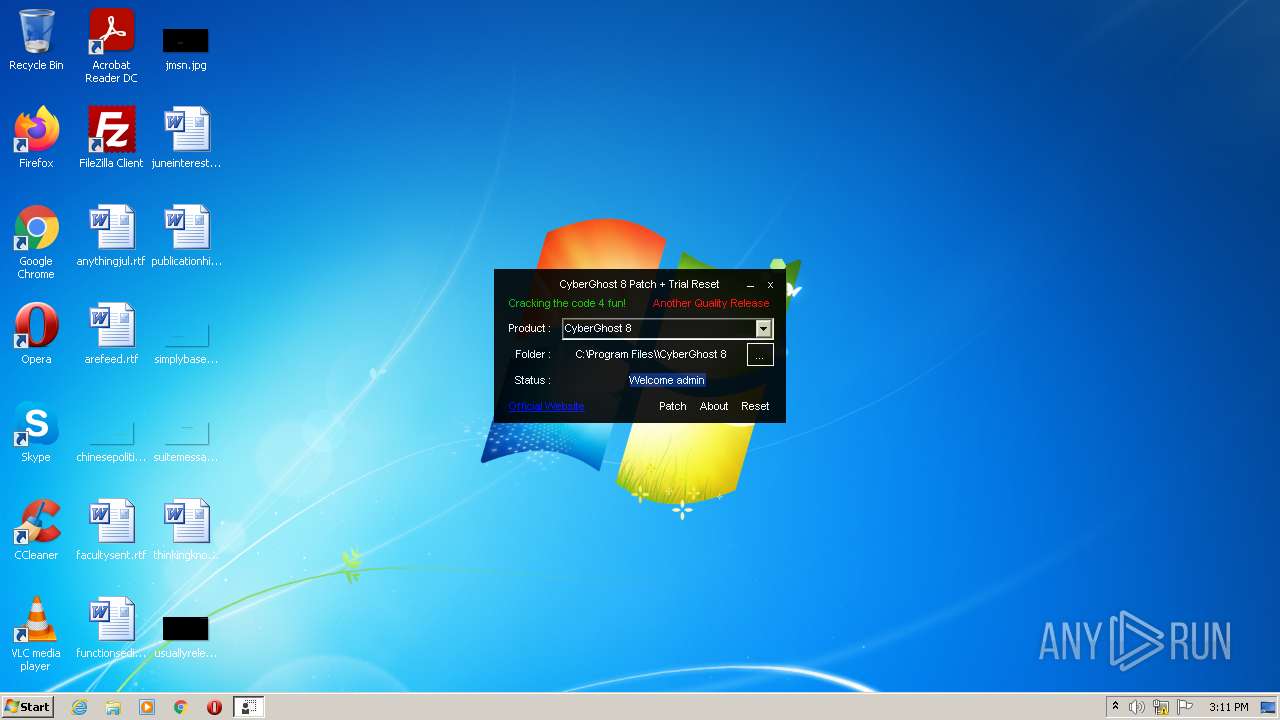
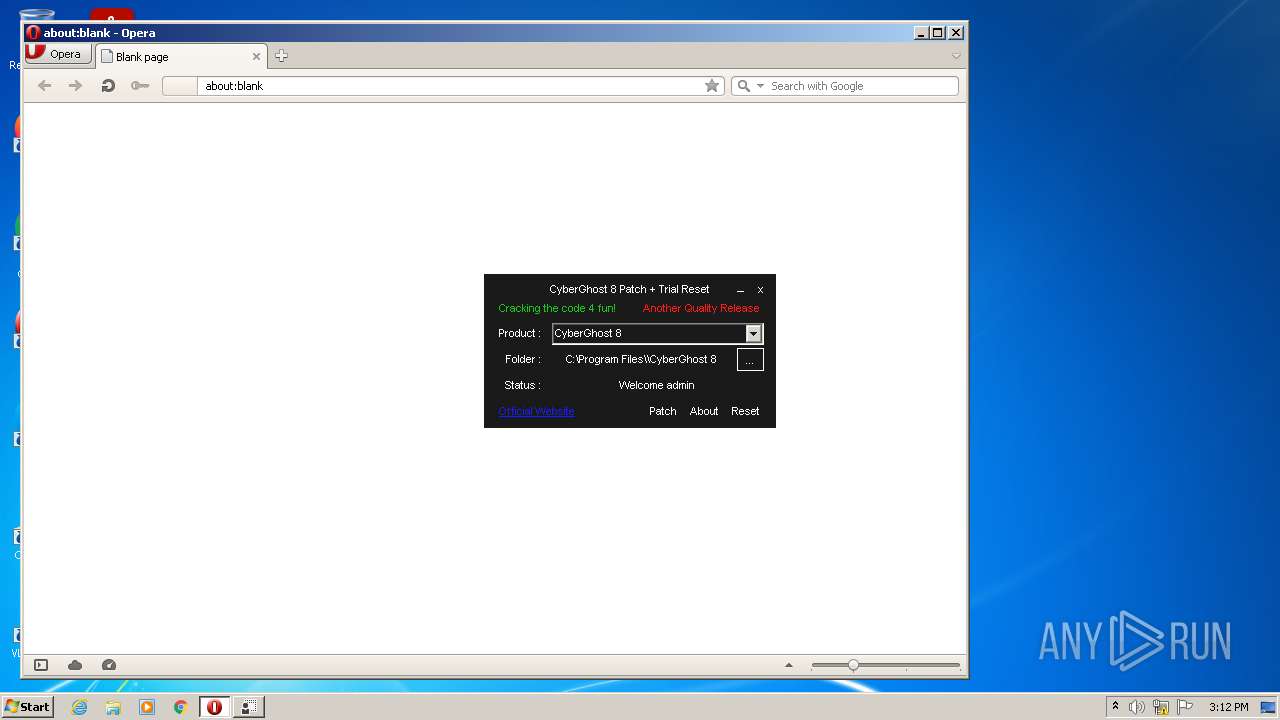
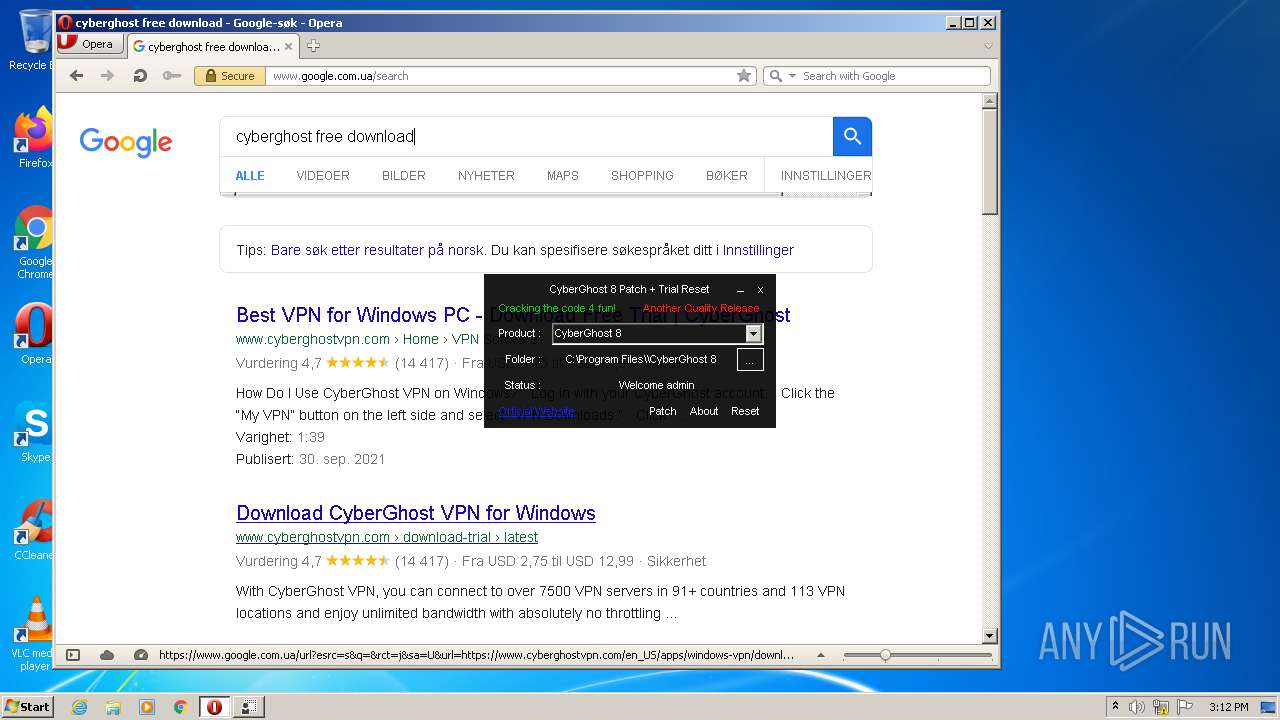
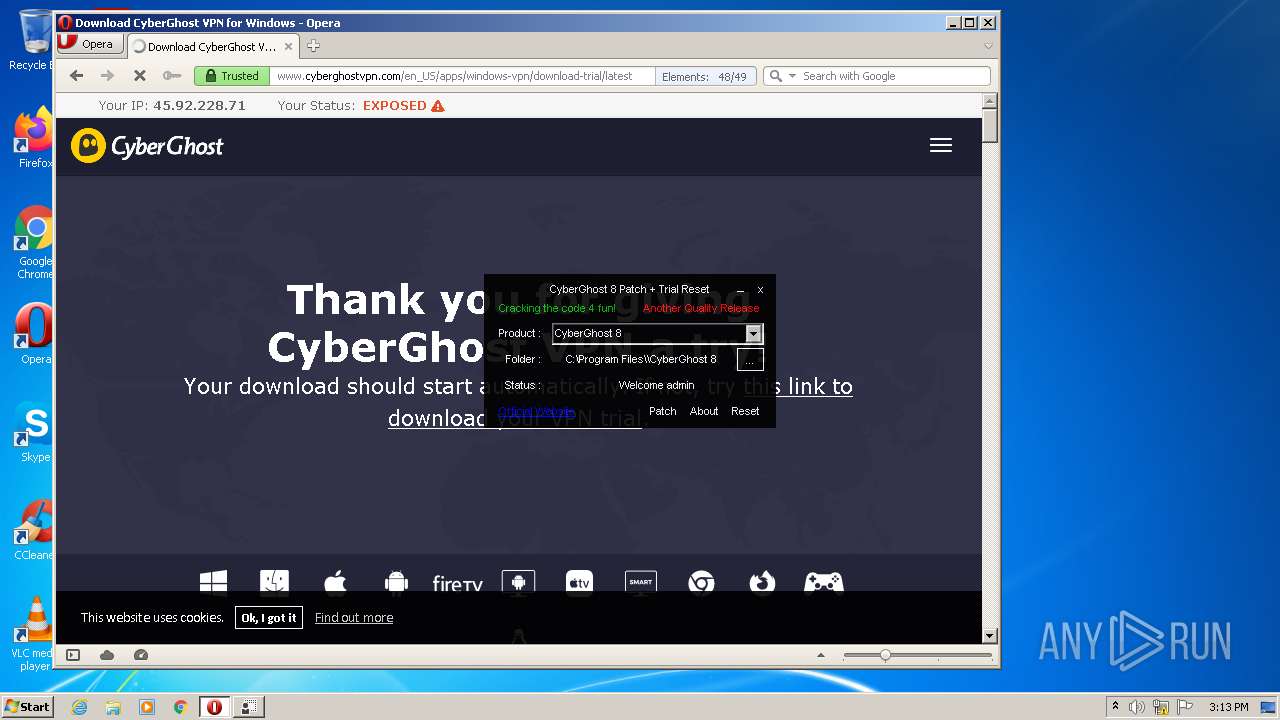
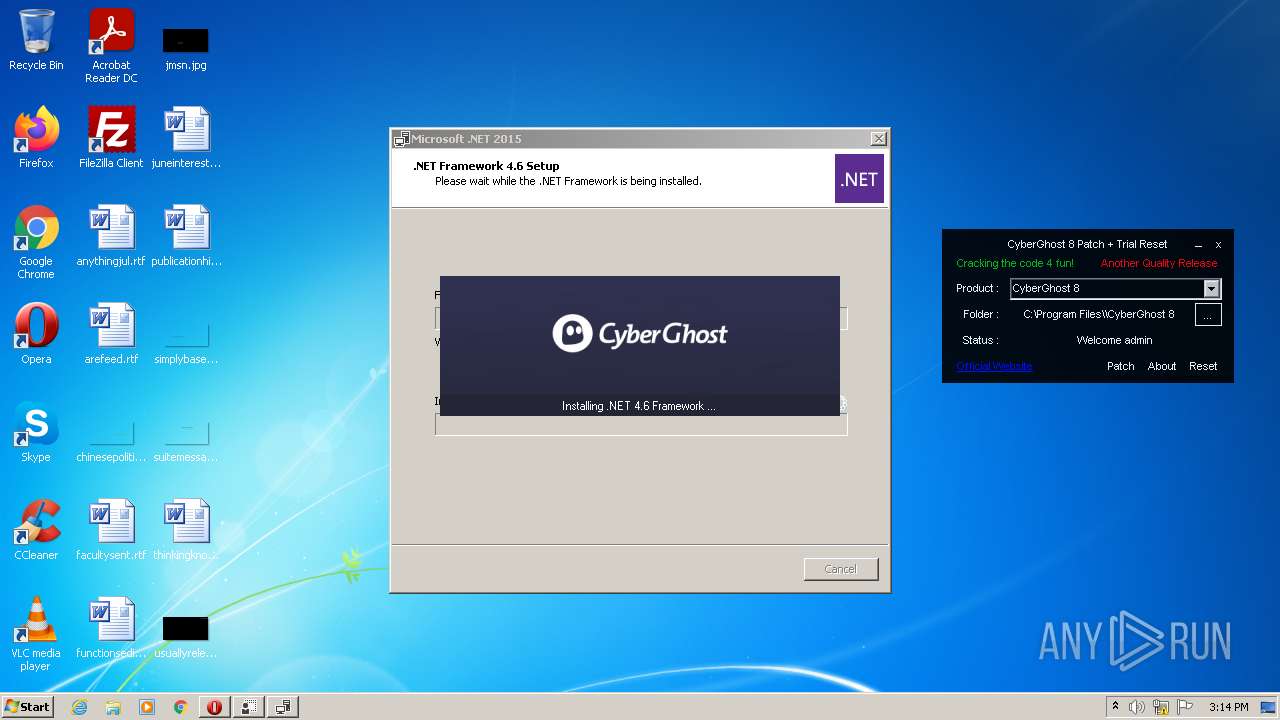
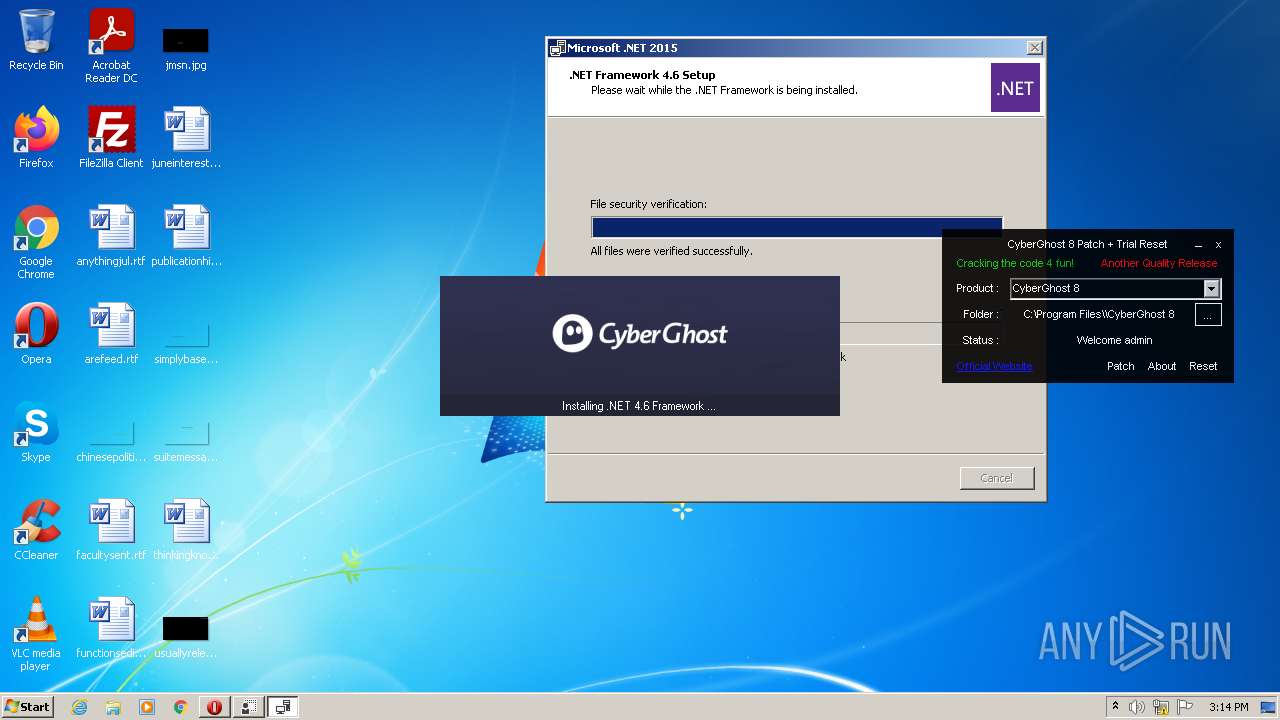
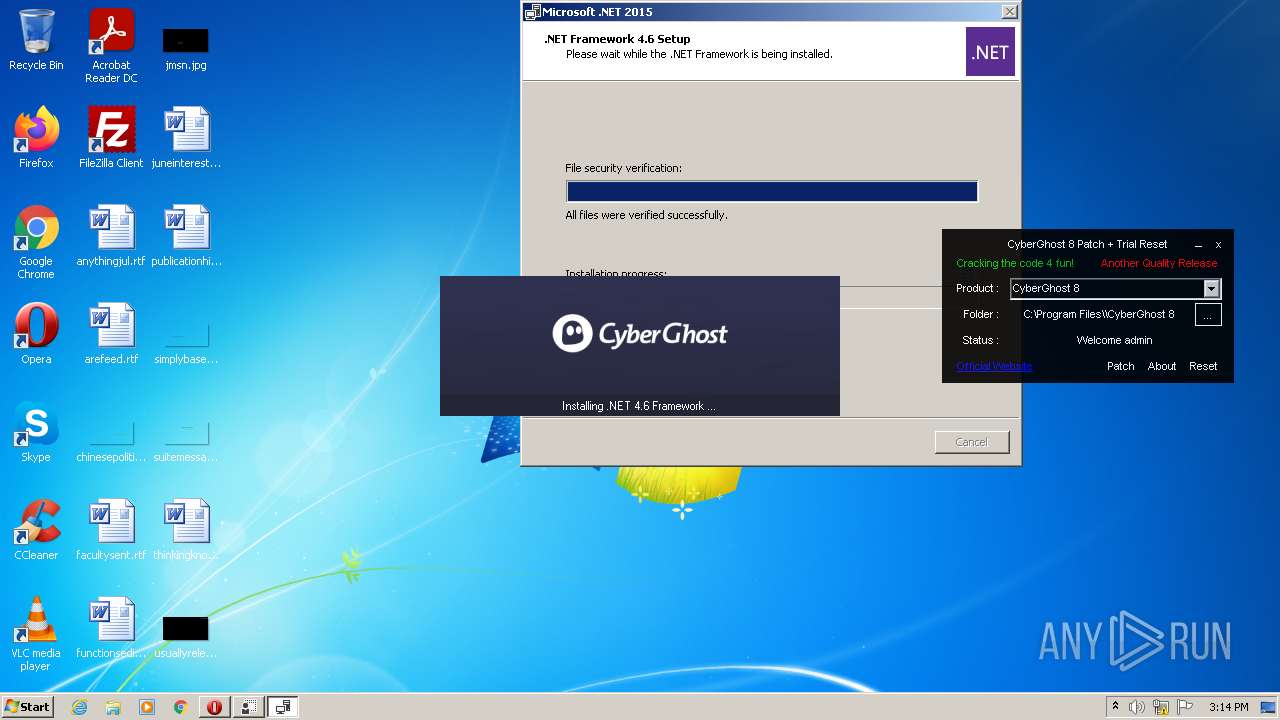
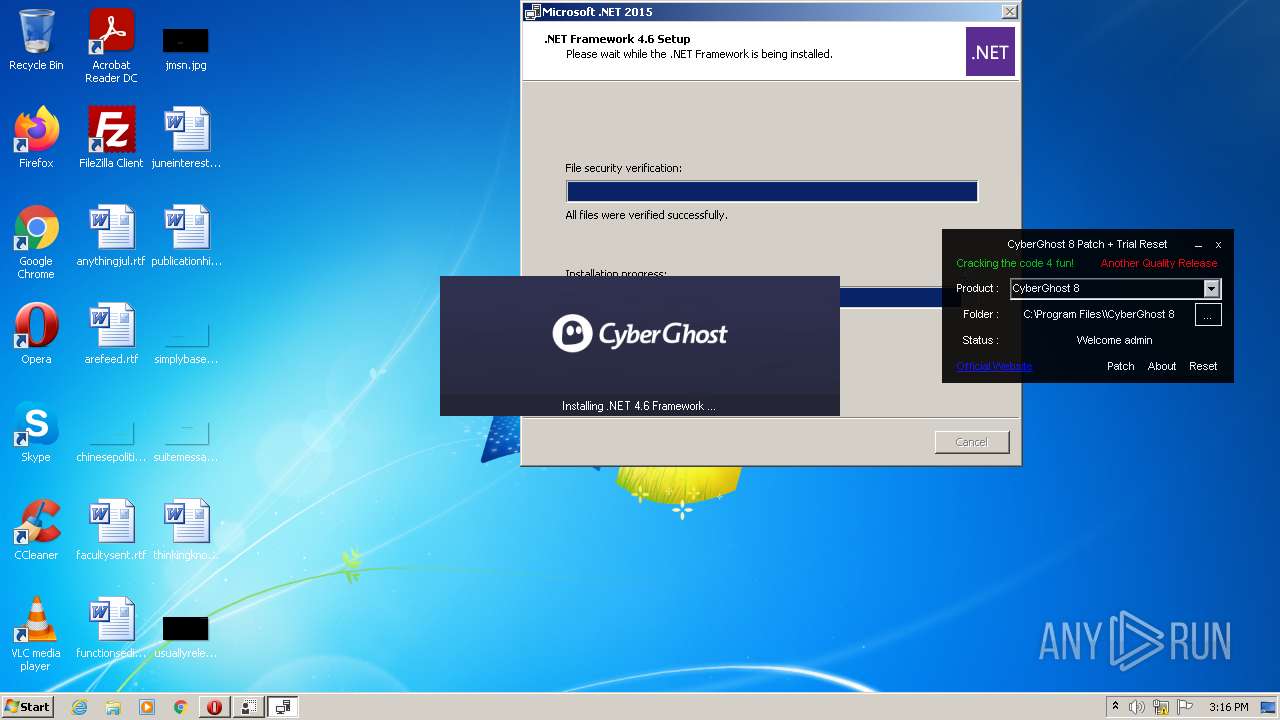
| File name: | CyberGhost 8 Patch + Trial Reset.exe |
| Full analysis: | https://app.any.run/tasks/dd716939-034d-4ad7-bc3b-3e7d4fd57c28 |
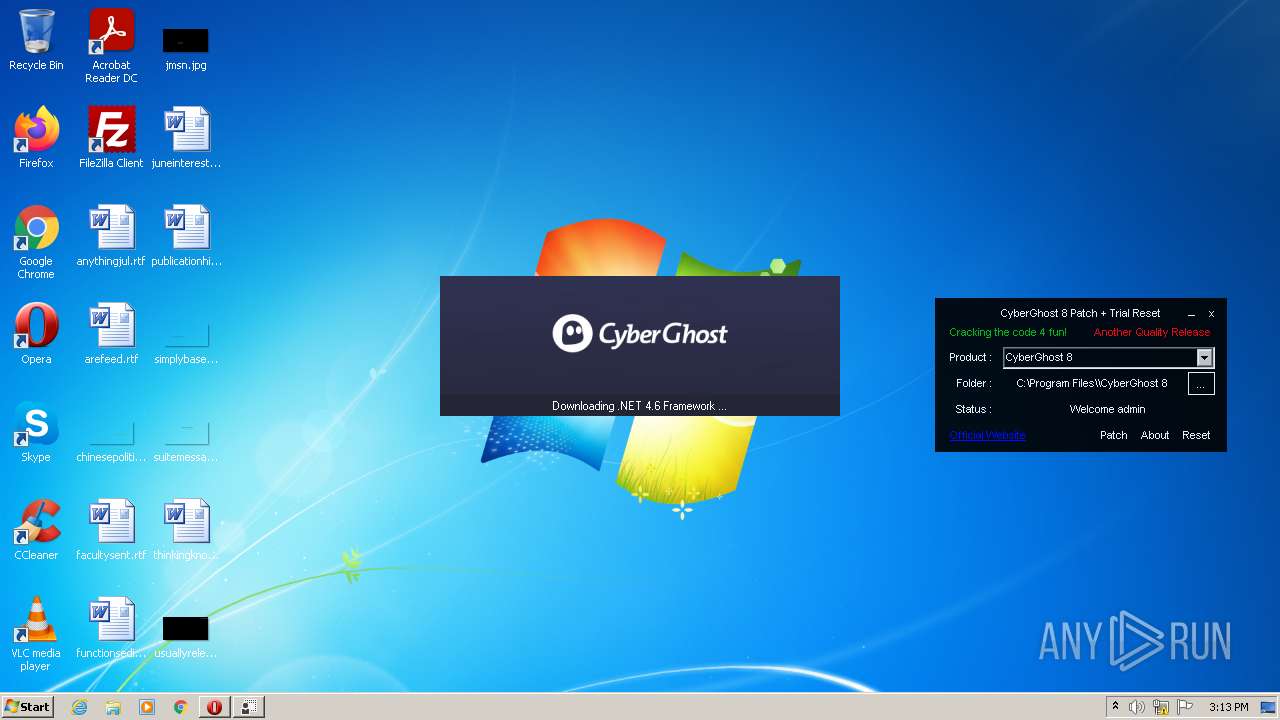
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2022, 15:11:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 5D395AAD19EF5AA9BE21B9DB5084A52E |
| SHA1: | 69773713F8F2BEA1A9BDA4380225E411BD82EACC |
| SHA256: | B01F9AA661F72F76FB0BD352DF82AD9A5CDA530254678D2AFE69E86B829443BD |
| SSDEEP: | 12288:iAZSnG3gueOCrPhYjIXPHtGJ76X+vk3hbT:7ZQjuWrZ+GNqFk1 |
MALICIOUS
Application was dropped or rewritten from another process
- cgsetup_en_.exe (PID: 3624)
- cgsetup_en_.exe (PID: 3644)
- Setup.exe (PID: 444)
- SetupUtility.exe (PID: 448)
- SetupUtility.exe (PID: 3660)
- ServiceModelReg.exe (PID: 3468)
- aspnet_regiis.exe (PID: 3904)
- regtlibv12.exe (PID: 2680)
Changes settings of System certificates
- cgsetup_en_.exe (PID: 3644)
Loads dropped or rewritten executable
- Setup.exe (PID: 444)
- MsiExec.exe (PID: 3916)
- MsiExec.exe (PID: 3048)
- CyberGhost 8 Patch + Trial Reset.exe (PID: 3800)
- cgsetup_en_.exe (PID: 3644)
- msiexec.exe (PID: 2100)
- svchost.exe (PID: 2012)
- aspnet_regiis.exe (PID: 3904)
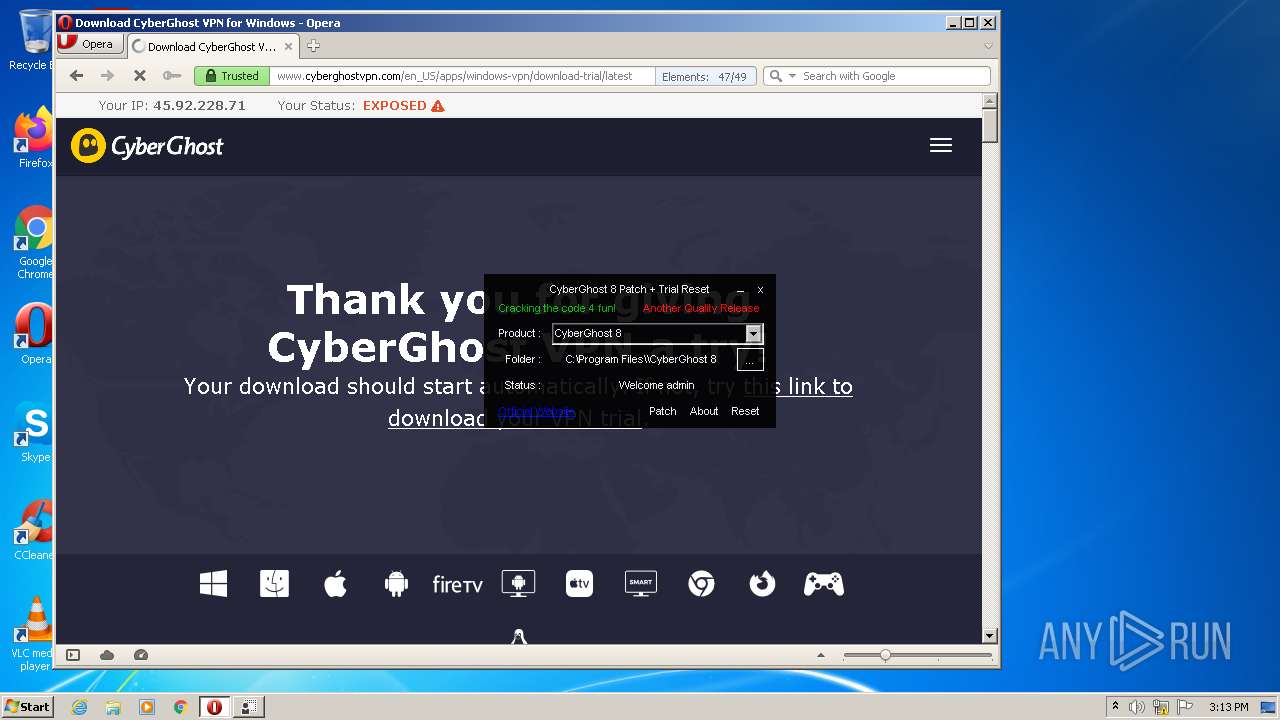
Actions looks like stealing of personal data
- tmp260.tmp.exe (PID: 3520)
Drops executable file immediately after starts
- msiexec.exe (PID: 2100)
Changes the autorun value in the registry
- msiexec.exe (PID: 2100)
SUSPICIOUS
Checks supported languages
- CyberGhost 8 Patch + Trial Reset.exe (PID: 3800)
- cgsetup_en_.exe (PID: 3644)
- tmp260.tmp.exe (PID: 3520)
- Setup.exe (PID: 444)
- SetupUtility.exe (PID: 3660)
- SetupUtility.exe (PID: 448)
- ServiceModelReg.exe (PID: 3468)
- mofcomp.exe (PID: 2168)
- mofcomp.exe (PID: 3592)
- regtlibv12.exe (PID: 2680)
- aspnet_regiis.exe (PID: 3904)
- mofcomp.exe (PID: 2296)
Reads the computer name
- CyberGhost 8 Patch + Trial Reset.exe (PID: 3800)
- cgsetup_en_.exe (PID: 3644)
- tmp260.tmp.exe (PID: 3520)
- Setup.exe (PID: 444)
- SetupUtility.exe (PID: 448)
- SetupUtility.exe (PID: 3660)
- ServiceModelReg.exe (PID: 3468)
- mofcomp.exe (PID: 2168)
- mofcomp.exe (PID: 3592)
- aspnet_regiis.exe (PID: 3904)
- mofcomp.exe (PID: 2296)
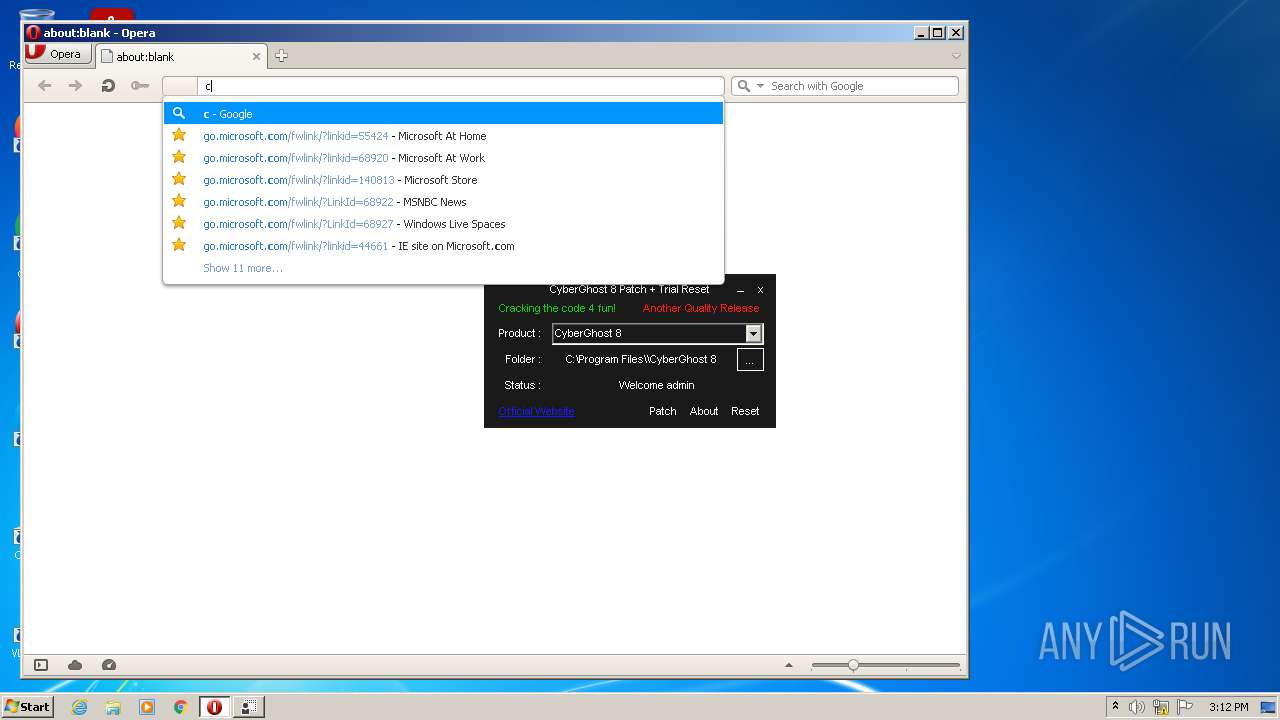
Reads internet explorer settings
- CyberGhost 8 Patch + Trial Reset.exe (PID: 3800)
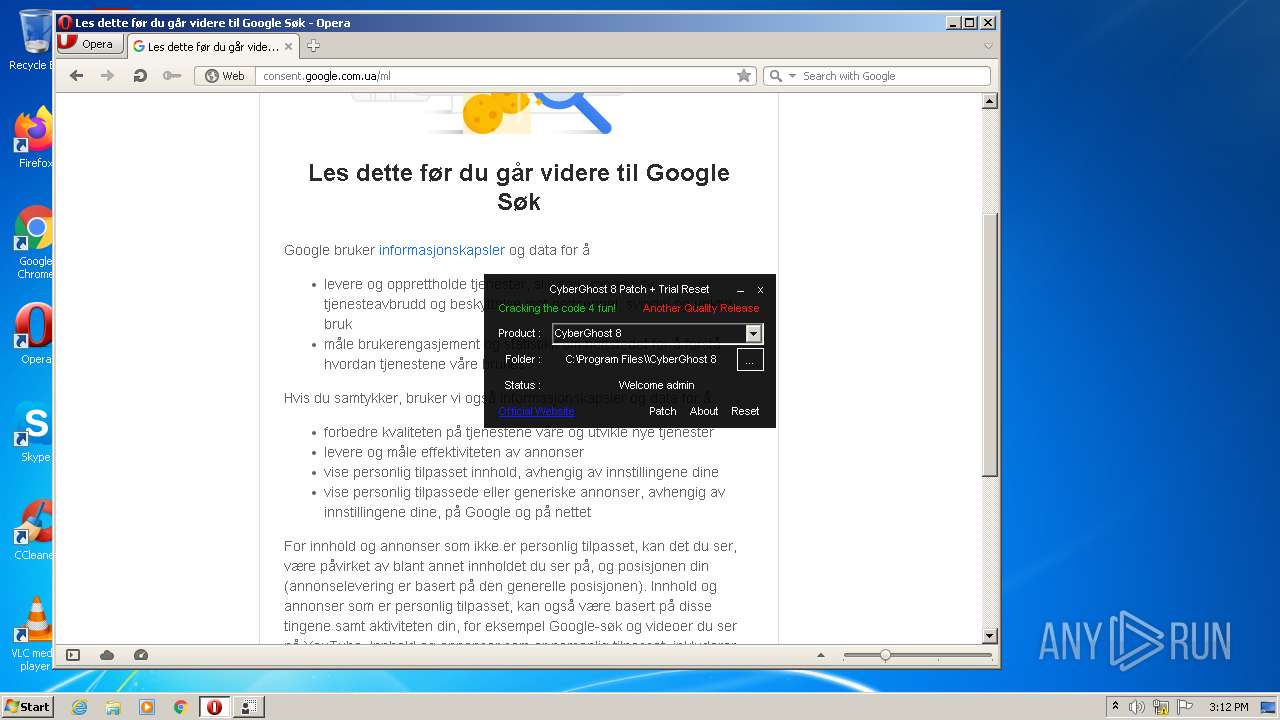
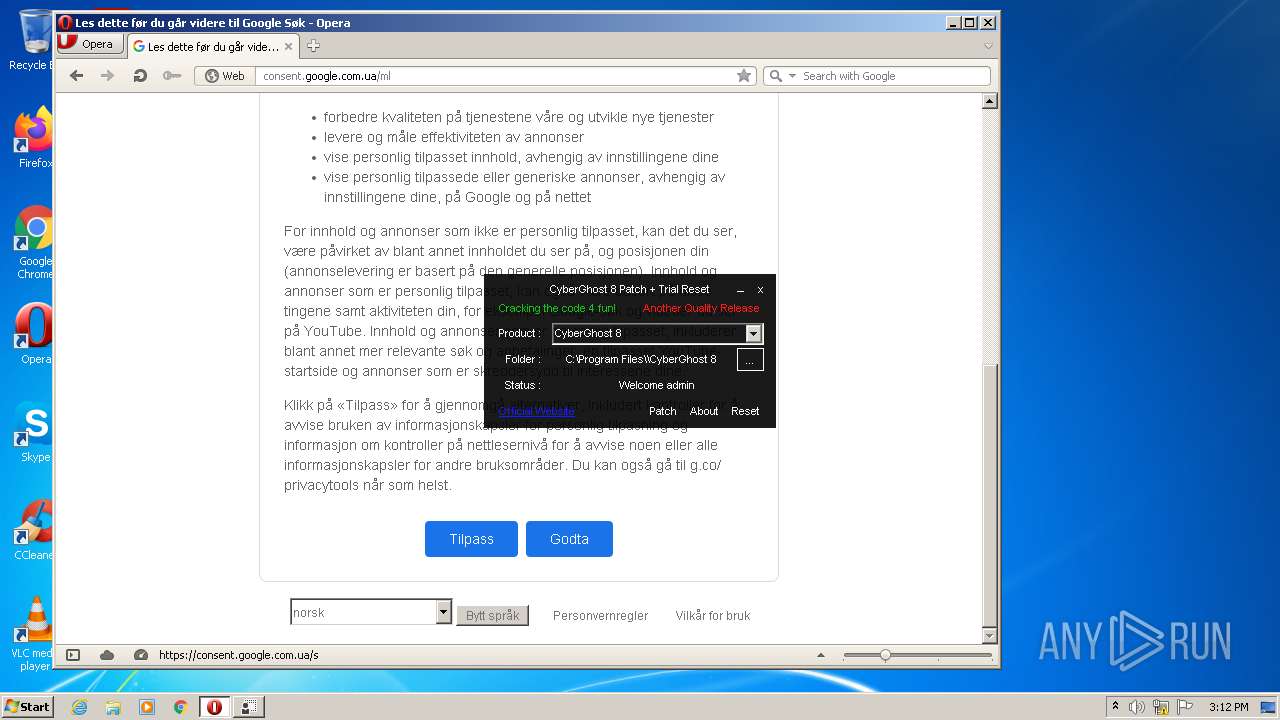
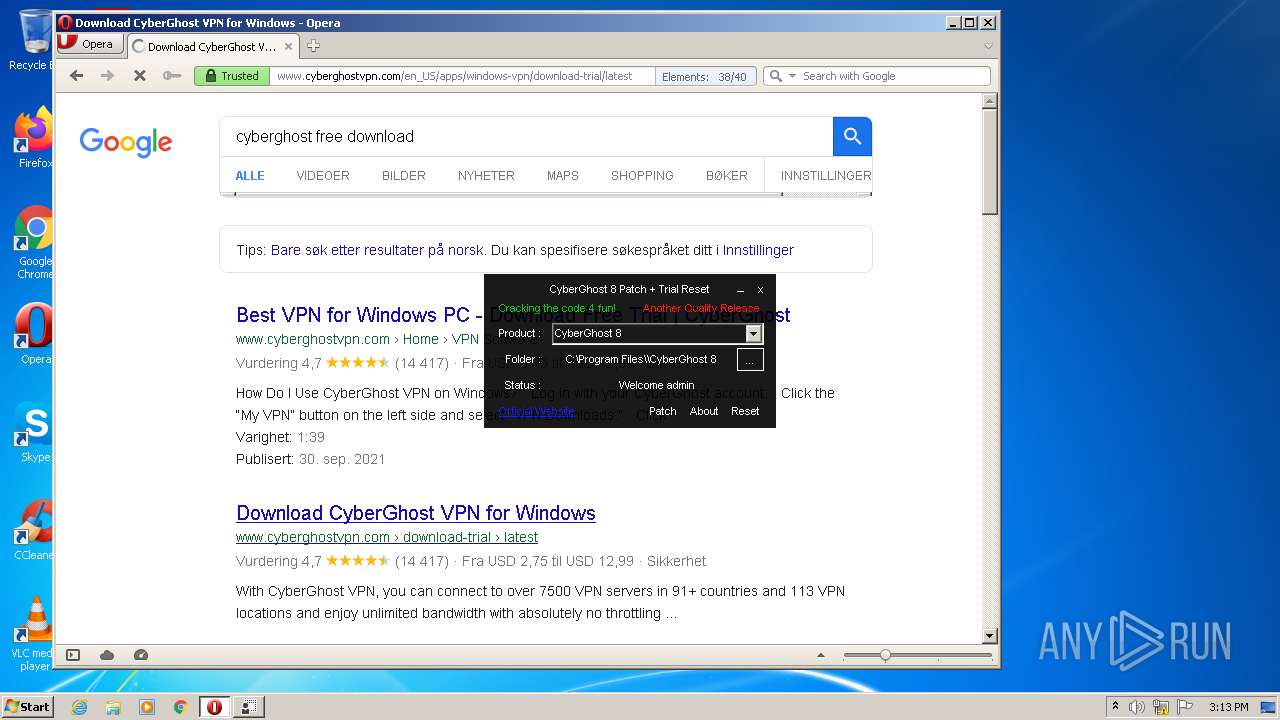
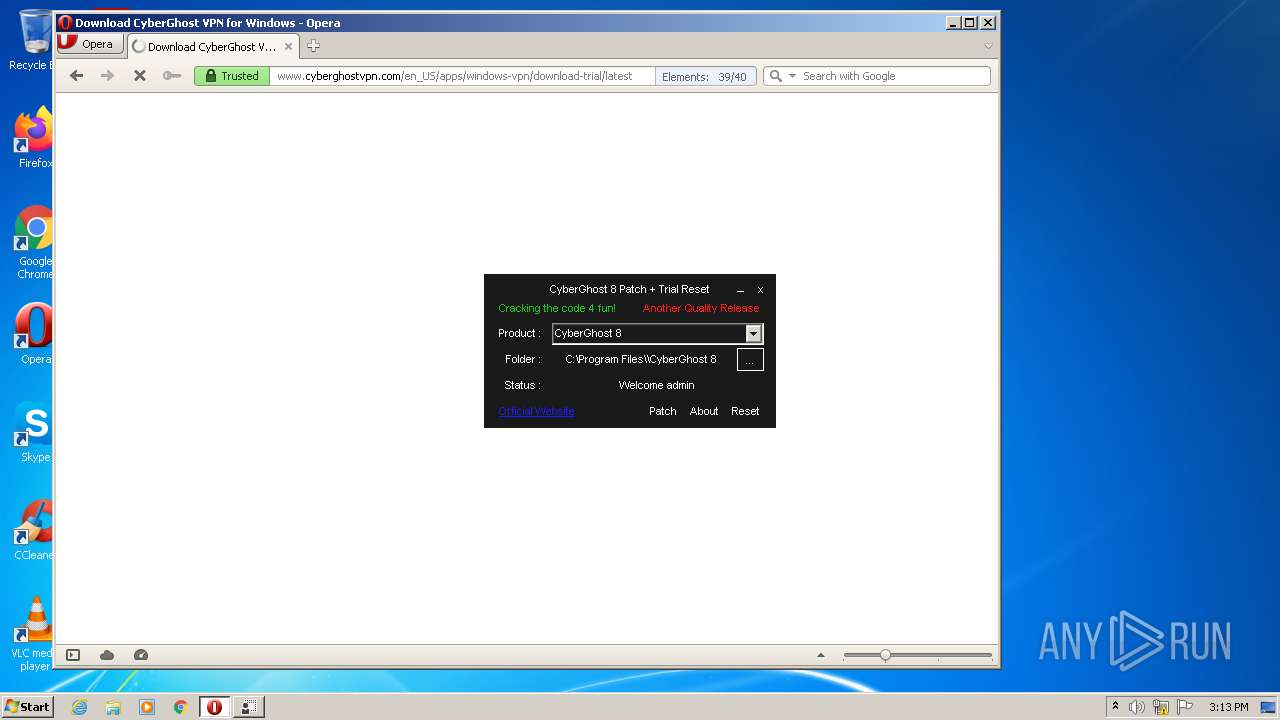
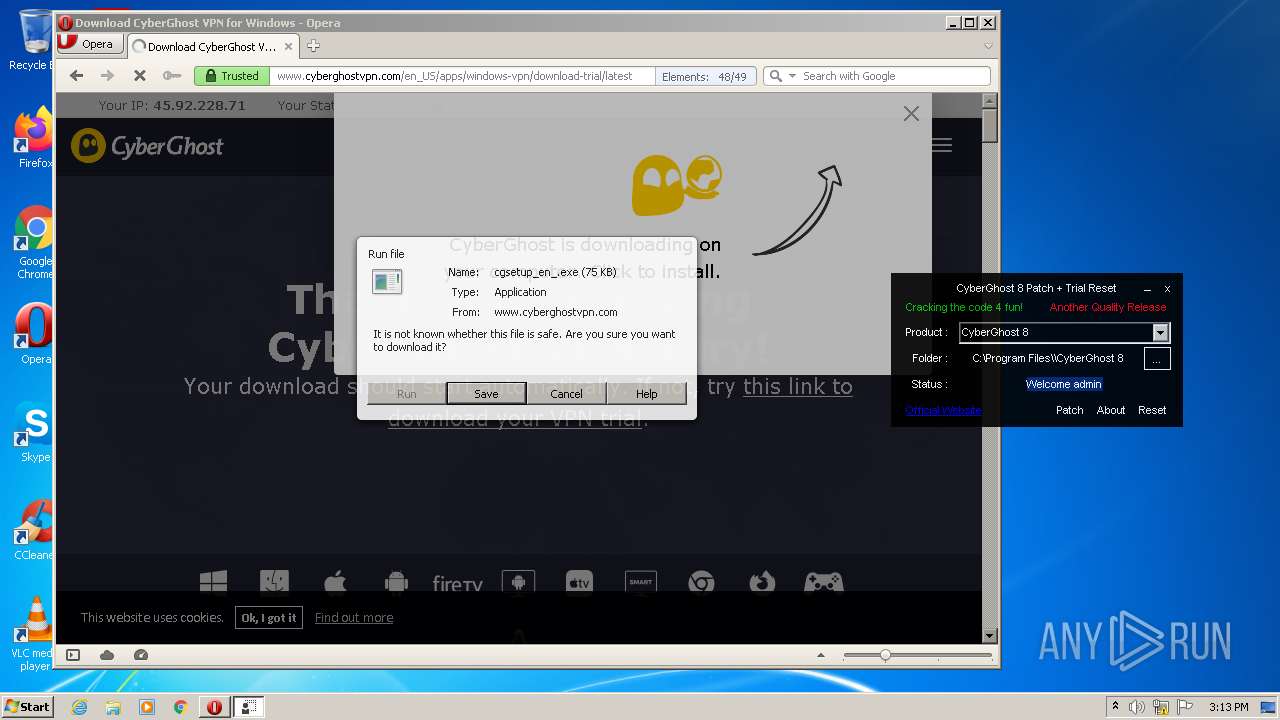
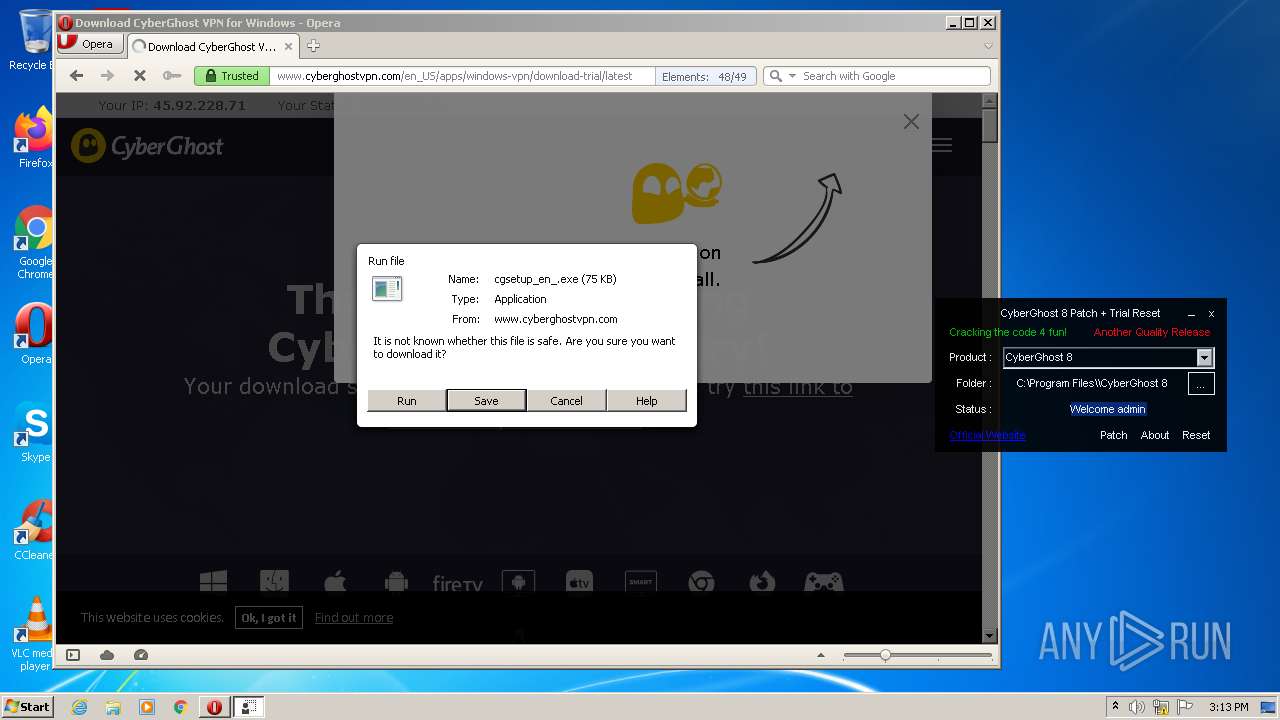
Executable content was dropped or overwritten
- opera.exe (PID: 4040)
- tmp260.tmp.exe (PID: 3520)
- msiexec.exe (PID: 2100)
Drops a file that was compiled in debug mode
- opera.exe (PID: 4040)
- tmp260.tmp.exe (PID: 3520)
- msiexec.exe (PID: 2100)
Adds / modifies Windows certificates
- cgsetup_en_.exe (PID: 3644)
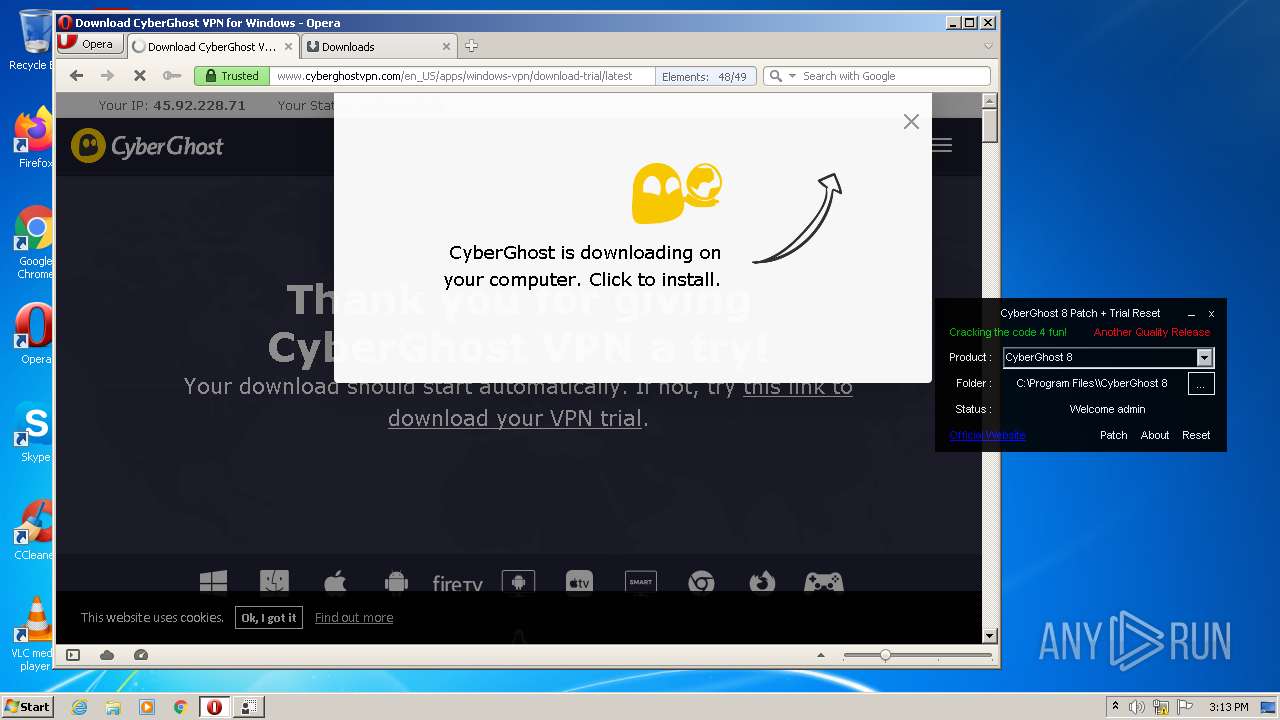
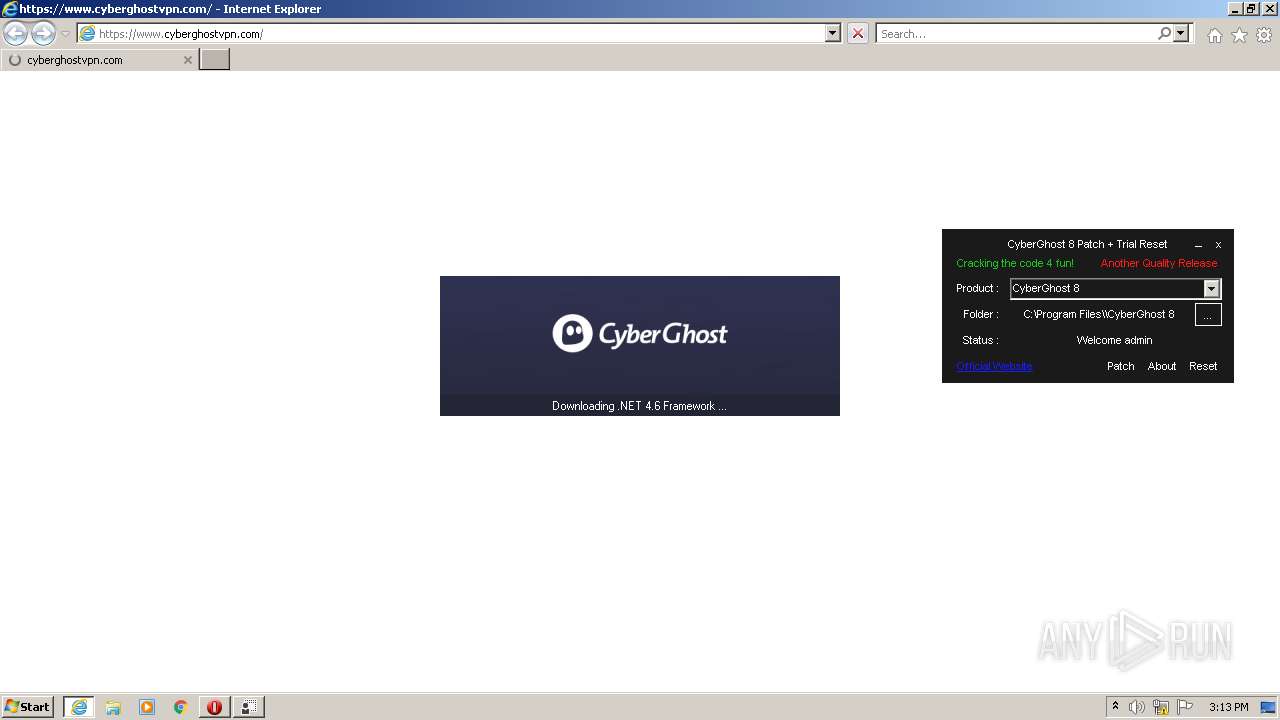
Starts Internet Explorer
- CyberGhost 8 Patch + Trial Reset.exe (PID: 3800)
Reads Environment values
- cgsetup_en_.exe (PID: 3644)
- Setup.exe (PID: 444)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1496)
Reads CPU info
- Setup.exe (PID: 444)
Executed as Windows Service
- msiexec.exe (PID: 2100)
Reads Windows owner or organization settings
- msiexec.exe (PID: 2100)
Reads the Windows organization settings
- msiexec.exe (PID: 2100)
Application launched itself
- msiexec.exe (PID: 2100)
Drops a file with too old compile date
- msiexec.exe (PID: 2100)
Searches for installed software
- msiexec.exe (PID: 2100)
Creates a software uninstall entry
- msiexec.exe (PID: 2100)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 2100)
- aspnet_regiis.exe (PID: 3904)
Creates files in the Windows directory
- msiexec.exe (PID: 2100)
- lodctr.exe (PID: 1284)
- aspnet_regiis.exe (PID: 3904)
Checks for the .NET to be installed
- msiexec.exe (PID: 2100)
Removes files from Windows directory
- msiexec.exe (PID: 2100)
- lodctr.exe (PID: 1284)
- aspnet_regiis.exe (PID: 3904)
INFO
Check for Java to be installed
- opera.exe (PID: 4040)
Reads the computer name
- opera.exe (PID: 4040)
- iexplore.exe (PID: 2488)
- iexplore.exe (PID: 1496)
- msiexec.exe (PID: 2100)
- MsiExec.exe (PID: 3048)
- MsiExec.exe (PID: 3916)
- wevtutil.exe (PID: 3728)
- wevtutil.exe (PID: 3988)
- lodctr.exe (PID: 1284)
Manual execution by user
- opera.exe (PID: 4040)
Checks supported languages
- opera.exe (PID: 4040)
- iexplore.exe (PID: 1496)
- iexplore.exe (PID: 2488)
- msiexec.exe (PID: 2100)
- MsiExec.exe (PID: 3916)
- MsiExec.exe (PID: 3048)
- wevtutil.exe (PID: 3988)
- wevtutil.exe (PID: 3728)
- lodctr.exe (PID: 1284)
Reads the date of Windows installation
- opera.exe (PID: 4040)
- iexplore.exe (PID: 2488)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 4040)
- tmp260.tmp.exe (PID: 3520)
- svchost.exe (PID: 2012)
- SetupUtility.exe (PID: 448)
- msiexec.exe (PID: 2100)
Reads CPU info
- opera.exe (PID: 4040)
Creates files in the user directory
- opera.exe (PID: 4040)
- iexplore.exe (PID: 1496)
Reads settings of System Certificates
- opera.exe (PID: 4040)
- cgsetup_en_.exe (PID: 3644)
- iexplore.exe (PID: 1496)
- Setup.exe (PID: 444)
- msiexec.exe (PID: 2100)
Checks Windows Trust Settings
- cgsetup_en_.exe (PID: 3644)
- iexplore.exe (PID: 1496)
- Setup.exe (PID: 444)
- msiexec.exe (PID: 2100)
Application launched itself
- iexplore.exe (PID: 2488)
Reads internet explorer settings
- iexplore.exe (PID: 1496)
Changes internet zones settings
- iexplore.exe (PID: 2488)
Changes settings of System certificates
- iexplore.exe (PID: 1496)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1496)
Creates or modifies windows services
- msiexec.exe (PID: 2100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | Project X |
| OriginalFileName: | MADARA.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright 2021 |
| InternalName: | MADARA.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Project X |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x6bdfe |
| UninitializedDataSize: | - |
| InitializedDataSize: | 12800 |
| CodeSize: | 434176 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2021:12:28 00:13:44+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Dec-2021 23:13:44 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Project X |
| FileVersion: | 1.0.0.0 |
| InternalName: | MADARA.exe |
| LegalCopyright: | Copyright 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | MADARA.exe |
| ProductName: | Project X |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 27-Dec-2021 23:13:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00069E04 | 0x0006A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.95428 |
.rsrc | 0x0006C000 | 0x00002F71 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.29719 |
.reloc | 0x00070000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.97846 | 693 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.51309 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 1.68675 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 1.19976 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.06992 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 2.33524 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
32512 | 2.66931 | 90 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
70
Monitored processes
24
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | C:\ca257797d2739384eb8e87\\Setup.exe /passive /norestart /x86 /x64 /redist | C:\ca257797d2739384eb8e87\Setup.exe | tmp260.tmp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 14.0.0081.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 448 | SetupUtility.exe /aupause | C:\ca257797d2739384eb8e87\SetupUtility.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.5 Setup Exit code: 0 Version: 14.0.0081.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1284 | "C:\Windows\system32\lodctr.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\netmemorycache.ini" | C:\Windows\system32\lodctr.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2488 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2012 | C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2100 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2168 | "C:\Windows\system32\wbem\mofcomp.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MOF\ServiceModel35.mof" | C:\Windows\system32\wbem\mofcomp.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: The Managed Object Format (MOF) Compiler Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2296 | mofcomp C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet.mof | C:\Windows\system32\wbem\mofcomp.exe | — | aspnet_regiis.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: The Managed Object Format (MOF) Compiler Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.cyberghostvpn.com/ | C:\Program Files\Internet Explorer\iexplore.exe | — | CyberGhost 8 Patch + Trial Reset.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2680 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\regtlibv12.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorlib.tlb" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\regtlibv12.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: RegTLib Exit code: 0 Version: 14.0.0081.0 built by: NETFXREL2 Modules
| |||||||||||||||
Total events
78 614
Read events
67 227
Write events
9 729
Delete events
1 658
Modification events
| (PID) Process: | (4040) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (4040) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2012) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Internet Explorer\LowRegistry\Audio\PolicyConfig\PropertyStore\625696e0_0 |
| Operation: | write | Name: | (default) |
Value: {0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6}|\Device\HarddiskVolume2\Program Files\Opera\opera.exe%b{00000000-0000-0000-0000-000000000000} | |||
| (PID) Process: | (2012) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Internet Explorer\LowRegistry\Audio\PolicyConfig\PropertyStore\625696e0_0\{219ED5A0-9CBF-4F3A-B927-37C9E5C5F14F} |
| Operation: | write | Name: | 3 |
Value: 04000000000000000000803F00000000 | |||
| (PID) Process: | (2012) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Internet Explorer\LowRegistry\Audio\PolicyConfig\PropertyStore\625696e0_0\{219ED5A0-9CBF-4F3A-B927-37C9E5C5F14F} |
| Operation: | write | Name: | 4 |
Value: 042000000000000010000000000000000000803F0000803F | |||
| (PID) Process: | (2012) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Internet Explorer\LowRegistry\Audio\PolicyConfig\PropertyStore\625696e0_0\{219ED5A0-9CBF-4F3A-B927-37C9E5C5F14F} |
| Operation: | write | Name: | 5 |
Value: 0B000000000000000000000000000000 | |||
| (PID) Process: | (4040) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4040) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4040) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4040) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2 083
Suspicious files
122
Text files
515
Unknown types
113
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4040 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:29DA06CCA02500F58B713FFC01E3DAD0 | SHA256:2648323474BB36D0F0C6AADA98FC793B9C76F8D44A13E8FEC0B6BAF9CB0AF8E6 | |||
| 4040 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00003.tmp | xml | |
MD5:7966F3F842F1E41B71A94EE31B6DED29 | SHA256:1298A8BC01D74ACDDF2825B82EB242D005C0A816617A7E187FCC0B7BA8E23272 | |||
| 4040 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr3194.tmp | xml | |
MD5:814D866CE4FF05A60F090923B613A2D7 | SHA256:C869EA96DBE5F477436064ADADDEFDECFACB86316B644B8322A7952F5F4FE42A | |||
| 4040 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:888BAAC81210F4FEB46566FC6D89290A | SHA256:2834DC3B027DAF06BA138E6FC37D12458E41DC9E6E26BFE406F9A6BFCD540520 | |||
| 4040 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:814D866CE4FF05A60F090923B613A2D7 | SHA256:C869EA96DBE5F477436064ADADDEFDECFACB86316B644B8322A7952F5F4FE42A | |||
| 4040 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:3F7590FD56AC999E0289444034C9CC80 | SHA256:632F80B7AD1F589FE608EF8546E3E7D1B0501A9EC3E38C0140EA1C10ED3E602B | |||
| 4040 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr3164.tmp | text | |
MD5:888BAAC81210F4FEB46566FC6D89290A | SHA256:2834DC3B027DAF06BA138E6FC37D12458E41DC9E6E26BFE406F9A6BFCD540520 | |||
| 4040 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\J0DGD4S23ZSWAM7OJFXQ.temp | binary | |
MD5:3F7590FD56AC999E0289444034C9CC80 | SHA256:632F80B7AD1F589FE608EF8546E3E7D1B0501A9EC3E38C0140EA1C10ED3E602B | |||
| 4040 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00004.tmp | compressed | |
MD5:086EFCD561B4A785FB85213124F1CCB0 | SHA256:C1873788E30221C4B832225929D9064A21073A185885FA7CAFC72F2D4D460DDF | |||
| 4040 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\icons\www.google.com.idx | text | |
MD5:021B3505AAFD914211FB373ECB1A713C | SHA256:2BFC75B1E231AB2636ECB846348102244F4F5DAF0ED2418D5A696223E65EC0ED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
139
DNS requests
57
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
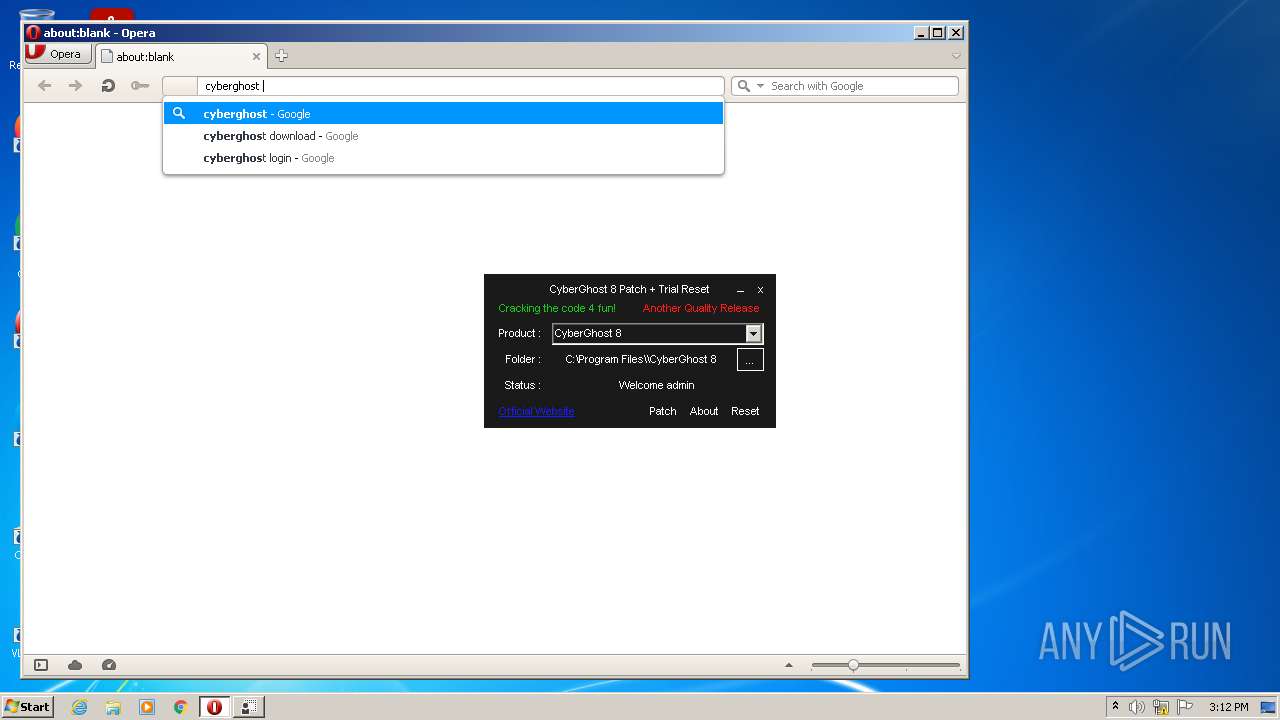
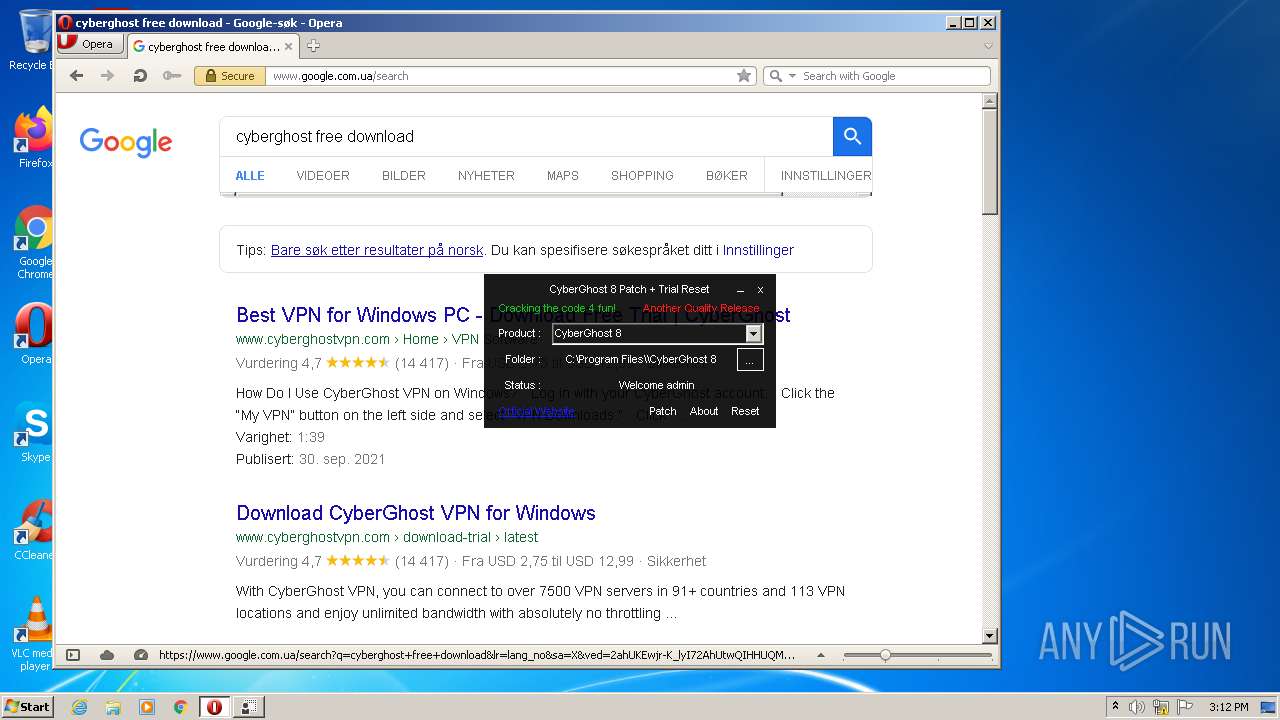
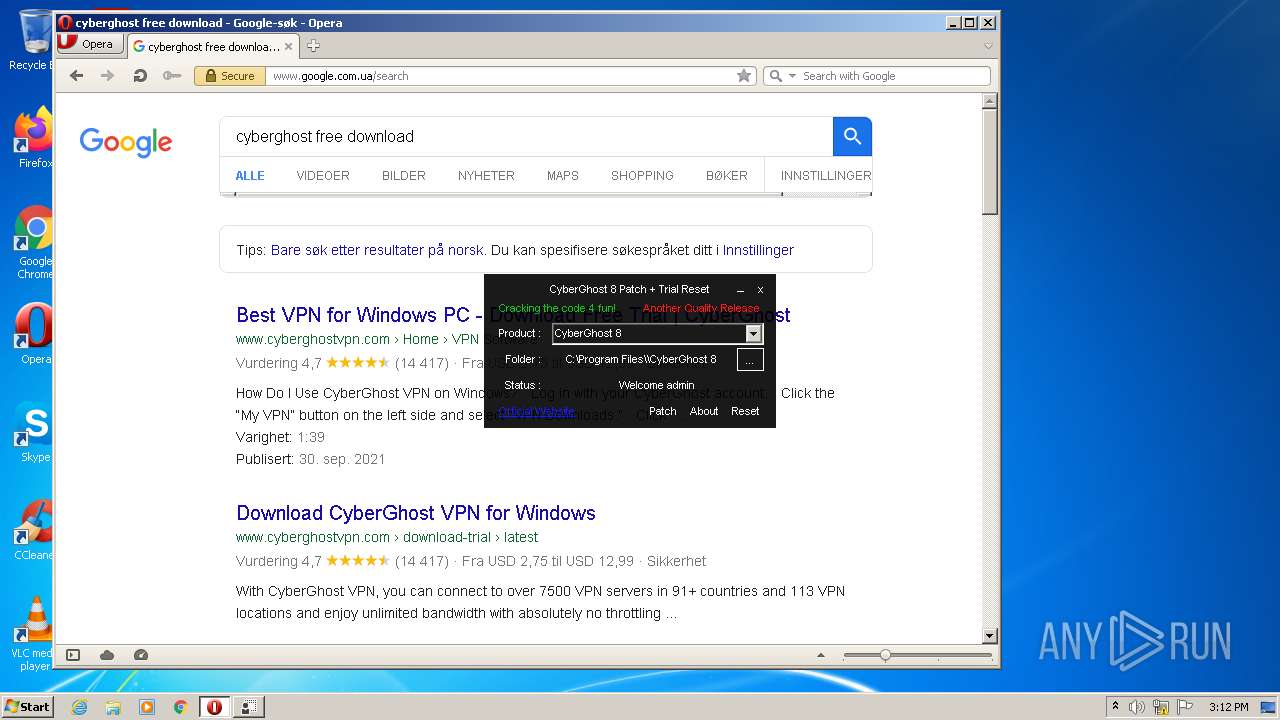
4040 | opera.exe | GET | 200 | 142.250.185.206:80 | http://clients1.google.com/complete/search?q=cyberghos&client=opera-suggest-omnibox&hl=de | US | text | 157 b | whitelisted |
4040 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
4040 | opera.exe | GET | 200 | 142.250.185.206:80 | http://clients1.google.com/complete/search?q=cyber&client=opera-suggest-omnibox&hl=de | US | text | 148 b | whitelisted |
4040 | opera.exe | GET | 200 | 142.250.185.206:80 | http://clients1.google.com/complete/search?q=cybergh&client=opera-suggest-omnibox&hl=de | US | text | 158 b | whitelisted |
4040 | opera.exe | GET | 200 | 142.250.185.206:80 | http://clients1.google.com/complete/search?q=cyberghost&client=opera-suggest-omnibox&hl=de | US | text | 155 b | whitelisted |
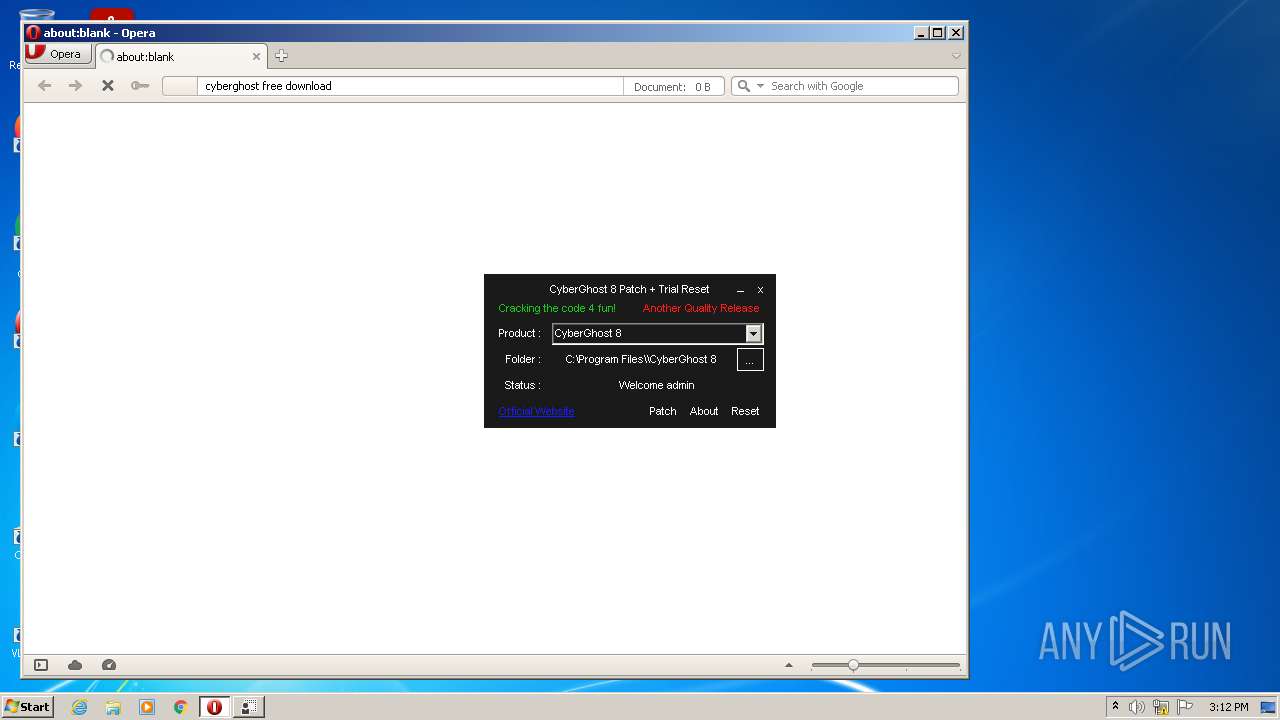
4040 | opera.exe | GET | 200 | 142.250.185.206:80 | http://clients1.google.com/complete/search?q=cyberghost+free+down&client=opera-suggest-omnibox&hl=de | US | text | 177 b | whitelisted |
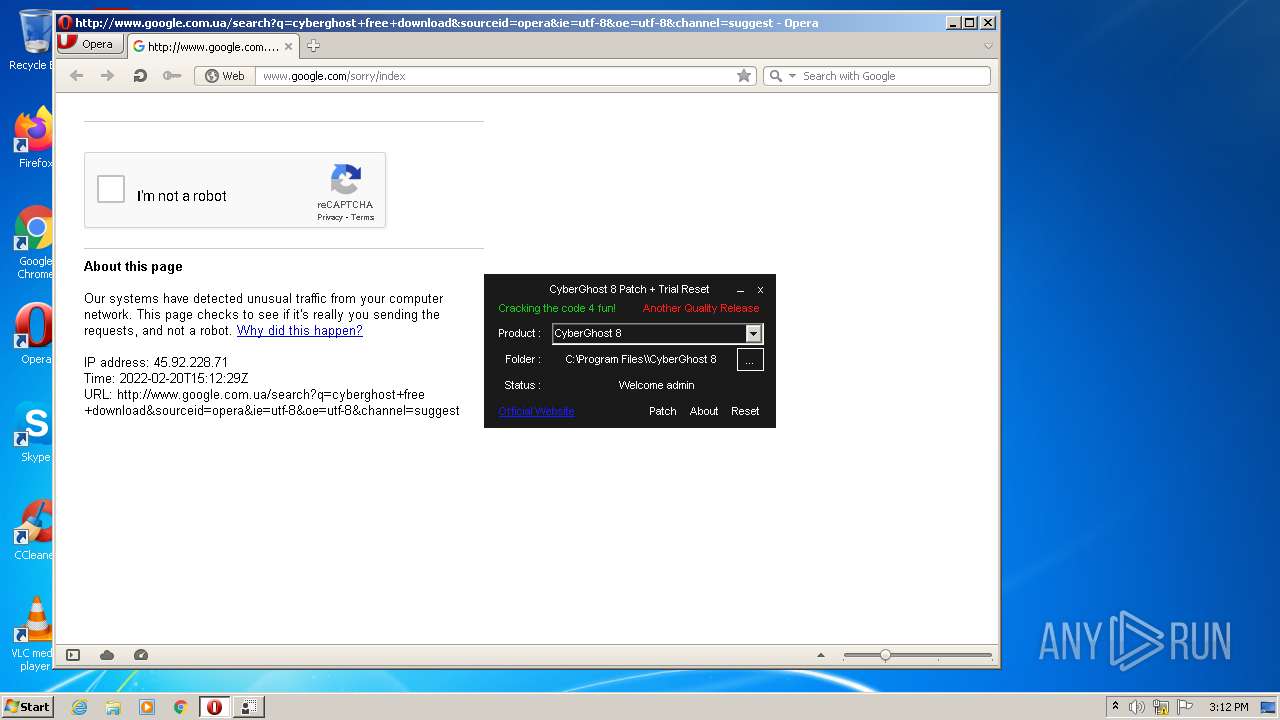
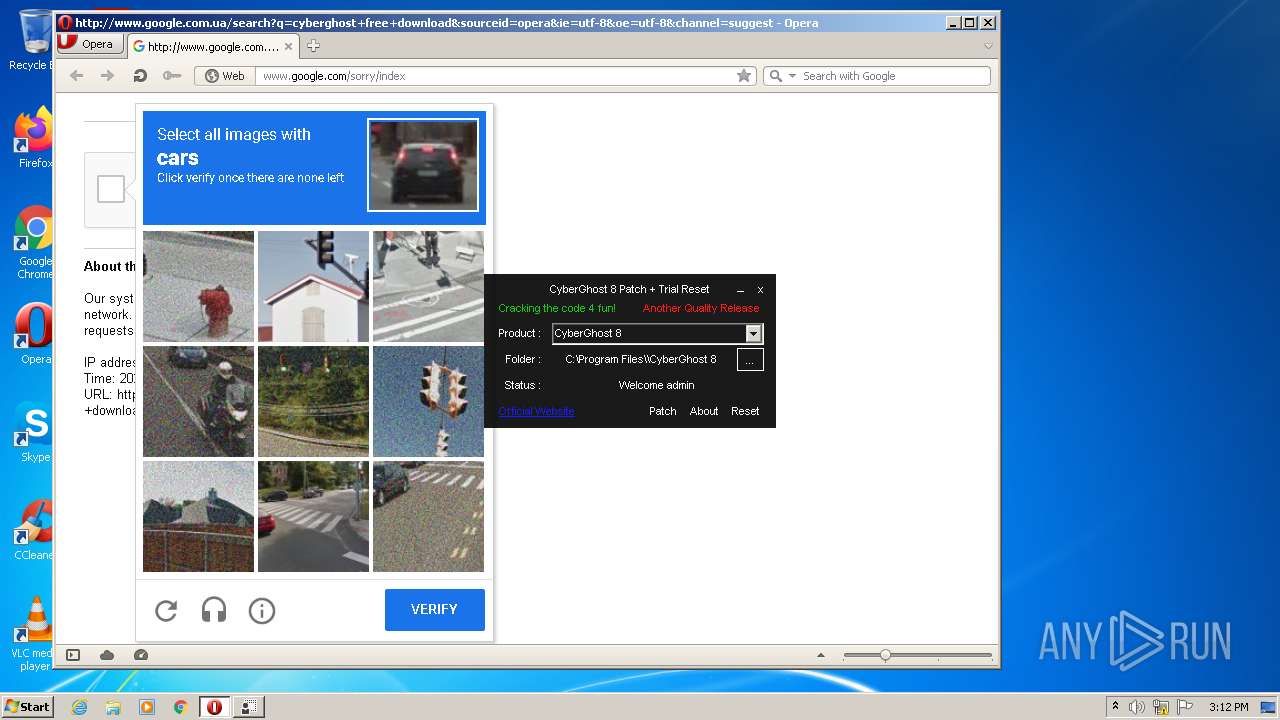
4040 | opera.exe | GET | 302 | 142.250.184.195:80 | http://www.google.com.ua/search?q=cyberghost+free+download&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 422 b | whitelisted |
4040 | opera.exe | GET | 200 | 142.250.185.206:80 | http://clients1.google.com/complete/search?q=cyberghost+free+download&client=opera-suggest-omnibox&hl=de | US | text | 174 b | whitelisted |
4040 | opera.exe | GET | 200 | 142.250.185.227:80 | http://crl.pki.goog/gsr1/gsr1.crl | US | der | 1.61 Kb | whitelisted |
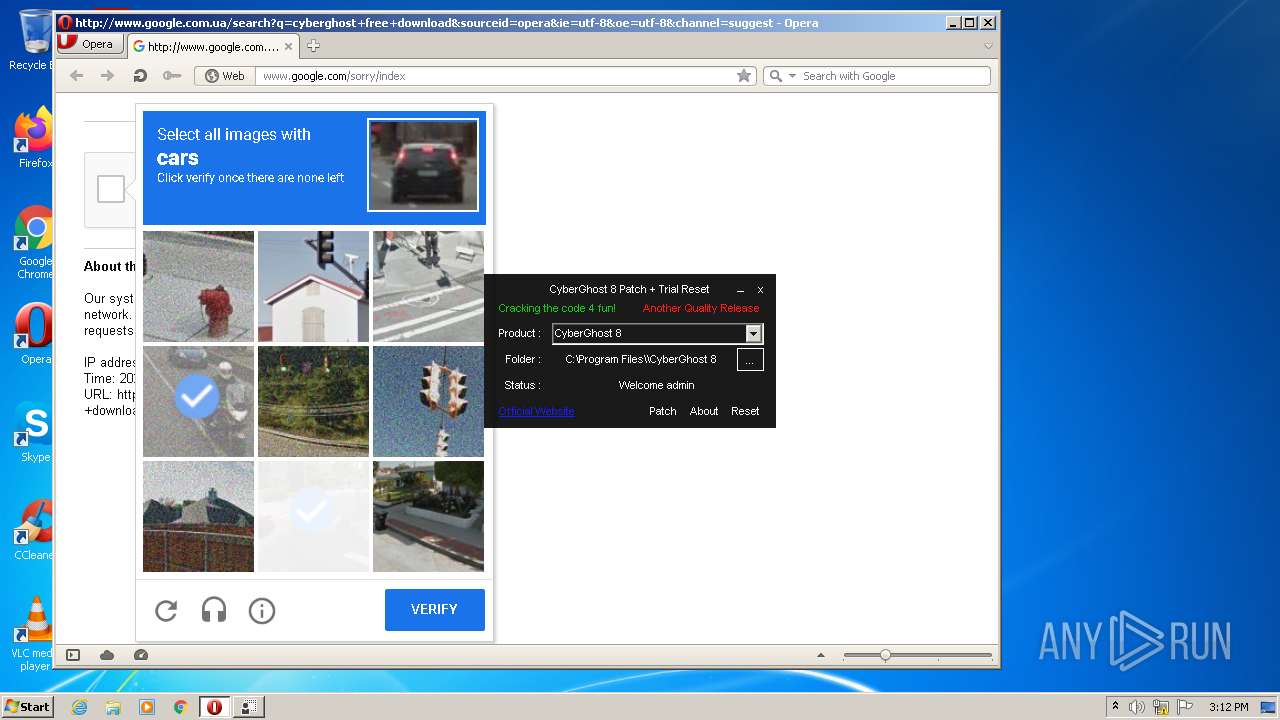
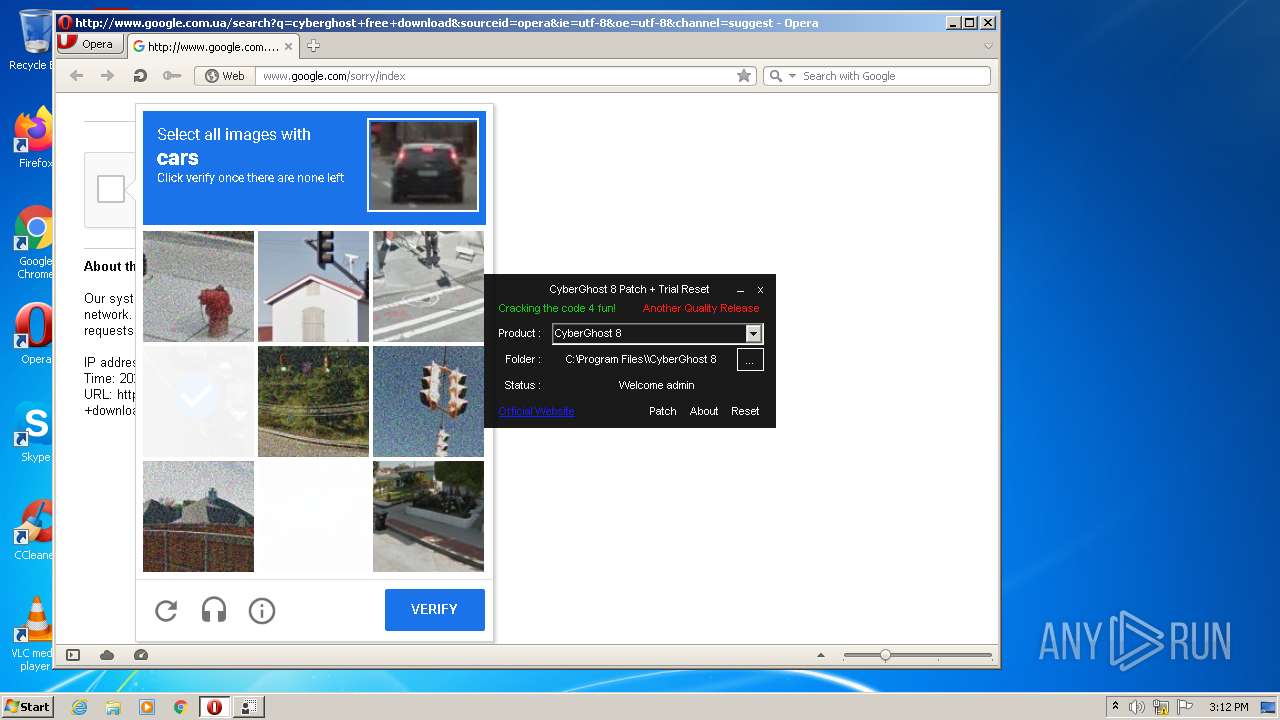
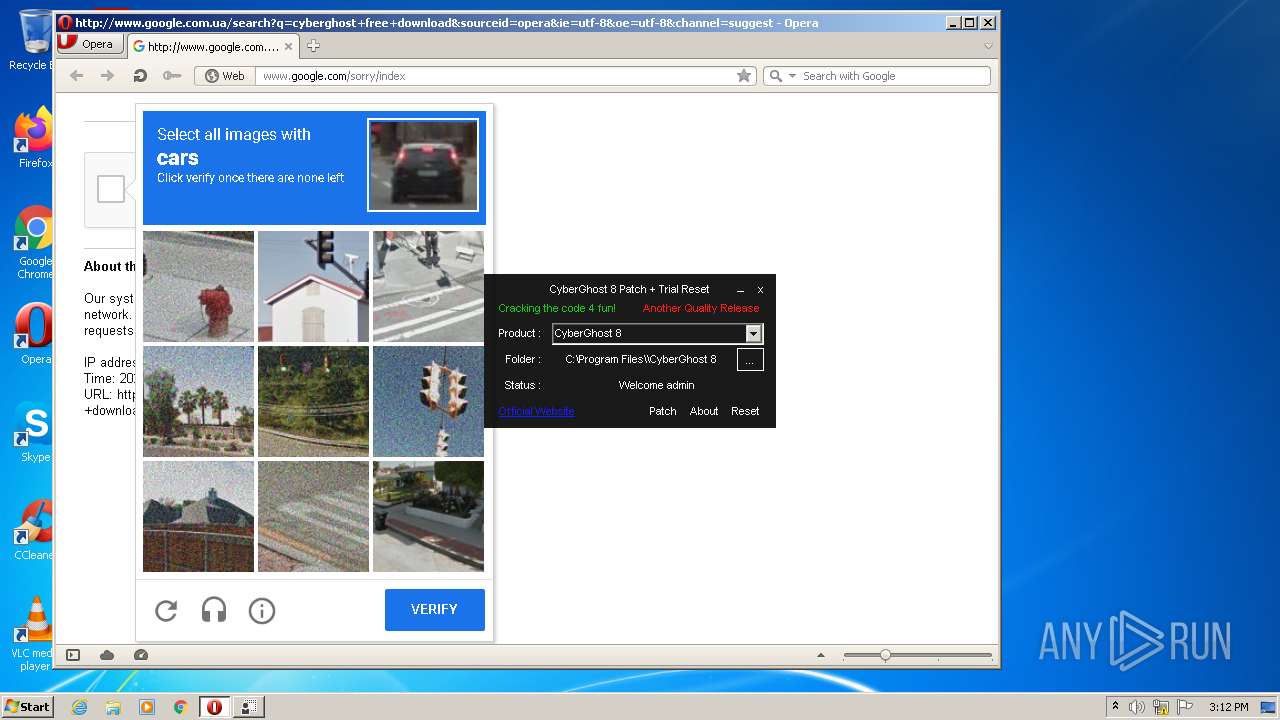
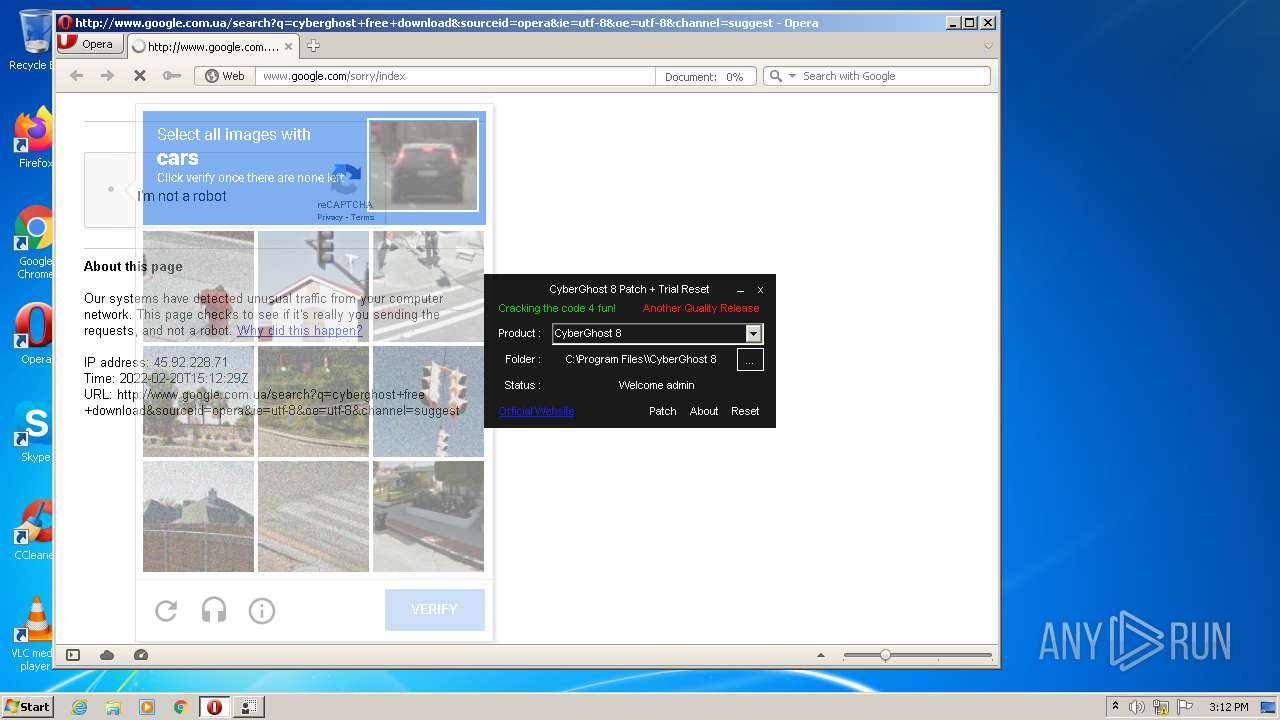
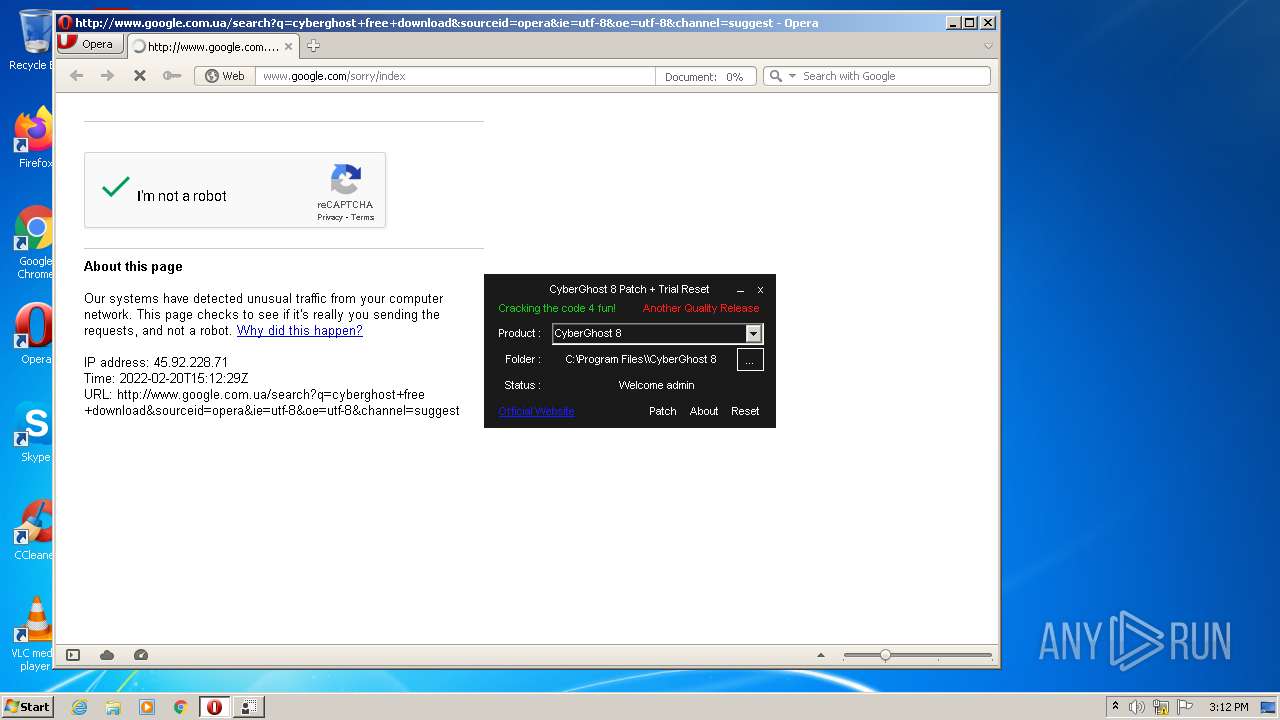
4040 | opera.exe | POST | 302 | 142.250.186.132:80 | http://www.google.com/sorry/index | US | html | 531 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4040 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
4040 | opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4040 | opera.exe | 142.250.185.206:80 | clients1.google.com | Google Inc. | US | whitelisted |
4040 | opera.exe | 142.250.184.195:80 | www.google.com.ua | Google Inc. | US | whitelisted |
4040 | opera.exe | 185.26.182.112:80 | sitecheck2.opera.com | Opera Software AS | — | malicious |
4040 | opera.exe | 142.250.186.132:443 | www.google.com | Google Inc. | US | whitelisted |
4040 | opera.exe | 142.250.186.132:80 | www.google.com | Google Inc. | US | whitelisted |
4040 | opera.exe | 142.250.186.131:80 | — | Google Inc. | US | whitelisted |
4040 | opera.exe | 142.250.185.227:80 | crl.pki.goog | Google Inc. | US | whitelisted |
4040 | opera.exe | 142.250.186.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
www.google.com |
| malicious |
crl.pki.goog |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4040 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
4040 | opera.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |