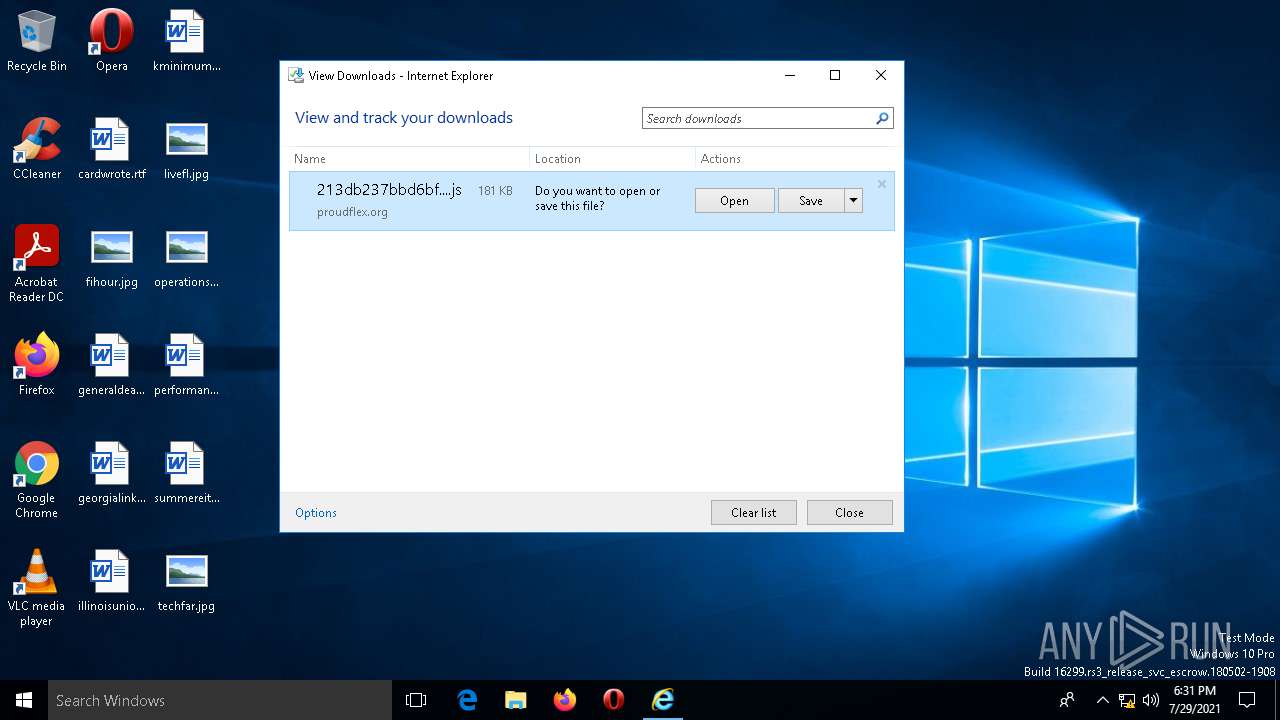
| URL: | https://proudflex.org/213db237bbd6bf854a.js |
| Full analysis: | https://app.any.run/tasks/c417000b-5965-43bb-9cd3-27af388fb2d0 |
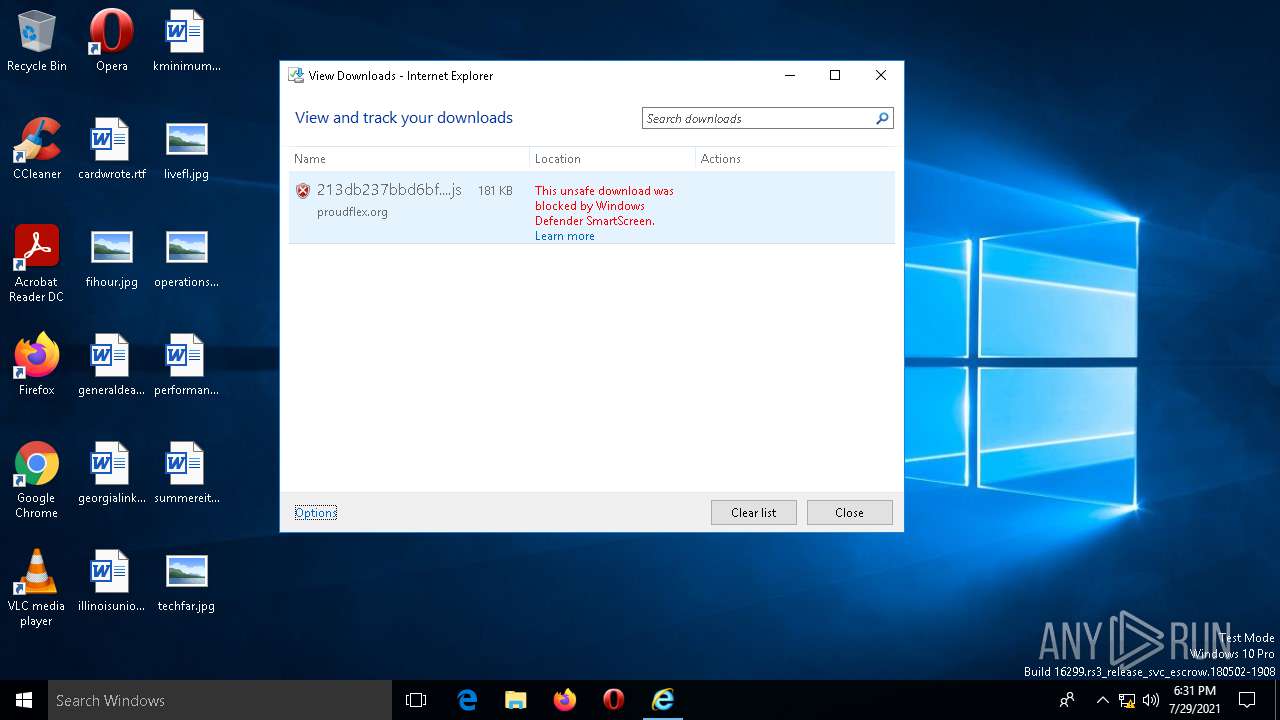
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2021, 18:31:33 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MD5: | 153E4643C12808119477A39F9241D93B |
| SHA1: | 30114CA1DAFA220DAE6928FB6772ACA00D7DDD8D |
| SHA256: | AFF86BDC7162AC2FD7A89A5353D5015BA69B7CD6129C863D486F954C20C2B3BA |
| SSDEEP: | 3:N8TKQBqE5XUGFBTHDdtS:2HDXUcBTHzS |
MALICIOUS
Scans artifacts that could help determine the target
- iexplore.exe (PID: 412)
- MicrosoftEdgeCP.exe (PID: 4244)
- MicrosoftEdgeCP.exe (PID: 5288)
- MicrosoftEdge.exe (PID: 1860)
SUSPICIOUS
Executed via COM
- ApplicationFrameHost.exe (PID: 1596)
- MicrosoftEdge.exe (PID: 1860)
- browser_broker.exe (PID: 3168)
- MicrosoftEdgeCP.exe (PID: 4244)
- MicrosoftEdgeCP.exe (PID: 5288)
- MicrosoftEdgeCP.exe (PID: 3020)
- MicrosoftEdgeCP.exe (PID: 5168)
- MicrosoftEdgeCP.exe (PID: 6000)
Reads Microsoft Outlook installation path
- IEXPLORE.EXE (PID: 2716)
Reads the computer name
- MicrosoftEdge.exe (PID: 1860)
- MicrosoftEdgeCP.exe (PID: 4244)
- browser_broker.exe (PID: 3168)
- MicrosoftEdgeCP.exe (PID: 3020)
- MicrosoftEdgeCP.exe (PID: 5288)
- MicrosoftEdgeCP.exe (PID: 5168)
- MicrosoftEdgeCP.exe (PID: 6000)
Checks supported languages
- MicrosoftEdge.exe (PID: 1860)
- MicrosoftEdgeCP.exe (PID: 3020)
- browser_broker.exe (PID: 3168)
- MicrosoftEdgeCP.exe (PID: 4244)
- MicrosoftEdgeCP.exe (PID: 5288)
- MicrosoftEdgeCP.exe (PID: 5168)
- MicrosoftEdgeCP.exe (PID: 6000)
Reads Environment values
- MicrosoftEdge.exe (PID: 1860)
INFO
Checks supported languages
- IEXPLORE.EXE (PID: 2716)
- ApplicationFrameHost.exe (PID: 1596)
- iexplore.exe (PID: 412)
Reads the computer name
- IEXPLORE.EXE (PID: 2716)
- iexplore.exe (PID: 412)
- ApplicationFrameHost.exe (PID: 1596)
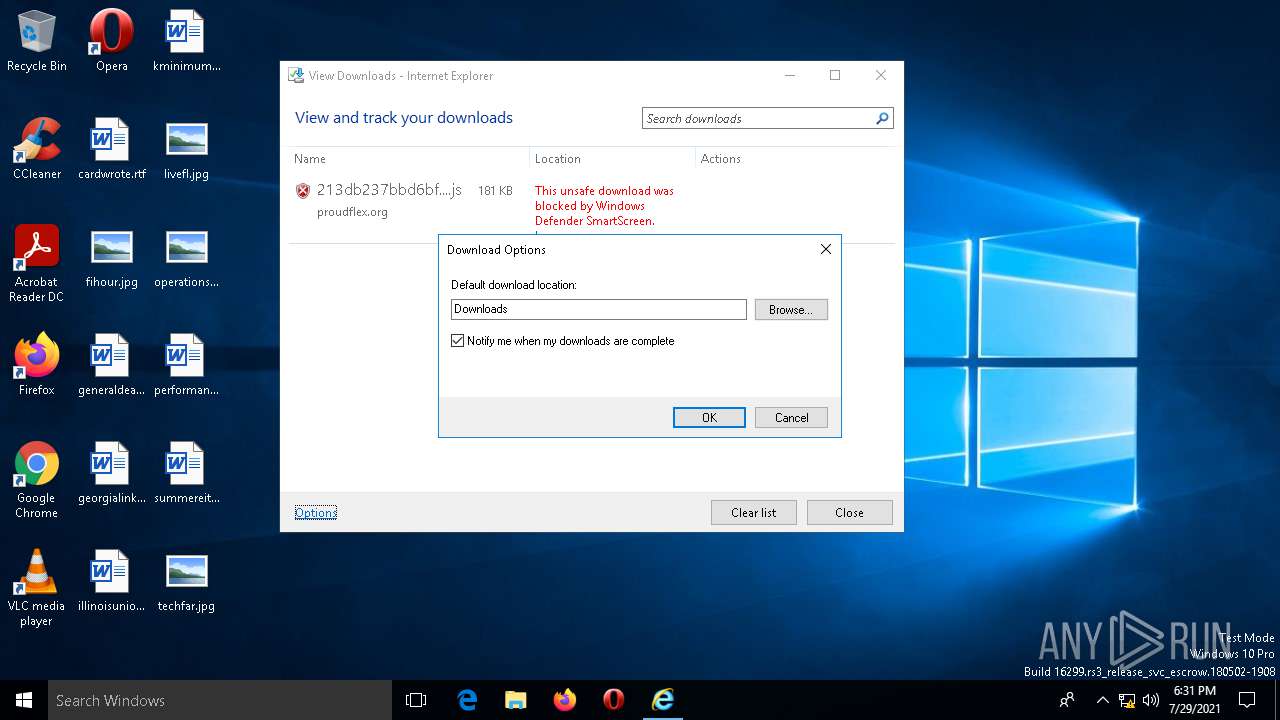
Modifies the phishing filter of IE
- iexplore.exe (PID: 412)
Checks Windows Trust Settings
- IEXPLORE.EXE (PID: 2716)
- iexplore.exe (PID: 412)
- MicrosoftEdgeCP.exe (PID: 4244)
- MicrosoftEdgeCP.exe (PID: 5288)
Reads the software policy settings
- IEXPLORE.EXE (PID: 2716)
- iexplore.exe (PID: 412)
- MicrosoftEdgeCP.exe (PID: 4244)
- MicrosoftEdgeCP.exe (PID: 5288)
Reads settings of System Certificates
- iexplore.exe (PID: 412)
- IEXPLORE.EXE (PID: 2716)
- MicrosoftEdgeCP.exe (PID: 4244)
- MicrosoftEdgeCP.exe (PID: 5288)
Reads the date of Windows installation
- iexplore.exe (PID: 412)
Changes internet zones settings
- iexplore.exe (PID: 412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
102
Monitored processes
10
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 412 | "C:\Program Files\internet explorer\iexplore.exe" "https://proudflex.org/213db237bbd6bf854a.js" | C:\Program Files\internet explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1596 | C:\WINDOWS\system32\ApplicationFrameHost.exe -Embedding | C:\WINDOWS\system32\ApplicationFrameHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Application Frame Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1860 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdge.exe" -ServerName:MicrosoftEdge.AppXdnhjhccw3zf0j06tkg3jtqr00qdm0khc.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdge.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2716 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:412 CREDAT:9474 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3020 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 0 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3168 | C:\WINDOWS\system32\browser_broker.exe -Embedding | C:\WINDOWS\system32\browser_broker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Browser_Broker Exit code: 2147500037 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4244 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 1 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5168 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 0 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5288 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 0 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6000 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 0 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 334
Read events
20 796
Write events
532
Delete events
6
Modification events
| (PID) Process: | (412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 956341420 | |||
| (PID) Process: | (412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 148313293 | |||
| (PID) Process: | (412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 239206604 | |||
| (PID) Process: | (412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30901416 | |||
| (PID) Process: | (412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
0
Suspicious files
8
Text files
129
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 412 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\SmartScreenCache.dat | binary | |
MD5:8F4162F8B5A527928EC303C0ECE90644 | SHA256:65AAEAE09263570F5D92364128828A0AAC5DEB926CC51FF562581617DDBE6723 | |||
| 2716 | IEXPLORE.EXE | C:\Users\admin\Downloads\213db237bbd6bf854a.js.wn3yrwd.partial | text | |
MD5:581066C8FDBC554DD2E653EAD77B6E8E | SHA256:C977FC22C41CC9B3B42D2ACBD552DFA9D2F7FC74D10DAC04FC2C23C5A181D7E2 | |||
| 2716 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\APFYKMZ9\213db237bbd6bf854a[1].js | text | |
MD5:4A33997F07989B688D3142ED7C2BBF6F | SHA256:A31B915EFCDD0CC5313AF1F08FE2EDB4CA607C4D57E362B058F4D193CE241023 | |||
| 412 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{39FE9BEB-F09B-11EB-B47A-18F7786F96EE}.dat | binary | |
MD5:A0FDAC92596783BFC5CEE6B474787654 | SHA256:0C39C0485BD1B9956198B5192F2256216D98EA37BB8F5715987DE68389806590 | |||
| 412 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5A4663C9F685386D.TMP | gmc | |
MD5:02E33B1845FF390318913C4B579AB3F5 | SHA256:34C22CA99A7A7A758967C225A58FED71D0C1EA058C3189C64142268D7230EFEC | |||
| 5288 | MicrosoftEdgeCP.exe | C:\Users\admin\AppData\Local\Packages\microsoft.microsoftedge_8wekyb3d8bbwe\AC\#!002\MicrosoftEdge\Cache\RCOFU4AK\dhp[1].htm | html | |
MD5:4B5E234553BAA55E5047FB6074C4BF02 | SHA256:746DEE35D771D735DC06EAA8C72085CE670A04F377B34798EB2D3EE81354E2F9 | |||
| 412 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7BDA91CFFEF11F45.TMP | gmc | |
MD5:B65215F801A4791284B16776AE6AE027 | SHA256:EDB046B5829C48C06914FFF675471CA9115FD07EFA1572AF45134B97DD7F2175 | |||
| 412 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{39FE9BE9-F09B-11EB-B47A-18F7786F96EE}.dat | binary | |
MD5:D6CAE994321F4FCE10FAAD21C591CC07 | SHA256:3F05FD26734E8F309729496B1D212C99A5A084B31AF0F583DE982AA2DD87BC18 | |||
| 1860 | MicrosoftEdge.exe | C:\Users\admin\AppData\Local\Packages\microsoft.microsoftedge_8wekyb3d8bbwe\AC\MicrosoftEdge\User\Default\DataStore\Data\nouser1\120712-0049\DBStore\spartan.edb | edb | |
MD5:152E6E9B5F09BF36011919414219D43D | SHA256:78998C63CCFDD8D789409CF3C5504487831C04D45D6D625DC40BEA64B42566F3 | |||
| 5288 | MicrosoftEdgeCP.exe | C:\Users\admin\AppData\Local\Packages\microsoft.microsoftedge_8wekyb3d8bbwe\AC\#!002\MicrosoftEdge\Cache\RCOFU4AK\AABiyAn[1].png | image | |
MD5:971232A1FF99B8DB0407002BC34E5571 | SHA256:0CB2ED0969537B3D538940FC991D4E470D6FA49353F6A05268D3EDEDE5A716DF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
219
TCP/UDP connections
115
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
412 | iexplore.exe | POST | 200 | 52.178.182.73:443 | https://t.urs.microsoft.com/urstelemetry.asmx?MSTel-Client-Key=mo8yRYlG8YY%2bt2dC5K9R6w%3d%3d&MSTel-MAC=OC3Us7RmFN8%3d | IE | text | 159 b | whitelisted |
412 | iexplore.exe | POST | 200 | 52.178.182.73:443 | https://urs.microsoft.com/urs.asmx?MSURS-Client-Key=mOOTtRA5VuYSOtB%2ba0NUbQ%3d%3d&MSURS-MAC=t9Imk1j5CnY%3d | IE | text | 1.08 Kb | whitelisted |
2716 | IEXPLORE.EXE | POST | 200 | 20.190.160.132:443 | https://login.live.com/RST2.srf | US | xml | 10.5 Kb | whitelisted |
2716 | IEXPLORE.EXE | POST | 200 | 20.190.160.132:443 | https://login.live.com/RST2.srf | US | xml | 9.87 Kb | whitelisted |
2284 | svchost.exe | GET | 200 | 204.79.197.203:443 | https://www.msn.com/spartan/dhp?locale=en-US&market=US&enableregulatorypsm=0&enablecpsm=0&ishostisolationenforced=0&targetexperience=default | US | html | 294 Kb | whitelisted |
2284 | svchost.exe | GET | 302 | 13.66.39.88:443 | https://microsoftedgetips.microsoft.com/?source=welcome | US | html | 120 b | whitelisted |
2284 | svchost.exe | GET | 302 | 104.111.242.51:443 | https://go.microsoft.com/fwlink/?LinkId=525773 | NL | — | — | whitelisted |
2284 | svchost.exe | GET | 302 | 40.71.11.133:443 | https://microsoftedgewelcome.microsoft.com/redirect/?source=firstrun | US | html | 154 b | whitelisted |
2284 | svchost.exe | GET | 200 | 23.32.238.171:443 | https://static-spartan-neu-s-msn-com.akamaized.net/spartan/en-us/_ssc/css/ac12fb0b-4e64c3a/kerneldhp-f44ca46e.css?ver=20210723_22747471&fdhead=1s-bing-news,1s-mobauthcf,1s-winblisp1,bbh20200521msncf,btrecrow1,modmmhac,msnallexpusers,onetrustpoplive,prg-1sw-scronc,prg-adspeek,prg-rotctrl,prg-wpo-hp750,prg-wpo-hpads,prg-wpo-hpads750,prg-wpo-olypc,vebudumu04302020 | US | text | 108 Kb | whitelisted |
2284 | svchost.exe | GET | 200 | 23.32.238.171:443 | https://static-spartan-neu-s-msn-com.akamaized.net/_h/975a7d20/webcore/externalscripts/jquery/jquery-2.1.1.min.js | US | text | 82.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
412 | iexplore.exe | 52.178.182.73:443 | urs.microsoft.com | Microsoft Corporation | IE | suspicious |
— | — | 20.190.160.73:443 | — | Microsoft Corporation | US | suspicious |
— | — | 104.111.242.51:443 | go.microsoft.com | Akamai International B.V. | NL | unknown |
3328 | svchost.exe | 51.103.5.159:443 | — | Microsoft Corporation | GB | whitelisted |
2284 | svchost.exe | 20.190.160.132:443 | — | Microsoft Corporation | US | suspicious |
— | — | 40.71.11.133:443 | microsoftedgewelcome.microsoft.com | Microsoft Corporation | US | suspicious |
— | — | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
— | — | 13.66.39.88:443 | microsoftedgetips.microsoft.com | Microsoft Corporation | US | unknown |
— | — | 23.32.238.171:443 | static-spartan-neu-s-msn-com.akamaized.net | XO Communications | US | suspicious |
— | — | 184.30.21.171:443 | www.microsoft.com | GTT Communications Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
proudflex.org |
| malicious |
urs.microsoft.com |
| whitelisted |
t.urs.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
microsoftedgewelcome.microsoft.com |
| whitelisted |
microsoftedgetips.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
static-spartan-neu-s-msn-com.akamaized.net |
| whitelisted |
img-s-msn-com.akamaized.net |
| whitelisted |