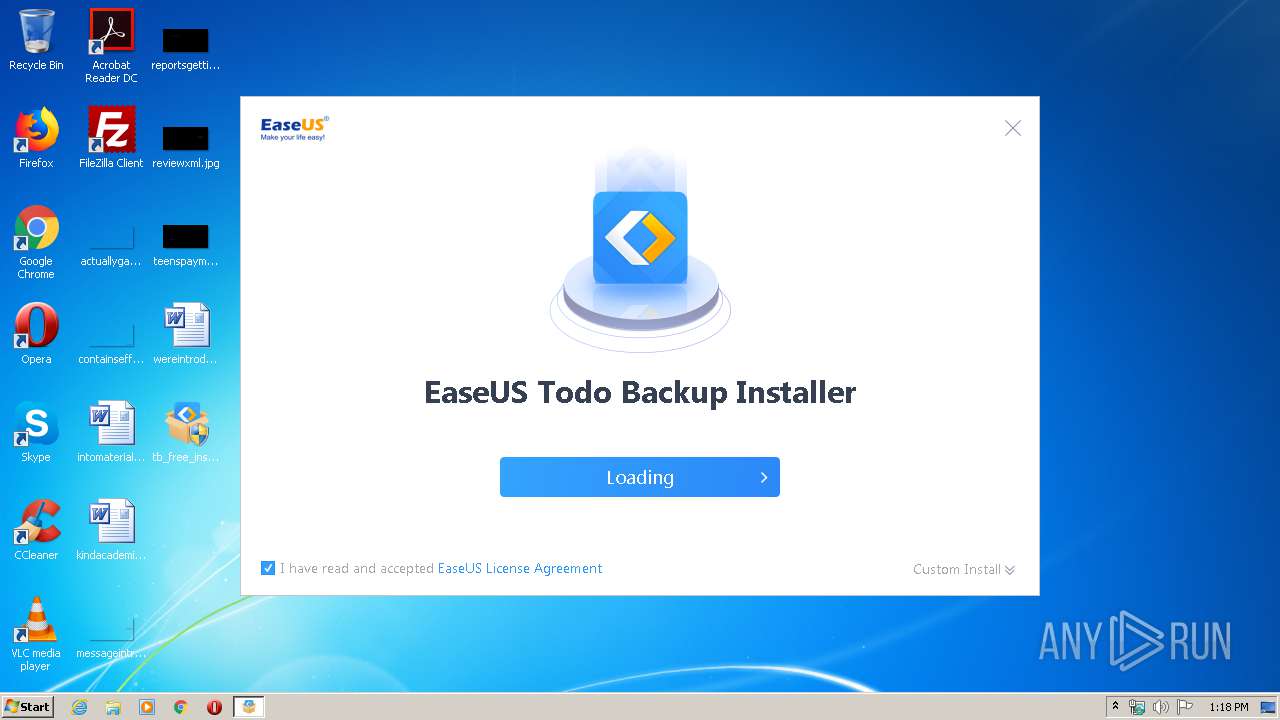
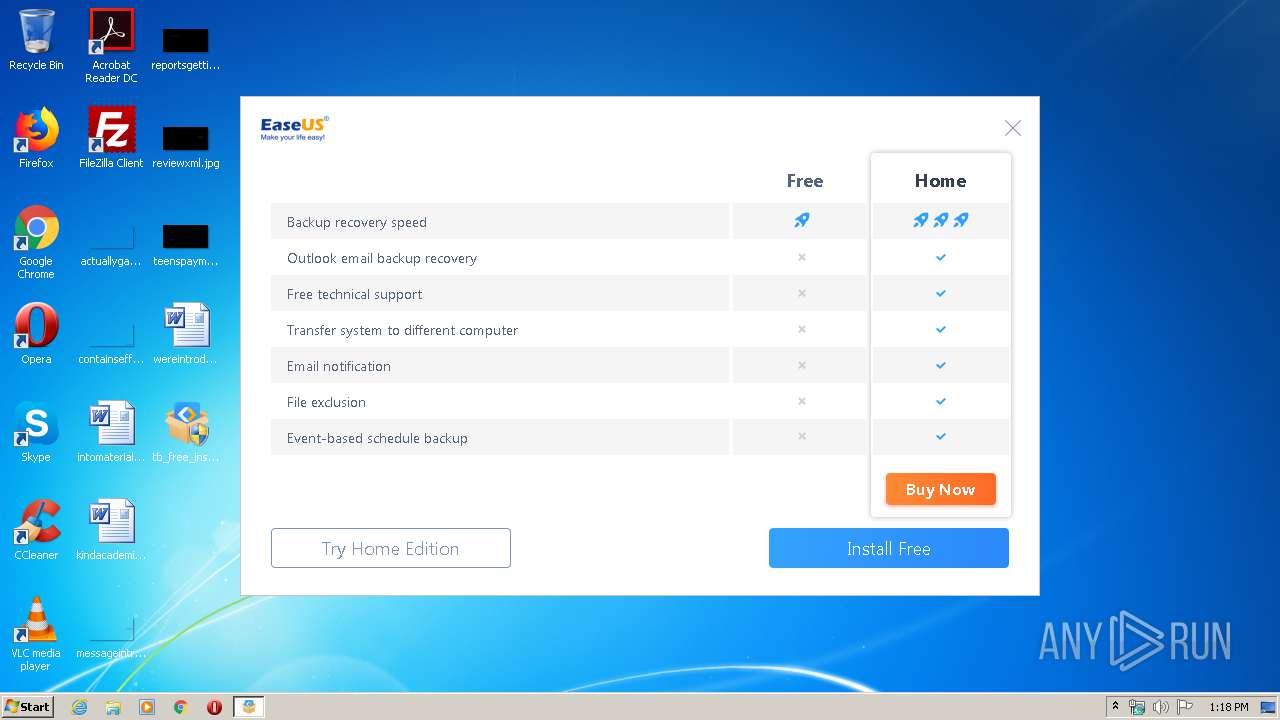
| download: | tb_free_installer.exe |
| Full analysis: | https://app.any.run/tasks/96d63d1a-d619-40b2-a368-2382121c2991 |
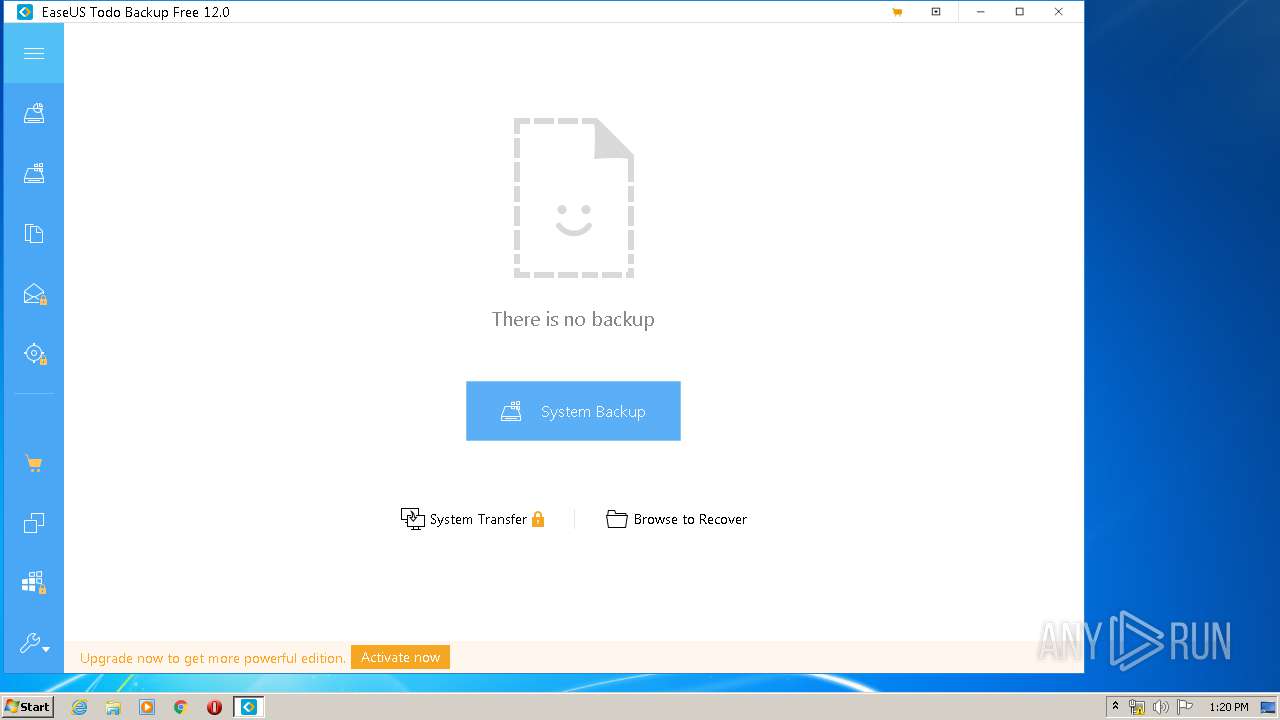
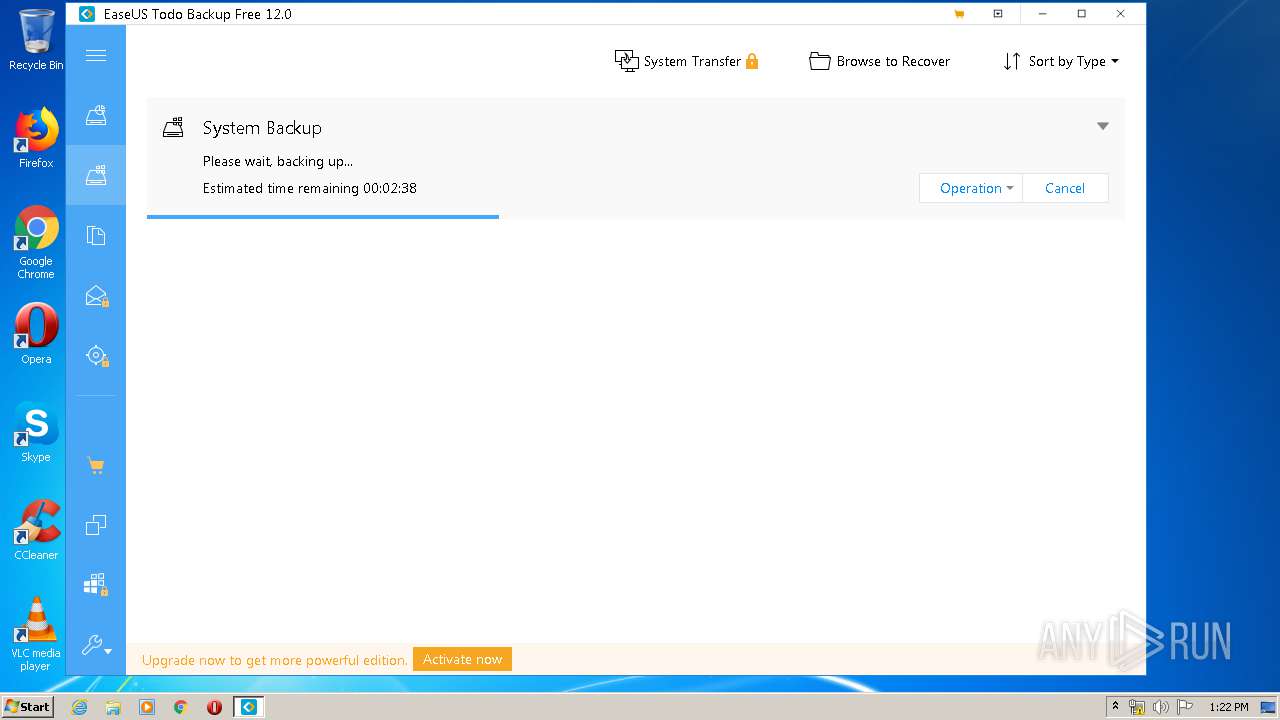
| Verdict: | Malicious activity |
| Analysis date: | April 04, 2020, 12:17:42 |
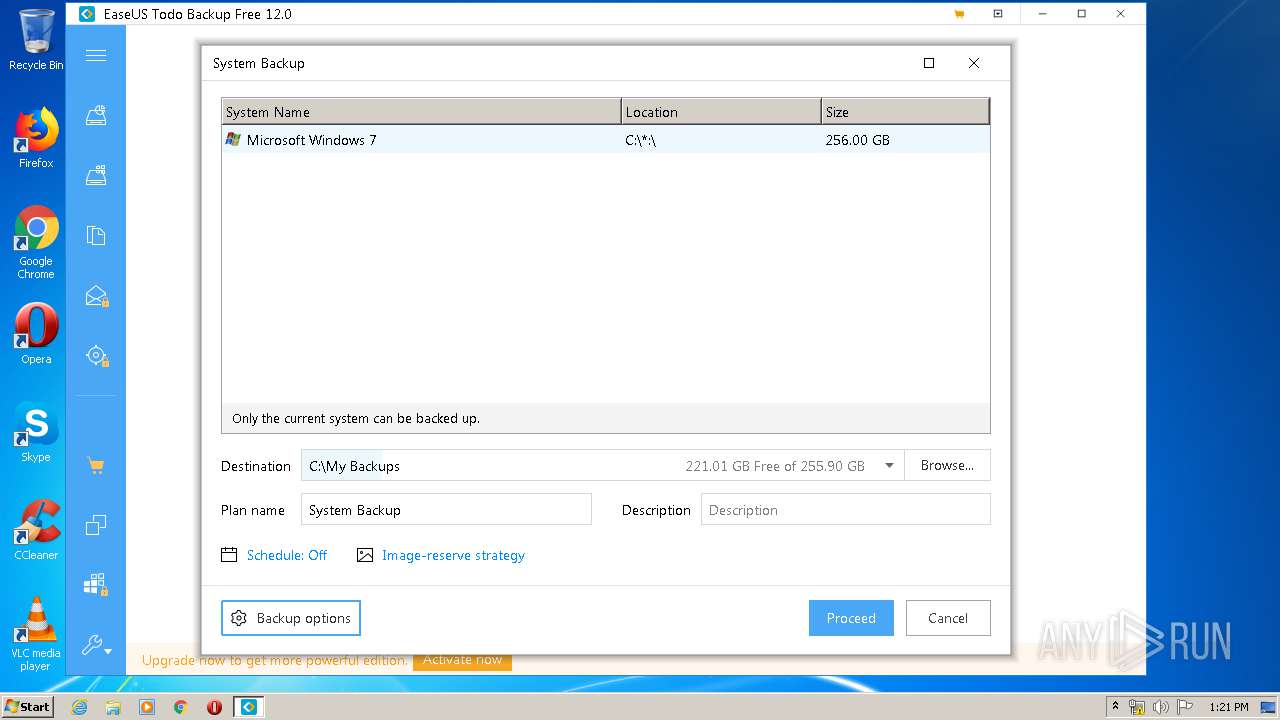
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 9B2C293A25B8B1D68222A6F1EF9274D7 |
| SHA1: | 77E0A6D76CDD2E7A2132C6F136924BF4659AD8B6 |
| SHA256: | B00563192C32023D99395DAD2A1173701F9E452F3D88C0A0D47E0E860884EE3B |
| SSDEEP: | 49152:q+BX83a1WT1hmSHwHHica/0zrmPzpMeDWn8dYMK:q+Bs371ISOicac2qeK8uF |
MALICIOUS
Loads dropped or rewritten executable
- InfoForSetup.exe (PID: 1740)
- InfoForSetup.exe (PID: 3056)
- AliyunWrapExe.Exe (PID: 3732)
- InfoForSetup.exe (PID: 3040)
- InfoForSetup.exe (PID: 3100)
- InfoForSetup.exe (PID: 4052)
- InfoForSetup.exe (PID: 3764)
- InfoForSetup.exe (PID: 2056)
- InfoForSetup.exe (PID: 3384)
- AppSetup.exe (PID: 1524)
- Agent.exe (PID: 2636)
- Agent.exe (PID: 3040)
- InfoForSetup.exe (PID: 1720)
- InfoForSetup.exe (PID: 2500)
- InfoForSetup.exe (PID: 2472)
- AliyunWrapExe.Exe (PID: 2744)
- InfoForSetup.exe (PID: 3908)
- TBConsoleUI.exe (PID: 2300)
- InfoForSetup.exe (PID: 2652)
- TodoBackupService.exe (PID: 3220)
- vds.exe (PID: 1920)
- TodoBackupEnumNetByFD_0.exe (PID: 3360)
- AdvertisingPopup.exe (PID: 1520)
- QtWebEngineProcess.exe (PID: 3852)
- TbService.exe (PID: 3160)
- TrayNotify.exe (PID: 2760)
Application was dropped or rewritten from another process
- EDownloader.exe (PID: 2524)
- InfoForSetup.exe (PID: 1740)
- InfoForSetup.exe (PID: 3040)
- InfoForSetup.exe (PID: 3056)
- AliyunWrapExe.Exe (PID: 3732)
- InfoForSetup.exe (PID: 3100)
- InfoForSetup.exe (PID: 4052)
- InfoForSetup.exe (PID: 3764)
- InfoForSetup.exe (PID: 2056)
- InfoForSetup.exe (PID: 3384)
- drvsetup.exe (PID: 3744)
- AppSetup.exe (PID: 1524)
- SetupSendData2Downloader.exe (PID: 3036)
- Agent.exe (PID: 2636)
- Agent.exe (PID: 3040)
- InfoForSetup.exe (PID: 1720)
- InfoForSetup.exe (PID: 2500)
- InfoForSetup.exe (PID: 2472)
- AliyunWrapExe.Exe (PID: 2744)
- EUinApp.exe (PID: 3072)
- SetupUE.exe (PID: 2836)
- InfoForSetup.exe (PID: 3908)
- InfoForSetup.exe (PID: 2652)
- Loader.exe (PID: 2700)
- TBConsoleUI.exe (PID: 2300)
- TodoBackupService.exe (PID: 3220)
- EuDownload.exe (PID: 3640)
- TodoBackupEnumNetByFD_0.exe (PID: 3360)
- EuDownload.exe (PID: 1900)
- AdvertisingPopup.exe (PID: 1520)
- EuDownload.exe (PID: 1688)
- TrayNotify.exe (PID: 2760)
- TbService.exe (PID: 3160)
- EuDownload.exe (PID: 3748)
- QtWebEngineProcess.exe (PID: 3852)
- WinChkdsk.exe (PID: 340)
Actions looks like stealing of personal data
- TB_Free_easeus.tmp (PID: 1268)
- TBConsoleUI.exe (PID: 2300)
Changes settings of System certificates
- AdvertisingPopup.exe (PID: 1520)
SUSPICIOUS
Executable content was dropped or overwritten
- tb_free_installer.exe (PID: 3984)
- TB_Free_easeus.exe (PID: 2076)
- drvsetup.exe (PID: 3744)
- Agent.exe (PID: 3040)
- TB_Free_easeus.tmp (PID: 1268)
Reads Internet Cache Settings
- AliyunWrapExe.Exe (PID: 3732)
- EDownloader.exe (PID: 2524)
- AliyunWrapExe.Exe (PID: 2744)
Reads internet explorer settings
- EDownloader.exe (PID: 2524)
- TBConsoleUI.exe (PID: 2300)
Reads the Windows organization settings
- TB_Free_easeus.tmp (PID: 1268)
Creates files in the Windows directory
- TB_Free_easeus.tmp (PID: 1268)
- drvsetup.exe (PID: 3744)
- Agent.exe (PID: 3040)
- WinChkdsk.exe (PID: 340)
- TbService.exe (PID: 3160)
Changes IE settings (feature browser emulation)
- TB_Free_easeus.tmp (PID: 1268)
- EUinApp.exe (PID: 3072)
Creates files in the program directory
- drvsetup.exe (PID: 3744)
- Agent.exe (PID: 2636)
- Agent.exe (PID: 3040)
- AliyunWrapExe.Exe (PID: 2744)
- EuDownload.exe (PID: 3640)
- TBConsoleUI.exe (PID: 2300)
- EuDownload.exe (PID: 1688)
- EuDownload.exe (PID: 3748)
- AdvertisingPopup.exe (PID: 1520)
Reads Windows owner or organization settings
- TB_Free_easeus.tmp (PID: 1268)
Creates COM task schedule object
- AppSetup.exe (PID: 1524)
Executed as Windows Service
- Agent.exe (PID: 3040)
- vds.exe (PID: 1920)
- vssvc.exe (PID: 1744)
Creates or modifies windows services
- Agent.exe (PID: 2636)
Removes files from Windows directory
- drvsetup.exe (PID: 3744)
Creates files in the driver directory
- drvsetup.exe (PID: 3744)
Modifies the open verb of a shell class
- AppSetup.exe (PID: 1524)
Low-level read access rights to disk partition
- vds.exe (PID: 1920)
- Agent.exe (PID: 3040)
- TbService.exe (PID: 3160)
Executed via COM
- vdsldr.exe (PID: 2676)
- vdsldr.exe (PID: 2248)
- vdsldr.exe (PID: 4072)
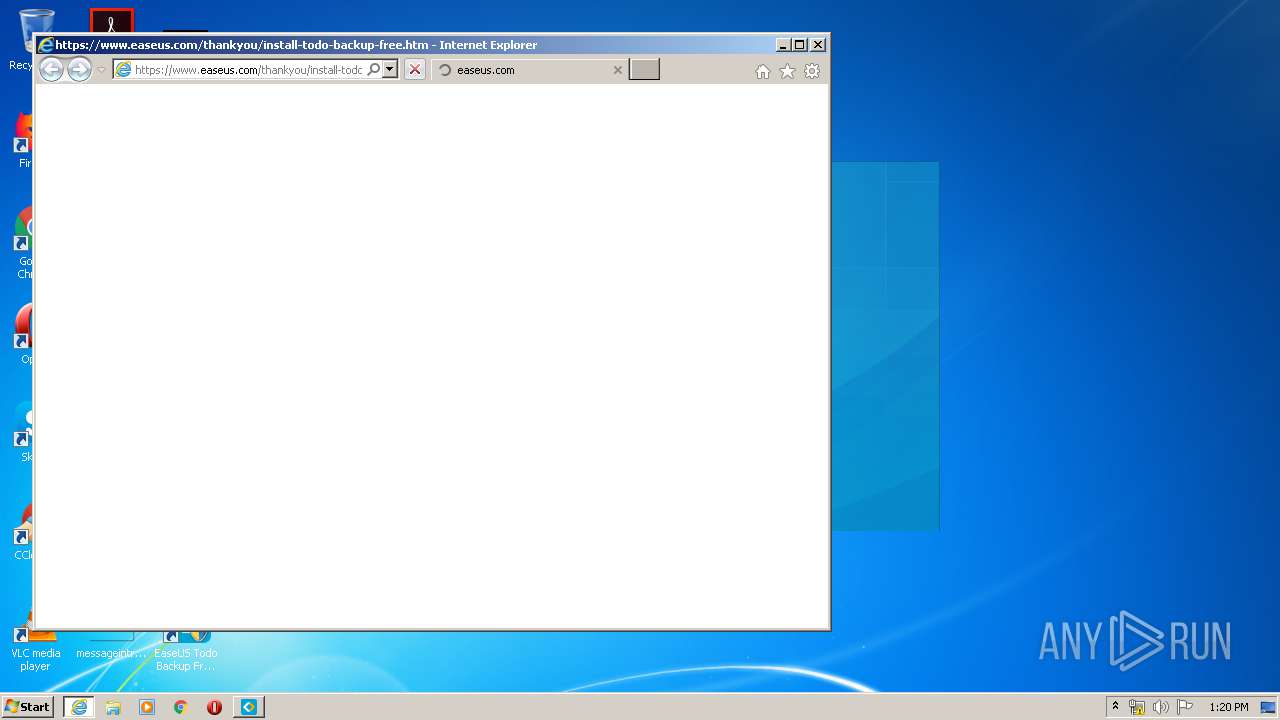
Starts Internet Explorer
- EDownloader.exe (PID: 2524)
Adds / modifies Windows certificates
- AdvertisingPopup.exe (PID: 1520)
INFO
Creates a software uninstall entry
- TB_Free_easeus.tmp (PID: 1268)
Loads dropped or rewritten executable
- TB_Free_easeus.tmp (PID: 1268)
Application was dropped or rewritten from another process
- TB_Free_easeus.tmp (PID: 1268)
Dropped object may contain Bitcoin addresses
- TB_Free_easeus.tmp (PID: 1268)
Reads Internet Cache Settings
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 3308)
Application launched itself
- iexplore.exe (PID: 3300)
Changes internet zones settings
- iexplore.exe (PID: 3300)
Reads the hosts file
- AdvertisingPopup.exe (PID: 1520)
Changes settings of System certificates
- iexplore.exe (PID: 3308)
Reads settings of System Certificates
- iexplore.exe (PID: 3308)
- AdvertisingPopup.exe (PID: 1520)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3308)
Creates files in the program directory
- TB_Free_easeus.tmp (PID: 1268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:48+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:48 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006627 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45224 |
.rdata | 0x00008000 | 0x0000149A | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00708 |
.data | 0x0000A000 | 0x0002AFF8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03532 |
.ndata | 0x00035000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00045000 | 0x00011470 | 0x00011600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.25819 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28733 | 841 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.97202 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.16314 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 3.78931 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 3.93282 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 3.6651 | 1640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.57587 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 5.45655 | 1128 | UNKNOWN | English - United States | RT_ICON |
9 | 3.94819 | 744 | UNKNOWN | English - United States | RT_ICON |
10 | 3.41104 | 296 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
101
Monitored processes
47
Malicious processes
16
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | WinChkdsk.exe \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963} NTFS 756 752 760 0 | C:\Program Files\EaseUS\Todo Backup\bin\WinChkdsk.exe | — | TbService.exe | |||||||||||
User: admin Company: CHENGDU YIWO Tech Development Co., Ltd Integrity Level: HIGH Description: EaseUS Todo Backup WinChkds Application Exit code: 0 Version: 5.8.0.0 Modules
| |||||||||||||||
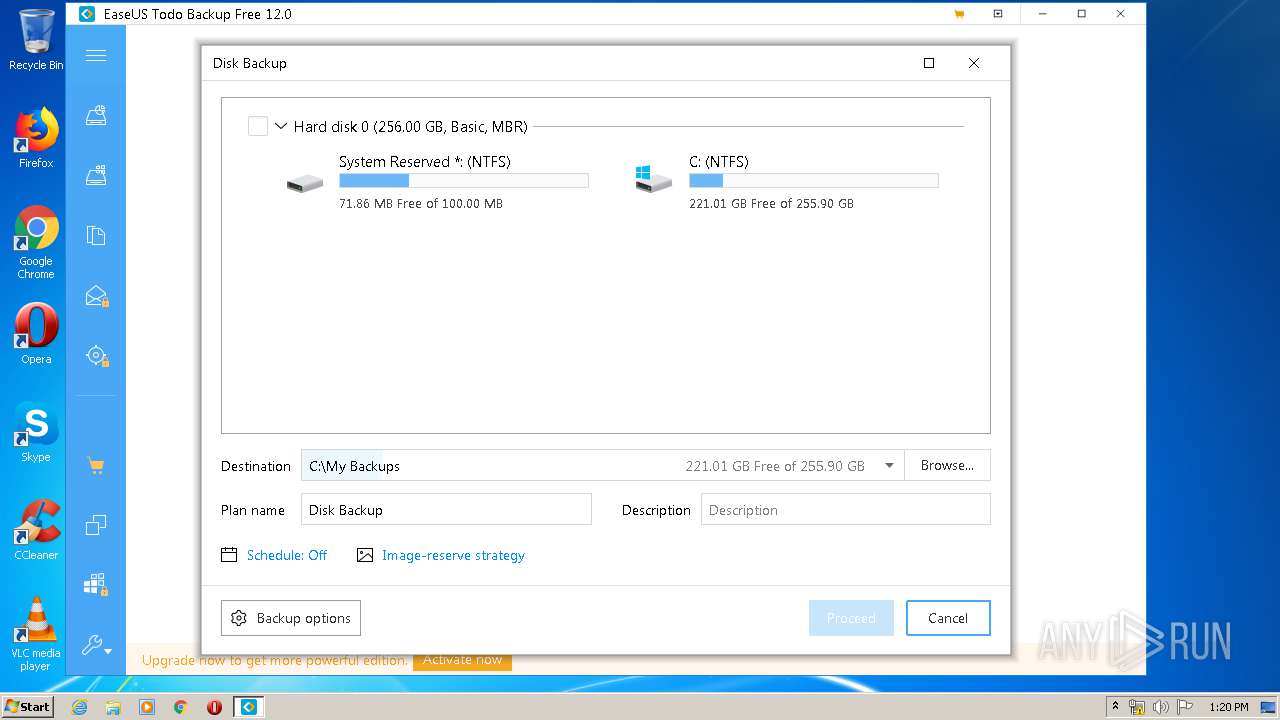
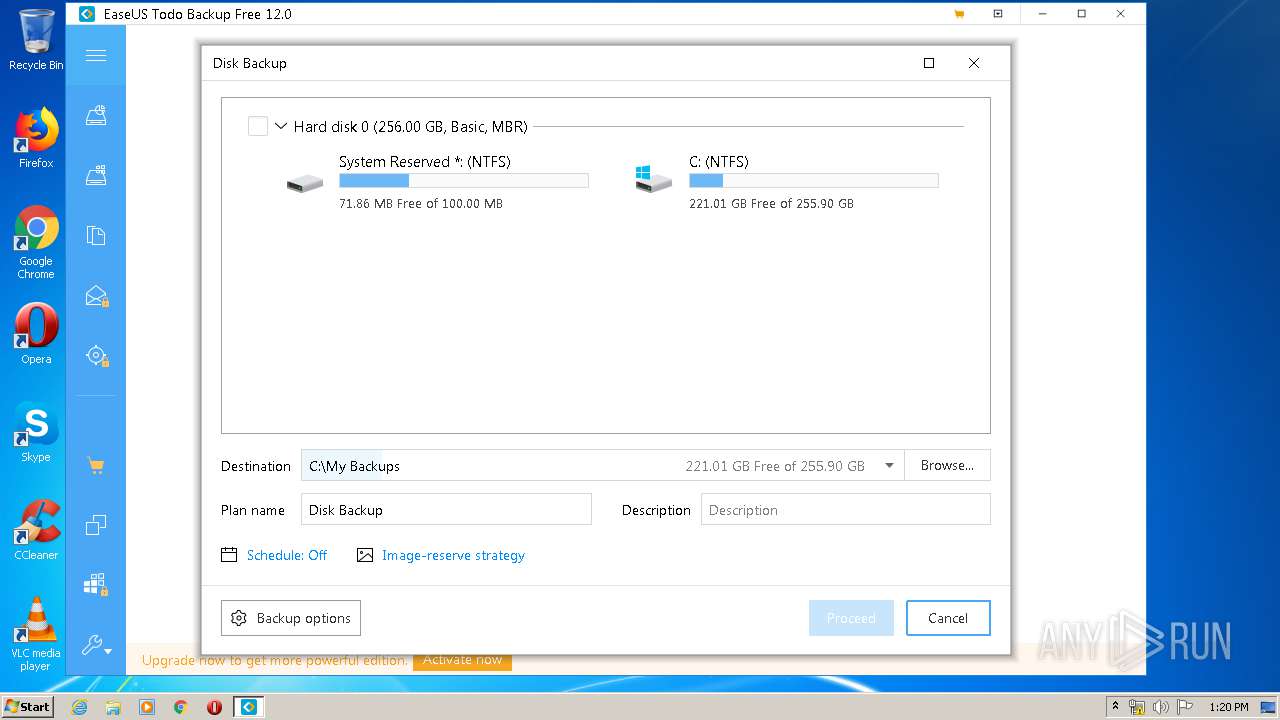
| 1268 | "C:\Users\admin\AppData\Local\Temp\is-CDDHQ.tmp\TB_Free_easeus.tmp" /SL5="$80264,96562474,677376,C:\Users\admin\Desktop\TB_Free_easeus.exe" /verysilent /DIR="C:\Program Files\EaseUS\Todo Backup" /IMAGEPATH="C:\My Backups" /LANG=English agreeImprove=true GUID=S-1-5-21-1302019708-1500728564-335382590-1000 /LOG=C:\Users\admin\AppData\Local\Temp\\easeusproductsetup.log | C:\Users\admin\AppData\Local\Temp\is-CDDHQ.tmp\TB_Free_easeus.tmp | TB_Free_easeus.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1520 | AdvertisingPopup.exe TBP Free | C:\Program Files\EaseUS\Todo Backup\bin\AdvertisingPopup.exe | TBConsoleUI.exe | ||||||||||||
User: admin Company: CHENGDU YIWO Tech Development Co., Ltd Integrity Level: HIGH Description: EaseUS Todo Backup Application Exit code: 0 Version: 12, 0, 0, 0 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\EaseUS\Todo Backup\bin\AppSetup.exe" Install | C:\Program Files\EaseUS\Todo Backup\bin\AppSetup.exe | — | TB_Free_easeus.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\EaseUS\Todo Backup\bin\EuDownload.exe" https://update.easeus.com/update/tb/free/versions.xml "C:\Program Files\EaseUS\Todo Backup\bin/update/versions.xml" 0 "" 1 3636 | C:\Program Files\EaseUS\Todo Backup\bin\EuDownload.exe | TBConsoleUI.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\EaseUS\Todo Backup\bin\InfoForSetup.exe" /Uid S-1-5-21-1302019708-1500728564-335382590-1000 | C:\Program Files\EaseUS\Todo Backup\bin\InfoForSetup.exe | — | TB_Free_easeus.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1740 | /Uid "S-1-5-21-1302019708-1500728564-335382590-1000" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3Free\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1744 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1900 | "C:\Program Files\EaseUS\Todo Backup\bin\EuDownload.exe" https://update.easeus.com/update/tb/innerbuy/tb_home_innerbuy_version_cfg2.ini "C:\Users\admin\AppData\Local\Temp\euphtupdate.ini" 0 "" 1 2816 | C:\Program Files\EaseUS\Todo Backup\bin\EuDownload.exe | TBConsoleUI.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1920 | C:\Windows\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 621
Read events
1 569
Write events
1 042
Delete events
10
Modification events
| (PID) Process: | (3732) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3732) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3732) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3732) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3732) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3732) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3732) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2524) EDownloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2524) EDownloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2524) EDownloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
1 054
Suspicious files
116
Text files
4 123
Unknown types
175
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3984 | tb_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3Free\Italian.ini | text | |
MD5:— | SHA256:— | |||
| 3984 | tb_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3Free\LanguageTransfor.ini | text | |
MD5:— | SHA256:— | |||
| 3984 | tb_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3Free\Japanese.ini | text | |
MD5:— | SHA256:— | |||
| 3984 | tb_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3Free\Portuguese.ini | text | |
MD5:— | SHA256:— | |||
| 3984 | tb_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3Free\Spanish.ini | text | |
MD5:— | SHA256:— | |||
| 3984 | tb_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3Free\Polish.ini | text | |
MD5:— | SHA256:— | |||
| 3984 | tb_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3Free\aliyun\AliyunConfig.ini | text | |
MD5:— | SHA256:— | |||
| 3732 | AliyunWrapExe.Exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3Free\aliyun\tempInfo.web | — | |
MD5:— | SHA256:— | |||
| 3984 | tb_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3Free\EDownloader.exe | executable | |
MD5:— | SHA256:— | |||
| 3984 | tb_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3Free\Chinese.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
11
DNS requests
3
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2524 | EDownloader.exe | GET | — | 205.185.216.10:80 | http://download.easeus.com/free/tb_free_12.0.exe | US | — | — | malicious |
2524 | EDownloader.exe | GET | — | 205.185.216.10:80 | http://download.easeus.com/free/tb_free_12.0.exe | US | — | — | malicious |
2524 | EDownloader.exe | GET | — | 205.185.216.10:80 | http://download.easeus.com/free/tb_free_12.0.exe | US | — | — | malicious |
2524 | EDownloader.exe | GET | — | 205.185.216.10:80 | http://download.easeus.com/free/tb_free_12.0.exe | US | — | — | malicious |
2524 | EDownloader.exe | POST | 200 | 205.185.216.10:80 | http://download.easeus.com/api/index.php/Home/Index/productInstall/ | US | text | 425 b | malicious |
3732 | AliyunWrapExe.Exe | GET | 200 | 216.92.47.198:80 | http://track.easeus.com/product/index.php?c=main&a=getstatus&pid=0 | US | binary | 1 b | suspicious |
3732 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_tbp_downloader/shards/lb | US | — | — | malicious |
3732 | AliyunWrapExe.Exe | POST | — | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_tbp_downloader/shards/lb | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2524 | EDownloader.exe | 205.185.216.10:80 | download.easeus.com | Highwinds Network Group, Inc. | US | whitelisted |
3732 | AliyunWrapExe.Exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
3732 | AliyunWrapExe.Exe | 47.252.97.15:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.easeus.com |
| malicious |
track.easeus.com |
| suspicious |
easeusinfo.us-east-1.log.aliyuncs.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2524 | EDownloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2524 | EDownloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
Agent.exe | Init Log |
Agent.exe | Ldq : Agent start install! |
Agent.exe |
Ldq : Agent call CreateService!
|
Agent.exe |
Ldq : Agent call CreateService is success!
|
Agent.exe | Init Log |
Agent.exe |
Ldq : Agent set service description!
|
Agent.exe |
Ldq : Agent entry ServiceMain!
|
Agent.exe |
Ldq : Agent start create model!
|
Agent.exe | Failed to Load lib (Err=0x12529002) CheckTool |
Agent.exe | socket closed
|