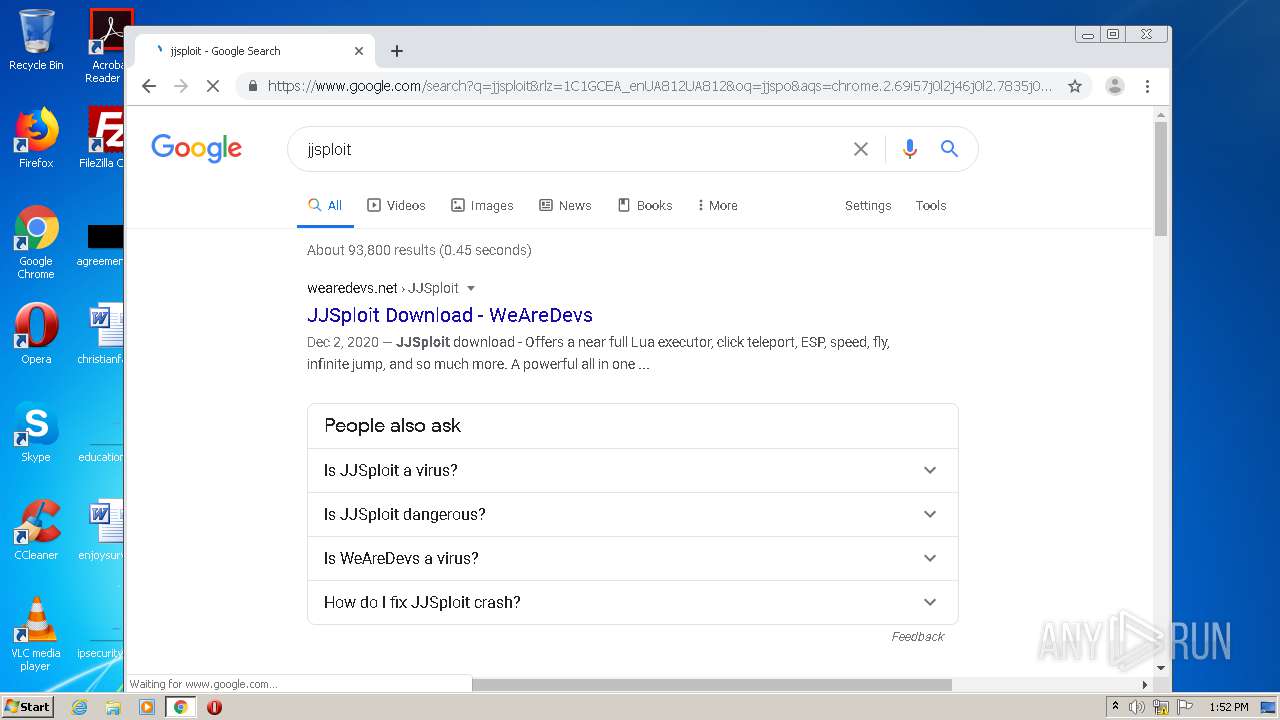
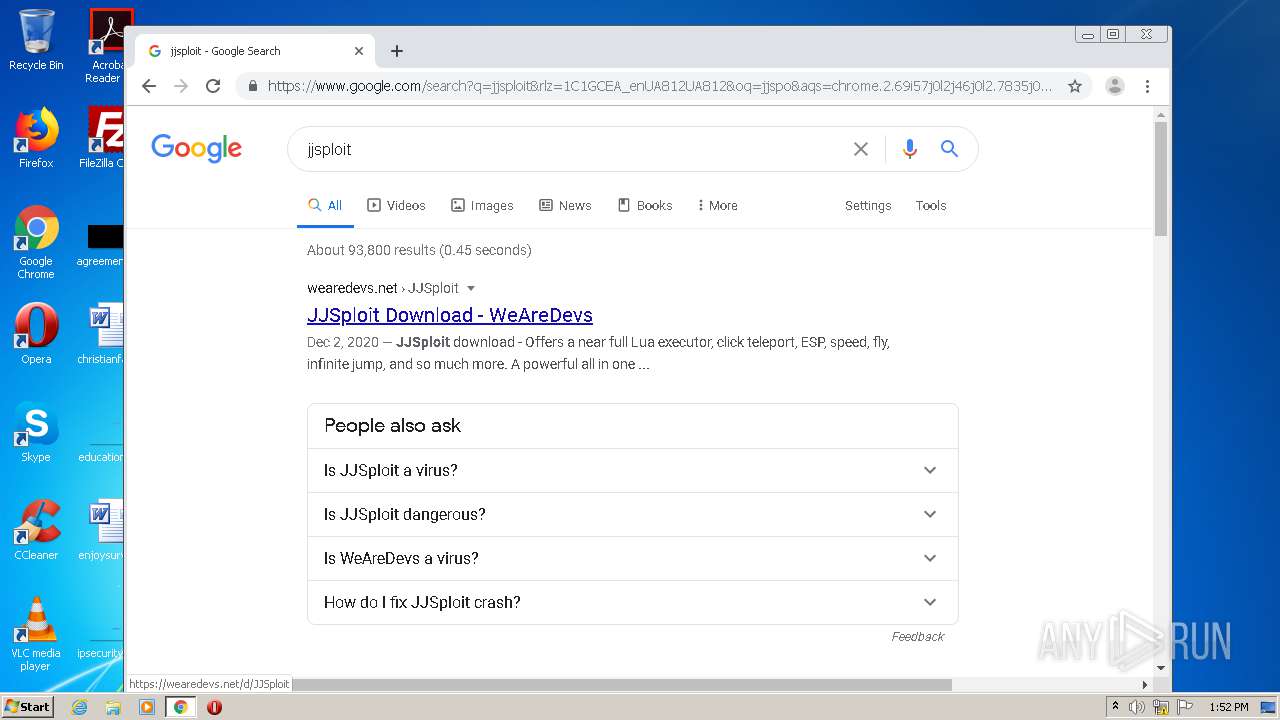
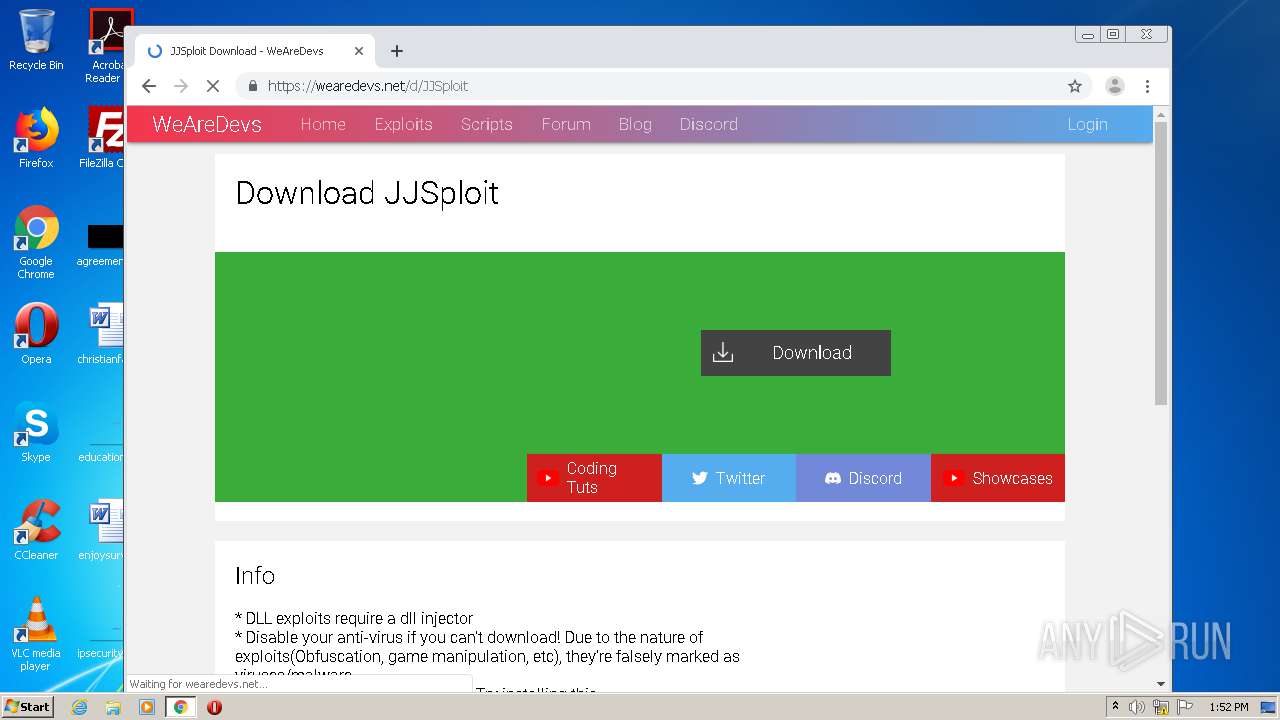
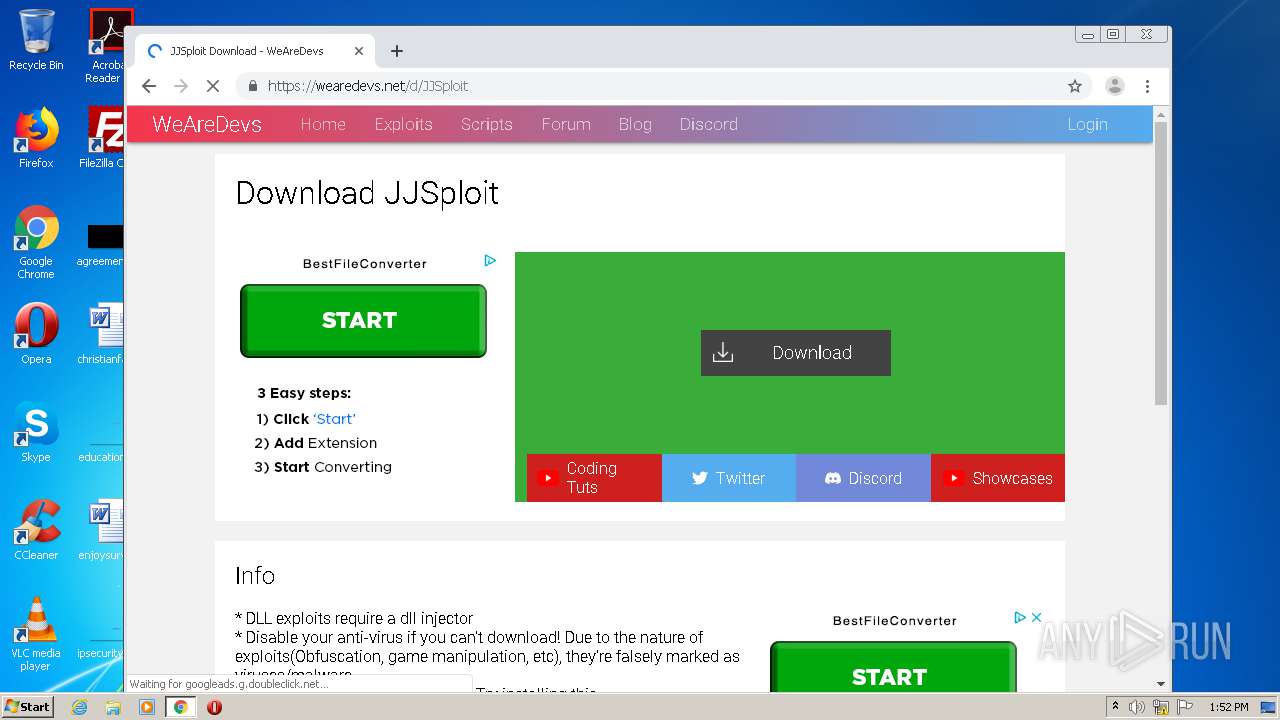
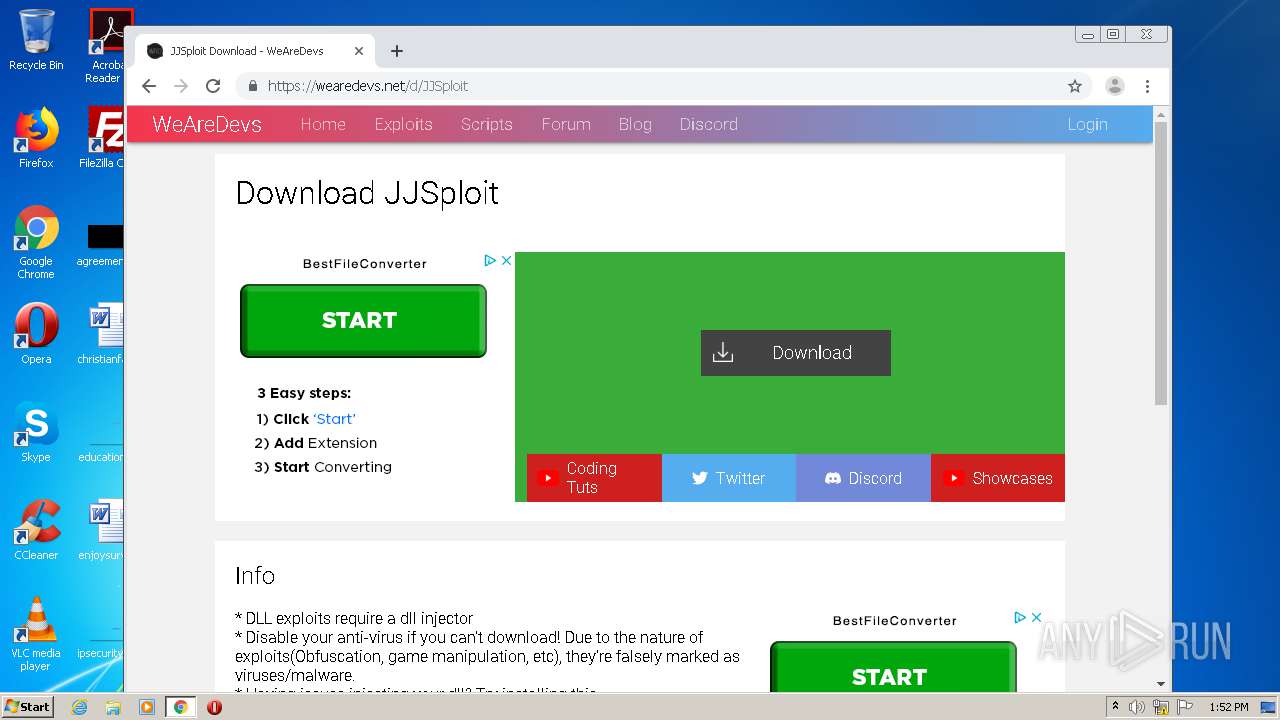
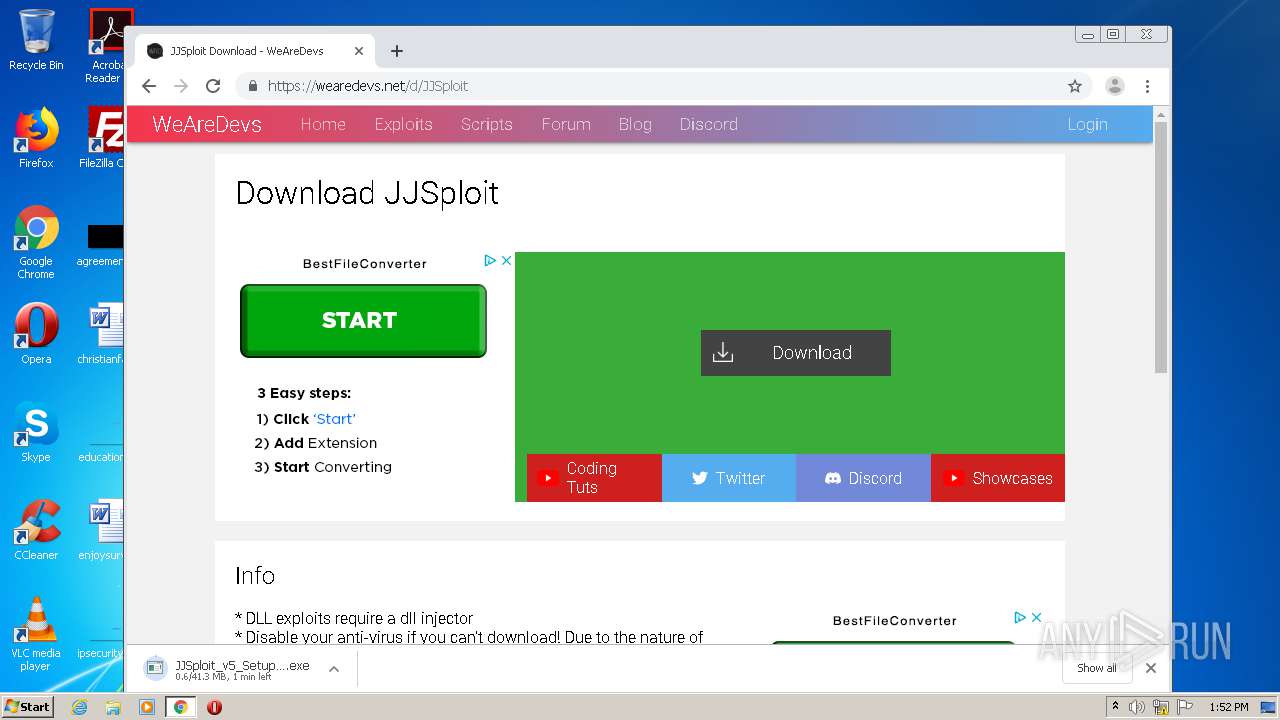
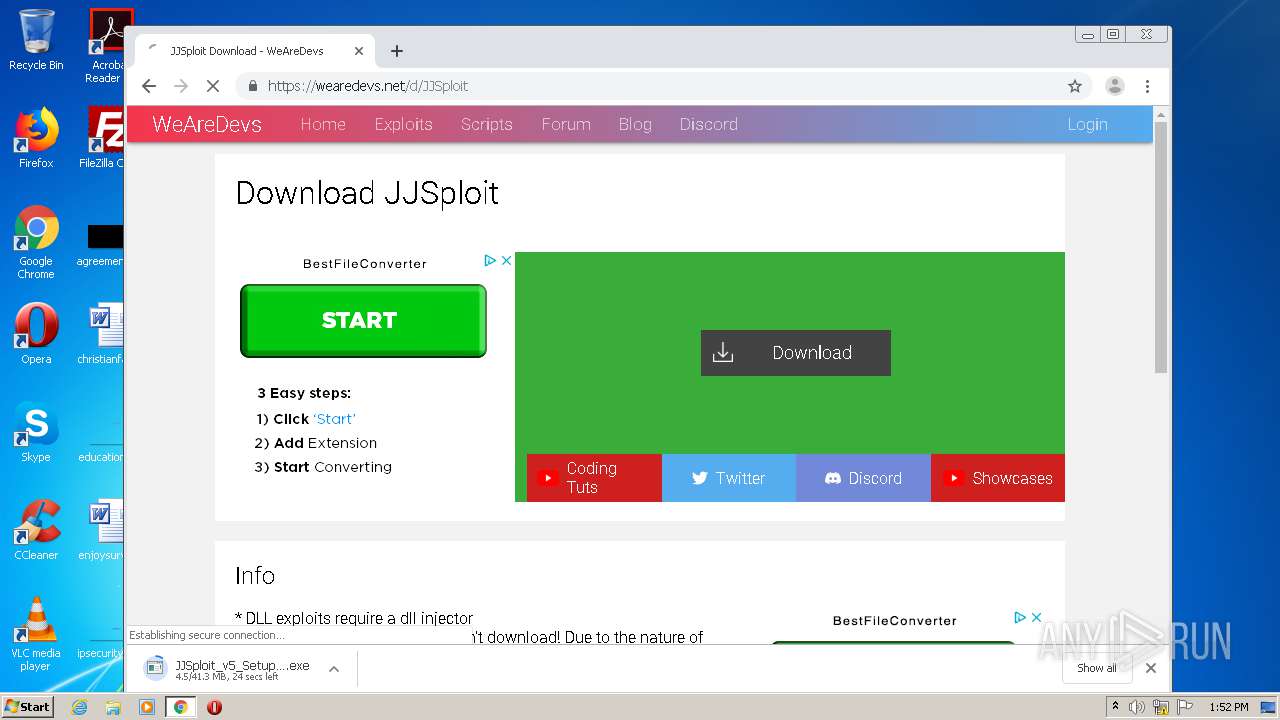
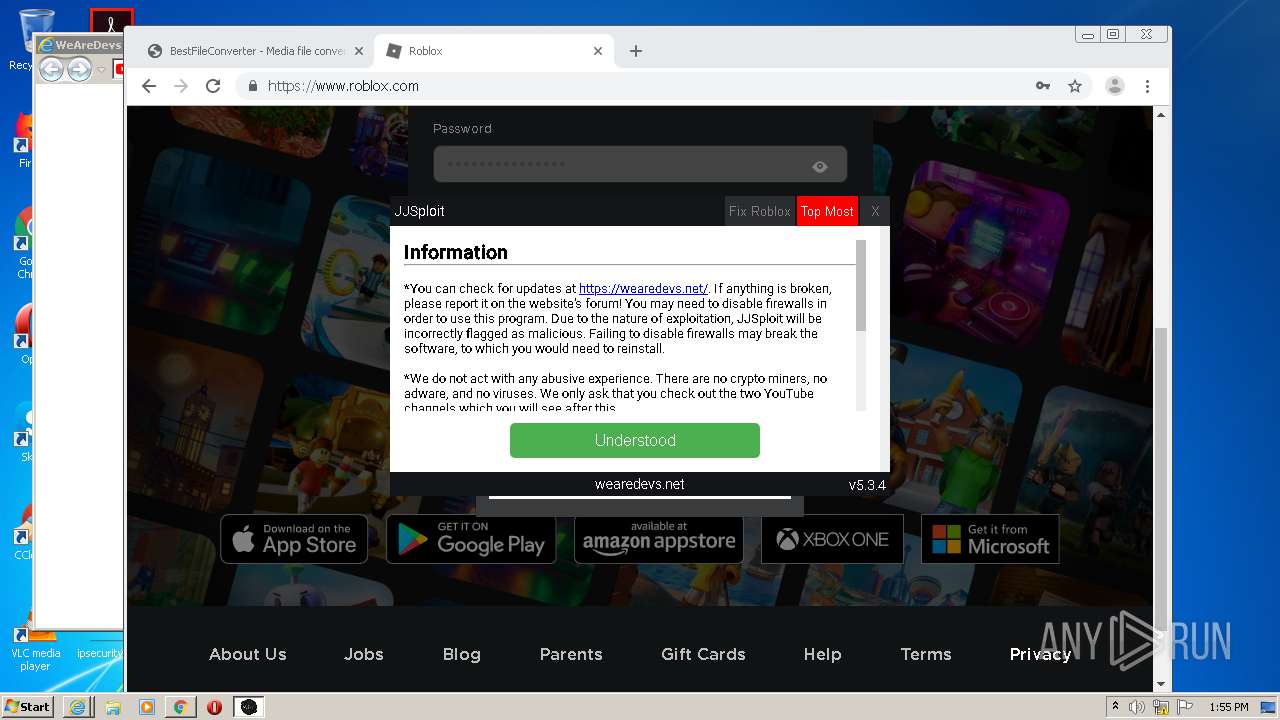
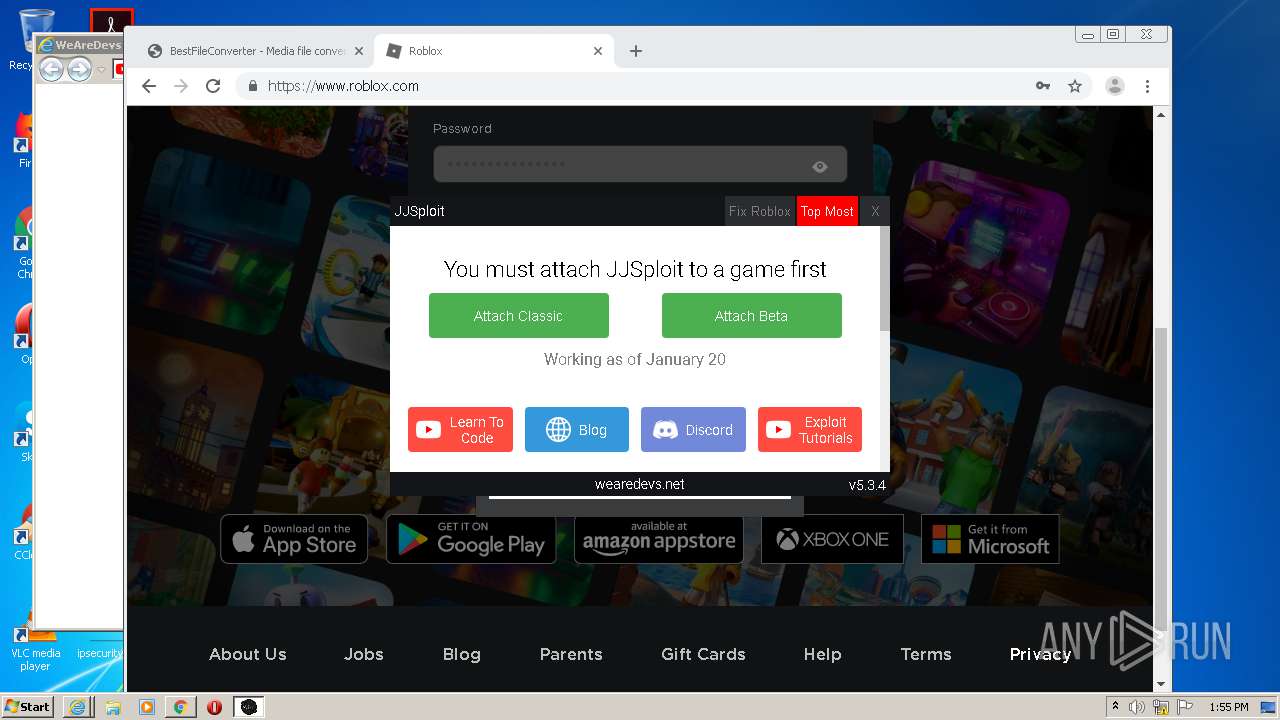
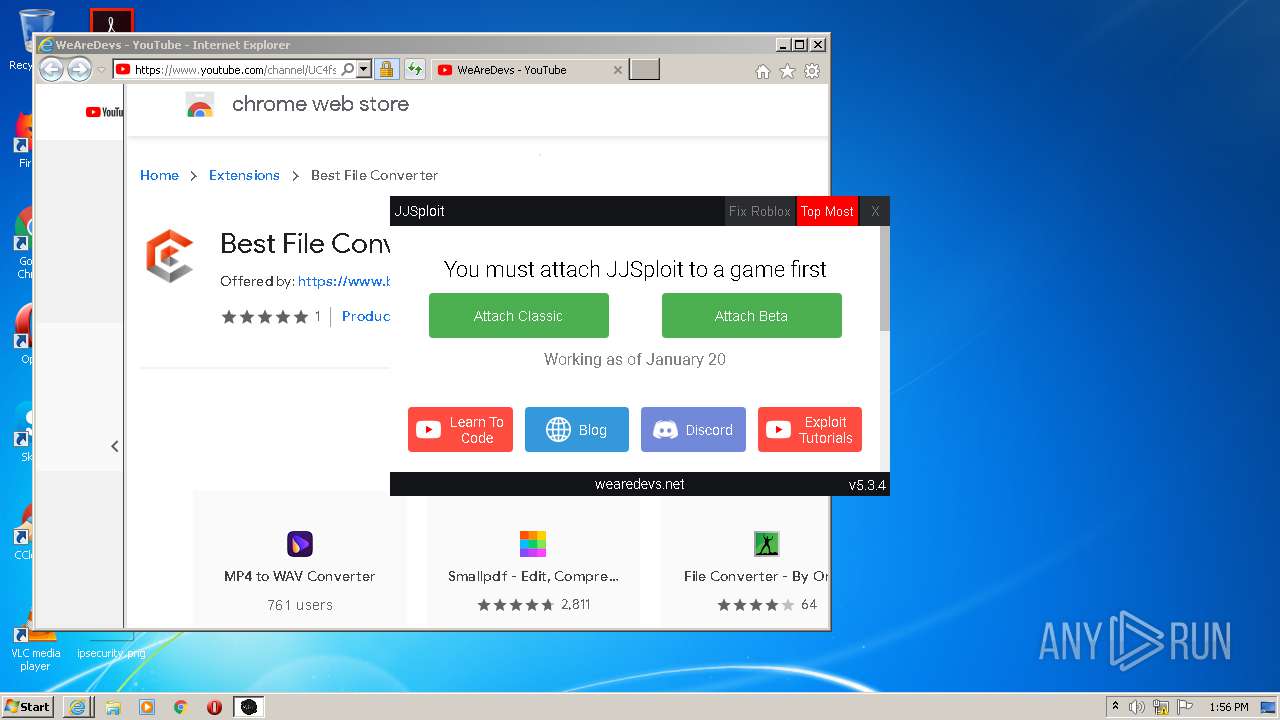
| download: | JJSploit |
| Full analysis: | https://app.any.run/tasks/7663a209-62ec-4086-a7c7-b7548ca726e6 |
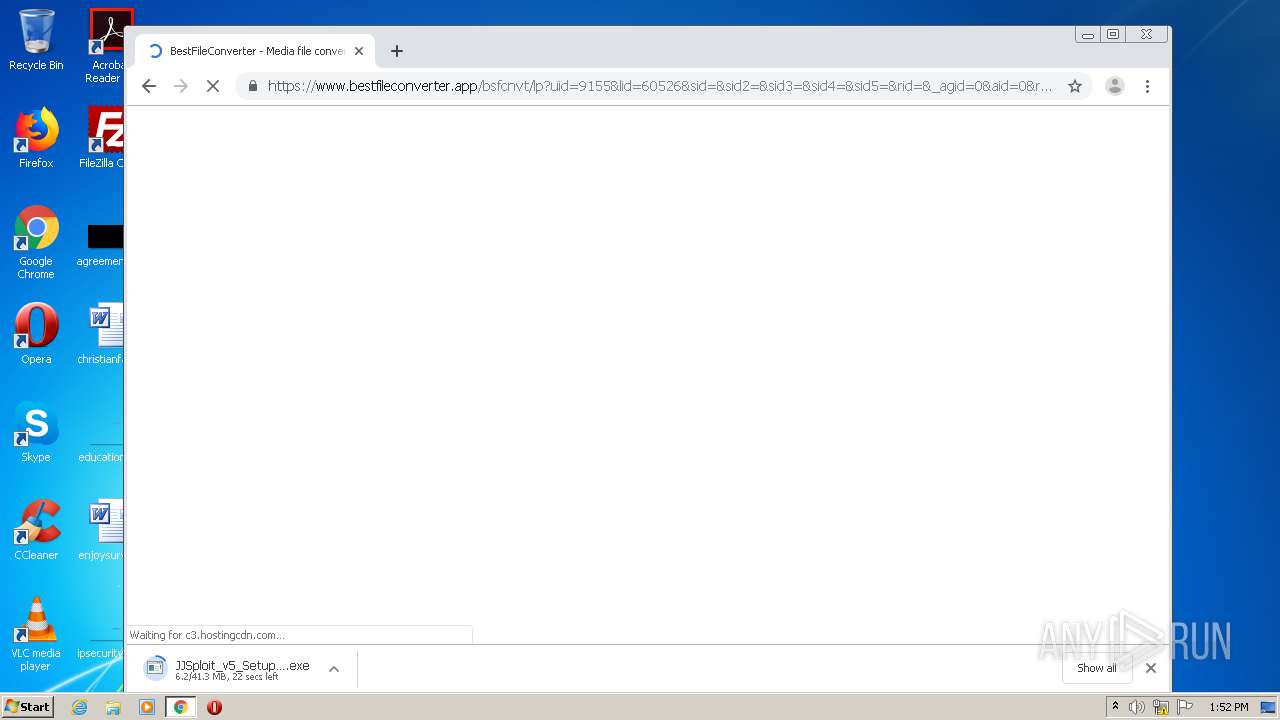
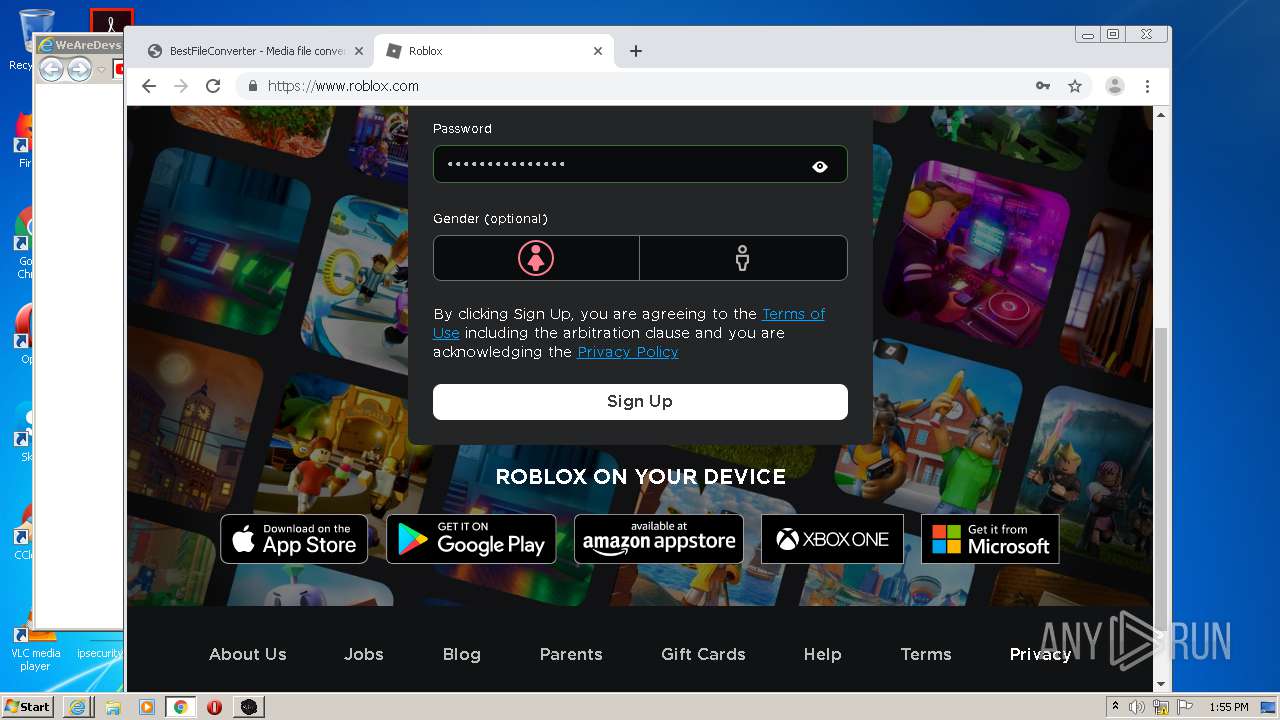
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2021, 13:51:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text |
| MD5: | 79AB48E63E06EA2542082659EEC2A05F |
| SHA1: | FC626E229556957315B73D959D2E2EA64B426533 |
| SHA256: | B014E3EE4B9FA9036AB2DE5D70D9EA2DB44FD18BC77E20B34666085066A04E24 |
| SSDEEP: | 384:4UWWlUkMmAxUeUmSEiRiT1UOUTVxWdJWDWimWiMStSimSiYSiksVGjfXMZE7jJpL:4lWlU7mgflS5YT1/8xWdJinmnMO7m7Yu |
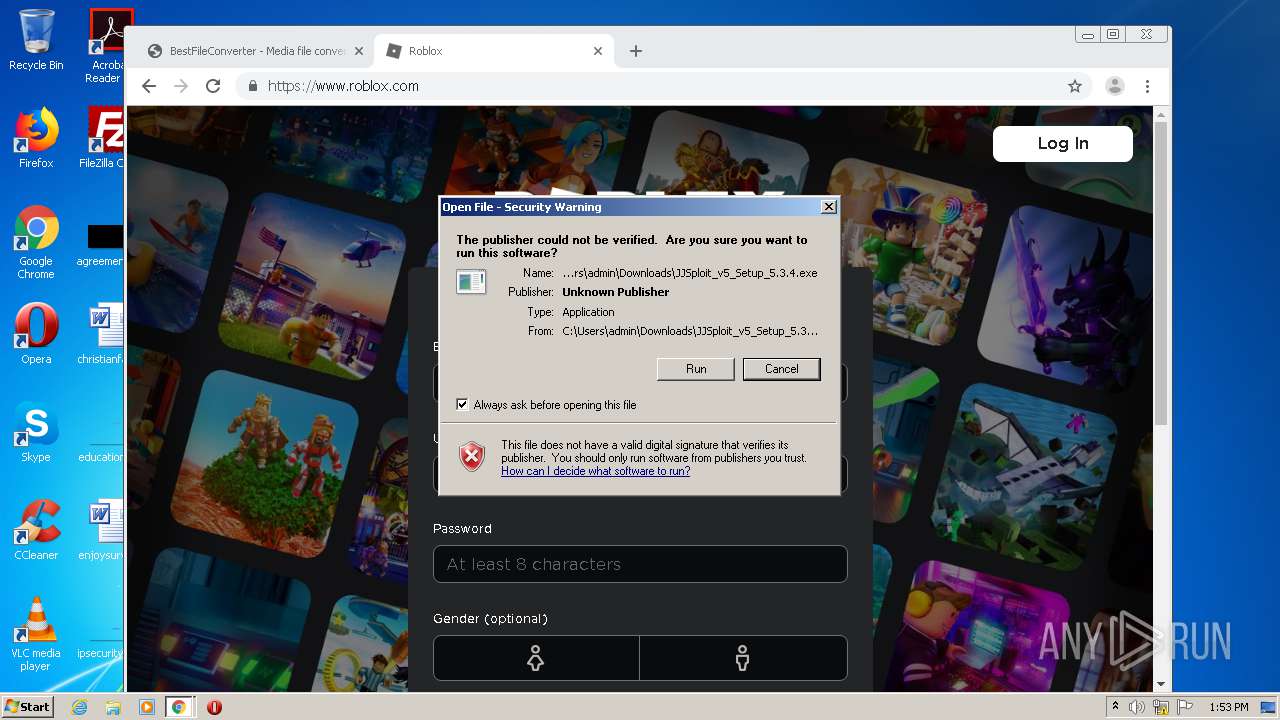
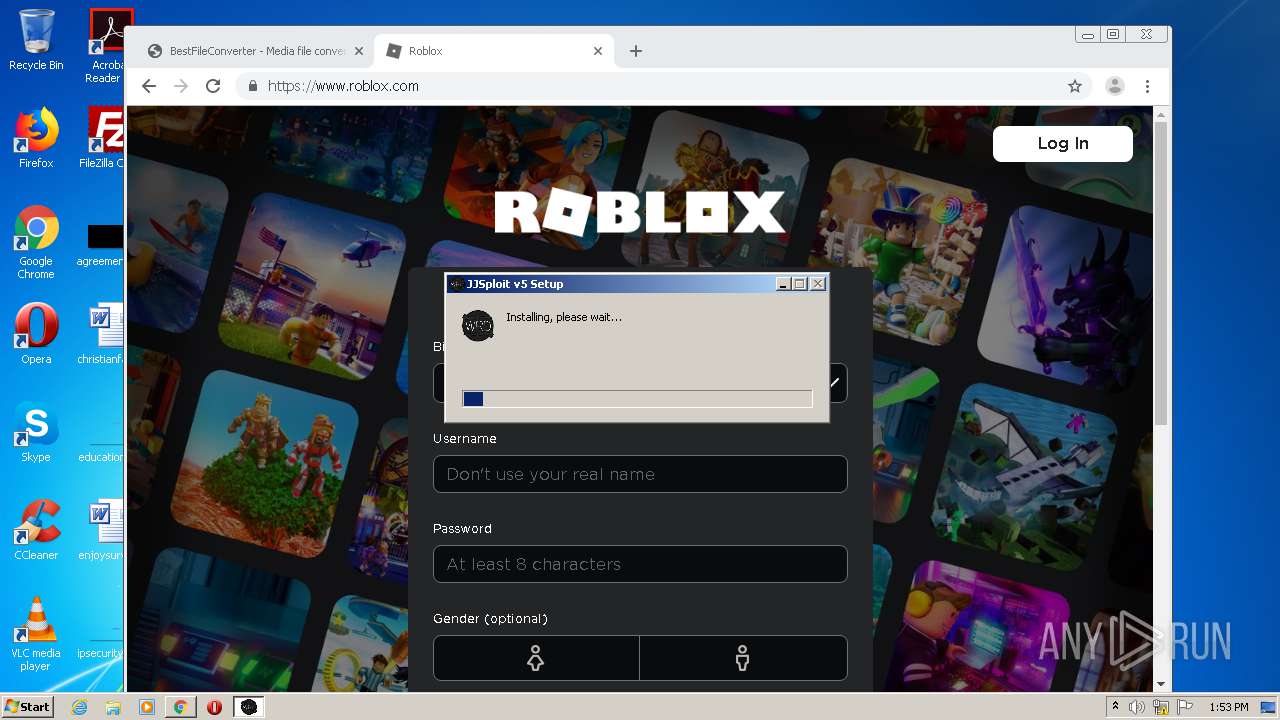
MALICIOUS
Loads dropped or rewritten executable
- JJSploit_v5_Setup_5.3.4.exe (PID: 2352)
- JJSploit v5.exe (PID: 3964)
- JJSploit v5.exe (PID: 1872)
- JJSploit v5.exe (PID: 3400)
Application was dropped or rewritten from another process
- JJSploit_v5_Setup_5.3.4.exe (PID: 2352)
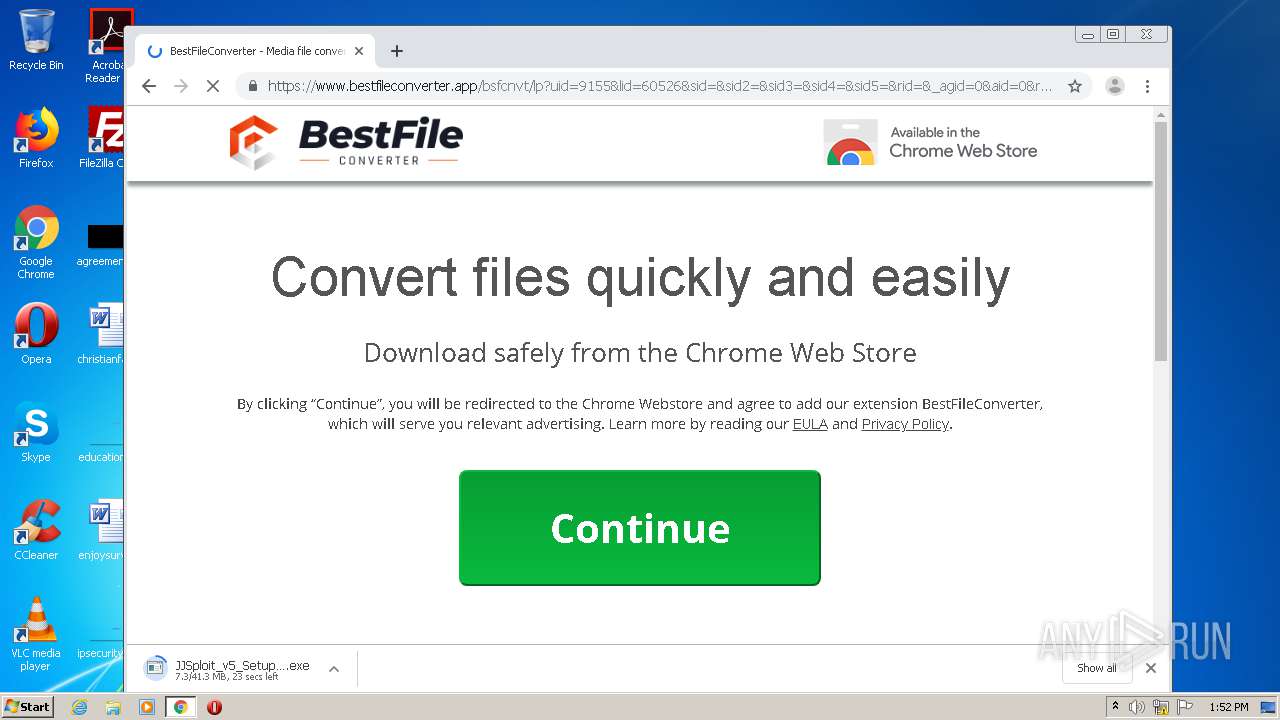
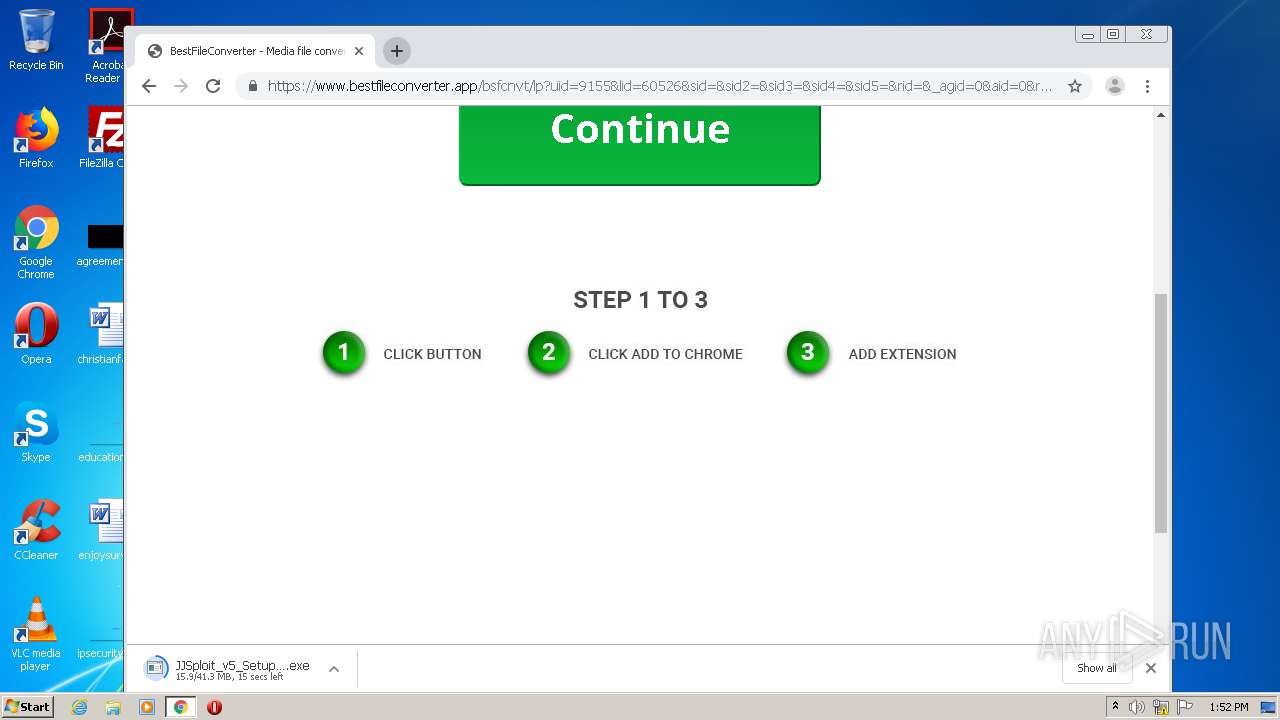
SUSPICIOUS
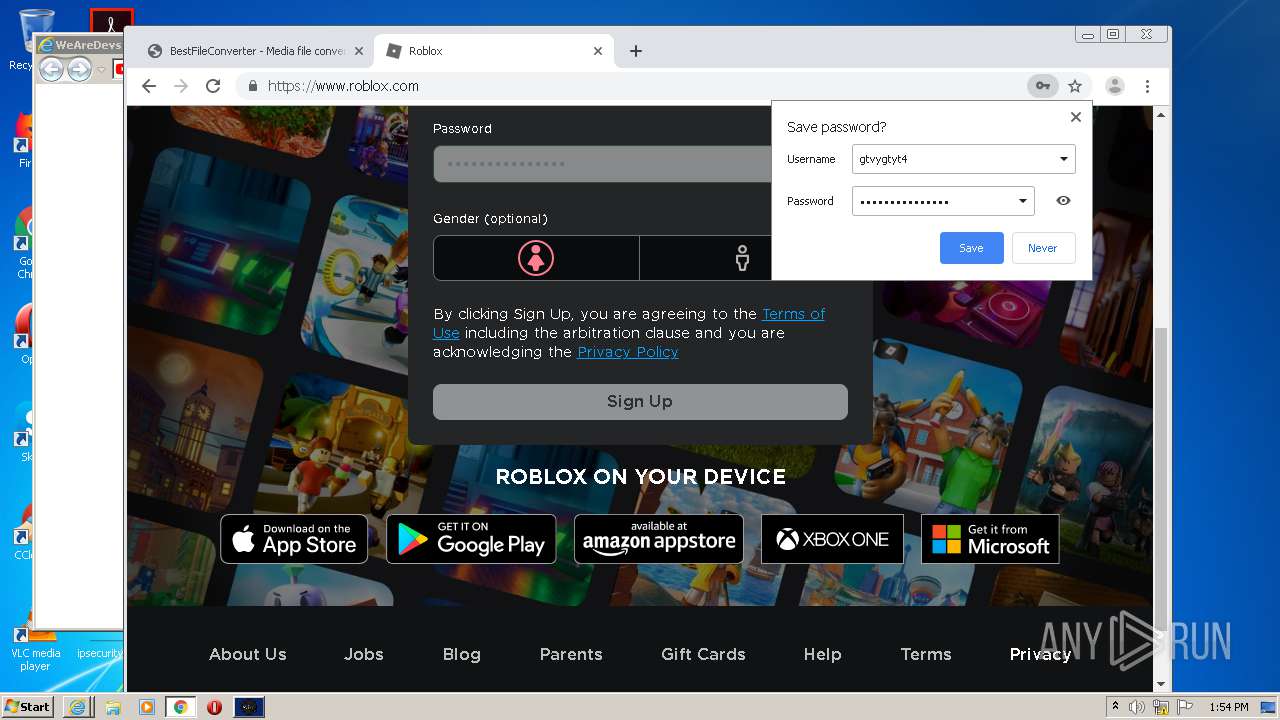
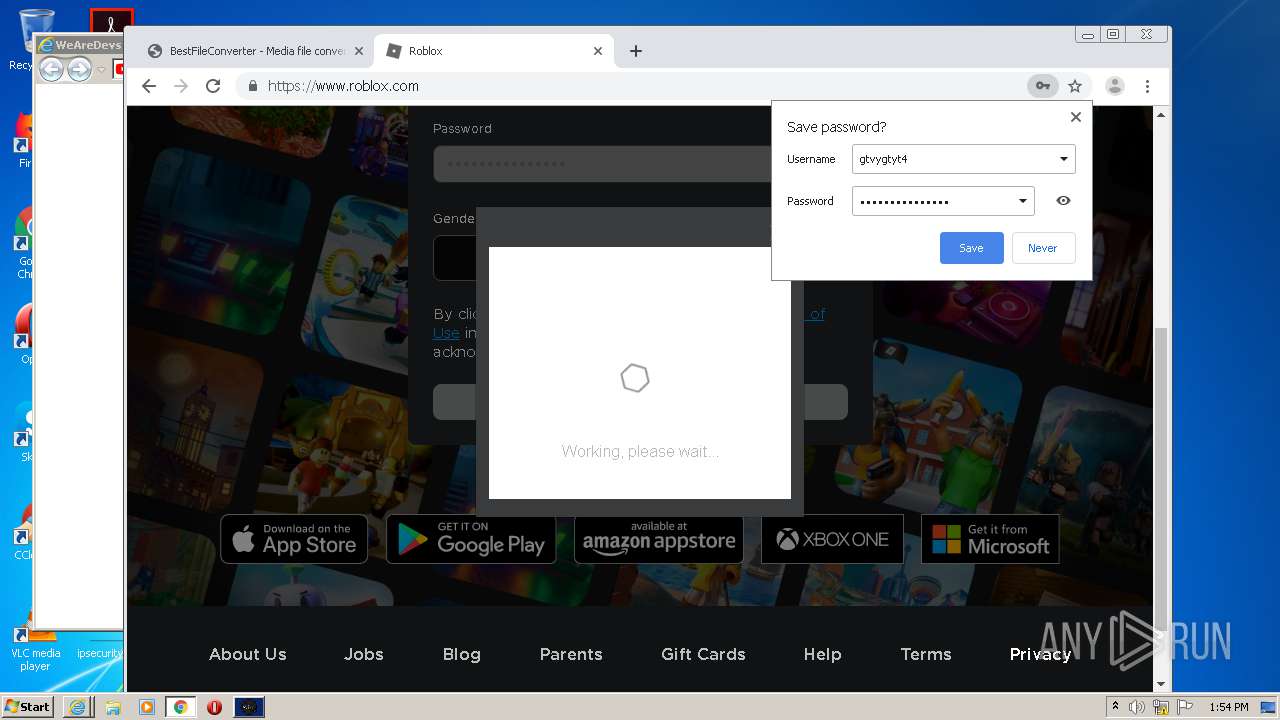
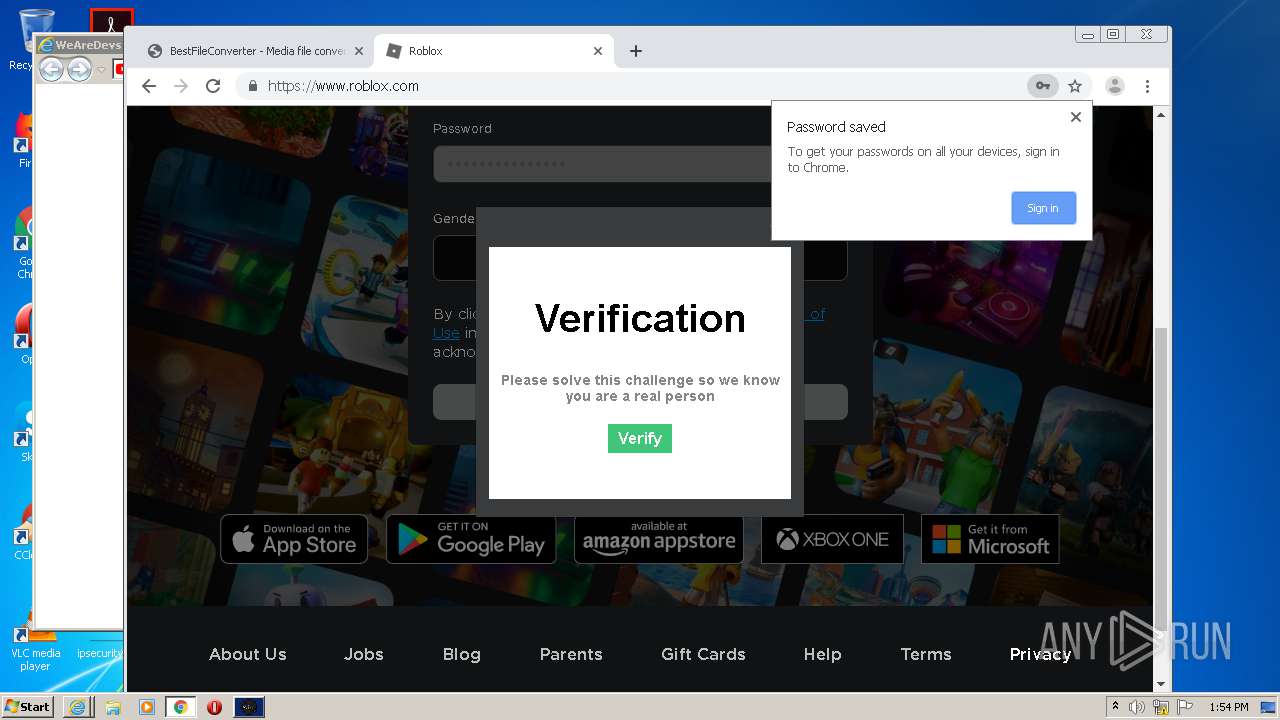
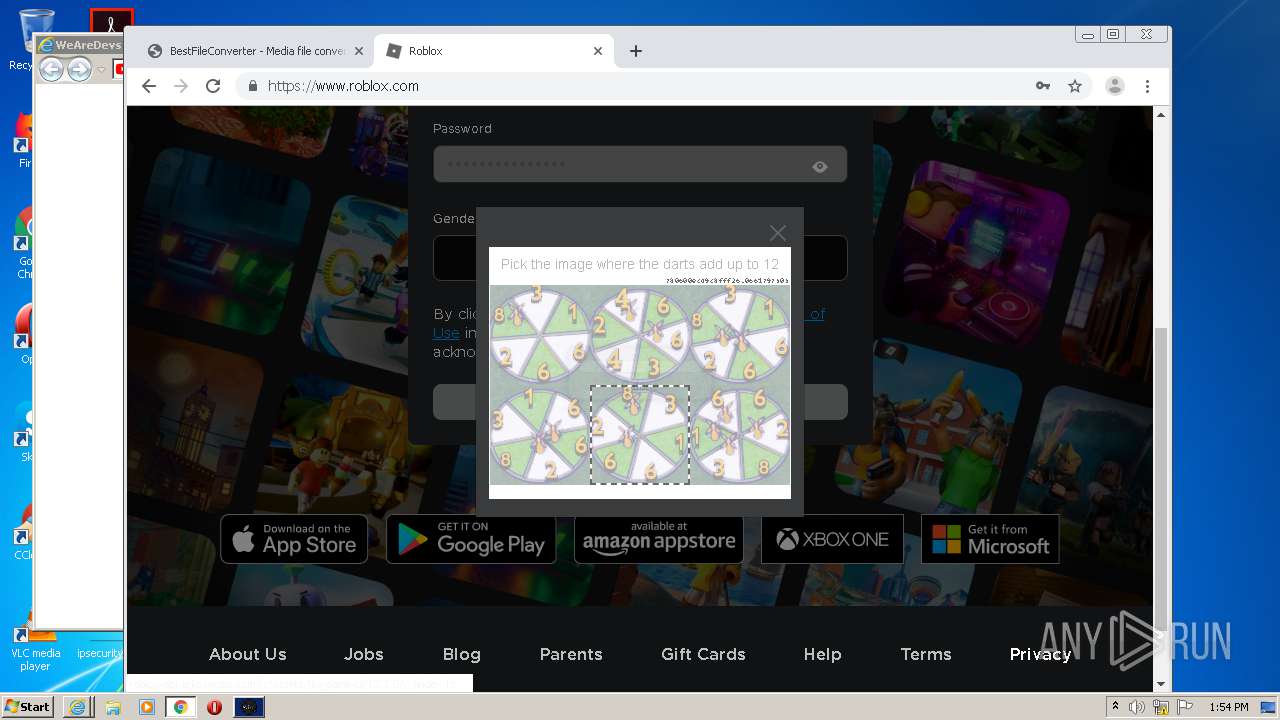
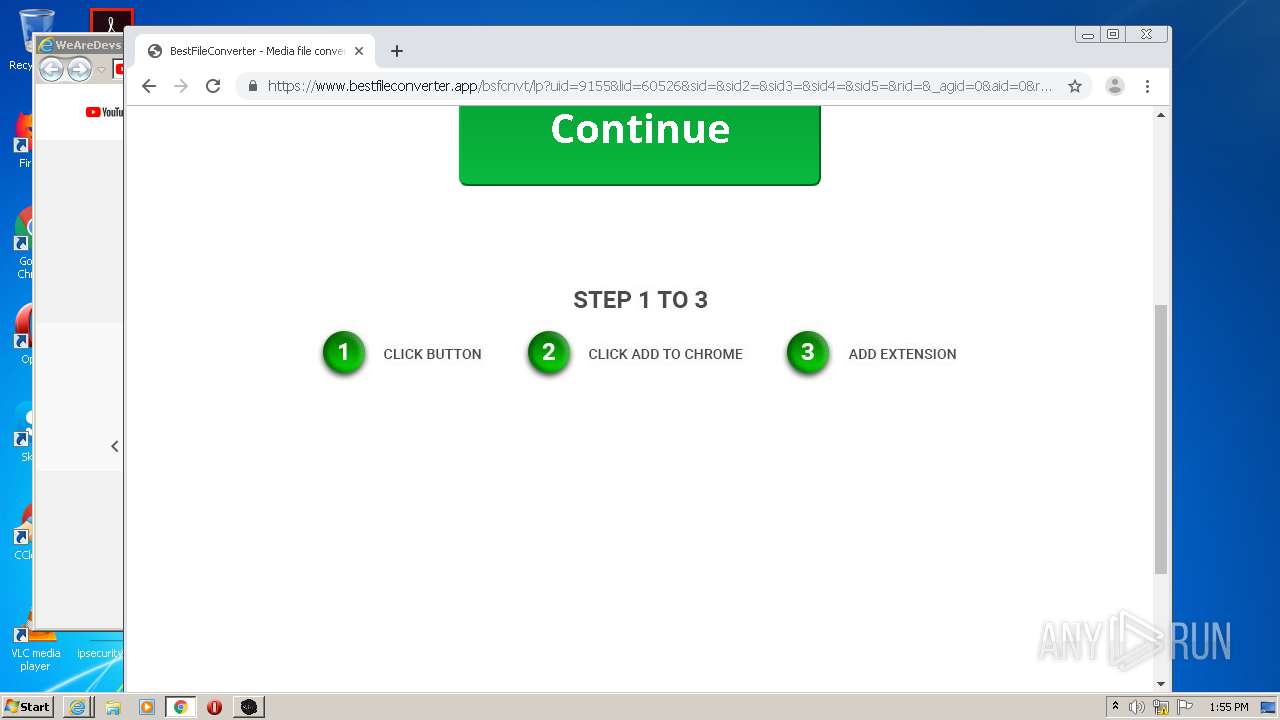
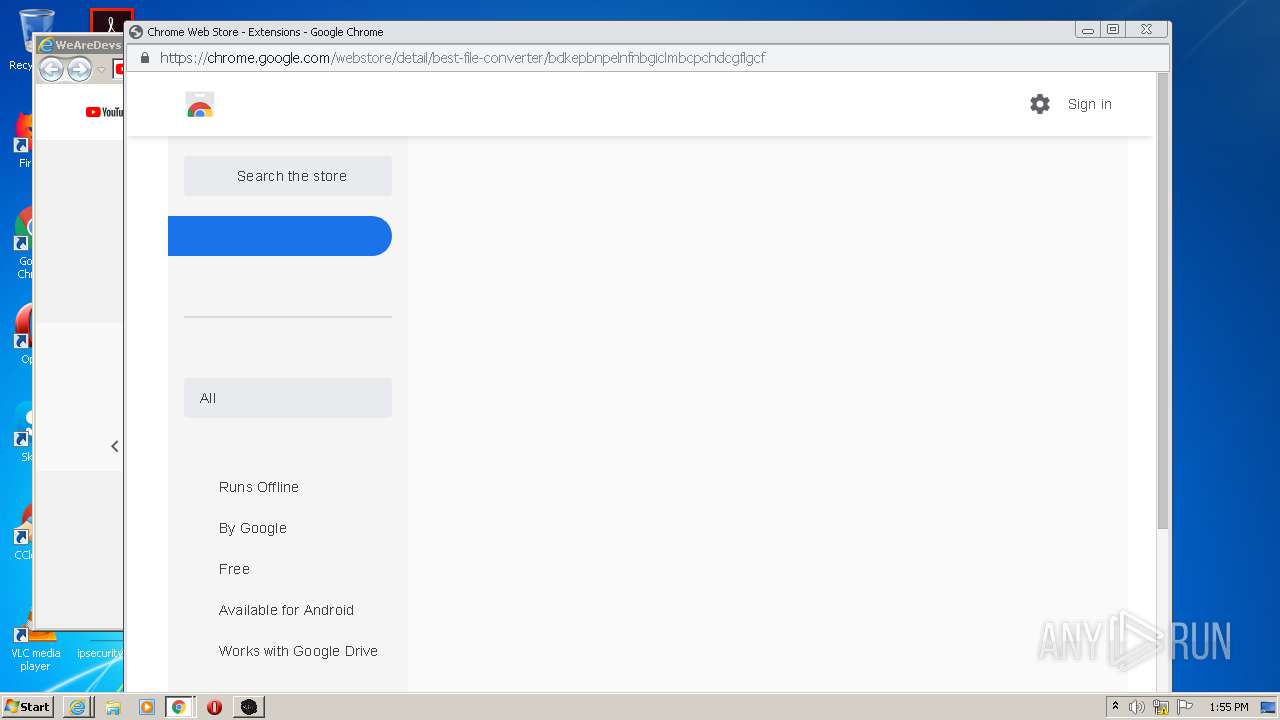
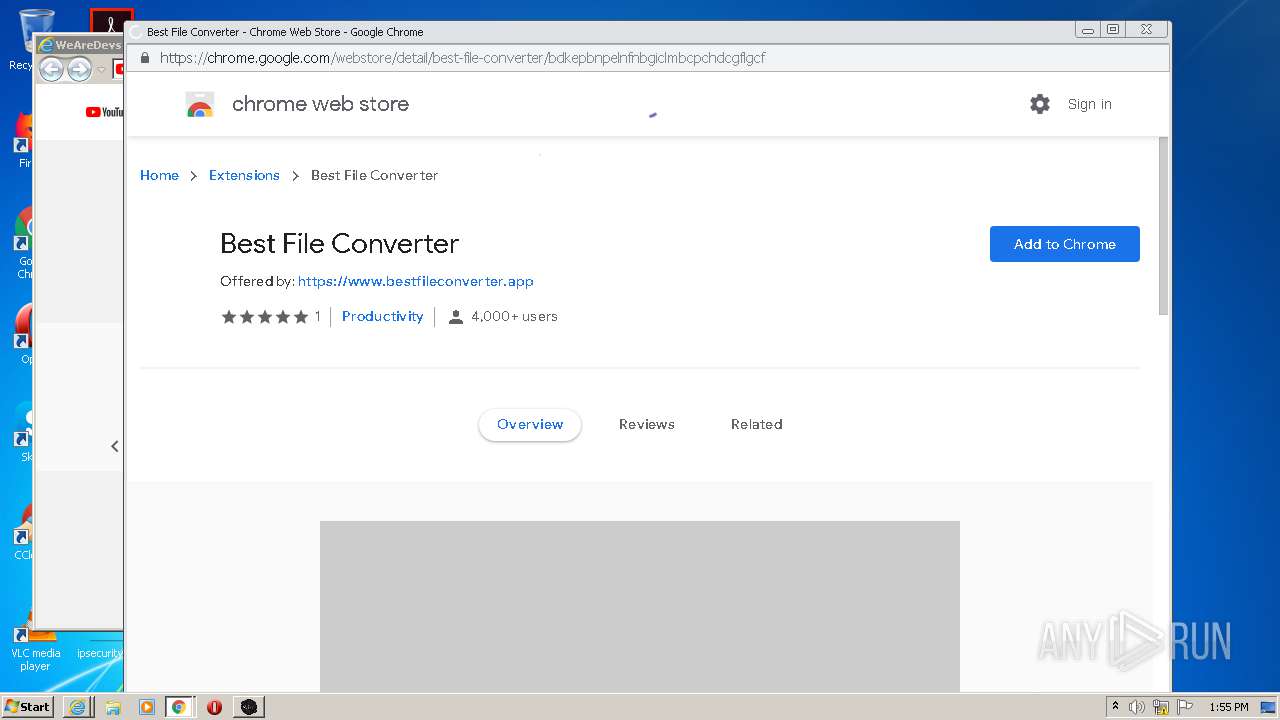
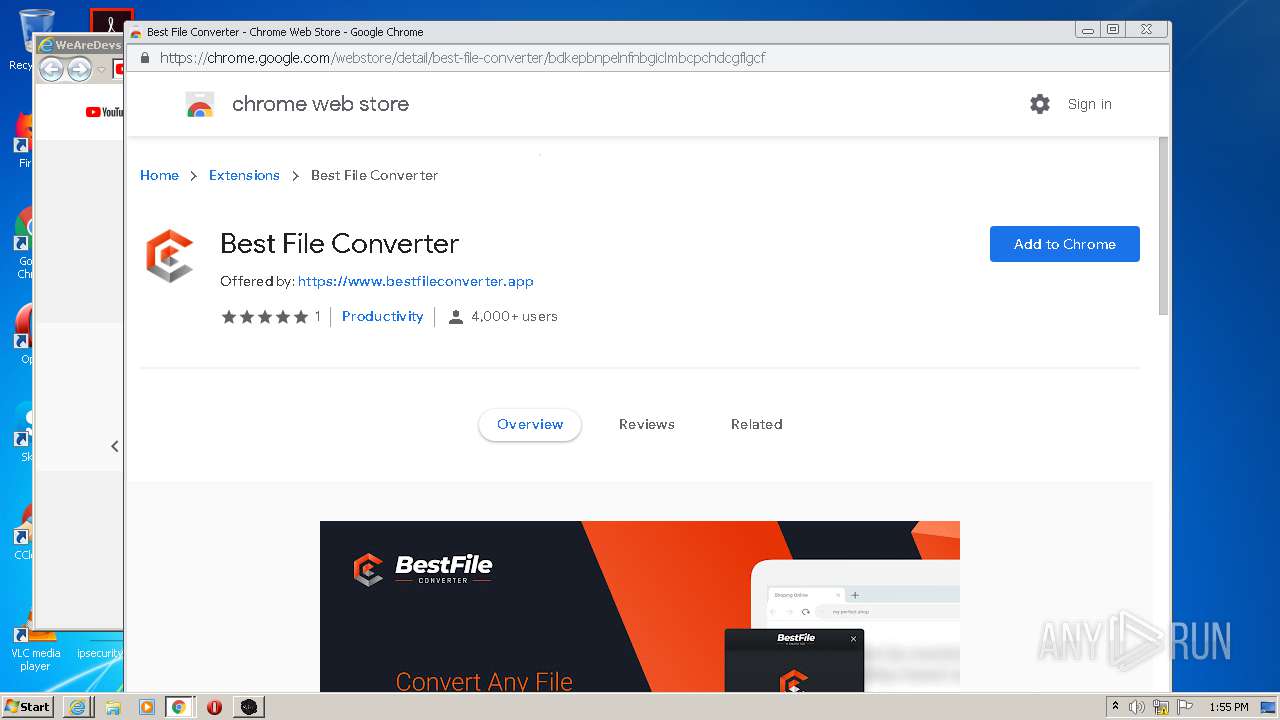
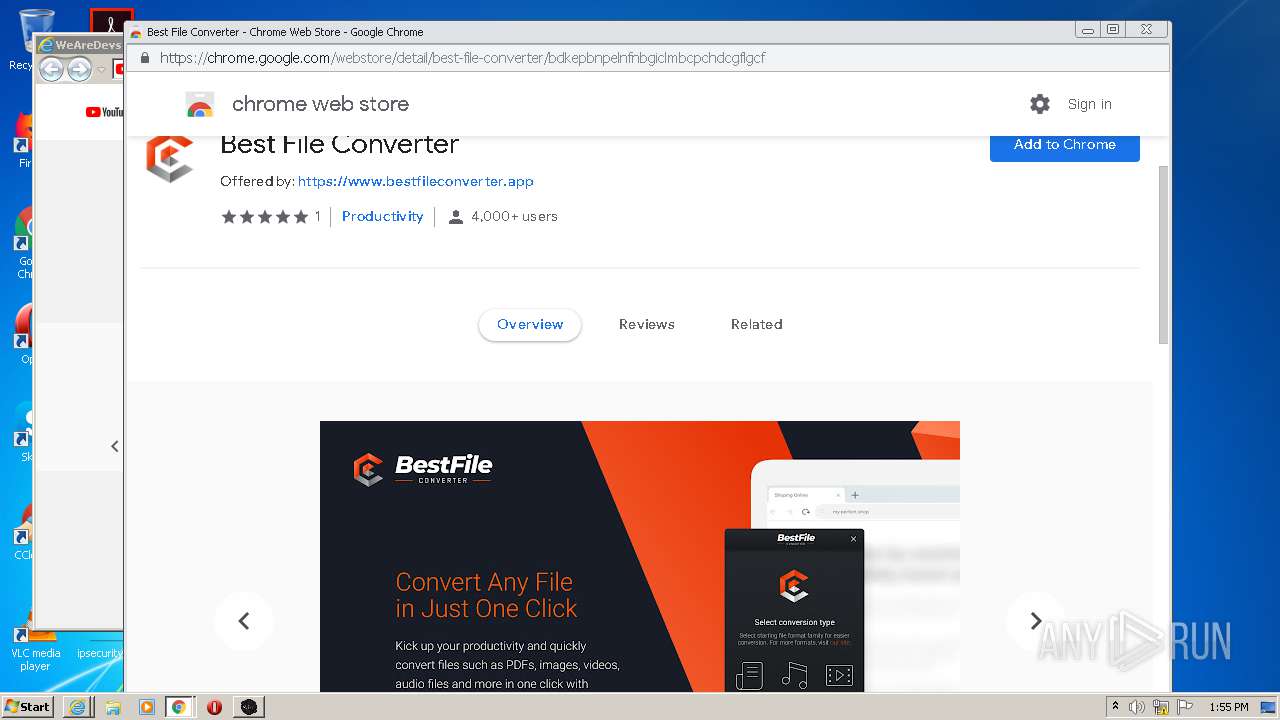
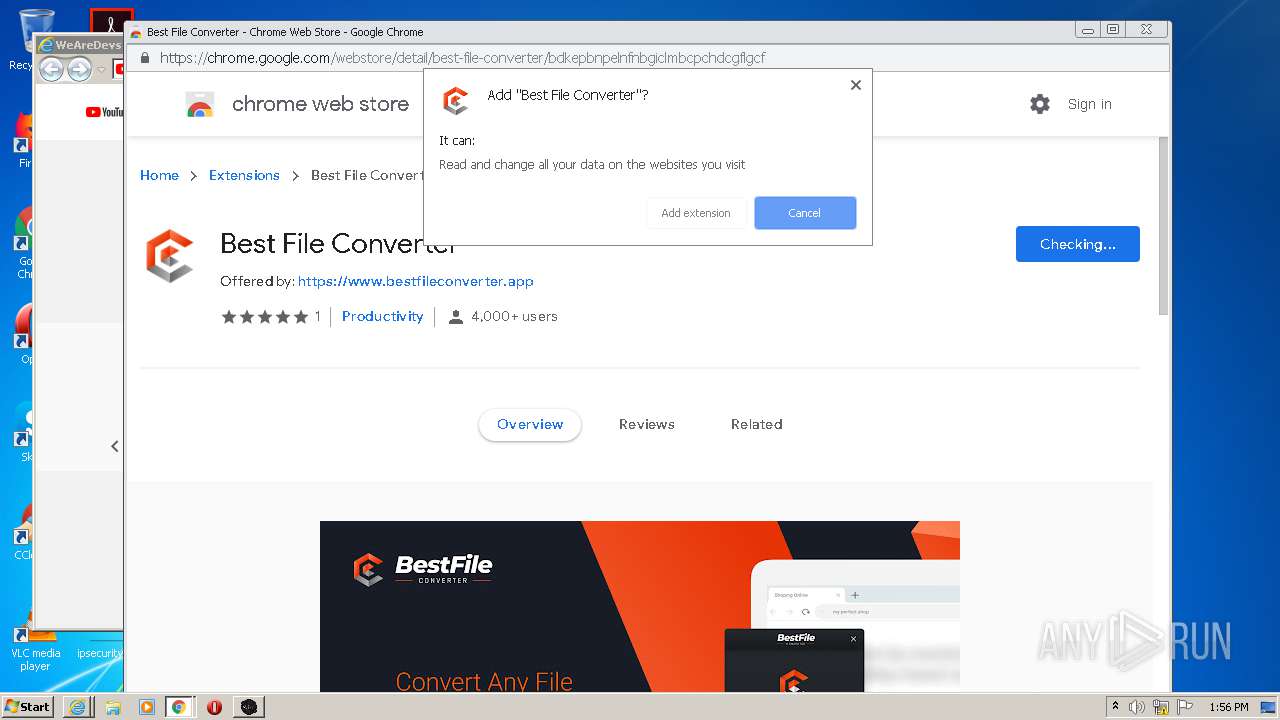
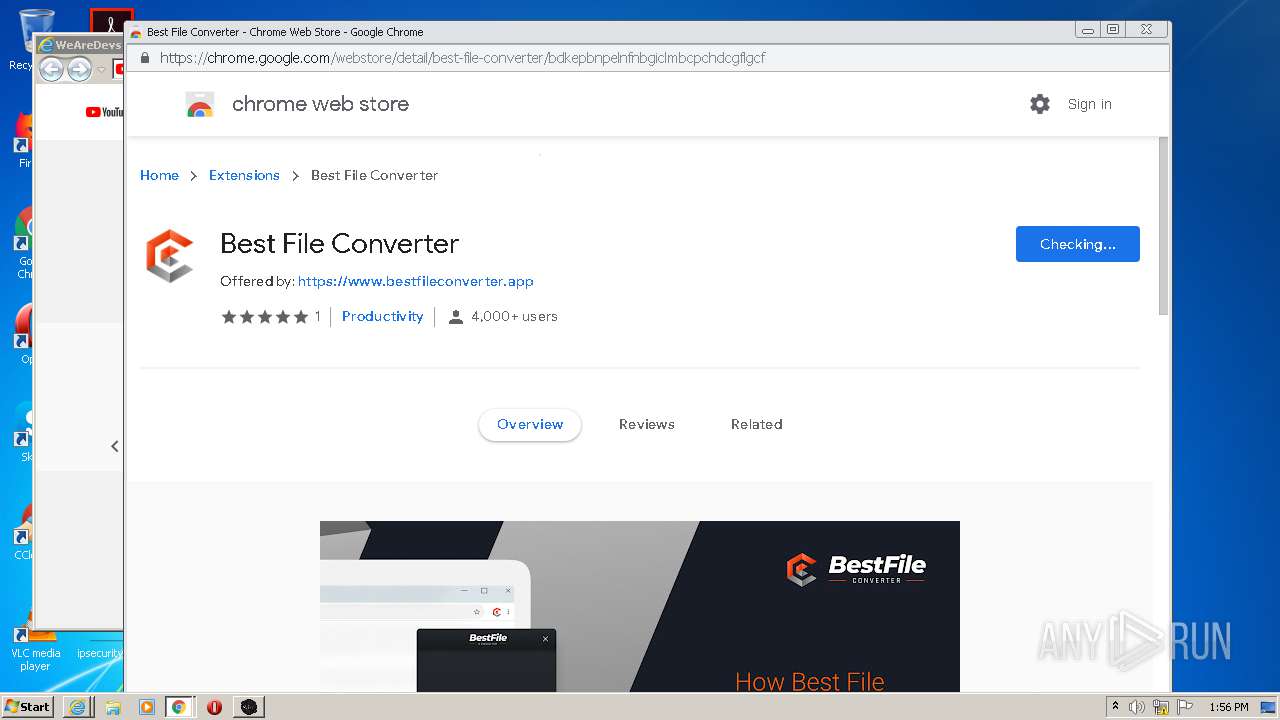
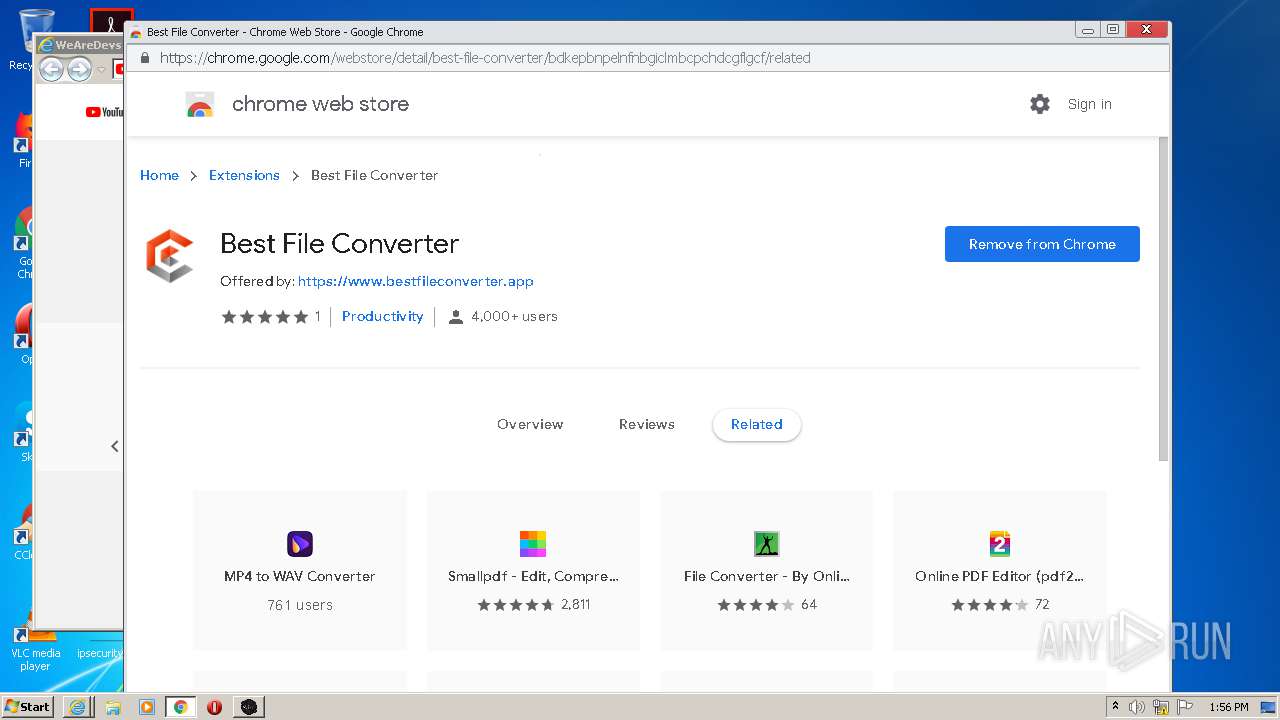
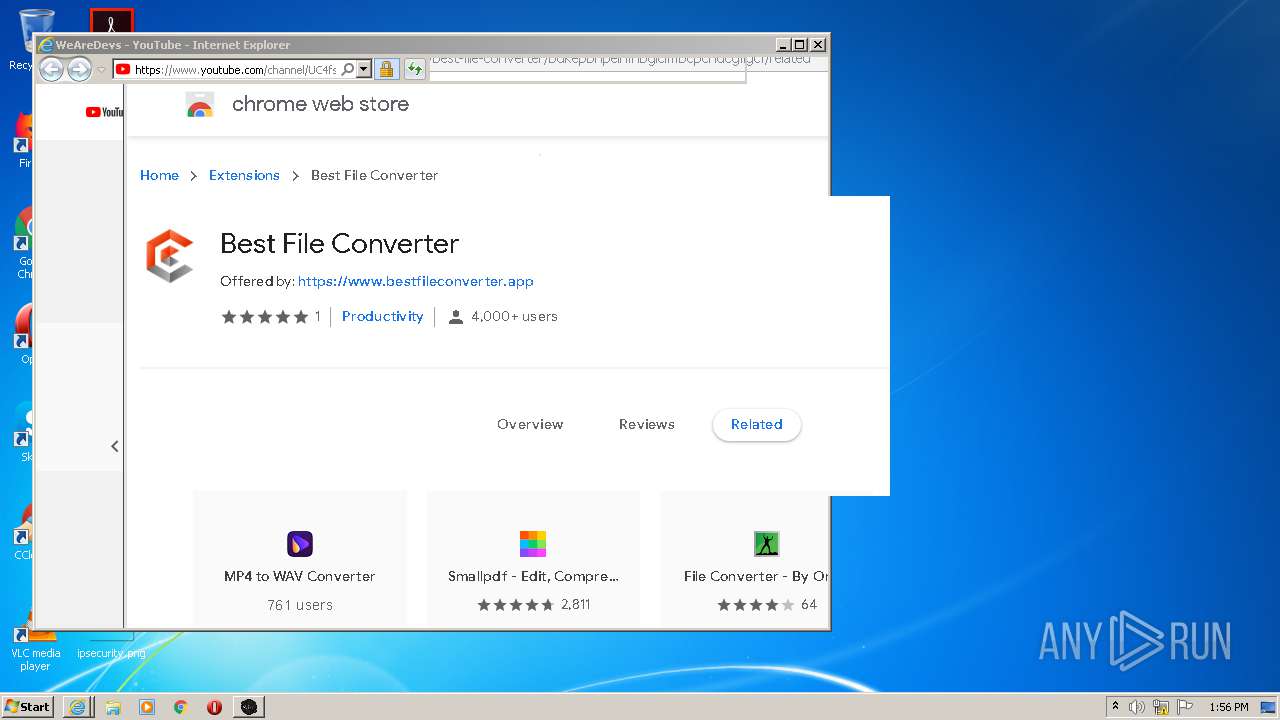
Modifies files in Chrome extension folder
- chrome.exe (PID: 3416)
Creates a software uninstall entry
- JJSploit_v5_Setup_5.3.4.exe (PID: 2352)
Executable content was dropped or overwritten
- chrome.exe (PID: 3416)
- JJSploit_v5_Setup_5.3.4.exe (PID: 2352)
- JJSploit v5.exe (PID: 3964)
Drops a file that was compiled in debug mode
- JJSploit_v5_Setup_5.3.4.exe (PID: 2352)
- JJSploit v5.exe (PID: 3964)
Creates files in the user directory
- JJSploit_v5_Setup_5.3.4.exe (PID: 2352)
- JJSploit v5.exe (PID: 3964)
Drops a file with too old compile date
- JJSploit_v5_Setup_5.3.4.exe (PID: 2352)
Application launched itself
- JJSploit v5.exe (PID: 3964)
Starts Internet Explorer
- JJSploit v5.exe (PID: 3964)
Drops a file with a compile date too recent
- JJSploit v5.exe (PID: 3964)
INFO
Application launched itself
- chrome.exe (PID: 3416)
- iexplore.exe (PID: 2768)
- iexplore.exe (PID: 2936)
Reads the hosts file
- chrome.exe (PID: 2880)
- chrome.exe (PID: 3416)
- JJSploit v5.exe (PID: 3964)
Reads settings of System Certificates
- chrome.exe (PID: 2880)
- iexplore.exe (PID: 668)
- iexplore.exe (PID: 2472)
- iexplore.exe (PID: 2936)
- iexplore.exe (PID: 2768)
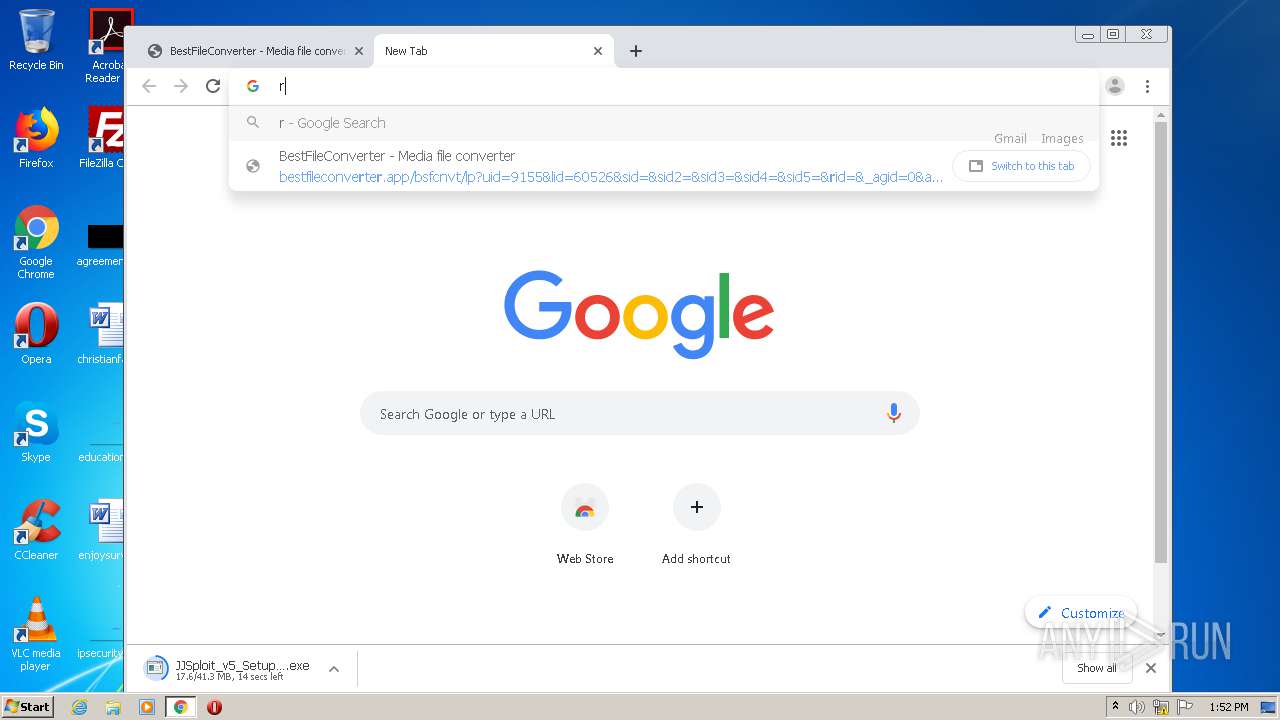
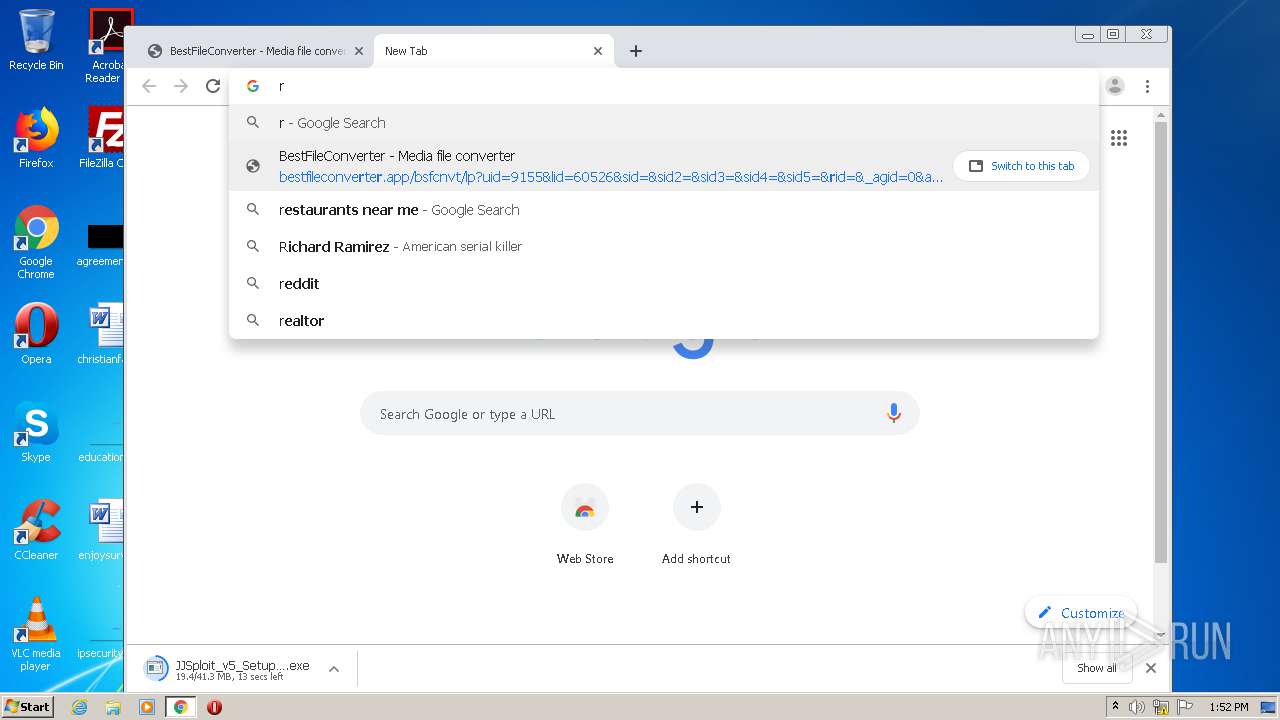
Manual execution by user
- chrome.exe (PID: 3416)
- JJSploit v5.exe (PID: 3964)
Changes internet zones settings
- iexplore.exe (PID: 2936)
- iexplore.exe (PID: 2768)
Creates files in the user directory
- iexplore.exe (PID: 668)
- iexplore.exe (PID: 2472)
- iexplore.exe (PID: 2936)
- chrome.exe (PID: 3416)
Reads internet explorer settings
- iexplore.exe (PID: 2472)
- iexplore.exe (PID: 668)
Changes settings of System certificates
- iexplore.exe (PID: 2936)
- iexplore.exe (PID: 2768)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2936)
- iexplore.exe (PID: 2768)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| viewport: | width=device-width, initial-scale=1, shrink-to-fit=no, maximum-scale=1, user-scalable=0 |
|---|---|
| Keywords: | JJSploit, Exploits, dll, hacks, cheats, developers, social, media |
| Description: | JJSploit download - Offers a near full Lua executor, click teleport, ESP, speed, fly, infinite jump, and so much more. A powerful all in one package. |
| Title: | JJSploit Download - WeAreDevs |
Total processes
110
Monitored processes
69
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2936 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,17227605587891407142,3830697807787597724,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12777919712591128459 --mojo-platform-channel-handle=2848 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,17227605587891407142,3830697807787597724,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7834938980958430145 --mojo-platform-channel-handle=4168 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,17227605587891407142,3830697807787597724,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17237007785318950681 --mojo-platform-channel-handle=4280 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,17227605587891407142,3830697807787597724,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8783658665146016365 --mojo-platform-channel-handle=3920 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,17227605587891407142,3830697807787597724,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16129670543325461986 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,17227605587891407142,3830697807787597724,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7925965703608965058 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,17227605587891407142,3830697807787597724,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13740370140623816674 --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4396 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,17227605587891407142,3830697807787597724,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17573313399058116120 --mojo-platform-channel-handle=3572 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,17227605587891407142,3830697807787597724,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12477279341036055765 --mojo-platform-channel-handle=3392 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 838
Read events
2 429
Write events
396
Delete events
13
Modification events
| (PID) Process: | (2392) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2392) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2392) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2392) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2392) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2392) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2392) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2392) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (2392) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (2392) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
21
Suspicious files
334
Text files
467
Unknown types
142
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-600ECCF4-D58.pma | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2a55138d-cd81-4df1-a4c0-6bcac47fb66e.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF155ffc.TMP | text | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF15601b.TMP | text | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1561b1.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
156
DNS requests
112
Threats
3 105
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
668 | iexplore.exe | GET | — | 172.217.21.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | — | — | whitelisted |
2472 | iexplore.exe | GET | — | 172.217.21.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | — | — | whitelisted |
668 | iexplore.exe | GET | — | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDHLJeKVKvb%2BAwAAAADHzUc%3D | US | — | — | whitelisted |
668 | iexplore.exe | GET | — | 172.217.21.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | — | — | whitelisted |
2472 | iexplore.exe | GET | — | 172.217.21.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | — | — | whitelisted |
668 | iexplore.exe | GET | — | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDHLJeKVKvb%2BAwAAAADHzUc%3D | US | — | — | whitelisted |
2472 | iexplore.exe | GET | — | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDHLJeKVKvb%2BAwAAAADHzUc%3D | US | — | — | whitelisted |
668 | iexplore.exe | GET | — | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCSph7JeRt7BgMAAAAAx82r | US | — | — | whitelisted |
2472 | iexplore.exe | GET | — | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCQs%2FPAqUkFkgUAAAAAhY%2FM | US | — | — | whitelisted |
668 | iexplore.exe | GET | — | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCSph7JeRt7BgMAAAAAx82r | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2880 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2880 | chrome.exe | 66.102.1.95:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 216.58.212.142:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2880 | chrome.exe | 216.58.210.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.16.206:443 | ogs.google.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 216.58.212.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.23.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
ogs.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2880 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED invalid ack |
2880 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM Packet with invalid ack |
2880 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
2880 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED invalid ack |
2880 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM Packet with invalid ack |
2880 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
2880 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
2880 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED invalid ack |
2880 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM Packet with invalid ack |
2880 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |