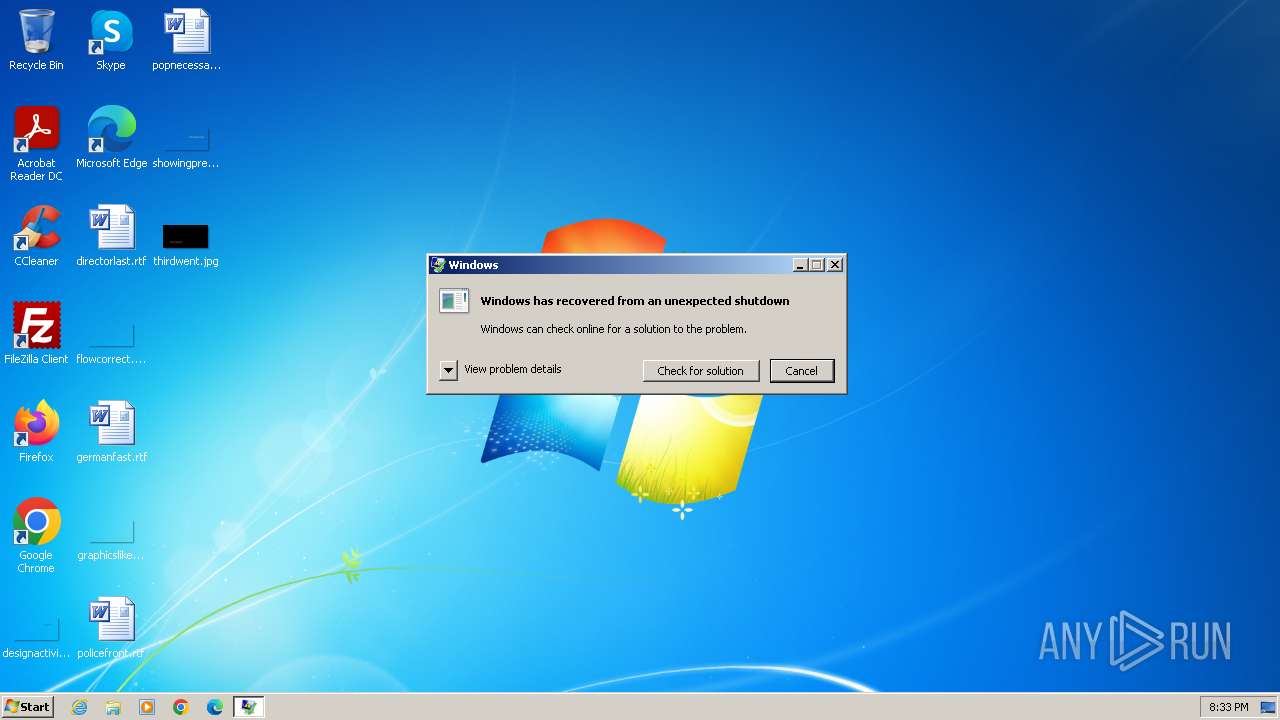
Application launched itself
- WerFault.exe (PID: 2084)
- MEMZ(1).exe (PID: 1072)
Non-standard symbols in registry
- WerFault.exe (PID: 2092)
Reads settings of System Certificates
- sipnotify.exe (PID: 1464)
Reads security settings of Internet Explorer
- MEMZ(1).exe (PID: 1072)
INFO
Application launched itself
- iexplore.exe (PID: 3416)
- firefox.exe (PID: 1112)
- firefox.exe (PID: 2100)
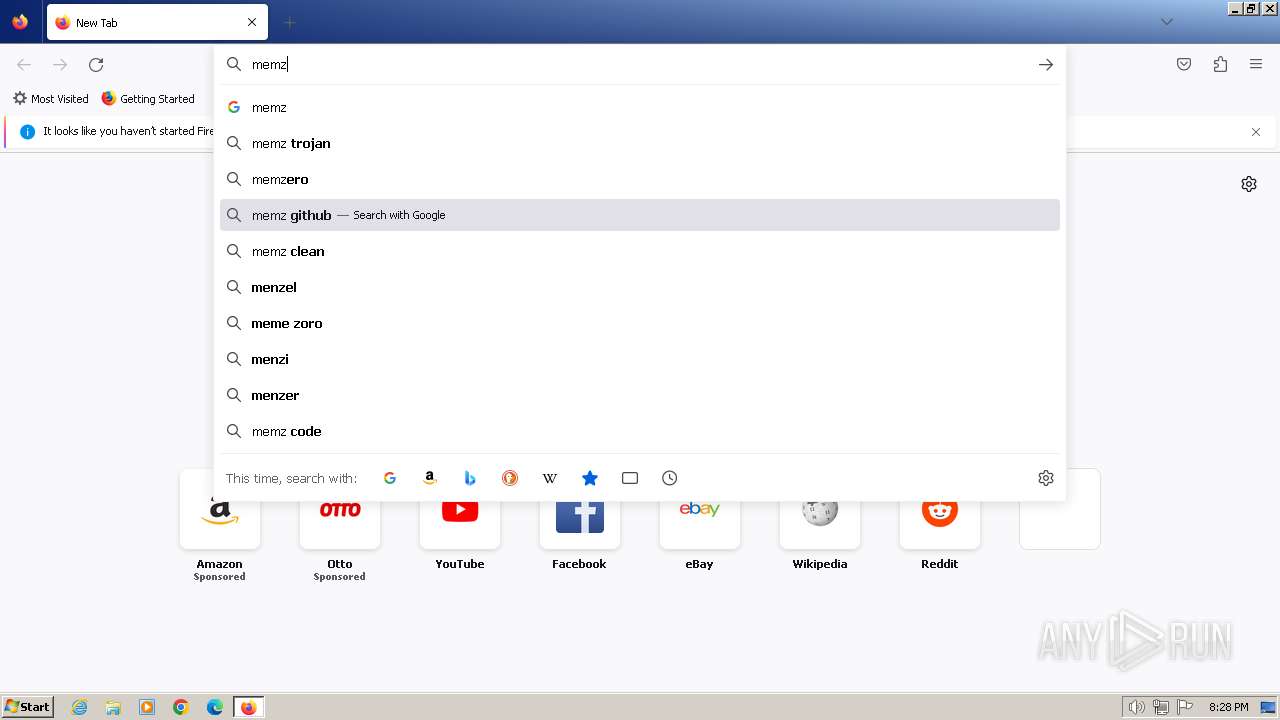
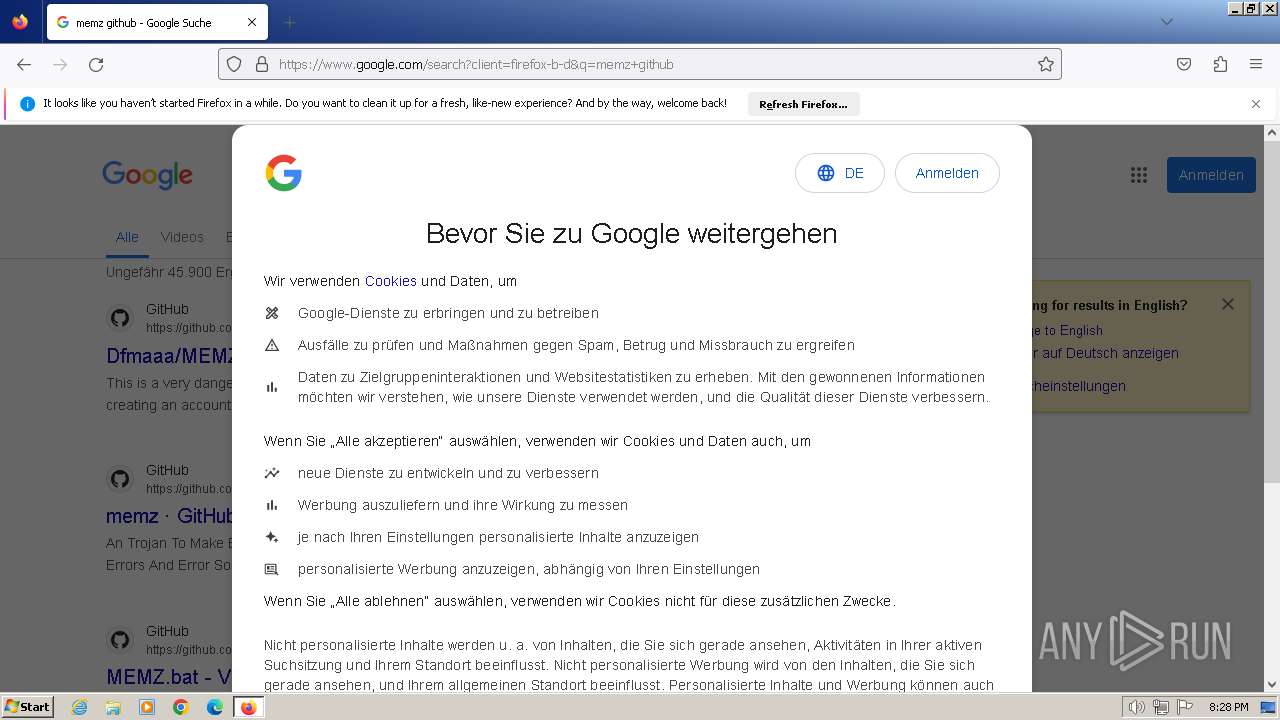
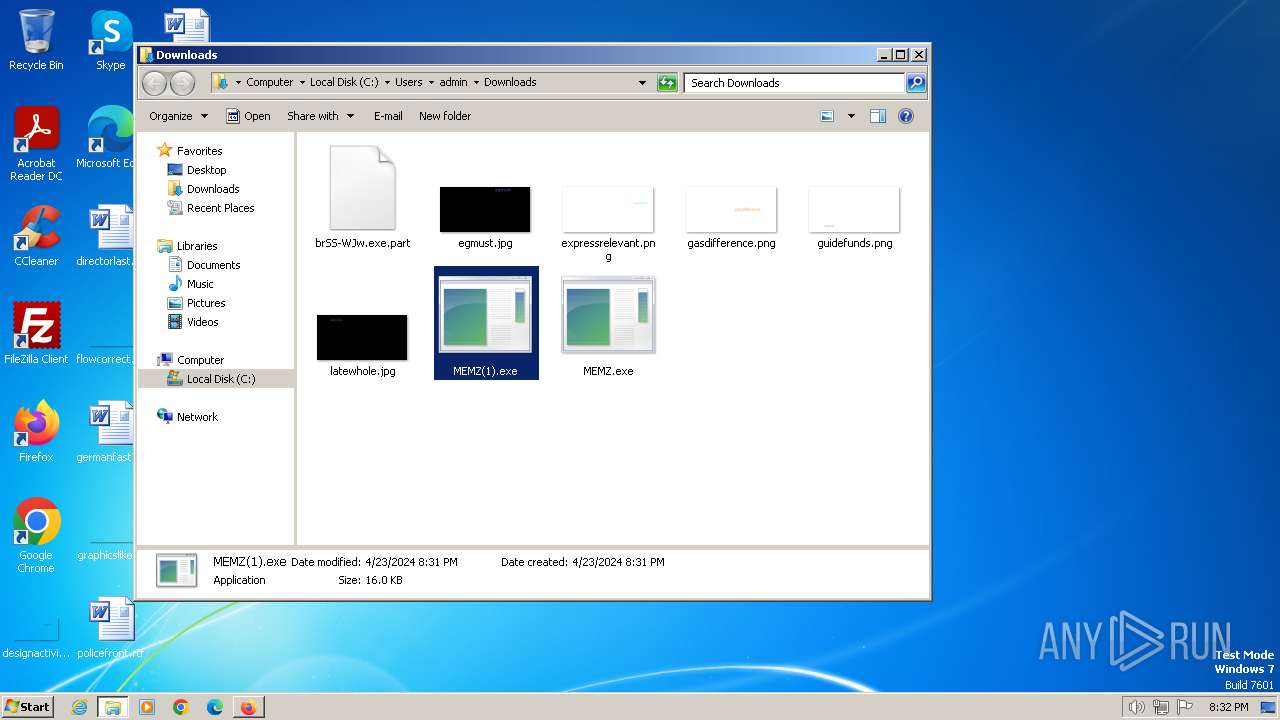
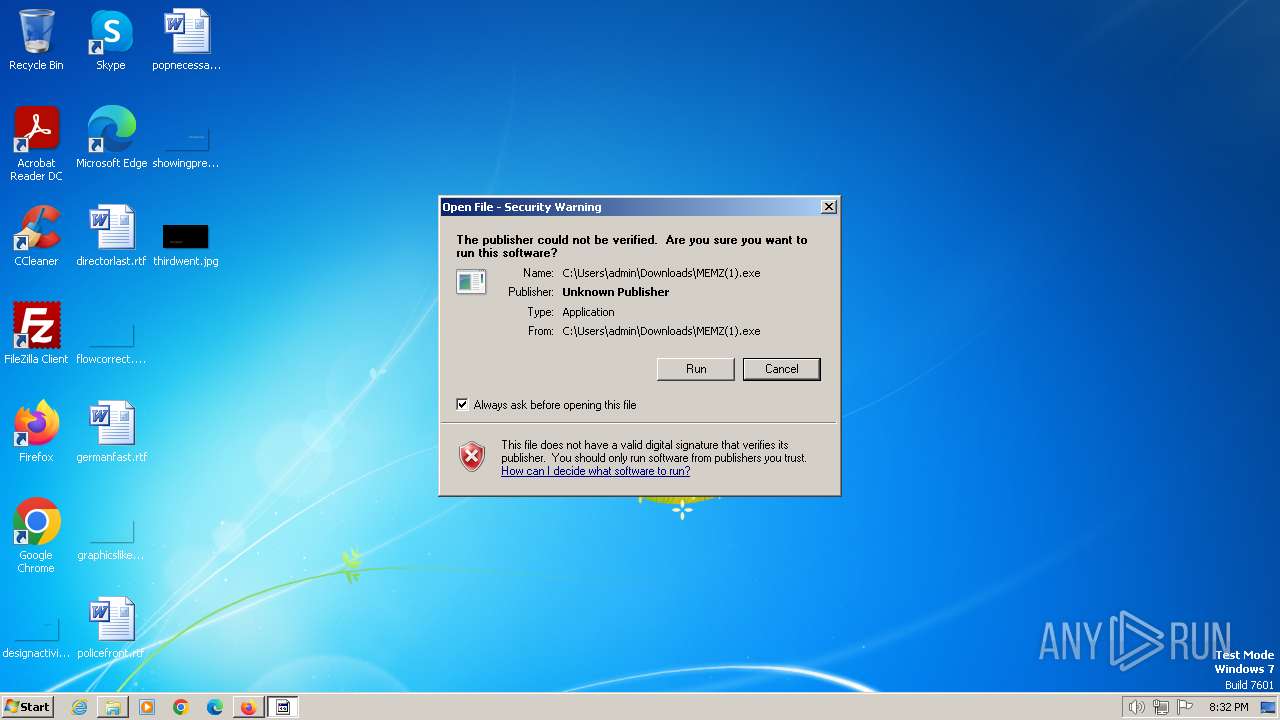
Manual execution by a user
- firefox.exe (PID: 1112)
- wmpnscfg.exe (PID: 2460)
- MEMZ(1).exe (PID: 1072)
- runonce.exe (PID: 1216)
- IMEKLMG.EXE (PID: 2188)
- IMEKLMG.EXE (PID: 2196)
- wmpnscfg.exe (PID: 2524)
- wmpnscfg.exe (PID: 2576)
- wmpnscfg.exe (PID: 2644)
Executable content was dropped or overwritten
- firefox.exe (PID: 2100)
Drops the executable file immediately after the start
- firefox.exe (PID: 2100)
Checks supported languages
- wmpnscfg.exe (PID: 2460)
- MEMZ(1).exe (PID: 1072)
- MEMZ(1).exe (PID: 3068)
- MEMZ(1).exe (PID: 1772)
- MEMZ(1).exe (PID: 3376)
- MEMZ(1).exe (PID: 1380)
- MEMZ(1).exe (PID: 316)
- MEMZ(1).exe (PID: 2640)
- IMEKLMG.EXE (PID: 2196)
- IMEKLMG.EXE (PID: 2188)
- wmpnscfg.exe (PID: 2524)
- wmpnscfg.exe (PID: 2576)
- wmpnscfg.exe (PID: 2644)
Reads the computer name
- wmpnscfg.exe (PID: 2460)
- IMEKLMG.EXE (PID: 2196)
- IMEKLMG.EXE (PID: 2188)
- wmpnscfg.exe (PID: 2524)
- wmpnscfg.exe (PID: 2576)
- wmpnscfg.exe (PID: 2644)
- MEMZ(1).exe (PID: 1072)
The process uses the downloaded file
- firefox.exe (PID: 2100)
- MEMZ(1).exe (PID: 1072)
Reads the machine GUID from the registry
- MEMZ(1).exe (PID: 1072)
- MEMZ(1).exe (PID: 3068)
- MEMZ(1).exe (PID: 316)
- MEMZ(1).exe (PID: 3376)
- MEMZ(1).exe (PID: 1772)
Reads the time zone
- runonce.exe (PID: 1216)
Reads security settings of Internet Explorer
- runonce.exe (PID: 1216)
- sipnotify.exe (PID: 1464)
Create files in a temporary directory
- WerFault.exe (PID: 2092)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2196)
- IMEKLMG.EXE (PID: 2188)
Reads the software policy settings
- sipnotify.exe (PID: 1464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
110
Monitored processes
31
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Users\admin\Downloads\MEMZ(1).exe" /watchdog | C:\Users\admin\Downloads\MEMZ(1).exe | — | MEMZ(1).exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1072 | "C:\Users\admin\Downloads\MEMZ(1).exe" | C:\Users\admin\Downloads\MEMZ(1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1216 | runonce.exe /Explorer | C:\Windows\System32\runonce.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "C:\Users\admin\Downloads\MEMZ(1).exe" /watchdog | C:\Users\admin\Downloads\MEMZ(1).exe | — | MEMZ(1).exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1464 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1552 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1772 | "C:\Users\admin\Downloads\MEMZ(1).exe" /watchdog | C:\Users\admin\Downloads\MEMZ(1).exe | — | MEMZ(1).exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2100.5.1649830359\257086062" -childID 4 -isForBrowser -prefsHandle 3980 -prefMapHandle 3820 -prefsLen 29209 -prefMapSize 244195 -jsInitHandle 868 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {0e6eb66c-2dd9-48a8-ba8f-f912f0c22945} 2100 "\\.\pipe\gecko-crash-server-pipe.2100" 4004 2143a280 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 2084 | "C:\Windows\System32\WerFault.exe" -k -rq | C:\Windows\System32\WerFault.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
43 476
Read events
43 221
Write events
190
Delete events
65
Modification events
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31102388 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31102388 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
7
Suspicious files
160
Text files
46
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:1C71CE18DB4C40197F42E4E161778546 | SHA256:46C225CF4D3110C4FD2DF4105E1C6C662B0982A3F3B7E0ECCCED204704D4C6BF | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F2DDCD2B5F37625B82E81F4976CEE400_CA99D5F5BECF87F64E60B4F8D443638C | binary | |
MD5:4CF3F621F684E9300B46C62E5B81182B | SHA256:8D169280A849BE95F62F835E0F0BFCC08C9EC410C76B5D50068C7ECAFE30BD5A | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:0EE3D2A2CC827A3E5A0109FEEF51633F | SHA256:FB212511BAFB0164E57965D40728E042BA1F2B5C0E5236157ABFA8D3478EDC4B | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F2DDCD2B5F37625B82E81F4976CEE400_CA99D5F5BECF87F64E60B4F8D443638C | der | |
MD5:D32CA08DA12C52AB7450E648A54527A0 | SHA256:4FA8B7FD391FC210195BA022F4F3C74322A0B374302CFAAA4C5375CEC43B4013 | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:AC89A852C2AAA3D389B2D2DD312AD367 | SHA256:0B720E19270C672F9B6E0EC40B468AC49376807DE08A814573FE038779534F45 | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\265C0DEB29181DD1891051371C5F863A_F035812844FEE93DCDCC1CD3A7F24400 | binary | |
MD5:EB37586B56180756E8F7562993CC319C | SHA256:07C6E3E2B32704C88CEC03F9E56CB8B2DFBCA473F6AEADBECED92D79BACB30DD | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\43SD4M7C.txt | text | |
MD5:362C62ACDB2CB227204909C051C64F0C | SHA256:D66EBA426C6E12FB7AE569B00282C510ADE4D09EAB7AC29CCC0CE3E28D1F1219 | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:C19AE50F8BC48D16421382ACDB958B64 | SHA256:DC41C90F633B4BDB489663C6B82DE3B06F4CF5A87029820A0F63A566BBBCC946 | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:807497F8020F3E4691C145BD1B276921 | SHA256:821B27805114F57856E6C774176933F8FBEF5195F8876753075974D9DD501567 | |||
| 2100 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
114
DNS requests
188
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3384 | iexplore.exe | GET | 304 | 173.222.108.243:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7f68a02ba6df2d36 | unknown | — | — | unknown |
3384 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFBwRbDjnKinCvbzPd%2BGMUY%3D | unknown | — | — | unknown |
3384 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | — | — | unknown |
3384 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEB3avVfM5rkCEm75%2BCxCBKE%3D | unknown | — | — | unknown |
3384 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD0crTFWCTVIAm4ZwPnmLpo | unknown | — | — | unknown |
3416 | iexplore.exe | GET | 304 | 173.222.108.249:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3ed6d2b4a8fbdc40 | unknown | — | — | unknown |
3416 | iexplore.exe | GET | 304 | 173.222.108.249:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ccd3f16cad753a85 | unknown | — | — | unknown |
2100 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | unknown |
3416 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | — | — | unknown |
2100 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3384 | iexplore.exe | 142.250.186.68:443 | www.google.com | GOOGLE | US | whitelisted |
3384 | iexplore.exe | 173.222.108.249:80 | ctldl.windowsupdate.com | Akamai International B.V. | CH | unknown |
3384 | iexplore.exe | 173.222.108.243:80 | ctldl.windowsupdate.com | Akamai International B.V. | CH | unknown |
3384 | iexplore.exe | 142.250.185.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3384 | iexplore.exe | 172.217.16.206:443 | consent.google.com | GOOGLE | US | whitelisted |
3384 | iexplore.exe | 172.217.18.3:443 | www.gstatic.com | GOOGLE | US | whitelisted |
3416 | iexplore.exe | 142.250.186.68:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
consent.google.com |
| shared |
www.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |