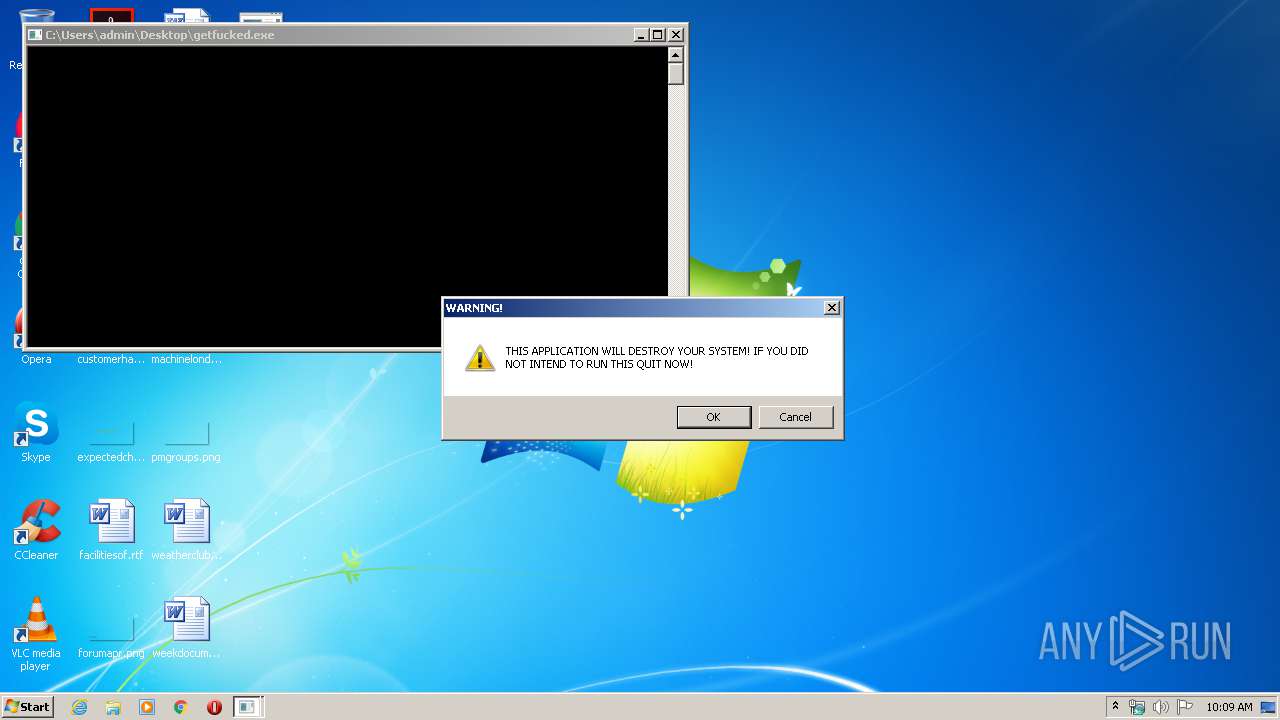
| File name: | getfucked.exe |
| Full analysis: | https://app.any.run/tasks/a388ad8d-ee16-426b-be81-da98a83f93ca |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2020, 10:09:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 397F61A253649EDAE532B903AB831A3F |
| SHA1: | E18A36FE1AA1967D02DEE4B21C5B98D9C476A798 |
| SHA256: | AFF30A8E02CB9E759503DDF055E8F07DFBE29299ADA934B8E7C5A1BA90240E6F |
| SSDEEP: | 192:wdPyOgj3BjqOW+tmzUeXruqDJDzwOak4oDj0jOLYI6E1LYQMy5bE53z6nVGNsWv2:wZyJ3NY3lz1ak4Ij0jtIGy5byNsWv |
MALICIOUS
Loads the Task Scheduler COM API
- rundll32.exe (PID: 3740)
Changes internet zones settings
- ie4uinit.exe (PID: 1392)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- ie4uinit.exe (PID: 1392)
- rundll32.exe (PID: 3740)
Executed as Windows Service
- taskhost.exe (PID: 2312)
Creates files in the program directory
- ie4uinit.exe (PID: 1392)
- chrmstp.exe (PID: 404)
Reads Internet Cache Settings
- taskhost.exe (PID: 2312)
Writes to a desktop.ini file (may be used to cloak folders)
- ie4uinit.exe (PID: 1392)
Application launched itself
- rundll32.exe (PID: 3740)
INFO
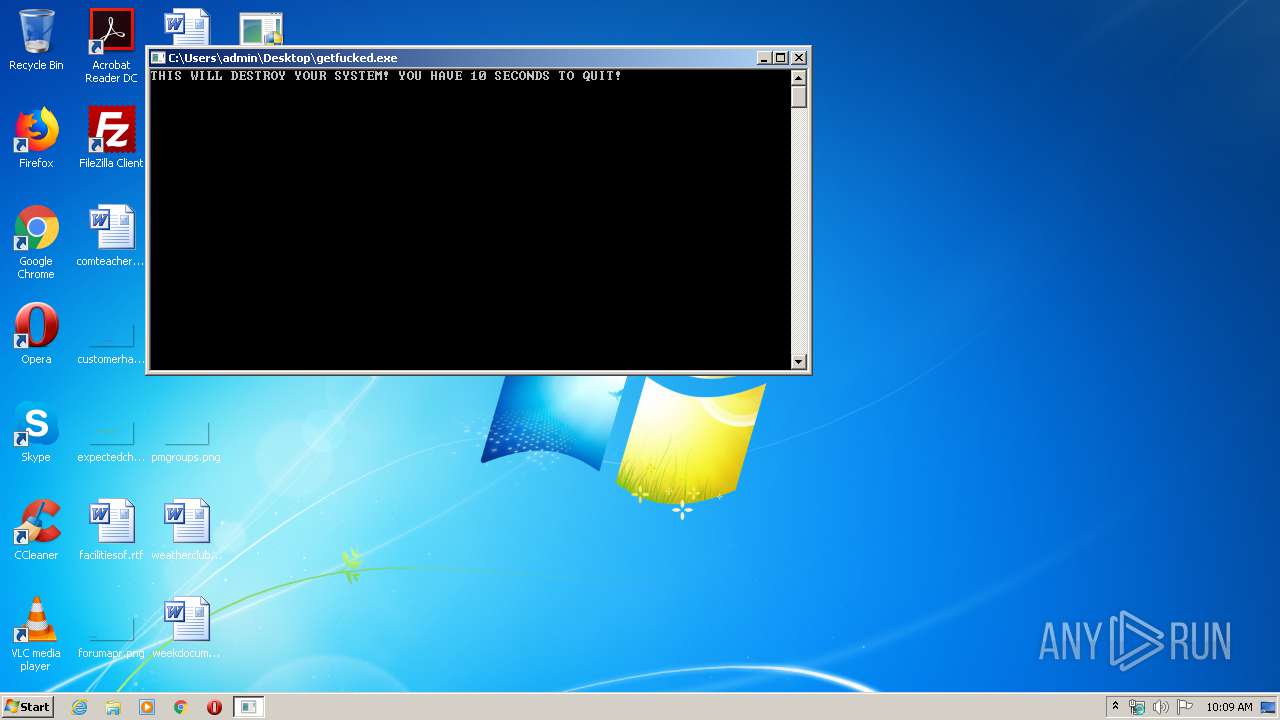
Manual execution by user
- ie4uinit.exe (PID: 1392)
- ie4uinit.exe (PID: 1388)
- chrmstp.exe (PID: 404)
- IMEKLMG.EXE (PID: 3868)
- IMEKLMG.EXE (PID: 4032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:08 11:08:37+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.24 |
| CodeSize: | 5120 |
| InitializedDataSize: | 7168 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x17d2 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 08-Mar-2020 10:08:37 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 08-Mar-2020 10:08:37 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00001284 | 0x00001400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.99622 |
.rdata | 0x00003000 | 0x0000114A | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.77879 |
.data | 0x00005000 | 0x00000400 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.75703 |
.rsrc | 0x00006000 | 0x000001E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75224 |
.reloc | 0x00007000 | 0x00000258 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.47476 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
VCRUNTIME140.dll |
api-ms-win-crt-heap-l1-1-0.dll |
api-ms-win-crt-locale-l1-1-0.dll |
api-ms-win-crt-math-l1-1-0.dll |
api-ms-win-crt-runtime-l1-1-0.dll |
api-ms-win-crt-stdio-l1-1-0.dll |
Total processes
66
Monitored processes
15
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Program Files\Google\Chrome\Application\75.0.3770.100\Installer\chrmstp.exe" --configure-user-settings --verbose-logging --system-level | C:\Program Files\Google\Chrome\Application\75.0.3770.100\Installer\chrmstp.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Installer Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | C:\Windows\System32\rundll32 advpack.dll,LaunchINFSectionEx C:\Windows\system32\ieuinit.inf,Install,,36 | C:\Windows\System32\rundll32.exe | — | ie4uinit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1388 | "C:\Windows\System32\ie4uinit.exe" -DisableSSL3 | C:\Windows\System32\ie4uinit.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1392 | "C:\Windows\System32\ie4uinit.exe" -UserConfig | C:\Windows\System32\ie4uinit.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1500 | "C:\Users\admin\Desktop\getfucked.exe" | C:\Users\admin\Desktop\getfucked.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
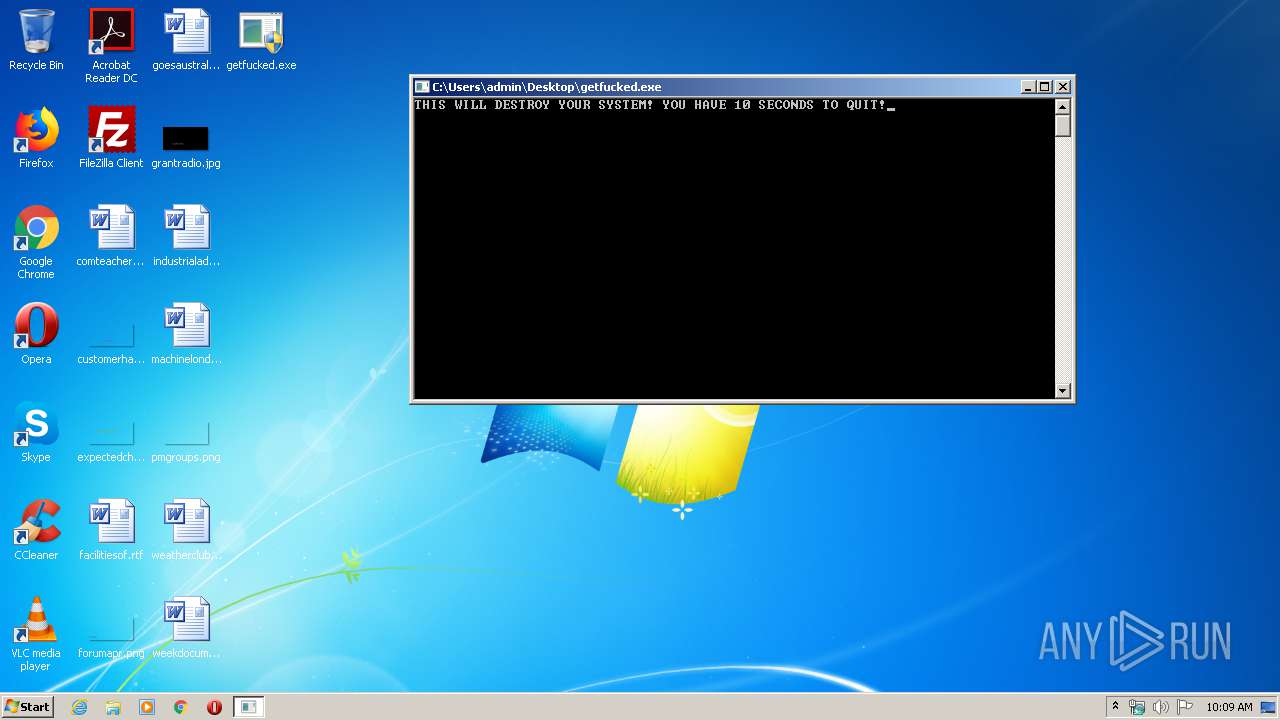
| 2120 | "C:\Users\admin\Desktop\getfucked.exe" | C:\Users\admin\Desktop\getfucked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2312 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2340 | C:\Windows\System32\ie4uinit.exe -ClearIconCache | C:\Windows\System32\ie4uinit.exe | — | ie4uinit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Google\Chrome\Application\75.0.3770.100\Installer\chrmstp.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Windows\TEMP\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0xd0,0xd8,0xdc,0xcc,0xe0,0x4e2238,0x4e2248,0x4e2254 | C:\Program Files\Google\Chrome\Application\75.0.3770.100\Installer\chrmstp.exe | — | chrmstp.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Installer Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3460 | "C:\Program Files\Common Files\Microsoft Shared\IME14\IMEKR\imkrmig.exe" | C:\Program Files\Common Files\Microsoft Shared\IME14\IMEKR\imkrmig.exe | — | IMEKLMG.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft IME 2010 Exit code: 0 Version: 14.0.4734.1000 Modules
| |||||||||||||||
Total events
618
Read events
305
Write events
309
Delete events
4
Modification events
| (PID) Process: | (1392) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Suggested Sites |
| Operation: | write | Name: | LogFileFolder |
Value: C:\Users\Administrator\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low | |||
| (PID) Process: | (1392) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\CLSID\{871C5380-42A0-1069-A2EA-08002B30309D}\ShellFolder |
| Operation: | write | Name: | Attributes |
Value: 0 | |||
| (PID) Process: | (1392) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Active Setup\Installed Components\>{26923b43-4d38-484f-9b9e-de460746276c} |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (1392) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\BrowserEmulation |
| Operation: | write | Name: | CVListTTL |
Value: 0 | |||
| (PID) Process: | (1392) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\Scripts\3 |
| Operation: | write | Name: | IEPropFontName |
Value: Times New Roman | |||
| (PID) Process: | (1392) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\Scripts\3 |
| Operation: | write | Name: | IEFixedFontName |
Value: Courier New | |||
| (PID) Process: | (1392) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\Scripts\4 |
| Operation: | write | Name: | IEPropFontName |
Value: Times New Roman | |||
| (PID) Process: | (1392) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\Scripts\4 |
| Operation: | write | Name: | IEFixedFontName |
Value: Courier New | |||
| (PID) Process: | (1392) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\Scripts\5 |
| Operation: | write | Name: | IEPropFontName |
Value: Times New Roman | |||
| (PID) Process: | (1392) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\Scripts\5 |
| Operation: | write | Name: | IEFixedFontName |
Value: Courier New | |||
Executable files
0
Suspicious files
6
Text files
62
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1392 | ie4uinit.exe | C:\Users\Administrator\AppData\Local\Temp\RGIAFB1.tmp | — | |
MD5:— | SHA256:— | |||
| 1392 | ie4uinit.exe | C:\Users\Administrator\AppData\Local\Temp\RGIAFD1.tmp | — | |
MD5:— | SHA256:— | |||
| 1392 | ie4uinit.exe | C:\Users\Administrator\AppData\Local\Temp\RGIB001.tmp | — | |
MD5:— | SHA256:— | |||
| 1392 | ie4uinit.exe | C:\Users\Administrator\AppData\Local\Temp\RGIB060.tmp | — | |
MD5:— | SHA256:— | |||
| 1392 | ie4uinit.exe | C:\Users\Administrator\AppData\Local\Temp\RGIB070.tmp | — | |
MD5:— | SHA256:— | |||
| 1392 | ie4uinit.exe | C:\Users\Administrator\AppData\Local\Temp\RGIB0CF.tmp | — | |
MD5:— | SHA256:— | |||
| 2312 | taskhost.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\WebCache\V01tmp.log | — | |
MD5:— | SHA256:— | |||
| 2312 | taskhost.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\WebCache\V01.log | — | |
MD5:— | SHA256:— | |||
| 2312 | taskhost.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | — | |
MD5:— | SHA256:— | |||
| 3940 | RunDll32.exe | C:\Users\Administrator\AppData\Local\Microsoft\Feeds Cache\3AVRJXZV\fwlink[1] | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report