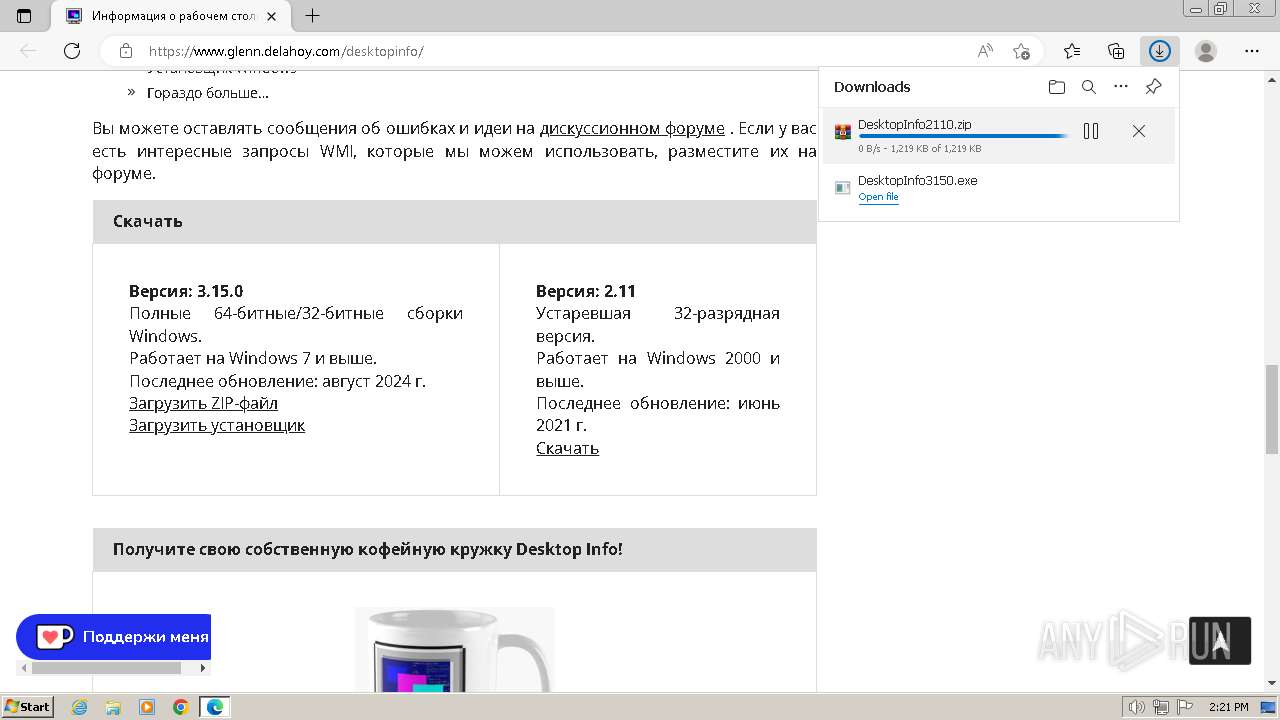
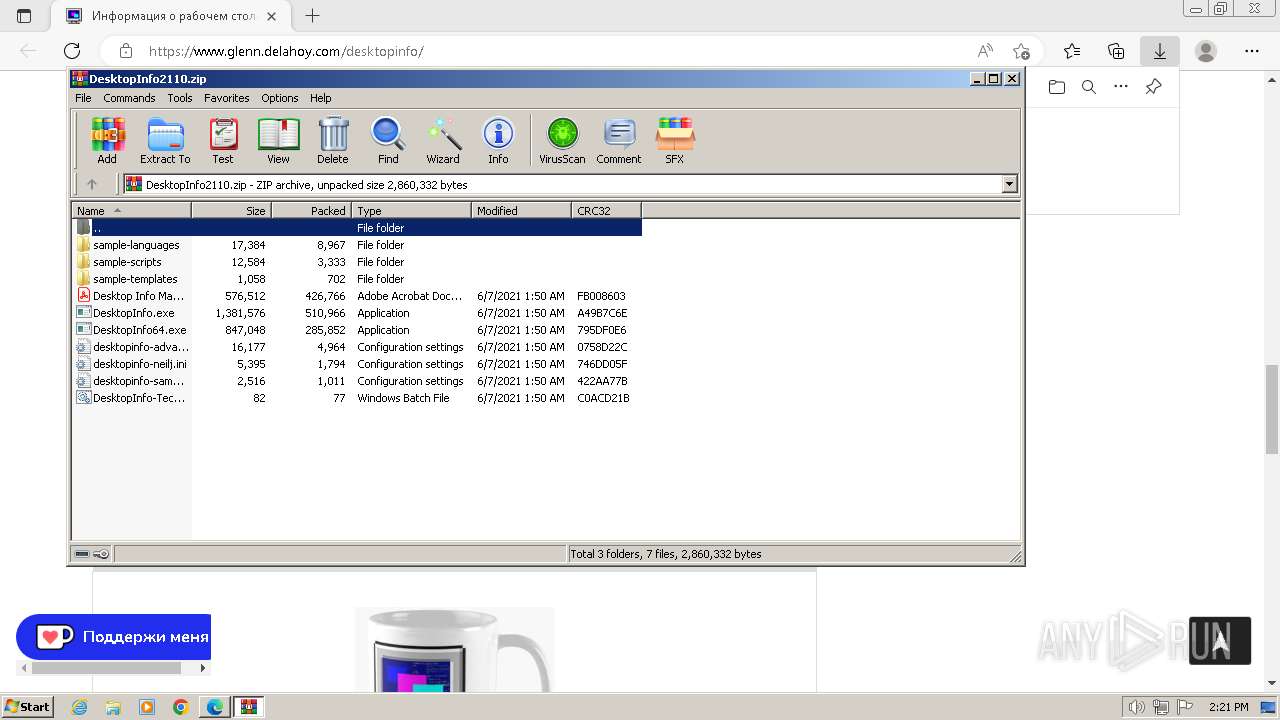
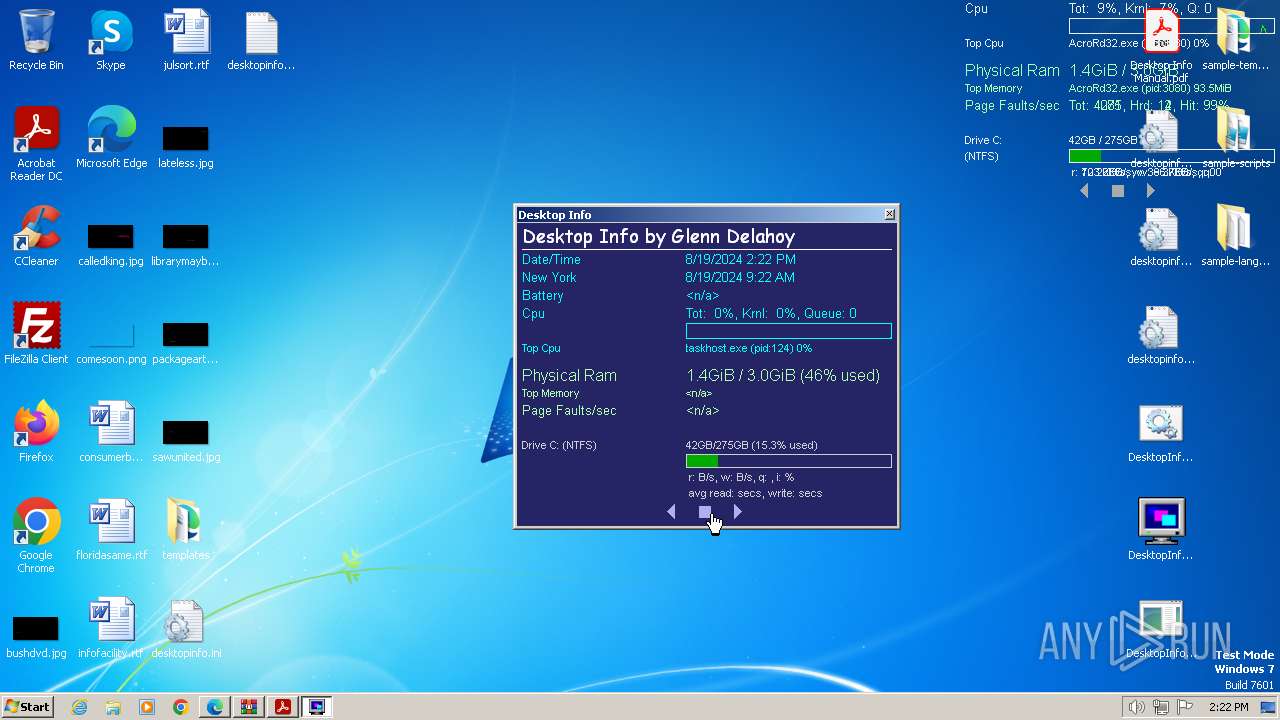
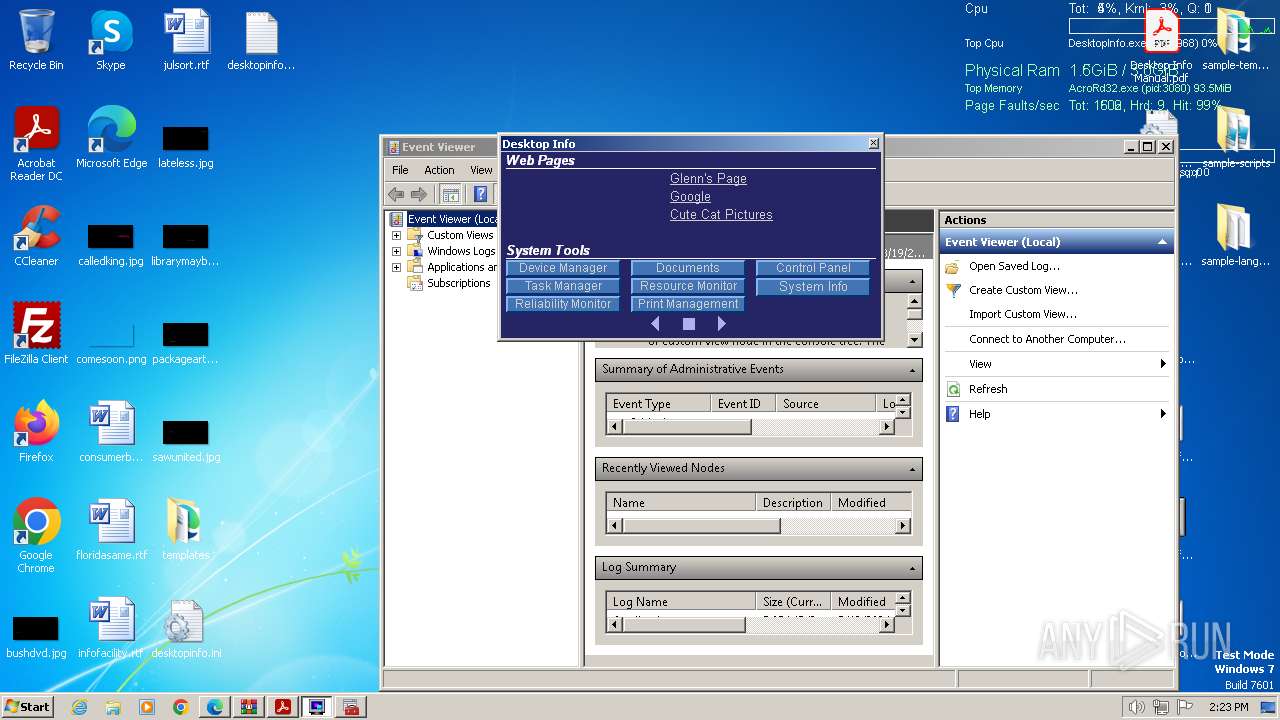
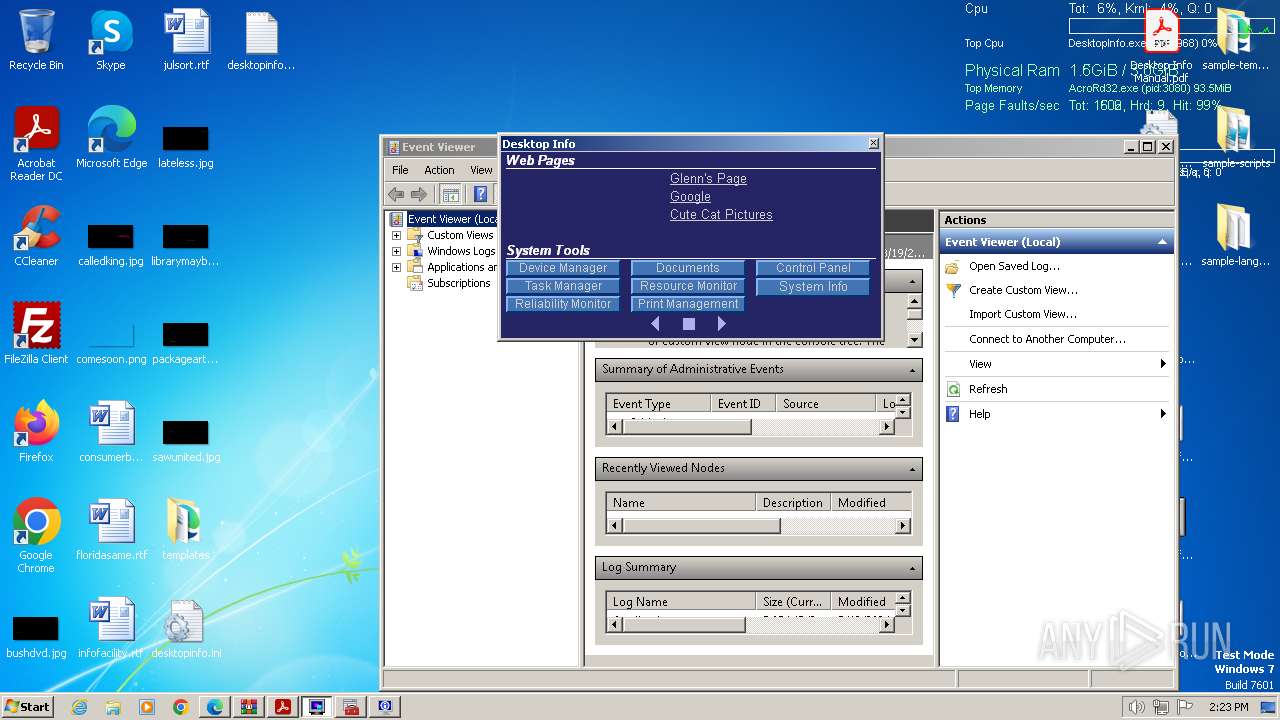
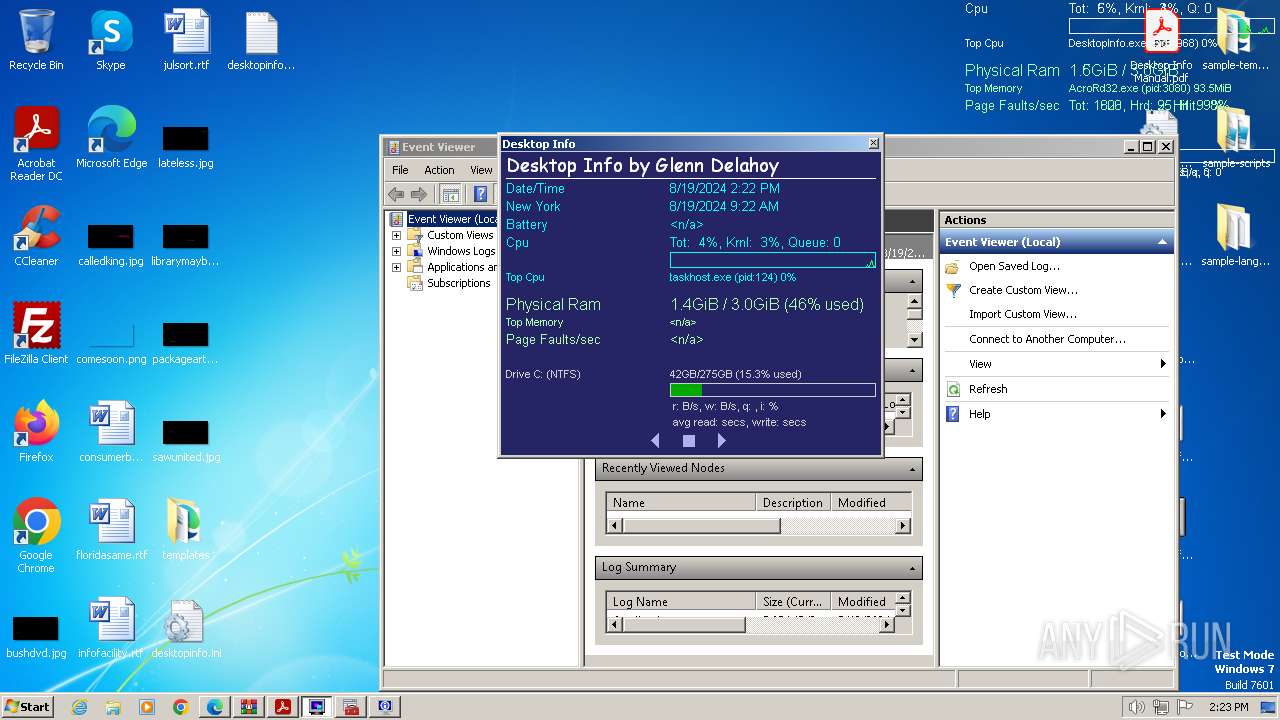
| URL: | https://www.glenn.delahoy.com/desktopinfo/ |
| Full analysis: | https://app.any.run/tasks/9003c50e-1a9a-4683-8d9e-4560d400d5cb |
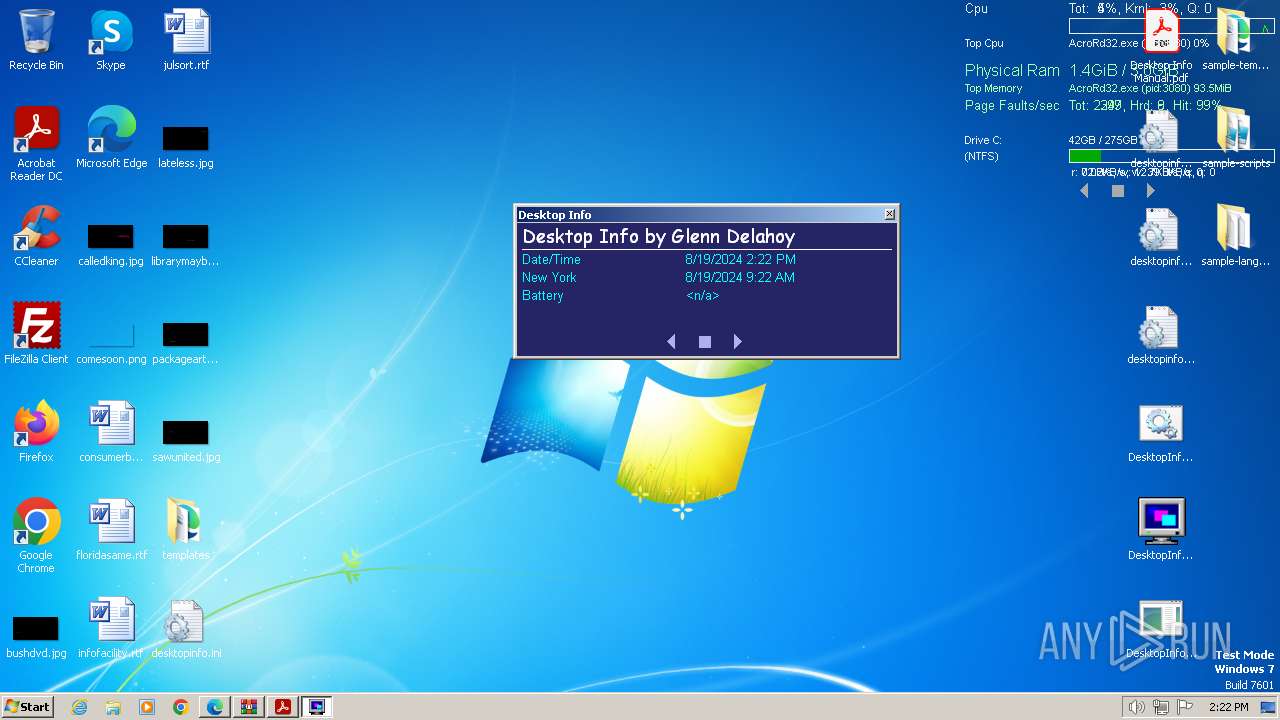
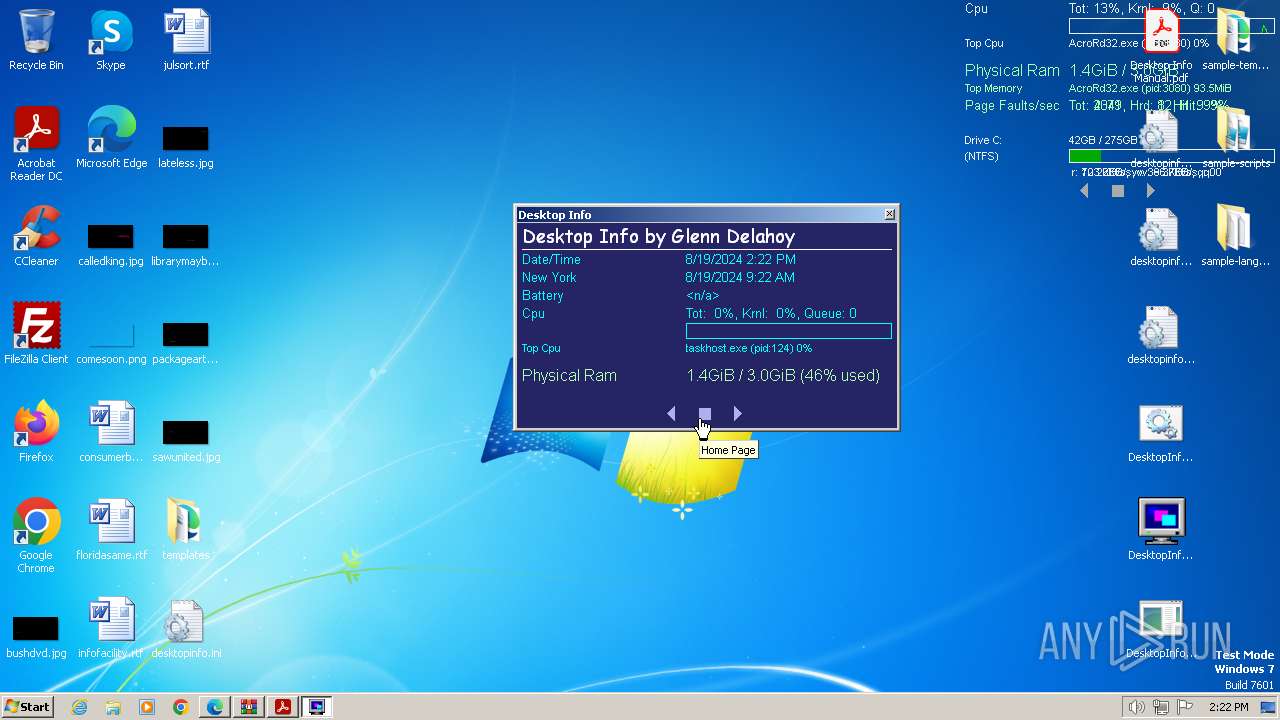
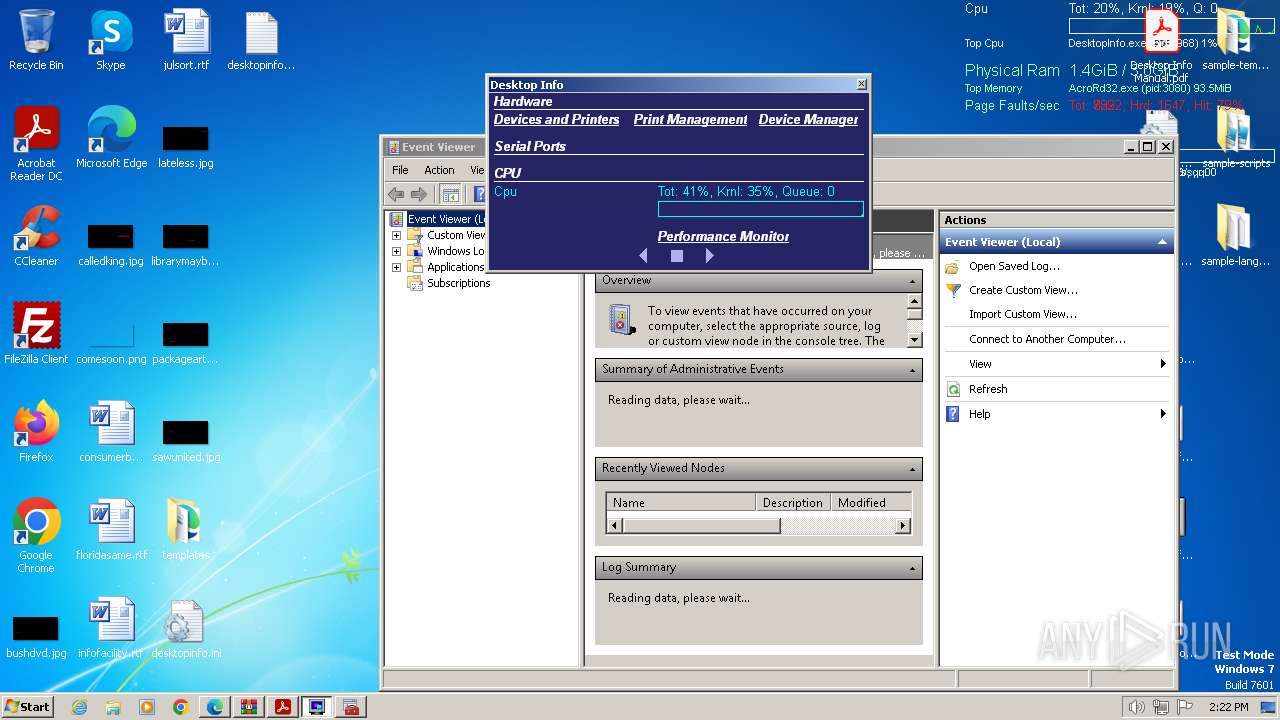
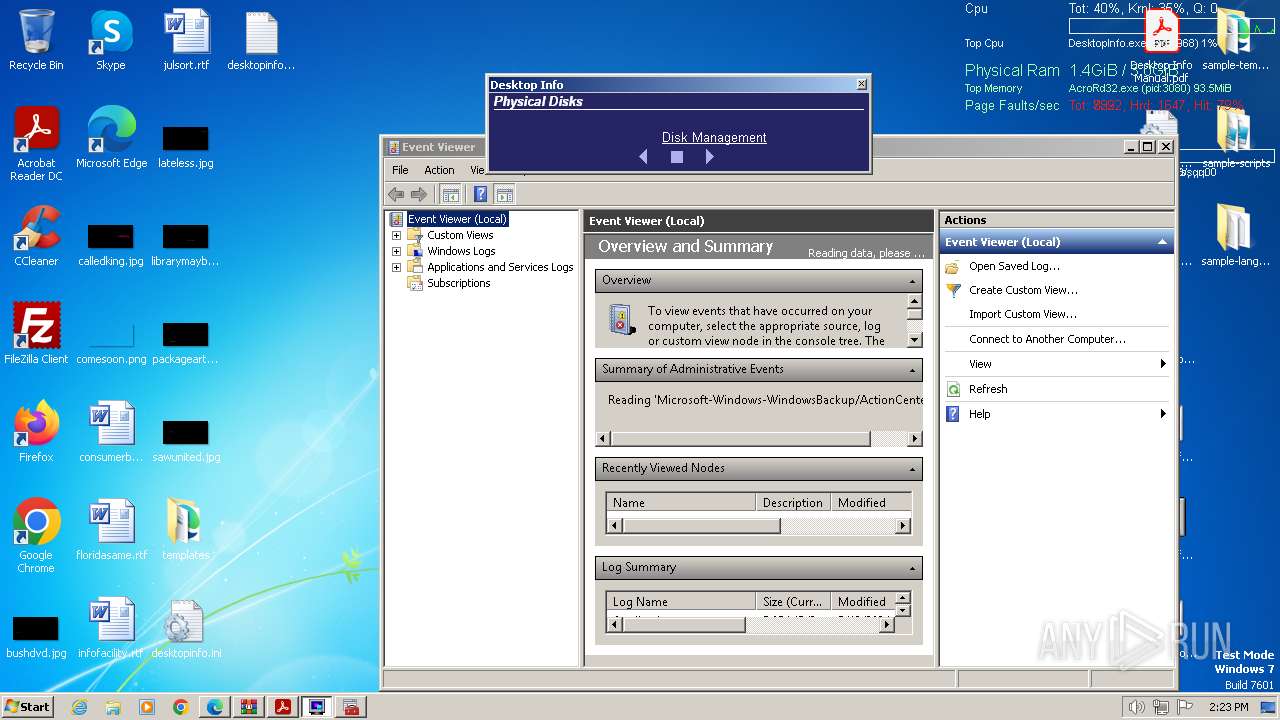
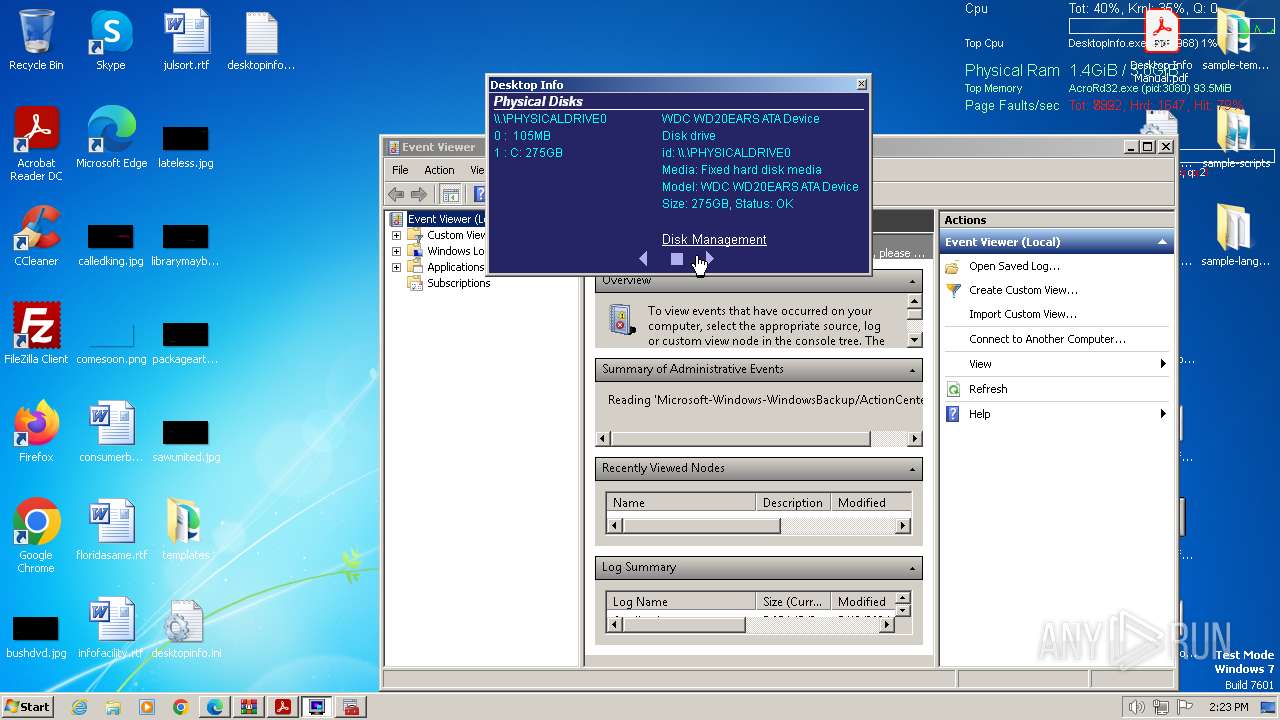
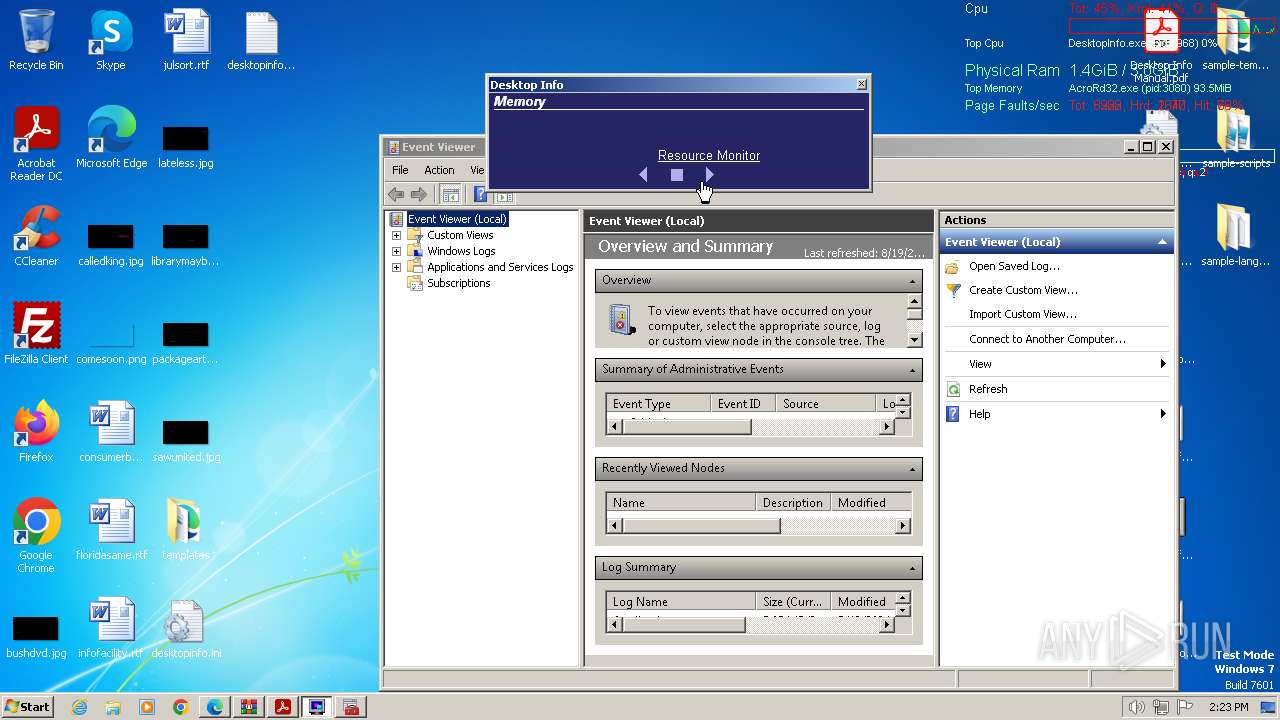
| Verdict: | Malicious activity |
| Analysis date: | August 19, 2024, 13:20:09 |
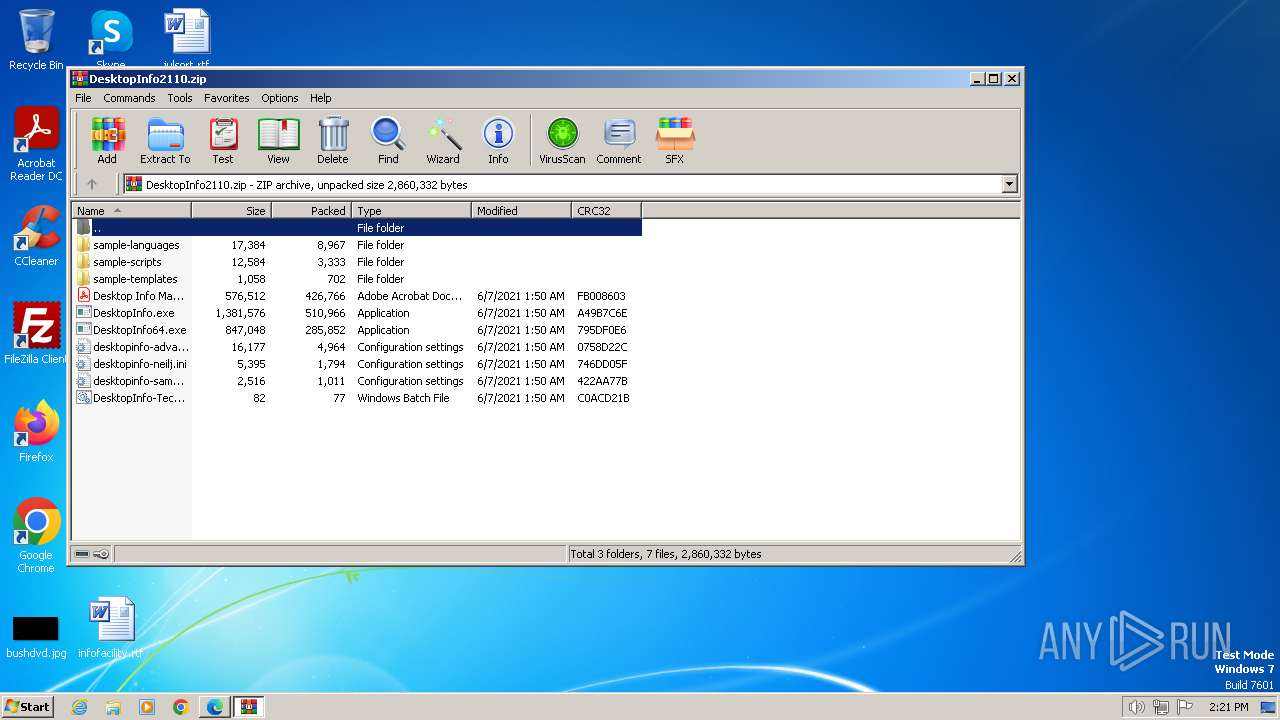
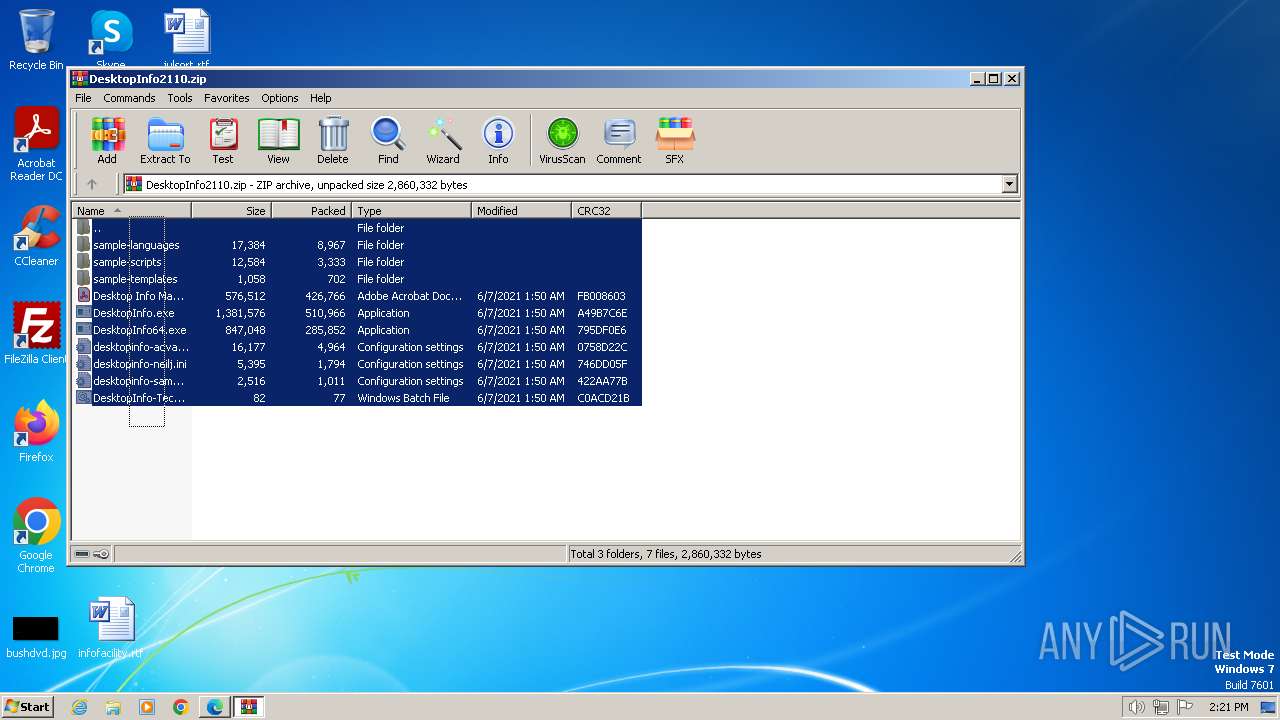
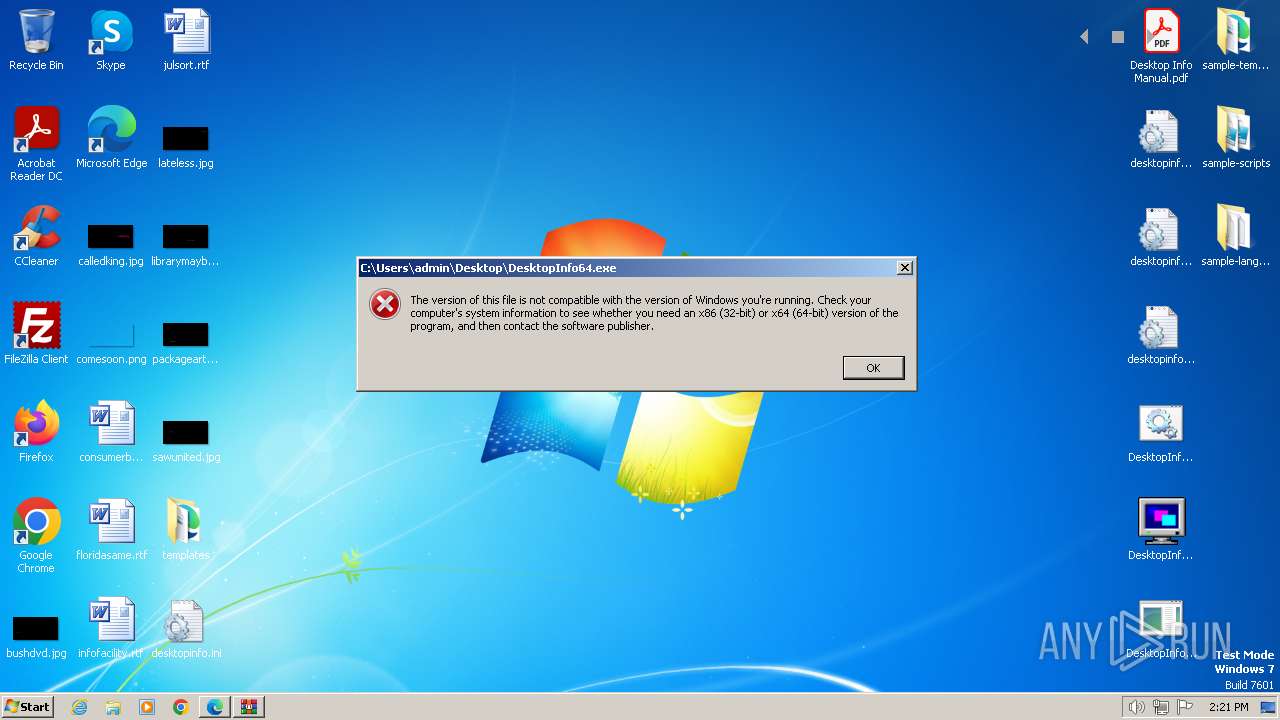
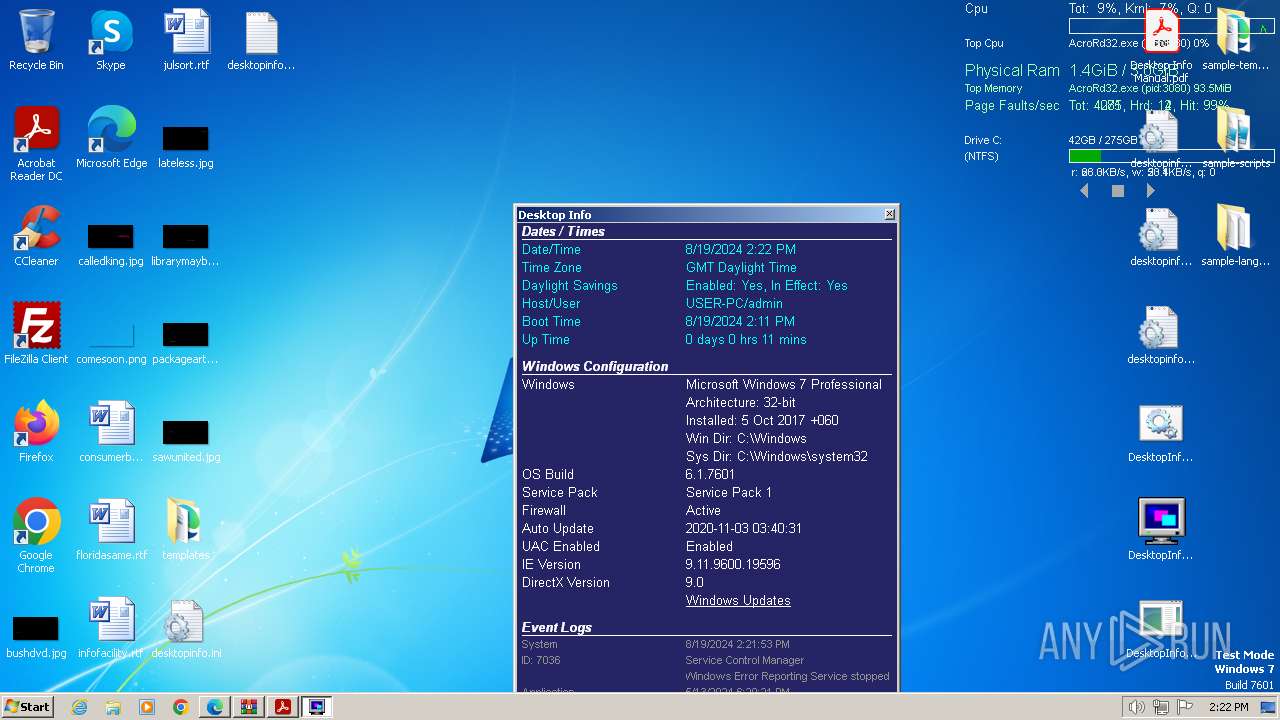
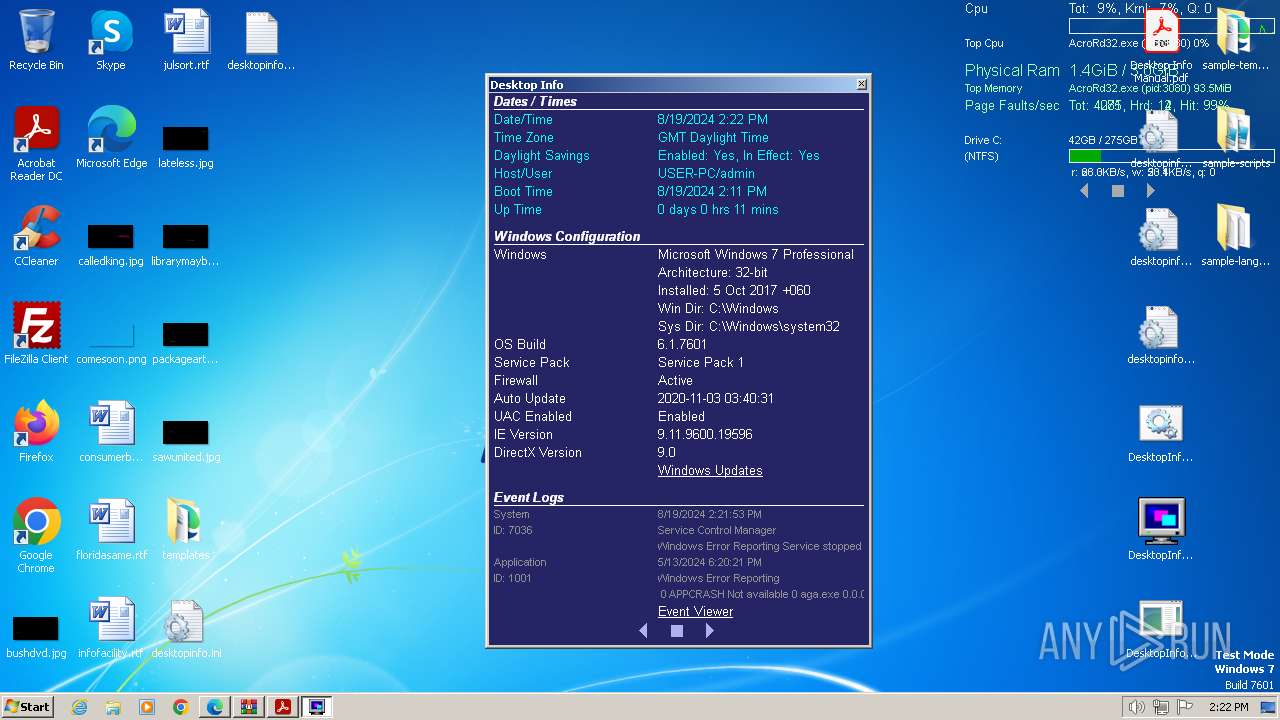
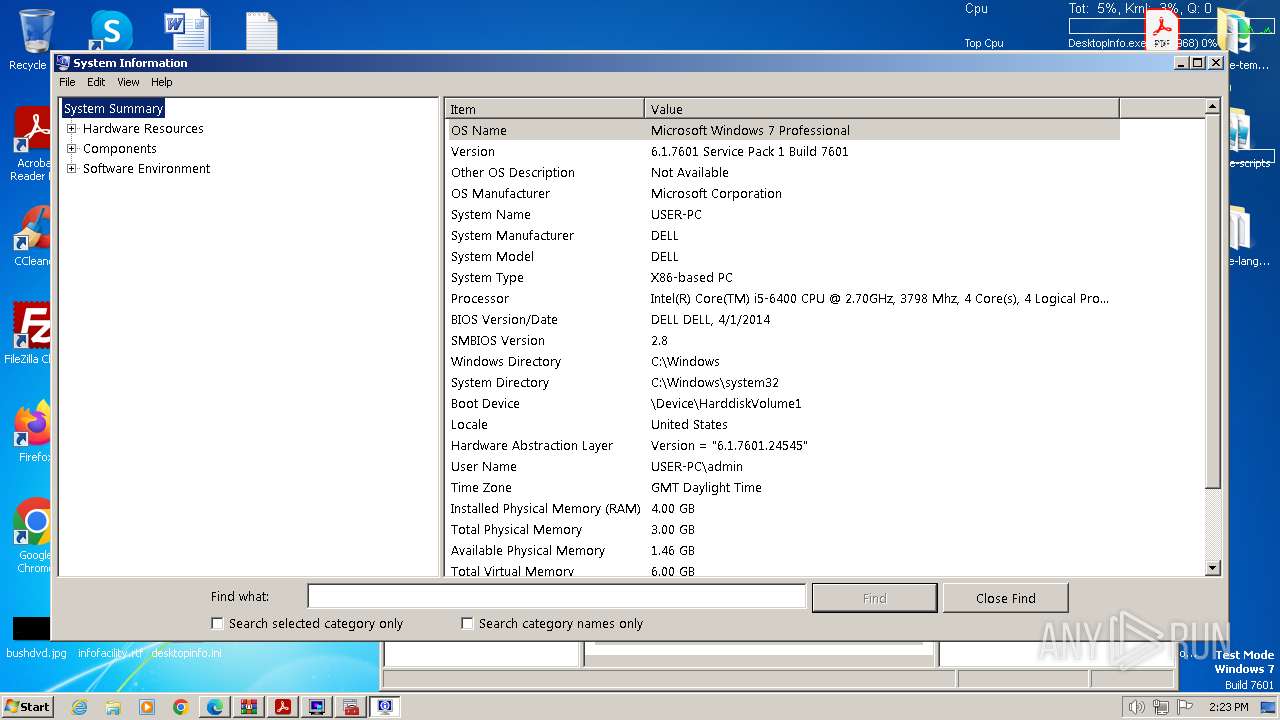
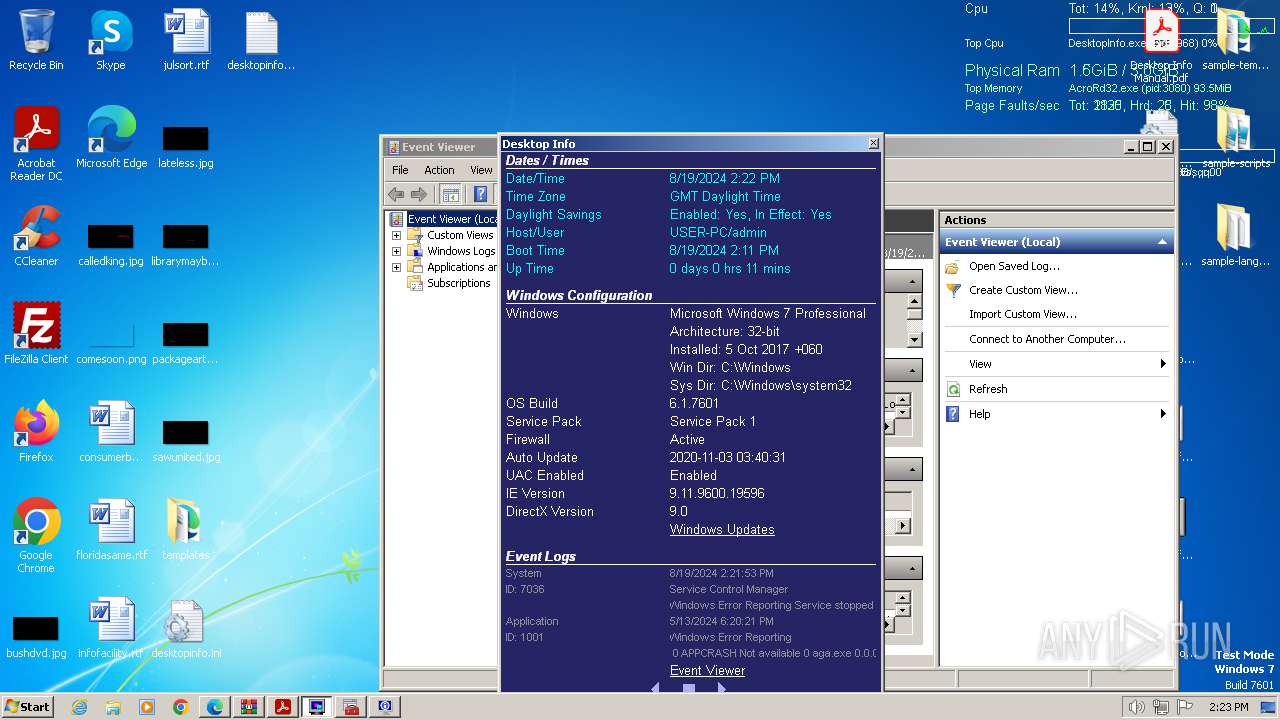
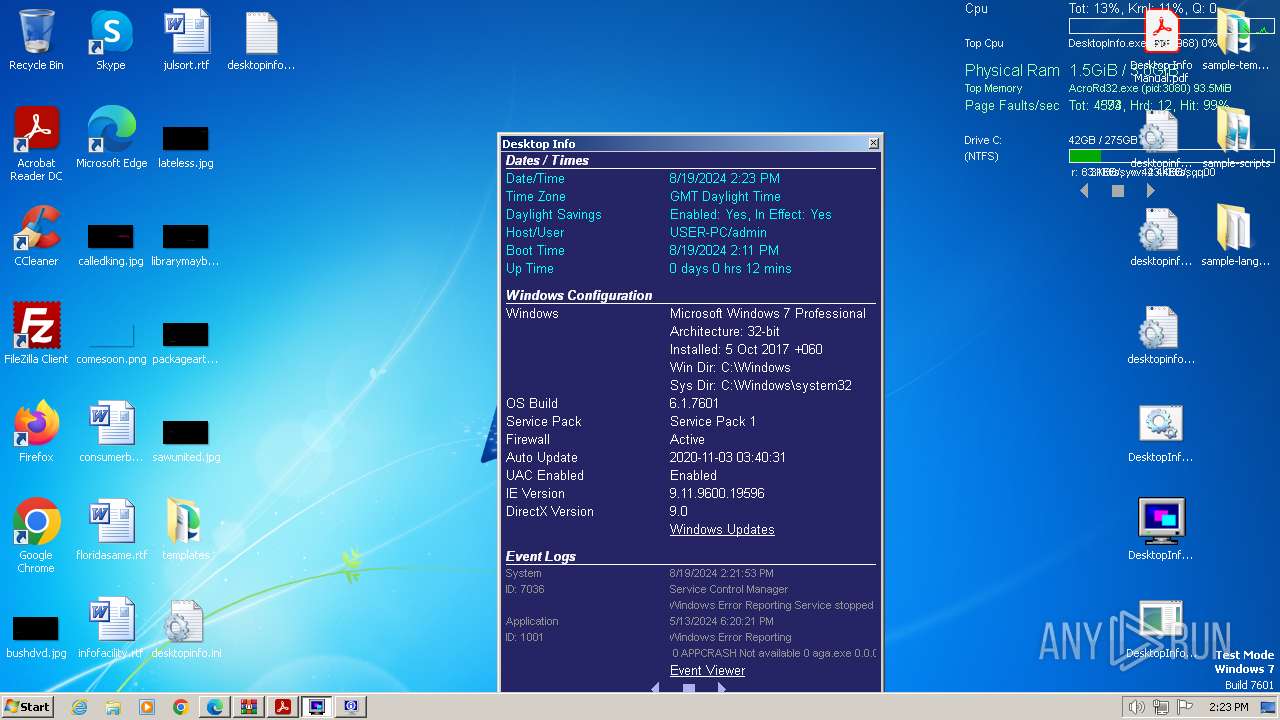
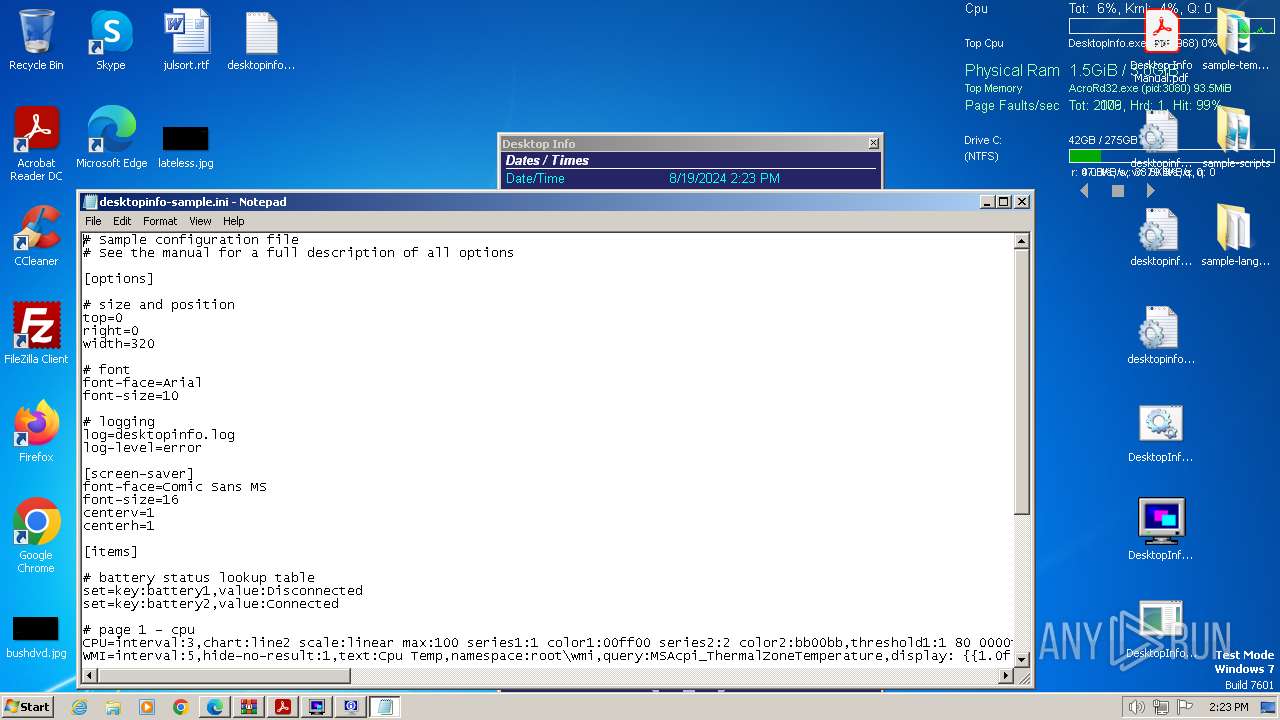
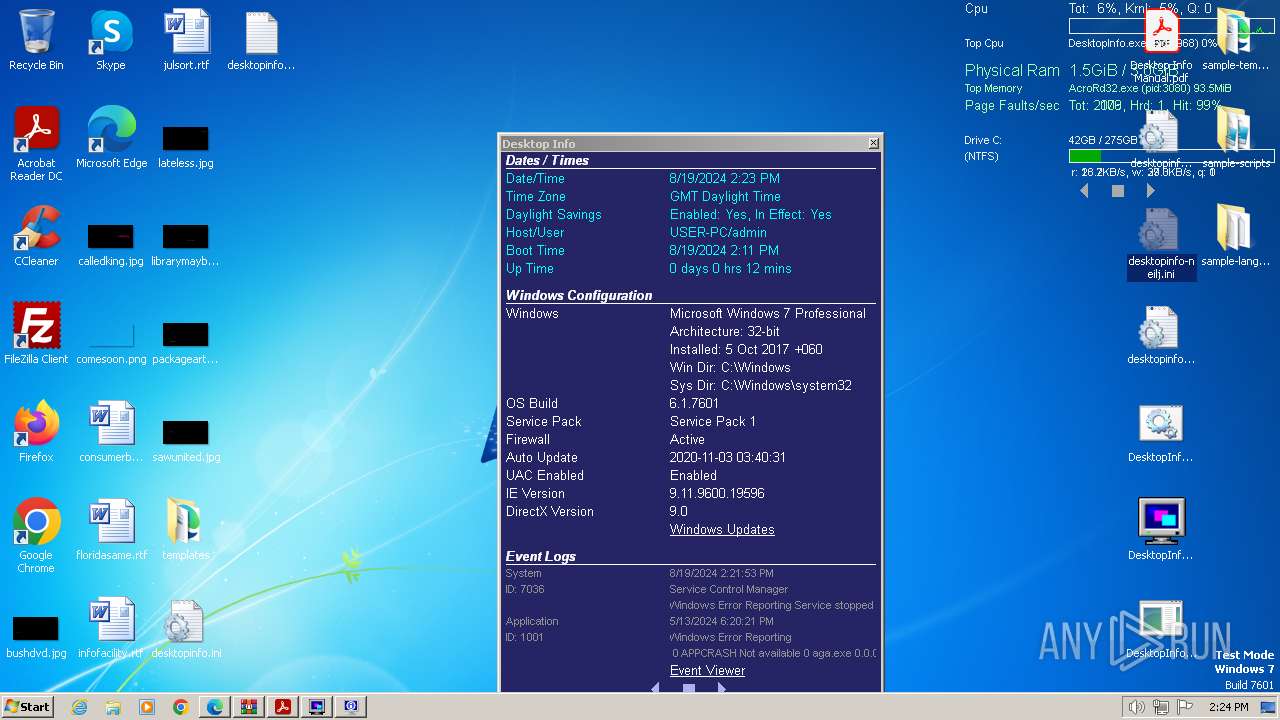
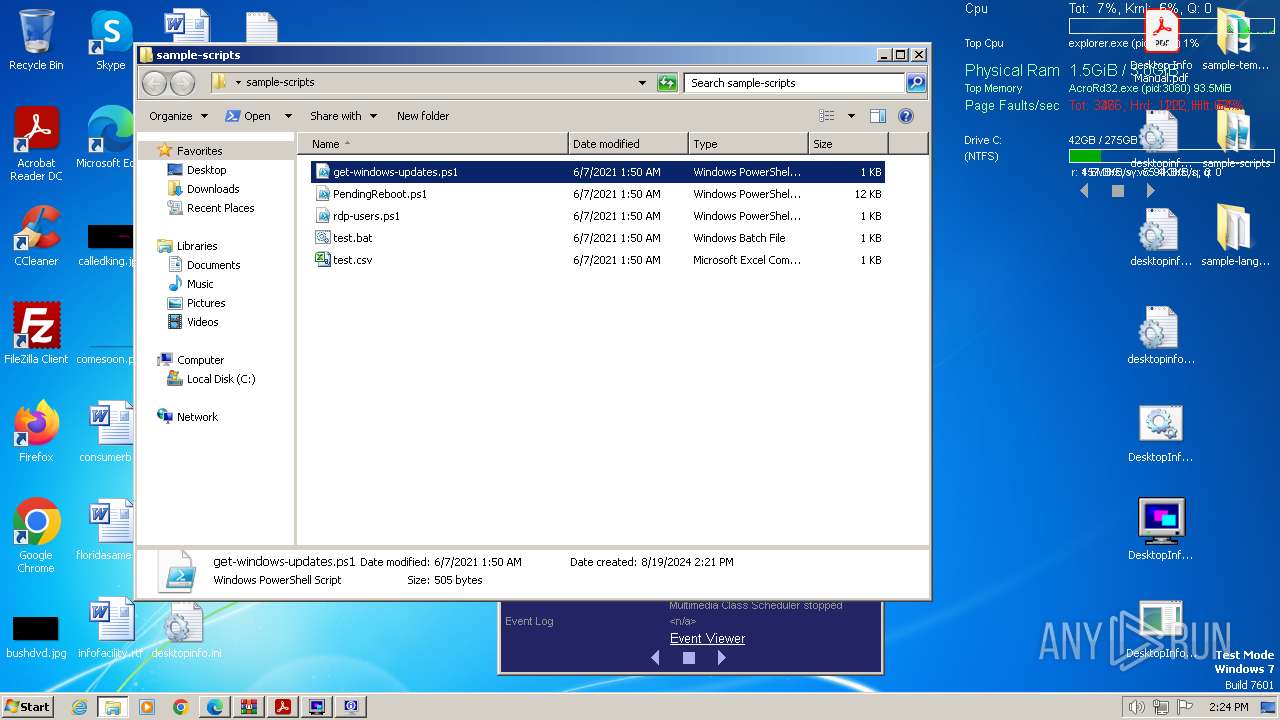
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1FEE486E31E0D073EF9D9E6DAEAF4CC8 |
| SHA1: | AD1F4F4DDAE8378C4FE3332652D0DA05FA6D8301 |
| SHA256: | B01176558B6CCE9AEA6F38AEE0C0220349C772654D8652320EED6829CF85DE3E |
| SSDEEP: | 3:N8DSLvLKJENSKGW1VM3R:2OLvmEUKG2K |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops the executable file immediately after the start
- DesktopInfo3150.exe (PID: 3636)
- DesktopInfo3150.exe (PID: 3700)
Executable content was dropped or overwritten
- DesktopInfo3150.exe (PID: 3636)
- DesktopInfo3150.exe (PID: 3700)
Creates file in the systems drive root
- AcroRd32.exe (PID: 3080)
Reads the Internet Settings
- DesktopInfo.exe (PID: 3968)
- eventvwr.exe (PID: 3792)
- powershell.exe (PID: 4012)
- powershell.exe (PID: 1368)
Checks for external IP
- DesktopInfo.exe (PID: 3968)
- svchost.exe (PID: 1060)
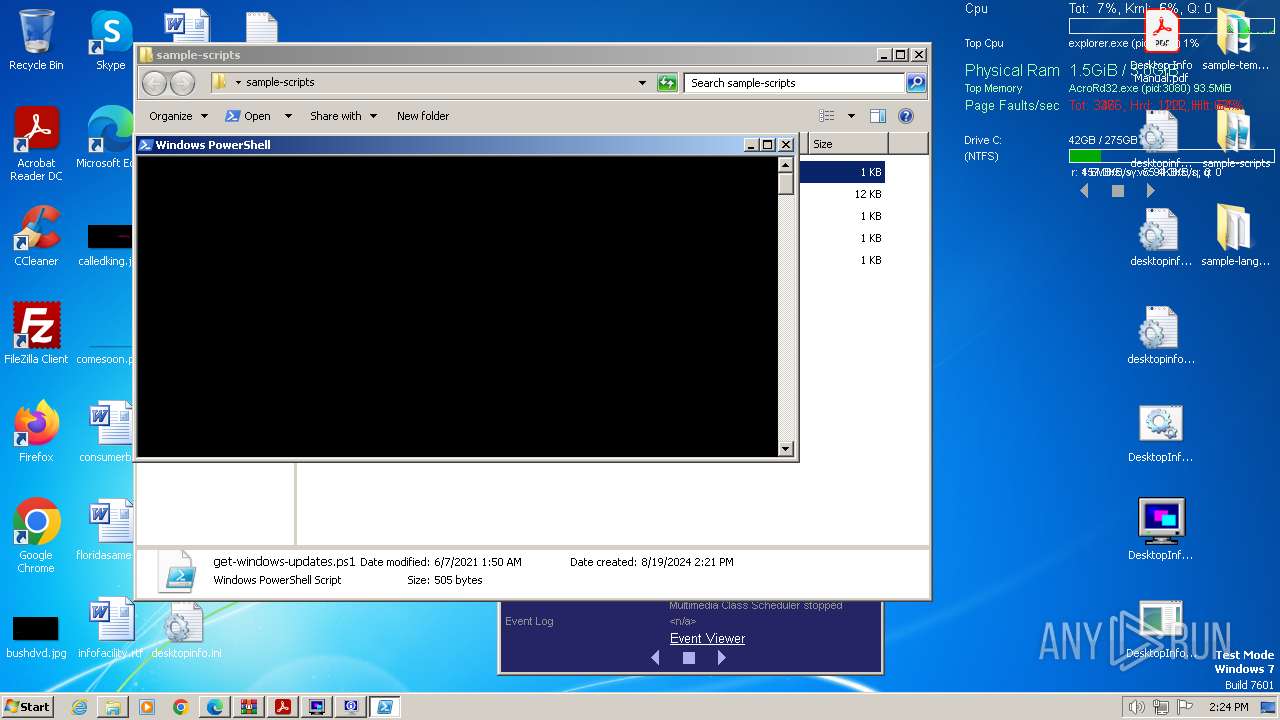
Starts POWERSHELL.EXE for commands execution
- DesktopInfo.exe (PID: 3968)
Reads security settings of Internet Explorer
- DesktopInfo.exe (PID: 3968)
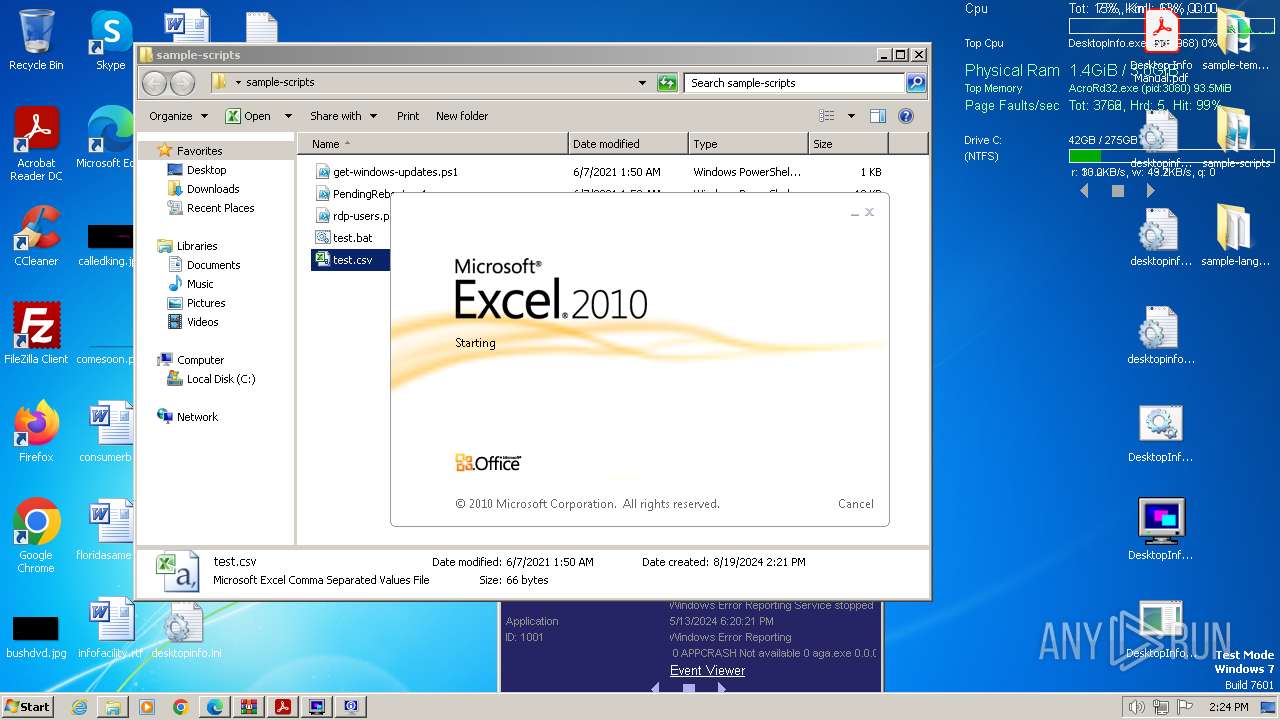
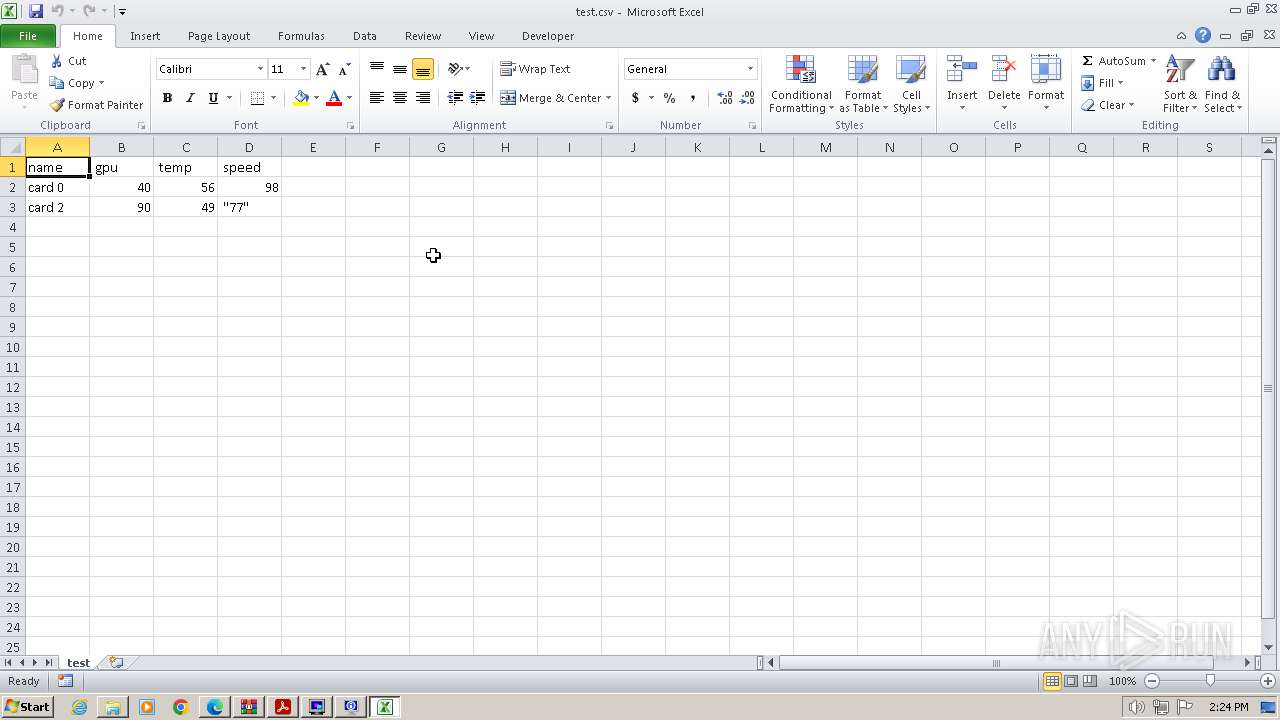
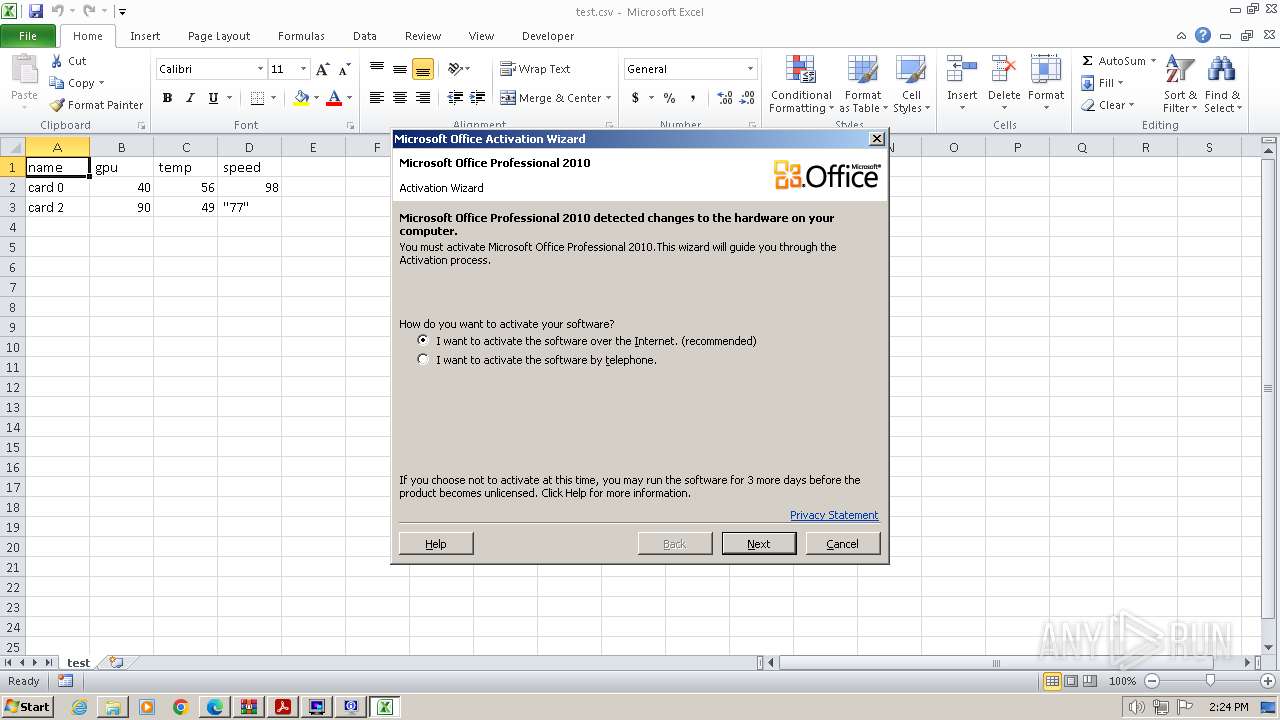
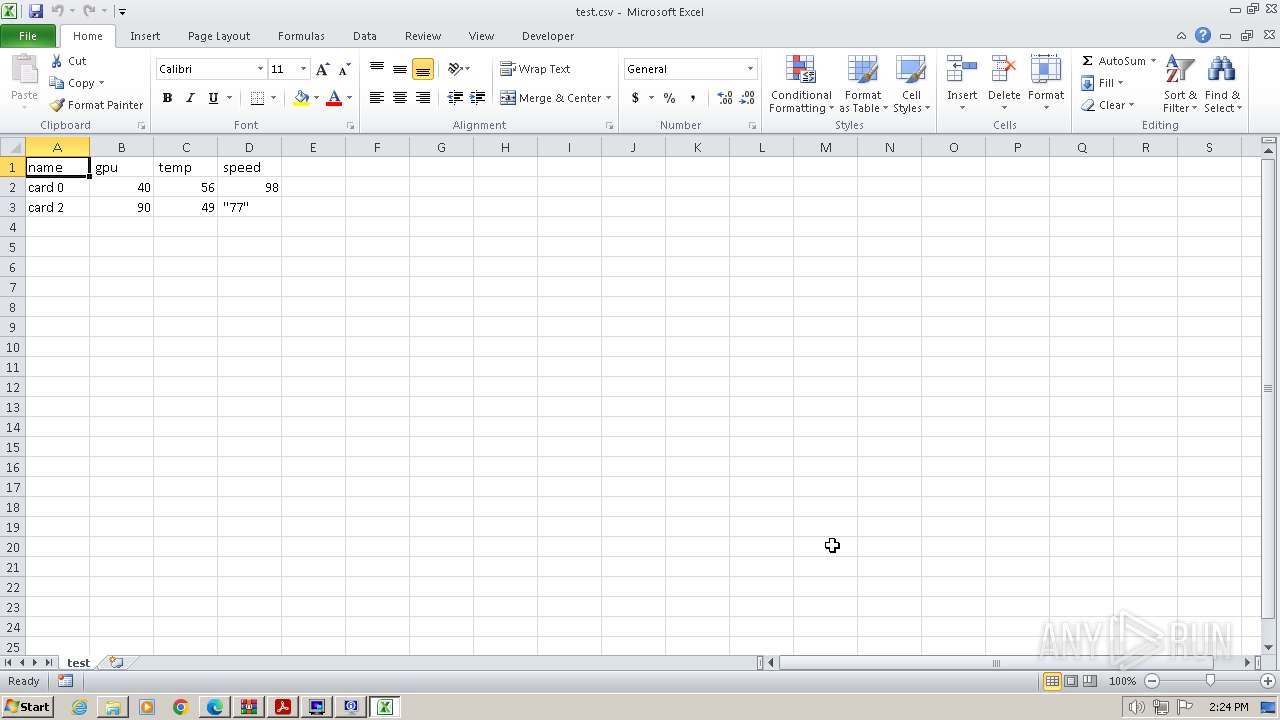
Opens a file (MACROS)
- EXCEL.EXE (PID: 2332)
Reads data from a file (MACROS)
- EXCEL.EXE (PID: 2332)
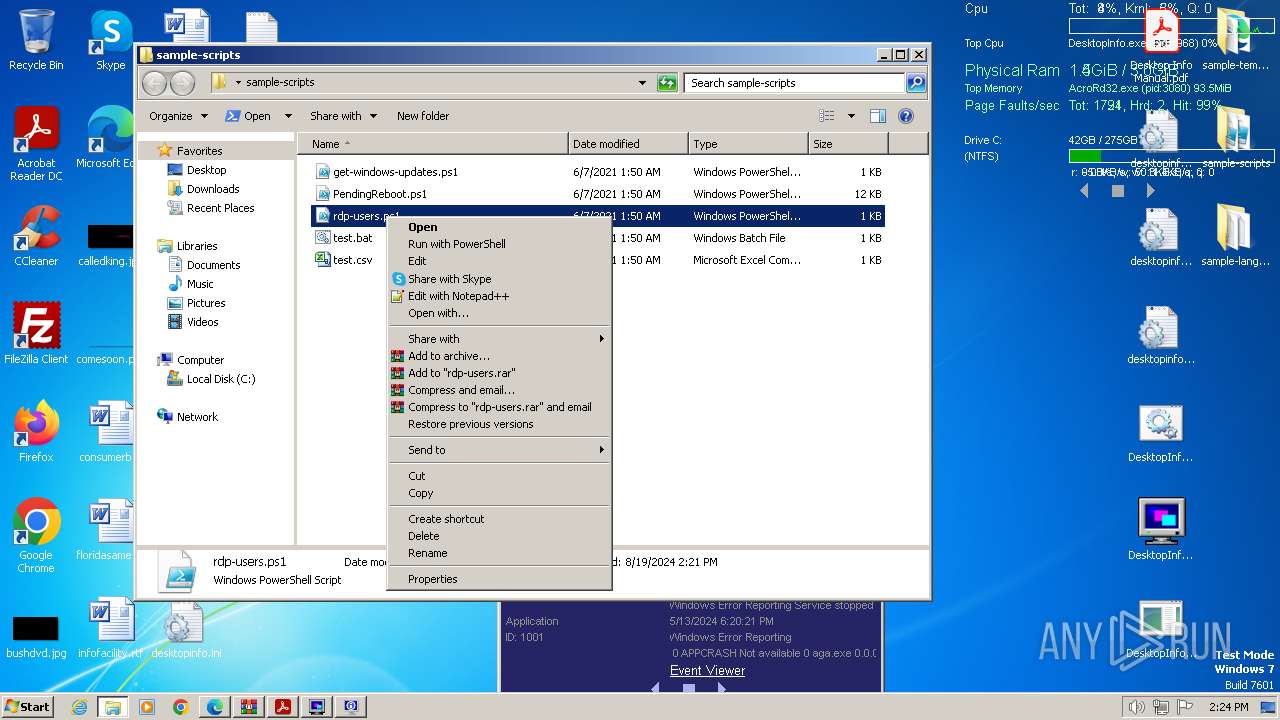
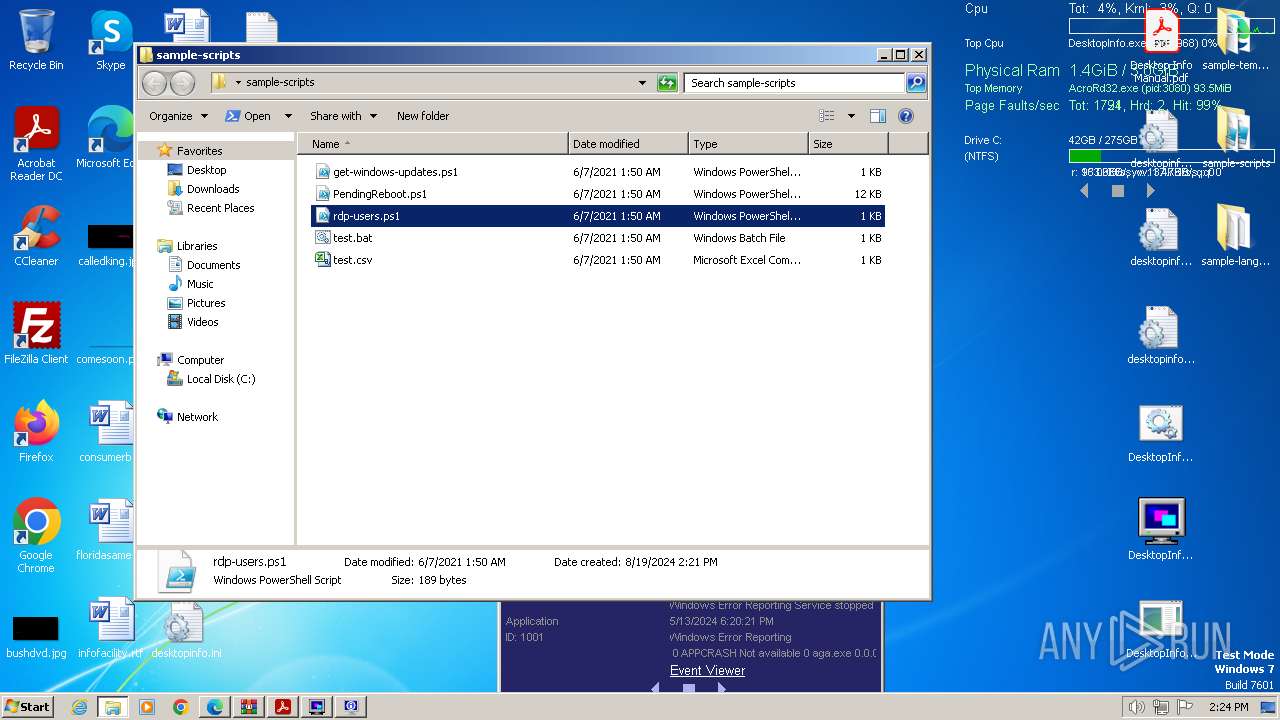
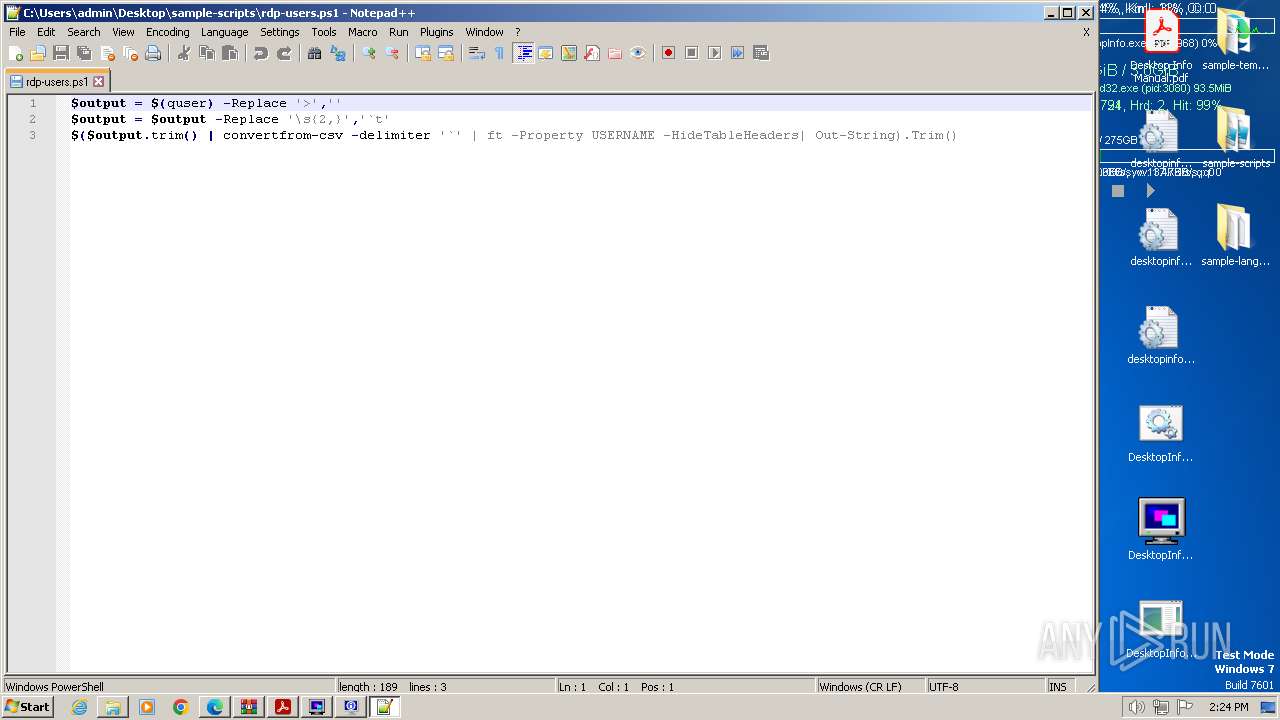
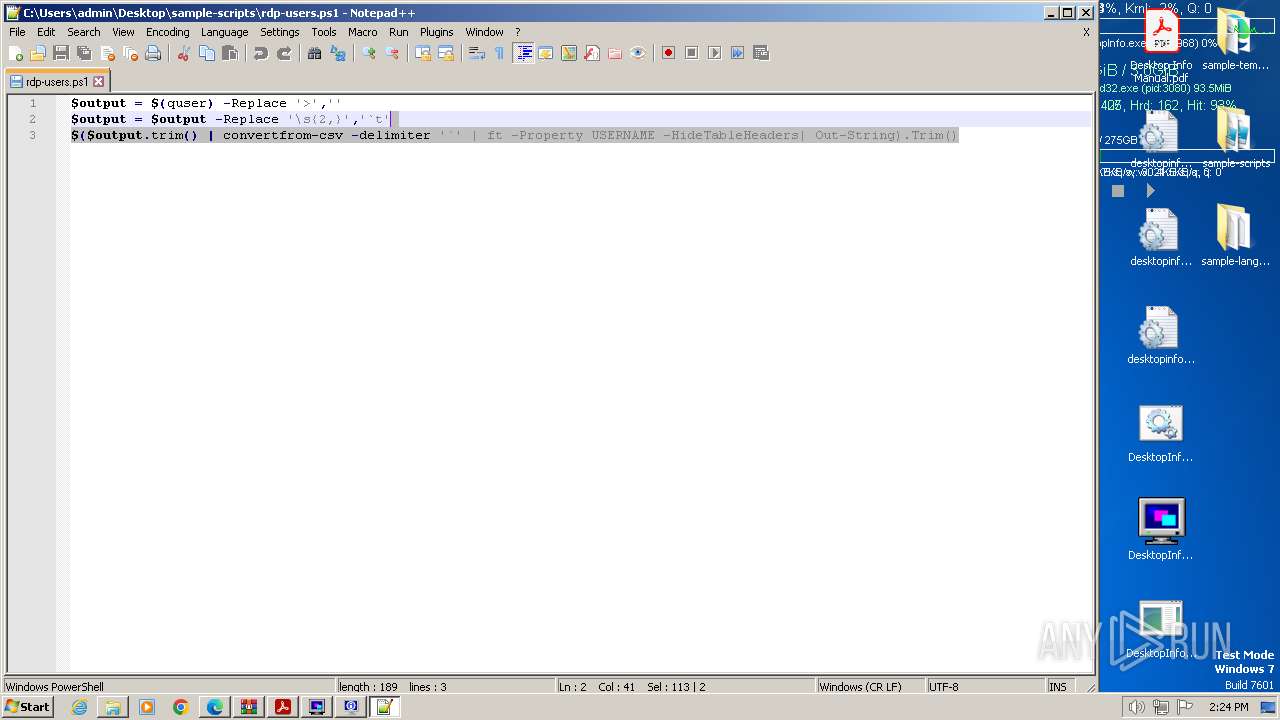
Uses QUSER.EXE to read information about current user sessions
- powershell.exe (PID: 4012)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 3048)
- DesktopInfo3150.tmp (PID: 3228)
- DesktopInfo3150.exe (PID: 3700)
- DesktopInfo3150.tmp (PID: 3856)
- DesktopInfo.exe (PID: 3492)
- DesktopInfo.exe (PID: 996)
- DesktopInfo.exe (PID: 3968)
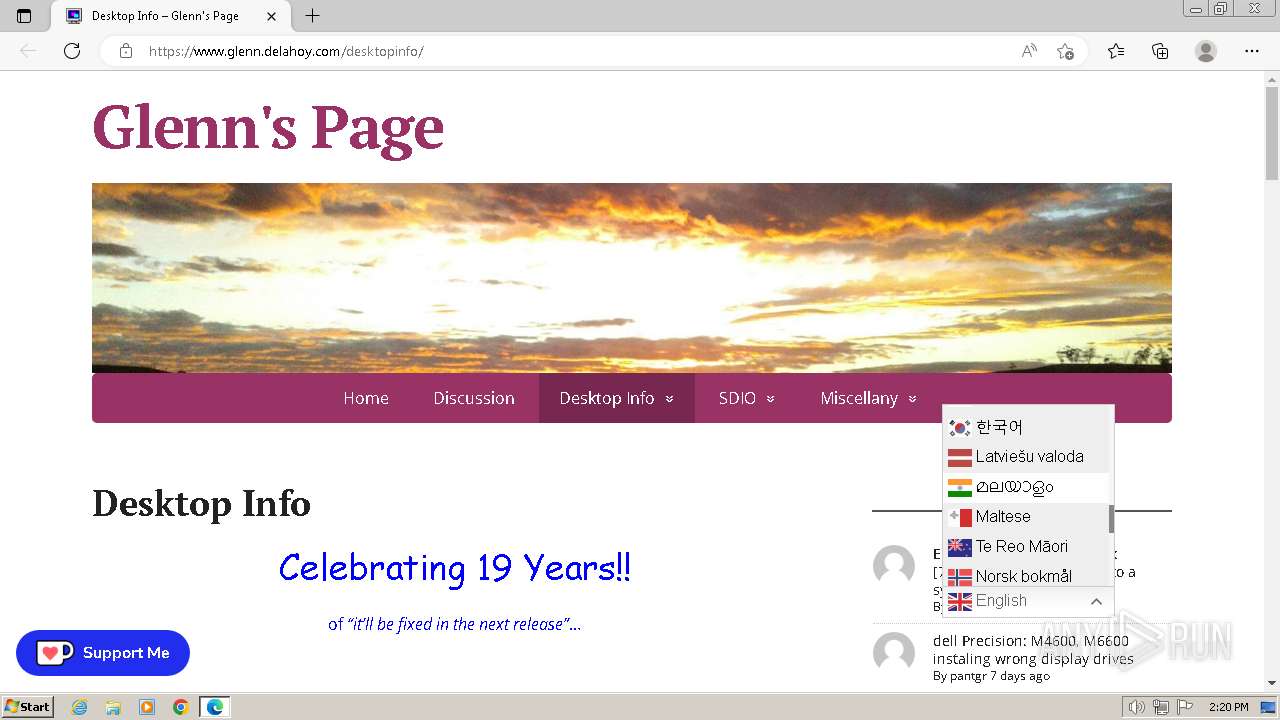
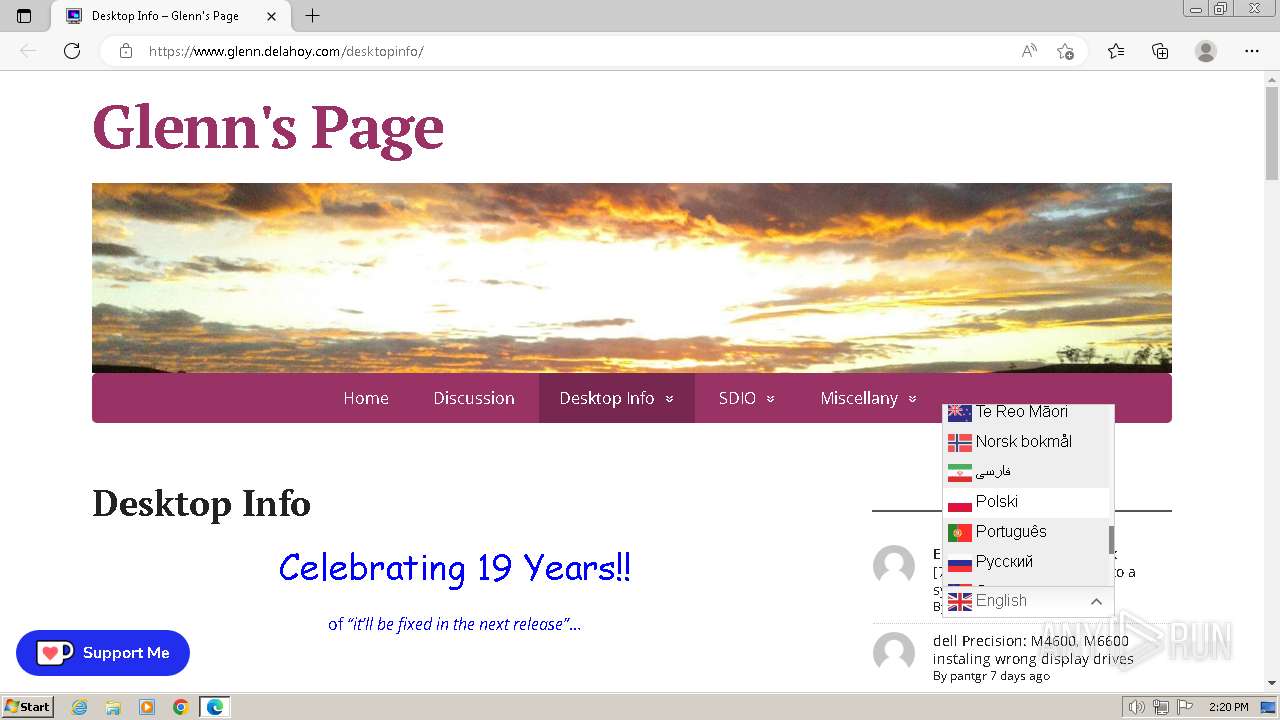
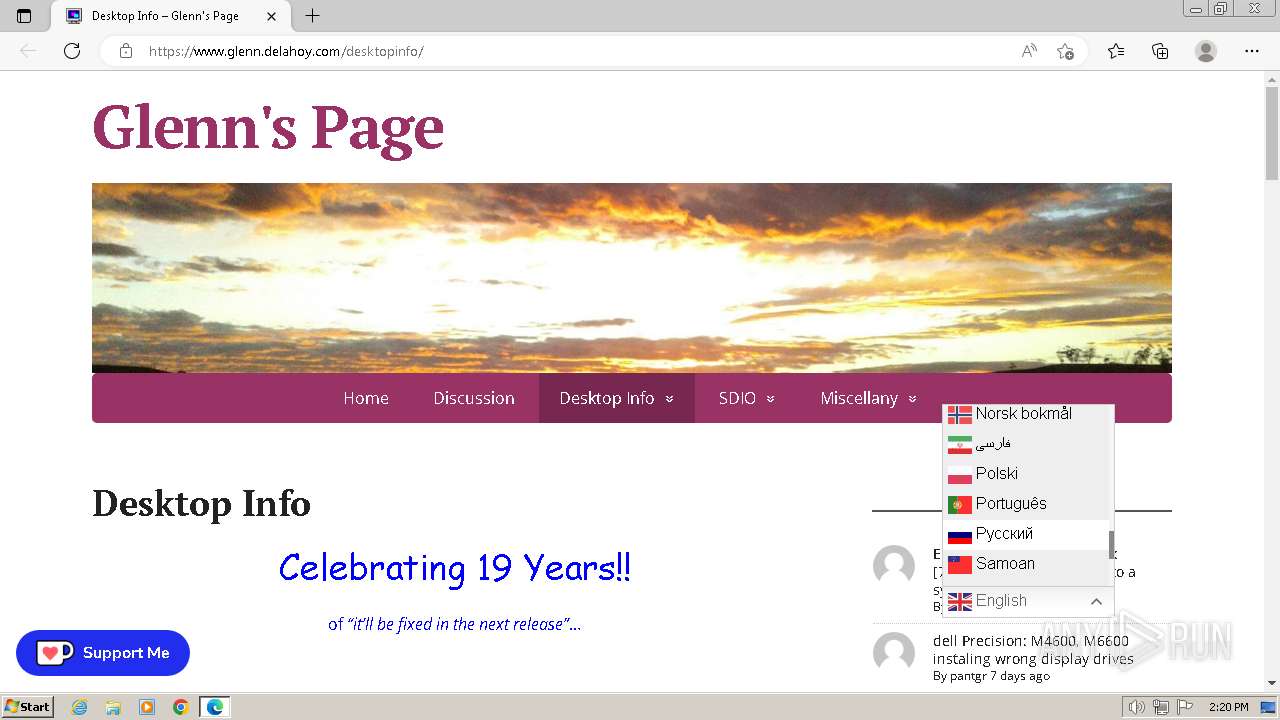
Checks supported languages
- wmpnscfg.exe (PID: 3048)
- DesktopInfo3150.exe (PID: 3636)
- DesktopInfo3150.exe (PID: 3700)
- DesktopInfo3150.tmp (PID: 3228)
- DesktopInfo3150.tmp (PID: 3856)
- DesktopInfo.exe (PID: 3492)
- DesktopInfo.exe (PID: 996)
- DesktopInfo.exe (PID: 3968)
Executable content was dropped or overwritten
- msedge.exe (PID: 2780)
- msedge.exe (PID: 3464)
- WinRAR.exe (PID: 2208)
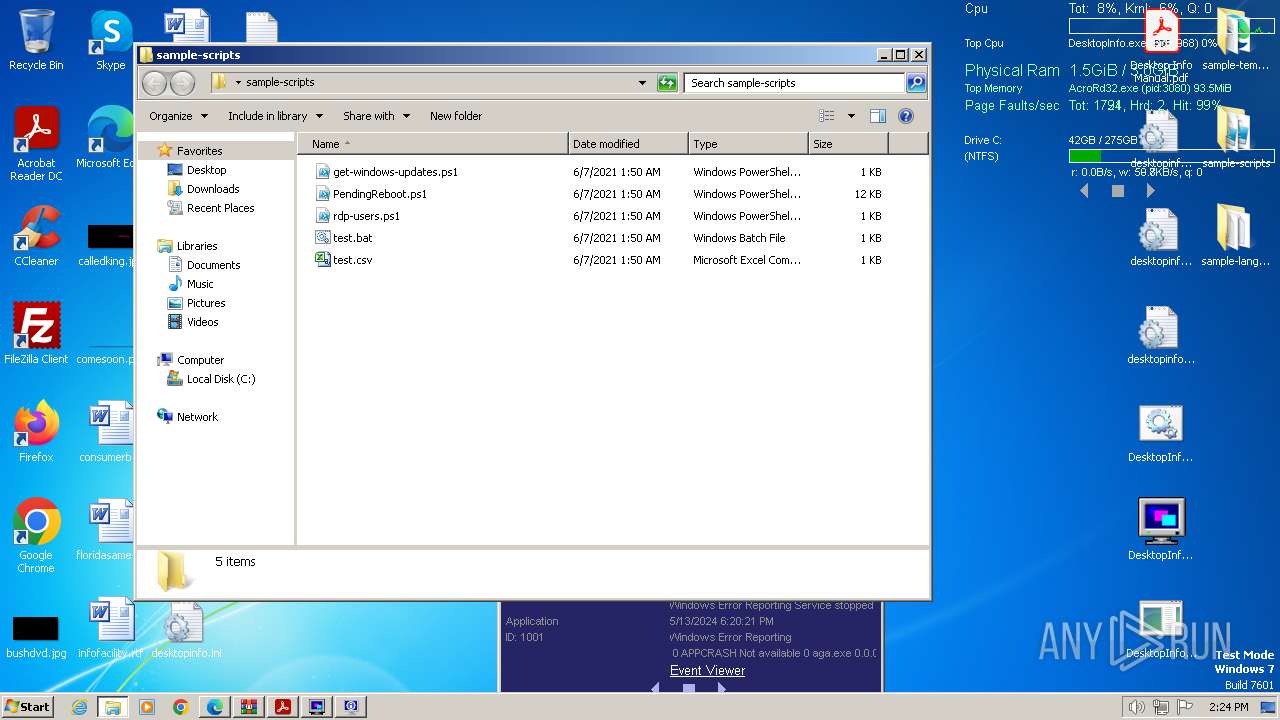
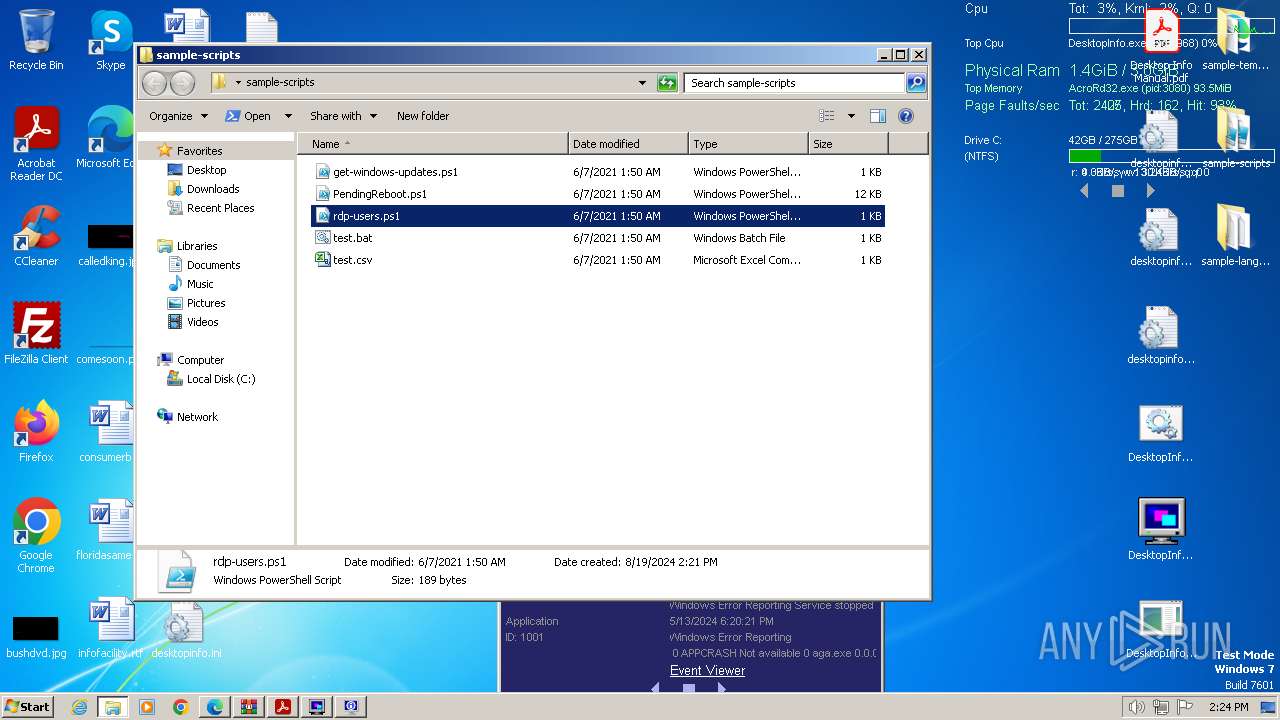
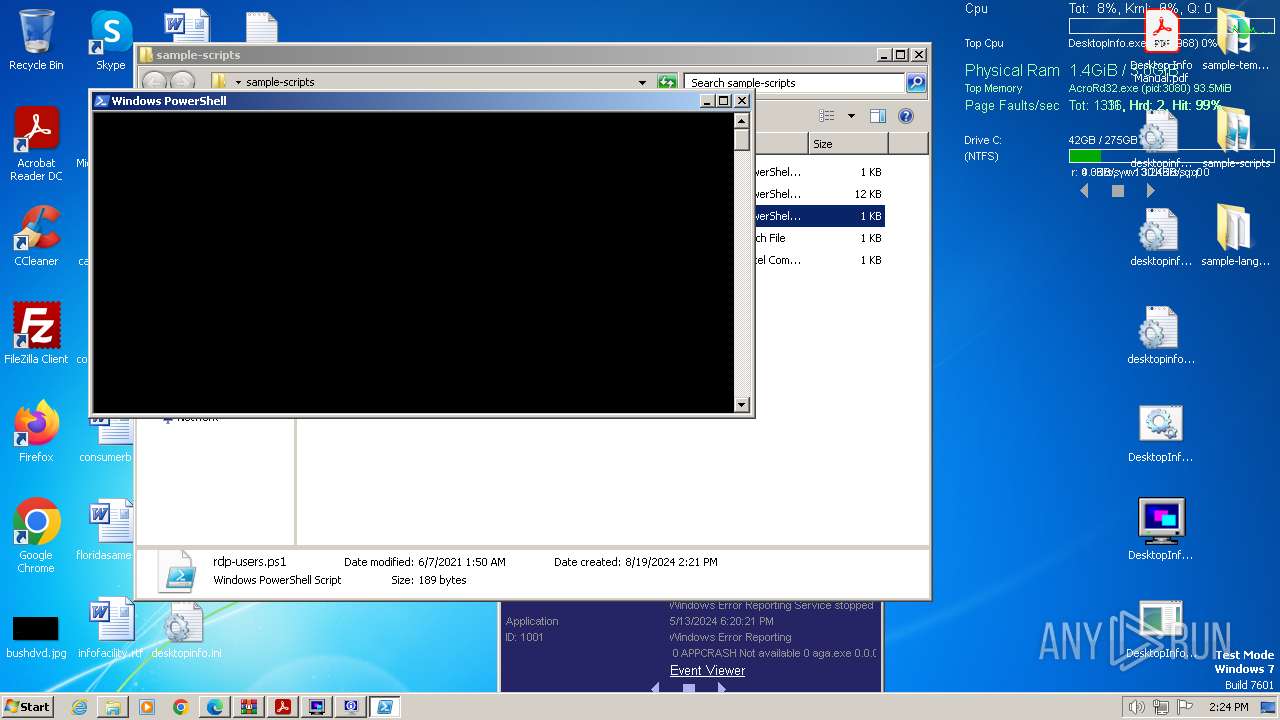
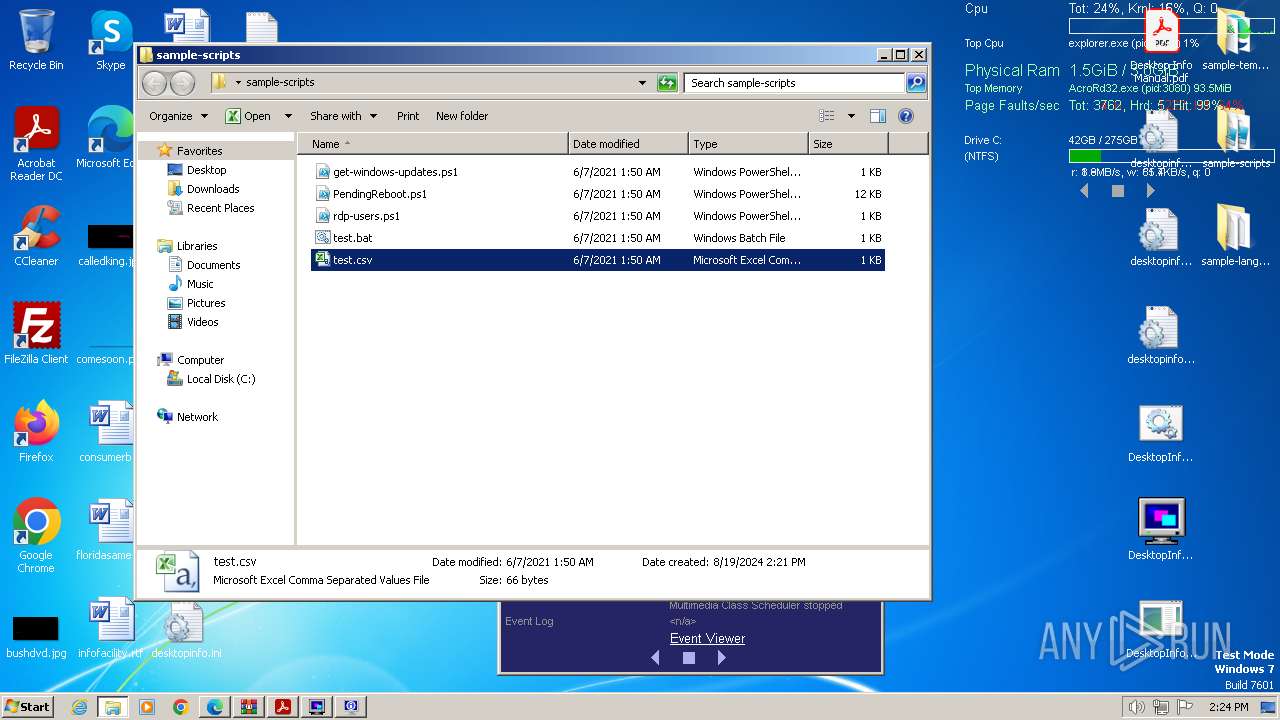
Manual execution by a user
- wmpnscfg.exe (PID: 3048)
- DesktopInfo.exe (PID: 3492)
- DesktopInfo.exe (PID: 996)
- AcroRd32.exe (PID: 3880)
- cmd.exe (PID: 1368)
- notepad++.exe (PID: 3820)
- notepad.exe (PID: 3188)
- powershell.exe (PID: 4012)
- cmd.exe (PID: 3228)
- EXCEL.EXE (PID: 2332)
- powershell.exe (PID: 1368)
The process uses the downloaded file
- msedge.exe (PID: 724)
- msedge.exe (PID: 2780)
- msedge.exe (PID: 1084)
- WinRAR.exe (PID: 2208)
Application launched itself
- msedge.exe (PID: 2780)
- AcroRd32.exe (PID: 3880)
- RdrCEF.exe (PID: 1196)
Create files in a temporary directory
- DesktopInfo3150.exe (PID: 3636)
- DesktopInfo3150.exe (PID: 3700)
Reads the machine GUID from the registry
- DesktopInfo.exe (PID: 3492)
- DesktopInfo.exe (PID: 996)
- DesktopInfo.exe (PID: 3968)
Reads Microsoft Office registry keys
- AcroRd32.exe (PID: 3080)
Checks proxy server information
- DesktopInfo.exe (PID: 3968)
Process checks whether UAC notifications are on
- DesktopInfo.exe (PID: 3968)
Reads Environment values
- DesktopInfo.exe (PID: 3968)
Reads security settings of Internet Explorer
- eventvwr.exe (PID: 3792)
Creates files in the program directory
- mmc.exe (PID: 1100)
Creates files or folders in the user directory
- DesktopInfo.exe (PID: 3968)
- mmc.exe (PID: 1100)
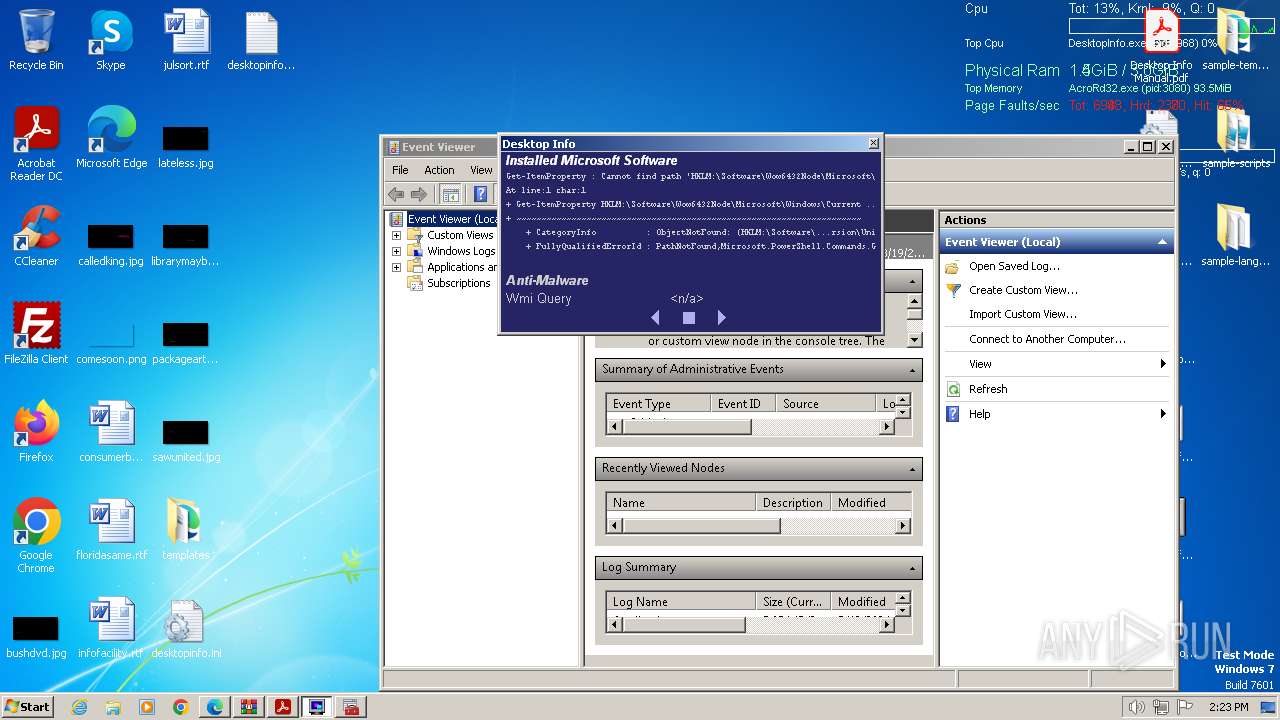
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
119
Monitored processes
61
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1176,919011937778991123,17354783791802431121,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6150241530844998899 --renderer-client-id=6 --mojo-platform-channel-handle=1428 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1176,919011937778991123,17354783791802431121,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12235761808257910537 --renderer-client-id=8 --mojo-platform-channel-handle=1260 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 724 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3904 --field-trial-handle=1200,i,17188160642287533069,411924677062945281,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 740 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --mojo-platform-channel-handle=3628 --field-trial-handle=1200,i,17188160642287533069,411924677062945281,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --mojo-platform-channel-handle=4484 --field-trial-handle=1200,i,17188160642287533069,411924677062945281,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3512 --field-trial-handle=1200,i,17188160642287533069,411924677062945281,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 996 | "C:\Users\admin\Desktop\DesktopInfo.exe" | C:\Users\admin\Desktop\DesktopInfo.exe | — | explorer.exe | |||||||||||
User: admin Company: Glenn Delahoy Integrity Level: MEDIUM Description: Desktop Info Version: 2.11.0.3870 Modules
| |||||||||||||||
| 1060 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1492 --field-trial-handle=1200,i,17188160642287533069,411924677062945281,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4964 --field-trial-handle=1200,i,17188160642287533069,411924677062945281,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
60 415
Read events
59 871
Write events
378
Delete events
166
Modification events
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: A56AD9739F7E2F00 | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (2780) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
9
Suspicious files
311
Text files
66
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF827c4.TMP | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF827d4.TMP | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF827e4.TMP | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF82832.TMP | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:9D14DCB158E3908F7CBFB13D762D8F6A | SHA256:D339CBEF1BC3E4CDF15D0DCE9E2D77324E5B4F7EE4F2749472BFCEA91BB54ACE | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:61FE7896F9494DCDF53480A325F4FB85 | SHA256:ACFD3CD36E0DFCF1DCB67C7F31F2A5B9BA0815528A0C604D4330DFAA9E683E51 | |||
| 2780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:4B74C392839DDD59792975091A30DB00 | SHA256:7A5A3B8CC4D5BB579FA5E6C6A831964FB245A5CFF9AD3B80F5E9DC34DA4A7D53 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
74
DNS requests
77
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 23.50.131.216:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | DE | — | — | whitelisted |
1060 | svchost.exe | GET | 304 | 23.50.131.216:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?67a3611ec3c0260d | DE | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
1372 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
3880 | AcroRd32.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | binary | 471 b | whitelisted |
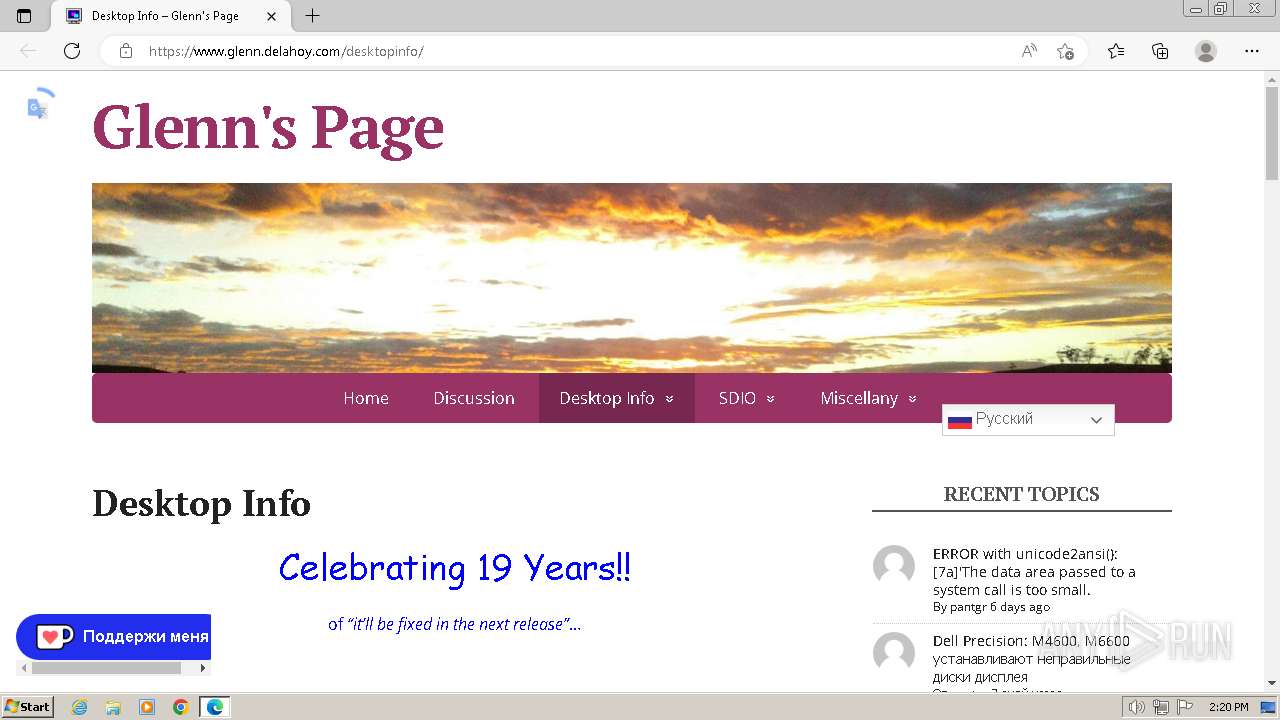
3968 | DesktopInfo.exe | GET | 200 | 34.160.111.145:80 | http://ipecho.net/plain | US | text | 12 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1372 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3464 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2780 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3464 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3464 | msedge.exe | 110.232.143.72:443 | www.glenn.delahoy.com | SYNERGY WHOLESALE PTY LTD | AU | unknown |
3464 | msedge.exe | 142.250.184.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3464 | msedge.exe | 142.250.186.67:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.glenn.delahoy.com |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
storage.ko-fi.com |
| whitelisted |
ko-fi.com |
| whitelisted |
secure.gravatar.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipecho .net) |
3968 | DesktopInfo.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - ipecho.net |
3968 | DesktopInfo.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
Process | Message |
|---|---|
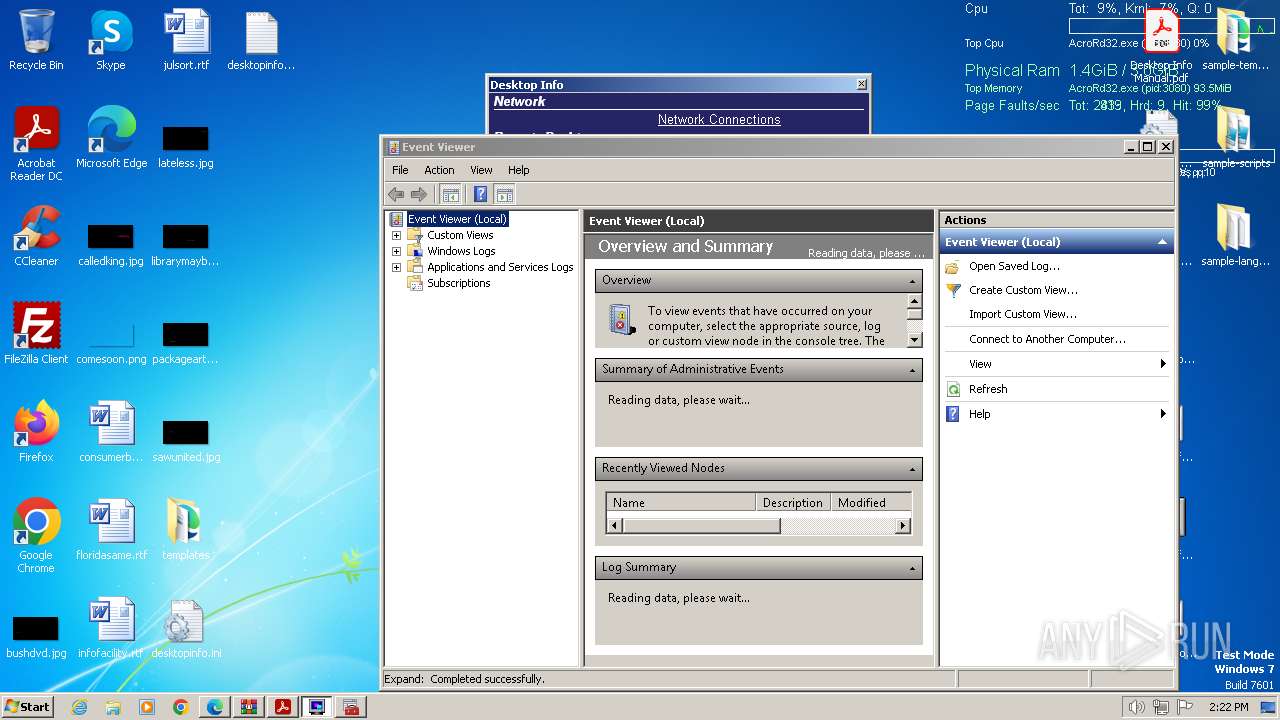
mmc.exe | ViewerConfigPath = 'C:\ProgramData\Microsoft\Event Viewer': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerAdminViewsPath = 'C:\ProgramData\Microsoft\Event Viewer\Views\ApplicationViewsRootNode': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerExternalLogsPath = 'C:\ProgramData\Microsoft\Event Viewer\ExternalLogs': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | Failed to get ChannelConfigOwningPublisher -122-The data area passed to a system call is too small
|
mmc.exe | Getting next publisher from enum failed-259-No more data is available
|
mmc.exe | Failed to get ChannelConfigOwningPublisher -122-The data area passed to a system call is too small
|
mmc.exe | ExpandNode:After EventsNode:InsertChildren CountOfChildren = 5
|
mmc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
mmc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|