| download: | ConfigTools.exe |
| Full analysis: | https://app.any.run/tasks/212ae7ce-99db-425d-86fb-dba4d8a20157 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2019, 14:02:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 08309869AC1579A0FC6FA2A15C9A8AD9 |
| SHA1: | FC28D70D065625BB014D8E8DB1B4C19A9D40736D |
| SHA256: | B0157462B095A63D576EFE19E05FDD8CAE555E237E03D4022CA41B456AE7EC1A |
| SSDEEP: | 12288:fF38RRD/yM+DzF5vM3/o4mScPy3+tnGAzwUrUcWPOUfvzJX8Gr2f:fx8RRD/yM+vFNMg4mhyu7wUrUc8nfdgf |
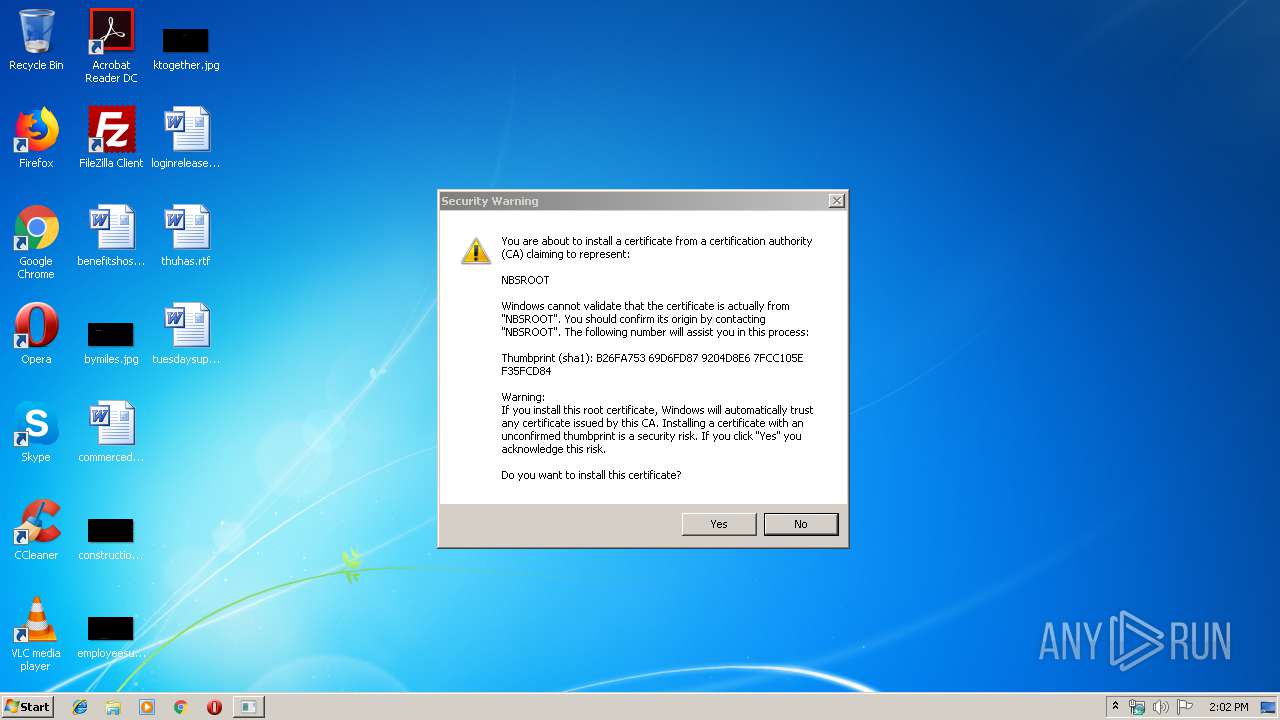
MALICIOUS
Changes settings of System certificates
- ConfigTools.exe (PID: 2456)
Changes internet zones settings
- ConfigTools.exe (PID: 2456)
SUSPICIOUS
Creates files in the user directory
- ConfigTools.exe (PID: 2456)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:06:01 08:15:28+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 204800 |
| InitializedDataSize: | 94208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4a001 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.9.7.0 |
| ProductVersionNumber: | 0.9.7.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Special build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | 格尔证书客户端配置工具 v0.9.7 |
| FileVersion: | 0, 9, 7, 0 |
| InternalName: | ConfigTools |
| LegalCopyright: | 上海格尔软件股份公司 版权所有 (C) 1998~2012 |
| LegalTrademarks: | - |
| OriginalFileName: | ConfigTools.EXE |
| PrivateBuild: | - |
| ProductName: | ConfigTools 应用程序 |
| ProductVersion: | 0, 9, 7, 0 |
| SpecialBuild: | 101 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jun-2012 06:15:28 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | 格尔证书客户端配置工具 v0.9.7 |
| FileVersion: | 0, 9, 7, 0 |
| InternalName: | ConfigTools |
| LegalCopyright: | 上海格尔软件股份公司 版权所有 (C) 1998~2012 |
| LegalTrademarks: | - |
| OriginalFilename: | ConfigTools.EXE |
| PrivateBuild: | - |
| ProductName: | ConfigTools 应用程序 |
| ProductVersion: | 0, 9, 7, 0 |
| SpecialBuild: | 101 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 01-Jun-2012 06:15:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00032000 | 0x00017C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99658 |
.rdata | 0x00033000 | 0x0000C000 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97538 |
.data | 0x0003F000 | 0x00008000 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.80084 |
.rsrc | 0x00047000 | 0x00003000 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.02842 |
.aspack | 0x0004A000 | 0x00002000 | 0x00001C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.38093 |
.adata | 0x0004C000 | 0x00001000 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.78598 | 876 | UNKNOWN | Chinese - PRC | RT_VERSION |
2 | 2.55844 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 5.46683 | 308 | UNKNOWN | Chinese - PRC | RT_CURSOR |
4 | 5.64929 | 180 | UNKNOWN | Chinese - PRC | RT_CURSOR |
7 | 4.9043 | 84 | UNKNOWN | Chinese - PRC | RT_STRING |
100 | 6.98854 | 230 | UNKNOWN | Chinese - PRC | RT_DIALOG |
102 | 7.35452 | 360 | UNKNOWN | Chinese - PRC | RT_DIALOG |
128 | 2.37086 | 34 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
129 | 6.4572 | 132 | UNKNOWN | Chinese - PRC | RT_DIALOG |
130 | 6.70591 | 134 | UNKNOWN | Chinese - PRC | RT_DIALOG |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
crypt32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
oledlg.dll |
olepro32.dll |
Total processes
34
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2456 | "C:\Users\admin\AppData\Local\Temp\ConfigTools.exe" | C:\Users\admin\AppData\Local\Temp\ConfigTools.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 格尔证书客户端配置工具 v0.9.7 Exit code: 0 Version: 0, 9, 7, 0 Modules
| |||||||||||||||
Total events
687
Read events
16
Write events
671
Delete events
0
Modification events
| (PID) Process: | (2456) ConfigTools.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2456) ConfigTools.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2456) ConfigTools.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (2456) ConfigTools.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (2456) ConfigTools.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (2456) ConfigTools.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (2456) ConfigTools.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\SystemCertificates\CA\Certificates\D2EA461E09EEB661F39DD88F63B2D1B592A7D341 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000835386AC99740CE18056990573803069140000000100000014000000C55D67F998AFD579DDACAAC0C3DBD12A19D7A4D519000000010000001000000047EC03079C99751ECB554C05121FD0A5030000000100000014000000D2EA461E09EEB661F39DD88F63B2D1B592A7D3410F00000001000000140000004195A1BE14577A61A451717EA113A477F2B4675D2000000001000000D5020000308202D1308201B9A003020102020C4F2648B8731A1A78AB8C528D300D06092A864886F70D0101050500302D310B300906035504061302434E310C300A060355040A0C034E42533110300E06035504030C074E4253524F4F54301E170D3133303731393038303030305A170D3230303731393038303030305A3039310B300906035504061302434E311B3019060355040A0C12E4B88AE6B5B7E5B882E7BB9FE8AEA1E5B180310D300B06035504030C045348434130819F300D06092A864886F70D010101050003818D00308189028181009300F1A725C32289773BD0FD381EA6A585AD735A27C0D8958D8677445DA58057726F7C4EB86E4FA50F415BDC8750E086928CAF7E48205F0F910378593F25FE08BC99A10BFBF994947D565170A556E89D6D9B7BB081CD9075DE26F9D02E0842406D8DECB482BEB84A08E3498933F3A22205CDC20FEEBFC80D4FFDB61F28F782D70203010001A3693067300E0603551D0F010100040403020086300F0603551D13010100040530030101FF30220603551D230101000418301680142C7AE7B0C78DE1A7958CC70293D76D2FE3DDF26830200603551D0E01010004160414C55D67F998AFD579DDACAAC0C3DBD12A19D7A4D5300D06092A864886F70D010105050003820101005B8759EA05E9256F4ABCD28CAB99A56C12E68EA1808DC7D4FCACD3A43BD29E0267A7861EA44986BFD46F3CCAC8E037EBA72368DE4222CD8DCFEF74FE00CD64EAA4E6783142D27D927860F077A4A6792147B7CB9E2BB269E79165DEC6F5949CED0C8462EEF10D14673AAE0AF7FF9EA42C15A08A53BEF3A401A12F9F67CB8DD41845F7A0896EA5A4BBFE8F5EDD1806610A272181AF0835F2144E027F40477554EDD75DC2CBE1AA3D25ECEB06B0C205C726A514960CF3249748C1044080E1462AA5240F1697154A4AD58D4D02D732B66D0B2B5067F8AD15E6FA95339188FDA4E83095B44303763841E557309968A78195E4FF16E47552C72AB3D4C7D043F3FA838B | |||
| (PID) Process: | (2456) ConfigTools.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2456) ConfigTools.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2456) ConfigTools.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | DisplayName |
Value: Trusted sites | |||
Executable files
0
Suspicious files
0
Text files
12
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2456 | ConfigTools.exe | C:\Users\admin\AppData\Roaming\configtools.dat | text | |
MD5:— | SHA256:— | |||
| 2456 | ConfigTools.exe | C:\Users\admin\AppData\Roaming\configtools.log | text | |
MD5:— | SHA256:— | |||
| 2456 | ConfigTools.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
ConfigTools.exe | 'C:\Users\admin\AppData\Local\Temp\ConfigTools.exe' size is 759544byte
|
ConfigTools.exe | RegisterOcx³ö´í: The specified module could not be found. (7e)(ConfigMngr.cpp:232) |
ConfigTools.exe | Register ocx 'C:\Windows\system32\KoalCspWrapper.ocx' failed:
|
ConfigTools.exe | RegOpenKeyEx³ö´í: The operation completed successfully. (0)(CertUtil.cpp:490) |
ConfigTools.exe | RegOpenKeyEx³ö´í: The operation completed successfully. (0)(CertUtil.cpp:490) |
ConfigTools.exe | Add 'NBSROOT,SHCA' to TrustCA Zone successfully.
|
ConfigTools.exe | Add 'http://*.tjj.sh.gov.cn' to TrustSite Zone successfully.
|
ConfigTools.exe | Add 'http://180.168.156.9' to TrustSite Zone successfully.
|
ConfigTools.exe | Add 'http://ytb.tjj.sh.gov.cn' to TrustSite Zone successfully.
|
ConfigTools.exe | Add 'https://*.tjj.sh.gov.cn' to TrustSite Zone successfully.
|